Chrome Zero-Day Pair (CVE-2026-3909, CVE-2026-3910) Enables Remote Browser Exploitation via Skia Memory Corruption and V8 Engine Flaws
BLUF
Enterprise organizations face elevated security risk from the Chrome vulnerability pair CVE-2026-3909 and CVE-2026-3910 because browser exploitation can transform routine web activity into an enterprise endpoint compromise vector. The vulnerabilities affect core browser components responsible for graphics rendering and JavaScript execution, specifically the Skia graphics library and the V8 engine that process untrusted web content delivered through external websites. Both vulnerabilities appear in the CISA Known Exploited Vulnerabilities catalog, confirming that exploitation activity has been observed in the wild and that organizations should treat the issue as an active operational exposure. Executive leadership should prioritize accelerated browser patch deployment, verification of Chromium-based browser exposure across enterprise endpoints, and monitoring for suspicious browser process activity.
S2B – Threat Severity Indicator
Threat Severity
High
Confidence Level
High
Primary Risk Domain
Enterprise Endpoint Compromise
Operational Risk Category
Known Exploited Browser Vulnerability Pair
Executive Risk Signals
Threat Severity
High
Exploit Maturity
Known Exploited Vulnerability
SOC Action Priority
Immediate Mitigation
Executive Risk Translation
If exploitation of CVE-2026-3909 or CVE-2026-3910 occurs inside an enterprise environment, attackers may leverage malicious web content to compromise browser processes running on user workstations. A compromised browser session may enable malware execution, credential harvesting, or follow-on intrusion activity across enterprise systems.
S2A – Why This Matters Now
Browser vulnerabilities remain strategically important because enterprise users rely heavily on browsers to access external websites, internal business platforms, and cloud services.
Several factors increase the operational significance of this vulnerability pair.
• Both vulnerabilities appear in the CISA Known Exploited Vulnerabilities catalog, indicating that confirmed exploitation activity has been observed and remediation should be treated as urgent.
• Chromium-based browsers are widely deployed across enterprise environments, meaning vulnerabilities affecting core rendering or scripting components may expose large numbers of endpoints simultaneously.
• Browser exploitation can occur during routine browsing activity, allowing attackers to deliver malicious content without requiring software installation or administrative privileges.
• Browser compromise frequently serves as an initial access mechanism that enables credential theft, malware deployment, or follow-on ransomware intrusion activity.
These conditions increase the likelihood that exploited browser vulnerabilities may create enterprise exposure before patching is completed across the environment.
S3 – Key Judgments
Based on vendor security disclosures, CISA Known Exploited Vulnerabilities catalog listings, and established patterns of browser exploitation observed in enterprise intrusion activity, the following analytical judgments can be made.
• The presence of CVE-2026-3909 and CVE-2026-3910 in the CISA Known Exploited Vulnerabilities catalog indicates that adversaries have already demonstrated operational capability to exploit these vulnerabilities in real-world environments.
• Vulnerabilities affecting core browser components such as the Skia graphics library and the V8 JavaScript engine present elevated enterprise risk because these components routinely process untrusted web content encountered during normal browsing activity.
• Browser exploitation vulnerabilities are frequently used as initial access mechanisms because they allow attackers to deliver malicious content through legitimate web browsing workflows without requiring software installation or elevated privileges.
• Organizations that delay patch deployment for widely deployed browser platforms may remain exposed to opportunistic exploitation attempts during routine user browsing activity.
• Enterprise environments lacking strong endpoint telemetry and monitoring of browser process behavior may experience delayed detection if browser exploitation occurs.
These judgments reflect currently available technical reporting and established adversary tradecraft patterns associated with browser exploitation activity. Analytical confidence may evolve as additional technical details regarding exploitation methods or attack campaigns become publicly available.
S4 – Strategic Threat Context
Browser exploitation vulnerabilities continue to represent a significant enterprise security concern because modern web browsers serve as primary access points for both external internet resources and internal business applications. Vulnerabilities affecting widely deployed browser platforms can therefore create large-scale enterprise exposure when exploited through routine web activity.
Attackers frequently target browser components responsible for rendering web content or executing scripting engines because these components process complex and often untrusted input delivered through websites. Exploiting weaknesses in these components can allow adversaries to execute code within the browser process without requiring users to download or install malicious software directly.
Historically, browser exploitation has been used by a wide range of threat actors, including financially motivated cybercriminal groups, ransomware operators, and advanced persistent threat actors. Successful browser compromise can enable attackers to establish an initial foothold on enterprise endpoints before expanding access through credential theft, malware staging, or lateral movement techniques.
Because enterprise users rely heavily on browsers to access cloud services, collaboration platforms, and internal web applications, compromise of a browser process may provide attackers with opportunities to access authenticated sessions or sensitive enterprise data.
The presence of CVE-2026-3909 and CVE-2026-3910 in the CISA Known Exploited Vulnerabilities catalog indicates that these vulnerabilities have already moved beyond theoretical risk and into active exploitation conditions. Organizations should therefore treat these vulnerabilities as part of the broader pattern of browser exploitation activity used by adversaries to gain initial access to enterprise environments.
S5 – Executive Risk Summary
The Chrome vulnerability pair CVE-2026-3909 and CVE-2026-3910 presents elevated enterprise risk because successful browser exploitation can allow adversaries to execute code within browser processes that routinely interact with both external internet resources and internal enterprise systems. Browser-based exploitation can occur during routine user activity, meaning that normal web browsing behavior may expose enterprise endpoints to malicious content designed to trigger vulnerable code paths.
Because modern enterprise environments rely heavily on web browsers for access to cloud services, internal applications, and external business resources, compromise of a browser process may provide attackers with opportunities to execute additional payloads, harvest credentials, or access authenticated enterprise sessions. In environments where endpoint monitoring or behavioral detection capabilities are limited, browser exploitation may initially appear indistinguishable from normal browsing activity, potentially delaying detection.
The presence of both vulnerabilities in the CISA Known Exploited Vulnerabilities catalog indicates that exploitation activity has already been observed and that adversaries have demonstrated the capability to leverage these weaknesses operationally. As a result, organizations that have not yet applied vendor patches or verified browser update status across enterprise endpoints may remain exposed to opportunistic exploitation attempts.
Enterprise risk is therefore driven primarily by the combination of widespread browser deployment, confirmed exploitation activity, and the potential for browser compromise to serve as an entry point for additional intrusion techniques affecting enterprise systems.
S5A – Estimated Probability of Recurrence
Based on currently available reporting, historical patterns of browser exploitation, and the widespread enterprise deployment of Chromium-based browsers, the probability that adversaries will continue attempting exploitation of these vulnerabilities in the near term is assessed as High.
Several factors contribute to this assessment.
• Both vulnerabilities are listed in the CISA Known Exploited Vulnerabilities catalog, indicating that active exploitation activity has already occurred.
• Browser vulnerabilities affecting core rendering or scripting engines frequently become targets for opportunistic exploitation once technical details become widely understood.
• Chromium-based browsers are deployed across large enterprise workstation populations, increasing the potential attack surface available to adversaries seeking initial access opportunities.
• Browser exploitation techniques are commonly used as entry points for broader intrusion activity, including credential theft, malware deployment, and follow-on ransomware campaigns.
The probability of continued exploitation attempts is therefore expected to remain elevated until enterprise patch adoption becomes widespread across affected browser versions.
S6 – Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
The cost ranges below are derived from common financial impacts observed in enterprise credential-compromise incidents affecting mid-size to large organizations, as browser exploitation frequently results in credential exposure or authentication abuse requiring enterprise remediation.
Core Cost Components
Incident Response and Forensics
· external incident response engagement
· internal SOC surge operations
· enterprise log analysis and threat hunting
Typical cost range: $120,000 – $600,000
Identity Infrastructure Remediation
· enterprise credential resets
· multi-factor authentication re-enrollment
· identity infrastructure validation
· privileged account review
Typical cost range: $80,000 – $1,200,000
Operational Disruption
· temporary access restrictions during containment
· workforce productivity disruption
· increased internal IT support demand
Typical cost range: $50,000 – $900,000
Legal and Compliance Review
· regulatory exposure assessment
· legal consultation and potential notification obligations
Typical cost range: $0 – $3,000,000
Credential-only incidents typically remain below $500,000 in this category unless regulated data exposure occurs.
Scenario-Based Cost Modeling
Limited Incident — Rapid Containment
Typical conditions
· small number of compromised endpoints or accounts
· rapid detection and containment
· no confirmed data exposure
Estimated cost range: $250,000 – $750,000
Typical Enterprise Intrusion
Typical conditions
· multiple compromised endpoints or accounts
· investigation of potential credential harvesting
· enterprise credential reset and multi-system remediation
Estimated cost range: $1.2M – $3.8M
Escalated Enterprise Incident
Typical conditions
· large-scale credential resets across enterprise systems
· operational disruption affecting business services
· regulatory investigation or data exposure review
Estimated cost range: $5M – $12M
S6A Risk Drivers
Several operational conditions increase the likelihood and potential impact of browser-driven enterprise compromise.
· delayed deployment of browser security updates across enterprise endpoint fleets
· limited visibility into browser process behavior and child-process execution activity
· incomplete inventories of Chromium-based browser deployments
· weak separation between browsing activity and access to sensitive enterprise systems
· insufficient correlation between endpoint telemetry, authentication logs, and network monitoring platforms
These conditions increase the probability that exploitation may progress before defenders can identify and contain malicious activity.
