[EXP] Multi-Stage Intrusion Chain Edge Exploit to Identity and Cloud Compromise
Report Type
CVE Vulnerability Intelligence Report
Threat Category
Active Exploitation Vulnerability (EXP)
Assessment Date
April 03, 2026
Primary Impact Domain
Identity and Cloud Control Plane Compromise
BLUF
Organizations face critical enterprise risk from intrusion chains that originate from exploitation of internet-facing edge devices and rapidly escalate into identity system takeover and cloud control compromise, enabling complete operational disruption, data exfiltration, and ransomware enablement. These attacks are initiated through vulnerabilities in perimeter appliances such as Fortinet VPNs, Ivanti Connect Secure gateways, and Palo Alto firewalls, allowing attackers to bypass traditional perimeter defenses and directly access trusted network zones. Exploitation is highly mature and operationalized, with threat actors consistently weaponizing vulnerabilities within hours and executing repeatable edge-to-identity-to-cloud compromise playbooks across multiple sectors. Organizations must treat exposed edge infrastructure and identity control planes as immediate enterprise risk priorities and reallocate security focus toward rapid patch enforcement, identity session protection, and privileged access restriction to prevent full-chain compromise.
Executive Risk Translation
A single exploited edge device can allow attackers to assume trusted identities and gain administrative control of cloud environments, resulting in full enterprise compromise before traditional security controls can respond.
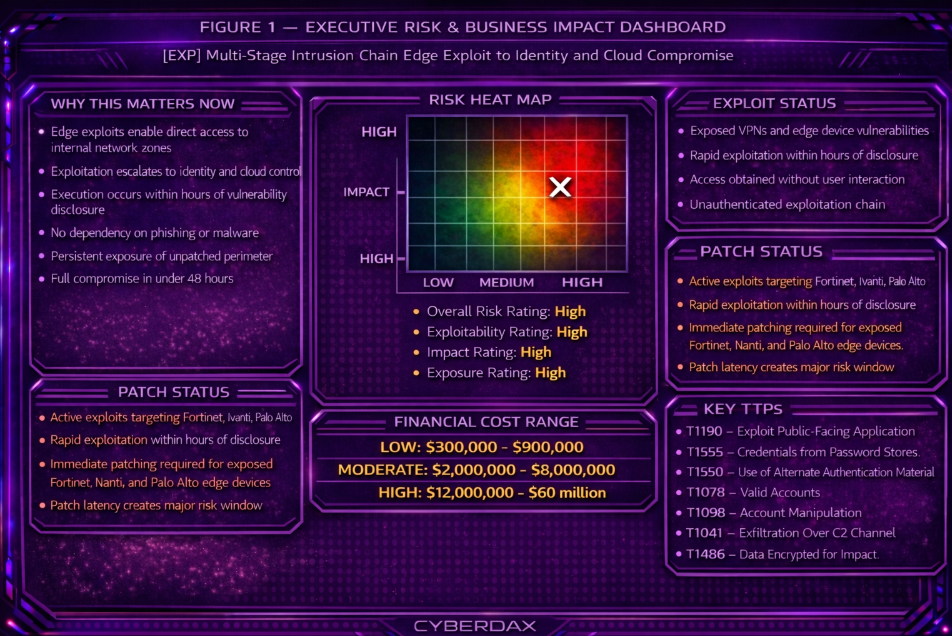
S3 Why This Matters Now
· Active exploitation campaigns targeting Fortinet, Ivanti, and Palo Alto edge vulnerabilities are occurring within hours to days of public disclosure.
· Public exploit code and automated scanning frameworks are rapidly integrated into attacker operations, increasing exploitation scale and speed.
· Observed intrusion timelines show full progression from edge access to cloud control in less than 48 hours.
· Persistent exposure of edge infrastructure combined with delayed patch cycles continues to expand the accessible attack surface.
· Detection visibility remains fragmented across edge, identity, and cloud layers, delaying recognition of multi-stage compromise.
S4 Key Judgments
· Edge device exploitation is the dominant and most reliable initial access vector in modern enterprise intrusion campaigns.
· Identity systems function as the primary control plane for attacker expansion, persistence, and privilege escalation.
· Cloud environments represent the ultimate objective due to centralized access to data, infrastructure, and administrative control.
· Attacker success depends on transitioning from network access to identity control without triggering detection.
· Organizations without integrated identity and cloud security controls remain highly susceptible to full-chain compromise.
S5 Executive Risk Summary
· Exploitation of edge devices enables unauthorized entry into trusted network zones, bypassing perimeter security controls.
· Attackers extract credentials and session artifacts, allowing impersonation of legitimate users and bypass of authentication safeguards.
· Compromised identities are leveraged to escalate privileges and gain administrative access within enterprise environments.
· Administrative access to cloud control planes enables persistent access, infrastructure manipulation, and large-scale data exfiltration.
S6 Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
· Low Impact Scenario
Edge exploitation detected and contained prior to identity compromise, resulting in limited investigation scope and minimal operational disruption. Estimated cost: 300,000 to 900,000 USD
· Moderate Impact Scenario
Identity compromise achieved with partial cloud access, resulting in data exposure, extended response operations, and regulatory notification requirements. Estimated cost: 2 million to 8 million USD
· High Impact Scenario
Full intrusion chain execution including identity takeover, cloud administrative control, data exfiltration, and ransomware deployment, resulting in enterprise-wide disruption, regulatory penalties, and prolonged recovery. Estimated cost: 12 million to 60 million USD or higher
S6A Key Cost Drivers
· Speed of detection between edge exploitation and identity compromise
· Degree of privileged identity access obtained by attackers
· Extent of cloud control-plane access and persistence mechanisms
· Volume and sensitivity of accessed or exfiltrated data
· Duration and complexity of incident response across multiple environments
· Regulatory exposure and legal obligations
· Operational downtime and business disruption
S6B Compliance and Risk Context
Compliance Exposure Indicator
Severe exposure for organizations handling regulated data due to unauthorized identity-based access across enterprise and cloud systems.
Risk Register Entry
· Risk Title: Edge-to-Identity-to-Cloud Intrusion Chain
· Risk Description: Exploitation of perimeter infrastructure enabling identity compromise and cloud administrative control
· Likelihood: High
· Impact: Severe
· Risk Rating: Critical
Annualized Risk Exposure
Estimated annualized exposure ranges from 5 million to 25 million USD based on high exploitation frequency, rapid attack execution timelines, and significant impact of full-chain compromise events.
S7 Operational Impact Assessment
· Initial access originating from exploited edge infrastructure is treated as trusted internal activity, allowing attacker operations to inherit legitimate network trust and bypass internal security controls.
· Authentication integrity is degraded as attackers operate using valid credentials and active session tokens, undermining confidence in identity-based access decisions.
· Session persistence mechanisms enable continued access even after credential resets, delaying effective containment.
· Administrative control over cloud environments allows unauthorized creation of privileged roles, persistence artifacts, and modification of critical services.
· Security monitoring effectiveness is reduced as attacker behavior blends with legitimate identity and cloud activity, complicating detection and investigation.
· Incident response requires synchronized containment across edge, identity, and cloud layers, significantly increasing operational complexity and recovery timelines.
S8 Bottom Line for Executives
Organizations must immediately eliminate exposed edge vulnerabilities, enforce strict identity session controls, and restrict privileged access to cloud environments to disrupt this attack chain. Security operations must prioritize detection of abnormal identity activity and cross-layer behavior rather than relying on endpoint-centric alerts. Failure to execute these controls allows attackers to progress from initial access to full enterprise control with minimal resistance.
S9 Board-Level Takeaway
This threat represents a governance-level failure condition where inadequate control over edge exposure, identity privilege, and cloud access enables enterprise-wide compromise. The board must ensure that management enforces accountability for vulnerability remediation at the edge, strict identity governance, and controlled cloud privilege boundaries as core risk controls. Failure to enforce these controls constitutes a material breakdown in enterprise risk management with direct financial and regulatory consequences.
S10 Campaign Overview
This campaign represents a multi-stage intrusion pattern in which attackers exploit internet-facing edge devices such as Fortinet SSL VPN, Ivanti Connect Secure, and Palo Alto GlobalProtect systems to gain trusted internal access. These systems act as authentication gateways, allowing attackers to transition from external access into enterprise identity systems without triggering traditional perimeter defenses.
Across observed incidents, attackers have leveraged device-level access to obtain authentication material, including credentials and active session artifacts, which are then used to establish valid identity sessions. This enables rapid pivot from initial access into identity control and subsequent expansion into cloud environments.
The campaign demonstrates a consistent operational model combining opportunistic exploitation at scale with targeted follow-on activity, including privilege escalation, data access, and ransomware deployment. The defining characteristic is the use of trusted identity pathways to achieve low-noise, high-impact compromise.
S11 Sectors Affected
· Financial Services where centralized identity systems provide access to financial data and transactional platforms
· Healthcare where remote access infrastructure supports distributed clinical systems and sensitive patient data
· Technology and SaaS providers where identity systems directly control cloud infrastructure and customer environments
· Government and Public Sector where large identity ecosystems and legacy edge infrastructure increase exposure
· Critical Infrastructure where remote access systems are essential for operational continuity
· Manufacturing where VPN access bridges corporate IT and operational technology environments
S12 Countries Affected
· United States
· United Kingdom
· Canada
· Germany
· Australia
· Japan
These regions are consistently targeted due to high concentrations of enterprise infrastructure, cloud adoption, and reliance on remote access technologies.
S13 Targeting Probability Assessment
Primary Targets
Organizations with exposed or unpatched edge devices that are directly integrated with identity providers and cloud platforms
Secondary Targets
Organizations with weak identity controls, including lack of session monitoring, token protection, or excessive privilege assignment
High-Probability Conditions
· Delayed patching of internet-facing edge infrastructure
· Direct trust relationships between VPN systems and identity providers
· Overprivileged cloud IAM roles and broad administrative access
· Limited monitoring of identity session activity
Attacker ROI Drivers
· Immediate access without user interaction or phishing
· Ability to scale exploitation across large numbers of targets
· Direct transition from access to identity control
· High-value outcomes through cloud and data access
S13A Exploit Conditions Snapshot
· Internet-facing edge device exposure with active remote access services
· Vulnerable firmware or software versions with publicly available exploit code
· Lack of segmentation between edge systems and identity infrastructure
· Active session handling or credential storage on edge devices
· Identity providers configured to trust upstream authentication without additional validation
These conditions enable rapid transition from exploitation to identity-level access.
S14 Initial Access Vector
The primary initial access vector is exploitation of vulnerabilities in internet-facing edge devices, including VPN gateways and firewall systems. These vulnerabilities allow attackers to access device file systems, configuration data, or session management components.
Because these systems function as authentication intermediaries, successful exploitation provides access within trusted network boundaries. This eliminates the need for phishing or endpoint compromise and allows attackers to interact directly with authentication infrastructure.
S15 Adversary Capability Profiling
Skill Level
High, with demonstrated ability to rapidly weaponize vulnerabilities and execute multi-stage intrusion chains
Infrastructure Maturity
Mature, leveraging distributed scanning infrastructure and automated exploitation frameworks
Operational Scalability
High during initial access, enabling exploitation of large numbers of exposed edge devices
Tooling Sophistication
Moderate to high, focused on exploit execution, credential extraction, and use of legitimate administrative interfaces
Escalation Likelihood
High, with consistent progression from initial access to identity compromise and privilege escalation
S16 Adversary Operational Objectives
· Establish authenticated access within enterprise identity systems
· Escalate privileges to administrative levels within identity providers
· Extend access into cloud environments through identity-based authorization
· Access and exfiltrate sensitive data from enterprise and cloud systems
· Establish persistent access through identity and cloud control mechanisms
· Execute monetization objectives including ransomware deployment
S17 Exploit Status
Exploitation of edge device vulnerabilities is actively occurring in the wild, with attackers leveraging publicly available exploit code and automated scanning tools. Observed campaigns demonstrate rapid weaponization following vulnerability disclosure, with exploitation timelines measured in hours.
The widespread exposure of vulnerable edge systems and delays in patch deployment contribute to sustained exploitation opportunities. This indicates a high likelihood of continued exploitation across affected environments.
S17B Defensive Weakness Profile
· Overreliance on perimeter security controls without sufficient identity-layer monitoring
· Lack of visibility into session-based authentication activity within identity providers
· Insufficient segmentation between edge infrastructure and internal identity systems
· Limited monitoring of cloud control-plane activity and identity-based access
· Delayed patching of critical edge infrastructure due to operational constraints
These weaknesses enable attackers to transition from initial access to identity control with minimal resistance and limited detection.
S18 Attack Chain Overview
This intrusion chain begins with exploitation of internet-facing edge devices that function as authentication gateways, allowing attackers to gain access within trusted network boundaries. Because these systems originate authenticated sessions, attacker activity inherits internal trust and bypasses traditional perimeter detection.
Following initial access, attackers obtain authentication material from compromised devices and use it to establish valid sessions within identity providers. This enables immediate access to enterprise identity systems without triggering authentication challenges.
Attackers then expand access through enumeration of identity structures and privilege relationships, identifying escalation pathways and high-value targets. Privilege escalation is subsequently achieved through modification of identity roles and permissions, transitioning attacker access to administrative control.
With identity-level administrative access established, attackers extend control into cloud environments through identity-based authorization. This enables direct manipulation of infrastructure, access to sensitive data, and establishment of persistence mechanisms.
The attack concludes with execution of objectives such as data exfiltration, persistence, or ransomware deployment, conducted entirely through legitimate identity and cloud control channels.
S19 MITRE ATT&CK Mapping
Initial Access — T1190 Exploit Public-Facing Application
Exploitation of edge devices provides direct access to trusted network and authentication infrastructure
Credential Access — T1555 Credentials from Password Stores
Access to configuration files and memory exposes stored credentials and authentication data
Credential Access — T1550 Use of Alternate Authentication Material
Session tokens and authentication artifacts are reused to establish authenticated sessions without reauthentication
Persistence — T1078 Valid Accounts
Compromised credentials and session tokens are used to maintain persistent identity-based access
Privilege Escalation — T1098 Account Manipulation
Identity roles and permissions are modified to elevate access and gain administrative control
Discovery — T1087 Account Discovery
Attackers enumerate users, roles, and identity structures within enterprise environments
Discovery — T1069 Permission Groups Discovery
Privilege group relationships and role assignments are analyzed to identify escalation pathways
Lateral Movement — T1021 Remote Services
Authenticated access is used to move across enterprise systems and services
Command and Control — T1071 Application Layer Protocol
Communication occurs through standard protocols, blending with legitimate traffic
Exfiltration — T1041 Exfiltration Over C2 Channel
Data is extracted using authenticated communication channels
Impact — T1486 Data Encrypted for Impact
Administrative access enables ransomware deployment or destructive actions
S20 Attack Stage Breakdown
Stage 1 – Credential Harvesting
Attackers exploit edge devices to access configuration storage, memory, and active session data. This allows extraction of stored credentials and authentication artifacts associated with legitimate users. In many cases, attackers obtain session tokens that represent already authenticated user sessions, eliminating the need for credential-based login attempts.
Stage 2 – Valid Account Authentication
Using harvested credentials and session artifacts, attackers establish authenticated sessions within identity providers. Session reuse allows access without triggering authentication workflows, bypassing multi-factor authentication enforcement tied to login events. Activity appears as legitimate user behavior within identity logs.
Stage 3 – Account and Resource Discovery
Once authenticated, attackers query identity providers and cloud environments to enumerate users, roles, service accounts, and privilege relationships. This stage identifies high-value targets, administrative roles, and escalation pathways across both enterprise identity systems and cloud environments.
Stage 4 – Privilege Escalation and Control Transition
Attackers escalate privileges by modifying identity roles, group memberships, or cloud IAM permissions through administrative interfaces and APIs. This transitions attacker access from standard user context to administrative control over identity systems and cloud resources.
Stage 5 – Persistence and Objective Execution
With administrative control established, attackers maintain persistent access through identity-based mechanisms and execute objectives. This includes accessing or exfiltrating data, creating additional access pathways, modifying infrastructure, or deploying ransomware. All activity occurs through legitimate identity and cloud control channels, reducing detection likelihood.
S20A Adversary Tradecraft Summary
This intrusion model reflects a mature operational approach centered on identity control rather than traditional system exploitation. Attackers prioritize acquisition of authenticated access early in the intrusion chain, recognizing that control of identity systems enables access to both enterprise and cloud environments without additional exploitation.
A defining characteristic of this tradecraft is the use of existing authentication material to establish trusted access. By leveraging session-based authentication rather than initiating new login attempts, attackers avoid triggering authentication controls and reduce visibility within security monitoring systems.
