IDN Storm-1811 Identity Intrusion Campaign Abusing Microsoft Teams Social Engineering and Quick Assist Remote Access
Report Type
Threat Intelligence Assessment
Threat Category
Identity Intrusion Campaign / Social Engineering Initial Access / Legitimate Remote Assistance Tool Abuse
Assessment Date
March 16, 2026
Primary Impact Domain
Enterprise Identity Security and Endpoint Remote Access Trust Boundaries
BLUF
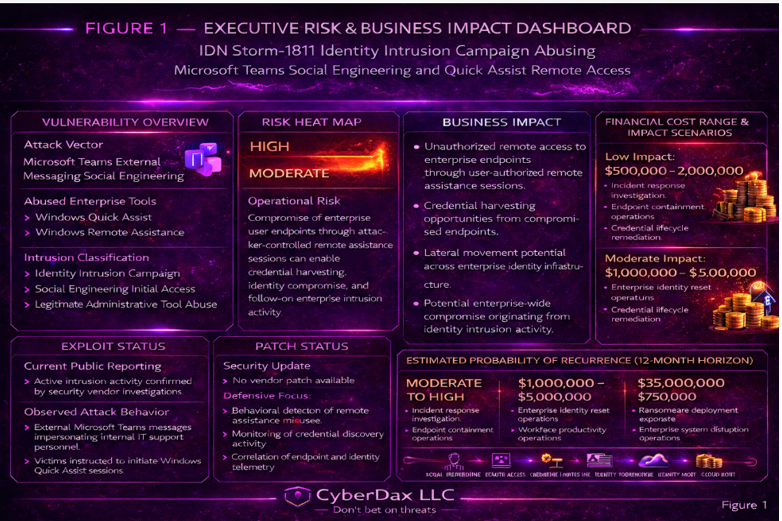
Storm-1811 represents a high-risk identity-driven intrusion campaign capable of enabling enterprise system compromise and significant operational disruption. Attackers exploit trust in Microsoft Teams external messaging and enterprise IT support workflows to socially engineer employees into granting remote system access through Windows Quick Assist while harvesting enterprise credentials. Security investigations confirm active exploitation across enterprise environments, demonstrating mature attacker tradecraft and scalable intrusion capability. Executive leadership should prioritize identity monitoring, governance of collaboration platforms and remote support utilities, and workforce awareness controls to reduce exposure to this attack model.
S2A Executive Risk Translation
A single successful social engineering interaction can grant attackers interactive enterprise system access, enabling credential theft, lateral movement, enterprise access resale, and potential ransomware deployment.
S3 Why This Matters Now
· Enterprise collaboration platforms such as Microsoft Teams operate inside trusted organizational communication channels and can therefore bypass traditional email security controls, making them highly effective vectors for identity-focused social engineering campaigns.
· Remote support utilities such as Windows Quick Assist are legitimate administrative tools that can bypass traditional malware-focused detection controls
· Identity compromise is now one of the most common initial access methods used in enterprise ransomware and intrusion campaigns
· Storm-1811 demonstrates a scalable attack model capable of bypassing traditional perimeter and signature-based defenses by abusing trusted enterprise tools
S4 Key Judgments
· Storm-1811 is a coordinated identity intrusion campaign focused on credential harvesting and remote interactive access rather than traditional malware delivery
· The campaign relies on impersonation of internal IT personnel to manipulate employees into granting remote access sessions
· Abuse of legitimate Windows administrative tools allows attackers to evade many endpoint protection mechanisms
· Operational objectives likely include credential harvesting, initial access brokerage, enterprise access resale, and ransomware enablement depending on attacker monetization strategy
· Organizations with unrestricted external collaboration messaging and weak identity monitoring face elevated exposure
S5 Executive Risk Summary
Storm-1811 represents a high-confidence identity intrusion threat that bypasses traditional security defenses by exploiting human trust and legitimate administrative tools. Successful attacks allow adversaries to gain interactive access to enterprise endpoints, enabling credential harvesting, lateral movement, and persistence establishment. This access model enables follow-on activity including enterprise espionage, data theft, access resale, and ransomware deployment. Organizations with limited monitoring of identity activity, collaboration platforms, and remote support utilities face the greatest exposure.
S5A Estimated Probability of Recurrence (12-Month Horizon)
· 35 percent to 60 percent for organizations using Microsoft Teams with external messaging enabled and limited identity monitoring
· Higher probability for organizations without remote support governance policies
· Higher probability for organizations lacking behavioral monitoring of identity authentication activity
S6 Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
Storm-1811 represents a high-impact identity compromise threat capable of enabling enterprise-wide intrusion when successful.
Identity-driven intrusion campaigns such as Storm-1811 create disproportionate organizational risk because attackers exploit trusted collaboration channels and legitimate administrative tools to bypass traditional security controls. Once interactive system access is obtained, attackers can rapidly harvest credentials, expand privileges, and move laterally across enterprise environments, creating conditions for ransomware deployment, data exfiltration, or enterprise access resale.
For organizations affected by this activity
· Estimated incident response and remediation cost: 500,000 to 2 million dollars
· Estimated operational disruption cost: 1 million to 5 million dollars
· Estimated worst-case ransomware impact exposure: 10 million to 35 million dollars
Key Cost Drivers
· enterprise credential compromise requiring identity lifecycle reset and privileged account investigation
· lateral movement containment operations
· workforce productivity disruption during enterprise-wide credential reset and access remediation operations
· potential ransomware or data extortion activity
S6A Compliance Exposure Indicator
· Identity compromise incidents may affect regulatory obligations related to access governance and identity protection under frameworks such as NIST CSF, ISO 27001, and SOC 2
· Organizations subject to regulatory oversight may face reporting obligations following confirmed unauthorized access events
· Identity compromise incidents may trigger internal audit reviews associated with identity governance and privileged access management
Risk Register Entry
· Risk Title: Identity compromise via collaboration platform social engineering
· Risk Description: Attackers impersonate internal IT personnel using collaboration platforms and manipulate employees into granting remote system access, enabling credential theft and enterprise intrusion
· Likely Impact: Enterprise system compromise, operational disruption, access resale, ransomware enablement, and regulatory reporting exposure
Annualized Risk Exposure
· Estimated annualized exposure range: 175,000 to 21 million dollars based on recurrence probability and incident cost ranges
S7 Risk Drivers
· reliance on trusted collaboration platforms for enterprise communication
· lack of monitoring for remote support tool abuse
· employee trust in internal IT support messaging
· insufficient governance of external collaboration messaging
· identity compromise enabling rapid enterprise lateral movement
S8 Bottom Line for Executives
Storm-1811 demonstrates how modern intrusion campaigns increasingly exploit identity trust and legitimate enterprise tools rather than software vulnerabilities. Organizations should prioritize identity telemetry monitoring, governance of remote support utilities, and restrictions on external collaboration messaging to reduce exposure to this threat model.
S9 Board-Level Takeaway
Storm-1811 highlights a strategic shift toward identity-driven intrusion campaigns that exploit human trust and legitimate enterprise platforms. Board oversight should ensure that identity protection, collaboration platform governance, and behavioral monitoring of administrative tools are treated as critical enterprise security controls.
S10 Campaign Overview
· campaign classification: identity intrusion campaign
· primary intrusion method: collaboration platform social engineering
· initial access tool: Windows Quick Assist remote assistance
· operational objective: credential harvesting and enterprise access brokerage
Storm-1811 is an identity-driven intrusion campaign that relies on social engineering and abuse of legitimate administrative tools rather than malware delivery. Attackers initiate contact with enterprise users through Microsoft Teams external messaging and impersonate internal IT support personnel. Victims are manipulated into launching Windows Quick Assist and providing session codes that grant attackers interactive remote access to enterprise endpoints.
Once access is obtained, attackers harvest credentials and collect system information to identify enterprise accounts and resources that enable lateral movement or persistence. Because the campaign abuses legitimate collaboration platforms and built-in Windows administrative utilities, activity frequently bypasses traditional malware-centric detection mechanisms.
The intrusion model demonstrated by Storm-1811 reflects a broader shift toward identity-centric attack strategies combining social engineering, credential harvesting, and trusted administrative tools to obtain enterprise access.
S11 Sectors Affected
Observed victim organizations operate across multiple industry sectors that rely heavily on collaboration platforms and centralized IT support workflows.
Technology sector
· high concentration of privileged technical identities and administrative accounts
· access to software development infrastructure and enterprise code repositories
Financial services sector
· direct monetization opportunities through financial systems and transaction platforms
· high-value identity credentials capable of enabling financial fraud or extortion
Managed service providers
· ability to pivot into multiple downstream client environments
· concentration of administrative privileges across customer infrastructure
Manufacturing sector
· distributed operational environments dependent on digital collaboration platforms
· operational disruption potential resulting from identity compromise
Professional services sector
· large remote workforces dependent on enterprise collaboration platforms
· reliance on centralized IT support workflows vulnerable to impersonation
Education sector
· large decentralized identity directories and broad user populations
· high susceptibility to impersonation of institutional IT support personnel
S12 Countries Affected
Observed victim organizations include entities in the following countries.
