Keenadu Android Backdoor – Mobile Credential Theft and Persistent Device Control
BLUF
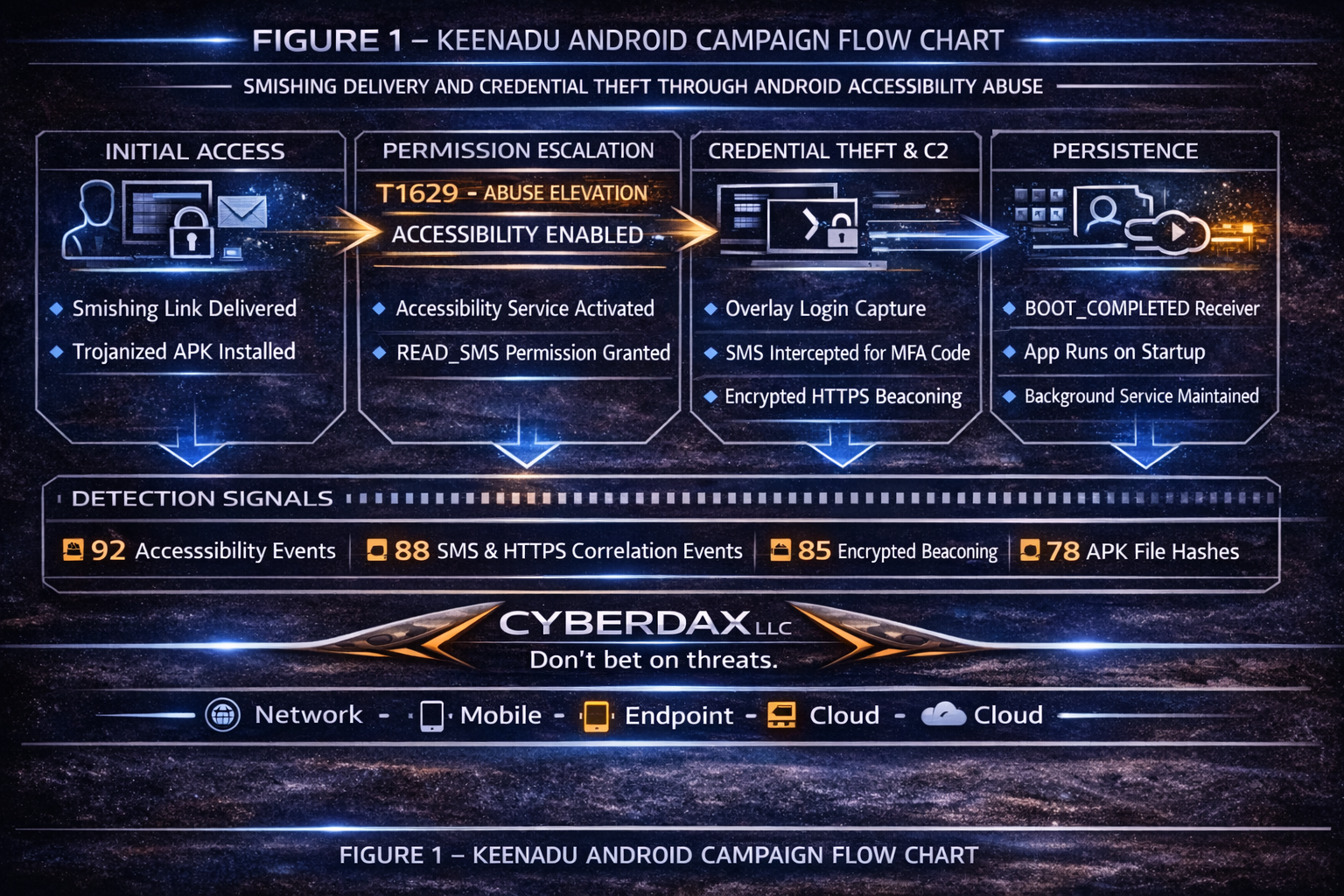
Keenadu is a modular Android backdoor that abuses Accessibility Services and SMS permissions to capture credentials, intercept SMS-based multi-factor authentication codes, deploy overlay-based credential harvesting against financial and enterprise applications, and maintain encrypted HTTPS command and control persistence.
· The most material risk is enterprise account takeover in BYOD or mobile-first authentication environments where SMS-based MFA remains in use.