S7 – Bottom Line for Executives
The Chrome vulnerability pair CVE-2026-3909 and CVE-2026-3910 represents an active enterprise exposure because both vulnerabilities have been confirmed as exploited in the wild and affect widely deployed browser software used across enterprise environments. Organizations that have not yet applied vendor security updates or verified browser patch deployment across enterprise endpoints may remain exposed to exploitation attempts delivered through routine web browsing activity. Accelerated browser patch deployment, validation of update coverage across enterprise systems, and monitoring for abnormal browser process behavior represent the most effective defensive actions to reduce enterprise exposure.
S7A – Board-Level Takeaway
Confirmed exploitation of widely deployed browser vulnerabilities creates enterprise risk because routine user activity such as normal web browsing may allow attackers to compromise endpoint systems. Executive leadership should ensure that enterprise patch management processes rapidly deploy browser security updates and that security teams maintain visibility into endpoint behavior that could indicate attempted exploitation activity.
S8 – Targeted Organization
The Chrome vulnerability pair CVE-2026-3909 and CVE-2026-3910 affects organizations that rely on Chromium-based browsers for routine business operations. Enterprise users routinely access external websites, cloud platforms, and internal business systems through web browsers, creating opportunities for malicious web content to be processed by vulnerable browser components.
Organizations with large browser deployments face increased exposure because vulnerable browsers may process attacker-controlled content before security patches are deployed across the enterprise environment.
Common characteristics of potentially affected organizations include:
· large enterprise workstation fleets using Chrome or Chromium-based browsers
· remote or hybrid workforces that frequently access external web services
· enterprise environments where browsers serve as a primary interface for cloud platforms and internal applications
· organizations with slower browser patch deployment cycles due to operational change-management processes
These conditions increase the likelihood that malicious browser activity may occur during routine user browsing sessions.
S9 – Sectors / Countries Affected
Sectors
· Financial services
· Healthcare
· Government and public sector
· Technology and software development
· Manufacturing and industrial enterprises
· Education and research institutions
Countries
· Global exposure due to widespread enterprise deployment of Chromium-based browsers
S10 – Targeting Probability Assessment
Browser exploitation vulnerabilities are typically opportunistic because adversaries can deliver malicious web content through controlled websites, compromised web infrastructure, or malicious advertising networks.
Several operational factors influence targeting probability.
· organizations with large enterprise workstation fleets present larger attack surfaces for exploitation attempts
· environments where browsers provide access to internal systems or cloud identity infrastructure create opportunities for follow-on intrusion activity
· organizations hosting valuable financial, personal, or intellectual property data may attract increased adversary interest
· environments with slower patch management cycles may remain exposed longer following vulnerability disclosure
Based on these conditions, targeting probability can be assessed as follows.
High probability sectors
· Financial services
· Government and defense organizations
· Technology companies
Moderate probability sectors
· Healthcare
· Manufacturing
· Education
S11 – Adversary Capability Profiling
Successful exploitation of browser vulnerabilities typically requires moderate to advanced technical capability because attackers must develop or obtain exploit techniques capable of triggering memory corruption or logic flaws within complex browser components.
Adversary capability can be evaluated across several operational dimensions.
Exploit Development Capability
· ability to develop or acquire exploit techniques targeting browser rendering engines or JavaScript execution environments
Operational Infrastructure
· ability to distribute malicious web content through attacker-controlled domains, compromised websites, or malicious advertising infrastructure
Scalability Potential
· browser exploitation enables adversaries to reach large user populations because browsers continuously process external web content
Operational Objective
· ability to transition from browser compromise to credential harvesting, malware deployment, or follow-on enterprise intrusion activity
Adversary groups most likely to exploit browser vulnerabilities include:
· cybercriminal groups seeking scalable enterprise access for credential theft or ransomware operations
· financially motivated intrusion groups targeting enterprise authentication infrastructure
· advanced threat actors capable of developing or acquiring browser exploit chains
S12 – Exploit Status
· CVE-2026-3909 and CVE-2026-3910 are listed in the CISA Known Exploited Vulnerabilities catalog, confirming active exploitation in the wild.
· Google addressed both vulnerabilities in Chrome version 146.0.7680.75 and 146.0.7680.76.
· Vulnerability management platforms such as Tenable/Nessus can identify endpoints running vulnerable Chrome versions associated with these CVEs.
S13 – Confidence & Assessment Statement
This assessment is based on publicly available vulnerability disclosures, CISA Known Exploited Vulnerabilities catalog listings, and established patterns of browser exploitation observed in enterprise intrusion activity. Confidence in this assessment is moderate to high due to the reliability of vulnerability disclosures and the consistent operational patterns associated with browser exploitation.
Analytic Confidence Drivers
• confirmation that both vulnerabilities appear in the CISA Known Exploited Vulnerabilities catalog
• consistent reporting describing the affected browser components and vulnerability class
• historical evidence demonstrating that browser vulnerabilities are frequently used as enterprise initial-access techniques
S13A – Key Intelligence Gaps
Several intelligence gaps remain regarding the exploitation of these vulnerabilities.
· The specific exploit techniques used in observed attacks have not been publicly disclosed
· Attribution for exploitation activity has not been confirmed
· The scale and geographic distribution of exploitation activity remains unknown
· Details regarding exploit delivery infrastructure have not been publicly reported
Additional technical disclosures may provide further insight into the methods used by adversaries.
S14 – What We Don’t Yet Know
Several operational aspects of the exploitation of CVE-2026-3909 and CVE-2026-3910 remain unclear at this time.
· whether exploitation activity relies on a full exploit chain that includes browser sandbox escape techniques
· the reliability and maturity of exploit tooling currently being used by adversaries
· the infrastructure used to host or distribute malicious browser content used in exploitation attempts
· whether observed exploitation is occurring opportunistically across large victim populations or within targeted intrusion campaigns
· the extent to which successful browser compromise is being used to facilitate credential theft or follow-on enterprise intrusion activity
Additional disclosures from vendor security teams, incident response investigations, or security research publications may provide further insight into these operational elements.
S15 – Attack Overview
The Chrome vulnerability pair CVE-2026-3909 and CVE-2026-3910 affects core browser components responsible for processing untrusted web content. The vulnerabilities impact the Skia graphics library and the V8 JavaScript execution engine used within Chromium-based browsers.
Exploitation scenarios typically occur when a user visits a malicious or compromised website delivering attacker-controlled web content. During normal page rendering or script execution, the browser processes this input through vulnerable code paths within the affected components. Carefully crafted content may trigger memory corruption or implementation flaws that allow attacker-controlled code to execute within the browser execution context.
Once browser execution is compromised, adversaries may attempt to deploy additional payloads or conduct follow-on intrusion activity. These activities may include credential harvesting, malware staging, persistence mechanisms, or communication with external attacker infrastructure.
Because enterprise browsers frequently serve as trusted interfaces for internal applications and cloud services, compromise of the browser execution environment may enable attackers to expand access beyond the initially affected endpoint.
