[CVE] From Foothold to Root: Copy Fail and the Linux Cloud Escalation Risk
Report Type:
[CVE] Threat Intelligence Report
Threat Category:
Local Linux Privilege Escalation / Post-Foothold Exploitation Risk
Assessment Date:
May 1, 2026
Primary Impact Domain:
Privilege Escalation and Host Compromise
Secondary Impact Domains:
Credential Access; Persistence; Container and Kubernetes Node Trust Boundary Exposure; Cloud Identity Abuse; Lateral Movement Preparation; Sensitive Data Exposure
Affected Asset Class:
Linux Servers; Cloud Linux Instances; Kubernetes Worker Nodes; Container Hosts; CI Runners; High-Value Production Linux Workloads
Threat Objective Classification:
Foothold-to-Root Escalation With Post-Compromise Expansion Potential
BLUF
Copy Fail, tracked in this report as CVE-2026-31431, creates material enterprise risk by allowing an attacker with existing local execution on a vulnerable Linux system to escalate from limited foothold to root-level control. The risk is driven by post-foothold exploitation across Linux servers, cloud Linux instances, Kubernetes worker nodes, container hosts, CI runners, and workload infrastructure where root access can expose credentials, runtime sockets, service accounts, cloud identity material, secrets, and production trust boundaries. The threat posture is elevated because successful exploitation can enable credential access, persistence, container or Kubernetes node compromise, cloud metadata access, security-tool tampering, and broader workload expansion. Executive action is required to identify vulnerable Linux assets, prioritize exposed and high-value workloads, accelerate remediation, validate host telemetry, and ensure response teams can detect suspicious local staging, abnormal low-privilege-to-root transition, and post-root activity before enterprise blast radius expands.
Executive Risk Translation
Copy Fail shifts business risk from initial compromise alone to what an attacker can do after gaining unprivileged execution on vulnerable Linux infrastructure. The primary concern is not simply whether a kernel is vulnerable, but whether that vulnerable system supports production workloads, cloud services, Kubernetes nodes, container infrastructure, CI/CD pipelines, privileged automation, or sensitive operational functions. If exploitation occurs on a high-value Linux workload, response may expand into host isolation, credential containment, cloud identity review, Kubernetes and container-runtime investigation, workload rebuilds, forensic preservation, patch verification, and executive incident governance. This creates operational, financial, compliance, cloud, and resilience exposure beyond the first affected host.
S3 Why This Matters Now
· Copy Fail should be treated as a post-foothold local privilege escalation risk, not as a remotely exploitable perimeter event.
· The primary enterprise concern is whether an attacker with unprivileged execution can gain root on vulnerable Linux systems that support production, cloud, Kubernetes, container, or CI/CD workloads.
· Linux systems frequently hold sensitive trust relationships, including SSH material, service credentials, Kubernetes service account tokens, container runtime access, cloud metadata reachability, workload identities, and deployment secrets.
· Successful root escalation can materially increase blast radius by allowing attackers to access sensitive files, tamper with security agents, establish persistence, inspect workload context, and prepare lateral movement.
· Kubernetes worker nodes, container hosts, CI runners, internet-facing Linux workloads, and cloud-hosted Linux instances require elevated prioritization because local root access can affect more than the individual host.
· Vulnerable kernel state alone does not prove exploitation, but it materially increases risk when paired with suspicious local execution, abnormal privilege transition, sensitive file access, or post-root behavior.
· Network-only monitoring is insufficient because the exploit path is local and occurs after code execution has already been obtained.
· Organizations without reliable process ancestry, command-line capture, effective-user context, vulnerable asset inventory, container-to-host mapping, Kubernetes node context, cloud workload context, and telemetry retention face elevated risk of delayed detection and incomplete scoping.
· Static indicators such as proof-of-concept filenames, hashes, CVE strings, or exploit nicknames are useful for supporting triage, but they are insufficient as the durable enterprise detection model.
S4 Key Judgments
· Copy Fail is a local Linux privilege escalation risk that becomes most consequential after an attacker already has unprivileged execution on a vulnerable host.
· The primary business risk is attacker conversion of limited access into root-level control over Linux workloads that support production, cloud, Kubernetes, container, CI/CD, or high-value operational environments.
· The strongest enterprise risk signal is suspicious low-privilege execution followed by abnormal root-owned process creation, privileged binary interaction, sensitive file access, credential access, security-tool tampering, or cloud and Kubernetes trust-boundary abuse.
· Vulnerable Linux kernel exposure should drive patch prioritization and hunt scoping, but it should not be treated as confirmed exploitation without behavioral evidence.
· Direct visibility into AF_ALG, algif_aead, splice-adjacent behavior, or page-cache manipulation may improve confidence, but it should not be required as the only detection path because many enterprise environments will not capture kernel-level telemetry consistently.
· Cloud control-plane telemetry can reveal post-escalation consequences such as credential use, secret retrieval, role activity, metadata-driven identity abuse, snapshot access, or security-control changes, but it cannot directly observe the local kernel exploit primitive.
· Kubernetes and container context materially increases priority because root-level host compromises may expose kubelet paths, service account tokens, runtime sockets, host-mounted secrets, namespaces, and workload credentials.
· Detection must remain behavior-led because proof-of-concept artifacts, filenames, command syntax, staging paths, and exploit implementation details can change.
· Endpoint, Linux audit, SIEM, vulnerability, cloud, Kubernetes, and container telemetry must be correlated to distinguish vulnerable-state exposure from suspected exploitation.
· Executive risk reduction depends on patch acceleration, vulnerable asset prioritization, host-behavior detection, cloud and Kubernetes blast-radius review, credential containment readiness, and validated telemetry coverage.
S5 Executive Risk Summary
Business Risk
Copy Fail can create severe operational and security risk when attackers use local privilege escalation to gain root control on vulnerable Linux systems. Risk increases when affected systems include internet-facing Linux workloads, production servers, Kubernetes worker nodes, container hosts, CI runners, cloud Linux instances, identity-adjacent infrastructure, or systems with access to sensitive credentials, secrets, deployment paths, or business-critical services.
Technical Cause
The risk is driven by a local Linux privilege escalation condition that may allow an attacker with existing unprivileged execution to move into root-level activity. The enterprise detection model should focus on suspicious local exploit staging, writable-path execution, privileged binary interaction, abnormal low-privilege-to-root transition, sensitive file access, post-escalation host behavior, container or Kubernetes node context, and cloud workload identity exposure.
Threat Posture
The threat posture is elevated because successful root escalation can convert a limited host foothold into privileged control over sensitive Linux infrastructure. Attackers may use that access to harvest credentials, inspect cloud metadata, access Kubernetes service account tokens, interact with container runtime sockets, disable security tooling, establish persistence, enumerate the environment, and prepare lateral movement or cloud-control-plane abuse.
Executive Decision Requirement
Executives must require immediate identification and prioritization of vulnerable Linux workloads, accelerated remediation for exposed and high-value systems, and validation that detection coverage can identify exploit staging, privilege transition, and post-root activity. Response leadership should also confirm that cloud, Kubernetes, container, CI/CD, and endpoint teams can coordinate containment, credential review, workload isolation, telemetry preservation, and patch verification.
S6 Executive Cost Summary
Copy Fail creates financial exposure based on the number and criticality of vulnerable Linux systems, whether attackers have obtained local execution, the business role of affected hosts, cloud and Kubernetes blast radius, credential exposure, detection latency, patch speed, telemetry completeness, containment burden, and the degree to which root-level compromise reaches production workloads, cloud identities, container infrastructure, CI/CD systems, or sensitive data stores.
Low Impact Scenario
Rapid assessment confirms vulnerable Linux systems are limited, prioritized patching is completed quickly, and no suspicious local execution, privilege transition, root-owned process activity, sensitive file access, cloud credential use, Kubernetes token access, container runtime interaction, persistence, or lateral movement is observed. Response still requires vulnerability validation, patch verification, targeted hunting, telemetry review, and executive tracking because vulnerable-state exposure on Linux infrastructure can become material when paired with local code execution; estimated impact $750K to $3M.
Moderate Impact Scenario
Suspicious local execution or abnormal privilege behavior is identified on a limited but meaningful set of vulnerable Linux systems, requiring host isolation, forensic review, credential containment, patch validation, vulnerable asset scoping, endpoint and Linux audit review, cloud identity review, Kubernetes or container context review, SOC surge activity, detection tuning, and executive incident coordination. Recovery and containment remain achievable, but confidence depends on determining whether root-level access reached sensitive files, workload credentials, cloud metadata, runtime sockets, CI/CD systems, or production services; estimated impact $5M to $25M.
High Impact Scenario
Confirmed or strongly suspected root escalation affects production Linux workloads, Kubernetes worker nodes, container hosts, CI runners, internet-facing systems, cloud Linux instances, privileged service hosts, or systems with access to sensitive credentials, cloud roles, deployment secrets, regulated data, or business-critical operations. Response may require broad containment, workload rebuilds, credential rotation, cloud-control-plane review, Kubernetes node replacement, container runtime validation, forensic preservation, legal and regulatory assessment, customer assurance, insurance reporting, and board-level incident governance; estimated impact $30M to $150M or higher.
S6A Key Cost Drivers
· Number and criticality of vulnerable Linux servers, cloud Linux instances, Kubernetes worker nodes, container hosts, CI runners, internet-facing workloads, and production systems.
· Whether attackers had local code execution on vulnerable systems before patching or containment.
· Whether suspicious local staging, writable-path execution, privileged binary interaction, abnormal root-owned process creation, sensitive file access, or post-root behavior was observed.
· Whether root-level activity reached credential stores, SSH keys, service credentials, Kubernetes service account tokens, cloud metadata services, managed identity material, host-mounted secrets, or container runtime sockets.
· Time from vulnerable-state identification or suspicious activity to detection, containment, patching, and credential review.
· Availability of process ancestry, command-line telemetry, executable path, working directory, source user, effective user, parent process, Linux audit, file access, and security-agent health data.
· Ability to correlate endpoint, Linux audit, vulnerability management, SIEM, cloud, Kubernetes, container, and identity context.
· Whether affected systems supported production services, customer-facing applications, privileged workloads, CI/CD jobs, build infrastructure, deployment pipelines, or sensitive business operations.
· Scope of Kubernetes review, including node role, namespace sensitivity, service account exposure, kubelet paths, hostPath usage, runtime socket access, and privileged workload context.
· Scope of cloud review, including instance roles, managed identities, metadata access, role assumption, secret retrieval, storage access, snapshot activity, security group changes, and unusual API behavior.
· Need for credential rotation, workload rebuilds, node replacement, container image review, CI runner validation, cloud access review, and forensic preservation.
· Need for legal review, regulatory notification analysis, customer assurance, cyber insurance reporting, executive incident governance, or board-level reporting.
Most Likely Scenario Justification
Moderate scenario is most likely when vulnerable Linux infrastructure includes cloud workloads, Kubernetes nodes, container hosts, CI runners, internet-facing systems, or high-value production servers because even limited suspected exploitation can require significant scoping, patch validation, telemetry reconciliation, credential review, and cross-team coordination. The estimate moves toward the lower end when telemetry confirms no local execution, rapid patching, strong process ancestry, intact agent coverage, no root transition, no sensitive file access, and no cloud or Kubernetes follow-on activity. The estimate moves toward the upper end when affected systems include production workloads, Kubernetes nodes, CI/CD infrastructure, privileged cloud roles, incomplete telemetry, delayed patching, exposed services, sensitive credentials, or evidence of post-root activity.
S6B Compliance and Risk Context
Compliance Exposure Indicator
Moderate to High depending on whether root-level access, credential exposure, cloud identity abuse, Kubernetes token access, production workload compromise, regulated data exposure, operational disruption, or incomplete forensic scoping affected systems subject to regulatory, contractual, customer, or material business obligations.
Risk Register Entry
Risk Title
Copy Fail Linux Privilege Escalation and Cloud Workload Blast-Radius Exposure
Risk Description
Adversaries may exploit vulnerable Linux systems after gaining local execution, escalate from low-privilege access to root, access sensitive files and credentials, interact with container or Kubernetes resources, abuse cloud identity material, impair security tooling, establish persistence, and expand impact across production, cloud, CI/CD, container, or Kubernetes environments.
Likelihood
High.
Impact
Severe.
Risk Rating
Critical.
Annualized Risk Exposure
Estimated $8M to $45M or higher based on vulnerable Linux asset exposure, local code-execution likelihood, production workload dependency, Kubernetes and container footprint, cloud identity privileges, credential concentration, patch latency, detection coverage, telemetry completeness, containment complexity, and regulatory or customer-facing obligations.
S7 Risk Drivers
· Local privilege escalation can convert an existing unprivileged foothold into root-level host control.
· Vulnerable Linux systems may support production services, cloud workloads, container infrastructure, Kubernetes nodes, CI/CD runners, or high-value operational functions.
· Internet-facing workloads and exposed application servers increase the likelihood that attackers can obtain the prerequisite local execution path.
· Kubernetes worker nodes and container hosts create expanded blast radius because root-level access may expose runtime sockets, kubelet material, service account tokens, host-mounted secrets, and workload trust boundaries.
· CI runners and build infrastructure may hold deployment credentials, repository access, artifact credentials, package registry credentials, or cloud automation permissions.
· Cloud Linux instances may expose metadata services, instance roles, managed identities, secret access, storage permissions, or control-plane paths after host compromise.
· Missing command-line capture weakens exploit staging detection.
· Missing process ancestry weakens abnormal low-privilege-to-root transition detection.
· Missing effective-user or UID transition context weakens privilege boundary analysis.
· Missing vulnerable asset inventory prevents reliable prioritization of exposed and high-value Linux systems.
· Missing container-to-host, Kubernetes node, pod, namespace, service account, or runtime context weakens blast-radius assessment.
· Missing cloud role, workload ownership, asset criticality, exposure, or identity context weakens prioritization and containment.
· Missing Linux audit, file access, or security-agent health telemetry can delay identification of sensitive file access, credential exposure, tool tampering, or visibility gaps.
· Over-reliance on CVE strings, exploit filenames, proof-of-concept artifacts, hashes, network alerts, or vulnerable-state exposure can miss behavior changes and delay recognition of exploitation.
S8 Bottom Line for Executives
Copy Fail should be treated as a high-priority Linux privilege escalation and cloud workload resilience risk because it can allow attackers to convert limited local execution into root-level control on vulnerable systems. The key executive concern is not only whether vulnerable kernels exist, but whether exposed or high-value Linux workloads can be abused after compromise to access credentials, Kubernetes trust boundaries, container runtime resources, cloud identity material, or production services. Risk reduction depends on rapid vulnerable asset identification, prioritized patching, validated endpoint and Linux audit telemetry, host-behavior detection, cloud and Kubernetes context enrichment, and response workflows that isolate affected hosts before root-level activity expands. Organizations should prioritize this report as an infrastructure trust and blast-radius issue because root compromise on Linux workloads can create operational disruption, credential exposure, cloud-control-plane risk, compliance uncertainty, and board-level incident governance requirements.
S9 Board-Level Takeaway
Copy Fail turns vulnerable Linux infrastructure into a post-foothold escalation path that can materially increase enterprise blast radius. The board-level risk is that attackers may move from limited execution to root-level control on systems that support cloud workloads, Kubernetes nodes, container hosts, CI/CD infrastructure, production services, and sensitive credential paths. Leadership should require evidence that vulnerable Linux assets have been identified, exposed and high-value workloads have been prioritized, patching is progressing, host telemetry is reliable, and response teams can detect abnormal privilege transition and post-root activity. This report supports governance decisions around Linux infrastructure risk, cloud workload protection, Kubernetes and container security, credential containment, exposure management, telemetry readiness, and executive oversight of privilege escalation risk.
Figure 2
S10 Vulnerability Overview
Copy Fail, tracked as CVE-2026-31431, is a high-severity local Linux privilege escalation vulnerability that allows an unprivileged local user to escalate to root on affected Linux systems. Microsoft assesses the vulnerability as affecting major Linux distributions, including Red Hat, SUSE, Ubuntu, and AWS Linux, with significant relevance to cloud Linux workloads and Kubernetes environments.
Copy Fail is not a standalone remote-entry condition. The vulnerability becomes operationally significant after an attacker has already obtained local execution on a vulnerable Linux host through another access path, such as compromised credentials, exposed application compromise, malicious workload execution, CI job abuse, container foothold, SSH access, or another vulnerability. The enterprise significance comes from the attacker’s ability to convert limited local execution into root-level host control.
The highest-risk environments are Linux systems that support cloud workloads, Kubernetes nodes, container infrastructure, CI runners, internet-facing applications, production services, privileged automation, or sensitive operational functions. In these environments, successful root escalation can expose credentials, runtime sockets, service account material, host-mounted secrets, workload identities, cloud metadata paths, and production trust boundaries.
Vulnerability Class
· Local Linux privilege escalation.
· Post-foothold root escalation.
· Linux kernel cryptographic subsystem abuse.
· Page-cache and privileged binary abuse.
· Host trust-boundary compromise.
· Cloud workload and Kubernetes node blast-radius amplifier.
Primary Risk Condition
The primary risk condition exists when an attacker has local code execution on a vulnerable Linux host and can abuse Copy Fail to gain root-level control. This condition is most consequential when the host supports production workloads, exposed services, privileged automation, container orchestration, CI/CD activity, cloud identity permissions, or sensitive operational data.
Enterprise Impact Model
Copy Fail should be treated as an infrastructure trust risk rather than a standalone endpoint event. Successful exploitation can allow an attacker to move from limited execution to privileged host control, access sensitive files, collect credentials, inspect workload context, tamper with security tooling, interact with container or Kubernetes resources, and prepare cloud or lateral movement activity.
Detection and Response Relevance
The vulnerability requires host-centered detection and response. Network telemetry can support broader compromise context, but it cannot directly confirm the local privilege escalation path. Detection should prioritize exploit staging, suspicious execution from writable paths, abnormal low-privilege-to-root transition, privileged binary interaction, sensitive file access, post-root behavior, cloud workload context, and Kubernetes or container context.
S11 Technical Vulnerability Details
Copy Fail affects the Linux kernel cryptographic subsystem through a logic flaw in the algif_aead module of the AF_ALG userspace crypto API. Microsoft reports that the flaw can be abused through interaction between AF_ALG and the splice system call to perform a controlled four-byte write into the kernel page cache of a readable file.
The practical exploit consequence is corruption of the in-memory representation of privileged binaries without necessarily modifying the on-disk file. Public technical reporting describes this as a page-cache corruption path that can affect SUID-root binaries and produce root-level privilege escalation.
Technical Scope
· The vulnerability affects Linux systems running vulnerable kernels before patched versions or mitigations are applied.
· Exploitation requires local execution as a non-privileged user.
· The attack path is local and host-centered.
· The practical security outcome is escalation from unprivileged or constrained execution into root-level control.
· The highest enterprise consequence occurs when root control is obtained on cloud, Kubernetes, container, CI/CD, or production Linux infrastructure.
Relevant Technical Concepts
· AF_ALG and algif_aead activity may provide high-value technical evidence where syscall, audit, EDR kernel, or eBPF telemetry is available.
· Splice-adjacent behavior may provide supporting evidence where host telemetry can capture the relevant file, memory, or kernel-interface activity.
· Page-cache manipulation is relevant because in-memory modification may not produce the same evidence pattern as durable on-disk file modification.
· SUID-root and privileged binary interaction are relevant because successful exploitation can involve corruption or abuse of privileged execution paths.
· Root-owned child process creation, sensitive file access, credential discovery, and security-tool tampering are stronger enterprise response signals than static exploit artifact discovery alone.
Operational Constraints
Direct kernel-primitive visibility should be treated as conditional. Many enterprise environments do not consistently capture AF_ALG, algif_aead, splice, page-cache, or syscall-level activity at sufficient fidelity for reliable production detection. Because of this, the report prioritizes behavior-led detection around local staging, privilege transition, post-root activity, and workload context.
Enterprise Interpretation
Technical exploit details are important for validation and forensic analysis, but the executive and operational risk model should focus on the root-transition outcome. The key enterprise question is whether a vulnerable Linux host with local attacker execution can become a privileged launch point into credentials, workloads, cloud identity, container resources, Kubernetes node trust, or production services.
S12 Exploitability Assessment
Copy Fail is exploitable when an attacker has local code execution on a vulnerable Linux system. Microsoft reports a working exploit in the wild and highlights the urgency of detecting, prioritizing, and remediating affected Linux workloads.
Exploitability Rating
High for attackers who already have local execution on a vulnerable Linux host.
Initial Access Dependency
Copy Fail depends on a prior foothold. Likely prerequisite access paths include compromised web applications, exposed services, stolen credentials, SSH access, malicious CI jobs, compromised containers, workload execution, developer access abuse, or another vulnerability that enables local code execution.
Privilege Escalation Value
The vulnerability is valuable because it may allow attackers to convert limited access into root-level control. This is a high-impact transition on Linux systems that host sensitive workloads, cloud identities, container runtime access, Kubernetes node resources, production services, or CI/CD execution paths.
Attacker Practicality
· Attackers do not need domain-level access to benefit from the vulnerability if they can execute locally on a vulnerable Linux host.
· Public proof-of-concept availability lowers operational friction for opportunistic exploitation once a foothold exists.
· The vulnerability is more attractive when the target host is internet-facing, cloud-hosted, production-critical, Kubernetes-adjacent, container-hosted, or CI/CD-related.
· The exploit path is more useful to attackers when local root access exposes credentials, tokens, secrets, metadata services, runtime sockets, or privileged automation.
· Exploit reliability, distribution-specific behavior, kernel version differences, mitigation state, and environmental hardening should be validated during defensive testing.
Enterprise Exploitability Factors
· Vulnerable kernel version and patch state.
· Exposure of Linux workloads to initial access paths.
· Presence of cloud metadata access, managed identity material, or instance roles.
· Presence of Kubernetes worker-node context, kubelet paths, service account tokens, runtime sockets, or host-mounted secrets.
· Presence of CI/CD credentials, deployment keys, build secrets, or package-registry access.
· Availability of security controls that can detect local staging and privilege transition.
· Ability to rapidly isolate affected systems and preserve forensic telemetry.
Exploitability Boundary
Vulnerable state alone is not exploitation evidence. Confirmed or suspected exploitation requires behavioral evidence such as suspicious local execution, abnormal privilege transition, root-owned process creation, sensitive file access, security-tool tampering, cloud identity abuse, Kubernetes interaction, or container follow-on activity.
S13 KEV Status and Patch Availability
KEV Status
CVE-2026-31431 is listed in the CISA Known Exploited Vulnerabilities catalog and should be treated as an urgent exploited-vulnerability management priority. Microsoft reports that a working exploit is already in the wild, increasing the likelihood of broader exploitation attempts against vulnerable Linux systems.
Patch Availability
Patch availability and mitigation status are distribution-specific. Microsoft reports that affected systems include major Linux distributions such as Red Hat, SUSE, Ubuntu, and AWS Linux, while public vulnerability reporting identifies broader Linux ecosystem exposure and available patch or mitigation activity across major distributions.
Patch and mitigation status must be validated against the affected Linux distribution, kernel package stream, cloud image source, container host baseline, Kubernetes node image, and vendor-maintained kernel channel. Linux patch state should not be inferred only from asset inventory or package naming; it should be confirmed through vulnerability management, kernel version validation, package state, reboot status, live-patch status where applicable, and host inventory reconciliation.
Remediation Priority
· Highest priority should be assigned to vulnerable internet-facing Linux workloads.
· Highest priority should be assigned to vulnerable Kubernetes worker nodes, container hosts, and CI runners.
· Highest priority should be assigned to vulnerable systems with privileged cloud roles, managed identities, deployment credentials, or access to sensitive secrets.
· Highest priority should be assigned to vulnerable production systems, high-value operational systems, and systems that support customer-facing services.
· Medium priority should be assigned to vulnerable internal Linux systems without exposed access paths but with sensitive local credentials, administrative reach, or workload trust.
· Lower priority should be assigned to vulnerable systems with no meaningful local execution exposure, no production role, no sensitive credentials, and rapid patch eligibility, while still tracking them through remediation.
Patch Validation Requirements
· Confirm affected kernel version and Linux distribution.
· Confirm package update status.
· Confirm reboot, live-patch, or mitigation effectiveness where applicable.
· Confirm cloud image, golden image, container-host, and Kubernetes node baseline updates.
· Confirm autoscaling groups, node pools, CI runner images, and ephemeral workload images are updated.
· Confirm vulnerability scanner findings are not stale, suppressed, archived, or disconnected from current host state.
· Confirm compensating controls remain active while patching is incomplete.
Operational Guidance
Patch management must be paired with hunting. If a system was vulnerable during the exposure window, defenders should review local execution, privilege transition, root-owned process creation, sensitive file access, credential access, cloud metadata interaction, Kubernetes token access, container runtime access, and security-tool tampering before treating remediation as complete.
S14 Sectors / Countries Affected
Sectors Affected
· Technology and SaaS.
· Cloud Service Providers and Cloud-Hosted Enterprises.
· Financial Services.
· Government and Public Sector.
· Healthcare and Life Sciences.
· Telecommunications and Managed Service Providers.
· Energy, Manufacturing, and Industrial Organizations.
· Education and Research.
· Retail, Logistics, and Business Services.
Countries Affected
· Global
Exposure Rationale
Exposure is global due to widespread enterprise use of Linux across cloud workloads, Kubernetes worker nodes, container hosts, CI/CD runners, internet-facing application servers, production systems, and high-value infrastructure. Risk is highest where vulnerable Linux systems support exposed services, privileged cloud roles, workload identities, Kubernetes node trust, container runtime access, deployment pipelines, or sensitive operational data.
S15 Adversary Capability Profiling
Copy Fail is most useful to adversaries that can already obtain local execution on Linux systems and want to escalate privileges to root. The vulnerability is not primarily valuable as an initial-access tool; it is valuable as a post-foothold escalation mechanism that can increase control, credential access, persistence options, and cloud or workload expansion potential.
Likely Adversary Users
· Opportunistic exploit operators seeking root access after compromising Linux servers.
· Ransomware and extortion operators seeking privileged control over Linux workloads, backups, cloud systems, or virtualization-adjacent infrastructure.
· Cloud-focused intrusion operators seeking access to metadata services, managed identities, workload credentials, or control-plane opportunities.
· Container and Kubernetes-focused attackers seeking node-level control, runtime socket access, kubelet material, service account tokens, or host-mounted secrets.
· CI/CD and supply-chain attackers seeking build secrets, deployment credentials, artifact access, or repository-connected infrastructure.
· Espionage-oriented operators seeking persistence, credential access, privileged reconnaissance, and stealthy expansion from Linux infrastructure.
Capability Requirements
· Ability to obtain local execution on a vulnerable Linux system.
· Ability to stage and execute local exploit code or public proof-of-concept material.
· Ability to adapt execution paths to Linux distribution, kernel version, host hardening, endpoint controls, and runtime constraints.
· Ability to convert root-level access into credential access, discovery, persistence, defense evasion, cloud identity abuse, container access, Kubernetes interaction, or lateral movement.
· Ability to avoid or withstand endpoint, audit, eBPF, SIEM, cloud, container, and Kubernetes detection paths.
Capability Assessment
· Low-capability actors may use public proof-of-concept code or lightly modified exploit artifacts after gaining local execution.
· Moderate-capability actors may modify filenames, staging paths, script wrappers, binary names, command syntax, and execution locations to avoid simple artifact detection.
· High-capability actors may integrate Copy Fail into multi-stage intrusions, target Kubernetes or cloud infrastructure, use stealthier local staging, suppress telemetry, avoid static indicators, and rapidly convert root access into cloud or workload expansion.
TTP Continuity Anchor
· Local execution must exist before Copy Fail becomes relevant.
· Exploit staging may occur from writable or user-controlled host paths.
· Privilege escalation centers on the low-privilege-to-root transition.
· Post-root activity may include credential access, defense evasion, container or Kubernetes interaction, cloud identity access, persistence, lateral movement preparation, or operational impact.
· S20 should expand these behaviors into the full Tactics, Techniques, and Procedures section without duplicating the MITRE chain-flow structure from S17.
Adversary Limitation
Copy Fail does not remove the need for initial access. Attackers must still obtain a foothold before using the vulnerability. This makes exposure management, initial-access hardening, endpoint telemetry, workload isolation, and rapid patching central to risk reduction.
S16 Targeting Probability Assessment
Overall Targeting Probability
High for organizations with vulnerable Linux systems that are exposed, cloud-hosted, production-critical, Kubernetes-adjacent, container-hosted, CI/CD-connected, or credential-rich.
Highest Probability Targets
· Internet-facing Linux application servers where attackers can obtain local code execution through web shells, application flaws, stolen credentials, or exposed services.
· Cloud Linux instances with instance roles, managed identities, metadata access, secrets, or production workload permissions.
· Kubernetes worker nodes that host sensitive workloads, privileged pods, hostPath mounts, runtime socket exposure, or service account material.
· Container hosts where root-level host compromise can expose runtime sockets, host-mounted secrets, images, volumes, or workload credentials.
· CI runners and build systems that contain deployment secrets, source-code access, artifact credentials, cloud permissions, or package-registry tokens.
· Production Linux systems supporting customer-facing services, regulated data processing, business-critical applications, or high-value operational functions.
· Developer, engineering, or administrative Linux systems with privileged access to cloud, source-code, deployment, or operational environments.
Moderate Probability Targets
· Internal Linux servers with sensitive credentials, administrative reach, shared service functions, or delayed patch cycles.
· Linux systems in segmented environments where local execution is harder to obtain but root access would materially increase impact.
· Research, lab, development, or staging Linux systems that connect to production-like credentials, CI/CD workflows, or cloud services.
Lower Probability Targets
· Isolated Linux systems with no meaningful local execution exposure, no sensitive credentials, no cloud role, no production function, strong patch cadence, and limited connectivity.
· Ephemeral systems that are rapidly rebuilt from patched images and lack persistent credentials or privileged workload context.
Targeting Drivers
· Public proof-of-concept availability and technical write-ups.
· Presence of vulnerable kernels on exposed or high-value Linux workloads.
· Delay between patch availability and operational remediation.
· Concentration of credentials, secrets, or cloud identity material on vulnerable hosts.
· Kubernetes, container, and CI/CD adoption without strong host telemetry.
· Weak process ancestry, command-line capture, audit coverage, and telemetry retention.
· Business value of affected workloads and expected response delay.
Targeting Boundary
Targeting probability should not be treated as confirmed exploitation in any specific environment. Confirmed targeting requires observed intrusion activity, suspicious staging, abnormal root transition, post-root behavior, cloud identity abuse, Kubernetes or container access, or other corroborating telemetry.
S17 MITRE ATT&CK Chain Flow Mapping
Only local execution and privilege escalation are directly required for Copy Fail exploitation. Initial foothold and post-root stages are included to show how the vulnerability fits into a realistic enterprise attack path, but post-escalation activity remains conditional on attacker objectives, host role, and available credentials or workload trust.
Stage 1: Prerequisite Foothold
The adversary obtains local execution or an authenticated operating position on a vulnerable Linux host. Copy Fail is not the initial access mechanism; it becomes relevant only after local execution exists.
· T1059 — Command and Scripting Interpreter
· T1078 — Valid Accounts
· T1190 — Exploit Public-Facing Application
Stage 2: Local Exploit Staging
The adversary stages exploit material, scripts, compiled binaries, or supporting tooling from writable or user-controlled locations on the vulnerable host.
· T1059 — Command and Scripting Interpreter
· T1105 — Ingress Tool Transfer
Stage 3: Privilege Escalation
The adversary abuses Copy Fail to transition from low-privilege execution to root-level control.
· T1068 — Exploitation for Privilege Escalation
Stage 4: Post-Root Defense Evasion
After root-level control is obtained, the adversary may impair endpoint, audit, cloud-agent, or container-security visibility to reduce detection and containment confidence.
· T1562.001 — Impair Defenses: Disable or Modify Tools
Stage 5: Credential and Trust Access
The adversary may access local credentials, SSH material, service credentials, Kubernetes tokens, cloud identity material, runtime sockets, or host-mounted secrets available from the compromised system.
· T1552 — Unsecured Credentials
· T1552.004 — Private Keys
· T1552.005 — Cloud Instance Metadata API
Stage 6: Expansion or Impact
If usable credentials, tokens, runtime sockets, cloud roles, or Kubernetes trust relationships are exposed, the adversary may expand into additional systems, workloads, cluster resources, or cloud-control-plane activity. Operational impact depends on host role and business criticality.
· T1021 — Remote Services
· T1078 — Valid Accounts
· T1489 — Service Stop
S18 Attack Path Narrative (Signal-Aligned Execution Flow)
Attack Path Purpose
Copy Fail is best understood as a post-foothold escalation path. The attacker must first obtain local execution or an authenticated operating position on a vulnerable Linux host. The critical attack transition occurs when that limited foothold is converted into root-level control, creating downstream risk to credentials, Kubernetes trust boundaries, container runtime resources, cloud identity material, CI/CD secrets, and production workload integrity.
Stage 1: Prerequisite Local Execution
The attacker begins from an existing foothold on a vulnerable Linux system. This may originate from exposed application compromise, stolen credentials, SSH access, malicious workload execution, container foothold, CI runner abuse, developer access misuse, or another vulnerability that provides local code execution.
Signal Alignment
· Local execution by a non-root user, service account, application account, workload identity, container process, or CI runner.
· Process creation from an exposed service, interactive shell, container process, CI workspace, or workload-controlled path.
· Host context showing vulnerable kernel state, cloud workload role, Kubernetes node role, container-host role, CI runner function, or production workload ownership.
· Vulnerable state alone should not be treated as exploitation evidence.
Stage 2: Local Exploit Staging
After obtaining execution, the attacker stages exploit material or supporting tooling on the host. Staging is most likely to appear in writable, transient, or user-controlled locations because the attacker usually lacks privileged write access before escalation.
Signal Alignment
· Execution from /tmp, /var/tmp, /dev/shm, user home directories, CI workspaces, build directories, mounted workload paths, or container writable layers.
· Use of shells, scripting engines, compiled temporary binaries, build tools, or unknown local executables.
· Rapid file creation, execution, permission change, or deletion in writable paths.
· Suspicious activity by non-root users, application users, service accounts, workload identities, or CI users.
· Higher priority when staging occurs on vulnerable Linux hosts that are internet-facing, cloud-hosted, Kubernetes-adjacent, container-hosted, or CI/CD-connected.
Stage 3: Privilege Transition
The attacker attempts to abuse the Copy Fail condition to move from low-privilege execution into root-level control. Technical evidence may include AF_ALG, algif_aead, splice-adjacent behavior, page-cache interaction, or privileged binary manipulation where telemetry supports it. In many environments, the more realistic signal is the privilege-transition outcome rather than direct observation of the kernel primitive.
Signal Alignment
· Abnormal low-privilege-to-root process transition.
· Root-owned process creation from suspicious low-privilege parentage.
· Privileged binary interaction from writable paths, scripting engines, CI contexts, application users, or container contexts.
· Unusual SUID-root or privileged utility activity outside expected administrative workflows.
· Conditional high-fidelity evidence involving AF_ALG, algif_aead, splice-adjacent activity, or page-cache behavior where syscall, audit, EDR kernel, or eBPF telemetry is available.
· Stronger confidence when privilege transition aligns with vulnerable host state and prior exploit staging.
Stage 4: Root-Level Host Control
If escalation succeeds, the attacker gains root-level process execution or equivalent privileged host control. This is the primary enterprise risk transition because the attacker can now access sensitive files, inspect the host, interact with workload resources, and weaken security visibility.
Signal Alignment
· Root-owned shell, command interpreter, or privileged child process creation from suspicious parentage.
· Root execution of discovery commands, file access utilities, credential access commands, network tools, or persistence-related utilities.
· Root-level access to sensitive paths, service credentials, SSH material, local credential stores, Kubernetes paths, runtime sockets, or host-mounted secrets.
· Security agent, audit service, cloud agent, vulnerability scanner, or container security tool tampering.
· Increased priority on production servers, cloud Linux instances, Kubernetes worker nodes, container hosts, CI runners, and internet-facing systems.
Stage 5: Credential and Trust Material Access
After gaining root, the attacker may attempt to collect credentials or trust material that allows expansion beyond the original host. This stage connects local Linux privilege escalation to cloud, Kubernetes, container, CI/CD, and enterprise identity risk.
