[SUP] TrueConf Trusted Update Channel Compromise (CVE-2026-3502)
Report Type
SUP
Threat Category
Supply Chain Compromise via Trusted Update Mechanism
Assessment Date
April 08, 2026
Primary Impact Domain
Enterprise Endpoint Compromise
Secondary Impact Domains
Software Supply Chain Integrity
Internal Network Trust Boundaries
Update Distribution Infrastructure
Affected Asset Class
Enterprise Endpoints (Windows Systems)
Software Update Mechanisms
Internal Update Distribution Systems
Threat Objective Classification
Initial Access Enablement
Persistence Enablement (Conditional Post-Exploitation)
Lateral Propagation via Trusted Distribution
Potential Espionage or Access Brokerage (Dependent on Attacker Objectives)
BLUF
This vulnerability creates high business risk by enabling attackers to distribute malicious code through a trusted software update channel across multiple endpoints. The technical cause is a failure to validate update integrity, allowing tampered payloads to execute as part of legitimate update workflows without requiring user interaction. The inclusion of CVE-2026-3502 in the CISA KEV catalog confirms active exploitation and materially increases the likelihood of enterprise impact. Immediate executive action is required to patch affected systems, validate update trust controls, and enforce behavioral monitoring of update-driven execution.
Executive Risk Translation
This is a trusted distribution compromise risk where normal update mechanisms can be abused to propagate attacker-controlled code across the enterprise.
S3 Why This Matters Now
Active exploitation confirmed through KEV inclusion removes uncertainty around threat viability and compresses remediation timelines. This vulnerability shifts the attack model from external intrusion to internal trusted delivery, reducing visibility during the initial execution stage of compromise. As a result, organizations relying on perimeter or signature-based controls will not detect the threat until after execution occurs. This creates an immediate exposure window where delayed detection increases the likelihood of multi-endpoint impact.
S4 Key Judgments
· The vulnerability stems from a failure to validate update integrity, enabling execution of tampered code as part of a trusted update workflow without requiring user interaction
· The TrueConf update mechanism can act as a trusted internal distribution node, allowing attacker-controlled payload propagation without triggering ingress controls
· Malicious delivery may appear legitimate, creating a trust inversion where detection begins only after execution
· The attack can scale across endpoints through standard update processes, introducing propagation risk beyond single-system compromise
· Effective detection depends on endpoint telemetry, process lineage validation, and cross-pillar correlation, not traditional preventive controls
S5 Executive Risk Summary
This exposure represents a high-impact supply chain scenario in which a trusted update mechanism can be leveraged to distribute and execute malicious payloads across multiple systems without requiring user interaction. Unlike traditional vulnerabilities that affect individual hosts, this model introduces the risk of coordinated multi-endpoint compromise driven by trusted distribution and delayed detection, increasing both speed and scale of impact. Business consequences include rapid endpoint compromise, persistence establishment, potential credential exposure, operational disruption, and significantly increased incident response cost. KEV designation further elevates risk by confirming active exploitation and reducing acceptable response timelines, increasing both operational and governance consequences.
S6 Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
· Low Impact
$15,000 to $150,000
Limited exposure affecting a small number of endpoints with no confirmed malicious execution. Costs include patch deployment, update validation, targeted endpoint review, and monitoring. Impact remains contained due to lack of propagation
· Moderate Impact
$150,000 to $1,500,000
Multi-endpoint exposure requiring validation of update distribution, expanded threat hunting, and containment actions. Costs include operational disruption, engineering effort, endpoint remediation, and monitoring expansion. Impact scales with the number of endpoints receiving updates through trusted distribution
· High Impact
$1,500,000 to $6,000,000+
Widespread compromise involving malicious update propagation across multiple endpoints, persistence, and external communication. Costs include enterprise-wide containment, reimaging, credential resets, downtime, third-party response services, and regulatory exposure. Impact is amplified by the trusted update mechanism enabling rapid distribution across the environment
S6A Key Cost Drivers
· Number of endpoints receiving updates from affected infrastructure
· Degree of propagation enabled through update workflows
· Speed of remediation relative to KEV urgency
· Maturity of endpoint telemetry and detection capability
· Scope of containment, reimaging, and credential reset operations
· Duration and scale of operational disruption
· Extent of persistence and follow-on attacker activity
· Regulatory, contractual, and governance exposure
S6B Compliance and Risk Context
Compliance Exposure Indicator
CVE-2026-3502 is included in the CISA Known Exploited Vulnerabilities catalog, confirming active exploitation and requiring prioritized remediation. This designation increases regulatory scrutiny and reduces acceptable remediation timelines.
Risk Register Entry
Risk Title
TrueConf Trusted Update Channel Compromise via CVE-2026-3502
Risk Statement
The organization may experience multi-endpoint compromise if malicious payloads are distributed through a trusted update mechanism
Business Impact
Operational disruption, endpoint compromise, credential exposure, and increased incident response cost
Priority
Critical
Annualized Risk Exposure
Annualized risk exposure is elevated in the near term due to confirmed exploitation and the ability to scale compromise through trusted update distribution. Likelihood remains high while vulnerable systems are unpatched and update integrity controls are not validated, with risk amplified by propagation potential across endpoints. Exposure decreases materially after remediation, baseline enforcement, and behavioral detection controls are operationalized.
S7 Risk Drivers
· Confirmed active exploitation through KEV classification
· Trusted update channel abuse bypassing traditional controls
· Reduced visibility during delivery phase of attack
· High propagation potential through internal update distribution
· Dependence on baseline accuracy for detection effectiveness
· Increased governance pressure and remediation urgency
S8 Bottom Line for Executives
This is a supply chain-style exposure where a trusted update mechanism becomes a delivery channel for malicious code. The primary risk is not initial access, but the ability to distribute and execute payloads under trusted conditions. Organizations must treat update infrastructure as a controlled trust boundary and enforce behavioral detection at the point of execution to reduce impact.
S9 Board-Level Takeaway
· Execute immediate patching aligned to KEV urgency with tracked completion status
· Validate and formally attest to the integrity of update distribution mechanisms
· Enforce monitoring of update-context execution and post-update behavior across all affected endpoints
· Require executive-level reporting on remediation progress and residual risk until closure
· Treat this as a supply chain risk requiring governance oversight, not a routine vulnerability
Figure 2
S10 Supply Chain Attack Overview
This event is classified as a supply chain attack because the primary attack vector is abuse of a trusted software update mechanism rather than a traditional external intrusion pathway. The vulnerability enables malicious payload delivery through the update process if the attacker can influence the update delivery path, allowing a legitimate distribution channel to be used for adversary-controlled code delivery.
The defining condition is a loss of reliable trust assurance between update source and endpoint. Instead of introducing foreign binaries through suspicious ingress, the attacker uses the existing update workflow to deliver code that may be accepted as legitimate. This shifts detection from perimeter visibility to endpoint execution, process lineage, and post-update behavior.
S11 Affected Product / Trust Dependency Overview
Affected Product
TrueConf Client for Windows
Affected Versions
Versions prior to 8.5.3
Trust Dependency
The client retrieves update content through its update workflow and executes or installs that content without verifying integrity or authenticity.
Trust Boundary Failure
The absence of integrity validation allows malicious payload substitution when the attacker can influence the update delivery path, extending execution trust beyond the intended vendor-controlled boundary.
Architectural Role
The update mechanism functions as a trusted internal distribution mechanism capable of delivering executable content to multiple endpoints.
Operational Implication
A single compromised or influenced update path can enable multi-endpoint payload distribution, introducing propagation risk not present in traditional single-host vulnerabilities.
S12 Enabling Vulnerability and Exposure Context
Vulnerability Type
Download of Code Without Integrity Check
CWE
CWE-494
Technical Root Cause
The application downloads update code and applies it without verifying integrity or authenticity, allowing substitution of malicious payloads when the attacker can influence the update delivery path.
Supply Chain Impact Mechanism
The vulnerability enables trusted-path code substitution, where malicious payloads are delivered through an approved update mechanism rather than an external or clearly suspicious channel.
Exposure Context
Exposure exists in environments where the attacker can influence the update delivery path, including:
· Compromised or controlled on-premises update servers
· Manipulated update distribution paths
· Insufficiently protected internal update infrastructure
Trust Boundary Impact
The vulnerability removes reliable assurance of update integrity, weakening the trust relationship between software provider, update mechanism, and endpoint.
S13 Exploitability, Patch, and Exposure Management Status
Exploitability
Active exploitation is confirmed through inclusion in the CISA Known Exploited Vulnerabilities catalog.
KEV Status
Present in the KEV catalog with a defined remediation deadline, indicating confirmed real-world exploitation and mandatory prioritization.
Patch Status
Vendor remediation is available in TrueConf Client version 8.5.3 and later supported builds.
Exposure Management Priority
Immediate action is required due to confirmed exploitation and the potential for multi-endpoint impact through trusted update distribution.
Required Actions
· Identify all vulnerable TrueConf client deployments
· Upgrade to patched versions without delay
· Validate integrity of update infrastructure and distribution paths
· Investigate for update-context execution anomalies
· Monitor post-update process behavior and outbound communication
· Track remediation completion against KEV deadlines
S14 Sectors / Countries Affected
Observed Target Sector
Government
Observed Target Region
Southeast Asia
Confirmed Targeting Context
Public reporting indicates targeting of government entities in Southeast Asia through exploitation of the update mechanism.
Potentially Affected Sectors
· Government and public administration
· State-affiliated organizations
· Regulated environments using centralized communication platforms
Global Exposure Consideration
Organizations operating vulnerable TrueConf deployments may be exposed, with increased risk in environments using centralized or on-premises update distribution.
S15 Adversary Capability Profiling
Capability Level
Moderate to High
Capability Characterization
The adversary demonstrates the ability to identify and operationalize a vulnerability in a trusted update mechanism and leverage that mechanism for payload delivery.
Tradecraft Strength
The defining capability is trust exploitation through update-channel abuse, allowing operation within legitimate system workflows rather than relying on overt intrusion techniques.
Operational Maturity
The activity reflects understanding of enterprise update architectures, enabling controlled payload delivery and reduced likelihood of early detection.
Scalability Assessment
High, as the update mechanism enables distribution of payloads across multiple endpoints from a single point of influence.
Primary Operational Objectives
· Expand initial access through trusted distribution
· Establish command-and-control
· Maintain persistence
· Conduct targeted intelligence collection
S16 Targeting Probability Assessment
Highest Probability Targets
· Government organizations
· Public sector entities using centralized collaboration infrastructure
· Environments where the attacker can influence the update delivery path
Rationale
The attack is most effective in environments where a centralized update mechanism can distribute code across multiple endpoints, enabling scalable impact from a single trust failure.
Moderate Probability Targets
· Large enterprises with internal software distribution systems
· Regulated industries with complex patch management workflows
Rationale
These environments provide sufficient scale and may have longer exposure windows due to operational complexity.
Lower Probability Targets
· Small organizations with limited deployment scope
· Environments with strong update validation and monitoring
Rationale
Reduced scale and stronger integrity controls limit propagation potential and overall impact.
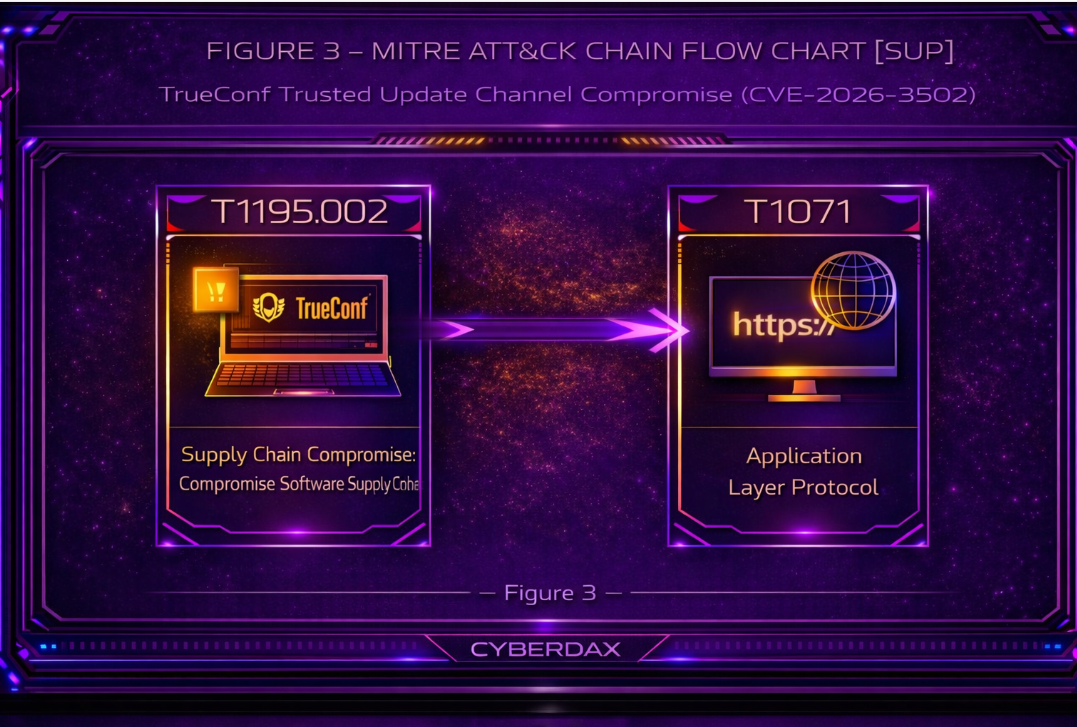
S17 MITRE ATT&CK Chain Flow Mapping
Stage 1 — Supply Chain Entry
Technique
T1195.002 – Supply Chain Compromise: Compromise Software Supply Chain
Application in This Attack
The attacker gains the ability to influence the update delivery path, enabling insertion of a malicious payload into the trusted update process.
Stage 2 — Payload Delivery via Trusted Channel
Technique
T1195 – Supply Chain Compromise
Application in This Attack
The modified payload is delivered through the legitimate update mechanism as part of the normal update workflow, rather than through an external intrusion path.
Stage 3 — Execution in Update Context
Technique
T1195 – Supply Chain Compromise
Application in This Attack
The substituted payload executes within the context of the update process, appearing consistent with legitimate update activity.
Stage 4 — Potential Expansion via Trusted Distribution
Technique
T1195 – Supply Chain Compromise
Application in This Attack
If the attacker maintains influence over the update delivery path, the mechanism may be reused to distribute modified payloads to additional endpoints.
S18 Attack Path Narrative (Signal-Aligned Execution Flow)
The attack sequence begins when the adversary gains the ability to influence the update delivery path used by the TrueConf client. This influence allows the insertion of a modified payload into the update workflow. Public reporting indicates that exploitation has been associated with environments where update distribution can be influenced, particularly in on-premises deployment models.
Once the delivery path is influenced, the adversary substitutes a legitimate update payload with a tampered version. Because the client does not validate update integrity, the modified payload is delivered through the expected update mechanism and received by endpoints without triggering traditional delivery-stage controls.
Execution occurs as part of the update process. The substituted payload runs within the context of the updater or associated process, aligning with normal update behavior. This reduces reliance on user interaction and limits visibility at the point of execution unless process lineage or behavioral monitoring is in place.
Following execution, the attacker gains a foothold on the endpoint. Subsequent activity is dependent on attacker objectives and target environment. Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment.
If the adversary maintains the ability to influence the update delivery path, the same process can be repeated across additional endpoints. This enables expansion through the trusted update workflow, allowing multiple systems to receive the modified payload without requiring separate compromise actions.
This sequence reflects a progression from trusted update delivery → execution within update context → potential expansion through repeated update distribution, aligning with the points where detection becomes feasible through endpoint execution monitoring and network correlation.
S19 Attack Chain Risk Amplification Summary
· Use of a trusted update mechanism reduces effectiveness of perimeter-based detection and shifts visibility to execution-stage behavior
· Lack of update integrity validation allows payload substitution without triggering delivery-stage controls
· Execution within update context reduces detection reliability without process lineage validation
· Centralized update distribution introduces risk of multi-endpoint impact from a single trust failure
· Reuse of the update workflow enables expansion without repeated intrusion activity
· Delayed detection increases likelihood of sustained access prior to response
Figure 3
S20 Tactics, Techniques, and Procedures
T1195.002 – Supply Chain Compromise: Compromise Software Supply Chain
· The attacker influences the update delivery path to insert a malicious payload into the update process, enabling execution through a legitimate software distribution mechanism
T1071 – Application Layer Protocol
· Post-execution communication may occur using standard application-layer protocols, allowing interaction with external infrastructure while blending with normal network activity
Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment
S20A Adversary Tradecraft Summary
The adversary’s tradecraft in this case is centered on trust exploitation within a software update mechanism. Rather than introducing malicious code through external delivery or relying on user interaction, the attacker leverages an existing trusted workflow to deliver and execute payloads.
The defining characteristic is execution under legitimate update conditions. This reduces dependence on user-driven execution and minimizes the need to bypass perimeter defenses, as the payload is delivered through an approved operational process.
The approach introduces potential for scalable impact in environments where update distribution is centralized. The extent of that impact depends on the attacker’s ability to maintain influence over the update delivery path.
Post-execution activity is not fully detailed in currently available reporting. However, typical follow-on behaviors such as persistence or external communication may occur depending on attacker objectives and target environment.
Overall, the tradecraft reflects a focus on trusted-channel abuse and execution within expected system behavior, rather than reliance on traditional intrusion or delivery techniques.
S21 Detection Strategy Overview
The detection strategy for CVE-2026-3502 must focus on identifying abuse of trusted internal software distribution, where malicious payloads are delivered through legitimate update mechanisms. In this scenario, the TrueConf server functions as a trusted update authority, and compromised or attacker-controlled update content is propagated directly to client endpoints, bypassing traditional perimeter defenses and reducing visibility at standard ingress control points.
Detection must treat internal update infrastructure as a potential threat distribution node, shifting emphasis from external threat detection to east-west propagation and endpoint execution control. Because the update mechanism is expected and trusted, the initial delivery stage may generate no inherently suspicious indicators, making endpoint execution the earliest reliable detection point.
Detection priorities must be enforced as follows:
· Endpoint telemetry serves as the authoritative detection layer, providing visibility into process execution, file origin, parent-child relationships, and behavioral deviation following update activity
· Internal network telemetry provides critical supporting visibility into abnormal server-to-client distribution patterns, including update volume, timing irregularities, and lateral propagation characteristics
· DNS and web proxy telemetry provide downstream confirmation of compromise through command-and-control communication and external infrastructure contact
Detection must focus on the following enforced behavioral pivots:
· Execution of binaries originating from TrueConf update paths that deviate from expected publisher, hash, execution behavior, or runtime characteristics
· Process lineage where update-related processes spawn unexpected child processes, initiate scripting engines, or establish outbound network connections
· Internal distribution anomalies where a single server delivers update payloads to multiple endpoints outside normal operational cadence or scope
· Post-update activity resulting in persistence, credential access, lateral movement, or external communication inconsistent with standard application behavior
This attack model introduces a trusted execution inversion, where malicious activity is delivered through approved and expected processes. As a result, traditional controls such as application allowlisting, signed binary trust, and update-channel exemptions may fail silently. Detection must therefore validate behavior and execution context, not just binary legitimacy.
Variant resistance must be explicitly enforced within detection logic:
· Payloads may be unsigned, legitimately signed, or signed using compromised certificates, requiring behavior-based validation rather than signature trust
· Execution may occur silently within standard update workflows, eliminating user-driven indicators
· Malicious actions may occur post-update using legitimate system utilities, requiring monitoring of downstream behavior rather than initial execution alone
· Update delivery may be staged, throttled, or scoped to evade volumetric detection, requiring correlation across endpoints and time windows
Effective detection depends on identifying behavioral deviation within trusted execution contexts, correlating endpoint execution with internal distribution activity, and treating update-driven execution as a high-risk event requiring continuous validation.
S22 Primary Detection Signals
Primary detection signals for CVE-2026-3502 must identify abuse of the TrueConf update trust relationship, where a trusted internal server distributes malicious payloads to endpoints. Detection must differentiate between expected update behavior and malicious update-driven execution, requiring enforcement of baseline-aware and context-driven signals.