The operational model supports separation between initial access and objective execution. Opportunistic exploitation identifies vulnerable edge systems and harvests access at scale, while follow-on actors leverage identity control for monetization or strategic objectives. This division increases efficiency, scalability, and resilience across campaigns.
The approach emphasizes low-noise execution, reliance on trusted system behavior, and rapid progression from initial access to full environment control, making detection dependent on correlation across identity, endpoint, and network telemetry.
S21 Indicators of Compromise (IOC Summary)
· Edge device access involving configuration files, session storage, or authentication components outside normal administrative activity
· Presence of unauthorized files or scripts on edge infrastructure indicative of persistent access mechanisms
· Identity session activity exhibiting inconsistencies in origin, continuity, or authentication lineage relative to expected user behavior
· Identity activity originating from infrastructure-associated IP ranges, including VPN gateways or edge systems, rather than user endpoints
· Privilege modification events within identity or cloud environments occurring outside established administrative workflows
· Cloud control-plane activity occurring in temporal proximity to identity session irregularities or privilege escalation
S22 Malware and Tooling
· Exploitation of internet-facing edge infrastructure including Fortinet, Ivanti, and Palo Alto systems to obtain configuration and session artifacts
· Use of web shells or equivalent mechanisms on edge appliances to maintain access and enable command execution
· Extraction of credential and session-related data from device storage and configuration components
· Reuse of authentication material through session inheritance, replay, or token reuse techniques
· Use of identity provider administrative interfaces and APIs to modify roles, permissions, and access control structures
· Use of cloud control-plane APIs to establish persistence, escalate privileges, and manipulate infrastructure
· Reliance on legitimate system functionality and trusted interfaces rather than traditional malware deployment
S23 Behavior and Log Artifacts
Purpose
To define stage-aligned attacker behaviors that represent observable activity and serve as candidate inputs for detection engineering validation.
Stage 1 – Credential Harvesting
· Access to edge device configuration and session storage components
· Interaction with credential-bearing system locations
· Presence or execution of unauthorized files or scripts on edge systems
Stage 2 – Valid Account Authentication
· Session establishment inconsistent with expected authentication flow
· Identity activity lacking clear authentication lineage
· Session behavior inconsistent with established user access patterns
Stage 3 – Account and Resource Discovery
· Enumeration of identity objects, roles, permissions, and service principals
· Repeated access to directory or IAM metadata
· Unusual query patterns within identity and cloud environments
Stage 4 – Privilege Escalation and Control Transition
· Modification of roles, group memberships, or IAM policies
· Elevation of privileges beyond normal identity usage patterns
· Administrative actions originating from previously non-privileged identities
Stage 5 – Persistence and Objective Execution
· Creation of new identities, credentials, or long-lived access mechanisms
· Data access inconsistent with identity baseline behavior
· Infrastructure modification or impact-aligned activity
S24 Detection Strategy
Purpose
To define the detection approach and prioritization model that will be implemented and validated through S25 detection engineering.
Detection Philosophy
· Focus on identity-centric intrusion behavior and post-authentication misuse rather than initial access signatures
· Prioritize session-based anomalies and identity activity patterns over login failure detection
· Detect multi-stage progression through correlation across edge, identity, and cloud activity
Stage-Aligned Detection Model
· Stage 1: Monitor interaction with edge systems and credential-bearing components
· Stage 2: Identify session anomalies and inconsistencies in authentication lineage
· Stage 3: Detect identity and IAM enumeration behavior
· Stage 4: Detect privilege escalation and access control modification
· Stage 5: Detect persistence mechanisms and impact-related activity
Detection Priorities
· Identity session irregularities and inconsistencies
· Privilege escalation events within identity providers and cloud environments
· Cloud administrative activity following identity anomalies
· Edge system interaction patterns associated with credential access
Detection Constraints
· Limited visibility into edge appliance internals depending on platform and logging configuration
· Incomplete session lineage visibility within identity providers
· Encrypted traffic limiting inspection of network-level activity
· High baseline of legitimate administrative behavior introducing potential detection noise
S25 Ultra-Tuned Detection Engineering Rules
Suricata
Engineering Position
These Suricata rules are intentionally limited to realistic network-layer observables. They provide supporting detection signals, not authoritative confirmation of credential theft, valid-account misuse, privilege escalation, or persistence. Incident-level conclusions require correlation with identity, endpoint, and cloud-audit telemetry.
Rule Name
Edge Appliance Sensitive Path Access Burst
Mapped Stage
Stage 1 Credential Harvesting
MITRE ATT&CK
T1190 – Exploit Public-Facing Application
T1555 – Credentials from Password Stores
T1550 – Use of Alternate Authentication Material
Purpose
Detect repeated access to high-risk administrative, export, configuration, and session-related web paths on internet-facing edge appliances consistent with post-access retrieval behavior.
What this rule detects
Repeated HTTP GET requests to sensitive edge appliance paths associated with administrative access, export functions, diagnostics, or session/configuration retrieval.
What this rule does not prove
Does not confirm credential theft, token theft, or successful session compromise.
Tuning Explanation
Restrict to known edge appliance IP ranges only.
Use only where HTTP URI visibility or TLS decryption is available.
Suppress approved vulnerability scanners, monitoring systems, backup collectors, and administrative bastions.
This path set is a generic baseline and should be replaced with product-specific paths where possible.
Treat as a collection-behavior signal, not exploit confirmation.
Suricata Rule
alert http $EXTERNAL_NET any -> $EDGE_APPLIANCES $HTTP_PORTS (
msg:"CYBERDAX EXP edge appliance sensitive path access burst";
flow:to_server,established;
http.method; content:"GET"; nocase;
http.uri;
pcre:"/^\/(?:admin|api|diag|debug|export|backup|session|config)(?:\/|\?|$)/Ui";
dsize:>50;
threshold:type both, track by_src, count 4, seconds 180;
classtype:attempted-admin;
metadata:service http, deployment Perimeter, attack_target edge-appliance, confidence Medium;
sid:410001;
rev:5;
)
Administrator Localization Instructions
Replace $EDGE_APPLIANCES with actual appliance ranges.
Replace URI patterns with vendor-specific paths where possible.
Clone POST variant only if required by the appliance.
Add suppressions for approved sources.
Disable if URI visibility is unavailable.
Logical Notes
Single-rule meaning: sensitive-path access anomaly.
Correlated meaning: possible credential or session artifact retrieval.
Rule Regret Check
Deployment caution
Requires URI visibility.
Confidence caution
May generate noise in managed environments.
Coverage value
Strong early-stage signal.
Rule Execution Validity
Correlation-ready detection. Not sufficient alone to confirm credential harvesting.
Rule Name
Identity Provider TLS Access from Non-User Infrastructure
Mapped Stage
Stage 2 Valid Account Authentication
MITRE ATT&CK
T1078 – Valid Accounts
T1550 – Use of Alternate Authentication Material
Purpose
Detect TLS access to identity-provider endpoints from infrastructure or edge network segments where user-authentication traffic is not expected.
What this rule detects
TLS sessions from non-user infrastructure to a specific identity-provider hostname.
What this rule does not prove
Does not confirm successful authentication or account compromise.
Tuning Explanation
Restrict to non-user infrastructure ranges.
Use exact IdP hostnames only.
Clone per IdP.
Suppress federation and proxy infrastructure.
Treat as contextual identity anomaly.
Suricata Rule
alert tls $INFRASTRUCTURE_NET any -> $EXTERNAL_NET 443 (
msg:"CYBERDAX EXP identity-provider TLS access from non-user infrastructure";
flow:to_server,established;
tls.sni;
content:"login.microsoftonline.com"; nocase; endswith;
threshold:type both, track by_src, count 3, seconds 300;
classtype:policy-violation;
metadata:service tls, deployment Egress, attack_target identity-provider, confidence Medium;
sid:410002;
rev:5;
)
Administrator Localization Instructions
Replace hostname with tenant IdP domains.
Scope infrastructure ranges correctly.
Suppress legitimate identity infrastructure.
Avoid generic matching.
Logical Notes
Single-rule meaning: unexpected IdP access origin.
Correlated meaning: possible session misuse.
Rule Regret Check
Deployment caution
SNI visibility may be reduced or eliminated in some environments.
Confidence caution
Middleware may generate similar traffic.
Coverage value
Strong supporting signal.
Rule Execution Validity
Correlation-ready detection. Requires identity telemetry for confirmation.
Rule Name
Cloud Control Plane TLS Access from Non-Admin Host
Mapped Stage
Late-Chain Activity (Privilege Escalation or Persistence — cannot be distinguished at network layer)
MITRE ATT&CK
T1098 – Account Manipulation
T1078 – Valid Accounts
Purpose
Detect TLS access to cloud control-plane endpoints from hosts that are not approved administrative systems.
What this rule detects
TLS connections to cloud management endpoints from atypical host classes.
What this rule does not prove
Does not confirm escalation, persistence, or objective execution.
Tuning Explanation
Restrict to non-admin hosts.
Use exact control-plane endpoints only.
Suppress automation and admin systems.
Azure is the only concretely implemented provider in this rule set.
Suricata Rule
alert tls $NON_ADMIN_HOSTS any -> $EXTERNAL_NET 443 (
msg:"CYBERDAX EXP cloud control-plane TLS access from non-admin host";
flow:to_server,established;
tls.sni;
content:"management.azure.com"; nocase; endswith;
threshold:type both, track by_src, count 5, seconds 600;
classtype:policy-violation;
metadata:service tls, deployment Egress, attack_target cloud-control-plane, confidence Medium;
sid:410003;
rev:5;
)
Administrator Localization Instructions
Replace host scope appropriately.
Clone per provider as needed.
Exclude admin and automation systems.
Logical Notes
Single-rule meaning: control-plane access from wrong host.
Correlated meaning: late-stage attack activity.
Rule Regret Check
Deployment caution
Depends on host-role accuracy and SNI visibility.
Confidence caution
Automation traffic may resemble malicious activity.
Coverage value
Strong late-chain signal.
Rule Execution Validity
Correlation-ready detection. Requires identity and cloud telemetry.
Engineering Note
Rule effectiveness depends on:
· HTTP visibility or TLS decryption (Rule 1)
· SNI visibility (Rules 2 and 3)
· Accurate asset scoping and suppression
These rules must be correlated with identity, endpoint, and cloud telemetry for full detection confidence.
SentinelOne
Engineering Position
These detections represent host-observable behavioral signals only. They do not independently confirm identity compromise, privilege escalation, or persistence. The modeled intrusion chain is identity-centric and requires correlation across endpoint, identity-provider, and cloud telemetry for confirmation.
These rules are deployment templates requiring enforcement controls. They are not safe for unrestricted standalone deployment.
Event Taxonomy Requirement
SentinelOne event schemas vary by tenant.
Before deployment, the following must be mapped:
· process events (for example: Process Creation, Process)
· network events (for example: Network Connection)
· file events (for example: File Read, File Creation)
Failure to map event taxonomy invalidates rule execution.
Rule Name
Sensitive Configuration or Session Artifact Access on Edge-Adjacent Systems
Mapped Stage
Stage 1 Credential Harvesting
MITRE ATT&CK
T1555 – Credentials from Password Stores
T1550 – Use of Alternate Authentication Material
SOC Usage Mode
Alert-capable supporting detection
Minimum Deployment Requirement
Deployment restricted to systems that store edge configuration exports, support bundles, or backup artifacts.
Enforcement Method
Enforced through deployment scoping only to approved host groups.
Implementation Constraint Notes
Deployment outside scoped edge-adjacent systems is not permitted.
Broad Linux deployment is not permitted.
SentinelOne Deep Visibility Query
EventType IN ("File Creation","File Modification","File Rename","File Read")
AND AgentOs = "linux"
AND FilePath RegExp "(?i)(session|token|config|backup|export)"
AND ProcessName IN ("bash","sh","python","python3","tar","cp","scp","curl","wget","grep","cat")
AND NOT ProcessName IN ("rsync")
AND NOT CommandLine RegExp "(?i)(ansible|puppet|chef|salt|backup|monitor|compliance)"
Logical Notes
Single-rule meaning: sensitive file-access behavior
Correlated meaning: potential credential or session artifact harvesting
Rule 2
Rule Name
Outbound Identity-Provider Access from Non-User Host
Mapped Stage
Stage 2 Valid Account Authentication
MITRE ATT&CK
T1078 – Valid Accounts
T1550 – Use of Alternate Authentication Material
SOC Usage Mode
Correlation-only
Minimum Deployment Requirement
Requires:
· host-role classification
· destination enrichment OR baseline deviation detection
Enforcement Method
Must be enforced through:
· deployment only on non-user host groups
· correlation with identity telemetry
· enrichment identifying identity-provider infrastructure
Implementation Constraint Notes
Standalone alerting is not permitted.
Deployment without host-role scoping is not permitted.
Deployment without enrichment or correlation is not permitted.
SentinelOne Deep Visibility Query
EventType = "Network Connection"
AND DstPort = "443"
AND ProcessName IN ("chrome","msedge","firefox","curl","wget","powershell","pwsh","python","python3")
AND NOT ProcessName IN ("java","node","kubelet")
AND NOT CommandLine RegExp "(?i)(identity-sync|federation|sso|proxy)"
Logical Notes
Single-rule meaning: authentication-capable outbound traffic
Correlated meaning: potential session misuse
Rule Name
Cloud and Identity Enumeration Command Activity
Mapped Stage
Stage 3 Discovery
MITRE ATT&CK
T1087 – Account Discovery
T1069 – Permission Groups Discovery
SOC Usage Mode
Correlation or hunt only
Minimum Deployment Requirement
Requires:
· multi-execution correlation
· OR time-based burst logic external to SentinelOne
Enforcement Method
Enforced through:
· SIEM/XDR correlation logic
· OR hunt-only operational use
Implementation Constraint Notes
Standalone alerting is not permitted.
Single execution must not trigger paging.
Deployment without correlation capability is not permitted.
SentinelOne Deep Visibility Query
EventType = "Process Creation"
AND (
CommandLine RegExp "(?i)\baz ad user list\b"
OR CommandLine RegExp "(?i)\baws iam list-"
OR CommandLine RegExp "(?i)\bgcloud projects get-iam-policy\b"
)
AND NOT CommandLine RegExp "(?i)(terraform|ansible|ci-runner|approved-admin)"
Logical Notes
Single-rule meaning: enumeration command execution
Correlated meaning: privilege discovery
Rule Name
Privilege Modification Command Execution from Non-Standard Host
Mapped Stage
Stage 4 Privilege Escalation
MITRE ATT&CK
T1098 – Account Manipulation
SOC Usage Mode
Enforced through:
· suppression lists
· host-role scoping
· workflow exclusion
Implementation Constraint Notes
Deployment without suppression maturity is not permitted.
Deployment on approved admin systems is not permitted.
SentinelOne Deep Visibility Query
EventType = "Process Creation"
AND CommandLine RegExp "(?i)(\baz role assignment create\b|\baws iam attach-role-policy\b|\bgcloud projects add-iam-policy-binding\b)"
AND NOT CommandLine RegExp "(?i)(terraform|ci-runner|approved-admin|change-window)"
Logical Notes
Single-rule meaning: privilege-changing command execution
Correlated meaning: escalation confirmed via audit logs
Rule Name
Persistence or High-Risk Cloud Operation Tool Execution
Mapped Stage
Stage 5 Persistence / Objective Execution
MITRE ATT&CK
T1078 – Valid Accounts
T1098 – Account Manipulation
SOC Usage Mode
Correlation-first
Minimum Deployment Requirement
Requires:
· host-role scoping
· exclusion of backup, migration, provisioning systems
Enforcement Method
Enforced through:
· deployment only on atypical hosts
· correlation with prior-stage activity
· optional rule splitting
Implementation Constraint Notes
Standalone alerting is not permitted until validated.
If noise persists, rule must be split into:
· persistence creation
· data operation
Weakening detection logic is not permitted.
SentinelOne Deep Visibility Query
EventType = "Process Creation"
AND (
CommandLine RegExp "(?i)(\bcreate-access-key\b|\bclient secret\b|\bservice-principal create\b)"
OR CommandLine RegExp "(?i)(\baws s3 cp\b|\bgsutil cp\b)"
)
AND NOT CommandLine RegExp "(?i)(backup|migration|provisioning|approved-admin|ci-runner)"
Logical Notes
Single-rule meaning: high-risk cloud tooling execution
Correlated meaning: persistence or objective execution
Splunk
Engineering Position
Splunk is the authoritative detection layer for identity and cloud control-plane activity. These rules detect confirmed authentication, privilege modification, persistence creation, and high-risk operational behavior when proper logging and normalization are present.
