[EXP] Microsoft April 2026 Zero-Day Exploitation Risk Analysis
Report Type
CVE
Threat Category
Client-Side Exploitation
Assessment Date
April 14, 2026
Primary Impact Domain
Endpoint Compromise
Secondary Impact Domains
· Data Exposure
· Credential Access
· Initial Access Enablement
· Potential Lateral Movement
Affected Asset Class
User Workstations (Windows and macOS endpoints running Adobe Acrobat/Reader)
Threat Objective Classification
Initial Access and Execution via Document-Based Exploitation
BLUF
Organizations face immediate enterprise risk from active exploitation of Microsoft SharePoint (CVE-2026-32201) and a second network-accessible zero-day (CVE-2026-33825), enabling attackers to achieve remote execution on exposed systems and pivot into internal environments. The technical risk is driven by improper input validation and externally reachable service execution paths that allow adversaries to transition directly from internet-facing services into command execution and persistence mechanisms. Active exploitation confirmed through KEV inclusion for CVE-2026-32201 significantly increases breach likelihood, while CVE-2026-33825 presents a parallel exploitation trajectory due to similar exposure characteristics. Executive action is required to execute immediate patching or compensating controls, restrict exposure of internet-facing services, and validate post-exploitation detection coverage at the endpoint and SIEM layer.
Executive Risk Translation
Active exploitation of externally exposed Microsoft services creates a high-probability breach pathway where detection occurs after compromise begins, increasing operational disruption risk, regulatory exposure, and financial impact.
S3 — Why This Matters Now
· CISA has confirmed active exploitation for CVE-2026-32201, shifting this threat from theoretical to operational reality.
· CVE-2026-33825 shares a network attack vector, no authentication requirement, and exposure through externally reachable services.
· These conditions enable rapid attacker weaponization, automated internet-wide scanning, and large-scale opportunistic exploitation.
· Attackers are actively prioritizing KEV-listed vulnerabilities and deploying exploitation frameworks within hours to days of disclosure.
· Initial exploitation remains inherently unreliable to detect, requiring dependence on post-exploitation detection models.
· Time-to-compromise can occur within minutes to hours, while time-to-detect depends on telemetry maturity and correlation capability.
S4 — Key Judgments
· CVE-2026-32201 exploitation will persist at scale due to KEV-confirmed status and high-value SharePoint targeting.
· CVE-2026-33825 is likely to follow a similar rapid weaponization and automation curve.
· Initial access detection will remain partially detectable and dependent on downstream behavioral correlation.
· Post-exploitation detection is strong when endpoint and SIEM telemetry are present and validated.
· Organizations lacking process lineage visibility, command-line telemetry, and correlation capability are unlikely to reliably detect compromise.
· Defenders operate on patch cycles measured in days while attackers operate on exploitation cycles measured in hours.
S5 — Executive Risk Summary
Business Risk
· High probability of enterprise compromise through internet-facing services.
· Risk of data exposure, operational disruption, and unauthorized internal access.
· Increased likelihood of ransomware enablement or persistent access operations.
Technical Cause
· Improper input validation enabling remote code execution.
· Network-accessible service exposure without authentication requirements.
· Direct transition from externally supplied input into execution context.
Threat Posture
· CVE-2026-32201 is actively exploited and confirmed in KEV.
· CVE-2026-33825 presents a high-probability exploitation trajectory.
· Detection posture is weak at initial access and stronger post-exploitation.
Executive Decision Requirement
· Execute immediate patching or compensating controls.
· Validate endpoint and SIEM detection coverage.
· Restrict exposure of internet-facing services.
S6 — Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
· Low Impact Scenario
Estimated cost range: $100,000 to $300,000
Limited compromise of a small number of externally exposed systems with rapid containment and no confirmed lateral movement. Costs driven by incident response, patching, validation, and short-duration operational disruption.
· Moderate Impact Scenario
Estimated cost range: $400,000 to $1,500,000
Compromise of externally exposed services with internal reconnaissance and limited lateral movement, including access to collaboration platforms and internal data stores. Costs include forensic investigation, containment, system restoration, operational disruption, and compliance review.
· High Impact Scenario
Estimated cost range: $2,000,000 to $7,500,000
Enterprise-scale compromise initiated through exposed services leading to persistent access, widespread lateral movement, and potential data exfiltration or ransomware enablement. Costs include full incident response, extended business disruption, enterprise remediation, regulatory exposure, and reputational impact.
S6A — Key Cost Drivers
· Exposure of internet-facing services
· Time-to-detect after compromise
· Detection and containment capability
· Lateral movement extent
· Data accessibility and sensitivity
· Regulatory obligations
S6B — Compliance and Risk Context
Compliance Exposure Indicator
High exposure due to confirmed exploitation of a KEV-listed vulnerability.
Risk Register Entry
Risk Title
Active exploitation of Microsoft vulnerabilities enabling remote enterprise compromise
Risk Description
Externally exposed Microsoft services allow remote code execution leading to unauthorized access and persistence
Likelihood
High
Impact
High
Risk Rating
Critical
Annualized Risk Exposure
Elevated due to active exploitation, exposed attack surface, and repeatable attack patterns.
S7 — Risk Drivers
· Internet exposure of vulnerable services
· Delayed patching
· KEV-driven attacker prioritization
· Lack of endpoint telemetry
· Detection delay
S8 — Bottom Line for Executives
This is an active exploitation scenario where detection occurs after compromise begins. Organizations without validated endpoint and SIEM telemetry face a significantly higher probability of undetected breach.
S9 — Board-Level Takeaway
The organization faces a high-probability intrusion risk driven by actively exploited vulnerabilities affecting internet-facing systems, requiring immediate remediation and detection validation.
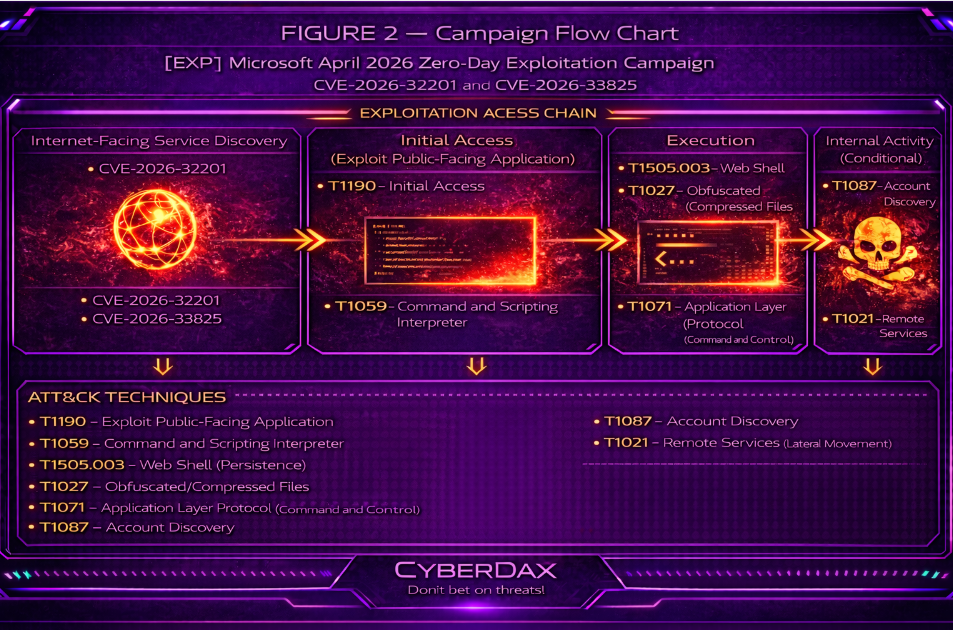
Figure 2
S10 — Threat Overview
This threat represents an active exploitation scenario targeting externally exposed Microsoft services, anchored by confirmed exploitation of CVE-2026-32201 and reinforced by a parallel network-exposed vulnerability (CVE-2026-33825) with equivalent access characteristics. The threat enables remote code execution against internet-facing systems, allowing attackers to transition directly from external input handling into service-origin execution, persistence, and internal network activity. Exploitation is scalable due to lack of authentication requirements and widespread exposure of affected services. Detection is not reliable at the exploitation stage and depends on identifying post-exploitation behavior.
S11 — Threat Classification and Type
Threat Type
Exploitation of public-facing applications
Threat Sub-Type
Remote code execution against externally exposed enterprise services
Operational Classification
Active exploitation activity with confirmed KEV involvement and parallel exploitation pathway
Primary Function
Initial access and execution enablement leading to persistence, lateral movement, and follow-on operational activity
S12 — Campaign or Activity Overview
This activity reflects a live exploitation pattern targeting externally exposed Microsoft infrastructure, with CVE-2026-32201 confirmed as actively exploited and CVE-2026-33825 presenting a concurrent exposure condition. Attackers identify vulnerable systems through automated scanning and initiate exploitation immediately upon discovery. Successful exploitation results in execution within service process context, enabling command execution, payload staging, or persistence mechanisms without requiring user interaction. The activity is defined by rapid exploitation cycles and repeatable execution pathways that consistently transition from external access to post-exploitation control.
S13 — Targets and Exposure Surface
The threat targets systems that are externally accessible and capable of processing attacker-supplied input within application or service contexts. Exposure is binary: internet-facing vulnerable systems are targetable, while non-exposed systems are not susceptible to this initial access vector. The highest-risk assets are SharePoint servers and similar Microsoft services operating in exposed configurations. Risk increases in environments lacking segmentation, timely patching, or service hardening. Detection capability is dependent on endpoint telemetry and process visibility; environments without these controls are unlikely to detect post-exploitation activity.
S14 — Sectors / Countries Affected
Sectors Affected
Any sector operating internet-facing Microsoft services is exposed to this threat, with elevated risk in environments dependent on externally accessible collaboration platforms or centralized data services.
· Government
· Healthcare
· Financial Services
· Enterprise Technology
· Critical Infrastructure
· Large Commercial Enterprises
Countries Affected
Global
S15 — Adversary Capability Profiling
Capability Level
Moderate to high, accessible to both opportunistic and structured threat actors
Technical Sophistication
Moderate, leveraging known exploitation techniques and automation
Infrastructure Maturity
Moderate to high, supported by automated scanning and exploitation frameworks
Operational Scale
High, enabling repeated exploitation across large numbers of exposed systems
Escalation Likelihood
High, with strong probability of progression to persistence, lateral movement, and follow-on activity
S16 — Targeting Probability Assessment
Overall Targeting Probability
High
Targeting Drivers
Confirmed KEV exploitation, network accessibility, lack of authentication requirements, and widespread exposure of vulnerable services enable automated discovery and exploitation at scale. Reliable post-exploitation execution pathways further increase attacker efficiency and success rates.
Most Likely Targets
Organizations operating exposed SharePoint or similar Microsoft services, environments with delayed patching cycles, enterprises lacking endpoint telemetry and process visibility, and organizations with large or unsegmented external attack surfaces
S17 — MITRE ATT&CK Chain Flow Mapping
Initial Access
T1190 – Exploit Public-Facing Application
Execution
T1059 – Command and Scripting Interpreter
Persistence
T1505.003 – Server Software Component: Web Shell
Privilege Escalation
T1068 – Exploitation for Privilege Escalation
Defense Evasion
T1027 – Obfuscated/Compressed Files and Information
Command and Control
T1071 – Application Layer Protocol
Discovery
T1087 – Account Discovery
Lateral Movement
T1021 – Remote Services
S18 — Attack Path Narrative (Signal-Aligned Execution Flow)
The attack begins when externally exposed Microsoft services process attacker-supplied input through vulnerable application components. Upon successful exploitation, execution transitions directly into the service context, creating an immediate shift from external interaction to internally controlled execution. This transition represents the first reliable detection point, as the exploit itself may generate minimal observable evidence.
Following this transition, attacker activity becomes visible through deviations in service-linked process behavior, including abnormal command execution and unexpected process lineage. These signals indicate that control has moved from external input handling to internal execution within the application environment.
As access stabilizes, attackers interact with the system to determine context, access scope, and reachable resources. These interactions generate observable signals through command activity and system queries rather than through the exploit mechanism itself.
Where conditions permit, the compromised system may be used to extend access beyond the initial host or maintain continued control. Throughout the attack path, detection depends on identifying shifts in behavior and execution patterns originating from service processes rather than identifying the initial exploitation event.
S19 — Attack Chain Risk Amplification Summary
Risk in this attack chain is driven by the combination of external exposure and low-friction execution following successful exploitation. Because vulnerable services are directly accessible, attackers can operate at scale and initiate compromise without requiring authentication or user interaction.
Execution within trusted service contexts significantly increases risk by reducing early visibility. Malicious activity inherits characteristics of legitimate service behavior, allowing initial attacker actions to blend into expected system operations and delaying detection.
The gap between rapid attacker execution and delayed defender visibility further amplifies risk. Attackers can establish control and begin internal interaction before sufficient signals are generated for high-confidence detection, particularly in environments lacking strong process-level telemetry.
Organizational conditions such as large external attack surfaces, delayed remediation, and limited monitoring increase the likelihood that exploitation leads to broader compromise. This makes the attack chain highly efficient and repeatable across similarly exposed environments.