Signal Alignment
· Access to /etc/shadow, /etc/sudoers, SSH private keys, service credentials, application secrets, or local credential stores.
· Access to Kubernetes service account tokens, kubelet paths, node credentials, namespace material, or host-mounted secrets.
· Interaction with container runtime sockets such as Docker, containerd, or CRI-related sockets.
· Access to cloud metadata services, managed identity endpoints, instance role credentials, deployment secrets, or workload identity material.
· Suspicious use of retrieved credentials in cloud, Kubernetes, SSH, repository, CI/CD, or workload contexts.
Stage 6: Expansion, Persistence, or Impact
Post-root activity depends on attacker objective and host role. The attacker may establish persistence, impair controls, move laterally, abuse cloud or Kubernetes trust, disrupt services, or use the host as a launch point into additional systems.
Signal Alignment
· Creation or modification of cron jobs, systemd units, SSH authorized keys, shell profiles, privileged services, or startup scripts.
· Disabling or weakening audit logging, endpoint security, cloud agents, container security tools, or vulnerability management agents.
· Remote access attempts, SSH use, role assumption, secret retrieval, snapshot access, storage access, security group modification, or unusual cloud API activity.
· Interaction with Kubernetes node resources, runtime sockets, host namespaces, service account material, or cluster resources.
· Service interruption, workload disruption, data access, operational degradation, or broader blast-radius expansion from the compromised host.
S19 Attack Chain Risk Amplification Summary
Risk Amplification Overview
Copy Fail amplifies enterprise risk because it can convert an existing local foothold into root-level control on Linux infrastructure that may hold credentials, cloud identity material, Kubernetes trust relationships, container runtime access, CI/CD secrets, or production workload authority. The vulnerability is not the initial access event, but it materially increases the value of any foothold obtained on a vulnerable Linux system.
Amplification Factor 1: Foothold Becomes Root Control
A low-privilege shell, service account, container process, CI job, or application execution context may become root-level host control if the system is vulnerable and exploitation succeeds. This increases attacker authority, expands available actions, and weakens assumptions that user-level containment is sufficient.
Business Effect
· Limited compromise can become privileged host compromise.
· Host isolation and credential review become more urgent.
· Response scope may expand beyond the initial user, process, container, or workload context.
Amplification Factor 2: Linux Hosts Often Carry High-Value Trust
Linux servers frequently support production applications, cloud workloads, Kubernetes nodes, container runtimes, CI/CD systems, automation paths, and sensitive service functions. Root access on these systems can expose more than local files; it can expose trust relationships that connect to broader enterprise infrastructure.
Business Effect
· Credential exposure may extend into cloud, Kubernetes, CI/CD, and operational environments.
· Production workload trust may require validation.
· Security teams may need to review host, cloud, container, Kubernetes, and identity activity together.
Amplification Factor 3: Cloud and Kubernetes Context Increase Blast Radius
Root compromise on a Kubernetes worker node, container host, or cloud Linux instance can expose runtime sockets, host-mounted secrets, service account material, cloud metadata credentials, managed identities, and workload-specific trust paths. This can turn host compromise into cluster, account, subscription, project, or workload expansion.
Business Effect
· A single host may become a bridge into cloud or cluster resources.
· Kubernetes node replacement, workload rescheduling, secret rotation, and cloud identity review may be required.
· Cloud-control-plane activity may become part of the incident even though the exploit itself is local.
Amplification Factor 4: CI/CD and Build Infrastructure Raise Supply-Chain Risk
If Copy Fail is exploited on CI runners, build systems, release hosts, or developer infrastructure, root access may expose deployment credentials, repository tokens, artifact credentials, cloud permissions, signing material, or package registry access.
Business Effect
· Incident scope may expand into software delivery assurance.
· Credential rotation may involve repositories, package registries, deployment platforms, and cloud services.
· Build outputs, runner images, and automation paths may require validation.
Amplification Factor 5: Telemetry Gaps Delay Confidence
Many organizations lack consistent visibility into Linux process ancestry, effective user transitions, writable-path execution, kernel-interface behavior, sensitive file access, container-to-host mapping, Kubernetes node context, and cloud workload identity. These gaps can delay confirmation of exploitation and increase the cost of scoping.
Business Effect
· Response teams may need broader forensic review.
· Vulnerable systems may need containment even without direct exploit-primitive evidence.
· Incomplete telemetry can increase legal, operational, and governance uncertainty.
Amplification Factor 6: Vulnerable State Can Be Misread
Vulnerable kernel state is an exposure signal, not exploitation evidence. The opposite mistake is also dangerous: absence of direct AF_ALG, algif_aead, splice, or page-cache telemetry does not prove exploitation did not occur. The strongest risk assessment requires correlation between vulnerable state, local staging, privilege transition, and post-root behavior.
Business Effect
· Overstating vulnerable inventory as confirmed exploitation can waste response effort.
· Understating suspicious behavior because kernel telemetry is absent can miss compromise.
· Executive reporting must distinguish exposure, suspected exploitation, and confirmed post-root activity.
Residual Attack Chain Position
The most consequential Copy Fail scenario is not simple vulnerability exposure. The highest-risk scenario is a vulnerable Linux workload where an attacker already has local execution, stages exploit material, obtains root, accesses credential or trust material, and uses that access to expand into cloud, Kubernetes, container, CI/CD, production, or identity-connected systems.
Figure 3
S20 Tactics, Techniques, and Procedures
TTP Purpose
This section defines the attacker behaviors most relevant to Copy Fail exploitation and post-escalation activity. It does not repeat the ordered MITRE chain flow from S17. Instead, it groups the practical tactics, techniques, and procedures defenders should hunt for across Linux host telemetry, vulnerability context, cloud workload telemetry, Kubernetes context, container telemetry, CI/CD infrastructure, and identity activity.
TTP 1: Prerequisite Local Execution
Tactic
Execution.
Techniques
Command and Scripting Interpreter, Valid Accounts, Exploit Public-Facing Application.
Procedure
The attacker must first obtain local execution or an authenticated operating position on a vulnerable Linux host before Copy Fail becomes relevant. This may occur through compromised credentials, SSH access, exposed application compromise, malicious workload execution, container foothold, CI job abuse, developer access misuse, or another vulnerability that enables local code execution.
Defensive Relevance
This behavior should be evaluated against vulnerable Linux assets, especially when execution originates from non-root users, service accounts, application accounts, workload identities, CI users, container processes, exposed services, or unexpected interactive sessions. Vulnerable state alone is not exploitation evidence; it becomes materially more important when paired with suspicious local execution.
TTP 2: Writable-Path Exploit Staging
Tactic
Execution.
Techniques
Command and Scripting Interpreter, Ingress Tool Transfer.
Procedure
The attacker may stage exploit code, scripts, compiled binaries, or supporting tooling in writable or user-controlled locations before attempting privilege escalation. Likely staging locations include /tmp, /var/tmp, /dev/shm, user home directories, CI workspaces, build directories, mounted workload paths, and container writable layers. Tooling may be renamed, minimized, embedded, recompiled, or executed through common shells, scripting engines, build tools, or temporary binaries to avoid simple artifact detection.
Defensive Relevance
Writable-path execution should be prioritized when it occurs on vulnerable Linux systems, internet-facing workloads, cloud Linux instances, Kubernetes worker nodes, container hosts, CI runners, or production systems. The strongest signals include suspicious process ancestry, non-administrative user context, executable path anomalies, command-line activity, rapid file creation and execution, and follow-on privilege-transition behavior.
TTP 3: Copy Fail Privilege Escalation
Tactic
Privilege Escalation.
Techniques
Exploitation for Privilege Escalation, Abuse Elevation Control Mechanism.
Procedure
The attacker abuses Copy Fail to transition from low-privilege execution to root-level control. The exploit path may involve AF_ALG, algif_aead, splice-adjacent behavior, page-cache manipulation, and privileged binary interaction, depending on exploit implementation and available telemetry. Direct kernel-primitive visibility is useful but should not be assumed in enterprise environments.
Defensive Relevance
The most practical enterprise signal is the outcome sequence: suspicious local staging followed by abnormal low-privilege-to-root transition, root-owned process creation, privileged binary interaction, or unexpected root shell activity. Confidence increases when these behaviors occur on a vulnerable Linux host and do not align with approved administrative workflows.
TTP 4: Root-Level Host Control
Tactic
Privilege Escalation, Discovery, Defense Evasion.
Techniques
Exploitation for Privilege Escalation, System Information Discovery, File and Directory Discovery, Impair Defenses.
Procedure
After successful escalation, the attacker may operate with root-level authority on the compromised host. Root control may enable host discovery, sensitive file access, privileged command execution, process inspection, security-control tampering, and interaction with workload resources that were not accessible from the original low-privilege context.
Defensive Relevance
Root-owned process creation from suspicious parentage should be treated as a high-priority signal when it follows writable-path execution or occurs on a vulnerable host. Analysts should review root shell creation, unexpected privileged child processes, discovery commands, sensitive path access, audit changes, security-agent tampering, and abnormal activity on Kubernetes nodes, container hosts, CI runners, cloud Linux instances, and production servers.
TTP 5: Credential and Trust Material Access
Tactic
Credential Access, Discovery.
Techniques
Unsecured Credentials, Private Keys, OS Credential Dumping, Cloud Instance Metadata API.
Procedure
With root-level access, the attacker may attempt to collect local credentials, SSH private keys, service credentials, application secrets, /etc/shadow, /etc/sudoers, Kubernetes service account tokens, cloud metadata credentials, managed identity material, host-mounted secrets, container runtime material, CI/CD secrets, deployment credentials, or other trust material available from the compromised system.
Defensive Relevance
Sensitive file and credential access should be correlated with prior staging, privilege transition, vulnerable host state, source process, effective user, host role, and workload context. Backup tools, monitoring agents, vulnerability scanners, and approved administrative workflows may overlap with portions of this behavior and require tuning, but sensitive access after suspicious privilege transition should remain a high-priority investigation path.
TTP 6: Cloud, Kubernetes, Container, and CI/CD Expansion
Tactic
Credential Access, Discovery, Lateral Movement.
Techniques
Valid Accounts, Use Alternate Authentication Material, Remote Services, Container and Resource Discovery.
Procedure
The attacker may use root access and collected trust material to expand beyond the original Linux host. Expansion paths may include SSH movement, cloud role or managed identity abuse, cloud API activity, Kubernetes token use, kubelet or node-resource access, container runtime socket interaction, host namespace access, CI/CD secret use, deployment credential abuse, repository access, package registry access, or workload-to-host trust-boundary abuse.
Defensive Relevance
Expansion activity should be reviewed across endpoint, cloud, Kubernetes, container, identity, CI/CD, and network telemetry. The strongest linkage is suspicious credential, token, role, runtime socket, or cloud API use after root escalation on a vulnerable Linux host. Cloud-control-plane activity should be treated as post-compromise evidence, not direct observation of the local kernel exploit primitive.
TTP 7: Defense Evasion, Persistence, or Impact
Tactic
Defense Evasion, Persistence, Impact.
Techniques
Impair Defenses, Create or Modify System Process, Boot or Logon Initialization Scripts, SSH Authorized Keys, Service Stop.
Procedure
After root escalation, the attacker may attempt to preserve access, reduce visibility, or create operational impact depending on objectives and host role. Possible actions include disabling audit logging, impairing EDR or cloud agents, tampering with container security tools, stopping vulnerability scanners, modifying telemetry forwarding, adding SSH keys, changing cron jobs, creating or modifying systemd units, altering shell profiles, modifying privileged services, stopping services, or disrupting workloads.
Defensive Relevance
Defense evasion, persistence, or impact should be prioritized when it occurs shortly after suspicious local execution, root-owned process creation, credential access, or cloud and Kubernetes trust access on a vulnerable Linux system. Impact should only be asserted when supported by observed service disruption, destructive activity, workload interruption, control-plane abuse, or measurable business-process degradation.
Defensive TTP Model
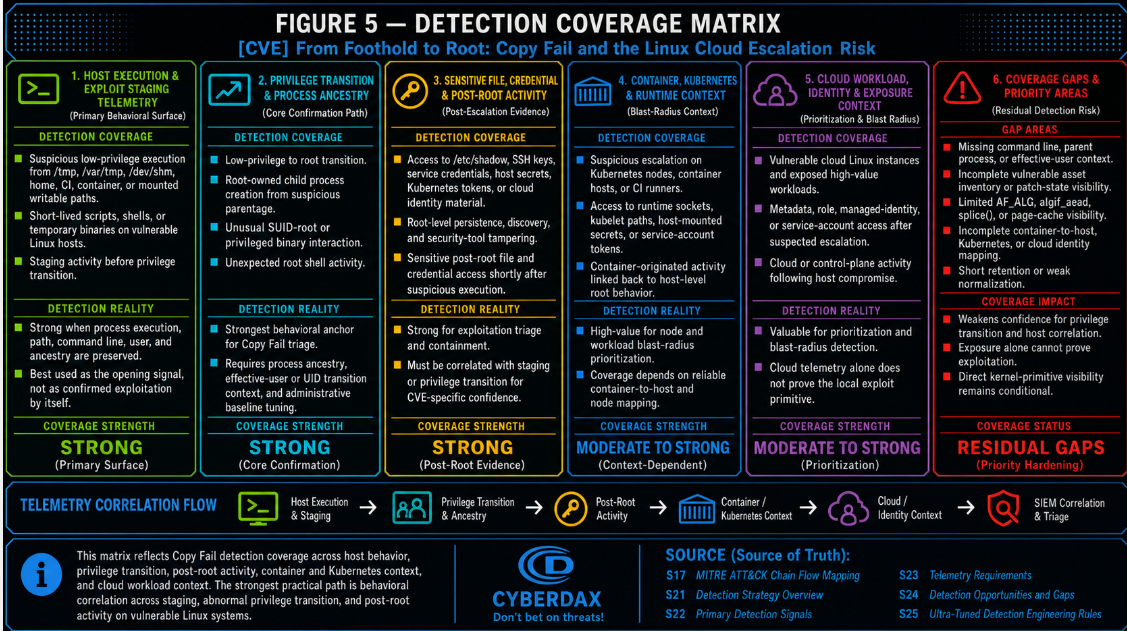
The highest-value defensive model is behavioral correlation across seven attacker behavior families: prerequisite local execution, writable-path exploit staging, Copy Fail privilege escalation, root-level host control, credential and trust material access, cloud or workload expansion, and post-root defense evasion, persistence, or impact. This structure preserves technical accuracy while keeping later visual outputs usable, especially the campaign flow, ATT&CK chain flow, behavior signal confidence matrix, detection coverage matrix, defensive architecture, and attack economics model.
S20A Adversary Tradecraft Summary
Tradecraft Summary
Copy Fail tradecraft is centered on post-foothold escalation rather than initial access. The attacker first needs local execution on a vulnerable Linux host, then uses exploit staging and privilege escalation to convert limited access into root-level control. The most important defensive transition is the movement from suspicious low-privilege activity to root-owned process execution.
Primary Tradecraft Themes
· Abuse of an existing local foothold rather than direct remote exploitation.
· Staging of exploit material from writable or user-controlled Linux paths.
· Use of shells, interpreters, build tools, compiled binaries, or renamed local executables to support exploit execution.
· Exploitation of Copy Fail to transition from low-privilege execution to root-level control.
· Post-root access to sensitive files, SSH keys, service credentials, Kubernetes tokens, runtime sockets, cloud metadata, and workload secrets.
· Defense evasion through audit, EDR, cloud-agent, container-security, or vulnerability-scanner tampering.
· Expansion into cloud, Kubernetes, container, CI/CD, identity, or production environments where exposed trust material exists.
· Conditional impact based on host role, credential exposure, workload criticality, and attacker objective.
Detection-Relevant Tradecraft
The strongest detection path is not static artifact discovery. The strongest detection path is behavioral correlation across vulnerable host state, suspicious local execution, writable-path staging, abnormal low-privilege-to-root transition, privileged binary interaction, sensitive file access, security-control tampering, and post-root cloud, Kubernetes, container, or CI/CD activity.
Operational Tradecraft Assessment
Low-capability actors may rely on public proof-of-concept code and obvious staging paths after gaining local execution. Moderate-capability actors may modify filenames, wrappers, paths, and command syntax to avoid basic detection. High-capability actors may integrate Copy Fail into a broader intrusion workflow, target cloud or Kubernetes infrastructure, suppress telemetry, minimize artifacts, and rapidly convert root access into credential theft or workload expansion.
Final Tradecraft Position
Copy Fail should be treated as a root-escalation enabler that increases the value of any Linux foothold. The vulnerability is most dangerous where vulnerable systems are exposed, credential-rich, cloud-connected, Kubernetes-adjacent, container-hosted, CI/CD-connected, or production-critical. Defensive success depends on detecting the privilege-transition sequence quickly and preventing root-level access from becoming credential exposure, cloud expansion, Kubernetes compromise, persistent access, or operational disruption.
S21 Detection Strategy Overview
Detection Objective
· The detection strategy for CVE-2026-31431 focuses on identifying local privilege escalation activity after an attacker has already obtained unprivileged execution on a vulnerable Linux system.
· The primary defensive objective is to detect the transition from foothold to root before the attacker can establish persistence, access credentials, compromise container or Kubernetes node trust boundaries, or expand into broader cloud infrastructure.
· This detection model treats Copy Fail as a post-foothold escalation risk, not as a remotely exploitable perimeter event.
· Detection should prioritize host behavior, privilege transition evidence, container or node context, and post-escalation activity rather than static indicators alone.
Detection Model
· Primary Detection Model
· Detect exploit staging and local privilege escalation behavior on vulnerable Linux systems.
· Detect suspicious low-privilege execution followed by root-owned process creation, root shell activity, privileged binary abuse, or abnormal access to sensitive host resources.
· Prioritize Linux EDR, audit telemetry, process ancestry, command-line telemetry, user context, container context, and host inventory.
· Secondary Detection Model
· Identify exposed vulnerable Linux workloads, Kubernetes nodes, container hosts, CI runners, and cloud Linux instances where exploitation would materially increase blast radius.
· Use cloud inventory, vulnerability management, kernel version visibility, container runtime context, and asset criticality to prioritize containment and patching.
· Tertiary Detection Model
· Detect post-root behavior that indicates successful escalation, including credential access, discovery, persistence setup, container escape follow-on activity, cloud credential harvesting, and lateral movement preparation.
· Excluded Detection Model
· Do not treat network intrusion detection as the primary detection layer for this CVE because exploitation is local and occurs after code execution has already been obtained.
Detection Strategy
· Anchor detections on attacker behavior that is difficult to remove from the exploitation sequence: local exploit staging, suspicious execution from writable paths, privilege boundary transition, privileged binary interaction, root-owned child process creation, and post-escalation host activity.
· Treat AF_ALG, algif_aead, and splice()-adjacent telemetry as conditional high-value evidence only where syscall, audit, EDR kernel, or eBPF telemetry is available.
· Do not require direct syscall visibility for all rules because many enterprise environments will not capture this level of Linux kernel interaction consistently.
· Favor detections that survive exploit modification, proof-of-concept renaming, script obfuscation, minor payload changes, and distribution-specific operational differences.
· Avoid detection logic that depends only on CVE strings, exploit nicknames, public proof-of-concept filenames, known hashes, or vendor alert names.
· Use vulnerability and exposure data to prioritize hosts, but do not confuse vulnerable state with confirmed exploitation.
· Use post-escalation behavior to trigger containment when the exploit primitive itself is not directly observable.
Detection Focus Areas
· Low-privilege user execution of Python, shell, or compiled binaries from /tmp, /var/tmp, /dev/shm, user home directories, container writable layers, or mounted build/workload paths.
· Suspicious execution followed by rapid root-owned process creation without expected administrative tooling.
· Unexpected root shell creation from non-administrative parent processes.
· Abnormal interaction with SUID-root binaries before or during privilege transition activity.
· Evidence of local privilege escalation on Kubernetes worker nodes, container hosts, CI runners, internet-facing Linux workloads, and cloud-hosted Linux instances.
· Conditional evidence of AF_ALG, crypto API, algif_aead, or splice()-adjacent activity where telemetry supports reliable collection.
· Post-escalation access to /etc/shadow, SSH private keys, cloud metadata services, Kubernetes service account tokens, container runtime sockets, host-mounted secrets, or privileged workload credentials.
· Root-level discovery, persistence, credential access, or lateral movement activity shortly after suspicious low-privilege execution.
System-Level Detection Position
· SentinelOne, Splunk, Elastic, and SIGMA should carry the strongest detection burden because they can represent host behavior, process ancestry, user context, and privilege transition logic with practical deployment paths.
· QRadar should be used where Linux audit, EDR, identity, and container telemetry are normalized well enough to support reliable correlation.
· AWS, Azure, and GCP detections should focus on vulnerable workload exposure, node or instance prioritization, cloud-side post-exploitation behavior, and suspicious activity after suspected escalation.
· YARA should be limited to supporting detection of known exploit artifacts or proof-of-concept-derived files and should not be treated as a primary exploitation detection layer.
· Suricata should not be used for CVE-specific detection unless the report scope expands to prerequisite initial access, payload delivery, or post-compromise command-and-control behavior.
Detection Limitations
· Network telemetry alone is insufficient for direct Copy Fail detection because the exploit path is local.
· File integrity monitoring may not reliably detect exploitation where the attack affects page-cache state without durable on-disk modification.
· Direct visibility into AF_ALG or splice() behavior depends on deployed syscall, audit, kernel, EDR, or eBPF telemetry.
· Cloud control-plane telemetry generally cannot observe the kernel exploit primitive directly.
· Static hashes, YARA-only logic, and proof-of-concept-name matching are fragile because exploit code can be renamed, minimized, embedded, or modified.
· Detection confidence depends heavily on command-line capture, process ancestry fidelity, user identity normalization, container context, kernel version inventory, and telemetry retention.
Recommended Engineering Direction
· Build host-behavior detections first.
· Use SIEM correlation to connect exploit staging, privilege transition, and post-root activity.
· Use cloud-native rules to prioritize exposed Linux workloads and detect suspicious cloud or Kubernetes activity after suspected escalation.
· Avoid forcing rules into telemetry systems that cannot observe local Linux privilege escalation behavior with sufficient fidelity.
· Preserve clear separation between exposure detection, exploitation detection, and post-exploitation detection.
· Reject rules that cannot meet realistic telemetry, noise, deployability, and standalone-evidence requirements.
· Prioritize systems with meaningful host, audit, process, identity, and cloud workload context, while excluding systems that cannot produce CVE-relevant evidence.
S22 Primary Detection Signals
Signal Purpose
· The primary detection signals for CVE-2026-31431 identify exploit staging, local privilege escalation behavior, root transition outcomes, and post-escalation activity on vulnerable Linux systems.
· The signal model does not assume universal visibility into the kernel exploit primitive.
· Detection should combine host behavior, process ancestry, user context, vulnerable asset state, and cloud or container workload context to distinguish exploitation risk from normal Linux administrative activity.
· Vulnerable-state signals support prioritization, but exploitation signals require observable behavior beyond kernel version exposure.
Signal Category 1: Exploit Staging on Linux Hosts
· Low-privilege execution of Python, shell scripts, compiled ELF binaries, or short-lived executables from writable locations.
· Execution from /tmp, /var/tmp, /dev/shm, user home directories, container writable layers, CI workspace paths, build directories, or mounted workload volumes.
· Rapid creation, execution, and deletion of local binaries or scripts by non-administrative users.
· Execution of unknown or unsigned Linux binaries from transient paths on internet-facing servers, container hosts, Kubernetes worker nodes, or cloud Linux instances.
· Local exploit testing behavior from low-privilege users, especially where followed by privilege transition activity.
Signal Category 2: Conditional Kernel-Interface Abuse Evidence
· Unusual AF_ALG socket usage by non-standard processes where syscall, EDR kernel, audit, or eBPF telemetry is available.
· algif_aead or related crypto interface interaction from userland processes that do not normally use Linux kernel crypto APIs.
· splice()-adjacent activity paired with access to readable privileged files or SUID-root binaries where telemetry can reliably capture this behavior.
· Kernel crypto interface activity shortly before privilege transition events.
· AF_ALG, algif_aead, and splice() evidence should be treated as high-value supporting telemetry, not as a universal prerequisite for detection.
Signal Category 3: SUID and Privileged Binary Interaction
· Low-privilege process interaction with SUID-root binaries shortly after suspicious local execution.
· Unexpected execution of SUID-root utilities from non-administrative parent processes.
· Abnormal access to locally deployed privileged binaries, including authentication, account-management, mount, shell, or service-control utilities.
· Execution of privileged binaries from unusual working directories, container contexts, temporary paths, or user-controlled sessions.
· Root-owned child process creation following privileged binary interaction where the parent chain does not match expected administrative workflows.
· SUID-related signals should be scoped carefully because legitimate administrative activity can generate overlapping telemetry.
Signal Category 4: Low-Privilege-to-Root Transition
· Low-privilege user process spawning a root-owned shell, command interpreter, or privileged child process without an expected administrative parent chain.
· Root process creation from temporary binaries, scripting engines, interactive shells, build tools, container processes, or unknown executables.
· Sudden privilege boundary change from user execution to root execution shortly after local exploit staging.
· Root-owned process creation by users, service accounts, workload identities, or application accounts that do not normally perform administrative actions.
· Privilege transition chains should be correlated with user identity, process ancestry, working directory, command line, host role, and vulnerable asset state.
Signal Category 5: Post-Escalation Host Activity
· Root-level access to /etc/shadow, /etc/sudoers, SSH private keys, host secrets, service credentials, or local credential stores shortly after suspicious low-privilege execution.
· Root-level host reconnaissance, including enumeration of users, groups, network interfaces, mounted file systems, running processes, kernel version, container runtime state, or cloud metadata reachability.
· Persistence setup through cron, systemd units, shell profile modification, SSH authorized keys, privileged service modification, or startup script changes.
· Root-level execution of credential access tools, discovery commands, tunneling utilities, reverse shells, or lateral movement tooling.
· Attempts to disable, tamper with, or evade EDR, audit logging, cloud agents, container security agents, or vulnerability management agents.
· Post-escalation signals should be treated as stronger evidence when paired with exploit staging, vulnerable host state, or abnormal privilege transition.
Signal Category 6: Container and Kubernetes Node Context
· Suspicious local privilege escalation behavior originating from containerized workloads, Kubernetes pods, CI jobs, or container runtime-adjacent processes.
· Root-owned host process creation following activity from a container context, mounted container volume, or workload service account.
· Access to Kubernetes service account tokens, kubelet directories, container runtime sockets, host-mounted secrets, or node-level credentials after suspicious local execution.
· Unexpected interaction with container runtime sockets, kubelet paths, host namespaces, or host-mounted resources.
· Privilege escalation behavior on Kubernetes worker nodes that host externally exposed workloads, privileged pods, sensitive namespaces, or high-value production services.
· Container and Kubernetes context should increase priority because successful local root escalation can expand host, node, and workload blast radius.
Signal Category 7: Cloud Workload and Exposure Context
· Vulnerable Linux kernel versions on cloud-hosted Linux instances, container hosts, Kubernetes nodes, CI runners, or high-value workload infrastructure.
· Vulnerable systems exposed to internet-facing applications, remote access services, build pipelines, developer access paths, or containerized workloads that increase the likelihood of local code execution.
· Suspicious root-level activity on cloud Linux instances shortly after workload compromise indicators, web-shell behavior, suspicious SSH access, or container breakout indicators.
· Access to instance metadata services, cloud credentials, managed identity tokens, role credentials, or workload identity material after suspected escalation.
· Cloud control-plane activity following suspected host compromise, including unusual API calls, credential use from unexpected locations, role assumption, security group modification, snapshot access, or secret retrieval.
· Cloud exposure signals should support prioritization and escalation, but they should not be labeled as confirmed exploitation without supporting host or post-escalation evidence.
Signal Category 8: Exploit Artifact and PoC-Derived Evidence
· Known public proof-of-concept filenames, strings, repository references, or compiled artifacts where available and validated.
· Local files, scripts, or binaries containing references to Copy Fail, CVE-2026-31431, AF_ALG, algif_aead, splice(), page-cache modification, or SUID corruption concepts.
· Download or execution of public exploit material on Linux systems.
· Hash or YARA matches for known exploit artifacts, when available and validated.
· Artifact-based signals should be treated as supporting evidence only because public proof-of-concept code can be renamed, minimized, embedded, or modified.
Signal Prioritization
· Highest-priority signals combine suspicious local execution, abnormal privilege transition, root-owned child process creation, and post-escalation activity on a vulnerable Linux system.
· High-priority signals include exploit staging or low-privilege-to-root transition activity on Kubernetes nodes, container hosts, CI runners, and cloud Linux workloads.
· Medium-priority signals include vulnerable kernel exposure on high-value systems without observed exploitation behavior.
· Supporting signals include PoC artifacts, exploit strings, or public exploit downloads without observed privilege transition.
· Low-priority signals include generic Linux administrative activity without vulnerable-state context, suspicious staging context, or privilege transition evidence.
Detection Boundaries
· Vulnerable kernel state alone is not exploitation evidence.
· Public PoC artifact discovery alone is not exploitation evidence unless paired with execution, staging, or privilege transition activity.
· AF_ALG, algif_aead, or splice() telemetry is highly useful when available but should not be required for all detection paths.
· Post-root activity may indicate successful exploitation but can also result from other local privilege escalation methods; correlation with staging behavior and vulnerable host state is required.
· Network-only telemetry cannot provide direct confirmation of Copy Fail exploitation.
· Detection logic must avoid relying on a single brittle indicator where attacker-controlled filenames, paths, strings, or hashes can change.
S23 Telemetry Requirements
Telemetry Objective
· The telemetry requirements for CVE-2026-31431 must support detection of local exploit staging, low-privilege-to-root transition, vulnerable asset prioritization, and post-escalation activity on Linux systems.
· Telemetry collection should not assume universal visibility into the kernel exploit primitive.
· The minimum viable model should rely on deployable enterprise telemetry: process execution, process ancestry, user context, vulnerable asset state, host role, and post-escalation behavior.
· Enhanced telemetry should improve confidence where syscall, eBPF, Linux audit, or EDR kernel visibility is available.
· Telemetry must distinguish vulnerable-state exposure from suspected exploitation.
Required Telemetry Sources
· Linux EDR telemetry capturing process execution, process ancestry, command-line arguments, user context, executable path, working directory, file activity, and security agent status.
· Linux audit telemetry capturing process execution, privilege transitions, privileged binary execution, sensitive file access, authentication activity, and user identity changes.
· Vulnerability management telemetry capturing Linux distribution, kernel version, package state, patch state, asset ownership, asset role, and exposure status.
· Host inventory telemetry identifying Linux servers, cloud Linux instances, Kubernetes worker nodes, container hosts, CI runners, internet-facing workloads, and high-value production systems.
· SIEM-normalized telemetry capable of correlating endpoint behavior, Linux audit events, vulnerability state, host role, identity context, and cloud or container context within short time windows.
· Cloud workload telemetry identifying instance, account, subscription, project, public exposure, cloud role, managed identity, workload owner, and security-control coverage.
· Container and Kubernetes telemetry identifying container, pod, namespace, service account, node, workload owner, privileged workload state, hostPath usage, and runtime socket exposure where available.
Conditional High-Fidelity Telemetry Sources
· Syscall telemetry for AF_ALG socket activity, splice()-adjacent behavior, privileged file interaction, and kernel-interface abuse.
· eBPF telemetry for process execution, file access, socket activity, privilege transitions, container context, and host-level process relationships.
· EDR kernel telemetry capable of identifying suspicious Linux crypto interface usage, unusual file access patterns, or abnormal process behavior.
· Tuned Linux audit policies for execution from writable paths, SUID-root binary execution, sensitive file access, authentication transitions, and privilege boundary changes.
· Live response or forensic telemetry from suspected compromised hosts when escalation or post-root activity is observed.
· Conditional high-fidelity telemetry should strengthen confidence but must not be treated as mandatory for baseline detection.
Required Field Coverage
· Host identity fields must include hostname, asset identifier, cloud instance identifier where applicable, Kubernetes node identifier where applicable, and container identifier where applicable.
· Process fields must include process name, executable path, command line, working directory, process user, effective user, parent process name, parent process path, parent command line, parent user, and process ancestry identifier where available.
· File fields must include file path, file operation, file owner, file permissions, and SUID or privilege-bit status where available.
· Identity fields must include source user, target user, effective UID or privilege context, authentication event type, and privilege transition event type where available.
· Vulnerability fields must include kernel version, Linux distribution, package version, patch state, vulnerable-state status, scan time, asset criticality, and exposure state.
· Container and Kubernetes fields must include container image, container ID, pod, namespace, service account, workload owner, node, privileged container status, hostPath usage, and runtime socket exposure where available.
· Cloud fields must include account, subscription, or project identifier; region; cloud role or managed identity; workload owner; public exposure indicator; and security agent coverage.
· Telemetry health fields must include EDR status, audit logging status, vulnerability scan status, cloud security agent status, and last-seen timestamp.
Normalization Requirements
· Normalize Linux host identity across EDR, audit, vulnerability management, SIEM, cloud inventory, Kubernetes, and container telemetry.
· Preserve both real user and effective user context so privilege boundary changes can be detected accurately.
· Preserve process ancestry during ingestion and correlation.
· Preserve command-line arguments, executable path, working directory, parent process context, and user context.
· Normalize kernel version, Linux distribution, package state, and patch state into vulnerability records.
· Normalize cloud instance identifiers, Kubernetes node names, hostnames, and asset IDs into a single host identity model.
· Map container and Kubernetes workload context back to the underlying host or node.
· Preserve timestamps with enough precision to correlate exploit staging, privilege transition, and post-escalation behavior within short windows.
· Avoid SIEM parsing or enrichment pipelines that drop path, parent, user, container, cloud, or vulnerability context.
Minimum Viable Telemetry Baseline
· Process creation telemetry with command line, executable path, working directory, and parent process context.
· User and effective-user context for Linux process execution.
· Linux audit or EDR visibility into privileged process creation, sensitive file access, and authentication or privilege transition events.
· Vulnerability management data showing kernel version, Linux distribution, patch state, and affected asset status.
· Host inventory showing whether the system is a cloud instance, Kubernetes node, container host, CI runner, internet-facing workload, or high-value production system.
· SIEM correlation across process execution, user context, host role, and vulnerable-state data.
· Security agent health telemetry confirming whether EDR, audit, vulnerability, cloud, and container security controls are active.
Enhanced Telemetry Baseline
· Syscall, eBPF, or EDR kernel visibility into AF_ALG, algif_aead, splice(), and related kernel-interface behavior.
· Container runtime telemetry linking container-originated activity to host-level processes.
· Kubernetes workload context tied to node-level host telemetry.
· Sensitive file access telemetry for credential stores, SSH keys, service credentials, Kubernetes tokens, cloud identity material, and host-mounted secrets.
· Privileged binary execution tracking with SUID context and parent-process correlation.
· Cloud metadata access telemetry where available.
· Agent tamper telemetry for EDR, auditd, cloud security agents, container security tools, and vulnerability management agents.
· Retention sufficient to support retrospective hunting across the exposure window.
Retention Requirements
· Retain process creation, process ancestry, Linux audit, EDR, vulnerability, cloud, Kubernetes, and container telemetry long enough to support retrospective hunting after patch delays, KEV-driven prioritization, or delayed discovery of suspicious activity.
· Retain vulnerability scan history so teams can determine whether a host was vulnerable at the time suspicious behavior occurred.
· Retain cloud, Kubernetes, and container context so workload-to-host relationships can be reconstructed during incident review.
· Retain security agent health history so visibility gaps can be identified during triage.
· Preserve telemetry from suspected compromised hosts before rebuilding, recycling, or replacing cloud instances, Kubernetes nodes, or ephemeral workloads.
Deployment Requirements
· Enable Linux process command-line capture where supported.
· Validate process ancestry fidelity across EDR, audit, and SIEM pipelines.
· Validate effective-user and privilege-transition visibility.
· Ensure audit policies do not exclude temporary directories, container paths, CI workspace paths, user home directories, or other writable execution locations.
· Ensure Linux EDR and audit telemetry capture activity from service accounts, workload identities, application users, CI users, and non-interactive users.
