[CVE] CVE-2026-34621 Adobe Acrobat Zero-Day Remote Code Execution Actively Exploited
Report Type
CVE
Threat Category
Client-Side Exploitation
Assessment Date
April 11, 2026
Primary Impact Domain
Endpoint Compromise
Secondary Impact Domains
Data Exposure, Credential Access, Initial Access Enablement, Potential Lateral Movement
Affected Asset Class
User Workstations (Windows and macOS endpoints running Adobe Acrobat/Reader)
Threat Objective Classification
Initial Access and Execution via Document-Based Exploitation
BLUF
CVE-2026-34621 is a zero-day remote code execution vulnerability in Adobe Acrobat and Reader that enables code execution through malicious PDF files delivered via routine enterprise workflows and is actively being exploited in the wild. The risk is driven by execution within a trusted application, delaying reliable detection until activity transitions into observable operating system behavior. This creates a high-likelihood initial access pathway with partial detection coverage, increasing the probability of delayed detection, unauthorized system access, and operational disruption.
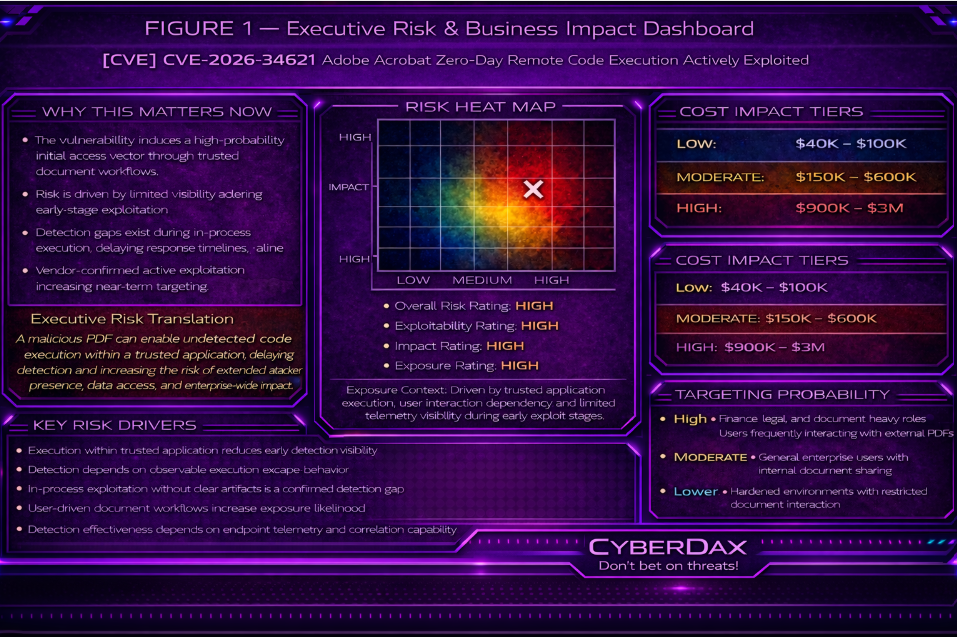
S3 Why This Matters Now
This vulnerability presents immediate risk due to confirmed active exploitation and Adobe’s issuance of a Priority 1 emergency bulletin. Exploitation aligns with common enterprise document workflows and requires minimal user interaction, while occurring within a trusted application context that reduces early-stage detection visibility. Organizations without strong endpoint telemetry and correlation capability face increased exposure to delayed detection, extended attacker dwell time, and increased likelihood of successful compromise.
S4 Key Judgments
· Exploitation is most likely through externally delivered PDF files.
· Reliable detection begins only after execution escapes the Acrobat process.
· In-process exploitation without child process creation is not covered by current detection capabilities.
· Endpoint process telemetry is required for effective detection.
· Cross-telemetry correlation materially improves detection confidence.
· Adversaries can reduce visibility through delayed execution or low-noise behavior.
S5 Executive Risk Summary
This vulnerability introduces a high-probability initial access vector through trusted document workflows. Risk is driven by limited visibility during early-stage exploitation, where malicious activity remains within the Acrobat process and may include local file access, environment interaction, or conditional staging behavior without generating reliable detection signals. Detection improves once execution transitions into operating system behavior, but environments lacking endpoint visibility or correlation capability remain exposed to undetected compromise. This increases the likelihood of delayed response, extended attacker presence, and potential progression into data access, operational disruption, or broader organizational impact depending on environment and adversary intent.
S6 Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
For organizations affected by CVE-2026-34621, financial impact depends primarily on detection timing, endpoint visibility, and the extent of post-exploitation activity.
· Low Impact Scenario: Early detection at execution escape stage with rapid containment to a single endpoint. Estimated cost range: $40,000 to $100,000.
· Moderate Impact Scenario: Delayed detection allowing staged execution or limited system access requiring coordinated incident response and remediation. Estimated cost range: $150,000 to $600,000.
· High Impact Scenario: Undetected exploitation enabling extended attacker activity, potential data access, or multi-system impact requiring enterprise-wide response, recovery operations, and potential regulatory engagement. Estimated cost range: $900,000 to $3,000,000.
S6A Key Cost Drivers
· Detection latency and time to containment
· Endpoint telemetry coverage and quality
· Scope of affected systems
· Extent of post-exploitation activity
· Data access or exposure potential
· Operational disruption and recovery effort
S6B Compliance and Risk Context
Compliance Exposure Indicator
Potential regulatory exposure exists if exploitation results in unauthorized access to sensitive, regulated, or proprietary data.
Risk Register Entry
Risk Title
Adobe Acrobat Zero-Day Remote Code Execution Exposure
Risk Statement
A zero-day vulnerability in Adobe Acrobat and Reader enables code execution through user interaction with malicious PDF files, with limited visibility during early-stage exploitation.
Business Impact
Delayed detection of endpoint compromise, potential unauthorized access to systems or sensitive data, operational disruption requiring coordinated incident response, and associated financial and regulatory exposure.
Priority
High
Annualized Risk Exposure
Elevated due to high likelihood of exploitation through common user workflows combined with partial detection coverage during early attack stages, increasing the probability of delayed detection and extended attacker activity.
S7 Risk Drivers
· Execution within a trusted application reduces early detection visibility
· Detection is dependent on observable execution escape behavior
· In-process exploitation without observable artifacts is a confirmed detection gap
· User-driven document workflows increase exposure likelihood
· Detection effectiveness depends on endpoint telemetry and correlation capability
· Adversary ability to delay or minimize observable behavior reduces detection opportunities
· Vendor-confirmed active exploitation increases likelihood of near-term targeting and campaign expansion
S8 Bottom Line for Executives
Organizations should assume exploitation will occur through routine document workflows and that early-stage detection is limited due to in-application exploit behavior that may not produce observable system-level signals. Risk reduction depends on rapid patching, strong endpoint visibility, and the ability to detect execution escape and subsequent behavior.
S9 Board-Level Takeaway
This vulnerability represents a high-likelihood risk driven by trusted application abuse and incomplete early detection coverage. Without strong endpoint visibility and timely patching, organizations face increased exposure to undetected compromise, operational disruption, and financial or regulatory consequences.
Figure 2
S10 Vulnerability Overview
Vulnerability Type
Remote Code Execution
Affected Systems
Adobe Acrobat and Reader Continuous 26.001.21367 and earlier, and Acrobat 2024 Classic 24.001.30356 and earlier on Windows and macOS
Exposure Conditions
Exposure occurs when users open malicious PDF files delivered through email, web downloads, chat platforms, or shared storage and document distribution workflows
Privilege Requirements
Execution occurs under the context of the current user without requiring elevated privileges
Attack Vector
User-driven interaction with a malicious PDF file within a trusted document processing application
S11 Technical Vulnerability Details
Root Cause
Improper handling of embedded PDF content within the application processing engine enables unintended code execution, including abuse of privileged Acrobat APIs
Vulnerable Component
Adobe Acrobat and Reader PDF processing engine
Trigger Mechanism
Execution is triggered when a user opens a crafted PDF file containing malicious embedded content
Exploitable Condition
The application processes malicious content within a trusted execution context, allowing in-application code execution that leverages privileged API access, enables local file interaction and environment awareness, and supports staged execution logic prior to payload delivery
S12 Exploitability Assessment
Exploit Complexity
Moderate, with staged execution and environment-aware behavior demonstrated in public technical analysis, while remaining practical for real-world exploitation under active attack conditions
Authentication Requirements
None
Network Exposure
Indirect, dependent on delivery through email, web access, chat platforms, or document distribution channels
Operational Constraints
Early-stage exploit activity occurs within the Acrobat process and may involve staged or conditional behavior, limiting observable telemetry until execution transitions into system-level activity
S13 KEV Status and Patch Availability
KEV Status
Not currently listed in the CISA Known Exploited Vulnerabilities catalog
Patch Availability
Vendor patches are available following a Priority 1 emergency advisory. Fixed versions include Acrobat/Reader Continuous 26.001.21411 and Acrobat 2024 Classic 24.001.30362 (Windows) and 24.001.30360 (macOS)
Remediation Priority
High
KEV Likelihood Assessment (EEP)
High likelihood of inclusion based on confirmed active exploitation, user-interaction-driven exploitability, trusted application execution context, and widespread exposure across enterprise document workflows
EEP is a forward-looking analytic measure of operational exploitation potential, not a statement of confirmed exploitation, KEV inclusion, or incident activity.
S14 Sectors / Countries Affected
Sectors Affected
· Finance
· Legal Services
· Government and Public Sector
· Healthcare
Countries Affected
· Global
Exposure due to widespread use of Adobe Acrobat and Reader across enterprise environments
S15 Adversary Capability Profiling
Skill Level
Moderate to High
Tooling Requirements
Capability to generate or weaponize malicious PDF files and leverage in-application execution behavior, including staged or conditional execution within the Acrobat context
Infrastructure Needs
Minimal infrastructure required for initial access, typically involving document delivery mechanisms such as phishing or hosted file distribution, with additional infrastructure optional for post-exploitation activity
Operational Scale
High, due to ease of delivery and broad exposure across user populations
S16 Targeting Probability Assessment
Highest Probability Targets
Users in finance, legal, document-processing, and email-facing roles with frequent interaction with externally sourced PDF documents
Rationale
High exposure to externally delivered documents combined with required user interaction increases likelihood of successful exploitation
Moderate Probability Targets
General enterprise users engaged in internal document-sharing workflows
Rationale
Exposure exists through internal document exchange but is reduced compared to externally facing roles
Lower Probability Targets
Restricted or hardened environments with limited document interaction
Rationale
Reduced exposure to external content and controlled execution environments lower likelihood of exploitation
S17 MITRE ATT&CK Chain Flow Mapping
Only Initial Access, Execution, and Defense Evasion stages are directly supported by current reporting. Additional stages are included for completeness and may occur during post-exploitation depending on attacker objectives and target environment.
Initial Access
T1566.001 – Phishing Attachment
Delivery of malicious PDF files through email or external document workflows
Execution
T1204 – User Execution
T1203 – Exploitation for Client Execution
Exploit executes within the Acrobat process, enabling in-application code execution that is not observable through standard telemetry until activity transitions into system-level behavior
Persistence
Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment
Privilege Escalation
Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment
Defense Evasion
T1027 – Obfuscated Files or Information
Exploit behavior may include staged or conditional execution within the application context, reducing early-stage visibility and delaying observable indicators
Command and Control
T1071 – Application Layer Protocol
Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment
Lateral Movement
Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment
Impact
Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment
S18 Attack Path Narrative (Signal-Aligned Execution Flow)
The attack begins with delivery of a malicious PDF through standard enterprise workflows such as email, web downloads, chat platforms, or shared storage. The victim opens the document in Adobe Acrobat or Reader, initiating exploit execution within a trusted application context. This activity is confirmed to be occurring in the wild under active exploitation conditions.
During this phase, the exploit operates within the Acrobat process and performs staged logic, including environment interaction and conditional execution behavior. Observed activity includes abuse of privileged Acrobat APIs, local file access, and system fingerprinting prior to payload staging. This allows attacker-controlled execution to occur in a context that aligns with normal application behavior while adapting to the target environment.
A critical transition occurs when execution moves beyond the Acrobat process into the user environment. At this point, the attacker gains broader execution capability under the current user context, potentially retrieving or executing follow-on payloads delivered from attacker-controlled infrastructure.
If this transition is successful, the attacker establishes a foothold that can support additional activity depending on objectives and environmental conditions. Current reporting supports malicious document delivery, user-triggered execution, staged in-application exploitation, and early-stage evasion. Persistence, privilege escalation, lateral movement, and impact behaviors are not directly observed and should be treated as conditional post-exploitation possibilities.
S19 Attack Chain Risk Amplification Summary
· Execution within a trusted application delays visibility during the earliest stage of compromise.
· User-triggered activation aligns with normal enterprise workflows, increasing likelihood of successful exploitation.
· Widespread use of Acrobat and Reader increases the number of exposed endpoints.
· In-application execution creates a gap between exploit initiation and observable system-level activity.
· External document delivery mechanisms enable scalable targeting across user populations.
· Confirmed active exploitation increases the probability of rapid campaign expansion and opportunistic targeting.
Figure 3
S20 Tactics, Techniques, and Procedures
User-Driven Exploit Activation
· T1204 – User Execution
· The attacker relies on user interaction with a malicious PDF to trigger execution within a trusted application context.
In-Application Exploitation
· T1203 – Exploitation for Client Execution
· Exploit logic executes within the Acrobat process using privileged API access, enabling local file interaction, environment-aware behavior, and staged execution prior to extension into the user environment.
Early-Stage Evasion Within Trusted Context
· T1027 – Obfuscated Files or Information
· Attack behavior may incorporate staged and conditional execution within the application context, reducing early visibility and delaying observable indicators until later stages.
Post-Exploitation Activity (Conditional)
· T1071 – Application Layer Protocol
· Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment.
· Persistence, Privilege Escalation, Lateral Movement, and Impact
· Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment.
S20A Adversary Tradecraft Summary (Final)
This tradecraft leverages a trusted enterprise application to execute attacker-controlled code in a context that aligns with normal user behavior while incorporating staged and environment-aware execution logic. The exploit operates within the Acrobat process during the initial phase, reducing early visibility and delaying the generation of observable activity.
Observed behavior demonstrates abuse of privileged Acrobat APIs, enabling local file access, system interaction, and environment fingerprinting prior to payload delivery. This allows the attacker to assess the target environment and conditionally retrieve or execute follow-on code from attacker-controlled infrastructure.