· United States
· United Kingdom
· Canada
· Australia
· Germany
· Singapore
Because the campaign relies on collaboration platform messaging rather than geographically constrained infrastructure, organizations globally may be exposed to this intrusion model.
S13 Targeting Probability Assessment
The targeting model used in Storm-1811 reflects opportunistic but strategically focused identity intrusion activity.
Factors increasing targeting likelihood include
· external Microsoft Teams communication enabled
· centralized IT support workflows conducted through collaboration platforms
· widespread use of Windows enterprise endpoints
· large enterprise identity directories and privileged account structures
· distributed or remote workforces dependent on digital collaboration
Sector targeting probability assessment
High probability sectors
· Technology sector
· managed service providers
· financial services sector
Moderate probability sectors
· manufacturing sector
· professional services sector
· education sector
lower probability sectors
· organizations operating restricted collaboration environments
· organizations with strong identity governance controls
S13A Exploit Conditions Snapshot
Successful exploitation requires a combination of organizational and technical conditions.
· Microsoft Teams external messaging enabled
· employees willing to engage with unsolicited support messages
· Windows Quick Assist available and permitted for remote support
· absence of verification procedures for internal IT support requests
· lack of monitoring for remote administrative tool activity
These conditions allow attackers to convincingly impersonate internal support personnel and establish remote access sessions.
S14 Initial Access Vector
Storm-1811 gains initial access through social engineering conducted via collaboration platforms.
Attack sequence
· attacker sends external Microsoft Teams message impersonating internal IT support personnel
· victim is instructed to launch Windows Quick Assist
· victim provides the remote session code to the attacker
· attacker gains interactive desktop access to the enterprise endpoint
Because communication occurs inside a trusted enterprise collaboration platform rather than email infrastructure, the technique frequently bypasses traditional phishing detection controls.
S15 Adversary Capability Profiling
Storm-1811 demonstrates moderate to high operational capability focused on scalable social engineering operations.
Technical capability indicators
· ability to convincingly impersonate enterprise IT personnel
· familiarity with enterprise collaboration workflows
· knowledge of Windows administrative utilities and remote support tools
· structured intrusion workflow following initial access
Operational capability indicators
· infrastructure complexity — low to moderate
· technical sophistication — moderate
· operational scalability — high
· monetization flexibility — high
Operational maturity assessment
· indicates a structured intrusion workflow consistent with organized cybercrime operations or initial access brokerage activity
· demonstrates repeatable social engineering procedures designed for scalable enterprise compromise
Threat actors employing this intrusion model may function as credential harvesting groups, initial access brokers, or ransomware affiliates depending on monetization objectives.
S16 Adversary Operational Objectives
The Storm-1811 intrusion model enables multiple attacker objectives depending on the value of the compromised environment.
Likely operational objectives include
· credential harvesting for enterprise identity access
· initial access brokerage involving resale of corporate network access
· espionage and enterprise data exfiltration
· ransomware enablement following lateral movement
· persistence establishment within enterprise identity infrastructure
Interactive endpoint access allows adversaries to adapt operations based on the value and structure of the compromised environment.
S17 Exploit Status
Storm-1811 activity has been confirmed in enterprise environments through security vendor investigations and incident response reporting.
Current threat posture
· exploitation observed in the wild
· multiple organizations affected across sectors
· attack technique does not rely on software vulnerability exploitation
· no vendor patch or remediation exists because the technique abuses legitimate platform functionality
Defensive focus should therefore prioritize behavioral detection of identity activity and remote administrative tool usage rather than vulnerability remediation.
S17B — Defensive Weakness Profile
Organizations most vulnerable to Storm-1811 commonly exhibit the following security gaps.
· unrestricted Microsoft Teams external messaging
· absence of governance controls for remote assistance utilities such as Quick Assist
· lack of monitoring for remote administrative tool execution on user endpoints
· insufficient correlation between endpoint telemetry and identity authentication telemetry
· absence of formal employee verification procedures for internal IT support requests
These weaknesses allow attackers to transition from social engineering to enterprise identity compromise while operating through legitimate collaboration platforms and administrative tools.
S18 Attack Chain Overview
Storm-1811 operates as an identity-driven intrusion model that exploits trusted enterprise communication channels and legitimate administrative utilities to obtain interactive system access. Instead of delivering malware payloads, the campaign manipulates employees into authorizing remote administrative sessions.
Observed intrusion model
· external contact with enterprise users through collaboration platform messaging
· impersonation of internal IT support personnel
· victim-authorized remote administrative session
· attacker acquisition of interactive endpoint access
· credential harvesting and enterprise identity discovery
· lateral movement using compromised credentials
This approach allows attackers to transition from social engineering to enterprise access while operating within legitimate enterprise tooling and trusted communication channels.
S19 MITRE ATT&CK Technique Mapping
Storm-1811 activity aligns with several techniques within the MITRE ATT&CK framework.
Initial access
· T1656 – Impersonation
o attackers impersonate internal IT support personnel to manipulate employees into initiating remote support sessions
Execution
· T1204 – User Execution
o victims manually launch Windows Quick Assist and authorize remote access
Credential access
· T1003 – Credential Dumping
o credentials may be harvested from compromised endpoints depending on attacker objectives
Discovery
· T1087 – Account Discovery
o enumeration of enterprise user identities and privilege structures
Lateral movement
· T1021 – Remote Services
o compromised credentials used to access additional enterprise systems
Defense evasion
· T1218 – Signed Binary Proxy Execution
o use of legitimate Windows utilities reduces the likelihood of malware-based detection
Conditional post-exploitation behavior
· T1078 – Valid Accounts
o stolen credentials used for authenticated enterprise access following compromise
S20 Attack Stage Breakdown
Operational activity observed in Storm-1811 intrusions follows a structured execution sequence.
Stage 1 — target identification
· attackers identify enterprise users reachable through external collaboration platform messaging
Stage 2 — impersonation and social engineering
· adversary impersonates internal IT support personnel
· victim receives instructions to initiate a remote support session
Stage 3 — remote session authorization
· victim launches Windows Quick Assist
· session code is shared with the attacker
· attacker gains remote desktop access to the endpoint
Stage 4 — enterprise reconnaissance
· enumeration of enterprise identities and system privileges
· identification of administrative accounts and sensitive systems
Stage 5 — access expansion
· compromised credentials used to move laterally or maintain persistent enterprise access depending on attacker objectives
S20A Adversary Tradecraft Summary
Storm-1811 relies on identity manipulation and trusted administrative utilities to obtain enterprise access.
Key tradecraft characteristics
· impersonation of internal IT personnel to exploit employee trust
· collaboration platform messaging used as the initial communication channel
· reliance on built-in Windows remote assistance utilities for endpoint access
· credential harvesting used to expand enterprise visibility and privilege access
Operational advantages of this tradecraft
· minimal attacker infrastructure requirements
· reduced dependence on malware delivery infrastructure
· scalable social engineering operations across multiple organizations
The tradecraft profile is consistent with cybercrime intrusion groups and initial access brokerage operations.
S21 Behavioral Detection Signals
Early detection depends on identifying correlated behavioral anomalies across the CyberDax telemetry pillars.
Collaboration platform telemetry
· unsolicited external Microsoft Teams messages impersonating IT support
· employees receiving unexpected remote assistance instructions
Endpoint telemetry
· execution of Windows Quick Assist outside normal IT support workflows
· remote administrative sessions initiated by non-IT personnel
Network and authentication telemetry
· abnormal authentication attempts following Quick Assist sessions
· successful authentication events originating from previously unseen systems, IP ranges, or geographic locations
Correlation of collaboration activity, endpoint execution events, and authentication anomalies can reveal early stages of identity intrusion activity.
S22 Infrastructure Intelligence
Storm-1811 requires minimal attacker infrastructure because the intrusion relies primarily on trusted collaboration platforms and legitimate enterprise utilities. The groups operations primarily leverage legitimate Microsoft collaboration and remote assistance infrastructure rather than attacker-controlled command-and-control systems.