Endpoint Telemetry Signals (Authoritative Detection Layer)
High-confidence signals must focus on execution behavior originating from update activity:
· Execution of binaries immediately following file writes within TrueConf update paths where the binary deviates from expected publisher, hash baseline, or known application behavior
· TrueConf-related processes spawning child processes not consistent with standard update behavior, including command shells, scripting engines, or unknown executables
· Execution of newly introduced binaries with no prior prevalence in the environment, specifically when temporally linked to update activity
· Rapid file write → execution sequences occurring within update directories, especially when followed by persistence or network activity
· Post-update execution resulting in registry modification, scheduled task creation, service installation, or credential access activity
Expected behavior constraint:
· TrueConf updates should not result in arbitrary child process spawning, scripting engine execution, or immediate persistence actions
Internal Network Telemetry Signals (Critical Supporting Layer)
Detection must identify abnormal behavior from the TrueConf server as a distribution source:
· Update distribution activity initiated outside defined administrative deployment windows or without corresponding administrative action
· Server distributing update payloads to multiple endpoints with inconsistent payload characteristics, size variation, or timing irregularities
· Sudden increase in server-to-endpoint transfer volume or frequency inconsistent with historical update patterns
· Distribution patterns indicating staged or lateral propagation across endpoints rather than centralized update deployment
· Internal server behavior deviating from baseline, including unexpected update initiation or irregular endpoint targeting
Expected behavior constraint:
· TrueConf update distribution should follow predictable timing, scope, and payload consistency across endpoints
DNS and Web Proxy Signals (Post-Execution Confirmation Layer)
These signals confirm compromise following update execution:
· Outbound connections initiated by processes executed from update paths to domains or IPs not associated with known TrueConf infrastructure
· DNS queries for newly observed, low-prevalence, or algorithmically generated domains immediately following update-related execution
· Beaconing behavior from update-delivered processes, including periodic outbound connections or encrypted sessions
· TLS sessions initiated by newly executed binaries with no historical baseline or expected communication pattern
Expected behavior constraint:
· TrueConf update processes should not initiate independent external communication beyond known service endpoints
Cross-Pillar Correlation Signals (High Confidence Detection)
High-confidence detection requires enforced correlation across telemetry sources:
· Endpoint execution of update-delivered binaries combined with abnormal internal server-to-client distribution within a defined time window
· Post-update process execution followed by outbound network communication within a short temporal sequence
· Multiple endpoints exhibiting similar execution behavior tied to update activity within a bounded time interval
· Internal distribution anomalies correlated with endpoint behavioral deviation and external communication signals
Operational enforcement:
· Single-signal alerts are insufficient; detection must require multi-signal correlation to reduce false positives
Variant-Resistant Detection Signals (Enforced)
Detection must remain effective across attacker adaptations:
· Detection must not rely on binary signature or signing status; behavior and execution context must be primary indicators
· Monitoring must account for delayed execution where payloads are delivered during update but executed later
· Detection must include downstream behavior such as use of legitimate system utilities following update execution
· Detection must account for low-and-slow distribution patterns by correlating activity across time and endpoints rather than relying on burst detection
SOC Prioritization Guidance
· High priority: Endpoint execution anomalies tied to update activity combined with network communication
· Medium priority: Internal distribution anomalies without confirmed execution
· Hunt priority: Low-prevalence binaries and delayed execution patterns associated with update workflows
Detection signals must be treated as context-dependent indicators within a trusted execution model. Reliable detection requires enforcing baseline expectations, validating update-driven execution behavior, and correlating endpoint and network activity to identify compromise early in the attack chain.
S23 Telemetry Requirements
Effective detection of CVE-2026-3502 requires high-fidelity, correlated telemetry across endpoint, internal network, DNS, and critically, the TrueConf server itself, because the attack model is driven by trusted internal distribution and downstream execution. Telemetry must enable validation of both update initiation and update execution behavior, not just post-compromise activity.
Telemetry must support the detection signals defined in S22 and must be treated as mandatory detection infrastructure. Absence of required telemetry creates direct detection blind spots, not partial degradation.
Endpoint Telemetry Requirements (Authoritative Detection Layer)
Endpoint visibility is the primary detection surface and must provide execution-level truth.
Required telemetry:
· Process creation events with full parent-child lineage, including command-line arguments and execution context
· File creation and modification events within TrueConf installation paths, update directories, and temporary staging locations
· File hash, reputation, and code-signing metadata for all executed binaries, including publisher validation
· Registry modification telemetry covering persistence mechanisms such as autoruns, services, and scheduled tasks
· Service creation and scheduled task execution events
· User and security context associated with execution
Critical enforcement requirements:
· Ability to correlate file write events with subsequent execution events on the same host within a defined time window
· Persistent process lineage visibility sufficient to trace execution back to update-related processes
· Detection of execution originating from update paths or update-triggered processes
Failure condition:
· Without endpoint lineage and execution telemetry, malicious update payloads will appear as legitimate application activity and evade detection entirely
TrueConf Server Telemetry Requirements (Critical Distribution Control Layer)
The TrueConf server must be treated as a potential threat distribution node, and telemetry must validate update initiation and payload staging behavior.
Required telemetry:
· Process creation and service activity on the TrueConf server, including update initiation processes
· File creation, modification, and staging activity within update distribution directories
· Administrative actions associated with update deployment or configuration changes
· Authentication and access logs for administrative interfaces or update-related services
· Network connection logs showing server-initiated communication to client endpoints
Critical enforcement requirements:
· Ability to correlate update initiation events with downstream endpoint activity
· Visibility into changes to update payloads prior to distribution
· Detection of update initiation outside expected administrative workflows or schedules
Failure condition:
· Without server-side telemetry, malicious update distribution cannot be attributed or detected at the source, and investigation will be limited to endpoint symptoms
Internal Network Telemetry Requirements (Propagation Visibility Layer)
Internal network visibility is required to detect abnormal distribution behavior across endpoints.
Required telemetry:
· East-west network flow logs capturing communication between the TrueConf server and client endpoints
· Session metadata including source, destination, timing, and transfer volume
· Protocol identification and transfer characteristics for update-related communication
· Connection frequency and distribution patterns across endpoints
Critical enforcement requirements:
· Ability to baseline normal update distribution patterns, including timing, scope, and frequency
· Detection of abnormal fan-out behavior where multiple endpoints receive update payloads outside expected cadence
· Correlation of server-initiated connections with endpoint execution events
Failure condition:
· Without internal network telemetry, large-scale propagation via trusted update channels may not be detected until post-exploitation activity occurs
DNS and Web Proxy Telemetry Requirements (Post-Execution Validation Layer)
DNS and web telemetry confirm compromise following execution of malicious payloads.
Required telemetry:
· DNS query logs with timestamped resolution data
· Outbound connection logs capturing destination domains, IP addresses, and ports
· TLS session metadata where available, including certificate attributes and session patterns
Critical enforcement requirements:
· Ability to correlate outbound network activity with originating process on the endpoint
· Detection of newly observed or low-prevalence domains contacted after update-related execution
· Identification of repeated outbound communication patterns consistent with beaconing
Failure condition:
· Without DNS and outbound telemetry, post-compromise communication may go undetected, reducing visibility into attacker control and persistence
Cross-Pillar Correlation Requirements (Mandatory Enforcement Layer)
Detection depends on enforced correlation across telemetry sources.
Required capabilities:
· Correlation of endpoint execution events with TrueConf server distribution activity within defined temporal windows
· Mapping of process execution to subsequent outbound network communication
· Identification of similar execution patterns across multiple endpoints within a shared timeframe
· Aggregation of low-prevalence indicators across hosts to identify distributed compromise
Critical enforcement requirements:
· Centralized log aggregation across endpoint, server, network, and DNS telemetry sources
· Time synchronization across all telemetry systems to ensure accurate event correlation
· Entity normalization allowing mapping of host, process, and network relationships across data sources
Failure condition:
· Without cross-pillar correlation capability, signals will remain isolated and fail to produce high-confidence detection
Minimum Detection Telemetry Baseline
The following telemetry is required to achieve minimum viable detection:
· Endpoint EDR with process creation, file activity, and persistence visibility
· Server-side logging for update initiation and file staging activity
· Internal network flow logs capturing server-to-endpoint communication
· DNS logging for outbound resolution activity
· Centralized logging platform capable of cross-source correlation
Enhanced Detection Telemetry (Recommended for High-Fidelity Detection)
The following telemetry significantly improves detection accuracy and response speed:
· Full command-line and module load visibility on endpoints
· File integrity monitoring on TrueConf server update directories
· Administrative audit logging for update configuration and deployment actions
· TLS inspection or enriched session metadata for outbound traffic
· Behavioral baselining systems to model normal update distribution and execution patterns
Telemetry Gaps and Limitations
Detection capability is reduced under the following conditions:
· Incomplete endpoint coverage or lack of process lineage visibility
· Absence of TrueConf server telemetry for update initiation and staging
· Limited visibility into internal east-west network traffic
· Encrypted traffic without sufficient metadata for analysis
· Short retention periods preventing multi-endpoint correlation
Telemetry for this threat must be treated as continuous validation of trusted execution and distribution behavior. Detection success depends on enforcing visibility at the endpoint, validating update activity at the server, and correlating propagation patterns across the environment to identify compromise early and accurately.
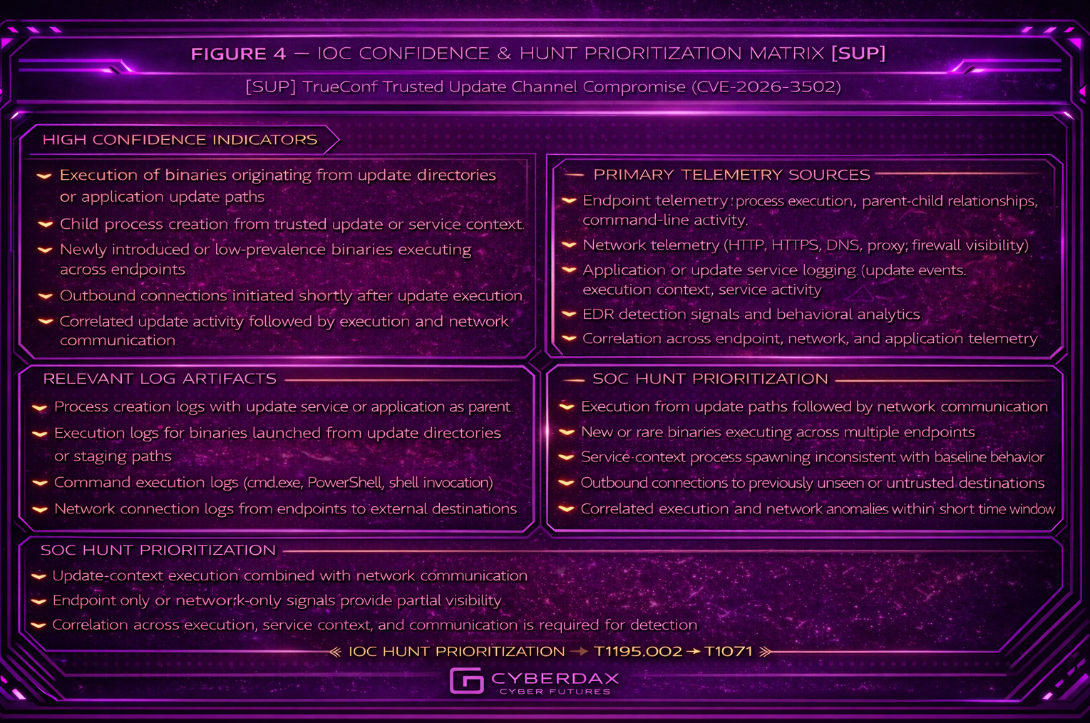
Figure 4
S24 Detection Opportunities and Gaps
Detection of CVE-2026-3502 presents a high-confidence opportunity at the endpoint execution layer, but introduces systemic detection gaps at the initial delivery stage due to abuse of a trusted update channel. Detection capability is therefore asymmetric: strong visibility exists post-execution, while pre-execution detection is inherently limited without additional control mechanisms.
Detection Opportunities (High-Confidence Coverage Areas)
Endpoint Execution Validation
· High-confidence detection is achievable at the point of binary execution following update delivery
· Behavioral deviation from expected TrueConf update activity provides strong detection signals
· Process lineage, execution context, and post-execution behavior enable reliable identification of malicious activity
Detection timing:
· Detection typically occurs at or shortly after execution, not at delivery
Post-Execution Activity Monitoring
· Persistence mechanisms, credential access, and lateral movement following update execution are detectable with standard endpoint telemetry
· Outbound communication to command-and-control infrastructure provides confirmatory signals
· Correlation of execution and network activity significantly increases detection confidence
Cross-Endpoint Correlation
· Fan-out distribution from the TrueConf server creates detectable patterns across multiple endpoints
· Similar execution behavior across hosts within a defined time window enables high-confidence detection
· Aggregation of low-prevalence binaries or behaviors across systems strengthens detection accuracy
Internal Distribution Anomaly Detection
· Abnormal update distribution patterns from the TrueConf server can be detected through network telemetry
· Deviations in update timing, scope, and frequency provide early indicators of compromise
· Server-to-endpoint propagation behavior can be identified even when payload content is not visible
Detection Opportunities (Moderate Confidence / Conditional)
Server-Side Anomaly Detection
· Detection of abnormal update initiation or payload staging on the TrueConf server is possible when sufficient logging is enabled
· Administrative activity outside expected workflows may indicate compromise
· Effectiveness is conditional on audit logging maturity and visibility into update processes
Baseline Deviation Analysis
· Behavioral baselining of update patterns can identify anomalies in distribution and execution
· Requires historical data, tuning, and environment stability
· Effectiveness is conditional and may degrade in dynamic environments
Detection Gaps (Inherent Limitations)
Pre-Execution Detection Gap
· Malicious payload delivery through the trusted update channel is indistinguishable from legitimate updates prior to execution
· Detection at delivery stage is not reliably achievable without integrity validation or content verification controls
· This creates a guaranteed blind spot before endpoint execution occurs
Attacker advantage:
· An attacker can deliver payloads that fully bypass detection until execution
Trusted Channel Blind Spot
· Internal update traffic is often exempt from inspection, reducing visibility into payload content
· Encrypted or internal-only communication prevents deep inspection
· Trust-based controls allow malicious updates to pass without scrutiny
Attacker advantage:
· Malicious payloads can traverse the environment using approved and expected communication paths
Signature and Reputation Limitations
· Signed or legitimate-looking payloads may bypass signature-based detection
· Low-prevalence or custom payloads evade reputation systems
· Static detection methods are ineffective in this attack model
Detection Gaps (Operational / Environmental)
TrueConf Server Compromise Dependency
· If the TrueConf server is compromised, it becomes a trusted distribution point for malicious payloads
· Detection is then dependent entirely on downstream endpoint behavior and correlation
· No reliable upstream detection exists without server-side integrity controls
Incomplete Endpoint Coverage
· Systems without EDR or with limited telemetry will not provide sufficient visibility into execution behavior
· Gaps in endpoint coverage directly translate to undetected compromise
Limited Internal Network Visibility
· Absence of east-west monitoring prevents detection of abnormal update distribution patterns
· Propagation activity may remain invisible until post-execution behavior occurs
Correlation Limitations
· Without centralized logging and time-synchronized telemetry, signals remain isolated and low-confidence
· Multi-endpoint compromise may not be recognized as a coordinated event
Coverage Boundary Summary
· Detected Behaviors:
o Endpoint execution anomalies following update delivery
o Post-execution persistence, lateral movement, and command-and-control activity
o Cross-endpoint propagation patterns
o Internal distribution anomalies when network telemetry is available
· Partially Detected Behaviors:
o Server-side update initiation and staging activity (dependent on logging maturity and audit coverage)
o Baseline deviations in update behavior (dependent on historical data and tuning)
· Not Covered Behaviors:
o Malicious payload delivery at the moment of update distribution prior to execution
o Content-level validation of update payloads without integrity enforcement mechanisms
Enforcement implication:
· Not Covered behaviors require preventive controls, not detection
· Partially Detected behaviors require telemetry and logging maturity improvements
Detection for this threat is fundamentally execution-anchored and correlation-dependent. Reliable detection occurs only after trusted update behavior transitions into observable malicious execution, making strong endpoint telemetry, internal visibility, and enforced correlation essential for early identification.
S25 Ultra-Tuned Detection Engineering Rules
Suricata
Rule Name
Abnormal TrueConf Internal Update Distribution Burst
Purpose
Detect unusually rapid internal distribution activity from an approved TrueConf server to internal clients, indicating possible trusted-server propagation inconsistent with expected update cadence or rollout scope.
SOC Usage Mode
Correlation-first
Standalone Alerting Allowed
No. This rule must not be used alone for incident declaration. It is a supporting detection that requires maintenance-window and operational-context validation.
Minimum Deployment Requirement
· Reliable east-west network visibility
· Maintained inventory of approved TrueConf server IP addresses
· Network segmentation or client scope awareness
· Environment-specific threshold tuning
· Time-synchronized event collection
Enforcement Method
· Restrict source to approved TrueConf server IP inventory
· Restrict destination to internal client address space
· Restrict to expected update transport ports where known
· Trigger only when one source generates an unusually high volume of matching internal update-session activity within a bounded window
· Require downstream correlation with maintenance-window context before escalation
Implementation Constraint Notes
· This rule detects distribution burst behavior, not true distinct-destination counting
· Distinct-host fan-out validation should be performed in the SIEM, flow platform, or enrichment layer if required
· This rule detects distribution anomaly, not malicious execution
· Large or centrally managed deployments may require per-subnet or per-server threshold tuning
· If normal bulk rollouts are frequent and highly variable, confidence is reduced
Tuning Explanation
· Initial thresholds must be localized to endpoint count and rollout design
· Narrow by known TrueConf transport ports or update service pathing where possible
· Use SIEM-side suppression for approved maintenance windows if native network timing controls are insufficient
· In segmented environments, tune by zone rather than globally
· Validate whether port 4307 is truly in scope for the target environment before enabling it
Telemetry Dependency
· Internal session visibility
· Accurate TrueConf server inventory
· Preferably flow enrichment that supports host-count validation
· Operational maintenance-window context outside the rule
SOC Usage Mode Detail
· Standalone alerting is not allowed
· Use as a supporting signal for SOC triage and cross-pillar correlation
Variant Analysis
· Low-and-slow rollouts may evade burst thresholds
· Attackers operating during approved maintenance windows reduce signal value
· Encrypted traffic does not defeat this rule because it is pattern-based
· If attackers limit scope to a very small endpoint set, signal strength drops
Rule Regret Check
Deployment caution
Threshold tuning is mandatory. Poor tuning will create noise during legitimate large-scale rollouts.
Confidence caution
This rule does not identify payload type or prove malicious update delivery.
Coverage value
Strongest credible Suricata signal for identifying suspicious internal propagation from the trusted update server.
Production Ready
Conditionally production-ready — only after threshold localization, server scoping, port validation, and maintenance-window validation
SIEM/system-ready code
alert tcp $TRUECONF_SERVERS any -> $HOME_NET [80,443,4307] (
msg:"CYBERDAX SURICATA TrueConf abnormal internal update distribution burst";
flow:to_client,established;
detection_filter:track by_src,count 40,seconds 300;
classtype:policy-violation;
sid:250350201;
rev:4;
)
Rule Name
Stateful TrueConf Post-Delivery External Egress Correlation
Purpose
Detect external outbound communication from an internal host shortly after that host receives traffic from an approved TrueConf server, providing a bounded network-only approximation of delivery followed by suspicious egress.
SOC Usage Mode
Correlation-first
Standalone Alerting Allowed
No. This rule must not stand alone for compromise declaration and must be treated as a supporting correlation signal.
Minimum Deployment Requirement
· East-west internal network visibility
· Outbound internet visibility
· Approved TrueConf server inventory
· Validated xbits support or equivalent Suricata state tracking
· Maintained allowlist of known-good external destinations associated with normal TrueConf operations
· Preferably SIEM or enrichment support for destination allowlist validation
Enforcement Method
· First create raw-event host state for internal clients recently contacted by approved TrueConf servers
· Within a bounded expiration window, alert when those same hosts initiate repeated outbound traffic
· Treat destination allowlist filtering as a required enrichment or local adaptation step before escalation
· Restrict logic to raw event state only
· Require endpoint or SIEM corroboration before escalation
Implementation Constraint Notes
· This is a paired stateful Suricata construct consisting of one marker rule and one alerting rule
· It counts as one logical detection pattern because the noalert marker exists only to support bounded raw-event state
· The base Suricata alert below does not natively enforce destination allowlisting in code
· Known-good destination filtering must be implemented through local variables, pass rules, SIEM enrichment, or downstream suppression
· If xbits behavior is unstable or unsupported in the deployed environment, move this logic to Splunk, Elastic, or QRadar rather than forcing weak Suricata correlation
· Destination allowlists must account for legitimate conferencing, telemetry, relay, and service infrastructure
Tuning Explanation
· Expiration windows should reflect realistic post-delivery execution timing, typically 5 to 30 minutes
· Tighten with destination scoping and frequency thresholds to reduce noise
· If legitimate client egress after TrueConf activity is common, downgrade confidence and require stronger SIEM-side enrichment
· Where supported, implement $KNOWN_GOOD_TRUECONF_EGRESS style exclusions through local variable sets or pass rules
Telemetry Dependency
· Internal and outbound session visibility
· Approved TrueConf server inventory
· External destination allowlist
· Stable host-state tracking support
· Time synchronization across network sensors
SOC Usage Mode Detail
· Standalone alerting is not allowed
· Use as a supporting correlation signal that queues endpoint review
Variant Analysis
· Delayed execution outside the state window can evade this logic
· Attackers using already-approved external destinations reduce signal quality
· Encrypted traffic does not defeat destination-and-timing correlation
· Low-frequency egress may require SIEM-side extended correlation windows
Rule Regret Check
Deployment caution
Requires validation of xbits behavior and careful destination allowlisting.
