CVE-2026-26119 Improper Authentication Privilege Escalation in Microsoft Windows Admin Center
BLUF
CVE-2026-26119 is an improper authentication vulnerability in Microsoft Windows Admin Center that allows an authenticated low-privileged user to escalate privileges over the network. Because Windows Admin Center functions as a centralized infrastructure management plane, successful exploitation may result in administrative host compromise and potential domain-wide control.
Executive Cost Summary
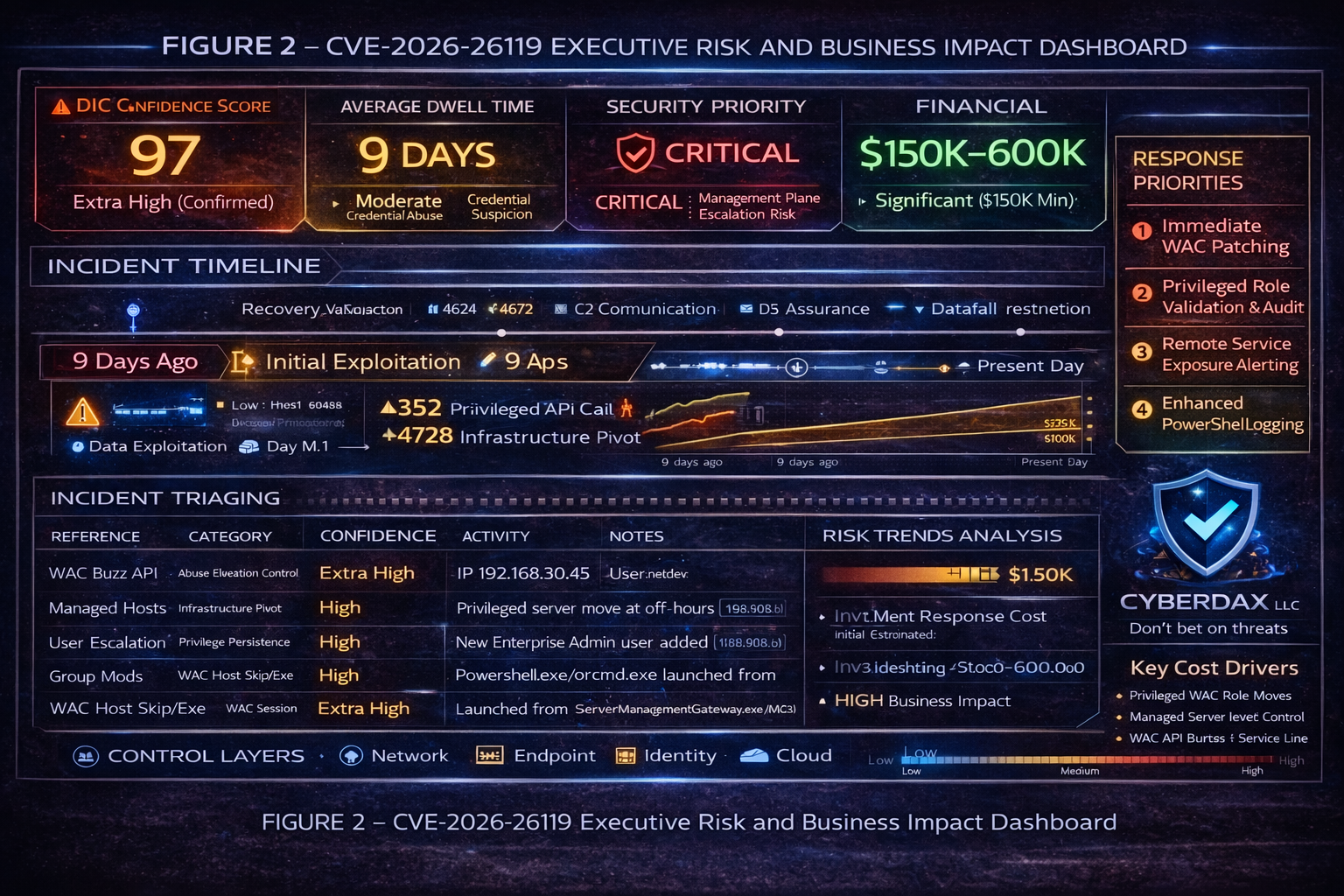
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
“For organizations affected by exploitation of CVE-2026-26119 in Microsoft Windows Admin Center, financial exposure primarily stems from privileged access misuse, containment complexity, and potential downstream data or infrastructure impact.”