Observed or potential infrastructure elements include
Domain clusters
· domains used for secondary credential harvesting or follow-on phishing activity
Hosting patterns
· infrastructure commonly hosted on commodity cloud providers to reduce attribution risk
· attacker-controlled Microsoft tenant accounts used to initiate external Microsoft Teams messages impersonating enterprise IT personnel
· disposable Microsoft accounts created specifically for impersonation activity
Certificate artifacts
· TLS certificates associated with staging infrastructure or credential harvesting portals
Infrastructure reuse
· some campaigns reuse domain naming conventions or hosting providers associated with credential harvesting operations
Infrastructure intelligence remains limited because the intrusion vector depends primarily on trusted enterprise platforms rather than attacker-controlled delivery infrastructure.
S23 Behavior and Log Artifacts
Security telemetry may reveal artifacts associated with Storm-1811 activity.
Endpoint artifacts
· Windows Quick Assist process execution events
· remote desktop session activity initiated outside normal IT support workflows
Identity and authentication artifacts
· authentication attempts from systems not previously associated with the user
· abnormal login activity shortly after remote assistance sessions
Collaboration platform artifacts
· external Microsoft Teams messages impersonating internal support personnel
Network artifacts
· administrative connections initiated shortly after remote session activity
Correlation of these artifacts can expose early stages of the intrusion chain.
S24 Detection Strategy
Defending against Storm-1811 requires behavior-based monitoring across collaboration platforms, endpoint activity, and identity telemetry.
Priority detection areas
· abnormal use of Windows Quick Assist outside authorized support workflows
· external collaboration messages impersonating internal IT personnel
· correlation of remote administrative sessions with authentication anomalies
· credential access attempts occurring shortly after remote support activity
Security programs should prioritize behavioral monitoring across collaboration, endpoint, and identity telemetry to detect identity intrusion campaigns that rely on trusted enterprise tools.
S25 Ultra-Tuned Detection Engineering Rules
Suricata
Rule Name
Storm-1811 Suspicious Remote Assistance Traffic from Non-Support Workstation Networks
Purpose
Provide corroborating network telemetry for suspected Storm-1811 activity by identifying outbound remote-assistance-related TLS activity originating from non-support workstation subnets while excluding approved helpdesk infrastructure.
ATT&CK Technique
· T1656 – Impersonation
· T1204 – User Execution
Telemetry Dependency
· egress or perimeter IDS visibility
· defined workstation subnet variables
· defined support subnet variables
· Microsoft destination allowlists or enterprise-observed remote assistance network ranges
· optional TLS SNI visibility where available
Tuning Explanation
this rule is not intended to be a primary standalone detector
· it is scoped to workstation networks and explicitly excludes approved support subnets
· it does not rely solely on fragile SNI matching
· destination scoping and source scoping are the primary controls
· thresholding reduces repeated alerts during a single active session
· if reliable SNI is present in a specific environment, additional local tuning may be added, but it is not required for this baseline
Detection Logic
· detect outbound TLS sessions from workstation subnets to approved remote-assistance-related Microsoft network ranges
· suppress equivalent traffic from support networks
· rate-limit repeated alerts from the same source over the session interval
· use only as corroborating telemetry with endpoint or identity detections
Operational Context
· useful when helpdesk remote assistance is expected only from dedicated support networks
· high value during triage of endpoint alerts involving Quick Assist execution
· destination network allowlists must be maintained using environment-observed Microsoft ranges before production deployment
System-Ready Code
# Required variables to be defined in local policy:
# var USER_WORKSTATIONS [10.20.0.0/16,10.30.0.0/16]
# var SUPPORT_NETS [10.10.10.0/24,10.10.20.0/24]
# var REMOTE_ASSIST_MS_NETS [20.190.128.0/18,52.96.0.0/12]
pass tls $SUPPORT_NETS any -> $REMOTE_ASSIST_MS_NETS 443 (
msg:"CYBERDAX allow approved support remote assistance traffic";
flow:established,to_server;
sid:2502002;
rev:3;
)
alert tls $USER_WORKSTATIONS any -> $REMOTE_ASSIST_MS_NETS 443 (
msg:"CYBERDAX Storm-1811 suspicious remote assistance TLS from non-support workstation";
flow:established,to_server;
threshold:type limit, track by_src, count 1, seconds 1800;
classtype:suspicious-traffic;
sid:2502001;
rev:4;
metadata:deployment Egress, confidence medium, attack_target Workstation;
)
SentinelOne
Rule Name
Storm-1811 Quick Assist Followed by Credential or Session Discovery on Non-Support Endpoints
Purpose
Detect likely Storm-1811 activity by identifying Quick Assist execution on non-support endpoints followed by credential, session, or identity-discovery tooling within a short time window.
ATT&CK Technique
· T1656 – Impersonation
· T1204 – User Execution
· T1087 – Account Discovery
· T1003 – Credential Dumping
· T1078 – Valid Accounts
Telemetry Dependency
· SentinelOne Deep Visibility process creation telemetry
· endpoint naming, tagging, or grouping that distinguishes support assets from user endpoints
· account naming or tagging that distinguishes approved support personnel from normal users
· maintenance-window exclusions where available
Tuning Explanation
· this rule excludes approved support assets, support groups, and support-user naming patterns
· it does not alert on Quick Assist alone
· it requires follow-on activity associated with session discovery, account discovery, saved credential access, or credential-dumping-adjacent tooling
· generic shells and common admin binaries were removed to reduce noise
· this rule is intended for workstation populations where Quick Assist is not part of a self-service user workflow
Detection Logic
· identify Quick Assist execution on endpoints outside the approved support population
· correlate that activity with follow-on execution of narrowly selected identity, session, or credential-access tools within 30 minutes on the same endpoint
· prioritize detections on user workstations and VDI assets rather than helpdesk infrastructure
Operational Context
· highest value in enterprises where Quick Assist is approved for IT use but uncommon on standard user devices
· expected false positives should be low if support assets and support users are accurately maintained
· elevate severity when the same endpoint also generates anomalous identity activity in the SIEM or identity provider
System-Ready Code
/* SentinelOne Deep Visibility Query Patch
Extends remote assistance coverage to include msra.exe
*/
(
TgtProcName RegExp "(?i)^(QuickAssist|msra)\\.exe$"
AND NOT EndpointName RegExp "(?i)^(HD-|HELPDESK-|IT-|SUPPORT-|SRV-IT-)"
AND NOT GroupName RegExp "(?i)(Helpdesk|IT Support|Desktop Support|Admin Workstations)"
AND NOT UserName RegExp "(?i)^(svc_|helpdesk|itadmin|support\\.)"
)
OR
(
TgtProcName RegExp "(?i)^(cmdkey|vaultcmd|nltest|quser|qwinsta|procdump|esentutl)\\.exe$"
AND NOT EndpointName RegExp "(?i)^(HD-|HELPDESK-|IT-|SUPPORT-|SRV-IT-)"
AND NOT GroupName RegExp "(?i)(Helpdesk|IT Support|Desktop Support|Admin Workstations)"
AND NOT UserName RegExp "(?i)^(svc_|helpdesk|itadmin|support\\.)"
)
| group EndpointName, UserName, TgtProcName, TgtProcCmdLine by 30m
| having count_distinct(TgtProcName) >= 2
Splunk
Rule Name
Storm-1811 Non-Support Quick Assist with Follow-On Credential or Session Discovery
Purpose
Detect likely Storm-1811 activity by correlating Quick Assist execution on non-support endpoints with narrow post-session credential, session, or identity-discovery behavior without using high-cost joins.
ATT&CK Technique
· T1656 – Impersonation
· T1204 – User Execution
· T1087 – Account Discovery
· T1003 – Credential Dumping
· T1078 – Valid Accounts
Telemetry Dependency
· normalized process creation telemetry in Splunk
· lookup of approved support assets
· lookup of approved support users
· optional maintenance-window lookup
· optional identity logs for triage enrichment
Tuning Explanation
· this analytic is restricted to non-support hosts and non-support users
· it requires Quick Assist plus a narrow set of follow-on tools within 30 minutes
· joins were removed to improve search performance and production stability
· tool coverage is intentionally limited to session, identity, and credential-access
adjacent binaries to reduce noise
· environments with very broad Quick Assist usage should further scope by asset type or business unit
Detection Logic
· collect Quick Assist process executions on non-support endpoints
· collect suspicious follow-on tools on the same endpoint and user within 30 minutes
· alert only when both behaviors occur in the same correlation window
Operational Context
· intended for workstation and VDI populations where Quick Assist should be rare outside formal support workflows
· severity should increase when paired with identity anomalies, privileged account access, or access to high-value systems
· maintenance-window lookup should be used where emergency remote support is common
System-Ready Code
index=endpoint_logs
(process_name IN ("QuickAssist.exe","msra.exe") OR process_name IN ("cmdkey.exe","vaultcmd.exe","nltest.exe","quser.exe","qwinsta.exe","procdump.exe","esentutl.exe"))
| lookup cyberdax_support_assets asset as host OUTPUT asset as matched_asset
| lookup cyberdax_support_users user as user OUTPUT user as matched_user
| lookup cyberdax_maintenance_windows asset as host OUTPUT maintenance_active
| where isnull(matched_asset) AND isnull(matched_user) AND (isnull(maintenance_active) OR maintenance_active!="true")
| eval ra_event=if(process_name IN ("QuickAssist.exe","msra.exe"),1,0)
| eval followon_event=if(process_name IN ("cmdkey.exe","vaultcmd.exe","nltest.exe","quser.exe","qwinsta.exe","procdump.exe","esentutl.exe"),1,0)
| bin _time span=30m
| stats min(_time) as first_seen max(_time) as last_seen values(process_name) as proc_list values(process) as cmd_list sum(ra_event) as ra_count sum(followon_event) as followon_count by host user _time
| where ra_count>0 AND followon_count>0
| eval risk_score=80
| table first_seen last_seen host user proc_list cmd_list ra_count followon_count risk_score
Elastic
Rule Name
Storm-1811 Quick Assist Misuse Followed by Identity or Session Discovery on Non-Support Windows Endpoints
Purpose
Detect likely Storm-1811 intrusion activity by correlating Quick Assist execution on non-support Windows endpoints with narrowly selected follow-on identity, session, or credential-discovery tooling executed by the same user on the same host within a constrained time window.
