[EXP] VECT Ransomware-Wiper Operational Risk Report
Report Type: [EXP] Operational Risk Report
Threat Category: Ransomware-wiper / destructive ransomware
Assessment Date: May 1, 2026
Primary Impact Domain: Data destruction and operational disruption
Secondary Impact Domains: Recovery failure; backup and snapshot compromise; virtualization disruption; business continuity degradation; incident response escalation; cloud recovery-control exposure
Affected Asset Class: Windows endpoints and servers; Linux servers; VMware ESXi and virtualization infrastructure; file servers and shared storage; backup systems, snapshots, vaults, and recovery repositories; cloud-hosted workloads and cloud recovery assets in AWS, Azure, and GCP
Threat Objective Classification: Destructive extortion through ransomware deployment with wiper-like data-loss outcomes
BLUF
VECT ransomware-wiper activity creates material enterprise risk by turning ransomware execution into a destructive data-loss condition that may permanently damage files rather than preserve a recoverable encryption path. The risk is driven by large-scale file transformation, ransomware-like rewrite behavior, ransom-note staging, backup and recovery-path interference, and cross-platform execution risk across Windows, Linux, and VMware ESXi environments. The threat posture is elevated because current reporting indicates VECT 2.0 can permanently destroy files larger than 131,072 bytes, which exposes ordinary documents, archives, databases, virtual disks, backup artifacts, shared repositories, and business-critical operational data to unrecoverable loss. Executive action is required to validate exposure across endpoint, server, shared-storage, virtualization, backup, and cloud recovery environments; confirm immutable recovery readiness; prioritize detection for destructive file transformation; and ensure incident response teams can isolate affected systems before file damage reaches critical repositories.
Executive Risk Translation
VECT shifts business risk from conventional ransomware recovery negotiation to destructive operational loss. The primary concern is not only whether affected systems are encrypted, but whether files have been transformed in a way that prevents reliable restoration from local recovery paths or attacker-provided decryption. If destructive activity reaches file servers, databases, virtualization datastores, backup-accessible systems, or ESXi-managed infrastructure, response may expand into enterprise-wide containment, recovery validation, virtualization review, backup integrity testing, credential containment, customer-impact assessment, legal review, insurance reporting, and board-level incident governance. This creates financial, operational, compliance, resilience, and trust exposure beyond the first infected endpoint.
S3 — Why This Matters Now
· VECT should be treated as a destructive ransomware-wiper risk because current reporting indicates VECT 2.0 can permanently destroy files larger than 131,072 bytes across Windows, Linux, and ESXi variants.
· The business impact can exceed ordinary ransomware expectations because affected files may be unrecoverable even if attackers later provide a decryptor or the organization obtains malware artifacts.
· The affected file-size threshold is low enough to include ordinary enterprise documents, databases, compressed archives, backup artifacts, virtual disks, and operational repositories.
· VECT’s reported Windows, Linux, and ESXi scope expands risk beyond user endpoints into servers, shared storage, administrative systems, virtualization infrastructure, and hypervisor-adjacent assets.
· ESXi and virtualization impact can rapidly amplify disruption because damage to virtual disks, datastores, snapshots, or management paths can affect many dependent systems at once.
· Backup and recovery-control interference materially increases business risk because destructive ransomware outcomes become more severe when restore points, snapshots, vault policies, or backup jobs are impaired before or during file transformation.
· Static indicators such as file extensions, ransom-note names, hashes, sample strings, or network artifacts are useful for triage, but they are insufficient as the durable enterprise risk model.
· Organizations without endpoint process telemetry, file modification visibility, file-size fields, backup-platform telemetry, ESXi or virtualization logs, host-role enrichment, and SIEM correlation face elevated risk of delayed detection and incomplete recovery assurance.
S4 — Key Judgments
· VECT is a destructive ransomware-wiper operational risk, not a standard recoverable ransomware event.
· The primary business risk is irreversible loss of business-critical files, databases, archives, virtual disks, backup artifacts, and shared repositories.
· The strongest enterprise risk signal is suspicious execution followed by high-volume file modification, rename, extension change, ransom-note staging, recovery-path interference, or virtualization-adjacent impact.
· Backup, snapshot, vault, restore-point, and retention-policy tampering should be treated as major risk amplifiers because they reduce the organization’s ability to recover after destructive file transformation.
· ESXi and virtualization-adjacent activity should be treated as high priority because compromise or destructive activity in virtual infrastructure can create immediate multi-system business interruption.
· File extension, ransom-note, hash, YARA, or network-only logic should not be treated as sufficient for high-confidence enterprise detection.
· Detection must remain behavior-led because VECT may change filenames, extensions, ransom-note names, packing, infrastructure, or affiliate delivery paths, and the actor may correct the current encryption flaw while retaining the same ransomware operating model.
· Network-only visibility is insufficient because current public evidence supports destructive file behavior and cross-platform execution more strongly than stable network-signature detection.
· Cloud-control telemetry can identify backup, snapshot, storage, vault, and recovery-control tampering, but it should not be represented as direct observation of local VECT encryption unless workload endpoint telemetry is available.
· Executive risk reduction depends on rapid destructive-activity detection, endpoint isolation, backup protection, ESXi and virtualization review, immutable backup validation, file-scope assessment, and recovery-path assurance.
S5 — Executive Risk Summary
Business Risk
VECT ransomware-wiper activity can create severe operational disruption by damaging files in a way that may prevent normal decryption or restoration from compromised recovery paths. Risk increases when affected systems include file servers, shared repositories, database servers, backup-accessible systems, administrative workstations, VMware ESXi environments, virtualization management systems, cloud workloads, or systems with access to business-critical operational data.
Technical Cause
The risk is driven by ransomware-like execution that performs high-volume file transformation, rewrite, rename, or extension-change activity while staging ransom-note artifacts and potentially interfering with backup, recovery, snapshot, logging, or virtualization-adjacent controls. Current reporting indicates the destructive condition is tied to flawed encryption handling that can permanently damage files larger than 131,072 bytes.
Threat Posture
The threat posture is elevated because VECT combines ransomware execution with wiper-like operational consequences. The risk is not limited to infected endpoints; destructive file activity can spread through shared storage, mapped drives, server repositories, virtualization datastores, backup paths, and privileged administrative contexts. If recovery controls are impaired or virtualization infrastructure is affected, the event can escalate from local compromise to broad business interruption.
Executive Decision Requirement
Executives must require immediate validation of endpoint and file telemetry, backup integrity, virtualization exposure, immutable recovery readiness, and detection coverage for mass file transformation. Response leadership should also confirm that SOC and incident response workflows prioritize host isolation, backup protection, ESXi administrative review, credential containment, affected-file scoping, and restoration validation before destructive activity expands.
S6 — Executive Cost Summary
VECT ransomware-wiper activity creates financial exposure based on affected file scope, system criticality, backup recoverability, virtualization impact, detection speed, telemetry completeness, containment burden, operational downtime, legal exposure, customer impact, and the degree to which destructive file transformation reaches shared repositories, databases, virtual disks, backup systems, or production workloads.
Low Impact Scenario
Rapid detection confirms attempted or limited VECT-like execution on a small number of endpoints or non-critical systems, with no confirmed impact to file servers, backups, databases, virtual disks, ESXi infrastructure, shared repositories, production systems, regulated data, or customer-facing services. Response still requires endpoint isolation, forensic validation, telemetry review, recovery assurance, detection tuning, and executive incident tracking because destructive ransomware-wiper activity cannot be treated as ordinary commodity malware; estimated impact $1M to $4M.
Moderate Impact Scenario
Confirmed destructive file transformation affects a limited but meaningful set of endpoints, servers, shared repositories, backup-accessible systems, or virtualization-adjacent assets, requiring endpoint isolation, file-scope review, backup validation, selective restoration, credential containment, SOC surge activity, forensic review, detection tuning, executive incident coordination, legal review, and business-unit recovery planning. Recovery remains achievable, but confidence depends on validating that backups, snapshots, virtual disks, databases, and shared repositories were not broadly impaired; estimated impact $6M to $25M.
High Impact Scenario
Destructive file transformation affects business-critical repositories, databases, virtual disks, VMware ESXi datastores, backup systems, recovery controls, production workloads, regulated data stores, or customer-facing services, resulting in prolonged operational interruption, broad restoration activity, virtualization recovery, backup rehydration, data-integrity validation, legal and regulatory review, customer assurance, insurance reporting, and board-level incident governance. Cost can escalate sharply when files are unrecoverable, backups are impaired, ESXi infrastructure is affected, or telemetry gaps prevent rapid scoping; estimated impact $30M to $150M or higher.
S6A — Key Cost Drivers
· Number and criticality of affected endpoints, servers, file shares, databases, backup-accessible systems, administrative workstations, ESXi hosts, virtualization management systems, and cloud workloads.
· Whether destructive file transformation reached business-critical documents, databases, archives, virtual disks, backup artifacts, shared repositories, or operational data stores.
· Whether files larger than 131,072 bytes were modified, rewritten, renamed, corrupted, or rendered unrecoverable.
· Time from initial execution or file transformation to detection, containment, host isolation, and backup protection.
· Availability of endpoint process telemetry, command-line visibility, file modification telemetry, file-size fields, initiating-process attribution, host-role enrichment, and SIEM correlation.
· Ability to determine the initiating process, user, host, affected path, file scope, asset criticality, and overlap with shared storage, backup paths, or virtualization assets.
· Scope of backup, snapshot, vault, recovery-point, retention-policy, restore-job, and immutable-backup validation.
· Scope of VMware, ESXi, vCenter, datastore, VM snapshot, virtual disk, and virtualization-management review.
· Whether cloud recovery assets, snapshots, images, storage controls, backup vaults, or recovery policies were modified by unusual identities, source hosts, or automation paths.
· Whether approved backup jobs, indexing, software deployment, compression, data migration, synchronization, or encryption workflows can be quickly distinguished from destructive ransomware behavior.
· Need for endpoint rebuilds, server restoration, database recovery, virtual machine restoration, backup rehydration, data-integrity validation, and business-process recovery.
· Need for legal review, regulatory notification analysis, customer assurance, cyber insurance reporting, executive incident governance, or board-level reporting.
Most Likely Scenario Justification
Moderate scenario is most likely when VECT-like activity affects enterprise endpoints, servers, shared repositories, backup-accessible systems, or virtualization-adjacent environments because even contained destructive file transformation can require extensive file-scope review, backup validation, restoration testing, telemetry reconciliation, legal coordination, and executive incident oversight. The estimate moves toward the lower end when telemetry confirms limited execution, rapid containment, no backup or ESXi impact, no critical file damage, no cloud recovery-control tampering, and validated immutable recovery. The estimate moves toward the upper end when affected systems include file servers, databases, virtual disks, backup infrastructure, VMware environments, privileged administrative systems, regulated data, incomplete telemetry, or customer-facing operational dependencies.
S6B — Compliance and Risk Context
Compliance Exposure Indicator
Moderate to High depending on whether destructive file transformation, recovery-path tampering, virtualization impact, or operational disruption affected regulated data, customer-facing services, material business operations, contractual service obligations, production systems, or evidence needed for incident scoping and recovery assurance.
Risk Register Entry
Risk Title
VECT Ransomware-Wiper Destructive File Transformation and Recovery-Path Exposure
Risk Description
Adversaries may deploy VECT ransomware-wiper activity that performs destructive file transformation across endpoint, server, shared-storage, backup-accessible, virtualization, or cloud-hosted environments, potentially rendering files unrecoverable, impairing backup or recovery controls, disrupting virtual infrastructure, and creating broad operational, financial, compliance, and governance exposure.
Likelihood
High.
Impact
Severe.
Risk Rating
Critical.
Annualized Risk Exposure
Estimated $8M to $45M or higher based on exposed data scope, file-server dependency, backup recoverability, virtualization reliance, cloud recovery architecture, detection latency, telemetry completeness, restoration complexity, operational downtime, customer exposure, and regulatory obligations.
S7 — Risk Drivers
· VECT’s destructive file transformation can create unrecoverable data loss rather than standard recoverable ransomware encryption.
· Current reporting indicates files larger than 131,072 bytes may be permanently destroyed, exposing common enterprise documents, databases, archives, backup artifacts, and virtual disks.
· Cross-platform scope across Windows, Linux, and ESXi increases exposure beyond ordinary endpoint ransomware.
· ESXi and virtualization-adjacent impact can amplify disruption across many dependent systems.
· Backup, snapshot, vault, recovery-point, retention-policy, or restore-job tampering can materially reduce recoverability.
· Shared drives, mapped drives, file servers, NAS paths, operational repositories, and database storage can allow one compromised system to affect broader enterprise data.
· Incomplete endpoint process telemetry can prevent responders from identifying the initiating process behind file transformation.
· Missing file telemetry or file-size fields can delay recognition of destructive activity and limit prioritization around the reported destructive threshold.
· Missing ESXi, vCenter, datastore, or virtualization-management telemetry can delay detection until downstream systems fail.
· Missing backup-platform telemetry can create false confidence in recovery readiness.
· Missing SIEM normalization can fragment suspicious execution, file modification, backup tampering, and virtualization impact into isolated low-confidence events.
· Over-reliance on file extensions, ransom-note names, hashes, YARA hits, or network indicators can miss behavior changes and delay detection of destructive activity.
S8 — Bottom Line for Executives
VECT ransomware-wiper activity should be treated as a high-priority destructive operational risk because it can convert ransomware execution into permanent data loss. The key executive concern is not only whether systems were encrypted, but whether critical files, databases, virtual disks, backup artifacts, or shared repositories were transformed in a way that prevents reliable recovery. Risk reduction depends on rapid detection of mass file transformation, immediate containment of affected systems, validation of backup and recovery controls, review of ESXi and virtualization infrastructure, and confirmation that endpoint, file, backup, virtualization, cloud, and SIEM telemetry can support scoping. Organizations should prioritize this report as a resilience and business-continuity issue because destructive file loss can create operational disruption, recovery uncertainty, customer assurance pressure, compliance exposure, and board-level incident governance requirements.
S9 — Board-Level Takeaway
VECT turns ransomware from a recoverability challenge into a destructive data-loss and operational-resilience problem. The board-level risk is that attackers may damage files, impair recovery paths, and disrupt virtualized infrastructure before the organization can determine scope or restore services with confidence. Leadership should require evidence that high-value repositories, backups, virtual infrastructure, cloud recovery assets, and endpoint telemetry have been validated against destructive file transformation risk. This report supports governance decisions around ransomware resilience, immutable backup strategy, virtualization protection, recovery assurance, telemetry readiness, incident response maturity, and executive oversight of destructive malware exposure.
Figure 2
S10 — Threat Overview
VECT is a ransomware-as-a-service operation whose current VECT 2.0 implementation creates destructive wiper-like outcomes rather than reliable recoverable encryption. The operation is marketed as ransomware, but current technical reporting indicates that its encryption implementation can permanently destroy files larger than 131,072 bytes across Windows, Linux, and VMware ESXi variants.
The enterprise risk is severe because the affected file-size threshold is low enough to include ordinary business documents, spreadsheets, archives, databases, virtual disks, backup artifacts, and operational repositories. In practical terms, VECT should not be treated as a standard ransomware event where recovery depends primarily on decryptor availability, ransom negotiation, or restoration from ordinary recovery paths.
VECT should be assessed as ransomware by operator intent and destructive malware by operational effect. The business impact includes unrecoverable data loss, backup assurance failure, virtualization disruption, file-integrity uncertainty, incident scoping difficulty, and executive uncertainty around whether affected systems can be restored with confidence.
S11 — Threat Classification and Type
Threat Type
Ransomware-wiper.
Threat Sub-Type
Cross-platform ransomware-as-a-service with destructive encryption failure affecting Windows, Linux, and VMware ESXi variants.
Operational Classification
Destructive extortion malware with ransomware branding, affiliate distribution, and wiper-like file-loss consequences.
Primary Function
The primary function is file transformation for extortion. The primary operational effect is destructive file loss for files above the reported 131,072-byte threshold because required decryption material is not preserved for full recovery.
S12 — Campaign or Activity Overview
VECT publicly emerged as a ransomware-as-a-service operation in late 2025 and continued to develop into VECT 2.0 with Windows, Linux, and VMware ESXi variants. The current version presents as an extortion operation, but the implementation flaw changes the operational effect from recoverable encryption to destructive file loss for many enterprise file types.
The campaign model should be treated as opportunistic and affiliate-driven rather than narrowly sector-specific. VECT’s cross-platform payload support, ransomware-as-a-service positioning, and supply-chain-adjacent reporting create concern for organizations with exposed developer ecosystems, enterprise servers, virtualization infrastructure, shared storage, backup systems, and operationally critical repositories.
TeamPCP and supply-chain adjacency should be treated as contextual risk factors, not as proof that every VECT event originates from a supply-chain compromise. The key enterprise concern is whether VECT execution or VECT-like activity can reach high-value files, shared repositories, backups, databases, or virtualization assets before containment occurs.
S13 — Targets and Exposure Surface
VECT’s exposure surface includes Windows endpoints, Linux servers, VMware ESXi environments, file servers, shared repositories, mapped drives, backup-accessible systems, databases, archives, and virtual disks. The risk is elevated wherever a compromised host can modify large volumes of business-critical files or reach virtualization and recovery infrastructure.
High-value exposure surfaces include:
· Windows endpoints and servers with access to shared storage.
· Linux servers hosting operational data, repositories, databases, or application files.
· VMware ESXi hosts, vCenter-managed environments, datastores, snapshots, and virtual disks.
· Backup servers, backup staging paths, recovery vaults, snapshot systems, and restore-management platforms.
· Administrative workstations and jump hosts with privileged access to file servers, backup platforms, and virtualization infrastructure.
· Cloud-hosted workloads where endpoint telemetry is available and cloud backup or snapshot controls support recovery.
· Developer, CI/CD, or package-consumer environments potentially exposed through supply-chain-linked delivery paths.
The decisive enterprise risk condition is not the presence of VECT artifacts alone. The decisive risk condition is whether suspicious execution can modify files across high-value repositories, impair recovery paths, or affect virtualization assets before containment occurs.
S14 — Sectors / Countries Affected
Sectors Affected
Current public reporting does not support a narrow confirmed sector-only victimology profile for VECT 2.0. Sector exposure should therefore be assessed by operational dependency, virtualization footprint, backup architecture, file-repository criticality, and exposure to affiliate or supply-chain-linked delivery paths.
Most exposed sectors include:
· Technology and software development.
· Cloud services and SaaS providers.
· Managed service providers and IT service providers.
· Financial services.
· Healthcare and life sciences.
· Manufacturing and industrial operations.
· Energy and utilities.
· Telecommunications.
· Government and public-sector organizations.
· Education and research institutions.
· Professional services and legal organizations.
· Enterprises with material VMware ESXi, file-server, database, or backup dependency.
The sector list above is an exposure-based assessment, not a confirmed victim list.
Countries Affected
Current public reporting does not support a fixed country-specific victim list for VECT 2.0. The exposure model should be treated as global because ransomware-as-a-service affiliate distribution, supply-chain adjacency, cloud-hosted workloads, and VMware ESXi deployment patterns are not geographically constrained.
Country exposure is most likely where organizations operate:
· Enterprise Windows, Linux, and VMware ESXi infrastructure.
· Shared storage, file servers, databases, and backup-dependent recovery models.
· Software supply-chain or developer environments exposed to affiliate delivery paths.
· Cross-border operations with centralized infrastructure or shared recovery platforms.
VECT’s criminal-market presence is relevant to actor ecosystem assessment, but it should not be treated as reliable evidence of a specific victim geography without additional incident-level reporting.
S15 — Adversary Capability Profiling
Capability Level
Moderate to High.
VECT demonstrates operational ambition through ransomware-as-a-service positioning, affiliate recruitment, cross-platform payload support, and enterprise-relevant ESXi targeting. Capability is not assessed as fully mature because current technical reporting identifies major encryption and software-design failures that undermine the operator’s claimed ransomware capability.
Technical Sophistication
Moderate.
The operation can produce Windows, Linux, and ESXi variants and target enterprise-relevant infrastructure. Technical sophistication is constrained by the flawed encryption implementation, which causes large-file destruction rather than reliable recovery, and by additional implementation weaknesses reported in current technical analysis.
Infrastructure Maturity
Moderate.
VECT has ransomware-as-a-service infrastructure, affiliate-facing operations, and public criminal-market positioning. Infrastructure maturity is not assessed as high because current reporting emphasizes operational ambition and affiliate expansion more than proven long-term intrusion infrastructure, mature tooling reliability, or consistent enterprise execution at scale.