Confidence caution
Detects suspicious sequence timing only. It does not prove update abuse or payload execution.
Coverage value
Strongest Suricata-accessible approximation of delivery followed by suspicious external communication without violating anti-loop controls.
Production Ready
Conditionally production-ready — only where xbits/state tracking, destination allowlisting, and window tuning are validated
SIEM/system-ready code
alert ip $TRUECONF_SERVERS any -> $HOME_NET any (
msg:"CYBERDAX SURICATA marker TrueConf client recently contacted by update server";
flow:to_client,established;
xbits:set,trueconf_recent_server_contact,track ip_dst,expire 1800;
noalert;
sid:250350203;
rev:4;
)
alert ip $HOME_NET any -> $EXTERNAL_NET any (
msg:"CYBERDAX SURICATA TrueConf-correlated suspicious external egress";
xbits:isset,trueconf_recent_server_contact,track ip_src;
detection_filter:track by_src,count 3,seconds 300;
classtype:trojan-activity;
sid:250350204;
rev:4;
)
Suricata Limitation Statement
Suricata provides two strong, credible supporting detections for this threat and does not provide a third equally strong default rule without relying on application-layer visibility that may not exist in many deployments. In alignment with CyberDax S25 anti-loop and no-filler standards, this subsection preserves only the strongest network-observable detections and does not pad the system with weaker content. This corrects the prior drift where the object-delivery concept appeared in the main rule set despite being explicitly environment-dependent.
Suricata credibly supports:
· Abnormal internal distribution burst detection
· Bounded network-only post-delivery egress correlation
Suricata does not credibly provide a third equally strong default rule for suspicious update-object delivery unless the environment has validated HTTP inspection, reverse-proxy artifact visibility, or SSL interception aligned to the TrueConf update path.
Additional High-Value Detection Candidate
Rule Name
Suspicious Update Object Delivery from TrueConf Server
Purpose
Detect delivery of executable or binary update objects from an approved TrueConf server to internal clients when application-layer visibility exists and the delivery deviates from approved update artifact patterns.
SOC Usage Mode
Alert-capable supporting detection
Standalone Alerting Allowed
No — must be corroborated with endpoint or SIEM context
Minimum Deployment Requirement
· HTTP inspection, reverse proxy logging, or SSL interception enabled
· Approved TrueConf server inventory
· Maintained allowlist of approved update artifact paths or naming conventions
· Validated application-layer visibility for update traffic
Enforcement Method
· Restrict source to approved TrueConf servers
· Restrict destination to internal clients
· Trigger only on executable or binary object delivery patterns
· Exclude known approved update artifact routes and naming patterns
· Require correlation with endpoint execution before escalation
Implementation Constraint Notes
· Not deployable in opaque TLS-only environments
· Must be scoped to known update paths or services
· Must not be used without artifact allowlisting
· Should be disabled if visibility is inconsistent
Tuning Explanation
· Replace placeholder URI filters with real approved update paths
· Maintain allowlist of update directories, file naming conventions, and artifact delivery routes
· Narrow rule to specific ports and known update endpoints
· Validate against real update traffic before enabling alerting
Telemetry Dependency
· HTTP or proxy-level object visibility
· Server inventory accuracy
· Artifact allowlist accuracy
· Preferably file-type or MIME metadata
SOC Usage Mode Detail
· Standalone alerting is not allowed
· Must be treated as a supporting signal that requires endpoint validation and process execution correlation
Variant Analysis
· Payload renaming may evade filename-based detection
· TLS-only delivery eliminates visibility unless intercepted
· Non-PE payload staging may evade simple binary checks
· Attackers using approved naming patterns reduce detection strength
Rule Regret Check
Deployment caution
Requires strong artifact allowlisting and validated visibility.
Confidence caution
Detects suspicious delivery characteristics only. Does not confirm execution.
Coverage value
High-value detection where update object visibility exists; otherwise not applicable.
Production Ready
Conditionally production-ready — only where application-layer visibility and artifact baselines are validated
SIEM/system-ready code
alert http $TRUECONF_SERVERS any -> $HOME_NET any (
msg:"CYBERDAX SURICATA TrueConf suspicious update object delivery";
flow:to_client,established;
file.data;
content:"MZ"; depth:2;
http.uri;
pcre:!"/approved_update_path1|approved_update_path2/";
classtype:policy-violation;
sid:250350205;
rev:2;
)
Engineering Note — Required Actions
To deploy this rule safely and effectively, engineers must:
· Identify and maintain approved TrueConf update artifact paths
· Validate whether HTTP object visibility or proxy logging is present
· Confirm whether TLS interception or reverse proxy inspection is enabled
· Build and maintain an artifact allowlist including update directories, file naming conventions, and delivery endpoints
· Test the rule against known-good update traffic and staged update rollouts
· Tune exclusions to prevent false positives during legitimate updates
Coverage remains conditional until these steps are completed.
Engineering Note — Suricata
Suricata remains a supporting network detection layer for this threat, not the authoritative platform for proving compromise.
Required validation actions before deployment:
· Confirm approved TrueConf server inventory
· Localize distribution-burst thresholds to actual rollout scale
· Maintain approved external destination allowlists
· Validate xbits stability in the deployed Suricata version
· Confirm east-west visibility is sufficient for server-to-client tracking
· Validate transport ports and any local TrueConf-specific service scoping
Coverage remains conditional where:
· Update traffic is fully opaque
· Rollout cadence is highly variable
· Client egress is broad and weakly controlled
· East-west visibility is incomplete
SentinelOne
Rule Name
TrueConf Update Context Execution Integrity Deviation
Purpose
Detect execution from approved TrueConf update or staging context where the executable violates expected execution integrity based on signer, prevalence, parent lineage, or writable-path conditions.
SOC Usage Mode
Alert-capable supporting detection
Standalone Alerting Allowed
Yes — only after baseline, allowlisting, and updater-lineage validation are complete
Minimum Deployment Requirement
· Process creation telemetry with lineage
· File path visibility
· Signer metadata where available
· File prevalence or reputation context where available
· Defined TrueConf install, update, cache, and staging paths
· Defined updater parent process inventory
Minimum Deployment Requirement
To safely enable standalone alerting, the environment must have:
· Approved TrueConf update and staging paths localized
· Approved updater parents localized
· Writable and temp-adjacent path definitions localized
· Approved signer baseline localized
· Known-good update binaries excluded
Enforcement Method
· Scope execution to:
o Approved TrueConf update paths
o Approved staging or cache paths
o Processes launched by approved updater parents
Trigger only when at least one strong integrity-deviation condition is present and no approved workflow suppression applies:
o Signer not in approved TrueConf signer set
o Binary is low-prevalence, previously unseen, or first-seen in the environment
o Execution originates from writable or temp-adjacent path where standard update execution should not occur
o Parent process not in approved TrueConf updater lineage
Raise priority when two or more integrity-deviation conditions are present simultaneously
Implementation Constraint Notes
· This is not a simple path rule; execution context plus integrity deviation is required
· Writable-path logic must reflect the real endpoint layout and installer behavior in the tenant
· Parent-chain validation must be based on documented TrueConf updater behavior, not inferred from prior detections
· If signer data is incomplete, prevalence and parent-lineage conditions must carry more weight
· If path baselines are immature, deploy initially in triage mode rather than direct alerting
Tuning Explanation
· Maintain external allowlists for:
o Approved updater binaries
o Approved signer set
o Approved updater parent chain
o Known-good execution paths
· Elevate severity when:
o Binary is unseen or low-prevalence
o Execution occurs from writable or temp-adjacent path
o Parent chain is inconsistent with standard TrueConf update behavior
· Lower confidence when only one weak deviation condition exists and signer or prevalence are unavailable
· Suppress approved installer, packaging, and maintenance workflows explicitly
Telemetry Dependency
· Process creation
· Parent process metadata
· Executable path
· Signer or publisher metadata where available
· Prevalence or reputation context where available
SOC Usage Mode Detail
· Standalone alerting is allowed only when baseline maturity is validated
· Highest-confidence use is when two or more integrity-deviation conditions are present
· Single-condition matches should be downgraded or suppressed unless they occur during suspicious update timing
Variant Analysis
· Payload renaming does not defeat the rule because logic is not filename-dependent
· Signed malicious binaries still surface through parent-lineage, writable-path, or prevalence deviation
· Delayed execution still triggers if execution remains in update-context lineage with integrity deviation
· Minor path variation remains covered when execution stays within the approved TrueConf update-context model
Rule Regret Check
Deployment caution
High noise is likely if update paths, writable paths, and updater parents are not tightly localized.
Confidence caution
Detects execution integrity deviation in trusted update context, not full compromise by itself.
Coverage value
Primary SentinelOne rule for catching abuse of trusted update execution before or during follow-on activity.
Production Ready
Yes — with strict baseline enforcement, updater-lineage validation, and allowlisting
Portable SentinelOne detection logic model
FROM ProcessEvents
WHERE EventType = "Process Creation"
AND (
ProcessImagePath IN TRUECONF_UPDATE_PATHS
OR ProcessImagePath IN TRUECONF_STAGING_PATHS
OR ParentProcessImagePath IN TRUECONF_UPDATE_PATHS
OR ParentProcessName IN APPROVED_TRUECONF_UPDATER_PARENTS
)
AND ProcessName NOT IN APPROVED_TRUECONF_UPDATE_BINARIES
AND (
Signer NOT IN APPROVED_TRUECONF_SIGNERS
OR FilePrevalence IN ("LOW","UNKNOWN","FIRST_SEEN")
OR ProcessImagePath IN WRITABLE_OR_TEMP_ADJACENT_PATHS
OR ParentProcessName NOT IN APPROVED_TRUECONF_UPDATER_PARENTS
)
AND NOT CommandLine MATCHES_ANY APPROVED_TRUECONF_MAINTENANCE_WORKFLOWS
Rule Name
TrueConf Updater Parent-Child Execution Abuse
Purpose
Detect TrueConf updater or application processes spawning unexpected child processes inconsistent with normal update behavior.
SOC Usage Mode
Alert-capable supporting detection
Standalone Alerting Allowed
Yes — high confidence after suppression and parent-lineage tuning
Minimum Deployment Requirement
· Full parent-child lineage
· Command-line visibility
· Approved updater parent inventory
· Approved admin and maintenance workflow allowlist
· Ability to identify suspicious child-process classes
Enforcement Method
· Scope parent process to approved TrueConf updater or application lineage
· Trigger when child process is:
o Shell, scripting engine, or LOLBin
o Unapproved or unsigned executable
o Unexpected executable path outside approved child-process expectations
· Increase severity when command line indicates:
o Download or remote content retrieval
o Encoded commands
o Script execution
o Service or task creation
o Registry persistence modification
· Suppress approved admin workflows and enterprise deployment tooling
Implementation Constraint Notes
· Parent must be validated TrueConf updater lineage
· Child-process classification must be based on behavioral class, not a short static list only
· Enterprise deployment tooling, software packaging, and approved maintenance automations must be explicitly suppressed
· This rule must not alert on every child process; it is restricted to unexpected child classes or unapproved executables
Tuning Explanation
· Maintain:
o APPROVED_TRUECONF_UPDATER_PARENTS
o APPROVED_TRUECONF_CHILD_PROCESSES
o APPROVED_ADMIN_WORKFLOWS
o APPROVED_ENTERPRISE_DEPLOYMENT_TOOLING
· Focus suspicious child classes on:
o cmd.exe
o powershell.exe
o pwsh.exe
o wscript.exe
o cscript.exe
o mshta.exe
o rundll32.exe
o regsvr32.exe
o schtasks.exe
o sc.exe
o bitsadmin.exe
o wmic.exe
o Unknown executables outside approved signer set
· Elevate when suspicious child class aligns with suspicious command-line behavior
Telemetry Dependency
· Parent-child lineage
· Command-line arguments
· Parent process metadata
· Child signer metadata where available
· Executable path metadata
SOC Usage Mode Detail
· Standalone alerting is allowed after suppression validation
· Highest-confidence form is:
o Approved TrueConf updater parent
o Suspicious child-process class
o Suspicious command-line or persistence-related argument
Variant Analysis
· Covers LOLBin substitution by detecting classes of utilities rather than only a short list
· Covers signed utility abuse through unexpected parent-child relationship
· Covers unknown child executables even when classic shells are avoided
Rule Regret Check
Deployment caution
Requires strong suppression of legitimate enterprise automation and software-management activity.
Confidence caution
Administrative or packaging activity may resemble this pattern if parent-child expectations are not localized.
Coverage value
Strongest SentinelOne rule for detecting abuse of update-related execution chains after payload launch.
Production Ready
Yes — with suppression discipline, parent-child baseline enforcement, and child-class scoping
Portable SentinelOne detection logic model
FROM ProcessEvents
WHERE EventType = "Process Creation"
AND ParentProcessName IN APPROVED_TRUECONF_UPDATER_PARENTS
AND (
ProcessName IN SUSPICIOUS_CHILD_PROCESS_CLASSES
OR Signer NOT IN (APPROVED_TRUECONF_SIGNERS, APPROVED_ENTERPRISE_SIGNERS)
OR ProcessImagePath NOT IN APPROVED_TRUECONF_CHILD_PATHS
)
AND NOT CommandLine MATCHES_ANY APPROVED_ADMIN_WORKFLOWS
AND NOT CommandLine MATCHES_ANY APPROVED_ENTERPRISE_DEPLOYMENT_TOOLING
SentinelOne Rule 3
Rule Name
TrueConf Update Context Execution Followed by Suspicious External Egress
Purpose
Detect execution from TrueConf update context where the same process or its validated descendants initiate outbound communication to non-approved destinations.
SOC Usage Mode
Correlation-first
Standalone Alerting Allowed
No
Minimum Deployment Requirement
· Process creation telemetry
· Process-linked network telemetry
· Process GUID or equivalent correlation field
· Approved destination allowlist
· Validated same-process or process-tree correlation capability
Enforcement Method
· Detect execution from approved TrueConf update or staging context
· Correlate outbound network events from:
o The same process identifier whenever possible
o A validated descendant process only where lineage linkage is proven
· Restrict to destinations outside approved TrueConf service expectations
· Apply bounded timing window
If process-level or validated process-tree correlation is not available, do not run this as alerting content; downgrade to hunt-only or analyst-triage use
Implementation Constraint Notes
· Same-process correlation must be validated before alerting is enabled
· Process-tree correlation must use lineage identifiers, not host-only joins
· Host-level fallback must not be treated as equivalent confidence
· Known conferencing, telemetry, relay, and update-validation destinations must be excluded or downgraded
· This rule should not be enabled in alerting mode if the tenant cannot reliably bind network events to the same process or validated descendant chain
Tuning Explanation
· Maintain:
o APPROVED_TRUECONF_DESTINATIONS
o APPROVED_CONFERENCING_AND_RELAY_DESTINATIONS
· Use 5–15 minutes where update execution is tightly coupled
· Extend modestly up to 30 minutes only where staging-to-execution delay is validated
· Elevate when:
o Destination is new or low-prevalence
o Repeated outbound connections occur
o Destination is not previously associated with normal TrueConf operations
· Suppress expected outbound service checks and normal conferencing endpoints
Telemetry Dependency
· Process creation
· Process GUID or equivalent lineage key
· Network telemetry tied to process
· Destination intelligence
· Optional destination prevalence or threat enrichment
SOC Usage Mode Detail
· Standalone alerting is not allowed
· Use as a high-confidence correlation rule only when process-linked network visibility is mature
· If only host-level linkage is available, downgrade to hunt-only or supporting triage content
Variant Analysis
· Delayed egress can evade a strict short window
· Use of approved infrastructure reduces signal quality
· Encrypted traffic does not prevent destination-based detection if process linkage remains visible
· Same-process or validated process-tree correlation materially improves resilience compared with host-only logic
Rule Regret Check
Deployment caution
Requires validated process-to-network linkage and mature destination allowlisting.
Confidence caution
Detects suspicious execution-to-egress sequence, not full incident truth by itself.
Coverage value
Best SentinelOne rule for identifying update-context execution that transitions into likely post-delivery command-and-control or staging communication.
Production Ready
Conditionally — only where same-process or validated process-tree network correlation is operationally proven
Portable SentinelOne detection logic model
LET execution_events =
FROM ProcessEvents
WHERE EventType = "Process Creation"
AND (
ProcessImagePath IN TRUECONF_UPDATE_PATHS
OR ProcessImagePath IN TRUECONF_STAGING_PATHS
OR ParentProcessName IN APPROVED_TRUECONF_UPDATER_PARENTS
)
LET network_events =
FROM NetworkEvents
WHERE Destination NOT IN APPROVED_TRUECONF_DESTINATIONS
AND Destination NOT IN APPROVED_CONFERENCING_AND_RELAY_DESTINATIONS
JOIN execution_events e WITH network_events n
ON e.ProcessGuid = n.ProcessGuid
OR n.ParentProcessGuid = e.ProcessGuid
WHERE n.Timestamp BETWEEN e.Timestamp AND e.Timestamp + 30m
Additional High-Value Detection Candidate
Rule Name
TrueConf Update Context Persistence Immediately After Execution
Purpose
Detect persistence created by processes executing from TrueConf update context or their direct descendants shortly after execution.
SOC Usage Mode
Correlation-first
Standalone Alerting Allowed
No
Minimum Deployment Requirement
· Process creation telemetry
· Persistence telemetry covering service creation, scheduled task creation, autorun or Run key modification, and startup-folder persistence where available
· Same-process or process-tree correlation capability
· Approved maintenance workflow allowlist
Enforcement Method
· Identify execution from approved TrueConf update or staging context
· Correlate persistence created by:
o The same process
o Or a validated descendant process
· Bound the correlation window to immediate post-execution behavior
· Exclude approved installation, packaging, and maintenance workflows
· Treat host-level fallback as hunt-only if process-tree linkage is unavailable
Implementation Constraint Notes
· This rule is strongest where persistence telemetry is normalized and process-linked
· It must prefer same-process or descendant-process correlation over host-only timing correlation
· Legitimate software deployment and packaging workflows must be explicitly suppressed
· It is a strong candidate, but remains below the top three because the selected primary set already covers initial execution deviation, updater-lineage abuse, and execution-to-egress transition
Tuning Explanation
· Use a short post-execution window, typically 5–20 minutes
· Prioritize persistence types unusual for standard TrueConf updates:
o New service creation
o Scheduled task creation
o Run or RunOnce registry additions
· Elevate when persistence is created by:
o Low-prevalence binaries
o Unexpected child processes
o Unsigned or unapproved executables
· In environments where persistence telemetry is substantially stronger than process-to-network linkage, this candidate may be promoted above Rule 3
Telemetry Dependency
· Process creation and lineage
· Process GUID or equivalent lineage key
· Persistence event telemetry
· Approved maintenance workflow allowlist
· Optional signer and prevalence enrichment
SOC Usage Mode Detail
· Standalone alerting is not allowed
· Use as a high-confidence supporting detection when persistence is tightly linked to update-context execution
· If only host-level linkage is available, downgrade to hunt-only or analyst triage content
Variant Analysis
· Delayed persistence outside the bounded window can evade strict correlation
· Attackers may use descendant processes to create persistence rather than the initial payload
· Signed binaries do not evade this rule if persistence remains linked to update-context execution
· Alternative persistence mechanisms outside current telemetry coverage reduce effectiveness
Rule Regret Check
Deployment caution
Requires reliable persistence telemetry and suppression of legitimate maintenance workflows.
Confidence caution
Detects suspicious execution-to-persistence transition, not full incident truth by itself.
Coverage value
Very strong follow-on detection for update-delivered payloads that establish immediate footholds after execution.