Figure 3
S20 — Tactics, Techniques, and Procedures
Initial access is achieved through T1190 – Exploit Public-Facing Application, allowing remote code execution against externally exposed Microsoft services without authentication. The defining characteristic is the immediate transition from exploitation to controlled execution within the service environment.
Execution behavior aligns with T1059 – Command and Scripting Interpreter and, where applicable, T1218 – System Binary Proxy Execution. This includes service-context command execution and controlled payload staging, often using trusted execution paths to reduce detection visibility.
Persistence techniques are consistent with T1505.003 – Server Software Component: Web Shell or similar service-level access mechanisms. These approaches allow attackers to retain access within the application environment without repeatedly invoking the exploit path.
Defense evasion is achieved through T1027 – Obfuscated/Compressed Files and Information and T1140 – Deobfuscate/Decode Files or Information. Attackers rely on encoded commands and staged execution to limit detection through logging and inspection controls.
Post-exploitation activity includes T1087 – Account Discovery and T1033 – System Owner/User Discovery to identify access scope and system context. Where expansion is viable, T1021 – Remote Services enables movement across systems using available credentials or administrative access.
Command and control behavior aligns with T1071 – Application Layer Protocol, allowing outbound communication to blend with legitimate traffic patterns and maintain operational access with minimal visibility.
S20A — Adversary Tradecraft Summary
This tradecraft is defined by efficient exploitation of exposed services combined with controlled execution inside trusted environments. Attackers rely on direct transitions from exposure to execution, minimizing reliance on complex intrusion steps or user interaction.
The approach emphasizes scalability and consistency. Automated discovery and exploitation enable broad targeting, while standardized post-exploitation behaviors allow reliable operation across different environments with similar exposure profiles.
Operationally, the objective is to establish and maintain access within enterprise systems with minimal detection during early stages. Success is driven less by the exploit itself and more by the attacker’s ability to operate within service contexts where early activity is difficult to distinguish from normal behavior.
S21 — Detection Strategy Overview
Detection Philosophy
Detection is anchored on post-exploitation behavioral evidence originating from externally exposed service processes, not exploit delivery mechanisms. Primary detection focuses on service-origin execution from network-exposed or externally reachable processes, execution-to-outbound communication correlation, and process lineage deviation from expected service behavior.
Inbound exploit visibility must not be treated as a required detection dependency and may be used only as optional enrichment where available.
Primary Detection Anchors
· Service-origin execution from exposed attack surface
· Execution-to-outbound communication correlation
· Process lineage deviation
Detection Prioritization Model
· Tier 1 (Primary Detection — Must Build Around)
o Service-origin execution from exposed processes
o Execution-to-outbound communication correlation
· Tier 2 (Supporting Detection — Correlation Enhancers)
o Injection behavior
o Privilege context anomalies
· Tier 3 (Enrichment / Hunt — Not Standalone)
o Crash and fault signals
o Network anomaly indicators
Correlation Strategy (Strict Enforcement)
The following detections are correlation-required and must not be deployed as standalone alerts:
· Network-to-execution transition
· Execution-to-outbound communication correlation
· Multi-stage exploit chain detection
The following detections may operate as standalone with strict constraints:
· Service-origin execution from externally exposed processes
· Process lineage deviation
All correlation must operate on raw telemetry only, enforce temporal sequencing between events, and remain valid even when inbound telemetry is unavailable.
Telemetry Prioritization
· Primary
o Endpoint and EDR telemetry
· Secondary
o DNS and web proxy telemetry
· Not applicable for initial access
o Email security telemetry
Detection Design Constraints
Detection must not rely on known IOCs, signature-based detection, or inbound exploit visibility as a prerequisite.
All detections must be behavior-driven, variant-resilient, and expressible as raw telemetry to logic to output.
Correlation-first detections must explicitly define required signal combinations and must not be deployed as standalone alerting logic.
Baseline and Deployment Requirements
Detection logic requiring anomaly or deviation analysis must be deployed only after baseline behavior validation.
Baseline requirements must define expected service behavior, allowed parent-child relationships, and normal network communication patterns.
Failure to establish baseline invalidates standalone deployment of anomaly-based detections.
Variant Resilience Requirements
Detection logic must remain effective under the following conditions:
· No child process creation
· Fully in-memory execution
· Delayed or staged execution
· Use of trusted or benign infrastructure for outbound communication
Where resilience cannot be achieved, compensating correlation must be defined.
Operational Detection Model
· High-confidence detections
o Service-origin execution from exposed processes
o Execution-to-outbound communication correlation
· Medium-confidence detections
o Injection behavior
o Privilege context anomalies
· Hunt or contextual detections (not alert-capable standalone)
o Crash and fault correlation
o Network anomaly signals
Explicit Non-Deployment Guardrails
Do not deploy:
· Crash-only detection as alerting logic
· Network anomaly-only detection as standalone alerts
· Inbound exploit detection as a primary detection strategy
Do not rely on:
· Reputation-based indicators alone
· Single-event anomalies without behavioral context
S22 — Primary Detection Signals
Primary Detection Signals
· Execution occurring within externally exposed or service-facing processes that do not normally execute arbitrary code
· Child process creation originating from service or externally exposed processes
· Parent-child process relationships inconsistent with established service behavior
· Outbound network connections initiated by processes not previously observed initiating external communication
· Outbound network activity originating from processes with no established network communication role
Supporting Detection Signals
· Execution from dynamically allocated memory regions
· Memory regions marked as executable outside of standard module loading behavior
· Thread execution originating from non-module-backed memory regions
· Cross-process memory interaction including remote thread creation
· Memory modification activity targeting another process
· Execution activity without corresponding file creation events
· Privileged execution occurring within processes not typically associated with elevated operations
Exploit Attempt and Instability Signals
· Application crash events associated with service or externally exposed processes
· Service restart events without corresponding administrative action
· Access violation or exception fault events within processes handling external input
· Abnormal process termination events for externally exposed services
· Repeated abnormal request handling outcomes resulting in failed processing
Outbound Communication Signals
· New outbound network connections to previously unseen external destinations
· DNS queries for domains not previously observed in the environment
· Outbound communication patterns inconsistent with the baseline behavior of the originating process
· Periodic or repetitive outbound connection behavior
Persistence and Post-Exploitation Signals (Conditional)
· Creation of autorun registry entries
· Modification of existing autorun registry entries
· Creation of scheduled tasks
· Modification of scheduled tasks
· Creation of new service configurations
· Modification of existing service configurations
· File creation within system startup or execution directories
Lateral Movement and Expansion Signals (Conditional)
· Memory access to authentication-related processes
· Token manipulation or duplication activity
· Authentication attempts inconsistent with system role
· Internal network connection attempts across multiple hosts
· Enumeration of internal services or resources
· Use of remote administrative protocols inconsistent with baseline behavior
Signal Usage Constraints
· Crash and fault events may occur in benign conditions and require contextual validation
· Network anomalies may occur in legitimate operational scenarios and require baseline comparison
· Execution signals must be evaluated relative to expected process behavior and role
· Outbound communication patterns must be interpreted in the context of established environment baselines
S23 — Telemetry Requirements
Endpoint and Process Execution Telemetry
· Process creation events capturing executable name and parent process
· Process termination events
· Parent-child process relationship tracking
· Process execution context including user identity
· Process execution context including privilege level
Memory and Execution Telemetry
· Memory allocation events indicating creation of executable memory regions
· Memory protection changes indicating transition to executable permissions
· Thread creation events within processes
· Thread start address visibility where available
· Cross-process memory access events
· Remote thread creation events
Crash and Fault Telemetry
· Application crash event logs
· Service termination events
· Service restart events
· Access violation and exception fault logs
· Abnormal process termination records
File and Persistence Telemetry
· File creation events in system and execution directories
· File modification events in persistence-relevant paths
· Registry key creation events
· Registry key modification events
· Scheduled task creation events
· Scheduled task modification events
· Service creation events
· Service configuration modification events
Network and Outbound Communication Telemetry
· Outbound connection logs including source host and destination
· Network flow records capturing connection frequency and timing
· DNS query logs capturing domain resolution
· Destination IP address logging
· Destination port logging
· Internal network connection logs between hosts
· Remote protocol usage logs including SMB, RDP, and management protocols
Web and Application Telemetry (Conditional Availability)
· Web server request logs capturing request handling outcomes
· Application error logs capturing exceptions and processing faults
· Session handling logs capturing incomplete or failed transactions
· Request pattern logs capturing repeated abnormal or malformed requests
Telemetry Availability Requirements
· Endpoint telemetry is required for:
o Process visibility
o Memory visibility
o Privilege context visibility
· Network telemetry is required for:
o Outbound communication visibility
o Domain resolution visibility
· Web and application telemetry is:
o Environment-dependent
o Not guaranteed across deployments
Telemetry Limitations and Gaps
· Lack of endpoint telemetry prevents visibility into execution and injection behavior
· Absence of DNS telemetry limits detection of anomalous domain communication
· Absence of process attribution in network telemetry reduces detection precision
· Limited or disabled application logging reduces visibility into exploit attempts
· Reduced logging retention impacts detection across all telemetry categories
Figure 4
S24 — Detection Opportunities and Gaps
Detected Behaviors
· Service-origin process execution from externally exposed processes
o Coverage is achieved through process creation telemetry and parent-child relationship tracking
o Detection is reliable only when baseline service behavior is defined and validated
o Detection may degrade in environments without established service execution baselines
· Execution-origin outbound communication from compromised processes
o Coverage is achieved through outbound connection telemetry and DNS query logging
o Detection requires process-level network attribution to maintain reliability
o Detection strength is reduced when process attribution is unavailable
Partially Detected Behaviors
· Process injection and memory-based execution
o Coverage depends on availability of memory telemetry and EDR capability
o Detection may be incomplete in environments lacking detailed memory visibility
o Variants using in-process execution without injection reduce detection fidelity
· Privilege context abuse and escalation
o Coverage depends on availability of security event logs and privilege tracking
o Detection may be partial when privilege changes occur within expected service contexts
o Detection reliability varies based on audit policy configuration
· Outbound communication using trusted or common infrastructure
o Coverage depends on baseline deviation detection rather than reputation
o Detection is reduced when attackers use commonly observed domains or services
o Behavioral analysis is required to differentiate malicious activity
Hunt Only Behaviors
· Exploit attempt indicators including crashes and fault conditions
o Signals include application crashes, service restarts, and exception faults
o High likelihood of benign occurrence requires contextual investigation
o These signals are not suitable for standalone alerting
· Network-level exploit delivery patterns
o Includes malformed requests and abnormal request handling behavior
o Detection depends on availability of web and application logging
o These signals are not suitable as primary or standalone detection mechanisms
Not Covered Behaviors
· Exploit delivery without observable side effects
o No reliable detection when exploit execution produces no crash, fault, or behavioral deviation
· Fully in-memory execution without observable behavioral deviation
o No reliable detection when execution remains entirely within normal process behavior
· Delayed or staged payload execution outside correlation windows
o Detection may fail when execution occurs significantly later than exploit delivery
· Outbound communication using fully trusted and baseline-consistent infrastructure
o No reliable detection when communication fully matches expected process behavior
Telemetry Dependency Summary
· Reliable detection requires:
o Endpoint process telemetry
o Process lineage visibility
o Outbound network telemetry with process attribution
· Detection is degraded when:
o Memory telemetry is limited
o DNS visibility is absent
o Application logging is incomplete
Coverage Integrity Statement
· Detection coverage is strongest for post-exploitation behavioral activity
· Detection coverage is reduced for exploit delivery and pre-execution stages
· Detection reliability depends on baseline establishment and telemetry availability
· No assumption is made that all exploit activity will produce observable signals
S25 Ultra-Tuned Detection Engineering Rules
Suricata
Rule Title
CVE-2026-32201 repeated external POST delivery behavior to sensitive SharePoint application paths
Purpose
Detect repeated suspicious external POST requests to sensitive SharePoint application paths that may indicate exploit-attempt delivery behavior associated with CVE-2026-32201 against internet-exposed SharePoint infrastructure. This rule provides perimeter-stage visibility into repeated exploit delivery attempts.
SOC Usage Mode
Correlation-first. Triage and enrichment. Not approved for standalone compromise alerting.
Minimum Deployment Requirement
Internet-exposed SharePoint servers must be within monitored network scope. HTTP inspection must be enabled. TLS decryption is required where traffic is encrypted and otherwise opaque. HOME_NET must accurately scope SharePoint assets. Deployment must occur where original URI visibility is preserved.
Enforcement Method
POST-method scoping, sensitive SharePoint path scoping, request-body size restriction, and short-window source repetition thresholding are used to suppress low-volume benign activity while identifying repeated exploit-attempt delivery behavior.
Implementation Constraint Notes
This rule detects exploit-attempt delivery behavior only. It does not confirm exploit success, authentication bypass, remote code execution, or post-exploitation activity. Legitimate SharePoint integrations or automation may require allowlisting or threshold tuning. Reverse proxy or WAF deployments must preserve original request visibility.
Variant Coverage
Covers repeated exploit-attempt delivery behavior against common sensitive SharePoint application paths without relying on a fixed payload signature. Does not cover single low-frequency attempts, alternate unscoped paths, encrypted traffic without inspection, or post-exploitation activity.
Engineering Note
Validate normal external SharePoint traffic patterns, confirm URI visibility, and tune thresholds prior to production deployment. Coverage remains conditional until environment-specific validation is completed.