Operational Scale
Moderate to High.
The operation’s scale could expand through affiliate recruitment, cross-platform tooling, criminal-market visibility, and supply-chain-adjacent delivery opportunities. The scale assessment remains conditional because distribution potential does not equal broad confirmed enterprise compromise.
Escalation Likelihood
High.
Escalation likelihood is high because VECT’s destructive behavior can rapidly move from a single compromised host to shared storage, backup-accessible systems, databases, virtual disks, or ESXi-managed infrastructure. Escalation risk remains high if the actor corrects the encryption flaw while preserving the same affiliate distribution model, cross-platform payload support, and extortion workflow.
S16 — Targeting Probability Assessment
Overall Targeting Probability
High for organizations with Windows, Linux, VMware ESXi, shared-storage, backup-dependent, or supply-chain-exposed environments.
Moderate for organizations with limited shared storage, limited virtualization dependency, strong backup isolation, mature endpoint telemetry, and rapid containment capability.
Low only where exposure is materially reduced by limited attack surface, strong segmentation, immutable offline backups, limited privileged write access, and validated behavior-based detection.
Targeting Drivers
· Affiliate-driven ransomware-as-a-service distribution increases opportunistic targeting probability.
· Supply-chain-adjacent reporting increases concern for downstream exposure through compromised software ecosystems.
· ESXi support increases risk for enterprises with virtualization-heavy infrastructure.
· Cross-platform Windows, Linux, and ESXi variants increase deployment flexibility.
· Shared storage and mapped-drive access increase destructive blast radius.
· Backup-accessible systems increase impact if restore paths are impaired.
· Databases, virtual disks, archives, and backup artifacts are high-value files above the destructive threshold.
· Incomplete endpoint, file, backup, ESXi, and SIEM telemetry increases attacker dwell and scoping uncertainty.
· Organizations that treat VECT as ordinary ransomware may under-prioritize immutable recovery validation and rapid containment.
Most Likely Targets
· Enterprises using VMware ESXi or virtualization-managed infrastructure.
· Organizations with large file repositories, file servers, NAS, or shared drives.
· Organizations with databases, archives, mail stores, virtual disks, or backup artifacts accessible from compromised systems.
· Backup-dependent environments with weak recovery-control monitoring.
· Technology, SaaS, and software development organizations exposed to supply-chain-linked delivery paths.
· Managed service providers, IT service providers, and organizations with broad administrative access paths.
· Regulated or operationally sensitive organizations where downtime and data loss create high extortion leverage.
· Cloud-hosted enterprises where workload endpoint compromise can combine with cloud backup, snapshot, storage, or recovery-control tampering.
S17 — MITRE ATT&CK Chain Flow Mapping
Stage 1 — Initial Access and Delivery
VECT’s initial access should be assessed as affiliate-dependent and opportunistic, with supply-chain-linked delivery treated as a contextual possibility rather than a universal pathway. The report does not require a single assumed initial-access method because VECT’s primary risk is the destructive behavior that follows execution on systems with access to high-value files or recovery assets.
· ATT&CK mapping: Supply Chain Compromise T1195.
· ATT&CK mapping: Valid Accounts T1078.
· Confidence: Conditional. Supply-chain adjacency and credential-enabled access are relevant risk paths, but incident-specific access method must be validated per environment.
Stage 2 — Execution
Once access is established, execution may occur on Windows endpoints, Linux systems, administrative hosts, servers, or ESXi-adjacent systems. The operational concern is not the initial binary name, extension, or staging artifact, but whether execution occurs from a context that can reach shared repositories, databases, virtual disks, backup paths, or recovery controls.
· ATT&CK mapping: Command and Scripting Interpreter T1059.
· Confidence: Conditional. Script or shell execution is a realistic execution pathway, but this report does not assume it is required for every VECT deployment.
Stage 3 — Privileged Context and Access Expansion
VECT impact increases when the executing user, host, or process context can write to shared storage, modify backups, affect recovery assets, or reach virtualization infrastructure. Privileged access is therefore an impact amplifier even when the initial compromise begins on a single system.
· ATT&CK mapping: Valid Accounts T1078.
· Confidence: Conditional to likely. Privileged or reusable access materially increases blast radius, but is not required for limited local file impact.
Stage 4 — Discovery and Target Selection
Before destructive impact, ransomware activity must identify reachable files, directories, shares, repositories, databases, archives, virtual disks, or backup-adjacent paths. For VECT, discovery and target selection are especially important because the destructive threshold is low enough to affect ordinary enterprise files and high-value operational assets.
· ATT&CK mapping: File and Directory Discovery T1083.
· ATT&CK mapping: Network Share Discovery T1135.
· ATT&CK mapping: System Information Discovery T1082.
· Confidence: Likely. Destructive file transformation requires reachable file and path selection.
Stage 5 — Recovery Suppression and Control Interference
VECT-aligned activity becomes more severe when endpoint protections, logs, backups, snapshots, vaults, restore points, or virtualization controls are impaired before or during file transformation. Recovery suppression materially changes the incident from contained malware activity to destructive operational loss.
· ATT&CK mapping: Inhibit System Recovery T1490.
· ATT&CK mapping: Impair Defenses T1562.
· ATT&CK mapping: Service Stop T1489.
· Confidence: Conditional to likely. Recovery-path interference is a high-priority risk amplifier, but should be confirmed through endpoint, backup, virtualization, or SIEM telemetry.
Stage 6 — Expansion Through Shared or Administrative Paths
Enterprise-scale impact can occur through mapped drives, administrative shares, remote services, file-server access, backup-accessible hosts, or virtualization administration paths. Broad host-to-host movement is not required for severe impact if one compromised system has privileged write access to shared or virtualized infrastructure.
· ATT&CK mapping: Remote Services T1021.
· ATT&CK mapping: SMB/Windows Admin Shares T1021.002.
· Confidence: Conditional. These paths are relevant where shared storage, administrative access, or remote management surfaces are present.
Stage 7 — Extortion Context and Conditional Data Exposure
VECT operates in an extortion context, but exfiltration should not be assumed without supporting telemetry. Data staging, unusual outbound transfer, leak-site activity, or suspicious external communication should be treated as escalation signals when observed, not as required conditions for detecting destructive VECT activity.
· ATT&CK mapping: Data Staged T1074.
· Confidence: Conditional. Extortion posture creates data-exposure concern, but this report does not assume exfiltration without evidence.
Stage 8 — Impact: Destructive File Transformation
The core impact stage is ransomware-like file transformation that becomes destructive for files larger than 131,072 bytes. This can damage business documents, databases, archives, backup artifacts, virtual disks, shared repositories, and operational data stores, creating recovery uncertainty even when ransom payment or decryptor access is available.
· ATT&CK mapping: Data Encrypted for Impact T1486.
· ATT&CK mapping: Data Destruction T1485.
· ATT&CK mapping: Inhibit System Recovery T1490.
· Confidence: High. This is the primary VECT behavior and the governing risk condition for the report.
Stage 9 — Business Disruption and Recovery Uncertainty
The final operational outcome is not simply encrypted files. The final outcome is uncertainty over restoration, file integrity, backup trust, virtualization recoverability, and continuity of business services. This stage is most severe when destructive file transformation overlaps with backup impairment, ESXi impact, database damage, regulated data stores, customer-facing services, or incomplete telemetry.
· ATT&CK mapping: Data Encrypted for Impact T1486.
· ATT&CK mapping: Data Destruction T1485.
· Confidence: High where destructive file transformation affects high-value repositories, backups, databases, or virtualization infrastructure.
S18 — Attack Path Narrative (Signal-Aligned Execution Flow)
VECT activity should be analyzed as a destructive ransomware-wiper execution path rather than a conventional ransomware chain. The defining risk is not merely that files are encrypted, but that file transformation can permanently destroy recoverable content once the malware reaches ordinary enterprise files, shared repositories, databases, archives, virtual disks, or backup artifacts.
The attack path begins with affiliate-dependent access or delivery into an environment where attacker-controlled execution can occur. Supply-chain-linked delivery, credential-enabled access, or other affiliate tradecraft may provide the initial path, but the governing risk begins when execution reaches a system with meaningful file access, privileged context, shared-storage reach, backup visibility, or virtualization-adjacent control.
After execution, the threat becomes materially dangerous when the process context can enumerate and modify files across local disks, mapped drives, shared repositories, Linux paths, or virtualization-accessible storage. At this stage, high-confidence signals include suspicious process execution, unusual file enumeration, rapid file opening, high-volume rewrite behavior, rename activity, extension changes, and file modification affecting operationally meaningful file types or file sizes.
Risk escalates when VECT-like activity overlaps with recovery-path interference. Backup deletion, snapshot removal, vault-policy modification, restore-point tampering, event-log clearing, service stopping, or endpoint-control impairment can materially reduce the organization’s ability to restore affected systems. This activity should be treated as an impact amplifier, not a secondary detail, because destructive file transformation becomes far more severe when recovery paths are degraded before or during the attack.
Risk escalates further when activity reaches VMware ESXi, vCenter-managed environments, datastores, virtual disks, VM snapshots, backup staging paths, or administrative jump hosts. Virtualization exposure can turn a single host or privileged account compromise into multi-system disruption because virtual disks and datastore-backed workloads may represent many dependent business services.
The core impact phase is destructive file transformation. VECT’s ransomware-like behavior can modify files in a way that prevents reliable recovery for files above the reported 131,072-byte threshold. This stage should be detected through behavior combinations rather than static indicators: suspicious execution with high-volume file modification, file transformation with ransom-note staging, file rewrite activity with backup tampering, or virtualization-adjacent modification with anomalous administrative context.
Ransom-note staging and extortion positioning may appear during or after file impact, but ransom-note artifacts should not be treated as the primary detection foundation. Ransom notes become meaningful when they appear near mass file modification, suspicious execution, shared-storage impact, backup tampering, or virtualization disruption.
The final operational outcome is recovery uncertainty. Affected organizations may need to determine whether files were merely encrypted, permanently corrupted, partially recoverable, restored from trusted backup, or still exposed through shared repositories and virtualized infrastructure. The response priority is containment, backup protection, ESXi and virtualization review, affected-file scoping, recovery validation, and preservation of telemetry needed to reconstruct the destructive window.
S19 — Attack Chain Risk Amplification Summary
VECT risk amplifies when execution moves from an isolated endpoint into systems with broad write access, backup reach, privileged administrative context, or virtualization control. The most severe outcomes occur when destructive file transformation intersects with recovery-path degradation or ESXi-adjacent infrastructure.
Primary risk amplification factors include:
· File transformation affects ordinary enterprise files above the reported 131,072-byte threshold.
· A compromised endpoint has mapped-drive, shared-storage, file-server, NAS, or repository access.
· A compromised server can modify databases, archives, mail stores, backup artifacts, or operational data stores.
· The executing process can access virtual disks, datastores, VM snapshots, or virtualization management paths.
· Backup, snapshot, vault, recovery-point, retention-policy, or restore-job controls are modified before or during file transformation.
· Endpoint telemetry cannot reliably identify the initiating process, user, command line, parent process, affected path, or file scope.
· File telemetry lacks file-size, rename, modification, delete, initiating-process, or host-role context.
· ESXi, vCenter, datastore, or virtualization-management logs are missing, incomplete, or not correlated into the SIEM.
· Backup-platform telemetry is unavailable, creating false confidence in recovery readiness.
· Cloud-control telemetry exists without workload endpoint telemetry, limiting visibility into local encryption or destructive file transformation.
· Ransom-note, extension, hash, or YARA-only logic is treated as sufficient detection, delaying recognition of active destructive behavior.
· Incident response treats VECT as ordinary ransomware instead of prioritizing irreversible file loss, immutable backup validation, and virtualization recovery assurance.
The most important amplification pattern is the convergence of destructive file modification, recovery-path interference, and high-value infrastructure exposure. When these conditions overlap, the business outcome can shift from contained malware response to enterprise restoration, service continuity disruption, legal review, customer assurance, and board-level incident governance.
Figure 3
S20 — Tactics, Techniques, and Procedures
Initial Access and Delivery
· VECT access should be assessed as affiliate-dependent rather than tied to one universal delivery path.
· Supply-chain-linked exposure remains a contextual pathway where affected ecosystems, developer environments, or downstream software dependencies create execution opportunity.
· Credential-enabled access remains a conditional pathway when stolen, reused, or exposed accounts allow access to systems with file, backup, or virtualization reach.
· This report does not assume phishing, external remote services, exploitation, or service-based execution without incident-specific evidence.
Execution
· VECT execution may occur on Windows endpoints, Linux servers, administrative hosts, or ESXi-adjacent systems.
· Execution risk is highest when the process context can reach shared repositories, mapped drives, databases, virtual disks, backup paths, or recovery controls.
· Suspicious execution should be prioritized when it originates from user-writable paths, temporary locations, staging directories, administrative shares, recently created folders, or unusual shell and script contexts.
· Static binary names, extensions, ransom-note names, and hashes should support triage only; they should not govern detection.
Discovery and File Targeting
· VECT-aligned activity requires identifying reachable files, directories, shares, repositories, archives, databases, virtual disks, or backup-adjacent paths.
· File and directory discovery is operationally important because destructive impact depends on which repositories and file types are reachable from the compromised context.
· Network share discovery is especially relevant where mapped drives, SMB shares, NAS paths, or shared repositories allow one system to affect broader enterprise data.
· Discovery signals should be prioritized when followed by high-volume file modification, rename activity, extension changes, or ransom-note staging.
Recovery Suppression and Defensive Interference
· Backup deletion, snapshot removal, restore-point tampering, vault-policy modification, retention-policy changes, event-log clearing, service stopping, and endpoint-control interference should be treated as high-priority impact amplifiers.
· Recovery suppression does not need to occur in every VECT event to be important; when present, it materially changes the recovery posture.
· Defensive interference should be assessed through endpoint, backup-platform, virtualization, identity, cloud-control, and SIEM telemetry where available.
· Legitimate backup administration and maintenance activity must be distinguished through user, host, timing, process, asset role, and approved workflow context.
Expansion Through Shared or Administrative Paths
· VECT can create enterprise-scale impact without broad host-to-host movement if the executing system already has write access to shared storage, file servers, backup paths, or virtualization infrastructure.
· Remote services, administrative shares, privileged accounts, management hosts, and jump systems should be treated as expansion paths when they increase access to high-value files or recovery assets.
· Expansion risk is highest when the same user, process, host, or service account touches multiple repositories, shares, servers, virtual disks, or backup-controlled resources in a short period.
· Lateral movement should be treated as a scope and severity signal, not as a required dependency for detecting active destructive file behavior.
Extortion and Conditional Data Exposure
· VECT operates in an extortion context, but data theft should not be assumed without supporting telemetry.
· Data staging, suspicious outbound transfer, unusual external communication, leak-site evidence, or abnormal access to repositories should increase severity when observed.
· Network and outbound communication signals should support investigation and enrichment, not replace endpoint and file-impact evidence.
· Data-exposure analysis should remain separate from the primary destructive-file-impact model unless telemetry confirms staging, transfer, or unauthorized access.
Impact
· The primary impact behavior is ransomware-like file transformation with wiper-like consequences.
· Files larger than the reported 131,072-byte threshold are the most important operational concern because the current implementation can render them unrecoverable.
· High-value impacted file types include documents, spreadsheets, archives, databases, virtual disks, backup artifacts, mail stores, and operational repositories.
· Impact severity increases when destructive file transformation overlaps with backup tampering, ESXi or datastore impact, privileged execution, shared-storage access, multi-host activity, or incomplete telemetry.
· The operational response must assume recovery uncertainty until backup integrity, file integrity, virtualization state, and affected-file scope are validated.
S20A — Adversary Tradecraft Summary
VECT tradecraft is best understood as an unstable but dangerous ransomware-as-a-service capability whose operational effect can exceed ordinary ransomware because flawed encryption creates destructive file loss. The actor ecosystem shows enough operational ambition to support affiliate distribution, cross-platform payloads, and enterprise-relevant targeting, but the current implementation quality creates wiper-like consequences that may be unintended by the operator.
The most important tradecraft feature is behavior, not branding. VECT should be detected and triaged through mass file transformation, suspicious execution context, recovery-path interference, virtualization-adjacent activity, and affected-file scope. Static indicators may support classification, but they are not durable enough to serve as the primary enterprise detection model.
VECT’s cross-platform support increases defensive complexity because Windows, Linux, and ESXi environments require different telemetry paths and response workflows. A Windows-only ransomware model is insufficient where Linux servers, ESXi hosts, datastores, virtual disks, or backup repositories are part of the enterprise operating environment.
The tradecraft risk increases when VECT execution reaches privileged systems, shared storage, backup-accessible hosts, administrative jump boxes, or virtualization management surfaces. In those conditions, destructive file transformation can expand beyond local endpoint damage and create multi-system restoration, business-continuity, and recovery-assurance pressure.
The tradecraft should be treated as high-risk even if the actor corrects the current encryption flaw. If future VECT versions become reliably decryptable, the same affiliate model, cross-platform payload scope, extortion posture, shared-storage access, recovery-path tampering, and ESXi targeting would still support significant ransomware impact. Current defensive planning should therefore focus on durable ransomware-wiper behaviors rather than the specific implementation defect alone.
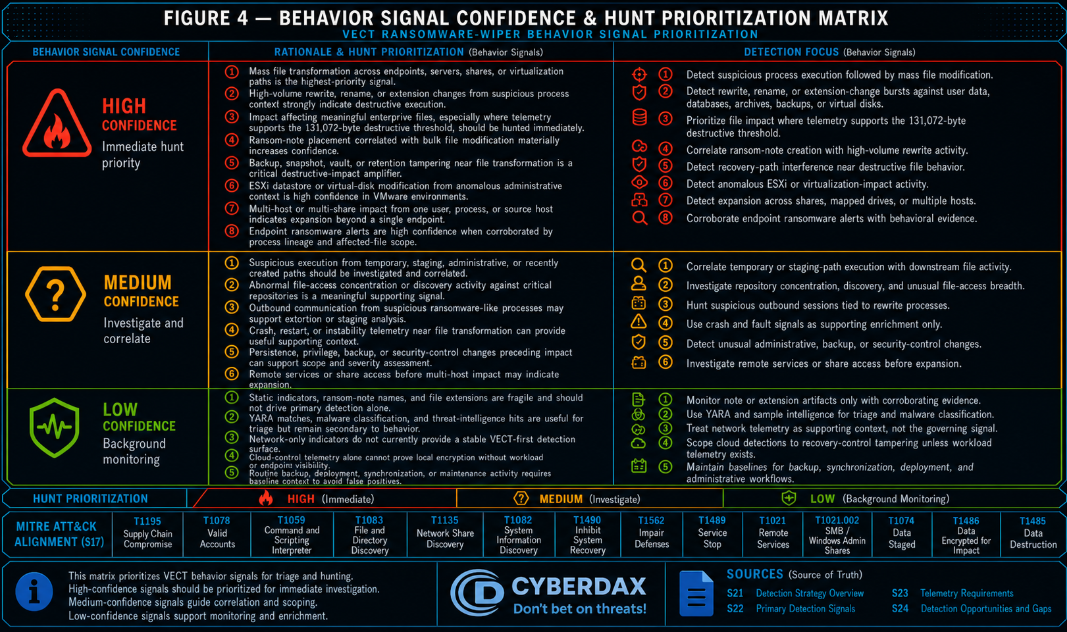
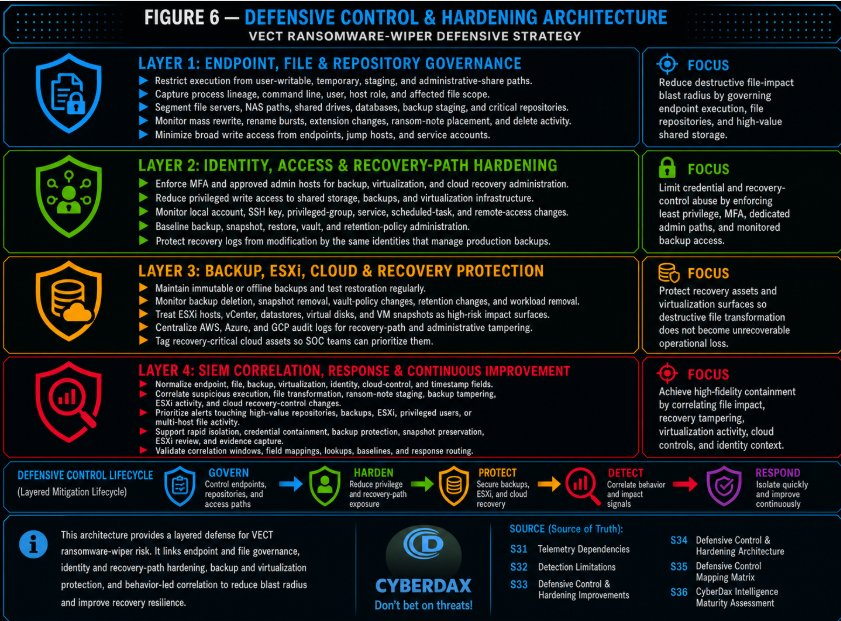
S21 — Detection Strategy Overview
Detection Philosophy
· Detection for the VECT ransomware-wiper threat must prioritize destructive operational behavior over static malware identity because the primary business risk is irreversible data loss caused by failed encryption logic.