· Ensure vulnerability management covers cloud Linux instances, Kubernetes nodes, container hosts, CI runners, and ephemeral Linux workloads.
· Ensure cloud inventory maps vulnerable systems to owners, accounts, subscriptions, projects, exposure state, and business criticality.
· Ensure Kubernetes telemetry identifies node, namespace, pod, service account, workload owner, hostPath usage, runtime socket exposure, and privileged workload state.
· Ensure SIEM parsing preserves process, user, file, host, cloud, vulnerability, container, and Kubernetes context.
· Ensure detections can separate expected administrative activity from abnormal low-privilege-to-root transitions.
Telemetry Gaps That Reduce Confidence
· Missing command-line capture.
· Missing parent process context.
· Missing effective-user or UID transition context.
· Missing kernel version, distribution, or patch-state visibility.
· Missing vulnerable asset inventory.
· Missing container-to-host relationship mapping.
· Missing Kubernetes node, pod, namespace, or service account context.
· Missing cloud asset ownership, role, identity, or exposure context.
· Missing Linux audit coverage for sensitive file access and privileged execution.
· Missing security agent health data.
· Missing telemetry retention across the suspected exposure period.
· SIEM normalization that drops executable path, working directory, parent process, command line, user, container, cloud, or vulnerability context.
Telemetry Confidence Position
· High-confidence detection is possible when process ancestry, command-line telemetry, user transition context, vulnerable asset state, host role, and post-escalation behavior are available in the same correlation path.
· Moderate-confidence detection is possible when endpoint telemetry and vulnerable-state data are available but direct kernel-interface visibility is absent.
· Low-confidence detection results when only vulnerability state, cloud inventory, network telemetry, or static artifact matching is available.
· Direct detection of AF_ALG, algif_aead, or splice() abuse should be treated as high-fidelity but environment-dependent.
· Exposure-only telemetry should support prioritization and hunting, not confirmed exploitation claims.
S24 Detection Opportunities and Gaps
Detection Opportunity Objective
· Detection opportunities for CVE-2026-31431 focus on local exploit staging, low-privilege-to-root transition, vulnerable Linux workload prioritization, and post-escalation activity.
· The strongest detection paths require correlation across Linux endpoint telemetry, audit telemetry, vulnerability state, user context, host role, container context, Kubernetes context, and cloud workload context.
· Detection should not depend on a single exploit artifact, proof-of-concept string, public filename, vendor alert name, or assumed kernel-interface event.
· Rule engineering should prioritize opportunities that are observable, low-noise, deployable, and resilient to minor exploit modification.
High-Value Detection Opportunities
· Detect suspicious low-privilege execution from writable or transient Linux paths followed by privilege escalation behavior.
· Detect abnormal low-privilege-to-root process transitions where the parent chain does not match expected administrative activity.
· Detect root-owned shell, command interpreter, or privileged child process creation from non-administrative parent processes.
· Detect suspicious interaction with SUID-root or privileged binaries shortly after exploit staging.
· Detect post-root access to sensitive host files, credentials, SSH keys, Kubernetes service account tokens, cloud identity material, host-mounted secrets, or container runtime sockets.
· Detect root-level discovery, persistence setup, credential access, security tool tampering, or lateral movement preparation after suspicious local execution.
· Detect suspicious escalation activity on vulnerable Kubernetes worker nodes, container hosts, CI runners, cloud Linux instances, and internet-facing Linux workloads.
· Detect cloud or Kubernetes activity that follows suspected host compromise, including metadata access, role credential use, secret retrieval, node-level activity, or workload-to-host trust-boundary abuse.
Conditional High-Fidelity Opportunities
· Detect unusual AF_ALG socket usage by non-standard processes where syscall, Linux audit, EDR kernel, or eBPF telemetry is available.
· Detect algif_aead interaction by scripting engines, temporary executables, containerized workloads, or low-privilege users where collection supports this visibility.
· Detect splice()-adjacent activity paired with privileged file interaction where telemetry can capture the behavior reliably.
· Detect page-cache or privileged file abuse patterns only where forensic, EDR kernel, or specialized host telemetry can produce meaningful evidence.
· Detect known proof-of-concept artifacts with YARA, hash, or string logic only where artifact intelligence is validated and current.
· Treat conditional high-fidelity opportunities as confidence amplifiers, not universal detection requirements.
Cloud and Container Opportunities
· Identify vulnerable Linux kernels on cloud instances, Kubernetes worker nodes, container hosts, CI runners, and other workload infrastructure.
· Prioritize vulnerable systems that host externally exposed applications, privileged workloads, sensitive namespaces, production services, or workload identities with meaningful cloud permissions.
· Correlate suspected local escalation with cloud credential access, instance metadata interaction, managed identity use, role assumption, secret retrieval, storage access, or control-plane modification.
· Correlate suspected local escalation on Kubernetes nodes with access to service account tokens, kubelet paths, host-mounted secrets, runtime sockets, privileged pod contexts, or host namespace resources.
· Use cloud and Kubernetes visibility to prioritize affected assets and detect post-escalation blast-radius expansion.
· Do not treat cloud control-plane telemetry as direct evidence of the local kernel exploit primitive.
Exposure Management Opportunities
· Use vulnerability management data to identify affected kernel versions, missing patches, exposed Linux workloads, and high-value systems.
· Prioritize patching and hunting based on host role, workload exposure, cloud identity permissions, Kubernetes node function, production criticality, and local code-execution likelihood.
· Use historical vulnerability scan data to determine whether suspicious behavior occurred while the host was vulnerable.
· Use asset ownership, business criticality, public exposure, and workload function to focus hunting on the most consequential systems first.
· Treat vulnerable-state data as prioritization evidence, not exploitation evidence.
Primary Detection Gaps
· Direct kernel exploit behavior may not be visible without syscall, eBPF, EDR kernel, or properly tuned Linux audit telemetry.
· AF_ALG, algif_aead, and splice() evidence may be unavailable even when exploitation occurs.
· Page-cache manipulation may not produce durable file modification evidence visible to traditional file integrity monitoring.
· Network detection has limited direct value because exploitation is local.
· Cloud control-plane telemetry cannot directly observe the local Linux kernel exploit primitive.
· Static artifact detection is fragile because proof-of-concept code can be renamed, minimized, embedded, recompiled, or modified.
· Vulnerability scan data may lag behind actual patch state, especially on ephemeral, autoscaled, or manually maintained Linux workloads.
Operational Detection Gaps
· Missing command-line telemetry weakens exploit staging detection.
· Missing process ancestry weakens low-privilege-to-root transition detection.
· Missing real-user, effective-user, or UID transition context weakens privilege boundary analysis.
· Missing vulnerable asset state prevents reliable CVE prioritization.
· Missing container-to-host mapping weakens detection for Kubernetes and container-host escalation scenarios.
· Missing cloud identity, workload ownership, and asset criticality context weakens blast-radius prioritization.
· Missing agent health history may hide blind spots caused by disabled EDR, audit logging, cloud agents, container security agents, or vulnerability scanners.
· Short telemetry retention can prevent retrospective hunting after KEV-driven urgency, delayed patch discovery, or delayed identification of suspicious behavior.
False Positive and Noise Considerations
· Legitimate Linux administration can resemble privilege transition behavior when approved users execute sudo, service-control utilities, package managers, maintenance scripts, or automation jobs.
· CI runners and build servers often execute short-lived binaries from workspace paths, which can overlap with exploit staging indicators.
· Container hosts and Kubernetes nodes may generate high-volume process and file telemetry that requires workload-aware scoping.
· Security tools, monitoring agents, backup agents, and vulnerability scanners may access privileged files or enumerate host state during legitimate operations.
· Authorized vulnerability validation may involve proof-of-concept execution and must be separated from unauthorized exploitation.
· Noise reduction should use host role, user role, parent process, working directory, command line, vulnerable-state context, asset criticality, and short-window correlation.
Rejected or Weak Detection Opportunities
· Network signatures for direct Copy Fail exploitation should be rejected as primary detection because the exploit path is local.
· Generic root process creation should be rejected unless correlated with suspicious parent process, low-privilege origin, vulnerable host state, or post-escalation behavior.
· Vulnerable kernel inventory alone should be rejected as exploitation detection and retained only for exposure management.
· Hash-only, filename-only, and string-only proof-of-concept detection should be rejected as primary detection because attacker-controlled artifacts can change easily.
· Vendor alert-name matching should be rejected as primary detection because it depends on another product’s output and does not provide standalone rule evidence.
· Broad SUID execution detection should be rejected unless scoped by unusual parent process, working directory, user role, vulnerable-state context, or privilege transition sequence.
· Direct AF_ALG, algif_aead, or splice() detection should be rejected where telemetry cannot capture the required behavior reliably.
· Broad post-root activity detection should be rejected unless correlated with suspicious staging, vulnerable-state context, abnormal privilege transition, or high-risk host role.
Rule Engineering Implications
· Prioritize rules that combine suspicious local execution, vulnerable host state, abnormal privilege transition, and post-escalation behavior.
· Prefer host and SIEM detections that remain valid when public proof-of-concept artifacts change.
· Include cloud and Kubernetes rules only where they support exposure prioritization or post-escalation blast-radius detection with meaningful context.
· Treat YARA as supporting artifact detection only.
· Do not force Suricata rules into direct CVE exploitation coverage.
· Exclude rules that rely on another CyberDax rule firing first.
· Exclude rules that cannot define required telemetry, expected fields, tuning assumptions, deployment boundary, and standalone evidence.
Residual Detection Position
· CVE-2026-31431 creates strong detection opportunities when host behavior, vulnerable asset state, identity context, and post-escalation activity can be correlated.
· Direct exploit-primitive visibility is valuable but conditional.
· The most reliable detection path is behavioral correlation around exploit staging, privilege transition, and post-root activity on vulnerable Linux systems.
· The highest-risk detection failure mode is over-reliance on exposure data, network telemetry, static artifacts, or assumed kernel-interface visibility.
S25 Ultra-Tuned Detection Engineering Rules
Suricata
Detection Viability Assessment
· Suricata does not receive a CVE-specific detection rule for CVE-2026-31431.
· CVE-2026-31431 is a local Linux privilege escalation condition that requires prior code execution on a vulnerable Linux host, container workload, Kubernetes node, or cloud Linux instance.
· Suricata cannot directly observe local Linux process execution, privilege boundary transitions, SUID-root interaction, page-cache behavior, AF_ALG, algif_aead, or splice()-adjacent host activity.
· Network telemetry may support broader compromise monitoring, but it does not provide direct evidence of Copy Fail exploitation.
· Final Suricata rule count: 0
Detection Position
· Suricata should remain a supporting network visibility layer for prerequisite access activity, suspicious payload transfer, command-and-control, tunneling, exfiltration, or lateral movement.
· Suricata-only alerts should not be labeled as confirmed Copy Fail exploitation without corroborating host, audit, vulnerability, container, Kubernetes, or cloud workload evidence.
· Direct detection responsibility should remain with systems that can observe Linux host behavior, process ancestry, user context, vulnerable asset state, and post-escalation activity.
Engineering Implementation Instructions
· Do not deploy a Suricata rule that claims direct CVE-2026-31431 exploitation coverage.
· Do not tune existing network rules to the Copy Fail CVE label unless they are clearly documented as adjacent initial-access or post-compromise monitoring.
· Require host-centered corroboration before escalating a Suricata-only event as suspected Copy Fail exploitation.
· Use Suricata to support broader incident context, not as the primary detection layer for this CVE.
SentinelOne
Rule 1
Suspicious Writable-Path Exploit Staging on Linux Workloads
Rule Format
· SentinelOne Deep Visibility query pattern suitable for STAR-style alerting after tenant field and event validation.
Detection Purpose
· Detect suspicious local exploit staging where a low-privilege Linux process executes from a writable, transient, user-controlled, CI, container, or mounted workload path.
· This rule identifies staging behavior that may precede Copy Fail exploitation without depending on exploit filenames, proof-of-concept strings, hashes, or direct kernel-interface telemetry.
Detection Logic
· Identify Linux process execution from writable or transient paths such as /tmp, /var/tmp, /dev/shm, user home directories, CI workspace paths, container writable layers, or mounted workload paths.
· Require execution by a non-root user, service account, workload identity, application account, or other non-administrative context.
· Prioritize scripting engines, shells, build tools, compiled temporary binaries, and unknown executables launched from those paths.
· Treat the alert as higher confidence when followed by root-owned process creation, privileged binary interaction, sensitive file access, or post-escalation behavior.
· Increase priority when the affected host is known to be vulnerable, internet-facing, cloud-hosted, a Kubernetes node, a container host, or a CI runner.
Required Telemetry
· Linux process creation telemetry.
· Process ancestry.
· Command-line capture.
· Executable path.
· Working directory.
· Source user and effective user context.
· Host role or asset context.
· Vulnerable kernel or affected asset context where available.
Engineering Implementation Instructions
· Validate SentinelOne tenant field names for process path, command line, user, parent process, effective user, endpoint operating system, and event type before deployment.
· Scope to Linux endpoints only.
· Add allowlists for approved automation, package managers, configuration management tools, backup agents, vulnerability scanners, and known CI build processes.
· Tune by host role because CI runners, build servers, and container hosts may legitimately execute short-lived binaries from writable paths.
· Treat vulnerable kernel state as confidence and prioritization context, not as the only alert condition.
· Use follow-on root process activity, privileged binary interaction, sensitive file access, or post-escalation behavior as triage evidence rather than assuming staging equals exploitation.
· Route alerts with container host, Kubernetes node, cloud Linux instance, CI runner, or internet-facing workload context at higher priority.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.3
· The rule is behaviorally anchored to exploit staging rather than brittle artifact matching.
· The rule remains useful if public proof-of-concept code is renamed, recompiled, embedded, or modified.
· The score is lower than a direct privilege-transition rule because staging alone is not confirmed exploitation and requires follow-on triage evidence.
· The rule remains deployable when tuned for CI, build, automation, and administrative environments.
TCR Assessment
· Operational TCR: 8.2
· Full-Telemetry TCR: 8.7
· Operational confidence depends on command-line capture, process ancestry fidelity, user context, endpoint coverage, and executable path preservation.
· Full-telemetry confidence improves when SentinelOne data is enriched with vulnerable host state, cloud workload context, and container or Kubernetes node context.
Limitations
· This rule detects suspicious staging behavior, not confirmed Copy Fail exploitation.
· Legitimate CI jobs, temporary maintenance scripts, administrative automation, and security tooling may overlap with this behavior.
· Confirmation requires correlation with vulnerable host state, privilege transition, privileged binary interaction, or post-escalation activity.
Detection Query Pattern
EndpointOS = "linux"
AND EventType = "Process Creation"
AND TgtProcImagePath IN CONTAINS ANY (
"/tmp/",
"/var/tmp/",
"/dev/shm/",
"/home/",
"/workspace/",
"/workdir/",
"/build/",
"/runner/",
"/mnt/"
)
AND TgtProcUser NOT IN ANY ("root")
AND (
TgtProcName IN ANY ("python", "python3", "perl", "ruby", "bash", "sh", "dash", "zsh", "gcc", "cc", "make")
OR TgtProcImagePath ENDSWITH ANY (".sh", ".py", ".out", ".bin", ".elf")
)
Rule 2
Suspicious Privileged Binary Interaction From Writable or Scripted Parentage
Rule Format
· SentinelOne Deep Visibility query pattern suitable for STAR-style alerting after tenant field and event validation.
Detection Purpose
· Detect suspicious interaction with SUID-root or privileged Linux binaries from unusual parent processes, writable paths, scripting engines, or non-administrative execution contexts.
· This rule targets privilege-boundary abuse patterns relevant to Copy Fail triage while avoiding broad SUID execution alerting.
Detection Logic
· Identify execution involving privileged binaries where the parent process originates from writable paths, scripting engines, interactive shells, container contexts, CI paths, or other user-controlled locations.
· Require non-root source user context where available.
· Prioritize activity on vulnerable Linux systems, Kubernetes nodes, container hosts, cloud Linux instances, CI runners, or internet-facing workloads.
· Treat the alert as higher confidence when paired with root-owned child process creation, abnormal effective-user transition, sensitive file access, or post-escalation activity.
· Suppress expected administrative workflows such as normal sudo use by approved administrators, package installation, system maintenance, service management, and configuration management automation.
Required Telemetry
· Linux process creation telemetry.
· Parent-child process relationships.
· Process user and effective user.
· Executable path.
· Command line.
· Working directory.
· Privileged binary execution visibility.
· Host role and administrative baseline context.
Engineering Implementation Instructions
· Validate whether SentinelOne tenant telemetry exposes effective user, target process user, parent process user, process ancestry, and privileged binary execution context.
· Scope to Linux endpoints only.
· Tune approved administrative parent chains, including trusted sudo, package managers, service-control workflows, configuration management, and enterprise automation.
· Prioritize alerts where the parent process originates from writable paths, scripting engines, interactive shells, application users, service accounts, containerized workloads, or CI jobs.
· Use vulnerable host state and container or Kubernetes node context as prioritization enrichment.
· Do not alert solely on ordinary privileged binary execution without abnormal parentage, non-administrative origin, suspicious path context, or follow-on root activity.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.5
· The rule is anchored to privileged binary interaction from suspicious parentage rather than generic root process creation.
· The rule is more resilient than hash or proof-of-concept matching because it detects privilege-boundary behavior.
· Noise risk exists in administrator-heavy environments, but scoping by parent process, user role, working directory, and host role keeps the rule deployable.
TCR Assessment
· Operational TCR: 7.9
· Full-Telemetry TCR: 8.6
· Operational confidence depends on process ancestry fidelity, user context, and privilege context visibility.
· Full-telemetry confidence improves when effective UID, SUID context, vulnerable asset state, and container or Kubernetes context are available.
Limitations
· Broad privileged binary execution is too noisy without context.
· This rule must not alert solely on normal administrative sudo activity.
· This rule indicates suspicious privilege behavior and requires correlation with vulnerable host state, staging behavior, root transition, or post-escalation activity for Copy Fail-specific triage.
Detection Query Pattern
EndpointOS = "linux"
AND EventType = "Process Creation"
AND (
TgtProcName IN ANY ("su", "sudo", "passwd", "chsh", "chfn", "mount", "umount", "newgrp")
OR TgtProcImagePath IN CONTAINS ANY (
"/usr/bin/su",
"/usr/bin/sudo",
"/usr/bin/passwd",
"/usr/bin/chsh",
"/usr/bin/chfn",
"/usr/bin/mount",
"/usr/bin/umount",
"/bin/su",
"/bin/mount",
"/bin/umount"
)
)
AND (
SrcProcImagePath IN CONTAINS ANY (
"/tmp/",
"/var/tmp/",
"/dev/shm/",
"/home/",
"/workspace/",
"/workdir/",
"/build/",
"/runner/",
"/mnt/"
)
OR SrcProcName IN ANY ("python", "python3", "perl", "ruby", "bash", "sh", "dash", "zsh")
)
AND SrcProcUser NOT IN ANY ("root")
Rule 3
Post-Escalation Root Activity on Vulnerable Linux Workloads
Rule Format
· SentinelOne Deep Visibility query pattern requiring process and file-event validation before STAR-style alerting.
Detection Purpose
· Detect post-escalation root activity that may follow successful Copy Fail exploitation on vulnerable Linux systems.
· This rule targets credential access, host discovery, persistence setup, agent tampering, container-host access, Kubernetes node activity, and workload credential exposure after suspicious local execution or privilege transition.
Detection Logic
· Identify root-level access to sensitive files, secrets, credential stores, Kubernetes tokens, cloud identity material, host-mounted secrets, or container runtime sockets.
· Identify root-level persistence setup, credential access, discovery, metadata access, or security tool tampering from suspicious parent chains.
· Prioritize activity on vulnerable Linux systems, Kubernetes nodes, container hosts, cloud Linux instances, CI runners, and internet-facing workloads.
· Treat the rule as strongest when paired with prior suspicious writable-path execution, privileged binary interaction, abnormal low-privilege-to-root transition, or vulnerable host state.
· Require file-event visibility for file-access portions of the rule; otherwise deploy only the process-command-line portions.
Required Telemetry
· Linux process creation telemetry.
· File access, file creation, or file modification telemetry where available.
· Command-line capture.
· User and effective user context.
· Process ancestry.
· Sensitive path visibility.
· Security agent status.
· Host role and vulnerability context.
Engineering Implementation Instructions
· Validate field availability for file path, file event type, process path, command line, effective user, parent process, source process, and endpoint role.
· Scope to Linux endpoints only.
· If SentinelOne file-access visibility is incomplete, deploy only command-line and process behavior portions until file-event coverage is validated.
· Prioritize sensitive path access by root-owned processes that originate from suspicious parent chains, temporary paths, scripting engines, CI jobs, container contexts, or workload service accounts.
· Add allowlists for approved backup tools, monitoring tools, vulnerability scanners, endpoint agents, configuration management platforms, and administrative maintenance windows.
· Escalate alerts on Kubernetes nodes, container hosts, cloud Linux instances, and CI runners because post-root activity can expand workload and credential blast radius.
· Use this rule as a containment trigger only when paired with exploit staging, abnormal privilege transition, vulnerable host state, or other corroborating evidence.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.4
· The rule targets durable post-escalation behavior commonly performed after obtaining root.
· It is resilient to exploit modification because it does not depend on the exploit primitive or public proof-of-concept artifacts.
· The score is constrained by overlap with legitimate administrative, backup, monitoring, and security tooling.
· The rule remains strong when scoped to suspicious parentage, vulnerable host state, workload context, and prior staging or privilege-transition evidence.
TCR Assessment
· Operational TCR: 7.8
· Full-Telemetry TCR: 8.7
· Operational confidence depends on file-event visibility, command-line capture, process ancestry, effective user context, and agent health.
· Full-telemetry confidence improves when vulnerable host state, Kubernetes context, cloud workload context, and prior staging or privilege transition evidence are available.
Limitations
· Post-root activity can result from other privilege escalation paths and is not unique to Copy Fail.
· File-event visibility may vary by SentinelOne policy, tenant configuration, and event type.
· This rule requires correlation with vulnerable host state or prior suspicious local execution to support CVE-specific triage.
· Legitimate backup, monitoring, and administrative tools may access sensitive files and must be tuned.
Detection Query Pattern
EndpointOS = "linux"
AND (
EventType = "File Modification"
OR EventType = "File Creation"
OR EventType = "File Access"
OR EventType = "Process Creation"
)
AND (
TgtFilePath IN CONTAINS ANY (
"/etc/shadow",
"/etc/sudoers",
"/root/.ssh/",
"/var/run/docker.sock",
"/run/containerd/containerd.sock",
"/run/cri-dockerd.sock",
"/var/lib/kubelet/",
"/var/run/secrets/kubernetes.io/",
"/etc/kubernetes/",
"/var/lib/containerd/",
"/var/lib/docker/"
)
OR TgtProcCmdLine CONTAINS ANY (
"cat /etc/shadow",
"cat /etc/sudoers",
"chmod +s",
"chattr",
"systemctl disable",
"auditctl -D",
"service auditd stop",
"pkill",
"iptables -F",
"curl 169.254.169.254",
"wget 169.254.169.254"
)
)
AND (
TgtProcUser = "root"
OR SrcProcUser = "root"
)
AND (
SrcProcImagePath IN CONTAINS ANY (
"/tmp/",
"/var/tmp/",
"/dev/shm/",
"/home/",
"/workspace/",
"/workdir/",
"/build/",
"/runner/",
"/mnt/"
)
OR SrcProcName IN ANY ("python", "python3", "bash", "sh", "dash", "zsh", "curl", "wget", "nc", "ncat", "socat")
)
Splunk
Required Search Macros and Lookups
· linux_vulnerability_inventory
· approved_linux_staging_activity
· approved_linux_admin_activity
· Normalized process fields: process_path, process_name, process_command_line, parent_process_name, parent_process_path
· Normalized identity fields: user, effective_user, dest_user, src_user
· Normalized file fields where available: file_path, file_action
· Normalized host context fields: host, asset_role, exposure_state, cloud_context, kubernetes_context, container_host_context
· Lookup and field names must be adjusted to the customer’s Splunk CIM mapping, EDR source format, Linux audit source format, and vulnerability-management integration before deployment.
Rule 1
Writable-Path Exploit Staging on Vulnerable Linux Assets
Rule Format
· Splunk SPL correlation search pattern.
Detection Purpose
· Detect suspicious local exploit staging where a non-root Linux process executes from a writable, transient, user-controlled, CI, container, or mounted workload path.
· This rule supports Copy Fail triage by identifying likely local exploit preparation on systems where vulnerable-state, exposure, or workload context increases risk.
· This rule does not rely on proof-of-concept names, hashes, CVE strings, or direct kernel-interface telemetry.
Detection Logic
· Identify Linux process execution from writable or transient paths such as /tmp, /var/tmp, /dev/shm, user home directories, CI workspace paths, mounted workload paths, or container writable layers.
· Require non-root user context where available.
· Prioritize scripting engines, shells, build tools, compiled temporary binaries, and executable-like files launched from writable locations.
· Increase confidence when host inventory or vulnerability data identifies the system as vulnerable, internet-facing, cloud-hosted, a Kubernetes node, a container host, or a CI runner.
· Treat root process creation, privileged binary interaction, sensitive file access, or post-escalation activity as follow-on triage evidence.
Required Telemetry
· Linux process creation events.
· Process command line.
· Process executable path.
· Parent process context.
· User or effective user context.
· Hostname or asset identifier.
· Vulnerability state or affected kernel context where available.
· Host role, cloud, Kubernetes, container-host, or CI context where available.
Engineering Implementation Instructions
· Validate Splunk source types, field names, CIM mappings, endpoint coverage, lookup names, and wildcard behavior before deployment.
· Scope the search to Linux process telemetry from EDR, Sysmon for Linux, Linux audit, osquery, or equivalent host sources.
· Use vulnerability enrichment to prioritize affected kernels, but do not alert on vulnerable state alone.
· Add allowlists for approved CI jobs, package managers, configuration management tools, vulnerability scanners, backup agents, and known administrative automation.
· Tune by host role because CI runners, build servers, and container hosts may legitimately execute short-lived binaries from writable locations.
· Preserve command line, executable path, parent process, user, and host role fields during parsing and enrichment.
· Treat this rule as suspicious staging unless follow-on privilege transition or post-escalation activity is present.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.3
· The rule is anchored to suspicious local exploit staging rather than brittle artifact indicators.
· The rule remains useful if public proof-of-concept material is renamed, recompiled, embedded, or modified.
· The score is constrained because staging alone is not confirmed exploitation and requires follow-on triage evidence.
· The rule remains deployable when tuned for CI, automation, build, and administrative workflows.
TCR Assessment
· Operational TCR: 8.0
· Full-Telemetry TCR: 8.7
· Operational confidence depends on process telemetry quality, command-line capture, path fidelity, user context, and host enrichment.
· Full-telemetry confidence improves when process events are enriched with vulnerable host state, cloud inventory, Kubernetes context, and container-host context.
Limitations
· This rule detects suspicious staging behavior, not confirmed Copy Fail exploitation.
· Legitimate CI jobs, administrative scripts, build processes, and temporary maintenance workflows may overlap with this behavior.
· Confirmation requires correlation with vulnerable host state, privilege transition, privileged binary interaction, or post-escalation activity.
· File-extension matching should be validated against normalized Splunk fields before production deployment.
Detection Query Pattern
index=<linux_process_index>
(os="linux" OR host_os="linux" OR platform="linux")
(event_type="process" OR action="process_create" OR EventCode=1)
(user!="root" AND user!="")
(
process_path="/tmp/*"
OR process_path="/var/tmp/*"
OR process_path="/dev/shm/*"
OR process_path="/home/*"
OR process_path="*/workspace/*"
OR process_path="*/workdir/*"
OR process_path="*/build/*"
OR process_path="*/runner/*"
OR process_path="/mnt/*"
)
| eval suspicious_extension=if(
like(process_path,"%.sh")
OR like(process_path,"%.py")
OR like(process_path,"%.out")
OR like(process_path,"%.bin")
OR like(process_path,"%.elf"),
"true",
"false"
)
| where process_name IN ("python","python3","perl","ruby","bash","sh","dash","zsh","gcc","cc","make")
OR suspicious_extension="true"
| lookup linux_vulnerability_inventory host OUTPUT cve_2026_31431_status vulnerable_kernel asset_role exposure_state cloud_context kubernetes_context container_host_context
| lookup approved_linux_staging_activity host user process_name process_path OUTPUT approved_activity
| where isnull(approved_activity)
| eval priority=case(
cve_2026_31431_status="vulnerable" AND exposure_state="internet-facing","high",
cve_2026_31431_status="vulnerable","medium",
true(),"triage"
)
| table _time host user parent_process_name parent_process_path process_name process_path process_command_line cve_2026_31431_status vulnerable_kernel asset_role exposure_state cloud_context kubernetes_context container_host_context priority
Rule 2
Abnormal Low-Privilege-to-Root Process Transition
Rule Format
· Splunk SPL correlation search pattern.
Detection Purpose
· Detect suspicious transition from low-privilege execution to root-owned process activity on vulnerable or high-risk Linux systems.
· This rule targets the privilege-boundary outcome most relevant to local Linux privilege escalation.
· The rule avoids broad root-process alerting by requiring suspicious parentage, user context, host context, or vulnerable-state enrichment.
Detection Logic
· Identify root-owned process creation where the parent process, previous process, or source context is suspicious.
· Prioritize parent processes originating from writable paths, scripting engines, interactive shells, application accounts, service accounts, CI jobs, or container contexts.
· Exclude expected administrative paths such as approved sudo use, package management, service management, and configuration management.
· Increase confidence when the host is vulnerable, internet-facing, cloud-hosted, a Kubernetes node, a container host, or a CI runner.
· Treat this rule as stronger when paired with exploit staging, privileged binary interaction, sensitive file access, or post-root activity.
Required Telemetry
· Linux process creation telemetry.
· Parent and child process relationships.
· Process user and effective user.
· Command line.
· Executable path.
· Parent process path.
· Host role and vulnerability context.
· Administrative baseline or allowlist context.
Engineering Implementation Instructions
· Validate whether Splunk receives real user, effective user, parent process user, target process user, UID, and process ancestry fields.
· Do not assume parent_user or src_user is always present in every pipeline.
· Scope to Linux process telemetry with reliable parent-child relationships.
· Tune approved administrative workflows, including trusted sudo, package managers, service-control utilities, configuration management, and scheduled maintenance.
· Prioritize events where the parent process originates from writable paths, scripting engines, web-service users, CI users, container processes, or application accounts.
· Use vulnerable host state as prioritization context, not as sole evidence of exploitation.
· Correlate with staging or post-escalation evidence before declaring suspected Copy Fail exploitation.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.8
· The rule is strongly anchored to the required privilege escalation outcome rather than static artifacts.
· The rule remains resilient if exploit code is renamed, modified, or delivered through a different staging path.
· The score is high because abnormal low-privilege-to-root transition is a durable behavioral signal for this CVE class.
· Noise is manageable when administrative workflows, approved automation, and package-management activity are tuned.
TCR Assessment
· Operational TCR: 8.0
· Full-Telemetry TCR: 8.9
· Operational confidence depends on process ancestry, user and effective-user context, command-line capture, and normalization quality.
· Operational score is constrained because some Splunk pipelines may not reliably preserve parent-user fields.
· Full-telemetry confidence improves when Linux audit, EDR, vulnerability, identity, cloud, Kubernetes, and container-host context are correlated.
Limitations
· Abnormal privilege transition can result from other local privilege escalation methods and is not unique to Copy Fail.
· Poor parent-child process fidelity can reduce confidence.
· The rule requires administrative baseline tuning to avoid alerting on expected root activity.
· Parent-user fields should be treated as confidence-enhancing where available, not as the only required detection condition.
Detection Query Pattern
index=<linux_process_index>
(os="linux" OR host_os="linux" OR platform="linux")
(event_type="process" OR action="process_create" OR EventCode=1)
(user="root" OR effective_user="root" OR dest_user="root")
(
parent_process_path="/tmp/*"
OR parent_process_path="/var/tmp/*"
OR parent_process_path="/dev/shm/*"
OR parent_process_path="/home/*"
OR parent_process_path="*/workspace/*"
OR parent_process_path="*/workdir/*"
OR parent_process_path="*/build/*"
OR parent_process_path="*/runner/*"
OR parent_process_path="/mnt/*"
OR parent_process_name IN ("python","python3","perl","ruby","bash","sh","dash","zsh","gcc","cc","make","curl","wget","nc","ncat","socat")
OR src_user!="root"
OR parent_user!="root"
)
NOT process_name IN ("apt","apt-get","yum","dnf","rpm","dpkg","systemctl","service")
| lookup approved_linux_admin_activity host user process_name process_command_line OUTPUT approved_admin_activity
| where isnull(approved_admin_activity)
| lookup linux_vulnerability_inventory host OUTPUT cve_2026_31431_status vulnerable_kernel asset_role exposure_state cloud_context kubernetes_context container_host_context
| eval priority=case(
cve_2026_31431_status="vulnerable" AND (exposure_state="internet-facing" OR kubernetes_context="true" OR container_host_context="true"),"high",
cve_2026_31431_status="vulnerable","medium",
true(),"triage"
)
| table _time host user effective_user dest_user src_user parent_user parent_process_name parent_process_path process_name process_path process_command_line cve_2026_31431_status vulnerable_kernel asset_role exposure_state cloud_context kubernetes_context container_host_context priority
Rule 3
Post-Escalation Root Activity on Vulnerable Linux Workloads
Rule Format
· Splunk SPL correlation search pattern requiring process and file-event validation.
Detection Purpose
· Detect post-escalation root activity on vulnerable or high-risk Linux systems after suspicious local execution or privilege transition.
· This rule targets credential access, sensitive file access, persistence setup, security tool tampering, cloud metadata access, Kubernetes token access, and container runtime interaction.
· The rule supports Copy Fail triage by identifying high-impact activity that may follow successful root escalation.
Detection Logic
· Identify root-level command-line behavior associated with credential access, persistence setup, agent tampering, metadata access, or host discovery.
· Identify root-level file access to sensitive host files, SSH material, Kubernetes tokens, container runtime sockets, cloud identity material, or credential stores where file-event telemetry is available.
· Increase confidence when paired with prior exploit staging, abnormal low-privilege-to-root transition, vulnerable host state, Kubernetes node context, container-host context, or cloud Linux workload context.
· Deploy process-command-line logic and file-path logic as separate branches if the environment does not support both telemetry types equally.
· Require file-event visibility for file-access portions and process telemetry for command-line portions.
Required Telemetry
· Linux process creation telemetry.
· Linux file access or audit telemetry where available.
· Command-line capture.
· User and effective-user context.
· Process ancestry.
· Sensitive path visibility.
· Host role and vulnerability context.
· Cloud, Kubernetes, and container context where available.
Engineering Implementation Instructions
· Validate source coverage for Linux file access events before enabling file-path alert logic.
· If file telemetry is incomplete, deploy the process-command-line portions first and use file-access logic for hunting until coverage is validated.
· Add allowlists for backup tools, monitoring agents, vulnerability scanners, configuration management, approved administrative maintenance, and endpoint security tooling.
· Prioritize alerts on vulnerable cloud Linux instances, Kubernetes nodes, container hosts, CI runners, internet-facing systems, and high-value production workloads.
· Correlate with prior suspicious staging or abnormal privilege transition before declaring suspected Copy Fail exploitation.
· Preserve enough retention to support retrospective hunting across the vulnerable exposure period.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.6
· The rule targets durable post-escalation behavior that attackers commonly perform after obtaining root.
· The rule is resilient to exploit modification because it does not depend on the exploit primitive, proof-of-concept strings, or hashes.
· The score is constrained by overlap with legitimate administrative, backup, monitoring, and security tooling.
· The rule remains strong when correlated with vulnerable host state, suspicious staging, or abnormal privilege transition.
TCR Assessment
· Operational TCR: 8.0
· Full-Telemetry TCR: 8.8
· Operational confidence depends on file-audit coverage, command-line telemetry, process ancestry, effective-user context, enrichment quality, and retention.
· Full-telemetry confidence improves when EDR, Linux audit, vulnerability, cloud, Kubernetes, container-host, and identity data are correlated.
