[CVE] Oracle Fusion Middleware Unauthenticated Remote Code Execution CVE-2026-21992
Report Type
CVE Vulnerability Assessment
Threat Category
Unauthenticated Remote Code Execution (RCE)
Assessment Date
March 30, 2026
Primary Impact Domain
Identity and Middleware Control Systems (Enterprise Identity, Authentication, and Service Integration Layers)
BLUF
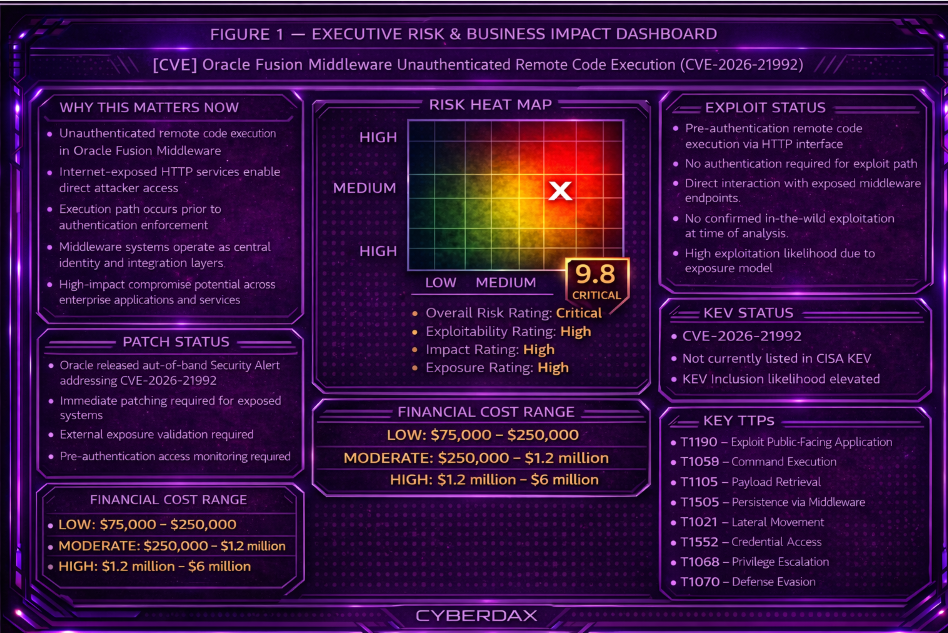
Unauthenticated remote code execution in Oracle Fusion Middleware creates a direct enterprise risk by exposing identity and integration layers to external compromise. The vulnerability enables attacker-controlled execution through internet-accessible HTTP interfaces without requiring authentication, bypassing trust boundaries within middleware architectures. Exploitability is high due to unauthenticated access, internet-facing exposure, and direct execution within middleware service context. Immediate executive action is required to patch affected systems, validate external exposure, and implement monitoring controls for pre-authentication activity.
Executive Risk Translation
This vulnerability creates a direct pathway to enterprise-wide identity compromise, operational disruption, and loss of trust in critical systems, resulting in financial loss, service disruption, and governance-level risk tied to identity system compromise.
S3 Why This Matters Now
· Unauthenticated remote code execution in Oracle Fusion Middleware
· Internet-exposed HTTP services enable direct attacker access
· Execution path occurs prior to authentication enforcement
· Middleware systems operate as central identity and integration layers
· High-impact compromise potential across enterprise applications and services
S4 Key Judgments
· The vulnerability presents a pre-authentication remote code execution condition that bypasses identity-based defenses
· Internet-exposed systems are at immediate risk of exploitation
· Middleware compromise creates disproportionate enterprise impact due to trust-layer positioning
· Detection requires correlation across network, endpoint, and application telemetry
· Lack of pre-authentication controls increases likelihood of rapid attacker adoption
S5 Executive Risk Summary
CVE-2026-21992 enables attacker-controlled execution within Oracle Fusion Middleware through unauthenticated HTTP interface access. The vulnerability allows attacker-supplied input to trigger execution within middleware services that underpin identity, authentication, and service integration.
Because these systems operate at the center of enterprise trust relationships, successful exploitation can result in identity compromise, unauthorized service interaction, and disruption of dependent applications. The absence of an authentication boundary prior to execution materially increases both likelihood and impact, particularly in environments with internet-exposed or insufficiently segmented middleware deployments.
S6 Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
· LOW: $75,000 – $250,000 — Limited compromise of isolated middleware instance with minimal downstream impact
· MODERATE: $250,000 – $1.2 million — Identity disruption, service degradation, and partial enterprise workflow impact
· HIGH: $1.2 million – $6 million — Widespread identity compromise, service disruption, and enterprise operational impact
S6A Key Cost Drivers
· Central role of middleware in authentication and service orchestration
· Identity and credential exposure risk
· Scope of internet-facing middleware deployments
· Degree of integration across enterprise systems
· Detection latency and response readiness
S6B Compliance and Risk Context
Compliance Exposure Indicator
High exposure for organizations subject to identity security, access control, and service availability requirements
Risk Register Entry
Unauthenticated remote code execution in Oracle Fusion Middleware enabling compromise of identity and integration layers
Annualized Risk Exposure
Elevated due to high exploitability, centralized system role, and potential for enterprise-wide impact
S7 Executive Risk Scoring
Overall Risk Rating
Critical
Exploitability Rating
High
Impact Rating
High
Exposure Rating
High
Exploitation Exposure Probability (EEP)
High due to unauthenticated exploitability and internet-exposed attack surface
EEP is a forward-looking analytic measure of operational exploitation potential, not a statement of confirmed exploitation, KEV inclusion, or incident activity.
KEV Alignment Status
Not currently listed
KEV Likelihood Assessment
High likelihood due to unauthenticated exploitability, internet exposure conditions, and high-value identity-layer targeting
Risk Prioritization Tier
Tier 1 — Immediate action required
Operational Priority
Immediate patching and exposure validation required for all affected systems
S8 Bottom Line for Executives
This vulnerability enables unauthenticated attackers to execute code within core enterprise middleware systems, compromising identity control pathways and exposing the organization to high-impact compromise. Immediate remediation, exposure validation, and monitoring are required to reduce exploitation risk and prevent downstream operational disruption.
S9 Board-Level Takeaway
This vulnerability represents a governance-level risk due to its potential to compromise systems that underpin identity, authentication, and enterprise service integration. Board-level oversight is required to ensure timely remediation, validation of control effectiveness, and accountability for managing enterprise exposure and operational risk, with executive accountability for remediation and exposure validation.
S10 CVE Overview
CVE
CVE-2026-21992
Vendor
Oracle
Product Family
Oracle Fusion Middleware
Affected Products
Oracle Identity Manager
Oracle Web Services Manager
Affected Components
REST Web Services
Web Services Security
Vulnerability Class
Missing Authentication for Critical Function (CWE-306)
Impact
Unauthenticated remote attackers with network access via HTTP can execute code and fully compromise affected systems, resulting in product takeover and potential downstream compromise of identity and service trust functions.
S11 Affected Product / Platform Overview
Oracle Identity Manager is an identity governance and provisioning platform used to manage user lifecycle, access policies, and privileged account workflows across enterprise environments. Oracle Web Services Manager provides policy enforcement and security controls for service-to-service communication within Oracle Fusion Middleware environments.
These components are commonly deployed as part of enterprise middleware infrastructure and are frequently integrated with directory services, authentication systems, and application backends. Their role in enforcing identity, authentication, and service trust relationships places them within the operational control layer rather than at the application edge.
S12 Enabling Vulnerability and Exposure Context
The vulnerability is caused by missing or improperly enforced authentication controls on HTTP-accessible service endpoints within Oracle Fusion Middleware components. This allows remote interaction with sensitive functionality without requiring valid credentials.
Exploitation requires only network access to the vulnerable service and the ability to send crafted HTTP requests. No prior authentication or foothold is necessary.
Exposure scenarios include externally reachable middleware services, internally exposed services within flat or weakly segmented networks, and deployments where reverse proxies or load balancers provide access to backend services. Because the vulnerability resides within application-layer service components, traditional perimeter filtering may not prevent exploitation if access is permitted.
S13 Exploitability, Patch, and Exposure Management Status
Oracle released an out-of-band Security Alert addressing this vulnerability, indicating a level of urgency beyond standard quarterly patch cycles. The vulnerability is rated CVSS 3.1 score 9.8, reflecting remote, unauthenticated exploitability with full impact potential.
As of this assessment, there is no confirmed public exploit code widely documented and no confirmed inclusion in the CISA Known Exploited Vulnerabilities catalog. However, the vulnerability characteristics support rapid exploit development, and the affected product family has recent precedent for real-world exploitation.
Patch application may require coordinated testing due to middleware dependencies and service integration complexity. Exposure management should prioritize identification of externally reachable instances and systems integrated with identity or authentication workflows.
Risk posture is elevated and time-sensitive despite the absence of confirmed exploitation.
S14 Sectors / Countries Affected
Primary Sectors at Risk
Financial services
Government and public sector
Healthcare
Telecommunications
Large enterprise IT environments
These sectors commonly deploy Oracle Fusion Middleware for identity governance and service integration, increasing potential impact from compromise.
Geographic Exposure
Global, with higher concentration in regions with significant enterprise Oracle adoption, including North America, Europe, and Asia-Pacific.
S15 Adversary Capability Profiling
Threat Actor Skill Requirement
Moderate
The vulnerability does not require authentication and can be exploited through crafted HTTP requests, reducing the barrier to entry while still requiring understanding of target deployment and payload execution.
Infrastructure Requirements
Low to moderate
Standard web request tooling is sufficient for initial exploitation. Additional tooling may be required for post-exploitation objectives.
Operational Maturity Indicators
The vulnerability is suitable for opportunistic attackers, initial access brokers, and more advanced actors seeking access to identity-layer systems.
Scalability
High
Pre-authentication HTTP-based vulnerabilities are conducive to automated scanning and exploitation across large target sets.
Escalation Likelihood
High
Compromise of identity and middleware systems provides access to credentials, service accounts, and trust relationships that support privilege escalation and lateral movement.
S16 Targeting Probability Assessment
Overall Targeting Probability
High
Targeting Drivers
Identity and middleware systems represent high-value targets due to their role in authentication and access control. Pre-authentication exploitability significantly reduces attacker cost and effort. Historical exploitation of similar Oracle Identity Manager vulnerabilities indicates established attacker interest in this technology stack.
Most Likely Targets
Internet-exposed Oracle Fusion Middleware deployments
Organizations with centralized identity governance platforms
Environments with limited network segmentation around middleware systems
Secondary Targets
Internally exposed middleware services accessible through lateral movement
Organizations with delayed patch cycles for enterprise infrastructure software
S17 MITRE ATT&CK Chain Flow Mapping
Initial Access
T1190 – Exploit Public-Facing Application
Attackers send crafted HTTP requests to exposed Oracle Fusion Middleware endpoints to exploit missing authentication controls and gain unauthenticated access.
Execution
T1059 – Command and Scripting Interpreter
Successful exploitation enables execution of attacker-controlled code within the middleware service context.
Persistence
T1505 – Server Software Component
Attackers may establish persistence by modifying middleware services or deploying malicious components within the application environment.
Privilege Escalation
T1068 – Exploitation for Privilege Escalation
Compromised middleware processes may allow escalation into higher-privileged service or administrative contexts.
Credential Access
T1552 – Unsecured Credentials
Attackers may extract stored credentials, tokens, or service account secrets from middleware or connected identity systems.
Lateral Movement
T1021 – Remote Services
Compromised credentials and trust relationships enable movement across enterprise systems.
Defense Evasion
T1070 – Indicator Removal
Attackers may manipulate or remove logs within middleware components to reduce detection visibility.
S18 Attack Path Narrative (Signal-Aligned Execution Flow)
The attack begins when an adversary identifies exposed Oracle Fusion Middleware services associated with Oracle Identity Manager or Oracle Web Services Manager. These services are reachable over HTTP and contain endpoints where authentication controls are not properly enforced.
The adversary sends crafted HTTP requests to these exposed service interfaces. Because authentication is not required, the attacker can directly interact with sensitive backend functionality without credentials or session context.
Successful exploitation results in execution of attacker-controlled code within the middleware service environment. This establishes a foothold within the middleware service context.
From this foothold, the attacker can interact with the middleware environment, including accessing configuration data and identifying connected systems and services.
Post-exploitation activity depends on attacker objectives and the target environment. This may include persistence within middleware components or use of the compromised service as a pivot point into connected enterprise systems.
Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment.
S19 Attack Chain Risk Amplification Summary
· Pre-authentication exploitability removes the need for credential acquisition, significantly reducing attacker effort
· HTTP-based exposure enables rapid scanning and automated exploitation at scale
· Execution occurs within middleware services, increasing operational impact of initial compromise
· Placement within identity and service control layers amplifies enterprise-wide risk
· Out-of-band vendor alert indicates elevated urgency and likely attacker prioritization
· Historical exploitation of similar Oracle Identity Manager vulnerabilities increases likelihood of targeting
S20 Tactics, Techniques, and Procedures
· T1190 – Exploit Public-Facing Application
Attackers exploit exposed Oracle Fusion Middleware endpoints by sending crafted HTTP requests that bypass authentication controls.
· T1059 – Command and Scripting Interpreter
Successful exploitation enables execution of attacker-controlled code within the middleware service context.
· T1505 – Server Software Component
Attackers may establish persistence by modifying middleware services or deploying malicious components.
Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment.
· T1021 – Remote Services
Compromised middleware systems may be used to access other internal systems through trusted service relationships.
Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment.
S20A Adversary Tradecraft Summary
Tradecraft associated with CVE-2026-21992 is characterized by low-complexity, high-impact exploitation of exposed middleware services. The absence of authentication requirements allows attackers to directly access application-layer functionality without relying on credential theft or social engineering.
The most relevant tradecraft pattern is rapid initial access through exploitation of HTTP-exposed services followed by execution within a middleware service context. This provides immediate operational access within enterprise application infrastructure.
Follow-on activity is expected to be environment-dependent. In higher-value environments, attackers may attempt to maintain access, expand privileges, or leverage trust relationships to move laterally. These behaviors are plausible given the system role but are not confirmed as baseline activity for this vulnerability.
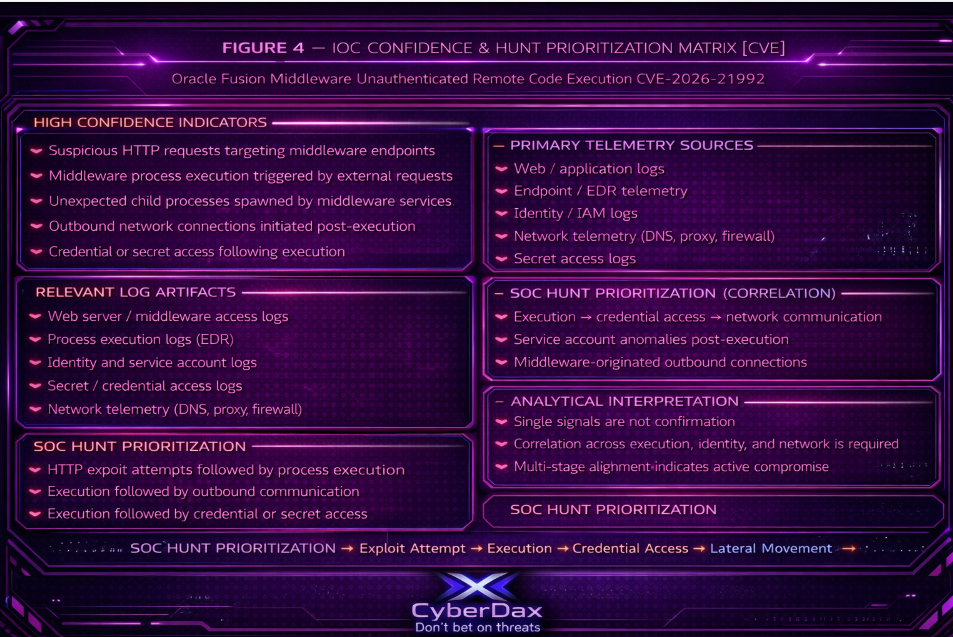
S21 Detection Strategy Overview
Detection for CVE-2026-21992 should be built around behavioral identification of unauthenticated interaction with Oracle Identity Manager and Oracle Web Services Manager service interfaces, followed by suspicious execution or service-side behavioral change on the affected middleware host.