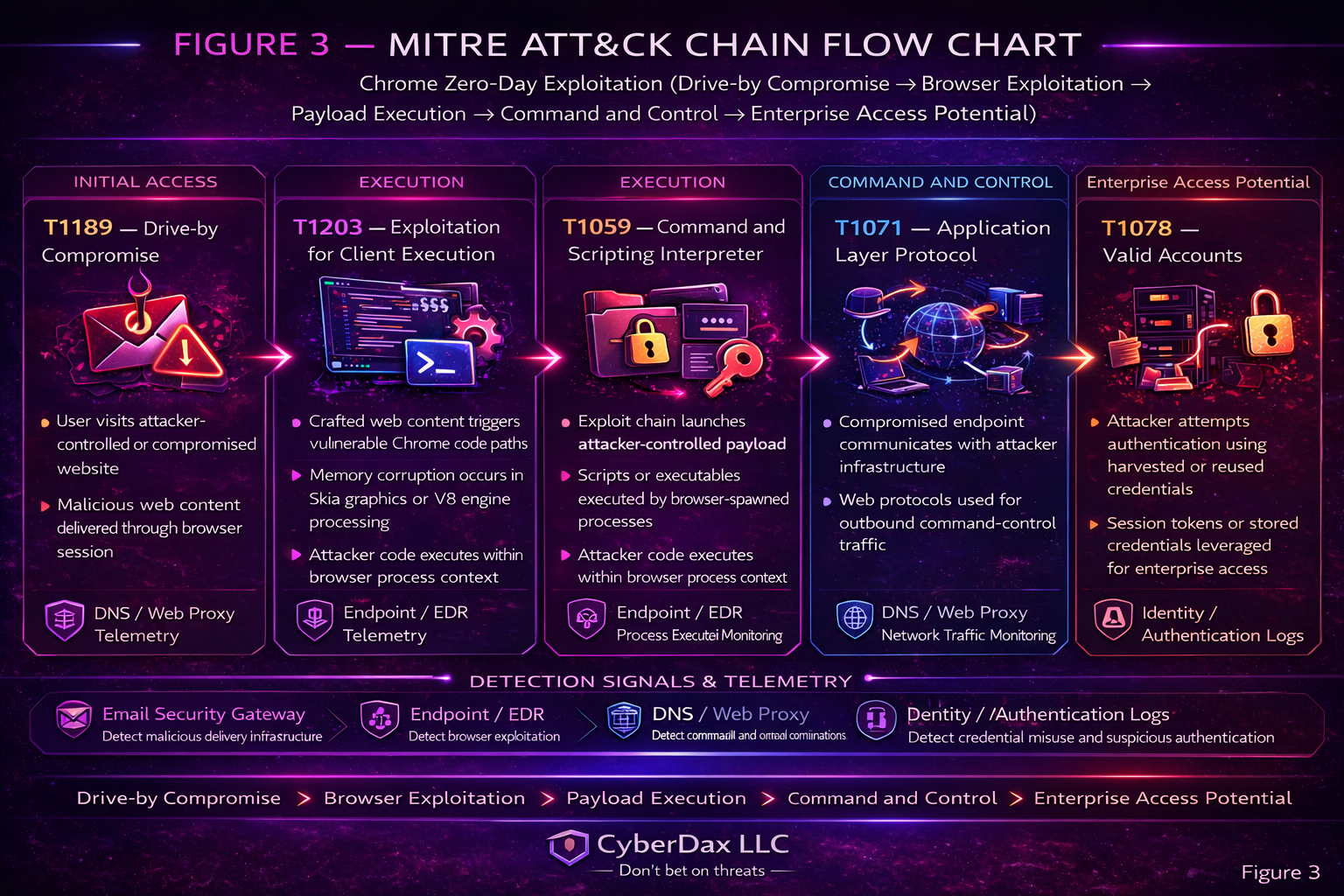
S16 – MITRE ATT&CK Chain Flow Mapping
Initial Access
T1189 – Drive-by Compromise
· adversaries deliver attacker-controlled web content through malicious websites, compromised domains, or advertising infrastructure
· users encounter malicious content during routine browsing activity
Execution
T1203 – Exploitation for Client Execution
· crafted web content triggers memory corruption conditions within vulnerable browser components
· exploitation occurs when the browser processes attacker-controlled input during page rendering or script execution
Defense Evasion
T1027 – Obfuscated or Encrypted Files or Information
· attackers may use obfuscation techniques or encrypted payload delivery to reduce the likelihood of detection by endpoint security controls
Persistence
T1547 – Boot or Logon Autostart Execution
· attackers may deploy additional payloads after successful exploitation to maintain access on the affected system
Credential Access
T1555 – Credentials from Password Stores
· adversaries may attempt to access credentials saved within browser credential storage mechanisms
Command and Control
T1071 – Application Layer Protocol
· compromised systems or deployed payloads may communicate with attacker infrastructure using common web protocols such as HTTP or HTTPS
S17 – Attack Flow
A typical exploitation sequence for browser vulnerabilities such as CVE-2026-3909 and CVE-2026-3910 may occur in several stages.
Stage 1 – Malicious Content Delivery
· attackers distribute crafted web content capable of triggering vulnerable browser code paths
· delivery may occur through compromised websites, malicious advertising networks, or attacker-controlled domains
Stage 2 – Browser Exploitation
· the victim browser processes attacker-controlled content during routine page rendering or script execution
· vulnerable browser components encounter crafted input that triggers memory corruption or logic flaws
Stage 3 – Code Execution within Browser Context
· successful exploitation allows attacker-controlled code to execute within the browser execution context
· adversaries may deploy additional payloads to establish persistence or enable follow-on intrusion activity
Stage 4 – Post-Exploitation Activity
· attackers may attempt credential harvesting, malware staging, or communication with command-and-control infrastructure
· compromised endpoints may be leveraged as entry points for additional intrusion activity within enterprise environments
S18 – Exploit Conditions Snapshot
Several operational conditions increase the likelihood that browser exploitation attempts may succeed.
· enterprise endpoints running vulnerable Chrome versions prior to patch deployment
· user interaction with malicious or compromised websites delivering crafted browser content
· limited endpoint telemetry capable of detecting abnormal browser execution behavior
· delayed patch deployment across enterprise workstation fleets
· limited correlation between browser activity, endpoint telemetry, and network monitoring systems
These conditions increase the probability that exploitation activity may occur before defenders identify and remediate vulnerable browser installations.
S19 – Malware Analysis
At this time, publicly available reporting does not confirm a specific malware family associated with exploitation of CVE-2026-3909 or CVE-2026-3910. These vulnerabilities represent browser exploitation conditions that may allow adversaries to execute attacker-controlled code within the browser execution environment.
Browser exploitation vulnerabilities commonly function as an initial access mechanism that allows adversaries to deploy additional payloads following successful exploitation. In such scenarios, the browser exploit provides code execution within the user context, which may then be used to retrieve or execute secondary tooling depending on the operational objectives of the attacker.
No malware artifacts or payload samples have been publicly attributed to exploitation activity involving these vulnerabilities at this time.
S20 – Malware Families
· No malware families have been publicly attributed to exploitation campaigns involving CVE-2026-3909 or CVE-2026-3910 at this time.
S20A – Adversary Tradecraft Summary
Browser exploitation vulnerabilities such as CVE-2026-3909 and CVE-2026-3910 are commonly used by adversaries seeking scalable initial access into enterprise environments.
Observed tradecraft patterns associated with browser exploitation activity typically include:
· delivery of malicious or attacker-controlled web content through compromised or attacker-operated websites
· triggering vulnerable browser components during routine browsing activity
· execution of attacker-controlled code within the browser execution environment
· deployment of follow-on payloads or tooling after successful exploitation
· communication with external attacker infrastructure using standard web protocols
This tradecraft allows adversaries to leverage normal user browsing behavior as an access vector while minimizing the need for additional user interaction.
S21 – Indicators and Behavioral Artifacts
Because exploitation infrastructure and payload artifacts have not been publicly disclosed, indicators associated with CVE-2026-3909 and CVE-2026-3910 are best identified through behavioral telemetry rather than static indicators.
Security teams should monitor for the following behavioral artifacts that may indicate browser exploitation attempts or related post-exploitation activity.
Process Execution Indicators
• browser processes spawning scripting interpreters or command shells
• abnormal child processes launched from chrome.exe, msedge.exe, or firefox.exe
• execution of interpreters such as powershell.exe, wscript.exe, cscript.exe, or cmd.exe shortly after browser activity
Network Communication Indicators
• outbound connections from browser-related processes to newly observed or rare external domains
• encrypted communications initiated by newly spawned processes following browser activity
• recurring network communication patterns between endpoints and previously unseen external infrastructure
File System Activity Indicators
• creation of temporary executables or scripts associated with browser sessions
• unexpected files written to user profile directories or temporary paths shortly after browser execution
Authentication Behavior Indicators
• abnormal authentication attempts originating from endpoints exhibiting suspicious browser execution activity
• authentication bursts or credential validation attempts occurring shortly after browser-related process anomalies
Monitoring these behavioral signals may assist security teams in identifying potential browser exploitation activity and detecting follow-on intrusion behavior.
S22 – Detection Coverage Matrix
The following assessment evaluates detection coverage across primary telemetry domains relevant to exploitation scenarios involving CVE-2026-3909 and CVE-2026-3910. Browser exploitation activity may generate observable signals across endpoint telemetry, DNS and web proxy monitoring systems, email security gateways, and endpoint detection and response platforms.
Endpoint Telemetry
Strongest Coverage
· abnormal parent-child process lineage originating from browser processes
· unexpected executable or interpreter execution shortly after browser sessions
· suspicious persistence mechanisms created following browser-driven execution activity
Primary Gaps
· exploitation activity occurring entirely within browser memory space
· limited visibility into exploit shellcode execution within browser runtime environments
Residual Risk
· in-memory exploitation may occur without filesystem artifacts
· exploitation activity may remain undetected until follow-on payload execution occurs
DNS / Web Proxy Logs
Strongest Coverage
· outbound browser connections to newly observed or rare external domains
· browser communication with infrastructure potentially associated with exploit hosting
Primary Gaps
· exploitation delivered through compromised but otherwise legitimate websites
· encrypted web traffic limiting payload inspection capability
Residual Risk
· attacker infrastructure may blend with normal browsing traffic patterns
· malicious activity may appear as legitimate browser traffic without behavioral correlation
Email Security Gateway
Strongest Coverage
· detection of malicious links distributed through phishing campaigns
· blocking of domains previously associated with exploit delivery infrastructure
Primary Gaps
· drive-by exploitation delivered through compromised websites rather than email campaigns
Residual Risk
· users may encounter malicious web content through direct browsing activity outside email delivery channels
EDR Correlation
Strongest Coverage
· correlation between suspicious browser execution activity and follow-on process behavior
· detection of abnormal browser process lineage combined with external network communication
Primary Gaps
· limited visibility into exploit activity occurring entirely within browser memory
Residual Risk
· exploitation activity may remain undetected until follow-on payload execution occurs
· Strategic Coverage Signals
abnormal process lineage associated with browser execution activity
· outbound connections to rare or newly observed domains following browser activity
· abnormal authentication telemetry associated with endpoints exhibiting suspicious browser behavior
Detection-to-Rule Alignment
The detection signals described in this section correspond directly to the detection engineering rules defined in Section S25 and the behavior-to-rule mappings defined in Section S26.
Browser exploitation detection coverage is primarily achieved through correlation of the following telemetry domains.
• endpoint process telemetry capturing browser parent-child execution behavior
• DNS and web proxy telemetry identifying external infrastructure communication
• authentication telemetry detecting abnormal identity activity following suspicious endpoint execution
This telemetry alignment ensures that observable behavioral signals generated by exploitation activity are mapped to deployable detection rules and SOC investigation procedures within the CyberDax detection engineering framework.