The approach relies on common document workflows and standard user interaction, allowing consistent initial access without requiring credentials, elevated privileges, or complex preconditions. This makes the technique effective across a wide range of enterprise environments.
A defining characteristic of this tradecraft is the separation between staged in-application execution and subsequent execution within the user environment. This separation enables the attacker to operate with reduced visibility during early stages while maintaining flexibility in payload delivery and execution timing.
Confirmed active exploitation indicates that this tradecraft is operationally viable and actively in use, with high potential for reuse and adaptation in near-term campaigns, particularly in environments with frequent document handling and limited visibility into trusted application behavior.
S21 Detection Strategy Overview
This zero-day vulnerability (CVE-2026-34621) represents a user-triggered exploitation path where a malicious PDF causes code execution within Adobe Acrobat/Reader, a highly trusted enterprise application. Because exploitation occurs inside a legitimate process, the exploit itself is not reliably observable at the point of trigger, and detection must focus on post-execution behavioral deviation.
Detection Anchoring Model
User opens a PDF (trusted action)
Exploit executes inside Acrobat (low visibility)
Execution escapes into OS-level behavior (detectable)
Optional outbound communication or payload staging (detectable)
Reliable detection begins at:
Execution escape (Step 3)
Post-execution activity (Step 4)
Core Detection Strategy
Detection must focus on behavior that Acrobat does not normally perform:
Spawning system-level processes
Invoking scripting engines or execution utilities
Initiating outbound network connections
Writing or executing content from user or temporary directories
These behaviors represent high-confidence indicators of compromise when originating from Acrobat/Reader.
Detection Signal Classes
Deterministic High-Confidence Signals
Acrobat/Reader spawning:
Command interpreters
Script engines
System execution binaries
Immediate process lineage violations from a document viewer context
These signals support standalone alerting.
Correlation-Dependent Signals
PDF interaction followed by:
Network communication
File write and execution chains
Time-bound sequence:
Document open → execution → outbound activity
These signals require multi-telemetry correlation and must not alert independently.
Telemetry Dependency Model
Minimum Viable Detection
Endpoint process creation logging
Parent-child process visibility
Without this, core detection coverage is not achievable.
Enhanced Detection Capability
EDR memory behavior telemetry
DNS and web proxy logging
Email attachment telemetry
These enable:
Correlation-based detection
Early-stage attack visibility
Reduced dwell time
Adversary Evasion Considerations
Detection reliability degrades if the attacker:
Executes entirely in memory without spawning processes
Uses COM or reflective loading techniques
Delays execution to evade time-based correlation
Uses trusted or previously observed infrastructure
Avoids outbound communication entirely
These scenarios represent conditional visibility gaps, not detection failures.
Operational Detection Priorities
Enable real-time alerting for:
Acrobat process lineage violations
Implement correlation logic across:
Endpoint execution
Network activity
Conduct retrospective hunting for:
Acrobat-driven execution chains
Prioritize monitoring for:
Users handling external PDFs
Email-facing roles
Detection Strategy Constraints
Exploit trigger is not reliably detectable pre-execution
Memory-only execution may evade file-based controls
Encrypted traffic limits payload inspection
Detection effectiveness depends on:
Endpoint visibility
Cross-telemetry correlation capability
S22 Primary Detection Signals
Detection signals for CVE-2026-34621 are derived from observable behavioral artifacts across the full exploitation chain, including pre-execution fingerprinting, API abuse within Acrobat/Reader, execution escape, and post-exploitation activity. All signals are defined as atomic, telemetry-bound units to support direct detection engineering in S25.
Endpoint Detection Signals
Deterministic High-Confidence Signals
· Acrobat/Reader spawning cmd.exe
· Acrobat/Reader spawning powershell.exe
· Acrobat/Reader spawning wscript.exe
· Acrobat/Reader spawning cscript.exe
· Acrobat/Reader spawning rundll32.exe
· Acrobat/Reader spawning mshta.exe
· Acrobat/Reader acting as parent process for non-document-handling executables
Correlation-Dependent Endpoint Signals
· Acrobat/Reader followed by execution of a binary from:
o User temp directory
o Downloads directory
o User profile paths
· Acrobat/Reader followed by file write event and subsequent execution within a short time window
· Acrobat/Reader exhibiting in-memory execution indicators (EDR-dependent)
· Acrobat/Reader exhibiting abnormal module load behavior inconsistent with standard PDF rendering
Acrobat API Abuse Signals
Correlation-Dependent Signals
· Acrobat/Reader invoking file-read functionality consistent with:
o Local file enumeration or access behavior
· Acrobat/Reader invoking API behavior consistent with:
o Data stream extraction from local files
· Acrobat/Reader invoking functionality consistent with:
o RSS feed or external resource retrieval mechanisms
· Acrobat/Reader performing sequential file access operations indicative of host fingerprinting
Email Delivery Signals
Deterministic Signals
· Email delivering PDF attachment from:
o External sender domain not previously observed
o Newly registered or low-reputation domain
Correlation-Dependent Email Signals
· Email-delivered PDF followed by endpoint execution anomalies on recipient host
· PDF attachment containing embedded scripting behavior (sandbox-dependent visibility)
· PDF attachment exhibiting structural obfuscation characteristics
Network and DNS Detection Signals
Correlation-Dependent Signals
· Outbound network connection initiated shortly after Acrobat/Reader execution
· DNS query initiated shortly after PDF open event
· First-time domain communication originating from user workstation following Acrobat execution
· HTTP or HTTPS connection to:
o Low-reputation domains
o Dynamic DNS infrastructure
· Periodic outbound communication behavior consistent with beaconing
· Outbound communication patterns consistent with data exfiltration following PDF interaction
· Network communication using user-agent patterns inconsistent with standard browser activity originating from Acrobat context
Cross-Telemetry Correlation Signals
· Email delivery of PDF followed by Acrobat execution and suspicious child process spawn
· Acrobat execution followed by sequential local file access and outbound network communication
· Acrobat execution followed by file write and execution of dropped content
· Acrobat execution followed by outbound network connection within defined time window
· Acrobat execution followed by host fingerprinting behavior and conditional network communication
Signal Classification Model
Deterministic Signals
· Direct process lineage violations from Acrobat/Reader
Correlation-Dependent Signals
· API abuse and local file access behavior
· Execution chains requiring sequence validation
· Network activity following execution or fingerprinting
· Email-to-endpoint linkage signals
S22 Primary Detection Signals
Detection signals for CVE-2026-34621 are derived from observable behavioral artifacts across the full exploitation chain, including pre-execution fingerprinting, API abuse within Acrobat/Reader, execution escape, and post-exploitation activity. All signals are defined as atomic, telemetry-bound units to support direct detection engineering in S25.
Endpoint Detection Signals
Deterministic High-Confidence Signals
· Acrobat/Reader spawning cmd.exe
· Acrobat/Reader spawning powershell.exe
· Acrobat/Reader spawning wscript.exe
· Acrobat/Reader spawning cscript.exe
· Acrobat/Reader spawning rundll32.exe
· Acrobat/Reader spawning mshta.exe
· Acrobat/Reader acting as parent process for non-document-handling executables
Correlation-Dependent Endpoint Signals
· Acrobat/Reader followed by execution of a binary from:
o User temp directory
o Downloads directory
o User profile paths
· Acrobat/Reader followed by file write event and subsequent execution within a short time window
· Acrobat/Reader exhibiting in-memory execution indicators (EDR-dependent)
· Acrobat/Reader exhibiting abnormal module load behavior inconsistent with standard PDF rendering
Acrobat API Abuse Signals
Correlation-Dependent Signals
· Acrobat/Reader invoking file-read functionality consistent with:
o Local file enumeration or access behavior
· Acrobat/Reader invoking API behavior consistent with:
o Data stream extraction from local files
· Acrobat/Reader invoking functionality consistent with:
o RSS feed or external resource retrieval mechanisms
· Acrobat/Reader performing sequential file access operations indicative of host fingerprinting
Email Delivery Signals
Deterministic Signals
· Email delivering PDF attachment from:
o External sender domain not previously observed
o Newly registered or low-reputation domain
Correlation-Dependent Email Signals
· Email-delivered PDF followed by endpoint execution anomalies on recipient host
· PDF attachment containing embedded scripting behavior (sandbox-dependent visibility)
· PDF attachment exhibiting structural obfuscation characteristics
Network and DNS Detection Signals
Correlation-Dependent Signals
· Outbound network connection initiated shortly after Acrobat/Reader execution
· DNS query initiated shortly after PDF open event
· First-time domain communication originating from user workstation following Acrobat execution
· HTTP or HTTPS connection to:
o Low-reputation domains
o Dynamic DNS infrastructure
· Periodic outbound communication behavior consistent with beaconing
· Outbound communication patterns consistent with data exfiltration following PDF interaction
· Network communication using user-agent patterns inconsistent with standard browser activity originating from Acrobat context
Cross-Telemetry Correlation Signals
· Email delivery of PDF followed by Acrobat execution and suspicious child process spawn
· Acrobat execution followed by sequential local file access and outbound network communication
· Acrobat execution followed by file write and execution of dropped content
· Acrobat execution followed by outbound network connection within defined time window
· Acrobat execution followed by host fingerprinting behavior and conditional network communication
Signal Classification Model
Deterministic Signals
· Direct process lineage violations from Acrobat/Reader
Correlation-Dependent Signals
· API abuse and local file access behavior
· Execution chains requiring sequence validation
· Network activity following execution or fingerprinting
· Email-to-endpoint linkage signals
S23 Telemetry Requirements
Telemetry requirements for CVE-2026-34621 must support detection across the full exploitation chain, including PDF-triggered execution, Acrobat JavaScript activity, privileged API abuse, local file access, outbound communication, and post-execution behavior. All telemetry is defined as implementable, collection-ready data sources aligned to S22 detection signals.
Endpoint Telemetry Requirements
Minimum Required Telemetry
· Process creation logs including:
o Process name
o Parent process name
o Command line
o Process path
o User context
· Parent-child process relationship tracking
· File execution events from:
o Temporary directories
o Downloads directories
o User profile paths
· File creation events with timestamp correlation capability
· Acrobat/Reader process start events
Enhanced Endpoint Telemetry
· EDR telemetry providing:
o In-memory execution indicators
o Process injection indicators
o Script execution within trusted processes
· Module load telemetry for Acrobat/Reader
· File write followed by execution correlation telemetry
· Persistence-related telemetry:
o Registry changes
o Scheduled tasks
o Service creation
Acrobat-Specific Telemetry Requirements
Minimum Required Telemetry
· Acrobat/Reader version inventory
· PDF file open events from:
o Endpoint telemetry
o File access logs
o DLP or application monitoring
· Mapping of Acrobat activity to:
o Host
o User
Enhanced Acrobat-Specific Telemetry
· PDF sandbox or detonation telemetry showing:
o Embedded JavaScript execution
o Obfuscation behavior
o External resource access
· Visibility into Acrobat JavaScript behavior where supported
· Detection visibility for API usage patterns consistent with:
o Local file access operations
o External resource retrieval
Email Telemetry Requirements
Minimum Required Telemetry
· Sender address and domain
· Recipient
· Delivery timestamp
· Attachment presence
· Attachment file type
· Message direction (external vs internal)
Enhanced Email Telemetry
· Attachment analysis results including:
o Embedded scripting
o Obfuscation indicators
o Structural anomalies
· Sender reputation and domain intelligence
Network and DNS Telemetry Requirements
Minimum Required Telemetry
· DNS logs including:
o Queried domain
o Source host
o Timestamp
· Network connection logs including:
o Source host
o Destination IP
o Destination domain
o Port
o Protocol
o Timestamp
Enhanced Network Telemetry
· HTTP/HTTPS proxy logs including:
o URL or host
o User agent
o TLS SNI
· Detection visibility for:
o First-seen domains
o Dynamic DNS usage
· Network flow telemetry for environments without full proxy visibility
Correlation Telemetry Requirements
Minimum Correlation Set
· Acrobat process start event
· File delivery or file access context
· Process creation telemetry
· File write and execution telemetry
· DNS or network connection telemetry
Enhanced Correlation Set
· Email attachment analysis output
· Acrobat JavaScript or sandbox telemetry
· EDR memory telemetry
· Proxy telemetry with user-agent visibility
· Domain or IP enrichment data
Telemetry Gaps and Limitations
· Lack of EDR reduces visibility into:
o In-memory execution
o API-level behavior
· Lack of sandboxing reduces visibility into:
o JavaScript execution
o PDF active content
· Lack of proxy telemetry reduces:
o User-agent visibility
o Detailed outbound request context
· Lack of process lineage prevents:
o Reliable execution escape detection
· Encrypted traffic limits:
o Payload inspection
Telemetry Dependency Model
Standalone Detection Capability
Requires:
· Process creation telemetry
· Parent-child relationship tracking
Enables:
· Detection of Acrobat spawning system processes
Correlation Detection Capability
Requires:
· Endpoint telemetry
· Network telemetry
· Email or file-delivery telemetry
Enables:
· PDF open → execution → network activity correlation
· File write → execution chain detection
· Fingerprinting behavior followed by outbound communication
S24 Detection Opportunities and Gaps
Detection opportunities and gaps for CVE-2026-34621 are assessed across the observed exploit chain: malicious PDF open, Acrobat JavaScript execution, privileged API abuse, local host fingerprinting, conditional second-stage activity, and post-execution behavior. This section identifies where detection is strongest, where correlation materially improves confidence, and where visibility remains constrained by telemetry or attacker-controlled evasion.
High-Confidence Detection Opportunities
· Detection of Acrobat/Reader spawning:
o cmd.exe
o powershell.exe
o wscript.exe
o cscript.exe
o rundll32.exe
o mshta.exe
· Detection of Acrobat/Reader acting as the parent process for non-document-handling executables
· Detection of file write followed by execution from:
o Temporary directories
o Downloads directories
o User profile paths
· Detection of Acrobat/Reader execution followed by near-immediate outbound network activity from the same host
These opportunities provide the strongest direct detection paths because they represent observable execution escape from a trusted document viewer into operating system or network behavior.
Correlation-Driven Detection Opportunities
· Correlation of:
o PDF delivery or file access context → Acrobat/Reader execution → suspicious child process creation
· Correlation of:
o Acrobat/Reader execution → local file access behavior → outbound communication
· Correlation of:
o Acrobat/Reader execution → file write → execution of dropped content
· Correlation of:
o Acrobat/Reader execution → DNS query → HTTP/HTTPS connection
· Correlation of:
o Acrobat/Reader execution → endpoint anomaly → network communication within a short time window
These opportunities provide higher-confidence detections than any single medium-fidelity signal in isolation.