Limitations
· Post-root activity may result from other privilege escalation methods and is not unique to Copy Fail.
· File telemetry coverage may vary significantly by source and policy.
· Backup agents, vulnerability scanners, monitoring tools, and approved administrators may generate overlapping activity.
· This rule requires correlation with vulnerable state or prior suspicious activity for CVE-specific triage.
· The process and file branches should be validated separately before being combined into a production correlation search.
Detection Query Pattern
index=<linux_process_index>
(os="linux" OR host_os="linux" OR platform="linux")
(event_type="process" OR action="process_create" OR EventCode=1)
(user="root" OR effective_user="root" OR dest_user="root")
(
process_command_line="*cat /etc/shadow*"
OR process_command_line="*cat /etc/sudoers*"
OR process_command_line="*chmod +s*"
OR process_command_line="*chattr*"
OR process_command_line="*systemctl disable*"
OR process_command_line="*auditctl -D*"
OR process_command_line="*service auditd stop*"
OR process_command_line="*iptables -F*"
OR process_command_line="*curl 169.254.169.254*"
OR process_command_line="*wget 169.254.169.254*"
)
| eval telemetry_branch="process_command"
| append [
search index=<linux_file_index>
(os="linux" OR host_os="linux" OR platform="linux")
(user="root" OR effective_user="root" OR dest_user="root")
(
file_path="/etc/shadow"
OR file_path="/etc/sudoers"
OR file_path="/root/.ssh/*"
OR file_path="/var/run/docker.sock"
OR file_path="/run/containerd/containerd.sock"
OR file_path="/run/cri-dockerd.sock"
OR file_path="/var/lib/kubelet/*"
OR file_path="/var/run/secrets/kubernetes.io/*"
OR file_path="/etc/kubernetes/*"
OR file_path="/var/lib/containerd/*"
OR file_path="/var/lib/docker/*"
)
| eval telemetry_branch="file_event"
]
| lookup linux_vulnerability_inventory host OUTPUT cve_2026_31431_status vulnerable_kernel asset_role exposure_state cloud_context kubernetes_context container_host_context
| lookup approved_linux_admin_activity host user process_name process_command_line OUTPUT approved_admin_activity
| where isnull(approved_admin_activity)
| eval priority=case(
cve_2026_31431_status="vulnerable" AND (kubernetes_context="true" OR container_host_context="true" OR cloud_context="true" OR exposure_state="internet-facing"),"high",
cve_2026_31431_status="vulnerable","medium",
true(),"triage"
)
| table _time host telemetry_branch user effective_user process_name process_path process_command_line file_path cve_2026_31431_status vulnerable_kernel asset_role exposure_state cloud_context kubernetes_context container_host_context priority
Elastic
Required Data Views and Field Assumptions
· Elastic endpoint or Linux process data view containing ECS-aligned process events.
· Elastic file event data view where sensitive file access or modification logic is enabled.
· Vulnerability or asset enrichment showing affected kernel state, host role, exposure state, cloud context, Kubernetes context, and container-host context.
· Normalized process fields: process.name, process.executable, process.command_line, process.parent.name, process.parent.executable, process.parent.command_line.
· Normalized identity fields: user.name, user.id, user.effective.name, user.effective.id, or tenant-specific equivalent mappings.
· Normalized host and workload fields: host.name, host.id, host.os.type, host.os.kernel, cloud.account.id, cloud.instance.id, kubernetes.node.name, and container context where available.
· Field names, event categories, EQL support, sequence behavior, file-event visibility, and enrichment fields must be validated against the tenant’s ECS mapping, Elastic integration version, endpoint policy, Linux audit configuration, and vulnerability enrichment model before production deployment.
Rule 1
Writable-Path Exploit Staging on Vulnerable Linux Workloads
Rule Format
· Elastic EQL detection rule pattern.
Detection Purpose
· Detect suspicious local exploit staging where a non-root Linux process executes from a writable, transient, user-controlled, CI, container, or mounted workload path.
· This rule supports Copy Fail triage by identifying likely local exploit preparation on vulnerable or high-risk Linux assets.
· This rule avoids proof-of-concept filenames, hashes, CVE strings, and mandatory kernel-interface telemetry.
Detection Logic
· Identify Linux process execution from writable or transient paths such as /tmp, /var/tmp, /dev/shm, user home directories, CI workspace paths, mounted workload paths, or container writable layers.
· Require non-root user context where available.
· Prioritize scripting engines, shells, build tools, compiled temporary binaries, and executable-like files launched from writable locations.
· Increase confidence when the host is vulnerable, internet-facing, cloud-hosted, a Kubernetes node, a container host, or a CI runner.
· Treat root process creation, privileged binary interaction, sensitive file access, or post-escalation behavior as follow-on triage evidence rather than assuming staging equals exploitation.
Required Telemetry
· Linux process start events.
· Process executable path.
· Process command line.
· Parent process context.
· User or effective user context.
· Host identity.
· Host role and vulnerable-state enrichment where available.
· Cloud, Kubernetes, container-host, or CI context where available.
Engineering Implementation Instructions
· Validate ECS field coverage before deployment, especially process.executable, process.name, process.command_line, process.parent.executable, user.name, user.id, host.os.type, and event.type.
· Scope to Linux endpoints only.
· Use vulnerable-state enrichment for prioritization, not as the only alert condition.
· Add exceptions for approved CI jobs, package managers, configuration management tools, vulnerability scanners, backup agents, and known administrative automation.
· Tune by host role because CI runners, build systems, and container hosts may legitimately execute temporary binaries.
· Treat this rule as exploit-staging detection unless follow-on privilege transition or post-escalation behavior is present.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.3
· The rule is anchored to exploit staging behavior rather than brittle artifact indicators.
· The rule remains useful if public proof-of-concept material is renamed, recompiled, embedded, or modified.
· The score is constrained because staging alone is not confirmed exploitation and requires follow-on triage evidence.
· The rule remains deployable when tuned for CI, build, automation, and administrative workflows.
TCR Assessment
· Operational TCR: 8.1
· Full-Telemetry TCR: 8.8
· Operational confidence depends on Elastic process telemetry quality, command-line capture, path fidelity, user context, and endpoint coverage.
· Full-telemetry confidence improves when Elastic endpoint events are enriched with vulnerable host state, cloud workload context, Kubernetes context, and container-host context.
Limitations
· This rule detects suspicious staging behavior, not confirmed Copy Fail exploitation.
· Legitimate CI jobs, temporary maintenance scripts, administrative automation, and security tooling may overlap with this behavior.
· Confirmation requires correlation with vulnerable host state, privilege transition, privileged binary interaction, or post-escalation activity.
Detection Query Pattern
process where host.os.type == "linux"
and event.type == "start"
and not user.name in ("root")
and process.executable : (
"/tmp/*",
"/var/tmp/*",
"/dev/shm/*",
"/home/*",
"*/workspace/*",
"*/workdir/*",
"*/build/*",
"*/runner/*",
"/mnt/*"
)
and (
process.name in ("python", "python3", "perl", "ruby", "bash", "sh", "dash", "zsh", "gcc", "cc", "make")
or process.executable : ("*.sh", "*.py", "*.out", "*.bin", "*.elf")
)
Rule 2
Abnormal Low-Privilege-to-Root Process Transition
Rule Format
· Elastic EQL sequence detection rule pattern.
Detection Purpose
· Detect suspicious transition from low-privilege execution to root-owned process activity on vulnerable or high-risk Linux systems.
· This rule targets the privilege-boundary outcome most relevant to local Linux privilege escalation.
· The rule avoids broad root-process alerting by requiring suspicious staging context before the root-owned activity.
Detection Logic
· Identify a suspicious non-root process from a writable path, scripting engine, shell, build tool, CI context, container context, application account, or service account.
· Correlate with a root-owned process on the same host within a short time window.
· Exclude expected administrative workflows such as approved sudo, package management, service management, configuration management, and scheduled maintenance.
· Increase confidence when the host is vulnerable, internet-facing, cloud-hosted, a Kubernetes node, a container host, or a CI runner.
· Treat this rule as stronger when paired with sensitive file access, privileged binary interaction, or post-root activity.
Required Telemetry
· Linux process start events.
· Parent and child process relationships where available.
· Process executable path.
· Command line.
· User and effective user context.
· Host identity.
· Administrative baseline or exception context.
· Vulnerable host and asset role enrichment where available.
Engineering Implementation Instructions
· Validate whether the tenant has reliable user.name, user.id, user.effective.name, user.effective.id, host.id, and process parent fields.
· Validate EQL sequence support and ensure the selected join key, preferably host.id, is populated consistently.
· Scope to Linux endpoints only.
· Tune trusted administrator workflows, package managers, service-control utilities, configuration management, and scheduled maintenance.
· Prioritize parent processes from writable paths, scripting engines, web-service users, CI users, application accounts, container processes, or unknown binaries.
· Use vulnerable host state as prioritization context, not as sole evidence of exploitation.
· Correlate with staging, sensitive file access, or post-escalation behavior before declaring suspected Copy Fail exploitation.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.8
· The rule is strongly anchored to the privilege escalation outcome rather than static indicators.
· The rule remains resilient if exploit code is renamed, modified, or delivered through a different staging path.
· The score is high because abnormal low-privilege-to-root transition is a durable behavioral signal for this CVE class.
· Noise is manageable when approved administration, automation, package-management, and service-management paths are tuned.
TCR Assessment
· Operational TCR: 8.0
· Full-Telemetry TCR: 8.9
· Operational confidence depends on process ancestry, user and effective-user context, command-line capture, ECS normalization quality, and reliable sequence join fields.
· Operational score is constrained because effective-user and parent context visibility may vary by Elastic integration and endpoint policy.
· Full-telemetry confidence improves when Elastic endpoint telemetry is enriched with vulnerability state, identity context, cloud context, Kubernetes context, and container-host context.
Limitations
· Abnormal privilege transition can result from other local privilege escalation methods and is not unique to Copy Fail.
· Poor parent-child process fidelity, missing effective-user context, or inconsistent host.id population can reduce confidence.
· The rule requires administrative baseline tuning to avoid alerting on expected root activity.
· Sequence logic should be validated in the tenant before production alerting.
Detection Query Pattern
sequence by host.id with maxspan=5m
[process where host.os.type == "linux"
and event.type == "start"
and not user.name in ("root")
and (
process.executable : (
"/tmp/*",
"/var/tmp/*",
"/dev/shm/*",
"/home/*",
"*/workspace/*",
"*/workdir/*",
"*/build/*",
"*/runner/*",
"/mnt/*"
)
or process.name in ("python", "python3", "perl", "ruby", "bash", "sh", "dash", "zsh", "gcc", "cc", "make", "curl", "wget", "nc", "ncat", "socat")
)
]
[process where host.os.type == "linux"
and event.type == "start"
and (
user.name == "root"
or user.effective.name == "root"
or user.id == "0"
or user.effective.id == "0"
)
and not process.name in ("apt", "apt-get", "yum", "dnf", "rpm", "dpkg", "systemctl", "service")
]
Rule 3
Post-Escalation Root Activity on Vulnerable Linux Workloads
Rule Format
· Elastic EQL detection rule pattern requiring process and file-event validation.
Detection Purpose
· Detect post-escalation root activity on vulnerable or high-risk Linux systems after suspicious local execution or privilege transition.
· This rule targets credential access, sensitive file access, persistence setup, security tool tampering, cloud metadata access, Kubernetes token access, and container runtime interaction.
· The rule supports Copy Fail triage by identifying high-impact activity that may follow successful root escalation.
Detection Logic
· Identify root-level command-line behavior associated with credential access, persistence setup, security tool tampering, metadata access, or host discovery.
· Identify root-level access to sensitive host files, SSH material, Kubernetes tokens, container runtime sockets, cloud identity material, or credential stores where file-event telemetry is available.
· Increase confidence when paired with prior exploit staging, abnormal low-privilege-to-root transition, vulnerable host state, Kubernetes node context, container-host context, or cloud Linux workload context.
· Deploy process-command logic and file-path logic separately if the environment does not support both telemetry types equally.
· Require file-event visibility for file-access portions and process telemetry for command-line portions.
Required Telemetry
· Linux process start events.
· Linux file access, creation, or modification events where available.
· Command-line capture.
· User and effective-user context.
· Process ancestry.
· Sensitive path visibility.
· Host role and vulnerability context.
· Cloud, Kubernetes, and container context where available.
Engineering Implementation Instructions
· Validate Elastic file-event coverage before enabling file-path alert logic.
· Validate support for combining process and file event categories in the selected Elastic rule type; deploy separate process and file rules if tenant support or event coverage is inconsistent.
· If file telemetry is incomplete, deploy process-command logic first and use file-path logic for hunting until file-event coverage is validated.
· Add exceptions for backup tools, monitoring agents, vulnerability scanners, configuration management, approved administrative maintenance, endpoint security tooling, and legitimate Kubernetes node operations.
· Prioritize alerts on vulnerable cloud Linux instances, Kubernetes nodes, container hosts, CI runners, internet-facing systems, and high-value production workloads.
· Correlate with prior suspicious staging or abnormal privilege transition before declaring suspected Copy Fail exploitation.
· Preserve enough retention to support retrospective hunting across the vulnerable exposure period.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.6
· The rule targets durable post-escalation behavior commonly performed after obtaining root.
· The rule is resilient to exploit modification because it does not depend on the exploit primitive, proof-of-concept strings, or hashes.
· The score is constrained by overlap with legitimate administrative, backup, monitoring, and security tooling.
· The rule remains strong when correlated with vulnerable host state, suspicious staging, abnormal privilege transition, or workload context.
TCR Assessment
· Operational TCR: 7.9
· Full-Telemetry TCR: 8.8
· Operational confidence depends on file-event coverage, command-line telemetry, process ancestry, effective-user context, ECS normalization quality, enrichment quality, and retention.
· Operational score is constrained because file-event availability and mixed event-category support may vary by Elastic integration, endpoint policy, and rule type.
· Full-telemetry confidence improves when Elastic endpoint, Linux audit, vulnerability, cloud, Kubernetes, container-host, and identity data are correlated.
Limitations
· Post-root activity may result from other privilege escalation methods and is not unique to Copy Fail.
· File telemetry coverage may vary by Elastic integration, endpoint policy, and Linux audit configuration.
· Backup agents, vulnerability scanners, monitoring tools, endpoint security tools, Kubernetes operations, and approved administrators may generate overlapping activity.
· This rule requires correlation with vulnerable state or prior suspicious activity for CVE-specific triage.
· Process and file logic should be validated separately before being combined into production alerting.
Detection Query Pattern
any where host.os.type == "linux"
and (
(event.category == "process"
and event.type == "start"
and (
user.name == "root"
or user.effective.name == "root"
or user.id == "0"
or user.effective.id == "0"
)
and process.command_line : (
"*cat /etc/shadow*",
"*cat /etc/sudoers*",
"*chmod +s*",
"*chattr*",
"*systemctl disable*",
"*auditctl -D*",
"*service auditd stop*",
"*iptables -F*",
"*curl 169.254.169.254*",
"*wget 169.254.169.254*"
)
)
or
(event.category == "file"
and event.type in ("access", "creation", "change")
and (
user.name == "root"
or user.effective.name == "root"
or user.id == "0"
or user.effective.id == "0"
)
and file.path : (
"/etc/shadow",
"/etc/sudoers",
"/root/.ssh/*",
"/var/run/docker.sock",
"/run/containerd/containerd.sock",
"/run/cri-dockerd.sock",
"/var/lib/kubelet/*",
"/var/run/secrets/kubernetes.io/*",
"/etc/kubernetes/*",
"/var/lib/containerd/*",
"/var/lib/docker/*"
)
)
)
QRadar
Required Log Sources, Reference Sets, and Custom Properties
· Linux process telemetry from EDR, Linux audit, Sysmon for Linux, osquery, or equivalent endpoint sources.
· Linux file access or audit telemetry where sensitive-file detection is enabled.
· Vulnerability or asset enrichment identifying affected kernel state, host role, exposure state, cloud context, Kubernetes context, and container-host context.
· Required normalized process properties: Process Name, Process Path, Process Command Line, Parent Process Name, Parent Process Path.
· Required normalized identity properties: Username, Effective Username, UID, Effective UID, where available.
· Required normalized host properties: Hostname, Asset ID, Host OS, Kernel Version, Asset Role, Exposure State, Cloud Context, Kubernetes Context, Container Host Context.
· Required reference sets or building blocks: vulnerable Linux assets, high-value Linux workloads, approved Linux administration, approved automation, approved CI activity, approved backup or monitoring tools, and approved vulnerability-scanning activity.
· Property names must be adjusted to the customer’s QRadar DSM mappings, custom property definitions, log-source configuration, CRE building blocks, reference set naming, and vulnerability-management integration before deployment.
Rule 1
Abnormal Low-Privilege-to-Root Transition on Vulnerable Linux Assets
Rule Format
· QRadar AQL and CRE correlation rule pattern.
Detection Purpose
· Detect suspicious transition from low-privilege or non-administrative execution to root-owned process activity on vulnerable or high-risk Linux systems.
· This rule targets the privilege-boundary outcome most relevant to local Linux privilege escalation.
· The rule avoids broad root-process alerting by requiring suspicious parentage, non-administrative origin, host context, vulnerable-state enrichment, or approved-activity exclusions.
Detection Logic
· Identify root-owned process activity where the parent process or process context originates from a writable path, scripting engine, interactive shell, application account, service account, CI job, container context, or other non-administrative context.
· Exclude approved administrative workflows, package management, service management, configuration management, scheduled maintenance, trusted automation, and authorized security tooling.
· Increase priority when the host is vulnerable, internet-facing, cloud-hosted, a Kubernetes node, a container host, a CI runner, or a high-value production system.
· Treat this rule as stronger when paired with exploit staging, privileged binary interaction, sensitive file access, or post-root activity.
· Do not label this as confirmed Copy Fail exploitation without vulnerable-state context or additional corroborating activity.
Required Telemetry
· Linux process creation telemetry.
· Parent and child process relationships where available.
· Process user and effective-user context.
· Process command line.
· Process executable path.
· Parent process path.
· Host role and vulnerable-state context.
· Approved-administration and automation reference sets.
Engineering Implementation Instructions
· Validate QRadar DSM parsing and custom properties for process name, process path, command line, parent process, username, effective username, UID, hostname, and host operating system.
· Do not assume parent-user or effective-user properties are available unless explicitly parsed and validated.
· Scope to Linux process telemetry with reliable parent-child context.
· Use vulnerable asset and high-value workload reference sets for prioritization, not as sole evidence of exploitation.
· Add approved-administration and automation reference sets before enabling offense generation.
· Suppress expected root activity from approved sudo, package managers, service-control utilities, configuration management, backup tools, vulnerability scanners, and maintenance windows.
· Route offenses involving vulnerable Kubernetes nodes, container hosts, cloud Linux instances, internet-facing workloads, CI runners, or high-value systems at higher priority.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.3
· The rule is anchored to privilege-transition behavior rather than static indicators.
· The rule remains useful if exploit code is renamed, modified, or delivered through a different staging path.
· The score is constrained by QRadar’s dependency on normalized endpoint or audit telemetry and reliable custom properties.
· The rule remains deployable when expected administrative workflows, approved automation, and security tooling are tuned through reference sets.
TCR Assessment
· Operational TCR: 7.6
· Full-Telemetry TCR: 8.5
· Operational confidence depends on Linux process telemetry quality, parent-child fidelity, effective-user visibility, custom property parsing, reference set quality, and enrichment quality.
· Operational score is constrained because parent-user and effective-user context may be inconsistent across QRadar log sources.
· Full-telemetry confidence improves when EDR, Linux audit, vulnerability, identity, cloud, Kubernetes, and container-host context are consistently normalized into QRadar.
Limitations
· Abnormal privilege transition can result from other local privilege escalation methods and is not unique to Copy Fail.
· QRadar confidence is reduced when custom properties are missing, inconsistent, or not mapped across log sources.
· Parent-user and effective-user context may not be consistently available.
· Administrative baseline tuning is required to avoid alerting on expected root activity.
· AQL syntax and custom property names must be validated in the customer tenant before production use.
Detection Query Pattern
SELECT
"starttime" AS event_time,
"Hostname" AS host,
"Username" AS user_name,
"Effective Username" AS effective_user,
"UID" AS uid,
"Effective UID" AS effective_uid,
"Process Name" AS process_name,
"Process Path" AS process_path,
"Process Command Line" AS process_command_line,
"Parent Process Name" AS parent_process_name,
"Parent Process Path" AS parent_process_path,
"Asset Role" AS asset_role,
"Exposure State" AS exposure_state,
"Cloud Context" AS cloud_context,
"Kubernetes Context" AS kubernetes_context,
"Container Host Context" AS container_host_context
FROM events
WHERE
"Host OS" ILIKE '%linux%'
AND (
"Effective Username" = 'root'
OR "Username" = 'root'
OR "Effective UID" = '0'
OR "UID" = '0'
)
AND (
"Parent Process Path" ILIKE '/tmp/%'
OR "Parent Process Path" ILIKE '/var/tmp/%'
OR "Parent Process Path" ILIKE '/dev/shm/%'
OR "Parent Process Path" ILIKE '/home/%'
OR "Parent Process Path" ILIKE '%/workspace/%'
OR "Parent Process Path" ILIKE '%/workdir/%'
OR "Parent Process Path" ILIKE '%/build/%'
OR "Parent Process Path" ILIKE '%/runner/%'
OR "Parent Process Path" ILIKE '/mnt/%'
OR "Parent Process Name" IN ('python','python3','perl','ruby','bash','sh','dash','zsh','gcc','cc','make','curl','wget','nc','ncat','socat')
)
AND "Process Name" NOT IN ('apt','apt-get','yum','dnf','rpm','dpkg','systemctl','service')
AND NOT REFERENCESETCONTAINS('Approved_Linux_Admin_Activity', "Hostname")
AND NOT REFERENCESETCONTAINS('Approved_Linux_Automation', "Hostname")
AND (
REFERENCESETCONTAINS('CVE_2026_31431_Vulnerable_Linux_Assets', "Hostname")
OR REFERENCESETCONTAINS('High_Value_Linux_Workloads', "Hostname")
)
LAST 10 MINUTES
Rule 2
Post-Escalation Root Activity on Vulnerable Linux Workloads
Rule Format
· QRadar AQL and CRE correlation rule pattern requiring process and file-event validation.
Detection Purpose
· Detect post-escalation root activity on vulnerable or high-risk Linux systems after suspicious local execution or abnormal privilege transition.
· This rule targets sensitive file access, credential access, persistence setup, security tool tampering, cloud metadata access, Kubernetes token access, and container runtime interaction.
· The rule supports Copy Fail triage by identifying high-impact behavior that may follow successful root escalation.
Detection Logic
· Identify root-level command-line behavior associated with credential access, persistence setup, security tool tampering, metadata access, or host discovery.
· Identify root-level file access to sensitive host files, SSH material, Kubernetes tokens, container runtime sockets, cloud identity material, or credential stores where file-event telemetry is available.
· Increase priority when the host is vulnerable, cloud-hosted, internet-facing, a Kubernetes node, a container host, a CI runner, or a high-value production system.
· Treat this rule as stronger when paired with prior exploit staging, abnormal privilege transition, vulnerable host state, or workload context.
· Deploy process-command and file-event logic separately if the environment does not support both telemetry types equally.
Required Telemetry
· Linux process creation telemetry.
· Linux file access or audit telemetry where available.
· Process command line.
· Process user and effective-user context.
· Process ancestry.
· Sensitive file path visibility.
· Host role and vulnerable-state context.
· Cloud, Kubernetes, and container-host context where available.
Engineering Implementation Instructions
· Validate QRadar DSM parsing for process command line, file path, file action, username, effective username, UID, hostname, and host operating system.
· Validate Linux file-event coverage before enabling sensitive-file access logic.
· If file telemetry is incomplete, deploy process-command logic first and use file-path logic for hunting until file coverage is validated.
· Add reference sets for approved backup tools, monitoring tools, vulnerability scanners, endpoint agents, configuration management tools, authorized maintenance windows, and legitimate Kubernetes node operations.
· Prioritize offenses on vulnerable cloud Linux instances, Kubernetes nodes, container hosts, CI runners, internet-facing workloads, and high-value production systems.
· Correlate with prior suspicious staging or abnormal privilege transition before declaring suspected Copy Fail exploitation.
· Preserve event retention long enough to support retrospective hunting across the vulnerable exposure period.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.2
· The rule targets durable post-escalation behavior that attackers commonly perform after obtaining root.
· The rule does not depend on exploit strings, proof-of-concept filenames, hashes, or direct kernel-interface telemetry.
· The score is constrained by overlap with legitimate administrative, backup, monitoring, vulnerability scanning, Kubernetes operations, and security tooling.
· The rule remains deployable when sensitive paths, approved tools, vulnerable assets, and high-value host roles are scoped through reference sets.
TCR Assessment
· Operational TCR: 7.5
· Full-Telemetry TCR: 8.4
· Operational confidence depends on process-command telemetry, file-event coverage, effective-user visibility, custom property parsing, enrichment quality, reference set quality, and retention.
· Operational score is constrained because file-event coverage and QRadar custom property parsing vary significantly by Linux audit, EDR source, and DSM mapping.
· Full-telemetry confidence improves when EDR, Linux audit, vulnerability, cloud, Kubernetes, container-host, and identity context are consistently normalized into QRadar.
Limitations
· Post-root activity may result from other privilege escalation methods and is not unique to Copy Fail.
· File-event coverage may vary by Linux audit policy, EDR source, and QRadar parsing.
· Backup agents, vulnerability scanners, monitoring tools, endpoint agents, Kubernetes operations, and approved administrators may generate overlapping activity.
· This rule requires correlation with vulnerable state or prior suspicious activity for CVE-specific triage.
· AQL syntax, custom property names, reference sets, and file-event fields must be validated in the customer tenant before production use.
Detection Query Pattern
SELECT
"starttime" AS event_time,
"Hostname" AS host,
"Username" AS user_name,
"Effective Username" AS effective_user,
"UID" AS uid,
"Effective UID" AS effective_uid,
"Process Name" AS process_name,
"Process Path" AS process_path,
"Process Command Line" AS process_command_line,
"File Path" AS file_path,
"File Action" AS file_action,
"Asset Role" AS asset_role,
"Exposure State" AS exposure_state,
"Cloud Context" AS cloud_context,
"Kubernetes Context" AS kubernetes_context,
"Container Host Context" AS container_host_context
FROM events
WHERE
"Host OS" ILIKE '%linux%'
AND (
"Effective Username" = 'root'
OR "Username" = 'root'
OR "Effective UID" = '0'
OR "UID" = '0'
)
AND (
"Process Command Line" ILIKE '%cat /etc/shadow%'
OR "Process Command Line" ILIKE '%cat /etc/sudoers%'
OR "Process Command Line" ILIKE '%chmod +s%'
OR "Process Command Line" ILIKE '%chattr%'
OR "Process Command Line" ILIKE '%systemctl disable%'
OR "Process Command Line" ILIKE '%auditctl -D%'
OR "Process Command Line" ILIKE '%service auditd stop%'
OR "Process Command Line" ILIKE '%iptables -F%'
OR "Process Command Line" ILIKE '%curl 169.254.169.254%'
OR "Process Command Line" ILIKE '%wget 169.254.169.254%'
OR "File Path" IN ('/etc/shadow','/etc/sudoers','/var/run/docker.sock','/run/containerd/containerd.sock','/run/cri-dockerd.sock')
OR "File Path" ILIKE '/root/.ssh/%'
OR "File Path" ILIKE '/var/lib/kubelet/%'
OR "File Path" ILIKE '/var/run/secrets/kubernetes.io/%'
OR "File Path" ILIKE '/etc/kubernetes/%'
OR "File Path" ILIKE '/var/lib/containerd/%'
OR "File Path" ILIKE '/var/lib/docker/%'
)
AND NOT REFERENCESETCONTAINS('Approved_Linux_Admin_Activity', "Hostname")
AND NOT REFERENCESETCONTAINS('Approved_Linux_Backup_Monitoring_Tools', "Process Name")
AND NOT REFERENCESETCONTAINS('Approved_Linux_Vulnerability_Scanners', "Process Name")
AND (
REFERENCESETCONTAINS('CVE_2026_31431_Vulnerable_Linux_Assets', "Hostname")
OR REFERENCESETCONTAINS('High_Value_Linux_Workloads', "Hostname")
)
LAST 10 MINUTES
SIGMA
Required Backend Mapping and Field Assumptions
· Linux process creation telemetry must be available in the target backend.
· Linux file access, creation, or modification telemetry is required only for file-event portions of post-escalation detection.
· Required normalized process fields include process name, process path, command line, parent process name, parent process path, and process user.
· Required normalized identity fields include user, effective user, UID, effective UID, or target user equivalents where available.
· Required host context should include hostname, host operating system, kernel version, host role, asset criticality, exposure state, and vulnerable-state enrichment where available.
· Optional workload context should include cloud account, cloud instance, Kubernetes node, container host, CI runner, and workload ownership fields where available.
· SIGMA translation must be validated in the target backend before production deployment because field names, path operators, user context, and file telemetry support vary significantly.
Rule 1
Writable-Path Exploit Staging on Linux Workloads
Rule Format
· SIGMA rule pattern for Linux process creation telemetry.
Detection Purpose
· Detect suspicious local exploit staging where a non-root Linux process executes from a writable, transient, user-controlled, CI, container, or mounted workload path.
· This rule supports Copy Fail triage by identifying likely local exploit preparation on vulnerable or high-risk Linux systems.
· This rule avoids proof-of-concept filenames, hashes, CVE strings, and mandatory kernel-interface telemetry.
Detection Logic
· Identify Linux process execution from writable or transient paths such as /tmp, /var/tmp, /dev/shm, user home directories, CI workspace paths, mounted workload paths, or container writable layers.
· Require non-root user context where available.
· Prioritize scripting engines, shells, build tools, compiled temporary binaries, and executable-like files launched from writable locations.
· Increase priority when the translated backend can enrich the host as vulnerable, internet-facing, cloud-hosted, a Kubernetes node, a container host, or a CI runner.
· Treat this rule as staging detection unless follow-on privilege transition or post-escalation activity is present.
Required Telemetry
· Linux process creation telemetry.
· Process executable path.
· Process command line.
· Parent process context.
· User or effective-user context.
· Host identity.
· Vulnerable-state enrichment where available.
· Host role, cloud, Kubernetes, container-host, or CI context where available.
Engineering Implementation Instructions
· Validate backend mapping for Image, CommandLine, ParentImage, ParentCommandLine, User, effective-user equivalents, host operating system, and process creation fields.
· Scope translated detections to Linux systems only.
· Add backend-specific exceptions for approved CI jobs, package managers, configuration management tools, vulnerability scanners, backup agents, and administrative automation.
· Tune by host role because CI runners, build systems, and container hosts may legitimately execute temporary binaries.
· Use vulnerable-state enrichment for prioritization only.
· Do not treat this rule as confirmed Copy Fail exploitation without privilege transition, vulnerable host state, or post-escalation evidence.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.2
· The rule is anchored to exploit staging behavior rather than brittle artifact indicators.
· The rule remains useful if public proof-of-concept material is renamed, recompiled, embedded, or modified.
· The score is constrained because staging alone is not confirmed exploitation and backend translation quality can vary.
· The rule remains deployable when translated with proper Linux process mappings and tuned for CI, build, automation, and administrative workflows.
TCR Assessment
· Operational TCR: 7.8
· Full-Telemetry TCR: 8.6
· Operational confidence depends on backend process telemetry quality, translation fidelity, command-line capture, user context, and enrichment quality.
· Full-telemetry confidence improves when the backend enriches SIGMA output with vulnerable host state, cloud workload context, Kubernetes context, and container-host context.
Limitations
· This rule detects suspicious staging behavior, not confirmed Copy Fail exploitation.
· Translation fidelity depends on backend field mappings and Linux process telemetry quality.
· Legitimate CI jobs, administrative scripts, build processes, and temporary maintenance workflows may overlap with this behavior.
· Confirmation requires vulnerable host state, privilege transition, privileged binary interaction, or post-escalation activity.
Detection Rule Pattern
title: Writable-Path Exploit Staging on Linux Workloads
id: 9d4e0a8a-4c7d-4e9c-8f7b-314310000001
status: test
description: Detects suspicious non-root Linux process execution from writable or transient paths that may indicate local exploit staging relevant to CVE-2026-31431 triage.
references:
- CVE-2026-31431
author: CyberDax
date: 2026/05/02
logsource:
product: linux
category: process_creation
detection:
selection_path:
Image|contains:
- '/tmp/'
- '/var/tmp/'
- '/dev/shm/'
- '/home/'
- '/workspace/'
- '/workdir/'
- '/build/'
- '/runner/'
- '/mnt/'
selection_interpreter_or_tool:
Image|endswith:
- '/python'
- '/python3'
- '/perl'
- '/ruby'
- '/bash'
- '/sh'
- '/dash'
- '/zsh'
- '/gcc'
- '/cc'
- '/make'
selection_executable_like:
Image|endswith:
- '.sh'
- '.py'
- '.out'
- '.bin'
- '.elf'
filter_root:
User:
- 'root'
- '0'
condition: selection_path and (selection_interpreter_or_tool or selection_executable_like) and not filter_root
fields:
- UtcTime
- Computer
- User
- Image
- CommandLine
- ParentImage
- ParentCommandLine
falsepositives:
- Approved CI jobs
- Administrative automation
- Package management
- Configuration management
- Vulnerability scanning
- Backup or monitoring tools
level: medium
tags:
- attack.privilege_escalation
- attack.t1068
- cve.2026.31431
Rule 2
Abnormal Low-Privilege-to-Root Process Transition
Rule Format
· SIGMA rule pattern for Linux process creation telemetry.
Detection Purpose
· Detect suspicious root-owned process activity where the parent process or execution context indicates low-privilege staging, writable-path execution, scripting activity, CI execution, container context, or application/service account origin.
· This rule targets the privilege-boundary outcome relevant to local Linux privilege escalation.
· This rule avoids broad root-process alerting by requiring suspicious parentage or execution context.
Detection Logic
· Identify root-owned process creation or effective-root execution.
· Require suspicious parentage from writable paths, scripting engines, shells, build tools, CI paths, container paths, or application-controlled paths.
· Exclude common administrative package and service-management activity.
· Increase priority when the backend can enrich the host as vulnerable, internet-facing, cloud-hosted, a Kubernetes node, a container host, a CI runner, or a high-value production system.
· Treat this rule as stronger when paired with exploit staging, sensitive file access, privileged binary interaction, or post-root activity.
Required Telemetry
· Linux process creation telemetry.
· Process user or effective-user context.
· Process executable path.
· Parent process executable path.
· Command line.
· Host identity.
· Administrative baseline or exception context.
· Vulnerable-state enrichment where available.
Engineering Implementation Instructions
· Validate backend field support for root or effective-root context before deployment.
· Validate parent process mapping because this rule depends on suspicious parentage.
· Add exceptions for approved sudo, package-management, service-management, configuration-management, backup, vulnerability-scanning, and maintenance workflows.
· Use vulnerable host state as prioritization context, not as proof of exploitation.
· Do not declare suspected Copy Fail exploitation without vulnerable-state context or corroborating staging or post-escalation behavior.
· Split into backend-specific variants if the target platform handles User, EffectiveUser, or UID fields differently.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.5
· The rule is anchored to privilege-transition behavior and suspicious parentage rather than static artifacts.
· The rule remains resilient if exploit code is renamed, modified, or delivered through a different staging path.
· The score is high for SIGMA because the behavior is durable, but constrained by backend translation and effective-user field availability.
· The rule remains deployable when expected administrative workflows and automation are tuned.
TCR Assessment
· Operational TCR: 7.7
· Full-Telemetry TCR: 8.6
· Operational confidence depends on backend process telemetry quality, parent process fidelity, user/effective-user mapping, and translation fidelity.
· Full-telemetry confidence improves when backend data includes Linux audit, EDR, vulnerable asset state, cloud, Kubernetes, and container-host context.
Limitations
· Abnormal privilege transition can result from other local privilege escalation methods and is not unique to Copy Fail.
· Effective-user and parent process fields may not translate consistently across backends.
· Administrative baseline tuning is required to avoid alerting on expected root activity.
