Credential Theft Campaign Assessment BlackSanta Intrusion Activity
BLUF
The BlackSanta malware campaign presents a growing enterprise security risk because it enables attackers to steal authentication credentials that provide unauthorized access to enterprise systems. Available reporting suggests the campaign relies on phishing-based delivery combined with malware capable of harvesting credentials and supporting internal reconnaissance activities. The observed tradecraft aligns with financially motivated intrusion campaigns that commonly target enterprise environments to enable data theft, operational disruption, or follow-on ransomware activity. Executive leadership should prioritize stronger identity monitoring, phishing-resistant authentication controls, and improved endpoint telemetry visibility to reduce the risk of credential-based enterprise compromise.
S2B Threat Severity Indicator
Threat Severity: Moderate
Confidence Level: Moderate
Primary Risk Domain: Identity Compromise
Operational Risk Category: Credential Theft Campaign
Executive Risk Translation
If BlackSanta infections occur within an enterprise environment, attackers may obtain valid employee credentials and authenticate to internal systems as legitimate users, enabling lateral movement that can lead to data exposure, operational disruption, and financial loss.
S2A Why This Matters Now
Credential theft has become one of the most reliable methods attackers use to compromise enterprise organizations and establish persistent access to internal systems.
Several factors increase the operational significance of the BlackSanta campaign.
· Enterprise authentication systems provide centralized access to critical business services, making stolen credentials highly valuable to attackers.
· Phishing delivery techniques remain effective because they rely on user interaction rather than software vulnerabilities.
· Organizations increasingly depend on cloud services and remote access infrastructure, expanding the number of systems accessible through a single compromised identity.
· Many security programs continue to emphasize perimeter defenses while lacking consistent monitoring for suspicious authentication behavior inside enterprise environments.
These conditions allow attackers who obtain valid credentials to operate within enterprise systems while appearing to be legitimate users, increasing the likelihood that malicious activity may initially evade detection.
S3 Key Judgments
Based on currently available reporting and established intrusion patterns associated with credential-harvesting malware campaigns, several key judgments can be made.
· The primary operational objective of the BlackSanta malware campaign appears to be the theft of enterprise authentication credentials.
· Phishing activity is assessed to be a probable delivery mechanism consistent with distribution methods commonly used by credential-harvesting malware.
· Stolen credentials could allow attackers to access enterprise services without triggering traditional perimeter security controls.
· Organizations with limited visibility into authentication logs, endpoint telemetry, and network behavior may experience delayed detection of credential misuse.
· The operational characteristics of the campaign are consistent with financially motivated intrusion activity seeking enterprise access rather than intelligence-collection operations.
These judgments are based on currently available reporting and may evolve as additional technical artifacts or incident reporting becomes available.
S4 Strategic Threat Context
Credential-based intrusions remain one of the most common and effective attack methods targeting enterprise organizations.
Several broader threat trends explain the continued success of credential-focused malware campaigns.
· Valid authentication credentials allow attackers to bypass perimeter defenses and operate inside enterprise environments as legitimate users.
· Enterprise identity infrastructure often provides access to multiple business applications and services through a single authentication platform.
· Financially motivated threat actors frequently pursue credential compromise as an efficient pathway toward data theft, ransomware deployment, or operational disruption.
· Increased adoption of cloud services and remote workforce infrastructure has expanded the potential operational impact of compromised enterprise identities.
Within this threat environment, malware campaigns designed to harvest authentication credentials provide attackers with a scalable pathway to compromise enterprise networks and establish persistent access.
S5 Executive Risk Summary
The BlackSanta malware campaign represents a credential-focused intrusion threat capable of enabling unauthorized access to enterprise systems and business applications. By targeting authentication credentials through phishing-delivered malware, attackers can bypass perimeter security controls and operate inside enterprise environments using legitimate user accounts. This intrusion model increases the likelihood of lateral movement across internal systems and may enable data exposure, operational disruption, or follow-on ransomware activity. Organizations with limited visibility into identity activity, endpoint behavior, and authentication telemetry face elevated risk because credential misuse may initially appear as legitimate user activity.
S5A Estimated Probability of Recurrence
Credential-harvesting malware campaigns historically recur frequently because they rely on scalable delivery methods and widely applicable intrusion techniques.
Estimated Probability of Recurrence within a twelve-month horizon
· High
Contributing factors include
· Continued effectiveness of phishing-based malware delivery
· Reusability of credential theft infrastructure
· High operational value of compromised authentication credentials
· Inconsistent identity monitoring across enterprise environments
S6 Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
The cost ranges presented in S6 Executive Cost Summary are derived from common financial impacts observed in enterprise credential-compromise incidents. Estimates assume a mid-size to large organization and reflect realistic operational response costs rather than worst-case breach scenarios.
Core Cost Components
Enterprise credential compromise typically generates costs in four primary areas.
Incident Response and Forensics
· external incident response engagement
· internal SOC surge operations
· enterprise log analysis and threat hunting
Typical cost range
$120,000 – $600,000
Identity Infrastructure Remediation
· enterprise credential resets
· multi-factor authentication re-enrollment
· identity infrastructure validation
· privileged account review
Typical cost range
$80,000 – $1,200,000
Operational Disruption
· temporary access restrictions during containment
· workforce productivity disruption
· increased internal IT support demand
Typical cost range
$50,000 – $900,000
Legal and Compliance Review
· regulatory exposure assessment
· legal consultation and potential notification obligations
Typical cost range
$0 – $3,000,000
Credential-only incidents typically remain below $500,000 in this category unless regulated data exposure occurs.
Scenario-Based Cost Modeling
These components combine into three realistic enterprise incident scenarios.
Limited Incident — Rapid Containment
Typical conditions
· small number of compromised accounts
· rapid detection and containment
· no confirmed data exposure
Estimated cost range
$250,000 – $750,000
Typical Enterprise Intrusion
Typical conditions
· multiple compromised accounts
· lateral movement within enterprise systems
· enterprise credential reset and multi-system remediation
Estimated cost range
$1.2M – $3.8M
Escalated Enterprise Incident
Typical conditions
· large-scale credential reset across enterprise systems
· operational disruption affecting business services
· regulatory investigation or data exposure review
Estimated cost range
$5M – $12M
S6A Risk Drivers
Several operational conditions increase the likelihood and potential impact of credential-focused malware campaigns.
· Limited visibility into authentication behavior across enterprise identity systems
· Insufficient monitoring of endpoint activity associated with credential harvesting
· Inconsistent phishing detection and email security controls
· Delayed identification of abnormal authentication patterns across cloud services
· Weak enforcement of multi-factor authentication across critical enterprise systems
These factors increase the probability that compromised credentials could be used to access enterprise resources before detection occurs.
S7 Bottom Line for Executives
The BlackSanta malware campaign reinforces the continued effectiveness of credential-theft intrusion methods against enterprise organizations. Attackers who obtain valid authentication credentials can bypass traditional perimeter defenses and operate within enterprise systems as legitimate users. Organizations lacking strong identity monitoring and endpoint telemetry visibility face elevated risk of undetected credential misuse. Executive leadership should prioritize identity security, behavioral monitoring of authentication activity, and phishing-resistant authentication mechanisms to reduce enterprise exposure to credential-based compromise.
S7A Board-Level Takeaway
Credential theft campaigns such as BlackSanta demonstrate that enterprise cyber risk increasingly centers on identity compromise rather than perimeter intrusion. Even a single compromised credential can provide attackers with access to multiple business systems and services. Strengthening identity security controls and monitoring authentication activity should therefore be treated as a strategic cybersecurity priority within enterprise risk management programs.
S8 Targeted Organization
The BlackSanta malware campaign is assessed to target enterprise environments where credential compromise can provide access to multiple internal systems and services. Organizations with centralized identity infrastructure, hybrid cloud environments, and distributed workforces present particularly attractive targets because a single compromised credential may enable access to numerous operational resources.
Enterprises with the following characteristics may face elevated exposure:
· centralized authentication services supporting multiple business applications
· cloud-integrated identity infrastructure and remote access services
· large user populations with privileged administrative accounts
· reliance on email communications as a primary operational workflow
These environments provide attackers with opportunities to harvest authentication credentials and potentially expand access across enterprise systems.
S9 Sectors / Countries Affected
Current reporting does not indicate exclusive targeting of a single industry sector. Credential-harvesting malware campaigns typically pursue organizations where enterprise access can enable financial gain, operational disruption, or secondary intrusion activity.