· The detection strategy must treat VECT as a destructive ransomware condition in which encryption activity, file rewrite behavior, ransom-note staging, and recovery-path interference are analyzed as a combined operational risk pattern.
· The primary detection objective is early identification of ransomware-wiper execution before broad file transformation reaches business-critical data stores, virtualization assets, backups, databases, shared storage, and endpoint-accessible repositories.
· VECT must not be handled as ordinary recoverable ransomware because current reporting indicates VECT 2.0 can permanently destroy files larger than 131,072 bytes across Windows, Linux, and ESXi variants, making recovery impossible even for the attacker in affected cases.
· Detection must be behavior-led, telemetry-grounded, and resilient to VECT version changes because the actor may correct the current encryption flaw while retaining the same cross-platform ransomware operating model.
· VECT-specific indicators may support triage, enrichment, and malware classification, but they must not become the primary detection foundation unless the artifacts are validated, stable, and sample-derived.
Primary Detection Anchors
· Bulk file transformation activity is the highest-priority detection anchor because VECT’s damaging behavior occurs through large-scale file modification rather than through a reliably recoverable encryption workflow.
· Ransom-note staging correlated with mass file modification is a strong supporting anchor because ransom-note creation alone is weak, but ransom-note placement during high-volume file rewrite activity indicates active extortion-stage execution.
· Suspicious file rewrite activity affecting operationally meaningful file sizes is a required anchor because VECT’s destructive flaw affects files above a low practical threshold, exposing ordinary documents, databases, archives, virtual disks, and backup artifacts.
· Virtualization and ESXi-adjacent impact behavior is a required anchor because VECT includes ESXi targeting, and damage to virtual machine disks or datastores can rapidly escalate from host compromise to enterprise-scale operational disruption.
· Backup, snapshot, and recovery-control interference is a required anchor because destructive ransomware risk increases sharply when attackers modify, delete, disable, or impair recovery paths before or during file transformation.
· Cross-platform execution context is a required anchor because Windows, Linux, and ESXi variants require the detection model to avoid Windows-only assumptions and to include Linux process telemetry, hypervisor administration signals, and SIEM-level correlation where available.
Detection Prioritization Model
· Highest-priority detections must identify active destructive file transformation where suspicious execution, high-volume writes, extension changes, ransom-note placement, or recovery-path interference occur in close temporal proximity.
· High-priority detections must cover ESXi and virtualization-impact activity because compromise of virtual infrastructure can create immediate multi-system business interruption.
· High-priority detections must cover backup and recovery-control tampering because recovery-path degradation materially changes the business outcome from contained ransomware to destructive operational loss.
· Medium-priority detections may include portable SIGMA-style process and file behaviors when telemetry quality supports reliable backend implementation.
· Conditional-priority detections may include YARA-based VECT classification only when derived from validated sample artifacts, malware repository intelligence, or stable extracted strings.
· Low-priority detections must be excluded when they rely only on generic ransomware keywords, isolated ransom-note names, unvalidated file extensions, unsourced network indicators, or single-event file-write volume without behavioral context.
Correlation Strategy (Strict Enforcement)
· Correlation must combine independent telemetry signals into a single behavior conclusion without requiring another CyberDax detection rule to fire first.
· Correlation logic must use raw or normalized telemetry inputs such as process execution, file creation, file modification, rename operations, command-line activity, endpoint alerts, backup control events, ESXi administration logs, cloud audit logs, and file integrity signals.
· Correlation must not depend on alert-to-alert chaining, inherited confidence from another rule, or downstream triage labels.
· Correlation windows must be defined around ransomware execution tempo and tuned to distinguish legitimate high-volume administrative activity from destructive file transformation.
· Correlation must prioritize high-confidence combinations such as suspicious process execution with mass file modification, mass file modification with ransom-note staging, backup deletion with suspicious execution, and ESXi datastore impact with anomalous administrative command activity.
· Correlation must preserve standalone rule validity, meaning each rule must remain explainable as telemetry-to-logic-to-output without relying on another rule’s conclusion.
Telemetry Prioritization
· Endpoint and EDR telemetry must be prioritized first because the most direct VECT detection surface is process execution, file rewrite behavior, ransom-note creation, and local destructive activity.
· File telemetry must be prioritized where available because bulk file modification, extension changes, rename bursts, and high-volume writes provide the strongest operational signal for ransomware-wiper activity.
· ESXi, hypervisor, and virtualization administration telemetry must be prioritized for environments running VMware infrastructure because VECT includes ESXi targeting and can affect virtualized operational assets.
· Backup platform telemetry must be prioritized because backup deletion, snapshot tampering, retention-policy changes, recovery-job modification, and vault access changes directly affect recoverability.
· SIEM correlation telemetry must be used to join endpoint, backup, virtualization, identity, and cloud-control events where single telemetry sources cannot provide sufficient context.
· Network telemetry must be treated as supporting telemetry only unless validated VECT C2, staging, exfiltration, or delivery indicators become available.
· Cloud-control telemetry must be used conditionally for AWS, Azure, and GCP recovery-path tampering, not as direct evidence of local VECT encryption unless endpoint telemetry from cloud workloads is available.
Detection Design Constraints
· Detections must be specific enough to avoid generic high-file-activity alerts that would trigger on backup jobs, software deployment, indexing, data migration, antivirus scanning, or legitimate administrative maintenance.
· Detections must include environment-specific baselines for expected file-write volume, backup administration, ESXi maintenance, endpoint software deployment, and data-processing workloads.
· Detections must distinguish destructive ransomware patterns from legitimate encryption tools, backup operations, compression utilities, synchronization clients, and enterprise data-management workflows.
· Detections must not overfit to the current VECT implementation flaw because the actor may correct the nonce-handling defect while retaining ransomware execution, extortion, and cross-platform targeting.
· Detections must not assume ransom-note artifacts alone are sufficient for high-confidence detection.
· Detections must not assume Windows-only telemetry because VECT affects Windows, Linux, and ESXi environments.
· Detections must not rely on attacker decryptor availability, ransom payment behavior, or post-incident recovery outcomes as detection inputs.
· Detections must not expose proprietary CyberDax scoring methodology, candidate rejection mechanics, rule-selection internals, or customer-specific tuning architecture in public-facing report content.
Baseline and Deployment Requirements
· Organizations must establish normal file-write, rename, delete, and extension-change baselines for endpoints, servers, shared drives, virtualization hosts, and backup-accessible systems.
· Organizations must identify high-value file repositories, operational databases, virtual machine disk locations, backup staging paths, and file shares where mass transformation should be treated as high severity.
· Organizations must baseline legitimate backup, snapshot, restore, retention-policy, and vault-administration behavior before deploying backup-tampering detections.
· Organizations must baseline ESXi administrative commands, datastore access patterns, VM power operations, snapshot activity, and authorized maintenance windows before deploying virtualization-impact detections.
· Organizations must ensure endpoint telemetry includes process lineage, command line, file modification activity, user context, host role, parent process, and executable path where available.
· Organizations must ensure SIEM normalization preserves process, file, host, user, timestamp, platform, and recovery-control fields needed for cross-source correlation.
· Organizations must define allowlists for approved backup agents, encryption utilities, administrative scripts, deployment tools, and data migration processes, but allowlists must be narrow, reviewed, and time-bound.
· Organizations must maintain immutable, offline, or logically isolated backup validation because detection alone does not restore data after destructive file transformation.
Variant Resilience Requirements
· Detections must remain effective if VECT changes file extension, ransom-note name, binary filename, mutex, packing method, obfuscation, infrastructure, or affiliate delivery path.
· Detections must remain effective if VECT corrects the current nonce-handling flaw and becomes recoverable ransomware rather than accidental wiper malware.
· Detections must remain effective across Windows, Linux, and ESXi execution paths by focusing on observable destructive behaviors rather than platform-specific filenames alone.
· Detections must account for attackers suppressing obvious child processes, using renamed binaries, staging from temporary directories, executing from user-writable paths, or launching through legitimate administrative tools.
· Detections must account for delayed ransom-note placement, partial encryption, selective file targeting, backup-first tampering, and virtualization-first impact sequencing.
· Detections must treat sample-derived YARA or IOC logic as supplemental classification, not as a substitute for behavioral coverage.
· Detections must preserve sensitivity to destructive outcomes while avoiding broad logic that would make routine administrative activity indistinguishable from ransomware execution.
Operational Detection Model
· Tier 1 SOC workflows should prioritize alerts involving active mass file transformation, backup tampering, ESXi impact, or ransom-note staging because these signals indicate immediate containment urgency.
· Tier 2 workflows should validate execution context, affected asset role, user legitimacy, file scope, host criticality, backup status, and whether activity is spreading across shared or virtualized infrastructure.
· Incident response workflows should prioritize host isolation, credential containment, backup protection, ESXi administrative review, snapshot preservation, and evidence capture before destructive activity expands.
· Threat hunting should focus on suspicious file rewrite bursts, unusual encryption utility behavior, anomalous access to backup or virtualization systems, and ransomware-note artifacts appearing near high-volume file changes.
· Malware analysis workflows may use VECT-specific YARA or sample-classification logic only where artifacts are validated and documented.
· Detection outputs must clearly distinguish active destructive behavior, suspected pre-impact staging, recovery-path tampering, and post-impact artifact discovery.
· Alerts must include enough context for responders to determine whether the activity is local endpoint ransomware, server-side file destruction, ESXi-impact activity, backup-control tampering, or cloud recovery-path interference.
Explicit Non-Deployment Guardrails
· Do not deploy a Suricata rule for VECT unless validated network indicators, protocol traits, payload signatures, delivery infrastructure, or C2 patterns are confirmed.
· Do not deploy a YARA rule as a primary enterprise detection control unless it is based on validated VECT samples and stable sample-derived artifacts.
· Do not deploy rules that trigger on .vect alone because extension-only logic is fragile and easily changed.
· Do not deploy rules that trigger on ransom-note names alone because ransom-note artifacts are insufficient without execution or file-transformation context.
· Do not deploy cloud-control rules that claim to detect local VECT encryption directly from AWS, Azure, or GCP audit logs.
· Do not deploy generic high-file-change rules without baseline controls, host-role context, allowlist governance, and ransomware-specific correlation.
· Do not deploy any rule that depends on another CyberDax rule firing first.
· Do not deploy any rule that requires customer-specific paths, asset labels, backup product names, ESXi host lists, or privileged account inventories without documenting those implementation inputs.
· Do not deploy detections that treat ransom payment, decryptor failure, or recovery outcome as detection logic.
S22 — Primary Detection Signals
Primary Detection Signals
· Mass file transformation across endpoint, server, shared-storage, or virtualization-accessible paths is the highest-priority detection signal because VECT’s operational impact occurs through destructive file modification rather than a reliably recoverable ransomware workflow.
· High-volume file rewrite, rename, or extension-change activity from a suspicious process context is a primary signal when the activity affects user data, databases, archives, virtual disks, backups, or operational repositories.
· File modification involving files larger than 131,072 bytes is a priority signal because current technical reporting indicates VECT’s destructive flaw affects files above that threshold, making many ordinary enterprise files unrecoverable after encryption.
· Ransom-note creation correlated with bulk file modification is a primary signal when ransom-note placement occurs near high-volume file rewrite activity, extension changes, or suspicious process execution.
· Suspicious execution from user-writable, temporary, staging, administrative, or recently created paths followed by file transformation is a primary signal because ransomware execution commonly begins from locations outside normal software deployment patterns.
· Rapid enumeration, opening, rewriting, renaming, or deletion of large file sets by a single process is a primary signal when the activity is inconsistent with the host role, user role, or normal workload.
· ESXi datastore, virtual machine disk, or hypervisor-adjacent file modification activity is a primary signal in VMware environments because VECT is reported across Windows, Linux, and ESXi variants, and virtual infrastructure impact can rapidly amplify business disruption.
· Backup, snapshot, vault, recovery-point, or retention-policy tampering near suspicious file transformation activity is a primary signal because destructive ransomware outcomes become materially worse when recovery paths are impaired before or during encryption.
· Endpoint or EDR behavioral alerts indicating ransomware-like encryption, file tampering, or destructive write behavior are primary signals when supported by process lineage, file-scope evidence, or affected asset criticality.
· Cross-platform ransomware execution indicators across Windows, Linux, and ESXi assets are primary signals because detection must not rely on Windows-only execution assumptions.
Supporting Detection Signals
· Creation of files with VECT-associated extensions or ransom-note artifacts may support detection when correlated with execution, file transformation, or host impact evidence.
· Known or suspected VECT sample classification from malware-analysis tooling may support triage when derived from validated YARA, sandbox, malware repository, or reverse-engineering artifacts.
· Suspicious use of encryption libraries, cryptographic functions, or packed binaries may support malware classification when tied to sample analysis, but these signals must not be used alone for enterprise detection.
· Unusual process lineage from script interpreters, remote administration tools, archive utilities, deployment tools, or unknown binaries may support detection when followed by bulk file modification.
· Abnormal file-access concentration against business-critical repositories may support detection when a single user, process, host, or service account touches an unusually broad set of files in a short period.
· Rapid creation of ransom-note-like files across multiple directories may support detection when paired with mass file rewrite or suspicious execution context.
· Unusual access to virtual machine disks, datastore paths, or hypervisor-managed file locations may support detection when activity is inconsistent with approved maintenance windows.
· Backup job interruption, restore-point deletion, snapshot removal, vault-policy changes, or recovery configuration modification may support detection when the initiating identity, source host, or timing is anomalous.
· Security tool interference, tamper events, logging disruption, or endpoint-protection degradation may support detection when it precedes file transformation or recovery-path tampering.
· Malware repository or threat-intelligence matches for VECT-associated samples may support enrichment, but they must remain secondary to direct behavioral telemetry unless the rule purpose is malware classification.
Exploit Attempt and Instability Signals
· Pre-impact execution of suspicious binaries on systems with access to high-value file repositories is a priority signal because VECT’s destructive outcome can occur quickly once file transformation begins.
· Unexpected process crashes, abnormal termination, failed encryption loops, or repeated execution attempts may indicate unstable ransomware execution when paired with suspicious file activity.
· High CPU, disk I/O, or file-handle activity from an unusual process may support early detection when the process rapidly touches many files and has no approved administrative purpose.
· Threading anomalies, performance degradation, or repeated process restarts during high-volume file operations may support instability analysis because current research describes additional VECT implementation and design failures beyond the nonce-handling flaw.
· Partial encryption behavior, inconsistent file output, corrupted files, or failed restore validation after ransomware activity may support post-impact assessment, but these signals are late-stage and must not be treated as primary prevention signals.
· Unusual execution on ESXi, Linux servers, or administrative jump hosts is a priority instability and exposure signal because compromise of these systems can extend destructive impact beyond a single endpoint.
· Pre-encryption access to backup infrastructure, shared storage, or virtualization management systems is a priority signal because it may indicate preparation for destructive operational impact.
· New or unusual binaries appearing shortly before file-transformation activity may support detection when correlated with process execution and affected-file scope.
Outbound Communication Signals
· Outbound communication from a suspicious process before or during file transformation may support detection when the destination, protocol, timing, or process lineage is abnormal.
· Connections to newly observed, low-reputation, rare, or suspicious external infrastructure may support detection when associated with ransomware staging, affiliate tooling, or extortion operations.
· Outbound communication from servers, ESXi-adjacent management hosts, backup servers, or administrative jump systems should be prioritized when paired with suspicious file activity.
· Unusual DNS queries, direct IP connections, encrypted outbound sessions, or unexpected external traffic from a process performing file rewrites may support detection when endpoint and network telemetry can be correlated.
· Potential data-staging or exfiltration behavior should be treated as a supporting signal because ransomware operations may combine encryption with extortion, but S22 must not assume exfiltration without telemetry evidence.
· Network indicators must remain conditional because current public VECT reporting primarily supports destructive file behavior and cross-platform execution rather than a stable network signature set.
· Suricata-style network detection should not be treated as viable for S25 unless validated C2, payload, protocol, delivery, or exploit-transport artifacts become available.
Persistence and Post-Exploitation Signals (Conditional)
· New services, scheduled tasks, startup entries, launch agents, cron jobs, or persistence-like modifications may support detection when they appear shortly before file transformation.
· Privilege escalation, credential access, token abuse, or suspicious administrative session activity may support detection when it expands access to file servers, backup systems, virtualization hosts, or shared storage.
· Security control tampering, endpoint agent disablement, log clearing, or telemetry suppression may support detection when observed before ransomware execution.
· Changes to backup software configuration, snapshot retention, recovery vault access, or restore-policy settings are priority post-exploitation signals when performed by unusual users, hosts, service accounts, or API callers.
· Unauthorized access to ESXi management, datastore paths, virtual machine inventory, or hypervisor administrative interfaces may support detection when followed by file modification or virtual machine disruption.
· Creation or modification of local accounts, SSH keys, privileged groups, or remote-access configurations may support detection when tied to ransomware staging or expansion.
· Persistence signals are conditional because they may not appear in every VECT intrusion and must not be required for a ransomware-wiper alert to fire.
· Post-exploitation signals must be used to enrich severity and scope, not to delay alerting when primary destructive file activity is already present.
Lateral Movement and Expansion Signals (Conditional)
· Rapid file activity across multiple hosts, shares, or mapped drives from the same user, process, source host, or service account may indicate expansion from a single compromised system to broader enterprise impact.
· Remote execution, administrative share access, SSH activity, WinRM, PsExec-like behavior, RDP access, or management-tool execution may support lateral movement assessment when followed by file transformation.
· Access to multiple file servers, NAS locations, backup repositories, or virtualization datastores from an unusual source should be treated as a high-severity expansion signal.
· Use of privileged or service accounts outside normal administration windows may support lateral movement detection when paired with file rewrite activity, backup tampering, or ESXi access.
· Unusual authentication patterns to backup consoles, virtualization management systems, cloud recovery services, or storage administration interfaces may support detection of ransomware expansion into recovery-control surfaces.
· Multi-platform execution across Windows, Linux, and ESXi assets may indicate coordinated ransomware deployment and should raise severity because VECT is reported across all three platform variants.
· Expansion signals are conditional because VECT can cause severe impact from a single privileged system with access to shared storage or virtualization assets.
· Lateral movement signals must be used to determine scope and severity, not as a required dependency for detecting active ransomware-wiper behavior.
Signal Usage Constraints
· Signals must be used in behavior combinations rather than isolated keyword or artifact matches.
· Extension-only logic must not be treated as high-confidence detection because file extensions can change across versions, affiliates, or copycat tooling.
· Ransom-note-only logic must not be treated as high-confidence detection because ransom-note artifacts are late-stage and can be renamed or copied.
· YARA and malware-classification signals must be treated as conditional support unless they are based on validated VECT samples and stable sample-derived artifacts.
· Network signals must not be promoted to primary detection unless validated VECT infrastructure, protocol behavior, payload signatures, or delivery artifacts are available.
· Cloud-control signals must be scoped to backup, snapshot, recovery, storage, and administrative tampering; they must not claim direct observation of local VECT encryption unless endpoint telemetry from cloud workloads is available.
· File-volume signals must be baseline-aware and must account for backup jobs, indexing, software deployment, data migration, antivirus scanning, compression, encryption tools, and synchronization clients.
· Backup and ESXi signals must include role-based context, maintenance-window awareness, authorized-user validation, and approved automation allowlists.
· Signals must not depend on another CyberDax rule firing first.
· Signals must preserve a direct telemetry-to-logic-to-output path so later S25 rules remain independently deployable and auditable.
· Signals must avoid overfitting to the current VECT encryption flaw because the actor may correct the flaw while retaining the same destructive ransomware operating model.
· Signal severity must increase when destructive file transformation overlaps with backup tampering, ESXi impact, privileged execution, shared-storage access, or multi-host expansion.
· Signal severity must remain lower when activity is isolated, explainable by approved administration, or unsupported by process, file, user, or asset-role context.