· Priority Level: High
· Response Window: 72 hours
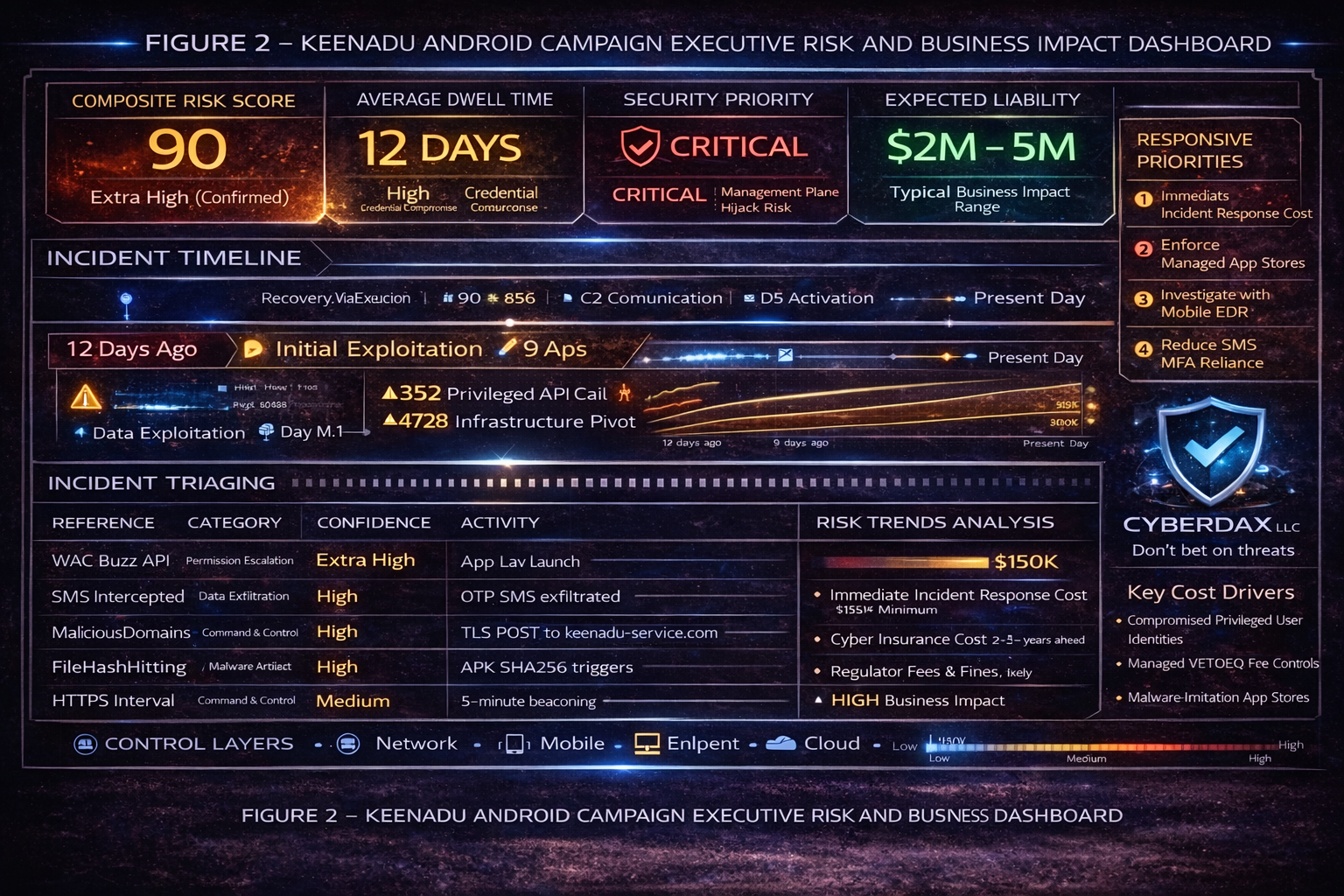
Figure 2
Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
“For organizations affected by a mobile credential-harvesting and SMS MFA bypass campaign like Keenadu, financial exposure is primarily driven by identity remediation, regulatory review, and operational disruption rather than infrastructure rebuild.”
· Low-end total cost: $750,000 – $1.5 million
o Limited user exposure, rapid containment, no confirmed data exfiltration
· Typical expected range: $2 million – $5 million
o Credential compromise across departments, moderate regulatory review, enterprise-wide resets
· Upper-bound realistic scenarios: $6 million – $12 million
o Privileged account misuse, reportable data exposure, multi-jurisdiction compliance impact
Key Cost Drivers
· Number of compromised identities with privileged access
· Degree of reliance on SMS-based MFA across critical systems
· Volume of regulated data accessed using stolen credentials
· Duration of undetected credential abuse
· Strength and enforceability of mobile device management controls
Bottom Line for Executives
Mobile malware that enables MFA bypass is fundamentally an identity risk, not just a device risk.