Production Ready
Conditionally — only where persistence telemetry and process-tree correlation are validated
Portable SentinelOne detection logic model
LET execution_events =
FROM ProcessEvents
WHERE EventType = "Process Creation"
AND (
ProcessImagePath IN TRUECONF_UPDATE_PATHS
OR ProcessImagePath IN TRUECONF_STAGING_PATHS
OR ParentProcessName IN APPROVED_TRUECONF_UPDATER_PARENTS
)
LET persistence_events =
FROM PersistenceEvents
WHERE PersistenceType IN ("ServiceCreate","ScheduledTaskCreate","RunKeyCreate","RunOnceCreate","StartupFolder")
JOIN execution_events e WITH persistence_events p
ON e.ProcessGuid = p.ProcessGuid
OR p.ParentProcessGuid = e.ProcessGuid
WHERE p.Timestamp BETWEEN e.Timestamp AND e.Timestamp + 20m
AND p.TargetObject NOT IN APPROVED_MAINTENANCE_PERSISTENCE
Engineering Note — Required Actions
To deploy this rule safely and effectively, engineers must:
· Validate that SentinelOne exposes persistence events with usable process linkage
· Define approved TrueConf update and staging paths
· Build and maintain allowlists for:
o Approved installer persistence artifacts
o Approved enterprise maintenance workflows
o Approved packaging or software deployment activity
· Test correlation against real update activity to confirm that normal TrueConf updates do not create flagged persistence
· Downgrade to hunt-only if only host-level timing correlation is available
Coverage remains conditional until these steps are completed.
Engineering Note — SentinelOne
SentinelOne is the primary detection layer for this threat and provides the highest-confidence detection opportunities in this report.
Required validation actions before deployment:
· Identify and maintain approved TrueConf install, update, cache, and staging paths
· Build and maintain external allowlists for:
o Approved updater parents
o Approved update binaries
o Approved signer and publisher expectations
o Approved child-process expectations where applicable
o Approved TrueConf outbound destinations
o Approved conferencing, relay, and telemetry destinations
· Validate process-to-network correlation quality before enabling Rule 3 as alerting content
· Suppress documented maintenance, packaging, and administrative workflows that legitimately interact with TrueConf update context
· Verify that writable-path and temp-adjacent execution logic reflects the real endpoint layout in the environment
Coverage is strong, but still depends on:
· Baseline maturity
· Process-lineage quality
· Destination allowlist maturity
· Suppression discipline
· Process-linked network telemetry quality
Splunk
Rule Name
TrueConf Update Context Execution Integrity Deviation
Purpose
Detect execution from approved TrueConf update, cache, or staging context where the process violates expected signer, prevalence, parent-lineage, or writable-path expectations.
SOC Usage Mode
Alert-capable supporting detection
Standalone Alerting Allowed
Yes — only after:
· path normalization is validated
· updater-parent baselines are validated
· maintenance workflow suppression is validated
Minimum Deployment Requirement
· Normalized endpoint process telemetry
· Parent-child lineage fields
· Process path visibility
· Signer or publisher metadata where available
· File prevalence, first-seen, or rarity enrichment where available
· Approved TrueConf path inventory localized to the tenant
Enforcement Method
· Scope execution only to:
o approved TrueConf update paths
o approved staging or cache paths
o processes launched by approved updater parents
· Trigger only when at least one strong integrity-deviation condition exists:
o signer outside approved TrueConf or enterprise signer expectations
o low-prevalence, unknown, or first-seen executable
o execution from writable or temp-adjacent update-context path
o parent outside approved updater lineage
· Raise severity when two or more deviation conditions occur together
· Suppress approved update binaries and approved maintenance workflows
Implementation Constraint Notes
· This is not a generic trueconf path rule
· The primary value comes from trusted update context plus integrity deviation
· Generic install-path hits must not be treated as equivalent to update-context execution
· If signer data is unavailable or inconsistent, parent-lineage and rarity conditions must carry more weight
· If path normalization is weak, deploy first in triage mode rather than direct alerting
Tuning Explanation
· Maintain lookups or macros for:
o approved TrueConf update paths
o approved TrueConf staging and cache paths
o approved updater parents
o approved update binaries
o approved signers
o writable or temp-adjacent update paths
· Elevate when:
o executable is low-prevalence
o signer is unapproved
o parent lineage is invalid
o execution occurs from writable update-context path
· Suppress approved software deployment and maintenance workflows explicitly
Telemetry Dependency
· Endpoint process telemetry
· Process lineage
· Path normalization
· Signer metadata where available
· Prevalence or rarity enrichment where available
SOC Usage Mode Detail
· Standalone alerting is allowed only after baseline maturity is validated
· Highest-confidence matches occur when multiple deviation conditions align
· Single weak-condition hits should be downgraded to triage or hunt review
Variant Analysis
· Renaming does not defeat the rule
· Signed malicious payloads still surface through lineage, path, or rarity deviation
· Delayed execution still triggers if update-context execution remains observable
· Minor path variation remains covered when approved update and staging contexts are properly maintained
Rule Regret Check
Deployment caution
Noisy if approved paths, updater parents, and maintenance workflows are not well maintained.
Confidence caution
Detects execution integrity deviation in trusted update context, not full compromise.
Coverage value
Primary Splunk rule for cross-validating suspicious execution abuse in trusted update context.
Production Ready
Yes — with normalized fields, approved-context lookups, and suppression discipline
Portable Splunk SPL implementation model
index=endpoint sourcetype IN ("edr:process","sysmon:process","osquery:process")
| eval update_context=if(
process_path IN TRUECONF_UPDATE_PATHS
OR process_path IN TRUECONF_STAGING_PATHS
OR parent_process_path IN TRUECONF_UPDATE_PATHS
OR parent_process_name IN APPROVED_TRUECONF_UPDATER_PARENTS,
1, 0
)
| where EventType="Process Creation" AND update_context=1
| lookup approved_trueconf_update_binaries process_name OUTPUT process_name as approved_binary
| lookup approved_trueconf_updater_parents parent_process_name OUTPUT parent_process_name as approved_parent
| lookup approved_trueconf_signers signer OUTPUT signer as approved_signer
| eval writable_context=if(process_path IN WRITABLE_OR_TEMP_ADJACENT_UPDATE_PATHS,1,0)
| eval rarity_flag=if(file_prevalence IN ("low","unknown","first_seen"),1,0)
| eval signer_flag=if(isnull(approved_signer),1,0)
| eval parent_flag=if(isnull(approved_parent),1,0)
| eval deviation_count=signer_flag+rarity_flag+writable_context+parent_flag
| where isnull(approved_binary)
| where deviation_count>=1
| search NOT [ | inputlookup approved_trueconf_maintenance_workflows | fields command_line ]
| eval severity=case(deviation_count>=3,"high",deviation_count=2,"medium",true(),"low")
| stats values(process_name) values(parent_process_name) values(process_path) values(signer) values(file_prevalence) values(severity) by host process_guid _time
Rule Name
Abnormal TrueConf Server-to-Endpoint Distribution Burst
Purpose
Detect distribution burst and scope anomalies from approved TrueConf servers to internal clients that are inconsistent with expected rollout behavior.
SOC Usage Mode
Correlation-first
Standalone Alerting Allowed
No — requires maintenance-window and rollout-context validation
Minimum Deployment Requirement
· Internal network flow or session telemetry
· Approved TrueConf server inventory
· Time-synchronized telemetry
· Preferably TrueConf server-side update or administrative logs
· Approved maintenance-window context
Enforcement Method
· Restrict source to approved TrueConf servers
· Restrict destination to internal clients
· Detect burst or scope anomalies using:
o distinct client count
o session count
o timing irregularity
· Elevate when no matching approved maintenance window or server-side rollout action exists
· Correlate with downstream endpoint execution where possible
Implementation Constraint Notes
· This rule detects distribution burst and scope anomaly, not malicious payload execution
· Distinct-destination counting is a strong proxy for fan-out, but not proof of malicious delivery
· This rule is strongest when paired with server-side update activity or approved rollout logs
· Environment-specific rollout patterns must be validated before alerting is enabled
Tuning Explanation
· Maintain:
o approved TrueConf server inventory
o approved maintenance windows
o expected rollout schedules
o optional server-side rollout logs
· Tune by segment, zone, business unit, or deployment ring where rollout behavior varies
· Suppress approved broad rollouts explicitly
· Require stricter thresholds in environments with frequent large scheduled updates
Telemetry Dependency
· Internal network telemetry
· Approved server inventory
· Maintenance-window lookup
· Optional TrueConf server administrative logs
SOC Usage Mode Detail
· Standalone alerting is not allowed
· Use as a correlation signal that queues endpoint review and update-context execution validation
Variant Analysis
· Low-and-slow distribution may evade burst logic
· Attackers operating during approved windows reduce signal value
· Encrypted traffic does not defeat the rule when flow timing and scope remain visible
· Small-scope targeted delivery may reduce sensitivity
Rule Regret Check
Deployment caution
Requires rollout-aware tuning and maintenance-window validation.
Confidence caution
Detects suspicious distribution behavior, not malicious payload execution.
Coverage value
Best Splunk rule for environment-wide trusted-server propagation anomalies.
Production Ready
Conditionally — only where server inventory, network telemetry, and maintenance-window context are mature
Portable Splunk SPL implementation model
index=netflow OR index=network
| lookup approved_trueconf_servers src_ip OUTPUT src_ip as approved_server
| where isnotnull(approved_server)
| eval internal_dst=if(
cidrmatch("10.0.0.0/8",dest_ip)
OR cidrmatch("172.16.0.0/12",dest_ip)
OR cidrmatch("192.168.0.0/16",dest_ip),
1, 0
)
| where internal_dst=1
| bucket time span=5m
| stats dc(destip) as unique_clients count as session_count values(dest_port) as dest_ports by src_ip time
| lookup approvedtrueconf_maintenance_windows src_ip time OUTPUT maintenancewindow
| where unique_clients >= 20 OR session_count >= 40
| where isnull(maintenance_window)
| eval alert_basis=case(unique_clients>=20 AND session_count>=40,"burst_and_scope",unique_clients>=20,"scope",session_count>=40,"burst")
Rule Name
TrueConf Update Context Execution Followed by Suspicious External Egress
Purpose
Detect execution from approved TrueConf update context where validated process-linked telemetry shows the same process initiating outbound communication to destinations outside approved TrueConf service expectations.
SOC Usage Mode
Correlation-first
Standalone Alerting Allowed
No
Minimum Deployment Requirement
· Endpoint process telemetry
· Process-linked network telemetry
· Process GUID or equivalent correlation key
· Approved destination allowlist
· Time-synchronized telemetry
· Validated process-to-network linkage
Enforcement Method
· Identify execution from approved TrueConf update or staging context
· Correlate outbound network activity from:
o the same process GUID where available
· Restrict to destinations outside approved TrueConf service expectations
· Apply bounded timing window
· If only host-level or weak parent-linkage correlation exists, do not alert; downgrade to hunt-only or analyst triage use
Implementation Constraint Notes
· This hardening rewrite intentionally prefers same-process correlation over optimistic descendant logic
· Do not enable this as alerting content if process GUID continuity across process and network telemetry is not trustworthy
· Known conferencing, telemetry, relay, and update-validation destinations must be excluded
· If descendant-process lineage is available and validated in the tenant, it may be added as a local enhancement, but it is not assumed by default here
Tuning Explanation
· Maintain:
o approved TrueConf destinations
o approved conferencing and relay destinations
· Use 5–15 minutes where update execution is tightly coupled
· Extend only where validated by real update behavior
· Elevate when destination is new, low-prevalence, or repeatedly contacted
· Suppress normal service checks and known-good relay traffic explicitly
Telemetry Dependency
· Endpoint process telemetry
· Process GUID or equivalent correlation key
· Process-linked network telemetry
· Destination allowlist
· Optional destination prevalence or threat enrichment
SOC Usage Mode Detail
· Standalone alerting is not allowed
· Use as a high-confidence correlation rule only when process-linked network telemetry is operationally proven
· If process linkage is not validated, do not alert; downgrade to hunt-only
Variant Analysis
· Delayed egress can evade a strict short window
· Approved infrastructure use reduces signal quality
· Encrypted traffic does not defeat the rule if destination linkage remains visible
· Same-process correlation is more operationally reliable than assumed descendant correlation in most tenants
Rule Regret Check
Deployment caution
Requires validated process-to-network linkage and mature destination allowlisting.
Confidence caution
Detects suspicious execution-to-egress sequence, not full incident truth by itself.
Coverage value
Best Splunk rule for identifying update-context execution that transitions into likely post-delivery external communication when process-linked network telemetry is trustworthy.
Production Ready
Conditionally — only where same-process network correlation is operationally proven
Portable Splunk SPL implementation model
index=endpoint sourcetype IN ("edr:process","sysmon:process")
| eval update_context=if(
process_path IN TRUECONF_UPDATE_PATHS
OR process_path IN TRUECONF_STAGING_PATHS
OR parent_process_name IN APPROVED_TRUECONF_UPDATER_PARENTS,
1, 0
)
| where EventType="Process Creation" AND update_context=1
| table time host processguid process_name process_path
| rename time as exectime
| join type=inner process_guid [
search index=endpoint sourcetype IN ("edr:network","sysmon:network")
| lookup approved_trueconf_destinations dest OUTPUT dest as approved_dest
| lookup approved_trueconf_relay_and_conferencing dest OUTPUT dest as approved_relay_dest
| where isnull(approved_dest) AND isnull(approved_relay_dest)
| table time processguid dest dest_ip
| rename time as nettime
]
| where net_time >= exec_time AND net_time <= exec_time + 1800
| stats values(process_name) values(process_path) values(dest) values(dest_ip) by host process_guid exec_time net_time
Additional High-Value Detection Candidate
Rule Name
TrueConf Update Context Persistence Immediately After Execution
Purpose
Detect persistence created by processes executing from approved TrueConf update context shortly after execution.
SOC Usage Mode
Correlation-first
Standalone Alerting Allowed
No
Minimum Deployment Requirement
· Endpoint process telemetry
· Persistence telemetry
· Process GUID or equivalent lineage key
· Approved maintenance workflow allowlist
· Time-synchronized telemetry
· Validated process-to-persistence linkage
Enforcement Method
· Identify execution from approved TrueConf update or staging context
· Correlate persistence activity from the same process or a validated descendant only where lineage is trustworthy
· Restrict to persistence types unusual for normal TrueConf updates
· Exclude approved packaging, deployment, and maintenance workflows
· If only host-level correlation is available, downgrade to hunt-only
Implementation Constraint Notes
· This rule is strongest where persistence telemetry is normalized and process-linked
· It remains outside the top three because the selected primary set already covers:
o initial execution deviation
o environment-wide distribution anomaly
o execution-to-egress transition
Promotion guidance:
· In tenants where persistence telemetry is stronger and more reliable than process-linked network telemetry, this candidate should be promoted above Rule 3
Tuning Explanation
· Prioritize:
o service creation
o scheduled task creation
o Run or RunOnce registry additions
o startup-folder persistence where captured
· Use 5–20 minute bounded windows
· Elevate when persistence is tied to low-prevalence or unexpected executables
· Suppress approved enterprise packaging and maintenance workflows explicitly
Telemetry Dependency
· Endpoint process telemetry
· Persistence telemetry
· Process GUID or lineage key
· Maintenance workflow allowlist
· Optional signer and prevalence enrichment
SOC Usage Mode Detail
· Standalone alerting is not allowed
· Use as a high-confidence supporting detection when persistence is tightly linked to update-context execution
Variant Analysis
· Delayed persistence can evade a strict short window
· Validated descendant-process persistence remains covered if lineage is preserved
· Signed binaries do not evade the rule if persistence remains linked to update-context execution
· Alternative persistence outside current telemetry coverage reduces effectiveness
Rule Regret Check
Deployment caution
Requires reliable persistence telemetry and suppression of legitimate maintenance workflows.
Confidence caution
Detects suspicious execution-to-persistence transition, not full incident truth by itself.
Coverage value
Very strong follow-on detection for update-delivered payloads that establish immediate footholds after execution.
Production Ready
Conditionally — only where persistence telemetry and process-tree correlation are validated
Portable Splunk SPL implementation model
index=endpoint sourcetype IN ("edr:process","sysmon:process")
| eval update_context=if(
process_path IN TRUECONF_UPDATE_PATHS
OR process_path IN TRUECONF_STAGING_PATHS
OR parent_process_name IN APPROVED_TRUECONF_UPDATER_PARENTS,
1, 0
)
| where EventType="Process Creation" AND update_context=1
| table time host processguid process_name process_path
| rename time as exectime
| join type=inner process_guid [
search index=endpoint sourcetype IN ("edr:persistence","sysmon:registry","sysmon:task","sysmon:service")
| eval persistence_type=coalesce(PersistenceType,EventCode,ActionType)
| table time processguid persistence_type target_object
| rename time as persistencetime
]
| where persistence_time >= exec_time AND persistence_time <= exec_time + 1200
| search NOT [ | inputlookup approved_trueconf_maintenance_persistence | fields target_object ]
| stats values(process_name) values(process_path) values(persistence_type) values(target_object) by host process_guid exec_time persistence_time
Engineering Note — Splunk
Splunk is the primary cross-source correlation platform for this threat, but its detection quality depends entirely on:
· normalized endpoint telemetry
· mature TrueConf-specific lookups and path baselines
· time synchronization across sources
· validated process-to-network and process-to-persistence linkage
· disciplined suppression of legitimate maintenance and deployment workflows
Required validation actions before deployment:
· Identify and maintain approved TrueConf server inventory
· Build and maintain lookups for:
o approved TrueConf paths
o approved updater parents
o approved update binaries
o approved signer expectations
o approved destinations
o approved maintenance windows
o approved deployment and admin workflows
· Validate whether process-linked network telemetry is trustworthy enough for Rule 3 alerting
· Validate whether persistence telemetry is strong enough to promote the additional candidate where appropriate
Tune thresholds by rollout segment, environment size, and operational cadence
Elastic
Rule Name
TrueConf Update Context Execution Integrity Deviation
Purpose
Detect execution from approved TrueConf update, cache, or staging context where the process violates expected signer, prevalence, parent-lineage, or writable-path expectations.
SOC Usage Mode
Alert-capable supporting detection
Standalone Alerting Allowed
Yes — only after:
· approved update and staging paths are localized
· approved updater parents are localized
· approved maintenance workflow suppression is validated
Minimum Deployment Requirement
· Process event telemetry
· Parent-child lineage fields
· Executable path visibility
· Code-signature metadata where available
· File prevalence or rarity enrichment where available
· Approved TrueConf update, cache, and staging path inventory
Enforcement Method
· Scope execution only to:
o approved TrueConf update paths
o approved TrueConf staging or cache paths
o processes launched by approved updater parents
· Trigger only when at least one strong integrity-deviation condition exists:
o signer is untrusted or outside approved signer expectations
o executable is low-prevalence, unknown, or first-seen
o execution occurs from writable or temp-adjacent update-context path
o parent is outside approved updater lineage
· Raise severity when two or more deviation conditions occur together
· Suppress approved update binaries and approved maintenance workflows
Implementation Constraint Notes
· This is not a broad trueconf string-matching rule
· Generic install-path hits must not be treated as equivalent to update-context execution
· Writable-path logic must reflect the tenant’s real endpoint layout
· If signature coverage is weak, parent-lineage and rarity conditions must carry more weight
· If path baselines are immature, deploy first in triage mode rather than high-confidence alerting
Tuning Explanation
· Maintain:
o TRUECONF_UPDATE_PATHS
o TRUECONF_STAGING_PATHS
o APPROVED_TRUECONF_UPDATER_PARENTS
o APPROVED_TRUECONF_UPDATE_BINARIES
o APPROVED_TRUECONF_SIGNERS
o WRITABLE_OR_TEMP_ADJACENT_UPDATE_PATHS
· Elevate when:
o executable is low-prevalence
o signer is unapproved
o parent lineage is invalid
o execution occurs from writable update-context path
· Downgrade single weak-condition hits to triage unless update timing is already suspicious
Telemetry Dependency
· process.entity_id
· process.executable
· process.parent.executable
· process.code_signature.trusted
· process.Ext.prevalence or equivalent enrichment
SOC Usage Mode Detail
· Standalone alerting is allowed only when baseline maturity is validated
· Highest-confidence matches occur when multiple deviation conditions align
Variant Analysis
· Renaming does not defeat the rule
· Signed malicious payloads still surface through lineage, path, or rarity deviation
· Delayed execution still triggers if update-context execution remains observable
· Minor path variation remains covered when approved update and staging contexts are properly maintained
Rule Regret Check
Deployment caution
Noisy if approved paths, updater parents, and maintenance workflows are not well maintained.
Confidence caution
Detects execution integrity deviation in trusted update context, not full compromise.
Coverage value
Primary Elastic rule for suspicious execution abuse in trusted update context.