· Low-end total cost: $250,000 – $600,000
o Single-server exposure, rapid patching, no lateral movement or data access
· Typical expected range: $750,000 – $2.5 million
o Privileged escalation requiring enterprise-wide credential resets and forensic review
· Upper-bound realistic scenarios: $3 million – $7 million
o Domain-level compromise affecting multiple production workloads
Key Cost Drivers
· Scope of privileged accounts requiring reset and review
· Extent of lateral movement beyond Windows Admin Center
· Downtime of revenue-generating or customer-facing systems
· Regulatory reporting obligations triggered by data access
· Cyber insurance retention levels and renewal repricing
This analysis reflects realistic enterprise cost exposure for authentication-related privilege escalation in centralized infrastructure management platforms, without assuming catastrophic breach conditions.
Bottom Line for Executives
CVE-2026-26119 represents a concentrated administrative risk rather than a broad operational failure. If exploited, the financial impact depends on how far elevated access extends beyond Windows Admin Center. Early containment typically limits exposure to mid-six figures driven by investigation, credential resets, and system validation. If attackers leverage privileged access to move laterally or access regulated data, total impact can rise into the low-to-mid seven figures due to downtime, compliance response, and extended recovery efforts.
For leadership, this is fundamentally a governance issue around privileged access control. Organizations with strong authentication enforcement, credential hygiene, and monitoring are positioned to keep impact contained. The primary cost driver is not patch deployment, it is restoring trust in administrative control across enterprise systems if that trust is compromised.
PRIORITY LEVEL AND RESPONSE WINDOW
· Priority Level: Critical
· Response Window:
o Tier-zero and domain-adjacent systems: 72 hours
o Internal-only deployments: 7 days
EXPLOIT CONDITIONS SNAPSHOT
· Network-accessible Windows Admin Center gateway
· Valid authenticated low-privileged account
· No user interaction required
· Low attack complexity
· High confidentiality, integrity, availability impact
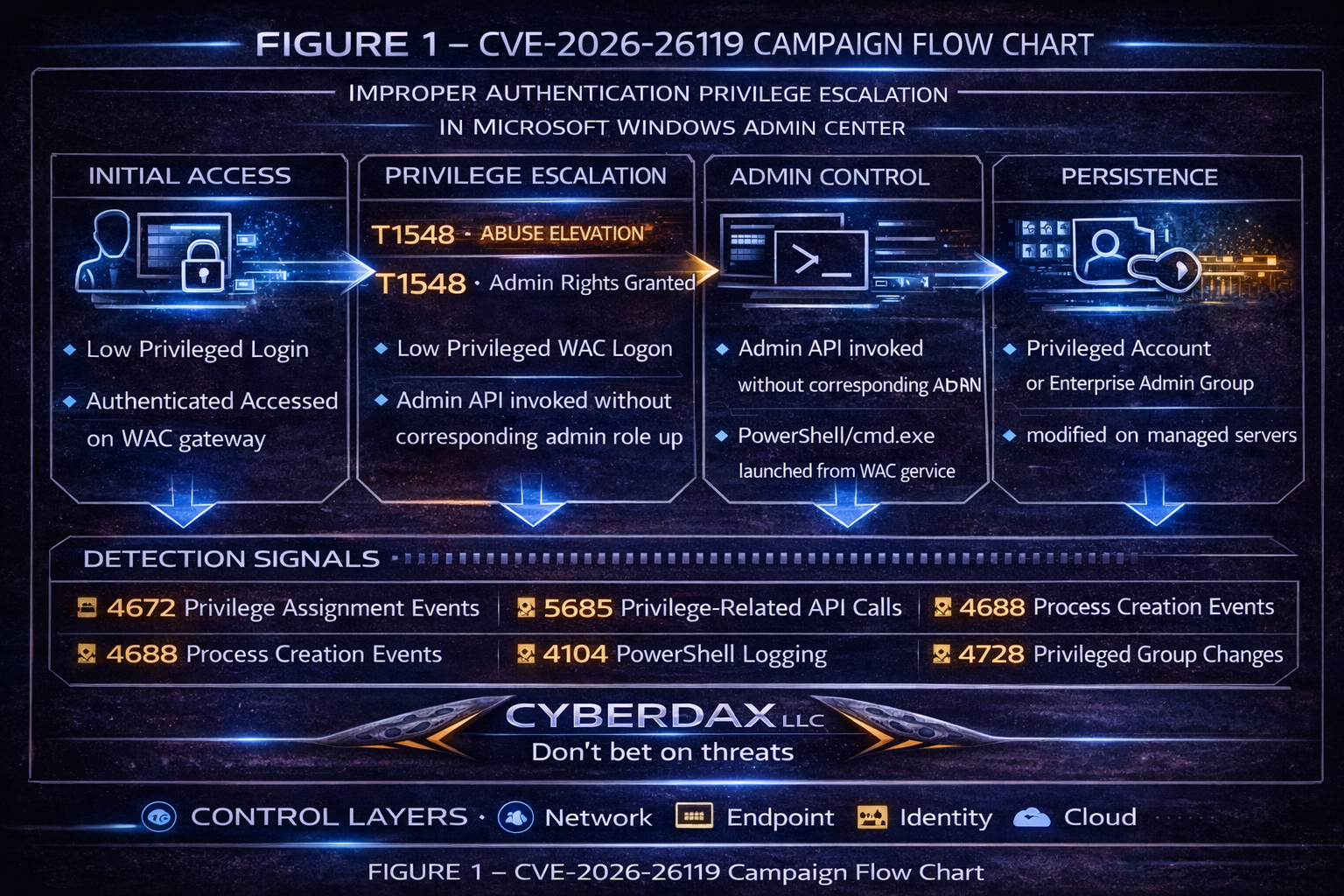