S23 — Telemetry Requirements
Endpoint and Process Execution Telemetry
· Endpoint telemetry must capture process creation, process termination, parent-child process lineage, executable path, command line, process hash, user context, host identity, host role, timestamp, and process privilege level where available.
· Endpoint telemetry must identify execution from user-writable paths, temporary directories, staging folders, administrative shares, recently created directories, removable media, and remote management execution contexts.
· Endpoint telemetry must preserve process relationships for binaries that initiate file enumeration, high-volume file writes, extension changes, ransom-note placement, backup interference, or virtualization-adjacent access.
· Endpoint telemetry must support Windows, Linux, and ESXi-adjacent visibility where deployed because VECT 2.0 targets Windows, Linux, and VMware ESXi variants through a shared codebase.
· Endpoint telemetry must capture command-line and script execution for PowerShell, Windows command shell, WMI, WinRM, Bash, shell scripts, Python, administrative utilities, backup tooling, and virtualization management utilities where present.
· Endpoint telemetry must include service creation, scheduled task creation, cron modification, launch-agent changes, startup modification, local account changes, SSH key modification, privilege escalation indicators, and endpoint protection tamper events when available.
· Endpoint telemetry must support host-role enrichment so suspicious execution on file servers, backup servers, ESXi management hosts, domain controllers, administrative jump hosts, and database servers can be prioritized over lower-impact endpoints.
· Endpoint telemetry must not be considered sufficient if it lacks process lineage, command-line visibility, user context, or host-role enrichment because those gaps make destructive ransomware behavior difficult to distinguish from approved administrative activity.
Memory and Execution Telemetry
· Memory and execution telemetry should capture suspicious packed binaries, unsigned or low-prevalence executables, abnormal process injection, unusual module loading, suspicious cryptographic library usage, and execution from nonstandard paths.
· Memory telemetry should support malware triage where sample behavior suggests ransomware logic, encryption routines, anti-analysis behavior, or code-obfuscation traits.
· Execution telemetry should capture abnormal thread behavior, rapid process restarts, excessive process resource use, and unexpected termination when associated with high-volume file activity.
· Execution telemetry should preserve binary metadata, signer information, file reputation, first-seen timestamps, and endpoint prevalence to distinguish ransomware staging from approved enterprise software.
· Execution telemetry should support classification of VECT-related samples where validated YARA, sandbox, malware repository, or reverse-engineering artifacts are available.
· Memory and execution telemetry must remain supporting telemetry unless directly tied to file transformation, recovery-path tampering, suspicious execution context, or validated sample classification.
· Memory telemetry must not be used as the sole basis for enterprise detection when it identifies only generic encryption libraries, generic packing traits, or common cryptographic routines.
Crash and Fault Telemetry
· Crash and fault telemetry should capture process crashes, abnormal process exits, repeated execution failures, application fault events, core dumps, segmentation faults, service failures, and repeated restart behavior during high-volume file operations.
· Crash telemetry should be correlated with suspicious file transformation, failed encryption loops, heavy disk I/O, or newly staged binaries because instability by itself is not sufficient to identify ransomware-wiper execution.
· Fault telemetry should include process name, executable path, user context, parent process, host identity, timestamp, error code, exception type, and affected asset role where available.
· Crash and fault telemetry is useful for VECT analysis because current reporting describes implementation flaws and design failures beyond the destructive nonce-handling defect.
· Crash telemetry should support post-impact analysis where partial encryption, corrupted files, failed restore validation, or repeated binary execution indicates unstable ransomware behavior.
· Crash telemetry must not be treated as a required detection dependency because destructive ransomware can execute without generating observable crash events.
· Crash telemetry must not be used as a standalone rule trigger unless paired with suspicious execution and destructive file activity.
File and Persistence Telemetry
· File telemetry must capture file creation, modification, rename, deletion, extension change, path, file size, file type, owner, initiating process, initiating user, host identity, timestamp, and affected directory where available.
· File telemetry must support detection of high-volume file rewrite activity, rapid directory traversal, mass extension changes, ransom-note placement, and suspicious access to high-value repositories.
· File telemetry must support size-aware analysis because VECT’s destructive flaw is reported to affect files larger than 131,072 bytes, a threshold low enough to include many documents, databases, archives, virtual disks, and backup artifacts.
· File telemetry must include coverage for local disks, mapped drives, network shares, file servers, NAS paths, database storage, backup staging areas, and virtualization datastore paths where available.
· File telemetry must identify rapid creation of ransom-note-like artifacts across multiple directories, but ransom-note creation must be correlated with execution or file transformation before severity is raised.
· Persistence telemetry must capture new services, scheduled tasks, registry run keys, startup folder changes, cron jobs, launch agents, SSH authorized key changes, local account creation, and remote-access configuration changes where applicable.
· File and persistence telemetry must be baseline-aware because legitimate backup operations, indexing, data migration, software deployment, compression, encryption tools, antivirus scanning, and synchronization clients can produce high file volume.
· File telemetry must not rely only on file extension or ransom-note name because those artifacts are fragile and can change across versions, affiliates, or copycat tooling.
Network and Outbound Communication Telemetry
· Network telemetry should capture DNS queries, direct IP connections, HTTP and HTTPS metadata, TLS metadata, proxy logs, firewall logs, NetFlow, endpoint network connections, and destination reputation where available.
· Network telemetry should preserve source process, source host, user context, destination, destination port, protocol, timestamp, byte count, connection direction, and first-seen status where available.
· Network telemetry should support detection of suspicious outbound communication from processes that are also performing file rewrite activity, backup tampering, or administrative execution.
· Network telemetry should prioritize unusual outbound communication from file servers, backup servers, ESXi management hosts, administrative jump hosts, and other systems with access to high-value data.
· Network telemetry may support extortion-stage analysis if data staging, unusual upload volume, rare destinations, or suspicious external communication is observed.
· Network telemetry must remain supporting telemetry for this report because current public VECT reporting primarily supports destructive file behavior and cross-platform execution rather than a stable network signature set.
· Network telemetry must not be used to justify Suricata deployment unless validated C2, protocol, payload, delivery, or exploit-transport artifacts become available.
· Network telemetry must not be treated as required for active ransomware-wiper detection when endpoint and file telemetry already show destructive transformation.
Web and Application Telemetry (Conditional Availability)
· Web telemetry should capture proxy events, web gateway events, file download activity, blocked payloads, suspicious archive downloads, newly observed domains, user-agent anomalies, and rare external destinations where available.
· Application telemetry should capture authentication, administrative action, data export, API activity, storage access, backup-console activity, and virtualization-management activity where relevant systems provide logs.
· Web and application telemetry should support pre-impact investigation when suspicious downloads, staging behavior, remote administration, or access to recovery-control interfaces precedes file transformation.
· Application telemetry from backup platforms must capture restore-point deletion, snapshot removal, retention-policy modification, vault access changes, protected workload removal, backup job disablement, and unusual restore configuration changes.
· Application telemetry from virtualization platforms must capture ESXi administrative access, datastore interaction, VM power operations, VM snapshot changes, virtual disk modification, host management actions, and administrative session anomalies.
· Cloud application telemetry must capture recovery-path and administrative tampering in AWS, Azure, and GCP environments where cloud-native backup, snapshot, storage, or recovery controls are used.
· Web and application telemetry are conditional because they may not exist in all environments and must not be required for every ransomware-wiper alert.
· Web and application telemetry must not claim direct visibility into local VECT encryption unless paired with endpoint, workload, file, or EDR telemetry from the affected system.
Telemetry Availability Requirements
· Minimum viable telemetry for ransomware-wiper detection must include endpoint process execution, file modification activity, user context, host identity, timestamp, and affected path information.
· Strong telemetry coverage must include process lineage, command line, file size, file action type, file path, file extension, initiating process, initiating user, endpoint role, and host criticality.
· High-confidence enterprise detection requires telemetry from endpoint, file, backup, virtualization, identity, and SIEM correlation sources where those systems are present.
· VMware environments require ESXi or virtualization-management telemetry because VECT is reported to include ESXi targeting, and virtual infrastructure compromise can create rapid multi-system impact.
· Backup-dependent environments require backup-platform telemetry because destructive ransomware risk cannot be accurately prioritized without visibility into recovery-path tampering.
· Cloud-hosted environments require workload endpoint telemetry for direct ransomware execution detection and cloud-control telemetry for backup, snapshot, storage, recovery, and administrative tampering.
· SIEM normalization must preserve source, host, user, process, file, action, timestamp, asset role, and control-plane fields needed for cross-source correlation.
· Telemetry must support time-window correlation between suspicious execution, file transformation, ransom-note placement, backup tampering, ESXi impact, outbound communication, and privilege activity.
· Telemetry must support environment-specific baselines for file volume, backup administration, virtualization maintenance, software deployment, indexing, synchronization, and approved encryption activity.
· Telemetry must be validated before deployment because missing process lineage, command-line visibility, file-size fields, or initiating-process attribution can turn high-value detection logic into noisy or incomplete alerting.
Telemetry Limitations and Gaps
· Environments without endpoint process telemetry cannot reliably identify the initiating process behind file transformation, ransom-note placement, or backup interference.
· Environments without file telemetry cannot reliably detect the mass rewrite, rename, extension-change, or size-aware file activity that defines the highest-confidence VECT detection surface.
· Environments without file-size visibility cannot directly evaluate the reported 131,072-byte destructive threshold and must rely on broader high-value file and repository context.
· Environments without ESXi or virtualization telemetry cannot reliably detect hypervisor-adjacent impact until symptoms appear in downstream systems.
· Environments without backup-platform telemetry cannot reliably detect recovery-path interference before restore attempts fail.
· Environments without normalized SIEM correlation may detect isolated signals but will struggle to connect suspicious execution, file transformation, backup tampering, and virtualization impact into a single operational-risk alert.
· Environments without host-role or asset-criticality enrichment may generate excessive noise because high-volume file activity has different meaning on endpoints, file servers, backup servers, administrative jump hosts, and virtualization hosts.
· Environments without command-line visibility may miss attacker staging, administrative-tool abuse, backup suppression commands, and virtualization-management activity.
· Network-only environments cannot provide adequate VECT ransomware-wiper detection because the current public evidence does not support a stable network signature model.
· Cloud-control-only environments cannot directly detect local encryption or destructive file transformation unless endpoint or workload telemetry is available.
· YARA-only coverage is insufficient for enterprise detection because sample classification does not prove active destructive execution, file impact, backup tampering, or operational scope.
· Telemetry limitations must be documented as deployment constraints in S25 and should influence DRI and TCR scoring without allowing one score to justify the other.
Figure 4
S24 — Detection Opportunities and Gaps
Detection Opportunities
· Mass file transformation detection is the strongest opportunity because VECT’s destructive impact depends on large-scale file modification, rewrite, rename, and extension-change behavior across endpoint, server, shared-storage, and virtualization-accessible paths.
· Size-aware file modification detection is a high-value opportunity because current technical reporting indicates VECT 2.0 destroys files larger than 131,072 bytes by discarding required decryption nonces, making file-size context operationally meaningful for prioritization.
· Ransom-note staging correlated with file transformation is a strong opportunity because ransom-note creation becomes meaningful when it occurs near suspicious file rewrite activity, affected directory expansion, or ransomware-like process execution.
· Endpoint process-to-file correlation is a strong opportunity because EDR and endpoint telemetry can connect suspicious execution, process lineage, command-line activity, and file transformation into a single destructive ransomware signal.
· Backup and recovery-control tampering detection is a strong opportunity because destructive ransomware risk escalates sharply when restore points, snapshots, vault policies, backup jobs, or retention settings are modified before or during file impact.
· ESXi and virtualization-impact detection is a strong opportunity in VMware environments because VECT 2.0 is reported across Windows, Linux, and ESXi variants, making virtual disks, datastores, snapshots, and hypervisor-adjacent administration critical detection surfaces.
· Cross-platform execution detection is a strong opportunity because VECT’s reported Windows, Linux, and ESXi scope allows defenders to build platform-aware but behavior-consistent logic around destructive file activity, staging, and recovery-path interference.
· SIEM correlation of endpoint, file, backup, virtualization, identity, and cloud-control events is a strong opportunity where normalized telemetry is available because individual events may be weak while combined behavior is high-confidence.
· Conditional YARA-based sample classification is a limited but valid opportunity where validated VECT samples, stable strings, binary traits, or malware repository artifacts are available.
· Cloud-native recovery-path protection is a conditional opportunity in AWS, Azure, and GCP environments where cloud audit logs can identify snapshot, backup, storage, vault, or recovery-control tampering that increases destructive ransomware impact.
· Outbound communication enrichment is a conditional opportunity when suspicious network activity occurs before or during file transformation, but current reporting does not support a stable network-signature-first detection model.
· Crash and instability enrichment is a conditional opportunity because reporting describes VECT implementation defects beyond the destructive nonce-handling flaw, but crash and fault signals must remain secondary unless paired with file-impact telemetry.
Detection Gaps
· Network-signature gap limits Suricata viability because current public reporting supports destructive file behavior and cross-platform execution more strongly than stable C2, protocol, payload, or delivery signatures.
· Sample-artifact gap limits YARA confidence because a strong YARA rule requires validated strings, binary traits, imports, structural markers, or sample-derived conditions rather than generic ransomware terms.
· File-size telemetry gap may prevent direct prioritization around the 131,072-byte threshold and force defenders to rely on broader repository, file-type, or asset-criticality context.
· Initiating-process attribution gap weakens file transformation detection because defenders may observe file modification without knowing which process, user, or host caused the activity.
· Command-line visibility gap weakens staging, administrative-tool abuse, backup suppression, and virtualization-management detection.
· Host-role enrichment gap increases noise because high-volume file activity has different significance on endpoints, file servers, backup servers, administrative jump hosts, database servers, and virtualization hosts.
· ESXi telemetry gap limits detection of hypervisor-adjacent impact until downstream disruption or file damage is visible elsewhere.
· Backup-platform telemetry gap limits detection of recovery-path interference before restore failure or post-impact investigation.
· Cloud-control-only visibility gap prevents direct detection of local encryption or file transformation when endpoint or workload telemetry is absent.
· Network-only visibility gap prevents adequate ransomware-wiper detection because VECT’s most reliable observable behavior is local destructive file transformation rather than network communication.
· Crash-only visibility gap prevents reliable detection because process instability may indicate defective malware execution but cannot confirm ransomware-wiper behavior without suspicious execution or file-impact evidence.
· YARA-only visibility gap prevents operational detection because sample classification does not prove active execution, affected scope, recovery-path tampering, or enterprise impact.
· Baseline gap increases false positives where normal backup jobs, indexing, software deployment, data migration, compression, synchronization, or encryption workflows are not defined.
· Correlation-normalization gap weakens SIEM rules when process, file, identity, backup, virtualization, and cloud-control fields cannot be joined reliably.
High-Confidence Detection Opportunities
· Suspicious process execution followed by mass file modification is high confidence when process lineage, user context, host role, file scope, and affected path information are available.
· Mass file modification followed by ransom-note placement is high confidence when note artifacts appear across impacted directories during or immediately after high-volume file rewrite activity.
· High-volume file rewrite activity affecting operationally meaningful file sizes is high confidence when file-size telemetry, initiating-process attribution, and host-role context are present.
· Backup or snapshot tampering near ransomware-like file transformation is high confidence because recovery-path interference materially increases destructive impact.
· ESXi datastore or virtual disk modification from anomalous administrative context is high confidence in VMware environments when tied to suspicious authentication, process execution, or maintenance-window deviation.
· Multi-host or multi-share file transformation from the same user, process, or source host is high confidence because it indicates expansion beyond a single endpoint.
· Endpoint ransomware behavioral alert with corroborating file transformation evidence is high confidence when supported by process lineage and affected-file scope.
· Cloud recovery-control tampering from unusual identity, source, or time window is high confidence for recovery-path protection, but it must be scoped as destructive-impact amplification rather than direct local encryption detection.
Conditional Detection Opportunities
· VECT-associated extension or ransom-note detection is conditional because these artifacts can support triage but are fragile if used alone.
· YARA-based VECT classification is conditional because it requires validated sample-derived artifacts and should be used for malware triage, repository scanning, sandbox classification, or threat-intelligence enrichment.
· Outbound communication from suspicious ransomware-like processes is conditional because it can support extortion or staging analysis but does not currently provide a stable primary detection surface for VECT.
· Crash or fault telemetry near file transformation is conditional because instability may support the VECT analytical model but is not required for ransomware-wiper execution.
· Persistence or post-exploitation activity preceding file impact is conditional because VECT may produce destructive impact without observable persistence.
· Lateral movement activity preceding mass file transformation is conditional because a single privileged system with shared-storage or virtualization access can cause severe impact without broad host-to-host movement.
· Cloud backup, snapshot, or recovery asset tampering is conditional because cloud logs can detect recovery-control compromise but cannot directly observe local file encryption unless workload telemetry is present.
· Threat-intelligence matches for VECT infrastructure or samples are conditional because they should enrich detection and triage, not replace behavior-based confirmation.
Detection Boundary Conditions
· VECT detection should prioritize validated destructive behavior, recovery-path risk, and virtualization impact.
· Static indicators, ransom-note artifacts, file extensions, network indicators, and YARA matches should be used only when supported by validated telemetry or sample evidence.
· Cloud-control detections should remain scoped to recovery-path tampering unless workload endpoint telemetry confirms local execution.
· Network detection should remain supporting telemetry unless validated VECT network artifacts become available.
System-Level Rule Viability
· SentinelOne has strong rule viability because endpoint process, behavioral, file, tamper, and ransomware activity telemetry can support high-confidence detection of destructive file transformation and recovery-path interference.
· Splunk has strong rule viability where endpoint, file, backup, virtualization, identity, and cloud-control logs are normalized into searchable correlation data.
· Elastic has strong rule viability where endpoint/file telemetry and EQL or KQL sequence logic can connect suspicious process execution, file transformation, and ransom-note staging.
· QRadar has moderate rule viability because correlation is feasible when upstream EDR, file, backup, VMware, and identity telemetry are normalized, but low-level file behavior may be inconsistent across deployments.
· SIGMA has moderate rule viability for portable process, file, backup-interference, and ransom-note correlation logic, but backend effectiveness depends heavily on available telemetry.
· YARA has conditional rule viability only for sample classification using validated VECT artifacts.
· AWS has conditional rule viability for recovery-path tampering, snapshot deletion, backup modification, storage-control changes, and unusual administrative activity.
· Azure has conditional rule viability for Recovery Services Vault, snapshot, backup-policy, protected-instance, storage, and administrative tampering.
· GCP has conditional rule viability for snapshot, image, backup, storage, recovery asset, and administrative tampering.
· Suricata has no current rule viability unless validated VECT network artifacts become available.
Detection Gap Impact
· Missing endpoint process lineage materially reduces confidence because file transformation cannot be tied to the responsible process or execution chain.
· Missing file telemetry materially reduces confidence because the primary VECT impact surface is mass file modification.
· Missing file-size fields reduce precision because defenders cannot directly prioritize the reported destructive threshold.
· Missing ESXi telemetry reduces visibility into virtualization-impact behavior and can delay detection until business disruption occurs.
· Missing backup telemetry reduces visibility into recovery-path degradation and can create false confidence in recoverability.
· Missing SIEM normalization reduces correlation quality and can fragment the attack into low-confidence isolated signals.
· Missing host-role enrichment increases false positives and weakens severity prioritization.
· Missing validated sample artifacts limits YARA to conditional or deferred status.
· Missing validated network artifacts blocks Suricata deployment and keeps network telemetry in a supporting role.
· Missing cloud workload telemetry prevents cloud-control logs from detecting local ransomware execution.
S25 — Ultra-Tuned Detection Engineering Rules
Suricata
Detection Viability Assessment
· Suricata does not have an audit-ready detection rule for this report at this time.
· The strongest observable VECT behavior is destructive file transformation, encryption failure, ransom-note staging, backup and recovery interference, and cross-platform execution across Windows, Linux, and ESXi environments.
· These behaviors are primarily endpoint, file-system, backup, virtualization, and SIEM-correlation detection surfaces rather than network-signature surfaces.
· Current Block 4 analysis already positions Suricata as non-viable unless validated VECT network artifacts become available.
· Network telemetry may still support investigation when suspicious outbound activity occurs near endpoint-confirmed destructive file transformation, but it should not be represented as primary VECT detection.
Final Rule Disposition
Rule Count
0
Disposition
No Suricata rule is included for this report.
Deployment Status
Do not deploy.
Reason
No validated VECT network indicator, protocol behavior, payload signature, delivery artifact, or command-and-control pattern is currently strong enough to support a low-noise, ransomware-wiper-specific Suricata rule.