Early-Stage Detection Opportunities
· Detection of Acrobat/Reader performing sequential local file access behavior within a short time window
· Detection of Acrobat/Reader behavior consistent with:
o Local file stream access
o External resource retrieval
· Detection of Acrobat/Reader local file access followed by outbound communication
· Detection of suspicious PDF active-content behavior through sandboxing or detonation telemetry where available
These opportunities are important because they may surface attacker fingerprinting or staging activity before obvious post-exploitation behavior occurs.
Network Detection Opportunities
· Detection of outbound connections initiated shortly after Acrobat/Reader execution
· Detection of first-seen domain communication originating from the same endpoint after PDF interaction
· Detection of HTTP or HTTPS activity from Acrobat-related execution context showing:
o Unusual user-agent behavior
o Non-browser communication patterns
· Detection of periodic outbound communication consistent with beaconing
· Detection of outbound communication patterns potentially consistent with exfiltration following Acrobat/Reader activity
These opportunities are strongest when endpoint timing and host attribution are available.
Detection Gaps — Endpoint Visibility
· In-process exploit execution without child process creation may evade lineage-based detection
· Memory-only exploitation may not create:
o Executable drop artifacts
o Durable file-system evidence
· Environments without EDR telemetry will have reduced visibility into:
o In-memory execution
o Injection-like behavior
o suspicious runtime behavior inside Acrobat/Reader
These gaps reduce visibility into exploit activity that remains confined to the trusted application process.
Detection Gaps — Application and Content Visibility
· Environments without sandboxing or application-level inspection may have limited visibility into:
o Acrobat JavaScript execution
o Obfuscated PDF active content
o Privileged API abuse
· Early fingerprinting behavior may be missed where no application-aware telemetry exists
· Local file access behavior may be observable only indirectly in lower-visibility environments
These gaps reduce the ability to identify malicious activity before later-stage execution escape or network behavior occurs.
Detection Gaps — Network Visibility
· Encrypted traffic limits inspection of payload content and exfiltrated content
· Environments without proxy telemetry or user-agent visibility may miss higher-fidelity web indicators
· Use of trusted, aged, or previously seen infrastructure can weaken reputation-based detections
· Environments with incomplete DNS visibility may miss early outbound resolution activity
These gaps reduce the precision of network-only detection approaches.
Detection Gaps — Correlation and Operational Limitations
· Environments without centralized event correlation cannot reliably detect multi-stage attack chains
· Inconsistent timestamping across endpoint, email, and network logs weakens short-window sequence detection
· Lack of email telemetry reduces the ability to tie malicious PDF delivery to downstream execution
· Fragmented logging coverage across business units or platforms can reduce detection consistency
These gaps reduce confidence in end-to-end detection even when isolated signals exist.
Detection Gaps — Adversary Evasion and Variants
· Delayed execution can weaken or defeat short-window correlation logic
· Selective second-stage delivery based on host fingerprinting can reduce observable malicious behavior on some systems
· Alternate execution mechanisms, including COM-mediated behavior or reflective loading, may bypass simple child-process-focused detections
· Low-noise operation that avoids outbound communication can reduce network detection opportunities
These gaps reflect attacker-controlled tradecraft variation rather than a failure in detection design.
Coverage Summary
· Strong coverage exists for:
o Process lineage violations
o Execution escape behavior
o Correlated endpoint and network activity
· Moderate coverage exists for:
o File write and execution chains
o Suspicious outbound communication patterns
o Early-stage behavior when sandbox or application-aware telemetry is available
· Limited coverage exists for:
o In-process exploit activity with no child process creation
o API abuse without supporting application-aware telemetry
o Early fingerprinting behavior in low-visibility environments
S25 Ultra-Tuned Detection Engineering Rules
Suricata
Suricata provides limited supporting detection capability for CVE-2026-34621. The exploit operates primarily within Adobe Acrobat/Reader using JavaScript, privileged API abuse, and in-memory execution paths that are not visible to network-based detection systems. Suricata is therefore constrained to post-exploitation network behavior and should be used as a correlation-supporting system, not a primary detection mechanism.
Suricata A Selected Detection Rule
Rule Name
Acrobat Suspicious User-Agent External Communication (High-Fidelity)
Purpose
Detect outbound HTTP activity associated with reported exploit behavior by identifying the Adobe Synchronizer user-agent observed in real-world exploitation.
Reason for Inclusion
This rule is included because it is the strongest Suricata-detectable network artifact currently tied to reported exploit behavior and offers the highest-confidence supporting signal available to this system.
SOC Usage Mode
Correlation-first. Standalone alerting is not permitted.
Minimum Deployment Requirement
· HTTP header visibility
· Outbound traffic inspection
· Host attribution for correlation
· Ability to correlate with:
o recent Acrobat/Reader execution
o suspicious PDF delivery context
Enforcement Method
Exact user-agent matching on outbound HTTP traffic, scoped to internal-to-external communications and workstation-originated traffic where feasible.
Implementation Constraint Notes
· Must not be used as a standalone alert
· Must be correlated with:
o recent Acrobat/Reader execution
o suspicious PDF delivery
o or a high-risk external PDF workflow
· Must suppress or allowlist:
o legitimate Adobe infrastructure
o approved enterprise destinations
o known benign proxy-mediated traffic
· Detection effectiveness is reduced in:
o TLS-only environments
o environments without reliable HTTP header visibility
Tuning Explanation
Restrict to workstation subnets, outbound-only traffic, and external destinations. Suppress known Adobe, SaaS, CDN, and enterprise-approved domains. Strengthen with external enrichment for destination rarity, first-seen domains, and recent Acrobat execution on the same host.
Variant Coverage
· Detects known exploit-associated user-agent behavior
· May surface second-stage retrieval or callback activity when the reported user-agent is reused
· Does not detect:
o modified or randomized user-agents
o non-HTTP protocols
o encrypted traffic without header visibility
o exploit paths with no outbound communication
Production Ready
Yes, as a supporting correlated detection.
Rule Regret Check
Deployment caution
Requires strict allowlisting and endpoint or delivery correlation to avoid noise.
Confidence caution
Moderate on network data alone; high when correlated with recent Acrobat/Reader activity.
Coverage value
High relative to Suricata’s visibility constraints, but limited to post-exploitation network behavior.
System-Ready Code
alert http $HOME_NET any -> $EXTERNAL_NET any (
msg:"Acrobat Suspicious User-Agent External Communication";
flow:established,to_server;
content:"User-Agent|3a| Adobe Synchronizer"; nocase;
http.header;
classtype:trojan-activity;
sid:100001;
rev:5;
)
Suricata B Additional High-Value Detection Candidates (Not Selected)
Rule 2
Rule Name
Acrobat Outbound HTTP to Unapproved External Domains (Context-Enforced)
Purpose
Detect outbound HTTP connections to non-allowlisted external domains that may indicate exploit-driven communication or staging activity.
Reason for Inclusion
This rule is included because attacker-controlled or uncommon external infrastructure remains a relevant post-exploitation pattern, even though Suricata alone cannot distinguish it cleanly from benign enterprise traffic.
SOC Usage Mode
Correlation-only. Standalone alerting is not permitted.
Minimum Deployment Requirement
· HTTP host visibility
· Mature domain allowlisting capability
· Endpoint correlation capability
· Network segmentation awareness
· External enrichment capability
Enforcement Method
Negative-match domain filtering using HTTP host values, supported by external enrichment, suppression, and endpoint correlation outside Suricata.
Implementation Constraint Notes
· Not viable without:
o strong domain allowlisting
o endpoint correlation
o destination enrichment
· Must suppress:
o SaaS platforms
o CDNs
o enterprise-approved services
o middleware traffic
o proxy-related traffic
· Not viable in dynamic SaaS-heavy environments without strong baseline controls
Tuning Explanation
Restrict to workstation networks and external-only traffic. Correlate with recent Acrobat/Reader execution. Apply domain age, rarity, and first-seen enrichment outside Suricata. Continuously validate and retune against tenant baseline traffic.
Variant Coverage
· May detect previously unseen or attacker-controlled destinations
· May retain value if the attacker changes user-agent but still uses uncommon infrastructure
· Does not detect:
o trusted-domain abuse
o encrypted traffic without usable HTTP host visibility
o benign but uncommon business traffic without mature enrichment
Production Ready
No.
CyberDax Non-Selection Rationale
This candidate was not selected as a primary production-ready rule because it is too noise-prone in enterprise environments, too dependent on external allowlisting and enrichment, and too reliant on endpoint correlation to meet CyberDax primary-rule standards for Suricata.
Engineer Uplift Requirements
· Enforce workstation-only scope
· Enforce external-destination-only scope
· Maintain strict destination allowlists
· Integrate domain age, rarity, and first-seen enrichment
· Correlate with recent Acrobat/Reader execution
· Suppress SaaS, CDN, middleware, proxy, and enterprise-approved services
· Validate repeatedly against tenant baseline traffic and change windows
Rule Regret Check
Deployment caution
Extremely noisy without mature allowlisting, enrichment, and endpoint correlation.
Confidence caution
Low standalone; moderate only after strong enrichment and scoping.
Coverage value
Moderate with mature controls; weak otherwise.
System-Ready Code
alert http $HOME_NET any -> $EXTERNAL_NET any (
msg:"Candidate Acrobat Outbound HTTP to Unapproved Domain";
flow:established,to_server;
http.host;
pcre:"/^(?!.*(microsoft|google|adobe|amazonaws|cloudfront|office)).*$/Hi";
classtype:trojan-activity;
sid:100002;
rev:5;
)
Rule 3
Rule Name
Acrobat-Initiated External XML or Feed Retrieval (Behavior-Constrained)
Purpose
Detect outbound XML or feed-style retrieval behavior that may align with exploit staging or reported feed-retrieval abuse patterns.
Reason for Inclusion
This rule is included because public exploit behavior indicates feed-style external retrieval may be relevant, even though this pattern is too environment-sensitive to treat as a selected production-ready Suricata rule.
SOC Usage Mode
Correlation-only. Standalone alerting is not permitted.
Minimum Deployment Requirement
· HTTP URI visibility
· Endpoint correlation capability
· Strong allowlisting
· Environment-aware suppression controls
· Reliable understanding of legitimate XML-heavy traffic patterns
Enforcement Method
URI inspection for outbound XML retrieval patterns, supported by contextual filtering, suppression, and endpoint correlation before analyst use.
Implementation Constraint Notes
· Extremely environment-sensitive
· Must suppress:
o enterprise integrations
o XML-heavy line-of-business applications
o middleware services
o known benign external data feeds
· Not viable without:
o strong suppression
o endpoint correlation
o tenant-specific baseline knowledge
Tuning Explanation
Restrict to workstation endpoints and external-only domains. Correlate with Acrobat/Reader execution timing. Suppress known XML-heavy services and enterprise integrations. Apply destination rarity and host-role filtering outside Suricata. Tune continuously against legitimate XML traffic patterns in the tenant environment.
Variant Coverage
· May detect some feed-based or XML-based external retrieval behavior
· May retain value when exploit stages use simple XML or feed retrieval over HTTP
· Does not detect:
o non-XML retrieval
o encrypted traffic without URI visibility
o legitimate XML traffic without mature suppression
o exploit paths that avoid network retrieval entirely
Production Ready
No.
CyberDax Non-Selection Rationale
This candidate was not selected as a primary production-ready rule because it is extremely noisy in most enterprise environments, weakly tied to malicious behavior without strong context, and highly dependent on suppression and endpoint correlation.
Engineer Uplift Requirements
· Enforce workstation-only scope
· Enforce external-only traffic filtering
· Suppress all known XML-heavy applications and services
· Correlate with recent Acrobat/Reader execution
· Integrate destination rarity and reputation enrichment
· Baseline legitimate enterprise XML traffic patterns and retune regularly
Rule Regret Check
Deployment caution
Very high noise risk without aggressive suppression and strong context.
Confidence caution
Low standalone; limited correlation value without mature baselining.
Coverage value
Limited to moderate, depending heavily on environment and supporting controls.
System-Ready Code
alert http $HOME_NET any -> $EXTERNAL_NET any (
msg:"Candidate Acrobat External XML Retrieval Pattern";
flow:established,to_server;
content:".xml"; http.uri; nocase;
classtype:trojan-activity;
sid:100003;
rev:5;
)
Suricata Limitation Statement
Suricata cannot reliably detect:
· the exploit trigger inside Acrobat/Reader
· malicious JavaScript execution within the PDF
· privileged API abuse such as local file access or feed invocation
· in-memory exploitation behavior
· endpoint process lineage violations
These limitations are driven by lack of endpoint telemetry, lack of application-process visibility, dependence on network-observable post-exploitation behavior, and reduced inspection value in encrypted environments.
Compensating Detection Guidance
Primary detection responsibility for this threat should remain with:
· EDR platforms
· SIEM or correlation engines
· Email security and sandboxing platforms
Suricata should be used as:
· a supporting network signal source
· a correlation enrichment layer
· a post-exploitation visibility component rather than a primary exploit detector
Engineering Note — Suricata
This Suricata subsection is deployment-ready for its selected rule and engineering-ready for its two additional candidates, but all three entries require tenant-specific validation of:
· HTTP header visibility
· HTTP URI visibility
· allowlisting quality
· legitimate Adobe-related traffic patterns
· endpoint-to-network correlation workflow
Coverage remains conditional on visibility into outbound web traffic and will be materially weaker in heavily encrypted environments without proxy-assisted inspection.
SentinelOne
SentinelOne is a primary-fit system for CVE-2026-34621 because the exploit chain relies on endpoint behaviors including Acrobat or Reader execution, execution escape, staged payload delivery, and conditional outbound communication. Detection strength is highest when anchored to process lineage and execution behavior, with temporal correlation reflecting exploit progression.
SentinelOne A Selected Detection Rule(s)
Rule 1
Rule Name
Acrobat or Reader Suspicious Child Process Spawn
Purpose
Detect execution escape from Acrobat or Reader into high-risk operating system interpreters and utilities.
Reason for Inclusion
This rule is included because parent-child process lineage from Acrobat or Reader into system interpreters is the most reliable and highest-confidence indicator of exploit-driven execution.
SOC Usage Mode
Standalone alerting permitted.