Because this is a pre-authentication HTTP-reachable vulnerability, the most reliable early-warning model is correlation across the primary telemetry pillars relevant to this threat: endpoint process and execution telemetry, network and web proxy telemetry, and Oracle middleware application logging. Identity-based detections alone are insufficient because successful exploitation does not require valid user authentication.
The strategy should prioritize three detection moments: anomalous inbound access to sensitive middleware endpoints, suspicious service-context execution after that access, and abnormal follow-on connections or service behavior originating from the compromised middleware system. Detection quality improves materially when these signals are correlated as a sequence rather than alerted on in isolation.
Variant handling is required. The strategy must cover direct internet-facing exploitation, exploitation routed through reverse proxies or load balancers, and internal exploitation where an attacker has already gained network reachability to the middleware tier.
S22 Primary Detection Signals
· Unauthenticated or otherwise anomalous HTTP requests to Oracle Identity Manager REST WebServices or Oracle Web Services Manager-related service interfaces
· Request patterns to sensitive middleware endpoints that are unusual in frequency, path usage, method usage, or client origin
· A short time gap between inbound suspicious HTTP activity and new process execution, command execution, or abnormal service behavior on the middleware host
· Middleware service instability or request-handling anomalies immediately following inbound requests to affected interfaces
· New outbound connections or unusual internal service calls originating from the middleware host shortly after suspicious inbound interaction
· Repeated probing of multiple middleware paths consistent with exploit validation or automated scanning
S23 Telemetry Requirements
· HTTP request visibility for inbound traffic to the affected middleware services, including URI path, method, status code, source IP, reverse-proxy headers where available, and timestamp fidelity
· Web proxy, application delivery controller, WAF, or load balancer logs where those devices front Oracle middleware services
· Oracle application and middleware logs capable of showing request handling, service invocation, fault conditions, and execution-side anomalies for the affected interfaces
· Endpoint or EDR telemetry from the middleware host showing process creation, command execution, parent-child lineage, user and service context, and file or script execution where available
· DNS, proxy, and network flow telemetry sufficient to observe unusual outbound connections or new east-west communication from the middleware system
· Time-synchronized logging across network, middleware, and endpoint sources so suspicious inbound activity can be reliably correlated to host-side effects
S24 Detection Opportunities and Gaps
Detection Opportunities
· External scanning and exploit delivery attempts may be identified through abnormal access patterns to exposed Oracle middleware service paths
· Correlation between suspicious inbound HTTP requests and immediate host-side execution provides the strongest detection opportunity for early exploitation
· New or unusual outbound communication from the middleware host after suspicious inbound activity can expose post-exploitation expansion
· Reverse-proxy, WAF, and load balancer logs may preserve early exploit evidence even when middleware logging is weak
Detection Gaps
· If TLS inspection is absent and middleware logging is limited, request-level visibility may be reduced to coarse connection metadata
· In environments with heavy service-to-service traffic, malicious requests may blend with legitimate middleware activity unless endpoint and application telemetry are also present
· Internal exploitation variants may evade perimeter-focused monitoring if the attacker already has reachability to the middleware tier
· Some exploit attempts may produce minimal pre-execution artifacts, narrowing the detection window before code execution occurs
· Weak time synchronization across proxy, middleware, and endpoint logs can break the correlation chain and materially reduce detection confidence
Variant Considerations
· Direct internet-facing variant: strongest opportunity at the network and proxy layer
· Reverse-proxy or load-balanced variant: strongest opportunity through upstream device logs and header-aware correlation
Internal reachability variant: strongest opportunity through endpoint execution telemetry, middleware logs, and east-west network monitoring
S25 Ultra-Tuned Detection Engineering Rules
Suricata
Rule Name
Oracle Fusion Middleware Suspicious Untrusted POST to Tuned OIM or OWSM Service Path
Purpose
Detect likely unauthenticated exploit delivery attempts against Oracle Identity Manager REST WebServices or Oracle Web Services Manager-related interfaces by alerting on untrusted POST requests to organization-validated middleware service paths.
Tuning Explanation
This is the primary Suricata exploit-attempt rule for CVE-2026-21992. It is intended to detect suspicious write-style requests to sensitive Oracle middleware interfaces without pretending that public reporting provides confirmed exploit-exact URIs.
The rule is production-ready in the CyberDax sense only when it is localized to the environment. That means destination assets, approved sources, and actual OIM or OWSM paths must be tuned by the engineering team.
Administrator Localization Instructions
· Replace $HOME_NET with a dedicated Oracle middleware destination variable such as $ORACLE_FMW_SERVERS
· Replace the candidate URI regex with the organization’s validated OIM and OWSM application paths wherever possible
· Suppress known reverse proxies, load balancers, health checks, approved integration gateways, and sanctioned vulnerability scanners
· If the environment supports both north-south and east-west inspection, deploy separate copies with different source scoping and thresholds
· If TLS is in use, confirm that Suricata is positioned after a decryption point or otherwise has HTTP visibility
· Consider adding a threshold or detection filter if the environment produces repeated legitimate POST activity to the same paths
SIEM or system-ready code
alert http $EXTERNAL_NET any -> $HOME_NET $HTTP_PORTS (
msg:"CYBERDAX Oracle FMW suspicious untrusted POST to tuned OIM/OWSM path";
flow:to_server,established;
http.method;
content:"POST"; nocase;
http.uri;
pcre:"/^\/(?:oim|identity|iam|owsm|wsm|rest|services|webservices)(?:\/|\\?|$)/Ui";
classtype:web-application-attack;
metadata:service http, attack_target server, deployment Oracle_FMW, confidence medium, severity medium;
sid:252199231;
rev:1;
)
Logical Notes
This is the primary Suricata rule for Scenario 1. It is designed to identify likely exploit delivery attempts, not successful compromise. It should be kept narrow and middleware-specific.
Rule Regret Check
Deployment caution
Will be noisy if deployed against generic web infrastructure or without path reduction.
Confidence caution
Medium confidence until destination assets and URI paths are tuned locally.
Coverage value
High-value network-side exploit-attempt detection.
Execution Validity
Deployable with mandatory environment localization.
Telemetry Dependency
HTTP request visibility and accurate Oracle middleware asset scoping.
Rule Name
Oracle Fusion Middleware Repeated Untrusted Access to Tuned OIM or OWSM Paths
Purpose
Detect repeated probing, exploit validation, or path discovery activity against known Oracle middleware service paths from untrusted sources.
Tuning Explanation
This is a precursor and context rule rather than a primary compromise rule. Its value is early warning and source prioritization. It should remain middleware-specific and should not function as a generic web scanning detector.
Administrator Localization Instructions
· Replace $HOME_NET with $ORACLE_FMW_SERVERS or equivalent Oracle middleware asset grouping
· Narrow the URI regex to validated OIM and OWSM paths if that information is available locally
· Suppress known vulnerability scanners, internal testing platforms, API gateways, and approved integration sources
· Tune thresholds separately for internet-origin traffic and internal east-west monitoring
· Lower thresholds only where background noise is known to be low
SIEM or system-ready code
alert http $EXTERNAL_NET any -> $HOME_NET $HTTP_PORTS (
msg:"CYBERDAX Oracle FMW repeated untrusted access to tuned OIM/OWSM path";
flow:to_server,established;
http.uri;
pcre:"/^\/(?:oim|identity|iam|owsm|wsm|rest|services|webservices)(?:\/|\\?|$)/Ui";
detection_filter:track by_src, count 6, seconds 120;
classtype:web-application-attack;
metadata:service http, attack_target server, deployment Oracle_FMW, confidence medium, severity low;
sid:252199232;
rev:1;
)
Logical Notes
This rule supports Scenario 6. It should enrich analyst prioritization and source risk scoring, especially when it precedes a higher-confidence exploit-attempt or endpoint execution alert.
Rule Regret Check
Deployment caution
Do not treat repeated access alone as exploitation.
Confidence caution
Medium to low if trusted scanners and integrations are not suppressed.
Coverage value
Useful early-warning reconnaissance coverage.
Execution Validity
Deployable with source suppression and threshold tuning required.
Telemetry Dependency
Reliable HTTP visibility and meaningful definition of untrusted source ranges.
Rule Name
Oracle Fusion Middleware Untrusted Service-Style POST to Tuned OIM or OWSM Interface
Purpose
Increase exploit-attempt confidence by detecting untrusted POST requests to tuned Oracle middleware paths where the payload presents as service-oriented XML, SOAP, or JSON traffic.
Tuning Explanation
This rule is stronger than path-only detection because it combines write method, middleware path, and service-style payload characteristics. However, legitimate middleware integrations may look similar, so this rule must be tightly scoped before deployment.
Administrator Localization Instructions
· Replace $HOME_NET with a dedicated Oracle middleware asset variable
· Restrict the path scope to known OIM and OWSM endpoints used in the environment
· Identify and suppress legitimate integration middleware, orchestration systems, approved API clients, and service accounts that normally send SOAP, XML, or JSON traffic
· Prefer deployment only on paths where untrusted service-style payloads are operationally unusual
· Consider restricting to internet-origin or otherwise untrusted zones only
SIEM or system-ready code
alert http $EXTERNAL_NET any -> $HOME_NET $HTTP_PORTS (
msg:"CYBERDAX Oracle FMW untrusted service-style POST to tuned OIM/OWSM interface";
flow:to_server,established;
http.method;
content:"POST"; nocase;
http.uri;
pcre:"/^\/(?:oim|identity|iam|owsm|wsm|services|webservices)(?:\/|\\?|$)/Ui";
http.header;
pcre:"/content-type\x3a\s*(?:application\/soap\+xml|text\/xml|application\/xml|application\/json)/Hi";
classtype:web-application-attack;
metadata:service http, attack_target server, deployment Oracle_FMW, confidence medium_high, severity medium;
sid:252199233;
rev:1;
)
Logical Notes
This is a higher-confidence exploit-attempt analytic when external or untrusted service-style writes are not expected. It should not be broadly enabled in integration-heavy environments without allowlisting.
Rule Regret Check
Deployment caution
Can alert on legitimate service integrations if source allowlisting is incomplete.
Confidence caution
Confidence becomes high only after trusted integrations are excluded.
Coverage value
Strong exploit-attempt signal when path and source scope are tight.
Execution Validity
Deployable with strict source allowlisting and path tuning required.
Telemetry Dependency
HTTP header visibility and reliable classification of trusted versus untrusted clients.
Rule Name
Oracle Fusion Middleware Suspicious 5xx Fault Response After Tuned Untrusted Middleware Request
Purpose
Provide supporting detection for exploit testing, malformed exploit delivery, or request patterns that trigger server fault conditions immediately after a suspicious tuned request to Oracle middleware.
Tuning Explanation
This is a supporting triage rule only. It should never be treated as a primary compromise rule. Its value is to escalate review when suspicious requests are followed by application fault behavior.
Administrator Localization Instructions
· Use only when the paired request-side helper rule has already been localized to real Oracle middleware assets and paths
· Restrict to environments where request and response visibility both exist on the same inspection path
· Suppress known maintenance windows, unstable services, upgrade periods, or recurring non-malicious 5xx conditions
· Treat this rule as enrichment for endpoint or application-log follow-up, not as stand-alone incident confirmation
· Adjust response-code matching if specific fault patterns are known locally
SIEM or system-ready code
alert http $EXTERNAL_NET any -> $HOME_NET $HTTP_PORTS (
msg:"CYBERDAX Oracle FMW helper - tuned suspicious untrusted middleware request";
flow:to_server,established;
http.method;
content:"POST"; nocase;
http.uri;
pcre:"/^\/(?:oim|identity|iam|owsm|wsm|services|webservices)(?:\/|\\?|$)/Ui";
flowbits:set,oraclefmw.req;
flowbits:noalert;
sid:252199234;
rev:1;
)
alert http $HOME_NET $HTTP_PORTS -> $EXTERNAL_NET any (
msg:"CYBERDAX Oracle FMW suspicious 5xx after tuned untrusted middleware request";
flow:to_client,established;
flowbits:isset,oraclefmw.req;
http.stat_code;
pcre:"/^5\d\d$/";
classtype:web-application-attack;
metadata:service http, attack_target server, deployment Oracle_FMW, confidence low_medium, severity low;
sid:252199235;
rev:1;
)
Logical Notes
This rule supports Scenario 5 and should be used for analyst prioritization and correlation only. It is useful for surfacing suspicious request-and-fault chains that merit immediate endpoint or middleware-log review.
Rule Regret Check
Deployment caution
Not suitable as a stand-alone compromise alert.
Confidence caution
Low to medium on its own.
Coverage value
Good triage support for exploit-attempt chains that trigger server-side instability.
Execution Validity
Deployable as a supporting analytic only.
Telemetry Dependency
Bidirectional HTTP visibility and localized request-side helper logic.
Suricata Deployment Variant Guidance
Direct internet-facing variant
Deploy the primary and supporting rules on perimeter inspection points protecting Oracle middleware assets.
Reverse proxy or load balancer variant
Deploy where decrypted HTTP visibility exists and preserve backend asset mapping. Account for trusted proxy ranges and forwarded-header behavior during source tuning.
Internal reachability variant
Deploy equivalent localized copies on east-west inspection points protecting middleware and identity tiers. Use different source scoping, suppressions, and thresholds than perimeter deployments.
SentinelOne
Rule Name
Oracle Middleware Java Process Spawning High-Risk Interpreter
Purpose
Detect likely successful exploitation of CVE-2026-21992 by identifying Oracle middleware service processes spawning shell or scripting interpreters that are not expected during normal Oracle Identity Manager or Oracle Web Services Manager operation.
Tuning Explanation
This is the primary SentinelOne execution-confirmation rule for this CVE. The highest-value host signal is abnormal child process creation from Oracle middleware service context after exploitation.
This rule is strongest when scoped to Java processes operating in WebLogic or Oracle middleware service context rather than generic Java activity across the enterprise.
Administrator Localization Instructions
· Validate the actual Oracle middleware parent processes in the environment, including:
o Java service binaries
o WebLogic-hosted service processes
o Oracle wrapper or startup processes
· Add parent command-line or path scoping where available, including:
o Oracle home paths
o WebLogic domain paths
o OIM, IDM, or OWSM startup arguments
· Split the rule by operating system if both Linux and Windows middleware hosts are present
· Suppress approved:
o maintenance scripts
o patching workflows
o orchestration jobs
o configuration management tooling
· Raise severity for internet-facing or reverse-proxy-backed middleware hosts
Logical Notes
This is the strongest SentinelOne rule for Scenario 2 and should be treated as a likely compromise indicator once localized. It is designed to confirm suspicious execution from trusted middleware service context.
Rule Regret Check
Deployment caution
Will over-alert if generic Java activity is not narrowed to Oracle middleware context.
Confidence caution
Confidence becomes high only after parent scoping and maintenance suppressions are added.
Coverage value
Very high. Strong host-side compromise detection.
Execution Validity
Deployable with mandatory parent-process localization and suppression tuning.
Telemetry Dependency
SentinelOne process creation telemetry with parent-child lineage.
SIEM or system-ready code
EventType = "Process Creation"
AND (
ParentProcessName IN ("java", "java.bin")
OR ParentCommandLine CONTAINS "weblogic"
)
AND ProcessName IN (
"sh","bash","ksh",
"python","python3","perl",
"powershell.exe","pwsh.exe",
"cmd.exe"
)
Rule Name
Oracle Middleware Service Launching External Retrieval Tool
Purpose
Detect likely post-exploitation staging behavior where compromised Oracle middleware launches utilities commonly used for payload retrieval or transfer.