Detection quality depends on:
· normalized fields
· complete cloud audit log ingestion
· suppression maturity for approved workflows
Event Normalization Requirement
User Identity
user, userPrincipalName, identity, principal
Source IP
src_ip, client_ip, ipAddress
Action
action, operationName, eventName
Failure to normalize invalidates detection consistency.
Rule Name
Sensitive Configuration or Session Artifact Access via File or Storage Logs
Mapped Stage
Stage 1 Credential Harvesting
MITRE ATT&CK
T1555 – Credentials from Password Stores
SOC Usage Mode
Correlation-only (low confidence standalone)
Minimum Deployment Requirement
Requires reliable file-access or storage-access logging.
Enforcement Method
Enforced through correlation with:
· endpoint telemetry
· edge access activity
Implementation Constraint Notes
Standalone alerting is not permitted.
Deployment without verified file or storage telemetry is not permitted.
Splunk Query
index=* (file_access OR storage_access)
| eval file_path=coalesce(file_path, object, uri)
| search file_path="*config*" OR file_path="*session*" OR file_path="*token*" OR file_path="*backup*"
| bin time span=10m
| stats count by user, srcip, file_path, _time
| where count > 3
Variant Analysis
Covered:
· config, session, token, backup artifacts
Not Covered:
· endpoint-local access without logging
· encrypted storage access without visibility
Rule Name
Successful Authentication from Atypical Source or First-Seen IP
Mapped Stage
Stage 2 Valid Account Authentication
MITRE ATT&CK
T1078 – Valid Accounts
SOC Usage Mode
Alert-capable supporting detection
Minimum Deployment Requirement
Requires:
· historical authentication data (baseline)
· source IP tracking
Enforcement Method
Enforced through:
· first-seen source detection OR
· deviation from historical user baseline
Implementation Constraint Notes
Standalone alerting without baseline comparison is not permitted.
Splunk Query
index=auth_logs
| eval user=coalesce(user, userPrincipalName, identity, principal)
| eval src_ip=coalesce(src_ip, client_ip, ipAddress)
| search result="success"
| stats earliest(_time) as first_seen by user, src_ip
| where first_seen > relative_time(now(), "-1d")
Variant Analysis
Covered:
· new source IP authentication events
Not Covered:
· token reuse without new login
· federated authentication without source visibility
Rule Name
Identity and IAM Enumeration Burst
Mapped Stage
Stage 3 Discovery
MITRE ATT&CK
T1087 – Account Discovery
T1069 – Permission Groups Discovery
SOC Usage Mode
Alert-capable with enforced burst logic
Minimum Deployment Requirement
Requires:
· cloud audit logs
· normalized action field
Enforcement Method
Enforced through:
· time-bound burst window
· user-level aggregation
Implementation Constraint Notes
Single-event alerting is not permitted.
Burst window enforcement is mandatory.
Splunk Query
index=cloud_logs
| eval user=coalesce(user, userPrincipalName, identity, principal)
| eval action=coalesce(action, operationName, eventName)
| search action IN ("ListUsers","ListRoles","GetRole","ListGroups","DescribeInstances")
| bin time span=5m
| stats count, dc(action) as distinctactions by user, time
| where count > 5 OR distinctactions > 3
Variant Analysis
Covered:
· multi-action enumeration bursts
Not Covered:
· low-and-slow enumeration
· provider-specific APIs not listed
Rule Name
Privilege Boundary Change or Role Assignment Modification
Mapped Stage
Stage 4 Privilege Escalation
MITRE ATT&CK
T1098 – Account Manipulation
SOC Usage Mode
Alert-capable primary detection
Minimum Deployment Requirement
Requires:
· cloud audit logs with administrative actions
· suppression of approved admin workflows
Enforcement Method
Enforced through:
· direct detection of privilege-changing actions only
Implementation Constraint Notes
Credential creation and data operations are not permitted in this rule.
Splunk Query
index=cloud_logs
| eval user=coalesce(user, userPrincipalName, identity, principal)
| eval action=coalesce(action, operationName, eventName)
| search action IN ("AddRoleAssignment","AttachRolePolicy","PutRolePolicy","AddMemberToPrivilegedGroup","GrantAdminRole")
| stats count by user, action
Variant Analysis
Covered:
· direct role and policy modification actions
Not Covered:
· indirect escalation paths
· inherited privilege escalation
Rule Name
Durable Access Artifact Creation
Mapped Stage
Stage 5 Persistence
MITRE ATT&CK
T1078 – Valid Accounts
T1098 – Account Manipulation
SOC Usage Mode
Alert-capable high-confidence detection
Minimum Deployment Requirement
Requires cloud audit logs capturing identity-object creation.
Enforcement Method
Enforced through:
· direct detection of credential and identity artifact creation
Implementation Constraint Notes
Privilege modification is not permitted in this rule.
Splunk Query
index=cloud_logs
| eval user=coalesce(user, userPrincipalName, identity, principal)
| eval action=coalesce(action, operationName, eventName)
| search action IN ("CreateAccessKey","CreateServicePrincipal","AddClientSecret","CreateApplicationCredential","GrantOAuthConsent")
| stats count by user, action
Variant Analysis
Covered:
· credential and identity artifact creation
Not Covered:
· delegated token creation not logged
· temporary token abuse
Rule Name
High-Risk Cloud Data or Control-Plane Action
Mapped Stage
Stage 5 Objective Execution
MITRE ATT&CK
T1078 – Valid Accounts
T1098 – Account Manipulation
SOC Usage Mode
Correlation-first (alert after tuning maturity)
Minimum Deployment Requirement
Requires:
· cloud audit logs
· suppression of normal data workflows
Enforcement Method
Enforced through:
· correlation with prior-stage activity
· or tuned action-family filtering
Implementation Constraint Notes
If noise is high, must split by:
· data actions
· control-plane actions
Splunk Query
index=cloud_logs
| eval user=coalesce(user, userPrincipalName, identity, principal)
| eval action=coalesce(action, operationName, eventName)
| search action IN ("PutObject","UploadObject","CreateSnapshot","ModifyLogging","DisableSecurityControl")
| stats count by user, action
Variant Analysis
Covered:
· storage, snapshot, and control-plane actions
Not Covered:
· encrypted or delegated operations
· provider-specific APIs not included
Elastic
Engineering Position
Elastic functions as the identity, cloud, and correlation enforcement layer. It is authoritative for:
· Successful authentication validation
· Privilege boundary changes
· Persistence artifact creation
· Multi-stage attack correlation
Elastic is not authoritative for edge appliance internals, and detection must account for:
· incomplete session lineage
· encrypted traffic limitations
· legitimate administrative noise
Detection is therefore identity-centric and correlation-driven, not single-signal dependent.
Data Normalization Requirement (Mandatory)
User Identity
user.name, user.email, user.id
Source Context
source.ip, source.geo.country_name
Action
event.action, event.type, cloud.audit.method_name
Outcome
event.outcome
Constraint
Deployment without validated normalization is not permitted
Rule Name
Edge-Adjacent Sensitive Artifact Access or Suspicious Tooling
Mapped Stage
Stage 1 Credential Harvesting
MITRE ATT&CK
T1555 – Credentials from Password Stores
T1550 – Use of Alternate Authentication Material
Rule Type
Custom query
SOC Usage Mode
Correlation-only
Minimum Deployment Requirement
· Edge-adjacent host scoping
· File and process telemetry availability
Enforcement Method
Enforced through strict host scoping only
Implementation Constraint Notes
· Standalone alerting is not permitted
· Provides partial Stage 1 coverage only
· Broad enterprise deployment is not permitted
Elastic Query
host.os.type:linux and
(
(event.category:file and file.path:(*session* or token or config or backup or export))
or
(event.category:process and process.command_line:(*session* or token or config or backup or tmp))
)
and not process.command_line:(*ansible* or puppet or chef or backup)
Administrator Localization Instructions
· Replace generic paths with real export and backup locations
· Restrict to systems handling edge-derived artifacts
· Add suppression for approved automation
Variant Analysis
Covered
· Artifact access patterns
· Basic suspicious tooling
Not Covered
· Appliance-internal access
· Memory-only harvesting
· Vendor-specific paths
Rule Name
Successful Authentication Deviating from Historical Baseline
Mapped Stage
Stage 2 Valid Account Authentication
MITRE ATT&CK
T1078 – Valid Accounts
T1550 – Use of Alternate Authentication Material
Rule Type
ES|QL
SOC Usage Mode
Alert-capable supporting detection
Minimum Deployment Requirement
· Minimum 14-day historical baseline
· Normalized identity and source fields
Enforcement Method
Baseline comparison (historical vs recent activity)
Implementation Constraint Notes
· Deployment without baseline data is not permitted
· Failed logins must not be included
Elastic Query
FROM auth-*
| WHERE event.outcome == "success"
| EVAL actor = COALESCE(user.name, user.email, user.id)
| EVAL src = COALESCE(source.ip, related.ip)
| WHERE actor IS NOT NULL AND src IS NOT NULL
| EVAL recent = CASE(@timestamp >= NOW() - 1 day, 1, 0)
| STATS
recent_count = SUM(recent),
historical_count = COUNT() - SUM(recent)
BY actor, src
| WHERE recent_count > 0 AND historical_count == 0
Administrator Localization Instructions
· Adjust baseline window if required
· Integrate with device trust or MFA context if available
Variant Analysis
Covered
· First-seen source authentication
Not Covered
· Token reuse
· Federated auth without source attribution
Rule Name
Identity and IAM Enumeration Burst
Mapped Stage
Stage 3 Discovery
MITRE ATT&CK
T1087 – Account Discovery
T1069 – Permission Groups Discovery
Rule Type
Threshold rule
SOC Usage Mode
Alert-capable (burst enforced)
Minimum Deployment Requirement
· Normalized cloud audit logs
· Exception lists for admin tooling
Enforcement Method
Time-bound threshold enforcement
Implementation Constraint Notes
· Single-event alerting is not permitted
· Exception tuning is mandatory
Elastic Query
event.action:(
"ListUsers" or
"ListRoles" or
"GetRole" or
"ListGroups" or
"ListServicePrincipals" or
"GetIamPolicy" or
"ListRoleAssignments" or
"ListApplications"
)
Threshold Configuration
Group by: user.name
Count: ≥ 6
Window: 5 minutes
Administrator Localization Instructions
· Replace with tenant-specific verbs
· Add suppression for governance tools
Variant Analysis
Covered
· Burst enumeration patterns
Not Covered
· Low-and-slow enumeration
· Unmapped provider actions
Rule Name
Privilege Boundary Change or Access-Control Modification
Mapped Stage
Stage 4 Privilege Escalation
MITRE ATT&CK
T1098 – Account Manipulation
Rule Type
Custom query
SOC Usage Mode
Alert-capable primary detection
Minimum Deployment Requirement
· Cloud audit logs
· Admin suppression rules
Enforcement Method
Direct privilege-change action matching
Implementation Constraint Notes
· Credential creation not permitted here
· Action set must be tenant-validated
Elastic Query
event.action:(
"AddRoleAssignment" or
"AttachRolePolicy" or
"PutRolePolicy" or
"AddMemberToPrivilegedGroup" or
"GrantAdminRole" or
"SetIamPolicy"
)
Administrator Localization Instructions
· Map provider-specific privilege actions
· Suppress approved workflows
Variant Analysis
Covered
· Direct privilege escalation actions
Not Covered
· Indirect escalation
· Unlogged permission inheritance
Rule Name
Durable Access Artifact Creation
Mapped Stage
Stage 5 Persistence
MITRE ATT&CK
T1078 – Valid Accounts
T1098 – Account Manipulation
Rule Type
Custom query
SOC Usage Mode
Alert-capable high-confidence detection
Minimum Deployment Requirement
· Credential creation logs
Enforcement Method
Direct artifact creation detection
Implementation Constraint Notes
· Privilege modification not permitted here
· Action set must be tenant-validated
Elastic Query
event.action:(
"CreateAccessKey" or
"CreateServicePrincipal" or
"AddClientSecret" or
"CreateApplicationCredential" or
"AddPasswordCredential" or
"AddKeyCredential"
)
Administrator Localization Instructions
· Map provider-specific credential verbs
· Keep suppression minimal and controlled
Variant Analysis
Covered
· Durable credential creation
Not Covered
· Temporary tokens
· Delegated access
Rule Name
High-Risk Cloud Action Following Privilege Transition
Mapped Stage
Stage 5 Objective Execution
MITRE ATT&CK
T1078 – Valid Accounts
T1098 – Account Manipulation
Rule Type
EQL
SOC Usage Mode
Correlation-first
Minimum Deployment Requirement
· Normalized logs
· Consistent user attribution
Enforcement Method
Sequence-based correlation
Implementation Constraint Notes
· Standalone alerting is not permitted
· Split rule if data noise is high
Elastic Query
sequence by user.name with maxspan=30m
[ any where event.action in (
"AddRoleAssignment",
"AttachRolePolicy",
"PutRolePolicy",
"GrantAdminRole",
"SetIamPolicy"
) ]
[ any where event.action in (
"PutObject",
"UploadObject",
"CreateSnapshot",
"ModifyLogging",
"DisableSecurityControl",
"DeleteTrail"
) ]
Administrator Localization Instructions
· Replace action sets with tenant-specific mappings
· Split into separate rules if needed
Variant Analysis
Covered
· Privilege transition followed by high-risk action
Not Covered
· Slow execution outside correlation window
· Unattributed delegated actions
QRadar
Engineering Position
QRadar is the stateful offense and correlation layer for this chain. Event rules in CRE are the primary detection mechanism, building blocks provide reusable scope and action families, and reference sets hold watchlist/baseline state used by rules.
Mandatory Pre-Deployment Controls
Before enabling any rule below:
1. Validate building blocks
· BB:HostDefinition:Edge_Adjacent_Systems
· BB:HostDefinition:Non_User_Infrastructure
· BB:HostDefinition:Non_Admin_Hosts
· BB:LogSource:Identity_Provider
· BB:Exclude:Approved_Admin_and_Automation
· BB:ActionFamily:Identity_IAM_Enumeration
· BB:ActionFamily:Privilege_Boundary_Change
· BB:ActionFamily:Durable_Access_Artifact_Creation
BB:ActionFamily:High_Risk_Cloud_Post_Control
2. Validate reference sets
· RS:User_Source_Baseline_14d
· RS:Recent_Stage2_Actors_30m
· RS:Recent_Stage4_Actors_30m
3. Validate custom event properties if DSM normalization is incomplete
· CEP_UserName
· CEP_SourceIP
· CEP_ActionName
· CEP_Outcome
· CEP_TargetObject
· CEP_ActorRole
Deployment without validated BB population and reference-set readiness is not permitted. QRadar supports custom event properties and reference-set-backed rule logic directly.
Reference Set Lifecycle Controls
RS:User_Source_Baseline_14d
· populate during a 7-day burn-in period
during burn-in, do not create offenses from first-seen user/source logic
· after burn-in, add CEP_UserName|CEP_SourceIP on successful auth events with 14-day expiry
· review top churn pairs weekly; remove known ephemeral or synthetic sources if needed
RS:Recent_Stage2_Actors_30m
· populated only by Rule 2
· 30-minute expiry
· used only for downstream Stage 5B correlation
RS:Recent_Stage4_Actors_30m
· populated only by Rule 4
· 30-minute expiry
· used only for downstream Stage 5B correlation
Starter Building Block Content
BB:ActionFamily:Privilege_Boundary_Change
Starter provider verbs:
· Azure / Entra: Add member to role, Add directory role member, Add app role assignment
· AWS: AttachRolePolicy, AttachUserPolicy, PutRolePolicy, PutUserPolicy
· GCP: SetIamPolicy, projects.setIamPolicy
BB:ActionFamily:Durable_Access_Artifact_Creation
Starter provider verbs:
· Azure / Entra: Add client secret, Add password credential, Add key credential, Create service principal
· AWS: CreateAccessKey, CreateLoginProfile
· GCP: service-account key creation equivalents as normalized in the tenant
BB:ActionFamily:High_Risk_Cloud_Post_Control
Starter provider verbs:
· Azure: storage upload, diagnostic/logging changes, snapshot or disk export equivalents as normalized
· AWS: PutObject, CloudTrail/logging changes, snapshot creation equivalents
· GCP: storage object upload, logging/config changes, snapshot equivalents as normalized
These are starter populations, not complete coverage. Variant completeness still depends on tenant-normalized event names and QIDs. Building blocks are specifically intended to hold reusable groups of event names, IPs, or privileged identities.