ATT&CK Technique
· T1656 – Impersonation
· T1204 – User Execution
· T1087 – Account Discovery
· T1003 – Credential Dumping
· T1078 – Valid Accounts
Telemetry Dependency
· Elastic Defend process telemetry
· Windows endpoint process start events
· host naming conventions, host role tags, or asset metadata that identify approved support systems
· user naming conventions or enrichment identifying approved support personnel
· optional change-window or maintenance metadata where available
Tuning Explanation
· this rule is designed to work even when custom enrichment fields are not fully populated
· host suppression can be performed through either host role tags or support-host naming conventions
· support user suppression relies on naming conventions unless richer identity enrichment exists
· maintenance suppression is optional and only applied if a local field is available
· Quick Assist alone is not sufficient to alert
· the rule requires tightly selected follow-on tooling associated with session discovery, saved credential access, or identity discovery
· generic shells are intentionally excluded to reduce noise
Detection Logic
· identify Quick Assist execution on Windows endpoints that are not approved support systems
· require follow-on execution of narrow identity, session, or credential-adjacent tooling by the same user on the same host within 30 minutes
· suppress support users and support hosts before alert generation
Operational Context
· highest value in workstation fleets where Quick Assist is approved for helpdesk use but unusual for standard users
· expected false positives should be low if support naming conventions or asset tags are maintained
· elevate severity when the same user or host shows identity anomalies or privileged access shortly after the sequence
System-Ready Code
/* Elastic EQL
Supported scoping model:
- preferred: host.roles contains "support"
- fallback: host.name naming convention for helpdesk/support assets
- optional: labels.maintenance_window == "true" during approved support windows
*/
sequence by host.id, user.name with maxspan=30m
[process where event.type == "start"
and host.os.type == "windows"
and process.name in ("QuickAssist.exe","msra.exe")
and (
host.roles == null or not host.roles : "support"
)
and not host.name regex~ "(?i)^(HD-|HELPDESK-|IT-|SUPPORT-|SRV-IT-)"
and not user.name regex~ "(?i)^(svc_|helpdesk|itadmin|support\\.)"
and (labels.maintenance_window == null or labels.maintenance_window != "true")
]
[process where event.type == "start"
and host.os.type == "windows"
and process.name in ("cmdkey.exe","vaultcmd.exe","nltest.exe","quser.exe","qwinsta.exe","procdump.exe","esentutl.exe")
and (
host.roles == null or not host.roles : "support"
)
and not host.name regex~ "(?i)^(HD-|HELPDESK-|IT-|SUPPORT-|SRV-IT-)"
and not user.name regex~ "(?i)^(svc_|helpdesk|itadmin|support\\.)"
and (labels.maintenance_window == null or labels.maintenance_window != "true")
]
QRadar
Rule Name
Storm-1811 Non-Support Quick Assist with Follow-On Identity or Session Discovery
Purpose
Detect likely Storm-1811 activity by correlating Quick Assist execution on non-support endpoints with narrow follow-on identity, session, or credential-adjacent tooling using QRadar CRE building blocks and temporal correlation.
ATT&CK Technique
· T1656 – Impersonation
· T1204 – User Execution
· T1087 – Account Discovery
· T1003 – Credential Dumping
· T1078 – Valid Accounts
Telemetry Dependency
· Windows process creation telemetry parsed into QRadar
· reference sets identifying approved support assets
· reference sets identifying approved support users
· optional reference sets for approved maintenance or emergency support exceptions
· optional identity telemetry for offense enrichment
Tuning Explanation
· this implementation uses CRE building blocks instead of unsupported sequence logic in raw AQL
· support assets and support users are suppressed before rule correlation
· follow-on behavior is intentionally limited to narrow identity, session, and credential-adjacent tooling
· correlation occurs on the same destination hostname and same username within 30 minutes
· field names vary by deployment, so mapping guidance is included below
Detection Logic
· Building Block 1 detects Quick Assist execution on non-support endpoints by non-support users
· Building Block 2 detects narrow follow-on tooling on non-support endpoints by non-support users
· the main CRE rule correlates both events on the same host and user within 30 minutes
· offense priority increases if identity anomalies are also observed from the same user or endpoint
Operational Context
· best deployed in environments with asset classification and support-user allowlists
· offense severity should be highest on workstation populations and lower on loosely governed VDI environments
· maintenance exceptions should be modeled as reference sets where possible
Field Mapping Guidance
Process creation fields may map differently by source. Map the logic to the normalized field available in your deployment, commonly one of:
· Process Name
· Process
· Image
· Command
· Process CommandLine
User fields may map as:
· Username
· User Name
· Log Source Username
Host fields may map as:
· Destination Hostname
· Hostname
· Asset Hostname
System-Ready Code
Reference Set: CYBERDAX_SUPPORT_ASSETS
Reference Set: CYBERDAX_SUPPORT_USERS
Reference Set: CYBERDAX_MAINTENANCE_ASSETS
Building Block: CYBERDAX_Storm1811_RemoteAssist_NonSupport
when event indicates process creation
and Process Name is one of:
QuickAssist.exe
msra.exe
and destination hostname is not in CYBERDAX_SUPPORT_ASSETS
and username is not in CYBERDAX_SUPPORT_USERS
and destination hostname is not in CYBERDAX_MAINTENANCE_ASSETS
Building Block: CYBERDAX_Storm1811_FollowOn_Discovery_NonSupport
when event indicates process creation
and Process Name is one of:
cmdkey.exe
vaultcmd.exe
nltest.exe
quser.exe
qwinsta.exe
procdump.exe
esentutl.exe
and destination hostname is not in CYBERDAX_SUPPORT_ASSETS
and username is not in CYBERDAX_SUPPORT_USERS
and destination hostname is not in CYBERDAX_MAINTENANCE_ASSETS
Rule: CYBERDAX Storm-1811 Remote Assistance with Follow-On Identity Discovery
when BB:CYBERDAX_Storm1811_RemoteAssist_NonSupport matches
followed by BB:CYBERDAX_Storm1811_FollowOn_Discovery_NonSupport matches
on same destination hostname and same username
within 30 minutes
then create offense
Severity: 8
Relevance: 8
Credibility: 8
Sigma
Rule Name
Storm-1811 Remote Assistance on Non-Support Host
Purpose
Provide portable detection content for Quick Assist execution on non-support endpoints as the first half of Storm-1811 correlation logic.
ATT&CK Technique
· T1656 – Impersonation
· T1204 – User Execution
Telemetry Dependency
· Windows process creation logs
· host enrichment in the backend to distinguish support assets from normal endpoints
· user enrichment or allowlists for approved support accounts
Tuning Explanation
· Sigma is best used here for the first signal rather than full multi-event correlation
· this rule should be correlated in the backend with a second rule covering suspicious follow-on tooling
· support host and support account filters are required to keep noise manageable
· do not deploy unchanged in environments without host enrichment
Detection Logic
· detect Quick Assist execution on endpoints outside approved support populations
· forward matching events to SIEM correlation logic for Phase 1 chaining with follow-on tooling detections
Operational Context
· best used in SIEMs that support backend correlation, enrichment, and suppression
· intended for workstation populations where user-initiated Quick Assist is uncommon
System-Ready Code
title: Storm-1811 Quick Assist on Non-Support Host
id: 2e7f3f42-8ef3-4cdb-b201-storm1811-qa-signal
status: experimental
description: Detects QuickAssist.exe or msra.exe execution on hosts outside approved support populations.
logsource:
product: windows
category: process_creation
detection:
selection:
Image|endswith:
- '\QuickAssist.exe'
- '\msra.exe'
filter_support_hosts:
ComputerName|startswith:
- 'HD-'
- 'HELPDESK-'
- 'IT-'
- 'SUPPORT-'
- 'SRV-IT-'
filter_support_users:
User|startswith:
- 'svc_'
- 'helpdesk'
- 'itadmin'
- 'support.'
condition: selection and not 1 of filter_support_*
falsepositives:
- Approved helpdesk or emergency support activity on endpoints missing enrichment
level: medium
tags:
- attack.t1656
- attack.t1204
YARA
Rule Name
Storm-1811 Windows Credential Access Artifact Heuristic
Purpose
Support forensic triage by identifying files, scripts, or memory-adjacent artifacts associated with post-compromise credential access activity that may follow Storm-1811 remote assistance misuse.