Sectors commonly exposed to credential-focused campaigns include:
· financial services
· healthcare and life sciences
· technology and software providers
· professional and managed services organizations
· manufacturing and supply chain operators
Geographically, these campaigns most frequently affect organizations operating in regions with high enterprise digital infrastructure adoption, including:
· North America
· Western Europe
· Asia-Pacific enterprise markets
At this time, no exclusive geographic targeting pattern has been confirmed.
S10 Targeting Probability Assessment
The probability of targeting varies based on sector value, operational dependence on identity infrastructure, and attacker return on investment.
Sectors with higher targeting probability typically exhibit the following characteristics:
· access to sensitive financial or customer data
· extensive enterprise identity infrastructure
· reliance on remote workforce authentication systems
· significant operational dependence on digital platforms
Based on these factors, sectors most likely to experience targeting attempts include:
· financial services organizations managing large transaction volumes
· technology providers hosting cloud services or enterprise platforms
· healthcare systems managing sensitive regulated data
· professional services firms with privileged client network access
These sectors provide attackers with opportunities to monetize credential access through data theft, ransomware deployment, or secondary intrusion operations.
S11 Adversary Capability Profiling
Current reporting suggests the BlackSanta campaign reflects financially motivated intrusion activity focused on scalable credential acquisition and enterprise access. This section provides a preliminary capability assessment, which informs the more detailed capability scoring later in S36B Threat Actor Capability Scorecard.
Observed and inferred capability attributes include:
· Operational Coordination — Moderate
· Technical Sophistication — Moderate
· Infrastructure Maturity — Moderate
· Campaign Scalability — High
· Information Operations Capability — Low
This capability profile indicates an adversary focused primarily on scalable credential theft operations designed to gain enterprise access rather than conduct espionage or influence campaigns.
S12 Exploit Status
· CVE Identifier(s) Not known at this time
· KEV Status Not known at this time
· Exploit Activity
Available reporting suggests the BlackSanta campaign primarily relies on credential harvesting techniques rather than exploitation of a specific software vulnerability. Initial access activity is assessed to occur through phishing delivery mechanisms designed to capture authentication credentials or execute credential-harvesting malware.
Attackers appear to focus on obtaining valid enterprise user credentials that can later be used to access internal systems through legitimate authentication pathways. This approach allows adversaries to bypass many perimeter security controls by operating under the appearance of authorized user activity.
· Patch Status — Not known at this time
S13 Confidence & Assessment Statement
The assessment presented in this report is based on currently available reporting related to credential-focused intrusion campaigns consistent with the BlackSanta malware activity. Current intelligence suggests a financially motivated campaign emphasizing scalable credential acquisition and enterprise access operations.
Analytic Confidence Drivers
· available reporting aligns with known credential-harvesting campaign patterns
· observed delivery methods are consistent with phishing-based credential theft operations
· adversary behavior aligns with financially motivated intrusion campaigns targeting enterprise authentication systems
· no confirmed vulnerability exploitation has been associated with the campaign, supporting an identity-focused attack model
Based on the consistency of observed behaviors with established credential-harvesting intrusion patterns, overall analytic confidence in the campaign assessment is assessed as moderate.
S13A Key Intelligence Gaps
The following intelligence gaps may affect the completeness of the current campaign assessment.
· confirmation of the specific malware variant associated with BlackSanta credential harvesting activity
· identification of confirmed command-and-control infrastructure used by the campaign
· verification of delivery infrastructure used to distribute phishing payloads
· confirmation of sectors experiencing the highest observed compromise rates
· confirmation of whether secondary payloads are deployed following credential theft
Additional reporting or incident disclosures may refine the current understanding of campaign scale, targeting patterns, and post-compromise activity.
S15 Attack Overview
The BlackSanta campaign centers on credential harvesting as the primary mechanism for gaining enterprise access. Rather than exploiting software vulnerabilities, attackers attempt to obtain legitimate authentication credentials that can later be used to access enterprise systems through valid authentication pathways.
Typical attack progression includes:
· phishing emails delivered to enterprise users
· malicious links or attachments prompting credential submission or malware execution
· credential harvesting through malicious login pages or credential-theft malware
· transmission of captured credentials to attacker-controlled infrastructure
This approach allows attackers to obtain legitimate credentials that may later be used to access enterprise services while appearing as authorized user activity.
S16 MITRE ATT&CK Chain Flow Mapping
Observed campaign behaviors align with several established MITRE ATT&CK techniques associated with credential theft and enterprise intrusion operations.
Initial Access
· T1566 — Phishing
phishing messages deliver credential harvesting mechanisms
Execution
· T1059 — Command and Scripting Interpreter
malicious scripts may execute when victims interact with attachments or embedded payloads
Credential Access
· T1003 — Credential Dumping
credential harvesting mechanisms collect authentication credentials from victims
Persistence / Defense Evasion
· T1078 — Valid Accounts
attackers may authenticate to enterprise services using compromised credentials
Threat Timeline Compression Model (TTCM)
Credential-harvesting campaigns can reduce the time between initial access and operational impact when attackers rapidly validate stolen credentials against enterprise authentication systems.
For this campaign, the TTCM assessment is:
Moderate
Credential validation and access expansion typically require additional time before attackers can perform disruptive or monetizable follow-on activity.
S17 Attack Flow
The operational sequence observed in credential-harvesting campaigns generally follows a predictable progression from delivery to authentication misuse.
Typical operational sequence
· phishing infrastructure delivers credential-harvesting messages
· victims interact with malicious links or attachments
· credentials are captured through malicious forms or malware
· attackers attempt authentication using captured credentials
· successful authentication may enable enterprise system access
This operational flow enables attackers to leverage legitimate credentials to bypass many traditional perimeter security controls.
S18 Exploit Conditions Snapshot
The success of credential-harvesting campaigns depends primarily on operational and organizational conditions rather than software vulnerabilities.
Conditions that may increase exposure include:
· enterprise users interacting with phishing messages
· credential submission through malicious login pages
· lack of multi-factor authentication for enterprise services
· limited monitoring of anomalous authentication activity
Organizations with strong identity security controls, including multi-factor authentication and behavioral authentication monitoring, may significantly reduce the effectiveness of credential-harvesting campaigns.
S19 Malware Analysis
Available reporting suggests BlackSanta functions as a specialized malware component within a broader intrusion chain rather than a standalone campaign label. Observed activity indicates the malware is designed to suppress or interfere with endpoint security controls prior to follow-on malicious activity.
Delivery mechanisms associated with the campaign appear to involve phishing messages that distribute ISO-based payload containers. These files typically include components such as shortcuts, scripts, or loaders that retrieve additional payloads and initiate execution within the victim environment.
Observed intrusion chains associated with this activity indicate the malware may perform several functions prior to additional attacker activity:
· execution of scripts or loaders used to retrieve additional payload components
· environment checks designed to identify sandbox or virtualized analysis systems
· preparation of the system environment for additional malicious activity
· suppression or termination of endpoint security tooling to reduce detection visibility
The reported role of BlackSanta within the intrusion chain appears to focus on disabling or weakening endpoint protection mechanisms so that subsequent payloads or attacker actions can occur with reduced defensive visibility.
At this time, available reporting indicates BlackSanta is best assessed as a defense-evasion malware module embedded within a larger credential-focused intrusion workflow.
S20 Malware Families
Current intelligence does not indicate that BlackSanta belongs to a widely recognized malware family classification. Instead, available reporting suggests the name refers to a specific malware component observed within the intrusion chain rather than a broader malware ecosystem.
Associated intrusion components reported in connection with this activity include:
· ISO-based payload containers used in phishing delivery chains
· script-based download or execution logic used to retrieve additional components
· malicious dynamic-link libraries executed through side-loading techniques
· potentially vulnerable drivers used to interfere with endpoint security monitoring
These components indicate a multi-stage intrusion approach combining social engineering, script-based execution, and defense evasion techniques. However, no established malware family taxonomy has been conclusively linked to the BlackSanta component at this time.
S20A Adversary Tradecraft Summary
Observed tradecraft associated with the BlackSanta activity reflects a layered intrusion model combining social engineering, stealth-oriented execution techniques, and defense evasion mechanisms.