Rule Name
Edge-Adjacent Artifact Access or Suspicious Tooling
Mapped Stage
Stage 1 Credential Harvesting
MITRE ATT&CK
T1555 – Credentials from Password Stores
T1550 – Use of Alternate Authentication Material
Rule Type
Event Rule — Local
SOC Usage Mode
Correlation-only
Minimum Deployment Requirement
· BB:HostDefinition:Edge_Adjacent_Systems validated
· edge-adjacent host telemetry available
· approved maintenance exclusions validated
Enforcement Method
Strict host scoping with BB:HostDefinition:Edge_Adjacent_Systems and BB:Exclude:Approved_Admin_and_Automation
Implementation Constraint Notes
· standalone offense creation is not permitted
· broad deployment is not permitted
· partial Stage 1 coverage only, consistent with the source model’s edge-visibility constraints
CRE Wizard Test Order
when the event matches any of:
o event name/category indicates file access to session, token, config, backup, or export artifacts
o event name/category indicates suspicious process or script touching those artifacts
and when the event matches BB:HostDefinition:Edge_Adjacent_Systems
and when the event does not match BB:Exclude:Approved_Admin_and_Automation
and when at least 3 events are seen with the same source IP or hostname in 10 minutes
Responses
· add to offense only
· magnitude: Low
· rule response note: Stage1_Supporting_Edge_Artifact_Access
AQL Validation
SELECT username, sourceip, destinationip, QIDNAME(qid), COUNT(*) AS event_count
FROM events
WHERE (
UTF8(payload) ILIKE '%session%' OR
UTF8(payload) ILIKE '%token%' OR
UTF8(payload) ILIKE '%config%' OR
UTF8(payload) ILIKE '%backup%' OR
UTF8(payload) ILIKE '%export%'
)
GROUP BY username, sourceip, destinationip, QIDNAME(qid)
LAST 10 MINUTES
Variant Analysis
Covered
copied config, session, token, and backup artifact access; suspicious tooling on edge-adjacent systems.
Not Covered
appliance-internal-only activity, memory-only harvesting, vendor-specific artifact names absent from normalized telemetry.
Rule Name
Successful Identity Activity from First-Seen or Infrastructure Source
Mapped Stage
Stage 2 Valid Account Authentication
MITRE ATT&CK
T1078 – Valid Accounts
T1550 – Use of Alternate Authentication Material
Rule Type
Event Rule — Global
SOC Usage Mode
Alert-capable supporting detection
Minimum Deployment Requirement
· BB:LogSource:Identity_Provider validated
· BB:HostDefinition:Non_User_Infrastructure validated
· RS:User_Source_Baseline_14d active after burn-in
· CEP_Outcome normalized
Enforcement Method
Infrastructure-origin scoping or first-seen user/source baseline test
Implementation Constraint Notes
· failed-auth-only logic is not permitted
· deployment before baseline burn-in is not permitted for first-seen mode
· this remains supporting detection because session lineage can be incomplete in the source model
CRE Wizard Test Order
1. when the event matches BB:LogSource:Identity_Provider
2. and when CEP_Outcome = success
3. and when any of:
o source IP is in BB:HostDefinition:Non_User_Infrastructure
o CEP_UserName|CEP_SourceIP is not in RS:User_Source_Baseline_14d
4. and when the event does not match BB:Exclude:Approved_Admin_and_Automation
Responses
· create offense
· magnitude: Medium
· add CEP_UserName to RS:Recent_Stage2_Actors_30m with 30-minute expiry
· after burn-in, add CEP_UserName|CEP_SourceIP to RS:User_Source_Baseline_14d with 14-day expiry
· rule response note: Stage2_Supporting_Identity_Anomaly
AQL Validation
SELECT username, sourceip, LOGSOURCENAME(logsourceid), QIDNAME(qid), COUNT(*) AS event_count
FROM events
WHERE LOGSOURCENAME(logsourceid) ILIKE '%okta%'
OR LOGSOURCENAME(logsourceid) ILIKE '%azure%'
OR LOGSOURCENAME(logsourceid) ILIKE '%entra%'
GROUP BY username, sourceip, LOGSOURCENAME(logsourceid), QIDNAME(qid)
LAST 1 DAY
Variant Analysis
Covered: infrastructure-origin successful identity activity and first-seen user/source pairs.
Not Covered: token reuse with no IdP event, federated flows with poor attribution, session inheritance without a new success event.
Rule Name
Identity and IAM Enumeration Burst
Mapped Stage
Stage 3 Account and Resource Discovery
MITRE ATT&CK
T1087 – Account Discovery
T1069 – Permission Groups Discovery
Rule Type
Event Rule — Global
SOC Usage Mode
Alert-capable with burst enforcement
Minimum Deployment Requirement
· BB:ActionFamily:Identity_IAM_Enumeration populated
· approved governance and inventory exclusions validated
· actor field normalized
Enforcement Method
Global burst threshold by actor, with distinct-action expectation
Implementation Constraint Notes
· single-event alerting is not permitted
· governance and inventory suppression is mandatory
· if the tenant cannot distinguish event families well, keep this rule supporting-only
CRE Wizard Test Order
1. when the event matches BB:ActionFamily:Identity_IAM_Enumeration
2. and when the event does not match BB:Exclude:Approved_Admin_and_Automation
3. and when at least 6 events are seen with the same CEP_UserName in 5 minutes
4. and when at least 2 different QIDs or normalized actions are observed for that same CEP_UserName in the same interval
Responses
· create offense if none exists
· otherwise add to existing offense for same CEP_UserName
· magnitude: Medium
· rule response note: Stage3_Enumeration_Burst
AQL Validation
SELECT username, QIDNAME(qid), COUNT(*) AS event_count
FROM events
WHERE QIDNAME(qid) ILIKE '%ListUsers%'
OR QIDNAME(qid) ILIKE '%ListRoles%'
OR QIDNAME(qid) ILIKE '%ListGroups%'
OR QIDNAME(qid) ILIKE '%GetIamPolicy%'
GROUP BY username, QIDNAME(qid)
LAST 5 MINUTES
Variant Analysis
Covered: burst enumeration of users, groups, roles, service principals, applications, and IAM metadata.
Not Covered: low-and-slow discovery, provider-specific verbs absent from the BB, and discovery only visible in upstream SaaS logs not ingested into QRadar.
Rule Name
Privilege Boundary Change or Access-Control Modification
Mapped Stage
Stage 4 Privilege Escalation and Control Transition
MITRE ATT&CK
T1098 – Account Manipulation
Rule Type
Event Rule — Local
SOC Usage Mode
Alert-capable primary detection
Minimum Deployment Requirement
· BB:ActionFamily:Privilege_Boundary_Change populated
· approved admin exceptions validated
· CEP_ActionName normalized
Enforcement Method
Direct action-family match only
Implementation Constraint Notes
· credential creation is not permitted in this rule
· data actions are not permitted in this rule
· deployment without approved admin exceptions is not permitted
CRE Wizard Test Order
1. when the event matches BB:ActionFamily:Privilege_Boundary_Change
2. and when the event does not match BB:Exclude:Approved_Admin_and_Automation
Responses
· create offense
· magnitude: High
· add CEP_UserName to RS:Recent_Stage4_Actors_30m with 30-minute expiry
· rule response note: Stage4_Privilege_Boundary_Change
AQL Validation
SELECT username, sourceip, QIDNAME(qid), COUNT(*) AS event_count
FROM events
WHERE QIDNAME(qid) ILIKE '%Role%'
OR QIDNAME(qid) ILIKE '%Policy%'
OR QIDNAME(qid) ILIKE '%PrivilegedGroup%'
GROUP BY username, sourceip, QIDNAME(qid)
LAST 1 DAY
Variant Analysis
Covered: direct role, policy, trust-policy, and privileged membership changes.
Not Covered: indirect escalation via inherited permissions, non-audited control expansion, and poorly normalized provider actions.
Rule Name
Durable Access Artifact Creation
Mapped Stage
Stage 5 Persistence
MITRE ATT&CK
T1078 – Valid Accounts
T1098 – Account Manipulation
Rule Type
Event Rule — Local
SOC Usage Mode
Alert-capable high-confidence detection
Minimum Deployment Requirement
· BB:ActionFamily:Durable_Access_Artifact_Creation populated
· credential/application creation logs ingested
· CEP_ActionName normalized
Enforcement Method
Direct artifact-creation match only
Implementation Constraint Notes
· privilege-boundary changes are not permitted in this rule
· bulk data or storage actions are not permitted in this rule
CRE Wizard Test Order
1. when the event matches BB:ActionFamily:Durable_Access_Artifact_Creation
2. and when the event does not match BB:Exclude:Approved_Admin_and_Automation
Responses
· create offense
· magnitude: High
· rule response note: Stage5_Persistence_Durable_Access
AQL Validation
SELECT username, sourceip, QIDNAME(qid), COUNT(*) AS event_count
FROM events
WHERE QIDNAME(qid) ILIKE '%AccessKey%'
OR QIDNAME(qid) ILIKE '%ServicePrincipal%'
OR QIDNAME(qid) ILIKE '%ClientSecret%'
OR QIDNAME(qid) ILIKE '%Credential%'
GROUP BY username, sourceip, QIDNAME(qid)
LAST 1 DAY
Variant Analysis
Covered: durable credential and identity-artifact creation.
Not Covered: temporary-token abuse, delegated grants without durable object creation, unmanaged trust-path persistence.
Rule Name
High-Risk Cloud Action Following Privilege Transition or Identity Anomaly
Mapped Stage
Stage 5 Objective Execution
MITRE ATT&CK
T1078 – Valid Accounts
T1098 – Account Manipulation
Rule Type
Event Rule — Global
SOC Usage Mode
Correlation-first
Minimum Deployment Requirement
· BB:ActionFamily:High_Risk_Cloud_Post_Control populated
· RS:Recent_Stage2_Actors_30m and RS:Recent_Stage4_Actors_30m active
· shared actor field normalized
· backup and sanctioned automation exceptions validated
Enforcement Method
Reference-set-backed staged correlation
Implementation Constraint Notes
· standalone single-event alerting is not permitted
· if CEP_UserName is unreliable, define and validate one fallback join key before deployment, such as:
o sourceip|targetobject
o service principal ID
o application ID
· do not mix join strategies inside one deployed rule
CRE Wizard Test Order
1. when the event matches BB:ActionFamily:High_Risk_Cloud_Post_Control
2. and when the event does not match BB:Exclude:Approved_Admin_and_Automation
3. and when either:
o CEP_UserName is in RS:Recent_Stage2_Actors_30m
o CEP_UserName is in RS:Recent_Stage4_Actors_30m
Responses
· create offense if none exists for CEP_UserName
· otherwise add to existing offense for CEP_UserName
· magnitude: Critical
· rule response note: Stage5_Objective_Execution_Post_Control
AQL Validation
SELECT username, QIDNAME(qid), COUNT(*) AS event_count
FROM events
WHERE QIDNAME(qid) ILIKE '%PutObject%'
OR QIDNAME(qid) ILIKE '%UploadObject%'
OR QIDNAME(qid) ILIKE '%Snapshot%'
OR QIDNAME(qid) ILIKE '%Logging%'
OR QIDNAME(qid) ILIKE '%SecurityControl%'
GROUP BY username, QIDNAME(qid)
LAST 30 MINUTES
Variant Analysis
Covered: late-stage storage, snapshot, logging, and security-control actions after earlier identity anomaly or privilege transition.
Not Covered: low-and-slow post-control activity outside the window, delegated-service actions without stable attribution, provider verbs missing from the BB.
Sigma
Engineering Position
Sigma is the portable detection-content layer. These rules are designed to be converted into backend-specific implementations, not to replace backend-native state, baseline, threshold, reference-set, or offense logic.
These rules are:
· detection-portable
· implementation-aware
· backend-dependent for enforcement of stateful logic
Global Backend Enforcement Requirement
Before conversion and deployment, validate backend mappings for:
User Identity
user.name, user.id, user.email
Source Context
source.ip, source.geo.country_name
Action / Operation
event.action
Outcome
event.outcome
Process / File Context
process.name, process.command_line, file.path
Constraint
Deployment without validated backend field mapping is not permitted.
Rule Name
Edge-Adjacent Sensitive Artifact Access or Suspicious Tooling
Mapped Stage
Stage 1 Credential Harvesting
MITRE ATT&CK
T1555 – Credentials from Password Stores
T1550 – Use of Alternate Authentication Material
SOC Usage Mode
Correlation-only
Minimum Deployment Requirement
Deploy only to:
· edge-adjacent Linux telemetry
· hosts that store copied edge artifacts
· hosts with process and file visibility
Enforcement Method
Host scoping and exclusion logic must be enforced in the destination backend.
Implementation Constraint Notes
· Standalone alerting is not permitted
· Broad enterprise deployment is not permitted
· Partial Stage 1 coverage only
· Backend host scoping is mandatory
Backend Enforcement Notes
The destination SIEM or EDR must restrict this rule to approved edge-adjacent host groups or equivalent tags.
title: Edge-Adjacent Sensitive Artifact Access or Suspicious Tooling
id: 8a3f1d2e-1c6b-4d15-9b11-110000000001
status: experimental
description: Detects suspicious access to copied edge configuration, session, token, backup, export, or support-bundle artifacts, or suspicious tooling interacting with those artifacts on edge-adjacent Linux systems.
references:
- internal-source
author: OpenAI
date: 2026-04-03
logsource:
product: linux
detection:
selection_file:
file.path|contains:
- session
- token
- config
- backup
- export
- support
selection_proc:
process.name|endswith:
- bash
- sh
- python
- python3
- curl
- wget
- chmod
- chown
selection_cmd:
process.command_line|contains:
- session
- token
- config
- backup
- export
- support
- /tmp/
- /var/tmp/
filter_main_legit:
process.command_line|contains:
- ansible
- puppet
- chef
- salt
- backup
- monitor
- compliance
condition: (selection_file or (selection_proc and selection_cmd)) and not filter_main_legit
falsepositives:
- Approved maintenance or support activity on edge-adjacent systems
level: medium
tags:
- attack.credential_access
- attack.t1555
- attack.t1550
Variant Analysis
Covered
· artifact access patterns
· suspicious tooling touching session, token, config, backup, export, or support artifacts
Not Covered
· appliance-internal-only activity
· memory-only harvesting
· vendor-specific artifact names not present in file or process telemetry
Rule Name
Successful Authentication from Infrastructure-Associated Source Context
Mapped Stage
Stage 2 Valid Account Authentication
MITRE ATT&CK
T1078 – Valid Accounts
T1550 – Use of Alternate Authentication Material
SOC Usage Mode
Alert-capable supporting detection
Minimum Deployment Requirement
Requires:
· successful authentication logs
· source IP visibility
· backend-specific infrastructure source scoping
Enforcement Method
Infrastructure-source context must be enforced in the destination backend.
Implementation Constraint Notes
This Sigma rule does not implement first-seen or baseline logic by itself
· Failed-login-only deployment is not permitted
· This is supporting detection only
Backend Enforcement Notes
If first-seen, baseline deviation, impossible-travel, or device-anomaly logic is required, it must be implemented in the destination backend after Sigma conversion.
title: Successful Authentication from Infrastructure-Associated Source Context
id: 8a3f1d2e-1c6b-4d15-9b11-110000000002
status: experimental
description: Detects successful authentication events from infrastructure-associated source ranges or other non-user source contexts. Historical baseline and first-seen logic must be implemented in the target backend if required.
references:
- internal-source
author: OpenAI
date: 2026-04-03
logsource:
category: authentication
detection:
selection_success:
event.outcome: success
selection_infra_source:
source.ip|cidr:
- 10.0.0.0/8
- 172.16.0.0/12
- 192.168.0.0/16
condition: selection_success and selection_infra_source
falsepositives:
- Approved identity middleware
- Federation services
- Infrastructure-based identity workflows
level: medium
tags:
- attack.persistence
- attack.valid_accounts
- attack.t1078
- attack.t1550
Variant Analysis
Covered
· successful auth from infrastructure-associated source context
Not Covered
· token reuse without new login
· baseline deviation or first-seen logic unless added downstream
· federated auth with poor source attribution
Rule Name
Identity and IAM Enumeration Activity
Mapped Stage
Stage 3 Account and Resource Discovery
MITRE ATT&CK
T1087 – Account Discovery
T1069 – Permission Groups Discovery
SOC Usage Mode
Correlation or threshold-backed alerting
Minimum Deployment Requirement
Requires:
· normalized cloud and identity audit verbs
· backend thresholding or correlation support
· exception lists for governance and inventory activity
Enforcement Method
Burst thresholds and actor grouping must be enforced in the destination backend.