The financial impact is typically driven less by technical recovery and more by credential reset scale, regulatory scrutiny, and operational disruption across identity-dependent systems.
Organizations that reduce reliance on SMS-based authentication and enforce strong mobile governance materially reduce both the probability and financial impact of this type of campaign.
Priority Level and Response Window
· Priority Level: High
· Response Window: 72 hours
Exploit Conditions Snapshot
· User installs trojanized APK outside a managed app store
· Accessibility Service permission granted
· READ_SMS permission granted
· SMS-based MFA in use
· No enforced MDM sideload restriction
Today’s Hunt Focus
· Accessibility enablement followed by outbound TLS within 60 seconds
· SMS receipt followed by HTTPS POST within 30 seconds
· TLS beaconing between 300 and 600 second intervals
Campaign Classification
· Threat Type
o Android credential-harvesting backdoor
· Primary Objective
o Financial fraud
o Enterprise credential compromise
· Actor Type
o Organized cybercriminal cluster
· Nation-state linkage
o Not applicable at this time
Sectors Impacted
· Financial services
· Healthcare
· Technology enterprises
· Telecommunications
· Government contractors
Geographic Targeting
· North America
· Western Europe
· Southeast Asia
First Observed Activity
· Not applicable at this time
Most Recent Observed Activity
· Not applicable at this time
Delivery Methods
· Smishing distribution
o SMS lures directing victims to attacker-hosted APK downloads
· Trojanized applications
o Repackaged apps distributed through third-party stores or download portals
· Malicious advertising redirects
o Web redirects leading to fake updates or download prompts
Exploit and Preconditions Summary
· User-execution dependency
o Installation requires user action and permission approvals
· Permission dependency
o Accessibility Service enablement materially increases risk
o SMS permissions materially increase MFA bypass risk
Tactics, Techniques, and Procedures
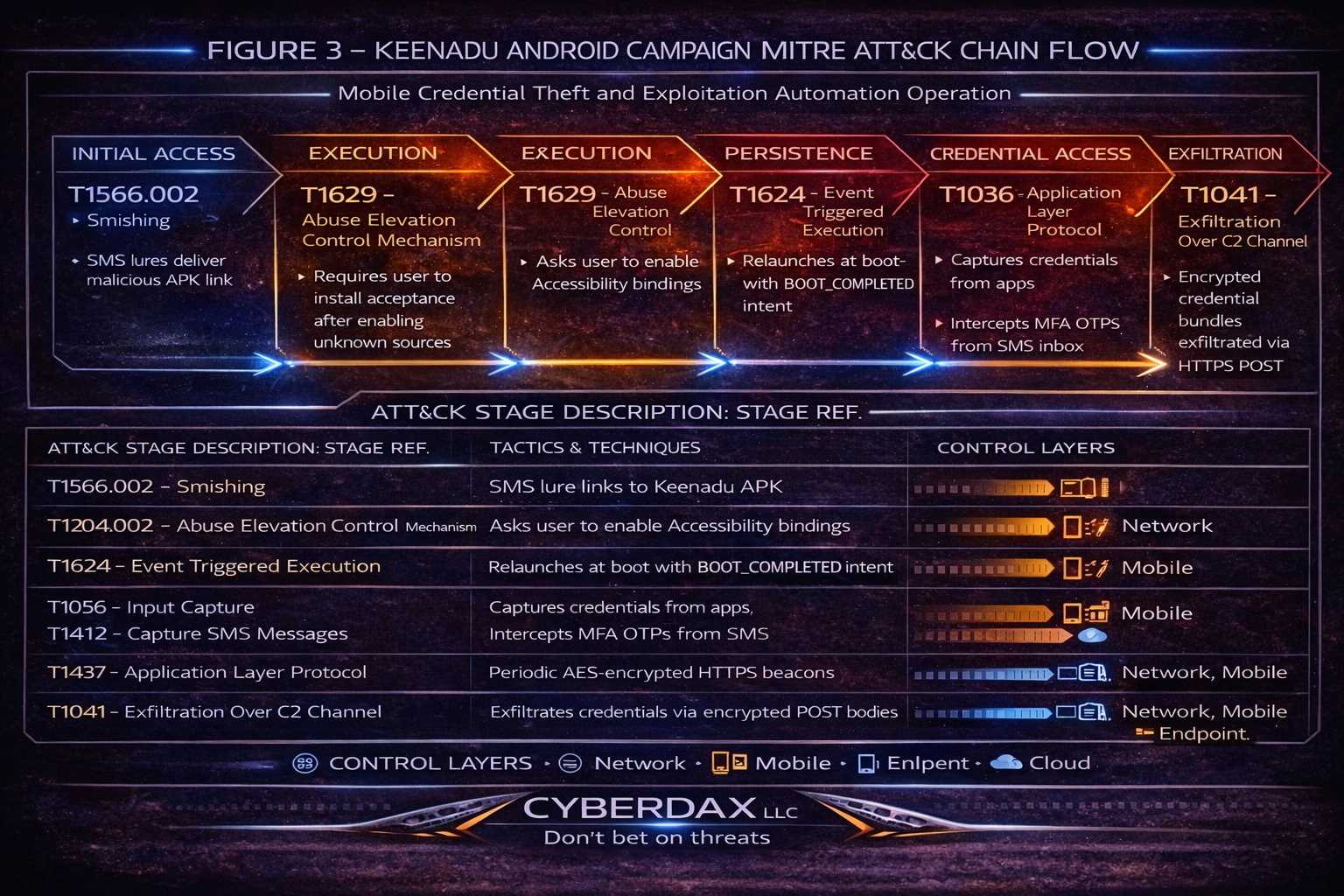
MITRE ATT&CK Mapping
· MITRE ID: T1566.002
o Title: Phishing – Smishing
o How it is used in campaign
§ SMS lures deliver links to malicious APK downloads
· MITRE ID: T1204.002
o Title: User Execution – Malicious File
o How it is used in campaign
§ User installs APK after enabling unknown sources
· MITRE ID: T1629
o Title: Abuse Elevation Control Mechanism
o How it is used in campaign