Production Ready
Yes — with localized baselines, allowlists, and suppression discipline
Portable Elastic implementation model
process where event.type == "start"
and (
process.executable in TRUECONF_UPDATE_PATHS or
process.executable in TRUECONF_STAGING_PATHS or
process.parent.executable in TRUECONF_UPDATE_PATHS or
process.parent.name in APPROVED_TRUECONF_UPDATER_PARENTS
)
and not process.name in APPROVED_TRUECONF_UPDATE_BINARIES
and (
process.code_signature.trusted == false or
process.executable in WRITABLE_OR_TEMP_ADJACENT_UPDATE_PATHS or
process.parent.name not in APPROVED_TRUECONF_UPDATER_PARENTS or
process.Ext.prevalence in ("low","unknown","first_seen")
)
and not process.command_line like~ APPROVED_TRUECONF_MAINTENANCE_WORKFLOWS
Rule Name
TrueConf Updater Parent-Child Execution Abuse
Purpose
Detect approved TrueConf updater or application processes spawning unexpected child processes inconsistent with normal update behavior.
SOC Usage Mode
Alert-capable supporting detection
Standalone Alerting Allowed
Yes — only after suppression of approved admin and deployment workflows is validated
Minimum Deployment Requirement
· Process start telemetry
· Parent-child lineage visibility
· Command-line visibility
· Approved updater parent inventory
· Approved admin and deployment workflow allowlists
Enforcement Method
· Restrict parent to approved TrueConf updater or application lineage
· Trigger when child process is:
o shell, scripting engine, or LOLBin class
o unapproved executable path
o untrusted or unapproved signer
· Elevate when command line indicates:
o remote retrieval
o encoded commands
o script execution
o service creation
o task creation
o registry persistence modification
· Suppress approved admin, packaging, and deployment workflows
Implementation Constraint Notes
· This rule must not rely only on a short static child-process list
· Child classification must be based on behavioral class plus allowlist discipline
· Approved enterprise automation must be explicitly suppressed
· Parent lineage must be validated from documented TrueConf behavior, not prior detections
Tuning Explanation
· Maintain:
o APPROVED_TRUECONF_UPDATER_PARENTS
o APPROVED_TRUECONF_CHILD_PATHS
o APPROVED_ADMIN_WORKFLOWS
o APPROVED_ENTERPRISE_DEPLOYMENT_TOOLING
o SUSPICIOUS_CHILD_PROCESS_CLASSES
· Elevate when:
o suspicious child class aligns with suspicious command-line behavior
o child executable is outside approved path and signer expectations
Telemetry Dependency
· process.command_line
· process.code_signature.trusted
· process.executable
SOC Usage Mode Detail
· Standalone alerting is allowed after suppression validation
· Highest-confidence matches occur when suspicious child class aligns with suspicious command-line content
Variant Analysis
· Covers LOLBin substitution by detecting classes of utilities rather than only a short fixed list
· Covers signed utility abuse through unexpected parent-child relationship
· Covers unknown child executables even when classic shells are avoided
Rule Regret Check
Deployment caution
Requires strong suppression of legitimate enterprise automation and software-management activity.
Confidence caution
Administrative or packaging activity may resemble this pattern if parent-child expectations are not localized.
Coverage value
Strongest Elastic rule for detecting update-related execution-chain abuse after payload launch.
Production Ready
Yes — with suppression discipline, parent-child baseline enforcement, and child-class scoping
Portable Elastic implementation model
process where event.type == "start"
and process.parent.name in APPROVED_TRUECONF_UPDATER_PARENTS
and (
process.name in SUSPICIOUS_CHILD_PROCESS_CLASSES or
process.code_signature.trusted == false or
process.executable not in APPROVED_TRUECONF_CHILD_PATHS
)
and not process.command_line like~ APPROVED_ADMIN_WORKFLOWS
and not process.command_line like~ APPROVED_ENTERPRISE_DEPLOYMENT_TOOLING
Rule Name
TrueConf Update Context Execution Followed by Suspicious External Egress
Purpose
Detect execution from approved TrueConf update context where validated process-linked telemetry shows the same process initiating outbound communication to destinations outside approved TrueConf service expectations.
SOC Usage Mode
Correlation-first
Standalone Alerting Allowed
No
Minimum Deployment Requirement
· Process telemetry
· Network telemetry tied to process.entity_id
· Approved destination allowlist
· Time-synchronized telemetry
· Validated process-to-network linkage
Enforcement Method
· Identify execution from approved TrueConf update or staging context
· Correlate outbound network activity from:
o the same process.entity_id only
· Restrict to destinations outside approved TrueConf service expectations
· Apply bounded timing window
If process-to-network linkage via process.entity_id is not validated, do not enable as alerting content; downgrade to hunt-only
Implementation Constraint Notes
· This hardening rewrite intentionally uses same-process correlation only
· Host-only joins are not acceptable for alerting
· Descendant-process correlation may be added only if the tenant has validated lineage continuity across process and network events
· Approved conferencing, relay, telemetry, and update-validation destinations must be excluded
· This rule must not be enabled in alerting mode if process-linked network telemetry is not operationally proven
Tuning Explanation
· Maintain:
o APPROVED_TRUECONF_DESTINATIONS
o APPROVED_CONFERENCING_RELAY_AND_TELEMETRY_DESTINATIONS
· Use 5–15 minutes where update execution is tightly coupled
· Extend only where validated by real tenant behavior
· Elevate when:
o destination is new or low-prevalence
o repeated outbound connections occur
o destination is not previously associated with normal TrueConf operations
Telemetry Dependency
· process.entity_id
· network.process.entity_id or equivalent
· destination fields
· approved destination allowlist
· optional destination prevalence or enrichment
SOC Usage Mode Detail
· Standalone alerting is not allowed
· Use as a high-confidence correlation rule only when process-linked network telemetry is operationally proven
· If process linkage is not validated, do not alert; downgrade to hunt-only
Variant Analysis
· Delayed egress can evade a strict short window
· Approved infrastructure use reduces signal quality
· Encrypted traffic does not defeat the rule if destination linkage remains visible
· Same-process correlation is more operationally reliable than optimistic descendant assumptions in most tenants
Rule Regret Check
Deployment caution
Requires validated process-to-network linkage and mature destination allowlisting.
Confidence caution
Detects suspicious execution-to-egress sequence, not full incident truth by itself.
Coverage value
Best Elastic rule for identifying update-context execution that transitions into likely post-delivery external communication when process-linked telemetry is trustworthy.
Production Ready
Conditionally — only where same-process network correlation is operationally proven
Portable Elastic implementation model
sequence by process.entity_id with maxspan=15m
[process where event.type == "start"
and (
process.executable in TRUECONF_UPDATE_PATHS or
process.executable in TRUECONF_STAGING_PATHS or
process.parent.name in APPROVED_TRUECONF_UPDATER_PARENTS
)
]
[network where
not destination.domain in APPROVED_TRUECONF_DESTINATIONS and
not destination.domain in APPROVED_CONFERENCING_RELAY_AND_TELEMETRY_DESTINATIONS
]
Additional High-Value Detection Candidate
Rule Name
TrueConf Update Context Persistence Immediately After Execution
Purpose
Detect persistence created by processes executing from approved TrueConf update context shortly after execution.
SOC Usage Mode
Correlation-first
Standalone Alerting Allowed
No
Minimum Deployment Requirement
· Process telemetry
· Persistence telemetry
· process.entity_id or validated lineage key
· Approved maintenance workflow allowlist
· Time-synchronized telemetry
Enforcement Method
· Identify execution from approved TrueConf update or staging context
· Correlate persistence from:
o the same process only by default
o a validated descendant process only if lineage continuity is proven in the tenant
· Restrict to persistence types unusual for normal TrueConf updates
· Exclude approved packaging, deployment, and maintenance workflows
· If only host-level correlation exists, downgrade to hunt-only
Implementation Constraint Notes
· This rule is strongest where persistence telemetry is normalized and process-linked
· It remains outside the top three because the selected primary set already covers:
o initial execution deviation
o updater lineage abuse
o execution-to-egress transition
Promotion guidance: in tenants where persistence telemetry is stronger and more reliable than process-linked network telemetry, this candidate should be promoted above Rule 3
Tuning Explanation
· Prioritize:
o service creation
o scheduled task creation
o Run or RunOnce registry additions
o startup-folder persistence where captured
· Use 5–20 minute bounded windows
· Elevate when persistence is tied to low-prevalence or unexpected executables
· Suppress approved enterprise packaging and maintenance workflows explicitly
Telemetry Dependency
· process.entity_id
· persistence telemetry
· maintenance workflow allowlist
· optional signer and prevalence enrichment
SOC Usage Mode Detail
· Standalone alerting is not allowed
· Use as a high-confidence supporting detection when persistence is tightly linked to update-context execution
Variant Analysis
· Delayed persistence can evade a strict short window
· Same-process persistence is strongest; descendant persistence requires validated lineage
· Signed binaries do not evade the rule if persistence remains linked to update-context execution
· Alternative persistence outside current telemetry coverage reduces effectiveness
Rule Regret Check
Deployment caution
Requires reliable persistence telemetry and suppression of legitimate maintenance workflows.
Confidence caution
Detects suspicious execution-to-persistence transition, not full incident truth by itself.
Coverage value
Very strong follow-on detection for update-delivered payloads that establish immediate footholds after execution.
Production Ready
Conditionally — only where persistence telemetry and process-linked correlation are validated
Portable Elastic implementation model
sequence by process.entity_id with maxspan=20m
[process where event.type == "start"
and (
process.executable in TRUECONF_UPDATE_PATHS or
process.executable in TRUECONF_STAGING_PATHS or
process.parent.name in APPROVED_TRUECONF_UPDATER_PARENTS
)
]
[any where
(registry.path in APPROVED_PERSISTENCE_KEYS) or
(file.path in STARTUP_FOLDER_PATHS) or
(event.action == "service_install") or
(event.action == "scheduled_task_create")
]
Engineering Note — Elastic
Elastic detection quality depends entirely on:
· ECS normalization
· process.entity_id consistency across process and network data
· lookup and allowlist hygiene
· suppression discipline
· correlation fidelity
· maintenance of tenant-specific TrueConf baselines
Required validation actions before deployment:
· Identify and maintain approved TrueConf install, update, cache, and staging paths
· Build and maintain allowlists for:
o approved updater parents
o approved update binaries
o approved signers
o approved child-process expectations
o approved destinations
o approved maintenance workflows
· Validate whether same-process network linkage is trustworthy enough for Rule 3 alerting
· Validate whether persistence telemetry is strong enough to promote the additional candidate where appropriate
· Tune path, suppression, and timing thresholds by environment segment and operational cadence
Coverage is strong, but only when field normalization, allowlist hygiene, and telemetry fidelity are mature. This hardening rewrite is intended to correct the earlier implementation-realism and correlation-safety weaknesses while preserving the analytic model already established in the Block 4 rule build.
QRadar
Rule Name
TrueConf Update Context Execution Integrity Deviation
Purpose
Detect execution from approved TrueConf update, cache, or staging context where the process violates expected signer, rarity, parent-lineage, or writable-path expectations.
SOC Usage Mode
Alert-capable supporting detection
Standalone Alerting Allowed
Yes — only after:
· custom properties for process path, parent process, and command line are validated
· approved path and workflow reference sets are mature
· maintenance workflow suppression is validated
Minimum Deployment Requirement
· Endpoint process telemetry parsed into QRadar
· Custom properties for:
o process path
o parent process name or path
o process command line where available
o signer or publisher where available
· Reference sets for:
o approved TrueConf update paths
o approved TrueConf staging paths
o approved updater parents
o approved update binaries
o approved maintenance workflows
· Optional rarity or first-seen enrichment
Enforcement Method
· Scope execution only to:
o approved TrueConf update paths
o approved TrueConf staging or cache paths
o processes launched by approved updater parents
Trigger only when at least one strong integrity-deviation condition exists:
o signer or publisher outside approved expectations
o executable rarity, first-seen, or unknown prevalence condition where available
o execution from writable or temp-adjacent update-context path
o parent outside approved updater lineage
Raise priority when two or more deviation conditions occur together
· Suppress approved update binaries and approved maintenance workflows
Implementation Constraint Notes
· This is not a broad “TrueConf-related process” rule
· Generic install-path activity must not be treated as equivalent to update-context execution
· Writable-path logic must reflect the tenant’s real endpoint layout
· If signer metadata is weak, parent-lineage and path-deviation conditions must carry more weight
· If rarity fields are unavailable, the rule remains viable but with lower confidence and should initially operate in triage mode
Tuning Explanation
· Maintain reference sets for:
o Approved_TrueConf_Update_Paths
o Approved_TrueConf_Staging_Paths
o Approved_TrueConf_Updater_Parents
o Approved_TrueConf_Update_Binaries
o Approved_TrueConf_Signers
o Writable_Update_Adjacent_Paths
· Elevate when:
o executable is first-seen or rare
o signer is unapproved
o parent lineage is invalid
o execution occurs from writable update-context path
· Downgrade single weak-condition hits to triage unless update timing is already suspicious
Telemetry Dependency
· Endpoint process events
· Process path custom property
· Parent process custom property
· Signer or publisher metadata where available
· Optional rarity or first-seen enrichment
SOC Usage Mode Detail
· Standalone alerting is allowed only when baseline maturity is validated
· Highest-confidence matches occur when multiple deviation conditions align
Variant Analysis
· Renaming does not defeat the rule
· Signed malicious payloads still surface through lineage, path, or rarity deviation
· Delayed execution still triggers if update-context execution remains observable
· Minor path variation remains covered when approved update and staging contexts are properly maintained
Rule Regret Check
Deployment caution
Noisy if path parsing, updater-parent parsing, and workflow suppression are immature.
Confidence caution
Detects execution integrity deviation in trusted update context, not full compromise.
Coverage value
Primary QRadar rule for suspicious execution abuse in trusted update context.
Production Ready
Yes — with validated custom properties, reference sets, and suppression discipline
Portable QRadar implementation model
CRE Rule Logic:
WHEN events are detected by the Local System
AND when Event Category = Process Creation
AND when (
ProcessPath is in ReferenceSet("Approved_TrueConf_Update_Paths")
OR ProcessPath is in ReferenceSet("Approved_TrueConf_Staging_Paths")
OR ParentProcessName is in ReferenceSet("Approved_TrueConf_Updater_Parents")
)
AND when ProcessName is NOT in ReferenceSet("Approved_TrueConf_Update_Binaries")
AND when any of the following are true:
- Signer is NOT in ReferenceSet("Approved_TrueConf_Signers")
- ProcessPath is in ReferenceSet("Writable_Update_Adjacent_Paths")
- ParentProcessName is NOT in ReferenceSet("Approved_TrueConf_Updater_Parents")
- FileRarity is "low" or "unknown" or "first_seen"
AND when CommandLine does NOT match ReferenceSet("Approved_TrueConf_Maintenance_Workflows")
THEN create alert with severity increased when multiple deviation conditions are present
Rule Name
Abnormal TrueConf Server-to-Endpoint Distribution Burst
Purpose
Detect distribution burst and scope anomalies from approved TrueConf servers to internal clients that are inconsistent with expected rollout behavior.
SOC Usage Mode
Correlation-first
Standalone Alerting Allowed
No — requires maintenance-window and rollout-context validation
Minimum Deployment Requirement
· Internal flow telemetry in QRadar
· Approved TrueConf server inventory
· Time-synchronized telemetry
· Approved maintenance-window context
· Preferably server-side TrueConf administrative or rollout logs
Enforcement Method
· Restrict source to approved TrueConf servers
· Restrict destination to internal clients
· Detect burst or scope anomalies using:
o distinct destination count
o flow count
o timing irregularity
· Elevate when no matching approved maintenance window or server-side rollout action exists
· Correlate with downstream endpoint execution where possible
Implementation Constraint Notes
· This rule detects distribution burst and scope anomaly, not malicious payload execution
· Distinct destination counts are a strong proxy for fan-out, not proof of malicious delivery
· This rule is strongest when paired with server-side update or rollout logs
· Environment-specific rollout patterns must be validated before alerting is enabled
Tuning Explanation
· Maintain:
o Approved_TrueConf_Servers
o Approved_TrueConf_Maintenance_Windows
o expected rollout schedules
o optional rollout or admin event correlation
· Tune by zone, business unit, or deployment ring where rollout behavior varies
· Suppress approved broad rollouts explicitly
· Require stricter thresholds in environments with frequent large scheduled updates
Telemetry Dependency
· Flow telemetry
· Approved server inventory
· Maintenance-window reference data
· Optional server-side rollout logs
SOC Usage Mode Detail
· Standalone alerting is not allowed
· Use as a correlation signal that queues endpoint review and update-context execution validation
Variant Analysis
· Low-and-slow distribution may evade burst logic
· Attackers operating during approved windows reduce signal value
· Encrypted traffic does not defeat the rule when flow timing and scope remain visible
· Small-scope targeted delivery may reduce sensitivity
Rule Regret Check
Deployment caution
Requires rollout-aware tuning and maintenance-window validation.
Confidence caution
Detects suspicious distribution behavior, not malicious payload execution.
Coverage value
Best QRadar rule for environment-wide trusted-server propagation anomalies.
Production Ready
Conditionally — only where server inventory, flow telemetry, and maintenance-window context are mature
Portable QRadar implementation model
AQL / CRE Hybrid Logic:
SELECT sourceip, COUNT(*) AS flow_count, COUNT(DISTINCT destinationip) AS unique_clients
FROM flows
WHERE sourceip IN ReferenceSet("Approved_TrueConf_Servers")
AND destinationip IN LocalNetworks
GROUP BY sourceip, STARTTIME(5 minutes)
HAVING unique_clients >= 20 OR flow_count >= 40
CRE Correlation Layer:
- suppress if sourceip and time window match approved maintenance window
- elevate if no matching rollout/admin event exists
Rule Name
TrueConf Update Context Execution Followed by Suspicious External Egress
Purpose
Detect execution from approved TrueConf update context where validated execution-to-egress linkage shows the same execution context initiating outbound communication to destinations outside approved TrueConf service expectations.
SOC Usage Mode
Correlation-first
Standalone Alerting Allowed
No
Minimum Deployment Requirement
· Endpoint process telemetry parsed into QRadar
· Network or proxy telemetry with reliable execution-to-egress linkage
· Approved destination allowlist
· Time-synchronized telemetry
· A validated correlation key stronger than host-only timing
Enforcement Method
· Identify execution from approved TrueConf update or staging context
· Correlate outbound network activity from:
o the same process identifier where available, or
o a tenant-validated normalized execution context where QRadar cannot preserve native process GUID end-to-end
· Restrict to destinations outside approved TrueConf service expectations
· Apply bounded timing window
· If only host-level timing correlation exists and no stronger linkage is available, do not enable as alerting content; downgrade to hunt-only or analyst triage use
Implementation Constraint Notes
· This hardening rewrite explicitly avoids offense-on-offense logic
· Host-only joins are not acceptable for alerting without additional validated context
· Approved conferencing, telemetry, relay, and update-validation destinations must be excluded
· This rule must not be enabled in alerting mode if the tenant cannot reliably correlate execution and outbound traffic at better-than-host-only fidelity
· Descendant-process assumptions must not be enabled by default unless the tenant has proven lineage continuity in normalized telemetry
Tuning Explanation
· Maintain:
o Approved_TrueConf_Destinations
o Approved_Conferencing_Relay_Telemetry_Destinations
· Use 5–15 minutes where update execution is tightly coupled
· Extend only where validated by real tenant behavior
· Elevate when:
o destination is new, rare, or repeatedly contacted
o the correlated execution event already contains strong integrity-deviation signals
· Suppress normal service checks and known-good relay traffic explicitly
Telemetry Dependency
· Endpoint process telemetry
· Correlation key between execution and network activity
· Destination fields
· Approved destination allowlist
· Optional destination rarity or enrichment
SOC Usage Mode Detail
· Standalone alerting is not allowed
· Use as a high-confidence correlation rule only when linkage between execution and egress is operationally proven
· If linkage is not validated, do not alert; downgrade to hunt-only
Variant Analysis
· Delayed egress can evade a strict short window
· Approved infrastructure use reduces signal quality
· Encrypted traffic does not defeat the rule if destination linkage remains visible
· Same execution context or validated normalized linkage is more operationally reliable than broad host-only correlation
Rule Regret Check
Deployment caution
Requires validated execution-to-egress linkage and mature destination allowlisting.
Confidence caution
Detects suspicious execution-to-egress sequence, not full incident truth by itself.
Coverage value
Best QRadar rule for identifying update-context execution that transitions into likely post-delivery external communication when execution-to-egress linkage is trustworthy.