TODAY’S HUNT FOCUS
· Event ID 4672 privilege assignments on WAC host
· Event ID 4688 interpreter execution under WAC service lineage
· Administrative API invocation without corresponding role modification
Impacted Sectors
· Enterprise IT
· Government
· Healthcare
· Financial Services
· MSPs
Countries
· Global
FIRST OBSERVED ACTIVITY
· Public disclosure: February 2026
LAST OBSERVED ACTIVITY
· Confirmed in-the-wild exploitation: Not applicable at this time
CVE-2026-26119
Vendor
· Microsoft
Product
· Windows Admin Center
CWE-287 Improper Authentication
· Improper authentication validation permits privilege escalation from authenticated low privilege to administrative context.
CVSS 3.1
· (8.8) AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H
CISA KEV STATUS
· Not listed in Known Exploited Vulnerabilities catalog
NESSUS COVERAGE
· Tenable Nessus plugin: Not available at time of reporting
PATCH DATA
Affected
· Windows Admin Center versions prior to 2.6.4 build 2511
Remediated
· Windows Admin Center 2.6.4 build 2511 and later
TECHNICAL ROOT CAUSE
Authorization boundary enforcement failure within WAC gateway role validation logic.
Weakness Conditions:
• Privileged API invocation without validated role enforcement
• Escalation into service execution context
• Insufficient authentication boundary integrity
Risk Multiplier: Management-plane exposure
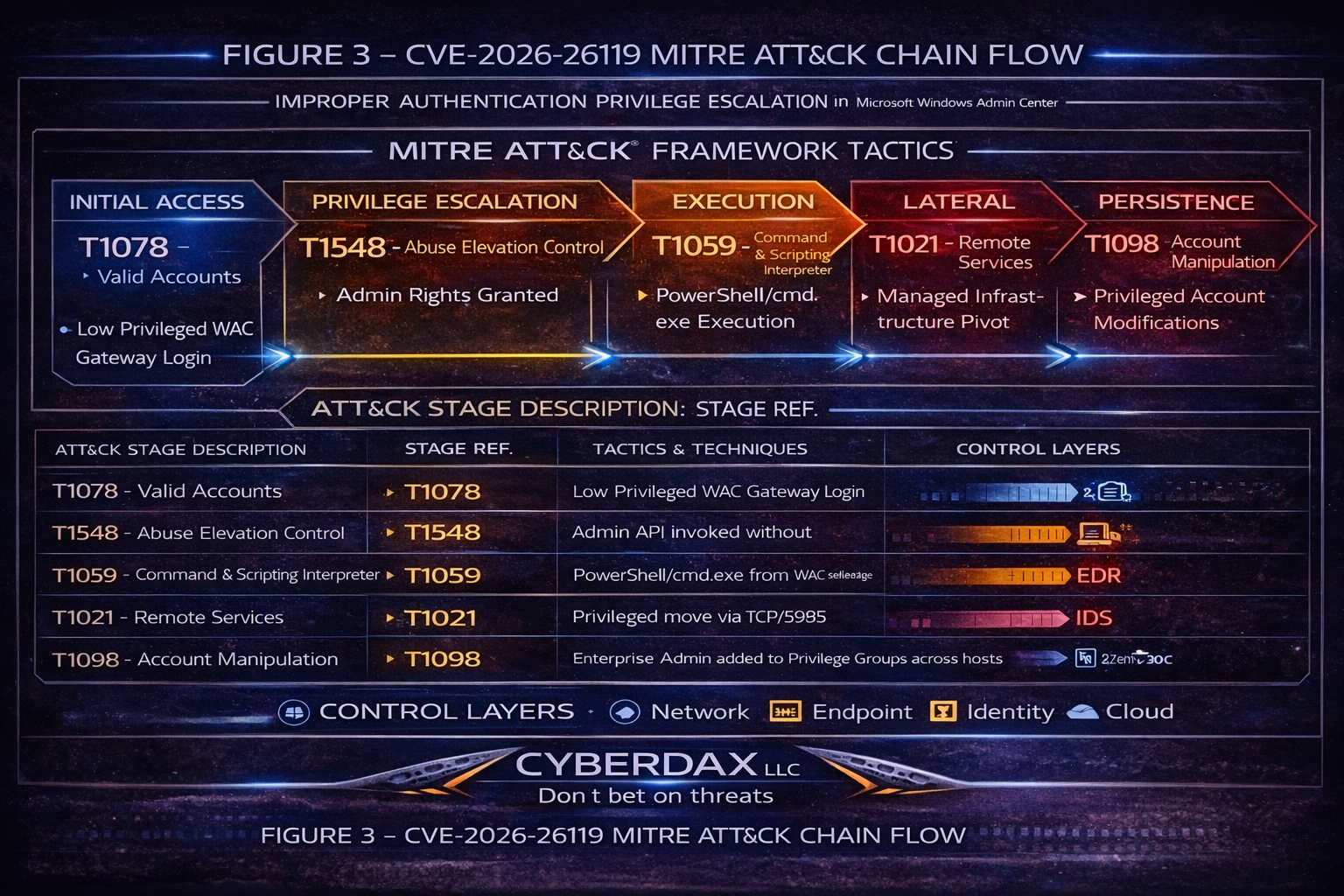
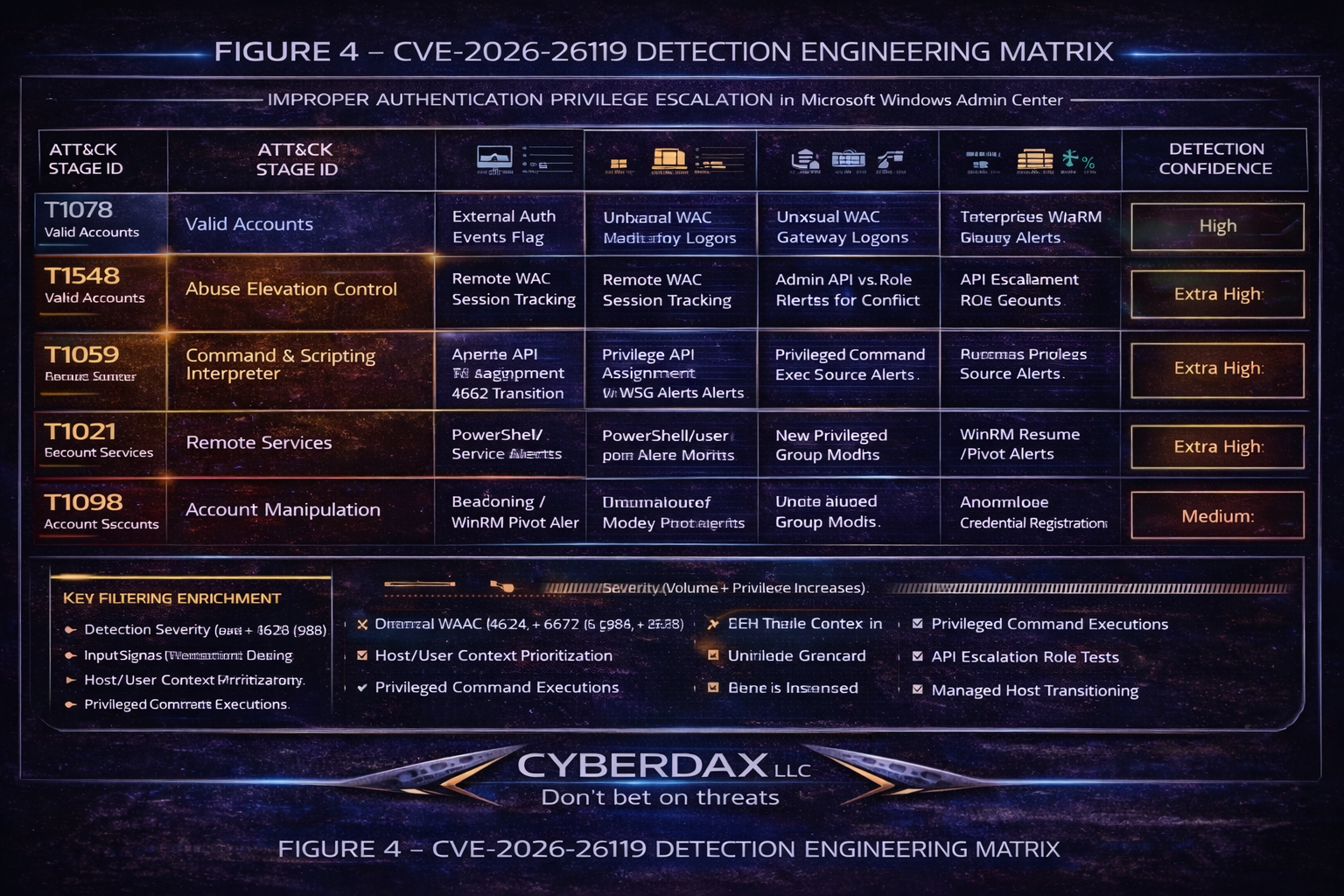
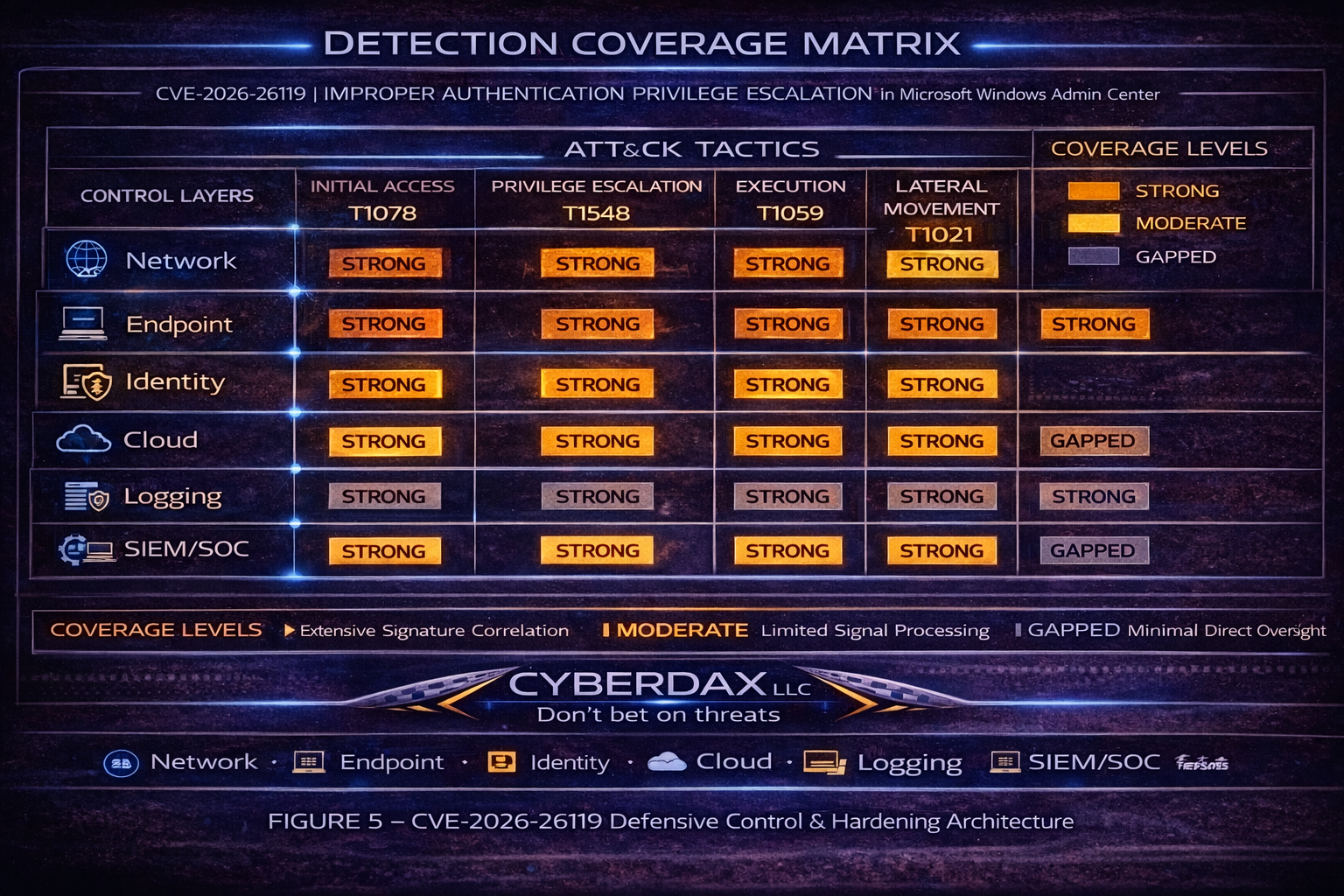
MITRE ATT&CK CHAIN
Initial Access T1078 Valid Accounts
Privilege Escalation T1548 Abuse Elevation Control Mechanism
Execution T1059 Command and Scripting Interpreter
Defense Evasion T1562 Impair Defenses
Persistence T1098 Account Manipulation
Lateral Movement T1021 Remote Services
STAGE-BASED TTP BREAKDOWN
Stage 1 Authenticated Access
T1078 Valid Accounts
Low privilege login to WAC
Stage 2 Privilege Escalation
T1548 Abuse Elevation Control Mechanism
Administrative API invocation without enforced role boundary
Stage 3 Execution
T1059 Command and Scripting Interpreter
PowerShell or cmd.exe launched under WAC service context
Stage 4 Lateral Movement
T1021 Remote Services
Remote management pivot to managed servers
Stage 5 Persistence
T1098 Account Manipulation
Privileged account creation or group modification