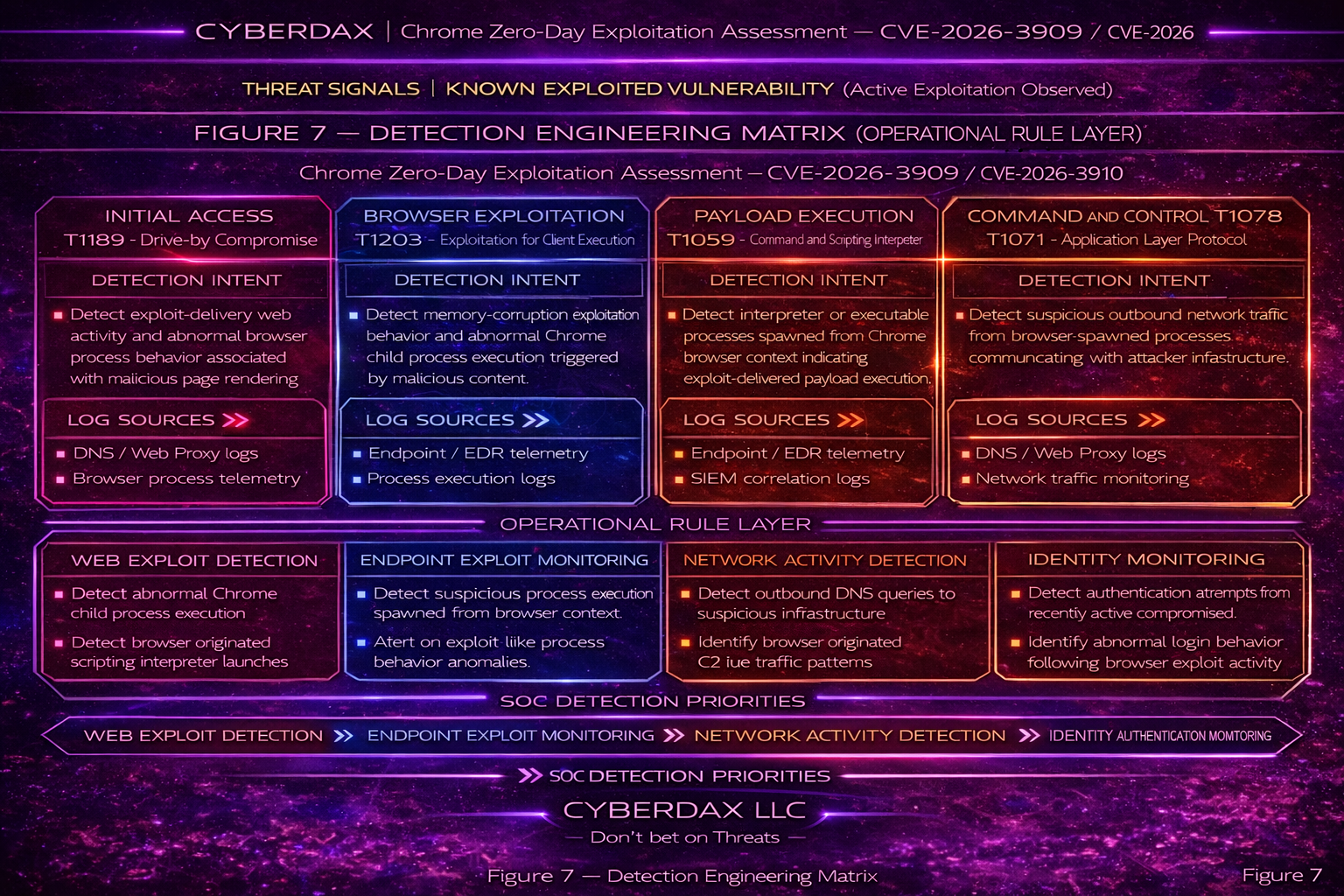
S23 – Detection Engineering Matrix (Strategic Layer)
The strategic detection layer identifies high-value detection opportunities mapped to the attack chain associated with browser exploitation vulnerabilities.
Initial Access – Drive-by Exploitation
Detection Intent
• identify delivery of malicious web content attempting to exploit browser vulnerabilities
Telemetry Sources
• DNS / Web Proxy Logs
• browser network activity telemetry
Strategic Detection Signals
• browser connections to newly observed domains associated with exploit hosting infrastructure
Execution – Exploitation for Client Execution
Detection Intent
• detect abnormal execution activity resulting from browser exploitation
Telemetry Sources
• endpoint process telemetry
• EDR activity logs
Strategic Detection Signals
• abnormal process lineage originating from browser execution
Defense Evasion
Detection Intent
• identify attempts to obscure or disguise exploit payloads and follow-on tooling
Telemetry Sources
• endpoint process telemetry
• network inspection telemetry
Strategic Detection Signals
• obfuscated or encrypted payload delivery associated with browser activity
Persistence – Post-Exploitation Access
Detection Intent
• identify persistence mechanisms deployed following successful exploitation
Telemetry Sources
• endpoint startup modification logs
• scheduled task creation telemetry
Strategic Detection Signals
• system persistence mechanisms created shortly after suspicious browser activity
Credential Access
Detection Intent
• detect attempts to access or misuse credentials following exploitation
Telemetry Sources
• authentication logs
• Identity provider telemetry
Strategic Detection Signals
• abnormal authentication telemetry associated with endpoints recently exhibiting suspicious browser behavior
Command and Control
Detection Intent
• identify communication between compromised endpoints and attacker infrastructure
Telemetry Sources
• DNS logs
• network flow telemetry
Strategic Detection Signals
• outbound connections to rare or newly registered domains
• recurring network communication patterns consistent with command-and-control activity
S24 – Detection Engineering Matrix (Operational Layer)
The operational detection layer translates strategic detection objectives into concrete monitoring signals aligned with SOC telemetry sources.
Exploit Path Segment — Script Execution
Detection Intent
• identify scripting interpreter execution originating from browser processes
Log Sources
• endpoint process telemetry
• EDR activity logs
Operational Signals
• browser process spawning powershell.exe
• browser process spawning wscript.exe or cscript.exe
• browser process spawning cmd.exe
Exploit Path Segment — Credential Misuse
Detection Intent
• detect abnormal authentication activity following suspicious browser execution
Log Sources
• identity provider authentication logs
• endpoint authentication telemetry
Operational Signals
• authentication attempts occurring shortly after suspicious browser activity
• abnormal authentication behavior originating from recently active endpoints
Exploit Path Segment — Network Communication
Detection Intent
• identify outbound communications associated with post-exploitation activity
Log Sources
• DNS telemetry
• web proxy logs
• network flow telemetry
Operational Signals
• newly observed domain connections following browser activity
• encrypted communications from newly spawned processes
S25 – Ultra-Tuned Detection Engineering Rules
Suricata
Rule Name
Browser Request For High-Risk Script Or Executable Payload
Purpose
Detect browser-driven requests for high-risk script or executable payload types commonly associated with post-exploitation staging.
ATT&CK Technique
T1189 – Drive-by Compromise
Telemetry Dependency
Suricata HTTP request inspection with user-agent, host, and URI visibility
Tuning Explanation
This rule is intentionally constrained to browser-like user agents requesting high-risk extensions that are uncommon in normal browsing. Noise should be reduced by suppressing trusted browser vendor domains, corporate package repositories, sanctioned software delivery infrastructure, approved remote support portals, and internal update hosts.
Detection Logic
Detect outbound HTTP GET requests from browser-like clients to external infrastructure for HTA, script, DLL, MSI, or executable payload types.
Operational Context
· indicates possible follow-on payload staging after browser exploitation and should trigger review of browser-driven download activity, destination domains, and related endpoint execution telemetry
system-ready code
alert http $HOME_NET any -> $EXTERNAL_NET any (
msg:"CYBERDAX Browser request for high-risk script or executable payload";
flow:established,to_server;
http.method; content:"GET";
http.user_agent; pcre:"/(Chrome|Firefox|Edg|Safari)/i";
http.uri; pcre:"/(\.hta|\.js|\.jse|\.vbs|\.vbe|\.ps1|\.dll|\.exe|\.msi)(\?|$)/Ui";
classtype:trojan-activity;
sid:2539091;
rev:6;
)SentinelOne
Rule Name
Browser Parent Launching Suspicious Interpreter From Remote Or User-Writable Context
Purpose
Detect likely post-exploitation behavior where a browser launches a high-risk interpreter with encoded, remote, or user-writable-path indicators.
ATT&CK Technique
T1203 – Exploitation for Client Execution
Telemetry Dependency
Deep Visibility process telemetry with parent-child lineage and full command-line visibility
Tuning Explanation
This rule is materially tighter than a simple browser-to-interpreter lineage alert. It requires a browser parent, a high-risk interpreter child, and suspicious command-line or path context such as encoded execution, remote retrieval, or Temp or Downloads execution. Noise should be reduced through tenant-specific exclusions for approved browser-integrated enterprise launchers, sanctioned administration utilities, software deployment agents, and known remote support tooling.
Detection Logic
Detect chrome.exe, msedge.exe, or firefox.exe spawning powershell.exe, cmd.exe, wscript.exe, or cscript.exe when the child command line contains encoded execution, remote retrieval, transfer behavior, or user-writable path indicators.