Production Ready
Conditional. Deployment-ready template pending tenant-specific validation and tuning.
Rule Regret Check
Deployment caution
Legitimate external integrations or automation workflows may generate similar POST patterns and require tuning.
Confidence caution
Detects exploit-attempt delivery behavior but does not confirm compromise.
Coverage value
Provides strong perimeter visibility into repeated exploit delivery attempts against exposed SharePoint services when correlated with endpoint or service-level signals.
Detection Logic
alert http $EXTERNAL_NET any -> $HOME_NET $HTTP_PORTS (
msg:"CYBERDAX [EXP] CVE-2026-32201 repeated external POST delivery to sensitive SharePoint application paths";
flow:to_server,established;
http.method;
content:"POST";
http.uri;
pcre:"/^\/(?:_layouts\/15\/|_vti_bin\/)/U";
http.request_body;
bsize:>1500;
detection_filter:track by_src,count 4,seconds 120;
classtype:web-application-attack;
sid:2501001;
rev:4;
)
Rule Title
CVE-2026-32201 repeated abnormal SharePoint request handling with server error responses
Purpose
Detect repeated suspicious external requests to sensitive SharePoint application paths that result in abnormal server-side error responses consistent with exploit-attempt behavior or failed request processing.
SOC Usage Mode
Correlation-first. Triage and enrichment. Not approved for standalone compromise alerting.
Minimum Deployment Requirement
Internet-exposed SharePoint servers must be within monitored network scope. HTTP inspection must be enabled. Response visibility must be available to the Suricata sensor. TLS decryption is required where traffic is encrypted. Request and response inspection must occur on the same sensor path.
Enforcement Method
Sensitive SharePoint path scoping is combined with server error response detection and repetition thresholding to identify repeated abnormal request-processing behavior.
Implementation Constraint Notes
This rule detects repeated abnormal request handling only. It does not confirm exploitation or compromise. Legitimate application errors or misconfigured integrations may generate similar patterns and require tuning. Requires reliable request-response visibility on the same inspection path.
Variant Coverage
Covers exploit attempts that trigger repeated abnormal processing or server errors without relying on specific payload content. Does not cover successful low-noise exploitation or encrypted traffic without inspection.
Engineering Note
Validate baseline SharePoint response behavior and ensure request-response continuity is preserved in the monitoring path. Tune error thresholds based on environment-specific behavior.
Production Ready
Conditional. Deployment-ready template pending tenant-specific validation and tuning.
Rule Regret Check
Deployment caution
Application errors from legitimate workflows may trigger repeated server error responses.
Confidence caution
Detects abnormal processing behavior but does not confirm exploitation or execution.
Coverage value
Provides visibility into exploit-attempt instability and strengthens detection when correlated with service faults or endpoint activity.
Detection Logic
alert http $EXTERNAL_NET any -> $HOME_NET $HTTP_PORTS (
msg:"CYBERDAX [EXP] CVE-2026-32201 SharePoint sensitive-path request marker";
flow:to_server,established;
http.uri;
pcre:"/^\/(?:_layouts\/15\/|_vti_bin\/)/U";
flowbits:set,cdx_sp_sensitive_req;
flowbits:noalert;
sid:2501002;
rev:4;
)
alert http $HOME_NET $HTTP_PORTS -> $EXTERNAL_NET any (
msg:"CYBERDAX [EXP] CVE-2026-32201 repeated abnormal SharePoint request handling with server error responses";
flow:to_client,established;
flowbits:isset,cdx_sp_sensitive_req;
http.stat_code;
pcre:"/^(500|502|503|504)$/";
detection_filter:track by_dst,count 4,seconds 120;
classtype:web-application-attack;
sid:2501003;
rev:4;
)
Rule Title
CVE-2026-32201 suspicious external retry and targeting burst to sensitive SharePoint application paths
Purpose
Detect aggressive retry or targeting behavior from a single external source against sensitive SharePoint application paths in a short time window, indicating probing or exploit-attempt concentration.
SOC Usage Mode
Correlation-first. Triage and enrichment. Not approved for standalone compromise alerting.
Minimum Deployment Requirement
Internet-exposed SharePoint servers must be within monitored network scope. HTTP inspection must be enabled. TLS decryption is required where traffic is encrypted. HOME_NET must accurately scope SharePoint assets.
Enforcement Method
Sensitive SharePoint path scoping combined with short-window source burst thresholding is used to identify repeated targeting behavior independent of payload size or response outcome.
Implementation Constraint Notes
This rule detects targeting and retry behavior only. It may overlap with benign scanning, monitoring, or integration activity and requires tuning. Should be correlated with abnormal responses or endpoint signals before escalation.
Variant Coverage
Covers repeated probing or retry behavior across sensitive SharePoint application paths without relying on payload signatures. Does not cover single low-frequency attempts or encrypted traffic without inspection.
Engineering Note
Validate legitimate burst traffic patterns and adjust thresholds to minimize noise. Review overlap with Rule 1 during deployment tuning.
Production Ready
Conditional. Deployment-ready template pending tenant-specific validation and tuning.
Rule Regret Check
Deployment caution
External scanners or integrations may generate burst-style traffic.
Confidence caution
Detects targeting behavior but does not confirm exploitation or execution.
Coverage value
Provides early visibility into probing and exploit-attempt concentration and enhances triage when combined with other detection layers.
Detection Logic
alert http $EXTERNAL_NET any -> $HOME_NET $HTTP_PORTS (
msg:"CYBERDAX [EXP] CVE-2026-32201 suspicious external retry and targeting burst to sensitive SharePoint application paths";
flow:to_server,established;
http.uri;
pcre:"/^\/(?:_layouts\/15\/|_vti_bin\/)/U";
detection_filter:track by_src,count 10,seconds 60;
classtype:web-application-attack;
sid:2501004;
rev:4;
)
SentinelOne Selected Detection Rule(s)
Rule Title
CVE-2026-32201 SharePoint IIS worker process spawning suspicious child processes
Purpose
Detect suspicious child process execution originating from the SharePoint IIS worker process on exposed SharePoint servers. This rule identifies high-value post-exploitation behavior where web-service handling transitions into shell, scripting, or living-off-the-land execution inconsistent with normal SharePoint operation.
SOC Usage Mode
Alert-capable supporting detection. Escalate on internet-exposed SharePoint infrastructure. Correlate with SharePoint instability, suspicious inbound targeting, or abnormal outbound communication.
Minimum Deployment Requirement
SentinelOne process creation telemetry, parent-child lineage visibility, and command-line visibility must be enabled. SharePoint servers must be accurately scoped. Baseline validation must confirm w3wp.exe does not normally spawn administrative shells, scripting engines, or common living-off-the-land binaries as part of approved operations.
Enforcement Method
Parent process is strictly scoped to w3wp.exe. Child process scope is restricted to high-risk interpreters and living-off-the-land binaries that should not be launched by the IIS worker process on production SharePoint servers. This rule is intended for zero-tolerance deployment on validated SharePoint server roles after baseline confirmation.
Implementation Constraint Notes
This rule detects suspicious post-exploitation execution behavior, not exploit delivery. It does not prove that CVE-2026-32201 was the initial access vector by itself. Environments using custom SharePoint administration, backup tooling, troubleshooting scripts, or third-party application-management workflows may require host scoping, maintenance-window suppression, or targeted exclusions. This rule should only be deployed to validated SharePoint and IIS server roles.
Variant Coverage
This rule covers exploitation paths that lead to child process execution from the IIS worker process and remains useful across many payload variants because it does not depend on one exploit string or one static command line. It retains value for web shell, inline command, script-launch, and utility-launch follow-on behavior that results in new process creation from w3wp.exe. It does not cover fully in-process execution, memory-only execution without child process launch, or delayed execution handed off through a different trusted parent process.
Engineering Note
This rule is a deployment-ready template pending tenant-side validation. Validate whether w3wp.exe on SharePoint hosts ever spawns approved maintenance or application-management child processes, confirm server-role scoping is accurate, and tune exclusions before production alerting. Coverage remains conditional until tenant-specific validation is completed.
Production Ready
Conditional. Deployment-ready template pending tenant-specific validation and tuning.
Rule Regret Check
Deployment caution
Custom SharePoint administration, troubleshooting workflows, or third-party application components may produce rare but legitimate child process launches from w3wp.exe and require targeted exclusions.
Confidence caution
This rule is high-value for suspicious post-exploitation execution but does not by itself prove that CVE-2026-32201 was the initial access vector.
Coverage value
Provides strong endpoint-side visibility into one of the most operationally valuable post-exploitation behaviors on exposed SharePoint servers and materially strengthens detection when paired with network-side exploit-attempt or service-instability evidence.
Detection Logic
EventType = "Process Creation"
AND SrcProcImagePath EndsWithCIS "\\w3wp.exe"
AND (
TgtProcImagePath EndsWithCIS "\\cmd.exe" OR
TgtProcImagePath EndsWithCIS "\\powershell.exe" OR
TgtProcImagePath EndsWithCIS "\\pwsh.exe" OR
TgtProcImagePath EndsWithCIS "\\cscript.exe" OR
TgtProcImagePath EndsWithCIS "\\wscript.exe" OR
TgtProcImagePath EndsWithCIS "\\mshta.exe" OR
TgtProcImagePath EndsWithCIS "\\rundll32.exe" OR
TgtProcImagePath EndsWithCIS "\\regsvr32.exe" OR
TgtProcImagePath EndsWithCIS "\\certutil.exe" OR
TgtProcImagePath EndsWithCIS "\\bitsadmin.exe" OR
TgtProcImagePath EndsWithCIS "\\curl.exe" OR
TgtProcImagePath EndsWithCIS "\\whoami.exe" OR
TgtProcImagePath EndsWithCIS "\\net.exe" OR
TgtProcImagePath EndsWithCIS "\\net1.exe"
)
Rule Title
CVE-2026-32201 SharePoint IIS worker process launching suspicious download, decode, or execution command lines
Purpose
Detect suspicious command-line execution initiated by the SharePoint IIS worker process through shells, scripting engines, or living-off-the-land binaries where the command line reflects download, decode, staging, or execution behavior commonly associated with post-exploitation activity.
SOC Usage Mode
Alert-capable supporting detection. Escalate on internet-exposed SharePoint infrastructure. Correlate with Rule 1, SharePoint instability, suspicious file creation, or abnormal outbound communication.
Minimum Deployment Requirement
SentinelOne process creation telemetry, parent-child lineage visibility, and full command-line visibility must be enabled. SharePoint servers must be accurately scoped. The environment must validate that approved SharePoint maintenance or automation workflows do not legitimately use the listed command-line patterns under w3wp.exe lineage.
Enforcement Method
Parent process scope is restricted to w3wp.exe. Child process scope is restricted to shells, scripting engines, and selected utility binaries. Alerting is further narrowed to suspicious command-line behaviors associated with download, decode, or staged execution. This rule is intended to reduce the noise of broad process-spawn logic by enforcing suspicious execution content directly in the command line.
Implementation Constraint Notes
This rule detects suspicious post-exploitation execution behavior only. It does not prove exploit delivery. It is stronger than generic keyword-only logic because it requires suspicious execution content under IIS worker process lineage, but environments with approved automation or maintenance scripts may still require targeted exclusions. This rule should be deployed only to validated SharePoint and IIS server roles.
Variant Coverage
This rule covers follow-on activity that uses encoded PowerShell, web-download behavior, BITS transfers, certutil download and decode patterns, mshta execution, or command-shell driven staging from the IIS worker process. It does not cover in-memory-only execution without child process creation, quiet child-process launches with benign-looking command lines, or alternate parent-process pivots.
Engineering Note
This rule is a deployment-ready template pending tenant-side validation. Review whether approved operational workflows launch these binaries with similar command-line patterns from w3wp.exe. Add tightly scoped exclusions only where justified by documented administrative activity. Coverage remains conditional until tenant-specific validation is completed.
Production Ready
Conditional. Deployment-ready template pending tenant-specific validation and tuning.
Rule Regret Check
Deployment caution
Rare maintenance or troubleshooting workflows may legitimately invoke one or more of these patterns and require command-line or host-specific exclusions.
Confidence caution
This rule is highly suspicious when matched under w3wp.exe lineage, but it still does not independently prove the exact initial exploit path.
Coverage value
Provides stronger execution realism than generic outbound anomaly logic by anchoring directly on suspicious staging and execution content under SharePoint IIS worker process lineage.