Tuning Explanation
This rule focuses on realistic attacker follow-on behavior after code execution in middleware context, specifically retrieval and staging utilities. It is intentionally narrower than the prior draft to avoid overlap with the encoded or inline execution rule.
This analytic is useful across direct internet-facing, reverse-proxy, and internal reachability variants.
Administrator Localization Instructions
· Confirm whether middleware hosts legitimately invoke:
o curl
o wget
o certutil
o bitsadmin
· Scope parent processes to validated Oracle middleware or WebLogic service context
· Suppress approved:
o deployment agents
o patching workflows
o backup tooling
o configuration management systems
· Where legitimate retrieval exists, add command-line exclusions for approved scripts, repositories, or destinations
· Split Linux and Windows variants if mixed middleware platforms are in use
Logical Notes
This is a strong post-exploitation staging rule. It becomes especially valuable when correlated with Suricata exploit-attempt alerts or suspicious middleware execution lineage.
Rule Regret Check
Deployment caution
May alert on legitimate automation if suppressions are incomplete.
Confidence caution
Medium to high depending on parent scoping and local exclusions.
Coverage value
High-value staging and payload-retrieval detection.
Execution Validity
Deployable with tool suppression and parent scoping required.
Telemetry Dependency
SentinelOne process creation telemetry with lineage.
SIEM or system-ready code
EventType = "Process Creation"
AND (
ParentProcessName IN ("java", "java.bin")
OR ParentCommandLine CONTAINS "weblogic"
)
AND ProcessName IN (
"curl","wget",
"certutil.exe","bitsadmin.exe"
)
Rule Name
Oracle Middleware Java Execution with Encoded or Inline Command
Purpose
Detect high-confidence malicious execution where Oracle middleware launches interpreters or shells with encoded, inline, staged, or temporary-path execution characteristics.
Tuning Explanation
This is a refined higher-confidence rule that improves fidelity over generic shell-spawn detection by requiring suspicious command-line characteristics. It is intended to distinguish clearly malicious middleware-spawned execution from generic administrative scripting.
Administrator Localization Instructions
· Confirm command-line telemetry coverage in the SentinelOne tenant
· Restrict parent process scope to validated Oracle middleware or WebLogic context
· Review whether encoded PowerShell, inline shell execution, or temporary-directory execution ever occurs legitimately in middleware administration
· Suppress approved automation, patch workflows, and known safe script patterns
· Consider separate Linux and Windows variants if platform-specific tuning is needed
Logical Notes
This is a high-confidence refinement rule and should be prioritized above generic shell-spawn rules when command-line visibility exists.
Rule Regret Check
Deployment caution
Requires command-line visibility and local script-pattern review.
Confidence caution
High after exclusions are added.
Coverage value
Very high. Strong compromise confirmation signal.
Execution Validity
Deployable where command-line telemetry exists and local scripting patterns are understood.
Telemetry Dependency
SentinelOne process and command-line telemetry with lineage.
SIEM or system-ready code
EventType = "Process Creation"
AND (
ParentProcessName IN ("java", "java.bin")
OR ParentCommandLine CONTAINS "weblogic"
)
AND ProcessName IN (
"powershell.exe","pwsh.exe",
"cmd.exe","sh","bash","python","python3"
)
AND (
CommandLine CONTAINS " -enc "
OR CommandLine CONTAINS "powershell -e"
OR CommandLine CONTAINS "base64"
OR CommandLine CONTAINS "/tmp/"
)
Rule Name
Oracle Middleware Process Initiating Disallowed Outbound Network Connection
Purpose
Detect post-exploitation expansion by identifying Oracle middleware processes initiating outbound connections to destinations not approved for normal middleware communications.
Tuning Explanation
This is a supporting post-exploitation analytic, not a primary exploit-confirmation rule. Its value comes from identifying egress behavior that deviates from established middleware communication patterns after likely compromise.
This rule becomes materially stronger when the environment can distinguish approved middleware communication paths from unusual outbound or east-west connections.
Administrator Localization Instructions
· Validate that SentinelOne network telemetry with process attribution is available for the relevant middleware hosts
· Scope initiating processes to confirmed Oracle middleware service parents and suspicious child processes where possible
· Build and maintain an allowlist of approved middleware destinations, including:
o databases
o identity stores
o internal APIs
o LDAP or directory services
o approved repositories
· Separate alert handling for:
o disallowed external destinations
o disallowed internal east-west destinations
· Where possible, correlate this rule with:
o middleware-spawned interpreter execution
o retrieval-tool execution
o recent suspicious inbound middleware activity
· Lower severity or suppress during approved maintenance, deployment, or patch windows if egress behavior is expected to change
Logical Notes
This is best used as a correlation-strengthening analytic for Scenario 4. It is especially valuable when paired with suspicious middleware execution, retrieval-tool activity, or other evidence of host compromise.
Rule Regret Check
Deployment caution
Will be noisy without a real middleware destination baseline.
Confidence caution
Medium as a standalone rule; high when correlated with suspicious execution.
Coverage value
High-value supporting detection for post-exploitation expansion, staging, or lateral movement.
Execution Validity
Deployable with destination allowlisting and process-attribution validation required.
Telemetry Dependency
SentinelOne network telemetry with reliable process attribution and a maintained approved-destination baseline.
SIEM or system-ready code
EventType = "Network Connection"
AND (
InitiatingProcessName IN ("java","java.bin")
OR InitiatingProcessParentName IN ("java","java.bin")
OR InitiatingProcessCommandLine CONTAINS "weblogic"
OR InitiatingProcessParentCommandLine CONTAINS "weblogic"
)
AND DestinationAddress NOT IN <APPROVED_MIDDLEWARE_DESTINATIONS>
SentinelOne Deployment Variant Guidance
Direct internet-facing variant
Prioritize the interpreter-spawn and encoded-command rules at highest severity on middleware hosts directly reachable from untrusted networks or backed by internet-facing reverse proxies.
Reverse proxy or load balancer variant
Apply the same parent-child execution logic on backend Oracle middleware hosts. Host-side execution remains visible even when inbound exploit delivery is abstracted behind upstream infrastructure.
Internal reachability variant
Maintain the same execution-focused rules on internal middleware tiers. In these cases, the retrieval-tool and disallowed outbound-connection rules often become more valuable because the initial exploit may not be visible at the perimeter.
Splunk
Rule Name
Oracle Middleware Exploit Attempt Followed by Host Execution
Purpose
Detect high-confidence compromise by correlating suspicious inbound HTTP requests to Oracle middleware with subsequent suspicious process execution on the same middleware host.
Tuning Explanation
This is the highest-value Splunk rule in the stack because it combines network-side exploit-attempt visibility with endpoint-side execution. It is intended to confirm likely exploitation rather than merely flag suspicious traffic.
This rule is written to avoid join and instead uses event normalization plus append and stats correlation. It must be localized to real Oracle middleware assets and real OIM or OWSM paths.
Administrator Localization Instructions
· Normalize network destination and endpoint host fields into a single host field
· Replace the candidate URI matching with validated local OIM and OWSM paths as a mandatory tuning step
· Confirm the correct EDR field mappings for:
o process name
o parent process name
o parent command line
· Ensure time synchronization across network and endpoint sources
· Tune the default 5-minute correlation window if delayed execution is observed locally
· Suppress:
o approved scanners
o internal testing systems
o sanctioned validation activity
· Restrict the search to Oracle middleware assets wherever possible
Logical Notes
This is the primary Splunk correlation rule for Scenario 1 plus Scenario 2 and should be among the highest-priority SOC alerts after localization.
Rule Regret Check
Deployment caution
Requires reliable field normalization, host identity consistency, and mandatory path tuning.
Confidence caution
Very high after URI, host, and endpoint field tuning.
Coverage value
Critical. Best high-confidence exploit confirmation rule in the stack.
Execution Validity
Deployable with normalization, host scoping, and validated path tuning required.
Telemetry Dependency
· Network telemetry from Suricata, proxy, WAF, or equivalent
· Endpoint telemetry from SentinelOne or equivalent EDR
SIEM or system-ready code
(
search index=network OR index=suricata OR index=proxy OR index=waf
| eval host=coalesce(dest, dvc, host, dest_host)
| eval uri_norm=lower(coalesce(uri_path, uri, url, request))
| search http_method=POST OR method=POST
| where like(uri_norm,"%/oim/%")
OR like(uri_norm,"%/identity/%")
OR like(uri_norm,"%/iam/%")
OR like(uri_norm,"%/owsm/%")
OR like(uri_norm,"%/wsm/%")
OR like(uri_norm,"%/oim?")
OR like(uri_norm,"%/identity?")
OR like(uri_norm,"%/iam?")
OR like(uri_norm,"%/owsm?")
OR like(uri_norm,"%/wsm?")
| eval network_time=_time
| eval signal_type="network_attempt"
| fields host network_time signal_type src uri_norm
)
| append [
search index=edr OR index=sentinelone
| eval host=coalesce(endpoint, host, computer_name, device_name)
| eval parent_name=lower(coalesce(parent_process, parent_process_name, ParentProcessName))
| eval parent_cmd=lower(coalesce(parent_command_line, parent_cmdline, ParentCommandLine))
| eval proc_name=lower(coalesce(process_name, process, ImageFileName))
| where parent_name="java"
OR parent_name="java.bin"
OR like(parent_cmd,"%weblogic%")
| where proc_name="sh"
OR proc_name="bash"
OR proc_name="ksh"
OR proc_name="python"
OR proc_name="python3"
OR proc_name="perl"
OR proc_name="powershell.exe"
OR proc_name="pwsh.exe"
OR proc_name="cmd.exe"
| eval edr_time=_time
| eval signal_type="host_execution"
| fields host edr_time signal_type proc_name parent_name parent_cmd
]
| stats
min(network_time) as network_time
min(edr_time) as edr_time
values(uri_norm) as uri_norm
values(src) as src
values(proc_name) as proc_name
values(parent_name) as parent_name
values(parent_cmd) as parent_cmd
values(signal_type) as signal_types
by host
| where mvfind(signal_types,"network_attempt")>=0
AND mvfind(signal_types,"host_execution")>=0
AND edr_time>=network_time
AND edr_time-network_time<=300
Rule Name
Oracle Middleware Execution Followed by Retrieval Tool Activity
Purpose
Detect post-exploitation staging by identifying suspicious middleware execution followed by retrieval-tool activity on the same host within a short time window.
Tuning Explanation
This rule is intended to detect follow-on staging after likely compromise, especially when exploit-attempt visibility is weak or absent. It correlates suspicious middleware-spawned execution with retrieval-tool usage.
This rule intentionally avoids overlap with the encoded or inline execution rule by focusing on retrieval tooling only.
Administrator Localization Instructions
· Confirm local field mappings for process name, parent process, and command line
· Restrict host scope to Oracle middleware assets if possible
· Validate whether middleware hosts legitimately use:
o curl
o wget
o certutil.exe
o bitsadmin.exe
· Suppress:
o deployment systems
o patch tooling
o backup or automation workflows
· Adjust the default 5-minute window if retrieval activity is typically delayed locally
· Consider raising severity only when retrieval is directed to untrusted or external destinations if network enrichment is available
Logical Notes
This rule maps to Scenario 2 plus post-exploitation staging. It is a strong supporting rule and becomes high-confidence when paired with the primary exploit-correlation rule.
Rule Regret Check
Deployment caution
Will be noisy if legitimate middleware retrieval tooling is common and not suppressed.
Confidence caution
High after parent-process scoping and operational exclusions.
Coverage value
High-value staging detection.
Execution Validity
Deployable with suppression, parent-process tuning, and host scoping required.
Telemetry Dependency
Endpoint process telemetry, ideally with command line and optional network enrichment.
SIEM or system-ready code
(
search index=edr OR index=sentinelone
| eval host=coalesce(endpoint, host, computer_name, device_name)
| eval parent_name=lower(coalesce(parent_process, parent_process_name, ParentProcessName))
| eval parent_cmd=lower(coalesce(parent_command_line, parent_cmdline, ParentCommandLine))
| eval proc_name=lower(coalesce(process_name, process, ImageFileName))
| where parent_name="java"
OR parent_name="java.bin"
OR like(parent_cmd,"%weblogic%")
| where proc_name="sh"
OR proc_name="bash"
OR proc_name="ksh"
OR proc_name="python"
OR proc_name="python3"
OR proc_name="perl"
OR proc_name="powershell.exe"
OR proc_name="pwsh.exe"
OR proc_name="cmd.exe"
| eval exec_time=_time
| fields host exec_time
)
| append [
search index=edr OR index=sentinelone
| eval host=coalesce(endpoint, host, computer_name, device_name)
| eval parent_name=lower(coalesce(parent_process, parent_process_name, ParentProcessName))
| eval parent_cmd=lower(coalesce(parent_command_line, parent_cmdline, ParentCommandLine))
| eval proc_name=lower(coalesce(process_name, process, ImageFileName))
| where parent_name="java"
OR parent_name="java.bin"
OR like(parent_cmd,"%weblogic%")
| where proc_name="curl"
OR proc_name="wget"
OR proc_name="certutil.exe"
OR proc_name="bitsadmin.exe"
| eval retrieval_time=_time
| fields host retrieval_time proc_name
]
| stats
min(exec_time) as exec_time
min(retrieval_time) as retrieval_time
values(proc_name) as retrieval_tools
by host
| where isnotnull(exec_time)
AND isnotnull(retrieval_time)
AND retrieval_time>=exec_time
AND retrieval_time-exec_time<=300
Rule Name
Oracle Middleware Encoded or Inline Command Execution
Purpose
Detect high-confidence malicious execution where Oracle middleware launches interpreters or shells with encoded, inline, staged, or temporary-path execution characteristics.
Tuning Explanation
This is a high-confidence refinement rule. It improves fidelity over the broader interpreter-spawn rule by requiring suspicious command-line characteristics that are more indicative of malicious execution.
Administrator Localization Instructions
· Confirm command-line telemetry is consistently available
· Restrict to Oracle middleware or WebLogic parent context
· Review whether encoded PowerShell, inline shell usage, or temporary-path execution is ever legitimate locally
· Suppress approved:
o maintenance scripts
o deployment tooling
o patch automation
· Tune suspicious command-line fragments to local realities if known
Logical Notes
This rule is a high-confidence refinement of Scenario 2 and should be prioritized above broader shell-spawn detections when it fires.
Rule Regret Check
Deployment caution
Requires command-line visibility and local review of legitimate scripting patterns.
Confidence caution
High after exclusions are added.
Coverage value
Very high. Strong compromise confirmation signal.
Execution Validity
Deployable where command-line telemetry exists and approved scripting patterns are understood.
Telemetry Dependency
Endpoint telemetry with process, parent, and command-line fields.
SIEM or system-ready code
search index=edr OR index=sentinelone
| eval host=coalesce(endpoint, host, computer_name, device_name)
| eval parent_name=lower(coalesce(parent_process, parent_process_name, ParentProcessName))
| eval parent_cmd=lower(coalesce(parent_command_line, parent_cmdline, ParentCommandLine))
| eval proc_name=lower(coalesce(process_name, process, ImageFileName))
| eval cmd=lower(coalesce(command_line, process_command_line, CommandLine))
| where parent_name="java"
OR parent_name="java.bin"
OR like(parent_cmd,"%weblogic%")
| where proc_name="powershell.exe"
OR proc_name="pwsh.exe"
OR proc_name="cmd.exe"
OR proc_name="sh"
OR proc_name="bash"
OR proc_name="python"
OR proc_name="python3"
| where like(cmd,"% -enc %")
OR like(cmd,"%powershell -e%")
OR like(cmd,"%base64%")
OR like(cmd,"%/tmp/%")
Rule Name
Oracle Middleware Execution with Disallowed Outbound Network Connection
Purpose
Detect post-exploitation expansion by correlating suspicious Oracle middleware execution with outbound connections to destinations not approved for normal middleware communications.