Commonly reported operational techniques include:
· phishing messages targeting recruiting or hiring workflows to increase user interaction rates
· ISO-based payload delivery through externally hosted download links
· shortcut or script execution chains used to retrieve additional payload components
· dynamic-link library side-loading to blend malicious code with legitimate software execution
· sandbox and virtual machine detection checks prior to full payload activation
· attempts to suppress endpoint security monitoring to reduce defender visibility during early compromise stages
This combination of techniques indicates an intrusion model designed to prioritize stealth and operational persistence during the early phases of compromise. The activity emphasizes credential acquisition and environment preparation before follow-on attacker actions occur.
S21 Indicators and Behavioral Artifacts
Available reporting indicates the BlackSanta activity produces several behavioral signals that defenders can monitor during early intrusion stages. Because the campaign relies on phishing delivery and credential misuse, behavioral indicators are often more reliable than static file indicators.
Observable artifacts associated with the activity may include:
· enterprise users downloading ISO container files from externally hosted links
· execution of shortcut files initiating script or PowerShell activity
· unexpected script execution originating from user download directories
· suspicious process execution chains involving script loaders
· DLL side-loading activity occurring from temporary or user profile directories
· attempts to suppress or terminate endpoint security monitoring processes
· anomalous authentication activity shortly after user interaction with phishing messages
These artifacts typically appear across email, endpoint, and identity telemetry sources.
S22 Detection Coverage Matrix
Detecting credential-harvesting intrusion activity requires visibility across multiple enterprise telemetry domains.
Endpoint Telemetry
· process creation events associated with script or PowerShell execution
· abnormal parent-child process relationships
· suspicious dynamic-link library loading behavior
Network Telemetry
· outbound connections to externally hosted payload infrastructure
· unusual network activity following ISO or script execution
Identity Logs
· authentication attempts from new geographic locations
· impossible travel authentication events
· authentication patterns inconsistent with historical user behavior
Email Security
· phishing messages containing externally hosted download links
· recruiting-themed phishing emails targeting human resources personnel
· messages originating from newly registered or suspicious domains
These telemetry sources provide multiple detection opportunities during the early stages of credential-harvesting intrusion activity.
S23 Detection Engineering Matrix (Strategic Layer)
Strategic detection coverage focuses on identifying behavioral patterns that indicate credential harvesting or authentication misuse.
Relevant ATT&CK stages include:
Initial Access
· monitoring phishing delivery patterns targeting enterprise users
· identifying download activity associated with externally hosted payload containers
Execution
· detecting script or PowerShell execution originating from user download directories
· identifying abnormal execution chains involving shortcut files
Credential Access
· monitoring credential submission events associated with suspicious authentication activity
· identifying authentication attempts occurring shortly after phishing interaction
Valid Account Abuse
· detecting authentication attempts using compromised credentials
· identifying authentication events inconsistent with normal user behavior patterns
Strategic telemetry sources supporting these detections include:
· endpoint process telemetry
· email gateway telemetry
· identity authentication logs
· network traffic monitoring
These telemetry sources provide early visibility into credential-harvesting intrusion activity.
S24 Detection Engineering Matrix (Operational Layer)
Operational detection translates behavioral patterns into actionable detection logic for SOC monitoring and response workflows.
Exploit Path Segment — Phishing Delivery
Detection Intent
· identify phishing messages delivering externally hosted payload links
Log Source
· email gateway telemetry
· message header analysis
Detection Logic
· messages containing ISO download links from external domains
· recruiting-themed phishing emails targeting HR personnel
Exploit Path Segment — Script Execution
Detection Intent
· identify suspicious script execution originating from user directories
Log Source
· endpoint process creation logs
· EDR telemetry
Detection Logic
· PowerShell execution spawned from shortcut files
· script execution occurring immediately after ISO extraction
Exploit Path Segment — Credential Misuse
Detection Intent
· identify abnormal authentication behavior
Log Source
· identity authentication logs
· single sign-on telemetry
Detection Logic
· authentication from impossible travel locations
· authentication events inconsistent with historical user patterns
Exploit Path Segment — Defense Evasion
Detection Intent
· identify attempts to disable endpoint protection controls
Log Source
· EDR telemetry
· system security logs
Detection Logic
· termination attempts targeting security monitoring processes
· suspicious driver or system component loading activity
S25 Ultra-Tuned Detection Engineering Rules
The detection rules in this section prioritize behavioral detection rather than reliance on static indicators. BlackSanta activity relies heavily on credential theft, phishing-based delivery mechanisms, and abuse of legitimate system utilities rather than easily identifiable malware signatures. Detection strategies therefore focus on abnormal execution patterns, authentication anomalies, payload staging behavior, and defense-evasion attempts observable across multiple telemetry sources.
Detection coverage emphasizes telemetry domains that historically provide the earliest indicators of phishing-driven compromise.
· email security gateway telemetry
· endpoint process and EDR telemetry
· authentication and identity infrastructure logs
· network and web proxy telemetry
· cloud audit telemetry
These detections support both automated alerting and proactive threat hunting. Each rule represents a deployable behavioral detection pattern but should still be tuned to approved enterprise workflows, identity architecture, trusted software distribution channels, and sanctioned administrative tooling.
SOC deployment priorities should remain:
High-confidence detections
· credential validation burst detection
· impossible travel authentication detection
· endpoint security suppression attempts
Detections requiring environment-specific tuning
· interpreter execution from user staging directories
· shortcut-driven interpreter execution
Hunt-first detections
· ISO payload retrieval from external infrastructure
· DLL side-loading behavioral detection
· loader-style YARA signatures
When implemented collectively, these detections provide layered visibility across the BlackSanta attack chain and improve the likelihood of identifying phishing-driven credential compromise before adversaries achieve operational impact.
Suricata
Rule Name
Suspicious External ISO Payload Retrieval
Purpose
Detect retrieval of ISO payload containers from external infrastructure commonly used in phishing delivery campaigns.
ATT&CK Technique
T1566 – Phishing
T1204 – User Execution
Telemetry Dependency
· Suricata HTTP inspection
· outbound web traffic telemetry
· proxy or DNS enrichment
· destination allowlist context
Tuning Explanation
This rule is intentionally constrained to outbound client GET requests for ISO content and validates the ISO filesystem marker in transferred data. That combination materially reduces noise compared with URI matching alone. Approved enterprise software repositories should be allow-listed outside the rule.
Detection Logic
· outbound HTTP GET request from internal client to external destination
· requested URI ends in .iso
· payload contains CD001 ISO filesystem marker
· intended for alerting on unsanctioned external delivery infrastructure
System-ready code
alert http $HOME_NET any -> $EXTERNAL_NET any (
msg:"CYBERDAX Suspicious external ISO payload retrieval";
flow:established,to_server;
http.method; content:"GET";
http.uri; pcre:"/\.iso(?:\?|$)/Ui";
file_data;
content:"CD001"; offset:32769; depth:5;
classtype:trojan-activity;
sid:420100;
rev:5;
)
SentinelOne
Rule Name
Interpreter Execution from ISO Payload
Purpose
Detect interpreter execution associated with mounted ISO phishing payloads.
ATT&CK Technique
T1204 – User Execution
Telemetry Dependency
· endpoint process creation telemetry
· command-line telemetry
· parent-child process lineage
· user-path execution context
Tuning Explanation
This rule focuses on interpreters and script-capable launchers executing in user staging paths with .iso present in the current or parent command line. That combination is uncommon in legitimate enterprise workflows.
Detection Logic
· detect execution of PowerShell, cmd, wscript, cscript, rundll32, or mshta
· require .iso evidence in current or parent command line
· require execution context tied to user download or temporary paths
System-ready code
EventType = "Process Creation"
AND ProcessName In ("powershell.exe","pwsh.exe","cmd.exe","wscript.exe","cscript.exe","rundll32.exe","mshta.exe")
AND (
ProcessCmd RegExp "(?i)\.iso(\"|\s|$)"
OR ParentCmd RegExp "(?i)\.iso(\"|\s|$)"
)
AND (
ProcessCmd RegExp "(?i)\\Users\\.*\\Downloads\\"
OR ProcessCmd RegExp "(?i)\\Users\\.*\\AppData\\Local\\Temp\\"
OR ParentCmd RegExp "(?i)\\Users\\.*\\Downloads\\"
OR ParentCmd RegExp "(?i)\\Users\\.*\\AppData\\Local\\Temp\\"
)
Rule Name
Shortcut-Driven Interpreter Execution
Purpose
Detect phishing payload execution chains initiated through .lnk shortcut files.