Minimum Deployment Requirement
· Process creation telemetry
· Parent-child lineage visibility
· Command-line visibility (recommended)
· Coverage on user workstations
Enforcement Method
· Parent process:
o AcroRd32.exe
o Acrobat.exe
· Child process:
o constrained high-risk interpreter set
Implementation Constraint Notes
· Must suppress:
o legitimate PDF automation workflows
o packaging and deployment tools
· Validate against:
o accessibility tooling
o enterprise scripting workflows
· Investigate:
o unexpected command-line arguments where available
· Recommended response:
o alert by default
o kill/isolate after validation
Tuning Explanation
· Restrict child processes to:
o cmd.exe
o powershell.exe
o wscript.exe
o cscript.exe
o rundll32.exe
o mshta.exe
· Prioritize workstation endpoints
· Suppress known admin or automation workflows
· Review command-line patterns for anomaly enrichment
Variant Coverage
· Strong detection of execution escape behavior
· Resilient to infrastructure changes
· Does not cover:
o in-process execution
o COM-only execution
o memory-only payloads
Production Ready
Yes
Rule Regret Check
Deployment caution
Requires suppression of rare automation workflows.
Confidence caution
High
Coverage value
Very high
System-Ready Code
EventType = "Process Creation"
AND ParentProcessName IN ("AcroRd32.exe","Acrobat.exe")
AND ProcessName IN ("cmd.exe","powershell.exe","wscript.exe","cscript.exe","rundll32.exe","mshta.exe")
Rule 2
Rule Name
Acrobat-Linked Rapid Execution from User-Writable Path (Staged Payload Detection)
Purpose
Detect rapid execution of suspicious payloads from user-writable directories where execution is temporally and causally linked to Acrobat or Reader activity.
Reason for Inclusion
This rule is included because the POC demonstrates local access and staging behavior, and rapid execution of newly introduced content following Acrobat activity is a high-confidence indicator of exploit progression beyond in-application activity.
SOC Usage Mode
Standalone alerting permitted after tuning.
Minimum Deployment Requirement
· Process creation telemetry
· Storyline correlation capability
· File path visibility
· Event timeline correlation
Enforcement Method
· Detect execution of suspicious file types from:
o Temp
o Downloads
o AppData
o User profile directories
· Require:
o storyline linkage to Acrobat
o temporal proximity to Acrobat execution (short window)
Implementation Constraint Notes
· Must suppress:
o browser-driven download execution chains
o enterprise installer workflows
· Must validate:
o user download behavior
o internal tooling execution patterns
· Must NOT alert on:
o long-delayed execution unrelated to Acrobat activity
· Requires tuning for:
o software installation patterns
o patch/update workflows
Tuning Explanation
· Focus on execution of:
o .exe, .dll, .js, .vbs, .ps1, .hta
· Enforce:
o Acrobat storyline parent linkage
o short execution window after Acrobat activity
· Prefer:
o newly introduced files followed by execution
· Suppress:
o signed installers
o known updaters
· Exclude:
o browser-only execution unless Acrobat-linked
Variant Coverage
· Detects staged payload execution following exploit activity
· Covers:
o file-based payloads
o script-based execution
· Does not cover:
o fileless execution
o API-only exploitation
o delayed or user-driven execution outside exploit chain
Production Ready
Yes (after tuning)
Rule Regret Check
Deployment caution
Requires suppression of installer and download workflows and enforcement of temporal correlation.
Confidence caution
High when temporal linkage is enforced; moderate otherwise.
Coverage value
High
System-Ready Code
EventType = "Process Creation"
AND (
ProcessPath CONTAINS "\\Temp\\"
OR ProcessPath CONTAINS "\\Downloads\\"
OR ProcessPath CONTAINS "\\AppData\\"
OR ProcessPath CONTAINS "\\Users\\"
)
AND (
ProcessName ENDSWITH ".exe"
OR ProcessName ENDSWITH ".dll"
OR ProcessName ENDSWITH ".js"
OR ProcessName ENDSWITH ".vbs"
OR ProcessName ENDSWITH ".ps1"
OR ProcessName ENDSWITH ".hta"
)
AND StorylineParentProcessName IN ("AcroRd32.exe","Acrobat.exe")
SentinelOne B Additional High-Value Detection Candidates (Not Selected)
Rule 3
Rule Name
Acrobat Outbound Network Activity to Rare External Destination
Purpose
Detect outbound network communication associated with exploit staging or exfiltration.
Reason for Inclusion
This rule is included because outbound communication is part of observed exploit behavior, but its reliability depends heavily on enrichment and environment maturity.
SOC Usage Mode
Correlation-only
Minimum Deployment Requirement
· Network telemetry
· Domain enrichment capability
· Endpoint correlation
Enforcement Method
· Detect outbound connections initiated by:
o Acrobat or Reader
o or their storyline
Implementation Constraint Notes
· Must suppress:
o Adobe infrastructure
o enterprise SaaS
o proxy traffic
· Requires:
o domain allowlisting
o enrichment
· Weak without:
o rarity scoring
o baseline knowledge
Tuning Explanation
· Restrict to:
o rare / first-seen domains
· Correlate with:
o Acrobat execution
o suspicious PDF context
· Exclude:
o trusted enterprise destinations
Variant Coverage
· Detects post-exploitation communication
· Covers retrieval and exfiltration phases
· Does not cover:
o trusted-domain abuse
o encrypted traffic without attribution
o local-only execution
Production Ready
No
CyberDax Non-Selection Rationale
This candidate was not selected because it is highly dependent on enrichment, highly environment-sensitive, and becomes noisy without strong domain intelligence and suppression controls.
Engineer Uplift Requirements
· Implement domain rarity scoring
· Maintain strict allowlists
· Correlate with Acrobat execution
· Suppress proxy and SaaS traffic
· Continuously baseline network behavior
Rule Regret Check
Deployment caution
High noise risk without enrichment.
Confidence caution
Moderate with strong context; low otherwise.
Coverage value
Moderate
System-Ready Code
EventType = "Network Connection"
AND (
InitiatingProcessName IN ("AcroRd32.exe","Acrobat.exe")
OR StorylineParentProcessName IN ("AcroRd32.exe","Acrobat.exe")
)
AND DestinationType = "External"
Splunk
Splunk is a primary-fit system for CVE-2026-34621 when the environment has normalized endpoint, email, and network telemetry because it can correlate the exploit chain across document delivery, host execution, staged activity, and external communication. Splunk’s strongest value for this threat is multi-source sequence detection, not simple endpoint alerting in isolation.
Splunk A Selected Detection Rule(s)
Rule 1
Rule Name
Suspicious PDF Delivery Followed by Acrobat Execution and Child Process Spawn
Purpose
Detect a high-confidence sequence where an externally delivered PDF is followed by Acrobat or Reader execution and then suspicious child-process creation.
Reason for Inclusion
This rule is included because Splunk is strongest when it links suspicious delivery context to suspicious endpoint behavior. This materially improves confidence beyond a standalone process-spawn alert.
SOC Usage Mode
Correlation-first. Standalone alerting is permitted only when all required stages are present.
Minimum Deployment Requirement
· Email telemetry with:
o sender
o recipient
o attachment name or attachment type
o message direction
· Endpoint process creation telemetry with:
o process name
o parent process name
o user
o host
· Reliable user normalization across sources
· Host visibility for endpoint stages
Enforcement Method
Correlate:
· inbound PDF delivery
· Acrobat or Reader launch
· suspicious child-process creation
within a short time window for the same user, and enforce same-host continuity across the endpoint stages.
Implementation Constraint Notes
· Requires normalized field mapping across email and endpoint sources
· Must suppress:
o trusted internal PDF distribution workflows
o automated document-processing pipelines
o known accessibility or scripting workflows
· Must validate:
o user-to-host mapping quality
o recipient normalization
o endpoint event timeliness
· Should not be deployed if email and endpoint timestamps are materially inconsistent
Tuning Explanation
· Focus on:
o externally delivered PDFs
o user workstations
o Acrobat or Reader process launch
o child processes:
§ cmd.exe
§ powershell.exe
§ wscript.exe
§ cscript.exe
§ rundll32.exe
§ mshta.exe
· Use a constrained correlation window
· Enforce same-host continuity for Acrobat launch and suspicious child activity
· Suppress bulk internal PDF workflows and known automation sources
Variant Coverage
· Strong for delivery-to-execution escape chains
· Stronger than endpoint-only logic because delivery context reduces noise
· Does not cover:
o local PDF opens with no delivery context
o in-process exploitation with no child process
o non-email delivery paths unless adapted
Production Ready
Yes, in environments with normalized email and endpoint telemetry
Rule Regret Check
Deployment caution
Requires reliable email-to-endpoint correlation and timestamp normalization.
Confidence caution
High when delivery, launch, and child-process stages align and endpoint stages occur on the same host.
Coverage value
Very high.
System-Ready Code
(
search index=endpoint (process_name="AcroRd32.exe" OR process_name="Acrobat.exe")
| eval corr_user=lower(user)
| eval corr_host=lower(host)
| eval stage="acrobat_launch"
| fields _time corr_user corr_host stage process_name
)
| append [
search index=endpoint
(parent_process_name="AcroRd32.exe" OR parent_process_name="Acrobat.exe")
(process_name="cmd.exe" OR process_name="powershell.exe" OR process_name="wscript.exe"
OR process_name="cscript.exe" OR process_name="rundll32.exe" OR process_name="mshta.exe")
| eval corr_user=lower(user)
| eval corr_host=lower(host)
| eval stage="suspicious_child"
| fields _time corr_user corr_host stage parent_process_name process_name process_command_line
]
| stats values(stage) as endpoint_stages
min(_time) as endpointFirstTime
max(_time) as endpointLastTime
values(process_name) as process_name
values(process_command_line) as process_command_line
by corr_user corr_host
| where mvfind(endpoint_stages,"acrobat_launch")>=0
AND mvfind(endpoint_stages,"suspicious_child")>=0
AND endpointLastTime-endpointFirstTime<=600
| join type=inner corr_user [
search index=email direction="inbound"
(attachment_name="*.pdf" OR attachment_type="application/pdf")
| eval corr_user=lower(coalesce(recipient,user))
| stats min(_time) as emailFirstTime
max(_time) as emailLastTime
values(sender) as sender
values(sender_domain) as sender_domain
values(attachment_name) as attachment_name
by corr_user
]
| where endpointFirstTime>=emailFirstTime
AND endpointFirstTime-emailFirstTime<=900
| eval firstTime=emailFirstTime, lastTime=endpointLastTime
| convert ctime(firstTime) ctime(lastTime)
Rule 2
Rule Name
Acrobat-Correlated Rapid Write-and-Execute Activity from User-Writable Location
Purpose
Detect staged execution activity where Acrobat or Reader-linked file creation in a user-writable location is followed by rapid execution activity on the same host and user within a short window.
Reason for Inclusion
This rule is included because Splunk can correlate write activity and later execution as a behavioral sequence, which is stronger and more realistic than relying on a single path-based endpoint event.
SOC Usage Mode
Correlation-first. Standalone alerting is permitted only after tenant-specific suppression and field validation.
Minimum Deployment Requirement
· Endpoint file creation telemetry
· Endpoint process creation telemetry
· Reliable host and user attribution
· Path visibility for:
o Temp
o Downloads
o AppData
o user profile paths
Enforcement Method
Correlate:
· Acrobat or Reader-linked file creation in a user-writable location
· subsequent execution activity from the same host and user
· short execution window
· matching or closely related directory context where available
Directory context is enforced as strengthening evidence rather than relying on exact full-path identity.
Implementation Constraint Notes
· Must suppress:
o approved installers
o approved updaters
o browser-driven download-and-run workflows
o enterprise deployment tooling
· Must validate:
o same-user correlation reliability
o endpoint field consistency
o prevalence of benign execution from user-writable paths
· Should not alert on:
o delayed execution outside the short correlation window
o execution chains with no Acrobat or Reader linkage
Tuning Explanation
· Focus on file types ending in:
o .exe
o .dll
o .js
o .vbs
o .ps1
o .hta
· Enforce:
o same host
o same user
o short correlation window
o related write and execution directory context
· Prefer:
o write-then-execute pairs
· Aggressively suppress:
o signed installer activity
o approved updater workflows
o common browser-originated execution patterns unless Acrobat-linked
Variant Coverage
· Strong for staged file-based payload delivery
· Stronger than simple path-based detections because it requires sequence logic
· More resilient than exact same-path matching because it tolerates minor filename changes within the same directory context
· Does not cover:
o fileless execution
o API-only exploitation with no written artifact
o long-delayed execution outside the correlation window
Production Ready
Yes, after tenant-specific suppression and field validation
Rule Regret Check
Deployment caution
Requires strong suppression for installer, updater, and browser download workflows.
Confidence caution
High when same-host, same-user, short-window linkage, and related directory context are enforced.
Coverage value
High.