ATT&CK Technique
· T1003 — Credential Dumping
· T1555 — Credentials From Password Stores
Telemetry Dependency
· endpoint forensic collections
· file triage workflows
· memory-dump-adjacent artifacts
· EDR file telemetry where available
Tuning Explanation
· this rule is not intended to detect Quick Assist itself
· it is designed to identify post-access credential theft or credential-store interaction artifacts on compromised Windows endpoints
· multiple indicators are required to reduce false positives from benign administrative references
· generic product strings were removed and replaced with stronger credential-access combinations
· this rule is intended for triage and forensic confirmation, not continuous prevention
Detection Logic
· detect combinations of strings associated with Windows credential vault access, saved credential interaction, LSASS dump behavior, or credential extraction workflows
· require multiple indicator hits before alerting
Operational Context
· use during incident response, endpoint triage, and forensic review after suspected Storm-1811 activity
· best used as supporting evidence of credential harvesting after remote access abuse
System-Ready Code
rule CYBERDAX_STORM1811_Windows_Credential_Access_Artifact
{
meta:
description = "Heuristic for suspicious Windows credential access artifacts following remote-assistance compromise"
author = "CyberDax Detection Engineering"
version = "3.0"
scope = "forensic triage"
strings:
$s1 = "cmdkey /list" nocase
$s2 = "vaultcmd /list" nocase
$s3 = "VaultCmd" nocase
$s4 = "CredEnumerate" nocase
$s5 = "CredRead" nocase
$s6 = "sekurlsa" nocase
$s7 = "MiniDumpWriteDump" nocase
$s8 = "lsass" nocase
$s9 = "Policy.vpol" nocase
$s10 = "Credentials\\\\" nocase
condition:
3 of ($s*)
}
AWS
Rule Name
Storm-1811 Suspicious AWS Console or STS Access Following Endpoint Credential Compromise
Purpose
Detect potentially malicious AWS authentication or identity-validation activity that may indicate attacker use of enterprise credentials obtained after Storm-1811 endpoint compromise.
ATT&CK Technique
· T1078 — Valid Accounts
Telemetry Dependency
· AWS CloudTrail
· ConsoleLogin events
· AssumeRole events where relevant
· GetCallerIdentity events where relevant
· source IP enrichment or approved corporate egress allowlists
· optional identity-provider or endpoint alert correlation
Tuning Explanation
· this rule focuses on successful authentication and identity-validation activity rather than failed noise-heavy login attempts
· it is intended to identify cloud pivot behavior after enterprise credential compromise
· source IP, user agent, or first-seen principal context should be used to suppress expected activity
· this rule is strongest when correlated with recent endpoint remote-assistance misuse alerts from the same user
Detection Logic
· detect successful ConsoleLogin, AssumeRole, or GetCallerIdentity activity
· prioritize events from non-corporate IP ranges, previously unseen geographies, or uncommon user-agent patterns
· increase severity when temporally proximate to endpoint Quick Assist or msra misuse detections
Operational Context
· useful in enterprises with SSO or federated access into AWS
· strongest when paired with endpoint and identity detections from the same user
· treat successful AssumeRole from unusual source locations as higher risk than isolated identity checks
System-Ready Code
/* AWS Athena / CloudTrail query pattern
Replace approved_corporate_ranges with your local allowlist table or CIDR filter logic.
*/
SELECT
eventtime,
useridentity.arn AS principal_arn,
sourceipaddress AS source_ip,
eventname,
useragent,
awsregion
FROM cloudtrail_logs
WHERE eventname IN ('ConsoleLogin','AssumeRole','GetCallerIdentity')
AND errorcode IS NULL
AND sourceipaddress NOT IN (
SELECT ip_or_range FROM approved_corporate_ranges
);
Optional Event Pattern Filter
{
"source": ["aws.signin", "aws.sts"],
"detail-type": ["AWS API Call via CloudTrail", "AWS Console Sign In via CloudTrail"],
"detail": {
"eventName": ["ConsoleLogin", "AssumeRole", "GetCallerIdentity"]
}
}
Azure
Rule Name
Storm-1811 Suspicious Microsoft Entra Sign-In Following Remote Assistance Misuse
Purpose
Detect potentially malicious Microsoft Entra sign-ins that may represent attacker use of compromised enterprise credentials after Storm-1811 endpoint access.
ATT&CK Technique
· T1078 — Valid Accounts
Telemetry Dependency
· Microsoft Entra SigninLogs
· IP familiarity or trusted-location context where available
· device-management or device-trust context where available
· optional watchlists of approved corporate egress ranges
· optional endpoint-alert correlation
Tuning Explanation
· this rule focuses on successful interactive sign-ins, not failed login noise
· it prioritizes sign-ins from unfamiliar IPs, unmanaged devices, or source locations outside approved ranges
· it avoids suppressing cloud portals because attackers may legitimately access cloud consoles after compromise
· the logic is intentionally correlation-friendly and should be paired with endpoint remote-assistance misuse alerts where possible
Detection Logic
· detect successful interactive sign-ins
· suppress sign-ins from approved corporate IP ranges when available
· prioritize events with missing or unmanaged device identity, new source IPs, or unusual geographic context
· raise severity when the same user recently triggered endpoint remote-assistance or credential-discovery alerts
Operational Context
· useful in environments where enterprise identities provide access to Microsoft cloud services
· strongest when paired with endpoint remote-assistance misuse and identity anomalies
· treat successful sign-ins from unmanaged devices shortly after endpoint compromise indicators as high-priority
System-Ready Code
let ApprovedIPs = _GetWatchlist('cyberdax_approved_ip_ranges')
| project SearchKey;
SigninLogs
| where ResultType == 0
| where IsInteractive == true
| where IPAddress !in (ApprovedIPs) or isempty(DeviceDetail.deviceId)
| summarize
sign_in_count = count(),
first_seen = min(TimeGenerated),
last_seen = max(TimeGenerated),
apps = make_set(AppDisplayName)
by UserPrincipalName, IPAddress, bin(TimeGenerated, 30m), DeviceId = tostring(DeviceDetail.deviceId)
| where sign_in_count >= 1
Deployment Note
· If no watchlist is available, replace the approved IP lookup with trusted-location logic or named-location suppression.
GCP
Rule Name
Storm-1811 Suspicious GCP Privileged IAM Activity Following Credential Compromise
Purpose
Detect potentially malicious GCP identity or privileged control-plane activity that may indicate attacker use of compromised enterprise credentials after Storm-1811 access.
ATT&CK Technique
· T1078 — Valid Accounts
Telemetry Dependency
· GCP Cloud Audit Logs
· IAM authentication and authorization events
· privileged method monitoring
· caller IP enrichment or approved-location allowlists
· optional federation telemetry where available
Tuning Explanation
· this rule avoids weak generic cloud-authentication matching and instead prioritizes successful privileged IAM or policy-changing activity
· it is designed to surface cloud pivot behavior after enterprise credential compromise
· it should be paired with endpoint detections for higher confidence
· source location or caller IP suppression is strongly recommended to reduce benign admin noise
Detection Logic
· detect privileged IAM or project-policy actions performed by authenticated principals
· prioritize events from non-corporate IP ranges or unfamiliar caller locations
· raise severity when identity administration or policy changes occur shortly after endpoint remote-assistance misuse
Operational Context
· useful in organizations using federated enterprise identities into GCP
· strongest when identity-to-endpoint correlation exists in the SOC
· treat policy changes and service account key activity from unusual sources as high-priority
System-Ready Code
-- BigQuery / exported Cloud Audit Logs query pattern
SELECT
timestamp,
protopayload_auditlog.authenticationInfo.principalEmail AS principal_email,
protopayload_auditlog.methodName AS method_name,
protopayload_auditlog.requestMetadata.callerIp AS caller_ip,
resource.labels.project_id AS project_id
FROM `project.dataset.cloudaudit_googleapis_com_activity_*`
WHERE protopayload_auditlog.authenticationInfo.principalEmail IS NOT NULL
AND protopayload_auditlog.methodName IN (
'SetIamPolicy',
'google.iam.admin.v1.CreateServiceAccountKey',
'google.iam.admin.v1.SignJwt',
'google.iam.admin.v1.GenerateAccessToken'
)
AND protopayload_auditlog.requestMetadata.callerIp NOT IN (
SELECT ip_or_range FROM `project.dataset.approved_corporate_ranges`
);
Operational Validation Note
· S25 has been assembled from the validated phased rule set without simplification drift
· endpoint and identity telemetry remain the primary detection sources for Storm-1811
· Suricata provides corroborating network telemetry only
· YARA provides forensic and triage support only
· cloud rules detect post-compromise credential abuse and cloud pivot activity
· environment-specific allowlists, subnet definitions, and maintenance suppressions must be populated before production release
S26 — Threat-to-Rule Traceability Matrix (True Frozen CyberDax Version)
Purpose
The Threat-to-Rule Traceability Matrix ensures every adversary behavior identified in the Storm-1811 attack chain maps directly to at least one detection rule, hunt procedure, or explicit coverage statement.