· Backend validation is required before production deployment.
Detection Rule Pattern
title: Abnormal Low-Privilege-to-Root Process Transition
id: c473df2b-ff45-47af-9b46-314310000002
status: test
description: Detects root-owned Linux process activity with suspicious parentage from writable paths, scripting engines, or user-controlled execution contexts relevant to local privilege escalation triage.
references:
- CVE-2026-31431
author: CyberDax
date: 2026/05/02
logsource:
product: linux
category: process_creation
detection:
selection_root_user:
User:
- 'root'
- '0'
selection_parent_path:
ParentImage|contains:
- '/tmp/'
- '/var/tmp/'
- '/dev/shm/'
- '/home/'
- '/workspace/'
- '/workdir/'
- '/build/'
- '/runner/'
- '/mnt/'
selection_parent_process:
ParentImage|endswith:
- '/python'
- '/python3'
- '/perl'
- '/ruby'
- '/bash'
- '/sh'
- '/dash'
- '/zsh'
- '/gcc'
- '/cc'
- '/make'
- '/curl'
- '/wget'
- '/nc'
- '/ncat'
- '/socat'
filter_admin_process:
Image|endswith:
- '/apt'
- '/apt-get'
- '/yum'
- '/dnf'
- '/rpm'
- '/dpkg'
- '/systemctl'
- '/service'
condition: selection_root_user and (selection_parent_path or selection_parent_process) and not filter_admin_process
fields:
- UtcTime
- Computer
- User
- Image
- CommandLine
- ParentImage
- ParentCommandLine
falsepositives:
- Approved administrator activity
- Package management
- Service management
- Configuration management
- Backup or monitoring tools
level: high
tags:
- attack.privilege_escalation
- attack.t1068
- cve.2026.31431
Rule 3
Post-Escalation Root Activity on Vulnerable Linux Workloads
Rule Format
· SIGMA rule patterns for Linux process telemetry and Linux file telemetry, requiring backend validation.
Detection Purpose
· Detect post-escalation root activity on vulnerable or high-risk Linux systems after suspicious local execution or privilege transition.
· This rule targets credential access, sensitive file access, persistence setup, security tool tampering, cloud metadata access, Kubernetes token access, and container runtime interaction.
· This rule supports Copy Fail triage by identifying high-impact activity that may follow successful root escalation.
Detection Logic
· Identify root-level command-line behavior associated with credential access, persistence setup, audit or security tool tampering, metadata access, or host discovery.
· Identify root-level access to sensitive files, SSH material, Kubernetes tokens, container runtime sockets, and container or Kubernetes directories where backend file-event telemetry is available.
· Increase priority when the backend can enrich the host as vulnerable, cloud-hosted, internet-facing, a Kubernetes node, a container host, a CI runner, or a high-value production system.
· Deploy process and file portions separately if the backend cannot combine process and file telemetry reliably.
· Treat this rule as strongest when paired with prior staging, abnormal privilege transition, or vulnerable host state.
Required Telemetry
· Linux process creation telemetry.
· Linux file telemetry where available.
· Process command line.
· Process user or effective-user context.
· Sensitive file path visibility.
· Host role and vulnerable-state enrichment where available.
· Cloud, Kubernetes, and container context where available.
Engineering Implementation Instructions
· Validate backend support for both process and file telemetry before using combined logic.
· If file telemetry is incomplete, deploy process-command logic first and use file-path logic as a hunt query until validated.
· Add exceptions for backup tools, monitoring agents, vulnerability scanners, configuration management, endpoint security tooling, Kubernetes operations, and approved maintenance.
· Prioritize alerts on vulnerable cloud Linux instances, Kubernetes nodes, container hosts, CI runners, internet-facing systems, and high-value production workloads.
· Correlate with prior staging or abnormal privilege transition before declaring suspected Copy Fail exploitation.
· Split process and file logic into separate backend rules where the target backend cannot combine process and file categories reliably.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.3
· The rule targets durable post-escalation behavior commonly performed after obtaining root.
· The rule is resilient to exploit modification because it does not depend on the exploit primitive, proof-of-concept strings, or hashes.
· The score is constrained by overlap with legitimate administrative, backup, monitoring, security tooling, and Kubernetes operations.
· The rule remains strong when correlated with vulnerable host state, suspicious staging, abnormal privilege transition, or workload context.
TCR Assessment
· Operational TCR: 7.5
· Full-Telemetry TCR: 8.5
· Operational confidence depends on backend support for process and file telemetry, user/effective-user mapping, field translation, enrichment, and retention.
· Full-telemetry confidence improves when backend data includes EDR, Linux audit, vulnerable asset state, cloud, Kubernetes, and container-host context.
Limitations
· Post-root activity can result from other privilege escalation methods and is not unique to Copy Fail.
· File telemetry support varies significantly across SIGMA backends.
· Combined process and file logic may need to be split during translation.
· Backup agents, vulnerability scanners, monitoring tools, endpoint security tools, Kubernetes operations, and approved administrators may generate overlapping activity.
Detection Rule Pattern
title: Post-Escalation Root Activity on Vulnerable Linux Workloads
id: 2fd2d7b0-7984-44f4-a935-314310000003
status: test
description: Detects root-level Linux activity involving sensitive credential files, persistence commands, audit tampering, cloud metadata access, Kubernetes material, or container runtime resources after suspected local privilege escalation.
references:
- CVE-2026-31431
author: CyberDax
date: 2026/05/02
logsource:
product: linux
detection:
selection_root_user:
User:
- 'root'
- '0'
selection_process_commands:
CommandLine|contains:
- 'cat /etc/shadow'
- 'cat /etc/sudoers'
- 'chmod +s'
- 'chattr'
- 'systemctl disable'
- 'auditctl -D'
- 'service auditd stop'
- 'iptables -F'
- 'curl 169.254.169.254'
- 'wget 169.254.169.254'
selection_sensitive_files:
TargetFilename|contains:
- '/etc/shadow'
- '/etc/sudoers'
- '/root/.ssh/'
- '/var/run/docker.sock'
- '/run/containerd/containerd.sock'
- '/run/cri-dockerd.sock'
- '/var/lib/kubelet/'
- '/var/run/secrets/kubernetes.io/'
- '/etc/kubernetes/'
- '/var/lib/containerd/'
- '/var/lib/docker/'
condition: selection_root_user and (selection_process_commands or selection_sensitive_files)
fields:
- UtcTime
- Computer
- User
- Image
- CommandLine
- ParentImage
- TargetFilename
falsepositives:
- Approved administrator activity
- Backup tools
- Vulnerability scanners
- Monitoring tools
- Endpoint security tooling
- Kubernetes node operations
level: high
tags:
- attack.privilege_escalation
- attack.credential_access
- attack.persistence
- attack.defense_evasion
- attack.t1068
- cve.2026.31431
YARA
Rule 1
Copy Fail Proof-of-Concept and Exploit Artifact Indicators
Rule Format
· YARA rule pattern for supporting artifact detection.
Detection Purpose
· Detect files that contain implementation-oriented strings, symbols, comments, or code references associated with Copy Fail or CVE-2026-31431 proof-of-concept material.
· This rule supports triage, threat hunting, malware repository review, endpoint collection review, suspicious file review, container image review, CI artifact review, and incident-response evidence analysis.
· This rule does not detect exploitation directly and must not be treated as confirmation of successful root escalation.
Detection Logic
· Identify executable or script-like artifacts containing references to Copy Fail, CVE-2026-31431, AF_ALG, algif_aead, splice(), page-cache manipulation, SUID behavior, Linux kernel crypto interfaces, or root escalation concepts.
· Require executable or script context before matching on exploit-adjacent string combinations.
· Require multiple indicator families to reduce matches on benign advisories, vulnerability notes, or documentation.
· Treat matches in executable files, scripts, temporary paths, container layers, CI workspaces, or suspicious user-controlled locations as higher priority when file path or collection context is available.
· Treat matches in documentation, reports, patch notes, advisories, or authorized validation material as lower priority unless paired with execution or staging telemetry.
· Use this rule as supporting evidence only.
Required Telemetry
· File collection or file scanning capability.
· File path and file name context.
· File type or magic-byte inspection.
· Endpoint, sandbox, malware repository, container image, CI artifact, or incident-response collection source.
· Host role and vulnerable-state context where available.
· Execution telemetry or file-write telemetry where available.
Engineering Implementation Instructions
· Deploy this rule in YARA scanning workflows for endpoint triage, sandbox review, malware repository scanning, incident-response collections, suspicious file downloads, CI artifacts, container layers, and collected Linux files.
· Do not run this rule as a high-confidence exploitation detector.
· Prioritize matches found in /tmp, /var/tmp, /dev/shm, user home directories, CI workspaces, container writable layers, mounted workload paths, and suspicious download locations.
· Deprioritize matches found only in reports, patch notes, advisories, vulnerability-management exports, or security-research documentation.
· Correlate YARA matches with process execution, writable-path staging, vulnerable host state, low-privilege-to-root transition, privileged binary interaction, or post-escalation activity before treating the event as suspected Copy Fail exploitation.
· Update strings if confirmed public exploit artifacts, symbols, implementation patterns, or proof-of-concept structures change.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 7.5
· The rule is artifact-focused and therefore less robust than behavior-based endpoint or SIEM detections.
· The rule can identify known, lightly modified, or research-derived proof-of-concept material, but attackers can remove strings, rename symbols, recompile code, encode content, or embed the logic into unrelated files.
· The score is constrained by artifact fragility and low standalone exploitation confidence.
· The rule remains useful as a supporting triage and evidence-discovery mechanism when paired with host behavior and vulnerable-state context.
TCR Assessment
· Operational TCR: 7.1
· Full-Telemetry TCR: 8.0
· Operational confidence depends on file collection coverage, scan scope, artifact availability, file type context, file path context, and analyst triage.
· Full-telemetry confidence improves when YARA matches are enriched with execution telemetry, vulnerable host state, endpoint context, container context, CI context, and incident-response collection metadata.
Limitations
· YARA cannot confirm successful exploitation of CVE-2026-31431.
· YARA cannot observe local privilege transitions, page-cache effects, root-owned child processes, kernel behavior, or post-root activity unless related artifacts are present in scanned files.
· Static strings can be removed, renamed, encoded, compressed, or replaced.
· Benign research, documentation, vendor advisories, vulnerability scans, and authorized validation materials may match.
· This rule requires correlation with host behavior and vulnerable-state context before escalation.
Detection Rule Pattern
rule CopyFail_CVE_2026_31431_Exploit_Artifact_Supporting
{
meta:
description = "Supporting detection for Copy Fail / CVE-2026-31431 proof-of-concept or exploit-adjacent artifacts"
author = "CyberDax"
date = "2026-05-02"
status = "test"
scope = "supporting artifact detection only"
caveat = "Does not confirm exploitation or privilege escalation"
strings:
$cve_1 = "CVE-2026-31431" ascii wide nocase
$name_1 = "Copy Fail" ascii wide nocase
$name_2 = "copy-fail" ascii wide nocase
$kernel_1 = "AF_ALG" ascii wide
$kernel_2 = "algif_aead" ascii wide
$kernel_3 = "splice(" ascii wide
$kernel_4 = "page cache" ascii wide nocase
$kernel_5 = "page-cache" ascii wide nocase
$kernel_6 = "sockaddr_alg" ascii wide
$kernel_7 = "SOL_ALG" ascii wide
$kernel_8 = "AF_ALG socket" ascii wide nocase
$concept_1 = "SUID" ascii wide
$concept_2 = "setuid" ascii wide nocase
$concept_3 = "/etc/shadow" ascii wide
$concept_4 = "/etc/sudoers" ascii wide
$concept_5 = "privilege escalation" ascii wide nocase
$concept_6 = "root shell" ascii wide nocase
$concept_7 = "kernel crypto" ascii wide nocase
$script_1 = "#!/bin/sh" ascii
$script_2 = "#!/bin/bash" ascii
$script_3 = "#!/usr/bin/env python" ascii
$script_4 = "#!/usr/bin/python" ascii
$script_5 = "#!/usr/bin/python3" ascii
condition:
(
(filesize > 4 and uint32(0) == 0x464c457f) or
any of ($script_*)
)
and
(
(
(any of ($cve_*) or any of ($name_*)) and
(
2 of ($kernel_*) or
(1 of ($kernel_*) and 2 of ($concept_*))
)
)
or
(
3 of ($kernel_*) and
2 of ($concept_*)
)
)
}
AWS
Required AWS Data Sources and Field Assumptions
· Amazon Inspector or Security Hub findings for CVE-2026-31431 affected Linux assets.
· AWS Config or equivalent cloud asset inventory for EC2 instance, AMI, platform, tags, account, region, exposure, and ownership context.
· EC2 metadata and tagging for workload owner, environment, internet exposure, business criticality, and production status.
· EKS inventory where applicable, including cluster name, node group, node role, namespace ownership, and workload criticality.
· CloudTrail or CloudTrail Lake for IAM, STS, Secrets Manager, SSM, EC2, EKS, KMS, S3, and control-plane activity.
· GuardDuty findings where available for suspicious credential use, instance compromise indicators, metadata access, anomalous API behavior, or unusual role activity.
· Identity context for IAM role, assumed role, instance profile, federated user, access key, session issuer, source IP, user agent, and account.
· Role-to-workload mapping that links IAM roles, instance profiles, EC2 instances, EKS nodes, CI runners, and high-value Linux workloads.
· All query patterns must be adapted to the customer’s AWS Organizations structure, Security Hub aggregation model, Config coverage, tagging taxonomy, CloudTrail Lake event data store, EKS architecture, IAM role model, and SIEM export format before deployment.
Rule 1
Vulnerable Linux Cloud Workload Exposure Prioritization
Rule Format
· AWS Security Hub, Amazon Inspector, AWS Config, and Athena query pattern for exposure prioritization.
Detection Purpose
· Identify AWS-hosted Linux workloads affected by CVE-2026-31431 where exposure, workload role, EKS node placement, IAM role permissions, or business criticality increases risk.
· This rule supports patch prioritization, hunt scoping, host telemetry collection, and containment planning.
· This rule does not detect confirmed exploitation by itself.
Detection Logic
· Identify active Amazon Inspector or Security Hub findings for CVE-2026-31431.
· Correlate affected resources with EC2 instance, EKS node, container host, CI runner, production workload, internet-facing system, or high-value workload context.
· Increase priority for systems with public exposure, privileged IAM instance profiles, production tags, EKS worker-node roles, CI/build roles, or sensitive workload ownership.
· Use vulnerability state as prioritization evidence only.
· Require host telemetry, post-escalation cloud activity, or other corroborating behavior before labeling the case as suspected exploitation.
· Suppress stale, archived, suppressed, resolved, or inventory-only findings that no longer represent active exposure.
Required Telemetry
· Amazon Inspector findings.
· Security Hub vulnerability findings.
· AWS Config resource inventory.
· EC2 instance metadata and tags.
· EKS node or node-group context where available.
· Internet exposure or security group context.
· IAM instance profile or role context.
· Workload owner and asset criticality tags.
· Finding state, workflow state, update time, and resource status.
Engineering Implementation Instructions
· Confirm Inspector coverage across EC2 instances, EKS nodes, container hosts, and Linux workloads.
· Confirm Security Hub aggregation across all relevant AWS accounts and regions.
· Validate that CVE-2026-31431 findings are active, not suppressed, not archived, not resolved, and not stale.
· Join vulnerability findings to Config, EC2, EKS, security group, IAM, and tagging data before prioritization.
· Prioritize internet-facing systems, EKS worker nodes, container hosts, CI runners, production workloads, and systems with privileged IAM roles.
· Treat stopped, terminated, replaced, or rebuilt instances carefully because vulnerability findings and inventory state may lag real asset state.
· Do not generate an exploitation alert from vulnerable-state data alone.
· Use this rule to drive patch urgency, hunt priority, host telemetry collection, and workload owner notification.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.0
· The rule is anchored to active vulnerable-state exposure and cloud workload prioritization, not exploitation behavior.
· The score is constrained because inventory and vulnerability findings do not prove local privilege escalation.
· The rule is resilient to exploit modification because it does not rely on proof-of-concept artifacts.
· The rule remains valuable for KEV-driven prioritization, hunt scoping, host telemetry collection, and patch urgency.
TCR Assessment
· Operational TCR: 7.9
· Full-Telemetry TCR: 8.8
· Operational confidence depends on Inspector coverage, Security Hub aggregation, Config accuracy, tag quality, account coverage, role-to-workload mapping, and finding freshness.
· Full-telemetry confidence improves when EC2, EKS, IAM, public exposure, workload ownership, vulnerability state, and endpoint telemetry are centrally correlated.
Limitations
· Vulnerable AWS workload state is not exploitation evidence.
· Inspector and Security Hub findings may lag behind actual patch state.
· Ephemeral, autoscaled, stopped, terminated, or manually maintained instances may create inventory drift.
· Missing tags, incomplete Config coverage, fragmented account visibility, or weak role-to-workload mapping can reduce prioritization accuracy.
· Host telemetry is required to determine whether Copy Fail exploitation occurred.
Detection Query Pattern
-- AWS Athena / Security Hub / Inspector / Config enrichment pattern
-- Table and field names must be adapted to the customer export model.
WITH vulnerable_findings AS (
SELECT
account_id,
region,
resource_id,
finding_id,
title,
description,
severity_label,
workflow_status,
record_state,
compliance_status,
updated_at
FROM security_hub_findings
WHERE record_state = 'ACTIVE'
AND workflow_status NOT IN ('SUPPRESSED', 'RESOLVED')
AND (
compliance_status IS NULL
OR compliance_status NOT IN ('PASSED')
)
AND (
vulnerability_id = 'CVE-2026-31431'
OR title LIKE '%CVE-2026-31431%'
OR description LIKE '%CVE-2026-31431%'
)
),
asset_context AS (
SELECT
account_id,
region,
resource_id,
resource_type,
instance_id,
instance_state,
platform,
kernel_version,
public_ip_present,
internet_facing,
iam_instance_profile,
iam_role_arn,
eks_cluster,
eks_node_group,
workload_type,
workload_owner,
environment,
asset_criticality,
tags
FROM aws_config_ec2_asset_inventory
WHERE platform LIKE '%Linux%'
AND instance_state NOT IN ('terminated')
)
SELECT
vf.account_id,
vf.region,
vf.resource_id,
ac.instance_id,
vf.severity_label,
ac.platform,
ac.kernel_version,
ac.instance_state,
ac.internet_facing,
ac.iam_instance_profile,
ac.iam_role_arn,
ac.eks_cluster,
ac.eks_node_group,
ac.workload_type,
ac.workload_owner,
ac.environment,
ac.asset_criticality,
CASE
WHEN ac.internet_facing = true
AND ac.asset_criticality IN ('critical','high') THEN 'high'
WHEN ac.eks_cluster IS NOT NULL
OR ac.eks_node_group IS NOT NULL
OR ac.workload_type IN ('eks-node','container-host','ci-runner')
OR ac.iam_role_arn IS NOT NULL THEN 'high'
WHEN ac.environment = 'production' THEN 'medium'
ELSE 'triage'
END AS priority
FROM vulnerable_findings vf
JOIN asset_context ac
ON vf.account_id = ac.account_id
AND vf.region = ac.region
AND vf.resource_id = ac.resource_id;
Rule 2
Post-Escalation AWS Credential and Control-Plane Activity After Suspected Linux Host Compromise
Rule Format
· CloudTrail Lake, GuardDuty, and AWS control-plane correlation pattern.
Detection Purpose
· Detect AWS control-plane behavior that may follow successful local root escalation on a vulnerable Linux workload.
· This rule focuses on credential use, metadata-driven role activity, secret access, SSM command execution, role assumption, snapshot or storage access, security group modification, KMS use, and other cloud-side blast-radius indicators after suspected host compromise.
· This rule does not detect the kernel exploit primitive directly.
Detection Logic
· Identify suspicious AWS API activity from IAM roles, instance profiles, access keys, or assumed-role sessions associated with vulnerable Linux workloads.
· Prioritize STS, IAM, Secrets Manager, SSM, EC2, EKS, KMS, and S3 activity that occurs after suspected host compromise, GuardDuty findings, suspicious metadata access, abnormal source IP, unusual user agent, or unexpected session behavior.
· Increase priority when the IAM role belongs to a vulnerable EC2 instance, EKS node, container host, CI runner, or high-value workload.
· Treat the alert as stronger when paired with host-level exploit staging, abnormal privilege transition, or post-root behavior from EDR or Linux audit telemetry.
· Do not label cloud API activity as confirmed Copy Fail exploitation without host-side corroboration.
· Suppress approved automation, deployment systems, backup workflows, security tooling, and known maintenance windows before escalation.
Required Telemetry
· CloudTrail or CloudTrail Lake management events.
· GuardDuty findings where available.
· IAM role and instance profile mapping.
· EC2 instance and EKS node inventory.
· Security Hub or Inspector vulnerable-state context.
· Source IP, user agent, access key, assumed role, session issuer, event source, event name, request parameters, and account.
· Secrets Manager, SSM, EC2, EKS, KMS, S3, STS, and IAM API event visibility.
· Approved cloud automation source IPs, user agents, roles, and maintenance context.
· Host compromise or endpoint telemetry enrichment where available.
Engineering Implementation Instructions
· Map IAM roles and instance profiles back to EC2 instances, EKS nodes, container hosts, CI runners, and high-value workloads.
· Validate CloudTrail coverage across all accounts and regions.
· Enable and aggregate GuardDuty findings where available.
· Establish expected role behavior for production workloads, EKS nodes, CI systems, automation roles, backup roles, deployment systems, and SSM-managed instances.
· Prioritize activity from vulnerable workloads where unusual API behavior follows host compromise indicators.
· Add allowlists for approved automation, deployment systems, backup jobs, security tooling, SSM maintenance windows, and known administrative role use.
· Correlate with host telemetry before declaring suspected Copy Fail exploitation.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.4
· The rule is anchored to post-escalation cloud activity and credential-use behavior rather than static exploit artifacts.
· The rule remains useful if the local exploit code changes because it focuses on cloud-side consequences of compromised workload credentials.
· The score is constrained because AWS control-plane events do not directly prove the local kernel exploit path.
· The rule is strong when tied to vulnerable workload context and host compromise indicators.
TCR Assessment
· Operational TCR: 7.7
· Full-Telemetry TCR: 8.7
· Operational confidence depends on CloudTrail coverage, GuardDuty coverage, IAM role mapping, instance-profile attribution, finding freshness, approved automation baselines, and enrichment quality.
· Full-telemetry confidence improves when CloudTrail, GuardDuty, Inspector, Security Hub, Config, EKS, IAM, and host telemetry are centrally correlated.
Limitations
· AWS control-plane activity may follow many compromise paths and is not unique to Copy Fail.
· CloudTrail cannot directly observe local Linux privilege escalation.
· Legitimate automation, deployment pipelines, SSM activity, backup operations, and security tooling may generate overlapping API activity.
· Instance profile and role mapping must be accurate to connect cloud activity to vulnerable workloads.
· Host telemetry is required for high-confidence Copy Fail exploitation assessment.
Detection Query Pattern
-- CloudTrail Lake SQL pattern.
-- Event data store, table names, and role-to-instance mapping must be adapted per environment.
SELECT
ct.eventTime,
ct.recipientAccountId,
ct.awsRegion,
ct.eventSource,
ct.eventName,
ct.userIdentity.type AS identity_type,
ct.userIdentity.arn AS identity_arn,
ct.userIdentity.accessKeyId AS access_key_id,
ct.userIdentity.sessionContext.sessionIssuer.arn AS session_issuer_arn,
ct.sourceIPAddress,
ct.userAgent,
ct.requestParameters,
ct.responseElements,
vrm.instance_id,
vrm.workload_type,
vrm.asset_criticality,
vrm.exposure_state,
vrm.eks_cluster,
vrm.eks_node_group
FROM <cloudtrail_lake_event_data_store> ct
JOIN vulnerable_linux_workload_role_map vrm
ON ct.userIdentity.sessionContext.sessionIssuer.arn = vrm.iam_role_arn
WHERE
ct.eventSource IN (
'sts.amazonaws.com',
'iam.amazonaws.com',
'secretsmanager.amazonaws.com',
'ssm.amazonaws.com',
'ec2.amazonaws.com',
'eks.amazonaws.com',
'kms.amazonaws.com',
's3.amazonaws.com'
)
AND ct.eventName IN (
'AssumeRole',
'GetCallerIdentity',
'GetSecretValue',
'PutParameter',
'GetParameter',
'GetParameters',
'SendCommand',
'StartSession',
'CreateAccessKey',
'AttachUserPolicy',
'AttachRolePolicy',
'CreatePolicyVersion',
'ModifyInstanceAttribute',
'AuthorizeSecurityGroupIngress',
'CreateSnapshot',
'CopySnapshot',
'CreateVolume',
'AttachVolume',
'DescribeCluster',
'Decrypt',
'ListBuckets',
'GetObject'
)
AND (
vrm.cve_2026_31431_status = 'vulnerable'
OR vrm.asset_criticality IN ('critical','high')
OR vrm.workload_type IN ('ec2','eks-node','container-host','ci-runner')
)
AND (
ct.sourceIPAddress NOT IN (
SELECT approved_source_ip
FROM approved_cloud_admin_sources
)
OR ct.userAgent NOT IN (
SELECT approved_user_agent
FROM approved_cloud_automation_user_agents
)
);
Azure
Required Azure Data Sources and Field Assumptions
· Microsoft Defender Vulnerability Management or Defender for Cloud findings for CVE-2026-31431 affected Linux assets.
· Azure Resource Graph inventory for VM, VMSS, AKS node, OS, image, subscription, resource group, tags, exposure, managed identity, and ownership context.
· Azure VM metadata and tagging for workload owner, environment, internet exposure, business criticality, and production status.
· AKS inventory where applicable, including cluster name, node pool, node resource group, node role, namespace ownership, and workload criticality.
· Azure Activity Logs for subscription, resource, role assignment, VM, network, Key Vault, Storage, AKS, and control-plane activity.
· Microsoft Entra ID sign-in and audit logs for identity activity, service principal activity, managed identity activity where available, conditional access context, and role assignment changes.
· Microsoft Defender for Cloud alerts where available for suspicious VM behavior, credential access, unusual workload activity, or compromised resource indicators.
· Key Vault diagnostic logs, Storage diagnostic logs, Azure Monitor logs, Defender for Endpoint telemetry, and Sentinel tables where available.
· Managed identity mapping that links system-assigned and user-assigned managed identities to Azure VMs, VMSS instances, AKS nodes, container hosts, CI runners, and high-value Linux workloads.
· All query patterns must be adapted to the customer’s Azure tenant structure, management group hierarchy, subscription model, Defender coverage, Resource Graph schema, AKS architecture, managed identity model, Sentinel workspace design, diagnostic settings, and SIEM export format before deployment.
Rule 1
Vulnerable Azure Linux Workload Exposure Prioritization
Rule Format
· Microsoft Defender for Cloud, Azure Resource Graph, and Sentinel KQL query pattern for exposure prioritization.
Detection Purpose
· Identify Azure-hosted Linux workloads affected by CVE-2026-31431 where exposure, workload role, AKS node placement, managed identity permissions, or business criticality increases risk.
· This rule supports patch prioritization, hunt scoping, host telemetry collection, and containment planning.
· This rule does not detect confirmed exploitation by itself.
Detection Logic
· Identify active Defender for Cloud or vulnerability-management findings for CVE-2026-31431.
· Correlate affected resources with Azure VM, VMSS, AKS node, container host, CI runner, production workload, internet-facing system, or high-value workload context.
· Increase priority for systems with public exposure, privileged managed identities, production tags, AKS node-pool roles, CI/build roles, or sensitive workload ownership.
· Use vulnerable state as prioritization evidence only.
· Require host telemetry, post-escalation cloud activity, Defender for Endpoint signal, or other corroborating behavior before labeling the case as suspected exploitation.
· Suppress stale, resolved, exempted, suppressed, or inventory-only findings that no longer represent active exposure.
Required Telemetry
· Defender for Cloud vulnerability findings.
· Microsoft Defender Vulnerability Management findings where available.
· Azure Resource Graph inventory.
· Azure VM and VMSS metadata and tags.
· AKS node or node-pool context where available.
· Public exposure or network security group context.
· Managed identity or service principal context.
· Workload owner and asset criticality tags.
· Finding state, update time, resource state, and exemption status.
Engineering Implementation Instructions
· Confirm Defender coverage across Azure VMs, VMSS instances, AKS nodes, container hosts, and Linux workloads.
· Confirm centralized visibility across relevant tenants, management groups, subscriptions, and resource groups.
· Validate that CVE-2026-31431 findings are active, not exempted, not suppressed, not resolved, and not stale.
· Join vulnerability findings to Resource Graph, VM metadata, AKS inventory, network exposure, managed identity, and tagging data before prioritization.
· Prioritize internet-facing systems, AKS worker nodes, container hosts, CI runners, production workloads, and systems with privileged managed identities.
· Treat stopped, deallocated, replaced, rebuilt, or ephemeral instances carefully because vulnerability findings and inventory state may lag real asset state.
· Do not generate an exploitation alert from vulnerable-state data alone.
· Use this rule to drive patch urgency, hunt priority, host telemetry collection, workload owner notification, and Defender for Endpoint evidence review.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.0
· The rule is anchored to active vulnerable-state exposure and Azure workload prioritization, not exploitation behavior.
· The score is constrained because inventory and vulnerability findings do not prove local privilege escalation.
· The rule is resilient to exploit modification because it does not rely on proof-of-concept artifacts.
· The rule remains valuable for KEV-driven prioritization, hunt scoping, host telemetry collection, and patch urgency.
TCR Assessment
· Operational TCR: 7.8
· Full-Telemetry TCR: 8.8
· Operational confidence depends on Defender coverage, Resource Graph accuracy, tag quality, subscription coverage, managed identity mapping, finding freshness, exposure context, and resource-state accuracy.
· Full-telemetry confidence improves when Azure VM, AKS, managed identity, public exposure, workload ownership, vulnerable state, and endpoint telemetry are centrally correlated.
Limitations
· Vulnerable Azure workload state is not exploitation evidence.
· Defender and vulnerability findings may lag behind actual patch state.
· Ephemeral, autoscaled, deallocated, rebuilt, or manually maintained instances may create inventory drift.
· Missing tags, incomplete Defender coverage, fragmented subscription visibility, or weak managed identity mapping can reduce prioritization accuracy.
· Host telemetry is required to determine whether Copy Fail exploitation occurred.
Detection Query Pattern
// Azure Resource Graph / Defender for Cloud / Sentinel enrichment pattern.
// Table and field names must be adapted to the customer export model.
let VulnerableFindings =
SecurityRecommendation
| where RecommendationDisplayName has "CVE-2026-31431"
or Description has "CVE-2026-31431"
or AdditionalData has "CVE-2026-31431"
| where RecommendationState == "Unhealthy"
| where tostring(AdditionalData) !has "Exempted"
| project
SubscriptionId,
ResourceId = tolower(AssessedResourceId),
FindingName = RecommendationDisplayName,
FindingState = RecommendationState,
Severity,
LastUpdated = TimeGenerated;
let AssetContext =
Resources
| where type =~ "microsoft.compute/virtualmachines"
or type =~ "microsoft.compute/virtualmachinescalesets/virtualmachines"
| extend ResourceId = tolower(id)
| extend PowerState = tostring(properties.extended.instanceView.powerState.displayStatus)
| extend OsType = tostring(properties.storageProfile.osDisk.osType)
| extend Environment = tostring(tags.environment)
| extend WorkloadOwner = tostring(tags.owner)
| extend AssetCriticality = tostring(tags.criticality)
| extend WorkloadType = tostring(tags.workload_type)
| extend InternetFacing = tostring(tags.internet_facing)
| extend ManagedIdentityPresent = iff(isnotempty(identity), true, false)
| where OsType =~ "Linux" or tostring(properties.storageProfile.imageReference.offer) has "linux"
| project
SubscriptionId = subscriptionId,
ResourceId,
ResourceName = name,
ResourceType = type,
ResourceGroup = resourceGroup,
Location = location,
PowerState,
OsType,
Environment,
WorkloadOwner,
AssetCriticality,
WorkloadType,
InternetFacing,
ManagedIdentityPresent;
VulnerableFindings
| join kind=inner AssetContext on SubscriptionId, ResourceId
| where PowerState !has "deallocated" and PowerState !has "stopped"
| extend Priority = case(
InternetFacing =~ "true" and AssetCriticality in~ ("critical","high"), "high",
ManagedIdentityPresent == true or WorkloadType in~ ("aks-node","container-host","ci-runner"), "high",
Environment =~ "production", "medium",
"triage"
)
| project
LastUpdated,
SubscriptionId,
ResourceGroup,
ResourceName,
ResourceType,
Location,
PowerState,
Severity,
FindingName,
FindingState,
Environment,
WorkloadOwner,
AssetCriticality,
WorkloadType,
InternetFacing,
ManagedIdentityPresent,
Priority
Rule 2
Post-Escalation Azure Managed Identity and Control-Plane Activity After Suspected Linux Host Compromise
Rule Format
· Azure Activity Logs, Microsoft Entra ID, Defender for Cloud, Key Vault, Storage, and Sentinel KQL correlation pattern.
Detection Purpose
· Detect Azure control-plane behavior that may follow successful local root escalation on a vulnerable Linux workload.
· This rule focuses on managed identity use, service principal activity, role assignment changes, Key Vault access, Storage access, VM command execution, AKS access, network modification, snapshot or disk activity, and other cloud-side blast-radius indicators after suspected host compromise.
· This rule does not detect the kernel exploit primitive directly.
Detection Logic
· Identify suspicious Azure API activity from managed identities, service principals, or identities associated with vulnerable Linux workloads.
· Prioritize role assignment changes, Key Vault secret access, VM Run Command activity, AKS credential or cluster access, Storage data access, network security group changes, disk snapshot activity, and privilege-relevant control-plane operations.
· Increase priority when the managed identity belongs to a vulnerable Azure VM, AKS node, container host, CI runner, or high-value workload.
· Treat the alert as stronger when paired with host-level exploit staging, abnormal privilege transition, or post-root behavior from Defender for Endpoint, Linux audit, or other host telemetry.
· Do not label cloud API activity as confirmed Copy Fail exploitation without host-side corroboration.
· Suppress approved automation, deployment systems, backup workflows, security tooling, maintenance windows, and known administrative role use before escalation.
Required Telemetry
· Azure Activity Logs.
· Microsoft Entra ID sign-in and audit logs where available.
· Defender for Cloud alerts where available.
· Managed identity and service principal mapping.
· Azure VM, VMSS, and AKS node inventory.
· Defender or vulnerability-management vulnerable-state context.
· Source IP, user agent where available, caller identity, app ID, service principal ID, managed identity resource ID, operation name, resource provider, resource group, subscription, and request status.
· Key Vault, Storage, AKS, Compute, Network, Authorization, and Managed Identity event visibility.
· Approved automation source IPs, user agents, identities, service principals, and maintenance context.
· Host compromise or endpoint telemetry enrichment where available.
Engineering Implementation Instructions
· Map managed identities and service principals back to Azure VMs, VMSS instances, AKS nodes, container hosts, CI runners, and high-value workloads.
· Validate Azure Activity Log coverage across all relevant subscriptions and management groups.
· Validate Microsoft Entra ID audit and sign-in visibility for service principals and managed identities where available.
· Enable and aggregate Defender for Cloud alerts where available.
· Establish expected identity behavior for production workloads, AKS nodes, CI systems, automation identities, backup identities, deployment systems, and Azure Run Command or VM extensions.
· Prioritize activity from vulnerable workloads where unusual API behavior follows host compromise indicators.
· Add allowlists for approved automation, deployment systems, backup jobs, security tooling, maintenance windows, and known administrative identity use.
· Correlate with host telemetry before declaring suspected Copy Fail exploitation.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.4
· The rule is anchored to post-escalation cloud activity and identity-use behavior rather than static exploit artifacts.
· The rule remains useful if the local exploit code changes because it focuses on cloud-side consequences of compromised workload identities.
· The score is constrained because Azure control-plane events do not directly prove the local kernel exploit path.
· The rule is strong when tied to vulnerable workload context and host compromise indicators.