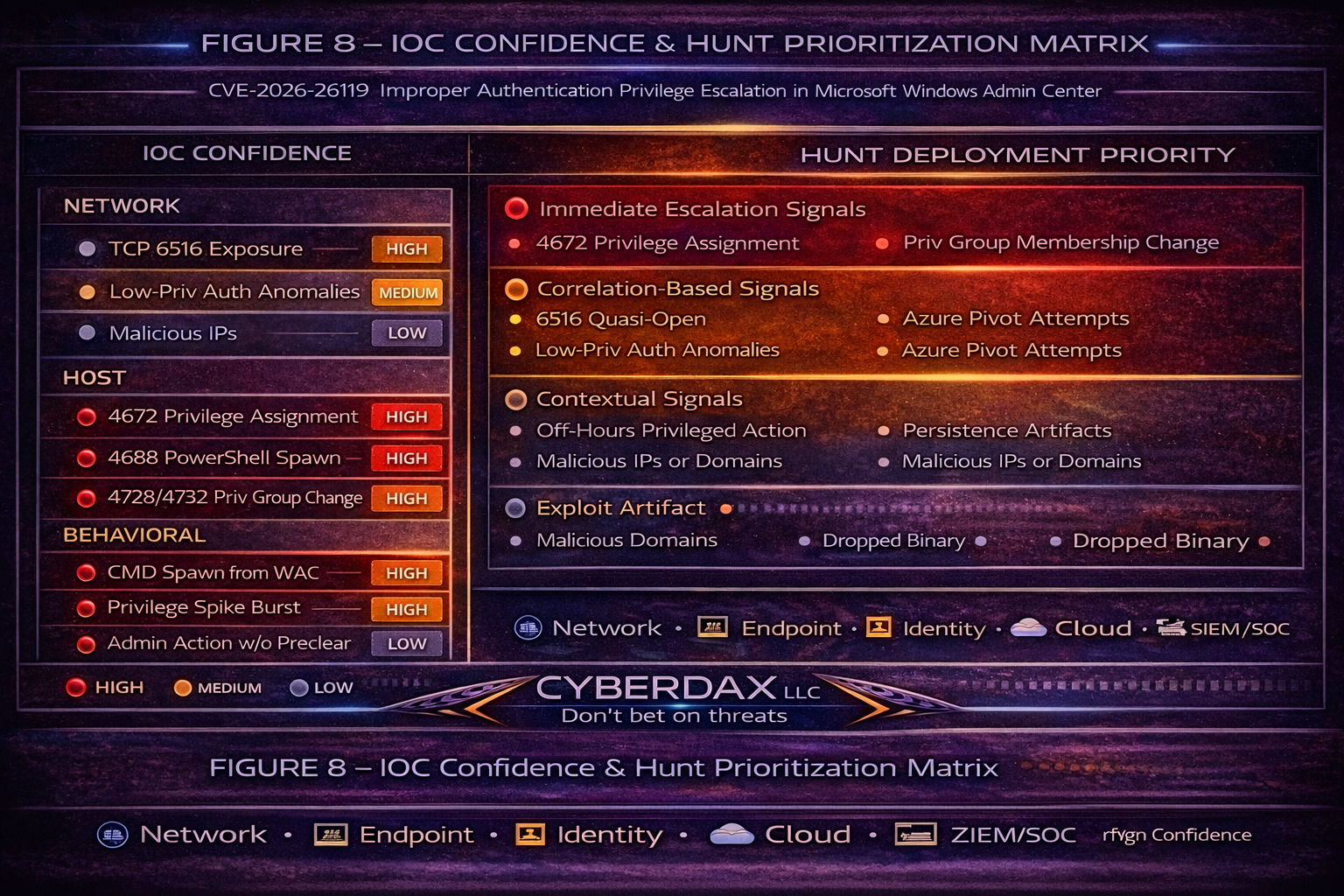
IOCs
Network Indicators
· Not applicable at this time
· Confidence Score: Low
Host Indicators
· Event ID 4672 privilege assignment
· Event ID 4688 process creation
· Event ID 4728 privileged group modification
· Confidence Score: High
Behavioral Indicators
· Non-admin WAC identity invoking administrative APIs
· Interpreter execution from WAC service lineage
· Confidence Score: High
MALWARE / SHA256
Malware: Not applicable at this time
SHA256: Not applicable at this time
BEHAVIOR AND LOG ARTIFACTS
Monitor:
4624 successful logon
4672 special privileges assigned
4688 process creation
4728 privileged group change
4104 PowerShell script block logging
Suspicious Processes:
powershell.exe
cmd.exe
wsmprovhost.exe
net.exe
dsadd.exe
· Endpoint Telemetry: High confidence
· Identity Telemetry: High confidence
· Network Telemetry: Moderate
· SIEM Correlation: High when correlating 4672 + 4688
Suggested Rules / Potential hunts
SentinelOne
· Title
o WAC Service Lineage Interpreter Execution
· Purpose
o Detect post-escalation interpreter execution under Windows Admin Center service lineage.