Production Ready
Conditionally — only where execution-to-egress linkage is operationally proven
Portable QRadar implementation model
CRE Rule Logic:
WHEN a Process Creation event occurs
AND (
ProcessPath is in ReferenceSet("Approved_TrueConf_Update_Paths")
OR ProcessPath is in ReferenceSet("Approved_TrueConf_Staging_Paths")
OR ParentProcessName is in ReferenceSet("Approved_TrueConf_Updater_Parents")
)
AND within 15 minutes the same validated execution context generates outbound communication
AND Destination is NOT in ReferenceSet("Approved_TrueConf_Destinations")
AND Destination is NOT in ReferenceSet("Approved_Conferencing_Relay_Telemetry_Destinations")
THEN create correlation alert
Critical deployment constraint:
- If the tenant cannot validate a correlation key stronger than host-only timing,
deploy as hunt-only and do not enable alerting.
Additional High-Value Detection Candidate
Rule Name
TrueConf Update Context Persistence Immediately After Execution
Purpose
Detect persistence created by processes executing from approved TrueConf update context shortly after execution.
SOC Usage Mode
Correlation-first
Standalone Alerting Allowed
No
Minimum Deployment Requirement
· Endpoint process telemetry
· Persistence telemetry
· A validated linkage key between execution and persistence activity
· Approved maintenance workflow allowlist
· Time-synchronized telemetry
Enforcement Method
· Identify execution from approved TrueConf update or staging context
· Correlate persistence activity from:
o the same process where available, or
o a validated descendant or normalized linkage only where the tenant has proven fidelity
· Restrict to persistence types unusual for normal TrueConf updates
· Exclude approved packaging, deployment, and maintenance workflows
· If only host-level correlation exists, downgrade to hunt-only
Implementation Constraint Notes
· This rule is strongest where persistence telemetry is normalized and process-linked
· It remains outside the top three because the selected primary set already covers:
o initial execution deviation
o environment-wide distribution anomaly
o execution-to-egress transition
Promotion guidance: in tenants where persistence telemetry is stronger and more reliable than execution-to-egress linkage, this candidate should be promoted above Rule 3
Tuning Explanation
· Prioritize:
o service creation
o scheduled task creation
o Run or RunOnce persistence
o startup persistence where captured
· Use 5–20 minute bounded windows
· Elevate when persistence is tied to low-prevalence or unexpected executables
· Suppress approved enterprise packaging and maintenance workflows explicitly
Telemetry Dependency
· Process telemetry
· Persistence telemetry
· Validated linkage key
· Maintenance workflow allowlist
· Optional signer and rarity enrichment
SOC Usage Mode Detail
· Standalone alerting is not allowed
· Use as a high-confidence supporting detection when persistence is tightly linked to update-context execution
Variant Analysis
· Delayed persistence can evade a strict short window
· Signed binaries do not evade the rule if persistence remains linked to update-context execution
· Alternative persistence outside telemetry coverage reduces effectiveness
Rule Regret Check
Deployment caution
Requires reliable persistence telemetry and suppression of legitimate maintenance workflows.
Confidence caution
Detects suspicious execution-to-persistence transition, not full incident truth by itself.
Coverage value
Very strong follow-on detection for update-delivered payloads that establish immediate footholds after execution.
Production Ready
Conditionally — only where persistence telemetry and execution-to-persistence linkage are validated
Portable QRadar implementation model
CRE Rule Logic:
WHEN a Process Creation event occurs
AND (
ProcessPath is in ReferenceSet("Approved_TrueConf_Update_Paths")
OR ProcessPath is in ReferenceSet("Approved_TrueConf_Staging_Paths")
OR ParentProcessName is in ReferenceSet("Approved_TrueConf_Updater_Parents")
)
AND within 20 minutes a persistence event occurs:
- service creation
- scheduled task creation
- Run / RunOnce persistence
- startup persistence
AND TargetObject is NOT in ReferenceSet("Approved_TrueConf_Maintenance_Persistence")
THEN create supporting correlation event
Promotion guidance:
- If persistence linkage is stronger than execution-to-egress linkage in the tenant,
promote this rule above Rule 3.
Engineering Note — QRadar
QRadar detection quality depends entirely on:
· DSM parsing quality
· custom property quality
· reference-set hygiene
· flow telemetry maturity
· maintenance-window context
· execution-to-network or execution-to-persistence linkage fidelity
· disciplined suppression of legitimate maintenance and deployment workflows
Required validation actions before deployment:
· Identify and maintain approved TrueConf server inventory
· Build and maintain reference sets for:
o approved TrueConf update and staging paths
o approved updater parents
o approved update binaries
o approved signers
o approved destinations
o approved maintenance windows
o approved deployment and administrative workflows
· Validate whether process or normalized execution-context linkage is trustworthy enough for Rule 3 alerting
· Validate whether persistence telemetry is strong enough to promote the additional candidate where appropriate
· Tune thresholds by rollout segment, environment size, and operational cadence
Sigma
Rule Name
TrueConf Update Context Execution Integrity Deviation
Purpose
Detect execution from approved TrueConf update or staging context where the process violates expected signer, parent-lineage, or writable-path expectations.
SOC Usage Mode
Alert-capable supporting detection
Standalone Alerting Allowed
Yes — only after path, parent, signer, and workflow baselines are localized
Minimum Deployment Requirement
· Process creation telemetry
· Parent process visibility
· Executable path visibility
· Signer metadata where available
· Approved TrueConf update and staging path inventory
Enforcement Method
· Scope execution only to:
o Approved TrueConf update paths
o Approved TrueConf staging or cache paths
o Processes launched by approved updater parents
· Trigger only when one or more strong deviation conditions exist:
o Signer outside approved expectations
o Execution from writable or temp-adjacent update-context path
o Parent outside approved updater lineage
· Suppress approved update binaries and approved maintenance workflows
Implementation Constraint Notes
· This is not a broad trueconf keyword rule
· Generic install-path activity must not be treated as equivalent to update-context execution
· Writable-path logic must reflect the tenant’s real endpoint layout
· Temporary-path matching must be constrained to update-adjacent staging locations, not every generic temp path in the environment
Tuning Explanation
· Maintain:
o Approved TrueConf update paths
o Approved TrueConf staging paths
o Approved updater parents
o Approved signer expectations
o Writable or temp-adjacent update paths
· Suppress known installer and maintenance workflows explicitly
· If only one weak deviation condition is present, consider triage-only deployment first
Telemetry Dependency
· Process creation
· Parent process name or path
· Executable path
· Signer metadata where available
SOC Usage Mode Detail
· Standalone alerting is allowed only after baseline maturity is validated
· Highest-confidence use occurs when multiple deviation conditions align in the backend implementation
Variant Analysis
· Renaming does not defeat the rule
· Signed malicious payloads still surface through lineage or writable-path deviation
· Minor path variation remains covered when approved update and staging contexts are maintained
Rule Regret Check
Deployment caution
Noisy if approved paths, updater parents, and workflow suppressions are not mature.
Confidence caution
Detects execution integrity deviation in trusted update context, not full compromise.
Coverage value
Primary Sigma rule for suspicious execution abuse in trusted update context.
Production Ready
Yes — with localized baselines, allowlists, and suppression discipline
Portable Sigma rule
title: TrueConf Update Context Execution Integrity Deviation
id: 4e9cbf66-6f5a-4b5d-9e70-trueconf-sigma-001
status: experimental
logsource:
category: process_creation
detection:
selection_update_path:
Image|contains:
- '\TrueConf\Update\'
- '\TrueConf\Cache\'
- '\TrueConf\Staging\'
selection_parent:
ParentImage|endswith:
- '\trueconf.exe'
- '\trueconf_updater.exe'
selection_writable_update_context:
Image|contains:
- '\AppData\Local\Temp\TrueConf\'
- '\Users\Public\TrueConf\'
selection_untrusted_signer:
SignatureStatus:
- 'Unsigned'
- 'Invalid'
- 'Untrusted'
selection_bad_parent:
ParentImage|endswith:
- '\cmd.exe'
- '\powershell.exe'
- '\wscript.exe'
- '\mshta.exe'
filter_approved_binary:
Image|endswith:
- '\approved_trueconf_updater.exe'
- '\approved_trueconf_patcher.exe'
filter_approved_workflow:
CommandLine|contains:
- 'approved_maintenance_workflow_marker'
- 'approved_deployment_workflow_marker'
condition: (selection_update_path or selection_parent) and (selection_writable_update_context or selection_untrusted_signer or selection_bad_parent) and not 1 of filter_*
fields:
- Image
- ParentImage
- CommandLine
- SignatureStatus
falsepositives:
- Approved maintenance or deployment workflows not yet allowlisted
level: high
Rule Name
TrueConf Updater Parent-Child Execution Abuse
Purpose
Detect approved TrueConf updater or application processes spawning unexpected child processes inconsistent with normal update behavior.
SOC Usage Mode
Alert-capable supporting detection
Standalone Alerting Allowed
Yes — after suppression of approved admin and deployment workflows is validated
Minimum Deployment Requirement
· Process creation telemetry
· Parent-child lineage visibility
· Command-line visibility preferred
· Approved updater parent inventory
· Approved admin and deployment workflow allowlists
Enforcement Method
· Restrict parent to approved TrueConf updater or application lineage
· Trigger when child process is:
o Shell
o Scripting engine
o LOLBin or dual-use utility
o Unapproved executable path
· Elevate where backend enrichment supports suspicious command-line context
· Suppress approved admin, packaging, and deployment workflows
Implementation Constraint Notes
· This rule must not rely only on a short static child list
· Child classification must be based on behavioral class
· Enterprise deployment tooling must be explicitly suppressed
· Parent lineage must be validated from documented TrueConf behavior
· The command-line branch must remain tied to suspicious child classes; it must not become a broad keyword detector on its own
· If command-line logging is absent, truncated, or unreliable, downgrade confidence and rely on parent-child plus path-based abuse only
Tuning Explanation
· Maintain:
o Approved TrueConf updater parents
o Approved child-process expectations
o Approved admin workflows
o Approved enterprise deployment tooling
· Expand suspicious child classes per tenant standards
· Elevate when suspicious child class aligns with suspicious command-line behavior
· If command-line fidelity is weak, use lower-confidence deployment until telemetry improves
Telemetry Dependency
· Process creation
· Parent process name
· Child process name
· Command line where available
SOC Usage Mode Detail
· Standalone alerting is allowed after suppression validation
· Highest-confidence matches occur when suspicious child class aligns with suspicious command-line behavior
· If command-line visibility is weak, downgrade severity rather than overclaiming certainty
Variant Analysis
· Covers LOLBin substitution by using utility classes
· Covers signed utility abuse through unexpected parent-child relationship
· Covers unknown child executables outside approved child expectations
Rule Regret Check
Deployment caution
Requires strong suppression of legitimate enterprise automation and software-management activity.
Confidence caution
Administrative or packaging activity may resemble this pattern if parent-child expectations are not localized.
Coverage value
Strongest Sigma rule for detecting update-related execution-chain abuse after payload launch.
Production Ready
Yes — with suppression discipline, parent-child baseline enforcement, and command-line quality validation
Portable Sigma rule
title: TrueConf Updater Parent-Child Execution Abuse
id: 7f67d3f5-1d80-42bb-9d0d-trueconf-sigma-002
status: experimental
logsource:
category: process_creation
detection:
selection_parent:
ParentImage|endswith:
- '\trueconf.exe'
- '\trueconf_updater.exe'
selection_child_class:
Image|endswith:
- '\cmd.exe'
- '\powershell.exe'
- '\pwsh.exe'
- '\wscript.exe'
- '\cscript.exe'
- '\mshta.exe'
- '\rundll32.exe'
- '\regsvr32.exe'
- '\schtasks.exe'
- '\sc.exe'
- '\bitsadmin.exe'
- '\wmic.exe'
selection_unapproved_child_path:
Image|contains:
- '\Users\'
- '\AppData\Local\Temp\'
selection_suspicious_cmd:
CommandLine|contains:
- ' -enc '
- 'FromBase64String'
- 'http://'
- 'https://'
- 'sc create'
- 'schtasks /create'
- 'reg add '
filter_approved_workflow:
CommandLine|contains:
- 'approved_admin_workflow_marker'
- 'approved_deployment_workflow_marker'
condition: selection_parent and ((selection_child_class and selection_suspicious_cmd) or selection_unapproved_child_path) and not filter_approved_workflow
fields:
- Image
- ParentImage
- CommandLine
falsepositives:
- Approved software deployment or administrative automation not yet suppressed
level: high
Sigma Limitation Statement
Sigma provides two strong, credible primary detections for this threat and does not credibly provide a third equally strong portable primary rule for bounded sequence correlation across backends without risking overclaim.
In alignment with CyberDax S25 anti-loop and no-filler standards, any more complex sequence logic is intentionally excluded from the main Sigma set unless backend support is proven. The primary Sigma set therefore remains:
· Update-context execution integrity deviation
· Updater parent-child execution abuse
More complex sequence logic should be:
· promoted only where backend support is proven
· or moved into backend-native SIEM content such as Splunk, Elastic, or QRadar
Additional High-Value Detection Candidate
Rule Name
TrueConf Update Context Persistence Immediately After Execution
Purpose
Detect persistence created shortly after execution from approved TrueConf update context where the backend supports reliable bounded sequence logic.
Why it is strong
This can be a very strong detection where the Sigma backend truly preserves bounded sequence behavior across process and persistence telemetry.
Why it is not in the top primary rules
It is excluded from the primary set because Sigma portability degrades quickly when sequence assumptions become backend-specific. In many tenants, this logic is more credibly implemented in Splunk, Elastic, or QRadar than as portable Sigma content.
When it should be deployed
· The Sigma backend supports validated sequence logic
· The backend preserves trustworthy execution-to-persistence correlation
· Approved maintenance workflow allowlists are mature
· Engineering has tested translation fidelity and acceptable noise
Tradeoffs
· Higher analytical value where backend sequence support is strong
· Lower portability across Sigma backends
· Greater risk of overclaim if correlation semantics are not truly preserved
Engineering Note — Required Actions
If promoting this candidate into active deployment:
· validate backend sequence fidelity
· validate persistence telemetry coverage
· confirm that host-only fallback is not being silently substituted for stronger linkage
· downgrade to hunt-only or move to backend-native SIEM content if fidelity is weak
Portable Sigma rule
title: TrueConf Update Context Persistence Immediately After Execution
id: a2f4f0f9-45b0-4f26-91f8-trueconf-sigma-003
status: experimental
logsource:
product: windows
detection:
exec_selection:
Image|contains:
- '\TrueConf\Update\'
- '\TrueConf\Cache\'
- '\TrueConf\Staging\'
persist_registry:
TargetObject|contains:
- '\Software\Microsoft\Windows\CurrentVersion\Run'
- '\Software\Microsoft\Windows\CurrentVersion\RunOnce'
persist_service:
EventType:
- 'ServiceInstalled'
persist_task:
EventType:
- 'ScheduledTaskCreated'
filter_approved_workflow:
CommandLine|contains:
- 'approved_maintenance_workflow_marker'
- 'approved_deployment_workflow_marker'
condition: exec_selection and 1 of persist_* and not filter_approved_workflow
fields:
- Image
- TargetObject
- CommandLine
falsepositives:
- Approved installer or maintenance workflows not yet suppressed
level: medium
Additional High-Value Detection Candidate
Rule Name
TrueConf Update Context External Egress After Execution
Purpose
Detect outbound network communication shortly after execution from approved TrueConf update context where the backend supports reliable execution-to-network sequence handling.
Why it is strong
This can be a very strong detection where the backend preserves trustworthy linkage between process execution and outbound network activity.
Why it is not in the top primary rules
It is excluded from the primary set because Sigma portability degrades quickly when correlation assumptions become backend-specific. In many tenants, this logic is more credibly implemented in Splunk, Elastic, or QRadar than as portable Sigma content.
When it should be deployed
· The Sigma backend supports validated sequence logic
· The backend preserves trustworthy execution-to-network linkage
· Approved destination allowlists are mature
· Engineering has tested translation fidelity and acceptable noise
Tradeoffs
· Higher analytical value where backend correlation is strong
· Lower portability across Sigma backends
· Greater risk of overclaim if correlation semantics are not truly preserved
Engineering Note — Required Actions
If promoting this candidate into active deployment:
· validate backend sequence fidelity
· validate destination allowlists
· confirm that host-only fallback is not being silently substituted for stronger linkage
· downgrade to hunt-only or move to backend-native SIEM content if fidelity is weak
Portable Sigma rule
title: TrueConf Update Context External Egress After Execution
id: c6e90b88-2f8a-4b12-8a8d-trueconf-sigma-004
status: experimental
logsource:
product: windows
detection:
exec_selection:
Image|contains:
- '\TrueConf\Update\'
- '\TrueConf\Cache\'
- '\TrueConf\Staging\'
net_selection:
DestinationHostname|endswith:
- '.example-external-domain.invalid'
DestinationIp|cidr:
- '0.0.0.0/0'
filter_approved_destinations:
DestinationHostname|contains:
- 'approved_trueconf_service_marker'
- 'approved_trueconf_relay_marker'
filter_private_ip_space:
DestinationIp|cidr:
- '10.0.0.0/8'
- '172.16.0.0/12'
- '192.168.0.0/16'
condition: exec_selection and net_selection and not 1 of filter_*
fields:
- Image
- DestinationHostname
- DestinationIp
- CommandLine
falsepositives:
- Backend sequence fidelity not validated
- Approved destinations not yet allowlisted
level: medium
Engineering Note — Sigma
Sigma detection quality depends entirely on:
· Field-mapping quality
· Backend translation fidelity
· Allowlist hygiene
· Maintenance workflow suppression
· Honest restraint around backend-specific correlation limits
Required validation actions before deployment:
· Identify and maintain approved TrueConf update, cache, and staging paths
· Build and maintain allowlists for:
o approved updater parents
o approved child-process expectations
o approved signer expectations
o approved maintenance and deployment workflows
o approved outbound destinations for any promoted correlation candidates
· Validate which Sigma features the backend truly supports
· Do not force correlation-heavy logic into Sigma when Splunk, Elastic, or QRadar provides more reliable implementation
· Keep atomic detections in Sigma and migrate complex correlation where portability degrades
YARA
Rule Name
TrueConf Suspicious Payload Artifact with Network Capability Indicators
Purpose
Detect suspicious PE artifacts delivered through update scope that contain embedded network capability indicators + structural traits inconsistent with standard update binaries
SOC Usage Mode
Hunt-first supporting detection
Standalone Alerting Allowed
No
Minimum Deployment Requirement
· File scanning capability
· Controlled scan scope:
o TrueConf update directories
o staging/cache artifacts
o newly dropped binaries
Enforcement Method
· Must be a PE file
· Must contain:
o network-related string indicator
o AND suspicious developer/debug artifact
· Avoids single-string triggers
Implementation Constraint Notes
· Does NOT rely on path
· Scope must be enforced externally
· Avoids generic strings like "http" alone
· Requires multi-condition matching to reduce noise
Tuning Explanation
· Replace placeholder domains with:
o observed suspicious infrastructure
o uncommon URI patterns
· Maintain exclusion list for:
o legitimate update binaries
o known vendor artifacts
Telemetry Dependency
· File scanning
· Controlled update artifact scope
Variant Analysis
· Evaded by encrypted payloads
· Resistant to simple renaming
· Moderate resistance to light obfuscation
Rule Regret Check
Deployment caution
High FP risk if scanning entire filesystem without scope restriction.
Confidence caution
Detects suspicious artifact traits, not malicious intent or delivery path.
Coverage value
Strong triage rule for newly delivered update artifacts.
Production Ready
Conditionally — requires scoped deployment
Portable YARA rule
rule TrueConf_Suspicious_Update_Artifact_Network_Capability
{
meta:
description = "Suspicious PE with network + debug traits in update-delivered artifacts"
author = "CyberDax"
confidence = "conditional"
scope = "file"
strings:
$net1 = "User-Agent:" ascii
$net2 = "POST /" ascii
$net3 = "GET /" ascii
$dbg1 = ".pdb" ascii
$dbg2 = "debug" ascii nocase
$mz = { 4D 5A }
condition:
uint16(0) == 0x5A4D and
(1 of ($net*)) and
(1 of ($dbg*)) and
filesize < 50MB
}
Rule Name
TrueConf Update Artifact with Suspicious Execution Toolmark Patterns
Purpose
Detect PE artifacts containing execution-enablement toolmarks (LOLBins, scripting indicators, or command fragments) uncommon in legitimate update binaries
SOC Usage Mode
Hunt-first supporting detection
Standalone Alerting Allowed
No
Minimum Deployment Requirement
· File scanning capability
· Controlled scan scope
Enforcement Method
· Must be PE
· Must contain:
o execution toolmarks
o AND suspicious command fragments
· Avoids generic matches
Implementation Constraint Notes
· Avoids relying on:
o cmd.exe alone
o powershell alone
· Requires combination to reduce false positives
Tuning Explanation
· Adjust toolmarks based on:
o enterprise tooling baseline
o allowed scripting usage
· Add exclusions for:
o packaging systems
o automation frameworks
Telemetry Dependency
· File scanning
Variant Analysis
· Resistant to simple string removal
· Weak against heavy obfuscation
Rule Regret Check
Deployment caution
False positives if enterprise automation tools are not excluded.