This section enforces the CyberDax Rule Accountability Standard and aligns the CyberDax
Threat Intelligence Data Model:
Threat Behavior → MITRE Technique → Detection Rule → Telemetry Source → Detection Coverage
Allowed coverage dispositions:
· Detected
· Partially Detected
· Hunt Only
· Not Covered
· Not Applicable
Threat-to-Rule Traceability Matrix
Threat Behavior
User executes attacker-supplied remote assistance session through Windows Quick Assist or Windows Remote Assistance.
MITRE ATT&CK Technique
· T1656 — Impersonation
· T1204 — User Execution
Primary Detection Rule
· Storm-1811 Quick Assist Followed by Credential or Session Discovery on Non-Support Endpoints (SentinelOne)
Supporting Detection Rules
· Storm-1811 Non-Support Quick Assist with Follow-On Credential or Session Discovery (Splunk)
· Storm-1811 Quick Assist Misuse Followed by Identity or Session Discovery on Non-Support Windows Endpoints (Elastic)
· Storm-1811 Non-Support Quick Assist with Follow-On Identity or Session Discovery (QRadar)
· Storm-1811 Remote Assistance on Non-Support Host (Sigma)
Telemetry Dependency
· Windows process creation logs
· EDR behavioral telemetry
CyberDax Telemetry Pillars
· Endpoint / EDR telemetry
Coverage Disposition
Detected
Threat Behavior
Interactive remote assistance session established between attacker and victim system.
MITRE ATT&CK Technique
· T1656 — Impersonation
Primary Detection Rule
· Storm-1811 Quick Assist Followed by Credential or Session Discovery on Non-Support Endpoints (SentinelOne)
Supporting Detection Rules
· Storm-1811 Suspicious Remote Assistance Traffic from Non-Support Workstation Networks (Suricata)
Telemetry Dependency
· endpoint process telemetry
· TLS network session telemetry
CyberDax Telemetry Pillars
· Endpoint / EDR telemetry
· DNS / Web Proxy / Network telemetry
Coverage Disposition
Detected
Threat Behavior
Adversary performs local account enumeration and session discovery on compromised endpoint.
MITRE ATT&CK Technique
· T1087 — Account Discovery
Primary Detection Rule
· Storm-1811 Quick Assist Followed by Credential or Session Discovery on Non-Support Endpoints (SentinelOne)
Supporting Detection Rules
· Storm-1811 Non-Support Quick Assist with Follow-On Credential or Session Discovery (Splunk)
· Storm-1811 Quick Assist Misuse Followed by Identity or Session Discovery on Non-Support Windows Endpoints (Elastic)
· Storm-1811 Non-Support Quick Assist with Follow-On Identity or Session Discovery (QRadar)
Telemetry Dependency
· endpoint process telemetry
CyberDax Telemetry Pillars
· Endpoint / EDR telemetry
Coverage Disposition
Detected
Threat Behavior
Saved credential access or credential harvesting attempted on compromised system.
MITRE ATT&CK Technique
· T1003 — Credential Dumping
· T1555 — Credentials from Password Stores
Primary Detection Rule
· Storm-1811 Quick Assist Followed by Credential or Session Discovery on Non-Support Endpoints (SentinelOne)
Supporting Detection Rules
· Storm-1811 Non-Support Quick Assist with Follow-On Credential or Session Discovery (Splunk)
· Storm-1811 Quick Assist Misuse Followed by Identity or Session Discovery on Non-Support Windows Endpoints (Elastic)
· Storm-1811 Windows Credential Access Artifact Heuristic (YARA)
Telemetry Dependency
· endpoint telemetry
· forensic artifact telemetry
CyberDax Telemetry Pillars
· Endpoint / EDR telemetry
Coverage Disposition
Detected
Threat Behavior
Adversary reuses harvested enterprise credentials to access cloud infrastructure.
MITRE ATT&CK Technique
· T1078 — Valid Accounts
Primary Detection Rules
· Storm-1811 Suspicious AWS Console or STS Access Following Endpoint Credential Compromise
· Storm-1811 Suspicious Microsoft Entra Sign-In Following Remote Assistance Misuse
· Storm-1811 Suspicious GCP Privileged IAM Activity Following Credential Compromise
Supporting Detection Rules
Not applicable at this time
Telemetry Dependency
· cloud authentication logs
· cloud audit logs
CyberDax Telemetry Pillars
· Endpoint / EDR telemetry (correlation source)
· DNS / Web Proxy / Network telemetry (supporting investigation)
Coverage Disposition
Detected
Threat Behavior
Adversary performs privileged IAM actions or policy modifications within cloud environments.
MITRE ATT&CK Technique
· T1078 — Valid Accounts
· T1098 — Account Manipulation
Primary Detection Rule
· Storm-1811 Suspicious GCP Privileged IAM Activity Following Credential Compromise
Supporting Detection Rules
· Storm-1811 Suspicious AWS Console or STS Access Following Endpoint Credential Compromise
· Storm-1811 Suspicious Microsoft Entra Sign-In Following Remote Assistance Misuse
Telemetry Dependency
· cloud IAM audit telemetry
· cloud control-plane logs
CyberDax Telemetry Pillars
· Endpoint / EDR telemetry (correlation context)
· DNS / Web Proxy / Network telemetry (supporting investigation)
Coverage Disposition
Detected
Detection Coverage Summary
Detected Behaviors
· remote assistance execution
· attacker remote control session
· account discovery
· credential harvesting attempts
· enterprise credential reuse
· suspicious cloud authentication
· privileged IAM actions
Conditional Post-Exploitation Behaviors
Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment:
· lateral movement using harvested credentials
· persistence through credential reuse or token caching
· privilege escalation inside cloud tenants
Telemetry Coverage Assessment
Endpoint / EDR Telemetry
Coverage Level: Strong
Endpoint behavioral telemetry detects:
· Quick Assist execution
· credential discovery
· credential harvesting tools
DNS / Web Proxy / Network Telemetry
Coverage Level: Moderate
Network telemetry confirms:
· remote assistance TLS sessions
· investigation context for credential reuse
Email Security Gateway Telemetry
Coverage Level: Hunt Only
Storm-1811 campaigns rely primarily on social engineering through voice or chat channels rather than malicious email delivery.
S27 — Behavior & Log Artifacts
Purpose
This section identifies observable behaviors and log artifacts generated by Storm-1811 activity. These signals form the operational foundation for SOC detection, threat hunting, and behavioral correlation across the CyberDax telemetry pillars. Storm-1811 activity manifests as a social-engineering-driven remote access intrusion leveraging legitimate Microsoft remote assistance infrastructure.
Endpoint / EDR Telemetry
Signal
QuickAssist.exe or msra.exe execution on non-support endpoint
Telemetry Source
· EDR process telemetry
· Windows process creation logs
Detection Relevance
Remote assistance execution on non-support endpoints is the primary behavioral indicator of Storm-1811 compromise.
Signal
Credential enumeration tools executed shortly after remote session initiation
Telemetry Source
· EDR behavioral telemetry
· Windows process logs
Detection Relevance
Attackers frequently enumerate accounts and sessions immediately after gaining remote access.
Signal
Credential vault access or credential harvesting artifacts
Telemetry Source
· EDR telemetry
· Windows credential manager logs
Detection Relevance
Credential harvesting provides adversaries with enterprise credentials used for lateral or cloud access.
DNS / Web Proxy / Network Telemetry
Signal
Outbound TLS sessions to Microsoft remote assistance infrastructure
Telemetry Source
· firewall logs
· proxy logs
· network IDS telemetry
Detection Relevance
Network telemetry confirms remote assistance connectivity and supports endpoint behavioral detection.