Tuning Explanation
This is a supporting correlation rule, not a primary exploit-confirmation rule. Its value comes from identifying suspicious egress after likely host compromise.
The rule is intentionally written around disallowed destinations, not “new” destinations, because “new” requires baseline logic beyond the raw rule itself.
Administrator Localization Instructions
· Confirm network-connection telemetry with process attribution is available in Splunk
· Restrict process scope to Oracle middleware or WebLogic parent context
· Build and maintain a real allowlist of approved middleware destinations, including:
o databases
o LDAP or directory services
o identity providers
o internal APIs
o approved repositories
· Separate severity handling for:
o disallowed external destinations
o disallowed east-west internal destinations
· Correlate this rule with:
o middleware interpreter-spawn alerts
o retrieval-tool alerts
o suspicious inbound middleware activity
· Replace the placeholder allowlist example with the organization’s actual destination logic before deployment
Logical Notes
This rule maps to Scenario 4 and is best used as a correlation-strengthening analytic rather than a stand-alone incident declaration.
Rule Regret Check
Deployment caution
Will be noisy without a real destination baseline and accurate process attribution.
Confidence caution
Medium as a standalone rule; high when paired with suspicious middleware execution.
Coverage value
High-value supporting detection for expansion, staging, or lateral movement.
Execution Validity
Deployable with destination allowlisting and process-attribution validation required.
Telemetry Dependency
Network telemetry with process attribution, plus endpoint process context where available.
SIEM or system-ready code
search index=edr OR index=sentinelone
| eval host=coalesce(endpoint, host, computer_name, device_name)
| eval proc_name=lower(coalesce(initiating_process, InitiatingProcessName, process_name, process))
| eval parent_name=lower(coalesce(initiating_process_parent, initiating_process_parent_name, parent_process, ParentProcessName))
| eval proc_cmd=lower(coalesce(initiating_process_command_line, InitiatingProcessCommandLine, command_line, CommandLine))
| eval parent_cmd=lower(coalesce(initiating_process_parent_command_line, InitiatingProcessParentCommandLine, parent_command_line, ParentCommandLine))
| where proc_name="java"
OR proc_name="java.bin"
OR parent_name="java"
OR parent_name="java.bin"
OR like(proc_cmd,"%weblogic%")
OR like(parent_cmd,"%weblogic%")
| where NOT cidrmatch("<APPROVED_CIDR_BLOCK>", dest_ip)
Splunk Deployment Variant Guidance
Direct internet-facing variant
Prioritize the exploit-attempt-plus-execution rule at highest severity for Oracle middleware hosts reachable from untrusted networks.
Reverse proxy or load balancer variant
Ensure backend host identity is preserved during normalization so inbound network telemetry can still correlate to the actual middleware host.
Internal reachability variant
Place more weight on the execution-plus-retrieval and execution-plus-disallowed-egress rules, since the initial exploit attempt may not be visible on perimeter sensors.
Elastic
Rule Name
Oracle Middleware Java Parent Spawning High-Risk Interpreter
Purpose
Detect likely successful exploitation of CVE-2026-21992 by identifying Oracle middleware service processes spawning shell or scripting interpreters that are not expected during normal Oracle Identity Manager or Oracle Web Services Manager operation.
Tuning Explanation
This is the primary Elastic host-execution rule for this CVE. The highest-value host signal remains abnormal interpreter execution from Oracle middleware Java service context.
This rule is intentionally written as an engineer-ready template, not a universal paste-in rule. The detection becomes strong only when Java parent activity is narrowed to confirmed Oracle middleware or WebLogic service context.
Administrator Localization Instructions
· Restrict the rule to Oracle middleware assets, asset tags, or middleware-specific data views wherever possible
· Validate the actual middleware parent process identities used in the environment
· Add local parent scoping using any of the following if available:
o Oracle home paths
o WebLogic domain paths
o OIM, IDM, or OWSM startup arguments
o service account context specific to middleware hosts
· Split Linux and Windows variants if both host types are present
· Suppress approved:
o maintenance scripts
o patching workflows
o orchestration jobs
o configuration-management tooling
· Raise severity on internet-facing or reverse-proxy-backed middleware hosts
Logical Notes
This is the primary Elastic compromise-detection rule for Scenario 2. It should outrank supporting post-exploitation rules once localized.
Rule Regret Check
Deployment caution
Will over-alert if generic Java activity is not narrowed to Oracle middleware context.
Confidence caution
High after parent-process, host, and path scoping are tuned locally.
Coverage value
Very high. Primary host-side compromise signal.
Execution Validity
Deployable with mandatory parent-process localization and asset scoping.
Telemetry Dependency
Elastic events normalized to ECS process fields.
SIEM or system-ready code
event.category: process and event.type: start and
host.name: and
(
process.parent.name: ("java" or "java.bin")
or process.parent.command_line: "weblogic*"
) and
process.name: ("sh" or "bash" or "ksh" or "python" or "python3" or "perl" or "powershell.exe" or "pwsh.exe" or "cmd.exe")
Rule Name
Oracle Middleware Suspicious Execution Followed by Retrieval Tool Activity
Purpose
Detect post-exploitation staging by identifying suspicious middleware-spawned execution followed by retrieval-tool activity on the same host within a short time window.
Tuning Explanation
This rule is intended to detect follow-on staging after likely compromise, especially when exploit-attempt visibility is weak or absent. It uses ordered sequence logic, which is where Elastic is strongest, but it is tightened here so both stages remain anchored to middleware parent context.
This rule intentionally avoids overlap with the encoded or inline execution rule by keeping the second stage retrieval-tool specific.
Administrator Localization Instructions
· Restrict the sequence to Oracle middleware assets if possible
· Validate actual middleware parent processes locally
· Confirm whether middleware hosts legitimately invoke:
o curl
o wget
o certutil.exe
o bitsadmin.exe
· Suppress approved:
o deployment systems
o patch tooling
o backup workflows
o automation frameworks
· Adjust the default 5-minute window if retrieval typically occurs later locally
· If the environment cannot support reliable sequence correlation, deploy the stages as separate building-block detections and correlate at the alert layer
Logical Notes
This rule maps to Scenario 2 plus post-exploitation staging. It is a strong supporting rule and becomes high-confidence when paired with the primary exploit-confirmation logic.
Rule Regret Check
Deployment caution
Will be noisy if legitimate middleware retrieval tooling is common and not suppressed.
Confidence caution
High after parent-process scoping and operational exclusions.
Coverage value
High-value staging detection.
Execution Validity
Deployable with suppression, parent-process tuning, and asset scoping required.
Telemetry Dependency
Elastic event-correlation or equivalent sequence-capable detection on ECS process fields.
SIEM or system-ready code
sequence by host.name with maxspan=5m
[process where event.type == "start" and
(
process.parent.name in ("java", "java.bin") or
process.parent.command_line like "*weblogic*"
) and
process.name in ("sh", "bash", "ksh", "python", "python3", "perl", "powershell.exe", "pwsh.exe", "cmd.exe")
]
[process where event.type == "start" and
(
process.parent.name in ("java", "java.bin") or
process.parent.command_line like "*weblogic*"
) and
process.name in ("curl", "wget", "certutil.exe", "bitsadmin.exe")
]
Rule Name
Oracle Middleware Encoded or Inline Command Execution
Purpose
Detect high-confidence malicious execution where Oracle middleware launches interpreters or shells with encoded, inline, staged, or temporary-path execution characteristics.
Tuning Explanation
This is the high-confidence Elastic refinement rule. It improves fidelity over the broader interpreter-spawn rule by requiring suspicious command-line characteristics in addition to middleware parent context.
Administrator Localization Instructions
· Confirm command-line telemetry is consistently available
· Restrict the rule to Oracle middleware or WebLogic parent context
· Review whether encoded PowerShell, inline shell usage, or temporary-path execution ever occurs legitimately in the environment
· Suppress approved:
o maintenance scripts
o deployment tooling
o patch automation
· Tune suspicious command-line fragments to local realities if known
· Split Linux and Windows severity handling if the environment treats these differently
Logical Notes
This is a high-confidence refinement of Scenario 2 and should be prioritized above broader shell-spawn detections when it fires.
Rule Regret Check
Deployment caution
Requires command-line visibility and local review of legitimate scripting patterns.
Confidence caution
High after exclusions are added.
Coverage value
Very high. Strong compromise confirmation signal.
Execution Validity
Deployable where command-line telemetry exists and approved scripting patterns are understood.
Telemetry Dependency
Elastic ECS process fields with command-line visibility.
SIEM or system-ready code
event.category: process and event.type: start and
(
process.parent.name: ("java" or "java.bin")
or process.parent.command_line: "*weblogic*"
) and
process.name: ("powershell.exe" or "pwsh.exe" or "cmd.exe" or "sh" or "bash" or "python" or "python3") and
(
process.command_line: "* -enc "
or process.command_line: "powershell -e*"
or process.command_line: "*base64*"
or process.command_line: "*/tmp/*"
)
Rule Name
Oracle Middleware Suspicious Execution Followed by Disallowed Process-Attributed Outbound Connection
Purpose
Detect post-exploitation expansion by correlating suspicious Oracle middleware execution with a subsequent process-attributed outbound network connection to a destination not approved for normal middleware communications.
Tuning Explanation
This is a supporting correlation rule, not a primary exploit-confirmation rule. Its value comes from identifying suspicious egress after likely host compromise.
This rewrite hardens the rule by tying the network event to the same host and requiring process-attributed network telemetry, rather than using generic host egress alone. It is intentionally written around disallowed destinations, not “new” destinations, because “new” requires external baseline logic beyond the raw rule itself.
Administrator Localization Instructions
· Confirm that Elastic has process-attributed network telemetry for the relevant middleware hosts
· Restrict the process scope to Oracle middleware or WebLogic parent context
· Replace the placeholder destination filter with the organization’s actual:
o approved CIDR ranges
o approved domains
o approved internal service destinations
· Build and maintain a real allowlist of approved middleware destinations, including:
o databases
o LDAP or directory services
o identity providers
o internal APIs
o approved repositories
· Separate handling for:
o disallowed external destinations
o disallowed east-west internal destinations
· Correlate this rule with:
o interpreter-spawn alerts
o retrieval-tool alerts
o suspicious inbound middleware activity
Logical Notes
This rule maps to Scenario 4 and is best used as a correlation-strengthening analytic rather than a stand-alone incident declaration.
Rule Regret Check
Deployment caution
Will be noisy without a real destination baseline, validated process-attributed network telemetry, and destination allowlisting.
Confidence caution
Medium as a standalone rule; high when paired with suspicious middleware execution.
Coverage value
High-value supporting detection for expansion, staging, or lateral movement.
Execution Validity
Deployable with destination allowlisting and process-attribution validation required.
Telemetry Dependency
Elastic ECS process and network fields with reliable host-level and process-attributed correlation.
SIEM or system-ready code
sequence by host.name with maxspan=5m
[process where event.type == "start" and
(
process.parent.name in ("java", "java.bin") or
process.parent.command_line like "*weblogic*"
) and
process.name in ("sh", "bash", "ksh", "python", "python3", "perl", "powershell.exe", "pwsh.exe", "cmd.exe")
]
[network where
process.name != null and
destination.ip != null and
not cidrmatch(destination.ip, "<APPROVED_MIDDLEWARE_DESTINATION_CIDR>")
]
Elastic Deployment Variant Guidance
Direct internet-facing variant
Prioritize the interpreter-spawn and encoded-command rules at highest severity on Oracle middleware hosts directly reachable from untrusted networks.
Reverse proxy or load balancer variant
Elastic host-side detections remain valuable on backend middleware systems even when inbound exploit delivery is partially abstracted behind upstream infrastructure.
Internal reachability variant
Place more weight on the execution-plus-retrieval and execution-plus-disallowed-egress rules, since the initial exploit attempt may not be visible at perimeter sensors.
QRadar
Rule Name
Oracle Middleware Exploit Attempt Followed by Suspicious Host Execution
Purpose
Detect high-confidence compromise by correlating a suspicious inbound HTTP request targeting Oracle middleware with subsequent suspicious process execution on the same Oracle middleware asset.
Tuning Explanation
This is the highest-value QRadar rule for CVE-2026-21992 because it combines network exploit-attempt evidence with host-side execution evidence.
This rule is explicitly built on asset-based correlation, not raw source or destination fields, to prevent correlation drift caused by directionality differences between network and endpoint logs.
Administrator Localization Instructions
· Ensure Oracle middleware systems are correctly grouped into a dedicated Oracle middleware asset group
· Normalize and validate:
o HTTP method
o URI path
o process name
o parent process name
o parent command line
· Replace candidate URI matching with validated OIM and OWSM paths as a mandatory step
· Ensure inbound web events correctly map the destination asset to the middleware asset group
· Ensure EDR events correctly map the host asset to the same middleware asset group
· Tune correlation window (default 5 minutes) if delayed execution is observed
· Suppress:
o approved scanners
o internal testing systems
o sanctioned validation activity
Logical Notes
This rule maps to Scenario 1 and Scenario 2 and should generate a high-priority offense once tuned.
Rule Regret Check
Deployment caution
Requires consistent asset mapping across network and endpoint telemetry.
Confidence caution
Very high after URI and asset tuning.
Coverage value
Critical. Primary exploit-confirmation rule.
Execution Validity
Deployable with asset normalization and path tuning.
Telemetry Dependency
· Network telemetry (IDS, proxy, WAF)
· Endpoint telemetry (EDR)
· QRadar asset model and custom properties
SIEM or system-ready code
Rule Logic
when an event matches ANY of the following BB rules:
BB:Oracle FMW Suspicious Inbound POST to Tuned Middleware Path
followed within 5 minutes by an event matches ANY of the following BB rules:
BB:Oracle Middleware Java Parent Spawning High-Risk Interpreter
on same asset (Oracle middleware asset group)
Building Block Guidance
BB:Oracle FMW Suspicious Inbound POST to Tuned Middleware Path
- Event category: Web / IDS / Proxy / WAF
- HTTP method equals POST
- URI matches tuned Oracle middleware paths
- Destination asset is in Oracle middleware asset group
BB:Oracle Middleware Java Parent Spawning High-Risk Interpreter
- Event category: Process Creation
- Parent process equals java or java.bin OR parent command line contains weblogic
- Child process in sh, bash, ksh, python, python3, perl, powershell.exe, pwsh.exe, cmd.exe
- Asset is in Oracle middleware asset group
Rule Name
Oracle Middleware Suspicious Execution Followed by Retrieval Tool Activity
Purpose
Detect post-exploitation staging by correlating suspicious middleware execution with retrieval-tool activity on the same Oracle middleware asset.
Tuning Explanation
This rule identifies attacker staging behavior after compromise. It uses asset-based correlation to ensure both execution and retrieval occur on the same middleware system.
Administrator Localization Instructions
· Restrict rule to Oracle middleware asset group
· Validate process telemetry normalization:
o process name
o parent process
o parent command line
· Confirm legitimate use of:
o curl
o wget
o certutil.exe
o bitsadmin.exe
· Suppress:
o deployment systems
o patching tools
o automation frameworks
· Adjust correlation window if needed
Logical Notes
Maps to Scenario 2 and post-exploitation staging.
Rule Regret Check
Deployment caution
Will be noisy without suppression of legitimate tooling.
Confidence caution
High after tuning.
Coverage value
High-value staging detection.
Execution Validity
Deployable with suppression and asset scoping.
Telemetry Dependency
Endpoint process telemetry normalized into QRadar.