System-Ready Code
(
index=endpoint event_type="FileCreate"
(initiating_process_name="AcroRd32.exe" OR initiating_process_name="Acrobat.exe")
(
target_file_path="*\\Temp\\*" OR target_file_path="*\\Downloads\\*"
OR target_file_path="*\\AppData\\*" OR target_file_path="*\\Users\\*"
)
(
target_file_path="*.exe" OR target_file_path="*.dll" OR target_file_path="*.js"
OR target_file_path="*.vbs" OR target_file_path="*.ps1" OR target_file_path="*.hta"
)
| eval corr_user=lower(user)
| eval corr_host=lower(host)
| eval write_dir=lower(replace(target_file_path,"\\\\[^\\\\]+$",""))
| eval dir_family=case(
like(lower(target_file_path),"%\\temp\\%"),"temp",
like(lower(target_file_path),"%\\downloads\\%"),"downloads",
like(lower(target_file_path),"%\\appdata\\%"),"appdata",
like(lower(target_file_path),"%\\users\\%"),"users",
true(),"other"
)
| eval stage="file_write"
| fields _time corr_user corr_host write_dir dir_family target_file_path initiating_process_name stage
)
| append [
search index=endpoint event_type="ProcessCreate"
(
process_path="*\\Temp\\*" OR process_path="*\\Downloads\\*"
OR process_path="*\\AppData\\*" OR process_path="*\\Users\\*"
)
(
process_name="*.exe" OR process_name="*.dll" OR process_name="*.js"
OR process_name="*.vbs" OR process_name="*.ps1" OR process_name="*.hta"
)
| eval corr_user=lower(user)
| eval corr_host=lower(host)
| eval exec_dir=lower(replace(process_path,"\\\\[^\\\\]+$",""))
| eval dir_family=case(
like(lower(process_path),"%\\temp\\%"),"temp",
like(lower(process_path),"%\\downloads\\%"),"downloads",
like(lower(process_path),"%\\appdata\\%"),"appdata",
like(lower(process_path),"%\\users\\%"),"users",
true(),"other"
)
| eval stage="file_execute"
| fields _time corr_user corr_host exec_dir dir_family process_path parent_process_name process_name process_command_line stage
]
| stats values(stage) as stages
min(_time) as firstTime
max(_time) as lastTime
values(write_dir) as write_dir
values(exec_dir) as exec_dir
values(dir_family) as dir_family
values(target_file_path) as target_file_path
values(process_path) as process_path
values(initiating_process_name) as initiating_process_name
values(parent_process_name) as parent_process_name
values(process_name) as process_name
values(process_command_line) as process_command_line
by corr_host corr_user
| where mvfind(stages,"file_write")>=0
AND mvfind(stages,"file_execute")>=0
AND lastTime-firstTime<=300
AND (
mvfind(initiating_process_name,"AcroRd32.exe")>=0
OR mvfind(initiating_process_name,"Acrobat.exe")>=0
OR mvfind(parent_process_name,"AcroRd32.exe")>=0
OR mvfind(parent_process_name,"Acrobat.exe")>=0
)
AND (
mvfind(dir_family,"temp")>=0 AND mvcount(write_dir)>0 AND mvcount(exec_dir)>0 AND like(mvjoin(exec_dir,";"),"%\\temp\\%")
OR mvfind(dir_family,"downloads")>=0 AND mvcount(write_dir)>0 AND mvcount(exec_dir)>0 AND like(mvjoin(exec_dir,";"),"%\\downloads\\%")
OR mvfind(dir_family,"appdata")>=0 AND mvcount(write_dir)>0 AND mvcount(exec_dir)>0 AND like(mvjoin(exec_dir,";"),"%\\appdata\\%")
OR mvfind(dir_family,"users")>=0 AND mvcount(write_dir)>0 AND mvcount(exec_dir)>0 AND like(mvjoin(exec_dir,";"),"%\\users\\%")
)
| convert ctime(firstTime) ctime(lastTime)
Rule 3
Rule Name
Suspicious PDF Delivery to Acrobat Execution to External Communication Correlation
Purpose
Detect a multi-telemetry sequence where suspicious PDF delivery is followed by Acrobat or Reader execution and then outbound communication to an external destination.
Reason for Inclusion
This rule is included because Splunk is the strongest place to correlate delivery, host activity, and external communication into a single sequence aligned to the reported exploit chain.
SOC Usage Mode
Correlation-first. Standalone alerting is not permitted unless telemetry normalization, destination allowlisting, and suppression are mature.
Minimum Deployment Requirement
· Email telemetry
· Endpoint Acrobat or Reader launch telemetry
· Network or proxy telemetry with external destination visibility
· Reliable user normalization across all three telemetry pillars
· Host visibility for endpoint and network stages where available
Enforcement Method
Correlate:
· inbound PDF delivery
· Acrobat or Reader execution
· outbound communication to an external destination
within a constrained time window for the same user, and enforce same-host continuity across endpoint and network stages when host attribution exists.
Implementation Constraint Notes
· Requires mature normalization across:
o email fields
o endpoint fields
o network fields
· Must suppress:
o trusted PDF workflows
o legitimate Adobe services
o enterprise proxy artifacts with weak host attribution
· Should be deployed only after validating:
o email normalization
o host attribution quality
o destination allowlisting maturity
Tuning Explanation
· Focus on:
o external inbound PDFs
o user workstations
o short windows after Acrobat launch
o non-allowlisted external destinations
· Raise severity when combined with:
o rare destination logic
o suspicious sender domain
o recent child-process or write-and-execute activity
· Downgrade or suppress:
o internal-only PDF delivery
o trusted business PDF workflows
o legitimate Adobe cloud traffic
Variant Coverage
· Strong for exploit paths that include delivery, execution, and outbound communication
· Helps cover scenarios where no suspicious child process is observed
· Does not cover:
o local-only exploitation with no network activity
o trusted-domain abuse without enrichment
o environments missing one of the three telemetry pillars
Production Ready
Yes, but only in mature environments with normalized telemetry, strong allowlisting, and suppression tuning
Rule Regret Check
Deployment caution
Needs strong normalization and suppression across email, endpoint, and network data.
Confidence caution
High when all three stages are present with good user and host attribution; moderate if attribution is imperfect.
Coverage value
High in mature Splunk environments; moderate in partially normalized environments.
System-Ready Code
(
search index=endpoint (process_name="AcroRd32.exe" OR process_name="Acrobat.exe")
| eval corr_user=lower(user)
| eval corr_host=lower(host)
| eval stage="acrobat_execution"
| fields _time corr_user corr_host stage process_name
)
| append [
search index=network direction="outbound" destination_type="external"
| eval corr_user=lower(user)
| eval corr_host=lower(host)
| eval stage="outbound_network"
| fields _time corr_user corr_host stage dest dest_domain url
]
| stats values(stage) as host_stages
min(_time) as hostFirstTime
max(_time) as hostLastTime
values(dest) as dest
values(dest_domain) as dest_domain
values(url) as url
by corr_user corr_host
| where mvfind(host_stages,"acrobat_execution")>=0
AND mvfind(host_stages,"outbound_network")>=0
AND hostLastTime-hostFirstTime<=900
| join type=inner corr_user [
search index=email direction="inbound"
(attachment_name="*.pdf" OR attachment_type="application/pdf")
| eval corr_user=lower(coalesce(recipient,user))
| stats min(_time) as emailFirstTime
max(_time) as emailLastTime
values(sender) as sender
values(sender_domain) as sender_domain
values(attachment_name) as attachment_name
by corr_user
]
| where hostFirstTime>=emailFirstTime
AND hostFirstTime-emailFirstTime<=900
| eval firstTime=emailFirstTime, lastTime=hostLastTime
| convert ctime(firstTime) ctime(lastTime)
Splunk B Additional High-Value Detection Candidates (Not Selected)
No additional high-value detection candidates are included for Splunk because the three selected entries already consume the system cap and represent the strongest distinct Splunk-native detection families for this threat.
Splunk Limitation Statement
Splunk cannot reliably detect:
· privileged Acrobat API invocation by semantic function name unless upstream telemetry exposes it
· purely in-process exploit behavior with no downstream host or network transition
· telemetry-light branches where the attacker fingerprints the environment and stops without spawning processes, writing staged content, or making attributable outbound connections
These are primarily telemetry limitations, not Splunk search-language limitations.
Compensating Detection Guidance
Splunk should be strengthened with:
· normalized endpoint telemetry for process and file events
· email security data for suspicious PDF delivery
· proxy or network data for external communication
· domain allowlisting and rarity enrichment
· Adobe version inventory and patch-validation context for exposed endpoints
Elastic
Elastic is a strong-fit system for CVE-2026-34621 when the environment has normalized endpoint and file telemetry. It is most effective for detecting execution escape and short-window staged execution behavior. It is not a strong primary system for network-driven detection in this scenario unless enrichment maturity is high.
Rule 1
Rule Name
Acrobat or Reader Suspicious Child Process Spawn
Purpose
Detect execution escape from Acrobat or Reader into high-risk operating system interpreters and execution utilities.
Reason for Inclusion
Parent-child execution from Acrobat or Reader into OS-level interpreters is one of the strongest and lowest-noise indicators of exploit progression. This behavior represents a clear transition from document processing into system-level execution.
SOC Usage Mode
Standalone alerting permitted.
Minimum Deployment Requirement
· Endpoint process creation telemetry
· Parent-child process lineage visibility
· Host and user attribution
Enforcement Method
Detect Acrobat or Reader spawning high-risk interpreters associated with post-exploitation activity.
Implementation Constraint Notes
Must suppress:
· document automation pipelines
· enterprise PDF processing tools
· software packaging systems
· accessibility integrations
Must validate:
· baseline frequency of Acrobat child processes
· enterprise scripting workflows
Recommended:
· deploy in alert-only mode initially
· move to enforcement after validation
Tuning Explanation
· Monitor child processes:
o cmd.exe
o powershell.exe
o wscript.exe
o cscript.exe
o rundll32.exe
o mshta.exe
· Prioritize:
o rare parent-child combinations
o suspicious command-line patterns
o unusual execution context
· Suppress:
o known automation workflows
o repeatable benign execution chains
Variant Coverage
· Strong execution escape detection
· Resilient to payload and infrastructure variation
· Does not cover:
o in-process-only exploitation
o memory-only execution
o COM-based execution without process creation
Production Ready
Yes
Rule Regret Check
Deployment caution
Low after suppression
Confidence caution
High
Coverage value
Very high
System-Ready Code
process
where event.type == "start"
and process.parent.name in ("AcroRd32.exe", "Acrobat.exe")
and process.name in ("cmd.exe", "powershell.exe", "wscript.exe", "cscript.exe", "rundll32.exe", "mshta.exe")
Rule 2
Rule Name
Acrobat-Correlated Rapid Writable-Path Write and Execute Sequence
Purpose
Detect staged execution behavior where Acrobat or Reader creates content in a writable user location and execution follows shortly after on the same host and user.
Reason for Inclusion
This rule captures realistic exploit progression where payloads are written to disk and executed shortly after. Elastic sequence logic enables detection of this behavior even when exact file identity cannot be guaranteed.
SOC Usage Mode
Correlation-first. Standalone alerting permitted after tuning.
Minimum Deployment Requirement
· File creation telemetry
· Process execution telemetry
· Host and user attribution
· Writable-path visibility
Enforcement Method
Sequence:
· Acrobat writes file to writable path
· execution occurs from writable path
· same host
· same user
· short time window
This rule enforces behavioral correlation, not exact file identity.
Implementation Constraint Notes
· Must suppress:
o installers
o updaters
o browser-driven downloads
o enterprise deployment tools
· Must validate:
o writable-path baseline activity
o frequency of benign execution
· Should not alert on:
o delayed execution
o non-Acrobat-linked execution
Tuning Explanation
· Focus writable paths:
o Temp
o Downloads
o AppData
o Users
· Enforce:
o same host
o same user
o short execution window
· Prefer:
o rapid write-to-execution sequences
· Suppress:
o known installer workflows
o update mechanisms
Variant Coverage
· Strong staged payload detection
· Resilient to filename variation
· Does not cover:
o fileless execution
o API-only exploitation
o delayed execution
Production Ready
Yes after tuning
Rule Regret Check
Deployment caution
Moderate due to writable-path noise
Confidence caution
Moderate to high depending on suppression quality
Coverage value
High
System-Ready Code
sequence by host.id, user.name with maxspan=5m
[file where event.type in ("creation", "change")
and process.name in ("AcroRd32.exe", "Acrobat.exe")
and file.path :
("*\\Temp\\*", "*\\Downloads\\*", "*\\AppData\\*", "*\\Users\\*")]
[process where event.type == "start"
and process.executable :
("*\\Temp\\*", "*\\Downloads\\*", "*\\AppData\\*", "*\\Users\\*")]
Elastic Limitation Statement
Elastic does not reliably support additional strong rules for this threat without introducing excessive noise or weak signal quality.
Specifically, Elastic cannot strongly detect:
· in-process Acrobat exploitation
· privileged API abuse without telemetry visibility
· outbound network behavior without enrichment maturity
· exploit chains lacking file or process artifacts
Compensating Detection Guidance
Elastic coverage should be supplemented with:
· endpoint-focused detection systems
· email delivery telemetry
· network enrichment and allowlisting
· Adobe patch and version monitoring
Engineering Note — Elastic
These rules are production-ready templates requiring:
· ECS field validation
· endpoint telemetry completeness
· writable-path baseline tuning
· suppression of installers and enterprise workflows
Coverage quality depends heavily on endpoint telemetry completeness and proper environment tuning.
QRadar
QRadar is a strong-fit system for CVE-2026-34621 when endpoint telemetry is ingested and normalized. It is most effective for detecting execution escape behavior and host-level multi-event correlation. It is not suited for precise file lineage or in-process exploit detection.
Rule 1
Rule Name
Acrobat or Reader Spawning High-Risk Interpreter Process
Purpose
Detect execution escape where Acrobat or Reader spawns a high-risk command interpreter or scripting engine.
Reason for Inclusion
This is the strongest QRadar-compatible detection for this threat. Acrobat spawning interpreters is highly abnormal and strongly indicative of exploitation.
SOC Usage Mode
Standalone alerting permitted.
Minimum Deployment Requirement
· Endpoint process telemetry ingested into QRadar
· Parent-child process visibility from EDR, Sysmon, or equivalent source
· Host and user attribution
· Proper DSM or custom field normalization
Enforcement Method
Trigger when:
· parent process is Acrobat or Reader
· child process is a high-risk interpreter or execution utility
Implementation Constraint Notes
· Requires normalized fields for:
o parent process name
o process name
o host
o user
· Must suppress:
o PDF automation workflows
o document processing tools
o packaging systems
o rare accessibility integrations
· Must validate:
o whether Acrobat or Reader legitimately spawns interpreters in the tenant
· Recommended:
o deploy in alert-only mode initially
o promote to offense after baseline validation
Tuning Explanation
· Monitor child processes:
o cmd.exe
o powershell.exe
o wscript.exe
o cscript.exe
o rundll32.exe
o mshta.exe
· Prioritize:
o user workstations
o rare parent-child relationships
· Review:
o command-line context where available
o parent-child prevalence by business unit
· Suppress:
o known automation chains
o repeatable benign document-processing workflows
Variant Coverage
· Strong execution escape detection
· Resilient to payload and infrastructure variation
· Does not cover:
o in-process exploitation
o memory-only payloads
o COM-only execution
Production Ready
Yes
Rule Regret Check
Deployment caution
Low after field normalization and baseline suppression.
Confidence caution
High.
Coverage value
Very high.
System-Ready Code (AQL)
SELECT *
FROM events
WHERE parent_process_name IN ('AcroRd32.exe','Acrobat.exe')
AND process_name IN ('cmd.exe','powershell.exe','wscript.exe','cscript.exe','rundll32.exe','mshta.exe')
Rule 2
Rule Name
Acrobat-Correlated Writable Path Execution Sequence
Purpose
Detect staged execution behavior where Acrobat or Reader interacts with a writable path and execution follows shortly after on the same host.