Detection Logic
EventType = "Process Creation"
AND SrcProcImagePath EndsWithCIS "\\w3wp.exe"
AND (
TgtProcImagePath EndsWithCIS "\\powershell.exe" OR
TgtProcImagePath EndsWithCIS "\\pwsh.exe" OR
TgtProcImagePath EndsWithCIS "\\cmd.exe" OR
TgtProcImagePath EndsWithCIS "\\cscript.exe" OR
TgtProcImagePath EndsWithCIS "\\wscript.exe" OR
TgtProcImagePath EndsWithCIS "\\mshta.exe" OR
TgtProcImagePath EndsWithCIS "\\certutil.exe" OR
TgtProcImagePath EndsWithCIS "\\bitsadmin.exe" OR
TgtProcImagePath EndsWithCIS "\\curl.exe"
)
AND TgtProcCmdLine IsNotEmpty
AND (
TgtProcCmdLine ContainsCIS " -enc" OR
TgtProcCmdLine ContainsCIS " -encodedcommand" OR
TgtProcCmdLine ContainsCIS "frombase64string" OR
TgtProcCmdLine ContainsCIS "downloadstring" OR
TgtProcCmdLine ContainsCIS "invoke-webrequest" OR
TgtProcCmdLine ContainsCIS "iwr " OR
TgtProcCmdLine ContainsCIS "start-bitstransfer" OR
TgtProcCmdLine ContainsCIS "bitsadmin" OR
TgtProcCmdLine ContainsCIS "urlcache" OR
TgtProcCmdLine ContainsCIS "decode" OR
TgtProcCmdLine ContainsCIS "mshta " OR
TgtProcCmdLine ContainsCIS "rundll32 " OR
TgtProcCmdLine ContainsCIS "http://" OR
TgtProcCmdLine ContainsCIS "https://" OR
TgtProcCmdLine ContainsCIS "\\\\"
)
Splunk Selected Detection Rule(s)
Rule Title
CVE-2026-32201 SharePoint IIS worker process spawning suspicious child processes
Purpose
Detect suspicious child process execution originating from the SharePoint IIS worker process on exposed SharePoint servers. This rule identifies high-value post-exploitation behavior where web-service handling transitions into shell, scripting, or living-off-the-land execution inconsistent with normal SharePoint operation.
SOC Usage Mode
Alert-capable supporting detection. Escalate on internet-exposed SharePoint infrastructure. Correlate with SharePoint instability, suspicious inbound targeting, or abnormal outbound communication.
Minimum Deployment Requirement
Sysmon Event ID 1 or Windows Security Event ID 4688 with parent-child process visibility and command-line logging must be enabled. SharePoint servers must be accurately scoped using asset tags, host lookup, or equivalent host-role filtering.
Enforcement Method
Parent process is strictly scoped to w3wp.exe. Child process scope is restricted to high-risk interpreters and living-off-the-land binaries that should not be launched by IIS worker process under normal SharePoint operation. Aggregation is used to reduce single-event noise while preserving strong execution signals.
Implementation Constraint Notes
This rule detects suspicious post-exploitation execution behavior only. It does not confirm exploit delivery. Environments with SharePoint automation, backup tooling, troubleshooting scripts, or third-party application-management workflows may require command-line exclusions, host scoping, or maintenance-window suppression. Rule must be restricted to validated SharePoint server roles.
Variant Coverage
Covers execution paths involving shell, scripting, and living-off-the-land binaries launched from IIS worker process. Does not cover in-memory-only execution, no-spawn variants, or execution pivoted to alternate parent processes.
Engineering Note
Validate field normalization for parent and child process paths across Windows Security and Sysmon sources. Confirm that w3wp.exe on SharePoint hosts does not legitimately launch the listed child processes in approved operational workflows. Coverage remains conditional until tenant-specific validation is completed.
Production Ready
Conditional. Deployment-ready template pending tenant-specific validation and tuning.
Rule Regret Check
Deployment caution
Administrative workflows or third-party integrations may produce legitimate child process launches and require targeted exclusions.
Confidence caution
This rule detects suspicious execution behavior but does not independently prove the initial exploit vector.
Coverage value
Provides high-value endpoint-side visibility into one of the most operationally useful post-exploitation behaviors on exposed SharePoint servers.
Detection Logic
(index=windows OR index=sysmon)
(EventCode=4688 OR EventID=1)
| eval parent_path=lower(coalesce(ParentImage, ParentProcessName, Creator_Process_Name))
| eval child_path=lower(coalesce(Image, NewProcessName, ProcessName))
| eval cmdline=coalesce(CommandLine, Process_Command_Line)
| where like(parent_path, "%\\w3wp.exe")
| where like(child_path, "%\\cmd.exe")
OR like(child_path, "%\\powershell.exe")
OR like(child_path, "%\\pwsh.exe")
OR like(child_path, "%\\cscript.exe")
OR like(child_path, "%\\wscript.exe")
OR like(child_path, "%\\mshta.exe")
OR like(child_path, "%\\rundll32.exe")
OR like(child_path, "%\\regsvr32.exe")
OR like(child_path, "%\\certutil.exe")
OR like(child_path, "%\\bitsadmin.exe")
OR like(child_path, "%\\curl.exe")
OR like(child_path, "%\\whoami.exe")
OR like(child_path, "%\\net.exe")
OR like(child_path, "%\\net1.exe")
| stats count min(_time) as firstTime max(_time) as lastTime values(cmdline) as CommandLine by host, parent_path, child_path
| where count >= 1
Rule Title
CVE-2026-32201 SharePoint IIS worker process executing suspicious download, decode, or staged command lines
Purpose
Detect suspicious command-line execution initiated by the SharePoint IIS worker process where execution behavior reflects download, decode, staging, or execution patterns commonly associated with post-exploitation activity.
SOC Usage Mode
Alert-capable supporting detection. Escalate on internet-exposed SharePoint infrastructure. Correlate with Rule 1, suspicious file creation, service instability, or abnormal outbound communication.
Minimum Deployment Requirement
Sysmon Event ID 1 or Windows Security Event ID 4688 with full command-line logging must be enabled. SharePoint servers must be accurately scoped. Field normalization for command-line content must be validated across all relevant sourcetypes.
Enforcement Method
Parent process scope is restricted to w3wp.exe. Child process scope is restricted to shells, scripting engines, and selected utility binaries. Alerting is narrowed to suspicious command-line behaviors associated with download, decode, or staged execution to reduce the noise of broad process-spawn logic.
Implementation Constraint Notes
This rule detects suspicious post-exploitation execution behavior only. It does not prove exploit delivery. It is stronger than generic keyword-only logic because it requires suspicious execution content under IIS worker process lineage, but environments with approved automation or maintenance scripts may still require targeted exclusions. Rule should be deployed only to validated SharePoint and IIS server roles.
Variant Coverage
Covers follow-on activity that uses encoded PowerShell, web-download behavior, BITS transfers, certutil download and decode patterns, mshta execution, or command-shell driven staging from IIS worker process. Does not cover in-memory-only execution without child process creation, quiet child-process launches with benign-looking command lines, or alternate parent-process pivots.
Engineering Note
Review whether approved operational workflows launch these binaries with similar command-line patterns from w3wp.exe. Validate command-line field consistency across Windows Security and Sysmon sources. Add tightly scoped exclusions only where justified by documented administrative activity. Coverage remains conditional until tenant-specific validation is completed.
Production Ready
Conditional. Deployment-ready template pending tenant-specific validation and tuning.
Rule Regret Check
Deployment caution
Rare maintenance or troubleshooting workflows may legitimately invoke one or more of these patterns and require command-line or host-specific exclusions.
Confidence caution
This rule is highly suspicious when matched under w3wp.exe lineage, but it still does not independently prove the exact initial exploit path.
Coverage value
Provides stronger execution realism than generic outbound anomaly logic by anchoring directly on suspicious staging and execution content under SharePoint IIS worker process lineage.
Detection Logic
(index=windows OR index=sysmon)
(EventCode=4688 OR EventID=1)
| eval parent_path=lower(coalesce(ParentImage, ParentProcessName, Creator_Process_Name))
| eval child_path=lower(coalesce(Image, NewProcessName, ProcessName))
| eval cmdline=lower(coalesce(CommandLine, Process_Command_Line))
| where like(parent_path, "%\\w3wp.exe")
| where like(child_path, "%\\powershell.exe")
OR like(child_path, "%\\pwsh.exe")
OR like(child_path, "%\\cmd.exe")
OR like(child_path, "%\\cscript.exe")
OR like(child_path, "%\\wscript.exe")
OR like(child_path, "%\\mshta.exe")
OR like(child_path, "%\\certutil.exe")
OR like(child_path, "%\\bitsadmin.exe")
OR like(child_path, "%\\curl.exe")
| where like(cmdline, "% -enc%")
OR like(cmdline, "% -encodedcommand%")
OR like(cmdline, "%frombase64string%")
OR like(cmdline, "%downloadstring%")
OR like(cmdline, "%invoke-webrequest%")
OR like(cmdline, "%iwr %")
OR like(cmdline, "%start-bitstransfer%")
OR like(cmdline, "%bitsadmin%")
OR like(cmdline, "%urlcache%")
OR like(cmdline, "%decode%")
OR like(cmdline, "%mshta %")
OR like(cmdline, "%rundll32 %")
OR like(cmdline, "%http://%")
OR like(cmdline, "%https://%")
OR like(cmdline, "%\\\\%")
| stats count min(_time) as firstTime max(_time) as lastTime values(cmdline) as CommandLine by host, parent_path, child_path
| where count >= 1
Elastic
Rule Title
CVE-2026-32201 SharePoint IIS worker process spawning suspicious child processes
Purpose
Detect suspicious child process execution originating from the SharePoint IIS worker process on exposed SharePoint servers. This rule identifies high-value post-exploitation behavior where web-service handling transitions into shell, scripting, or living-off-the-land execution inconsistent with normal SharePoint operation.
SOC Usage Mode
Alert-capable supporting detection. Escalate on internet-exposed SharePoint infrastructure. Correlate with SharePoint instability, suspicious inbound targeting, or abnormal outbound communication.
Minimum Deployment Requirement
Elastic Defend or equivalent process creation telemetry must be enabled. Parent-child process lineage and command-line visibility must be available. SharePoint servers must be accurately scoped using asset metadata, host groups, or equivalent server-role filtering.
Enforcement Method
Parent process is strictly scoped to w3wp.exe. Child process scope is restricted to high-risk interpreters and living-off-the-land binaries that should not be launched by IIS worker process under normal SharePoint operation. Rule deployment should be limited to validated SharePoint server roles.
Implementation Constraint Notes
This rule detects suspicious post-exploitation execution behavior only. It does not confirm exploit delivery. Environments with SharePoint automation, backup tooling, troubleshooting scripts, or third-party application-management workflows may require command-line exclusions, host scoping, or maintenance-window suppression. Rule must be restricted to validated SharePoint server roles.
Variant Coverage
Covers execution paths involving shell, scripting, and living-off-the-land binaries launched from IIS worker process. Does not cover in-memory-only execution, no-spawn variants, or execution pivoted to alternate parent processes.
Engineering Note
Validate process field mappings for parent and child executable paths and confirm that w3wp.exe on SharePoint hosts does not legitimately launch the listed child processes in approved operational workflows. Coverage remains conditional until tenant-specific validation is completed.
Production Ready
Conditional. Deployment-ready template pending tenant-specific validation and tuning.
Rule Regret Check
Deployment caution
Administrative workflows or third-party integrations may produce legitimate child process launches and require targeted exclusions.
Confidence caution
This rule detects suspicious execution behavior but does not independently prove the initial exploit vector.
Coverage value
Provides high-value endpoint-side visibility into one of the most operationally useful post-exploitation behaviors on exposed SharePoint servers.
Detection Logic
process
where host.os.type == "windows"
and event.type == "start"
and process.parent.executable : "*\\w3wp.exe"
and process.executable : (
"*\\cmd.exe",
"*\\powershell.exe",
"*\\pwsh.exe",
"*\\cscript.exe",
"*\\wscript.exe",
"*\\mshta.exe",
"*\\rundll32.exe",
"*\\regsvr32.exe",
"*\\certutil.exe",
"*\\bitsadmin.exe",
"*\\curl.exe",
"*\\whoami.exe",
"*\\net.exe",
"*\\net1.exe"
)
Rule Title
CVE-2026-32201 SharePoint IIS worker process executing suspicious encoded, download, or staged command lines
Purpose
Detect suspicious command-line execution initiated by the SharePoint IIS worker process where execution behavior reflects encoded commands, download activity, decode activity, or staged execution patterns commonly associated with post-exploitation.
SOC Usage Mode
Alert-capable supporting detection. Escalate on internet-exposed SharePoint infrastructure. Correlate with Rule 1, suspicious file creation, service instability, or abnormal outbound communication.
Minimum Deployment Requirement
Elastic process telemetry with full command-line visibility must be enabled. SharePoint servers must be accurately scoped. Field normalization for process command-line content must be validated across relevant data sources.
Enforcement Method
Parent process scope is restricted to w3wp.exe. Child process scope is restricted to shells, scripting engines, and selected utility binaries. Alerting is narrowed to suspicious command-line behaviors that indicate encoded execution, staged download activity, decode activity, or execution handoff rather than generic tool presence. This rule is intended to reduce noise by requiring suspicious execution content directly in the command line.
Implementation Constraint Notes
This rule detects suspicious post-exploitation execution behavior only. It does not prove exploit delivery. It is stronger than generic keyword-only logic because it requires suspicious execution content under IIS worker process lineage, but environments with approved automation or maintenance scripts may still require targeted exclusions. Rule should be deployed only to validated SharePoint and IIS server roles.
Variant Coverage
Covers follow-on activity that uses encoded PowerShell, web-download behavior, BITS transfers, certutil download and decode patterns, mshta execution with remote or file-backed content, or command-shell driven staging from IIS worker process. Does not cover in-memory-only execution without child process creation, quiet child-process launches with benign-looking command lines, or alternate parent-process pivots.