SIEM or system-ready code
Rule Logic
when an event matches ANY of the following BB rules:
BB:Oracle Middleware Java Parent Spawning High-Risk Interpreter
followed within 5 minutes by an event matches ANY of the following BB rules:
BB:Oracle Middleware Retrieval Tool Execution
on same asset (Oracle middleware asset group)
Building Block Guidance
BB:Oracle Middleware Retrieval Tool Execution
- Event category: Process Creation
- Parent process equals java or java.bin OR parent command line contains weblogic
- Child process in curl, wget, certutil.exe, bitsadmin.exe
- Asset is in Oracle middleware asset group
Rule Name
Oracle Middleware Encoded or Inline Command Execution
Purpose
Detect high-confidence malicious execution involving encoded or inline commands originating from Oracle middleware processes.
Tuning Explanation
This rule improves detection fidelity by requiring suspicious command-line indicators in addition to middleware execution context.
Administrator Localization Instructions
· Ensure command-line logging is enabled and parsed
· Create custom properties for:
o full command line
o parent command line
· Restrict to Oracle middleware asset group
· Suppress legitimate:
o maintenance scripts
o deployment tooling
· Tune command-line indicators if needed
Logical Notes
High-confidence refinement of Scenario 2.
Rule Regret Check
Deployment caution
Requires command-line visibility.
Confidence caution
High after exclusions.
Coverage value
Very high.
Execution Validity
Deployable with command-line parsing and tuning.
Telemetry Dependency
Endpoint telemetry with command-line fields.
SIEM or system-ready code
Rule Logic
when an event matches ALL of the following:
- Event category is Process Creation
- Asset is in Oracle middleware asset group
- Parent process equals java or java.bin OR parent command line contains weblogic
- Process name in powershell.exe, pwsh.exe, cmd.exe, sh, bash, python, python3
- Command line contains:
" -enc "
"powershell -e"
"base64"
"/tmp/"
then create offense "Oracle Middleware Encoded or Inline Command Execution"
Rule Name
Oracle Middleware Suspicious Execution Followed by Disallowed Outbound Connection
Purpose
Detect post-exploitation expansion by correlating suspicious middleware execution with outbound connections originating from the same middleware asset to disallowed destinations.
Tuning Explanation
This is a supporting correlation rule. It is hardened to ensure that outbound activity is tied to middleware-originated traffic rather than generic host-level network noise.
Administrator Localization Instructions
· Ensure network telemetry correctly attributes traffic to middleware assets
· Build and maintain approved destination reference sets
· Replace placeholder allowlist logic with:
o approved CIDR ranges
o approved domains
· Separate handling for:
o external disallowed traffic
o internal east-west disallowed traffic
· Correlate with:
o execution rules
o staging rules
Logical Notes
Maps to Scenario 4 and supports correlation-based detection.
Rule Regret Check
Deployment caution
Requires destination baseline and asset attribution.
Confidence caution
Medium standalone, high when correlated.
Coverage value
High-value supporting detection.
Execution Validity
Deployable with destination allowlisting.
Telemetry Dependency
Network telemetry with asset attribution and reference sets.
SIEM or system-ready code
Rule Logic
when an event matches ANY of the following BB rules:
BB:Oracle Middleware Java Parent Spawning High-Risk Interpreter
followed within 5 minutes by an event matches ANY of the following BB rules:
BB:Oracle Middleware Disallowed Outbound Connection
on same asset (Oracle middleware asset group)
Building Block Guidance
BB:Oracle Middleware Disallowed Outbound Connection
- Event category: Network / Flow / Proxy
- Source asset is in Oracle middleware asset group and represents middleware-originated traffic
- Destination is NOT in approved middleware destination reference sets
QRadar Deployment Variant Guidance
Direct internet-facing variant
Prioritize exploit-attempt plus execution rule at highest severity.
Reverse proxy variant
Ensure backend middleware asset identity is preserved.
Internal reachability variant
Prioritize execution plus staging and outbound correlation rules.
Sigma
Rule Name
Oracle Middleware Java Parent Spawning High-Risk Interpreter
Purpose
Detect likely successful exploitation of CVE-2026-21992 by identifying Oracle middleware service processes spawning shell or scripting interpreters that are not expected during normal Oracle Identity Manager or Oracle Web Services Manager operation.
Tuning Explanation
This is the primary Sigma host-execution rule for this CVE. The strongest signal is abnormal interpreter execution from Oracle middleware Java service context.
This rule is intentionally written as a portable template and requires backend-specific field mapping and middleware scoping before deployment.
Administrator Localization Instructions
· Map fields for:
o process image
o parent process image
o parent command line
· Restrict to Oracle middleware assets or host groups
· Add environment-specific scoping:
o Oracle home paths
o WebLogic domain paths
o middleware service accounts
· Ensure both Linux and Windows coverage are preserved
· Suppress approved:
o maintenance scripts
o patching workflows
o orchestration tooling
Logical Notes
Primary Sigma detection for Scenario 2.
Rule Regret Check
Deployment caution
Will over-alert without middleware scoping.
Confidence caution
High after tuning.
Coverage value
Very high.
Execution Validity
Deployable with field mapping and asset scoping.
Telemetry Dependency
Process creation logs with parent-child relationships.
SIEM or system-ready code
title: Oracle Middleware Java Parent Spawning High-Risk Interpreter
id: 6a2f4d3d-5f65-4e4e-b9b4-2d0cc6d4e201
status: experimental
logsource:
category: process_creation
detection:
selection_parent_image:
ParentImage|endswith:
- '\java.exe'
- '\java.bin'
- '/java'
selection_parent_cmd:
ParentCommandLine|contains: 'weblogic'
selection_child:
Image|endswith:
- '\cmd.exe'
- '\powershell.exe'
- '\pwsh.exe'
- '\python.exe'
- '\python3.exe'
- '\perl.exe'
- '/sh'
- '/bash'
- '/ksh'
- '/python'
- '/python3'
condition: (1 of selection_parent_*) and selection_child
falsepositives:
- Approved middleware administration
level: high
tags:
- attack.execution
- attack.t1059
Rule Name
Oracle Middleware Service Launching External Retrieval Tool
Purpose
Detect post-exploitation staging where Oracle middleware launches tools commonly used for payload retrieval.
Tuning Explanation
This rule focuses strictly on retrieval tooling to avoid overlap with execution or encoded-command detections.
Administrator Localization Instructions
· Map process fields correctly
· Restrict to Oracle middleware hosts
· Validate legitimate use of:
o curl
o wget
o certutil
o bitsadmin
· Suppress automation and deployment tooling
· Ensure Linux and Windows coverage
Logical Notes
Maps to staging activity following execution.
Rule Regret Check
Deployment caution
May trigger on automation without suppression.
Confidence caution
Medium to high after tuning.
Coverage value
High.
Execution Validity
Deployable with suppression and scoping.
Telemetry Dependency
Process creation logs.
SIEM or system-ready code
title: Oracle Middleware Service Launching External Retrieval Tool
id: bfd2d497-1f49-4b0d-bb18-736f4ee8f202
status: experimental
logsource:
category: process_creation
detection:
selection_parent:
ParentImage|endswith:
- '\java.exe'
- '\java.bin'
- '/java'
selection_parent_cmd:
ParentCommandLine|contains: 'weblogic'
selection_child:
Image|endswith:
- '\curl.exe'
- '\wget.exe'
- '\certutil.exe'
- '\bitsadmin.exe'
- '/curl'
- '/wget'
condition: (1 of selection_parent_*) and selection_child
falsepositives:
- Deployment tools
- Patch automation
level: medium
tags:
- attack.command_and_control
- attack.t1105
Rule Name
Oracle Middleware Encoded or Inline Command Execution
Purpose
Detect high-confidence malicious execution using encoded or inline command patterns originating from Oracle middleware.
Tuning Explanation
Refinement rule requiring suspicious command-line indicators in addition to middleware execution context.
Administrator Localization Instructions
· Ensure command-line logging is available
· Map command-line fields correctly
· Restrict to middleware hosts
· Suppress approved scripts
· Tune patterns based on environment
Logical Notes
High-confidence execution confirmation.
Rule Regret Check
Deployment caution
Requires command-line visibility.
Confidence caution
High.
Coverage value
Very high.
Execution Validity
Deployable with command-line telemetry.
Telemetry Dependency
Process creation with command-line fields.
SIEM or system-ready code
title: Oracle Middleware Encoded or Inline Command Execution
id: 94d5c32b-80f8-4cb5-8fd2-28cc6f91f203
status: experimental
logsource:
category: process_creation
detection:
selection_parent:
ParentImage|endswith:
- '\java.exe'
- '\java.bin'
- '/java'
selection_parent_cmd:
ParentCommandLine|contains: 'weblogic'
selection_child:
Image|endswith:
- '\powershell.exe'
- '\pwsh.exe'
- '\cmd.exe'
- '\python.exe'
- '\python3.exe'
- '/sh'
- '/bash'
- '/python'
- '/python3'
selection_cmd:
CommandLine|contains:
- ' -enc '
- 'powershell -e'
- 'base64'
- '/tmp/'
condition: (1 of selection_parent_*) and selection_child and selection_cmd
falsepositives:
- Approved encoded scripts
level: high
tags:
- attack.execution
- attack.t1059
Rule Name
Oracle Middleware Process with Disallowed Outbound Network Connection
Purpose
Detect middleware-originated outbound connections to disallowed destinations, indicating possible post-exploitation activity.
Tuning Explanation
Sigma cannot reliably enforce process-to-network correlation across all backends. This rule is intentionally written as a portable detection that must be correlated downstream with execution alerts.
Administrator Localization Instructions
· Confirm backend supports:
o process-attributed network telemetry
· Map fields for:
o source host
o destination IP
o destination domain
· Replace placeholders with:
o approved CIDR ranges
o approved domains
· Restrict to Oracle middleware assets
· Correlate with execution detections in SIEM
Logical Notes
Supporting rule for Scenario 4. Requires correlation.
Rule Regret Check
Deployment caution
Not all environments support process-attributed network logs.
Confidence caution
Medium standalone, high when correlated.
Coverage value
Supporting but important.
Execution Validity
Conditionally deployable depending on telemetry.
Telemetry Dependency
Network telemetry with process attribution (e.g., Sysmon, Elastic Defend, EDR-backed logs).
SIEM or system-ready code
title: Oracle Middleware Process with Disallowed Outbound Network Connection
id: 2c9f8e51-f8c0-4f4d-9c86-bd66535ff204
status: experimental
logsource:
category: network_connection
detection:
selection_process:
Image|endswith:
- '\java.exe'
- '\java.bin'
- '/java'
selection_cmd:
CommandLine|contains: 'weblogic'
filter_dest:
DestinationIp|cidr:
- <APPROVED_CIDR_RANGE>
condition: (1 of selection_*) and not filter_dest
falsepositives:
- Approved middleware communications
level: medium
tags:
- attack.command_and_control
Sigma Correlation Guidance (Critical)
Sigma rules do not enforce cross-event correlation.
These detections must be correlated downstream by:
· host identity
· time proximity
· execution plus staging behavior
Recommended correlation pattern:
· Execution rule → primary signal
· Retrieval or outbound rule → confirmation
Encoded rule → high-confidence escalation
YARA
Rule Name
Oracle Middleware Suspicious JSP or Java Web Shell Artifact
Purpose
Detect suspicious JSP or Java-based web shell artifacts that may be dropped or modified on Oracle middleware hosts after successful exploitation of CVE-2026-21992.
Tuning Explanation
This is the highest-confidence YARA use case for this CVE: identifying execution-capable web-shell-like content in middleware-adjacent application material. The rule is intentionally focused on JSP and Java execution constructs rather than mixing in broader script patterns.
This rule should be used against:
· recently created or modified JSP files
· extracted application content
· suspicious web-accessible deployment paths
· middleware temp locations where modified application components may appear
Administrator Localization Instructions
· Restrict scanning to:
o WebLogic domain application paths
o Oracle middleware deployment directories
o recently modified JSP or web application content
· Exclude known-good vendor files and approved custom applications where possible
· Prefer change-based scoping:
o recent file creation
o recent modification
o unexpected deployment path changes
· Pair hits with:
o suspicious process execution
o web application file modification alerts
o deployment change windows
· Do not run this broadly across all Java content without location scoping
Logical Notes
This is the primary YARA rule for web-shell-style persistence or modified web component detection in Oracle middleware environments.
Rule Regret Check
Deployment caution
Can be noisy if run indiscriminately across all JSP or Java application content.
Confidence caution
High when scoped to recent or suspicious files in middleware-relevant locations.
Coverage value
Very high for post-exploitation persistence and artifact confirmation.
Execution Validity
Deployable with path scoping and vendor-content exclusions required.
Telemetry Dependency
Filesystem or artifact scanning capability against middleware deployment content.
SIEM or system-ready code
rule CYBERDAX_Oracle_Middleware_Suspicious_JSP_Or_Java_WebShell_Artifact
{
meta:
description = "Detects suspicious JSP or Java web-shell-like content on Oracle middleware hosts"
author = "CyberDax"
reference = "CVE-2026-21992"
scope = "Post-exploitation JSP/Java artifact detection"
confidence = "high"
strings:
$jsp_1 = "<%@ page" nocase
$jsp_2 = "request.getParameter(" nocase
$jsp_3 = "response.getWriter()" nocase
$java_1 = "Runtime.getRuntime().exec" nocase
$java_2 = "new ProcessBuilder" nocase
$java_3 = "java.lang.Runtime" nocase
$util_1 = "cmd.exe /c" nocase
$util_2 = "/bin/sh -c" nocase
condition:
(2 of ($jsp_*)) and (1 of ($java_*) or 1 of ($util_*))
or
(2 of ($java_*)) and 1 of ($util_*)
}
Rule Name
Oracle Middleware Suspicious Encoded or Staged Script Artifact
Purpose
Detect suspicious encoded, staged, or inline-execution script artifacts that may be dropped or stored on Oracle middleware systems after compromise.
Tuning Explanation
This rule is focused on encoded or staged script content rather than JSP or Java web-shell content. It is intended for file hunting, malware triage, and post-incident sweeps where suspicious scripts may remain on disk even after execution has occurred.
This rule is strongest when used against:
· newly created scripts
· temp or staging directories
· suspicious administrative script locations
· artifact collections tied to prior execution alerts
Administrator Localization Instructions
· Restrict scans to:
o temp directories
o staging directories
o recently created script files
o middleware-adjacent script repositories
· Exclude known-good encoded administrative artifacts if they exist
· Validate local legitimate use of:
o base64 decoding
o inline PowerShell
o inline Python
o temp-path execution
· Use alongside:
o SentinelOne encoded-command detections
o SIEM process telemetry
o file creation events
· Do not rely on this as a stand-alone exploit detector
Logical Notes
This is a focused hunt and confirmation rule for suspicious encoded or staged script content.
Rule Regret Check
Deployment caution
Can alert on legitimate automation artifacts if encoded content is normal in the environment.
Confidence caution
Medium to high after local exclusions and file-scope reduction.
Coverage value
Strong post-exploitation artifact and hunting support.
Execution Validity
Deployable with scope reduction and encoded-content exclusions required.
Telemetry Dependency
YARA-capable file or memory scanning on middleware hosts or collected artifacts.
SIEM or system-ready code
rule CYBERDAX_Oracle_Middleware_Encoded_Or_Staged_Script_Artifact
{
meta:
description = "Detects encoded or staged script artifacts associated with suspicious Oracle middleware post-exploitation behavior"
author = "CyberDax"
reference = "CVE-2026-21992"
scope = "Post-exploitation script hunting"
confidence = "medium_high"
strings:
$enc_1 = " -enc " nocase
$enc_2 = "powershell -e" nocase
$enc_3 = "FromBase64String" nocase
$enc_4 = "base64 -d" nocase
$enc_5 = "python -c" nocase
$stager_1 = "curl " nocase
$stager_2 = "wget " nocase
$stager_3 = "certutil -urlcache" nocase
$stager_4 = "bitsadmin /transfer" nocase
condition:
(2 of ($enc_*))
or
(1 of ($enc_*) and 1 of ($stager_*))
}
Rule Name
Oracle Middleware Suspicious Dropped Tool or Payload Bundle
Purpose
Detect suspicious dropped binaries, archives, or bundled payload material that may be staged on Oracle middleware hosts after exploitation.