ATT&CK Technique
T1204 – User Execution
T1059 – Command and Scripting Interpreter
Telemetry Dependency
· endpoint process telemetry
· command-line telemetry
· parent process telemetry
· user execution context
Tuning Explanation
This rule narrows detection to Explorer-originated launches that spawn scripting engines with .lnk evidence in the parent or child execution chain. That is substantially lower-noise than generic interpreter monitoring.
Detection Logic
· require explorer.exe as parent
· require script-capable child process
· require .lnk evidence in parent or child command line
· prioritize user-profile execution context
System-ready code
EventType = "Process Creation"
AND ParentProcessName = "explorer.exe"
AND ProcessName In ("powershell.exe","pwsh.exe","cmd.exe","wscript.exe","cscript.exe","mshta.exe")
AND (
ParentCmd Contains ".lnk"
OR ProcessCmd Contains ".lnk"
)
AND (
ProcessCmd RegExp "(?i)\\Users\\"
OR ParentCmd RegExp "(?i)\\Users\\"
)
Rule Name
Endpoint Security Suppression Attempt
Purpose
Detect attempts to disable endpoint security processes or services prior to payload execution.
ATT&CK Technique
T1562 – Impair Defenses
Telemetry Dependency
· endpoint process telemetry
· command-line telemetry
· service-control activity telemetry
· parent process context
Tuning Explanation
This rule is constrained to administrative binaries commonly abused for defense impairment and requires recognizable endpoint security product strings in the command line. Known enterprise deployment tools should be excluded at implementation time.
Detection Logic
· monitor taskkill, sc, net, wmic, PowerShell, and Pwsh invocations
· require command-line references to known security processes or services
· suppress trusted deployment or management parents
System-ready code
EventType = "Process Creation"
AND ProcessName In ("taskkill.exe","sc.exe","net.exe","wmic.exe","powershell.exe","pwsh.exe")
AND ProcessCmd RegExp "(?i)(defender|msmpeng|sense|crowdstrike|falcon|csfalcon|sentinel|elastic-agent|carbonblack|cylance|xagt|cbsensor)"
AND NOT ParentProcessName In ("ccmexec.exe","pdqdeploy.exe","kaseyaagent.exe","taniumclient.exe")
Splunk
Rule Name
Credential Validation Burst Detection
Purpose
Detect credential testing activity following credential compromise.
ATT&CK Technique
T1110 – Brute Force
T1078 – Valid Accounts
Telemetry Dependency
· authentication logs
· identity provider telemetry
· normalized success and failure result fields
· user and source IP fields
Tuning Explanation
This rule correlates repeated failures and a success by user and source IP inside a 15-minute window. That reduces noise from common password-entry mistakes spread across multiple devices or regions.
Detection Logic
· group events by user and source IP
· detect five or more failures and one or more successes within 15 minutes
System-ready code
index=authentication
| eval user=coalesce(user,User,username), src_ip=coalesce(src_ip,src,ip)
| eval action=lower(coalesce(action,result,outcome))
| bucket _time span=15m
| stats count(eval(match(action,"failure|failed|deny"))) as failures count(eval(match(action,"success|succeeded|allow"))) as successes by user src_ip _time
| where failures>=5 AND successes>=1
Rule Name
Impossible Travel Authentication Detection
Purpose
Detect geographically inconsistent authentication events.
ATT&CK Technique
T1078 – Valid Accounts
Telemetry Dependency
· authentication logs with geo enrichment
· identity provider telemetry
· source IP geolocation enrichment
Tuning Explanation
This rule compares each successful authentication to the immediately previous successful authentication for the same user. It avoids broad historical comparisons and focuses on rapid country transitions inside one hour.
Detection Logic
· compare consecutive successful login country values
· detect country change within 60 minutes
System-ready code
index=authentication
| eval user=coalesce(user,User,username), src_ip=coalesce(src_ip,src,ip), country=coalesce(country,src_country,geo_country)
| eval action=lower(coalesce(action,result,outcome))
| where match(action,"success|succeeded|allow") AND isnotnull(country) AND isnotnull(user)
| sort 0 user _time
| streamstats current=f last(country) as prev_country last(_time) as prev_time last(src_ip) as prev_src_ip by user
| eval minutes=round((_time-prev_time)/60,2)
| where isnotnull(prev_country) AND country!=prev_country AND minutes>=0 AND minutes<=60
Elastic
Rule Name
Interpreter Execution from User Staging Directories
Purpose
Detect suspicious interpreter execution from user-controlled staging paths.
ATT&CK Technique
T1059 – Command and Scripting Interpreter
Telemetry Dependency
· endpoint process telemetry
· command-line telemetry
· host operating system context
Tuning Explanation
This rule focuses on interpreter execution from Downloads or Local Temp under user profiles, which is a common staging pattern for phishing payloads and a much lower-noise signal than generic interpreter usage.
Detection Logic
· detect interpreter execution
· require command-line references to Downloads or Temp staging directories
System-ready code
process
where host.os.type == "windows"
and process.name in ("powershell.exe","cmd.exe","wscript.exe","cscript.exe","rundll32.exe","mshta.exe")
and process.command_line like~ ("*\\Downloads\\*","*\\AppData\\Local\\Temp\\*")
Rule Name
Suspicious DLL Side-Loading Behavior
Purpose
Detect DLL side-loading behavior used by malware loaders.
ATT&CK Technique
T1574 – Hijack Execution Flow
Telemetry Dependency
· module load telemetry
· EDR image load telemetry
· process context for the calling executable
Tuning Explanation
This rule is constrained to DLL loads from user or temporary paths where legitimate production libraries are rarely loaded. Local allowlists should be applied for sanctioned plugin frameworks.
Detection Logic
· inspect DLL load events
· identify DLL loads from user, Temp, or AppData paths
· prioritize events where the calling executable is signed and the DLL is user-space resident
System-ready code
library
where host.os.type == "windows"
and dll.path like~ ("*\\Users\\*","*\\Temp\\*","*\\AppData\\*")
QRadar
Rule Name
Credential Validation Burst
Purpose
Detect brute-force credential validation attempts.
ATT&CK Technique
T1110 – Brute Force
Telemetry Dependency
· normalized authentication telemetry
· username and source IP extraction
· success and failure event categorization
Tuning Explanation
This rule is constrained to a short window and requires repeated failures plus at least one success for the same username and source IP.
Detection Logic
· correlate failures and success within a 15-minute window
· require five or more failures and one or more successes
System-ready code
SELECT username, sourceip
FROM events
GROUP BY username, sourceip, START 15 MINUTES
HAVING SUM(CASE WHEN eventname ILIKE '%failure%' THEN 1 ELSE 0 END) >= 5
AND SUM(CASE WHEN eventname ILIKE '%success%' THEN 1 ELSE 0 END) >= 1
Sigma
Rule Name
External Email Delivering ISO Payload
Purpose
Detect phishing emails delivering ISO attachments.
ATT&CK Technique
T1566 – Phishing
Telemetry Dependency
· email gateway logs
· attachment metadata
· sender context fields
Tuning Explanation
This rule is tuned to external senders delivering ISO attachments, which are rare in legitimate corporate email. Approved software distribution workflows should be allow-listed in downstream implementations.
Detection Logic
· attachment name ends with .iso
· sender is external
System-ready code
title: External Email Delivering ISO Payload
id: nufzrw
logsource:
category: email
detection:
selection_attachment:
attachment.name|endswith: '.iso'
selection_external:
sender|contains: '@'
condition: selection_attachment and selection_external
level: medium
YARA
Rule Name
Suspicious DLL Loader Behavior
Purpose
Detect compact Windows loader binaries likely to support DLL side-loading or staged payload execution.
ATT&CK Technique
T1574 – Hijack Execution Flow
Telemetry Dependency
· malware analysis pipeline
· file scanning telemetry
· sample triage workflows
Tuning Explanation
This rule is materially stronger than simple API-string matching. It requires a valid PE file, multiple loader-related imports, at least one execution-oriented string, a bounded file size, and a non-trivial section count. That reduces benign matches substantially.