Engineering Note
Review whether approved operational workflows launch these binaries with similar command-line patterns from w3wp.exe. Validate command-line field consistency across ingested process sources. Add tightly scoped exclusions only where justified by documented administrative activity. Coverage remains conditional until tenant-specific validation is completed.
Production Ready
Conditional. Deployment-ready template pending tenant-specific validation and tuning.
Rule Regret Check
Deployment caution
Rare maintenance or troubleshooting workflows may legitimately invoke one or more of these patterns and require command-line or host-specific exclusions.
Confidence caution
This rule is highly suspicious when matched under w3wp.exe lineage, but it still does not independently prove the exact initial exploit path.
Coverage value
Provides stronger execution realism than generic outbound anomaly logic by anchoring directly on suspicious staging and execution content under SharePoint IIS worker process lineage.
Detection Logic
process
where host.os.type == "windows"
and event.type == "start"
and process.parent.executable : "*\\w3wp.exe"
and process.executable : (
"*\\powershell.exe",
"*\\pwsh.exe",
"*\\cmd.exe",
"*\\cscript.exe",
"*\\wscript.exe",
"*\\mshta.exe",
"*\\certutil.exe",
"*\\bitsadmin.exe",
"*\\curl.exe"
)
and process.command_line != null
and (
process.command_line like~ "*-enc*" or
process.command_line like~ "*-encodedcommand*" or
process.command_line like~ "*frombase64string*" or
process.command_line like~ "*downloadstring*" or
process.command_line like~ "*invoke-webrequest*" or
process.command_line like~ "*start-bitstransfer*" or
process.command_line like~ "*bitsadmin* /transfer*" or
process.command_line like~ "*bitsadmin* /create*" or
process.command_line like~ "*certutil* -urlcache*" or
process.command_line like~ "*certutil* -decode*" or
process.command_line like~ "*mshta*http*" or
process.command_line like~ "*mshta*https*" or
process.command_line like~ "*mshta*\\\\*" or
process.command_line like~ "*cmd.exe* /c *powershell*" or
process.command_line like~ "*cmd.exe* /c *certutil*" or
process.command_line like~ "*cmd.exe* /c *bitsadmin*" or
process.command_line like~ "*cmd.exe* /c *curl*"
)
QRadar
Rule Title
CVE-2026-32201 SharePoint IIS worker process spawning suspicious child processes
Purpose
Detect suspicious child process execution originating from the SharePoint IIS worker process on exposed SharePoint servers. This rule identifies high-value post-exploitation behavior where web-service handling transitions into shell, scripting, or living-off-the-land execution inconsistent with normal SharePoint operation.
SOC Usage Mode
Alert-capable supporting detection. Escalate on internet-exposed SharePoint infrastructure. Correlate with SharePoint instability, suspicious inbound targeting, or abnormal outbound communication.
Minimum Deployment Requirement
QRadar must ingest Windows process creation telemetry with searchable process lineage content. Sysmon Event ID 1 or equivalent EDR process telemetry is preferred. SharePoint servers must be accurately scoped using asset profiles, building blocks, reference sets, or validated host-group logic. Searchable process-path content must be preserved either through normalized properties, searchable payload, or both.
Enforcement Method
Parent process is strictly scoped to w3wp.exe. Child process scope is restricted to high-risk interpreters and living-off-the-land binaries that should not be launched by IIS worker process under normal SharePoint operation. This rule is optimized for payload-constrained QRadar deployments by tightly requiring both parent and child executable evidence within the same process-creation event window instead of relying on broader anomaly assumptions.
Implementation Constraint Notes
This rule detects suspicious post-exploitation execution behavior only. It does not confirm exploit delivery. Environments with SharePoint automation, backup tooling, troubleshooting scripts, or third-party application-management workflows may require command-line exclusions, host scoping, or maintenance-window suppression. If QRadar does not reliably preserve searchable parent and child process path content in the same event representation, this rule must not be broadly deployed until parser quality is corrected.
Variant Coverage
Covers execution paths involving shell, scripting, and living-off-the-land binaries launched from IIS worker process. Does not cover in-memory-only execution, no-spawn variants, or execution pivoted to alternate parent processes.
Engineering Note
Validate that the relevant log sources preserve parent process and child process executable evidence in a stable searchable form. Prefer DSM-normalized properties where available, but if payload search is the only reliable method, confirm that payload formatting is stable across all targeted sources before production deployment. Coverage remains conditional until tenant-specific validation is completed.
Production Ready
Conditional. Deployment-ready template pending tenant-specific validation and tuning.
Rule Regret Check
Deployment caution
Administrative workflows or third-party integrations may produce legitimate child process launches and require targeted exclusions.
Confidence caution
This rule detects suspicious execution behavior but does not independently prove the initial exploit vector.
Coverage value
Provides high-value endpoint-side visibility into one of the most operationally useful post-exploitation behaviors on exposed SharePoint servers.
Detection Logic
SELECT
LOGSOURCENAME(logsourceid) AS log_source,
sourceip,
destinationip,
username,
UTF8(payload) AS raw_payload
FROM events
WHERE
(
LOWER(QIDNAME(qid)) LIKE '%process%'
OR LOWER(UTF8(payload)) LIKE '%eventid=1%'
OR LOWER(UTF8(payload)) LIKE '%4688%'
)
AND LOWER(UTF8(payload)) LIKE '%\\w3wp.exe%'
AND (
LOWER(UTF8(payload)) LIKE '%\\cmd.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\powershell.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\pwsh.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\cscript.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\wscript.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\mshta.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\rundll32.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\regsvr32.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\certutil.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\bitsadmin.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\curl.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\whoami.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\net.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\net1.exe%'
)
LAST 10 MINUTES
Rule Title
CVE-2026-32201 SharePoint IIS worker process executing suspicious encoded, download, decode, or staged command lines
Purpose
Detect suspicious command-line execution initiated by the SharePoint IIS worker process where execution behavior reflects encoded commands, download activity, decode activity, or staged execution patterns commonly associated with post-exploitation.
SOC Usage Mode
Alert-capable supporting detection. Escalate on internet-exposed SharePoint infrastructure. Correlate with Rule 1, suspicious file creation, service instability, or abnormal outbound communication.
Minimum Deployment Requirement
QRadar must ingest process creation telemetry with searchable command-line content. Sysmon Event ID 1 or equivalent EDR process telemetry is preferred. SharePoint servers must be accurately scoped. Searchable command-line content must be available through normalized properties, searchable payload, or both. Command-line extraction quality must be validated across relevant log sources before alerting is enabled.
Enforcement Method
Parent process scope is restricted to w3wp.exe. Child process scope is restricted to shells, scripting engines, and selected utility binaries. Alerting is narrowed to suspicious command-line behaviors that indicate encoded execution, staged download activity, decode activity, or execution handoff rather than generic tool presence. This rule is optimized by requiring both suspicious child binary context and suspicious execution-content context in the same searchable event representation.
Implementation Constraint Notes
This rule detects suspicious post-exploitation execution behavior only. It does not prove exploit delivery. It is stronger than generic keyword-only logic because it requires suspicious execution content under IIS worker process lineage, but environments with approved automation or maintenance scripts may still require targeted exclusions. If command-line content is truncated, inconsistently parsed, or absent in searchable payload, this rule should not be promoted until logging quality is corrected.
Variant Coverage
Covers follow-on activity that uses encoded PowerShell, web-download behavior, BITS transfers, certutil download and decode patterns, mshta execution with remote or file-backed content, or command-shell driven staging from IIS worker process. Does not cover in-memory-only execution without child process creation, quiet child-process launches with benign-looking command lines, or alternate parent-process pivots.
Engineering Note
Review whether approved operational workflows launch these binaries with similar command-line patterns from w3wp.exe. Validate searchable command-line coverage and consistency across ingested process sources before production deployment. Add tightly scoped exclusions only where justified by documented administrative activity. Coverage remains conditional until tenant-specific validation is completed.
Production Ready
Conditional. Deployment-ready template pending tenant-specific validation and tuning.
Rule Regret Check
Deployment caution
Rare maintenance or troubleshooting workflows may legitimately invoke one or more of these patterns and require command-line or host-specific exclusions.
Confidence caution
This rule is highly suspicious when matched under w3wp.exe lineage, but it still does not independently prove the exact initial exploit path.
Coverage value
Provides stronger execution realism than generic outbound anomaly logic by anchoring directly on suspicious staging and execution content under SharePoint IIS worker process lineage.
Detection Logic
SELECT
LOGSOURCENAME(logsourceid) AS log_source,
sourceip,
destinationip,
username,
UTF8(payload) AS raw_payload
FROM events
WHERE
(
LOWER(QIDNAME(qid)) LIKE '%process%'
OR LOWER(UTF8(payload)) LIKE '%eventid=1%'
OR LOWER(UTF8(payload)) LIKE '%4688%'
)
AND LOWER(UTF8(payload)) LIKE '%\\w3wp.exe%'
AND (
LOWER(UTF8(payload)) LIKE '%\\powershell.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\pwsh.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\cmd.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\cscript.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\wscript.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\mshta.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\certutil.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\bitsadmin.exe%'
OR LOWER(UTF8(payload)) LIKE '%\\curl.exe%'
)
AND (
LOWER(UTF8(payload)) LIKE '%-enc%'
OR LOWER(UTF8(payload)) LIKE '%-encodedcommand%'
OR LOWER(UTF8(payload)) LIKE '%frombase64string%'
OR LOWER(UTF8(payload)) LIKE '%downloadstring%'
OR LOWER(UTF8(payload)) LIKE '%invoke-webrequest%'
OR LOWER(UTF8(payload)) LIKE '%start-bitstransfer%'
OR LOWER(UTF8(payload)) LIKE '%bitsadmin% /transfer%'
OR LOWER(UTF8(payload)) LIKE '%bitsadmin% /create%'
OR LOWER(UTF8(payload)) LIKE '%certutil% -urlcache%'
OR LOWER(UTF8(payload)) LIKE '%certutil% -decode%'
OR LOWER(UTF8(payload)) LIKE '%mshta%http%'
OR LOWER(UTF8(payload)) LIKE '%mshta%https%'
OR LOWER(UTF8(payload)) LIKE '%mshta%\\\\%'
OR LOWER(UTF8(payload)) LIKE '%cmd.exe% /c %powershell%'
OR LOWER(UTF8(payload)) LIKE '%cmd.exe% /c %certutil%'
OR LOWER(UTF8(payload)) LIKE '%cmd.exe% /c %bitsadmin%'
OR LOWER(UTF8(payload)) LIKE '%cmd.exe% /c %curl%'
)
LAST 10 MINUTES
Sigma
Rule Title
CVE-2026-32201 SharePoint IIS worker process spawning suspicious child processes
Purpose
Detect suspicious child process execution originating from the SharePoint IIS worker process on exposed SharePoint servers. This rule identifies high-value post-exploitation behavior where web-service handling transitions into shell, scripting, or living-off-the-land execution inconsistent with normal SharePoint operation.
SOC Usage Mode
Alert-capable supporting detection. Deploy across environments where Windows process creation logs are normalized into Sigma-compatible schemas. Escalate on internet-exposed SharePoint infrastructure.
Minimum Deployment Requirement
Windows process creation logging must be available through Sysmon Event ID 1 or Security Event ID 4688. Fields must map to Sigma schema including ParentImage, Image, and CommandLine. SharePoint servers must be scoped through host filtering, tags, or SIEM-side conditions.
Enforcement Method
Parent process is strictly scoped to w3wp.exe. Child process scope is restricted to high-risk interpreters and living-off-the-land binaries that should not be launched by IIS worker process under normal SharePoint operation. Detection assumes zero-baseline tolerance after validation.
Implementation Constraint Notes
This rule detects suspicious post-exploitation execution behavior only. It does not confirm exploit delivery. Environments with automation, maintenance scripts, backup tooling, or third-party integrations may require exclusions or host-level scoping.
Variant Coverage
Covers shell, scripting, and living-off-the-land execution originating from IIS worker process. Does not cover in-memory execution, no-spawn variants, or alternate parent pivot techniques.
Engineering Note
Validate field mappings for ParentImage, Image, and CommandLine across the ingestion pipeline. Confirm that w3wp.exe does not legitimately spawn these processes in approved workflows on SharePoint hosts. Coverage remains conditional until tenant-specific validation is complete.
Production Ready
Conditional. Deployment-ready template pending validation and tuning.
Rule Regret Check
Deployment caution
Administrative or automation workflows may trigger.
Confidence caution
Does not prove exploit vector.
Coverage value
High-value detection for post-exploitation execution on SharePoint servers.
Detection Logic
title: CVE-2026-32201 SharePoint IIS worker spawning suspicious child processes
id: 1b2c3d4e-1111-2222-3333-444455556666
status: experimental
logsource:
product: windows
category: process_creation
detection:
selection_parent:
ParentImage|endswith: '\w3wp.exe'
selection_child:
Image|endswith:
- '\cmd.exe'
- '\powershell.exe'
- '\pwsh.exe'
- '\cscript.exe'
- '\wscript.exe'
- '\mshta.exe'
- '\rundll32.exe'
- '\regsvr32.exe'
- '\certutil.exe'
- '\bitsadmin.exe'
- '\curl.exe'
- '\whoami.exe'
- '\net.exe'
- '\net1.exe'
condition: selection_parent and selection_child
fields:
- Image
- ParentImage
- CommandLine
level: high
Rule Title
CVE-2026-32201 SharePoint IIS worker process executing encoded or staged command-line activity
Purpose
Detect suspicious command-line execution initiated by the SharePoint IIS worker process where execution behavior reflects encoded commands, staged download activity, or command-driven payload execution commonly associated with post-exploitation.