Implementation Constraint Notes
· Single-event alerting is not permitted
· Backend thresholding is mandatory for production use
Backend Enforcement Notes
Destination backend should require:
· actor grouping
· short interval threshold
· approved inventory/admin suppressions
title: Identity and IAM Enumeration Activity
id: 8a3f1d2e-1c6b-4d15-9b11-110000000003
status: experimental
description: Detects identity and IAM enumeration actions associated with discovery of users, roles, groups, service principals, applications, and IAM policy metadata.
references:
- internal-source
author: OpenAI
date: 2026-04-03
logsource:
category: cloud
detection:
selection_actions:
event.action:
- ListUsers
- ListRoles
- GetRole
- ListGroups
- ListServicePrincipals
- GetIamPolicy
- ListRoleAssignments
- GetDirectoryRole
- ListApplications
filter_main_legit:
user.name:
- governance-service
- inventory-service
- approved-admin
condition: selection_actions and not filter_main_legit
falsepositives:
- Governance collectors
- Inventory tooling
- Approved administrative review activity
level: medium
tags:
- attack.discovery
- attack.account_discovery
- attack.permission_groups_discovery
- attack.t1087
- attack.t1069
Variant Analysis
Covered
· identity and IAM read actions for users, roles, groups, service principals, applications, and policy metadata
Not Covered
· low-and-slow discovery
· provider-specific unmapped verbs
· production-safe burst logic unless enforced downstream
Rule Name
Privilege Boundary Change or Access-Control Modification
Mapped Stage
Stage 4 Privilege Escalation
MITRE ATT&CK
T1098 – Account Manipulation
SOC Usage Mode
Alert-capable primary detection
Minimum Deployment Requirement
Requires:
· normalized cloud and identity admin verbs
· approved admin exclusions
· tenant verb validation
Enforcement Method
Direct privilege-change matching in the destination backend.
Implementation Constraint Notes
· Credential creation is not permitted in this rule
· Post-control data actions are not permitted in this rule
· Provider verb validation is mandatory
Backend Enforcement Notes
Destination backend should preserve direct action-family semantics and maintain approved admin exceptions.
title: Privilege Boundary Change or Access-Control Modification
id: 8a3f1d2e-1c6b-4d15-9b11-110000000004
status: experimental
description: Detects direct authority-expanding changes such as role assignment, privileged group membership modification, or IAM policy change.
references:
- internal-source
author: OpenAI
date: 2026-04-03
logsource:
category: cloud
detection:
selection_actions:
event.action:
- AddRoleAssignment
- AttachRolePolicy
- PutRolePolicy
- AddMemberToPrivilegedGroup
- GrantAdminRole
- UpdateAssumeRolePolicy
- SetIamPolicy
- AddDirectoryRoleMember
filter_main_legit:
user.name:
- approved-admin
- pam-service
- breakglass-approved
condition: selection_actions and not filter_main_legit
falsepositives:
- Approved privileged administration
- Emergency access workflows
level: high
tags:
- attack.privilege_escalation
- attack.account_manipulation
- attack.t1098
Variant Analysis
Covered
· direct role, policy, trust-policy, and privileged membership changes
Not Covered
· indirect escalation through inherited permissions
· poorly normalized provider verbs
Rule Name
Durable Access Artifact Creation
Mapped Stage
Stage 5 Persistence
MITRE ATT&CK
T1078 – Valid Accounts
T1098 – Account Manipulation
SOC Usage Mode
Alert-capable high-confidence detection
Minimum Deployment Requirement
Requires:
· cloud and identity audit coverage for credential and identity-object creation
· tenant verb validation
Enforcement Method
Direct durable-artifact creation matching in the destination backend.
Implementation Constraint Notes
· Privilege-boundary change actions are not permitted here
· Bulk data actions are not permitted here
· Provider verb validation is mandatory
Backend Enforcement Notes
Destination backend should keep suppressions narrow and tied only to approved provisioning workflows.
title: Durable Access Artifact Creation
id: 8a3f1d2e-1c6b-4d15-9b11-110000000005
status: experimental
description: Detects creation of long-lived access artifacts such as access keys, service principals, client secrets, and application credentials.
references:
- internal-source
author: OpenAI
date: 2026-04-03
logsource:
category: cloud
detection:
selection_actions:
event.action:
- CreateAccessKey
- CreateServicePrincipal
- AddClientSecret
- CreateApplicationCredential
- GrantOAuthConsent
- AddPasswordCredential
- AddKeyCredential
filter_main_legit:
user.name:
- approved-provisioning
- approved-admin
condition: selection_actions and not filter_main_legit
falsepositives:
- Approved provisioning systems
- Narrowly scoped credential rotation workflows
level: high
tags:
- attack.persistence
- attack.valid_accounts
- attack.account_manipulation
- attack.t1078
- attack.t1098
Variant Analysis
Covered
· durable credential and identity-artifact creation
Not Covered
· temporary-token abuse
· delegated access paths without durable object creation
Rule Name
High-Risk Cloud Action Following Privilege Transition
Mapped Stage
Stage 5 Objective Execution
MITRE ATT&CK
T1078 – Valid Accounts
T1098 – Account Manipulation
SOC Usage Mode
Correlation-first
Minimum Deployment Requirement
Requires a backend that supports:
· Sigma correlation
· or equivalent translated sequence logic
· stable actor attribution
Enforcement Method
Sequence or correlation logic must be implemented in the destination backend.
Implementation Constraint Notes
· Standalone single-event alerting is not permitted
· This rule requires a backend supporting Sigma correlation or an equivalent translated feature
· If storage-heavy activity is common, split storage actions from control-plane impairment actions downstream
Backend Enforcement Notes
Do not deploy this rule as a plain single-event Sigma conversion. It must be converted into backend correlation or sequence logic.
title: High-Risk Cloud Action Following Privilege Transition
id: 8a3f1d2e-1c6b-4d15-9b11-110000000006
status: experimental
description: Detects high-risk cloud data or control-plane actions following a privilege boundary change by the same actor within a constrained interval.
references:
- internal-source
author: OpenAI
date: 2026-04-03
correlation:
type: event_count
rules:
- 8a3f1d2e-1c6b-4d15-9b11-110000000004
- 8a3f1d2e-1c6b-4d15-9b11-110000000006-base
group-by:
- user.name
timespan: 30m
level: high
tags:
- attack.exfiltration
- attack.impact
- attack.valid_accounts
- attack.account_manipulation
- attack.t1078
- attack.t1098
---
title: High-Risk Cloud Action Following Privilege Transition Base
id: 8a3f1d2e-1c6b-4d15-9b11-110000000006-base
status: experimental
description: Base detector for high-risk cloud post-control actions.
references:
- internal-source
author: OpenAI
date: 2026-04-03
logsource:
category: cloud
detection:
selection_actions:
event.action:
- PutObject
- UploadObject
- CreateSnapshot
- ModifyLogging
- DisableSecurityControl
- StopLogging
- DeleteTrail
- UpdateBucketPolicy
filter_main_legit:
user.name:
- approved-backup
- approved-admin
- approved-automation
condition: selection_actions and not filter_main_legit
falsepositives:
- Approved backup workflows
- Sanctioned cloud administration
level: medium
tags:
- attack.exfiltration
- attack.impact
- attack.t1078
- attack.t1098
Variant Analysis
Covered
· ordered progression from privilege transition into storage, snapshot, logging, and security-control-impacting actions
Not Covered
· slow post-control actions outside the correlation window
· delegated service activity without stable actor attribution
· backends that do not support Sigma correlation or equivalent translated logic
YARA
Engineering Position
YARA is the artifact and content-detection layer.
It is appropriate for:
· suspicious web shells
· dropped scripts
· copied session or credential dump artifacts
· shell-history fragments
· recovered admin tooling
· operator notes and staging files
It is not the authoritative layer for:
· successful authentication detection
· identity session anomalies
· privilege changes in IdP or cloud logs
· cloud control-plane sequencing
Those behaviors are identity- and cloud-native in this intrusion model and belong in log and correlation layers rather than static content signatures.
Rule Name
Edge Web Shell or Unauthorized Edge Script Artifact
Mapped Stage
Stage 1 Credential Harvesting
MITRE ATT&CK
T1190 – Exploit Public-Facing Application
T1555 – Credentials from Password Stores
SOC Usage Mode
Alert-capable supporting detection
Minimum Deployment Requirement
Deploy only on:
· edge-adjacent file collections
· suspicious web directories
· extracted appliance file systems
· support bundles
· forensic triage sets from suspected edge compromise
Enforcement Method
Restrict scanning scope to edge-adjacent artifacts only.
Implementation Constraint Notes
Broad enterprise-wide YARA deployment is not permitted.
This rule is intended for unauthorized files or scripts on edge systems, which the intrusion model explicitly identifies as a Stage 1 behavior.
rule CYBERDAX_EXP_Edge_Webshell_Or_Unauthorized_Script
{
meta:
description = "Detects suspicious edge web shells or unauthorized script artifacts associated with edge-to-identity intrusion chains"
author = "OpenAI"
date = "2026-04-03"
stage = "Stage 1 Credential Harvesting"
mitre_1 = "T1190 - Exploit Public-Facing Application"
mitre_2 = "T1555 - Credentials from Password Stores"
usage_mode = "Alert-capable supporting detection"
strings:
$php_1 = "system($_" ascii nocase
$php_2 = "shell_exec($_" ascii nocase
$php_3 = "passthru($_" ascii nocase
$php_4 = "eval(base64_decode(" ascii nocase
$php_5 = "assert($_POST" ascii nocase
$jsp_1 = "Runtime.getRuntime().exec" ascii nocase
$jsp_2 = "ProcessBuilder(" ascii nocase
$py_1 = "subprocess.Popen(" ascii nocase
$py_2 = "os.system(" ascii nocase
$sh_1 = "/bin/sh" ascii nocase
$sh_2 = "/bin/bash" ascii nocase
$net_1 = "curl -k" ascii nocase
$net_2 = "wget --no-check-certificate" ascii nocase
$net_3 = "chmod +x /tmp/" ascii nocase
$edge_1 = "sessionid" ascii nocase
$edge_2 = "auth_token" ascii nocase
$edge_3 = "vpn" ascii nocase
$edge_4 = "support bundle" ascii nocase
$edge_5 = "configuration export" ascii nocase
condition:
(
2 of ($php_*) or
2 of ($jsp_*) or
2 of ($py_*) or
2 of ($sh_*,$net_*)
)
or
(
1 of ($php_*,$jsp_*,$py_*,$sh_*,$net_*) and
2 of ($edge_*)
)
}
Variant Analysis
Covered
· PHP, JSP, Python, and shell-style web-shell or script artifacts
· unauthorized tooling with edge/session-oriented context
Not Covered
· heavily obfuscated shells
· compiled implants with no useful strings
· pure memory-only shell activity
· benign admin scripts that do not contain shell-like or web-shell-like behavior markers
Rule Name
Edge Session or Credential Dump Artifact
Mapped Stage
Stage 1 Credential Harvesting
MITRE ATT&CK
T1555 – Credentials from Password Stores
T1550 – Use of Alternate Authentication Material
SOC Usage Mode
Correlation-first
Minimum Deployment Requirement
Use only on:
· copied config files
· extracted edge storage
· support bundles
· memory string dumps exported to text
· recovered dump artifacts from suspected edge compromise
Enforcement Method
Restrict to artifacts collected from exploited or suspected edge infrastructure.
Implementation Constraint Notes
Standalone alerting is not permitted.
This rule is intended to detect artifact content consistent with session or credential exposure, which the intrusion model places at the core of Stage 1.
rule CYBERDAX_EXP_Edge_Session_Or_Credential_Dump_Artifact
{
meta:
description = "Detects edge-derived dump artifacts containing session, cookie, token, or credential-related content"
author = "OpenAI"
date = "2026-04-03"
stage = "Stage 1 Credential Harvesting"
mitre_1 = "T1555 - Credentials from Password Stores"
mitre_2 = "T1550 - Use of Alternate Authentication Material"
usage_mode = "Correlation-first"
strings:
$h1 = "Set-Cookie:" ascii nocase
$h2 = "Authorization: Bearer " ascii nocase
$h3 = "Cookie:" ascii nocase
$t1 = "sessionid=" ascii nocase
$t2 = "auth_token=" ascii nocase
$t3 = "remember_token=" ascii nocase
$t4 = "refresh_token" ascii nocase
$t5 = "access_token" ascii nocase
$c1 = "password=" ascii nocase
$c2 = "credential" ascii nocase
$c3 = "saml" ascii nocase
$c4 = "oauth" ascii nocase
$c5 = "vpn" ascii nocase
condition:
(
2 of ($h*) and
2 of ($t*,$c*)
)
or
(
4 of ($t*,$c*)
)
}
Variant Analysis
Covered
· dumped cookies, bearer headers, token fields, and credential-bearing text artifacts
· support-bundle or copied-storage text with auth-related residue
Not Covered
· encrypted dumps
· binary-only token containers
· proprietary vendor encodings with no readable auth markers
Rule Name
Recovered Identity and Cloud Administration Script Artifact
Mapped Stage
Stage 3 Account and Resource Discovery
Stage 4 Privilege Escalation and Control Transition
MITRE ATT&CK
T1087 – Account Discovery
T1069 – Permission Groups Discovery
T1098 – Account Manipulation
SOC Usage Mode
Hunt-only
Minimum Deployment Requirement
Use on:
· recovered scripts
· dropped admin tooling
· shell-history exports
· forensic text collections
· operator notes
Enforcement Method
Hunt in recovered files only. Do not use as a standalone production alert.
Implementation Constraint Notes
Standalone alerting is not permitted.
This rule is hunt-only because these stages are primarily expressed through IdP and cloud administrative interfaces and APIs, not static malware artifacts.
rule CYBERDAX_EXP_Recovered_Identity_Cloud_Admin_Script
{
meta:
description = "Detects recovered scripts or textual artifacts containing identity and cloud enumeration or privilege modification tooling"
author = "OpenAI"
date = "2026-04-03"
stage = "Stage 3 and Stage 4"
mitre_1 = "T1087 - Account Discovery"
mitre_2 = "T1069 - Permission Groups Discovery"
mitre_3 = "T1098 - Account Manipulation"
usage_mode = "Hunt-only"
strings:
$az_1 = "az ad user list" ascii nocase
$az_2 = "az role assignment list" ascii nocase
$az_3 = "az role assignment create" ascii nocase
$aws_1 = "aws iam list-" ascii nocase
$aws_2 = "aws iam get-" ascii nocase
$aws_3 = "aws iam attach-role-policy" ascii nocase
$gcp_1 = "gcloud projects get-iam-policy" ascii nocase
$gcp_2 = "gcloud projects add-iam-policy-binding" ascii nocase
$ms_1 = "Add-AzureADDirectoryRoleMember" ascii nocase
$ms_2 = "Add-MgGroupMember" ascii nocase
$ms_3 = "Get-MgUser" ascii nocase
$ms_4 = "Get-MgDirectoryRole" ascii nocase
condition:
2 of them
}
Variant Analysis
Covered
· recovered scripts or notes containing common Azure, AWS, GCP, and Microsoft identity administration verbs
Not Covered
· pure API abuse with no script artifact
· GUI-only admin activity
· renamed or encoded tooling with no readable command residue
Rule Name
Durable Access Creation Artifact
Mapped Stage
Stage 5 Persistence
MITRE ATT&CK
T1078 – Valid Accounts
T1098 – Account Manipulation
SOC Usage Mode
Alert-capable supporting detection
Minimum Deployment Requirement
Use on:
· attacker scripts
· shell-history exports
· automation fragments
· recovered admin tooling files
· textual forensic artifacts
Enforcement Method
Restrict to recovered or suspicious artifacts and pair with cloud-audit confirmation.
Implementation Constraint Notes
This rule does not confirm successful persistence on its own.