TCR Assessment
· Operational TCR: 7.6
· Full-Telemetry TCR: 8.7
· Operational confidence depends on Azure Activity Log coverage, Microsoft Entra ID visibility, Defender coverage, managed identity mapping, workload attribution, approved automation baselines, and enrichment quality.
· Operational score is constrained because managed identity attribution, user-agent visibility, and diagnostic logging coverage may vary across tenants.
· Full-telemetry confidence improves when Activity Logs, Defender, Resource Graph, Entra ID, AKS, Key Vault, Storage, managed identity mapping, and host telemetry are centrally correlated.
Limitations
· Azure control-plane activity may follow many compromise paths and is not unique to Copy Fail.
· Azure Activity Logs cannot directly observe local Linux privilege escalation.
· Legitimate automation, deployment pipelines, VM Run Command activity, backup operations, and security tooling may generate overlapping control-plane activity.
· Managed identity and service principal mapping must be accurate to connect cloud activity to vulnerable workloads.
· Host telemetry is required for high-confidence Copy Fail exploitation assessment.
Detection Query Pattern
// Sentinel / Log Analytics KQL pattern.
// Table names and field names must be adapted to the customer workspace, connector design, diagnostic settings, and enrichment model.
let VulnerableWorkloadIdentities =
Resources
| where type =~ "microsoft.compute/virtualmachines"
or type =~ "microsoft.compute/virtualmachinescalesets/virtualmachines"
| extend ResourceId = tolower(id)
| extend ManagedIdentityPrincipalId = tostring(identity.principalId)
| extend Environment = tostring(tags.environment)
| extend WorkloadOwner = tostring(tags.owner)
| extend AssetCriticality = tostring(tags.criticality)
| extend WorkloadType = tostring(tags.workload_type)
| where isnotempty(ManagedIdentityPrincipalId)
| join kind=inner (
SecurityRecommendation
| where RecommendationDisplayName has "CVE-2026-31431"
or Description has "CVE-2026-31431"
or AdditionalData has "CVE-2026-31431"
| where RecommendationState == "Unhealthy"
| project AssessedResourceId = tolower(AssessedResourceId)
) on $left.ResourceId == $right.AssessedResourceId
| project ManagedIdentityPrincipalId, ResourceId, Environment, WorkloadOwner, AssetCriticality, WorkloadType;
let SuspiciousAzureActivity =
AzureActivity
| where OperationNameValue in~ (
"Microsoft.Authorization/roleAssignments/write",
"Microsoft.Authorization/roleDefinitions/write",
"Microsoft.Compute/virtualMachines/runCommand/action",
"Microsoft.Compute/virtualMachines/extensions/write",
"Microsoft.Network/networkSecurityGroups/securityRules/write",
"Microsoft.Compute/snapshots/write",
"Microsoft.Compute/disks/write",
"Microsoft.ContainerService/managedClusters/listClusterUserCredential/action",
"Microsoft.ContainerService/managedClusters/listClusterAdminCredential/action",
"Microsoft.KeyVault/vaults/secrets/read",
"Microsoft.Storage/storageAccounts/listKeys/action"
)
| where ActivityStatusValue in~ ("Success", "Succeeded", "Accepted")
| project
TimeGenerated,
SubscriptionId,
ResourceGroup,
ResourceId = tolower(ResourceId),
OperationNameValue,
Caller,
CallerIpAddress,
ActivityStatusValue,
CorrelationId,
Properties;
SuspiciousAzureActivity
| join kind=inner VulnerableWorkloadIdentities on $left.Caller == $right.ManagedIdentityPrincipalId
| where CallerIpAddress !in~ (dynamic(["<approved_admin_ip_1>", "<approved_admin_ip_2>"]))
| extend Priority = case(
AssetCriticality in~ ("critical","high"), "high",
WorkloadType in~ ("aks-node","container-host","ci-runner"), "high",
Environment =~ "production", "medium",
"triage"
)
| project
TimeGenerated,
SubscriptionId,
ResourceGroup,
OperationNameValue,
Caller,
CallerIpAddress,
ActivityStatusValue,
ResourceId,
Environment,
WorkloadOwner,
AssetCriticality,
WorkloadType,
Priority,
CorrelationId,
Properties
GCP
Required GCP Data Sources and Field Assumptions
· Security Command Center or VM Manager vulnerability findings for CVE-2026-31431 affected Linux assets.
· Cloud Asset Inventory for Compute Engine instance, instance template, image, service account, project, folder, organization, labels, exposure, and ownership context.
· Compute Engine metadata and labels for workload owner, environment, internet exposure, business criticality, production status, and attached service account.
· GKE inventory where applicable, including cluster name, node pool, node service account, namespace ownership, workload identity context, and workload criticality.
· Cloud Audit Logs for IAM, service account, Compute Engine, GKE, Secret Manager, Cloud KMS, Cloud Storage, firewall, and control-plane activity.
· Data Access logs for Secret Manager, Cloud Storage, and Cloud KMS where required and operationally approved.
· Security Command Center findings where available for suspicious VM behavior, credential access, anomalous service account use, or compromised resource indicators.
· Service account mapping that links service accounts and workload identities to Compute Engine instances, GKE nodes, container hosts, CI runners, and high-value Linux workloads.
· Approved automation context for expected source IPs, user agents, service accounts, deployment systems, backup workflows, security tooling, and maintenance windows.
· All query patterns must be adapted to the customer’s GCP organization structure, folder hierarchy, project model, Security Command Center tier, VM Manager coverage, Cloud Asset Inventory export schema, GKE architecture, service account model, audit log coverage, Data Access logging posture, and SIEM export format before deployment.
Rule 1
Vulnerable GCP Linux Workload Exposure Prioritization
Rule Format
· Security Command Center, VM Manager, Cloud Asset Inventory, and BigQuery query pattern for exposure prioritization.
Detection Purpose
· Identify GCP-hosted Linux workloads affected by CVE-2026-31431 where exposure, workload role, GKE node placement, service account permissions, or business criticality increases risk.
· This rule supports patch prioritization, hunt scoping, host telemetry collection, workload owner notification, and containment planning.
· This rule does not detect confirmed exploitation by itself.
Detection Logic
· Identify active Security Command Center or VM Manager vulnerability findings for CVE-2026-31431.
· Correlate affected resources with Compute Engine VM, managed instance group, GKE node, container host, CI runner, production workload, internet-facing system, or high-value workload context.
· Increase priority for systems with public exposure, privileged service accounts, production labels, GKE node-pool roles, CI/build roles, or sensitive workload ownership.
· Use vulnerable state as prioritization evidence only.
· Require host telemetry, post-escalation cloud activity, Security Command Center compromise signal, or other corroborating behavior before labeling the case as suspected exploitation.
· Suppress inactive, muted, resolved, stale, deleted, terminated, or inventory-only findings that no longer represent active exposure.
Required Telemetry
· Security Command Center vulnerability findings.
· VM Manager vulnerability findings where available.
· Cloud Asset Inventory exports.
· Compute Engine VM metadata and labels.
· GKE node or node-pool context where available.
· Public exposure or firewall context.
· Service account context.
· Workload owner and asset criticality labels.
· Finding state, update time, resource state, mute status, and exposure status.
Engineering Implementation Instructions
· Confirm Security Command Center and VM Manager coverage across Compute Engine instances, GKE nodes, container hosts, and Linux workloads.
· Confirm centralized visibility across relevant organizations, folders, projects, and regions.
· Validate that CVE-2026-31431 findings are active, not muted, not resolved, not stale, and not tied only to retired inventory.
· Join vulnerability findings to Cloud Asset Inventory, Compute Engine metadata, GKE inventory, firewall exposure, service account context, and labels before prioritization.
· Prioritize internet-facing systems, GKE worker nodes, container hosts, CI runners, production workloads, and systems with privileged service accounts.
· Treat stopped, deleted, replaced, rebuilt, autoscaled, or ephemeral instances carefully because vulnerability findings and inventory state may lag real asset state.
· Do not generate an exploitation alert from vulnerable-state data alone.
· Use this rule to drive patch urgency, hunt priority, host telemetry collection, workload owner notification, and endpoint evidence review.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.0
· The rule is anchored to active vulnerable-state exposure and GCP workload prioritization, not exploitation behavior.
· The score is constrained because inventory and vulnerability findings do not prove local privilege escalation.
· The rule is resilient to exploit modification because it does not rely on proof-of-concept artifacts.
· The rule remains valuable for KEV-driven prioritization, hunt scoping, host telemetry collection, and patch urgency.
TCR Assessment
· Operational TCR: 7.8
· Full-Telemetry TCR: 8.8
· Operational confidence depends on Security Command Center coverage, VM Manager coverage, Cloud Asset Inventory accuracy, label quality, project coverage, service account mapping, finding freshness, exposure context, and resource-state accuracy.
· Full-telemetry confidence improves when Compute Engine, GKE, service account, public exposure, workload ownership, vulnerable state, and endpoint telemetry are centrally correlated.
Limitations
· Vulnerable GCP workload state is not exploitation evidence.
· Security Command Center and VM Manager findings may lag behind actual patch state.
· Ephemeral, autoscaled, stopped, deleted, rebuilt, or manually maintained instances may create inventory drift.
· Missing labels, incomplete vulnerability coverage, fragmented project visibility, or weak service account mapping can reduce prioritization accuracy.
· Host telemetry is required to determine whether Copy Fail exploitation occurred.
Detection Query Pattern
-- BigQuery / Security Command Center / VM Manager / Cloud Asset Inventory enrichment pattern.
-- Table and field names must be adapted to the customer export model.
WITH vulnerable_findings AS (
SELECT
organization_id,
folder_id,
project_id,
resource_name,
finding_id,
category,
severity,
state,
mute,
event_time,
update_time,
finding_class,
description
FROM `security_command_center_findings`
WHERE state = 'ACTIVE'
AND (mute IS NULL OR mute != 'MUTED')
AND (
description LIKE '%CVE-2026-31431%'
OR category LIKE '%CVE-2026-31431%'
OR finding_id LIKE '%CVE-2026-31431%'
)
),
asset_context AS (
SELECT
project_id,
resource_name,
asset_type,
instance_id,
instance_status,
os_type,
kernel_version,
public_ip_present,
internet_facing,
service_account_email,
gke_cluster,
gke_node_pool,
workload_type,
workload_owner,
environment,
asset_criticality,
labels
FROM `cloud_asset_inventory_compute_instances`
WHERE LOWER(os_type) LIKE '%linux%'
AND instance_status NOT IN ('TERMINATED', 'DELETED')
)
SELECT
vf.organization_id,
vf.folder_id,
vf.project_id,
vf.resource_name,
ac.instance_id,
vf.severity,
ac.os_type,
ac.kernel_version,
ac.instance_status,
ac.internet_facing,
ac.service_account_email,
ac.gke_cluster,
ac.gke_node_pool,
ac.workload_type,
ac.workload_owner,
ac.environment,
ac.asset_criticality,
CASE
WHEN ac.internet_facing = true
AND ac.asset_criticality IN ('critical','high') THEN 'high'
WHEN ac.gke_cluster IS NOT NULL
OR ac.gke_node_pool IS NOT NULL
OR ac.workload_type IN ('gke-node','container-host','ci-runner')
OR ac.service_account_email IS NOT NULL THEN 'high'
WHEN ac.environment = 'production' THEN 'medium'
ELSE 'triage'
END AS priority
FROM vulnerable_findings vf
JOIN asset_context ac
ON vf.project_id = ac.project_id
AND vf.resource_name = ac.resource_name;
Rule 2
Post-Escalation GCP Service Account and Control-Plane Activity After Suspected Linux Host Compromise
Rule Format
· Cloud Audit Logs, Security Command Center, and BigQuery correlation pattern.
Detection Purpose
· Detect GCP control-plane behavior that may follow successful local root escalation on a vulnerable Linux workload.
· This rule focuses on service account use, IAM policy modification, service account key creation, Secret Manager access, Cloud Storage access, Cloud KMS use, GKE credential or cluster activity, Compute Engine metadata or instance modification, firewall changes, disk snapshot or image activity, and other cloud-side blast-radius indicators after suspected host compromise.
· This rule does not detect the kernel exploit primitive directly.
Detection Logic
· Identify suspicious GCP API activity from service accounts, workload identities, or identities associated with vulnerable Linux workloads.
· Prioritize IAM policy changes, service account key creation, Secret Manager access, Cloud Storage access, KMS decrypt activity, GKE credential or cluster activity, Compute Engine metadata changes, firewall changes, disk snapshot or image activity, and privilege-relevant control-plane operations.
· Increase priority when the service account belongs to a vulnerable Compute Engine VM, GKE node, container host, CI runner, or high-value workload.
· Treat the alert as stronger when paired with host-level exploit staging, abnormal privilege transition, or post-root behavior from EDR, Linux audit, or other host telemetry.
· Do not label cloud API activity as confirmed Copy Fail exploitation without host-side corroboration.
· Suppress approved automation, deployment systems, backup workflows, security tooling, maintenance windows, and known administrative service account use before escalation.
Required Telemetry
· Cloud Audit Logs.
· Security Command Center findings where available.
· IAM policy and service account audit events.
· Service account and workload identity mapping.
· Compute Engine and GKE node inventory.
· VM Manager or Security Command Center vulnerable-state context.
· Source IP, user agent where available, principal email, service account email, authentication info, method name, service name, resource name, project ID, request metadata, and status.
· Secret Manager, Cloud Storage, Cloud KMS, GKE, Compute Engine, IAM, and firewall event visibility.
· Approved automation source IPs, user agents, service accounts, deployment systems, and maintenance context.
· Host compromise or endpoint telemetry enrichment where available.
Engineering Implementation Instructions
· Map service accounts and workload identities back to Compute Engine instances, GKE nodes, container hosts, CI runners, and high-value workloads.
· Validate Cloud Audit Logs coverage across all relevant organizations, folders, and projects.
· Validate Data Access logs for Secret Manager, Cloud Storage, and Cloud KMS where required and appropriate.
· Enable and aggregate Security Command Center findings where available.
· Establish expected service account behavior for production workloads, GKE nodes, CI systems, automation identities, backup identities, deployment systems, and managed workloads.
· Prioritize activity from vulnerable workloads where unusual API behavior follows host compromise indicators.
· Add allowlists for approved automation, deployment systems, backup jobs, security tooling, maintenance windows, and known administrative identity use.
· Correlate with host telemetry before declaring suspected Copy Fail exploitation.
Deployment Scaling Note
Deployment scope should be adjusted based on environment size, Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence requirement for suspected Copy Fail exploitation.
DRI Assessment
· DRI: 8.4
· The rule is anchored to post-escalation cloud activity and service-account-use behavior rather than static exploit artifacts.
· The rule remains useful if the local exploit code changes because it focuses on cloud-side consequences of compromised workload identities.
· The score is constrained because GCP control-plane events do not directly prove the local kernel exploit path.
· The rule is strong when tied to vulnerable workload context and host compromise indicators.
TCR Assessment
· Operational TCR: 7.6
· Full-Telemetry TCR: 8.7
· Operational confidence depends on Cloud Audit Logs coverage, Data Access log coverage, Security Command Center coverage, service account mapping, workload attribution, approved automation baselines, and enrichment quality.
· Operational score is constrained because Data Access logging, user-agent visibility, service account attribution, and diagnostic coverage may vary across projects and organizations.
· Full-telemetry confidence improves when Cloud Audit Logs, Security Command Center, VM Manager, Cloud Asset Inventory, IAM, GKE, Secret Manager, Cloud Storage, Cloud KMS, service account mapping, and host telemetry are centrally correlated.
Limitations
· GCP control-plane activity may follow many compromise paths and is not unique to Copy Fail.
· Cloud Audit Logs cannot directly observe local Linux privilege escalation.
· Legitimate automation, deployment pipelines, backup operations, managed services, and security tooling may generate overlapping control-plane activity.
· Service account and workload identity mapping must be accurate to connect cloud activity to vulnerable workloads.
· Host telemetry is required for high-confidence Copy Fail exploitation assessment.
Detection Query Pattern
-- BigQuery / Cloud Audit Logs pattern.
-- Table names and field names must be adapted to the customer logging export and enrichment model.
WITH vulnerable_workload_identities AS (
SELECT
project_id,
resource_name,
instance_id,
service_account_email,
workload_type,
workload_owner,
environment,
asset_criticality,
internet_facing,
gke_cluster,
gke_node_pool
FROM `gcp_vulnerable_linux_workload_service_account_map`
WHERE cve_2026_31431_status = 'vulnerable'
OR asset_criticality IN ('critical','high')
OR workload_type IN ('compute','gke-node','container-host','ci-runner')
),
suspicious_audit_activity AS (
SELECT
timestamp,
resource.labels.project_id AS project_id,
protoPayload.serviceName AS service_name,
protoPayload.methodName AS method_name,
protoPayload.authenticationInfo.principalEmail AS principal_email,
protoPayload.requestMetadata.callerIp AS caller_ip,
protoPayload.requestMetadata.callerSuppliedUserAgent AS user_agent,
protoPayload.resourceName AS resource_name,
protoPayload.status.code AS status_code,
protoPayload.request AS request,
protoPayload.response AS response
FROM `gcp_cloud_audit_logs`
WHERE protoPayload.serviceName IN (
'iam.googleapis.com',
'secretmanager.googleapis.com',
'storage.googleapis.com',
'cloudkms.googleapis.com',
'container.googleapis.com',
'compute.googleapis.com'
)
AND protoPayload.methodName IN (
'SetIamPolicy',
'google.iam.admin.v1.CreateServiceAccountKey',
'google.iam.admin.v1.SetIAMPolicy',
'google.cloud.secretmanager.v1.SecretManagerService.AccessSecretVersion',
'storage.objects.get',
'storage.objects.list',
'cloudkms.cryptoKeyVersions.useToDecrypt',
'google.container.v1.ClusterManager.GetCluster',
'google.container.v1.ClusterManager.GetServerConfig',
'v1.compute.instances.setMetadata',
'v1.compute.firewalls.insert',
'v1.compute.firewalls.patch',
'v1.compute.disks.createSnapshot',
'v1.compute.images.insert'
)
AND protoPayload.status.code = 0
)
SELECT
saa.timestamp,
saa.project_id,
saa.service_name,
saa.method_name,
saa.principal_email,
saa.caller_ip,
saa.user_agent,
saa.resource_name,
vwi.instance_id,
vwi.workload_type,
vwi.workload_owner,
vwi.environment,
vwi.asset_criticality,
vwi.internet_facing,
vwi.gke_cluster,
vwi.gke_node_pool,
CASE
WHEN vwi.asset_criticality IN ('critical','high') THEN 'high'
WHEN vwi.workload_type IN ('gke-node','container-host','ci-runner') THEN 'high'
WHEN vwi.environment = 'production' THEN 'medium'
ELSE 'triage'
END AS priority
FROM suspicious_audit_activity saa
JOIN vulnerable_workload_identities vwi
ON saa.principal_email = vwi.service_account_email
WHERE saa.caller_ip NOT IN (
SELECT approved_source_ip
FROM `approved_gcp_admin_sources`
)
AND saa.user_agent NOT IN (
SELECT approved_user_agent
FROM `approved_gcp_automation_user_agents`
);
S26 Threat-to-Rule Traceability Matrix
Traceability Objective
· This section maps finalized S25 detection rules to the primary observable behaviors associated with CVE-2026-31431.
· The goal is to show where each rule contributes to prioritization, triage, investigation, containment, or supporting evidence.
· The rule set does not rely on direct visibility into AF_ALG, algif_aead, splice(), page-cache manipulation, or other local kernel-primitive activity.
· Vulnerable-state exposure, cloud control-plane activity, and YARA artifact matches do not confirm exploitation by themselves.
· Suspected exploitation requires host behavior, abnormal privilege activity, post-escalation evidence, or corroborated cloud-side blast-radius activity.
Traceability Coverage Summary
· Suricata has no direct CVE-specific rule because Copy Fail exploitation is local and not directly network-observable.
· SentinelOne provides primary Linux host-behavior coverage.
· Splunk provides SIEM correlation and enrichment coverage.
· Elastic provides endpoint and ECS-aligned behavior coverage.
· QRadar provides SIEM offense-generation coverage where Linux telemetry is normalized.
· SIGMA provides portable backend-translated detection logic.
· YARA provides supporting artifact detection only.
· AWS, Azure, and GCP provide cloud-native exposure prioritization and post-escalation cloud activity detection.
Threat Behavior 1: Vulnerable Linux Workload Exposure
Detection Purpose
· Identify Linux workloads affected by CVE-2026-31431 where exposure, workload role, production criticality, cloud identity permissions, or node placement increases operational risk.
Mapped Rules
· AWS Rule 1: Vulnerable Linux Cloud Workload Exposure Prioritization
· Azure Rule 1: Vulnerable Azure Linux Workload Exposure Prioritization
· GCP Rule 1: Vulnerable GCP Linux Workload Exposure Prioritization
· Splunk Rule 1: Writable-Path Exploit Staging on Vulnerable Linux Assets
· Elastic Rule 1: Writable-Path Exploit Staging on Vulnerable Linux Workloads
· QRadar Rule 1: Abnormal Low-Privilege-to-Root Transition on Vulnerable Linux Assets
Coverage Position
· Coverage is strong for prioritization, hunt scoping, patch urgency, host telemetry collection, and workload owner notification.
· Exposure alone is not exploitation evidence.
· Suspected exploitation requires host behavior, abnormal privilege activity, post-escalation behavior, or cloud-side blast-radius evidence.
Threat Behavior 2: Local Exploit Staging From Writable or Transient Paths
Detection Purpose
· Detect suspicious local execution that may precede Copy Fail exploitation, especially from temporary, user-controlled, CI, container, or mounted workload paths.
Mapped Rules
· SentinelOne Rule 1: Suspicious Writable-Path Exploit Staging on Linux Workloads
· Splunk Rule 1: Writable-Path Exploit Staging on Vulnerable Linux Assets
· Elastic Rule 1: Writable-Path Exploit Staging on Vulnerable Linux Workloads
· SIGMA Rule 1: Writable-Path Exploit Staging on Linux Workloads
· YARA Rule 1: Copy Fail Proof-of-Concept and Exploit Artifact Indicators
Coverage Position
· Coverage is strong where process creation, executable path, command line, user context, and host enrichment are available.
· Staging does not prove exploitation.
· Confidence increases when staging occurs on a vulnerable host and is followed by abnormal privilege transition, privileged binary interaction, or post-escalation activity.
· YARA supports artifact discovery only and requires execution or behavioral corroboration.
Threat Behavior 3: Abnormal Low-Privilege-to-Root Transition
Detection Purpose
· Detect suspicious movement from a non-root or non-administrative execution context to root-owned activity.
Mapped Rules
· Splunk Rule 2: Abnormal Low-Privilege-to-Root Process Transition
· Elastic Rule 2: Abnormal Low-Privilege-to-Root Process Transition
· QRadar Rule 1: Abnormal Low-Privilege-to-Root Transition on Vulnerable Linux Assets
· SIGMA Rule 2: Abnormal Low-Privilege-to-Root Process Transition
· SentinelOne Rule 1: Suspicious Writable-Path Exploit Staging on Linux Workloads
· SentinelOne Rule 2: Suspicious Privileged Binary Interaction From Writable or Scripted Parentage
Coverage Position
· This is the strongest behavioral anchor for Copy Fail triage.
· Coverage is strong where process ancestry, user context, effective-user context, command-line telemetry, and host-role enrichment are available.
· This behavior is not unique to Copy Fail and must be tuned against approved administration, automation, package management, service management, backup activity, security tooling, and maintenance windows.
Threat Behavior 4: Privileged Binary or SUID-Adjacent Interaction
Detection Purpose
· Detect suspicious privileged binary interaction or SUID-adjacent behavior that may accompany local privilege escalation attempts.
Mapped Rules
· SentinelOne Rule 2: Suspicious Privileged Binary Interaction From Writable or Scripted Parentage
· Splunk Rule 2: Abnormal Low-Privilege-to-Root Process Transition
· Elastic Rule 2: Abnormal Low-Privilege-to-Root Process Transition
· QRadar Rule 1: Abnormal Low-Privilege-to-Root Transition on Vulnerable Linux Assets
· SIGMA Rule 2: Abnormal Low-Privilege-to-Root Process Transition
Coverage Position
· Coverage is moderate to strong where parent process, user context, effective-user context, and privileged execution telemetry are available.
· The mapped rules avoid broad privileged-binary alerting by requiring suspicious parentage, writable-path context, non-administrative origin, or abnormal privilege outcome.
· Confidence increases when privileged interaction follows suspicious staging or occurs on a vulnerable Linux workload.
Threat Behavior 5: Post-Escalation Root Activity on Linux Workloads
Detection Purpose
· Detect activity that may follow successful root escalation, including credential access, sensitive file access, persistence setup, audit or security tool tampering, container runtime interaction, Kubernetes material access, cloud metadata interaction, and lateral movement preparation.
Mapped Rules
· SentinelOne Rule 3: Post-Escalation Root Activity on Vulnerable Linux Workloads
· Splunk Rule 3: Post-Escalation Root Activity on Vulnerable Linux Workloads
· Elastic Rule 3: Post-Escalation Root Activity on Vulnerable Linux Workloads
· QRadar Rule 2: Post-Escalation Root Activity on Vulnerable Linux Workloads
· SIGMA Rule 3: Post-Escalation Root Activity on Vulnerable Linux Workloads
Coverage Position
· Coverage is strong where process, command-line, file-event, user, host-role, and vulnerability context are available.
· This behavior is not unique to Copy Fail and must be correlated with vulnerable-state context, staging, abnormal privilege transition, privileged binary interaction, or other host compromise evidence.
· Coverage is reduced where file access telemetry is incomplete or where approved backup, monitoring, security, and administrative tools are not tuned.
Threat Behavior 6: Cloud Credential Use and Control-Plane Activity After Suspected Host Compromise
Detection Purpose
· Detect cloud-side blast-radius activity that may follow host compromise, including role use, managed identity use, service account activity, secret access, storage access, control-plane changes, remote command execution, key use, and privilege-relevant cloud operations.
Mapped Rules
· AWS Rule 2: Post-Escalation AWS Credential and Control-Plane Activity After Suspected Linux Host Compromise
· Azure Rule 2: Post-Escalation Azure Managed Identity and Control-Plane Activity After Suspected Linux Host Compromise
· GCP Rule 2: Post-Escalation GCP Service Account and Control-Plane Activity After Suspected Linux Host Compromise
· Splunk Rule 3: Post-Escalation Root Activity on Vulnerable Linux Workloads
· Elastic Rule 3: Post-Escalation Root Activity on Vulnerable Linux Workloads
· QRadar Rule 2: Post-Escalation Root Activity on Vulnerable Linux Workloads
Coverage Position
· Coverage is strong for blast-radius detection when cloud identity mapping, audit coverage, workload ownership, approved automation baselines, and host telemetry are mature.
· Cloud-native rules do not detect the local Linux kernel exploit primitive.
· Cloud activity becomes CVE-relevant when tied to vulnerable workloads, host compromise evidence, suspicious service identity use, or post-escalation behavior.
· Cloud activity alone should not be labeled confirmed Copy Fail exploitation.
Threat Behavior 7: Supporting Exploit Artifact Discovery
Detection Purpose
· Identify known, lightly modified, or research-derived proof-of-concept material and exploit-adjacent artifacts during file scanning, incident response, sandboxing, malware repository review, CI artifact review, or container image inspection.
Mapped Rules
· YARA Rule 1: Copy Fail Proof-of-Concept and Exploit Artifact Indicators
· SentinelOne Rule 1: Suspicious Writable-Path Exploit Staging on Linux Workloads
· Splunk Rule 1: Writable-Path Exploit Staging on Vulnerable Linux Assets
· Elastic Rule 1: Writable-Path Exploit Staging on Vulnerable Linux Workloads
· SIGMA Rule 1: Writable-Path Exploit Staging on Linux Workloads
Coverage Position
· Coverage is limited but useful for triage and evidence discovery.
· YARA is supporting only and cannot confirm exploitation.
· Artifact matches require correlation with execution telemetry, vulnerable-state context, staging behavior, privilege transition, or post-escalation activity.
· Static indicators are fragile and can be removed, renamed, encoded, compressed, recompiled, or embedded into unrelated files.
Threat Behavior 8: Direct Kernel Primitive Visibility
Detection Purpose
· Identify direct evidence of AF_ALG, algif_aead, splice(), page-cache manipulation, or kernel-interface behavior where telemetry supports it.
Mapped Rules
· No S25 rule relies on direct kernel primitive visibility as a mandatory detection requirement.
· Conditional enrichment may support SentinelOne, Splunk, Elastic, QRadar, or SIGMA-backed detections only where syscall, eBPF, Linux audit, or EDR kernel telemetry is validated.
Coverage Position
· Coverage is intentionally conditional.
· Direct primitive visibility is high-value but environment-dependent.
· The finalized rule set remains deployable without assuming universal syscall, eBPF, or kernel-level EDR visibility.
· Cloud-native systems and Suricata cannot directly observe this local kernel behavior.
System Traceability Summary
Suricata
· Validated rules: 0
· Traceability role: no direct CVE-specific coverage.
· Coverage boundary: adjacent initial-access or post-compromise network monitoring only.
SentinelOne
· Validated rules: 3
· Traceability role: primary Linux host-behavior detection.
· Covered behaviors: writable-path staging, suspicious privileged binary interaction, post-escalation root activity.
Splunk
· Validated rules: 3
· Traceability role: SIEM correlation and enrichment.
· Covered behaviors: staging, abnormal privilege transition, vulnerable asset correlation, post-escalation activity.
Elastic
· Validated rules: 3
· Traceability role: endpoint and ECS-aligned behavior detection.
· Covered behaviors: staging, abnormal privilege transition, post-escalation root activity.
QRadar
· Validated rules: 2
· Traceability role: SIEM correlation and offense generation.
· Covered behaviors: abnormal privilege transition, post-escalation root activity.
SIGMA
· Validated rules: 3
· Traceability role: portable backend-translated detection logic.
· Covered behaviors: staging, abnormal privilege transition, post-escalation activity.
YARA
· Validated rules: 1
· Traceability role: supporting artifact detection.
· Covered behaviors: proof-of-concept or exploit-adjacent artifact discovery.
AWS
· Validated rules: 2
· Traceability role: cloud-native exposure prioritization and post-escalation AWS activity detection.
· Covered behaviors: vulnerable Linux workload exposure, IAM role activity, cloud credential activity, control-plane blast-radius indicators.
Azure
· Validated rules: 2
· Traceability role: cloud-native exposure prioritization and post-escalation Azure managed identity or control-plane activity detection.
· Covered behaviors: vulnerable Linux workload exposure, managed identity activity, control-plane blast-radius indicators.
GCP
· Validated rules: 2
· Traceability role: cloud-native exposure prioritization and post-escalation GCP service account or control-plane activity detection.
· Covered behaviors: vulnerable Linux workload exposure, service account activity, control-plane blast-radius indicators.
Final Traceability Assessment
· The finalized S25 rule set provides strong traceability across vulnerable workload exposure, local exploit staging, abnormal privilege transition, post-escalation host activity, cloud blast-radius activity, and supporting artifact discovery.
· The strongest direct behavioral coverage is provided by SentinelOne, Splunk, Elastic, QRadar, and SIGMA-translated host or SIEM logic.
· AWS, Azure, and GCP provide strong prioritization and post-compromise cloud-activity coverage, but they do not independently confirm local Copy Fail exploitation.
· YARA provides useful supporting evidence but cannot serve as a primary exploitation detector.
· Suricata remains intentionally excluded from direct CVE-specific rule coverage because it cannot observe the local Linux exploitation path.
· The rule set preserves deployability by avoiding mandatory dependence on direct AF_ALG, algif_aead, splice(), page-cache, or kernel-interface visibility.
Figure 4
S27 Behavior and Log Artifacts
Artifact Objective
· This section identifies the behavioral, host, identity, cloud, container, Kubernetes, vulnerability, and supporting artifact evidence needed to investigate CVE-2026-31431 activity.
· The artifact model supports triage of Copy Fail as a local Linux privilege escalation risk after prior unprivileged execution.
· Artifacts should be interpreted in sequence: exposure, staging, privilege transition, post-escalation activity, and cloud or workload blast-radius activity.
· No single artifact should be treated as confirmed exploitation without supporting behavioral context.
· Vulnerable-state data, cloud activity, and YARA matches support prioritization and investigation, but they do not independently confirm local exploitation.
Primary Host Behavior Artifacts
· Low-privilege execution of shell, Python, compiled ELF binaries, build tools, or short-lived executables from writable or transient paths.
· Process execution from /tmp, /var/tmp, /dev/shm, user home directories, CI workspace paths, build directories, mounted workload paths, container writable layers, or mounted volumes.
· Suspicious process creation followed by root-owned process activity.
· Non-administrative parent processes spawning privileged utilities, shells, interpreters, or root-owned child processes.
· Unexpected root shell creation from scripting engines, temporary binaries, application accounts, service accounts, CI users, container-originated processes, or unknown executables.
· Post-root execution involving credential access, discovery, persistence setup, security tool tampering, metadata access, or lateral movement preparation.
Primary Process Artifacts
· Process name.
· Executable path.
· Command line.
· Working directory.
· Parent process name.
· Parent process path.
· Parent process command line.
· Process ancestry identifier where available.
· Process user.
· Effective user.
· Source user.
· Destination user.
· UID and effective UID where available.
· Process start time.
· Hostname or endpoint identifier.
· Container, Kubernetes, cloud, or workload context where available.
Privilege Transition Artifacts
· Non-root process followed by root-owned process creation within a short investigative window.
· Root-owned process activity where the parent process originates from a writable path, scripting engine, CI workspace, container context, user home directory, or application-controlled path.
· Root-owned shell, interpreter, command runner, privileged utility, or service-control process spawned from non-administrative parentage.
· Effective-user or UID transition from non-root to root.
· SUID or privileged binary interaction from suspicious parentage.
· Privilege boundary activity that does not match approved administrative workflows.
· Root-owned activity on hosts known to be vulnerable, internet-facing, cloud-hosted, container-hosted, Kubernetes nodes, CI runners, or high-value production systems.
Sensitive File and Credential Artifacts
· Root-level access to /etc/shadow.
· Root-level access to /etc/sudoers.
· Access to /root/.ssh/.
· Access to SSH private keys, service credentials, local credential stores, host secrets, or application secrets.
· Access to Kubernetes service account tokens.
· Access to /var/run/secrets/kubernetes.io/.
· Access to /var/lib/kubelet/.
· Access to /etc/kubernetes/.
· Access to container runtime sockets such as /var/run/docker.sock, /run/containerd/containerd.sock, or /run/cri-dockerd.sock.
· Access to host-mounted secrets, container runtime directories, workload identity material, or cloud credential material.
· File access, creation, modification, permission change, or ownership change events involving sensitive host or workload paths.
Persistence and Defense Evasion Artifacts
· Root-level cron modification.
· Root-level systemd unit creation or modification.
· SSH authorized key modification.
· Shell profile modification.
· Privileged service modification.
· Startup script modification.
· SUID bit changes or suspicious chmod +s activity.
· Use of chattr against security-relevant files.
· Audit tampering, including auditctl -D or audit service disruption.
· Attempts to stop, disable, tamper with, or evade EDR, audit logging, cloud agents, container security agents, or vulnerability management agents.
· Firewall or packet-filter manipulation, including suspicious iptables changes.
Cloud Metadata and Workload Identity Artifacts
· Root-level access to cloud metadata endpoints after suspicious staging or privilege transition.
· Access to role credentials, managed identity tokens, service account tokens, or workload identity material.
· Use of cloud credentials shortly after suspected host compromise.
· Cloud API activity from roles, managed identities, or service accounts associated with vulnerable workloads.
· Secret access, storage access, key use, snapshot access, role assumption, service account key creation, managed identity activity, or control-plane modification after suspected escalation.
· Cloud activity from unexpected source IPs, unusual user agents, abnormal sessions, nonstandard automation patterns, or identities mapped to vulnerable workloads.
Container and Kubernetes Artifacts
· Suspicious process execution originating from a containerized workload.
· Host process creation following container-context activity.
· Access to kubelet paths, Kubernetes service account tokens, host-mounted secrets, or container runtime sockets.
· Activity involving privileged pods, hostPath mounts, host namespaces, or sensitive namespaces.