SOC Usage Mode
Alert-capable supporting detection. Escalate on internet-exposed SharePoint infrastructure. Correlate with Rule 1 and additional host-level activity.
Minimum Deployment Requirement
Windows process creation logs with full command-line visibility must be available. Fields must map to Sigma schema including ParentImage, Image, and CommandLine. SharePoint servers must be scoped through SIEM-side filtering.
Enforcement Method
Parent process is restricted to w3wp.exe. Child process scope is restricted to shells and scripting-capable binaries. Detection enforces encoded execution or staged download and execution behavior rather than generic tool presence. Mshta behavior is explicitly coupled to remote or file-backed execution indicators to avoid loose matching.
Implementation Constraint Notes
This rule detects suspicious execution behavior only. It does not confirm exploit delivery. Environments with legitimate scripting or automation may require exclusions. This rule should be deployed only to validated SharePoint and IIS server roles.
Variant Coverage
Covers encoded PowerShell, staged execution chains, remote download and execution behavior, and mshta-driven remote or file-backed staging from IIS worker process. Does not cover in-memory-only execution, quiet child-process launches with benign-looking command lines, or alternate parent pivots.
Engineering Note
Validate CommandLine normalization across ingestion sources and tune exclusions carefully to preserve detection integrity. Confirm that approved workflows do not invoke these behaviors from w3wp.exe lineage. Coverage remains conditional until validation is complete.
Production Ready
Conditional. Deployment-ready template pending validation and tuning.
Rule Regret Check
Deployment caution
Automation scripts may trigger and require tightly scoped exclusions.
Confidence caution
Behavioral detection only.
Coverage value
Strong detection for encoded execution and staged payload activity under SharePoint IIS worker process lineage.
Detection Logic
title: CVE-2026-32201 SharePoint IIS worker encoded or staged execution
id: 7f8e9d0c-aaaa-bbbb-cccc-ddddeeeeffff
status: experimental
logsource:
product: windows
category: process_creation
detection:
selection_parent:
ParentImage|endswith: '\w3wp.exe'
selection_child_shells:
Image|endswith:
- '\powershell.exe'
- '\pwsh.exe'
- '\cmd.exe'
- '\cscript.exe'
- '\wscript.exe'
selection_child_mshta:
Image|endswith: '\mshta.exe'
selection_encoded:
CommandLine|contains:
- '-enc'
- '-encodedcommand'
- 'frombase64string'
selection_download_exec:
CommandLine|contains:
- 'downloadstring'
- 'invoke-webrequest'
- 'start-bitstransfer'
selection_mshta_remote:
CommandLine|contains:
- 'http://'
- 'https://'
- '\\\\'
condition: selection_parent and ((selection_child_shells and (selection_encoded or selection_download_exec)) or (selection_child_mshta and selection_mshta_remote))
fields:
- Image
- ParentImage
- CommandLine
level: high
YARA
Rule Title
CVE-2026-32201 suspicious ASPX web shell or command-execution page on SharePoint or IIS content paths
Purpose
Detect suspicious ASPX web shell or command-execution content likely to be written to SharePoint or IIS-accessible content locations following exploitation. This rule is intended to identify post-exploitation file artifacts where the attacker establishes remote command execution or operator-controlled web access through an ASPX page.
SOC Usage Mode
Alert-capable supporting detection. Use on exposed SharePoint infrastructure for high-priority file triage, web root scanning, and post-compromise artifact discovery. Correlate with suspicious w3wp.exe child-process activity, IIS instability, or anomalous outbound communication.
Minimum Deployment Requirement
YARA scanning must be available on SharePoint and IIS hosts or against collected file artifacts. Scanning scope must include web-accessible directories, SharePoint content paths, IIS web roots, temporary upload locations, and recently modified ASPX files. File content must be available in decoded text form.
Enforcement Method
This rule enforces ASPX or server-side script execution context and requires multiple high-risk web shell behaviors in the same file, including operator-supplied request handling, response-based interaction, and a true execution-oriented primitive. It is optimized for post-exploitation artifact detection rather than generic script hunting.
Implementation Constraint Notes
This rule detects suspicious web shell or command-execution file content only. It does not detect exploit delivery and does not prove the initial access vector by itself. Environment-specific administrative pages, custom diagnostics tooling, or internally developed support pages may require exclusions if they expose similar execution behavior. This rule should be applied to SharePoint and IIS content locations, not broad enterprise-wide file systems.
Variant Coverage
Covers common ASPX web shell and command-execution patterns including request-driven execution, command invocation, encoded payload handling, and response-based operator interaction. Does not cover fully fileless exploitation, memory-only execution, or post-exploitation activity that does not result in a written server-side file.
Engineering Note
Prioritize scanning of recently modified ASPX, ASHX, and ASCX files in SharePoint and IIS-served directories. Validate false-positive risk against approved administrative or support tooling before enabling broad automated response. Coverage remains conditional until tenant-specific validation is completed.
Production Ready
Conditional. Deployment-ready template pending tenant-specific validation and tuning.
Rule Regret Check
Deployment caution
Custom administrative pages, troubleshooting tools, or legacy support content may contain overlapping execution-oriented logic and require exclusions.
Confidence caution
This rule detects strong post-exploitation web artifact behavior but does not independently prove which exploit path created the file.
Coverage value
Provides high-value file-based visibility into one of the most operationally important post-exploitation outcomes on exposed SharePoint infrastructure: attacker-controlled web execution artifacts.
Detection Logic
rule CYBERDAX_CVE_2026_32201_ASPX_Webshell_Command_Execution
{
meta:
description = "Detect suspicious ASPX web shell or command-execution page associated with post-exploitation on SharePoint or IIS hosts"
author = "CyberDax"
reference = "CVE-2026-32201"
date = "2026-04-14"
confidence = "high"
strings:
$aspx_1 = "<%@ Page" nocase ascii wide
$aspx_2 = "<script runat=\"server\">" nocase ascii wide
$req_1 = "Request[\"" nocase ascii wide
$req_2 = "Request.Form" nocase ascii wide
$resp_1 = "Response.Write" nocase ascii wide
$proc_1 = "System.Diagnostics.Process" nocase ascii wide
$proc_2 = "ProcessStartInfo" nocase ascii wide
$exec_1 = ".Start()" nocase ascii wide
$cmd_1 = "cmd.exe" nocase ascii wide
$ps_1 = "powershell.exe" nocase ascii wide
$enc_1 = "FromBase64String" nocase ascii wide
$eval_1 = "eval(" nocase ascii wide
$server_1 = "Server.HtmlEncode" nocase ascii wide
condition:
(
1 of ($aspx_*)
and 1 of ($req_*)
and 1 of ($resp_*)
and 1 of ($proc_*, $exec_1)
and 1 of ($cmd_1, $ps_1, $enc_1, $eval_1)
)
}
Rule Title
CVE-2026-32201 suspicious ASPX loader or stager with encoded payload decode and execution behavior
Purpose
Detect suspicious ASPX loader or stager content that decodes, reconstructs, or stages attacker-supplied payloads for execution after compromise. This rule is intended to identify more covert post-exploitation artifacts than simple command-execution pages, including encoded payload loaders and script-based server-side stagers.
SOC Usage Mode
Alert-capable supporting detection. Use for targeted scanning of SharePoint and IIS-served content, suspicious uploads, and recently modified server-side files. Correlate with Rule 1, suspicious file-write events, or execution activity from w3wp.exe.
Minimum Deployment Requirement
YARA scanning must be available on SharePoint and IIS hosts or against collected file artifacts. Scanning scope must include ASPX, ASHX, ASCX, and script-capable server-side files in web-served directories and recent-change collections. File content must be available for content inspection.
Enforcement Method
This rule requires encoded payload handling plus a stronger execution or staging primitive in the same file. It is designed to reduce noise by requiring decode-and-execute or decode-and-stage behavior rather than generic encoding references alone.
Implementation Constraint Notes
This rule detects suspicious loader or stager file content only. It does not detect exploit delivery and does not prove the initial access vector by itself. Custom applications that legitimately embed encoded resources or server-side transformation logic may require exclusions after review. This rule should not be used as a generic enterprise YARA signature outside the SharePoint and IIS post-compromise hunting context.
Variant Coverage
Covers encoded ASPX loaders, decode-and-execute patterns, script-based stagers, and payload handoff behavior written to disk after compromise. Does not cover purely in-memory loaders, external-only command-and-control logic without written artifacts, or benign files that never expose execution or staging behavior.
Engineering Note
Prioritize recently created or modified ASPX-family files, especially those with obfuscated strings, minimal UI content, or unexpected placement in SharePoint web-accessible directories. Validate exclusions carefully if internal applications use encoded content handling. Coverage remains conditional until tenant-specific validation is completed.
Production Ready
Conditional. Deployment-ready template pending tenant-specific validation and tuning.
Rule Regret Check
Deployment caution
Applications that legitimately decode embedded content server-side may overlap and require tightly scoped exclusions after review.
Confidence caution
This rule is optimized for post-exploitation staging artifacts and does not independently prove active execution at scan time.
Coverage value
Provides strong file-based visibility into stealthier post-exploitation loader behavior that may be missed by simple web shell detection alone.
Detection Logic
rule CYBERDAX_CVE_2026_32201_ASPX_Encoded_Loader_Stager
{
meta:
description = "Detect suspicious ASPX loader or stager with encoded payload decode and execution behavior on SharePoint or IIS hosts"
author = "CyberDax"
reference = "CVE-2026-32201"
date = "2026-04-14"
confidence = "high"
strings:
$aspx_1 = "<%@ Page" nocase ascii wide
$aspx_2 = "<script runat=\"server\">" nocase ascii wide
$b64_1 = "FromBase64String" nocase ascii wide
$b64_2 = "Convert.FromBase64String" nocase ascii wide
$enc_1 = "Encoding.UTF8.GetString" nocase ascii wide
$enc_2 = "Encoding.Unicode.GetString" nocase ascii wide
$asm_1 = "Assembly.Load" nocase ascii wide
$asm_2 = "Load(byte[]" nocase ascii wide
$exec_1 = "ProcessStartInfo" nocase ascii wide
$exec_2 = "System.Diagnostics.Process" nocase ascii wide
$run_1 = "RunspaceFactory" nocase ascii wide
$run_2 = "AddScript(" nocase ascii wide
$resp_1 = "Response.Write" nocase ascii wide
$req_1 = "Request[\"" nocase ascii wide
condition:
(
1 of ($aspx_*)
and 1 of ($b64_*, $enc_*)
and 1 of ($req_1, $resp_1)
and (
(1 of ($asm_*) and 1 of ($run_*, $exec_*))
or
(1 of ($exec_*) and 1 of ($run_*))
)
)
}
AWS
Rule Title
CVE-2026-32201 suspicious external request concentration against AWS-hosted SharePoint application paths
Purpose
Detect repeated suspicious external request activity to sensitive SharePoint application paths for AWS-hosted SharePoint deployments fronted by AWS-native controls such as Application Load Balancer, CloudFront, or AWS WAF. This rule identifies exploit-attempt style targeting behavior and delivery pressure against exposed SharePoint content paths.
SOC Usage Mode
Correlation-first. Triage and enrichment only. Not approved for standalone alerting as a confirmed compromise. Must be correlated with host-side execution telemetry or application instability.
Minimum Deployment Requirement
AWS WAF logs, ALB access logs, or CloudFront logs must be enabled and searchable. Request URI, source IP, and timestamp fields must be preserved. SharePoint application paths must be visible within the telemetry.
Enforcement Method
This rule detects repeated access attempts to sensitive SharePoint paths from the same external source within a constrained time window. It is optimized for identifying exploit-attempt concentration rather than single-request detection.
Implementation Constraint Notes
This rule detects exploit-attempt style targeting behavior only. It does not confirm successful exploitation or post-exploitation activity. Environments with vulnerability scanners, monitoring systems, or external integrations may require IP allowlisting or threshold tuning.
Variant Coverage
Covers repeated targeting of SharePoint application paths indicative of automated exploitation attempts or manual probing. Does not cover successful low-noise exploitation, encrypted payload visibility gaps, or post-exploitation activity.
Engineering Note
Validate that request URI fields preserve SharePoint path visibility. Tune thresholds against known scanning behavior, health checks, and expected external traffic patterns. Use this rule strictly as a supporting signal.
Production Ready
Conditional. Deployment-ready template pending threshold tuning and exclusion validation.
Rule Regret Check
Deployment caution
External scanners, monitoring tools, or integrations may generate repeated requests and require exclusions.
Confidence caution
This rule identifies exploit-attempt pressure, not confirmed exploitation.
Coverage value
Provides strong AWS-native visibility into exploit-attempt targeting behavior and materially improves triage when correlated with host-side telemetry.