· Tuning Explanation
o Replace wildcard parent path with verified WAC binary path. Correlate with privilege assignment events within 120 seconds. Exclude validated administrative automation accounts only after change-control verification.
SQL Syntax:
SELECT
event_time,
agent_hostname,
src_user,
parent_process_name,
parent_process_path,
process_name,
process_cmdline
FROM deep_visibility
WHERE event_type = 'Process Creation'
AND LOWER(parent_process_path) LIKE '%servermanagement%'
AND LOWER(process_name) IN ('powershell.exe','cmd.exe','wsmprovhost.exe')
ORDER BY event_time DESC;
· Title
o Escalation Follow-On Account Manipulation
· Purpose
o Detect account or group manipulation following interpreter execution.
· Tuning Explanation
o Limit to WAC hosts. Reduce interval to 60 seconds for higher confidence. Add off-hours filter for severity elevation.
SQL Syntax:
SELECT
a.agent_hostname,
a.src_user,
a.process_name AS interpreter,
b.process_name AS follow_on,
b.process_cmdline
FROM deep_visibility a
JOIN deep_visibility b
ON a.agent_id = b.agent_id
WHERE LOWER(a.parent_process_path) LIKE '%servermanagement%'
AND a.process_name IN ('powershell.exe','cmd.exe')
AND b.process_name IN ('net.exe','dsadd.exe','dsmod.exe','whoami.exe')
AND b.event_time BETWEEN a.event_time AND a.event_time + INTERVAL '120 seconds';
Splunk Detection Rule
· Title
o Privilege Assignment Burst on WAC Host
· Purpose
o Detect escalation indicators via rapid privilege events.
· Tuning Explanation:
o Increase threshold to 4 for noisy admin environments. Join with EventCode=4688 within 2 minutes for higher precision.
SPL Syntax:
index=wineventlog (EventCode=4672 OR EventCode=4728 OR EventCode=4732)
| stats count values(EventCode) by ComputerName, SubjectUserName
| where count > 2
Sigma Detection Rule
· Title
o Suspicious Privilege Escalation on Management Host
· Purpose
o Portable escalation detection for Windows systems.
· Title
o Windows Admin Center Privilege Escalation Indicator
· Tuning Explanation
o Add correlation logic with 4688 interpreter execution and host scoping to WAC systems.
logsource:
product: windows
service: security
detection:
selection:
EventID: 4672
condition: selection
level: high
Suricata Detection Rule
Windows Admin Center Privileged API Abuse
· Purpose
o Detect suspicious API invocation patterns targeting WAC service port.
· Tuning Explanation
o Restrict destination IPs to known WAC hosts. Combine with TLS fingerprinting for higher confidence.
Rule Syntax:
alert tcp any any -> any 6516 (
msg:"WAC Privileged API Abuse Heuristic CVE-2026-26119";
flow:established,to_server;
content:"/api/"; nocase;
sid:202626119;
rev:1;
)
YARA
Title: Not applicable at this time
Purpose: No malware artifacts associated with CVE-2026-26119 in public reporting.