Operational Context
· indicates likely post-exploitation behavior following browser compromise and should trigger investigation of browser process lineage, child process command lines, user-writable path execution, and outbound communications from the affected host
system-ready code
(ParentProcessName ContainsCIS "chrome.exe" OR ParentProcessName ContainsCIS "msedge.exe" OR ParentProcessName ContainsCIS "firefox.exe")
AND (ProcessName ContainsCIS "powershell.exe" OR ProcessName ContainsCIS "cmd.exe" OR ProcessName ContainsCIS "wscript.exe" OR ProcessName ContainsCIS "cscript.exe")
AND (
ProcessCmd RegExp "(?i)(-enc\\b|-encodedcommand\\b|downloadstring\\(|invoke-webrequest\\b|http[s]?://|frombase64string\\b|start-bitstransfer\\b)"
OR ProcessCmd RegExp "(?i)\\\\Users\\\\[^\\\\]+\\\\Downloads\\\\"
OR ProcessCmd RegExp "(?i)\\\\Users\\\\[^\\\\]+\\\\AppData\\\\Local\\\\Temp\\\\"
)
AND NOT (
ProcessCmd ContainsCIS "\\Program Files\\"
)Splunk
Rule Name
Browser Child Interpreter With Near-Term Public Egress
Purpose
Detect likely browser exploitation by correlating suspicious browser-spawned interpreter execution with near-term public outbound network activity.
ATT&CK Technique
T1203 – Exploitation for Client Execution
Telemetry Dependency
Endpoint process telemetry and network telemetry with host correlation
Tuning Explanation
This rule is intentionally stronger than a standalone parent-child detection. It requires suspicious interpreter execution from a browser parent and public outbound traffic from the same host within five minutes. Noise should be reduced by excluding enterprise proxies, sanctioned software repositories, approved browser-based launchers, remote support tooling, and expected automation hosts.
Detection Logic
Detect browser-spawned powershell.exe, cmd.exe, wscript.exe, or cscript.exe with suspicious command-line indicators and correlate the same host to public outbound network traffic within five minutes.
Operational Context
· indicates likely browser exploitation follow-on activity and should trigger triage of browser parent-child execution, correlated external connections, and nearby authentication or persistence events on the host
system-ready code
(
search index=endpoint
(parent_process_name="chrome.exe" OR parent_process_name="msedge.exe" OR parent_process_name="firefox.exe")
(process_name="powershell.exe" OR process_name="cmd.exe" OR process_name="wscript.exe" OR process_name="cscript.exe")
(
process_command_line="*http://*"
OR process_command_line="*https://*"
OR process_command_line="*-enc *"
OR process_command_line="*\\AppData\\Local\\Temp\\*"
OR process_command_line="*\\Downloads\\*"
)
| eval host_key=coalesce(host, dest, ComputerName)
| eval proc_time=_time
| table host_key proc_time parent_process_name process_name process_command_line user
)
| join type=inner host_key [
search index=network
| eval host_key=coalesce(host, dest, ComputerName)
| where NOT cidrmatch("10.0.0.0/8", dest_ip)
AND NOT cidrmatch("172.16.0.0/12", dest_ip)
AND NOT cidrmatch("192.168.0.0/16", dest_ip)
| table host_key _time dest_ip dest_domain
]
| where _time>=proc_time AND _time<=proc_time+300
| stats values(process_name) as child_process values(process_command_line) as cmd values(dest_ip) as dest_ip values(dest_domain) as dest_domain values(user) as user by host_key parent_process_nameElastic
Rule Name
Browser Exploit Sequence To Suspicious Interpreter And Public Egress
Purpose
Detect likely browser exploitation by sequencing suspicious browser child-process execution with near-term external network activity.
ATT&CK Technique
T1203 – Exploitation for Client Execution
Telemetry Dependency
Elastic Defend process and network events with EQL support
Tuning Explanation
This sequence reduces noise by requiring two linked behaviors on the same host: suspicious browser-spawned interpreter execution and public network communication shortly afterward. This is materially lower-noise than a lineage-only detection. Approved browser helper workflows and sanctioned administration tools should be excluded where present.
Detection Logic
Detect browser-spawned interpreters with encoded, remote, or user-writable path indicators, followed within five minutes by a public outbound network connection from the suspicious process.
Operational Context
· indicates a correlated execution-and-egress sequence consistent with post-exploitation activity and should trigger investigation of browser lineage, outbound destination history, and any additional execution on the same endpoint
system-ready code
sequence by host.id with maxspan=5m
[process where host.os.type == "windows"
and process.parent.name in ("chrome.exe","msedge.exe","firefox.exe")
and process.name in ("powershell.exe","cmd.exe","wscript.exe","cscript.exe")
and process.command_line like~ ("*http://*","*https://*","*-enc *","*\\AppData\\Local\\Temp\\*","*\\Downloads\\*")
]
[network where host.os.type == "windows"
and process.name in ("powershell.exe","cmd.exe","wscript.exe","cscript.exe")
and destination.ip != null
and not cidrmatch(destination.ip, "10.0.0.0/8")
and not cidrmatch(destination.ip, "172.16.0.0/12")
and not cidrmatch(destination.ip, "192.168.0.0/16")
]QRadar
Rule Name
Browser-Launched Interpreter With Public Network Follow-On
Purpose
Detect suspicious browser exploitation by correlating high-risk interpreter execution and public outbound network activity from the same host.
ATT&CK Technique
T1203 – Exploitation for Client Execution
Telemetry Dependency
Normalized endpoint process telemetry and network telemetry in QRadar
Tuning Explanation
This rule avoids a broad lineage-only approach. It requires a browser parent, a suspicious interpreter child, suspicious command-line context, and near-term public network activity from the same source. Noise should be reduced through reference sets for enterprise proxies, sanctioned browser-based launchers, software repositories, and approved admin tools.
Detection Logic
Detect browser-spawned interpreters with encoded, remote, or user-writable path indicators and correlate that to outbound public network communication from the same host within five minutes.
Operational Context
· indicates suspicious post-browser-exploitation activity and should trigger review of correlated process execution, destination reputation, user context, and subsequent endpoint behavior from the same source system
system-ready code
SELECT p.sourceip AS host_ip, p.username, p.parent_process, p.process_name, p.commandline, n.destinationip
FROM events p, events n
WHERE p.parent_process IN ('chrome.exe','msedge.exe','firefox.exe')
AND p.process_name IN ('powershell.exe','cmd.exe','wscript.exe','cscript.exe')
AND (
LOWER(p.commandline) LIKE '%http://%'
OR LOWER(p.commandline) LIKE '%https://%'
OR LOWER(p.commandline) LIKE '%-enc %'
OR LOWER(p.commandline) LIKE '%appdata\\local\\temp%'
OR LOWER(p.commandline) LIKE '%\\downloads\\%'
)
AND n.sourceip = p.sourceip
AND n.destinationip NOT LIKE '10.%'
AND n.destinationip NOT LIKE '192.168.%'
AND p.starttime <= n.starttime
AND n.starttime <= p.starttime + 300000Sigma
Rule Name
Browser Parent Launching Suspicious Interpreter From Remote Or User-Writable Context
Purpose
Provide a portable, high-confidence detection for suspicious browser-spawned interpreter execution associated with likely post-exploitation activity.
ATT&CK Technique
T1203 – Exploitation for Client Execution
Telemetry Dependency
Windows process creation logs with parent image and command-line visibility
Tuning Explanation
This rule is intentionally narrower than common browser-child-process detections. It requires a browser parent, a high-risk interpreter child, and suspicious command-line or user-writable path context. Downstream implementations should allowlist approved browser-based enterprise launchers, sanctioned administrative utilities, and expected helper workflows.
Detection Logic
Detect browser-spawned powershell.exe, cmd.exe, wscript.exe, or cscript.exe when the child command line includes URLs, encoded execution, Temp paths, or Downloads paths.
Operational Context
· indicates suspicious browser-originated interpreter execution and should be prioritized for environments where browsers rarely launch scripting engines or command interpreters during legitimate workflows
system-ready code
title: Browser Parent Launching Suspicious Interpreter From Remote Or User-Writable Context
id: 7c4a0bb5-f0d9-4ab7-8e0a-cdax253909
status: experimental
logsource:
category: process_creation
product: windows
detection:
selection_parent:
ParentImage|endswith:
- '\chrome.exe'
- '\msedge.exe'
- '\firefox.exe'
selection_child:
Image|endswith:
- '\powershell.exe'
- '\cmd.exe'
- '\wscript.exe'
- '\cscript.exe'
selection_cmd:
CommandLine|contains:
- 'http://'
- 'https://'
- '-enc '
- '\AppData\Local\Temp\'
- '\Downloads\'
condition: selection_parent and selection_child and selection_cmd
level: high
falsepositives:
- Approved browser-based enterprise launchersYARA
Rule Name
Suspicious Script Downloader Stager Following Browser Initial Access
Purpose
High-confidence triage and enrichment detection for likely malicious script-based downloader stagers used after browser exploitation.
ATT&CK Technique
T1203 – Exploitation for Client Execution
Telemetry Dependency
File or memory scanning in malware triage workflows
Tuning Explanation
This rule avoids weak generic shellcode signatures. It requires downloader objects, local file-write behavior, and execution primitives characteristic of malicious staging logic. It should be used in triage and enrichment workflows rather than as a primary production alert.