Tuning Explanation
This is the lowest-confidence YARA rule in the set and should be treated as a supporting hunt rule, not a primary artifact-confirmation rule. It is intended for targeted scans of suspicious new files, bundles, or archives found near middleware systems after likely compromise.
This rule is deliberately narrower than the prior draft and should be used only in:
· recently created files
· suspicious temp or staging locations
· artifact triage following execution alerts
· bundle or archive review during incident response
Administrator Localization Instructions
· Restrict scanning to:
o newly created or recently modified files
o temp and staging directories
o middleware-adjacent suspicious locations
· Exclude:
o vendor installers
o approved patches
o sanctioned deployment bundles
· Use with:
o file creation telemetry
o hash reputation workflows
o endpoint execution history
· Do not use this as a broad recursive scan across all Oracle software directories
· Treat hits as triage leads that require context, not as stand-alone compromise proof
Logical Notes
This is a supporting artifact-hunting rule for staged tools or packaged payload material.
Rule Regret Check
Deployment caution
Can be noisy without recent-change scoping and approved-bundle exclusions.
Confidence caution
Low to medium as a stand-alone artifact rule.
Coverage value
Useful supporting hunt logic when tied to suspicious execution or file creation.
Execution Validity
Deployable with recent-change scoping and approved-bundle exclusions required.
Telemetry Dependency
File collection, archive scanning, or endpoint artifact triage workflow with YARA support.
SIEM or system-ready code
rule CYBERDAX_Oracle_Middleware_Suspicious_Dropped_Tool_Or_Payload_Bundle
{
meta:
description = "Detects suspicious dropped tools or payload bundles on Oracle middleware hosts"
author = "CyberDax"
reference = "CVE-2026-21992"
scope = "Supporting dropped artifact hunting"
confidence = "low_medium"
strings:
$mz = "MZ"
$zip = "PK\x03\x04"
$script1 = "#!/bin/sh" nocase
$script2 = "#!/bin/bash" nocase
$tool_1 = "curl " nocase
$tool_2 = "wget " nocase
$tool_3 = "certutil" nocase
$tool_4 = "bitsadmin" nocase
$tool_5 = "base64" nocase
condition:
($mz at 0 and 1 of ($tool_*))
or
($zip at 0 and 1 of ($tool_*))
or
((1 of ($script*)) and 1 of ($tool_*))
}
YARA Deployment Variant Guidance
Direct internet-facing variant
Prioritize targeted scans of recently created or modified files on internet-facing or reverse-proxy-backed middleware systems after suspicious inbound activity or suspicious host execution.
Reverse proxy or load balancer variant
Use YARA against backend middleware hosts and recently modified application content, because payload artifacts and web-shell-style implants are more likely to reside there than on upstream proxy infrastructure.
Internal reachability variant
Place more weight on encoded-script and dropped-tool hunting, especially where initial exploit delivery may not be visible at the perimeter.
YARA Correlation Guidance
YARA detections do not confirm exploitation by themselves.
These rules should be correlated downstream with:
· suspicious middleware interpreter execution
· retrieval-tool execution
· new or modified middleware-adjacent files
· suspicious outbound connections
· maintenance and deployment change windows
Recommended use pattern:
· endpoint or SIEM alert triggers targeted YARA sweep
· YARA hit strengthens confidence in post-exploitation artifact presence
· no YARA hit does not prove absence of compromise
AWS
Rule Name
Oracle Middleware Suspicious Untrusted POST to Tuned Middleware Path via AWS WAF
Purpose
Detect likely exploit-attempt activity targeting Oracle middleware exposed through AWS-managed ingress by identifying suspicious POST requests to tuned Oracle middleware paths.
Tuning Explanation
This is the primary AWS ingress-layer detection for exploit attempts where AWS WAF is deployed in front of Oracle middleware.
This rule assumes structured WAF logs have been normalized into CloudWatch Logs fields. If logs are ingested in raw JSON form or routed through a SIEM pipeline, field names must be adjusted accordingly.
This remains a supporting exploit-attempt signal, not proof of compromise.
Administrator Localization Instructions
· Restrict scope to WAF web ACLs protecting Oracle middleware applications
· Replace all path patterns with validated, application-specific middleware routes
· Validate whether logged URI reflects:
o original request path
o rewritten backend path
· Suppress:
o health checks
o synthetic monitoring
o approved scanners
· Confirm ingestion pipeline parsing produces:
o httpRequest.clientIp
o httpRequest.uri
o httpRequest.httpMethod
· Correlate with:
o endpoint execution detections
o outbound anomalies
o application fault spikes
Logical Notes
Ingress visibility is often incomplete in cloud environments. Treat this as an early signal, not a confirmation.
Rule Regret Check
Deployment caution
Fails silently if field normalization is incorrect or URI logging is altered by upstream services.
Confidence caution
Medium to high after tuning.
Coverage value
High-value ingress detection.
Execution Validity
Deployable with log normalization validation and path tuning.
Telemetry Dependency
AWS WAF logs with structured request fields.
SIEM or system-ready code
fields @timestamp,
httpRequest.clientIp as client_ip,
httpRequest.httpMethod as http_method,
httpRequest.uri as uri,
action
| filter http_method = "POST"
| filter like(tolower(uri), "/oim/%")
or like(tolower(uri), "/identity/%")
or like(tolower(uri), "/iam/%")
or like(tolower(uri), "/owsm/%")
or like(tolower(uri), "/wsm/%")
| stats count(*) as request_count by client_ip, uri, action
| sort request_count desc
Rule Name
Oracle Middleware Ingress 5xx Spike Following Suspicious Tuned POST Activity via ALB
Purpose
Detect application instability or exploit testing by identifying spikes in server error responses following suspicious middleware-targeted requests.
Tuning Explanation
This is a supporting side-effect detection rule. Static thresholds are inherently unreliable in cloud environments.
This rule should be deployed using a baseline-first approach:
· establish normal 5xx rate
· identify deviation
· only fall back to static thresholds if necessary
Administrator Localization Instructions
· Restrict to ALBs fronting Oracle middleware
· Validate log parsing for:
o request path
o status codes
· Establish baseline:
o average 5xx rate
o peak expected rate
· Preferred:
o anomaly detection or percentile thresholds
· Fallback:
o static threshold only after baseline validation
· Suppress:
o deployments
o maintenance windows
o known instability events
Logical Notes
This rule detects exploit side effects, not exploitation itself.
Rule Regret Check
Deployment caution
Static thresholds without baseline will produce noise.
Confidence caution
Medium standalone; higher when correlated.
Coverage value
Good supporting signal.
Execution Validity
Deployable with baseline tuning.
Telemetry Dependency
ALB access logs with parsed fields.
SIEM or system-ready code
fields @timestamp,
client_ip,
request_verb,
request_url,
elb_status_code,
target_status_code
| filter request_verb = "POST"
| filter like(tolower(request_url), "/oim/%")
or like(tolower(request_url), "/identity/%")
or like(tolower(request_url), "/iam/%")
or like(tolower(request_url), "/owsm/%")
or like(tolower(request_url), "/wsm/%")
| filter elb_status_code >= 500 or target_status_code >= 500
| stats count(*) as fault_count by client_ip, request_url
| sort fault_count desc
Rule Name
Oracle Middleware Exposure Increase via Security Group or Load Balancer Change
Purpose
Detect control-plane changes that increase exposure of Oracle middleware resources and raise exploitation risk.
Tuning Explanation
This rule is implemented as a two-stage detection model:
1. EventBridge selector detects relevant CloudTrail events
2. Enrichment and decision logic determines whether the change impacts Oracle middleware
EventBridge alone does not provide full detection context.
Administrator Localization Instructions
· Maintain authoritative tagging:
o App=OracleMiddleware
· Build enrichment pipeline to:
o map security groups to middleware resources
o validate change against:
§ change tickets
§ deployment pipelines
· Suppress:
o infrastructure-as-code deployments
o approved change windows
· Elevate severity when:
o exposure expands to 0.0.0.0/0 or equivalent
Logical Notes
This is a risk amplification rule, not a compromise detection.
Rule Regret Check
Deployment caution
Incomplete tagging or enrichment breaks detection accuracy.
Confidence caution
High for exposure change, not compromise.
Coverage value
Very high for preventive monitoring.
Execution Validity
Deployable with enrichment and tagging maturity.
Telemetry Dependency
CloudTrail via EventBridge.
SIEM or system-ready code
{
"source": ["aws.ec2", "aws.elasticloadbalancing"],
"detail-type": ["AWS API Call via CloudTrail"],
"detail": {
"eventName": [
"AuthorizeSecurityGroupIngress",
"ModifySecurityGroupRules",
"SetSecurityGroups",
"ApplySecurityGroupsToLoadBalancer"
]
}
}
Required Enrichment Logic
· Match affected resources to middleware asset inventory
· Validate against approved changes
· Determine exposure delta
Rule Name
Oracle Middleware Disallowed Outbound Connection from Middleware-Attributed AWS Resource
Purpose
Detect potential post-exploitation activity by identifying outbound connections from AWS resources attributed to Oracle middleware.
Tuning Explanation
This rule is conditionally deployable and depends on accurate asset attribution.
Without:
· ENI to instance mapping
· tag-based workload identification
· destination allowlists
this rule will either fail silently or produce noise.
Administrator Localization Instructions
· Prefer tag-based scoping over static ENI lists
· Maintain mapping between:
o EC2 instances
o ENIs
o middleware workloads
· Build approved destination allowlists:
o internal services
o identity systems
o databases
· Separate:
o external egress
o internal east-west traffic
· Correlate with:
o execution alerts
o staging activity
Logical Notes
Supporting detection only. Not valid as standalone compromise signal.
Rule Regret Check
Deployment caution
Fails open if asset attribution is weak.
Confidence caution
Medium standalone; high when correlated.
Coverage value
High-value supporting detection.
Execution Validity
Conditionally deployable based on asset maturity.
Telemetry Dependency
VPC Flow Logs with enrichment.
SIEM or system-ready code
fields @timestamp, interfaceId, srcAddr, dstAddr, dstPort, action
| filter action = "ACCEPT"
| filter interfaceId in [<TAG_RESOLVED_MIDDLEWARE_ENIS>]
| filter not isIpInSubnet(dstAddr, "<APPROVED_DESTINATION_CIDR>")
| stats count(*) as connection_count by interfaceId, dstAddr, dstPort
| sort connection_count desc
AWS Correlation Guidance
AWS signals must be correlated with:
· endpoint execution telemetry
· SIEM detections
· network IDS signals
AWS alone does not confirm exploitation.
Azure
Rule Name
Oracle Middleware Suspicious Untrusted POST to Tuned Middleware Path via Azure WAF
Purpose
Detect likely exploit-attempt activity targeting Oracle middleware by identifying suspicious POST requests to middleware-relevant paths in Azure WAF telemetry.
Tuning Explanation
This is the primary Azure ingress-layer detection for exploit-attempt visibility. It is intended for environments where Oracle middleware is fronted by Azure Application Gateway WAF or Azure Front Door WAF.
This rule assumes Log Analytics ingestion and must be localized to the actual schema in use. It is a supporting exploit-attempt signal, not proof of compromise.
Administrator Localization Instructions
· Confirm whether logs are stored in AzureDiagnostics or a normalized Sentinel table.
· Validate the actual field names for:
o client IP
o request URI
o HTTP method
· Replace all generic URI fragments with validated Oracle middleware routes.
· Confirm whether the logged URI reflects the original request path or a rewritten backend route.
· Scope the rule to WAF instances protecting Oracle middleware only.
· Suppress:
o health probes
o synthetic monitoring
o approved scanners
o sanctioned internal testing
· Correlate with:
o endpoint execution detections
o outbound anomaly detections
o application fault detections
Logical Notes
This rule provides early ingress visibility only. It should not be treated as exploit confirmation.
Rule Regret Check
Deployment caution
Will fail or degrade if schema normalization is incorrect or URI rewriting obscures the real middleware route.
Confidence caution
Medium to high after path and schema tuning.
Coverage value
High-value ingress exploit-attempt visibility.
Execution Validity
Deployable after schema validation and path localization.
Telemetry Dependency
Azure WAF logs in Log Analytics.
SIEM or system-ready code
AzureDiagnostics
| where Category in ("ApplicationGatewayFirewallLog", "FrontDoorWebApplicationFirewallLog")
| extend method = coalesce(httpMethod_s, tostring(parse_json(request_s).method))
| extend uri = coalesce(requestUri_s, tostring(parse_json(request_s).uri))
| extend client_ip = coalesce(clientIP_s, clientIp_s)
| where method == "POST"
| where tolower(uri) has_any ("/oim", "/identity", "/iam", "/owsm", "/wsm")
| summarize request_count = count() by client_ip, uri
| order by request_count desc
Rule Name
Oracle Middleware 5xx Fault Spike Following Suspicious Requests via Azure Application Gateway
Purpose
Detect exploit-side effects by identifying abnormal increases in 5xx responses tied to middleware-targeted requests.
Tuning Explanation
This is a side-effect detection rule. It is useful for detecting exploit testing, malformed requests, or application instability following suspicious requests to Oracle middleware.
This rule must be baseline-driven. Static thresholds should be used only after normal fault behavior is understood.
Administrator Localization Instructions
· Confirm whether the relevant logs are in AzureDiagnostics or a normalized access-log table.
· Validate actual fields for:
o request URI
o HTTP method
o status code
· Establish:
o normal 5xx rate
o peak expected rate
o known noisy periods
· Prefer anomaly- or baseline-based alerting over static thresholds.
· Suppress:
o maintenance windows
o deployment periods
o known instability events
· Correlate with suspicious ingress activity from Rule 1.
Logical Notes
This is supporting evidence only. It does not confirm exploitation.
Rule Regret Check
Deployment caution
Static thresholds without a baseline will create noise.
Confidence caution
Medium standalone; higher when correlated with suspicious POST activity.
Coverage value
Strong supporting exploit-side-effect signal.
Execution Validity
Deployable after baseline establishment.
Telemetry Dependency
Application Gateway or Front Door access logs in Log Analytics.
SIEM or system-ready code
AzureDiagnostics
| where Category in ("ApplicationGatewayAccessLog", "FrontDoorAccessLog")
| extend method = coalesce(httpMethod_s, tostring(parse_json(request_s).method))
| extend uri = coalesce(requestUri_s, tostring(parse_json(request_s).uri))
| where method == "POST"
| where tolower(uri) has_any ("/oim", "/identity", "/iam", "/owsm", "/wsm")
| where httpStatus_d between (500 .. 599)
| summarize fault_count = count() by bin(TimeGenerated, 5m), uri
| order by fault_count desc
Rule Name
Oracle Middleware Exposure Increase via NSG, Public IP, or Application Gateway Change
Purpose
Detect control-plane changes that materially increase the exposure of Oracle middleware resources.
Tuning Explanation
This is a risk-amplification rule, not a compromise-detection rule. It should identify meaningful exposure increase, not generic configuration churn.
A production-quality implementation requires a two-stage model:
· change selector
· exposure delta evaluation using prior state
Without prior-state comparison, this degrades into noisy config-change monitoring.
Administrator Localization Instructions
· Maintain authoritative identification of Oracle middleware resources through:
o resource tags
o resource groups
o CMDB or inventory linkage
· Scope to:
o NSG rules
o Public IP resources
o Application Gateway frontend exposure
· Build enrichment to determine:
o whether the changed resource supports Oracle middleware
o whether exposure increased relative to prior state
o whether the change was approved
· Suppress:
o infrastructure-as-code pipelines
o approved change windows
· Elevate severity when the change results in:
o new public exposure
o broader inbound allow ranges
o 0.0.0.0/0
o ::/0
Logical Notes
This rule detects increased exploitability, not compromise.
Rule Regret Check
Deployment caution
Will be weak and noisy without prior-state comparison and change-context enrichment.