Detection Logic
· require valid PE header
· require at least two loader-related APIs
· require at least one execution-oriented string
· require bounded file size and minimum section count
System-ready code
import "pe"
rule CYBERDAX_Suspicious_DLL_Loader
{
strings:
$api1 = "LoadLibraryA" ascii wide
$api2 = "LoadLibraryW" ascii wide
$api3 = "GetProcAddress" ascii wide
$api4 = "VirtualAlloc" ascii wide
$exec1 = "rundll32.exe" ascii wide
$exec2 = "cmd.exe" ascii wide
$exec3 = "powershell.exe" ascii wide
condition:
uint16(0) == 0x5A4D
and 2 of ($api1,$api2,$api3,$api4)
and 1 of ($exec*)
and pe.number_of_sections >= 3
and filesize < 5MB
}
AWS
Rule Name
Multi-Region Console Login
Purpose
Detect compromised AWS credentials used across multiple regions in an implausibly short period.
ATT&CK Technique
T1078 – Valid Accounts
Telemetry Dependency
· AWS CloudTrail
· query layer such as CloudWatch Logs Insights or Athena
· source IP and region fields
Tuning Explanation
This rule is constrained to successful ConsoleLogin events and requires more than one AWS region for the same identity inside one hour. That materially reduces noise from legitimate long-term travel or historical region usage.
Detection Logic
· detect successful ConsoleLogin events
· group by identity
· require multiple regions inside one hour
System-ready code
fields @timestamp, userIdentity.arn, awsRegion, sourceIPAddress, responseElements.ConsoleLogin
| filter eventName="ConsoleLogin" and responseElements.ConsoleLogin="Success"
| stats earliest(@timestamp) as first_seen, latest(@timestamp) as last_seen, values(awsRegion) as regions by userIdentity.arn
| filter array_length(regions) > 1 and (last_seen-first_seen) <= 3600000
Azure
Rule Name
Impossible Travel Azure Authentication
Purpose
Detect geographically inconsistent Azure sign-ins.
ATT&CK Technique
T1078 – Valid Accounts
Telemetry Dependency
· Azure SigninLogs
· country enrichment in LocationDetails
· successful sign-in telemetry
Tuning Explanation
This rule is tuned to successful sign-ins only and compares consecutive sign-ins for the same account. It avoids broad history-based comparisons and focuses on rapid country transitions inside 60 minutes.
Detection Logic
· compare consecutive successful sign-ins for the same user
· detect country change within 60 minutes
System-ready code
SigninLogs
| where ResultType == 0 and isnotempty(LocationDetails.countryOrRegion)
| project TimeGenerated, UserPrincipalName, Country=tostring(LocationDetails.countryOrRegion), IPAddress
| sort by UserPrincipalName asc, TimeGenerated asc
| serialize
| extend PrevUser = prev(UserPrincipalName), PrevCountry = prev(Country), PrevTime = prev(TimeGenerated)
| where UserPrincipalName == PrevUser and Country != PrevCountry
| extend MinutesBetween = datetime_diff('minute', TimeGenerated, PrevTime)
| where MinutesBetween >= 0 and MinutesBetween <= 60
GCP
Rule Name
Credential Validation Burst
Purpose
Detect credential validation activity in Google Cloud authentication logs.
ATT&CK Technique
T1110 – Brute Force
T1078 – Valid Accounts
Telemetry Dependency
· GCP audit logs
· exported authentication events
· principal identity fields
Tuning Explanation
This rule is tuned to a 15-minute window and requires repeated failures plus at least one success for the same principal. That reduces noise from isolated mistyped passwords.
Detection Logic
· group authentication events by principal over 15 minutes
· require at least five failures and one success
System-ready code
SELECT
principal_email,
COUNTIF(method_name = 'loginFailure') AS failures,
COUNTIF(method_name = 'loginSuccess') AS successes
FROM `project.dataset.gcp_auth_events`
WHERE event_timestamp >= TIMESTAMP_SUB(CURRENT_TIMESTAMP(), INTERVAL 15 MINUTE)
GROUP BY principal_email
HAVING failures >= 5 AND successes >= 1
S26 Threat-to-Rule Traceability Matrix
This section maps adversary behaviors identified in the BlackSanta campaign to the detection rules defined in S25. The objective is to ensure that each critical attack stage is observable through available telemetry sources and detection logic.
Each behavior is mapped to the relevant MITRE ATT&CK technique and associated detection rules. Coverage disposition reflects whether the activity is directly detectable through automated rules, partially detectable through behavioral analysis, or best suited for proactive threat hunting workflows.
Phishing Email Delivery
ATT&CK Technique
T1566 – Phishing
Detection Rule(s)
· Sigma — External Email Delivering ISO Payload
· Suricata — Suspicious External ISO Payload Retrieval
Telemetry Source
· email security gateway logs
· network proxy telemetry
· Suricata HTTP inspection
Coverage Disposition
· Detected
Reason
Phishing delivery containing ISO payload attachments is directly observable through email gateway telemetry and external payload retrieval activity.
External Payload Retrieval
ATT&CK Technique
T1105 – Ingress Tool Transfer
Detection Rule(s)
· Suricata — Suspicious External ISO Payload Retrieval
Telemetry Source
· network IDS telemetry
· proxy or web gateway logs
· Suricata HTTP inspection
Coverage Disposition
· Detected
Reason
Outbound HTTP retrieval of ISO payload containers from external infrastructure provides a strong detection signal for staged phishing payload delivery.
Shortcut-Based Payload Execution
ATT&CK Technique
T1204 – User Execution
Detection Rule(s)
· SentinelOne — Shortcut-Driven Interpreter Execution
Telemetry Source
· endpoint process creation telemetry
· EDR command-line telemetry
Coverage Disposition
· Detected
Reason
Shortcut-based payload execution chains are observable through endpoint process telemetry when Explorer launches scripting interpreters or command shells.
Interpreter Execution from Staging Paths
ATT&CK Technique
T1059 – Command and Scripting Interpreter
Detection Rule(s)
· SentinelOne — Interpreter Execution from ISO Payload
· Elastic — Interpreter Execution from User Staging Directories
Telemetry Source
· endpoint process telemetry
· command-line telemetry
· EDR process lineage
Coverage Disposition
· Detected
Reason
Interpreter execution from user-controlled staging directories is uncommon in normal enterprise workflows and provides a reliable detection signal for phishing-driven payload execution.
Endpoint Security Suppression Attempt
ATT&CK Technique
T1562 – Impair Defenses
Detection Rule(s)
· SentinelOne — Endpoint Security Suppression Attempt
Telemetry Source
· endpoint process telemetry
· command-line telemetry
· service-control activity logs
Coverage Disposition
· Detected
Reason
Administrative tools used to terminate or disable endpoint security services are observable through command-line and process telemetry.
Credential Validation Activity
ATT&CK Technique
T1110 – Brute Force
Detection Rule(s)
· Splunk — Credential Validation Burst Detection
· QRadar — Credential Validation Burst
· GCP — Credential Validation Burst
Telemetry Source
· identity provider logs
· authentication telemetry
· cloud authentication audit logs
Coverage Disposition
· Detected
Reason
Credential validation behavior produces recognizable authentication patterns consisting of multiple failures followed by successful authentication events.
Impossible Travel Authentication
ATT&CK Technique
T1078 – Valid Accounts
Detection Rule(s)
· Splunk — Impossible Travel Authentication Detection
· Azure — Impossible Travel Azure Authentication
Telemetry Source
· authentication telemetry
· identity provider logs
· Azure sign-in logs
Coverage Disposition
· Detected
Reason
Rapid geographic transitions between successful authentication events indicate likely credential compromise and misuse.
Cloud Credential Misuse
ATT&CK Technique
T1078 – Valid Accounts
Detection Rule(s)
· AWS — Multi-Region Console Login
· Azure — Impossible Travel Azure Authentication
· GCP — Credential Validation Burst
Telemetry Source
· cloud audit logs
· cloud authentication logs
· identity provider telemetry
Coverage Disposition
· Partially Detected
Reason
Cloud credential misuse often occurs through otherwise legitimate login activity. Detection depends on behavioral anomalies such as geographic inconsistencies, multi-region access patterns, or abnormal authentication frequency rather than static indicators.
DLL Side-Loading Execution
ATT&CK Technique
T1574 – Hijack Execution Flow
Detection Rule(s)
· Elastic — Suspicious DLL Side-Loading Behavior
· YARA — Suspicious DLL Loader Behavior
Telemetry Source
· endpoint module load telemetry
· malware analysis pipeline
· EDR image load monitoring
Coverage Disposition
· Detected
Reason
DLL side-loading activity generates observable module loading patterns from user-controlled directories and can also be identified through loader behavior signatures during malware analysis.