Detection Logic
Detect JavaScript, VBScript, or HTA-style stagers that combine web retrieval, local file creation, and process execution behavior.
Operational Context
· indicates potential secondary staging artifacts associated with browser exploitation and should support malware triage, enrichment, and correlation with browser-driven execution or download activity rather than serve as a standalone production alert
system-ready code
rule CYBERDAX_Suspicious_Script_Downloader_Stager
{
meta:
description = "Likely malicious script downloader stager associated with browser-driven initial access"
author = "CyberDax"
strings:
$s1 = "MSXML2.XMLHTTP" ascii wide
$s2 = "WinHttp.WinHttpRequest.5.1" ascii wide
$s3 = "ADODB.Stream" ascii wide
$s4 = "SaveToFile" ascii wide
$s5 = "WScript.Shell" ascii wide
$s6 = "CreateObject" ascii wide
$s7 = ".Run(" ascii wide
$s8 = "AppData\\Local\\Temp" ascii wide
$s9 = "Downloads" ascii wide
condition:
1 of ($s1,$s2) and
2 of ($s3,$s4,$s5,$s6,$s7) and
1 of ($s8,$s9)
}AWS
Rule Name
EC2 Windows Browser Child Interpreter With Public Egress Correlation
Purpose
High-confidence production alert for suspicious browser exploitation indicators on Windows EC2 workloads where centralized endpoint telemetry is available.
ATT&CK Technique
T1203 – Exploitation for Client Execution
Telemetry Dependency
Windows process telemetry and network telemetry from EC2 instances forwarded into CloudWatch Logs
Tuning Explanation
This rule is explicitly limited to environments collecting Windows endpoint telemetry from EC2 instances. It is not a generic VPC anomaly rule. Noise is reduced by requiring suspicious browser-child execution and public outbound activity from the same instance. Approved browser launchers, sanctioned management tools, and expected automation should be excluded.
Detection Logic
Detect browser-spawned interpreters with suspicious command-line context on Windows EC2 and correlate them to non-private outbound activity from the same instance.
Operational Context
· indicates likely suspicious follow-on activity on a Windows EC2 workload and should trigger validation of endpoint telemetry integrity, process lineage, outbound destination history, and related identity activity from the instance
system-ready code
fields @timestamp, InstanceId, ParentProcessName, ProcessName, CommandLine, DestinationIp
| filter ParentProcessName in ["chrome.exe","msedge.exe","firefox.exe"]
| filter ProcessName in ["powershell.exe","cmd.exe","wscript.exe","cscript.exe"]
| filter CommandLine like /http:\/\/|https:\/\/|-enc |AppData\\Local\\Temp|\\Downloads\\/
| stats earliest(@timestamp) as proc_time, values(DestinationIp) as dst by InstanceId, ParentProcessName, ProcessName, CommandLine
| filter ispresent(dst)
| filter not like(dst[0], "10.%") and not like(dst[0], "192.168.%")Azure
Rule Name
Browser-To-Interpreter With Public Network Follow-On On Windows Endpoint
Purpose
High-confidence production alert for likely browser exploitation on Azure-managed Windows endpoints by correlating suspicious browser child-process execution with outbound public network activity.
ATT&CK Technique
T1203 – Exploitation for Client Execution
Telemetry Dependency
Microsoft Defender for Endpoint DeviceProcessEvents and DeviceNetworkEvents
Tuning Explanation
This rule is stronger than a simple browser-child analytic because it requires suspicious command-line context and near-term public network activity from the same device. Noise is reduced by focusing on high-risk interpreters and public destinations. Approved enterprise launchers, sanctioned administration tools, and expected helper-process behavior should be excluded where applicable.
Detection Logic
Detect chrome.exe, msedge.exe, or firefox.exe spawning powershell.exe, cmd.exe, wscript.exe, or cscript.exe with suspicious arguments, followed by a public network connection from the same device within five minutes.
Operational Context
· indicates likely browser exploitation follow-on behavior on a monitored Windows endpoint and should trigger investigation of browser lineage, Defender process history, remote destinations, and any associated credential activity from the same device
system-ready code
let suspicious_proc =
DeviceProcessEvents
| where InitiatingProcessFileName in ("chrome.exe","msedge.exe","firefox.exe")
| where FileName in ("powershell.exe","cmd.exe","wscript.exe","cscript.exe")
| where ProcessCommandLine has_any ("http://","https://","-enc ","\\AppData\\Local\\Temp\\","\\Downloads\\")
| project DeviceId, ProcTime=Timestamp, Browser=InitiatingProcessFileName, Child=FileName, ProcessCommandLine;
let suspicious_net =
DeviceNetworkEvents
| where isnotempty(RemoteIP)
| where not(ipv4_is_private(RemoteIP))
| project DeviceId, NetTime=Timestamp, RemoteIP, RemoteUrl;
suspicious_proc
| join kind=inner suspicious_net on DeviceId
| where NetTime between (ProcTime .. ProcTime + 5m)
| project DeviceId, ProcTime, NetTime, Browser, Child, ProcessCommandLine, RemoteIP, RemoteUrlGCP
Rule Name
Windows GCE Browser Child Interpreter With Public Network Follow-On
Purpose
High-confidence production alert for suspicious browser exploitation indicators on Windows GCE workloads where centralized endpoint telemetry is available.
ATT&CK Technique
T1203 – Exploitation for Client Execution
Telemetry Dependency
Windows process telemetry and network telemetry from GCE instances forwarded into centralized logging or BigQuery
Tuning Explanation
This rule is intentionally limited to environments collecting Windows endpoint telemetry from GCE instances. It is not a generic cloud audit anomaly analytic. Noise is reduced by requiring suspicious browser-child execution plus public outbound activity on the same host. Approved enterprise launchers, sanctioned management tools, and expected helper-process behavior should be excluded if present.
Detection Logic
Detect browser-spawned interpreters with suspicious command-line context on Windows GCE and correlate them to public outbound activity from the same host.
Operational Context
· indicates likely suspicious post-exploitation activity on a Windows GCE host and should trigger review of centralized endpoint telemetry, process lineage, external destinations, and any additional execution or authentication anomalies involving the host
system-ready code
SELECT
host,
MIN(event_time) AS first_seen,
ANY_VALUE(parent_process) AS parent_process,
ANY_VALUE(process_name) AS process_name,
ANY_VALUE(command_line) AS command_line,
ARRAY_AGG(DISTINCT destination_ip IGNORE NULLS) AS destination_ips
FROM `project.dataset.endpoint_events`
WHERE parent_process IN ('chrome.exe','msedge.exe','firefox.exe')
AND process_name IN ('powershell.exe','cmd.exe','wscript.exe','cscript.exe')
AND REGEXP_CONTAINS(command_line, r'http://|https://|-enc |AppData\\Local\\Temp|\\Downloads\\')
GROUP BY host
HAVING ARRAY_LENGTH(destination_ips) > 0 Operational Validation Note
Detection logic presented in this section reflects deployable detection patterns aligned with commonly available enterprise telemetry sources including endpoint process telemetry, network monitoring logs, and authentication telemetry.S26 – Threat-to-Rule Traceability Matrix
Phishing-Based Payload Delivery
Coverage Disposition
• Not Applicable
• Not observed in currently available reporting.
External Payload Retrieval
Coverage Disposition
Detected
• Suricata – Browser Request For High-Risk Script Or Executable Payload
o Detects browser-originated HTTP requests retrieving high-risk script or executable payload types from external infrastructure.
• Splunk – Browser Child Interpreter With Near-Term Public Egress
o Detects suspicious interpreter execution originating from browser processes followed by outbound external network communication.
• Elastic – Browser Exploit Sequence To Suspicious Interpreter And Public Egress
o Detects sequence-based behavior where browser exploitation activity leads to suspicious interpreter execution and subsequent outbound communication.
Shortcut-Based Payload Execution
Coverage Disposition
Not Applicable
• Not observed in currently available reporting.
• May occur during post-exploitation depending on attacker objectives and target environment.
Interpreter Execution from Staging Paths
Coverage Disposition
Detected
• SentinelOne – Browser Parent Launching Suspicious Interpreter From Remote Or User-Writable Context
Detects browser processes spawning scripting interpreters executing from user-writable directories such as Temp or Downloads.
• Splunk – Browser Child Interpreter With Near-Term Public Egress
o Detects browser-driven interpreter execution combined with suspicious outbound network communication.
• Elastic – Browser Exploit Sequence To Suspicious Interpreter And Public Egress
o Detects correlated browser exploitation activity followed by suspicious interpreter execution.
• Sigma – Browser Parent Launching Suspicious Interpreter From Remote Or User-Writable Context
Portable rule detecting browser processes launching high-risk interpreters with suspicious command-line arguments.
Endpoint Security Suppression Attempt
Coverage Disposition
Hunt Only
• Not observed in currently available reporting.
• May occur during post-exploitation depending on attacker objectives and target environment.
Credential Validation Activity
Coverage Disposition
Hunt Only
• Not observed in currently available reporting.
• May occur during post-exploitation depending on attacker objectives and target environment.
Impossible Travel Authentication
Coverage Disposition
Hunt Only
• Not observed in currently available reporting.
• May occur during post-exploitation depending on attacker objectives and target environment.
Cloud Credential Misuse
Coverage Disposition
Hunt Only
• Not observed in currently available reporting.