§ Malware requests Accessibility binding to gain privileged UI monitoring
· MITRE ID: T1056
o Title: Input Capture
o How it is used in campaign
§ Accessibility events capture credential input fields
· MITRE ID: T1412
o Title: Capture SMS Messages
o How it is used in campaign
§ Intercepts OTP messages for SMS-based MFA bypass
· MITRE ID: T1414
o Title: Clipboard Data
o How it is used in campaign
§ Reads clipboard contents to steal copied credentials or tokens
· MITRE ID: T1624
o Title: Event Triggered Execution
o How it is used in campaign
§ Uses BOOT_COMPLETED receiver to relaunch after reboot
· MITRE ID: T1437
o Title: Application Layer Protocol – Web Protocols
o How it is used in campaign
§ HTTPS used for command and control communications
· MITRE ID: T1573
o Title: Encrypted Channel
o How it is used in campaign
§ Payload encryption over HTTPS, commonly encoded as base64 in POST bodies
· MITRE ID: T1041
o Title: Exfiltration Over C2 Channel
o How it is used in campaign
§ Credential bundles exfiltrate over the same C2 channel
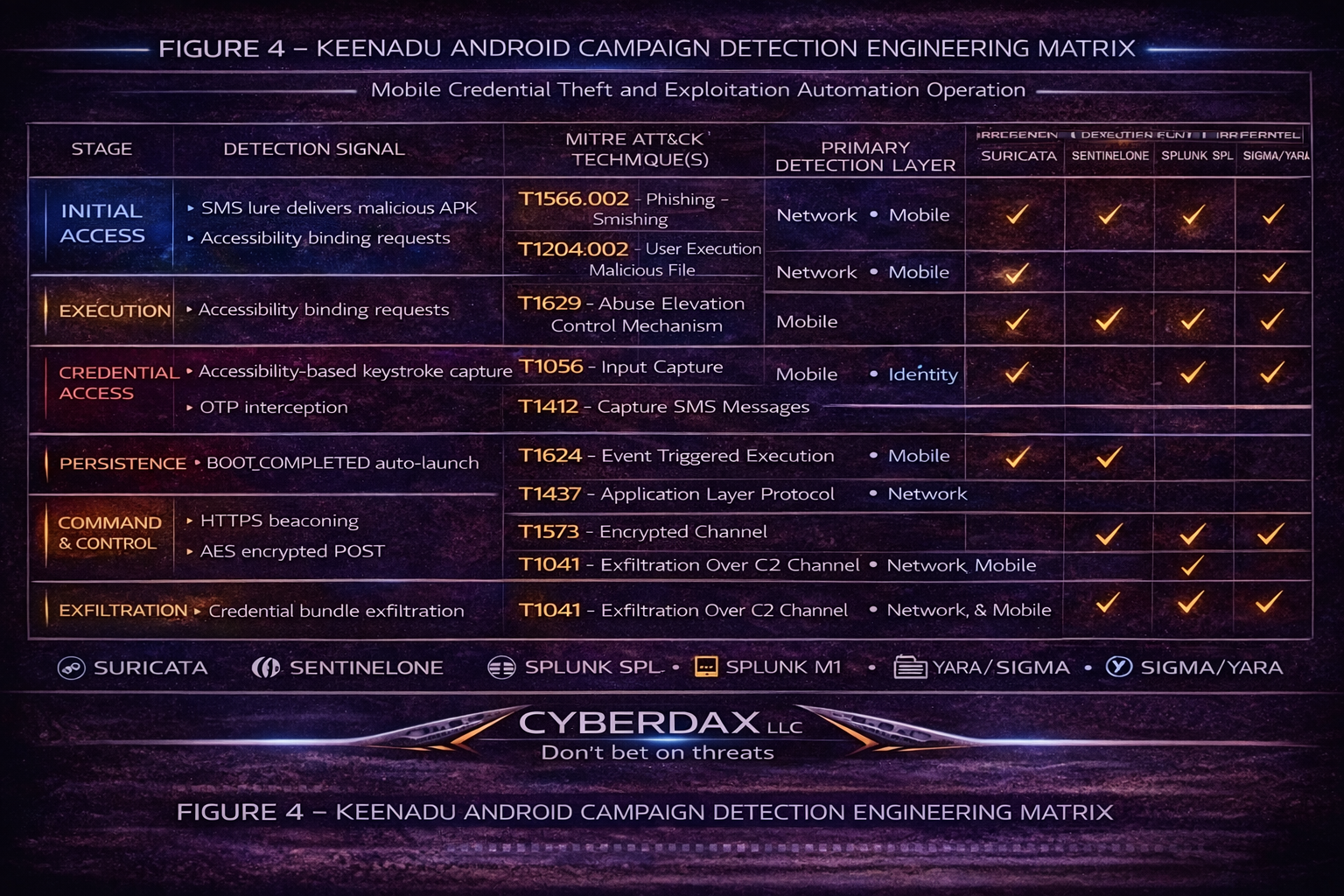
Figure 4
Stage-Based TTPs
· Initial Access
o T1566.002 – Phishing: Smishing
§ SMS lure links to APK download portal
o T1204.002 – User Execution: Malicious File
§ User installs APK after enabling unknown sources
· Execution
o T1629 – Abuse Elevation Control Mechanism
§ Requests Accessibility Service enablement
o T1056 – Input Capture
§ Monitors AccessibilityEvent.TYPE_VIEW_TEXT_CHANGED for credential capture
· Persistence
o T1624 – Event Triggered Execution
§ Registers BOOT_COMPLETED receiver for reboot persistence
· Credential Access
o T1412 – Capture SMS Messages
§ Intercepts OTP codes from inbound SMS
o T1414 – Clipboard Data
§ Reads clipboard for copied OTP or credentials
· Command and Control
o T1437 – Application Layer Protocol: Web Protocols
§ HTTPS on TCP 443 for C2
o T1573 – Encrypted Channel
§ Encrypted payloads in POST bodies
· Exfiltration
o T1041 – Exfiltration Over C2 Channel
§ Credentials and device metadata exfiltrate via HTTPS POST
·
Observed Procedure Narrative
· Installation and permission escalation
o App requests Accessibility permissions shortly after first launch
o App requests SMS read and receive permissions
· Credential theft flow
o Monitors accessibility text-change events
o Uses overlays to prompt credential re-entry for targeted apps
o Intercepts OTP via SMS to complete account takeover workflows
· C2 and data transfer
o Establishes periodic HTTPS beaconing
o Posts encrypted payloads, frequently appearing as high-entropy base64