Reason for Inclusion
QRadar is effective at correlating multiple events across a host. While it cannot enforce exact file identity, it can detect realistic exploit progression through short-window writable-path activity followed by execution.
SOC Usage Mode
Correlation-first. Offense generation required.
Minimum Deployment Requirement
· File creation or file activity telemetry
· Process execution telemetry
· Host correlation capability
· CRE rule support
· Proper DSM or custom field normalization for:
o process name
o file path
o process path
o host
Enforcement Method
Implement as a QRadar CRE correlation rule, not as a standalone AQL alert.
CRE logic:
Event A
o Acrobat or Reader process activity involving a writable path
Event B
o Process execution from a writable path
Correlation conditions
o same host
o short time window
This rule enforces behavioral correlation, not exact file identity.
Implementation Constraint Notes
· Must be built in CRE using same-host correlation with hostname, source IP, or equivalent stable host key
· Must suppress:
o installers
o updaters
o browser download execution
o enterprise deployment tools
· Must validate:
o writable-path baseline activity
o event timing consistency
o host-level correlation accuracy
· Must not be deployed as a standalone single-event AQL detection
· Should not alert on:
o delayed execution outside the intended window
o non-Acrobat-linked execution chains
Tuning Explanation
· Focus writable paths:
o Temp
o Downloads
o AppData
o Users
· Enforce:
o same host
o short time window
· Prefer:
o rapid writable-path activity followed by execution
· Suppress:
o known installer workflows
o update mechanisms
o common browser-driven download chains
· Consider separate tuning profiles for:
o standard user workstations
o developer endpoints
o VDI/shared environments
Variant Coverage
· Strong staged payload detection
· Resilient to filename variation because it does not depend on exact artifact identity
· Does not cover:
o fileless execution
o API-only exploitation
o delayed execution
o local-only exploitation with no writable-path execution chain
Production Ready
Yes, after CRE implementation and tuning
Rule Regret Check
Deployment caution
Moderate due to writable-path noise and correlation dependency.
Confidence caution
Moderate to high depending on CRE implementation quality, baseline maturity, and suppression quality.
Coverage value
High.
System-Ready Code (AQL Building Blocks)
Event A — Acrobat Writable Path Activity
SELECT *
FROM events
WHERE process_name IN ('AcroRd32.exe','Acrobat.exe')
AND (
file_path ILIKE '%\\Temp\\%'
OR file_path ILIKE '%\\Downloads\\%'
OR file_path ILIKE '%\\AppData\\%'
OR file_path ILIKE '%\\Users\\%'
)
Event B — Execution from Writable Path
SELECT *
FROM events
WHERE
process_path ILIKE '%\\Temp\\%'
OR process_path ILIKE '%\\Downloads\\%'
OR process_path ILIKE '%\\AppData\\%'
OR process_path ILIKE '%\\Users\\%'
CRE Build Requirement
· Correlate Event A and Event B on the same host
· Enforce a short time window
· Generate an offense only when both stages are present
QRadar Limitation Statement
QRadar does not reliably support additional strong rules for this threat without introducing excessive noise or weak correlation quality.
QRadar cannot strongly detect:
· in-process Acrobat exploitation
· exact file lineage between write and execution
· outbound network behavior without enrichment and mature allowlisting
· exploit chains without file or process artifacts
Compensating Detection Guidance
QRadar should be supplemented with:
· endpoint-native detection
· email telemetry
· network enrichment and allowlisting
· Adobe patch and version monitoring
Engineering Note — QRadar
These rules require:
· proper DSM field normalization
· CRE rule construction for sequence correlation
· baseline tuning for writable-path activity
· suppression of installers and enterprise workflows
Rule 1 is directly deployable after field validation. Rule 2 is deployable only when implemented as a CRE correlation rule with same-host matching and short-window timing.
Sigma
Sigma is a detection abstraction layer for CVE-2026-34621 that is effective when endpoint telemetry is available. It is best used to express execution escape behavior and portable endpoint detection logic. It is not suited for complex multi-event correlation without backend SIEM support.
Rule 1
Rule Name
Acrobat or Reader Spawning High-Risk Interpreter Process
Purpose
Detect execution escape from Acrobat or Reader into high-risk operating system interpreters and execution utilities.
Reason for Inclusion
This is the strongest portable detection for this threat. Acrobat spawning interpreters is highly abnormal and directly aligned with exploit execution behavior.
SOC Usage Mode
Standalone alerting permitted.
Minimum Deployment Requirement
· Process creation telemetry
· Parent-child process visibility
· Host and user attribution
Enforcement Method
Detect:
· parent process = Acrobat or Reader
· child process = high-risk interpreter
Implementation Constraint Notes
· Must suppress:
o document automation tools
o enterprise PDF processing workflows
o packaging systems
· Must validate:
o whether Acrobat-driven scripting exists in the environment
Tuning Explanation
· Child processes:
o cmd.exe
o powershell.exe
o wscript.exe
o cscript.exe
o rundll32.exe
o mshta.exe
· Prioritize:
o rare parent-child combinations
· Suppress:
o known automation workflows
Variant Coverage
· Strong execution escape detection
· Resilient to payload variation
· Does not cover:
o in-process exploitation
o memory-only payloads
Production Ready
Yes
Rule Regret Check
Deployment caution
Low after suppression
Confidence caution
High
Coverage value
Very high
System-Ready Code (Sigma)
title: Acrobat Spawning High-Risk Interpreter
id: 7f1c9c44-1a9c-4c9f-9e3e-ecf0c8b41c1a
status: experimental
description: Detects Acrobat or Reader spawning high-risk interpreters indicative of exploit execution escape
logsource:
category: process_creation
product: windows
detection:
selection_parent:
ParentImage|endswith:
- '\AcroRd32.exe'
- '\Acrobat.exe'
selection_child:
Image|endswith:
- '\cmd.exe'
- '\powershell.exe'
- '\wscript.exe'
- '\cscript.exe'
- '\rundll32.exe'
- '\mshta.exe'
condition: selection_parent and selection_child
falsepositives:
- PDF automation workflows
- enterprise document processing tools
- software packaging systems
level: high
Rule 2
Rule Name
Execution of Script or Binary from Suspicious Writable Directory
Purpose
Detect execution of executable or script content from writable directories commonly used for payload staging.
Reason for Inclusion
Execution from writable staging directories is a realistic post-exploitation behavior. This rule complements Acrobat exploitation scenarios by identifying likely payload execution paths without requiring multi-event correlation.
SOC Usage Mode
Standalone alerting with tuning required.
Minimum Deployment Requirement
· Process execution telemetry
· File path visibility
Enforcement Method
Detect:
· execution of executable or script file types
· from high-risk writable directories
Implementation Constraint Notes
· Must suppress:
o installers
o update mechanisms
o browser download workflows
o enterprise deployment tools
· Must validate:
o baseline execution frequency from writable paths
Tuning Explanation
· Focus on execution from:
o \Temp\
o \Downloads\
o \AppData\
· Restrict to:
o executable or script file types
· Combine with backend capabilities if available:
o signer validation
o rarity scoring
· Suppress:
o known installer and update paths
Variant Coverage
· Strong staging-path execution detection
· Resilient to filename variation
· Does not cover:
o fileless execution
o in-process exploitation
Production Ready
Yes after tuning
Rule Regret Check
Deployment caution
Moderate due to writable-path activity
Confidence caution
Moderate until suppression tuning is complete
Coverage value
High
System-Ready Code (Sigma)
title: Execution of Script or Binary from Suspicious Writable Directory
id: 3b2d4f7a-9e2b-4c9e-bc2f-8f2a9e1d6c3f
status: experimental
description: Detects execution of scripts or binaries from writable directories commonly used for payload staging
logsource:
category: process_creation
product: windows
detection:
selection_path:
Image|contains:
- '\Temp\'
- '\Downloads\'
- '\AppData\'
selection_extension:
Image|endswith:
- '.exe'
- '.dll'
- '.js'
- '.vbs'
- '.ps1'
- '.hta'
condition: selection_path and selection_extension
falsepositives:
- software installers
- update mechanisms
- browser downloads
- enterprise deployment tools
level: medium
Sigma Limitation Statement
Sigma cannot reliably support additional strong rules for this threat without backend SIEM or EDR correlation.
Sigma cannot strongly detect:
· multi-event correlation (write to execute)
· exact file lineage
· in-process exploitation
· network correlation behavior
Compensating Detection Guidance
Sigma should be deployed with:
· SIEM or EDR correlation support
· endpoint telemetry enrichment
· suppression tuning
· patch and version monitoring
Engineering Note — Sigma
These rules require:
· backend translation into SIEM or EDR platforms
· field mapping validation
· suppression tuning
· environment-specific baselining
Rule 1 provides the strongest portable detection. Rule 2 should be tuned carefully due to writable-path activity patterns.
YARA
YARA is a strong-fit system for CVE-2026-34621 only for file-content detection and triage, not runtime detection. For this threat, YARA is best used to identify suspicious embedded JavaScript, Acrobat API abuse indicators, and exploit-tradecraft strings in PDFs or extracted PDF object content. It is not appropriate for process lineage, network correlation, or purely runtime-only exploit branches.
Rule 1
Rule Name
PDF JavaScript Privileged Acrobat API Abuse Pattern
Purpose
Detect PDF content or extracted JavaScript that references privileged Acrobat APIs associated with the observed exploit chain.
Reason for Inclusion
This is the strongest YARA detection for this threat because privileged Acrobat API references provide a more stable and threat-specific file-content anchor than generic obfuscation or PDF JavaScript alone.
SOC Usage Mode
Standalone triage and content-scanning detection permitted.
Minimum Deployment Requirement
· YARA scanning of:
o suspicious PDFs
o email attachments
o extracted PDF object streams
o extracted JavaScript content
· Ability to scan raw files or decompressed/decoded content where available
Enforcement Method
Match PDF-linked content containing privileged Acrobat API references together with JavaScript and suspicious stream-handling context.
Implementation Constraint Notes
· Best applied to:
o suspicious inbound PDFs
o sandbox-extracted content
o mail attachment repositories
o retrospective file hunting
· May miss:
o heavily transformed or re-obfuscated variants
o samples where APIs are dynamically assembled at runtime
· Should be paired with:
o PDF detonation
o object-stream extraction
o endpoint or email telemetry for escalation
Tuning Explanation
· Require multiple conditions rather than one API string alone
· Combine:
o PDF context
o JavaScript context
o privileged API references
o supporting stream or encoding indicators
· Prefer scans against:
o extracted object streams
o decoded JavaScript
· Suppress or downgrade:
o research samples
o internal testing corpora
o benign security-lab artifacts
Variant Coverage
· Strong for samples reusing privileged Acrobat API abuse patterns
· Covers file-access and remote-retrieval logic tied to:
o util.readFileIntoStream
o RSS.addFeed
· Does not cover:
o variants that dynamically construct API names
o runtime-only behavior with no recoverable script artifacts
o non-JavaScript exploit paths
Production Ready
Yes, for file-content scanning and triage
Rule Regret Check
Deployment caution
Requires extracted or decodable content for best results.
Confidence caution
High when PDF context, JavaScript context, and both privileged API strings are present together.
Coverage value
Very high for YARA-relative capability.
System-Ready Code
rule PDF_Privileged_Acrobat_API_Abuse_CVE_2026_34621
{
meta:
description = "Detects PDF or extracted JavaScript content abusing privileged Acrobat APIs linked to CVE-2026-34621-style exploitation"
author = "CyberDax"
reference_1 = "CVE-2026-34621"
date = "2026-04-11"
confidence = "high"
strings:
$pdf_magic = "%PDF-" ascii
$js_1 = "/JavaScript" ascii nocase
$js_2 = "app.setTimeOut" ascii nocase
$api_1 = "util.readFileIntoStream" ascii
$api_2 = "RSS.addFeed" ascii
$ctx_1 = "stringFromStream" ascii
$ctx_2 = "streamFromString" ascii
$ctx_3 = "streamDecode" ascii
$ctx_4 = "base64" ascii nocase
condition:
$pdf_magic and
1 of ($js_*) and
$api_1 and $api_2 and
2 of ($ctx_*)
}
Rule 2
Rule Name
PDF Obfuscated JavaScript and Retrieval Tradecraft Pattern
Purpose
Detect suspicious PDF content or extracted JavaScript that combines obfuscation, deferred execution, and retrieval-related tradecraft consistent with the observed exploit chain.
Reason for Inclusion
This rule is included because exploit-tradecraft strings such as delayed execution, stream decoding, encoding, and retrieval markers provide useful hunting and triage value when combined carefully. It is intentionally positioned as a tradecraft rule, not an exploit-confirmation rule.
SOC Usage Mode
Standalone triage rule with analyst review required.
Minimum Deployment Requirement
· YARA scanning against:
o raw PDFs
o extracted PDF objects
o extracted JavaScript
· Preferably integrated with:
o sandboxing
o archive or object extraction workflows
Enforcement Method
Match suspicious combinations of PDF JavaScript context, obfuscation markers, delayed execution, and retrieval-oriented tradecraft.
Implementation Constraint Notes
· Should not be treated as proof of CVE-2026-34621 exploitation by itself
· Best used as:
o high-priority triage
o retrospective hunting
o email attachment screening support
· May require backend extraction because relevant strings can be hidden inside compressed or encoded object streams
· More fragile than Rule 1 because tradecraft strings are easier to change
Tuning Explanation
· Require multiple tradecraft strings together
· Avoid single-string triggers such as only:
o base64
o app.setTimeOut
o streamDecode
· Raise confidence when matched alongside:
o PDF JavaScript markers
o privileged API strings
o suspicious retrieval markers
· Downgrade:
o generic obfuscation-only hits
o isolated JavaScript utility usage with no PDF context
Variant Coverage
· Strong for samples reusing similar obfuscation and staging tradecraft
· Covers:
o delayed JavaScript execution
o stream decoding
o encoded content handling
o retrieval-support artifacts
· Does not cover:
o fully retooled variants with different obfuscation logic
o exploit paths that minimize static script artifacts
o runtime-only memory behavior
Production Ready
Yes, for triage and threat hunting
Rule Regret Check
Deployment caution
Can become noisy if extraction quality is poor or thresholds are weakened.
Confidence caution
Moderate to high when multiple tradecraft markers are present together with PDF JavaScript context.
Coverage value
High.