• May occur during post-exploitation depending on attacker objectives and target environment.
DLL Side-Loading Execution
Coverage Disposition
Hunt Only
• Not observed in currently available reporting.
• May occur during post-exploitation depending on attacker objectives and target environment.
Detection Coverage Summary
Detected Behaviors
• browser-based retrieval of high-risk script or executable payloads
• interpreter execution originating from browser parent processes
• suspicious outbound communication occurring after interpreter execution
Conditional Post-Exploitation Behaviors
· credential abuse or credential validation activity
· impossible travel authentication anomalies
· cloud identity misuse activity
· endpoint security suppression attempts
· DLL side-loading execution techniques
These behaviors have not been observed in currently available reporting but may occur during post-exploitation depending on attacker objectives and the victim environment.
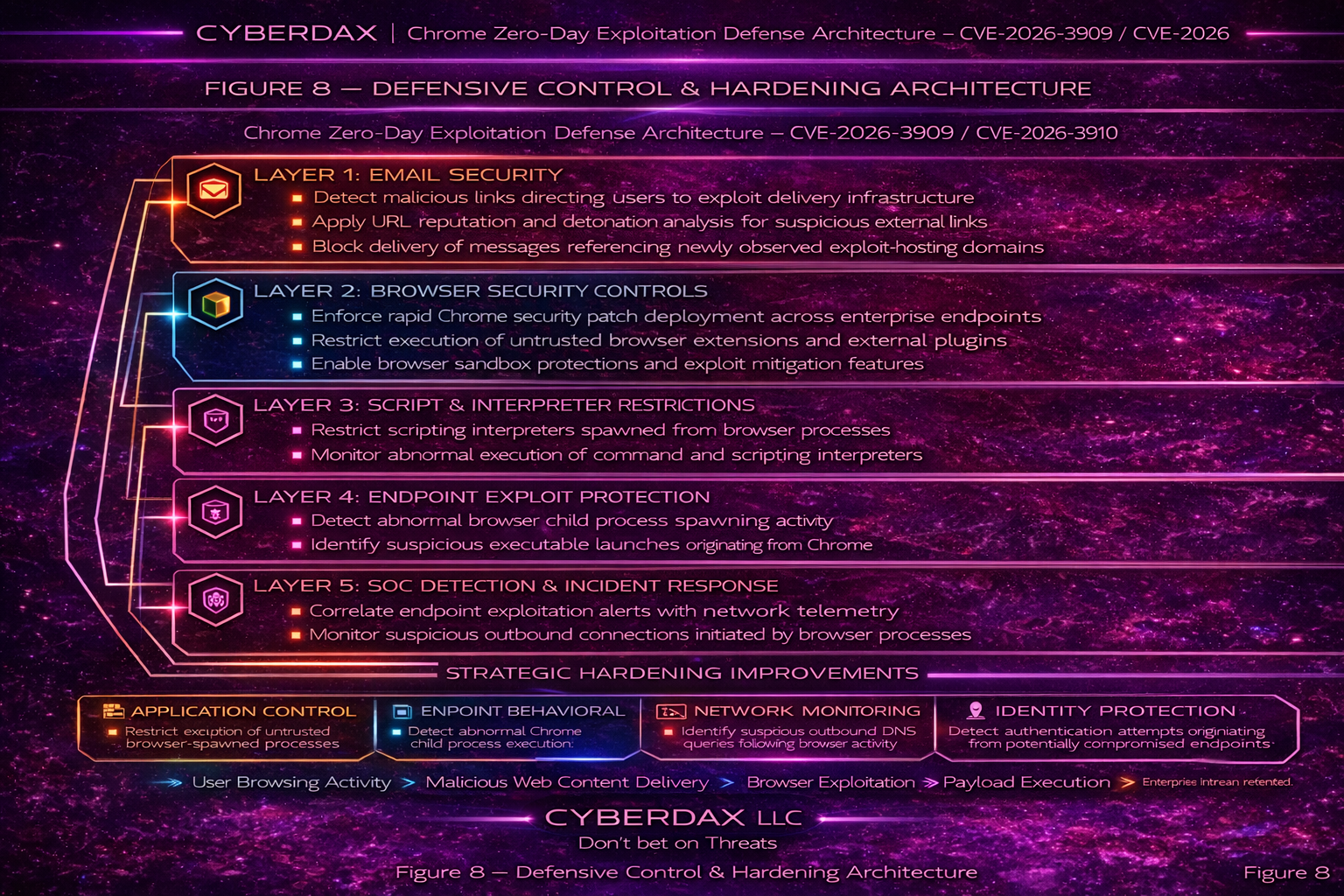
S27 – Defensive Control and Hardening Architecture
Email Security Layer — Initial Access Disruption
• Not applicable to the currently observed exploitation vector.
Identity Security Layer — Credential Abuse Prevention
• enforce multi-factor authentication for enterprise identity providers
• monitor abnormal authentication patterns following endpoint exploitation alerts
• implement conditional access policies restricting risky authentication activity
Endpoint Security Layer — Execution and Defense Evasion Detection
• detect browser parent processes spawning scripting interpreters or command shells
• monitor encoded or remote command execution originating from browser processes
• capture command-line parameters and parent-child process telemetry for endpoint execution activity
Network Monitoring Layer — Payload Delivery Detection
• monitor outbound browser requests retrieving high-risk script or executable payload types
• identify suspicious domains associated with newly observed payload retrieval activity
• correlate endpoint execution telemetry with external network communication events
Security Operations Layer — Cross-Domain Detection and Response
• correlate endpoint process telemetry with network telemetry for exploitation indicators
• investigate browser processes spawning scripting interpreters or command shells
• initiate containment procedures when suspicious interpreter execution from browser processes is confirmed
Operational Hardening Priorities
• enforce rapid Chrome and Chromium-based browser patch deployment
• maintain enterprise visibility into browser versions across workstation fleets
• ensure endpoint telemetry captures browser process execution chains and command-line parameters
Architectural Security Outcome
• improved detection capability for browser exploitation indicators
• increased visibility into suspicious interpreter execution originating from browser processes
• strengthened correlation between endpoint telemetry and network monitoring signals
S28 – Today’s Hunt Focus
Signal 1 — Suspicious Payload Retrieval from External Infrastructure
• Not observed in currently available reporting.
Signal
· Not observed in currently available reporting
Telemetry
· DNS / web proxy logs
· network flow telemetry
· endpoint process telemetry
Why It Matters
· payload retrieval commonly follows successful browser exploitation and may indicate staging of secondary tooling
· monitoring for unusual browser-driven payload downloads may reveal early post-exploitation activity
Signal 2 — Interpreter Execution from User Staging Directories
Signal
· browser processes spawning scripting interpreters or command shells
Telemetry
· endpoint process creation logs
· parent-child process lineage telemetry
· command-line execution parameters
Hunt Logic
· identify chrome.exe, msedge.exe, or firefox.exe spawning powershell.exe, cmd.exe, wscript.exe, or cscript.exe
· prioritize executions originating from Temp or Downloads directories
Why It Matters
· browser exploitation frequently results in interpreter execution used to stage additional payloads or attacker tooling
· browser processes launching command interpreters is uncommon during legitimate browsing workflows
Signal 3 — Credential Validation Burst Activity
Signal
· Not observed in currently available reporting
Telemetry
· authentication logs
· identity provider telemetry
Why It Matters
· credential validation activity may occur during post-exploitation if attackers attempt to test harvested credentials or expand access
S28A – Detection Priority Signals
• browser processes spawning scripting interpreters or command shells
• interpreter execution originating from user-writable directories such as Temp or Downloads
• suspicious outbound network communication occurring after browser-driven interpreter execution
• browser retrieval of high-risk script or executable payload types from external domains
S29 – Detection Gaps and Residual Risk
Although the implemented detection coverage provides strong visibility into suspicious browser exploitation indicators, several residual risks remain due to the inherent characteristics of client-side exploitation.
Detection Visibility Limitations
• browser exploitation that executes entirely within the browser process may produce limited observable telemetry depending on endpoint monitoring capabilities
• encrypted outbound communications may obscure malicious command-and-control activity when domain intelligence or behavioral monitoring coverage is limited
• short-lived attacker infrastructure used for payload delivery may evade reputation-based detection systems
Residual Risk
• attackers may leverage browser exploitation to execute malicious code that avoids spawning scripting interpreters or command shells
• attackers may stage payloads using legitimate hosting infrastructure or cloud services to reduce detection probability
• attackers may conduct limited post-exploitation activity designed to minimize observable endpoint and network telemetry
These residual risks highlight the importance of strong endpoint telemetry collection, network monitoring, and rapid patch deployment for vulnerable browser versions.
S30 – Intelligence Maturity Assessment
CyberDax Intelligence Maturity Reference
The CyberDax Intelligence Maturity Model evaluates an organization’s ability to detect, investigate, and respond to emerging threat activity across endpoint, identity, and network telemetry domains.
Low Maturity
Organizations operating at low maturity levels typically exhibit the following characteristics.
• limited endpoint telemetry visibility
• minimal correlation between endpoint and network telemetry
• reactive vulnerability patch management processes
• limited ability to detect browser exploitation indicators
In these environments, browser exploitation activity may remain undetected for extended periods.
Moderate Maturity
Organizations operating at moderate maturity levels demonstrate improved detection capability.