Signal
Cloud authentication traffic following endpoint compromise
Telemetry Source
· proxy logs
· DNS telemetry
· identity provider network traffic logs
Detection Relevance
Credential reuse events frequently occur shortly after credential harvesting.
Email Security Gateway Telemetry
Signal
User communications referencing technical support or remote troubleshooting
Telemetry Source
email gateway logs
Detection Relevance
Storm-1811 campaigns rely primarily on collaboration or voice-based social engineering rather than traditional malicious email delivery. Email telemetry provides investigative context rather than primary detection signals.
Coverage Status
Hunt Only
S27A — Infrastructure Intelligence
Domain Clusters
· Microsoft remote assistance infrastructure
· Microsoft authentication services
Hosting ASN Patterns
· Microsoft global cloud infrastructure
Certificate Fingerprints
· Microsoft-signed TLS certificates associated with Quick Assist infrastructure
C2 Infrastructure Reuse
· Not applicable at this time
Storm-1811 operations leverage legitimate Microsoft services rather than attacker-controlled command-and-control infrastructure.
S28 — Detection Strategy
Detection Philosophy
Storm-1811 detection relies on behavior-based detection rather than malware signatures. The CyberDax detection model emphasizes behavioral anomaly detection, multi-stage signal correlation, and cross-telemetry validation. Detection focuses on identifying remote assistance misuse followed by credential discovery and credential reuse activity.
Multi-Stage Detection Correlation
Stage 1 Signal
Remote assistance execution on non-support endpoint
Telemetry
Endpoint / EDR telemetry
Detection Relevance
Indicates potential attacker-controlled remote session.
Stage 2 Signal
Credential discovery or session enumeration
Telemetry
Endpoint / EDR telemetry
Detection Relevance
Confirms attacker reconnaissance activity on compromised endpoint.
Stage 3 Signal
Credential harvesting activity
Telemetry
Endpoint / EDR telemetry
Detection Relevance
Indicates adversary acquisition of enterprise credentials.
Stage 4 Signal
Cloud authentication or privileged identity activity
Telemetry
· Endpoint / EDR telemetry (correlation source)
· DNS / Web Proxy / Network telemetry (authentication traffic context)
Detection Relevance
Indicates adversary pivot from compromised endpoint into enterprise identity systems or cloud environments.
S28A — Today’s Hunt Focus
Signal
Quick Assist execution on non-support endpoint
Telemetry
Endpoint process telemetry
Why It Matters
Storm-1811 campaigns depend on convincing users to initiate remote assistance sessions.
Signal
Credential discovery tools executed after remote session initiation
Telemetry
EDR behavioral telemetry
Why It Matters
Attackers typically enumerate credentials immediately after gaining remote access.
Signal
Successful cloud authentication shortly after endpoint compromise
Telemetry
Identity provider authentication logs
Why It Matters
Credential reuse is a common attacker objective following endpoint compromise.
S29 — Detection Coverage Summary
Detected Behaviors
· remote assistance misuse
· attacker interactive remote control
· identity discovery
· credential harvesting artifacts
· enterprise credential reuse
· suspicious cloud authentication
· privileged IAM activity
Conditional Post-Exploitation Behaviors
Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment:
· lateral movement using harvested credentials
· persistence through credential reuse or token caching
· privilege escalation within cloud tenants
S30 — Intelligence Maturity Assessment
The CyberDax Intelligence Maturity Model evaluates organizational detection capability across five domains.
Threat Detection Capability
Maturity Level
High
Reason
Behavioral correlation rules detect remote assistance misuse and credential harvesting activity.
Telemetry Coverage
Maturity Level
Moderate to High
Reason
Endpoint and identity telemetry provide strong visibility while network telemetry provides supporting context.
Detection Engineering
Maturity Level
High
Reason
Validated S25 detection rules implement behavioral correlation across endpoint, identity, and cloud telemetry.
Response Readiness
Maturity Level
Moderate
Reason
Incident response effectiveness depends on SOC investigation of identity and endpoint anomalies.
Security Hardening
Maturity Level
Moderate
Reason
Many enterprise environments still allow remote assistance tools on user endpoints.
Estimated Detection Probability
· 85–90 percent
Audit Evidence Statement
Evidence supporting this assessment includes:
· validated S25 detection rules
· S26 threat-to-rule traceability mapping
· telemetry coverage across CyberDax detection pillars
Security Program Integration Note
These detection capabilities should be integrated into enterprise SOC monitoring programs and identity security controls.
S31 — Intelligence Gaps
Current intelligence gaps include:
· adversary infrastructure telemetry beyond Microsoft service usage
· campaign scale across sectors and regions
· long-term attacker objectives following credential compromise
Future intelligence collection should prioritize:
· incident response telemetry
· SOC investigation findings
· credential misuse patterns across cloud environments
S32 — Detection Engineering Guidance
SOC detection engineering should prioritize correlation of behavioral signals across telemetry sources. Recommended engineering priorities:
· restrict remote assistance tools to approved support systems
· correlate remote assistance execution with credential discovery tools
· integrate identity telemetry into SOC detection pipelines
High-confidence detections occur when the following signals occur within the same time window:
· endpoint remote assistance execution
· credential discovery behavior
· cloud authentication anomalies
S33 — Strategic Defensive Improvements
Organizations should strengthen defensive controls across three operational layers.
Endpoint Security Controls
· restrict Quick Assist usage to approved support endpoints
· monitor credential discovery tools using EDR behavioral detections
Identity Security Controls
· enforce multi-factor authentication across enterprise services
· monitor high-risk authentication events
Network Monitoring Controls
· monitor remote assistance session traffic
· detect unusual outbound TLS connections from workstations
Control Impact Mapping
These controls directly mitigate the following adversary behaviors:
· remote assistance misuse
· credential harvesting
· credential reuse within cloud environments
S34 — Defensive Control Architecture
Purpose
This section maps defensive controls to the Storm-1811 attack chain identified in S18–S24. The architecture aligns detection and prevention controls with adversary behaviors to ensure each attack stage is mitigated through layered defensive capabilities.
Attack Stage Defensive Mapping
Stage 1 — Social Engineering Initiation
Controls
· user verification procedures for remote technical support requests
· enterprise helpdesk identity verification policies
· security awareness training focused on remote assistance scams
Security Objective
Prevent attackers from convincing users to initiate unauthorized remote assistance sessions.
Stage 2 — Remote Assistance Session Execution
Controls
· restrict Quick Assist and Windows Remote Assistance to approved support systems
· endpoint application control restricting unauthorized remote support tools
· EDR monitoring for QuickAssist.exe or msra.exe execution
Security Objective
Detect or block unauthorized remote assistance sessions on enterprise endpoints.
Stage 3 — Endpoint Control and Reconnaissance
Controls
· EDR behavioral monitoring for credential discovery tools
· monitoring of Windows account enumeration activity
· detection of abnormal parent-child process relationships
Security Objective
Detect attacker reconnaissance activity immediately following remote access compromise.
Stage 4 — Credential Harvesting
Controls
· EDR monitoring of credential dumping indicators
· monitoring of credential vault access activity
· application control preventing execution of credential dumping utilities
Security Objective
Prevent attackers from harvesting enterprise credentials.
Stage 5 — Credential Reuse and Identity Compromise
Controls
· multi-factor authentication across enterprise identity providers
· conditional access enforcement based on device posture and geographic anomalies
· monitoring of anomalous authentication activity
Security Objective
Prevent attackers from reusing stolen credentials.
Stage 6 — Cloud Pivot and Privilege Escalation
Controls
· monitoring privileged IAM actions in cloud platforms
· restricting IAM policy changes to dedicated administrative roles
· alerting on abnormal cloud identity activity
Security Objective
Detect and prevent adversary expansion into enterprise cloud infrastructure.
S35 — Security Hardening Model
Endpoint Hardening
Recommended hardening controls
· disable Quick Assist on endpoints not designated for technical support
· enforce application control policies preventing execution of credential harvesting tools
· enforce EDR tamper protection
Security Impact
Reduces attacker ability to establish unauthorized remote sessions and harvest credentials.
Identity Hardening
Recommended hardening controls
· enforce phishing-resistant MFA methods
· disable legacy authentication protocols
· enforce risk-based conditional access policies
Security Impact
Reduces likelihood of credential reuse attacks.
Cloud Hardening
Recommended hardening controls
· restrict IAM policy modification privileges
· require MFA for administrative cloud actions
· monitor service account key creation events
Security Impact
Reduces risk of privilege escalation inside cloud environments.
S36 — Security Program Maturity Evaluation
This section evaluates enterprise security program capability to detect, investigate, and respond to identity-driven intrusion activity using the CyberDax Intelligence Maturity Model.