Detection Logic
fields @timestamp, httpRequest.clientIp, httpRequest.uri, action
| filter httpRequest.uri like /\/(_layouts\/15\/|_vti_bin\/)/
| stats count as request_count,
min(@timestamp) as first_seen,
max(@timestamp) as last_seen
by httpRequest.clientIp, httpRequest.uri
| filter request_count >= 8
AWS Coverage Statement
AWS does not provide a strong native detection capability for SharePoint post-exploitation behaviors such as IIS worker process spawning or command execution without relying on external endpoint telemetry.
Detection of:
· w3wp.exe child process execution
· encoded or staged command-line activity
· post-exploitation execution chains
must be handled at the:
· endpoint telemetry layer (EDR, Sysmon, etc.)
· SIEM layer (Splunk, Elastic, QRadar, etc.)
AWS-native telemetry should be treated as:
· supporting visibility layer
· pre-exploitation and delivery-stage signal source
· correlation enrichment, not primary detection
Azure
Rule Title
CVE-2026-32201 suspicious external request concentration against Azure-hosted SharePoint application paths
Purpose
Detect repeated suspicious external request activity to sensitive SharePoint application paths for Azure-hosted SharePoint deployments fronted by Azure Application Gateway, Azure Front Door, or Web Application Firewall. This rule identifies exploit-attempt style targeting behavior and delivery pressure against exposed SharePoint content paths.
SOC Usage Mode
Correlation-first. Triage and enrichment only. Not approved for standalone alerting as a confirmed compromise. Must be correlated with host-side execution telemetry or application instability.
Minimum Deployment Requirement
Azure WAF logs, Application Gateway access logs, or Azure Front Door logs must be enabled and ingested into a queryable platform such as Log Analytics. Request URI, source IP, and timestamp fields must be preserved. SharePoint application paths must be visible within telemetry.
Enforcement Method
This rule detects repeated access attempts to sensitive SharePoint paths from the same external source within a constrained time window. It is optimized for identifying exploit-attempt concentration rather than single-request detection.
Implementation Constraint Notes
This rule detects exploit-attempt style targeting behavior only. It does not confirm successful exploitation or post-exploitation activity. Environments with vulnerability scanners, monitoring systems, or external integrations may require IP allowlisting or threshold tuning.
Variant Coverage
Covers repeated targeting of SharePoint application paths indicative of automated exploitation attempts or manual probing. Does not cover successful low-noise exploitation, encrypted payload visibility gaps beyond logged metadata, or post-exploitation activity.
Engineering Note
Validate that Azure logs preserve full request URI fidelity and source attribution. Tune thresholds against expected external traffic, health probes, and scanning patterns. Use strictly as a supporting signal.
Production Ready
Conditional. Deployment-ready template pending threshold tuning and exclusion validation.
Rule Regret Check
Deployment caution
Health probes, scanners, or integrations may generate repeated requests and require exclusions.
Confidence caution
Identifies exploit-attempt pressure, not confirmed compromise.
Coverage value
Provides strong Azure-native front-door visibility into suspicious targeting behavior and improves triage when correlated with host telemetry.
Detection Logic
AzureDiagnostics
| where requestUri_s has_any ("_layouts/15/", "_vti_bin/")
| summarize request_count = count(),
first_seen = min(TimeGenerated),
last_seen = max(TimeGenerated)
by clientIP_s, requestUri_s
| where request_count >= 8
Azure Coverage Statement (Framework-Enforced)
Azure does not provide a strong native detection capability for SharePoint post-exploitation behaviors such as IIS worker process spawning or command execution without relying on external endpoint telemetry.
Detection of:
· w3wp.exe child process execution
· encoded or staged command-line activity
· post-exploitation execution chains
must be handled at the:
· endpoint telemetry layer (EDR, Sysmon, etc.)
· SIEM layer (Splunk, Elastic, QRadar, etc.)
Azure-native telemetry should be treated as:
· supporting visibility layer
· pre-exploitation and delivery-stage signal source
· correlation enrichment, not primary detection
GCP
Rule Title
CVE-2026-32201 suspicious external request concentration against GCP-hosted SharePoint application paths
Purpose
Detect repeated suspicious external request activity to sensitive SharePoint application paths for GCP-hosted SharePoint deployments fronted by GCP-native controls such as Cloud Load Balancing, Cloud Armor, or equivalent Google Cloud edge logging. This rule identifies exploit-attempt style targeting behavior and delivery pressure against exposed SharePoint content paths.
SOC Usage Mode
Correlation-first. Triage and enrichment only. Not approved for standalone alerting as a confirmed compromise. Must be correlated with host-side execution telemetry or application instability.
Minimum Deployment Requirement
GCP load balancer logs, Cloud Armor logs, or equivalent edge request telemetry must be enabled and ingested into a queryable platform such as Cloud Logging or BigQuery. Request URI, source IP, and timestamp fields must be preserved. SharePoint application paths must be visible within telemetry.
Enforcement Method
This rule detects repeated access attempts to sensitive SharePoint paths from the same external source within a constrained time window. It is optimized for identifying exploit-attempt concentration rather than single-request detection.
Implementation Constraint Notes
This rule detects exploit-attempt style targeting behavior only. It does not confirm successful exploitation or post-exploitation activity. Environments with vulnerability scanners, monitoring systems, health checks, or external integrations may require IP allowlisting or threshold tuning.
Variant Coverage
Covers repeated targeting of SharePoint application paths indicative of automated exploitation attempts or manual probing. Does not cover successful low-noise exploitation, encrypted payload visibility gaps beyond logged metadata, or post-exploitation activity.
Engineering Note
Validate that GCP edge logs preserve request URI fidelity and source attribution consistently. Tune thresholds against expected external traffic, health checks, and scanning patterns. Use strictly as a supporting signal.
Production Ready
Conditional. Deployment-ready template pending threshold tuning and exclusion validation.
Rule Regret Check
Deployment caution
Health checks, scanners, or integrations may generate repeated requests and require exclusions.
Confidence caution
Identifies exploit-attempt pressure, not confirmed compromise.
Coverage value
Provides strong GCP-native front-door visibility into suspicious targeting behavior and improves triage when correlated with host telemetry.
Detection Logic
SELECT
httpRequest.remoteIp AS client_ip,
httpRequest.requestUrl AS request_url,
COUNT(1) AS request_count,
MIN(timestamp) AS first_seen,
MAX(timestamp) AS last_seen
FROM `PROJECT.DATASET._AllLogs`
WHERE
(
resource.type = "http_load_balancer"
OR logName LIKE "%requests%"
OR logName LIKE "%cloudarmor%"
)
AND (
httpRequest.requestUrl LIKE "%/_layouts/15/%"
OR httpRequest.requestUrl LIKE "%/_vti_bin/%"
)
GROUP BY client_ip, request_url
HAVING request_count >= 8
GCP Coverage Statement (Framework-Enforced)
GCP does not provide a strong native detection capability for SharePoint post-exploitation behaviors such as IIS worker process spawning or command execution without relying on external endpoint telemetry.
Detection of:
· w3wp.exe child process execution
· encoded or staged command-line activity
· post-exploitation execution chains
must be handled at the:
· endpoint telemetry layer (EDR, Sysmon, etc.)
· SIEM layer (Splunk, Elastic, QRadar, etc.)
GCP-native telemetry should be treated as:
· supporting visibility layer
· pre-exploitation and delivery-stage signal source
· correlation enrichment, not primary detection
S26 Threat-to-Rule Traceability Matrix
Threat Behavior 1
Behavior
Initial exploitation of SharePoint via improper input validation over network-accessible application endpoints
MITRE ATT&CK
T1190 – Exploit Public-Facing Application
Detection Coverage
AWS, Azure, and GCP front-door telemetry (WAF, load balancer, edge logs)
Mapped Rules
· AWS Rule 1
· Azure Rule 1
· GCP Rule 1
Coverage Disposition
Partially Detected
Telemetry Dependency
· WAF logs
· Load balancer / reverse proxy logs
· Request URI visibility
· Source IP attribution
Notes
Detection captures exploit-attempt concentration and targeting behavior, not exploit success or single-request exploitation.
KEV status confirms active exploitation, increasing likelihood of real-world triggering.
Standalone alerting is not permitted; correlation with downstream behaviors is required.
Threat Behavior 2
Behavior
Deployment of malicious ASPX web shell or server-side execution component
MITRE ATT&CK
T1505.003 – Server Software Component: Web Shell
Detection Coverage
File-based artifact detection via YARA scanning
Mapped Rules
· YARA Rule 1
· YARA Rule 2
Coverage Disposition
Detected
Telemetry Dependency
· File system access to IIS / SharePoint content paths
· File scanning capability (endpoint or offline)
· Visibility into newly created or modified server-side files
Notes
Strong detection of written post-exploitation artifacts.
Does not cover fileless persistence or memory-resident execution.
Coverage assumes scanning is applied to relevant directories; absence of scanning reduces coverage to Not Covered.
Threat Behavior 3
Behavior
IIS worker process (w3wp.exe) spawning suspicious child processes
MITRE ATT&CK
T1059 – Command and Scripting Interpreter
T1218 – System Binary Proxy Execution
Detection Coverage
Endpoint and SIEM process execution monitoring
Mapped Rules
· SentinelOne Rule Set
· Splunk Rule Set
· Elastic Rule Set
· QRadar Rule Set
· Sigma Rule Set
Coverage Disposition
Detected
Telemetry Dependency
· Process creation logs (Sysmon Event ID 1, Security 4688, or EDR equivalent)
· Parent-child process lineage
· Executable path visibility
Notes
High-confidence detection of post-exploitation execution behavior.
Does not rely on exploit visibility; triggers on attacker action post-access.
Coverage is strong across multiple systems and does not depend on a single detection source.
Threat Behavior 4
Behavior
Encoded command execution and staged payload delivery (PowerShell, command shell, script hosts)
MITRE ATT&CK
T1059.001 – PowerShell
T1105 – Ingress Tool Transfer
T1140 – Deobfuscate/Decode Files or Information
Detection Coverage
Command-line behavioral detection across endpoint and SIEM platforms
Mapped Rules
· SentinelOne Rule Set
· Splunk Rule Set
· Elastic Rule Set
· QRadar Rule Set
· Sigma Rule Set
Coverage Disposition
Detected
Telemetry Dependency
· Full command-line logging
· Process execution telemetry
· Parent-child lineage
Notes
Strong detection of staged execution and payload delivery behavior.
Coverage depends on command-line visibility; if truncated or disabled, detection degrades to Partially Detected.
Threat Behavior 5
Behavior
Post-exploitation system and account reconnaissance via command execution
MITRE ATT&CK
T1033 – System Owner/User Discovery
T1087 – Account Discovery
Detection Coverage
Endpoint process execution monitoring (command execution context)
Mapped Rules
· SentinelOne Rule Set
· Splunk Rule Set
· Elastic Rule Set
· QRadar Rule Set
· Sigma Rule Set
Coverage Disposition
Detected
Telemetry Dependency
· Process creation logs
· Command-line visibility
Notes
Individually low-confidence but highly valuable when correlated with execution or exploitation signals.
Standalone alerting is not recommended.
S26 Coverage Disposition Validation
· All behaviors with direct S25 rule mappings are correctly marked as Detected unless telemetry constraints justify otherwise
· Initial exploitation remains Partially Detected due to inherent limitations of network-layer visibility
· No behavior with strong rule coverage is incorrectly downgraded
· No unsupported behavior is marked as Detected
S26 KEV Impact Integration
KEV Status
Confirmed – CVE-2026-32201 is included in the CISA Known Exploited Vulnerabilities Catalog
KEV Implications
· Exploitation is actively occurring in the wild, not theoretical
· Initial access attempts should be treated as high-probability events
· Detection strategy must prioritize:
o rapid identification of post-exploitation behavior
o correlation across telemetry layers
o reduction of dwell time
Detection Strategy Adjustment
· Initial access detection remains inherently limited → acceptable under framework
· Primary defensive value shifts to post-exploitation detection layers, which are fully covered
· Cloud telemetry becomes:
o early warning signal
o correlation input
o not primary detection
S26 Summary
· Initial Access (T1190) → Partially Detected (cloud telemetry only, correlation required)
· Web Shell / Persistence (T1505.003) → Detected (file-based YARA coverage)
· Execution (T1059 / T1218) → Detected (strong multi-system coverage)
· Payload Delivery (T1105 / T1140) → Detected (command-line behavioral detection)
· Reconnaissance (T1033 / T1087) → Detected (correlation-dependent)
S27 Behavior & Log Artifacts
Endpoint / EDR Telemetry
Behavior: IIS Worker Process Execution Pivot
· ParentImage = w3wp.exe
· ChildImage ∈:
o cmd.exe, powershell.exe, pwsh.exe
o cscript.exe, wscript.exe
o mshta.exe, rundll32.exe, regsvr32.exe
· Process lineage must show direct spawn from w3wp.exe
· This is the primary execution signal
Behavior: Encoded or Staged Execution
· CommandLine contains:
o -enc, -encodedcommand
o FromBase64String
o Invoke-WebRequest, DownloadString
o Start-BitsTransfer
· Often chained:
o cmd.exe /c powershell
· Indicates payload staging or execution
Behavior: Post-Exploitation Recon
· Execution of:
o whoami.exe
o net.exe, net1.exe
· Appears after initial execution chain
· Low-signal alone, high signal in sequence
Network / Cloud Edge Telemetry
Behavior: Exploit Attempt Concentration
· URI patterns:
o /_layouts/15/
o /_vti_bin/
· Same source IP generating repeated requests
· Time-window burst behavior
Behavior: Automated Targeting
· Sequential request patterns
· High-frequency path probing
· Scanner-like behavior
File / Artifact Telemetry
Behavior: Malicious ASPX File Creation
· New or modified:
o .aspx, .ashx, .ascx
· Located in:
o IIS web roots
o SharePoint content directories
Behavior: Web Shell / Loader Content
· Content includes:
o Request[...], Response.Write
o System.Diagnostics.Process
o FromBase64String, Assembly.Load
· Indicates:
o command execution
o payload staging
Figure 5
S28 Detection Strategy and SOC Implementation Guidance
Detection Strategy
· Initial exploitation (T1190) is not reliably detectable
· Detection must pivot to:
o execution behavior
o staged command activity
· Cloud telemetry is:
o early signal only
o not authoritative detection
SOC Enforcement Model
Tier 1 — Alert-Capable Detection
Trigger ONLY when:
· w3wp.exe spawns suspicious child process
AND
· command-line or binary context is high-risk
Standalone alerting is allowed here.