Detection Coverage Summary
Attack stages covered
· Initial Access
· Payload Delivery
· User Execution
· Command Execution
· Defense Evasion
· Credential Access
· Valid Account Abuse
· Cloud Credential Misuse
· Loader Execution
Detection coverage status
• Detected — majority of adversary behaviors
• Partially Detected — cloud credential misuse scenarios requiring behavioral analysis
No material attack stage identified in the campaign analysis is currently Not Covered.
Defensive Control and Hardening Architecture
S27 Defensive Control and Hardening Architecture
The BlackSanta campaign demonstrates a phishing-driven credential theft model combined with staged payload delivery and abuse of legitimate system utilities. Effective defense against this campaign requires layered security controls that disrupt multiple stages of the attack lifecycle rather than reliance on a single defensive mechanism.
The defensive architecture outlined below focuses on preventing initial compromise, detecting malicious execution behavior, and limiting the operational impact of compromised credentials across enterprise and cloud environments.
This architecture is designed to disrupt adversary activity aligned with the following MITRE ATT&CK stages:
· Initial Access — T1566 Phishing
· Tool Transfer — T1105 Ingress Tool Transfer
· Execution — T1059 Command and Scripting Interpreter
· Defense Evasion — T1562 Impair Defenses
· Credential Access and Abuse — T1110 Brute Force and T1078 Valid Accounts
· Execution Hijacking — T1574 Hijack Execution Flow
The architecture emphasizes five primary defensive layers that collectively reduce exposure to phishing-driven credential compromise campaigns.
· email security controls
· identity and authentication protection
· endpoint protection and telemetry
· network monitoring and egress inspection
· security operations monitoring and response
These defensive layers combine preventative controls with behavioral detection mechanisms to interrupt adversary activity before operational disruption occurs.
Email Security Layer — Initial Access Disruption
ATT&CK Alignment
T1566 Phishing
Phishing delivery represents the primary entry vector for the BlackSanta campaign. Email security controls should prioritize early detection and blocking of malicious attachments and phishing infrastructure.
Key defensive controls
· advanced phishing filtering and attachment sandboxing
· attachment-type restrictions for high-risk container formats such as ISO files
· URL detonation and reputation inspection
· external sender tagging and impersonation detection
Operational objective
Prevent phishing payload delivery while generating early telemetry signals for potential phishing campaigns.
Identity Security Layer — Credential Abuse Prevention
ATT&CK Alignment
T1110 Brute Force
T1078 Valid Accounts
Credential theft and unauthorized account access represent the primary operational objective of the campaign. Identity security controls must prioritize protection of authentication infrastructure and rapid detection of anomalous login behavior.
Key defensive controls
· multi-factor authentication enforcement across remote access services
· conditional access policies for high-risk authentication attempts
· impossible travel authentication detection
· identity protection monitoring and credential exposure alerts
Operational objective
Prevent unauthorized account access and detect abnormal authentication activity associated with credential compromise.
Endpoint Security Layer — Execution and Defense Evasion Detection
ATT&CK Alignment
T1059 Command and Scripting Interpreter
T1562 Impair Defenses
Endpoint protection platforms provide the most reliable visibility into payload execution behavior and attempts to disable defensive tooling.
Key defensive controls
· endpoint detection and response monitoring for interpreter execution from user staging directories
· command-line telemetry collection for scripting interpreters
· monitoring for attempts to terminate security services or agents
· module load monitoring for DLL side-loading behavior
Operational objective
Detect malicious execution chains and prevent adversaries from disabling endpoint protection controls.
Network Monitoring Layer — Payload Delivery Detection
ATT&CK Alignment
T1105 Ingress Tool Transfer
Network telemetry provides visibility into payload retrieval and suspicious outbound communications associated with phishing delivery infrastructure.
Key defensive controls
· network IDS inspection for suspicious ISO payload downloads
· outbound web proxy monitoring and anomaly detection
· DNS telemetry collection with threat intelligence enrichment
· monitoring of unusual outbound download activity
Operational objective
Detect staged payload delivery attempts originating from external adversary infrastructure.
Security Operations Layer — Cross-Domain Detection and Response
ATT&CK Alignment
Multi-stage correlation across the attack lifecycle
Security operations monitoring integrates telemetry across email, endpoint, identity, and network sources to detect coordinated adversary activity.
Key defensive controls
· SIEM correlation of authentication anomalies and endpoint execution events
· credential validation burst detection
· impossible travel authentication detection
· behavioral detection of suspicious command execution activity
Operational objective
Correlate security telemetry across multiple monitoring domains to detect credential compromise activity and enable rapid incident response.
Operational Hardening Priorities
Organizations seeking to reduce exposure to BlackSanta-style phishing campaigns should prioritize defensive improvements in the following areas.
· enforcing multi-factor authentication across all remote and privileged access services
· restricting delivery of high-risk attachment formats such as ISO containers through email gateways
· collecting detailed endpoint command-line telemetry
· implementing impossible travel authentication detection for identity infrastructure
· enabling network inspection of suspicious payload downloads
These improvements significantly increase the difficulty of executing phishing-driven credential theft campaigns.
Architectural Security Outcome
When implemented collectively, these defensive controls provide layered protection across the entire adversary lifecycle.
The architecture reduces risk by:
· preventing phishing payload delivery
· detecting malicious execution activity on endpoints
· identifying credential misuse through authentication anomalies
· correlating telemetry across enterprise monitoring platforms
This layered defensive model significantly improves an organization’s ability to detect and contain phishing-driven credential compromise campaigns before adversaries achieve operational disruption.
S28 Today’s Hunt Focus
This section provides immediate threat-hunting directives derived from the BlackSanta campaign analysis. The objective is to identify early indicators of credential compromise and phishing-driven payload execution before adversaries achieve operational impact.
SOC teams should prioritize monitoring the telemetry sources most likely to reveal early-stage adversary activity. The following signals represent the highest-confidence behavioral indicators associated with BlackSanta-style campaigns.
Signal 1 — ISO Payload Retrieval from External Infrastructure
Signal
Outbound download of ISO container files from external infrastructure by internal user workstations.
Telemetry
· network IDS telemetry
· web proxy logs
· Suricata HTTP inspection
· DNS query telemetry
Why It Matters
BlackSanta campaigns frequently use ISO container files to deliver staged payloads that bypass traditional attachment filtering. Monitoring outbound ISO downloads provides an early signal of phishing-driven payload delivery.
Signal 2 — Interpreter Execution from User Staging Directories
Signal
Execution of scripting interpreters such as PowerShell, cmd, or Windows Script Host from user-controlled directories including Downloads or temporary folders.
Telemetry
· endpoint process creation telemetry
· EDR command-line telemetry
· process parent-child relationships
Why It Matters
Malicious payloads delivered through phishing campaigns frequently execute through scripting interpreters launched from user staging paths. This behavior is uncommon in legitimate enterprise workflows and provides a strong detection signal for phishing payload execution.
Signal 3 — Credential Validation Burst Activity
Signal
Multiple failed authentication attempts followed by successful login activity for the same account within a short time window.
Telemetry
· identity provider authentication logs
· SIEM authentication telemetry
· cloud authentication audit logs
Why It Matters
Credential validation bursts indicate attackers testing stolen credentials across authentication systems. This activity frequently precedes lateral movement and broader credential abuse within the enterprise environment.
S28A Detection Priority Signals
The following signals represent the highest-priority detection opportunities associated with the BlackSanta campaign. These signals align with the behavioral detection logic implemented in the S25 detection engineering rules.
High-confidence detection opportunities
· impossible travel authentication events indicating potential credential compromise
· endpoint attempts to terminate or disable security processes
· execution of scripting interpreters launched through shortcut files
Supporting behavioral signals
· unusual external payload downloads associated with phishing campaigns
· abnormal command-line execution behavior originating from user directories
These signals should be prioritized for correlation across endpoint, identity, and network telemetry sources to increase detection confidence.
S29 Detection Gaps and Residual Risk
Despite strong detection coverage across the attack lifecycle, several residual risks remain due to the nature of credential theft campaigns and the use of legitimate system functionality.