Use with identity or cloud logs to confirm long-lived access creation, which the intrusion model identifies as Stage 5 behavior.
rule CYBERDAX_EXP_Durable_Access_Creation_Artifact
{
meta:
description = "Detects scripts or text artifacts used to create durable cloud or identity access artifacts"
author = "OpenAI"
date = "2026-04-03"
stage = "Stage 5 Persistence"
mitre_1 = "T1078 - Valid Accounts"
mitre_2 = "T1098 - Account Manipulation"
usage_mode = "Alert-capable supporting detection"
strings:
$a1 = "CreateAccessKey" ascii nocase
$a2 = "CreateServicePrincipal" ascii nocase
$a3 = "AddClientSecret" ascii nocase
$a4 = "AddPasswordCredential" ascii nocase
$a5 = "AddKeyCredential" ascii nocase
$a6 = "CreateApplicationCredential" ascii nocase
$a7 = "service-principal create" ascii nocase
$a8 = "create-access-key" ascii nocase
$a9 = "grant oauth consent" ascii nocase
condition:
2 of them
}
Variant Analysis
Covered
· scripts or text showing durable credential, secret, key, or service-principal creation
Not Covered
· direct console/API activity without artifact residue
· temporary token abuse
· delegated-consent paths with no local script or text evidence
Rule Name
High-Risk Cloud Objective or Impact Artifact
Mapped Stage
Stage 5 Objective Execution
MITRE ATT&CK
T1041 – Exfiltration Over C2 Channel
T1486 – Data Encrypted for Impact
T1098 – Account Manipulation
SOC Usage Mode
Hunt-only or correlation-first
Minimum Deployment Requirement
Use on:
· recovered scripts
· operator notes
· shell-history files
· dumped command files
· staging artifacts
Enforcement Method
Use as hunt content or supporting artifact detection only.
Implementation Constraint Notes
Standalone alerting is not permitted.
This rule is supporting-only because Stage 5 objective execution in the intrusion model occurs largely through legitimate identity and cloud control channels, not necessarily static malware files.
rule CYBERDAX_EXP_High_Risk_Cloud_Objective_Artifact
{
meta:
description = "Detects scripts or artifacts associated with high-risk cloud data access, logging impairment, snapshot activity, or destructive objective execution"
author = "OpenAI"
date = "2026-04-03"
stage = "Stage 5 Objective Execution"
mitre_1 = "T1041 - Exfiltration Over C2 Channel"
mitre_2 = "T1486 - Data Encrypted for Impact"
mitre_3 = "T1098 - Account Manipulation"
usage_mode = "Hunt-only or correlation-first"
strings:
$d1 = "aws s3 cp" ascii nocase
$d2 = "gsutil cp" ascii nocase
$d3 = "PutObject" ascii nocase
$d4 = "UploadObject" ascii nocase
$d5 = "CreateSnapshot" ascii nocase
$d6 = "DeleteTrail" ascii nocase
$d7 = "DisableSecurityControl" ascii nocase
$d8 = "ModifyLogging" ascii nocase
$d9 = "encrypt" ascii nocase
$d10 = "ransom" ascii nocase
condition:
(
2 of ($d1,$d2,$d3,$d4,$d5,$d6,$d7,$d8)
)
or
(
1 of ($d1,$d2,$d3,$d4,$d5,$d6,$d7,$d8) and
1 of ($d9,$d10)
)
}
Variant Analysis
Covered
· recovered artifacts indicating bulk data movement, snapshot creation, logging impairment, security-control manipulation, or destructive intent
Not Covered
· pure console/API activity with no file or text artifact
· provider-specific verbs not represented in strings
· minimalist operator behavior leaving no script residue
Engineering Note
This hardened YARA set now matches the intrusion model’s real detection boundaries:
· strongest at Stage 1 for web shells, dump artifacts, and unauthorized files/scripts
· supporting or hunt-only for later stages where the attack shifts into identity and cloud control channels
· not a replacement for identity or cloud-native telemetry, which the source model explicitly prioritizes for detection across Stage 2 through Stage 5
AWS
Engineering Position
AWS is the native cloud audit and control-plane detection layer for AWS-visible behavior in this intrusion chain. It is strongest for:
· Stage 3 discovery
· Stage 4 privilege escalation
· Stage 5 persistence
· Stage 5 objective execution
It is weaker for:
· direct Stage 1 edge exploit visibility
· upstream identity-provider session lineage outside AWS-visible telemetry
· appliance-internal artifact access
Mandatory Data Source Requirement
Before deployment, validate:
CloudTrail
· Management events enabled
· Write events enabled
· Read events enabled where required
· Global service events enabled
S3 / Data Events
· Enable S3 data events for relevant buckets if using object-level actions like PutObject
Identity Context
· Principal attribution fields available and consistent enough for downstream joins
Constraint
Deployment without validated CloudTrail coverage is not permitted. Rules using object-level S3 actions are not valid unless S3 data events are enabled for the relevant scope.
Rule Name
AWS Identity and IAM Enumeration Burst
Mapped Stage
Stage 3 Account and Resource Discovery
MITRE ATT&CK
T1087 – Account Discovery
T1069 – Permission Groups Discovery
SOC Usage Mode
Correlation or threshold-backed alerting
Minimum Deployment Requirement
Requires:
· CloudTrail IAM read activity
· downstream thresholding
· downstream exclusions for approved inventory, governance, and admin automation
Enforcement Method
EventBridge matches IAM enumeration APIs.
Burst logic must be enforced in the downstream target.
Implementation Constraint Notes
· Single-event alerting is not permitted
· Production use requires short-window actor grouping
· Approved governance and inventory tooling must be excluded downstream
· Failed API calls should be excluded
EventBridge Event Pattern JSON
{
"source": ["aws.iam"],
"detail-type": ["AWS API Call via CloudTrail"],
"detail": {
"eventSource": ["iam.amazonaws.com"],
"eventName": [
"ListUsers",
"ListRoles",
"ListAttachedUserPolicies",
"ListAttachedRolePolicies",
"GetRole",
"GetPolicy",
"GetPolicyVersion",
"ListAccessKeys",
"GetAccountAuthorizationDetails"
],
"readOnly": [true],
"errorCode": [
{ "exists": false }
]
}
}
Target / Downstream Action Guidance
Downstream logic should:
· group by actor, such as principal ARN or username
· alert only when the same actor performs repeated enumeration in a short window such as 5 minutes
· optionally require 3 or more distinct enumeration APIs
· suppress known inventory, governance, and approved admin tooling
Variant Analysis
Covered
· common AWS IAM enumeration APIs
Not Covered
· low-and-slow discovery
· non-IAM enumeration outside this action family
· service-specific read APIs not listed here
Logical Notes
Single-rule meaning: IAM enumeration activity observed.
Correlated meaning: privilege-path or target discovery in AWS.
Rule Execution Validity
Deployable only with downstream thresholding or correlation.
Rule Name
Privilege Boundary Change via IAM Policy or Role Modification
Mapped Stage
Stage 4 Privilege Escalation
MITRE ATT&CK
T1098 – Account Manipulation
SOC Usage Mode
Alert-capable primary detection
Minimum Deployment Requirement
Requires:
· CloudTrail write activity
· downstream allowlist for approved administration and automation
· principal normalization
Enforcement Method
Direct match on privilege-boundary-changing IAM APIs.
Implementation Constraint Notes
· Durable-access creation is not permitted in this rule
· Storage or data actions are not permitted in this rule
· Approved admin exceptions must be enforced downstream
· Failed API calls should be excluded
EventBridge Event Pattern JSON
{
"source": ["aws.iam"],
"detail-type": ["AWS API Call via CloudTrail"],
"detail": {
"eventSource": ["iam.amazonaws.com"],
"eventName": [
"AttachUserPolicy",
"AttachRolePolicy",
"PutUserPolicy",
"PutRolePolicy",
"PutRolePermissionsBoundary",
"CreatePolicyVersion",
"UpdateAssumeRolePolicy",
"AddUserToGroup"
],
"readOnly": [false],
"errorCode": [
{ "exists": false }
]
}
}
Target / Downstream Action Guidance
Downstream logic should:
· suppress explicitly approved admin and automation identities
· raise severity when the actor is not a normal administrator
· optionally inspect whether CreatePolicyVersion created a new default version
· enrich AddUserToGroup to confirm the group is privileged
Variant Analysis
Covered
· direct IAM role, user, inline policy, permissions-boundary, trust-policy, and group membership changes
Not Covered
· indirect escalation through inherited permissions
· escalation caused by pre-existing over-privileged roles without a new IAM change
· privilege changes hidden behind unmapped APIs
Logical Notes
Single-rule meaning: direct privilege-boundary change in AWS IAM.
Correlated meaning: confirmed escalation into higher authority.
Rule Execution Validity
Deployable as a primary escalation detector.
Rule Name
Durable Access Artifact Creation in AWS
Mapped Stage
Stage 5 Persistence
MITRE ATT&CK
T1078 – Valid Accounts
T1098 – Account Manipulation
SOC Usage Mode
Alert-capable high-confidence detection
Minimum Deployment Requirement
Requires:
· CloudTrail write activity
· downstream exception handling for tightly controlled provisioning workflows
Enforcement Method
Direct match on durable-access artifact creation APIs.
Implementation Constraint Notes
· Privilege-boundary changes are not permitted in this rule
· Storage and data actions are not permitted in this rule
· Suppressions must remain narrow and explicit
· CreateUser is often legitimate in some environments; split or suppress aggressively if onboarding volume is high
· Failed API calls should be excluded
EventBridge Event Pattern JSON
{
"source": ["aws.iam"],
"detail-type": ["AWS API Call via CloudTrail"],
"detail": {
"eventSource": ["iam.amazonaws.com"],
"eventName": [
"CreateAccessKey",
"CreateLoginProfile",
"CreateUser"
],
"readOnly": [false],
"errorCode": [
{ "exists": false }
]
}
}
Target / Downstream Action Guidance
Downstream logic should:
· exclude only tightly controlled provisioning identities
· raise severity on access-key creation by non-admin or non-provisioning actors
· distinguish expected onboarding from suspicious persistence creation
· strongly consider splitting CreateUser into its own rule if it is common in the tenant
Variant Analysis
Covered
· access key creation
· console credential creation
· IAM user creation where relevant to the environment
Not Covered
· STS-only temporary session abuse
· delegated access paths without durable IAM artifact creation
· persistence through unmanaged or external identity trust not reflected in IAM creation events
Logical Notes
Single-rule meaning: durable access artifact creation in AWS.
Correlated meaning: persistence establishment through legitimate AWS control-plane mechanisms.
Rule Execution Validity
Deployable as a primary persistence detector, with careful CreateUser handling.
Rule Name
High-Risk Cloud Action Following Privilege Transition
Mapped Stage
Stage 5 Objective Execution
MITRE ATT&CK
T1078 – Valid Accounts
T1098 – Account Manipulation
SOC Usage Mode
Correlation-first
Minimum Deployment Requirement
Requires:
· CloudTrail write activity
· a stateful downstream target
· actor continuity or an alternate join-key strategy
· mature backup and automation exceptions
· S3 data events enabled for the relevant buckets if PutObject is used
Enforcement Method
EventBridge matches high-risk post-control actions.
Downstream logic must correlate them to a prior Rule 2 privilege-transition event.
Implementation Constraint Notes
· Standalone single-event alerting is not permitted
· Actor continuity must be validated downstream
· If storage-heavy workloads are common, split data actions from logging or security-control impairment actions
· Do not rely on event proximity alone; use the same actor or a validated fallback join key
· PutObject requires S3 data events and should be removed if those data events are not enabled
· Failed API calls should be excluded
EventBridge Event Pattern JSON
{
"source": ["aws.s3", "aws.ec2", "aws.cloudtrail"],
"detail-type": ["AWS API Call via CloudTrail"],
"detail": {
"eventSource": [
"s3.amazonaws.com",
"ec2.amazonaws.com",
"cloudtrail.amazonaws.com"
],
"eventName": [
"PutObject",
"PutBucketPolicy",
"CreateSnapshot",
"StopLogging",
"DeleteTrail",
"UpdateTrail"
],
"readOnly": [false],
"errorCode": [
{ "exists": false }
]
}
}
Target / Downstream Action Guidance
Downstream logic should:
· correlate to a prior privilege-transition event by the same actor within a bounded interval such as 30 minutes
· separate storage-heavy operations from trail or logging impairment if needed
· elevate to critical only when prior privilege-transition context exists
· define fallback join strategy if actor naming is inconsistent, such as:
o principal ARN
o session issuer ARN
o assumed-role principal ID
Variant Analysis
Covered
· storage policy or object actions
· snapshot creation
· CloudTrail trail/logging changes after privilege transition
Not Covered
· low-and-slow post-control activity outside the correlation window
· delegated-service execution with weak actor attribution
· high-risk post-control APIs outside the listed services or event names
Logical Notes
Single-rule meaning: high-risk AWS action observed.
Correlated meaning: objective execution, defense impairment, or late-stage operational action after escalation.
Rule Execution Validity
Deployable only as correlation-first content.
Rule Name
AWS Administrative API Activity Signal Aggregator from Infrastructure-Associated Source Context
Mapped Stage
Stage 2 Valid Account Authentication
Stage 3 Account and Resource Discovery
MITRE ATT&CK
T1078 – Valid Accounts
T1087 – Account Discovery
SOC Usage Mode
Supporting detection or correlation-first
Minimum Deployment Requirement
Requires:
· source IP visibility in CloudTrail-delivered events
· downstream infrastructure-source scoping
· approved automation exclusions
Enforcement Method
EventBridge matches a narrow AWS IAM administrative signal family.
Downstream logic must determine whether source context is infrastructure-associated or otherwise suspicious.
Implementation Constraint Notes
· Standalone paging is not permitted unless infrastructure-source logic is mature
· This remains supporting-only because AWS-native logs do not always prove the upstream identity anomaly by themselves
· Approved automation and CI or CD roles must be excluded
· This is a signal aggregator, not a primary high-confidence rule
· Failed API calls should be excluded
EventBridge Event Pattern JSON
{
"source": ["aws.iam"],
"detail-type": ["AWS API Call via CloudTrail"],
"detail": {
"eventSource": ["iam.amazonaws.com"],
"eventName": [
"ListUsers",
"ListRoles",
"GetRole",
"AttachUserPolicy",
"AttachRolePolicy"
],
"errorCode": [
{ "exists": false }
]
}
}
Target / Downstream Action Guidance
Downstream logic should:
· compare source IP against known infrastructure or non-user ranges
· exclude approved automation, CI or CD, and sanctioned admin roles
· treat as a supporting signal linking infrastructure-origin activity to AWS discovery or control actions
· optionally enrich with VPC, proxy, NAT, or organization egress context
Variant Analysis
Covered
· AWS IAM administrative APIs from potentially suspicious source context
Not Covered
· token reuse without distinguishable source context
· AWS service-to-service paths that mask the initiating actor
· persistence creation or high-risk storage actions, which are intentionally excluded from this aggregator
Logical Notes
Single-rule meaning: AWS administrative API signal observed.
Correlated meaning: suspicious authenticated-session use leading into AWS discovery or control activity.
Rule Execution Validity
Deployable as supporting or correlation-first content only.
Engineering Note
This corrected AWS rule set is now explicitly written in the agreed system-ready format: Amazon EventBridge event pattern JSON.
That means:
· EventBridge handles matching
· downstream targets handle state
· downstream targets handle thresholding
· downstream targets handle correlation
· downstream targets handle exceptions and severity
It is therefore easier to translate for teams using:
· EventBridge directly
· Lambda
· Step Functions
· SIEM forwarding
· Security Hub custom findings
· other cloud-native or third-party pipelines
Azure
Engineering Position
Azure Activity Log Alert JSON is strongest for:
· Stage 4 privilege-boundary and access-control modification
· Stage 5 high-risk post-control Azure management actions
It is weaker for:
· Stage 1 edge artifact visibility
· Stage 2 identity session lineage and sign-in anomaly detection
· Stage 3 burst-based discovery detections
· identity-native persistence actions that live primarily outside Azure Activity Log
Mandatory Data Source Requirement
Before deployment, validate:
· Azure Activity Log coverage for all intended subscriptions or scopes
· reliable use of:
o category
o operationName
o caller
o status
o resourceProvider
o resourceType
· action groups for downstream handling
Constraint
Deployment without validated Activity Log coverage is not permitted.