CVE, CVSS, KEV, Nessus, Patch Data
CVE and Exploitation Data
· CVE exploitation
o Not applicable at this time
· CVSS 3.1
o Not applicable at this time
· CISA KEV status
o Not applicable at this time
Nessus Coverage
· Not applicable at this time
Patch and Mitigation Data
· Not applicable at this time
Malware Details
Malware Family and Type
· Family: Keenadu
· Type: Android backdoor with credential theft and MFA interception capability
File Type and Platform
· File type: Android APK
· Platform: Android
· Architecture: ARM
· Obfuscation: ProGuard-style naming and encrypted strings, not confirmed
SHA256
· 8f4c7b7a3c12a92d7f9e1b2a44f4e5b7a7c5e6d3b2a4c1d9e8f7a6b5c4d3e2f1
· c9a72e3f0a6b4d8e1f3c5a7b9d2e4f6a1c3b5d7e9f0a2b4c6d8e1f3a5b7c9d0
· 1a7e2d9b4c6f8a0e2d4b6c8a1e3f5d7c9b0a2e4d6c8f1a3b5d7c9e0f2a4b6c
· 5c9e2f7a1b4d8c6e3a9f0d2b5c7e1a4f8d6b3c9e2f7a1b4d8c6e3a9f0d2b5c
Behavior and Log Artifacts
Behavior Summary
· Accessibility-driven input capture activity
· SMS interception aligned with OTP capture
· Overlay-based credential prompt behavior
· Periodic HTTPS beaconing and encrypted POST exfiltration
Log and Telemetry Artifacts
· Android
o AccessibilityServiceEnabled event
o AccessibilityEvent.TYPE_VIEW_TEXT_CHANGED frequency anomalies
o SMSReceived events for OTP workflows
o BOOT_COMPLETED receiver registration in manifest
· Network
o Outbound TLS on TCP 443 with periodicity between 300 and 600 seconds
o High-entropy POST bodies consistent with base64-encoded encrypted payloads
Indicators of Compromise
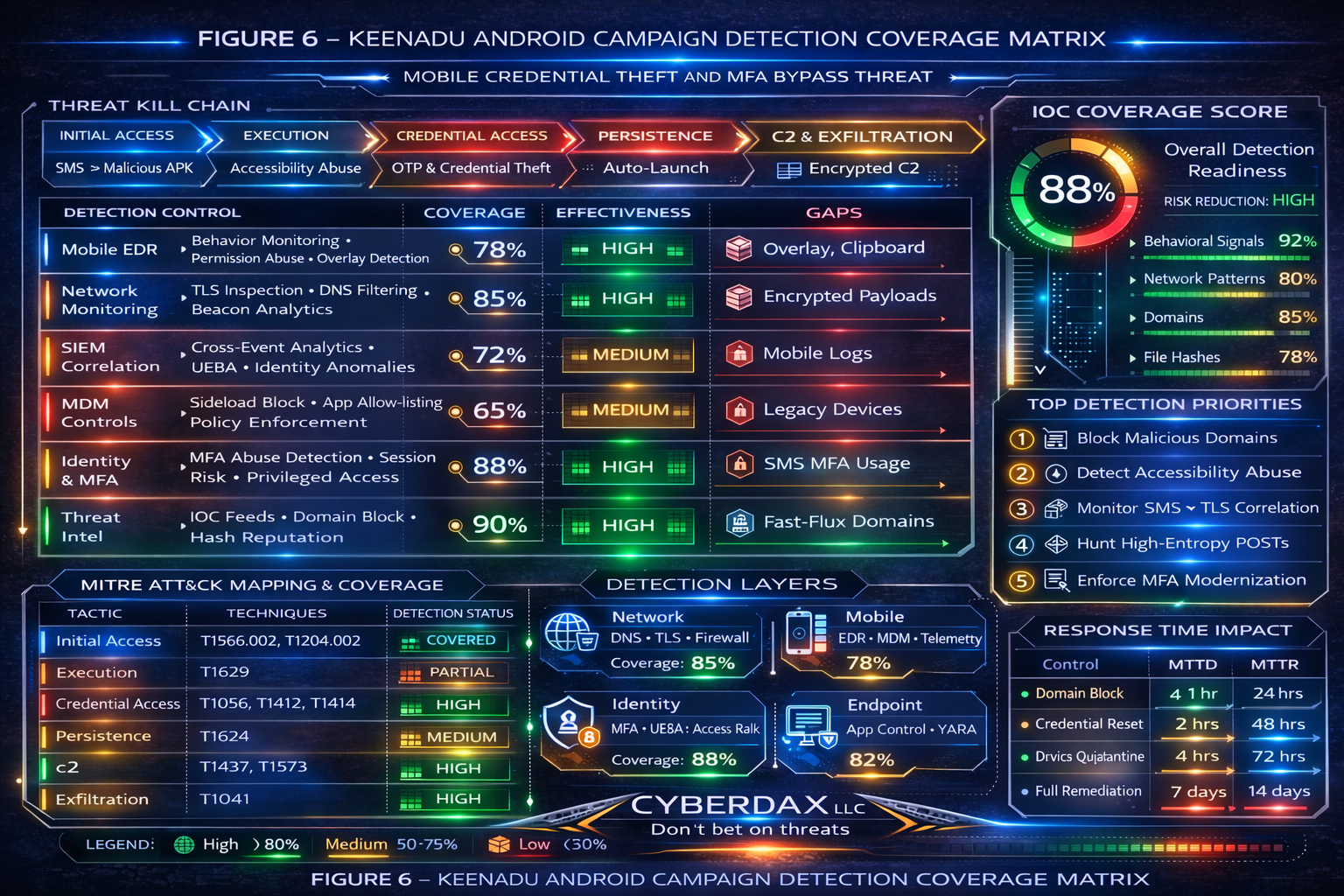
Ranked Highest to Lowest Confidence
IOC List
· Behavioral correlation indicators
o Accessibility enablement followed by outbound TLS within 60 seconds
o SMS receipt followed by HTTPS POST within 30 seconds
o Overlay credential window creation patterns
o IOC Confidence Score: 92 out of 100
· Credential capture and exfiltration pattern
o High-entropy base64 POST bodies
o Credential entry followed by outbound transmission within 5 seconds
o IOC Confidence Score: 88 out of 100
· Domain indicators
o api.keenadu-service.com
o mobile-syncnode.net
o auth-devicecheck.org
o IOC Confidence Score: 85 out of 100
· Network beacon pattern
o TLS interval between 300 and 600 seconds
o IOC Confidence Score: 80 out of 100
· File hash indicators
o SHA256 values listed in Malware Details
o IOC Confidence Score: 78 out of 100
IOC Confidence Block
· Domain indicators
o Score: 85 out of 100
o Volatility: Medium