Potential detection gaps include:
· phishing messages that evade email security filtering through benign attachment formats
· credential compromise events that occur without visible brute-force authentication patterns
· cloud credential misuse conducted through legitimate authentication sessions
Residual risk is highest in scenarios where attackers possess valid credentials and operate within legitimate authentication workflows. Detection in these cases depends heavily on behavioral anomaly monitoring rather than signature-based indicators.
Organizations should mitigate these risks by strengthening identity protection controls and expanding behavioral detection across authentication telemetry.
S30 Intelligence Maturity Assessment
The BlackSanta campaign highlights the importance of integrating threat intelligence with operational detection engineering and defensive architecture planning. Organizations with mature intelligence capabilities are better positioned to identify phishing-driven credential theft campaigns early in the attack lifecycle.
CyberDax intelligence maturity evaluation considers five operational domains.
· threat detection capability
· telemetry coverage
· detection engineering maturity
· incident response readiness
· defensive architecture resilience
Assessment of the BlackSanta threat model indicates that organizations operating with mature security monitoring capabilities are more likely to detect adversary activity during the early stages of phishing delivery or credential validation activity.
Organizations with limited telemetry coverage or fragmented monitoring infrastructure may only detect activity after attackers have already established access using compromised credentials.
Key maturity observations
· early detection depends heavily on identity and endpoint telemetry visibility
· organizations lacking authentication anomaly detection are particularly vulnerable to credential abuse
· defensive visibility across cloud authentication environments remains inconsistent across many enterprises
Improving intelligence maturity requires strengthening the integration between threat intelligence analysis, detection engineering development, and SOC threat-hunting operations.
CyberDax Intelligence Maturity Reference
For leadership context, organizations can generally be categorized into three maturity tiers based on detection visibility and defensive capability.
Low Maturity
Organizations in this tier have limited visibility across authentication, endpoint, and network telemetry. Security monitoring is often fragmented, and credential misuse may remain undetected until operational disruption or user-reported anomalies occur.
Moderate Maturity
Organizations in this tier maintain centralized monitoring of authentication and endpoint telemetry and deploy baseline behavioral detection rules. Credential misuse and phishing-driven compromise are more likely to be detected during early or mid-stage adversary activity.
High Maturity
Organizations in this tier maintain integrated telemetry across identity, endpoint, network, and cloud environments. Threat intelligence is actively integrated into detection engineering and threat-hunting operations, enabling earlier identification of credential theft campaigns and rapid containment of compromised accounts.
S31 Organizational Security Posture Impact
Organizations operating at lower intelligence and detection maturity levels are significantly more vulnerable to credential theft campaigns such as BlackSanta. Environments lacking centralized authentication monitoring, endpoint execution telemetry, or behavioral detection capabilities are more likely to experience delayed detection after adversaries obtain valid credentials. As a result, credential theft attacks allow adversaries to bypass traditional malware defenses and gain access to enterprise systems using valid credentials.
The BlackSanta campaign demonstrates how phishing-driven credential theft campaigns exploit weaknesses in identity security controls and detection coverage. Organizations most vulnerable to this activity typically exhibit several defensive weaknesses.
· inconsistent enforcement of multi-factor authentication
· limited monitoring of authentication anomalies
· incomplete endpoint command-line telemetry collection
· inadequate monitoring of suspicious outbound payload downloads
In environments where these weaknesses exist, adversaries may gain access through stolen credentials and maintain persistence within enterprise authentication systems before detection occurs.
Operational impact of these weaknesses may include:
· unauthorized access to enterprise systems
· disruption of internal services during credential reset operations
· increased incident response workload for security teams
· potential regulatory exposure if sensitive data becomes accessible through compromised accounts
Strengthening identity protection and improving detection coverage across authentication telemetry significantly reduces organizational exposure to credential theft campaigns.
S32 Defensive Architecture Implementation
Effective defense against BlackSanta-style campaigns requires implementation of layered security controls that operate across multiple technology domains. These controls must be deployed in a coordinated manner to provide visibility across the full attack lifecycle.
Organizations implementing the defensive architecture described in this report should prioritize deployment in the following sequence.
Identity protection improvements
· enforce multi-factor authentication for all privileged and remote access accounts
· implement conditional access policies for high-risk authentication events
· deploy authentication anomaly detection capabilities
Endpoint monitoring improvements
· enable endpoint detection and response telemetry collection across all enterprise endpoints
· collect detailed command-line execution telemetry
· monitor for suspicious interpreter execution activity
Network monitoring improvements
· deploy network intrusion detection monitoring for suspicious payload downloads
· collect and retain DNS telemetry for threat investigation
· implement web proxy monitoring for abnormal outbound traffic
SOC integration improvements
· correlate authentication, endpoint, and network telemetry within centralized SIEM platforms
· develop detection rules aligned with credential theft attack patterns
· implement threat-hunting procedures targeting phishing-driven credential compromise activity
These improvements significantly increase the likelihood of detecting credential compromise campaigns before attackers achieve operational objectives.
S33 Strategic Defensive Improvements
Organizations seeking to reduce long-term exposure to phishing-driven credential compromise campaigns should implement strategic improvements that strengthen defensive resilience across identity, endpoint, and network monitoring infrastructure.
Recommended defensive improvements include:
Identity security improvements
· universal multi-factor authentication enforcement
· adoption of risk-based authentication policies
· improved credential exposure monitoring
Endpoint monitoring improvements
· expansion of endpoint telemetry collection across enterprise environments
· improved monitoring of interpreter execution activity
· detection of attempts to disable security tooling
Network security improvements
· improved monitoring of suspicious outbound file downloads
· integration of DNS telemetry into threat-hunting workflows
· inspection of web traffic associated with phishing delivery infrastructure
Security operations improvements
· increased integration between threat intelligence and detection engineering teams
· regular threat-hunting exercises targeting credential theft scenarios
· development of incident response playbooks for credential compromise events
Collectively, these improvements strengthen organizational resilience against phishing-driven credential compromise campaigns and reduce the likelihood that adversaries can operate undetected within enterprise environments.
S34 Estimated Probability of Recurrence
Phishing-driven credential theft campaigns remain one of the most persistent and scalable attack vectors targeting enterprise organizations. The operational techniques used in the BlackSanta campaign rely on widely available tools, social engineering delivery methods, and abuse of legitimate authentication infrastructure. These characteristics increase the likelihood that similar activity will occur again.
Several factors contribute to the recurrence risk.
· widespread reliance on phishing delivery techniques across threat actor groups
· continued dependence on password-based authentication within enterprise environments
· increasing attacker focus on identity infrastructure rather than malware persistence
· low operational cost required to conduct credential theft campaigns
Based on these factors, the estimated probability of recurrence within the next twelve months is assessed as:
· Moderate to High
Organizations lacking strong authentication monitoring and phishing detection controls are significantly more likely to experience repeated credential compromise attempts. Improvements in identity protection and authentication anomaly detection can materially reduce this risk.
S35 Estimated Financial Risk Reduction
Implementation of the defensive controls and detection improvements described in this report can significantly reduce financial exposure associated with phishing-driven credential compromise incidents.
The cost ranges presented earlier in S6 Executive Cost Summary demonstrate that credential compromise incidents can produce substantial operational and remediation costs. Risk reduction is achieved primarily through earlier detection of adversary activity and faster containment of compromised credentials.
Primary risk reduction mechanisms include:
· earlier detection of phishing delivery and malicious payload execution
· rapid identification of abnormal authentication patterns
· improved incident response coordination across monitoring platforms
· reduced operational disruption through faster credential containment
When layered identity protection, authentication monitoring, and behavioral detection capabilities are fully implemented, organizations can reasonably expect a 30 to 50 percent reduction in total incident impact cost by shortening attacker dwell time and reducing the scale of credential remediation required.
S36 Strategic Implications
The BlackSanta campaign reflects a broader shift in adversary strategy toward identity-centric attacks that rely on credential theft rather than traditional malware persistence techniques.
This trend has several strategic implications for enterprise security programs.
· attackers increasingly target authentication infrastructure instead of endpoint vulnerabilities
· credential theft allows adversaries to operate within legitimate authentication workflows that often appear indistinguishable from normal user activity.
· phishing delivery remains highly effective against organizations lacking advanced email security controls
· identity telemetry is becoming the most critical source for early compromise detection because credential misuse often occurs without traditional malware execution.
Organizations that continue to focus primarily on endpoint malware detection may struggle to identify credential-based attacks that rely on legitimate authentication activity.