· Suspicious node-level activity on Kubernetes worker nodes hosting externally exposed workloads or high-value production services.
· Container-to-host mapping showing that suspicious workload activity occurred on a vulnerable node or container host.
· GKE, EKS, or AKS node identity activity after suspected host compromise.
Vulnerability and Exposure Artifacts
· CVE-2026-31431 vulnerable-state finding.
· Linux distribution and kernel version.
· Patch state.
· Vulnerability scan time.
· Finding state.
· Finding freshness.
· Host role.
· Asset criticality.
· Workload owner.
· Exposure state.
· Internet-facing status.
· Cloud account, subscription, or project.
· Kubernetes cluster, node group, or node pool.
· Container-host role.
· CI runner role.
· Security agent coverage and health.
· Historical vulnerability state showing whether the host was vulnerable when suspicious behavior occurred.
System-Specific Artifact Position
Suricata
· Direct CVE-specific exploitation artifacts are not expected.
· Relevant artifacts are limited to adjacent network context such as payload transfer, command-and-control, tunneling, exfiltration, or lateral movement.
· Suricata artifacts require host corroboration before being associated with suspected Copy Fail activity.
SentinelOne
· Key artifacts include process creation, process ancestry, executable path, command line, parent process context, user context, effective-user context where available, file activity, sensitive path access, and agent health.
· SentinelOne artifacts provide primary host-behavior evidence for staging, privileged binary interaction, and post-escalation root activity.
Splunk
· Key artifacts include normalized Linux process, file, identity, host, vulnerability, cloud, Kubernetes, and container fields.
· Splunk artifacts support correlation across exploit staging, privilege transition, vulnerable asset context, and post-escalation behavior.
Elastic
· Key artifacts include ECS-aligned process, file, user, host, vulnerability, cloud, Kubernetes, and container fields.
· Elastic artifacts support endpoint behavior detection and sequence-based correlation where ECS mappings and data views are validated.
QRadar
· Key artifacts include DSM-parsed process properties, custom identity properties, reference sets, vulnerable asset context, approved activity context, and file-event properties where available.
· QRadar artifacts support offense generation when Linux telemetry is normalized consistently.
SIGMA
· Key artifacts depend on backend translation.
· Required artifacts include Linux process creation, parent process context, user or effective-user mapping, command line, file telemetry where available, and vulnerable-state enrichment.
· SIGMA artifact value depends on backend field fidelity and translation accuracy.
YARA
· Key artifacts include executable or script-like files containing Copy Fail, CVE-2026-31431, AF_ALG, algif_aead, splice(), page-cache, SUID, kernel crypto, or root escalation implementation references.
· YARA artifacts are supporting evidence only.
· YARA matches require execution, staging, vulnerable-state, privilege-transition, or post-escalation corroboration.
AWS
· Key artifacts include Inspector findings, Security Hub findings, AWS Config inventory, EC2 metadata, EKS context, IAM role mapping, CloudTrail activity, GuardDuty findings, Secrets Manager activity, SSM activity, KMS activity, S3 activity, and approved automation baselines.
· AWS artifacts support exposure prioritization and cloud-side blast-radius detection, not direct local kernel exploit confirmation.
Azure
· Key artifacts include Defender findings, Resource Graph inventory, Azure Activity Logs, Microsoft Entra ID activity, managed identity mapping, AKS context, Key Vault logs, Storage logs, Defender for Endpoint enrichment, and approved automation baselines.
· Azure artifacts support exposure prioritization and managed identity or control-plane blast-radius detection, not direct local kernel exploit confirmation.
GCP
· Key artifacts include Security Command Center findings, VM Manager findings, Cloud Asset Inventory, Compute Engine metadata, GKE context, service account mapping, Cloud Audit Logs, Data Access logs, Secret Manager access, Cloud Storage access, Cloud KMS activity, and approved automation baselines.
· GCP artifacts support exposure prioritization and service account or control-plane blast-radius detection, not direct local kernel exploit confirmation.
Artifact Correlation Requirements
· Correlate suspicious staging with vulnerable host state.
· Correlate writable-path execution with user context, parent process context, and host role.
· Correlate abnormal root activity with prior non-root execution or suspicious parentage.
· Correlate sensitive file access with root context, process ancestry, and timing after staging.
· Correlate cloud control-plane activity with the role, managed identity, or service account mapped to a vulnerable workload.
· Correlate YARA matches with file path, file type, execution evidence, vulnerable-state context, and host behavior.
· Correlate Kubernetes and container artifacts back to the underlying host or node.
· Correlate security agent health with any telemetry gaps observed during the suspected exposure period.
Artifact Confidence Position
· High-confidence artifacts combine suspicious staging, vulnerable host state, abnormal privilege transition, and post-escalation activity.
· Moderate-confidence artifacts include staging or post-escalation behavior with partial vulnerable-state or host-role context.
· Low-confidence artifacts include vulnerable-state exposure alone, cloud inventory alone, network-only context, or static artifact matches without execution evidence.
· Direct kernel-primitive artifacts are high-value when available, but they remain conditional and are not required for baseline detection.
S28 Detection Strategy and SOC Implementation Guidance
Figure 5
SOC Implementation Objective
This section provides operational guidance for deploying, triaging, tuning, and escalating the CVE-2026-31431 detection strategy. SOC handling must separate vulnerable-state exposure, suspected exploitation, confirmed post-escalation behavior, and cloud or workload blast-radius activity.
The SOC should not treat vulnerable-state findings, cloud control-plane events, network-only activity, or YARA matches as confirmed Copy Fail exploitation without host-behavior corroboration. The primary SOC objective is to detect and contain the transition from unprivileged local execution to root-level or post-root activity on vulnerable Linux systems.
Operational Detection Strategy
· Deploy host-behavior detections first for Linux process execution, process ancestry, user context, privilege transition, sensitive file access, and post-escalation behavior.
· Use SIEM correlation to connect exploit staging, vulnerable-state context, abnormal privilege transition, and post-root behavior.
· Use cloud-native detections to prioritize vulnerable cloud Linux workloads and detect suspicious control-plane activity after suspected host compromise.
· Use Kubernetes and container telemetry to assess node, runtime, namespace, service account, hostPath, and workload trust exposure after suspected escalation.
· Use CI/CD telemetry to identify suspicious runner activity, build-host exposure, deployment credential access, repository access, artifact activity, or package registry interaction after suspected root compromise.
· Use YARA only for supporting artifact discovery, suspicious file review, incident-response collection, malware repository review, container image review, or CI artifact review.
· Do not force network-only detections into direct CVE coverage because Copy Fail exploitation is local and requires prior execution.
· Treat direct AF_ALG, algif_aead, splice-adjacent, or page-cache telemetry as high-value enrichment only where collection is validated.
Deployment Scaling Position
CyberDax detection guidance is designed to support scaled deployment across small, mid-size, enterprise, and cloud-native environments. Scaling should adjust deployment scope, enrichment depth, triage ownership, and operational routing based on Linux telemetry maturity, vulnerable asset coverage, host criticality, cloud context, Kubernetes and container visibility, CI/CD exposure, and SOC operating model. Scaling must not weaken the behavioral evidence required to distinguish vulnerable-state exposure, suspected exploitation, confirmed root compromise, and post-root expansion.
SOC Triage Flow
Step 1: Confirm Exposure Context
· Determine whether the host was affected by CVE-2026-31431 at the time of suspicious activity.
· Confirm kernel version, Linux distribution, patch state, scan time, asset role, and exposure state.
· Identify whether the host is internet-facing, cloud-hosted, a Kubernetes node, a container host, a CI runner, or a high-value production system.
· Validate whether the vulnerability finding is active, stale, suppressed, resolved, or tied to a decommissioned asset.
Step 2: Review Staging Behavior
· Review execution from /tmp, /var/tmp, /dev/shm, user home directories, CI workspaces, build paths, mounted workload paths, or container writable layers.
· Identify scripting engines, shells, build tools, compiled ELF binaries, or short-lived executables launched by non-root users.
· Review command line, executable path, working directory, parent process, user context, and host role.
· Determine whether the behavior matches approved CI, automation, maintenance, package management, scanning, backup, or administrative activity.
Step 3: Validate Privilege Transition
· Identify whether suspicious non-root activity was followed by root-owned process creation.
· Review process ancestry, effective user, UID, parent process, parent path, command line, and time sequence.
· Determine whether root activity originated from expected administrative tooling or abnormal parentage.
· Prioritize transitions involving vulnerable hosts, suspicious staging, privileged binary interaction, sensitive file access, or post-root activity.
Step 4: Review Post-Root Activity
· Review root-owned shells, command interpreters, privileged child processes, discovery commands, persistence commands, and sensitive file access.
· Review access to /etc/shadow, /etc/sudoers, SSH private keys, service credentials, Kubernetes service account tokens, cloud metadata services, runtime sockets, and host-mounted secrets.
· Review tampering with EDR, audit logging, cloud agents, container security tools, vulnerability scanners, or telemetry forwarding.
· Determine whether activity reflects expected administration, approved tooling, unauthorized escalation, or confirmed post-root compromise.
Step 5: Assess Cloud, Kubernetes, Container, and CI/CD Blast Radius
· Review cloud API activity tied to the host role, managed identity, instance role, workload identity, or exposed credentials.
· Review Kubernetes audit activity, node activity, service account use, kubelet paths, runtime sockets, host namespaces, privileged pods, and hostPath exposure.
· Review container runtime activity, mounted secrets, image access, container directories, and workload-to-host trust relationships.
· Review CI runner activity, build logs, repository access, deployment credentials, artifact changes, package registry activity, and release automation.
· Treat cloud, Kubernetes, container, and CI/CD activity as post-compromise evidence unless host telemetry supports local exploitation or root compromise.
Escalation Criteria
Exposure-Level Escalation
· Vulnerable Linux host is internet-facing, cloud-hosted, production-critical, Kubernetes-adjacent, container-hosted, CI/CD-connected, or credential-rich.
· No suspicious local execution or privilege-transition behavior is observed.
· Escalation should focus on patching, exposure reduction, telemetry validation, and targeted hunting.
Suspected Exploitation Escalation
· Suspicious local execution or writable-path staging occurs on a vulnerable Linux host.
· Suspicious non-root activity is followed by privileged binary interaction, abnormal root-owned process creation, or unusual root-context behavior.
· Escalation should include host isolation consideration, forensic preservation, expanded hunting, and credential exposure review.
Confirmed or Strongly Suspected Root Compromise Escalation
· Root-level activity follows suspicious staging or abnormal privilege transition on a vulnerable host.
· Sensitive file access, credential access, security-control tampering, persistence setup, runtime socket access, Kubernetes token access, or cloud metadata interaction is observed.
· Escalation should include containment, credential rotation, workload trust validation, cloud and Kubernetes review, and recovery-confidence validation.
Blast-Radius Escalation
· Post-root activity reaches cloud identities, Kubernetes trust paths, container runtime resources, CI/CD credentials, repositories, package registries, deployment systems, production workloads, or sensitive data.
· Escalation should include cross-functional incident coordination across SOC, endpoint, Linux, cloud, Kubernetes, container, CI/CD, identity, legal, and business stakeholders.
Tuning Guidance
· Tune approved Linux administration, package management, service management, configuration management, backup tooling, vulnerability scanning, monitoring agents, CI jobs, and security tooling.
· Tune by host role because CI runners, build servers, Kubernetes nodes, container hosts, and production Linux systems may generate different expected behavior.
· Preserve high-priority routing for vulnerable systems with internet exposure, cloud identity permissions, Kubernetes node roles, container runtime access, CI/CD access, production criticality, or sensitive credential paths.
· Do not suppress abnormal low-privilege-to-root transitions solely because the host has administrative activity.
· Do not suppress post-root sensitive file access unless the process, user, timing, host role, and workflow are clearly approved.
· Keep static artifact, hash, filename, CVE-string, and YARA matches as supporting evidence rather than primary exploitation evidence.
Containment Guidance
· Isolate vulnerable hosts when suspicious staging and abnormal privilege transition appear in the same sequence.
· Preserve telemetry before rebuilding, terminating, recycling, draining, replacing, or resetting affected systems.
· Rotate credentials where root compromise, sensitive file access, token access, cloud metadata interaction, runtime socket access, Kubernetes service account access, CI/CD secret access, or deployment credential exposure is confirmed or strongly suspected.
· Cordon, drain, replace, or rebuild Kubernetes worker nodes where node trust cannot be validated.
· Rebuild cloud Linux workloads, container hosts, and CI runners from patched baselines where root-level compromise is confirmed or host integrity cannot be trusted.
· Validate that patched images, node pools, autoscaling templates, container-host baselines, golden images, and CI runner templates do not reintroduce vulnerable systems.
SOC Reporting Requirements
· Report vulnerable-state exposure separately from suspected exploitation.
· Report suspected exploitation separately from confirmed root compromise.
· Report post-root cloud, Kubernetes, container, CI/CD, repository, or identity activity separately from the local exploit path.
· Document whether direct kernel-primitive telemetry was available, absent, or not collected.
· Document telemetry gaps, agent-health issues, missing process ancestry, missing command line, missing effective-user context, missing file access telemetry, missing cloud logs, missing Kubernetes logs, or missing CI/CD logs.
· Document containment actions, credential rotation decisions, patch validation status, host rebuild status, node replacement status, and recovery-confidence evidence.
Implementation Position
The SOC implementation model should prioritize behavioral correlation over static indicators. The strongest operational posture combines vulnerable asset context, suspicious local execution, writable-path staging, abnormal low-privilege-to-root transition, root-owned process activity, sensitive file access, security-control tampering, and post-root cloud, Kubernetes, container, or CI/CD activity. This approach preserves accuracy while avoiding overstatement from vulnerable inventory alone, cloud-only events, network-only detections, or artifact-only matches.
S29 Detection Coverage Summary
Coverage Summary Objective
· This section summarizes detection coverage across the finalized S25 rule set.
· Coverage is assessed by observable behavior, telemetry type, and system role.
· The rule set prioritizes deployable behavioral detection over fragile artifact matching.
· The strongest coverage is achieved when host behavior, vulnerable-state context, identity context, workload context, and cloud control-plane telemetry are correlated.
Overall Coverage Position
· Coverage is strong for vulnerable workload prioritization.
· Coverage is strong for local exploit staging where Linux process telemetry is available.
· Coverage is strong for abnormal privilege transition where process ancestry and user context are available.
· Coverage is strong for post-escalation activity where process, command-line, file-event, and sensitive path telemetry are available.
· Coverage is moderate for privileged binary and SUID-adjacent interaction because administrative workflows require careful tuning.
· Coverage is moderate for cloud blast-radius activity because cloud control-plane events require accurate workload identity mapping and host-side corroboration.
· Coverage is limited for direct kernel-primitive visibility because syscall, eBPF, audit, or kernel-level EDR telemetry is not universally available.
· Coverage is limited for static artifact detection because YARA matches are fragile and supporting only.
· Coverage is not direct through Suricata because Copy Fail exploitation is local and not network-observable.
Coverage by Threat Behavior
Vulnerable Linux Workload Exposure
· Coverage level: strong.
· Covered by AWS, Azure, GCP, Splunk, Elastic, and QRadar.
· Detection value includes patch prioritization, hunt scoping, host telemetry collection, and workload owner notification.
· Coverage depends on vulnerability-management freshness, asset inventory accuracy, tagging, cloud context, workload ownership, and exposure state.
· Exposure does not confirm exploitation.
Local Exploit Staging
· Coverage level: strong.
· Covered by SentinelOne, Splunk, Elastic, SIGMA, and YARA as supporting evidence.
· Detection value includes identifying suspicious execution from writable, transient, user-controlled, CI, container, and mounted workload paths.
· Coverage depends on Linux process telemetry, command-line capture, executable path fidelity, parent process context, and user context.
· Staging does not confirm exploitation without privilege transition or post-escalation evidence.
Abnormal Low-Privilege-to-Root Transition
· Coverage level: strong.
· Covered by Splunk, Elastic, QRadar, SIGMA, and SentinelOne-related privileged behavior logic.
· Detection value includes identifying the strongest behavioral anchor for local privilege escalation triage.
· Coverage depends on process ancestry, effective-user context, UID context, command-line telemetry, parent process fidelity, and administrative baseline tuning.
· This behavior is not unique to Copy Fail and requires vulnerable-state or staging correlation for CVE-specific triage.
Privileged Binary or SUID-Adjacent Interaction
· Coverage level: moderate to strong.
· Covered by SentinelOne, Splunk, Elastic, QRadar, and SIGMA through suspicious privilege-boundary logic.
· Detection value includes identifying suspicious interaction with privileged utilities and SUID-adjacent behavior.
· Coverage depends on parent process context, user role, working directory, effective-user context, and tuning for legitimate administrative activity.
· Broad privileged-binary detection without context is intentionally avoided.
Post-Escalation Root Activity
· Coverage level: strong.
· Covered by SentinelOne, Splunk, Elastic, QRadar, and SIGMA.
· Detection value includes identifying credential access, sensitive file access, persistence, security tool tampering, metadata access, Kubernetes token access, container runtime interaction, and lateral movement preparation.
· Coverage depends on process telemetry, command-line capture, file-event coverage, sensitive path visibility, host role, and vulnerable-state context.
· This behavior can result from multiple compromise paths and requires correlation for CVE-specific confidence.
Cloud Credential and Control-Plane Activity
· Coverage level: moderate to strong.
· Covered by AWS, Azure, GCP, Splunk, Elastic, and QRadar as correlated escalation context.
· Detection value includes identifying cloud blast-radius behavior after suspected host compromise.
· Coverage depends on CloudTrail, Azure Activity Logs, GCP Cloud Audit Logs, identity mapping, role mapping, managed identity mapping, service account mapping, Data Access logs, diagnostic logging, approved automation baselines, and host telemetry.
· Cloud control-plane activity alone does not confirm Copy Fail exploitation.
Supporting Artifact Discovery
· Coverage level: limited but useful.
· Covered by YARA and supported by staging detections in SentinelOne, Splunk, Elastic, and SIGMA.
· Detection value includes identifying proof-of-concept-derived files, exploit-adjacent artifacts, scripts, compiled samples, sandbox submissions, CI artifacts, and collected incident-response files.
· Coverage depends on scan scope, file collection, file type context, artifact availability, and triage workflow.
· Static artifact detection is supporting evidence only.
Direct Kernel Primitive Visibility
· Coverage level: conditional.
· No finalized S25 rule requires this visibility.
· Direct evidence may support SentinelOne, Splunk, Elastic, QRadar, or SIGMA-backed workflows if syscall, eBPF, Linux audit, or EDR kernel telemetry is available.
· Coverage depends on specialized telemetry collection and validation.
· The rule set remains deployable without universal kernel-primitive visibility.
Coverage by System
Suricata
· Coverage level: no direct CVE-specific coverage.
· Rule count: 0.
· Coverage role is limited to adjacent network context.
· Direct detection of Copy Fail exploitation is not supported through Suricata.
SentinelOne
· Coverage level: strong.
· Rule count: 3.
· Coverage includes writable-path staging, suspicious privileged binary interaction, and post-escalation root activity.
· Coverage depends on Linux endpoint telemetry, process ancestry, command-line capture, user context, file-event visibility, and tenant field validation.
Splunk
· Coverage level: strong.
· Rule count: 3.
· Coverage includes staging, abnormal privilege transition, vulnerable asset correlation, and post-escalation activity.
· Coverage depends on source type quality, CIM or field normalization, lookup accuracy, Linux telemetry coverage, and enrichment validation.
Elastic
· Coverage level: strong.
· Rule count: 3.
· Coverage includes staging, abnormal privilege transition, and post-escalation activity.
· Coverage depends on ECS field quality, data view coverage, EQL sequence support, file-event visibility, and enrichment validation.
QRadar
· Coverage level: moderate to strong.
· Rule count: 2.
· Coverage includes abnormal privilege transition and post-escalation root activity.
· Coverage depends on DSM parsing, custom properties, reference sets, log-source coverage, and vulnerability enrichment.
SIGMA
· Coverage level: moderate to strong.
· Rule count: 3.
· Coverage includes portable detection logic for staging, abnormal privilege transition, and post-escalation activity.
· Coverage depends on backend translation, field mapping, exception handling, enrichment, and file-telemetry support.
YARA
· Coverage level: limited supporting coverage.
· Rule count: 1.
· Coverage includes proof-of-concept or exploit-adjacent artifact discovery.
· Coverage depends on scan scope, file type, file collection, and behavioral corroboration.
AWS
· Coverage level: moderate to strong.
· Rule count: 2.
· Coverage includes vulnerable Linux workload exposure, IAM role activity, cloud credential activity, and AWS control-plane blast-radius indicators.
· Coverage depends on Inspector, Security Hub, Config, CloudTrail, GuardDuty, IAM role mapping, EKS inventory, tagging, approved automation baselines, and host telemetry.
Azure
· Coverage level: moderate to strong.
· Rule count: 2.
· Coverage includes vulnerable Linux workload exposure, managed identity activity, and Azure control-plane blast-radius indicators.
· Coverage depends on Defender, Resource Graph, Activity Logs, Entra ID visibility, managed identity mapping, AKS inventory, diagnostic logging, approved automation baselines, and host telemetry.
GCP
· Coverage level: moderate to strong.
· Rule count: 2.
· Coverage includes vulnerable Linux workload exposure, service account activity, and GCP control-plane blast-radius indicators.
· Coverage depends on Security Command Center, VM Manager, Cloud Asset Inventory, Cloud Audit Logs, Data Access logs, service account mapping, GKE inventory, labels, approved automation baselines, and host telemetry.
Coverage Strengths
· The rule set emphasizes behavior that is difficult for attackers to remove from the exploitation sequence.
· Host and SIEM coverage targets staging, privilege transition, and post-root activity.
· Cloud-native coverage improves prioritization and blast-radius detection.
· YARA provides supporting artifact discovery without being overstated.
· Suricata is appropriately excluded from direct CVE detection because the exploitation path is local.
· The rule set does not depend on brittle proof-of-concept names, hashes, CVE strings, or vendor alert names.
· The rule set does not require universal syscall, eBPF, or kernel-level telemetry.
Coverage Gaps
· Direct AF_ALG, algif_aead, splice(), and page-cache telemetry may be unavailable in many environments.
· File-event visibility may vary across endpoint, Linux audit, SIEM, and backend platforms.
· Effective-user and UID transition fields may be incomplete or inconsistently normalized.
· Container-to-host and Kubernetes node mapping may be incomplete.
· Cloud identity mapping may be incomplete for roles, managed identities, service accounts, and workload identities.
· Vulnerability findings may lag actual patch state.
· Ephemeral and autoscaled workloads may create inventory drift.
· Approved automation baselines may be incomplete during early deployment.
· Static artifact detection can be bypassed through renaming, recompilation, encoding, compression, or embedding.
Final Coverage Assessment
· The finalized rule set provides strong practical coverage for CVE-2026-31431 detection and triage when host telemetry and vulnerable-state context are available.
· The strongest detection path is behavioral correlation across suspicious staging, abnormal privilege transition, and post-escalation activity on vulnerable Linux systems.
· Cloud-native coverage is valuable for prioritization and blast-radius detection, but it does not replace host telemetry.
· Static artifact detection is useful for supporting evidence, but it does not replace behavioral detection.
· The residual detection risk is highest in environments with weak Linux process telemetry, poor identity normalization, incomplete vulnerability inventory, limited file-event coverage, weak cloud identity mapping, or short telemetry retention.
S30 Intelligence Maturity Assessment
Maturity Assessment Objective
· This section assesses the maturity required to detect, investigate, and respond to CVE-2026-31431 activity with confidence.
· Intelligence maturity is based on the organization’s ability to connect vulnerable-state context, Linux host behavior, privilege-transition evidence, post-escalation activity, cloud workload context, and SOC response workflows.
· The maturity model separates exposure awareness from exploitation detection and post-compromise response.
Overall Maturity Position
· Current maturity requirement: moderate to high.
· Baseline detection is achievable with Linux endpoint telemetry, process ancestry, command-line capture, user context, vulnerable asset state, and SIEM correlation.
· High-confidence detection requires stronger effective-user context, file-event visibility, host-role enrichment, container and Kubernetes mapping, cloud identity mapping, and sufficient telemetry retention.
· Advanced maturity requires conditional syscall, eBPF, Linux audit, or EDR kernel visibility for AF_ALG, algif_aead, splice(), or related kernel-interface behavior.
· The rule set is designed to remain operationally useful even without universal kernel-primitive telemetry.
Maturity Dimension 1: Vulnerability and Exposure Intelligence
Current Requirement
· Maintain accurate visibility into affected Linux kernel versions, Linux distribution, patch state, asset role, exposure state, and workload ownership.
Maturity Indicators
· Vulnerability findings are current and tied to active assets.
· Kernel version and patch state are tracked historically.
· Cloud, Kubernetes, container-host, CI, and production workload context is available.
· Asset criticality and workload ownership are populated.
· Exposure state is validated through cloud inventory, network context, and workload metadata.
Maturity Gaps
· Findings may lag patch state.
· Ephemeral workloads may create inventory drift.
· Missing asset tags or labels may reduce prioritization accuracy.
· Cloud and Kubernetes assets may not map cleanly back to host identity.
Improvement Priority
· Improve kernel and patch-state accuracy.
· Preserve historical vulnerability state.
· Strengthen host identity normalization across endpoint, vulnerability, cloud, Kubernetes, and SIEM systems.
· Require owner, criticality, and exposure metadata for high-value Linux workloads.
Maturity Dimension 2: Linux Host Behavior Intelligence
Current Requirement
· Capture process creation, command line, executable path, working directory, parent process context, user context, effective-user context, and file-event telemetry where available.
Maturity Indicators
· Suspicious writable-path execution can be detected.
· Low-privilege-to-root transitions can be correlated.
· Privileged binary interaction can be scoped by parentage and user context.
· Post-root sensitive file access can be detected.
· Security agent health is visible.
Maturity Gaps
· Command-line capture may be incomplete.
· Parent process fidelity may vary.
· Effective-user or UID transition context may be missing.
· File-event coverage may be inconsistent.
· Security agent tampering may not be retained long enough for retrospective analysis.
Improvement Priority
· Ensure command-line capture is enabled.
· Validate process ancestry fidelity.
· Preserve real-user and effective-user context.
· Expand sensitive file and privileged execution telemetry.
· Monitor EDR, audit, cloud agent, container security, and vulnerability agent health.
Maturity Dimension 3: Container and Kubernetes Intelligence
Current Requirement
· Map suspicious workload activity to the underlying container host or Kubernetes node.
Maturity Indicators
· Container ID, pod, namespace, service account, node, workload owner, and image context are available.
· Kubernetes node-level telemetry can be linked to workload activity.
· Runtime socket access, hostPath usage, privileged workload state, and host-mounted secrets are visible.
· Node-level escalation can be prioritized by workload sensitivity and exposure.
Maturity Gaps
· Container-to-host mapping may be incomplete.
· Kubernetes audit data may not align with endpoint telemetry.
· Service account and namespace ownership may be missing.
· HostPath and runtime socket exposure may not be tracked consistently.
Improvement Priority
· Normalize Kubernetes node, pod, namespace, service account, workload owner, and container-host relationships.
· Track privileged workload placement and hostPath usage.
· Correlate container-originated activity with host-level process and file telemetry.
· Prioritize vulnerable Kubernetes nodes and container hosts that support exposed or sensitive workloads.
Maturity Dimension 4: Cloud Workload and Identity Intelligence
Current Requirement
· Map cloud roles, managed identities, service accounts, workload identities, and instance profiles back to vulnerable Linux workloads.
Maturity Indicators
· AWS IAM roles are mapped to EC2 instances, EKS nodes, container hosts, and CI runners.
· Azure managed identities and service principals are mapped to VMs, VMSS instances, AKS nodes, and high-value workloads.
· GCP service accounts and workload identities are mapped to Compute Engine instances, GKE nodes, container hosts, and CI runners.
· Cloud audit logs are retained and centrally searchable.
· Approved automation baselines are documented.
Maturity Gaps
· Identity-to-workload mapping may be incomplete.
· Cloud Data Access or diagnostic logging may be inconsistent.
· Approved automation baselines may not be mature.
· Cloud activity may be difficult to distinguish from legitimate deployment or maintenance workflows.
Improvement Priority
· Build and maintain role-to-workload, managed-identity-to-workload, and service-account-to-workload mapping.
· Enable required cloud audit and Data Access logging for sensitive services.
· Establish approved automation baselines.
· Correlate cloud activity with host-side compromise indicators before escalation.
Maturity Dimension 5: Detection Engineering and Correlation Maturity
Current Requirement
· Correlate staging, vulnerable-state context, privilege transition, post-escalation activity, and cloud blast-radius evidence.
Maturity Indicators
· SIEM detections can join endpoint behavior with vulnerability, host role, identity, cloud, Kubernetes, and container context.
· Rules avoid brittle artifact dependencies.
· Detections preserve evidence boundaries between exposure, suspected exploitation, and confirmed post-escalation activity.
· Alert routing reflects host role, workload criticality, and cloud blast-radius potential.
Maturity Gaps
· SIEM normalization may drop critical fields.
· Lookup and enrichment data may be incomplete.
· Correlation windows may be too short or too broad.
· Rules may initially require tuning for administrative workflows, CI systems, container hosts, and security tooling.
Improvement Priority
· Validate SIEM field mappings and enrichment paths before production deployment.
· Preserve process, user, file, host, cloud, Kubernetes, vulnerability, and container context.
· Use short-window correlation for staging and privilege transition.
· Route high-priority alerts involving Kubernetes nodes, container hosts, CI runners, internet-facing workloads, and privileged cloud identities.
Maturity Dimension 6: SOC Response Maturity
Current Requirement
· SOC teams must triage CVE-2026-31431 alerts using evidence sequence and containment impact.
Maturity Indicators
· Analysts can distinguish exposure-only findings from suspected exploitation.
· Analysts can validate process ancestry, privilege transition, and post-root behavior.
· Analysts can identify whether cloud identity activity maps back to a vulnerable workload.
· Incident response can preserve telemetry before rebuild or replacement.
· Credential rotation and cloud containment workflows are defined.
Maturity Gaps
· Vulnerability, endpoint, SIEM, cloud, and Kubernetes teams may operate with incomplete shared context.
· Analysts may over-escalate exposure-only findings or under-escalate post-root activity.
· Cloud role or service account ownership may be unclear.
· Ephemeral workload replacement may destroy evidence.
Improvement Priority
· Standardize triage playbooks for exposure-only, staging, suspected exploitation, post-escalation, and cloud blast-radius cases.
· Preserve telemetry before terminating or rebuilding affected workloads.
· Define credential rotation and identity containment workflows.
· Establish owner notification paths for vulnerable high-value workloads.
· Retain telemetry across the suspected exposure window.
Maturity Dimension 7: Intelligence Confidence
High Confidence
· Suspicious staging, abnormal privilege transition, post-escalation root activity, vulnerable host state, and host-role context are correlated.
· Cloud identity activity is mapped to the affected workload and occurs after host compromise indicators.
· File-event, process, identity, vulnerability, and cloud telemetry are complete enough to reconstruct the attack sequence.
Moderate Confidence
· Suspicious staging or post-root behavior is present with partial vulnerable-state or host-role context.
· Cloud control-plane activity is suspicious but host-side exploitation evidence is incomplete.
· Artifact evidence exists with partial execution or staging evidence.
Low Confidence
· Only vulnerable-state exposure is present.
· Only static artifact evidence is present.
· Only cloud inventory or cloud activity exists without host-side corroboration.
· Only network telemetry exists without host behavior.
Final Intelligence Maturity Assessment
· CVE-2026-31431 detection maturity is strongest in environments with mature Linux endpoint telemetry, vulnerability management, SIEM correlation, cloud identity mapping, and workload ownership data.
· The current detection model supports practical deployment because it does not depend on universal kernel-primitive visibility.
· The highest-value maturity improvement is closing telemetry gaps around command-line capture, process ancestry, effective-user context, sensitive file access, cloud identity mapping, and vulnerability-state freshness.
· Organizations with mature host and cloud correlation can detect likely exploitation paths and post-compromise blast-radius activity with strong confidence.
· Organizations relying only on vulnerability inventory, network telemetry, cloud inventory, or static artifacts will have limited exploitation confidence and should treat those signals as prioritization or supporting evidence only.
· Mature intelligence improves confidence in suspected exploitation assessment, but no maturity level converts exposure-only, cloud-only, network-only, or artifact-only evidence into confirmed Copy Fail exploitation.
S31 Mitigation and Remediation
Mitigation Priority
Copy Fail remediation should prioritize vulnerable Linux systems where local execution is plausible and root escalation would materially increase attacker control. Highest priority should be assigned to internet-facing Linux workloads, cloud Linux instances, Kubernetes worker nodes, container hosts, CI runners, production servers, and systems with privileged cloud roles, deployment credentials, runtime sockets, service account material, or sensitive operational data.
Immediate Remediation Actions
· Identify affected Linux systems by kernel version, distribution, cloud image, container-host baseline, Kubernetes node image, and CI runner image.
· Prioritize vulnerable systems that are internet-facing, externally reachable, cloud-hosted, production-critical, Kubernetes-adjacent, container-hosted, CI/CD-connected, or credential-rich.
· Apply vendor-supported kernel patches, live patches, mitigations, or updated package streams where available.
· Confirm that patched systems have rebooted or that live-patch coverage is effective.
· Validate cloud images, golden images, autoscaling templates, node pools, container-host baselines, and CI runner images so vulnerable instances are not reintroduced.
· Review vulnerable systems for suspicious local execution, writable-path staging, privilege transition, root-owned process creation, sensitive file access, credential access, and post-root activity.
· Isolate systems with suspicious local staging, abnormal low-privilege-to-root transition, or post-root behavior until exploitation can be scoped.
· Rotate credentials, secrets, SSH keys, service account material, Kubernetes tokens, cloud roles, deployment secrets, and CI/CD credentials where root-level compromise is confirmed or strongly suspected.
· Preserve endpoint, Linux audit, cloud, Kubernetes, container, CI/CD, and identity telemetry before rebuilding, terminating, replacing, or resetting affected systems.
· Confirm that vulnerability scanner findings are current, mapped to real host state, and not stale, suppressed, archived, or disconnected from active infrastructure.
Cloud Linux Workloads
· Validate vulnerable instances, instance roles, managed identities, metadata exposure, storage access, snapshot permissions, secret-manager access, and unusual cloud API activity.
· Review cloud activity after suspected host compromise for role assumption, secret retrieval, snapshot access, storage access, security group changes, or unusual automation behavior.
· Rebuild or replace affected cloud workloads from patched images where compromise is confirmed or host integrity cannot be trusted.
Kubernetes Worker Nodes
· Validate vulnerable node images, kubelet exposure, service account material, hostPath usage, privileged pod placement, runtime socket access, and namespace sensitivity.
· Cordon, drain, replace, or rebuild nodes where exploitation is suspected or node trust cannot be restored.
· Rotate exposed service account tokens, workload secrets, and node-related credentials where root-level access is confirmed or strongly suspected.
Container Hosts
· Review runtime socket access, container directory access, host namespaces, mounted secrets, privileged containers, and workload-to-host trust boundaries.
· Rebuild compromised hosts from patched baselines where root-level access or runtime socket interaction is suspected.
· Validate that container images and orchestration templates do not reintroduce vulnerable host baselines.
CI/CD and Build Infrastructure
· Validate CI runner images, build hosts, release systems, package registry access, deployment credentials, repository tokens, artifact credentials, and cloud automation permissions.
· Rotate CI/CD secrets and deployment credentials where root-level access or suspicious activity is identified.
· Review recent build jobs, runner activity, artifact publication, package registry access, and repository access for unauthorized use.
Containment Guidance
· Treat abnormal low-privilege-to-root transition on a vulnerable host as a high-priority containment event.
· Prioritize isolation when suspicious staging and post-root behavior appear on the same vulnerable system.
· Avoid treating vulnerable-state inventory alone as exploitation evidence.
· Avoid clearing or rebuilding systems before preserving telemetry needed for scoping.
· Coordinate endpoint, Linux, cloud, Kubernetes, container, CI/CD, identity, and SOC teams during containment.
Recovery Validation
· Confirm patch effectiveness after reboot or live-patch application.