Confidence caution
High after enrichment; low if used as raw write-event monitoring only.
Coverage value
Very high for preventive exposure monitoring.
Execution Validity
Deployable only with enrichment and prior-state context.
Telemetry Dependency
AzureActivity plus a baseline or prior-state source.
SIEM or system-ready code
let MiddlewareResources =
ResourceGraphResources
| where tags.App =~ "OracleMiddleware"
| project ResourceId = tolower(id);
let Changes =
AzureActivity
| where ActivityStatusValue == "Succeeded"
| where OperationNameValue has_any (
"NETWORKSECURITYGROUPS/SECURITYRULES/WRITE",
"APPLICATIONGATEWAYS/WRITE",
"PUBLICIPADDRESSES/WRITE"
)
| extend ResourceId = tolower(_ResourceId)
| join kind=inner MiddlewareResources on ResourceId
| extend Props = tostring(parse_json(Properties).requestBody)
| extend PublicExposure = Props has "0.0.0.0/0" or Props has "::/0"
| extend InboundAllow = Props has "Inbound" and Props has "Allow"
| extend PublicIP = OperationNameValue has "PUBLICIPADDRESSES"
| where PublicExposure or InboundAllow or PublicIP
| project TimeGenerated, ResourceId, OperationNameValue, Caller
| order by TimeGenerated desc
Required Enrichment Logic
· Map resource to Oracle middleware inventory.
· Retrieve prior exposure state.
· Determine whether exposure increased.
· Validate against approved change context.
Rule Name
Oracle Middleware Suspicious Outbound Connection from Middleware-Attributed Azure Resource
Purpose
Detect potential post-exploitation behavior by identifying outbound connections from Azure resources attributed to Oracle middleware.
Tuning Explanation
This is a supporting post-exploitation rule and is conditionally deployable. Its value depends on accurate middleware attribution and outbound allowlisting.
Without mature attribution, this rule becomes noisy or misleading.
Administrator Localization Instructions
· Prefer:
o tag-based scoping
o resource-group scoping
o CMDB-backed workload mapping
· Maintain mapping between:
o VM and middleware workload
o subnet and middleware tier
· Build approved destination allowlists for:
o internal services
o identity systems
o databases
o approved repositories
· Separate handling for:
o external outbound traffic
o internal east-west traffic
· Correlate with:
o endpoint execution detections
o staging behavior
o ingress exploit-attempt signals
Logical Notes
This is supporting detection only. It should not stand alone as proof of compromise.
Rule Regret Check
Deployment caution
Will fail open if asset attribution is weak or stale.
Confidence caution
Medium standalone; high when correlated.
Coverage value
High-value supporting post-exploitation signal.
Execution Validity
Conditionally deployable based on attribution maturity.
Telemetry Dependency
AzureNetworkAnalytics_CL or equivalent Azure network telemetry.
SIEM or system-ready code
AzureNetworkAnalytics_CL
| where FlowDirection_s == "O"
| where AllowedOutFlows_d > 0
| where VM_s in (<TAG_RESOLVED_MIDDLEWARE_QUERY>)
| summarize connection_count = sum(AllowedOutFlows_d) by VM_s, DestIP_s, DestPort_d
| order by connection_count desc
Azure Correlation Guidance
Azure detections should be correlated with:
· endpoint execution telemetry
· SIEM detections
· ingress exploit-attempt signals
· control-plane change context
Azure alone does not confirm exploitation.
GCP
Rule Name
Oracle Middleware Suspicious Untrusted POST to Tuned Middleware Path via Cloud Armor or External Application Load Balancer
Purpose
Detect likely exploit-attempt activity targeting Oracle middleware by identifying suspicious POST requests to middleware-relevant paths observed at GCP ingress.
Tuning Explanation
This is the primary GCP ingress-layer detection for exploit-attempt visibility. It applies where Oracle middleware is exposed through Cloud Armor and external HTTP(S) Load Balancers.
This rule depends on:
· request logging being enabled for the relevant backend service
· correct backend-to-middleware mapping
· validation that logged request paths reflect the paths actually used to reach Oracle middleware
This is a signal rule, not proof of compromise.
Administrator Localization Instructions
· Enable and validate request logging for backend services serving Oracle middleware
· Restrict scope to:
o specific backend services
o specific URL maps
o forwarding rules that front Oracle middleware
· Replace all generic URI fragments with validated Oracle middleware routes
· Confirm whether the logged request path reflects:
o the original client request
o a rewritten backend path
· Suppress:
o health checks
o synthetic monitoring
o approved scanners
o sanctioned internal testing
· Correlate with:
o endpoint execution telemetry
o outbound anomaly detections
o load balancer fault detections
Logical Notes
This rule is valuable for early ingress visibility but should not be treated as exploitation confirmation. It is strongest where Cloud Armor and backend logging are both complete and accurately attributed to middleware-serving backends.
Rule Regret Check
Deployment caution
Will degrade sharply if backend logging is disabled, backend attribution is weak, or URI rewriting obscures the true middleware route.
Confidence caution
Medium to high after path and backend tuning.
Coverage value
High-value ingress exploit-attempt visibility.
Execution Validity
Deployable after:
· backend logging validation
· backend-to-middleware scoping
· route localization
Telemetry Dependency
· Cloud Armor request logs
· external HTTP(S) Load Balancer logs
· backend-service attribution
SIEM or system-ready code
resource.type="http_load_balancer"
resource.labels.backend_service_name="<MIDDLEWARE_BACKEND_SERVICE>"
httpRequest.requestMethod="POST"
(
REGEXP_CONTAINS(LOWER(httpRequest.requestUrl), "/oim") OR
REGEXP_CONTAINS(LOWER(httpRequest.requestUrl), "/identity") OR
REGEXP_CONTAINS(LOWER(httpRequest.requestUrl), "/iam") OR
REGEXP_CONTAINS(LOWER(httpRequest.requestUrl), "/owsm") OR
REGEXP_CONTAINS(LOWER(httpRequest.requestUrl), "/wsm")
)
Rule Name
Oracle Middleware 5xx Fault Spike Following Suspicious Requests via External Load Balancer
Purpose
Detect exploit-side effects by identifying abnormal increases in 5xx responses tied to middleware-targeted requests.
Tuning Explanation
This is a supporting side-effect detection rule. It is intended to surface:
· exploit testing
· malformed payload attempts
· application instability following suspicious requests to Oracle middleware
This rule must use a baseline-first model:
· establish normal 5xx behavior
· measure deviation
· use static thresholds only as a fallback
This is not a primary exploit-confirmation rule.
Administrator Localization Instructions
· Confirm load balancer logging is enabled for middleware-serving backend services
· Restrict scope to:
o the same backend services used by Rule 1
o middleware-facing load balancers only
· Validate actual fields used in your logging pipeline for:
o request path
o response status
o backend identity
· Establish:
o normal 5xx rate
o peak expected rate
o known noisy periods
· Prefer:
o logs-based metrics
o anomaly or deviation alerting
· Suppress:
o maintenance windows
o deployments
o known instability periods
· Correlate with:
o Rule 1 activity
o same path
o same client source
o same backend service where possible
Logical Notes
This rule detects exploit side effects, not exploitation itself. It is most valuable when correlated with suspicious inbound requests and backend-specific error concentration.
Rule Regret Check
Deployment caution
Static thresholds without baseline create noise and reduce trust.
Confidence caution
Medium standalone; higher when correlated with suspicious ingress activity.
Coverage value
Strong supporting exploit-side-effect signal.
Execution Validity
Deployable after baseline establishment and backend scoping.
Telemetry Dependency
· external HTTP(S) Load Balancer logs
· backend-specific request and response visibility
SIEM or system-ready code
resource.type="http_load_balancer"
resource.labels.backend_service_name="<MIDDLEWARE_BACKEND_SERVICE>"
httpRequest.requestMethod="POST"
(
REGEXP_CONTAINS(LOWER(httpRequest.requestUrl), "/oim") OR
REGEXP_CONTAINS(LOWER(httpRequest.requestUrl), "/identity") OR
REGEXP_CONTAINS(LOWER(httpRequest.requestUrl), "/iam") OR
REGEXP_CONTAINS(LOWER(httpRequest.requestUrl), "/owsm") OR
REGEXP_CONTAINS(LOWER(httpRequest.requestUrl), "/wsm")
)
(httpRequest.status>=500)
Rule Name
Oracle Middleware Exposure Increase via Firewall, Forwarding Rule, or Public Entry Change
Purpose
Detect control-plane changes that materially increase exposure of Oracle middleware resources.
Tuning Explanation
This is a risk-amplification rule, not a compromise-detection rule. It is intended to detect actual exposure increase, not generic control-plane churn.
This rule must operate as a delta-based detection model:
1. detect a relevant change
2. map the changed resource to Oracle middleware
3. compare prior state vs new state
4. alert only if exposure materially increased
Without prior-state comparison, this becomes weak configuration-change monitoring.
Administrator Localization Instructions
· Maintain authoritative middleware identification through:
o labels
o instance groups
o backend services
o CMDB or inventory linkage
· Scope to changes affecting:
o firewall rules
o forwarding rules
o backend services
o public entry points or VIP exposure
· Validate fields used in your pipeline for:
o protoPayload.methodName
o request source ranges
o direction
o allowed or denied behavior
· Build enrichment to determine:
o whether the changed resource serves Oracle middleware
o whether prior exposure was lower
o whether the change was approved
· Suppress:
o infrastructure-as-code pipelines
o approved change windows
o validated migration activity
· Elevate severity when the result is:
o 0.0.0.0/0
o ::/0
o newly enabled ingress allow
o newly introduced public entry point
o broadened forwarding-rule reachability to middleware-serving backends
Logical Notes
This rule detects increased exploitability conditions, not attacker activity. It is a preventive monitoring rule and should be treated as such.
Rule Regret Check
Deployment caution
Will be noisy and operationally weak without prior-state comparison and change-context enrichment.
Confidence caution
High after enrichment; low if used as raw write-event monitoring only.
Coverage value
Very high for preventive exposure monitoring.
Execution Validity
Deployable only with:
· middleware resource mapping
· prior-state comparison
· approved-change enrichment
Telemetry Dependency
· Cloud Audit Logs
· prior-state or baseline dataset
· middleware resource inventory
SIEM or system-ready code
logName:"cloudaudit.googleapis.com"
protoPayload.methodName=(
"v1.compute.firewalls.insert" OR
"v1.compute.firewalls.patch" OR
"v1.compute.firewalls.update" OR
"v1.compute.forwardingRules.insert" OR
"v1.compute.forwardingRules.setTarget" OR
"v1.compute.backendServices.update"
)
protoPayload.request.direction="INGRESS"
protoPayload.request.allowed:*
(
protoPayload.request.sourceRanges:"0.0.0.0/0" OR
protoPayload.request.sourceRanges:"::/0"
)
Required Enrichment Logic
· map changed resource to Oracle middleware inventory
· retrieve prior exposure state
· determine whether exposure increased
· validate against approved change context
· downgrade to triage only if prior-state comparison is unavailable
Rule Name
Oracle Middleware Suspicious Outbound Connection from Middleware-Attributed GCP Resource
Purpose
Detect potential post-exploitation behavior via outbound connections from middleware systems.
Tuning Explanation
This is a supporting post-exploitation rule and is conditionally deployable. Its reliability depends on:
· VPC Flow Logs being enabled and accessible
· workload attribution maturity
· destination allowlists being maintained
· the ability to map instances, subnets, or instance groups to Oracle middleware
Without these, the rule becomes noisy or misleading.
Administrator Localization Instructions
· Prefer:
o label-based scoping
o instance-group scoping
o subnet scoping tied to middleware tiers
· Maintain mapping between:
o VM and middleware workload
o subnet and middleware tier
o backend service and instance group where relevant
· Build approved destination allowlists for:
o internal services
o identity systems
o databases
o approved repositories
· Separate handling for:
o external outbound traffic
o internal east-west traffic
· Correlate with:
o endpoint execution detections
o staging behavior
o ingress exploit-attempt signals
· If attribution maturity is weak, downgrade this rule to:
o hunt support
o correlation support
o not direct alerting
Logical Notes
This is supporting detection only. It should not stand alone as proof of compromise.
Rule Regret Check
Deployment caution
Fails open if workload attribution is weak, stale, or inconsistently labeled.
Confidence caution
Medium standalone; high when correlated with suspicious execution or ingress activity.
Coverage value
High-value supporting post-exploitation signal.
Execution Validity
Conditionally deployable based on attribution maturity and destination allowlisting.
Telemetry Dependency
· VPC Flow Logs
· workload attribution via labels, instance groups, or subnet mapping
· destination allowlists
SIEM or system-ready code
resource.type="gce_subnetwork"
log_id("compute.googleapis.com/vpc_flows")
jsonPayload.reporter="SRC"
jsonPayload.src_instance.labels.app="oracle-middleware"
NOT (
jsonPayload.connection.dest_ip=("<APPROVED_IP_1>" OR "<APPROVED_IP_2>")
)
GCP Correlation Guidance
GCP detections should be correlated with:
· endpoint execution telemetry
· SIEM detections
· ingress exploit-attempt signals
· control-plane change context
GCP alone does not confirm exploitation.
S26 Threat-to-Rule Traceability Matrix
Traceability Model
Each entry maps:
Threat Behavior → MITRE Technique → Detection Rules → Telemetry → Coverage Disposition
Coverage classifications:
• Detected — Reliable detection when required telemetry is enabled and scoped
• Partially Detected — Detection depends on baseline, correlation, or incomplete telemetry
• Hunt Only — Detection possible through investigation but not reliable alerting
• Not Covered — No reliable detection via available telemetry
Detected Behaviors
Behavior: Unauthenticated Exploit Delivery and Initial Access
MITRE Techniques
T1190 – Exploit Public-Facing Application
Threat Behavior
Unauthenticated crafted HTTP requests are sent to exposed Oracle middleware interfaces to trigger exploitation of vulnerable components.
Detection Rules
• Suricata — Oracle Fusion Middleware Suspicious Untrusted POST to Tuned OIM or OWSM Service Path
• Suricata — Oracle Fusion Middleware Repeated Untrusted Access to Tuned OIM or OWSM Paths
• Suricata — Oracle Fusion Middleware Untrusted Service-Style POST to Tuned OIM or OWSM Interface
• Suricata — Oracle Fusion Middleware Suspicious 5xx Fault Response After Tuned Untrusted Middleware Request
• Splunk — Oracle Middleware Exploit Attempt Followed by Host Execution
• QRadar — Oracle Middleware Exploit Attempt Followed by Suspicious Host Execution
• AWS — Oracle Middleware Suspicious Untrusted POST to Tuned Middleware Path via AWS WAF
• Azure — Oracle Middleware Suspicious Untrusted POST to Tuned Middleware Path via Azure WAF
• GCP — Oracle Middleware Suspicious Untrusted POST to Tuned Middleware Path via Cloud Armor or External Application Load Balancer
Telemetry Dependency
• HTTP request visibility (method, URI, status)
• WAF, proxy, IDS, or load balancer logs
• Middleware asset and path tuning
Coverage Disposition
Detected
Behavior: Middleware Service Execution and Command Invocation
MITRE Techniques
T1059 – Command and Scripting Interpreter
Threat Behavior
Successful exploitation results in execution of shell commands or scripting interpreters within the Oracle middleware service context.