Rule Name
Azure Privilege Boundary Change or Access-Control Modification
Mapped Stage
Stage 4 Privilege Escalation
MITRE ATT&CK
T1098 – Account Manipulation
SOC Usage Mode
Alert-capable primary detection
Minimum Deployment Requirement
Requires:
· Administrative Activity Log coverage
· approved admin exception process
· scope set to relevant subscription or management scope
Enforcement Method
Direct Activity Log matching on high-risk RBAC, policy, and access-control operations
Implementation Constraint Notes
· Durable-access creation is not permitted in this rule
· Data-plane actions are not permitted in this rule
· Approved admin exceptions must be enforced downstream
Azure Activity Log Alert JSON
{
"type": "Microsoft.Insights/activityLogAlerts",
"apiVersion": "2020-10-01",
"name": "cdx-az-priv-boundary-change",
"location": "Global",
"properties": {
"enabled": true,
"description": "Detect direct Azure privilege-boundary or access-control modification events.",
"scopes": [
"/subscriptions/<SUBSCRIPTION_ID>"
],
"condition": {
"allOf": [
{
"field": "category",
"equals": "Administrative"
},
{
"anyOf": [
{
"field": "operationName",
"containsAny": [
"Microsoft.Authorization/roleAssignments/write",
"Microsoft.Authorization/roleDefinitions/write",
"Microsoft.Authorization/denyAssignments/write",
"Microsoft.Authorization/policyAssignments/write",
"Microsoft.Authorization/policyDefinitions/write",
"Microsoft.Authorization/policySetDefinitions/write",
"Microsoft.Authorization/elevateAccess/Action"
]
}
]
},
{
"field": "status",
"equals": "Succeeded"
}
]
},
"actions": {
"actionGroups": [
{
"actionGroupId": "/subscriptions/<SUBSCRIPTION_ID>/resourceGroups/<RG>/providers/microsoft.insights/actionGroups/<ACTION_GROUP_NAME>"
}
]
}
}
}
Target / Downstream Action Guidance
Downstream handling should:
· suppress approved change windows and sanctioned admin workflows
· enrich with caller, resourceGroup, resourceProvider, and resourceType
· elevate severity when the caller is not part of a known privileged-admin set
Variant Analysis
Covered
· direct RBAC, deny-assignment, policy, and elevate-access control-plane changes
Not Covered
· indirect escalation through pre-existing privilege
· identity-native entitlement changes visible only in Entra-focused audit sources
Logical Notes
Single-rule meaning: direct Azure privilege-boundary or access-control modification observed.
Correlated meaning: confirmed escalation into higher authority in Azure control plane.
Rule Execution Validity
Deployable as a primary escalation detector.
Rule Name
Azure High-Risk Control-Surface Change Signal
Mapped Stage
Stage 4 Privilege Escalation
Stage 5 Objective Execution
MITRE ATT&CK
T1098 – Account Manipulation
SOC Usage Mode
Supporting detection
Minimum Deployment Requirement
Requires:
· Administrative Activity Log coverage
· downstream approved-admin and approved-governance handling
· well-chosen scope
Enforcement Method
Direct Activity Log matching on policy and diagnostics control-surface changes
Implementation Constraint Notes
· This is a supporting signal, not a primary high-confidence detector
· Use this to enrich investigations around policy rollback, diagnostics tampering, or broader control-surface manipulation
· If noisy, split policy changes from diagnostics changes
Azure Activity Log Alert JSON
{
"type": "Microsoft.Insights/activityLogAlerts",
"apiVersion": "2020-10-01",
"name": "cdx-az-control-surface-signal",
"location": "Global",
"properties": {
"enabled": true,
"description": "Detect high-impact Azure policy or diagnostics control-surface changes as supporting signals.",
"scopes": [
"/subscriptions/<SUBSCRIPTION_ID>"
],
"condition": {
"allOf": [
{
"field": "category",
"equals": "Administrative"
},
{
"anyOf": [
{
"field": "operationName",
"containsAny": [
"Microsoft.Authorization/policyAssignments/write",
"Microsoft.Authorization/policyDefinitions/write",
"Microsoft.Authorization/policySetDefinitions/write",
"Microsoft.Insights/diagnosticSettings/write",
"Microsoft.Insights/diagnosticSettings/delete"
]
}
]
},
{
"field": "status",
"equals": "Succeeded"
}
]
},
"actions": {
"actionGroups": [
{
"actionGroupId": "/subscriptions/<SUBSCRIPTION_ID>/resourceGroups/<RG>/providers/microsoft.insights/actionGroups/<ACTION_GROUP_NAME>"
}
]
}
}
}
Target / Downstream Action Guidance
Downstream logic should:
· suppress known approved governance and diagnostics workflows
· annotate this alert as supporting-only unless tied to earlier suspicious identity or privilege events
Variant Analysis
Covered
· policy assignment and definition changes
· diagnostics-setting changes
Not Covered
· identity-only events outside Activity Log
· semantically risky but operationally normal governance changes
Logical Notes
Single-rule meaning: Azure policy or diagnostics control-surface change observed.
Correlated meaning: supporting signal for escalation or post-control activity.
Rule Execution Validity
Deployable as supporting detection only.
Rule Name
High-Risk Azure Control-Plane Action Following Privilege Transition
Mapped Stage
Stage 5 Objective Execution
MITRE ATT&CK
T1078 – Valid Accounts
T1098 – Account Manipulation
SOC Usage Mode
Correlation-first
Minimum Deployment Requirement
Requires:
· Administrative Activity Log coverage
· a stateful downstream target
· actor continuity or a validated fallback join-key strategy
· mature automation and backup exceptions
Enforcement Method
The Activity Log alert matches high-risk post-control management actions.
Downstream logic must correlate them to a prior Rule 1 privilege-transition event.
Implementation Constraint Notes
· Standalone single-event alerting is not permitted
· This rule is intentionally stateless at the Activity Log layer and must be correlated downstream
· If one action family is noisy, split resource-write actions from diagnostics or logging actions
Azure Activity Log Alert JSON
{
"type": "Microsoft.Insights/activityLogAlerts",
"apiVersion": "2020-10-01",
"name": "cdx-az-high-risk-post-control",
"location": "Global",
"properties": {
"enabled": true,
"description": "Detect high-risk Azure control-plane actions intended for downstream correlation after privilege transition.",
"scopes": [
"/subscriptions/<SUBSCRIPTION_ID>"
],
"condition": {
"allOf": [
{
"field": "category",
"equals": "Administrative"
},
{
"anyOf": [
{
"field": "operationName",
"containsAny": [
"Microsoft.Storage/storageAccounts/write",
"Microsoft.Compute/snapshots/write",
"Microsoft.Insights/diagnosticSettings/write",
"Microsoft.Insights/diagnosticSettings/delete",
"Microsoft.Security/securitySolutions/write"
]
}
]
},
{
"field": "status",
"equals": "Succeeded"
}
]
},
"actions": {
"actionGroups": [
{
"actionGroupId": "/subscriptions/<SUBSCRIPTION_ID>/resourceGroups/<RG>/providers/microsoft.insights/actionGroups/<ACTION_GROUP_NAME>"
}
]
}
}
}
Target / Downstream Action Guidance
Downstream logic should:
· correlate this event to a prior Rule 1 privilege-transition event by the same caller within a bounded window such as 30 minutes
· define fallback join strategy if caller is inconsistent, such as service principal ID or application ID
· split storage-heavy actions from diagnostics modifications if they behave differently in the tenant
Variant Analysis
Covered
· storage-account changes
· snapshot creation
· diagnostics changes
· selected security-control-related management actions
Not Covered
· data-plane actions not represented in Activity Log
· low-and-slow post-control activity outside the downstream correlation window
· delegated or unattributed actions without stable actor continuity
Logical Notes
Single-rule meaning: high-risk Azure control-plane action observed.
Correlated meaning: objective execution or late-stage operational action after privilege transition.
Rule Execution Validity
Deployable only as correlation-first content.
Rule Name
Azure Administrative Signal Aggregator for Suspicious Caller Context
Mapped Stage
Stage 2 Valid Account Authentication
Stage 3 Account and Resource Discovery
MITRE ATT&CK
T1078 – Valid Accounts
T1087 – Account Discovery
SOC Usage Mode
Supporting detection or correlation-first
Minimum Deployment Requirement
Requires:
· Activity Log visibility
· downstream caller-context enrichment
· approved automation exclusions
Enforcement Method
The Activity Log alert matches a narrow Azure administrative signal family.
Downstream logic must determine whether the caller or execution context is suspicious.
Implementation Constraint Notes
· Activity Log Alert JSON does not natively implement first-seen caller logic, impossible travel, or identity-risk logic
· Standalone paging is not permitted unless downstream caller-context enrichment is mature
· This is intentionally a signal wrapper, not a primary self-contained detector
Azure Activity Log Alert JSON
{
"type": "Microsoft.Insights/activityLogAlerts",
"apiVersion": "2020-10-01",
"name": "cdx-az-admin-signal-wrapper",
"location": "Global",
"properties": {
"enabled": true,
"description": "Detect Azure administrative signal family intended for downstream correlation with suspicious caller context.",
"scopes": [
"/subscriptions/<SUBSCRIPTION_ID>"
],
"condition": {
"allOf": [
{
"field": "category",
"equals": "Administrative"
},
{
"anyOf": [
{
"field": "operationName",
"containsAny": [
"Microsoft.Authorization/roleAssignments/write",
"Microsoft.Authorization/policyAssignments/write",
"Microsoft.Storage/storageAccounts/write",
"Microsoft.Insights/diagnosticSettings/write"
]
}
]
},
{
"field": "status",
"equals": "Succeeded"
}
]
},
"actions": {
"actionGroups": [
{
"actionGroupId": "/subscriptions/<SUBSCRIPTION_ID>/resourceGroups/<RG>/providers/microsoft.insights/actionGroups/<ACTION_GROUP_NAME>"
}
]
}
}
}
Target / Downstream Action Guidance
Downstream logic should:
· enrich with caller, execution context, and known admin or automation exceptions
· compare caller context against non-user or otherwise suspicious indicators
· treat as a supporting signal linking suspicious caller context to Azure discovery or control activity
Variant Analysis
Covered
· Azure administrative signal family for supporting suspicious-context detections
Not Covered
· true first-seen caller logic
· impossible-travel or device-anomaly logic
· Entra-native session anomalies outside Activity Log visibility
Logical Notes
Single-rule meaning: Azure administrative activity observed.
Correlated meaning: suspicious authenticated use leading into Azure control activity.
Rule Execution Validity
Deployable as supporting or correlation-first content only.
GCP / Eventarc
Rule Name
GCP IAM Discovery Signal
Mapped Stage
Stage 3 Account and Resource Discovery
MITRE ATT&CK
T1087 – Account Discovery
T1069 – Permission Groups Discovery
SOC Usage Mode
Supporting detection
Minimum Deployment Requirement
· Cloud Audit Logs enabled
· downstream processor capable of actor grouping and short-window counting
· allowlisting for governance, inventory, and approved admin tooling
Enforcement Method
Eventarc matches narrow IAM discovery events only. Burst enforcement must happen downstream.
Implementation Constraint Notes
· Standalone alerting is not permitted
· Single events should be treated as signal only
· This rule should not be used as a complete burst detector by itself
Variant Analysis
Covered
· IAM role enumeration
· service account listing
· IAM policy retrieval
Not Covered
· broad service-specific discovery outside these methods
· low-and-slow enumeration
· data-plane discovery
Logical Notes
Single event = benign-capable discovery signal
Correlated pattern = discovery activity
Rule Execution Validity
Supporting only
System-Ready Code
# Primary trigger
eventType: google.cloud.audit.log.v1.written
filters:
- attribute: serviceName
value: iam.googleapis.com
- attribute: methodName
value: google.iam.admin.v1.ListRoles
# Additional variants
---
eventType: google.cloud.audit.log.v1.written
filters:
- attribute: serviceName
value: iam.googleapis.com
- attribute: methodName
value: google.iam.admin.v1.ListServiceAccounts
---
eventType: google.cloud.audit.log.v1.written
filters:
- attribute: serviceName
value: cloudresourcemanager.googleapis.com
- attribute: methodName
value: GetIamPolicy
Log Type Dependency
Admin Activity only.
Rule Name
GCP IAM Policy Modification
Mapped Stage
Stage 4 Privilege Escalation
MITRE ATT&CK
T1098 – Account Manipulation
SOC Usage Mode
Primary detection
Minimum Deployment Requirement
· Cloud Audit Logs enabled
· admin and automation allowlisting defined
· resource hierarchy context available downstream
Enforcement Method
Direct match on privilege-boundary-changing IAM methods.
Implementation Constraint Notes
· Persistence behavior is not permitted in this rule
· Post-control or storage behavior is not permitted in this rule
· Approved admin exceptions must be applied downstream
Variant Analysis
Covered
· IAM policy changes
· custom role creation
· custom role update
Not Covered
· indirect escalation through pre-existing privilege
· adjacent identity-system privilege changes not emitted here
Logical Notes
Single event = privilege-boundary change
Correlated meaning = escalation
Rule Execution Validity
Primary alert-capable detection
System-Ready Code
# Primary trigger
eventType: google.cloud.audit.log.v1.written
filters:
- attribute: serviceName
value: cloudresourcemanager.googleapis.com
- attribute: methodName
value: SetIamPolicy
# Additional variants
---
eventType: google.cloud.audit.log.v1.written
filters:
- attribute: serviceName
value: iam.googleapis.com
- attribute: methodName
value: google.iam.admin.v1.CreateRole
---
eventType: google.cloud.audit.log.v1.written
filters:
- attribute: serviceName
value: iam.googleapis.com
- attribute: methodName
value: google.iam.admin.v1.UpdateRole
Log Type Dependency
Admin Activity only.
Rule Name
GCP Service Account Key Creation
Mapped Stage
Stage 5 Persistence
MITRE ATT&CK
T1078 – Valid Accounts
T1098 – Account Manipulation
SOC Usage Mode
Supporting detection
Minimum Deployment Requirement
· Cloud Audit Logs enabled
· provisioning workflows identified
· tight suppressions for approved service-account lifecycle operations
Enforcement Method
Direct match on durable access artifact creation visible in audit logs.
Implementation Constraint Notes
· Broad provisioning suppressions are not permitted
· This is supporting detection because not every persistence path is equally visible here
· Temporary-token abuse is out of scope for this rule
Variant Analysis
Covered
· service account key creation
· service account creation
Not Covered
· temporary-token abuse
· delegated access without durable artifact creation
· external trust-based persistence
Logical Notes
Single event = credential or identity artifact creation
Correlated meaning = persistence
Rule Execution Validity
Supporting, high-confidence with tuning
System-Ready Code
# Primary trigger
eventType: google.cloud.audit.log.v1.written
filters:
- attribute: serviceName
value: iam.googleapis.com
- attribute: methodName
value: google.iam.admin.v1.CreateServiceAccountKey
# Additional variant
---
eventType: google.cloud.audit.log.v1.written
filters:
- attribute: serviceName
value: iam.googleapis.com
- attribute: methodName
value: google.iam.admin.v1.CreateServiceAccount
Log Type Dependency
Admin Activity only.
Rule Name
GCP High-Risk Post-Control Action
Mapped Stage
Stage 5 Objective Execution
MITRE ATT&CK
T1078 – Valid Accounts
T1098 – Account Manipulation
SOC Usage Mode
Correlation-first
Minimum Deployment Requirement
· Cloud Audit Logs enabled
· stateful downstream processor
· actor continuity or fallback join strategy
· automation and backup exceptions
Enforcement Method
Eventarc matches high-risk post-control management actions. Downstream logic must correlate them to a prior Rule 2 event.
Implementation Constraint Notes
· Standalone alerting is not permitted
· Eventarc itself does not provide the needed state
· If noisy, split storage-permission changes from logging-impact changes
Variant Analysis
Covered
· snapshot creation
· logging sink changes
· storage bucket IAM policy changes
Not Covered
· data-plane object activity
· low-and-slow post-control activity outside correlation window
· unattributed delegated actions
Logical Notes
Single event = high-risk action
Correlated meaning = objective execution
Rule Execution Validity
Correlation-only
System-Ready Code
# Primary trigger
eventType: google.cloud.audit.log.v1.written
filters:
- attribute: serviceName
value: compute.googleapis.com
- attribute: methodName
value: v1.compute.snapshots.insert
# Additional variants
---
eventType: google.cloud.audit.log.v1.written
filters:
- attribute: serviceName
value: logging.googleapis.com
- attribute: methodName
value: google.logging.v2.ConfigServiceV2.UpdateSink
---
eventType: google.cloud.audit.log.v1.written
filters:
- attribute: serviceName
value: storage.googleapis.com
- attribute: methodName
value: storage.buckets.setIamPolicy
Log Type Dependency
Admin Activity only in this canonical set. Data Access is intentionally excluded here.
Rule Name
GCP Administrative Signal Wrapper
Mapped Stage
Stage 2 Valid Account Authentication
Stage 3 Account and Resource Discovery
MITRE ATT&CK
T1078 – Valid Accounts
T1087 – Account Discovery
SOC Usage Mode
Supporting / correlation input
Minimum Deployment Requirement
· Cloud Audit Logs enabled
· downstream caller-context enrichment
· admin and automation exception handling
Enforcement Method
Eventarc matches a narrow admin signal family. Downstream logic determines whether caller context is suspicious.