System-Ready Code
rule PDF_Obfuscated_JS_Retrieval_Tradecraft_CVE_2026_34621
{
meta:
description = "Detects obfuscated PDF JavaScript tradecraft linked to CVE-2026-34621-style exploit staging"
author = "CyberDax"
reference_1 = "CVE-2026-34621"
date = "2026-04-11"
confidence = "medium_high"
strings:
$pdf_magic = "%PDF-" ascii
$js_1 = "/JavaScript" ascii nocase
$js_2 = "app.setTimeOut" ascii nocase
$obf_1 = "base64" ascii nocase
$obf_2 = "streamDecode" ascii
$obf_3 = "stringFromStream" ascii
$obf_4 = "streamFromString" ascii
$ret_1 = "RSS.addFeed" ascii
$ret_2 = "Adobe Synchronizer" ascii
$ret_3 = "decrypt" ascii nocase
condition:
$pdf_magic and
1 of ($js_*) and
3 of ($obf_*) and
1 of ($ret_*)
}
YARA Limitation Statement
YARA does not reliably support additional strong rules for this threat without introducing excessive noise or weak signal quality.
YARA cannot strongly detect:
· in-process exploitation with minimal static artifacts
· exact runtime API invocation if strings are dynamically constructed
· process lineage or child-process spawning
· outbound communication behavior
· correlation across email, endpoint, and network stages
Compensating Detection Guidance
YARA coverage should be supplemented with:
· endpoint-focused detection systems for process behavior
· email and sandbox telemetry for PDF delivery and extraction
· SIEM correlation for delivery, execution, and outbound communication
· Adobe patch and version monitoring
Engineering Note — YARA
These rules are production-ready templates for file-content scanning and require:
· extraction of compressed or encoded PDF objects where possible
· validation against benign PDF and JavaScript corpora
· tuning for research repositories and sandbox detonation environments
· regular review as variants change obfuscation or API-string construction
Rule 1 provides the strongest YARA value. Rule 2 is best treated as a high-priority triage and hunting rule rather than a standalone incident-confirmation signal.
AWS
AWS is a weak-fit system for CVE-2026-34621 as a primary detection layer because this threat is fundamentally a client-side Adobe Acrobat or Reader exploitation problem, not an AWS control-plane or cloud-service-native attack path. The strongest behaviors in this exploit chain occur on the endpoint, including malicious PDF execution, Acrobat JavaScript abuse, and potential staged execution or outbound communication.
AWS-native telemetry such as CloudTrail, EventBridge, Security Hub, and GuardDuty are designed to detect AWS account activity, cloud resource behavior, and API usage, not user workstation application execution.
AWS Selected Detection Rule(s)
No strong AWS-native selected rules are recommended for this threat.
AWS Limitation Statement
AWS does not reliably support strong primary detection rules for CVE-2026-34621 without introducing weak signal quality or forcing detections that are not truly cloud-native.
AWS cannot strongly detect:
· malicious PDF delivery to user workstations
· Acrobat or Reader process execution
· Acrobat spawning child processes
· privileged Acrobat API abuse
· local staged write-and-execute behavior
· short-window endpoint execution chains
CloudTrail records AWS API activity and EventBridge processes AWS service events. Neither natively observes endpoint-level exploit behavior.
Compensating Detection Guidance
For this threat, AWS should be used in a supporting role rather than as a primary detection layer.
Appropriate uses include:
· centralizing alerts from:
o endpoint detection platforms
o email security systems
o sandboxing tools
· routing alerts through:
o EventBridge
o Security Hub
o Lambda-based response workflows
· monitoring AWS-hosted workloads where:
o Acrobat or Reader exists on EC2 or WorkSpaces
o endpoint telemetry is forwarded into a detection system
Engineering Note — AWS
For this report, the correct CyberDax approach is to maintain zero selected rules rather than introduce weak or artificial detections.
AWS becomes relevant only if the environment includes:
· EC2 or WorkSpaces endpoints running Acrobat or Reader
· forwarded endpoint telemetry
· Security Hub or EventBridge used for orchestration after detection occurs in another system
This preserves detection integrity and aligns with the CyberDax requirement to prioritize strong, deployable detections over completeness.
Azure
Azure is a weak-fit system for CVE-2026-34621 as a primary detection layer because this threat is fundamentally a client-side Adobe Acrobat or Reader exploitation scenario, not an Azure control-plane, identity-first, or SaaS-native attack. The core exploit behaviors occur on endpoints, including malicious PDF execution, JavaScript abuse, and potential staged execution.
Azure-native telemetry sources such as Azure Activity Logs, Entra ID (Azure AD) logs, and Microsoft Defender for Cloud focus on identity activity, resource access, and cloud workload behavior. They do not natively observe Acrobat execution or endpoint process behavior unless integrated with endpoint security platforms.
Azure Selected Detection Rule(s)
No strong Azure-native selected rules are recommended for this threat.
Azure Limitation Statement
Azure does not reliably support strong primary detection rules for CVE-2026-34621 without introducing weak signal quality or forcing detections that are not truly aligned to the threat.
Azure cannot strongly detect:
· malicious PDF delivery to endpoints
· Acrobat or Reader process execution
· Acrobat spawning child processes
· privileged Acrobat API abuse
· local staged write-and-execute behavior
· short-window endpoint execution chains
Azure Activity Logs and Entra ID logs capture authentication and resource access events, not application-level execution on user workstations.
Compensating Detection Guidance
Azure should be used in a supporting role rather than as a primary detection layer.
Appropriate uses include:
· centralizing alerts from:
o Microsoft Defender for Endpoint
o Microsoft Defender for Office 365
o sandboxing and detonation systems
· routing alerts through:
o Microsoft Sentinel
o Logic Apps
o automation and response playbooks
· monitoring Azure-hosted workloads where:
o Acrobat or Reader exists on Azure Virtual Machines or Azure Virtual Desktop
o endpoint telemetry from those systems is forwarded into Microsoft Sentinel or another analytics platform
Engineering Note — Azure
For this report, the correct CyberDax approach is to maintain zero selected rules rather than introduce weak or artificial detections.
Azure becomes relevant only if the environment includes:
· Azure Virtual Desktop or VM-based endpoints running Acrobat or Reader
· Microsoft Defender for Endpoint integration
· Microsoft Sentinel used for correlation and orchestration
This preserves detection integrity and aligns with the CyberDax requirement to prioritize strong, deployable detections over completeness.
GCP
GCP is a weak-fit system for CVE-2026-34621 as a primary detection layer because this threat is a client-side Adobe Acrobat or Reader exploitation scenario, not a GCP control-plane or cloud-service-native attack. The critical behaviors occur on endpoints, including malicious PDF execution, JavaScript abuse, and potential staged execution.
GCP-native telemetry sources such as Cloud Audit Logs, Security Command Center, and VPC Flow Logs are designed to capture cloud resource activity, API usage, and network-level events. They do not natively observe endpoint application execution such as Acrobat process behavior unless external telemetry is integrated.
GCP Selected Detection Rule(s)
No strong GCP-native selected rules are recommended for this threat.
GCP Limitation Statement
GCP does not reliably support strong primary detection rules for CVE-2026-34621 without introducing weak signal quality or forcing detections that are not aligned to the threat.
GCP cannot strongly detect:
· malicious PDF delivery to endpoints
· Acrobat or Reader process execution
· Acrobat spawning child processes
· privileged Acrobat API abuse
· local staged write-and-execute behavior
· short-window endpoint execution chains
Cloud Audit Logs capture API activity within GCP services, not application-level execution on user workstations.
Compensating Detection Guidance
GCP should be used in a supporting role rather than as a primary detection layer.
Appropriate uses include:
· centralizing alerts from:
o endpoint detection platforms
o email security systems
o sandboxing tools
· routing alerts through:
o Security Command Center
o Eventarc
o Cloud Functions for automated response
· monitoring GCP-hosted workloads where:
o Acrobat or Reader exists on Compute Engine instances
o endpoint telemetry from those systems is forwarded into a detection platform
Engineering Note — GCP
For this report, the correct CyberDax approach is to maintain zero selected rules rather than introduce weak or artificial detections.
GCP becomes relevant only if the environment includes:
· Compute Engine or virtual desktop environments running Acrobat or Reader
· forwarded endpoint telemetry
· Security Command Center or Eventarc used for orchestration and response
This preserves detection integrity and aligns with the CyberDax requirement to prioritize strong, deployable detections over completeness.
S26 Threat-to-Rule Traceability Matrix
Overview
This section maps each material threat behavior for CVE-2026-34621 to the corresponding S25 detection rules. The objective is to enforce detection accountability, validate real-world coverage, and explicitly identify residual gaps under adversarial conditions.
Coverage Disposition Values
· Detected
· Partially Detected
· Hunt Only
· Not Covered
· Not Applicable
All dispositions reflect validated assessment against telemetry realism, deployability, adversarial bypass potential, and system capability limits.
Threat-to-Rule Traceability Matrix
Behavior 1
Threat Behavior
Malicious PDF delivery and user execution
MITRE ATT&CK Mapping
T1566.001 – Phishing Attachment
Detection Coverage
· YARA Rule 1
· YARA Rule 2
Telemetry Dependencies
· Email security gateway telemetry
· Attachment scanning
· Sandbox or detonation capability
· File-content extraction
Coverage Disposition
Partially Detected
Rationale
Detection depends on successful attachment inspection and extractable PDF or JavaScript content. Adversarial bypass remains possible through heavy obfuscation, alternate delivery channels, or extraction-resistant content.
Behavior 2
Threat Behavior
Acrobat JavaScript execution
MITRE ATT&CK Mapping
T1059.007 – JavaScript
Detection Coverage
· YARA Rule 1
· YARA Rule 2
Telemetry Dependencies
· File scanning
· PDF object extraction
· JavaScript extraction
· Sandbox analysis
Coverage Disposition
Partially Detected
Rationale
JavaScript execution is not inherently malicious. Detection relies on suspicious API usage and identifiable tradecraft. Adversarial bypass remains possible through benign-looking or dynamically constructed scripts.
Behavior 3
Threat Behavior
Privileged Acrobat API abuse
MITRE ATT&CK Mapping
T1106 – Native API
Detection Coverage
· YARA Rule 1
Telemetry Dependencies
· Extracted JavaScript
· Static file-content visibility
· PDF object extraction
Coverage Disposition
Partially Detected
Rationale
Detection depends on visibility of static API strings. Adversarial bypass remains possible through string obfuscation, encoding, or runtime construction.
Behavior 4
Threat Behavior
Execution escape to OS interpreter
MITRE ATT&CK Mapping
T1203 – Exploitation for Client Execution
T1059 – Command and Scripting Interpreter
Detection Coverage
· SentinelOne Rule 1
· Splunk Rule 1
· Elastic Rule 1
· QRadar Rule 1
· Sigma Rule 1
Telemetry Dependencies
· Endpoint process telemetry
· Parent-child process visibility
· Host attribution
· Field normalization where required
Coverage Disposition
Detected
Rationale
This behavior produces strong and consistent telemetry when execution escapes from Acrobat into OS-level interpreters. Detection is reliable across multiple systems but is conditional on observable child-process execution. Adversarial bypass remains possible through fully in-process or indirect execution techniques.
Behavior 5
Threat Behavior
Staged execution from writable directories
MITRE ATT&CK Mapping
T1204 – User Execution
T1059 – Command and Scripting Interpreter
Detection Coverage
· SentinelOne Rule 2
· Splunk Rule 2
· Elastic Rule 2
· QRadar Rule 2
· Sigma Rule 2
Telemetry Dependencies
· File creation telemetry
· Process execution telemetry
· Writable-path visibility
· Host correlation capability
· Time-window correlation fidelity
Coverage Disposition
Partially Detected
Rationale
Detection depends on correct correlation, complete telemetry, and properly tuned time windows. Sequence-based detection is fragile and may fail if telemetry is delayed or incomplete, execution is delayed, or alternate or fileless techniques are used.
Behavior 6
Threat Behavior
Obfuscated JavaScript execution and delayed execution
MITRE ATT&CK Mapping
T1027 – Obfuscated Files or Information
Detection Coverage
· YARA Rule 2
Telemetry Dependencies
· File scanning
· PDF object extraction
· JavaScript extraction
· Sandbox analysis
Coverage Disposition
Partially Detected
Rationale
Obfuscation detection is probabilistic and depends on recognizable tradecraft and recoverable static indicators. Adversarial bypass remains possible through novel encoding or minimal artifact exposure.
Behavior 7
Threat Behavior
Outbound communication or retrieval
MITRE ATT&CK Mapping
T1071 – Application Layer Protocol
Detection Coverage
· No strong S25 rule coverage
Telemetry Dependencies
· Network telemetry
· Proxy logs
· DNS logs
· Destination enrichment
· Allowlisting maturity
Coverage Disposition
Hunt Only
Rationale
No stable, high-confidence rules exist due to variability in infrastructure and communication patterns. Detection requires enrichment, correlation, and analyst-driven hunting.
Behavior 8
Threat Behavior
In-process exploitation without child-process creation
MITRE ATT&CK Mapping
T1203 – Exploitation for Client Execution
Detection Coverage
· None
Telemetry Dependencies
· Memory telemetry
· Exploit detection mechanisms
· Advanced EDR visibility
Coverage Disposition
Not Covered
Rationale
No observable process, file, or network artifacts are produced in this path. This remains an explicit detection gap.
Detection Dependency Reality
All detection coverage for CVE-2026-34621 depends on:
· Endpoint process telemetry
· File visibility for PDF and staged payload analysis
· Correlation capability for multi-event detection
Detection effectiveness degrades significantly if any of these are incomplete or unavailable. No single system provides complete coverage; effective detection requires coordinated visibility across endpoint, file, and correlation layers.
Coverage Validation Summary
Strong detection coverage
· Execution escape to interpreter
Moderate detection coverage
· Staged writable-path execution
· PDF content and JavaScript abuse
· Obfuscation tradecraft
Limited detection coverage
· Malicious PDF delivery
· Outbound communication
Explicit detection gap
· In-process exploit execution without observable artifacts
Coverage Disposition Validation Check
All behaviors mapped to S25 rules were validated against telemetry realism, backend capability, tuning requirements, and adversarial bypass potential. No behavior is marked as Detected where meaningful bypass exists without explicit qualification.
Figure 4
S27 Behavior and Log Artifacts
Overview
This section defines observable artifacts for CVE-2026-34621 mapped to log-level detection signals across endpoint, file, and network telemetry. Artifacts are aligned to realistic field availability in EDR, Sysmon, and SIEM pipelines.