Tuning Explanation: Not applicable at this time
DELIVERY METHODS
· Credential compromise
· Insider misuse
· Password spraying
· Session token replay
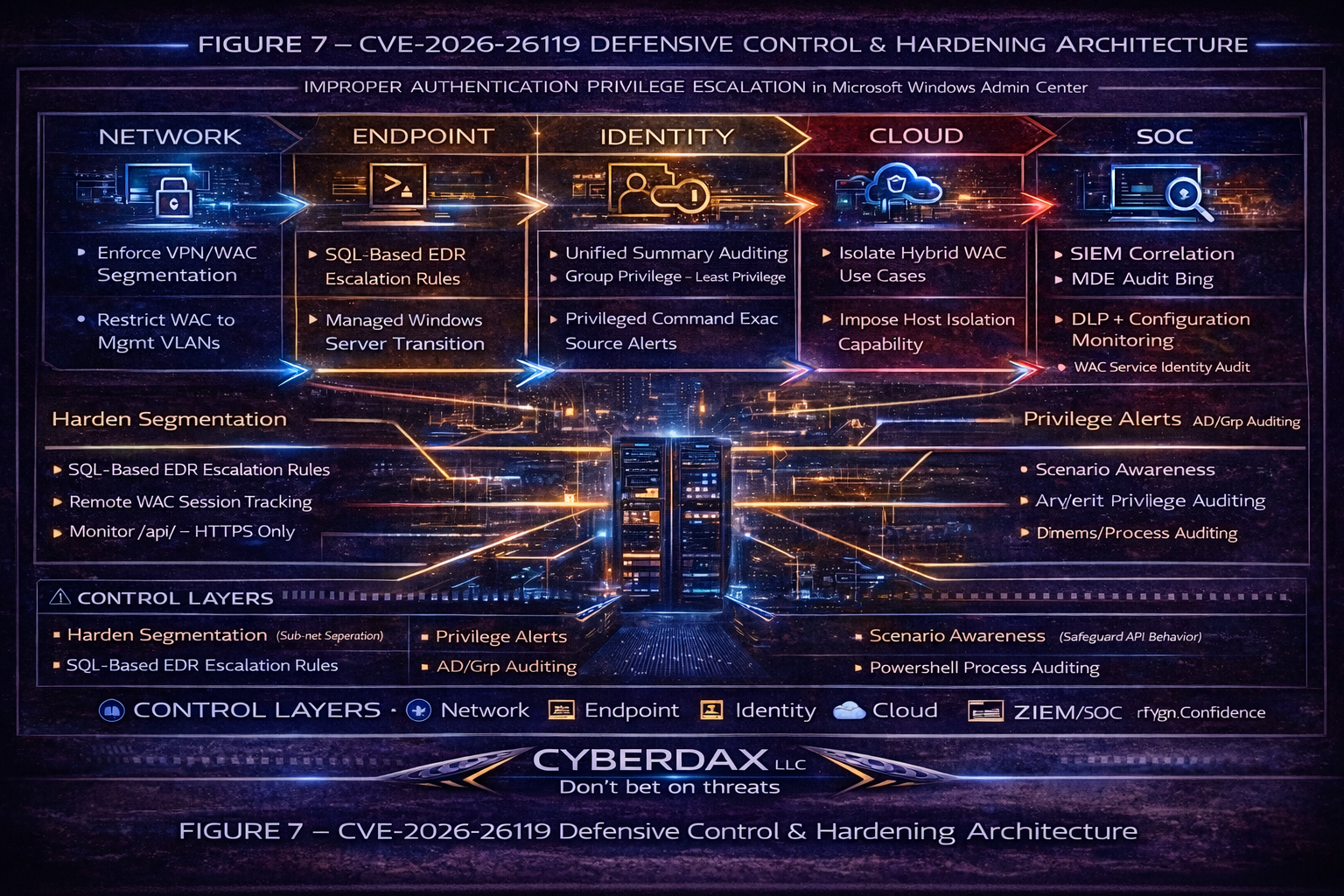
7-DAY DEFENSIVE PLAN
· Day 1 Inventory deployments
· Day 2 Patch vulnerable instances
· Day 3 Restrict network exposure
· Day 4 Audit privileged roles
· Day 5 Deploy detection rules
· Day 6 Retrospective hunt
· Day 7 Validate detection efficacy
BOTTOM LINE FOR EXECUTIVES
CVE-2026-26119 targets the infrastructure control plane. An authenticated low-privileged user may escalate to administrative authority, enabling potential domain compromise. Immediate patching and monitoring are strongly recommended.
Estimated Impact:
Incident response: 150,000 to 500,000 dollars
Potential domain compromise: Severe
Operational disruption: High
REFERENCES
Microsoft Security Update Guide
· hxxps[:]//msrc[.]microsoft[.]com/update-guide/vulnerability/CVE-2026-26119
NIST National Vulnerability Database
· hxxps[:]//nvd[.]nist[.]gov/vuln/detail/CVE-2026-26119
CISA Known Exploited Vulnerabilities Catalog
· hxxps[:]//www[.]cisa[.]gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-26119
The Hacker News Microsoft Patches CVE-2026-26119
· hxxps[:]//thehackernews[.]com/2026/02/microsoft-patches-cve-2026-26119[.]html
TechRepublic Windows Admin Center Privilege Escalation Coverage
· hxxps[:]//www[.]techrepublic[.]com/article/news-windows-admin-center-privilege-escalation-february-2026/
MITRE T1078 Valid Accounts
· hxxps[:]//attack[.]mitre[.]org/techniques