· Confirm affected systems no longer report vulnerable kernel state.
· Confirm no recurring suspicious local execution, privilege transition, root-owned process activity, or security-control tampering.
· Confirm rotated credentials are no longer valid from prior locations.
· Confirm cloud, Kubernetes, container, and CI/CD trust paths have been reviewed for misuse.
· Confirm monitoring coverage remains intact after remediation.
· Confirm rebuilt systems derive from patched, validated, and governed baselines.
S32 Security Control Recommendations
Control Objective
Security controls should reduce the likelihood that a local Linux foothold can become root-level compromise and reduce the blast radius if escalation occurs. Controls must focus on patch assurance, host behavior visibility, privilege-transition monitoring, credential protection, cloud and Kubernetes context, container runtime protection, CI/CD hardening, and coordinated response.
Vulnerability and Patch Management
· Maintain kernel inventory across Linux distributions, cloud images, Kubernetes nodes, container hosts, CI runners, and production servers.
· Prioritize remediation based on exposure, host criticality, local execution likelihood, cloud identity privileges, Kubernetes role, container-host role, and CI/CD connectivity.
· Track reboot status, live-patch effectiveness, package state, node image version, golden image version, autoscaling image version, and ephemeral runner baseline.
· Validate that scanner results match active host state and current kernel versions.
· Establish exception governance for Linux systems that cannot be patched immediately.
Endpoint and Linux Host Visibility
· Capture process creation telemetry with parent process, command line, executable path, working directory, source user, effective user, and host role.
· Enable Linux audit or equivalent host telemetry for sensitive file access, privilege-relevant execution, security-control tampering, and unusual root activity.
· Monitor writable-path execution from /tmp, /var/tmp, /dev/shm, user home directories, CI workspaces, build directories, mounted workload paths, and container writable layers.
· Monitor abnormal low-privilege-to-root transitions and root-owned process creation from suspicious parentage.
· Where available, use eBPF, EDR kernel telemetry, audit telemetry, or syscall-level visibility to increase confidence around AF_ALG, algif_aead, splice-adjacent, and page-cache-related activity.
Credential and Secret Protection
· Reduce credential material stored on Linux hosts.
· Protect SSH private keys, service credentials, Kubernetes tokens, cloud credentials, deployment secrets, CI/CD secrets, and host-mounted secrets.
· Limit metadata service access where feasible.
· Apply least privilege to cloud instance roles, managed identities, service accounts, deployment roles, and CI/CD automation identities.
· Rotate credentials when root compromise is confirmed or suspected.
· Monitor sensitive file access after suspicious local execution or privilege transition.
Cloud Workload Controls
· Map cloud roles, managed identities, storage permissions, snapshot permissions, secret-manager permissions, and workload ownership to vulnerable Linux assets.
· Alert on unusual role use, secret retrieval, storage access, snapshot access, security group changes, or cloud API activity following suspected host compromise.
· Limit cloud instance and workload identities to minimum required permissions.
· Harden metadata access and workload identity exposure.
· Preserve cloud-control-plane logs long enough to support post-compromise scoping.
Kubernetes and Container Controls
· Maintain current inventory of Kubernetes node images, container-host baselines, runtime socket exposure, privileged pods, hostPath mounts, service account permissions, and namespace sensitivity.
· Limit privileged containers and host-mounted paths.
· Restrict runtime socket access.
· Rotate Kubernetes tokens and secrets after suspected root compromise.
· Monitor kubelet paths, service account material, runtime sockets, container directories, host namespaces, and node-level activity.
· Rebuild nodes or container hosts when trust cannot be validated after suspected root compromise.
CI/CD and Build Controls
· Treat CI runners and build hosts as high-value Linux infrastructure.
· Patch runner images, build-host baselines, and ephemeral runner templates.
· Limit CI/CD secrets available to individual jobs.
· Restrict long-lived deployment credentials, repository tokens, package registry tokens, artifact credentials, and cloud permissions.
· Monitor unexpected local execution, writable-path staging, root-owned process creation, repository access, package publication, cloud deployment activity, and artifact changes.
· Rebuild or replace runners after suspected root-level compromise.
Detection and Response Controls
· Correlate vulnerable host state with local execution, writable-path staging, privilege transition, root-owned process creation, sensitive file access, security-control tampering, and post-root cloud or Kubernetes activity.
· Avoid treating vulnerable inventory as confirmed exploitation.
· Avoid treating absence of direct kernel-primitive telemetry as proof that exploitation did not occur.
· Route high-confidence privilege-transition events for immediate host isolation and credential review.
· Preserve telemetry before rebuilds, terminations, node replacements, or runner resets.
· Validate that SOC playbooks distinguish exposure, suspected exploitation, confirmed root compromise, and post-root expansion.
S33 Strategic Defensive Improvement
Strategic Improvement Objective
Copy Fail highlights a recurring defensive challenge: organizations often patch Linux systems but lack consistent visibility into what happens between initial local execution and root-level compromise. Strategic improvement should focus on reducing Linux privilege-escalation blast radius, improving host-to-cloud context, strengthening workload trust boundaries, and ensuring that remediation does not stop at patch deployment.
Linux Exposure and Patch Assurance
Organizations should move from asset-level vulnerability tracking to exposure-aware Linux remediation. Patch priority should reflect whether a vulnerable host is internet-facing, cloud-connected, Kubernetes-adjacent, container-hosted, CI/CD-connected, production-critical, or credential-rich.
Required Improvement
· Maintain kernel-aware inventory across cloud, on-premises, Kubernetes, container, CI/CD, and ephemeral infrastructure.
· Tie vulnerability findings to host role, exposure, cloud identity, Kubernetes context, and workload ownership.
· Validate reboot, live-patch, image, autoscaling, node pool, and CI runner baseline status.
· Prevent vulnerable images from being redeployed after remediation.
Privilege-Transition Visibility
Organizations should treat low-privilege-to-root transition as a critical telemetry requirement for Linux security operations. Root-owned activity is common in enterprise environments, but root-owned activity following suspicious non-root execution, writable-path staging, or vulnerable host exposure is materially different.
Required Improvement
· Capture process ancestry, command line, effective user, source user, executable path, and working directory.
· Monitor root-owned process creation from suspicious parentage.
· Identify unusual privileged binary interaction and sensitive file access.
· Correlate privilege transition with vulnerability state and host criticality.
Cloud and Workload Context Enrichment
Local Linux exploitation can become cloud, Kubernetes, container, or CI/CD compromise when host trust material is exposed. Defensive maturity requires linking host events to workload role, identity permissions, and operational blast radius.
Required Improvement
· Enrich Linux host telemetry with cloud account, subscription, project, instance role, managed identity, Kubernetes cluster, node, namespace, container host, runtime, CI runner, and workload owner context.
· Map sensitive credentials and trust relationships available from high-value hosts.
· Correlate suspected root compromise with cloud API, Kubernetes, container, repository, CI/CD, and identity activity.
Secret and Identity Blast-Radius Reduction
Root compromise becomes more severe when hosts contain reusable credentials, broad cloud roles, deployment secrets, Kubernetes tokens, or CI/CD authority. Reducing secret concentration reduces the operational value of successful privilege escalation.
Required Improvement
· Limit long-lived credentials on Linux systems.
· Restrict instance roles, managed identities, Kubernetes service accounts, CI/CD secrets, and deployment credentials.
· Rotate secrets after suspected root compromise.
· Prefer short-lived credentials and scoped workload identities where practical.
· Monitor sensitive token and secret access after privilege-transition events.
Recovery and Trust Revalidation
Patch completion does not automatically restore trust when exploitation may have occurred. Recovery must include scoping, credential review, telemetry preservation, and workload validation.
Required Improvement
· Define rebuild thresholds for vulnerable hosts with suspicious staging, privilege transition, or post-root behavior.
· Preserve telemetry before destructive remediation actions.
· Validate cloud, Kubernetes, container, and CI/CD activity after suspected compromise.
· Confirm that replaced systems derive from patched baselines.
· Document exposure, suspected exploitation, confirmed compromise, and residual risk separately.
Strategic Outcome
The desired end state is a Linux security program that can rapidly identify vulnerable systems, prioritize the systems that matter most, detect suspicious local escalation, contain root-level compromise, validate exposed trust paths, and restore infrastructure confidence without relying solely on static vulnerability inventory or after-the-fact forensic reconstruction.
S34 Defensive Architecture Overview
Figure 6
Architecture Objective
The defensive architecture for Copy Fail should interrupt the attack path at multiple points: vulnerable host exposure, local execution, exploit staging, privilege transition, root-level control, credential access, cloud or workload expansion, and post-root persistence or impact. The architecture must combine vulnerability management, endpoint telemetry, Linux audit visibility, cloud telemetry, Kubernetes and container context, CI/CD monitoring, identity controls, and response orchestration.
Layer 1: Vulnerable Asset and Exposure Management
This layer identifies where Copy Fail matters most by combining kernel version, patch state, distribution, cloud image, node image, container-host baseline, CI runner image, exposure, workload role, and business criticality.
Control Focus
· Kernel inventory.
· Patch and reboot validation.
· Cloud image and golden image validation.
· Kubernetes node image validation.
· Container-host baseline validation.
· CI runner image validation.
· Exposure and host criticality prioritization.
Layer 2: Local Execution and Staging Detection
This layer identifies suspicious execution activity that may precede exploitation. It prioritizes writable-path execution, unexpected interpreters, local binaries, file creation and execution bursts, suspicious command lines, and non-root execution on vulnerable high-value hosts.
Control Focus
· Process creation telemetry.
· Parent and child process lineage.
· Command-line capture.
· Executable path and working directory.
· Writable-path execution monitoring.
· CI workspace and build directory monitoring.
· Container writable-layer awareness.
Layer 3: Privilege-Transition Detection
This layer identifies the core risk transition from limited access to root-level authority. It combines host vulnerability state, local staging, root-owned process creation, privileged binary interaction, effective-user changes, and direct kernel-primitive evidence where available.
Control Focus
· Low-privilege-to-root transition monitoring.
· Root-owned process creation from suspicious parentage.
· Privileged binary and SUID-root activity review.
· Linux audit telemetry.
· EDR or eBPF telemetry where available.
· Conditional AF_ALG, algif_aead, splice-adjacent, and page-cache telemetry.
Layer 4: Post-Root Credential and Trust Protection
This layer detects and limits the attacker’s ability to turn root access into broader compromise. It monitors access to sensitive files, secrets, tokens, runtime sockets, cloud metadata services, Kubernetes paths, CI/CD credentials, and deployment material.
Control Focus
· Sensitive file access monitoring.
· SSH key access monitoring.
· Service credential and application secret protection.
· Kubernetes service account and kubelet path monitoring.
· Container runtime socket monitoring.
· Cloud metadata and managed identity monitoring.
· CI/CD secret and deployment credential monitoring.
Layer 5: Cloud, Kubernetes, Container, and CI/CD Correlation
This layer identifies expansion beyond the original host by correlating host compromise signals with cloud APIs, Kubernetes audit activity, container runtime activity, repository access, CI/CD events, artifact activity, and identity usage.
Control Focus
· Cloud audit logs.
· Kubernetes audit logs.
· Container runtime and node telemetry.
· CI/CD job and runner logs.
· Repository and package registry logs.
· Identity and access logs.
· Workload ownership and host role enrichment.
Layer 6: Response and Recovery Orchestration
This layer ensures suspected exploitation leads to rapid, coordinated action without destroying evidence. It defines isolation, credential rotation, node replacement, workload rebuild, image validation, cloud review, and recovery validation workflows.
Control Focus
· Host isolation.
· Telemetry preservation.
· Credential rotation.
· Kubernetes node replacement.
· Container host rebuild.
· CI runner reset or replacement.
· Cloud identity review.
· Patch validation.
· Recovery confidence documentation.
Architecture Design Principle
The architecture should not depend on a single detection source. Copy Fail defense requires layered correlation across vulnerable host state, suspicious local execution, writable-path staging, privilege transition, sensitive access, security-control tampering, and post-root cloud or workload activity. This layered model reduces false confidence from patch inventory alone and improves response confidence when direct kernel-level exploit telemetry is unavailable.
S35 Security Hardening Guidance
Hardening Objective
Security hardening should reduce the likelihood that attackers can obtain local execution, reduce the probability that local execution becomes root compromise, and reduce the blast radius if root escalation occurs. Hardening should apply across Linux hosts, cloud workloads, Kubernetes nodes, container hosts, CI/CD systems, credentials, and telemetry pipelines.
Linux Host Hardening
· Apply vendor-supported kernel updates and security patches.
· Validate reboot or live-patch effectiveness.
· Reduce unnecessary SUID-root binaries where operationally feasible.
· Restrict execution from writable paths where feasible.
· Monitor or constrain execution from /tmp, /var/tmp, /dev/shm, user home directories, CI workspaces, build directories, and mounted workload paths.
· Harden SSH access and disable unnecessary interactive access.
· Enforce least privilege for local users, service accounts, application accounts, and automation accounts.
· Remove unnecessary compilers, build tools, interpreters, and debugging utilities from production systems where feasible.
· Enable audit coverage for privilege-relevant activity, sensitive file access, and security-control tampering.
· Validate EDR, Linux audit, cloud agent, and vulnerability agent health after patching.
Cloud Workload Hardening
· Restrict instance roles and managed identities to minimum required permissions.
· Harden metadata service access where supported.
· Limit broad secret-manager, storage, snapshot, and role-assumption permissions.
· Enforce workload ownership and cloud identity mapping.
· Monitor unusual cloud API activity following suspicious host events.
· Use patched and validated cloud images for autoscaling, recovery, and redeployment.
· Prevent vulnerable images from being reused in golden image pipelines.
Kubernetes Hardening
· Patch and rotate vulnerable worker nodes through controlled node replacement.
· Restrict privileged pods and hostPath mounts.
· Limit service account permissions.
· Review kubelet exposure, node credentials, runtime socket exposure, and namespace sensitivity.
· Rotate service account tokens and secrets where node compromise is suspected.
· Monitor Kubernetes audit activity after suspected host compromise.
· Validate node pool images and cluster autoscaling templates.
Container Host Hardening
· Restrict access to Docker, containerd, CRI, and runtime sockets.
· Limit host namespace exposure and host-mounted secrets.
· Reduce privileged container use.
· Validate container-host kernel versions and baseline images.
· Monitor container-to-host activity and runtime socket interaction.
· Rebuild container hosts from patched baselines when trust cannot be confirmed.
CI/CD Hardening
· Patch CI runner hosts and runner images.
· Use ephemeral runners where feasible and ensure they are built from patched templates.
· Reduce secrets exposed to build jobs.
· Scope deployment credentials, repository tokens, package registry tokens, and cloud permissions.
· Monitor build jobs for unexpected writable-path execution, local compilation, privilege transition, and root-owned process creation.
· Rebuild runners after suspected root-level compromise.
· Validate artifacts, package publication, and deployment activity after suspected runner compromise.
Credential and Secret Hardening
· Reduce long-lived credentials on Linux hosts.
· Rotate secrets after suspected root-level compromise.
· Use scoped, short-lived credentials where feasible.
· Restrict access to SSH private keys, deployment keys, cloud credentials, service account tokens, and application secrets.
· Monitor access to credential paths after suspicious local execution or root transition.
· Separate build, deployment, production, and administrative credentials.
Telemetry Hardening
· Capture process creation, command line, parent process, executable path, working directory, source user, effective user, and host role.
· Enable Linux audit or equivalent telemetry for sensitive file access and privilege-relevant behavior.
· Preserve logs long enough to support exposure-window scoping.
· Enrich host telemetry with cloud, Kubernetes, container, CI/CD, and identity context.
· Monitor security-agent health and telemetry gaps as investigation signals.
· Validate that detections do not depend solely on static exploit filenames, proof-of-concept artifacts, hashes, or vulnerable-state inventory.
S36 Security Program Maturity Assessment
Maturity Assessment Purpose
Copy Fail exposes maturity gaps in Linux vulnerability management, privilege-transition monitoring, cloud workload security, Kubernetes and container visibility, CI/CD hardening, credential protection, and incident response coordination. Mature programs will not only patch the vulnerability; they will also prove whether vulnerable systems were abused and whether root-level access created broader enterprise exposure.
Low Maturity
Organizations at low maturity rely primarily on vulnerability scans, patch tickets, and basic endpoint alerts. They may know that Linux systems are vulnerable but cannot reliably determine whether local execution occurred, whether privilege escalation was attempted, or whether root-level compromise exposed credentials or workload trust.
Common Indicators
· Incomplete Linux asset inventory.
· Weak kernel, reboot, and image tracking.
· Limited process ancestry or command-line telemetry.
· Limited Linux audit visibility.
· Minimal cloud, Kubernetes, container, or CI/CD context.
· No reliable mapping between vulnerable hosts and workload ownership.
· Weak credential rotation triggers after suspected root compromise.
· Limited ability to distinguish exposure from exploitation.
Operational Effect
Response may become broad, slow, and confidence-limited. Teams may either overreact to vulnerable inventory or underreact to suspicious behavior because they lack the telemetry needed to prove escalation.
Moderate Maturity
Organizations at moderate maturity can identify vulnerable systems, prioritize exposed assets, apply patches, and review some host behavior. They may have endpoint telemetry and cloud logs, but correlation across Linux hosts, Kubernetes, containers, CI/CD systems, and identity activity may still require manual effort.
Common Indicators
· Kernel and patch visibility across most Linux systems.
· Partial command-line and process ancestry coverage.
· Some Linux audit or EDR visibility.
· Vulnerability prioritization based on exposure and criticality.
· Cloud and Kubernetes logs available but not consistently correlated to host events.
· CI/CD runner visibility available but incomplete.
· Credential rotation processes exist but may be slow or manually triggered.
· SOC playbooks distinguish exposure and suspected exploitation but require analyst judgment.
Operational Effect
Response is viable but may be labor-intensive. Teams can reduce risk with targeted hunting and patching, but full confidence may require cross-team investigation and manual enrichment.
High Maturity
Organizations at high maturity can rapidly identify vulnerable Linux systems, prioritize based on blast radius, detect suspicious staging and privilege transition, correlate host events with cloud and Kubernetes context, rotate exposed credentials, and rebuild or replace untrusted systems from patched baselines.
Common Indicators
· Comprehensive Linux, cloud, Kubernetes, container, and CI/CD asset inventory.
· Kernel, package, reboot, image, node pool, and runner baseline validation.
· Strong process telemetry with command line, parent process, source user, effective user, path, and working directory.
· Linux audit, EDR, or eBPF telemetry for sensitive file access and privilege-relevant activity.
· Cloud identity, Kubernetes, container, and CI/CD context enrichment.
· Automated prioritization for exposed, production-critical, credential-rich, and workload-sensitive systems.
· Clear response workflows for isolation, credential rotation, node replacement, runner rebuild, image validation, and recovery assurance.
· Strong ability to separate vulnerable-state exposure, suspected exploitation, confirmed root compromise, and post-root expansion.
Operational Effect
Response can be targeted, fast, and evidence-driven. Teams can patch quickly, preserve telemetry, identify suspicious privilege-transition behavior, validate exposed trust paths, and report residual risk with confidence.
Target Maturity State
The target maturity state is high maturity for Linux infrastructure that supports cloud workloads, Kubernetes nodes, container hosts, CI runners, production services, and sensitive credential paths. Organizations do not need uniform perfect telemetry across every Linux asset, but they do need strong coverage for systems where root escalation would create material business impact.
S37 Residual Risk and Forward Outlook
Residual Risk Summary
Residual risk remains after patching because Copy Fail is part of a broader post-foothold Linux escalation problem. Patching closes the known vulnerability path, but it does not automatically prove that vulnerable systems were not exploited during the exposure window, that credentials were not accessed, or that cloud, Kubernetes, container, CI/CD, or production trust paths were not affected.
Primary Residual Risks
· Previously vulnerable systems may have been exposed before patching.
· Local execution may have occurred without direct exploit-primitive visibility.
· Root escalation may be missed if process ancestry, effective-user, or Linux audit telemetry is incomplete.
· Credential or secret exposure may remain unresolved if access was not reviewed after suspicious root activity.
· Cloud, Kubernetes, container, or CI/CD expansion may occur after host compromise through exposed trust material.
· Vulnerable images, node templates, runner images, or golden images may reintroduce exposure.
· Security-control tampering may reduce confidence in telemetry from the compromise window.
· Unpatched or exception-managed systems may remain exploitable if local execution is later obtained.
Forward Outlook
Copy Fail will likely remain operationally relevant because local privilege escalation vulnerabilities retain value after attackers obtain footholds through exposed applications, stolen credentials, container execution, CI job abuse, or other intrusion paths. Public exploit availability and KEV status increase the likelihood that opportunistic operators will incorporate the vulnerability into post-compromise workflows where affected systems remain unpatched or poorly monitored.
Expected Defensive Pressure
· Linux patch validation will remain a near-term priority.
· Cloud Linux workload exposure will remain a high-priority scoping issue.
· Kubernetes node and container-host trust validation will remain important where vulnerable systems supported workload infrastructure.
· CI/CD runner and build-host exposure will remain a supply-chain risk concern.
· Credential and secret rotation decisions will depend on whether root-level access is confirmed or strongly suspected.
· Detection programs will need to emphasize behavior correlation rather than static exploit artifacts.
Risk Reduction Outlook
Risk decreases materially when vulnerable systems are patched, rebooted or live-patched effectively, rebuilt from trusted baselines where needed, and reviewed for suspicious execution, privilege transition, sensitive file access, and post-root behavior. Risk remains elevated where Linux systems are exposed, credential-rich, cloud-connected, Kubernetes-adjacent, container-hosted, CI/CD-connected, or production-critical and where telemetry cannot support confident scoping.
Executive Forward View
Executives should treat Copy Fail as both a vulnerability remediation issue and a Linux infrastructure trust issue. The durable lesson is that local privilege escalation on high-value Linux systems can convert ordinary footholds into cloud, Kubernetes, container, CI/CD, identity, and production risk. Long-term resilience depends on exposure-aware patching, strong privilege-transition visibility, reduced credential concentration, hardened workload trust boundaries, validated telemetry, and response workflows that can restore trust after root-level compromise.
Final Residual Risk Position
Residual risk is acceptable only when vulnerable Linux assets are patched or mitigated, high-value systems are validated, suspicious local execution is reviewed, privilege-transition behavior is scoped, exposed credentials are rotated where needed, cloud and Kubernetes activity is checked, and vulnerable images or templates are removed from redeployment paths. Where those conditions are not met, residual risk should remain elevated until exposure, exploitation, and post-root blast radius can be confidently ruled out.
S38 Intelligence Confidence Assessment
Figure 7
Overall Confidence Level
High for vulnerability existence, local privilege escalation class, affected Linux ecosystem breadth, KEV status, patch availability, and the root-level escalation outcome. Moderate for organization-specific exploitation, confirmed post-root activity, credential exposure, cloud expansion, Kubernetes impact, CI/CD impact, and business impact without environment-specific telemetry.
Source Reliability
High reliability based on Microsoft security research, CISA KEV catalog status, NVD vulnerability tracking, Linux distribution advisories, and public technical research. Microsoft reporting supports the core assessment that CVE-2026-31431 affects major Linux distributions, enables root privilege escalation, is relevant to cloud Linux workloads and Kubernetes environments, and has working exploit availability. Public technical research supports the exploit-mechanics assessment involving AF_ALG, algif_aead, splice-adjacent behavior, page-cache manipulation, privileged binary corruption, and root escalation.
Analytical Confidence Drivers
· Microsoft identifies Copy Fail as a high-severity local privilege escalation vulnerability affecting major Linux distributions.
· CISA KEV status confirms the vulnerability requires urgent exploited-vulnerability management attention.
· Public technical research describes a plausible and concrete root-escalation path involving page-cache manipulation and privileged binary corruption.
· Vendor and distribution advisories support patch and mitigation tracking across major Linux ecosystems.
· The report’s attack model aligns with the vulnerability’s core operating condition: local execution followed by privilege escalation.
· The completed detection model aligns with the expected behavior chain: local execution, writable-path staging, privilege transition, root-owned process activity, sensitive access, and post-root cloud, Kubernetes, container, or CI/CD activity.
· The report consistently separates vulnerable-state exposure from suspected exploitation and confirmed post-root compromise.
· The report treats cloud, Kubernetes, container, CI/CD, persistence, lateral movement, and impact as conditional post-escalation outcomes unless supported by telemetry.
High-Confidence Judgments
· Copy Fail is a post-foothold Linux local privilege escalation vulnerability, not a standalone remote-entry mechanism.
· The primary enterprise risk is conversion of limited local execution into root-level host control.
· Vulnerable Linux systems with cloud, Kubernetes, container, CI/CD, production, or credential-rich roles carry elevated business risk.
· KEV status and public exploit availability make patch validation and exposure-aware prioritization necessary.
· Vulnerable-state inventory alone does not prove exploitation.
· Absence of direct AF_ALG, algif_aead, splice, or page-cache telemetry does not prove exploitation did not occur.
· The strongest detection model is behavioral correlation across local execution, writable-path staging, privilege transition, root-owned process creation, sensitive file access, and post-root activity.
· Patch completion must be paired with hunting, credential review, and trust-path validation where exposure existed during the vulnerable window.
Moderate-Confidence Judgments
· Organizations with internet-facing Linux workloads, Kubernetes worker nodes, container hosts, CI runners, cloud Linux instances, or production Linux systems are more likely to require urgent scoping.
· Root-level compromise may expose cloud identity material, Kubernetes tokens, runtime sockets, deployment credentials, CI/CD secrets, or production workload trust depending on host role.
· Public exploit availability may drive opportunistic exploitation where affected hosts remain unpatched and local execution is obtainable.
· Cloud-control-plane activity, Kubernetes activity, container runtime access, CI/CD activity, and repository activity may become relevant after root compromise, but they require source-specific evidence.
Lower-Confidence / Conditional Judgments
· Confirmed exploitation cannot be assumed from vulnerable kernel state alone.
· Confirmed credential theft cannot be assumed without sensitive file access, token access, cloud metadata interaction, or credential-use evidence.
· Confirmed Kubernetes, container, cloud, CI/CD, repository, or identity expansion cannot be assumed without relevant telemetry.
· Confirmed service disruption, data destruction, or operational impact cannot be assumed without observed impact behavior.
· Precise financial impact depends on organization-specific exposure, workload criticality, credential scope, telemetry quality, recovery complexity, regulatory obligations, and response duration.
Telemetry Confidence Assessment
Endpoint and Linux Host Telemetry
Moderate to High where process creation, command line, parent-child lineage, executable path, working directory, source user, effective user, Linux audit, sensitive file access, and agent-health telemetry are available. Confidence is reduced where Linux systems lack command-line capture, process ancestry, effective-user context, or audit coverage.
Kernel-Primitive Telemetry
Moderate where eBPF, syscall, audit, or EDR kernel telemetry can observe AF_ALG, algif_aead, splice-adjacent behavior, page-cache-related activity, or privileged binary interaction. Confidence is reduced where defenders must rely only on surrounding process behavior and privilege-transition outcomes.
Cloud Telemetry
Moderate to High where cloud audit logs, identity logs, instance role activity, managed identity activity, secret-manager access, storage access, snapshot activity, and source-host correlation are retained. Confidence is reduced where cloud credentials are reusable but cannot be tied back to a source host or compromise window.
Kubernetes and Container Telemetry
Moderate where Kubernetes audit logs, node telemetry, runtime socket monitoring, pod context, namespace context, service account activity, hostPath use, and container-host mapping are available. Confidence is reduced where node-level telemetry, runtime activity, or workload-to-host mapping is incomplete.
CI/CD and Build Telemetry
Moderate where runner logs, job history, build logs, artifact logs, repository events, package registry activity, deployment records, and runner identity are retained. Confidence is reduced for ephemeral runners, unmanaged build hosts, or workflows without process-level visibility.
Network and Egress Telemetry
Moderate where DNS, proxy, firewall, EDR network telemetry, cloud flow logs, and source-host attribution are available. Confidence is reduced because Copy Fail exploitation itself is local, and network telemetry primarily supports initial-access, tooling, credential-use, or post-root expansion analysis.
Intelligence Confidence Disposition
The overall intelligence confidence is High for the governing conclusion that Copy Fail is a local Linux privilege escalation vulnerability with significant cloud, Kubernetes, container, and CI/CD blast-radius relevance. Confidence is Moderate for environment-specific exploitation and business impact until host execution, privilege-transition behavior, credential access, cloud activity, Kubernetes activity, container runtime interaction, CI/CD activity, and recovery evidence are validated in the affected environment.
S39 Analytical Notes and Limitations
Analytical Notes Objective
Document the assumptions, evidence boundaries, and analytical limitations that should guide interpretation of this report.
Analytical Note 1 — Report Type and Governing Frame
This report is governed as a [CVE] vulnerability intelligence report. The core issue is a Linux local privilege escalation vulnerability that becomes most consequential after an attacker has already obtained local execution on a vulnerable system.
Analytical Note 2 — Local Exploitation Boundary
Copy Fail is not assessed as a standalone remote-entry condition. The vulnerability requires local execution or an authenticated operating position before exploitation becomes possible. Remote exposure matters because exposed applications, stolen credentials, containers, CI jobs, or other access paths may provide the prerequisite local execution.
Analytical Note 3 — Vulnerable State Versus Exploitation
Vulnerable kernel state indicates exposure, not confirmed exploitation. Confirmed or higher-confidence exploitation requires behavioral evidence such as suspicious local execution, writable-path staging, abnormal low-privilege-to-root transition, root-owned process creation, privileged binary interaction, sensitive file access, security-control tampering, or post-root activity.
Analytical Note 4 — Kernel-Primitive Visibility Is Conditional
Direct evidence of AF_ALG, algif_aead, splice-adjacent behavior, or page-cache activity may materially improve confidence, but many enterprise environments do not capture that telemetry consistently. Absence of direct kernel-primitive evidence should not be interpreted as proof that exploitation did not occur.
Analytical Note 5 — Page-Cache Behavior Limits Traditional File Integrity Assumptions
Public technical analysis indicates the exploit can affect in-memory page-cache state without necessarily modifying the on-disk file. This means traditional on-disk file integrity monitoring may not fully capture the exploit condition. Defenders should prioritize process behavior, privilege-transition evidence, and post-root activity rather than relying only on persistent file modification.
Analytical Note 6 — Post-Root Expansion Is Conditional
Cloud, Kubernetes, container, CI/CD, repository, and identity expansion are conditional outcomes. They depend on the role of the compromised host, available credentials, trust relationships, runtime access, identity permissions, and attacker objectives.
Analytical Note 7 — Credential Exposure May Be Difficult to Prove
Credential or secret exposure may occur without durable artifacts if credentials are read from environment variables, memory, temporary files, mounted secrets, metadata services, runtime paths, or CI/CD contexts. Absence of file-read telemetry does not prove absence of credential exposure.
Analytical Note 8 — Cloud-Control-Plane Activity Is Post-Compromise Evidence
Cloud audit logs can reveal credential use, secret access, role activity, storage access, snapshot activity, or control-plane changes after host compromise. They should not be represented as direct observation of the local Linux kernel exploit primitive.
Analytical Note 9 — Kubernetes and Container Impact Requires Context
Kubernetes or container impact cannot be assumed solely from vulnerable Linux host exposure. Higher confidence requires node role, pod context, service account access, runtime socket interaction, hostPath exposure, kubelet path access, namespace sensitivity, or Kubernetes audit evidence.
Analytical Note 10 — Patch Completion Does Not Automatically Restore Trust
Patching closes the known vulnerable path, but it does not prove that exploitation did not occur during the exposure window. Systems with suspicious staging, privilege transition, sensitive access, or security-tool tampering require additional scoping, credential review, and trust validation.
Analytical Note 11 — Cost Estimates Are Scenario-Based
Executive cost ranges in Block 1 are scenario-based estimates. Actual impact depends on vulnerable asset scope, local execution likelihood, cloud and Kubernetes dependency, credential concentration, telemetry availability, detection latency, patch timing, containment complexity, regulatory exposure, customer impact, and recovery duration.
Analytical Note 12 — References Are Public-Source Anchors
The references in S40 provide public-source grounding for vulnerability context, exploitation mechanics, KEV status, vendor advisories, and ATT&CK mapping. They do not replace organization-specific forensic validation, patch validation, or telemetry review.
Analytical Limitations
· This report does not prove that any specific organization experienced Copy Fail exploitation.
· This report does not prove exploitation based on vulnerable kernel state alone.
· This report does not prove credential theft without sensitive access, credential-use, forensic, or telemetry evidence.
· This report does not prove cloud, Kubernetes, container, CI/CD, repository, or identity compromise without source-specific evidence.
· This report does not prove service disruption, data destruction, or operational impact without impact telemetry or business-process evidence.
· This report does not include proprietary customer telemetry, kernel inventory, cloud logs, Kubernetes logs, CI/CD logs, endpoint telemetry, or forensic artifacts unless separately provided.
· This report does not rely on static exploit filenames, proof-of-concept artifacts, hashes, or CVE strings as the sole detection or remediation model.
Analytical Notes and Limitations Disposition
The analytical conclusions are strong for vulnerability framing, exploitability class, attack path, detection strategy, mitigation priorities, and defensive control requirements. Organization-specific impact remains dependent on exposure scoping, telemetry validation, credential assurance, cloud and Kubernetes review, CI/CD review, and recovery-confidence validation.
S40 References
Primary Vendor and Vulnerability Sources
· Microsoft Security Blog — CVE-2026-31431: Copy Fail vulnerability enables Linux root privilege escalation across cloud environments — hxxps://www[.]microsoft[.]com/en-us/security/blog/2026/05/01/cve-2026-31431-copy-fail-vulnerability-enables-linux-root-privilege-escalation/
· CISA — Known Exploited Vulnerabilities Catalog — hxxps://www[.]cisa[.]gov/known-exploited-vulnerabilities-catalog
· NVD — CVE-2026-31431 vulnerability record — hxxps://nvd[.]nist[.]gov/vuln/detail/CVE-2026-31431
Linux Distribution and Platform Advisories
· Amazon Linux Security Center — CVE-2026-31431 — hxxps://explore[.]alas[.]aws[.]amazon[.]com/CVE-2026-31431.html
· Ubuntu Security — CVE-2026-31431 — hxxps://ubuntu[.]com/security/CVE-2026-31431
· Debian Security Tracker — CVE-2026-31431 — hxxps://security-tracker[.]debian[.]org/tracker/CVE-2026-31431
· Red Hat Bugzilla — CVE-2026-31431 kernel crypto algif_aead — hxxps://bugzilla[.]redhat[.]com/show_bug.cgi?id=CVE-2026-31431
· Red Hat Customer Portal — Mitigation for CVE-2026-31431 in Azure Red Hat OpenShift — hxxps://access[.]redhat[.]com/solutions/7141990
· SUSE CVE Tracker — CVE-2026-31431 — hxxps://www[.]suse[.]com/security/cve/CVE-2026-31431.html
Technical Research and Security Analysis
· Xint Code Research Team — Copy Fail: 732 Bytes to Root on Every Major Linux Distribution — hxxps://xint[.]io/blog/copy-fail-linux-distributions
· Copy Fail Project Site — Copy Fail CVE-2026-31431 technical overview — hxxps://copy[.]fail/
· BleepingComputer — New Linux Copy Fail flaw gives hackers root on major distros — hxxps://www[.]bleepingcomputer[.]com/news/security/new-linux-copy-fail-flaw-gives-hackers-root-on-major-distros/
· The Hacker News — New Linux Copy Fail vulnerability enables root access on major distributions — hxxps://thehackernews[.]com/2026/04/new-linux-copy-fail-vulnerability.html
· Tenable — Copy Fail CVE-2026-31431 frequently asked questions about Linux kernel privilege escalation vulnerability — hxxps://www[.]tenable[.]com/blog/copy-fail-cve-2026-31431-frequently-asked-questions-about-linux-kernel-privilege-escalation
· OSTechNix — Copy Fail CVE-2026-31431 Linux kernel root exploit overview — hxxps://ostechnix[.]com/copy-fail-cve-2026-31431-linux-kernel-root-exploit/
Threat Technique Framework
· MITRE ATT&CK Framework — Enterprise Matrix / Techniques Catalog — hxxps://attack[.]mitre[.]org/