Detection Role
Supporting telemetry only, not primary detection.
Reconsideration Trigger
Will reassess Suricata only if future reporting provides validated VECT C2 infrastructure, delivery traffic, exploit transport, payload-transfer patterns, protocol markers, JA3 or JA4 fingerprints, TLS traits, HTTP URI structures, or other network artifacts that can be expressed safely in Suricata rule format.
SentinelOne
SentinelOne Rule 1
Mass Destructive File Transformation from Suspicious Execution Context
System-Native Format
SentinelOne Deep Visibility hunting query suitable for STAR rule conversion after tenant-specific field validation.
Detection Objective
Detect suspicious endpoint execution associated with high-volume file modification, rename, or extension-change behavior consistent with destructive ransomware activity.
Detection Rationale
· VECT’s primary operational impact is destructive file transformation rather than a reliably recoverable encryption workflow.
· This rule targets suspicious process context associated with ransomware-like file activity across user data, shared repositories, archives, databases, backup-adjacent files, and virtualization-accessible assets.
· The rule is designed to remain effective if VECT changes file extension, ransom-note name, binary name, staging path, or affiliate deployment method.
Required Telemetry
· Process creation telemetry.
· File modification telemetry.
· File rename telemetry where available.
· Process lineage.
· Command-line visibility.
· User context.
· Host identity.
· Host role.
· File path.
· File name.
· File size where available.
Engineering Implementation Instructions
· Validate SentinelOne field names and event labels in the customer tenant before deployment.
· Scope initial deployment to servers, file servers, administrative workstations, backup-accessible hosts, and systems with access to high-value repositories.
· Review approved backup agents, indexing tools, data migration utilities, software deployment tools, encryption products, and synchronization clients before enabling broad alerting.
· Tune by host role and maintenance window rather than suppressing high-volume file activity broadly.
· Validate alert context for initiating process, parent process, user, affected file scope, affected directory scope, and overlap with backup or virtualization assets.
Detection Quality
DRI
8.6
DRI Justification
The rule is behavior-anchored to destructive file transformation from suspicious execution context, making it resilient to changes in VECT filenames, extensions, ransom-note names, and static indicators.
Operational TCR
7.8
Operational TCR Justification
Operational confidence is strong where SentinelOne captures process lineage, command line, file modification, file rename, and host-role context. Confidence may degrade where file telemetry, file-size visibility, or initiating-process attribution is incomplete.
Full-Telemetry TCR
8.8
Full-Telemetry TCR Justification
Full-telemetry confidence is high when endpoint process events, file events, command-line fields, host-role enrichment, and affected-file scope are available.
Deployment Limitations
· This rule must not trigger on file volume alone.
· This rule requires customer validation of approved high-volume file activity.
· This rule must not rely on .vect, ransom-note artifacts, or known hashes as required conditions.
· This rule must not be represented as definitive VECT attribution without supporting sample, sandbox, threat-intelligence, or forensic evidence.
Deployment Tier Guidance
Tier 1
Deploy on high-risk endpoints, administrative workstations, and systems with direct access to business-critical user data or commonly targeted file paths.
Tier 2
Expand deployment to file servers, backup-accessible systems, database-adjacent systems, and servers with access to operational repositories.
Tier 3
Expand deployment across enterprise server groups, privileged-user workstations, remote administration systems, mapped-drive users, and systems with access to shared repositories.
Tier 4
Deploy broadly across enterprise endpoint and server populations where licensing, telemetry retention, and SOC capacity support wide-scale behavioral detection.
Tier Usage Constraints
· Tiering changes deployment scope, enrichment priority, and response routing; it must not weaken detection evidence requirements.
· Smaller environments should prioritize high-value assets and shared-storage access points.
· Larger environments should enrich SentinelOne events with host role, user context, asset criticality, backup activity, and virtualization activity where available.
Rule Code
// SentinelOne Deep Visibility hunting logic
// Suitable for STAR conversion after tenant-specific validation.
// Rule: Mass Destructive File Transformation from Suspicious Execution Context
// Purpose: Detect ransomware-like file transformation from suspicious process context.
(
EventType In ("File Modification", "File Rename", "File Creation")
)
AND
(
FileFullName ContainsCIS "\\Users\\"
OR FileFullName ContainsCIS "\\Shares\\"
OR FileFullName ContainsCIS "\\Documents\\"
OR FileFullName ContainsCIS "\\Desktop\\"
OR FileFullName ContainsCIS "\\Downloads\\"
OR FileFullName ContainsCIS "\\Finance\\"
OR FileFullName ContainsCIS "\\HR\\"
OR FileFullName ContainsCIS "\\Legal\\"
OR FileFullName ContainsCIS "\\Datastore\\"
OR FileFullName ContainsCIS ".vmdk"
OR FileFullName ContainsCIS ".vhdx"
OR FileFullName ContainsCIS ".sql"
OR FileFullName ContainsCIS ".bak"
OR FileFullName ContainsCIS ".zip"
OR FileFullName ContainsCIS ".7z"
OR FileFullName ContainsCIS ".rar"
)
AND
(
ProcessCmd ContainsCIS "temp"
OR ProcessCmd ContainsCIS "tmp"
OR ProcessCmd ContainsCIS "appdata"
OR ProcessCmd ContainsCIS "programdata"
OR ProcessCmd ContainsCIS "users"
OR ProcessCmd ContainsCIS "public"
OR ProcessCmd ContainsCIS "downloads"
OR ProcessCmd ContainsCIS "desktop"
OR ProcessCmd ContainsCIS "admin$"
OR ProcessCmd ContainsCIS "c$"
OR ProcessCmd ContainsCIS "powershell"
OR ProcessCmd ContainsCIS "cmd.exe"
OR ProcessCmd ContainsCIS "wscript"
OR ProcessCmd ContainsCIS "cscript"
OR ProcessCmd ContainsCIS "rundll32"
OR ProcessCmd ContainsCIS "regsvr32"
OR ProcessCmd ContainsCIS "bash"
OR ProcessCmd ContainsCIS " sh "
)
AND NOT
(
ProcessName ContainsCIS "veeam"
OR ProcessName ContainsCIS "commvault"
OR ProcessName ContainsCIS "rubrik"
OR ProcessName ContainsCIS "cohesity"
OR ProcessName ContainsCIS "backup"
OR ProcessName ContainsCIS "onedrive"
OR ProcessName ContainsCIS "dropbox"
OR ProcessName ContainsCIS "splunk"
)
SentinelOne Rule 2
Ransom-Note Staging Correlated with Ransomware-Like File Activity
System-Native Format
SentinelOne Deep Visibility hunting query suitable for STAR rule conversion after tenant-specific field validation.
Detection Objective
Detect ransom-note-like artifact creation when it appears in suspicious execution or file-transformation context.
Detection Rationale
· Ransom-note creation alone is not sufficient for high-confidence detection.
· Ransom-note staging becomes meaningful when paired with suspicious process context, high-value paths, file modification activity, or affected asset criticality.
· This rule treats ransom-note artifacts as supporting behavior rather than a standalone VECT identifier.
Required Telemetry
· File creation telemetry.
· File modification telemetry.
· Process lineage.
· Command-line visibility.
· File path.
· User context.
· Host identity.
· Host role.
Engineering Implementation Instructions
· Validate legitimate readme, installer, helpdesk, script, software deployment, and administrative automation behavior before deployment.
· Prioritize ransom-note-like files created in multiple user, shared, server, or high-value directories.
· Treat isolated ransom-note-like files as triage context unless paired with file modification, suspicious execution, or asset criticality.
· Do not require exact VECT ransom-note naming because filenames may change across variants, affiliates, or copycat tooling.
Detection Quality
DRI
8.1
DRI Justification
The rule is anchored to ransom-note staging with suspicious ransomware-like context, making it stronger than note-name-only detection and more resilient to simple artifact changes.
Operational TCR
7.6
Operational TCR Justification
Operational confidence is strong where SentinelOne captures file creation, process lineage, command line, file path, and host-role context. Confidence may degrade where file creation events or initiating-process attribution are incomplete.
Full-Telemetry TCR
8.5
Full-Telemetry TCR Justification
Full-telemetry confidence is high when ransom-note-like artifact creation can be tied to suspicious process context, affected directories, host role, and concurrent file modification behavior.
Deployment Limitations
· This rule must not fire solely on a ransom-note filename.
· This rule must not depend only on !!!READ_ME!!!.txt, !!!_READ_ME_!!!.txt, .vect, or other single artifacts.
· This rule should escalate suspicious ransomware activity, not independently prove VECT attribution.
· This rule requires customer validation of legitimate text, HTML, and help-file generation behavior.
Deployment Tier Guidance
Tier 1
Deploy on high-risk endpoints and administrative workstations where ransom-note staging would indicate immediate user-data or local-data impact.
Tier 2
Expand deployment to file servers, shared repositories, backup-accessible systems, and systems that commonly host business-critical documents or operational data.
Tier 3
Expand deployment across enterprise servers, mapped-drive users, remote administration systems, and systems with access to multiple shared directories or high-value repositories.
Tier 4
Deploy broadly across endpoint and server populations where file creation telemetry, alert triage capacity, and SIEM enrichment are available at scale.
Tier Usage Constraints
· Tiering changes deployment scope and enrichment priority; it must not lower the requirement for ransomware-like context.
· Smaller environments should prioritize high-value directories and shared repositories.
· Larger environments should enrich ransom-note alerts with endpoint file activity, user context, host role, and affected-directory scope.
Rule Code
// SentinelOne Deep Visibility hunting logic
// Suitable for STAR conversion after tenant-specific validation.
// Rule: Ransom-Note Staging Correlated with Ransomware-Like File Activity
// Purpose: Detect ransom-note-like artifact staging in suspicious ransomware context.
(
EventType In ("File Creation", "File Modification")
)
AND
(
FileFullName ContainsCIS "read_me"
OR FileFullName ContainsCIS "readme"
OR FileFullName ContainsCIS "decrypt"
OR FileFullName ContainsCIS "restore"
OR FileFullName ContainsCIS "recover"
OR FileFullName ContainsCIS "how_to"
OR FileFullName ContainsCIS "!!!"
)
AND
(
FileFullName ContainsCIS ".txt"
OR FileFullName ContainsCIS ".html"
OR FileFullName ContainsCIS ".hta"
)
AND
(
ProcessCmd ContainsCIS "temp"
OR ProcessCmd ContainsCIS "tmp"
OR ProcessCmd ContainsCIS "appdata"
OR ProcessCmd ContainsCIS "programdata"
OR ProcessCmd ContainsCIS "users"
OR ProcessCmd ContainsCIS "public"
OR ProcessCmd ContainsCIS "downloads"
OR ProcessCmd ContainsCIS "powershell"
OR ProcessCmd ContainsCIS "cmd.exe"
OR ProcessCmd ContainsCIS "bash"
OR ProcessCmd ContainsCIS " sh "
OR ProcessName Is Not Empty
)
AND NOT
(
ProcessName ContainsCIS "msiexec"
OR ProcessName ContainsCIS "setup"
OR ProcessName ContainsCIS "installer"
OR ProcessName ContainsCIS "updater"
OR ProcessName ContainsCIS "onedrive"
OR ProcessName ContainsCIS "dropbox"
)
SentinelOne Rule 3
Recovery-Path and Virtualization-Adjacent Interference Before or During File Impact
System-Native Format
SentinelOne Deep Visibility hunting query suitable for STAR rule conversion after tenant-specific field validation.
Detection Objective
Detect endpoint-visible activity targeting backup, recovery, snapshot, logging, or virtualization-adjacent assets that may increase destructive ransomware impact.
Detection Rationale
· VECT-aligned destructive risk increases when recovery paths are impaired before or during file transformation.
· This rule targets endpoint-visible activity involving backup suppression, shadow copy interference, recovery-control tampering, event-log clearing, and virtualization-adjacent operations.
· The rule supports the report’s recovery-first risk model without claiming that SentinelOne alone can observe every backup-platform, cloud-control, or ESXi management event.
Required Telemetry
· Process execution telemetry.
· Command-line telemetry.
· File modification telemetry.
· File deletion telemetry where available.
· Process lineage.
· User context.
· Host identity.
· Host role.
· Endpoint tamper events where available.
Engineering Implementation Instructions
· Scope this rule to systems with access to backup tooling, recovery utilities, virtualization management utilities, administrative functions, and high-value storage.
· Validate approved administrative scripts, backup-management tools, virtualization tools, and maintenance workflows before broad deployment.
· Prioritize alerts when the initiating process also touches user data, shared storage, virtual disks, backup directories, or administrative recovery tooling.
· Correlate SentinelOne events with backup-platform, VMware, identity, and SIEM telemetry where available.
· Do not use this rule as a replacement for dedicated backup-platform, virtualization, or cloud-control telemetry.
Detection Quality
DRI
8.4
DRI Justification
The rule targets recovery-path interference and virtualization-adjacent destructive preparation, which are durable ransomware impact behaviors and less dependent on static VECT artifacts.
Operational TCR
7.5
Operational TCR Justification
Operational confidence is strong where command-line, process lineage, file activity, and host-role context are complete. Confidence varies based on visibility into backup utilities, virtualization tooling, and administrative scripts.
Full-Telemetry TCR
8.6
Full-Telemetry TCR Justification
Full-telemetry confidence is high when endpoint activity can be correlated with backup, virtualization, identity, and SIEM telemetry.
Deployment Limitations
· This rule must not treat legitimate backup administration as malicious without user, host, timing, process, or asset-context anomalies.
· This rule must not claim direct visibility into cloud backup-control changes unless cloud audit telemetry is available from another source.
· This rule must not claim direct ESXi detection unless the monitored system has visibility into ESXi management activity, datastore interaction, or virtualization-adjacent file access.
· This rule requires customer validation of approved backup, recovery, logging, and virtualization tools.
Deployment Tier Guidance
Tier 1
Deploy on administrative workstations and endpoints with local recovery tooling, shadow copy access, or elevated administrative capability.
Tier 2
Expand deployment to backup-accessible systems, servers with recovery tooling, administrative jump hosts, and systems that interact with high-value storage or backup paths.
Tier 3
Expand deployment across server groups, privileged-user workstations, remote administration systems, and systems with access to virtualization management utilities or backup staging paths.
Tier 4
Deploy broadly where SentinelOne telemetry can be enriched with backup-platform, virtualization, identity, and SIEM data to identify recovery-path interference before destructive impact expands.
Tier Usage Constraints
· Tiering changes deployment scope and enrichment priority; it must not lower the requirement for recovery-path or virtualization-adjacent context.
· Smaller environments should prioritize systems with backup, recovery, administrative, or virtualization access.
· Larger environments should correlate SentinelOne events with backup, virtualization, identity, and SIEM telemetry where available.
Rule Code
// SentinelOne Deep Visibility hunting logic
// Suitable for STAR conversion after tenant-specific validation.
// Rule: Recovery-Path and Virtualization-Adjacent Interference Before or During File Impact
// Purpose: Detect endpoint-visible recovery-path or virtualization-adjacent interference.
(
EventType In ("Process Creation", "Command Script", "File Modification", "File Deletion", "File Rename")
)
AND
(
ProcessCmd ContainsCIS "vssadmin"
OR ProcessCmd ContainsCIS "delete shadows"
OR ProcessCmd ContainsCIS "shadowcopy"
OR ProcessCmd ContainsCIS "wmic shadowcopy"
OR ProcessCmd ContainsCIS "wbadmin"
OR ProcessCmd ContainsCIS "bcdedit"
OR ProcessCmd ContainsCIS "recoveryenabled"
OR ProcessCmd ContainsCIS "bootstatuspolicy"
OR ProcessCmd ContainsCIS "wevtutil cl"
OR ProcessCmd ContainsCIS "Clear-EventLog"
OR ProcessCmd ContainsCIS "backup"
OR ProcessCmd ContainsCIS "snapshot"
OR ProcessCmd ContainsCIS "restore"
OR ProcessCmd ContainsCIS "vault"
OR ProcessCmd ContainsCIS "vmdk"
OR ProcessCmd ContainsCIS "vmfs"
OR ProcessCmd ContainsCIS "esxcli"
OR ProcessCmd ContainsCIS "vim-cmd"
)
AND
(
ProcessCmd ContainsCIS "delete"
OR ProcessCmd ContainsCIS "remove"
OR ProcessCmd ContainsCIS "disable"
OR ProcessCmd ContainsCIS "stop"
OR ProcessCmd ContainsCIS "clear"
OR ProcessCmd ContainsCIS "modify"
OR ProcessCmd ContainsCIS "set"
)
AND NOT
(
ProcessName ContainsCIS "veeam"
OR ProcessName ContainsCIS "commvault"
OR ProcessName ContainsCIS "rubrik"
OR ProcessName ContainsCIS "cohesity"
OR ProcessName ContainsCIS "backup"
)
Splunk
Splunk Rule 1
Mass File Transformation with Ransom-Note Correlation
System-Native Format
Splunk SPL correlation search.
Detection Objective
Detect suspicious high-volume file modification, rename, or creation activity correlated with ransom-note-like artifact creation.
Detection Rationale
· VECT’s destructive impact is driven by file transformation activity, making file modification and rename telemetry a primary detection surface.
· Ransom-note creation is weak when isolated, but becomes stronger when observed near high-volume file changes or suspicious process activity.
· This rule is designed to detect ransomware-wiper behavior without requiring .vect, a specific ransom-note filename, or VECT-specific hashes.
Required Telemetry
· Endpoint file creation events.
· Endpoint file modification events.
· Endpoint file rename events where available.
· Process execution telemetry.
· User context.
· Host identity.
· Host role or asset criticality.
· File path.
· File name.
· File size where available.
Engineering Implementation Instructions
· Validate data sources before deployment, including endpoint, Sysmon, EDR, Windows file telemetry, Linux file telemetry, or file-integrity monitoring sources.
· Map customer telemetry into Splunk CIM fields where possible, including host, user, process_name, process, file_name, file_path, file_size, action, and _time.
· Replace placeholder thresholds with environment-specific baselines for file servers, user endpoints, backup-accessible systems, administrative workstations, and high-value repositories.
· Suppress approved high-volume file activity only after validating backup jobs, indexing, software deployment, data migration, synchronization clients, compression tools, and approved encryption workflows.
· Prioritize alerts where high-volume file transformation overlaps with ransom-note-like artifacts, unusual process context, high-value paths, or critical asset roles.
Detection Quality
DRI
8.7
DRI Justification
The rule is anchored to destructive file transformation correlated with ransom-note staging, making it resilient to VECT filename, extension, ransom-note, and static IOC changes.
Operational TCR
7.7
Operational TCR Justification
Operational confidence is strong where file telemetry, process context, host role, and user context are normalized into Splunk. Confidence degrades where file events lack initiating-process attribution or where file telemetry is incomplete.
Full-Telemetry TCR
8.9
Full-Telemetry TCR Justification
Full-telemetry confidence is high when process execution, file transformation, ransom-note-like artifact creation, file size, user context, and host role are available in normalized Splunk fields.
Deployment Limitations
· This rule must not trigger on file volume alone.
· This rule requires customer-defined file-volume baselines.
· This rule must not rely solely on .vect, !!!READ_ME!!!.txt, !!!_READ_ME_!!!.txt, or any single artifact.
· This rule must not be represented as definitive VECT attribution without validated malware sample, sandbox, threat-intelligence, or forensic support.
· This rule requires consistent endpoint or file telemetry ingestion into Splunk.
Deployment Tier Guidance
Tier 1
Deploy against high-risk endpoints, administrative workstations, and systems with access to business-critical user data, common document paths, or sensitive local repositories.
Tier 2
Expand deployment to file servers, shared repositories, backup-accessible systems, database-adjacent systems, and operational data stores.
Tier 3
Expand deployment across enterprise server groups, mapped-drive users, remote administration systems, and high-value shared-storage access points.
Tier 4
Deploy broadly where endpoint, file, user, asset-role, and SIEM enrichment are available at enterprise scale.
Tier Usage Constraints
· Tiering changes search scope, enrichment priority, and alert routing; it must not weaken the requirement for file-transformation and ransomware-like context.
· Smaller environments should prioritize high-value repositories and shared-storage access points.
· Larger environments should enrich results with host role, user context, asset criticality, backup activity, and virtualization context where available.