• endpoint telemetry captures parent-child process relationships and command-line execution
• security operations teams perform limited cross-domain telemetry correlation
• vulnerability patch deployment processes are defined but may not be consistently enforced
These organizations may detect suspicious interpreter execution originating from browser processes but may struggle to identify subtle exploitation activity occurring entirely within browser memory.
High Maturity
Organizations operating at high maturity levels demonstrate strong defensive capability.
• comprehensive endpoint telemetry collection and monitoring
• integrated correlation between endpoint, identity, and network telemetry sources
• rapid vulnerability patch deployment across workstation fleets
• proactive threat hunting for browser exploitation indicators
These organizations are significantly more likely to detect and contain exploitation attempts early in the attack lifecycle.
Security Program Integration Note
• Threat intelligence assessments within the CyberDax framework are designed to inform vulnerability management, detection engineering, incident response readiness, and enterprise defensive architecture decisions.
S31 – Organizational Security Posture Impact
Exploitation of browser vulnerabilities such as CVE-2026-3909 and CVE-2026-3910 may impact enterprise security posture if vulnerable browser versions remain deployed within the environment.
Potential impact areas include:
• compromise of enterprise endpoints used for business operations
• potential exposure of browser session tokens or stored credentials depending on attacker post-exploitation objectives
• increased risk of follow-on malware staging, privilege escalation, or lateral movement activity
Organizations maintaining large workstation fleets with inconsistent browser patching practices may experience elevated exposure to exploitation attempts.
Maintaining strong endpoint telemetry, identity monitoring, and network detection capability significantly reduces the likelihood of successful exploitation.
S32 – Defensive Architecture Implementation
Effective mitigation of browser exploitation threats requires coordinated implementation of defensive controls across multiple security domains.
Endpoint Telemetry
• capture parent-child process relationships for browser processes and spawned interpreters
• collect command-line execution telemetry for scripting engines and command interpreters
• ensure endpoint detection platforms monitor abnormal browser process behavior
Network Monitoring
• monitor outbound network connections following suspicious browser process execution
• detect external infrastructure hosting suspicious payload retrieval activity
• correlate endpoint execution telemetry with outbound network traffic patterns
Identity Monitoring
• monitor authentication events following endpoint exploitation indicators
• detect abnormal authentication patterns potentially associated with credential abuse
Patch Management
• deploy security patches for Chrome and Chromium-based browsers rapidly after release
• maintain centralized visibility into browser versions across enterprise workstation fleets
These architectural controls collectively reduce the likelihood that browser exploitation activity will progress beyond initial compromise.
S33 – Strategic Defensive Improvements
Organizations seeking to improve resilience against browser exploitation threats should consider the following strategic improvements.
• enforce centralized enterprise browser management to maintain version consistency and accelerate patch deployment
• integrate endpoint telemetry with network monitoring systems to improve cross-domain detection capability
• develop threat hunting procedures targeting browser processes spawning scripting interpreters and suspicious external payload retrieval activity
• expand security operations capability to investigate browser exploitation indicators and associated post-exploitation activity
Implementing these improvements strengthens enterprise defensive capability and reduces operational risk associated with browser exploitation threats.
Control Impact Mapping
• These defensive improvements support enterprise security controls associated with vulnerability management, endpoint monitoring, and incident detection as described in frameworks such as NIST Cybersecurity Framework PR.IP, NIST 800-53 SI-4, ISO 27001 A.12.6, and CIS Critical Security Controls 7 and 8.
S34 – Estimated Probability of Recurrence
Browser vulnerabilities affecting widely deployed enterprise software frequently experience recurring exploitation attempts following public disclosure.
Estimated Probability of Recurrence (12-Month Horizon)
• high probability of opportunistic exploitation attempts during the initial vulnerability disclosure and patch deployment window
• moderate probability of continued exploitation attempts targeting organizations with delayed browser patch deployment
• lower probability of sustained exploitation activity once enterprise patch adoption stabilizes across workstation fleets
Recurrence probability is primarily influenced by the speed of enterprise vulnerability remediation and the visibility organizations maintain into deployed browser versions.
S35 – Estimated Financial Risk Reduction
Implementation of the defensive controls described in this report reduces the likelihood that browser exploitation incidents progress into the higher-cost enterprise intrusion scenarios described in Section S6.
Potential Risk Reduction Drivers
• rapid deployment of browser security updates
• improved endpoint telemetry collection and monitoring
• integration of endpoint and network telemetry for cross-domain detection
• proactive threat hunting focused on browser exploitation indicators
Organizations implementing these improvements reduce the probability that exploitation attempts escalate into incidents requiring enterprise-wide credential resets, extensive incident response engagement, or operational disruption.
S36 – Strategic Implications
The exploitation of widely deployed browser platforms highlights the operational importance of rapid vulnerability remediation and strong endpoint visibility across enterprise workstation fleets.
Strategic implications for enterprise defenders include:
• browser platforms remain a common initial access vector due to routine interaction with untrusted web content
• delayed patch deployment across large workstation environments increases the window of opportunity for opportunistic exploitation
• effective detection of client-side exploitation requires coordinated monitoring across endpoint, network, and identity telemetry sources
These factors reinforce the importance of maintaining coordinated defensive architecture across multiple security domains.
S36A – Threat Forecast / Adversary Next Moves
Based on historical exploitation patterns for browser vulnerabilities, several adversary behaviors may occur following vulnerability disclosure.
Potential adversary activity may include:
• opportunistic exploitation attempts targeting unpatched enterprise endpoints
• delivery of malicious web content designed to trigger vulnerable browser code paths
• staging of follow-on payloads after successful browser compromise
These behaviors have not been observed in currently available reporting for this vulnerability pair but may occur depending on attacker objectives and the target environment.
S36B – Threat Actor Capability Scorecard
Based on currently available reporting, exploitation of CVE-2026-3909 and CVE-2026-3910 has not been attributed to a specific threat actor group.
Threat Actor Capability Assessment
Operational Complexity
· exploitation of browser memory corruption vulnerabilities generally requires moderate to advanced technical capability
Infrastructure Requirements
· attacker-controlled web infrastructure capable of hosting malicious content or exploit delivery mechanisms
Operational Scalability
· browser exploitation campaigns can scale rapidly when delivered through compromised websites or malicious advertising infrastructure
Attribution
• Not known at this time
S37 – Post-Incident Insights and Recommendations
Structural Lessons
· browser vulnerabilities represent a persistent attack surface due to continuous user interaction with web content
· enterprise environments with delayed patch deployment remain vulnerable for extended periods following public vulnerability disclosure
· endpoint telemetry capable of identifying suspicious interpreter execution provides valuable early detection capability for browser exploitation activity
Defensive Improvement Priorities
· enforce enterprise browser version management and patch compliance monitoring
· maintain endpoint telemetry visibility into browser process execution behavior
· improve correlation between endpoint telemetry and network monitoring systems
Strategic Hardening Recommendations
· deploy centralized enterprise browser management to accelerate vulnerability remediation
· expand threat hunting capability focused on browser exploitation indicators
· strengthen cross-domain telemetry integration across endpoint, identity, and network security systems
S38 – Board-Level Takeaway
Browser exploitation vulnerabilities affecting widely deployed enterprise software represent a persistent risk to organizational security posture.
Rapid vulnerability remediation, strong endpoint telemetry visibility, and integrated security monitoring significantly reduce the likelihood that exploitation attempts progress beyond initial compromise.
Organizations that maintain disciplined vulnerability management and proactive detection capability are significantly better positioned to contain browser exploitation attempts before operational disruption occurs.
S39 – Attack Economics and Organizational Impact Model
Browser exploitation provides adversaries with a relatively low-cost initial access mechanism when vulnerable endpoints remain unpatched.
Attacker Investment Factors
· development or acquisition of browser exploit capability
· hosting infrastructure used for malicious web content delivery
· distribution mechanisms designed to trigger vulnerable browser code paths
Defender Cost Factors
· incident response and forensic investigation
· endpoint remediation and patch deployment
· operational disruption during containment and recovery
Effective vulnerability management and early detection capability increase attacker operational cost by reducing the likelihood of successful exploitation and shortening the available attack window.
Source Validation Note
• This assessment is based on primary-source vulnerability disclosures, authoritative exploitation status reporting, and established analytical frameworks available at the time of publication.
• Secondary reporting was excluded where it duplicated original source material in order to preserve source integrity and reduce analytical redundancy.
S40 – References
Vendor Advisory
Google Chrome Stable Channel Update – Security fixes addressing CVE-2026-3909 and CVE-2026-3910
· hxxps://chromereleases[.]googleblog[.]com/2026/03/stable-channel-update-for-desktop.html
Vulnerability Records
MITRE CVE Record – CVE-2026-3909
· hxxps://cve[.]mitre[.]org/cgi-bin/cvename.cgi?name=CVE-2026-3909
MITRE CVE Record – CVE-2026-3910
· hxxps://cve[.]mitre[.]org/cgi-bin/cvename.cgi?name=CVE-2026-3910
Known Exploited Vulnerabilities (KEV)
CISA Known Exploited Vulnerabilities Catalog – CVE-2026-3909
· hxxps://www[.]cisa[.]gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-3909
CISA Known Exploited Vulnerabilities Catalog – CVE-2026-3910
· hxxps://www[.]cisa[.]gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-3910
Analytical Framework
MITRE ATT&CK Framework
· hxxps://attack[.]mitre[.]org/