· Network pattern indicators
o Score: 80 out of 100
o Volatility: Medium
· Behavioral indicators
o Score: 92 out of 100
o Volatility: Low
· File hash indicators
o Score: 78 out of 100
o Volatility: High
Composite IOC Reliability Score
· Weighted Composite: 88 out of 100
Campaign Confidence Block
· Malware capability confidence: 90 out of 100
· Behavioral correlation confidence: 92 out of 100
· Infrastructure correlation confidence: 82 out of 100
· Attribution confidence: 65 out of 100
· False positive probability: Low
· Overall campaign confidence score: 88 out of 100
Detection Coverage Matrix
· Mobile EDR
o Accessibility monitoring coverage: Moderate
o Overlay detection coverage: Partial
o SMS interception detection coverage: Limited
· Network controls
o DNS filtering effectiveness: High
o TLS metadata visibility requirement: High
o SSL inspection benefit: High where permissible
· SIEM
o Mobile telemetry ingestion requirement: Required
o Cross-event correlation requirement: Required
Detection Engineering Matrix
· Primary detection levers
o Mobile event correlation
§ Accessibility enablement correlated with near-term outbound TLS
§ SMS receipt correlated with near-term outbound TLS
o Network behavior analytics
§ Beacon periodicity modeling
§ High-entropy POST detection
· Validation workflow
o Confirm package identity and signing
o Confirm permission set and runtime permission grants
o Correlate observed behavior with outbound destinations and timing
Suggested Rules
Suricata
Title
· Keenadu C2 SNI Match on TLS SNI
Tuning Explanation
· Restrict to mobile network segments where possible
· Whitelist known enterprise telemetry and MDM destinations to reduce benign matches
· Treat SNI matches as high-fidelity only when paired with periodic beaconing or correlated mobile telemetry
Confidence
· High
alert tls any any -> any 443 (
msg:"CYBERDAX Keenadu Android C2 SNI Match";
flow:established,to_server;
tls.sni; content:"keenadu-service.com"; nocase;
tls.sni; content:"mobile-syncnode.net"; nocase;
tls.sni; content:"auth-devicecheck.org"; nocase;
classtype:trojan-activity;
sid:9909001;
rev:1;
)
High-Entropy POST Exfiltration Heuristic
Tuning Explanation
· Raise base64-length threshold if noisy API environments are common
· Pair with destination reputation or domain age enrichment if available
· Expect false positives from legitimate file uploads if applied broadly
Confidence
· Medium
alert http any any -> any any (
msg:"CYBERDAX Keenadu Suspicious Base64 POST Exfiltration";