Rule Code
`comment("Splunk SPL correlation search")`
`comment("Rule: Mass File Transformation with Ransom-Note Correlation")`
`comment("Purpose: Detect high-volume file transformation correlated with ransom-note-like artifacts.")`
`comment("Deployment note: Replace placeholder macros and thresholds with customer-validated data models, indexes, and baselines.")`
(
index=<endpoint_or_file_telemetry_index>
(
action IN ("created", "modified", "renamed", "file_create", "file_modify", "file_rename")
OR EventCode IN (11, 4663)
)
)
| eval normalized_file=coalesce(file_name, FileName, TargetFilename, file_path, FileFullName)
| eval normalized_path=coalesce(file_path, FilePath, TargetFilename, FileFullName)
| eval normalized_process=coalesce(process_name, Image, ProcessName, process)
| eval normalized_user=coalesce(user, User, Account_Name)
| eval normalized_action=coalesce(action, EventType)
| eval is_ransom_note=if(
match(lower(normalized_file), "(read_me|readme|decrypt|restore|recover|how_to|!!!).*(txt|html|hta)$"),
1,
0
)
| eval is_high_value_path=if(
match(lower(normalized_path), "(users|documents|desktop|downloads|shares|finance|hr|legal|database|datastore|backup|vmdk|vhdx|sql|bak|zip|7z|rar)"),
1,
0
)
| bucket _time span=<customer_defined_time_window>
| stats
count AS file_event_count
dc(normalized_file) AS distinct_files
dc(normalized_path) AS distinct_paths
max(is_ransom_note) AS ransom_note_observed
max(is_high_value_path) AS high_value_path_observed
values(normalized_process) AS processes
values(normalized_user) AS users
values(normalized_action) AS actions
by _time host
| where
file_event_count >= <customer_defined_file_event_threshold>
AND distinct_files >= <customer_defined_distinct_file_threshold>
AND high_value_path_observed=1
AND ransom_note_observed=1
| eval severity="high"
| eval detection_reason="High-volume file transformation correlated with ransom-note-like artifact creation"
| table _time host users processes actions file_event_count distinct_files distinct_paths severity detection_reason
Splunk Rule 2
Backup and Recovery-Control Tampering Near Ransomware-Like Activity
System-Native Format
Splunk SPL correlation search.
Detection Objective
Detect suspicious backup, snapshot, recovery, vault, or restore-control activity occurring near ransomware-like execution or file transformation behavior.
Detection Rationale
· VECT-aligned destructive risk increases when recovery paths are impaired before or during file impact.
· Backup and recovery-control tampering is a high-priority signal because recovery failure materially changes the business outcome.
· This rule is designed to detect destructive-impact amplification rather than claiming direct VECT attribution.
Required Telemetry
· Endpoint process execution telemetry.
· Command-line telemetry.
· Backup-platform telemetry where available.
· File telemetry where available.
· Identity context.
· Host identity.
· Host role.
· Administrative action logs.
· Backup, snapshot, vault, restore, or recovery-control events.
Engineering Implementation Instructions
· Validate backup and recovery data sources before deployment, including platform logs, endpoint command-line telemetry, administrative logs, and SIEM-normalized control-plane events.
· Map relevant fields into Splunk where possible, including host, user, process, process_name, command_line, action, object, resource, vendor_action, and _time.
· Replace placeholder windows and thresholds with customer-validated baselines for backup administration and restore-control activity.
· Validate approved backup administrators, maintenance windows, backup agents, recovery scripts, and automation jobs before enabling enforcement.
· Prioritize alerts when recovery-path tampering overlaps with suspicious process execution, high-value hosts, file transformation, or privileged-user activity.
Detection Quality
DRI
8.5
DRI Justification
The rule targets recovery-path interference near ransomware-like behavior, which is a durable destructive-ransomware impact pattern and does not depend on static VECT indicators.
Operational TCR
7.6
Operational TCR Justification
Operational confidence is strong where endpoint command-line, backup-platform, identity, and administrative telemetry are available. Confidence degrades where backup tools do not send detailed action logs to Splunk.
Full-Telemetry TCR
8.8
Full-Telemetry TCR Justification
Full-telemetry confidence is high when backup-control activity, endpoint process execution, identity context, host role, and file activity can be correlated in Splunk.
Deployment Limitations
· This rule must not treat legitimate backup administration as malicious without identity, timing, host, process, or asset-context anomalies.
· This rule must not claim direct VECT detection unless supported by malware, forensic, or threat-intelligence evidence.
· This rule must not rely only on command keywords such as backup, snapshot, or restore.
· This rule requires customer validation of backup platforms, recovery tooling, administrative workflows, and approved automation.
Deployment Tier Guidance
Tier 1
Deploy against administrative workstations, backup-accessible systems, and endpoints with local recovery tooling or elevated administrative capability.
Tier 2
Expand deployment to backup servers, recovery-management systems, restore-control systems, and servers with access to backup staging paths or recovery repositories.
Tier 3
Expand deployment across enterprise server groups, privileged-user workstations, administrative jump hosts, and systems with access to recovery-control interfaces.
Tier 4
Deploy broadly where backup-platform telemetry, endpoint telemetry, identity logs, and SIEM correlation are available at scale.
Tier Usage Constraints
· Tiering changes search scope, enrichment priority, and alert routing; it must not weaken the requirement for recovery-path or ransomware-like context.
· Smaller environments should prioritize systems with backup, recovery, administrative, or storage-control access.
· Larger environments should correlate backup-control events with endpoint, identity, file, virtualization, and cloud-control telemetry where available.
Rule Code
`comment("Splunk SPL correlation search")`
`comment("Rule: Backup and Recovery-Control Tampering Near Ransomware-Like Activity")`
`comment("Purpose: Detect recovery-path interference near suspicious ransomware-like execution or file activity.")`
`comment("Deployment note: Replace placeholder macros and thresholds with customer-validated data models, indexes, and baselines.")`
(
index=<endpoint_backup_identity_or_admin_index>
(
command_line="*vssadmin*" OR command_line="*delete shadows*" OR command_line="*shadowcopy*"
OR command_line="*wbadmin*" OR command_line="*bcdedit*" OR command_line="*recoveryenabled*"
OR command_line="*bootstatuspolicy*" OR command_line="*wevtutil cl*" OR command_line="*Clear-EventLog*"
OR action IN ("delete_snapshot", "remove_snapshot", "disable_backup", "delete_restore_point", "modify_retention", "delete_vault", "disable_protection")
OR vendor_action IN ("delete_snapshot", "remove_snapshot", "disable_backup", "delete_restore_point", "modify_retention", "delete_vault", "disable_protection")
)
)
| eval normalized_user=coalesce(user, User, Account_Name, src_user)
| eval normalized_host=coalesce(host, dest, ComputerName)
| eval normalized_process=coalesce(process_name, Image, ProcessName, process)
| eval normalized_command=coalesce(command_line, CommandLine, process)
| eval recovery_action=if(
match(lower(normalized_command), "(vssadmin|delete shadows|shadowcopy|wbadmin|bcdedit|recoveryenabled|bootstatuspolicy|wevtutil cl|clear-eventlog|backup|snapshot|restore|vault)")
OR match(lower(coalesce(action, vendor_action, "")), "(delete_snapshot|remove_snapshot|disable_backup|delete_restore_point|modify_retention|delete_vault|disable_protection)"),
1,
0
)
| bucket _time span=<customer_defined_time_window>
| stats
count AS recovery_event_count
values(normalized_user) AS users
values(normalized_process) AS processes
values(normalized_command) AS commands
values(action) AS actions
values(vendor_action) AS vendor_actions
by _time normalized_host
| where recovery_event_count >= <customer_defined_recovery_event_threshold>
| lookup <customer_approved_backup_admin_lookup> user AS users OUTPUT user AS approved_backup_admin
| lookup <customer_maintenance_window_lookup> host AS normalized_host OUTPUT maintenance_status
| where isnull(approved_backup_admin) OR maintenance_status!="approved"
| eval severity="high"
| eval detection_reason="Backup or recovery-control tampering observed outside approved administrative context"
| table _time normalized_host users processes commands actions vendor_actions recovery_event_count severity detection_reason
Splunk Rule 3
ESXi or Virtualization-Adjacent Destructive Activity Correlation
System-Native Format
Splunk SPL correlation search.
Detection Objective
Detect suspicious ESXi, datastore, virtual disk, or virtualization-adjacent activity correlated with ransomware-like file impact or anomalous administrative behavior.
Detection Rationale
· VECT’s reported Windows, Linux, and ESXi scope makes virtualization impact a required detection surface for VMware environments.
· Virtual disk, datastore, snapshot, and ESXi-adjacent activity can rapidly amplify destructive ransomware impact across many systems.
· This rule is scoped to virtualization-impact detection and should not be represented as direct VECT attribution without supporting forensic or malware evidence.
Required Telemetry
· VMware or ESXi administrative telemetry.
· ESXi shell or command telemetry where available.
· Datastore access telemetry where available.
· Endpoint process telemetry from management hosts.
· Identity and authentication telemetry.
· File telemetry for virtual disks or datastore paths where available.
· Host role and asset criticality.
Engineering Implementation Instructions
· Validate VMware, ESXi, vCenter, administrative host, identity, and endpoint data sources before deployment.
· Map virtualization events into Splunk fields such as host, user, src, dest, action, object, resource, command, file_path, and _time.
· Replace placeholder thresholds with customer baselines for VM administration, datastore operations, snapshot activity, and approved maintenance windows.
· Prioritize alerts when virtualization activity occurs from unusual users, unusual source hosts, outside maintenance windows, or near endpoint-confirmed file transformation.
· Correlate with SentinelOne, EDR, backup-platform, and identity telemetry where available.
Detection Quality
DRI
8.4
DRI Justification
The rule targets virtualization-adjacent destructive behavior and anomalous administrative context, making it resilient to static malware indicator changes and aligned to the VECT ESXi risk model.
Operational TCR
7.4
Operational TCR Justification
Operational confidence is moderate to strong where VMware, ESXi, identity, endpoint, and file telemetry are available. Confidence degrades when ESXi or datastore telemetry is incomplete or not normalized into Splunk.
Full-Telemetry TCR
8.7
Full-Telemetry TCR Justification
Full-telemetry confidence is high when virtualization activity, administrative identity, endpoint management-host activity, datastore interaction, and file-impact telemetry can be correlated.
Deployment Limitations
· This rule applies only where VMware, ESXi, vCenter, datastore, or virtualization-management telemetry is available.
· This rule must not treat approved VM administration as malicious without user, source, timing, command, asset, or maintenance-window anomalies.
· This rule must not claim direct ESXi malware execution unless supported by ESXi host telemetry, forensic evidence, or validated malware artifacts.
· This rule requires customer validation of approved virtualization administrators, management hosts, automation jobs, and maintenance windows.
Deployment Tier Guidance
Tier 1
Deploy where Splunk ingests telemetry from virtualization administrators, management workstations, and systems with access to VM or datastore administration.
Tier 2
Expand deployment to vCenter, ESXi management logs, administrative jump hosts, and systems with access to virtualization-management utilities.
Tier 3
Expand deployment across VMware clusters, datastore access points, backup-adjacent virtualization systems, and privileged administration paths.
Tier 4
Deploy broadly where VMware, ESXi, identity, endpoint, backup, and SIEM telemetry can be correlated across enterprise virtualization infrastructure.
Tier Usage Constraints
· Tiering changes virtualization scope, enrichment priority, and response routing; it must not weaken the requirement for anomalous virtualization or datastore context.
· Smaller environments should prioritize vCenter, ESXi administrative access, and management hosts.
· Larger environments should correlate virtualization events with endpoint, identity, backup, and asset-criticality telemetry.
Rule Code
`comment("Splunk SPL correlation search")`
`comment("Rule: ESXi or Virtualization-Adjacent Destructive Activity Correlation")`
`comment("Purpose: Detect suspicious virtualization-adjacent activity associated with destructive ransomware risk.")`
`comment("Deployment note: Replace placeholder macros and thresholds with customer-validated data models, indexes, and baselines.")`
(
index=<vmware_esxi_endpoint_identity_index>
(
action IN ("DatastoreFileDeleted", "DatastoreFileModified", "VmRemoved", "VmReconfigured", "SnapshotRemoved", "SnapshotReconfigured", "HostServiceStopped")
OR command="*esxcli*"
OR command="*vim-cmd*"
OR command="*vmdk*"
OR command="*vmfs*"
OR file_path="*.vmdk*"
OR file_path="*datastore*"
OR process="*esxcli*"
OR process="*vim-cmd*"
)
)
| eval normalized_user=coalesce(user, User, src_user, account)
| eval normalized_src=coalesce(src, src_host, source_host, host)
| eval normalized_dest=coalesce(dest, dest_host, esxi_host, vcenter_host)
| eval normalized_action=coalesce(action, EventType, event_name)
| eval normalized_object=coalesce(object, resource, file_path, vm_name, datastore)
| eval virtualization_signal=if(
match(lower(coalesce(normalized_action, "")), "(datastore|snapshot|vmremoved|vmreconfigured|hostservicestopped)")
OR match(lower(coalesce(command, process, file_path, normalized_object, "")), "(esxcli|vim-cmd|vmdk|vmfs|datastore)"),
1,
0
)
| bucket _time span=<customer_defined_time_window>
| stats
count AS virtualization_event_count
dc(normalized_object) AS distinct_virtualization_objects
max(virtualization_signal) AS virtualization_signal
values(normalized_user) AS users
values(normalized_src) AS sources
values(normalized_action) AS actions
values(normalized_object) AS objects
by _time normalized_dest
| where
virtualization_signal=1
OR virtualization_event_count >= <customer_defined_virtualization_event_threshold>
OR distinct_virtualization_objects >= <customer_defined_virtualization_object_threshold>
| lookup <customer_approved_virtualization_admin_lookup> user AS users OUTPUT user AS approved_virtualization_admin
| lookup <customer_virtualization_maintenance_window_lookup> host AS normalized_dest OUTPUT maintenance_status
| where isnull(approved_virtualization_admin) OR maintenance_status!="approved"
| eval severity="high"
| eval detection_reason="Anomalous ESXi or virtualization-adjacent activity observed outside approved administrative context"
| table _time normalized_dest users sources actions objects virtualization_event_count distinct_virtualization_objects severity detection_reason
Elastic
Elastic Rule 1
Suspicious Process Followed by High-Value File Transformation
System-Native Format
Elastic Security EQL detection rule.
Detection Objective
Detect suspicious process execution followed by file modification or rename activity affecting user data, shared repositories, archives, databases, backups, or virtualization-adjacent files.
Detection Rationale
· VECT’s destructive impact is driven by file transformation behavior, making endpoint process-to-file sequencing a high-confidence detection surface.
· This rule identifies suspicious execution followed by file activity against high-value paths or file types.
· The rule does not depend on .vect, a specific ransom-note name, known hashes, or static VECT identifiers.
Required Telemetry
· Elastic Defend or equivalent endpoint process telemetry.
· File creation, modification, and rename telemetry.
· Process lineage.
· Command-line telemetry.
· User context.
· Host identity.
· Host role or asset criticality.
· File path.
· File extension.
· File size where available.
Engineering Implementation Instructions
· Validate Elastic ECS mappings before deployment, especially event.category, event.action, process.name, process.command_line, file.path, file.extension, host.name, and user.name.
· Scope initial deployment to servers, file servers, administrative workstations, backup-accessible hosts, and systems with access to high-value repositories.
· Validate approved backup agents, indexing tools, data migration utilities, software deployment tools, encryption products, compression utilities, and synchronization clients before enabling broad alerting.
· Tune with host role, asset criticality, and maintenance windows rather than broadly suppressing high-volume file activity.
· Use alert context to confirm initiating process, parent process, user, affected path, affected asset role, and overlap with backup or virtualization assets.
Detection Quality
DRI
8.6
DRI Justification
The rule is behavior-anchored to suspicious execution followed by high-value file transformation, making it resilient to changes in VECT filenames, extensions, ransom-note names, and static indicators.
Operational TCR
7.7
Operational TCR Justification
Operational confidence is strong where Elastic Defend captures process lineage, command line, file events, and host metadata. Confidence may degrade where file event coverage, file-size visibility, or host-role enrichment is incomplete.
Full-Telemetry TCR
8.8
Full-Telemetry TCR Justification
Full-telemetry confidence is high when process events, file events, command-line fields, user context, host role, affected path, and file-scope evidence are available in Elastic.
Deployment Limitations
· This rule must not trigger on file activity alone.
· This rule requires customer validation of approved high-volume file activity.
· This rule must not rely on .vect, ransom-note artifacts, or known hashes as required conditions.
· This rule must not be represented as definitive VECT attribution without supporting sample, sandbox, threat-intelligence, or forensic evidence.
· This rule requires Elastic endpoint and file event coverage sufficient to support ordered EQL correlation.
Deployment Tier Guidance
Tier 1
Deploy on high-risk endpoints, administrative workstations, and systems with direct access to business-critical user data or commonly targeted file paths.
Tier 2
Expand deployment to file servers, backup-accessible systems, database-adjacent systems, and servers with access to operational repositories.
Tier 3
Expand deployment across enterprise server groups, privileged-user workstations, remote administration systems, mapped-drive users, and systems with access to shared repositories.
Tier 4
Deploy broadly across enterprise endpoint and server populations where Elastic telemetry retention, host metadata, and SOC capacity support wide-scale behavioral detection.
Tier Usage Constraints
· Tiering changes deployment scope, enrichment priority, and response routing; it must not weaken detection evidence requirements.
· Smaller environments should prioritize high-value assets and shared-storage access points.
· Larger environments should enrich Elastic detections with host role, user context, asset criticality, backup activity, and virtualization activity where available.
Rule Code
/* Elastic Security EQL detection rule
Rule: Suspicious Process Followed by High-Value File Transformation
Purpose: Detect suspicious process execution followed by ransomware-like file transformation.
Deployment note: Validate ECS field mappings, event.action values, and allowlists before deployment.
*/
sequence by host.id with maxspan=5m
[process where event.category == "process" and event.type == "start" and
(
process.command_line : ("*\\Temp\\*", "*\\AppData\\*", "*\\ProgramData\\*", "*\\Users\\Public\\*", "*\\Downloads\\*", "*\\Desktop\\*",
"*/tmp/*", "*/var/tmp/*", "*/dev/shm/*", "*powershell*", "*cmd.exe*", "*wscript*", "*cscript*",
"*rundll32*", "*regsvr32*", "*bash*", "* sh *")
or process.name : ("powershell.exe", "cmd.exe", "wscript.exe", "cscript.exe", "rundll32.exe", "regsvr32.exe", "bash", "sh")
)
and not process.name : ("veeam*", "commvault*", "rubrik*", "cohesity*", "backup*", "onedrive*", "dropbox*", "splunk*")
]
[file where event.category == "file" and event.action : ("creation", "modification", "rename", "file_create", "file_modify", "file_rename") and
(
file.path : ("*\\Users\\*", "*\\Shares\\*", "*\\Documents\\*", "*\\Desktop\\*", "*\\Downloads\\*", "*\\Finance\\*", "*\\HR\\*", "*\\Legal\\*",
"*/home/*", "*/shares/*", "*/finance/*", "*/hr/*", "*/legal/*", "*datastore*", "*.vmdk", "*.vhdx", "*.sql", "*.bak", "*.zip", "*.7z", "*.rar")
)
]
Elastic Rule 2
File Transformation Followed by Ransom-Note Staging
System-Native Format
Elastic Security EQL detection rule.
Detection Objective
Detect high-value file modification or rename activity followed by ransom-note-like artifact creation within the same host context.
Detection Rationale
· Ransom-note creation alone is not sufficient for high-confidence detection.
· Ransom-note staging becomes meaningful when it occurs during or after suspicious file modification activity.
· This rule treats ransom-note artifacts as supporting behavior rather than standalone VECT identity.
· The sequence order prioritizes file transformation first and ransom-note staging second, which better aligns with ransomware impact behavior.
Required Telemetry
· File creation telemetry.
· File modification telemetry.
· File rename telemetry where available.
· Process execution telemetry where available.
· Process lineage where available.
· Command-line telemetry where available.
· User context.
· Host identity.
· Host role or asset criticality.
· File path.
Engineering Implementation Instructions
· Validate Elastic ECS mappings before deployment, especially event.category, event.action, file.path, file.name, file.extension, process.name, process.command_line, host.name, and user.name.
· Validate legitimate readme, installer, helpdesk, software deployment, script, update, and administrative automation behavior before broad deployment.
· Prioritize alerts where ransom-note-like files are created after file modification across user paths, shared repositories, servers, or high-value directories.
· Treat isolated ransom-note-like files as triage context unless paired with file modification, suspicious execution, or asset criticality.
· Do not require exact VECT ransom-note naming because note names can change across variants, affiliates, and copycat tooling.