Implementation Constraint Notes
· Standalone alerting is not permitted
· This rule must not duplicate primary rule families
· First-seen logic, baseline deviation, and identity-risk scoring are downstream-only
Variant Analysis
Covered
· IAM read operations used as supporting admin-context signals
Not Covered
· true identity anomalies
· session risk analytics
· device or impossible-travel context
Logical Notes
Single event = admin activity signal
Correlated meaning = suspicious authenticated usage
Rule Execution Validity
Supporting / correlation-only
System-Ready Code
# Primary trigger
eventType: google.cloud.audit.log.v1.written
filters:
- attribute: serviceName
value: iam.googleapis.com
- attribute: methodName
value: google.iam.admin.v1.ListRoles
# Additional variant
---
eventType: google.cloud.audit.log.v1.written
filters:
- attribute: serviceName
value: iam.googleapis.com
- attribute: methodName
value: google.iam.admin.v1.ListServiceAccounts
Log Type Dependency
Admin Activity only
S26 Threat-to-Rule Traceability Matrix
Behavior
IAM role, service account, and policy discovery through repeated control-plane read activity
MITRE ATT&CK
T1087 – Account Discovery
T1069 – Permission Groups Discovery
Mapped Rule(s)
· Rule 1 — GCP IAM Discovery Signal
· Rule 5 — GCP Administrative Signal Wrapper
Telemetry Source
Cloud Audit Logs — Admin Activity
Coverage Disposition
Hunt Only
Detection Limitation
· Single events are benign-capable
· Detection requires downstream aggregation and thresholding
Behavior
Privilege boundary change through IAM policy modification or custom-role manipulation
MITRE ATT&CK
T1098 – Account Manipulation
Mapped Rule(s)
· Rule 2 — GCP IAM Policy Modification
Telemetry Source
Cloud Audit Logs — Admin Activity
Coverage Disposition
Detected
Detection Limitation
· Abuse of existing privileges does not generate new IAM change events
Behavior
Creation of durable access through service account or service account key creation
MITRE ATT&CK
T1078 – Valid Accounts
T1098 – Account Manipulation
Mapped Rule(s)
· Rule 3 — GCP Service Account Key Creation
Telemetry Source
Cloud Audit Logs — Admin Activity
Coverage Disposition
Detected
Detection Limitation
· Token-based or federated persistence may not generate equivalent artifacts
Behavior
High-risk post-escalation action through snapshot creation, logging modification, or storage permission change
MITRE ATT&CK
T1078 – Valid Accounts
T1098 – Account Manipulation
Mapped Rule(s)
· Rule 4 — GCP High-Risk Post-Control Action
Telemetry Source
Cloud Audit Logs — Admin Activity
Coverage Disposition
Partially Detected
Detection Limitation
· Requires correlation with prior escalation events
Behavior
Suspicious administrative activity from a caller context inconsistent with operational expectations
MITRE ATT&CK
T1078 – Valid Accounts
Mapped Rule(s)
· Rule 5 — GCP Administrative Signal Wrapper
Telemetry Source
Cloud Audit Logs — Admin Activity
Coverage Disposition
Hunt Only
Detection Limitation
· Requires downstream identity enrichment and context analysis
S27 Behavior & Log Artifacts
Behavioral Profile
· Control-plane activity driven through legitimate cloud APIs
· IAM and policy discovery preceding privilege changes
· Transition from read operations to write operations
· Creation of service account credentials for persistence
· Administrative actions following escalation affecting critical resources
Primary Log Artifacts
· iam.googleapis.com — ListRoles
· iam.googleapis.com — ListServiceAccounts
· cloudresourcemanager.googleapis.com — SetIamPolicy
· iam.googleapis.com — CreateServiceAccountKey
· compute.googleapis.com — snapshots.insert
· logging.googleapis.com — UpdateSink
Behavior-to-Artifact Logic
· Discovery manifests as repeated IAM read operations
· Escalation manifests as IAM policy modification
· Persistence manifests as credential creation
· Objective activity manifests as high-risk administrative actions
Telemetry Pillar Mapping
Cloud Control-Plane Telemetry
· Cloud Audit Logs — Admin Activity
Identity Context
· Principal identity
· User versus service account
Operational Context
· Project, folder, or organization scope
S27A Infrastructure Intelligence
Infrastructure Characteristics
· Single principal performing multiple IAM and administrative actions
· Transition from read-heavy to write-heavy API usage
· Execution through service accounts or delegated identities
Operational Pattern
· Discovery followed by escalation
· Escalation followed by persistence or administrative action
· Repeated use of the same identity across multiple resources
· Activity spanning multiple scopes
Infrastructure Insight
· Cloud control-plane APIs function as the attacker’s operational infrastructure
· Identity reuse is a primary indicator of activity chaining
· Traditional external infrastructure indicators are less relevant
S28 Detection Strategy and SOC Implementation Guidance
Detection Strategy
· Use Eventarc as a signal-generation layer
· Apply correlation and aggregation in downstream systems
· Prioritize escalation and persistence signals
SOC Implementation Model
Signal Intake
· Ingest Eventarc-triggered events
· Normalize identity and resource context
Correlation Layer
· Correlate escalation to post-control actions
· Apply thresholds to discovery behavior
Decision Layer
· Suppress approved workflows
· Escalate abnormal or unauthorized activity
Decision Conditions
· Escalate on unauthorized IAM policy modification
· Escalate on unauthorized service account key creation
· Escalate critically when escalation is followed by high-risk action
· Do not alert on isolated discovery events
SOC Usage Mapping
· Rule 2 — Primary detection
· Rule 3 — High-confidence supporting detection
· Rule 4 — Correlation-only
· Rule 1 and Rule 5 — Supporting signals
S29 Detection Coverage Matrix (Strategic Layer)
Coverage Mapping
IAM discovery
· Coverage Disposition: Hunt Only
· Detection Strength: Low
· Strategic Value: Early-stage signal requiring aggregation
Privilege escalation
· Coverage Disposition: Detected
· Detection Strength: High
· Strategic Value: Strong control-plane indicator
Persistence through service account key creation
· Coverage Disposition: Detected
· Detection Strength: High
· Strategic Value: Durable access indicator
High-risk post-control actions
· Coverage Disposition: Partially Detected
· Detection Strength: Medium
· Strategic Value: Correlation-dependent signal
Suspicious administrative context
· Coverage Disposition: Hunt Only
· Detection Strength: Low
· Strategic Value: Contextual enrichment signal
Strategic Assessment
· Strong coverage of escalation and persistence
· Moderate coverage of post-escalation activity
· Limited coverage of early discovery behavior
Coverage Gaps
· Identity-session anomalies
· Low-and-slow discovery patterns
· Cross-project lateral movement
· Non-key persistence mechanisms
S30 Detection Validation
Validation Approach
· Validate against known administrative workflows
· Simulate escalation, persistence, and post-control activity
· Verify suppression and correlation logic
Validation Criteria
· Rules trigger on expected malicious behavior
· Rules do not generate excessive false positives
· Correlation produces actionable alerts
Validation Outcome
· Escalation detection is reliable
· Persistence detection is reliable with tuning
· Post-control detection requires correlation
· Discovery and context signals require enrichment
Validation Limitations
· Eventarc provides no native stateful logic
· Detection depends on downstream correlation
· Identity context requires additional telemetry
Final Validation Statement
· Detection model is effective for control-plane threats
· Full effectiveness depends on a properly implemented correlation layer
S31 — Telemetry Dependencies
Purpose
Define the required telemetry and context necessary to support detection and correlation of control-plane abuse across the attack lifecycle.
Dependencies
Cloud Audit Logs — Admin Activity
· Required for IAM policy changes, service account activity, and high-risk administrative actions
· Must be enabled across project, folder, and organization scope
Eventarc Trigger Layer
· Required for ingestion of audit-log events using serviceName and methodName
· Misconfiguration results in loss of detection signals
Principal Identity Context
· Required to track actor continuity across discovery, escalation, and execution
· Must distinguish user identities, service accounts, and delegated identities
Downstream Correlation Engine
· Required for aggregation of discovery activity
· Required to correlate escalation to post-control actions
· Required for suppression of approved workflows
Allowlisting and Administrative Context
· Required to differentiate approved administrative actions from unauthorized activity
· Includes admin roles, automation identities, and change windows
S32 — Detection Limitations
Purpose
Define detection gaps and adversarial conditions that reduce detection effectiveness.
Identified Gaps
Pre-existing privilege abuse
· Attackers using existing elevated access do not trigger IAM change events
Identity-layer visibility limitations
· No native visibility into login anomalies, token theft, or session hijacking
Low-and-slow discovery
· Distributed or delayed discovery avoids aggregation thresholds
Persistence without key creation
· Workload identity, federation, or delegated access may bypass key-based detection
Distributed execution
· Activity spread across multiple identities reduces correlation effectiveness
Logging manipulation risk
· Early modification of logging configuration may degrade visibility
Impact
· Detection effectiveness depends on centralized and consistent attacker behavior
· Distributed or delayed activity reduces detection reliability
· Identity-layer attacks remain partially unobserved
S33 — Defensive Control & Hardening Improvements
Purpose
Define control improvements directly aligned to detection gaps and attacker bypass paths.
Strategic Improvements
Restrict IAM policy modification permissions
· Limit SetIamPolicy capability to controlled roles
· Enforce approval workflows for privilege changes
Reduce service account key exposure
· Disable unnecessary key creation
· Replace long-lived keys with short-lived identity mechanisms
Enforce identity isolation
· Reduce reuse of service accounts across systems
· Limit identity reuse across attack stages
Protect logging configuration
· Monitor and restrict logging sink modifications
· Preserve telemetry integrity
Strengthen correlation capability
· Implement actor-based aggregation
· Enforce escalation-to-action correlation
Control Impact Mapping
· IAM restriction reduces escalation risk
· Service account hardening reduces persistence risk
· Identity isolation reduces attack chaining capability
· Logging protection preserves detection visibility
· Correlation improves multi-stage detection accuracy
S34 — Defensive Control & Hardening Architecture
Purpose
Define the defensive architecture and its alignment to attack phases.
Defensive Architecture Layers
Signal Layer
· Eventarc ingestion of Cloud Audit Logs
· Supports rule-based signal generation
Correlation Layer
· Aggregates discovery activity
· Correlates escalation to post-control actions
Decision Layer
· Produces alerts based on unauthorized escalation and persistence
· Applies suppression and prioritization
Governance Layer
· Enforces IAM control and identity management
· Maintains allowlisting and policy enforcement
Architecture Alignment to Attack Phases
Discovery
· Detected through aggregated IAM activity
Escalation
· Detected through IAM policy modification
Persistence
· Detected through service account and key creation
Objective Execution
· Detected through correlated administrative actions
Architecture Objectives
· Detect privilege escalation immediately
· Detect persistence through credential creation
· Correlate multi-stage attack behavior
· Maintain low false positives through contextual suppression
S35 — Defensive Control Mapping Matrix
Purpose
Map defensive controls to each attack phase and assess effectiveness.
Control Mapping by Phase
Phase 1A — Credential Lure Delivery
· Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment
Phase 1B — Credential and Session Artifact Access
· Limited visibility in control-plane telemetry
· Requires identity-provider integration
Phase 2 — Discovery
· Control: IAM activity monitoring and aggregation
· Effectiveness: Low without correlation
Phase 3 — Privilege Escalation
· Control: IAM policy change detection
· Effectiveness: High
Phase 4 — Persistence
· Control: Service account and key monitoring
· Effectiveness: High with suppression
Phase 5 — Objective Execution
· Control: Correlated administrative action detection
· Effectiveness: Medium
Control Effectiveness
· Strong for escalation and persistence detection
· Moderate for post-escalation activity
· Weak for identity-layer and early discovery behavior
S36 — CyberDax Intelligence Maturity Assessment
Purpose
Assess detection, telemetry, and response maturity for this threat model.
Maturity Assessment
Detection Maturity
· Moderate
· Strong for escalation and persistence events
· Dependent on correlation for full coverage
Telemetry Maturity
· Moderate to High
· Strong control-plane visibility
· Limited identity-layer visibility
Response Maturity
· Moderate
· Requires structured triage and correlation workflows
Control Effectiveness Score
· Moderate
Audit Evidence Statement
· Detection capability validated against control-plane activity
· Known bypass paths identified in detection limitations
· Detection effectiveness depends on correlation implementation
Security Program Integration Note
· Detection must integrate with centralized SOC workflows
· Correlation and enrichment are required for full effectiveness
· IAM governance must align with detection and response
S37 — Strategic Defensive Improvements
Purpose
Define prioritized actions to improve security posture and detection capability.
Recommendations
· Restrict IAM policy modification to approved roles
· Monitor all service account key creation
· Implement correlation for multi-stage detection
· Protect logging configuration from unauthorized changes
· Reduce identity reuse across environments
Implementation Priorities
Immediate
Alert on unauthorized IAM policy changes
Alert on service account key creation
Near-Term
Implement correlation between escalation and post-control actions
Apply aggregation to discovery activity
Long-Term
Adopt identity-centric security model
Replace long-lived credentials with short-lived mechanisms
Strengthen cross-scope governance
S38 — Attack Economics & Organizational Impact Model
Purpose
Model adversary operational investment, execution efficiency, and return on investment to determine exploitation attractiveness and recurrence likelihood.
Adversary Operational Investment
· Low infrastructure cost due to reliance on native GCP control-plane APIs rather than external command-and-control infrastructure
· Minimal tooling requirements; activity executed through authenticated API calls
· Operational dependency centered on identity access acquisition rather than malware development
· High scalability through reuse of compromised identities
Credential Harvesting Operations
· Acquisition of valid authentication material through phishing, token capture, or credential reuse
· Low operational cost relative to success rate in cloud-enabled environments
· High success probability due to credential reuse and exposure patterns
Credential Store and Session Artifact Access
· Immediate access when valid credentials or session artifacts are obtained
· Eliminates need for initial privilege escalation when sufficient permissions exist
· Reduces time-to-impact and operational complexity
Authentication Material Staging and Reuse Preparation
· Service account key creation enables durable credential staging
· Credentials reusable across sessions, systems, and time periods
· Persistence cost negligible once credentials are established
Credential Reuse Against Enterprise Services
· Reuse of credentials enables access across multiple services and projects
· Supports lateral movement without additional exploitation effort
· Enables repeated operational use without re-compromise
Adversary Return on Investment
· High return due to elimination of infrastructure cost and low execution complexity
· Durable access increases long-term value of compromise
· Minimal reinvestment required after initial compromise
Return on Investment Assessment
· High ROI driven by low operational cost and high scalability
· Attack model economically sustainable and repeatable
· Detection gaps increase probability of successful execution
Economic Alignment to S6
· Low attacker cost combined with moderate-to-high enterprise impact creates asymmetric risk
· Detection limitations increase likelihood of prolonged unauthorized access
· Control gaps increase total impact cost through extended exposure duration
S39 — Economic Impact & Organizational Exposure
Incident Response and Remediation Costs
· Investigation of IAM policy changes and control-plane activity
· Revocation and rotation of compromised credentials and service account keys
· Revalidation of IAM policies across project, folder, and organization scope
· Comprehensive audit of identity permissions and access paths
Operational Disruption
· Temporary loss of access during credential revocation and policy correction
· Service disruption where access dependencies are impacted
· Increased operational load on security and cloud operations teams
Security Exposure
· Unauthorized access to cloud resources and administrative control surfaces
· Potential data exposure, modification, or destruction depending on attacker objectives
· Persistent access extending exposure duration through credential reuse
Alignment with Executive Cost Model
· Aligns with identity compromise, privilege escalation, and persistence cost drivers
· Impact increases with duration of undetected access and scope of compromised permissions
· Extended access amplifies operational and remediation costs
Annualized Risk Exposure
· Elevated due to repeatable and scalable attack model
· Increased by dependence on correlation for effective detection
· Amplified in environments with weak IAM governance and high service account usage
Estimated Probability of Recurrence
· Moderate to High
· Driven by low attacker cost, high scalability, and persistence capability
· Increased in environments lacking mature detection correlation and identity governance
S40 — References
Security Vendor Analysis
Google Cloud — Security Best Practices for IAM
· hxxps://cloud[.]google[.]com/iam/docs/using-iam-securely
Google Cloud — Cloud Audit Logs Documentation
· hxxps://cloud[.]google[.]com/logging/docs/audit
Google Cloud — Service Account Security Guidance
· hxxps://cloud[.]google[.]com/iam/docs/best-practices-service-accounts
Mandiant — Cloud Threat Landscape and Identity-Based Attacks
· hxxps://www[.]mandiant[.]com/resources
Analytical Framework
MITRE ATT&CK Framework
· hxxps://attack[.]mitre[.]org