Confidence caution
Detects suspicious execution-enablement patterns, not actual execution.
Coverage value
Strong supporting signal for suspicious payload capability.
Production Ready
Conditionally — requires allowlist tuning
Portable YARA rule
rule TrueConf_Suspicious_Update_Artifact_Execution_Toolmarks
{
meta:
description = "Suspicious execution-enablement patterns in update-delivered artifacts"
author = "CyberDax"
confidence = "conditional"
scope = "file"
strings:
$tool1 = "powershell" ascii nocase
$tool2 = "cmd.exe" ascii nocase
$tool3 = "rundll32" ascii nocase
$cmd1 = "-enc" ascii
$cmd2 = "FromBase64String" ascii
$cmd3 = "Invoke-" ascii
$mz = { 4D 5A }
condition:
uint16(0) == 0x5A4D and
(1 of ($tool*)) and
(1 of ($cmd*)) and
filesize < 50MB
}
Additional High-Value Detection Candidate
Rule Name
TrueConf Memory-Resident Payload Indicators in Suspicious Process Scope
Purpose
Detect candidate malicious payload content in memory where:
· unpacking has occurred
· payload is visible post-execution
Why it is strong
· Memory reveals:
o decrypted payloads
o unpacked implants
· Often bypasses disk-based evasion
Why it is not primary
· Memory scanning:
o not universally available
o high overhead
o backend dependent
Portable YARA rule
rule TrueConf_Candidate_Memory_Payload_Indicators
{
meta:
description = "Candidate in-memory payload indicators in suspicious process scope"
author = "CyberDax"
confidence = "conditional"
scope = "memory"
strings:
$s1 = "User-Agent:" ascii
$s2 = "POST /" ascii
$s3 = "GET /" ascii
$s4 = "powershell" ascii nocase
$s5 = "cmd.exe" ascii nocase
condition:
2 of ($s*)
}
Engineering Note — YARA
Critical deployment rules:
· NEVER run across full filesystem blindly
· ALWAYS restrict to:
o update artifacts
o staging directories
o suspicious binaries
Validation requirements:
· test against:
o enterprise software
o security tools
o update packages
· validate:
o FP rate
o performance impact
Do not:
· treat YARA hit as compromise
· treat YARA hit as supply-chain proof
· treat YARA hit as execution confirmation
AWS
Rule Name
Suspicious External Egress from AWS-Scoped TrueConf-Associated Workloads
Purpose
Detect outbound communication from explicitly scoped AWS workloads associated with affected infrastructure to unapproved external destinations.
SOC Usage Mode
Alert-capable supporting detection
Standalone Alerting Allowed
Yes — only if all enforcement conditions are met
Minimum Deployment Requirement
· VPC Flow Logs enabled
· ENI or instance tagging for:
o TrueConf-related workloads
o VDI hosts
o update relay systems
· Approved destination allowlist
· Private IP space definition
Enforcement Method
· MUST restrict to:
o ENIs or instances tagged as:
§ TrueConfScope=true
· MUST exclude:
o RFC1918 internal traffic
o approved service endpoints
· MUST require:
o repeated connections OR
o sustained traffic pattern
Implementation Constraint Notes
· This rule is invalid without:
o asset tagging
o destination allowlists
· Must NOT run across all EC2 instances
· Must NOT alert on single connection events
Tuning Explanation
· Maintain:
o Approved_Destinations
o Approved_Service_Domains
· Threshold examples:
o 5+ connections in 10 minutes
o or sustained bytes transferred
Telemetry Dependency
· VPC Flow Logs
· ENI tags
· destination allowlists
Variant Analysis
· Domain rotation still detectable via novelty
· Low-and-slow partially mitigated via repetition thresholds
· Encrypted traffic does not affect detection
Rule Regret Check
Deployment caution
High noise if tagging or allowlists are incomplete.
Confidence caution
Detects suspicious egress, not execution.
Coverage value
Strong cloud-side signal for post-delivery behavior.
Production Ready
Conditionally — requires strict scoping enforcement
Portable AWS implementation model
Data Sources:
- VPC Flow Logs
- EC2 / ENI Tags
- Destination Allowlist
Logic:
- Select flows where:
ENI.Tag.TrueConfScope == true
AND Destination NOT in Approved_Destinations
AND Destination NOT in RFC1918 space
- Aggregate:
Count connections per destination per 10 minutes
- Trigger when:
Connection count >= threshold OR sustained traffic observed
Rule Name
Unauthorized Modification or Overwrite of Update Artifacts in S3 Scope
Purpose
Detect unauthorized or unexpected modification of update-related artifacts in S3 where S3 is part of the distribution chain.
SOC Usage Mode
Alert-capable supporting detection
Standalone Alerting Allowed
Yes — only with strict principal + path enforcement
Minimum Deployment Requirement
· CloudTrail S3 Data Events enabled
· Defined:
o Approved buckets
o Approved prefixes
o Approved principals (roles/users)
· Maintenance window definition
Enforcement Method
· MUST restrict to:
o specific bucket AND prefix
· MUST require:
o object overwrite OR modification event
· MUST validate:
o principal NOT in approved list
OR
o action outside approved maintenance window
Implementation Constraint Notes
· Must NOT run on all S3 activity
· Must enforce BOTH:
o path scope
o principal validation
· Overwrite detection is key signal (not just creation)
Tuning Explanation
· Maintain:
o Approved_Buckets
o Approved_Prefixes
o Approved_Principals
o Maintenance_Windows
· Elevate:
o overwrite + unapproved principal
o overwrite outside window
Telemetry Dependency
· CloudTrail S3 Data Events
· Principal identity
· Bucket/prefix mapping
Variant Analysis
· Compromised credentials reduce signal quality
· Small changes during valid windows may evade detection
· Does not inspect object content
Rule Regret Check
Deployment caution
Fails if bucket and principal scoping are weak.
Confidence caution
Detects suspicious artifact manipulation, not payload maliciousness.
Coverage value
Strong signal for cloud-side artifact tampering.
Production Ready
Conditionally — requires strict scoping + identity control
Portable AWS implementation model
Data Sources:
- CloudTrail S3 Data Events
Logic:
- Monitor:
PutObject
CopyObject
CompleteMultipartUpload
- Conditions:
Bucket IN Approved_Buckets
AND KeyPrefix IN Approved_Prefixes
AND (
Principal NOT IN Approved_Principals
OR EventTime NOT IN Maintenance_Windows
)
AND ObjectOverwrite == true
- Trigger alert
AWS Limitation Statement
AWS provides only 2 strong rules for this threat when applicable.
It does NOT support:
· endpoint execution detection
· updater lineage tracking
· process-level abuse detection
Per S25 standards:
👉 No additional rules are added
👉 No filler is introduced
👉 If AWS scope is absent → mark Not Applicable
Additional High-Value Detection Candidate
Rule Name
Suspicious DNS Resolution from AWS-Scoped Workloads
Purpose
Detect abnormal DNS queries from scoped AWS workloads.
Why it is not primary
· Requires:
o Route 53 logging
o strong domain baselines
· Lower reliability than flow logs
When to deploy
· DNS logging enabled
· domain allowlists mature
Portable AWS implementation model
Data Sources:
- Route 53 Resolver Logs
Logic:
- Select queries where:
Source workload tagged TrueConfScope == true
AND Domain NOT IN Approved_Domains
- Aggregate:
Repeated queries per domain per time window
- Trigger when:
threshold exceeded
Engineering Note — Required Actions
· Validate DNS logging coverage
· Build domain allowlists
· Scope strictly to tagged workloads
· Use hunt-mode first if baseline immature
Engineering Note — AWS
Critical enforcement requirements
· Asset scoping is mandatory
· Destination allowlists are mandatory
· Principal allowlists are mandatory
· Maintenance windows must exist
Do not:
· deploy globally
· assume AWS relevance
· treat AWS alerts as proof of compromise
GCP
Rule Name
Scoped GCP Workload External Egress Anomaly
Purpose
Detect outbound communication from explicitly scoped GCP workloads to unapproved external destinations using enforceable workload identity and repetition thresholds.
SOC Usage Mode
Alert-capable supporting detection
Standalone Alerting Allowed
Yes — only when all enforcement conditions are met
Minimum Deployment Requirement
· VPC Flow Logs enabled
· Instance labeling or equivalent inventory mapping:
o TrueConfScope=true
· Approved destination allowlists
· Private IP space definition
· Project-level scope definition
Enforcement Method
· Must bind to:
o instance_id, vm_name, or equivalent workload identity
· Must enforce:
o resource label or equivalent scoped inventory mapping
· Must exclude:
o RFC1918/private traffic
o approved destinations
· Must require:
o repeated connections threshold
o or sustained traffic threshold
· Must remain scoped to approved GCP projects or folders where the workload actually exists
Implementation Constraint Notes
· Invalid if:
o instance labeling or equivalent inventory scope is absent
o destination allowlist is absent
o project scope is not defined
· Must not:
o run across all projects indiscriminately
o alert on single connection events
· Resource identity must be part of the detection logic, not just analyst interpretation
Tuning Explanation
· Maintain:
o Approved_Destinations
o Approved_Service_Domains
o Scoped_GCP_Projects
· Threshold example:
o five or more connections per destination per 10 minutes
o or sustained byte transfer threshold
· Elevate when:
o destination is new or rare in the scoped workload set
o traffic begins near other suspicious cloud-side events in the same workload scope
Telemetry Dependency
· VPC Flow Logs
· Instance labels or scoped workload inventory
· Project identifiers
· Destination allowlists
SOC Usage Mode Detail
· Standalone alerting is allowed only when workload scope and destination baselines are validated
· Highest-confidence use occurs when repeated external egress aligns with other scoped suspicious activity
Variant Analysis
· Destination rotation remains partially detectable through novelty
· Low-and-slow can be partly mitigated via repeated-connection logic
· Encryption does not affect destination-based detection
Rule Regret Check
Deployment caution
Fails if labeling, project scoping, or destination allowlists are incomplete.
Confidence caution
Detects anomalous egress only, not execution or compromise.
Coverage value
Strong cloud-side behavioral signal where GCP workloads are actually relevant to the threat.
Production Ready
Conditionally — requires strict workload identity, project scope, and destination enforcement
Portable GCP implementation model
Data Sources:
- VPC Flow Logs
Logic:
- Select flows where:
project_id IN Scoped_GCP_Projects
AND instance.label.TrueConfScope == true
AND destination NOT IN Approved_Destinations
AND destination NOT IN Private_IP_Ranges
- Aggregate:
count(destination_connections) BY project_id, instance_id, destination, 10m window
- Trigger when:
connection_count >= threshold
OR sustained_bytes >= threshold
Rule Name
Unauthorized Update Artifact Modification in GCS Scope
Purpose
Detect unauthorized modification, overwrite, rewrite, or deletion of update artifacts in Google Cloud Storage using strict identity, path, and mutation-action coupling.
SOC Usage Mode
Alert-capable supporting detection
Standalone Alerting Allowed
Yes — only with full enforcement
Minimum Deployment Requirement
· Cloud Audit Logs Data Access enabled for GCS
· Defined:
o approved projects
o approved buckets
o approved object prefixes
o approved service accounts
· maintenance windows defined
Enforcement Method
· Must enforce all of the following simultaneously:
o project scope
o bucket scope
o object-prefix scope
o mutation-action type
o service account validation
· Must detect:
o overwrite
o rewrite
o delete
o update or metadata mutation where operationally relevant
· Must require:
o service account not approved
o or action outside maintenance window
Implementation Constraint Notes
· Must not:
o monitor all buckets globally
o trigger on read-only activity
o treat generic object creation as equal to overwrite or rewrite without artifact context
· Overwrite, rewrite, and delete are higher-value signals than generic object creation
· Identity and action must be evaluated together, not independently
· This rule is invalid if Data Access logging is not enabled for the relevant GCS scope
Tuning Explanation
· Maintain:
o Scoped_GCP_Projects
o Approved_Buckets
o Approved_Prefixes
o Approved_Service_Accounts
o Maintenance_Windows
· Elevate when:
o overwrite or rewrite is performed by unapproved identity
o delete occurs outside an approved window
o repeated modification attempts occur in the same prefix
Telemetry Dependency
· Cloud Audit Logs Data Access for GCS
· principalEmail
· project, bucket, and object-prefix mapping
· maintenance-window context
SOC Usage Mode Detail
· Standalone alerting is allowed only when project, bucket, prefix, and identity baselines are validated
· Highest-confidence use occurs when suspicious artifact modification aligns with downstream workload anomalies
Variant Analysis
· Compromised service accounts reduce signal quality
· Valid actions inside approved windows reduce sensitivity
· This rule does not inspect payload content and must not claim to
Rule Regret Check
Deployment caution
Fails if identity, prefix, or Data Access coverage is incomplete.
Confidence caution
Detects suspicious artifact manipulation, not malicious payload content.
Coverage value
Strong cloud-side artifact integrity signal where GCS participates in relevant artifact workflows.
Production Ready
Conditionally — requires strict identity, project, and scope enforcement
Portable GCP implementation model
Data Sources:
- Cloud Audit Logs (GCS Data Access)
Logic:
- Select events where:
project_id IN Scoped_GCP_Projects
AND bucket IN Approved_Buckets
AND object_prefix IN Approved_Prefixes
AND methodName IN (
"storage.objects.update",
"storage.objects.delete",
"storage.objects.rewrite"
)
- Condition:
principalEmail NOT IN Approved_Service_Accounts
OR timestamp NOT IN Maintenance_Windows
- Trigger alert
Additional High-Value Detection Candidate
Rule Name
Scoped GCP DNS Query Anomaly
Purpose
Detect abnormal DNS queries from scoped GCP workloads using strict workload identity binding, domain allowlisting, and repetition thresholds.
Why it is strong
This can be strong where:
· Cloud DNS logging is enabled
· scoped workload labels are mature
· domain allowlists are well maintained
Why it is not primary
It is excluded from the main set because:
· Cloud DNS logging is not always enabled
· domain baselines vary significantly
· flow-based detection is usually stronger and more direct
When it should be deployed
· Cloud DNS logging is enabled
· GCP workload scope is relevant to the threat
· approved domain allowlists are mature
· engineering has validated acceptable noise
Tradeoffs
· good visibility into outbound intent
· less direct than flow telemetry
· noisy without mature domain baselines
Portable GCP implementation model
Data Sources:
- Cloud DNS Logs
Logic:
- Select queries where:
project_id IN Scoped_GCP_Projects
AND instance.label.TrueConfScope == true
AND domain NOT IN Approved_Domains
- Aggregate:
count(domain_queries) BY project_id, instance_id, domain, time window
- Trigger when:
threshold exceeded
Engineering Note — Required Actions
If promoting this candidate into active deployment:
· validate Cloud DNS logging coverage
· validate approved domain allowlists
· scope strictly to labeled workloads in approved projects
· use hunt mode first if domain baselines are immature
Engineering Note — GCP
GCP detection quality depends entirely on:
· whether the tenant actually has relevant TrueConf-associated scope in GCP
· VPC Flow Log coverage
· Cloud Audit Logs Data Access coverage for GCS
· Cloud DNS log coverage where applicable
· workload labeling discipline
· service account allowlists
· maintenance-window context
· disciplined suppression of legitimate maintenance and deployment workflows
Required validation actions before deployment:
· confirm whether any relevant TrueConf-associated assets or telemetry pipelines exist in GCP
· identify and maintain approved workload inventory and project scope
· identify and maintain approved GCS buckets and object prefixes where applicable
· build and maintain allowlists for:
o approved outbound destinations
o approved domains
o approved service accounts
o approved maintenance windows
· do not force GCP detections where the threat has no meaningful GCP footprint
S26 Threat-to-Rule Traceability Matrix
Methodology Enforcement Statement
This matrix enforces CyberDax v2.6 rule-accountability requirements:
· Every material threat behavior is mapped to at least one detection rule or explicitly declared as Not Covered or Conditional
· Coverage disposition is assigned using allowed values: Detected, Partially Detected, Hunt Only, Not Covered, Not Applicable
· Every mapped detection includes telemetry dependency, system ownership, and enforcement realism
· No behavior is left unmapped without justification
This matrix has undergone adversarial validation, anti-loop validation, coverage completeness validation, and telemetry realism validation.
Behavior 1 — Malicious Update Payload Delivery via Trusted Channel
MITRE ATT&CK
T1195.002 — Supply Chain Compromise: Compromise Software Supply Chain
Behavior Description
Malicious code is delivered through the legitimate TrueConf update mechanism.
Detection Coverage
· YARA Rule 1 — Suspicious Payload Artifact with Network Capability Indicators
· YARA Rule 2 — Suspicious Execution Toolmark Artifact
· AWS Rule 2 — S3 Artifact Modification (Conditional)
· Azure Rule 2 — Storage Artifact Modification (Conditional)
· GCP Rule 2 — GCS Artifact Modification (Conditional)
Coverage Disposition
Partially Detected
Telemetry Dependency
· File scanning
· Cloud storage logs
· Artifact scope baselines
Coverage Rationale
Payload presence can be detected via content inspection. Cloud storage anomalies may indicate staging manipulation. Delivery through the trusted update channel itself is not directly observable.
Behavior 2 — Execution of Malicious Payload in Update Context
MITRE ATT&CK
T1204 — User Execution
T1059 — Command and Scripting Interpreter
Behavior Description
Malicious payload executes under trusted updater context.
Detection Coverage
· SentinelOne Rule Set — Execution Context Abuse
· Sigma Rule 1 — Update Context Execution Integrity Deviation
· Splunk Rule Set — Execution Anomaly Detection
· Elastic Rule Set — Execution Context Deviation
Coverage Disposition
Detected
Telemetry Dependency
· Endpoint process telemetry
· Parent-child lineage
· Execution path context
· Signer validation
Coverage Rationale
Strong endpoint and SIEM detections exist. Multiple systems independently detect execution anomalies with high reliability.
Behavior 3 — Parent-Child Execution Abuse from Updater
MITRE ATT&CK
T1036 — Masquerading
T1059 — Command and Scripting Interpreter
Behavior Description
Updater spawns unexpected child processes such as shells or scripting engines.
Detection Coverage
· SentinelOne Rule Set — Parent-Child Abuse
· Sigma Rule 2 — Updater Parent-Child Execution Abuse
· Splunk Rule Set — Suspicious Process Lineage
· Elastic Rule Set — Parent-Child Anomaly Detection
Coverage Disposition
Detected
Telemetry Dependency
· Process creation logs
· Parent-child lineage
· Command-line telemetry
Coverage Rationale
Cross-platform behavioral detection is strong and consistent. Signal quality is high when baselines are enforced.
Behavior 4 — Post-Execution Persistence Establishment
MITRE ATT&CK
T1547 — Boot or Logon Autostart Execution
T1053 — Scheduled Task/Job
Behavior Description
Attacker establishes persistence after payload execution.
Detection Coverage
· SentinelOne Rule Set — Persistence Detection
· Splunk Rule Set — Persistence Creation Detection
· Elastic Rule Set — Persistence Indicators
· Sigma Additional Candidate — Conditional
Coverage Disposition
Detected
Telemetry Dependency
· Registry telemetry
· Task scheduler logs
· Service creation logs
· Endpoint monitoring
Coverage Rationale
Endpoint and SIEM coverage is strong. Persistence actions produce high-signal telemetry.
Behavior 5 — Outbound Command and Control Communication
MITRE ATT&CK
T1071 — Application Layer Protocol
T1095 — Non-Application Layer Protocol
Behavior Description
Compromised system communicates with attacker-controlled infrastructure.
Detection Coverage
· Suricata Rule Set — Network Communication Detection
· Splunk Rule Set — Network Correlation
· Elastic Rule Set — Network Anomaly Detection
· AWS Rule 1 — Egress Anomaly (Conditional)
· Azure Rule 1 — Egress Anomaly (Conditional)
· GCP Rule 1 — Egress Anomaly (Conditional)
Coverage Disposition
Detected
Telemetry Dependency
· Network telemetry
· DNS logs where available
· Endpoint network events
Coverage Rationale
Detection is strong across IDS, SIEM, and conditional cloud telemetry. Reliability is high when baselines are enforced.
Behavior 6 — Artifact Staging or Tampering in Cloud Storage
MITRE ATT&CK
T1565 — Data Manipulation
Behavior Description
Malicious artifacts are staged or modified in cloud storage.