Detection Quality
DRI
8.2
DRI Justification
The rule is anchored to file transformation followed by ransom-note staging, making it stronger than note-name-only detection and more resilient to single-artifact changes.
Operational TCR
7.6
Operational TCR Justification
Operational confidence is strong where Elastic captures file modification, file creation, process context, host metadata, and user context. Confidence may degrade where file events lack initiating-process attribution or where file creation telemetry is incomplete.
Full-Telemetry TCR
8.6
Full-Telemetry TCR Justification
Full-telemetry confidence is high when high-value file modification can be tied to ransom-note-like artifact creation, affected directory scope, host role, user context, and process context.
Deployment Limitations
· This rule must not fire solely on a ransom-note filename.
· This rule must not depend only on !!!READ_ME!!!.txt, !!!_READ_ME_!!!.txt, .vect, or other single artifacts.
· This rule should escalate suspicious ransomware activity, not independently prove VECT attribution.
· This rule requires customer validation of legitimate text, HTML, installer, help, and update-file generation behavior.
· This rule requires file telemetry sufficient to support ordered EQL correlation.
Deployment Tier Guidance
Tier 1
Deploy on high-risk endpoints and administrative workstations where file transformation followed by ransom-note staging would indicate immediate user-data or local-data impact.
Tier 2
Expand deployment to file servers, shared repositories, backup-accessible systems, and systems that commonly host business-critical documents or operational data.
Tier 3
Expand deployment across enterprise servers, mapped-drive users, remote administration systems, and systems with access to multiple shared directories or high-value repositories.
Tier 4
Deploy broadly across endpoint and server populations where file creation telemetry, Elastic enrichment, and alert triage capacity are available at scale.
Tier Usage Constraints
· Tiering changes deployment scope and enrichment priority; it must not lower the requirement for file-transformation and ransomware-like context.
· Smaller environments should prioritize high-value directories and shared repositories.
· Larger environments should enrich ransom-note alerts with endpoint file activity, user context, host role, and affected-directory scope.
Rule Code
/* Elastic Security EQL detection rule
Rule: File Transformation Followed by Ransom-Note Staging
Purpose: Detect high-value file transformation followed by ransom-note-like artifact staging.
Deployment note: Validate ECS field mappings, event.action values, and allowlists before deployment.
*/
sequence by host.id with maxspan=10m
[file where event.category == "file" and event.action : ("creation", "modification", "rename", "file_create", "file_modify", "file_rename") and
(
file.path : ("*\\Users\\*", "*\\Shares\\*", "*\\Documents\\*", "*\\Desktop\\*", "*\\Downloads\\*",
"*/home/*", "*/shares/*", "*datastore*", "*.vmdk", "*.vhdx", "*.sql", "*.bak", "*.zip", "*.7z", "*.rar")
)
]
[file where event.category == "file" and event.action : ("creation", "file_create", "modification", "file_modify") and
(
file.name : ("*read_me*", "*readme*", "*decrypt*", "*restore*", "*recover*", "*how_to*", "*!!!*")
or file.path : ("*read_me*", "*readme*", "*decrypt*", "*restore*", "*recover*", "*how_to*", "*!!!*")
)
and file.extension : ("txt", "html", "hta")
and not process.name : ("msiexec.exe", "setup.exe", "installer*", "updater*", "onedrive*", "dropbox*")
]
Elastic Rule 3
Recovery-Path and Virtualization-Adjacent Interference Activity
System-Native Format
Elastic Security EQL detection rule.
Detection Objective
Detect suspicious process activity involving backup, recovery, snapshot, logging, or virtualization-adjacent operations that may increase destructive ransomware impact.
Detection Rationale
· VECT-aligned destructive risk increases when recovery paths are impaired before or during file transformation.
· This rule targets endpoint-visible activity involving backup suppression, shadow copy interference, recovery-control tampering, event-log clearing, and virtualization-adjacent commands or paths.
· The rule supports the report’s recovery-first risk model without claiming that Elastic alone can observe every backup-platform, cloud-control, or ESXi management event.
· This rule is written as a focused process activity detection rather than an ordered sequence because the target behavior can be high-confidence from command context alone when properly scoped and validated.
Required Telemetry
· Process execution telemetry.
· Command-line telemetry.
· Process lineage.
· User context.
· Host identity.
· Host role or asset criticality.
· Endpoint tamper events where available.
· File modification or deletion telemetry where available.
Engineering Implementation Instructions
· Validate Elastic ECS mappings before deployment, especially event.category, event.action, process.name, process.command_line, file.path, host.name, and user.name.
· Scope this rule to systems with access to backup tooling, recovery utilities, virtualization management utilities, administrative functions, and high-value storage.
· Validate approved administrative scripts, backup-management tools, virtualization tools, recovery operations, event-log maintenance, and maintenance workflows before broad deployment.
· Prioritize alerts when the initiating process also touches user data, shared storage, virtual disks, backup directories, or administrative recovery tooling.
· Correlate Elastic detections with backup-platform, VMware, identity, and SIEM telemetry where available.
Detection Quality
DRI
8.4
DRI Justification
The rule targets recovery-path interference and virtualization-adjacent destructive preparation, which are durable ransomware impact behaviors and less dependent on static VECT artifacts.
Operational TCR
7.5
Operational TCR Justification
Operational confidence is strong where Elastic captures command line, process lineage, host role, and user context. Confidence varies based on visibility into backup utilities, virtualization tooling, and administrative scripts.
Full-Telemetry TCR
8.6
Full-Telemetry TCR Justification
Full-telemetry confidence is high when endpoint activity can be correlated with backup, virtualization, identity, and SIEM telemetry.
Deployment Limitations
· This rule must not treat legitimate backup administration as malicious without user, host, timing, process, or asset-context anomalies.
· This rule must not claim direct visibility into cloud backup-control changes unless cloud audit telemetry is available from another source.
· This rule must not claim direct ESXi detection unless the monitored system has visibility into ESXi management activity, datastore interaction, or virtualization-adjacent file access.
· This rule requires customer validation of approved backup, recovery, logging, and virtualization tools.
Deployment Tier Guidance
Tier 1
Deploy on administrative workstations and endpoints with local recovery tooling, shadow copy access, or elevated administrative capability.
Tier 2
Expand deployment to backup-accessible systems, servers with recovery tooling, administrative jump hosts, and systems that interact with high-value storage or backup paths.
Tier 3
Expand deployment across server groups, privileged-user workstations, remote administration systems, and systems with access to virtualization management utilities or backup staging paths.
Tier 4
Deploy broadly where Elastic telemetry can be enriched with backup-platform, virtualization, identity, and SIEM data to identify recovery-path interference before destructive impact expands.
Tier Usage Constraints
· Tiering changes deployment scope and enrichment priority; it must not lower the requirement for recovery-path or virtualization-adjacent context.
· Smaller environments should prioritize systems with backup, recovery, administrative, or virtualization access.
· Larger environments should correlate Elastic detections with backup, virtualization, identity, and SIEM telemetry where available.
Rule Code
/* Elastic Security EQL detection rule
Rule: Recovery-Path and Virtualization-Adjacent Interference Activity
Purpose: Detect endpoint-visible recovery-path or virtualization-adjacent interference activity.
Deployment note: Validate ECS field mappings, event.action values, and allowlists before deployment.
*/
process where event.category == "process" and event.type == "start" and
(
process.command_line : ("*vssadmin*", "*delete shadows*", "*shadowcopy*", "*wmic shadowcopy*", "*wbadmin*",
"*bcdedit*", "*recoveryenabled*", "*bootstatuspolicy*", "*wevtutil cl*", "*Clear-EventLog*",
"*backup*", "*snapshot*", "*restore*", "*vault*", "*vmdk*", "*vmfs*", "*esxcli*", "*vim-cmd*")
)
and
(
process.command_line : ("*delete*", "*remove*", "*disable*", "*stop*", "*clear*", "*modify*", "*set*")
)
and not process.name : ("veeam*", "commvault*", "rubrik*", "cohesity*", "backup*")
QRadar
QRadar Rule 1
Correlated Mass File Transformation with Ransomware-Like Context
System-Native Format
QRadar AQL saved search suitable for Custom Rules Engine implementation after log-source and custom-property validation.
Detection Objective
Detect high-volume file modification, rename, or creation activity correlated with suspicious process, user, host, or high-value repository context.
Detection Rationale
· VECT-aligned destructive impact is primarily file-system driven, making mass file transformation the highest-value detection surface.
· QRadar can provide useful coverage when upstream endpoint, file, and EDR telemetry is normalized into searchable event fields.
· This rule is designed to measure file-event volume and distinct file or path spread across a grouped host, user, process, and time window.
· This rule is designed to identify ransomware-wiper behavior without requiring .vect, exact ransom-note names, known hashes, or VECT-specific attribution.
Required Telemetry
· Endpoint process telemetry.
· File creation telemetry.
· File modification telemetry.
· File rename telemetry where available.
· EDR or file-monitoring telemetry.
· User context.
· Host identity.
· Asset role or criticality.
· File path.
· File name.
· File size where available.
· Initiating process where available.
Engineering Implementation Instructions
· Validate QRadar log sources before deployment, including EDR, file-integrity monitoring, Windows event logs, Linux audit logs, Sysmon, endpoint telemetry, and file server logs where available.
· Validate custom properties for process name, command line, file path, file name, file size, file action, initiating process, username, source host, destination host, and endpoint product action.
· Convert this AQL into a QRadar saved search or CRE rule only after confirming the required fields exist in the customer deployment.
· Use customer-specific baselines for high-volume file activity across endpoints, file servers, administrative workstations, backup-accessible systems, and high-value repositories.
· Validate approved backup jobs, indexing, software deployment, data migration, compression, encryption tools, synchronization clients, and file-management automation before enabling broad alerting.
· Prioritize offenses where file transformation overlaps with suspicious process context, privileged user context, critical asset role, or high-value file paths.
Detection Quality
DRI
8.0
DRI Justification
The rule is anchored to mass file transformation correlated with ransomware-like context, making it resilient to static VECT indicator changes while still requiring enough context to avoid generic file-volume alerting.
Operational TCR
7.1
Operational TCR Justification
Operational confidence is moderate because QRadar depends on upstream telemetry quality, custom-property parsing, and normalization for file actions, process context, and file path fields.
Full-Telemetry TCR
8.3
Full-Telemetry TCR Justification
Full-telemetry confidence is strong when QRadar receives complete endpoint, file, process, user, host-role, and file-scope telemetry from normalized log sources.
Deployment Limitations
· This rule must not trigger on file volume alone.
· This rule requires validated custom properties and source-specific parsing before deployment.
· This rule must not rely solely on .vect, ransom-note strings, file extensions, or known hashes.
· This rule must not be represented as definitive VECT attribution without validated malware sample, sandbox, threat-intelligence, or forensic evidence.
· This rule should not be deployed broadly until file-volume baselines and approved high-volume workflows are reviewed.
· QRadar rule performance must be reviewed before production deployment because broad event scans and custom-property logic can be expensive in large environments.
Deployment Tier Guidance
Tier 1
Deploy against high-risk endpoints, administrative workstations, and systems with access to business-critical user data or sensitive local repositories where endpoint and file events are already available in QRadar.
Tier 2
Expand deployment to file servers, shared repositories, backup-accessible systems, database-adjacent systems, and operational data stores where file-monitoring or EDR telemetry is normalized.
Tier 3
Expand deployment across enterprise server groups, mapped-drive users, administrative systems, and high-value shared-storage access points where file activity can be tied to user and host context.
Tier 4
Deploy broadly where QRadar receives endpoint, file, user, asset, and host-role telemetry at scale and where rule-performance review confirms the search can run safely.
Tier Usage Constraints
· Tiering changes deployment scope, enrichment priority, and offense routing; it must not weaken the requirement for file-transformation and ransomware-like context.
· Smaller environments should prioritize high-value repositories and systems with strong endpoint-to-file telemetry.
· Larger environments should enrich QRadar offenses with asset role, user context, endpoint product context, backup activity, and virtualization context where available.
· QRadar deployments should avoid overly broad regular-expression matching or payload searches when normalized fields can support the logic.
Rule Code
-- QRadar AQL saved search suitable for CRE implementation after custom-property validation.
-- Rule: Correlated Mass File Transformation with Ransomware-Like Context
-- Purpose: Detect high-volume file transformation correlated with ransomware-like context.
-- Deployment note: Replace placeholder log source names, custom properties, thresholds, and reference sets with customer-validated values.
SELECT
DATEFORMAT(starttime, 'yyyy-MM-dd HH:mm:ss') AS event_time,
sourceip,
destinationip,
username,
LOGSOURCENAME(logsourceid) AS log_source,
"Process Name" AS process_name,
"Command Line" AS command_line,
COUNT(*) AS file_event_count,
COUNT(DISTINCT "File Name") AS distinct_file_count,
COUNT(DISTINCT "File Path") AS distinct_path_count
FROM events
WHERE
LOGSOURCENAME(logsourceid) IN (<customer_endpoint_or_file_log_sources>)
AND (
"File Action" IN ('created', 'modified', 'renamed', 'file_create', 'file_modify', 'file_rename')
OR QIDNAME(qid) ILIKE '%file created%'
OR QIDNAME(qid) ILIKE '%file modified%'
OR QIDNAME(qid) ILIKE '%file renamed%'
)
AND (
"File Path" ILIKE '%\\Users\\%'
OR "File Path" ILIKE '%\\Shares\\%'
OR "File Path" ILIKE '%\\Documents\\%'
OR "File Path" ILIKE '%\\Desktop\\%'
OR "File Path" ILIKE '%\\Downloads\\%'
OR "File Path" ILIKE '%\\Finance\\%'
OR "File Path" ILIKE '%\\HR\\%'
OR "File Path" ILIKE '%\\Legal\\%'
OR "File Path" ILIKE '%/home/%'
OR "File Path" ILIKE '%/shares/%'
OR "File Path" ILIKE '%datastore%'
OR "File Name" ILIKE '%.vmdk'
OR "File Name" ILIKE '%.vhdx'
OR "File Name" ILIKE '%.sql'
OR "File Name" ILIKE '%.bak'
OR "File Name" ILIKE '%.zip'
OR "File Name" ILIKE '%.7z'
OR "File Name" ILIKE '%.rar'
)
AND NOT REFERENCESETCONTAINS('<customer_approved_high_volume_file_tools>', "Process Name")
GROUP BY
sourceip,
destinationip,
username,
LOGSOURCENAME(logsourceid),
"Process Name",
"Command Line"
HAVING
COUNT(*) >= <customer_defined_file_event_threshold>
OR COUNT(DISTINCT "File Name") >= <customer_defined_distinct_file_threshold>
OR COUNT(DISTINCT "File Path") >= <customer_defined_distinct_path_threshold>
LAST <customer_defined_time_window>
QRadar Rule 2
Recovery-Path or Virtualization-Control Tampering with Suspicious Administrative Context
System-Native Format
QRadar AQL saved search suitable for Custom Rules Engine implementation after log-source and custom-property validation.
Detection Objective
Detect suspicious backup, recovery, snapshot, restore, vault, ESXi, datastore, or virtualization-control activity occurring outside approved administrative context.
Detection Rationale
· VECT-aligned destructive risk increases when recovery paths or virtualization assets are impaired before or during file impact.
· QRadar can support this detection where backup-platform, VMware, endpoint command-line, identity, and administrative telemetry are normalized into events.
· This rule detects destructive-impact amplification and suspicious administrative behavior rather than claiming direct VECT attribution.
Required Telemetry
· Endpoint command-line telemetry.
· Backup-platform telemetry.
· VMware, ESXi, or vCenter telemetry where available.
· Identity and authentication telemetry.
· Administrative action logs.
· User context.
· Host identity.
· Asset role or criticality.
· Source and destination context.
· Backup, snapshot, restore, vault, datastore, or virtualization action fields.
Engineering Implementation Instructions
· Validate QRadar log sources before deployment, including backup platforms, VMware, vCenter, ESXi, identity providers, EDR, endpoint process telemetry, and administrative control-plane logs.
· Validate custom properties for command line, process name, administrative action, object, resource, snapshot name, datastore path, VM name, backup job, vault name, username, source host, and destination host.
· Convert this AQL into a QRadar saved search or CRE rule only after confirming the required fields exist in the customer deployment.
· Validate approved backup administrators, virtualization administrators, maintenance windows, recovery automation, backup jobs, snapshot workflows, and approved administrative hosts before enabling broad alerting.
· Prioritize offenses where recovery-path or virtualization-control activity overlaps with suspicious process execution, privileged-user anomalies, high-value systems, endpoint-confirmed file transformation, or activity outside approved maintenance windows.
Detection Quality
DRI
8.1
DRI Justification
The rule targets recovery-path and virtualization-control tampering with suspicious administrative context, which are durable ransomware impact behaviors and do not depend on static VECT indicators.
Operational TCR
7.0
Operational TCR Justification
Operational confidence is moderate because QRadar depends on upstream backup, VMware, identity, endpoint, and administrative telemetry quality, as well as customer-specific custom-property normalization.
Full-Telemetry TCR
8.4
Full-Telemetry TCR Justification
Full-telemetry confidence is strong when backup-platform, VMware, identity, administrative, endpoint, and asset-role telemetry are available in QRadar with usable custom properties.
Deployment Limitations
· This rule must not treat legitimate backup or virtualization administration as malicious without identity, timing, source, host, process, object, or asset-context anomalies.
· This rule must not claim direct VECT detection unless supported by malware, forensic, or threat-intelligence evidence.
· This rule must not rely only on generic command keywords such as backup, snapshot, restore, vmdk, or esxcli.
· This rule requires customer validation of backup platforms, virtualization platforms, administrative workflows, maintenance windows, privileged accounts, and approved automation.
· QRadar rule performance must be reviewed before deployment because broad scope, inefficient regular expressions, or payload-heavy tests can create operational issues.
Deployment Tier Guidance
Tier 1
Deploy against administrative workstations, backup-accessible systems, and endpoints with local recovery tooling, elevated administrative capability, or access to virtualization-management utilities.
Tier 2
Expand deployment to backup servers, recovery-management systems, vCenter, ESXi management logs, restore-control systems, administrative jump hosts, and servers with access to backup staging paths or recovery repositories.
Tier 3
Expand deployment across enterprise server groups, privileged-user workstations, administrative systems, VMware clusters, datastore access points, and systems with access to recovery-control interfaces.
Tier 4
Deploy broadly where QRadar receives backup-platform, VMware, endpoint, identity, asset, and administrative telemetry at scale and where rule-performance review confirms the search can run safely.
Tier Usage Constraints
· Tiering changes deployment scope, enrichment priority, and offense routing; it must not weaken the requirement for recovery-path, virtualization-control, or suspicious administrative context.
· Smaller environments should prioritize systems with backup, recovery, virtualization, administrative, or storage-control access.
· Larger environments should correlate QRadar offenses with endpoint, identity, file, backup, virtualization, and asset-criticality telemetry where available.
· QRadar deployments should prefer normalized fields and reference sets over broad payload searches where possible.
Rule Code
-- QRadar AQL saved search suitable for CRE implementation after custom-property validation.
-- Rule: Recovery-Path or Virtualization-Control Tampering with Suspicious Administrative Context
-- Purpose: Detect backup, recovery, snapshot, restore, ESXi, or virtualization-control tampering outside approved administrative context.
-- Deployment note: Replace placeholder log sources, custom properties, thresholds, windows, and reference sets with customer-validated values.