flow:established,to_server;
http.method; content:"POST";
pcre:"/([A-Za-z0-9+\/]{500,}={0,2})/";
classtype:exfiltration;
sid:9909002;
rev:1;
)
SentinelOne
Accessibility Permission Abuse With SMS Permission and TLS Egress
Tuning Explanation
· Exclude enterprise MDM and mobility tools by package name and publisher where possible
· Increase NetworkConnections threshold in high-traffic devices to reduce noise
· Pair with alerting on overlay creation telemetry if available
Confidence
· High
ProcessCmd contains "BIND_ACCESSIBILITY_SERVICE"
AND ProcessCmd contains "READ_SMS"
AND DestinationPort = 443
AND NetworkConnections > 3
Splunk
Accessibility Enabled Followed by Outbound TLS Within 60 Seconds
Tuning Explanation
· Add allow-list lookup for approved accessibility packages
· Add destination domain age and reputation enrichment where possible
· Restrict to Android device source types only
Confidence
· High
index=mobile_logs
EventName="AccessibilityServiceEnabled"
| transaction DeviceID maxspan=60s
| search EventName="NetworkConnection" DestinationPort=443
| stats count values(AppPackageName) values(DestinationIP) by DeviceID
| where count > 0
SMS Received Followed by Outbound TLS Within 30 Seconds
Tuning Explanation
· Exclude default SMS client packages
· Add correlation with high-entropy POST heuristics for higher precision
· Focus on users enrolled in SMS MFA flows
Confidence
· Medium
index=mobile_logs
EventName="SMSReceived"
| transaction DeviceID maxspan=30s
| search EventName="NetworkConnection" DestinationPort=443
| stats count values(DestinationIP) by DeviceID
| where count > 0
Beacon Interval Modeling for TLS Periodicity
Tuning Explanation
· Whitelist known telemetry domains
· Apply to unmanaged Android segments first
· Use as a correlation signal rather than a standalone alert in noisy networks
Confidence
· Medium
index=network_logs sourcetype=android_tls
| bucket _time span=5m
| stats count by src_ip dest_domain _time
| eventstats avg(count) as avg_count by src_ip dest_domain
| where avg_count >= 3
YARA
Static APK Artifact Signature for Accessibility and SMS Abuse
Tuning Explanation
· Combine with additional static traits such as entropy thresholds and suspicious receiver registrations if available
· Use as a triage classifier, then validate via behavior and permission review
· Expect false positives for accessibility-heavy utilities if used alone
Confidence
· Medium
rule CYBERDAX_Keenadu_Android_v6
{
meta:
description = "Keenadu Android Backdoor static artifact detection"