Detection Rules
• SentinelOne — Oracle Middleware Java Process Spawning High-Risk Interpreter
• SentinelOne — Oracle Middleware Java Execution with Encoded or Inline Command
• Splunk — Oracle Middleware Exploit Attempt Followed by Host Execution
• Splunk — Oracle Middleware Encoded or Inline Command Execution
• Elastic — Oracle Middleware Java Parent Spawning High-Risk Interpreter
• Elastic — Oracle Middleware Encoded or Inline Command Execution
• QRadar — Oracle Middleware Exploit Attempt Followed by Suspicious Host Execution
• QRadar — Oracle Middleware Encoded or Inline Command Execution
• Sigma — Oracle Middleware Java Parent Spawning High-Risk Interpreter
• Sigma — Oracle Middleware Encoded or Inline Command Execution
Telemetry Dependency
• Endpoint process creation telemetry
• Parent-child process lineage
• Command-line visibility
• Middleware process context (Java/WebLogic)
Coverage Disposition
Detected
Behavior: Payload Retrieval and Tool Transfer
MITRE Techniques
T1105 – Ingress Tool Transfer
Threat Behavior
Compromised middleware downloads additional payloads, scripts, or tools to enable further execution or staging.
Detection Rules
• SentinelOne — Oracle Middleware Service Launching External Retrieval Tool
• Splunk — Oracle Middleware Execution Followed by Retrieval Tool Activity
• Elastic — Oracle Middleware Suspicious Execution Followed by Retrieval Tool Activity
• QRadar — Oracle Middleware Suspicious Execution Followed by Retrieval Tool Activity
• Sigma — Oracle Middleware Service Launching External Retrieval Tool
• YARA — Oracle Middleware Suspicious Dropped Tool or Payload Bundle
• YARA — Oracle Middleware Suspicious Encoded or Staged Script Artifact
Telemetry Dependency
• Endpoint process telemetry
• Parent-child lineage
• Command-line visibility (optional but high value)
• File or artifact inspection capability
Coverage Disposition
Detected
Behavior: Cloud Exposure Increase and Attack Surface Expansion
MITRE Techniques
Not directly mapped to a single ATT&CK technique (control-plane risk amplification)
Threat Behavior
Changes to cloud configuration increase exposure of Oracle middleware systems, enabling or accelerating exploitation.
Detection Rules
• AWS — Oracle Middleware Exposure Increase via Security Group or Load Balancer Change
• Azure — Oracle Middleware Exposure Increase via NSG, Public IP, or Application Gateway Change
• GCP — Oracle Middleware Exposure Increase via Firewall, Forwarding Rule, or Public Entry Change
Telemetry Dependency
• Cloud control-plane logs
• Resource tagging or middleware inventory
• Prior-state comparison for exposure delta
Coverage Disposition
Detected
Conditional Post-Exploitation Behaviors
Behavior: Persistence via Middleware or Server Component Modification
MITRE Technique
T1505 – Server Software Component
Coverage Disposition
Partially Detected
Validation Notes
Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment.
Behavior: Privilege Escalation from Middleware Service Context
MITRE Technique
T1068 – Exploitation for Privilege Escalation
Coverage Disposition
Partially Detected
Validation Notes
Not observed in currently available reporting; may occur if execution context allows escalation beyond middleware service privileges.
Behavior: Lateral Movement via Remote Services
MITRE Technique
T1021 – Remote Services
Coverage Disposition
Partially Detected
Validation Notes
Not observed in currently available reporting; may occur if compromised middleware systems are used to access additional internal services or infrastructure.
Behavior: Credential Access from Middleware Context
MITRE Technique
T1552 – Unsecured Credentials
Coverage Disposition
Hunt Only
Validation Notes
Not observed in currently available reporting; may occur during post-exploitation if attackers access configuration files, environment variables, or service credentials.
Not Covered Behaviors
Behavior: Indicator Removal and Log Tampering
MITRE Technique
T1070 – Indicator Removal
Coverage Disposition
Not Covered
Validation Notes
• No direct S25 detection rules monitor log clearing, audit suppression, or forensic artifact removal
• Would require dedicated log integrity monitoring or audit tampering detection
Behavior: Direct Exploit-to-Execution Mapping at Application Layer
Coverage Disposition
Not Covered
Validation Notes
• No native telemetry links inbound HTTP request directly to backend execution decision
• Detection relies on correlation across ingress, endpoint, and network signals rather than deterministic mapping
S27 Behavior & Log Artifacts
· HTTP requests to affected Oracle middleware interfaces from unusual client sources, with uncommon methods, paths, or request cadence
· Middleware request-handling errors, fault responses, or abnormal transaction patterns associated with the affected interfaces
· Service-process-spawned execution on the middleware host that deviates from normal baseline behavior
· Parent-child process chains in which an Oracle middleware service process is the parent of shell, scripting, or other execution-capable child processes
· New outbound connections, DNS lookups, or internal service communications initiated from the middleware host soon after suspicious inbound requests
· Repeated path discovery, interface probing, or validation-style access across multiple middleware URLs or service paths
· Log timing patterns showing suspicious inbound activity immediately preceding host-side execution anomalies
S28 Detection Strategy and SOC Implementation Guidance
SOC handling should treat this threat as a correlation problem, not a single-event signature problem. A suspicious inbound request to an Oracle middleware service should increase analyst attention, but priority should rise materially when that request is followed by service-context execution, abnormal middleware faults, or unusual outbound communication from the same host.
Triage should begin by confirming whether the destination system is Oracle Identity Manager or Oracle Web Services Manager, whether the targeted path maps to an affected interface, and whether the request appears unauthenticated or operationally unusual for that service. Analysts should then pivot immediately into endpoint telemetry on the middleware host to determine whether the request was followed by process creation, command execution, or abnormal service behavior.
For environments using reverse proxies, WAFs, or load balancers, SOC workflows should preserve the linkage between client source, forwarded request metadata, and backend host impact. For internally reachable variants, priority should shift toward middleware log anomalies, endpoint execution telemetry, and east-west connection analysis.
Analyst escalation should be high when two or more of the following occur in sequence: suspicious inbound access to an affected interface, host-side execution from a middleware service context, and new outbound or lateral communication from the middleware host. Containment playbooks should prioritize isolating the affected middleware node, preserving application and proxy logs, and reviewing connected identity and service-trust relationships for secondary impact.
S29 Detection Coverage Summary
Detected Behaviors
· Suspicious inbound access to affected Oracle middleware interfaces when HTTP, proxy, or application-layer visibility exists
· Host-side execution anomalies on middleware systems when endpoint telemetry is present
· Correlated exploit sequence detection when inbound request data, middleware logs, and endpoint execution telemetry are all available
· Scanning, probing, or exploit-validation behavior against exposed middleware services
Conditional Post-Exploitation Behaviors
Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment.
· Persistence through modification of middleware components
· Lateral movement using trusted service relationships or newly accessed internal paths
· Credential or token access from middleware configuration stores or connected systems
· Defense evasion through selective log manipulation or reduction of forensic visibility
S30 Intelligence Maturity Assessment
Threat Detection Maturity
Moderate
Organizations can detect this threat with reasonable fidelity when they correlate suspicious inbound middleware access with host-side execution behavior. Detection maturity is lower where monitoring remains perimeter-only or identity-only.
Telemetry Coverage
Variable
Coverage is strongest where Oracle middleware logging, endpoint telemetry, and proxy or network visibility are all present. Coverage is materially weaker where TLS visibility is absent, middleware logging is sparse, or endpoint telemetry is not deployed to the middleware tier.
Detection Engineering Maturity
Moderate
Detection engineering is feasible but requires environment-specific tuning to separate malicious interface interaction from legitimate service traffic. Correlation logic is more important than static signatures for this vulnerability class.
Response Readiness
Moderate
Response readiness depends on whether the organization has playbooks for application-tier compromise, middleware isolation, and review of downstream identity or service-trust impact. Generic server IR processes alone are usually insufficient.
Security Hardening Maturity
Variable
Organizations with restricted exposure, segmented middleware tiers, and disciplined upstream access control are better positioned to reduce exploitability and improve signal quality. Flat reachability and broad service exposure materially increase both risk and detection difficulty.
Improvement Priorities
· Improve visibility into Oracle middleware request handling and error conditions
· Correlate suspicious inbound interface access with service-context execution on the middleware host
· Preserve reverse-proxy, WAF, or load balancer metadata needed to trace backend impact
· Baseline normal service behavior for affected interfaces to reduce false positives
· Strengthen segmentation and access control around middleware and identity-service tiers
Security Program Integration Note
This maturity assessment should be used to prioritize telemetry engineering, middleware-specific detection content, incident response playbooks for application-tier compromise, and segmentation improvements around identity and service-control infrastructure.
S31 Defensive Architecture Overview
Defensive architecture for CVE-2026-21992 must focus on eliminating unauthenticated access paths to Oracle Fusion Middleware services and constraining the execution impact of any successful compromise within middleware environments. The vulnerability enables direct interaction with sensitive service interfaces over HTTP without authentication, making exposure control the primary defensive objective.
The architecture should enforce three core principles: strict control of inbound access to middleware interfaces, isolation of identity and service-control systems from general network access, and containment of execution capability within middleware hosts. These principles reduce both exploitability and the ability of an attacker to expand access after initial compromise.
Defensive design must account for multiple exposure variants, including direct internet-facing services, exposure through reverse proxies or application gateways, and internal reachability from already compromised network positions.
S32 Preventive Controls and Hardening Measures
· Restrict access to Oracle Identity Manager and Oracle Web Services Manager interfaces to explicitly authorized source systems only
· Remove direct internet exposure of middleware services wherever possible
· Enforce access through controlled entry points such as reverse proxies or application gateways with strict request validation
· Apply vendor patches immediately to eliminate the underlying vulnerability
· Disable or restrict non-essential service endpoints and exposed interfaces within middleware configurations
· Enforce network segmentation to isolate middleware and identity systems from broader enterprise access
· Limit middleware service account privileges to the minimum required for operation
· Restrict outbound connections from middleware hosts to required destinations only
· Apply secure configuration baselines across Oracle Fusion Middleware components
S33 Control Impact Mapping
· Access restriction reduces the likelihood of unauthenticated exploitation over HTTP
· Removal of external exposure significantly lowers attack surface availability
· Patch application eliminates the exploit condition entirely
· Endpoint reduction decreases the number of reachable attack paths
· Segmentation limits attacker movement from middleware systems to other enterprise assets
· Privilege reduction constrains execution impact within compromised service contexts
· Outbound restrictions reduce the ability to establish persistence or expand access
S34 Compensating Controls
· Temporarily restrict access to affected middleware services to trusted network zones when patching cannot be immediately completed
· Implement emergency firewall or access control rules to block external access to vulnerable endpoints
· Apply application gateway or WAF filtering to limit interaction with sensitive service paths
· Increase logging and monitoring of middleware service activity to improve visibility during the exposure window
· Reduce operational use of privileged service accounts associated with middleware systems during the risk period
· Isolate middleware systems from downstream identity or critical application systems where feasible
S35 Security Hardening Priorities
· Prioritize immediate patching of affected Oracle Fusion Middleware components
· Eliminate unnecessary external exposure of middleware services
· Enforce segmentation between middleware, identity, and application tiers
· Reduce service account privileges and validate least-privilege configurations
· Validate middleware interface exposure and remove unnecessary access paths
· Establish controlled access pathways through managed gateways or proxies
S36 Control Effectiveness Assessment
Control Effectiveness Score
Moderate to High when fully implemented
Audit Evidence Statement
Validation requires confirmation that affected systems are patched, middleware interfaces are not externally exposed, access controls are enforced at network boundaries, segmentation is in place, and service account privileges are minimized and reviewed.
Assessment Summary
Control effectiveness is strongly dependent on exposure reduction. Organizations that remove unauthenticated access paths and enforce segmentation materially reduce both the likelihood of exploitation and the impact of compromise. Environments with externally accessible middleware services or weak internal segmentation remain at elevated risk despite partial control implementation.
Security Program Integration Note
These controls should be integrated into vulnerability management, network architecture, identity governance, and application security programs to ensure consistent enforcement across middleware environments.
S37 Strategic Defensive Improvements
· Adopt zero-trust access models for middleware services where all access is explicitly authenticated and authorized
· Implement micro-segmentation to isolate middleware and identity systems from general network access
· Standardize secure configuration and exposure management for Oracle Fusion Middleware deployments
· Improve governance of service-to-service communication and trust relationships
· Establish rapid-response patching workflows for critical enterprise software vulnerabilities
· Reduce implicit trust within identity and service architectures to limit downstream compromise impact
S38 Economic Impact Assessment
The economic impact of CVE-2026-21992 is driven primarily by its ability to enable unauthenticated remote code execution within Oracle Fusion Middleware environments that frequently support identity governance and service control functions. This creates a direct pathway to disruption of authentication workflows, service orchestration, and enterprise application access.
In environments where middleware services are externally exposed, the most significant economic driver is rapid initial compromise followed by cascading operational disruption. Identity and middleware systems often act as dependencies for multiple business services, meaning a single compromised node can trigger broad service degradation, access failures, and emergency operational response efforts.
Cost impact is amplified in scenarios where the compromised middleware system interacts with identity services, service accounts, or privileged workflows. In these cases, remediation extends beyond system restoration and requires validation of trust relationships, credential integrity, and service-level dependencies across connected systems.
Variant conditions materially influence economic impact:
· Internet-facing exposure increases likelihood of rapid exploitation and reduces time to impact, driving higher incident response and recovery costs
· Reverse proxy or gateway exposure may delay exploitation but still allows compromise of backend services, leading to similar downstream recovery costs
· Internal reachability scenarios may delay detection but can result in broader lateral impact if compromise occurs within trusted network segments
Operational cost drivers include emergency patching, service downtime, forensic investigation, system validation, and re-establishment of identity and service trust relationships. In higher-impact scenarios, organizations may incur additional costs related to business interruption, access control failures, and extended remediation across dependent systems.
The financial impact profile is therefore not limited to initial exploitation but is significantly influenced by the complexity of restoring trust in identity and middleware systems following compromise.
S39 Strategic Risk Analysis
CVE-2026-21992 represents a strategic risk to organizations that rely on Oracle Fusion Middleware for identity governance and service orchestration due to its ability to compromise control-plane systems without authentication. This shifts risk from isolated system compromise to systemic exposure affecting authentication integrity, service trust, and enterprise access control.
Risk likelihood is elevated based on pre-authentication exploitability, HTTP-based exposure, and the historical targeting of similar Oracle Identity Manager vulnerabilities. Even in the absence of confirmed widespread exploitation at the time of assessment, the vulnerability characteristics support rapid attacker adoption and prioritization.
Strategically, the most significant risk is erosion of trust within identity and service-control layers. Compromise of these systems can undermine access governance, enable unauthorized privilege escalation, and disrupt critical business workflows. This introduces governance-level risk, including loss of control over authentication processes and potential downstream impact to regulated or sensitive systems.
Control effectiveness plays a decisive role in risk reduction. Organizations that remove external exposure, enforce segmentation, and apply patches promptly can significantly reduce both likelihood and impact. Conversely, environments with exposed middleware services, weak segmentation, or delayed remediation maintain elevated residual risk and increased probability of operational disruption.
From a governance perspective, this vulnerability highlights the importance of treating middleware and identity systems as high-value assets requiring strict access control, rapid patching, and continuous monitoring. Failure to do so results in persistent exposure to control-plane compromise and associated enterprise-wide risk.
S40 References
Vendor Advisory
Oracle Security Alert addressing CVE-2026-21992
· hxxps://www.oracle[.]com/security-alerts/alert-cve-2026-21992.html
Vulnerability Records
NVD vulnerability record for CVE-2026-21992
· hxxps://nvd[.]nist[.]gov/vuln/detail/CVE-2026-21992
Known Exploited Vulnerabilities (KEV)
CISA KEV catalog reference (no current listing for CVE-2026-21992 at time of assessment)
· hxxps://www.cisa[.]gov/known-exploited-vulnerabilities-catalog
Security Vendor Analysis
Tenable analysis of CVE-2026-21992 and related Oracle Identity Manager exploitation patterns
· hxxps://www.tenable[.]com/blog/cve-2026-21992-critical-out-of-band-oracle-identity-manager-and-oracle-web-services-manager
Analytical Framework
MITRE ATT&CK Framework (Enterprise Matrix)
· hxxps://attack[.]mitre[.]org