Detection Coverage
· AWS Rule 2 — S3 Modification Detection
· Azure Rule 2 — Blob Modification Detection
· GCP Rule 2 — GCS Modification Detection
Coverage Disposition
Detected
Telemetry Dependency
· Cloud storage audit logs
· Identity telemetry
· Path and prefix baselines
Coverage Rationale
Detection is strong where cloud storage is used. Effectiveness depends on proper scoping and logging.
Behavior 7 — DNS-Based Command and Control or Discovery
MITRE ATT&CK
T1071.004 — Application Layer Protocol: DNS
Behavior Description
Compromised system performs DNS queries to attacker-controlled domains.
Detection Coverage
· AWS DNS Candidate
· Azure DNS Candidate
· GCP DNS Candidate
Coverage Disposition
Hunt Only
Telemetry Dependency
· DNS logs
· Domain allowlists
· Query frequency baselines
Coverage Rationale
Detection quality depends on logging availability and baseline maturity. Best used as enrichment or hunting signal.
Behavior 8 — Supply Chain Trust Abuse (Vendor Integrity Compromise)
MITRE ATT&CK
T1195 — Supply Chain Compromise
Behavior Description
Attacker compromises the trusted update mechanism itself.
Detection Coverage
No direct detection coverage
Coverage Disposition
Not Covered
Telemetry Dependency
External vendor visibility only
Coverage Rationale
This behavior occurs outside enterprise visibility. Detection depends on downstream signals and vendor disclosures.
Coverage Validation Summary
Detected Behaviors
· Execution in update context
· Parent-child abuse
· Persistence establishment
· Network communication
· Cloud artifact manipulation
Partially Detected Behaviors
· Malicious payload delivery
Hunt Only Behaviors
· DNS-based activity
Not Covered Behaviors
· Vendor-side supply chain compromise
S27 Behavior & Log Artifacts
Behavioral Telemetry Model
This section maps observable behavior across the three primary telemetry pillars: email security gateway telemetry, endpoint and EDR process telemetry, and DNS, web proxy, or network telemetry. Detection emphasis is placed on correlated behavioral evidence across pillars rather than isolated indicators, because the trusted-update delivery stage itself is only partially visible while post-delivery execution and follow-on activity are materially observable.
Update Context Execution Anomaly
Primary Telemetry Source
Endpoint and EDR
Observable Artifacts
· Process execution from approved update, cache, or staging paths outside expected updater lineage
· Execution from writable or temp-adjacent update-context paths
· Unsigned, invalidly signed, or low-prevalence binaries launched in update context
· Execution by unexpected parent processes or from abnormal execution chains
Correlated Signals
· Suspicious child-process spawning shortly after execution
· External communication or rare destination access shortly after launch
· Persistence-related activity following the same execution chain
Detection Value
High. This is one of the strongest early observable indicators because it captures the transition from trusted delivery context into suspicious local execution.
Parent-Child Process Abuse
Primary Telemetry Source
Endpoint and EDR
Observable Artifacts
· Updater or TrueConf-associated processes spawning shells, scripting engines, or dual-use administrative utilities
· Unexpected child processes outside approved updater lineage
· Command-line patterns associated with encoded execution, remote retrieval, persistence creation, or system modification
Correlated Signals
· Immediate persistence actions
· Outbound communication from the same process or process tree
· Additional suspicious children in the same lineage chain
Detection Value
Very High. This is one of the most reliable post-delivery abuse signals because legitimate updater behavior should rarely produce these execution chains.
Persistence Establishment
Primary Telemetry Source
Endpoint and EDR
Observable Artifacts
· Run or RunOnce registry modification
· Scheduled task creation
· Service creation or modification
· Startup persistence where telemetry captures it
· Persistence activity occurring shortly after suspicious update-context execution
Correlated Signals
· Prior execution anomaly
· Prior parent-child abuse
· Subsequent outbound communication or repeated tasking behavior
Detection Value
High. Persistence is not the earliest signal, but it is a durable and high-confidence indicator of post-execution compromise activity.
Outbound Network Communication
Primary Telemetry Source
DNS and Network
Observable Artifacts
· External connections to destinations outside approved service expectations
· Repeated communication to rare, new, or low-prevalence domains or IPs
· Beacon-like or periodic traffic patterns
· Outbound communication initiated shortly after suspicious update-context execution
Correlated Signals
· Endpoint execution anomalies
· Parent-child abuse
· DNS query anomalies involving the same destination set
Detection Value
High when correlated with endpoint evidence. Network activity alone may be noisy, but it becomes materially stronger when it follows suspicious execution in update context.
DNS Anomaly Activity
Primary Telemetry Source
DNS and Web Proxy
Observable Artifacts
· Queries to rare, new, or unapproved domains
· Repeated query bursts to the same domain or cluster
· Resolution behavior inconsistent with approved TrueConf-related communications
Correlated Signals
· Subsequent outbound network communication
· Endpoint execution anomalies
· Cloud-side scoped egress anomalies where applicable
Detection Value
Moderate. DNS is valuable as enrichment and early warning, but reliability depends on logging coverage, domain baselines, and correlation with stronger endpoint or network evidence.
Cloud Artifact Manipulation
Primary Telemetry Source
Cloud Control Plane
Observable Artifacts
· Object overwrite, rewrite, deletion, or mutation in approved storage scope
· Access from unapproved identities or principals
· Changes outside approved maintenance windows
· Artifact manipulation in tightly scoped cloud storage locations associated with update or relay workflows
Correlated Signals
· Downstream endpoint execution anomalies
· Scoped cloud workload egress anomalies
· Timing alignment with suspicious administrative actions
Detection Value
Conditional High. This is strong only where cloud storage is actually part of the tenant’s relevant architecture and logging plus scope enforcement are mature.
Suspicious Artifact Content
Primary Telemetry Source
File and Memory Inspection
Observable Artifacts
· Executables with suspicious network-capability indicators or execution toolmarks
· Memory-resident payload indicators in suspicious process scope
· Content traits inconsistent with normal signed update artifacts
Correlated Signals
· Endpoint execution anomalies
· Persistence or outbound communication
· Scoped artifact staging anomalies in cloud storage where applicable
Detection Value
Supporting. Content inspection is useful for triage and enrichment but is not sufficient to prove update abuse or execution by itself.
Early Detection Correlation Model
High-confidence early detection occurs when at least two of the following align within a bounded timeframe:
· Update-context execution anomaly
· Parent-child process abuse
· Outbound network communication anomaly
Maximum confidence occurs when all three are present, because that combination materially reduces ambiguity between benign update activity and malicious post-delivery abuse.
Detection Strategy and SOC Implementation Guidance
Detection Strategy Overview
Detection strategy is behavior-driven and correlation-led rather than signature-dependent. The core objective is to identify the transition from trusted update context into suspicious execution, follow-on abuse, and external communication. Single weak signals should not be treated as sufficient proof of compromise unless the system-specific rule explicitly supports standalone alerting under validated baselines.
SOC Detection Model
Tier 1 Detection
· Update-context execution anomaly combined with parent-child abuse
· Update-context execution anomaly combined with suspicious external communication
· Parent-child abuse combined with immediate persistence creation
Tier 2 Detection
· Update-context execution anomaly alone where the rule is explicitly standalone-capable and baseline maturity is validated
· Parent-child abuse alone where approved updater lineage and workflow suppression are mature
· Cloud artifact manipulation aligned with scoped workload anomalies in cloud-relevant environments
Tier 3 Detection
· DNS anomalies
· YARA or memory-content hits
· Cloud DNS or cloud-side enrichment signals
· Artifact-content anomalies without corroborating behavioral evidence
Tier assignment is based on deployment realism, signal strength, and the degree to which the underlying telemetry can independently support alerting.
Implementation Guidance
SOC Workflow Requirements
· Maintain baselines for approved update paths, updater parents, outbound destinations, cloud storage scope, identities, and maintenance workflows
· Enforce system-specific deployment constraints exactly as written in S25
· Require correlation across endpoint, network, and cloud telemetry where standalone alerting is not explicitly allowed
· Downgrade detections to hunt or triage mode when required telemetry fidelity is not validated
Alert Handling Guidance
· Do not escalate single weak signals as confirmed compromise
· Prioritize detections that show transition from trusted update context into suspicious execution behavior
· Escalate immediately when execution anomaly, lineage abuse, and outbound communication align
· Treat cloud-side anomalies as supporting evidence unless the architecture makes them directly relevant to the affected workflow
False Positive Management
· Suppress approved maintenance, deployment, packaging, and administrative workflows
· Maintain destination, identity, artifact, and path allowlists as controlled operational baselines
· Revalidate baselines after legitimate updater changes, release-process changes, or infrastructure migration
· Avoid relying on generic temp-path or generic network-anomaly logic without explicit scoping
This strategy keeps the detection model aligned to observable behavior and prevents false confidence from weak or loosely correlated signals.
Figure 5
S28 Detection Strategy and SOC Implementation Guidance
Detection Strategy Overview
Detection strategy is behavior-driven and correlation-led rather than signature-dependent. The core objective is to identify the transition from trusted update context into suspicious execution, follow-on abuse, and external communication. Single weak signals should not be treated as sufficient proof of compromise unless the system-specific rule explicitly supports standalone alerting under validated baselines.
SOC Detection Model
Tier 1 Detection
· Update-context execution anomaly combined with parent-child abuse
· Update-context execution anomaly combined with suspicious external communication
· Parent-child abuse combined with immediate persistence creation
Tier 2 Detection
· Update-context execution anomaly alone where the rule is explicitly standalone-capable and baseline maturity is validated
· Parent-child abuse alone where approved updater lineage and workflow suppression are mature
· Cloud artifact manipulation aligned with scoped workload anomalies in cloud-relevant environments
Tier 3 Detection
· DNS anomalies
· YARA or memory-content hits
· Cloud DNS or cloud-side enrichment signals
· Artifact-content anomalies without corroborating behavioral evidence
Tier assignment is based on deployment realism, signal strength, and the degree to which the underlying telemetry can independently support alerting.
Implementation Guidance
SOC Workflow Requirements
· Maintain baselines for approved update paths, updater parents, outbound destinations, cloud storage scope, identities, and maintenance workflows
· Enforce system-specific deployment constraints exactly as written in S25
· Require correlation across endpoint, network, and cloud telemetry where standalone alerting is not explicitly allowed
· Downgrade detections to hunt or triage mode when required telemetry fidelity is not validated
Alert Handling Guidance
· Do not escalate single weak signals as confirmed compromise
· Prioritize detections that show transition from trusted update context into suspicious execution behavior
· Escalate immediately when execution anomaly, lineage abuse, and outbound communication align
· Treat cloud-side anomalies as supporting evidence unless the architecture makes them directly relevant to the affected workflow
False Positive Management
· Suppress approved maintenance, deployment, packaging, and administrative workflows
· Maintain destination, identity, artifact, and path allowlists as controlled operational baselines
· Revalidate baselines after legitimate updater changes, release-process changes, or infrastructure migration
· Avoid relying on generic temp-path or generic network-anomaly logic without explicit scoping
This strategy keeps the detection model aligned to observable behavior and prevents false confidence from weak or loosely correlated signals.
S29 Detection Coverage Summary
Detected Behaviors
· Execution in update context
· Parent-child abuse
· Persistence establishment
· Outbound communication
· Cloud artifact manipulation where relevant architecture and logging exist
Partially Detected Behaviors
· Malicious payload delivery through the trusted channel
· Early cloud-side staging anomalies where cloud scope is only partially relevant
Hunt Only Behaviors
· DNS-based activity in environments with immature baselines
· Suspicious artifact content and memory indicators without corroborating behavioral evidence
· Cloud DNS enrichment signals where logging exists but confidence is limited
Not Covered Behaviors
· Vendor-side supply chain compromise at the vendor control-plane level
· Direct proof of malicious vendor update generation before enterprise delivery
Detection Strength Assessment
Strong Coverage Areas
· Endpoint behavioral detection
· Process lineage abuse
· Correlated execution-to-network transition
· Persistence detection after suspicious execution
Moderate Coverage Areas
· Cloud artifact manipulation in cloud-relevant architectures
· DNS anomaly activity where logging and baselines are mature
· Artifact-content inspection as supporting evidence
Weak Coverage Areas
· Initial trusted delivery vector before local execution
· Vendor integrity compromise outside enterprise visibility
· Highly delayed or extremely low-and-slow follow-on activity without corroborating telemetry
This summary aligns with S25 and S26 by preserving honest coverage boundaries and avoiding artificial inflation of detection capability.
S30 Intelligence Maturity Assessment
Detection Maturity Level
Moderately Mature to Mature
Assessment Across Key Domains
Threat Detection
Strong. Behavioral detection across endpoint and network telemetry is well developed and reinforced by multi-platform rule coverage.
Telemetry Coverage
Moderate to Strong. Endpoint and network visibility are strong; cloud visibility is conditional and architecture-dependent; vendor-side visibility remains out of scope.
Detection Engineering
Strong. Rule content is behavior-based, enforceable, system-specific, and hardened against fake correlation, overclaim, and filler-rule drift.
Response Readiness
Moderate. Detection quality is high, but response speed and confidence still depend on correlation maturity, workflow discipline, and baseline hygiene.
Security Hardening
Moderate. Control effectiveness depends heavily on maintaining approved path, identity, signer, and destination baselines without drift.
Key Maturity Strengths
· Multi-layer behavioral detection model
· Strong endpoint and SIEM correlation coverage
· Cross-platform rule consistency
· Honest conditional handling of cloud systems
· Reduced dependence on signatures for primary detection
Key Maturity Gaps
· Limited visibility into vendor-side compromise
· Dependence on baseline accuracy and maintenance discipline
· DNS detection quality varies by environment
· Cloud detections are only strong where architecture makes them relevant
· Some high-value correlation paths depend on mature telemetry normalization
Maturity Improvement Priorities
· Strengthen baseline management for paths, lineage, identities, and destinations
· Increase automation for cross-pillar correlation and downgrade logic when fidelity is weak
· Expand and validate DNS logging and domain-baseline maturity where operationally justified
· Regularly validate cloud logging coverage and conditional applicability before enabling cloud rules
· Reassess persistence and egress promotion logic as telemetry quality changes across tenants
Control Effectiveness Score
High for post-execution detection
Moderate for early-stage behavioral detection
Low for vendor-side compromise detection outside enterprise visibility
Audit Evidence Statement
Detection coverage is derived from validated telemetry sources and enforceable detection logic across endpoint, network, content-inspection, and conditional cloud layers. All major observable behaviors are either mapped to credible detection capability or explicitly identified as partial, hunt-only, or not covered.
Security Program Integration Note
These detection capabilities align with existing SOC workflows, SIEM correlation models, cloud monitoring controls, and detection engineering pipelines. Integration does not require structural changes, but it does require disciplined baseline maintenance, telemetry validation, and continued enforcement of system-specific deployment constraints.
S31 Mitigation and Remediation
Containment
· Immediately isolate endpoints that executed updates during the identified exposure window
· Restrict access to update distribution systems until integrity is confirmed
Validation
· Validate the integrity of update distribution mechanisms and confirm no unauthorized payload substitution has occurred
· Identify all systems that received updates from potentially influenced delivery paths to determine full exposure scope
Eradication
· Upgrade all affected TrueConf client systems to version 8.5.3 or later to remove the vulnerable update behavior
· Rebuild or reimage systems where update integrity cannot be confidently verified
Recovery
· Reset credentials associated with administrative access, update distribution systems, and affected endpoints
· Confirm update delivery paths can no longer be influenced through misconfiguration, unauthorized access, or infrastructure exposure
Figure 6
S32 Security Control Recommendations
Artifact Integrity Controls
· Enforce cryptographic signing and verification of all update artifacts prior to execution
· Reject update content that fails integrity validation
· Maintain authoritative baselines of approved update artifacts and continuously validate against them
Dependency Governance Controls
· Establish governance over internally distributed update packages and client update mechanisms
· Maintain controlled distribution paths and prevent unauthorized modification of update payloads
· Continuously validate integrity of update packages across distribution systems
CI/CD Execution Controls
· Secure release and update distribution workflows to prevent unauthorized insertion of malicious payloads into update mechanisms
· Enforce separation of duties between build, approval, and release functions where applicable to update distribution infrastructure
· Validate release artifacts immediately prior to distribution
Credential Security Controls
· Protect credentials associated with update distribution systems and release infrastructure
· Enforce strong authentication and access controls for systems capable of influencing update delivery
· Monitor for anomalous access targeting update-related systems
Access and Release Infrastructure Controls
· Restrict access to update servers and distribution mechanisms to authorized roles
· Continuously monitor and audit update configuration and distribution path changes
· Enforce strict change control over update infrastructure
S33 Strategic Defensive Improvements
Control Impact Mapping
· Integrity validation controls
Prevent execution of malicious payloads delivered through trusted update workflows
· Update distribution governance controls
Reduce attacker ability to influence delivery paths and limit multi-endpoint propagation
· Endpoint execution monitoring controls
Enable detection of malicious activity executing within trusted updater context
· Network behavior monitoring controls
Detect post-execution communication anomalies originating from update processes
Strategic Improvements
· Treat all software update mechanisms as high-risk trust boundaries requiring validation
· Integrate update distribution security into enterprise security architecture and governance
· Implement continuous validation of software delivery and update paths
· Expand behavioral monitoring to include execution within trusted processes such as updaters
· Replace implicit trust in software delivery with validation-driven control models
S34 Defensive Architecture Overview
Upstream Integrity Layer
Enforces trust validation at the point of software distribution. Update mechanisms are treated as external-equivalent trust boundaries requiring strict control over artifact integrity and release authorization.
Pipeline Execution Layer
Provides visibility into execution within update workflows. Monitoring focuses on process lineage, execution context, and deviations from expected update behavior.
Monitoring and Response Layer
Correlates endpoint execution anomalies with network behavior to identify malicious activity originating from update-context processes and enable rapid containment.
S35 Security Hardening Guidance
· Enforce mandatory cryptographic validation for all update mechanisms
· Harden update distribution infrastructure with strict access controls and monitoring
· Restrict execution privileges of update processes
· Implement application control policies for update-related execution paths
· Enable detailed logging of update execution, file changes, and network activity
· Segment update infrastructure from broader network environments
· Conduct regular audits of update workflows and distribution paths
S36 Security Program Maturity Assessment
Current Maturity State
Moderate — organizations typically monitor endpoint activity but do not validate execution within trusted update workflows, creating a systemic detection blind spot
Risk Alignment
Security programs are not fully aligned to supply chain threats that exploit trusted software delivery mechanisms, as controls often assume trust rather than validate it
Maturity Improvement Priorities
· Implement integrity validation across all software distribution mechanisms
· Establish monitoring for execution within trusted processes such as update clients
· Strengthen governance over update distribution infrastructure
· Align response processes to handle multi-endpoint compromise scenarios
S37 Residual Risk and Forward Outlook
Residual risk remains due to reliance on trusted software distribution mechanisms. While remediation addresses this vulnerability, the broader class of update-channel compromise remains a persistent threat.
This represents a recurring enterprise risk driven by implicit trust in software delivery systems. Attackers will continue to target update mechanisms due to their scalability and reduced visibility during execution.
Organizations must treat update workflows as a persistent attack surface and implement continuous validation, monitoring, and governance to reduce exposure.
Figure 7
S38 Intelligence Confidence Assessment
Overall Confidence Level
Moderate to High
Source Reliability
High — based on vendor-provided update information and confirmed KEV inclusion
Analytical Confidence Drivers
· Confirmed exploitation status
· Clearly defined vulnerability mechanism involving update integrity failure
· Strong alignment with supply chain attack patterns
Confidence Limitations
· Limited visibility into how the update delivery path was influenced
· Lack of detailed reporting on post-execution activity
Intelligence Gaps
· Specific mechanism used to influence update distribution
· Detailed attacker workflow beyond update execution
· Attribution to a specific threat actor
S39 Analytical Notes and Limitations
· Analysis is based on vendor disclosures and public reporting with limited insight into attacker control of update distribution
· Post-exploitation behavior is not fully documented and is treated as conditional
· Detection strategy emphasizes behavioral signals due to lack of reliable infrastructure indicators
· Analysis focuses on exploitation mechanics rather than attribution
S40 References
Vendor Advisory
Vendor-issued update addressing CVE-2026-3502 in TrueConf Client (security fix included in TrueConf 8.5 release)
· hxxps://trueconf[.]com/blog/update/trueconf-8-5
Vulnerability Records
CVE-2026-3502 vulnerability record and technical details
· hxxps://nvd.nist[.]gov/vuln/detail/CVE-2026-3502
Known Exploited Vulnerabilities (KEV)
CISA KEV Catalog entry confirming active exploitation of CVE-2026-3502
· hxxps://www.cisa[.]gov/known-exploited-vulnerabilities-catalog
Analytical Framework
MITRE ATT&CK Framework
hxxps://attack[.]mitre[.]org