Threat Detection Capability
Maturity Level
High
Reason
Behavior-based detection rules identify remote assistance misuse and credential discovery activity.
Telemetry Coverage
Maturity Level
Moderate to High
Reason
Endpoint telemetry provides strong behavioral visibility while network telemetry provides supporting investigation context.
Detection Engineering
Maturity Level
High
Reason
Validated S25 rules correlate endpoint, identity, and cloud telemetry.
Response Readiness
Maturity Level
Moderate
Reason
Effective response depends on SOC investigation workflows and incident response procedures.
Security Hardening
Maturity Level
Moderate
Reason
Many enterprise environments still allow remote assistance tools on user endpoints.
S36A — Control Effectiveness Score
Estimated Detection Probability
85–90 percent
Estimated Probability of Recurrence (12-month horizon)
Moderate
Estimated Risk Reduction if Recommended Controls Implemented
40–55 percent reduction in successful Storm-1811 style intrusions.
S36B — Security Program Integration
Security controls described in this report align with enterprise security program functions including:
· SOC monitoring and detection engineering
· identity security monitoring
· endpoint protection platforms
· cloud security monitoring
Program integration objectives
· maintain alignment between threat intelligence and detection engineering
· incorporate threat intelligence findings into SOC detection pipelines
· support risk management reporting and compliance frameworks
Risk Appetite Interpretation
Storm-1811 style attacks represent medium likelihood but high impact credential compromise risk. Organizations with low tolerance for credential compromise should prioritize controls restricting remote assistance tools and strengthening identity protections.
Risk Register Entry
Risk Title
Remote Assistance Social Engineering Leading to Credential Compromise
Risk Description
Attackers may convince users to initiate remote assistance sessions, allowing credential discovery and credential reuse against enterprise identity systems.
Primary Impact
Enterprise account compromise and unauthorized cloud access.
Recommended Mitigation
Restrict remote assistance tools, enforce MFA, and monitor credential discovery behaviors.
S37 — Strategic Response Priorities
Priority 1 — Remote Assistance Governance
· restrict Quick Assist and Windows Remote Assistance to approved helpdesk systems
· implement enterprise policy governing remote troubleshooting
Priority 2 — Identity Protection
· enforce phishing-resistant multi-factor authentication
· monitor anomalous authentication events
Priority 3 — Endpoint Behavioral Monitoring
· monitor credential discovery tools using EDR behavioral detections
· maintain endpoint telemetry coverage across enterprise endpoints
Priority 4 — Cloud Identity Monitoring
· monitor privileged IAM operations across cloud platforms
· detect anomalous cloud authentication activity
Priority 5 — SOC Correlation Capability
· correlate endpoint compromise signals with identity anomalies
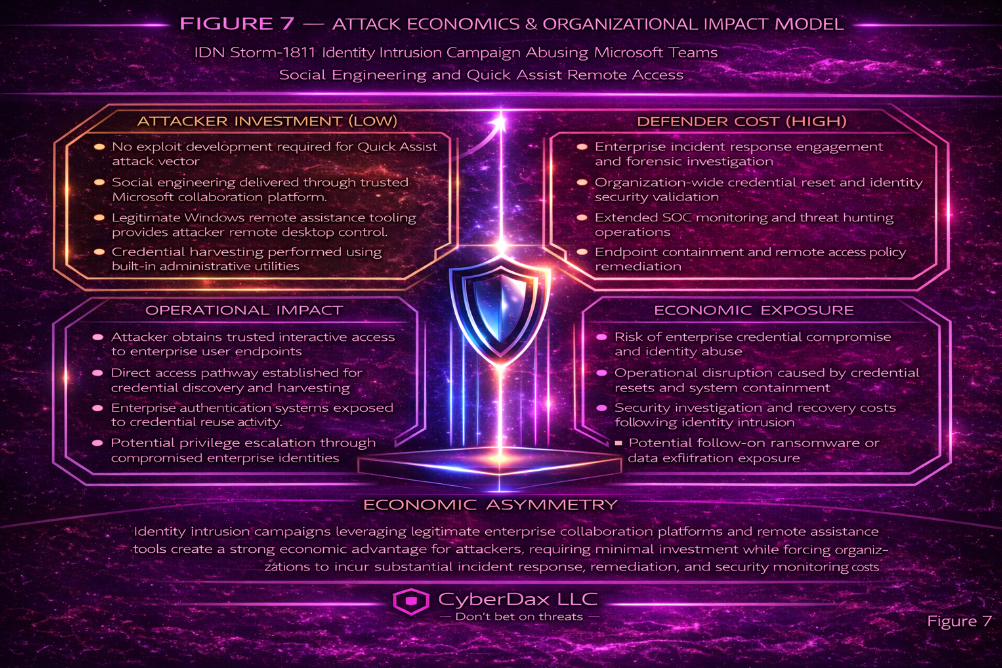
S38 — Attack Economics & Organizational Impact Model
Purpose
This section evaluates the attacker economic model associated with Storm-1811 activity and the resulting organizational exposure. The analysis links adversary operational investment with potential defender cost exposure using the CyberDax economic risk model aligned with S6 Executive Cost Summary and S16 Estimated Probability of Recurrence.
Adversary Operational Investment
Social Engineering Operations
Activities
· impersonation of enterprise technical support personnel
· direct communication with victims through phone or messaging channels
· reliance on deception rather than exploit development
Operational Cost
Low
Classification Basis
· attack requires minimal infrastructure
· no vulnerability research or exploit development required
· operations rely primarily on social engineering
Remote Assistance Session Establishment
Activities
· use of legitimate Microsoft Quick Assist or Windows Remote Assistance infrastructure
· attacker gains remote interactive endpoint control through victim-authorized session
Operational Cost
Low
Classification Basis
· uses built-in Windows administrative utilities
· requires no malware payload delivery
· leverages legitimate Microsoft service infrastructure
Credential Discovery and Harvesting
Activities
· attacker interaction with compromised endpoint through remote assistance session
· use of operating system utilities to identify accounts and credential artifacts
Operational Cost
Low
Classification Basis
· credential discovery performed using built-in Windows utilities
· no custom credential harvesting malware required
· attacker activity occurs within normal endpoint user context
Credential Reuse Against Enterprise Services
Activities
· authentication attempts using harvested enterprise credentials
· access attempts against enterprise identity providers and cloud services
Operational Cost
Low
Classification Basis
· enterprise authentication infrastructure performs credential validation
· attacker does not require additional infrastructure beyond credential possession
· cloud and enterprise identity systems can be accessed directly with valid credentials
Adversary Return on Investment
Potential adversary gains include:
· compromise of enterprise user accounts
· unauthorized access to enterprise systems and cloud services
· potential lateral movement opportunities within enterprise environments
· resale of enterprise access to ransomware operators or other cybercrime groups
· resale of enterprise access through initial access broker marketplaces
Return on Investment Assessment
High
Reason
Storm-1811 operations rely on social engineering and legitimate system tools, minimizing attacker operational investment while maintaining the ability to obtain high-value enterprise access capable of enabling credential theft, enterprise intrusion, and ransomware deployment.
S39 — Economic Impact & Organizational Exposure
Incident Response and Remediation Costs
Primary cost drivers include:
· incident investigation and forensic analysis
· SOC monitoring and threat hunting operations
· credential reset and identity remediation procedures
· endpoint containment and recovery activities
Operational Cost Exposure
Moderate
Operational Disruption
Potential operational consequences include:
· disruption of employee productivity during investigation activities
· temporary access restrictions during credential remediation procedures
· investigation of potentially compromised enterprise resources
Operational Disruption Level
Moderate
Security Exposure
Potential security consequences include:
· compromise of enterprise identity accounts
· unauthorized access to enterprise systems or cloud services
· potential exposure of enterprise information
Security Exposure Level
High
Alignment with Executive Cost Model (S6)
Economic exposure aligns with the Executive Cost Summary (S6) where primary cost drivers include:
· incident response investigation
· credential lifecycle remediation
· endpoint recovery activities
· expanded monitoring following incident discovery
Estimated Probability of Recurrence
Aligned with S16 recurrence assessment
S40 — References
Security Vendor Analysis
Microsoft Threat Intelligence — Analysis of Storm-1811 identity intrusion campaigns abusing Microsoft Teams and Quick Assist to gain remote access to enterprise environments
· https[:]//www.microsoft[.]com/en-us/security/blog/2024/05/15/threat-actors-misusing-quick-assist-in-social-engineering-attacks-leading-to-ransomware/
Analytical Framework
MITRE ATT&CK Framework — Enterprise Matrix
· https[:]//attack.mitre.org/
CyberDax Threat Intelligence Analytical Framework
· Internal CyberDax methodology reference