Endpoint Process and Execution Artifacts
Primary Execution Context
· process.parent.name:
o AcroRd32.exe
o Acrobat.exe
· process.name:
o cmd.exe
o powershell.exe
o wscript.exe
o cscript.exe
o rundll32.exe
o mshta.exe
Process Relationship Indicators
· process.parent.name = AcroRd32.exe OR Acrobat.exe
· process.name IN (interpreter list)
Command-Line Indicators (where available)
· process.command_line:
o encoded or obfuscated commands
o inline script execution
o unusual execution flags
Execution Timing Signals
· event.type = process_start immediately following:
o PDF open event
o Acrobat process spawn
Anomalies
· rare parent-child combinations per host baseline
· interpreter execution from document context
· previously unseen execution chains
File and Writable Path Artifacts
File Creation Events
· event.type = file_create OR file_modify
· file.path CONTAINS:
o \Temp\
o \Downloads\
o \AppData\
o \Users\
Execution Events
· process.executable CONTAINS writable path locations
Correlation Signals
· same host.id or hostname
· short time delta between:
o file creation
o process execution
File Indicators
· file.extension:
o exe, dll, js, vbs, ps1, hta
Anomalies
· execution from low-prevalence directories
· unsigned or rare binaries
· newly created file execution
PDF and JavaScript Artifacts
PDF Structure
· raw content contains:
o %PDF-
o /JavaScript
JavaScript Indicators
· app.setTimeOut
· stringFromStream
· streamFromString
· streamDecode
· base64
Privileged API Indicators
· util.readFileIntoStream
· RSS.addFeed
Behavioral Signals
· layered decoding chains
· delayed execution patterns
· obfuscated script structures
Network and Retrieval Artifacts
Network Events
· event.type = network_connection
· network.direction = outbound
Indicators
· unusual user_agent (if available)
· low-prevalence destination.domain
· rare destination.ip
Correlation Signals
· outbound activity shortly after:
o Acrobat execution
o interpreter spawn
Cross-Telemetry Correlation Patterns
High-Confidence Chains
· process.parent.name = Acrobat → process.name = interpreter
· file write → execution from same path
· PDF detection → endpoint execution
Artifact Limitations
· in-process exploitation may not generate process or file logs
· obfuscation may remove static indicators
· delayed execution may break correlation windows
· fileless execution reduces file visibility
Figure 5
S28 Detection Strategy and SOC Implementation Guidance
Overview
Detection strategy prioritizes execution-stage certainty, reinforced by correlation and file-content signals. Strategy is designed for SOC operability, not just detection theory.
Primary Detection Layers
Execution Escape Detection (Tier 1)
Trigger Condition
· Acrobat or Reader spawning interpreter
SOC Action
· Immediate triage
· escalate to incident if:
o no known automation baseline
· consider:
o process termination
o host isolation (after validation)
Staged Execution Detection (Tier 2)
Trigger Condition
· writable path execution OR write → execute correlation
SOC Action
· validate:
o file origin
o signer
o prevalence
· escalate if:
o rare path + new file + execution
· suppress if:
o known installer or update pattern
File Content Detection (Tier 3)
Trigger Condition
· YARA match on PDF or extracted content
SOC Action
· detonate file
· check endpoint exposure
· correlate with:
o email logs
o endpoint execution
Correlation Strategy
Escalate when
· Acrobat execution + interpreter spawn
· PDF detection + endpoint execution
· writable path execution + rarity
Do not escalate when
· isolated writable-path execution with known installer behavior
· known automation workflows
Detection Failure Modes
· in-process exploit path
· delayed execution outside correlation window
· heavy obfuscation removing static indicators
· missing endpoint telemetry
S29 Detection Coverage Summary
Detected Behaviors
· Execution escape to OS interpreter
o strong, low-noise, high-confidence signal
Partially Detected Behaviors
· Staged execution from writable paths
o dependent on correlation fidelity and tuning
· PDF JavaScript abuse
o dependent on extractable content
· Privileged API usage
o dependent on static visibility
· Obfuscation tradecraft
o dependent on recognizable patterns
Hunt Only Behaviors
· Outbound communication
o requires enrichment and correlation
o no stable indicators
Conditional Post-Exploitation Behaviors
· Data staging
· persistence
· lateral movement
Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment.
Not Covered Behaviors
· In-process exploitation without observable artifacts
o no reliable detection signals available
Coverage Integrity Statement
Detection strength is highest at execution escape and degrades across earlier delivery and stealth execution paths due to telemetry and adversarial limitations.
S30 Intelligence Maturity Assessment
Overview
Assessment evaluates detection maturity against realistic adversarial conditions and known detection gaps.
Detection Coverage Maturity
Moderate to high
· strong detection at execution stage
· partial detection for staging and delivery
· explicit blind spot for in-process exploitation
Risk Impact
· attackers can bypass detection by remaining in-process
· early-stage detection remains inconsistent
Telemetry Coverage Maturity
Moderate
· endpoint telemetry is critical dependency
· file visibility varies by environment
· network telemetry provides limited detection value
Risk Impact
· missing endpoint telemetry = detection failure
· poor correlation fidelity reduces detection effectiveness
Detection Engineering Maturity
Moderate to high
· strong rule capability exists
· effectiveness depends on:
o tuning quality
o suppression accuracy
o correlation logic
Risk Impact
· poorly tuned environments produce noise or missed detections
Response Readiness
Moderate
· high-confidence alerts available
· response effectiveness depends on:
o SOC maturity
o automation integration
Risk Impact
· delayed response reduces containment effectiveness
Security Hardening Maturity
Moderate
· patching is primary control
· sandboxing reduces exposure
· endpoint hardening improves resilience
Risk Impact
· unpatched systems remain highly vulnerable
· weak email controls increase exposure probability
Maturity Improvement Priorities
· ensure complete endpoint telemetry coverage
· improve correlation accuracy and timing
· enhance PDF inspection and sandboxing
· reduce reliance on static indicators
· accelerate patch management
Risk Reduction Impact
· reduces probability of successful exploitation
· increases detection likelihood at execution stage
· reduces attacker dwell time
Security Program Integration Note
These improvements align with:
· endpoint detection maturity
· email security effectiveness
· SOC triage and correlation capability
· vulnerability and patch management
S31 Mitigation and Remediation
Containment
· Immediately isolate endpoints with confirmed or suspected compromise following malicious PDF execution.
· Temporarily restrict access to externally sourced PDF files in high-risk workflows until patch deployment is complete.
· Limit outbound network communication from affected systems where compromise is identified.
Validation
· Validate patch deployment across all affected Acrobat and Reader installations, ensuring fixed versions are consistently applied.
· Confirm that no unauthorized system activity persists following PDF execution events on affected endpoints.
· Review recent document delivery channels, including email, web, chat, and shared storage, to identify potential exposure.
Eradication
· Remove malicious PDF files from endpoints, email systems, and shared storage repositories.
· Terminate unauthorized processes resulting from exploit execution where compromise is identified.
· Reimage or restore affected systems where exploit impact cannot be confidently contained.
Recovery
· Restore systems to a trusted operational state following patch validation and removal of malicious artifacts.
· Reinstate document workflows after confirming control effectiveness and system integrity.
· Monitor for re-exploitation attempts in environments with continued exposure to external document sources.
S32 Security Control Recommendations
Artifact Integrity Control
· Enforce inspection of externally sourced PDF files prior to user access to reduce exposure to active exploitation, focusing on detecting malicious embedded content and exploit-triggering structures within Acrobat-compatible PDF files.
· Apply attachment filtering policies specific to PDF files delivered through email and external communication channels to limit exploitation opportunities.
Dependency Governance Control
· Maintain real-time visibility into Acrobat and Reader versions across all endpoints.
· Enforce immediate patch deployment for document-processing applications exposed to external content, prioritizing emergency advisories associated with active exploitation.
CI/CD Execution Control
· Validate that internal document generation and distribution systems cannot introduce or propagate untrusted PDF content.
· Enforce integrity validation for internally generated PDFs before distribution to users.
Credential Security Control
· Enforce least-privilege access models to limit the impact of user-context execution following exploit activity.
· Monitor for abnormal credential usage following execution originating from document-based workflows.
Access and Release Infrastructure Control
· Restrict distribution of externally sourced PDF files through shared storage and collaboration platforms to reduce active exploitation pathways.
· Apply access controls and validation mechanisms to document repositories handling untrusted content.
S33 Strategic Defensive Improvement
Control Impact Mapping
· Artifact inspection controls reduce likelihood of successful malicious document delivery during active exploitation.
· Patch governance removes the vulnerable execution condition currently being targeted in the wild.
· Endpoint monitoring of trusted application execution improves visibility after transition into the user environment where exploitation becomes observable.
· Network controls limit the ability for attacker-controlled activity to extend beyond initial execution.
Strategic Improvement
· Prioritize detection strategies focused on execution transitions from trusted applications into the user environment under active exploitation conditions.
· Expand visibility into application-layer execution behavior for high-risk user applications such as document processors.
· Strengthen correlation across document delivery, endpoint execution, and network activity to identify active exploitation patterns.
· Establish rapid patch response processes for widely deployed applications exposed to external content.
S34 Defensive Architecture Overview
Figure 6
Upstream Integrity Layer
· Email, web, and collaboration platform controls to reduce delivery of malicious PDF files during active exploitation campaigns.
· Pre-access inspection of externally sourced documents to identify malicious content before user interaction.
Pipeline Execution Layer
· Monitoring of trusted application execution, specifically Acrobat and Reader processes, to identify execution transitions from Acrobat or Reader processes into the broader user environment.
· Controls limiting execution from document-triggered contexts into broader user environment operations.
Monitoring and Response Layer
· Correlation of endpoint, network, and document delivery telemetry to identify active multi-stage exploitation behavior.
· Centralized alerting for activity following PDF execution events.
· Rapid response capability to isolate endpoints and contain exploitation attempts.
S35 Security Hardening Guidance
· Enforce immediate updates for Adobe Acrobat and Reader across all endpoints.
· Restrict execution capabilities of document-processing applications where operationally feasible.
· Limit user execution of content from untrusted or externally sourced locations.
· Disable non-essential features within Acrobat and Reader that expand attack surface.
· Strengthen visibility into application execution behavior and process relationships.
S36 Security Program Maturity Assessment
Current Maturity State
· Many organizations rely on post-execution detection approaches that are insufficient against threats currently exploiting trusted applications in the wild.
Risk Alignment
· Existing detection models are not fully aligned with threats that exploit trusted applications and delay observable behavior under active exploitation conditions.
Maturity Improvement Priorities
· Expand endpoint telemetry coverage to improve visibility into application-layer execution.
· Implement behavior-based detection focused on execution transitions into the user environment.
· Improve integration between email, endpoint, and network telemetry sources.
· Establish rapid patch deployment processes for critical user-facing applications.
Figure 7
S37 Residual Risk and Forward Outlook
Residual risk remains due to continued reliance on document-based workflows and trusted application execution. Even with patching and improved controls, similar vulnerabilities or exploit variants may be developed to target widely deployed document-processing applications.
Confirmed active exploitation indicates that this attack method is operationally viable and likely to be reused or adapted in future campaigns. Organizations should prioritize sustained improvements in behavioral detection, application control, and cross-telemetry visibility to reduce long-term exposure.
S38 Intelligence Confidence Assessment
Overall Confidence Level
High for initial access and execution behavior; moderate for full attack lifecycle and post-exploitation activity. Adobe confirmed active exploitation and released APSB26-43 on April 11, 2026, while the EXPMON public research provides concrete technical detail on exploit behavior inside Adobe Reader.
Source Reliability
High reliability based on Adobe’s official security update record and the publicly available EXPMON technical analysis documenting privileged Acrobat API abuse, local file access, remote server interaction, and staged JavaScript delivery behavior.
Analytical Confidence Drivers
· Vendor-confirmed active exploitation in the wild.
· Official Adobe Priority 1 emergency security update for Acrobat and Reader.
· Public technical analysis showing privileged API abuse, local file access, remote communication, and staged follow-on JavaScript execution behavior.
· Clear exploit vector involving malicious PDF delivery and user interaction.
· Strong alignment between the observed exploit behavior and the report’s execution-transition detection model.
Confidence Limitations
· The full exploit chain remains only partially characterized despite the public technical analysis. EXPMON confirmed the initial exploit, privileged API abuse, data collection, and remote code delivery capability, but did not obtain the final attacker-delivered RCE or sandbox-escape payload from the live server.
· Public reporting remains limited regarding confirmed post-exploitation behavior beyond initial execution and staging.
· Attribution, infrastructure breadth, and campaign targeting specificity remain incomplete.
Intelligence Gaps
· Full exploit chain behavior within Acrobat prior to execution transition.
· Confirmed use of persistence, privilege escalation, or lateral movement techniques.
· Specific threat actor attribution and broader campaign infrastructure.
· Indicators associated with large-scale exploitation activity beyond the publicly documented infrastructure and variants.
S39 Analytical Notes and Limitations
· This analysis is based on Adobe’s confirmed exploitation statement and currently available public technical reporting.
· The EXPMON research materially improves visibility into exploit behavior, including privileged API abuse, local file access, remote JavaScript retrieval, and conditional follow-on delivery logic, but does not fully resolve final payload behavior in the observed campaign.
· In-application exploit execution still limits direct observation of early-stage activity inside the Acrobat process.
· Findings may evolve as additional vendor, researcher, or campaign reporting becomes available.
S40 References
Vendor Advisory
Adobe Security Update Record — Security update available for Adobe Acrobat and Reader | APSB26-43
· hxxps://helpx.adobe[.]com/security/products/acrobat.html
Vulnerability Records
CVE Record — CVE-2026-34621 vulnerability details
· hxxps://nvd.nist[.]gov/vuln/detail/CVE-2026-34621
Known Exploited Vulnerabilities (KEV)
CISA Known Exploited Vulnerabilities Catalog — CVE-2026-34621 status (not currently listed)
· hxxps://www.cisa[.]gov/known-exploited-vulnerabilities-catalog
Security Vendor Analysis
EXPMON Research — EXPMON detected sophisticated zero-day fingerprinting attack targeting Adobe Reader users
· hxxps://justhaifei1.blogspot[.]com/2026/04/expmon-detected-sophisticated-zero-day-adobe-reader.html?m=1
Analytical Framework
MITRE ATT&CK Framework — Enterprise Matrix
· hxxps://attack.mitre[.]org