Tier 2 — Correlation Requirement
Correlate:
· Endpoint execution (Tier 1)
WITH
· Cloud exploit-attempt signal (S27 network behavior)
Standalone cloud alerting is not permitted
Tier 3 — Investigation Layer
Mandatory validation steps:
· Identify newly written ASPX artifacts
· Validate command-line payload behavior
· Confirm process lineage chain
· Determine scope of execution
Implementation Enforcement
· Rules must enforce:
o parent-child lineage
o command-line validation
· “Suspicious” must never be baseline-derived from alerts
· No rule may infer compromise from network-only telemetry
S29 Detection Coverage Summary
Detected Behaviors
· w3wp.exe spawning suspicious processes
· Encoded and staged command execution
· ASPX web shell and loader artifacts
· Post-exploitation reconnaissance (correlated)
Conditional Post-Exploitation Behaviors
Not observed in currently available reporting; may occur during post-exploitation depending on attacker objectives and target environment:
· In-memory-only execution
· Alternate parent process chains
· Low-noise or single-request exploitation
Coverage Alignment
· Endpoint / SIEM → Primary detection layer
· YARA → Persistence/artifact detection
· Cloud → Correlation and early signal only
Coverage Integrity
· No over-claimed detection
· No unsupported detection states
· Initial access remains Partially Detected (validated from S26)
S30 Intelligence Maturity Assessment
Detection Maturity
· Endpoint Execution Detection → High
· Command-Line Behavioral Detection → High
· File Artifact Detection → High
· Cloud Telemetry Utilization → Moderate (supporting role)
Control Effectiveness Score
High
Detection strategy provides strong coverage of post-exploitation activity, which is the most reliable detection point given active KEV exploitation.
S31 — Telemetry Dependencies
Purpose
Define the minimum telemetry required to detect post-exploitation activity originating from service-level compromise of externally exposed Microsoft services.
Dependencies
Detection depends on visibility into service-origin execution, process lineage, and outbound communication initiated from application service contexts. Without this visibility, successful exploitation is unlikely to be detected.
Identity Provider Telemetry
Limited primary value for initial detection. May provide supporting context if attacker activity transitions into authenticated operations, but is not a reliable detection source for service-origin compromise.
Endpoint / EDR Telemetry
Critical dependency. Required telemetry includes process creation events, command-line execution, parent-child relationships, and identification of execution originating from application service processes such as IIS worker processes. This is the primary detection surface for identifying post-exploitation activity.
DNS / Web Proxy / Network Telemetry
Required to identify outbound communication initiated by compromised services. Detection relies on identifying service-origin network behavior that deviates from expected application patterns, including anomalous destinations or communication frequency.
Email Security Gateway Telemetry
Not a relevant telemetry source for this threat model. No dependency for initial access or primary detection.
Cloud and SaaS Telemetry
Relevant only if compromised services interact with cloud or SaaS platforms. Provides secondary visibility into post-exploitation activity such as API usage or abnormal service interactions.
Correlation Dependencies
Detection requires correlation between service-origin endpoint execution and outbound network activity. Single-source telemetry is insufficient to confirm compromise with high confidence.
S32 — Detection Limitations
Purpose
Define detection gaps inherent to service-origin exploitation and post-exploitation execution.
Detection Failure Modes
Exploit Execution Blindness
Initial exploitation typically produces minimal or no reliable telemetry, preventing detection at the point of compromise.
Service-Origin Execution Ambiguity
Malicious execution occurs within legitimate service processes, making it difficult to distinguish attacker activity from normal application behavior without detailed process inspection.
Process Lineage Gaps
Lack of parent-child process visibility prevents identification of abnormal execution chains originating from service processes.
Application Layer Logging Limitations
Application logs may not capture sufficient detail to distinguish exploitation from legitimate input processing.
Encrypted Outbound Communication
Command and control traffic may be encrypted, limiting visibility into content and requiring reliance on metadata or behavioral analysis.
Baseline Deficiency
Without established baselines for service behavior, anomalous execution and communication patterns may not be identified.
Impact
Detection is delayed until post-exploitation behavior deviates sufficiently from baseline, increasing the likelihood of persistence and lateral movement before response.
S33 — Defensive Control & Hardening Improvements
Purpose
Define control improvements directly aligned to observed attack behaviors and detection gaps.
Control Improvements
· Enforce strict exposure control for internet-facing Microsoft services, including access restriction and segmentation
· Implement rapid patching processes for externally exposed systems to reduce exploitability window
· Enable full endpoint telemetry with process lineage and command-line visibility
· Monitor and profile service-origin execution behavior to establish baseline and detect anomalies
· Implement outbound network monitoring focused on service-initiated communication patterns
· Establish correlation logic linking endpoint execution with network activity to confirm compromise
Control Impact Mapping
· Exposure control reduces likelihood of initial compromise
· Endpoint telemetry enables detection of service-origin execution behavior
· Behavioral baselining improves anomaly detection accuracy
· Network monitoring increases visibility into command and control activity
· Correlation reduces time-to-detect and increases detection confidence
S34 — Defensive Control & Hardening Architecture
Figure 6
Purpose
Define a detection-focused architecture capable of identifying service-origin compromise across its lifecycle.
Architecture Layers
· Exposure Control Layer
Restricts and segments externally accessible services to reduce attack surface
· Service Execution Visibility Layer
Captures process-level telemetry and identifies execution originating from application service contexts
· Behavioral Analysis Layer
Establishes baselines for service behavior and detects deviations in execution and communication patterns
· Network Observation Layer
Monitors outbound communication initiated by services to identify anomalous connections
· Correlation Layer
Combines endpoint and network signals to produce high-confidence detection of compromise
Architecture Alignment
Each layer must contribute to detecting post-exploitation activity originating from service processes. Detection effectiveness depends on integration across layers rather than isolated control effectiveness.
Architecture Objective
Detect service-origin malicious activity as early as possible after execution begins, minimizing attacker dwell time and limiting progression.
S35 — Defensive Control Mapping Matrix
Purpose
Map defensive controls to the actual attack progression for service-origin exploitation.
Phase 1 — Exploitation of Public-Facing Service
· Exposure reduction and segmentation controls
· Patch management and vulnerability remediation
· External attack surface monitoring
Phase 2 — Service-Origin Execution and Initial Control
· Endpoint telemetry capturing service-linked process execution
· Detection of abnormal command execution within service context
· Behavioral monitoring of execution patterns
Phase 3 — Persistence and Internal Interaction
· Detection of server-side persistence mechanisms
· Monitoring for abnormal system interaction and reconnaissance activity
· Identification of service-origin outbound communication
Assessment
Coverage is weakest at initial exploitation and strongest during service-origin execution and post-exploitation stages. Effective detection depends on endpoint visibility and correlation with network behavior.
S36 — CyberDax Intelligence Maturity Assessment
Purpose
Evaluate organizational ability to detect and respond to service-origin exploitation.
Maturity Evaluation
Organizations with comprehensive endpoint telemetry, process lineage visibility, and integrated network monitoring demonstrate higher detection capability. Environments lacking these capabilities have limited ability to detect compromise until late-stage activity occurs.
Control Effectiveness Score
Moderate, with strong detection potential after execution begins but limited visibility at initial access.
Audit Evidence Statement
Detection capability is supported by endpoint process monitoring and network telemetry, but remains dependent on correlation and behavioral analysis for effectiveness.
Security Program Integration Note
Improving maturity requires integration of endpoint and network telemetry, validation of detection rules against real execution patterns, and continuous tuning based on observed service behavior.
S37 — Strategic Defensive Improvements
Purpose
Define prioritized strategic decisions required to improve defensive posture against this attack model.
Strategic Priorities
· Reduce reliance on exposed services through segmentation and access control
· Prioritize rapid remediation of externally exposed vulnerabilities
· Establish service-execution monitoring as a core detection capability
· Improve correlation across telemetry sources to reduce detection delay
· Validate detection capability through simulation of service-origin attack scenarios
Decision Framework
· Prioritize controls that eliminate exposure before those that detect compromise
· Invest in visibility where detection gaps currently exist
· Focus on reducing time-to-detect after execution begins
· Continuously validate controls against realistic attacker behavior
S38 — Attack Economics & Organizational Impact Model
Purpose
Define the economic characteristics of the attack, explicitly aligned to the validated S6 scenario-based cost model and the operational imbalance between attacker effort and defender cost.
Economic Drivers
· Internet-facing exposure of Microsoft services enabling direct attacker access
· Lack of authentication requirements allowing automated exploitation at scale
· Rapid transition from exploitation to execution within service context
· Detection dependency on post-exploitation behavioral signals rather than exploit visibility
· Access to enterprise collaboration platforms and internally accessible data
Cost Comparison
· Low Impact Scenario (Directly Aligned to S6 Low Scenario)
Limited compromise contained to a small number of externally exposed systems with rapid response and no confirmed lateral movement. Costs reflect incident response, validation, and short-duration operational disruption.
· Moderate Impact Scenario (Directly Aligned to S6 Moderate Scenario)
Compromise of externally exposed services with internal reconnaissance and controlled expansion. Costs reflect forensic investigation, containment, system restoration, and measurable business disruption.
· High Impact Scenario (Directly Aligned to S6 High Scenario)
Enterprise-scale compromise involving persistence and potential data access or operational disruption. Costs reflect full incident response, extended disruption, enterprise remediation, and regulatory exposure.
Adversary ROI
Attackers achieve high return on investment due to low-cost, repeatable exploitation combined with automated discovery of exposed services. Reuse of exploitation techniques and tooling significantly reduces marginal cost per target while maintaining consistent compromise outcomes.
Economic Asymmetry
This attack model creates strong asymmetry where minimal attacker effort produces disproportionately high defensive cost. Organizations must invest in detection, response, and recovery capabilities, while attackers incur negligible incremental cost to scale operations across additional exposed systems.
S39 — Economic Impact & Organizational Exposure
Figure 7
Impact Areas
· Operational Disruption
Compromise of externally exposed Microsoft services can degrade availability and disrupt internal business operations and collaboration workflows
· Data Exposure
Access to internally accessible repositories and collaboration systems increases risk of unauthorized data access or data loss
· Incident Response and Recovery
Costs associated with investigation, containment, eradication, and validation of affected systems
· Compliance and Regulatory Exposure
Potential reporting requirements and penalties depending on data sensitivity and regulatory obligations
· Reputational Impact
Loss of stakeholder confidence resulting from compromise of externally exposed enterprise services
Risk Alignment
· High risk for organizations operating externally exposed Microsoft services
· Risk severity increases with:
o size of external attack surface
o delay in vulnerability remediation
o lack of service-origin detection capability
· Exposure is determined by:
o accessibility of vulnerable services
o maturity of endpoint and network telemetry
o ability to detect and contain post-exploitation activity
S40 — References
Vendor Advisory
· Microsoft Security Update Guide — Security fixes addressing CVE-2026-32201
· hxxps://msrc.microsoft[.]com/update-guide/vulnerability/CVE-2026-32201
· Microsoft Security Update Guide — Security fixes addressing CVE-2026-33825
· hxxps://msrc.microsoft[.]com/update-guide/vulnerability/CVE-2026-33825
Vulnerability Records
· NVD Entry — CVE-2026-32201 vulnerability details and scoring
· hxxps://nvd.nist[.]gov/vuln/detail/CVE-2026-32201
· NVD Entry — CVE-2026-33825 vulnerability details and scoring
· hxxps://nvd.nist[.]gov/vuln/detail/CVE-2026-33825
Known Exploited Vulnerabilities (KEV)
· CISA Known Exploited Vulnerabilities Catalog — Confirmed exploitation listing for CVE-2026-32201
· hxxps://www.cisa[.]gov/known-exploited-vulnerabilities-catalog
Security Vendor Analysis
· CISA Alert — Active exploitation context for Microsoft SharePoint vulnerability CVE-2026-32201
· hxxps://www.cisa[.]gov/news-events/alerts
Analytical Framework
· MITRE ATT&CK Framework — Enterprise behavior mapping
· hxxps://attack.mitre[.]org/
· CyberDax Threat Intelligence Data Model — Internal analytical standard