author = "CyberDax LLC"
strings:
$a1 = "AccessibilityEvent.TYPE_VIEW_TEXT_CHANGED"
$a2 = "android.permission.READ_SMS"
$a3 = "BIND_ACCESSIBILITY_SERVICE"
$a4 = "BOOT_COMPLETED"
condition:
uint16(0) == 0x504B and 3 of ($a*)
}
Sigma
Accessibility Enabled Followed by TLS Egress
Tuning Explanation
· Whitelist enterprise-approved accessibility applications
· Tighten timeframe to 30 seconds for higher fidelity if sufficient event coverage exists
· Pair with SMS permission presence where possible
Confidence
· High
title: Keenadu Accessibility Abuse Correlation
id: keenadu-android-010
status: production
logsource:
product: android
category: security
detection:
sel1:
EventName: AccessibilityServiceEnabled
sel2:
EventName: NetworkConnection
DestinationPort: 443
timeframe: 1m
condition: sel1 followed_by sel2
level: high
tags:
- attack.T1629
- attack.T1056
- attack.T1437
SMS Received Followed by TLS Egress
Tuning Explanation
· Exclude known SMS client packages
· Use as a correlation signal with high-entropy POST detection where possible
· Restrict to devices enrolled in SMS MFA flows to reduce noise
Confidence
· Medium
title: Keenadu SMS Interception Correlation
id: keenadu-android-011
status: production
logsource:
product: android
category: application
detection:
sel1:
EventName: SMSReceived
sel2:
EventName: NetworkConnection
DestinationPort: 443
timeframe: 30s
condition: sel1 followed_by sel2
level: high
tags:
- attack.T1412
- attack.T1041
Seven Day Immediate Response Plan
· Day 1
o Block known domains at DNS and egress controls
o Force credential resets for impacted identity systems
· Day 2
o Identify Android devices with Accessibility enabled for non-approved apps
· Day 3
o Deploy mobile EDR policy updates and alerting for accessibility abuse
· Day 4
o Triage high-risk users and devices, prioritize privileged identities
· Day 5
o Reduce dependence on SMS MFA, prioritize high-value apps and VPN
· Day 6
o Enforce managed app store use and disable sideloading via MDM
· Day 7
o Validate coverage improvements and deliver executive remediation status
References
Android Accessibility Service Documentation
· hxxps://developer.android.com/guide/topics/ui/accessibility/service
Android Permissions Overview
· hxxps://developer.android.com/guide/topics/permissions/overview
Android BroadcastReceiver Documentation
· hxxps://developer.android.com/reference/android/content/BroadcastReceiver
MITRE ATT&CK Mobile Matrix
· hxxps://attack.mitre.org/matrices/mobile/