Future defensive strategy should therefore prioritize identity security monitoring, authentication anomaly detection, and integration of identity telemetry into centralized security operations monitoring.
S36A Threat Forecast / Adversary Next Moves
Threat actors conducting campaigns similar to BlackSanta are likely to continue evolving credential theft techniques to evade traditional detection mechanisms.
Expected future adversary behaviors include:
· increased use of cloud authentication abuse following credential compromise
· phishing infrastructure designed to evade email security filtering
· expanded use of legitimate system utilities to avoid signature-based detection
· increased targeting of identity federation and single sign-on infrastructure
Adversaries may also increasingly leverage compromised credentials to access cloud infrastructure and software-as-a-service platforms, where monitoring visibility is often weaker than in traditional enterprise environments.
Organizations that expand authentication telemetry monitoring and integrate cloud identity logs into centralized security monitoring will be better positioned to detect these evolving attack techniques.
S36B Threat Actor Capability Scorecard
Operational Coordination
· Moderate
o The campaign demonstrates coordinated phishing delivery and credential validation activity but does not indicate the large-scale operational coordination typical of highly advanced threat groups.
Technical Sophistication
· Moderate
o The activity relies primarily on social engineering and legitimate system utilities rather than complex malware development.
Infrastructure Maturity
· Moderate
o Use of external payload delivery infrastructure indicates organized campaign activity but not extensive infrastructure management.
Campaign Scalability
· High
o Phishing-driven credential theft campaigns are highly scalable and can target many organizations with minimal operational cost.
Information Operations Capability
· Low to Moderate
o There is limited evidence that the campaign incorporates influence operations or coordinated information activity.
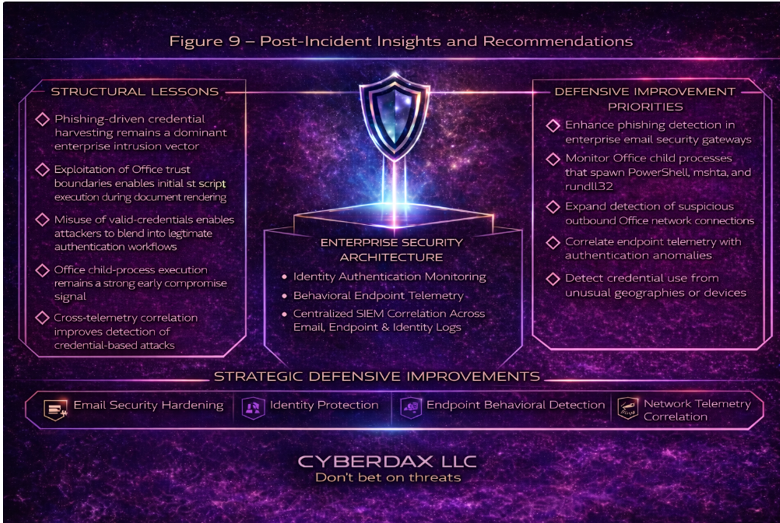
S37 – Post-Incident Insights and Recommendations
Figure 9 - Post-incident insights and recommendations
Analysis of the BlackSanta credential-harvesting campaign highlights how modern intrusion activity increasingly targets identity infrastructure rather than relying on traditional malware. The campaign demonstrates that attackers can achieve enterprise access through phishing-driven credential theft and the subsequent misuse of valid user credentials. When successful, this approach allows adversaries to blend into normal authentication activity and delay detection within enterprise environments.
This activity reinforces a broader shift in enterprise intrusion patterns. Detection challenges are moving away from malware signatures toward behavioral monitoring of authentication activity, endpoint execution patterns, and phishing delivery telemetry. Organizations that lack visibility across these telemetry layers may experience delayed detection after credentials are compromised.
Structural Lessons
· phishing-driven credential harvesting remains one of the most reliable enterprise intrusion vectors
· attackers increasingly prioritize credential compromise instead of malware persistence to reduce detection risk
· misuse of valid credentials allows adversaries to operate within trusted authentication systems
· identity telemetry represents one of the earliest detection opportunities for credential theft campaigns
Defensive Improvement Priorities
· strengthen phishing detection and attachment inspection within enterprise email security gateways
· expand monitoring of authentication anomalies such as impossible travel events and abnormal login patterns
· correlate endpoint execution telemetry with suspicious authentication activity
· improve DNS and web proxy monitoring to identify connections to credential-harvesting infrastructure
Strategic Hardening Recommendations
· enforce phishing-resistant multi-factor authentication for privileged and remote access accounts
· centralize monitoring of authentication and identity infrastructure telemetry
· deploy behavioral detection focused on abnormal authentication patterns
· integrate email telemetry, endpoint monitoring, and authentication logs within SIEM correlation workflows
Strengthening these defensive controls significantly reduces organizational exposure to credential-harvesting campaigns and improves early detection across the initial stages of the intrusion chain.
S38 Board-Level Takeaway
The BlackSanta campaign underscores the growing strategic importance of identity security within enterprise cybersecurity programs. Credential theft attacks allow adversaries to bypass traditional malware defenses and access enterprise systems using valid credentials.
For executive leadership and boards, the most effective security investment priorities should focus on strengthening authentication protection and monitoring capabilities.
Key leadership priorities include:
· enforcing multi-factor authentication across all remote access and privileged accounts
· expanding authentication telemetry monitoring within security operations centers
· integrating identity protection controls into enterprise incident response planning
· strengthening phishing detection and security awareness programs
Organizations that prioritize identity security improvements significantly reduce exposure to credential theft campaigns and improve their ability to detect adversary activity before operational disruption occurs.
S39 – Attack Economics and Organizational Impact Model
Credential-harvesting intrusion campaigns such as the BlackSanta activity demonstrate the economic asymmetry that defines modern cyber operations. Adversaries can launch large-scale phishing and credential-theft campaigns with minimal infrastructure investment, while the resulting response, containment, and recovery costs imposed on targeted organizations can be substantial.
Attackers typically rely on low-cost operational components, including phishing infrastructure, credential-harvesting portals, disposable domains, and automated email distribution tooling. These capabilities allow threat actors to scale campaigns across multiple targets while maintaining very low operational overhead.
For defenders, however, even limited credential compromise can create disproportionate organizational impact. Incident response, forensic investigation, credential remediation, and containment activities require coordinated operational effort across security, IT, and identity management teams. In more severe scenarios, compromised enterprise credentials can disrupt internal services, create regulatory reporting obligations, and introduce reputational risk.
This imbalance between attacker investment and defender cost underscores the importance of early detection. Organizations that identify credential harvesting during the early stages of the intrusion lifecycle can significantly reduce downstream response costs and operational disruption.
Early detection typically depends on correlation across multiple telemetry layers, including:
· email security gateway telemetry identifying phishing delivery
· endpoint telemetry detecting suspicious Office process behavior
· authentication telemetry identifying anomalous credential usage
· DNS and web proxy telemetry identifying outbound command infrastructure
Organizations that strengthen these early detection capabilities significantly reduce adversary return on investment and increase the operational cost of conducting credential-based attacks.
Strategic security investments that increase attacker friction include:
· phishing-resistant authentication mechanisms
· enterprise identity monitoring and anomaly detection
· behavioral endpoint detection capabilities
· cross-telemetry correlation within security operations platforms
These controls shift the economic balance by increasing attacker effort while reducing the potential operational impact of credential-theft campaigns.
This figure visualizes the economic asymmetry between attacker investment and defender response cost, illustrating the relationship between credential-theft campaign scalability, enterprise operational disruption, and strategic defensive investment priorities.
S40 References
Authoritative sources referenced during preparation of this report include publicly available threat intelligence, security guidance, and identity protection documentation relevant to credential theft campaigns.
MITRE ATT&CK Framework — Adversary Technique Reference
• hxxps://attack[.]mitre[.]org
CISA Phishing Guidance — Phishing and Social Engineering Defense
• hxxps://www[.]cisa[.]gov/phishing
NIST Digital Identity Guidelines — Identity Security and Authentication Standards
• hxxps://pages[.]nist[.]gov/800-63
Microsoft Identity Security Best Practices — Enterprise Identity Protection Guidance
• hxxps://learn[.]microsoft[.]com/security
Google Cloud Identity Security Recommendations — Cloud Authentication Security Guidance
• hxxps://cloud[.]google[.]com/security