SELECT
DATEFORMAT(starttime, 'yyyy-MM-dd HH:mm:ss') AS event_time,
sourceip,
destinationip,
username,
LOGSOURCENAME(logsourceid) AS log_source,
"Process Name" AS process_name,
"Command Line" AS command_line,
"Administrative Action" AS administrative_action,
"Object Name" AS object_name,
"Resource Name" AS resource_name,
COUNT(*) AS suspicious_admin_event_count
FROM events
WHERE
LOGSOURCENAME(logsourceid) IN (<customer_backup_vmware_identity_endpoint_log_sources>)
AND (
"Command Line" ILIKE '%vssadmin%'
OR "Command Line" ILIKE '%delete shadows%'
OR "Command Line" ILIKE '%shadowcopy%'
OR "Command Line" ILIKE '%wbadmin%'
OR "Command Line" ILIKE '%bcdedit%'
OR "Command Line" ILIKE '%recoveryenabled%'
OR "Command Line" ILIKE '%bootstatuspolicy%'
OR "Command Line" ILIKE '%wevtutil cl%'
OR "Command Line" ILIKE '%Clear-EventLog%'
OR "Command Line" ILIKE '%backup%'
OR "Command Line" ILIKE '%snapshot%'
OR "Command Line" ILIKE '%restore%'
OR "Command Line" ILIKE '%vault%'
OR "Command Line" ILIKE '%vmdk%'
OR "Command Line" ILIKE '%vmfs%'
OR "Command Line" ILIKE '%esxcli%'
OR "Command Line" ILIKE '%vim-cmd%'
OR "Administrative Action" IN ('delete_snapshot', 'remove_snapshot', 'disable_backup', 'delete_restore_point', 'modify_retention', 'delete_vault', 'disable_protection', 'vm_removed', 'vm_reconfigured', 'snapshot_removed', 'datastore_file_deleted')
OR QIDNAME(qid) ILIKE '%snapshot removed%'
OR QIDNAME(qid) ILIKE '%backup disabled%'
OR QIDNAME(qid) ILIKE '%restore point deleted%'
OR QIDNAME(qid) ILIKE '%datastore file deleted%'
OR QIDNAME(qid) ILIKE '%vm removed%'
)
AND NOT REFERENCESETCONTAINS('<customer_approved_backup_admins>', username)
AND NOT REFERENCESETCONTAINS('<customer_approved_virtualization_admins>', username)
AND NOT REFERENCESETCONTAINS('<customer_approved_admin_hosts>', sourceip)
GROUP BY
sourceip,
destinationip,
username,
LOGSOURCENAME(logsourceid),
"Process Name",
"Command Line",
"Administrative Action",
"Object Name",
"Resource Name"
HAVING
COUNT(*) >= <customer_defined_admin_event_threshold>
LAST <customer_defined_time_window>
SIGMA
SIGMA Rule 1
Ransomware-Like File Transformation Across High-Value Paths
System-Native Format
SIGMA YAML detection rule.
Detection Objective
Detect ransomware-like file creation, modification, or rename activity affecting high-value user, shared, backup-adjacent, archive, database, or virtualization-adjacent paths.
Detection Rationale
· VECT-aligned destructive impact is file-system driven, making high-value file transformation a strong portable detection opportunity.
· This rule avoids depending on command-line fields because many file-event log sources do not reliably preserve full command-line context.
· This rule uses file-event fields and initiating image context where available, making it more appropriate for a SIGMA file_event rule.
· This rule does not depend on .vect, exact ransom-note names, known hashes, or VECT-specific attribution.
Required Telemetry
· File creation telemetry.
· File modification telemetry.
· File rename telemetry where available.
· File path.
· File name.
· File extension.
· Initiating image or process field where available.
· User context.
· Host identity.
· Endpoint or file-monitoring product action.
Engineering Implementation Instructions
· Validate backend field mappings before deployment because SIGMA translation depends on the target SIEM, log source, parser, and field normalization.
· Confirm whether the backend provides Image, InitiatingProcessFileName, ProcessName, or equivalent initiating-process fields for file events.
· Convert and test the rule using the customer’s approved SIGMA translation workflow before production deployment.
· Validate file-event coverage for Windows endpoints, file servers, and systems with access to shared repositories or high-value storage.
· Review approved backup agents, indexing tools, synchronization clients, data migration utilities, software deployment tools, compression tools, encryption tools, and administrative file-management automation before enabling broad alerting.
· Prioritize translated alerts where file transformation affects high-value repositories, shared paths, backup-accessible systems, database files, archives, or virtualization-adjacent file types.
Detection Quality
DRI
7.8
DRI Justification
The rule is behavior-anchored to high-value file transformation and avoids fragile VECT-specific artifacts, making it stronger than extension-only or ransom-note-only logic.
Operational TCR
6.9
Operational TCR Justification
Operational confidence is moderate because SIGMA depends on backend translation quality, file-event availability, initiating-process field support, and consistent path normalization.
Full-Telemetry TCR
8.2
Full-Telemetry TCR Justification
Full-telemetry confidence is strong when the backend supports file action, file path, file name, file extension, initiating image, user, host, and endpoint product fields with consistent normalization.
Deployment Limitations
· This rule must not be deployed without backend translation validation.
· This rule must not trigger on file activity alone without high-value path, file-type, or initiating-process context.
· This rule must not rely on .vect, ransom-note artifacts, known hashes, or exact VECT strings as required conditions.
· This rule must not be represented as definitive VECT attribution without malware sample, sandbox, threat-intelligence, or forensic support.
· This rule may require backend-specific tuning after conversion because SIGMA portability does not guarantee equivalent field semantics across SIEMs.
Deployment Tier Guidance
Tier 1
Deploy after translation validation on high-risk endpoints, administrative workstations, and systems with direct access to business-critical user data or commonly targeted file paths.
Tier 2
Expand deployment to file servers, shared repositories, backup-accessible systems, database-adjacent systems, and systems that host operational data.
Tier 3
Expand deployment across enterprise server groups, mapped-drive users, privileged-user workstations, remote administration systems, and high-value shared-storage access points.
Tier 4
Deploy broadly where endpoint and file telemetry are consistently normalized in the target SIEM and where translated SIGMA detections can be tested and maintained at enterprise scale.
Tier Usage Constraints
· Tiering changes deployment scope, backend translation priority, enrichment, and alert routing; it must not weaken detection evidence requirements.
· Smaller environments should prioritize systems with direct access to high-value files and shared repositories.
· Larger environments should enrich translated alerts with host role, user context, asset criticality, backup activity, and virtualization context where available.
· SIGMA tiering must account for backend differences in field names, event categories, and supported modifiers.
Rule Code
title: Ransomware-Like File Transformation Across High-Value Paths
id: 8f0cdb3e-c6f4-48e6-94f5-341e447c2d8e
status: experimental
description: Detects ransomware-like file transformation across high-value user, shared, backup-adjacent, archive, database, or virtualization-adjacent paths.
author: CyberDax
date: 2026-05-01
references:
- https://research.checkpoint.com/2026/vect-ransomware-by-design-wiper-by-accident/
logsource:
category: file_event
product: windows
detection:
selection_file_action:
EventType|contains:
- File Creation
- File Modification
- File Rename
TargetFilename|contains:
- '\Users\'
- '\Shares\'
- '\Documents\'
- '\Desktop\'
- '\Downloads\'
- '\Finance\'
- '\HR\'
- '\Legal\'
- '\Datastore\'
- '.vmdk'
- '.vhdx'
- '.sql'
- '.bak'
- '.zip'
- '.7z'
- '.rar'
selection_initiating_image_optional:
Image|contains:
- '\Temp\'
- '\AppData\'
- '\ProgramData\'
- '\Users\Public\'
- '\Downloads\'
- '\Desktop\'
- 'powershell.exe'
- 'cmd.exe'
- 'wscript.exe'
- 'cscript.exe'
- 'rundll32.exe'
- 'regsvr32.exe'
filter_approved_tools:
Image|contains:
- 'veeam'
- 'commvault'
- 'rubrik'
- 'cohesity'
- 'backup'
- 'onedrive'
- 'dropbox'
- 'splunk'
condition: selection_file_action and not filter_approved_tools
fields:
- UtcTime
- Computer
- User
- Image
- TargetFilename
- EventType
falsepositives:
- Approved backup activity
- File indexing
- Software deployment
- Data migration
- Synchronization clients
- Approved encryption or compression workflows
level: high
tags:
- attack.impact
- attack.t1486
- attack.t1485
SIGMA Rule 2
Recovery Suppression or Virtualization-Adjacent Interference Activity
System-Native Format
SIGMA YAML detection rule.
Detection Objective
Detect suspicious command-line or process activity involving backup suppression, shadow copy deletion, recovery-control tampering, event-log clearing, or virtualization-adjacent operations.
Detection Rationale
· VECT-aligned destructive risk increases when recovery paths, logs, snapshots, or virtualization assets are impaired before or during file impact.
· SIGMA can express a portable rule for suspicious recovery-path and virtualization-adjacent command activity across compatible backends.
· This rule detects destructive-impact amplification and suspicious administrative behavior rather than definitive VECT attribution.
Required Telemetry
· Process creation telemetry.
· Command-line telemetry.
· User context.
· Host identity.
· Parent process where available.
· Process image.
· Endpoint product action where available.
· Administrative tool execution telemetry where available.
Engineering Implementation Instructions
· Validate backend field mappings before deployment because SIGMA translation depends on the target SIEM, log source, parser, and field normalization.
· Convert and test the rule using the customer’s approved SIGMA translation workflow before production deployment.
· Validate command-line capture for Windows and Linux systems where the translated rule will be used.
· Review approved backup administrators, virtualization administrators, recovery workflows, event-log maintenance, administrative scripts, and automation jobs before enabling broad alerting.
· Prioritize translated alerts when recovery-path or virtualization-adjacent activity occurs on administrative workstations, servers, backup-accessible systems, virtualization management hosts, or high-value storage systems.
Detection Quality
DRI
7.9
DRI Justification
The rule targets recovery-path interference and virtualization-adjacent destructive preparation, which are durable ransomware impact behaviors and less dependent on static VECT indicators.
Operational TCR
6.8
Operational TCR Justification
Operational confidence is moderate because SIGMA depends on backend translation quality, command-line visibility, and the target SIEM’s ability to preserve process fields consistently.
Full-Telemetry TCR
8.1
Full-Telemetry TCR Justification
Full-telemetry confidence is strong when the backend supports complete process creation, command line, user, host, parent process, and administrative tool context.
Deployment Limitations
· This rule must not be deployed without backend translation validation.
· This rule must not treat legitimate backup, recovery, event-log, or virtualization administration as malicious without user, host, timing, process, or asset-context anomalies.
· This rule must not claim direct VECT detection unless supported by malware, forensic, or threat-intelligence evidence.
· This rule must not rely only on generic command keywords without destructive or recovery-path context.
· This rule may require backend-specific tuning after conversion because SIGMA portability does not guarantee equivalent detection behavior across SIEMs.
Deployment Tier Guidance
Tier 1
Deploy after translation validation on administrative workstations and endpoints with local recovery tooling, shadow copy access, event-log administration access, or elevated administrative capability.
Tier 2
Expand deployment to backup-accessible systems, servers with recovery tooling, administrative jump hosts, and systems that interact with high-value storage or backup paths.
Tier 3
Expand deployment across server groups, privileged-user workstations, remote administration systems, virtualization-management hosts, and systems with access to backup staging paths.
Tier 4
Deploy broadly where process and command-line telemetry are consistently normalized in the target SIEM and where translated SIGMA detections can be tested and maintained at enterprise scale.
Tier Usage Constraints
· Tiering changes deployment scope, backend translation priority, enrichment, and alert routing; it must not lower the requirement for recovery-path or virtualization-adjacent context.
· Smaller environments should prioritize systems with backup, recovery, administrative, or virtualization access.
· Larger environments should enrich translated alerts with identity, host role, asset criticality, backup activity, virtualization activity, and maintenance-window context.
· SIGMA tiering must account for backend differences in command-line fields, process fields, event categories, and supported modifiers.
Rule Code
title: Recovery Suppression Or Virtualization-Adjacent Interference Activity
id: 2c0c85ab-4d36-4df2-a8b2-1556da8e45f0
status: experimental
description: Detects suspicious recovery suppression, logging interference, backup-related, or virtualization-adjacent command activity associated with destructive ransomware impact.
author: CyberDax
date: 2026-05-01
references:
- https://research.checkpoint.com/2026/vect-ransomware-by-design-wiper-by-accident/
logsource:
category: process_creation
detection:
selection_recovery_or_virtualization_terms:
CommandLine|contains:
- 'vssadmin'
- 'delete shadows'
- 'shadowcopy'
- 'wmic shadowcopy'
- 'wbadmin'
- 'bcdedit'
- 'recoveryenabled'
- 'bootstatuspolicy'
- 'wevtutil cl'
- 'Clear-EventLog'
- 'backup'
- 'snapshot'
- 'restore'
- 'vault'
- 'vmdk'
- 'vmfs'
- 'esxcli'
- 'vim-cmd'
selection_destructive_or_control_action:
CommandLine|contains:
- 'delete'
- 'remove'
- 'disable'
- 'stop'
- 'clear'
- 'modify'
- 'set'
filter_approved_tools:
Image|contains:
- 'veeam'
- 'commvault'
- 'rubrik'
- 'cohesity'
- 'backup'
condition: selection_recovery_or_virtualization_terms and selection_destructive_or_control_action and not filter_approved_tools
fields:
- UtcTime
- Computer
- User
- Image
- ParentImage
- CommandLine
falsepositives:
- Approved backup administration
- Approved virtualization administration
- Approved event-log maintenance
- Recovery testing
- Administrative maintenance windows
level: high
tags:
- attack.impact
- attack.t1490
- attack.t1489
- attack.t1562
YARA
YARA Rule 1
Conditional VECT Ransomware Sample Classification
System-Native Format
YARA rule for malware sample triage, repository scanning, sandbox classification, and incident-response enrichment.
Detection Objective
Classify suspected VECT ransomware samples using a compound set of public artifact traits, while avoiding overreliance on a single fragile indicator.
Detection Rationale
· VECT has enough public sample and artifact reporting to support one conditional YARA classification rule.
· Check Point reports that VECT 2.0 has Windows, Linux, and ESXi variants, uses a shared codebase, embeds libsodium, uses ChaCha20-IETF with 12-byte nonces, appends the .vect extension, and creates a ransom note named !!!READ_ME!!!.txt. (research.checkpoint.com)
· MalwareBazaar currently lists a public VECT_Ransomware YARA rule with recent sightings, supporting the existence of sample-level classification opportunities. (bazaar.abuse.ch)
· This rule is intentionally scoped as conditional classification because VECT may change file extension, note name, strings, packing, compiler output, or embedded library artifacts.
· This rule must not be used as a substitute for endpoint, file-transformation, backup-tampering, virtualization-impact, or SIEM-correlation detections.
Required Telemetry
· Malware sample files.
· Endpoint file collection where available.
· Sandbox output where available.
· Malware repository scanning capability.
· File type identification.
· PE and ELF sample handling.
· Extracted strings where available.
· Hashes and sample metadata for enrichment.
· Incident-response evidence packages where available.
Engineering Implementation Instructions
· Use this rule only in malware triage, sandbox, repository scanning, endpoint file collection, or forensic-analysis workflows.
· Validate the rule against known benign binaries that use libsodium, ChaCha20, embedded cryptographic strings, backup tooling, and administrative utilities.
· Validate the rule against available VECT samples, public malware-repository matches, and incident-specific suspicious binaries before operational use.
· Treat a YARA hit as classification or enrichment, not as proof of active ransomware execution.
· Pair any YARA match with endpoint, file-system, process, backup, identity, or virtualization telemetry before making operational severity claims.
· Use hashes as references or enrichment, not as the only matching condition.
· Review the rule if future VECT versions change extension naming, ransom-note naming, packing, compiler output, or embedded cryptographic artifacts.
Detection Quality
DRI
7.6
DRI Justification
The rule uses a compound artifact model rather than single-string matching, which improves resilience compared with extension-only, ransom-note-only, hash-only, or generic crypto-only logic. DRI remains conditional because YARA classification depends on sample availability and may degrade if VECT changes static artifacts.
Operational TCR
6.5
Operational TCR Justification
Operational confidence is moderate when organizations can collect suspicious binaries, scan malware repositories, or analyze samples through sandbox workflows. Confidence is lower for live enterprise detection because YARA alone does not observe active execution or operational impact.
Full-Telemetry TCR
8.1
Full-Telemetry TCR Justification
Full-telemetry confidence is strong in malware-lab, repository-scanning, or forensic workflows where suspicious binaries, extracted strings, file type, sample metadata, and enrichment sources are available.
Deployment Limitations
· This rule must not be deployed as a primary enterprise ransomware detection control.
· This rule must not be used as proof of active file encryption, destructive file transformation, backup tampering, or ESXi impact.
· This rule must not rely only on .vect, ransom-note strings, hashes, libsodium strings, or generic ChaCha20 strings.
· This rule may miss packed, obfuscated, refactored, rebuilt, or artifact-changed VECT variants.
· This rule may require separate validation for PE and ELF samples because VECT is reported across Windows, Linux, and ESXi variants.
· This rule should be treated as conditional support for incident response, malware triage, and threat-intelligence enrichment.
Deployment Tier Guidance
Tier 1
Deploy in malware-analysis workflows for suspicious binaries recovered from high-risk endpoints, administrative workstations, file servers, backup-accessible systems, and systems with ransomware-like activity.
Tier 2
Expand use to endpoint file collection workflows, sandbox triage, and repository scanning for suspicious binaries collected from shared repositories, operational servers, backup-accessible systems, and administrative jump hosts.
Tier 3
Expand to centralized malware repositories, incident-response evidence intake, EDR file retrieval workflows, and SOC triage pipelines where suspicious binaries can be scanned before broader investigation.
Tier 4
Deploy broadly across malware-lab, sandbox, repository, EDR file-collection, and incident-response workflows where sample availability, version control, rule testing, and false-positive review can be maintained.
Tier Usage Constraints
· Tiering changes sample-collection scope, scanning coverage, enrichment priority, and triage workflow; it must not change the rule’s classification-only purpose.
· Smaller environments should use this rule for recovered suspicious binaries and sandbox submissions rather than broad enterprise claims.
· Larger environments should correlate YARA hits with endpoint execution, file-transformation, backup, virtualization, identity, and SIEM telemetry before escalating to confirmed ransomware activity.
· YARA tiering must account for sample availability, rule testing capacity, false-positive review, and PE/ELF validation requirements.
Rule Code
rule VECT_Ransomware_Conditional_Sample_Classification
{
meta:
description = "Conditional classification rule for suspected VECT ransomware samples; intended for malware triage, repository scanning, sandbox classification, and incident-response enrichment."
author = "CyberDax"
date = "2026-05-01"
reference_1 = "https://research.checkpoint.com/2026/vect-ransomware-by-design-wiper-by-accident/"
reference_2 = "https://bazaar.abuse.ch/browse/yara/VECT_Ransomware/"
scope = "sample classification only"
confidence = "conditional"
warning = "Do not use as primary enterprise detection or as proof of active ransomware execution."
strings:
$note_exact = "!!!READ_ME!!!.txt" ascii wide
$note_readme_1 = "READ_ME" ascii wide nocase
$note_readme_2 = "readme" ascii wide nocase
$ext_vect = ".vect" ascii wide
$crypto_libsodium = "libsodium" ascii wide nocase
$crypto_chacha = "ChaCha20" ascii wide nocase
$crypto_chacha_ietf = "ChaCha20-IETF" ascii wide nocase
$esxi_1 = "esxcli" ascii wide nocase
$esxi_2 = "vim-cmd" ascii wide nocase
$esxi_3 = "vmfs" ascii wide nocase
$esxi_4 = "vmdk" ascii wide nocase
$win_recovery_1 = "vssadmin" ascii wide nocase
$win_recovery_2 = "delete shadows" ascii wide nocase
$win_recovery_3 = "wbadmin" ascii wide nocase
$win_recovery_4 = "bcdedit" ascii wide nocase
$ransom_1 = "decrypt" ascii wide nocase
$ransom_2 = "recover" ascii wide nocase
$ransom_3 = "restore" ascii wide nocase
condition:
(
uint16(0) == 0x5A4D or
uint32(0) == 0x464C457F
)
and filesize < 50MB
and
(
(
any of ($note_*) and
$ext_vect and
any of ($crypto_*)
)
or
(
$ext_vect and
any of ($crypto_*) and
2 of ($ransom_*)
)
or
(
any of ($crypto_*) and
2 of ($esxi_*) and
any of ($ransom_*)
)
or
(
any of ($crypto_*) and
2 of ($win_recovery_*) and
any of ($note_*)
)
)
}
AWS
AWS Rule 1
AWS Backup, Snapshot, AMI, and Backup-Vault Policy Tampering Associated with Destructive Ransomware Risk
System-Native Format
AWS CloudTrail-based EventBridge or SIEM detection logic using CloudTrail event fields.
Detection Objective
Detect suspicious AWS Backup, EBS snapshot, AMI, backup-vault, or backup-vault policy tampering that could reduce recoverability during a destructive ransomware event.
Detection Rationale
· VECT-aligned business impact increases when attackers impair recovery paths before or during destructive file transformation.
· AWS control-plane telemetry can identify backup, snapshot, AMI, and backup-vault policy tampering, but it does not directly prove local ransomware execution.
· AWS Backup recovery-point and vault actions are high-value recovery-control signals because they can affect backup availability and recovery readiness.
· Amazon EC2 snapshot and AMI actions are high-value recovery-control signals where EBS snapshots or AMIs are used for recovery, restoration, golden images, or disaster-recovery workflows.
· S3 and KMS events may be relevant only where the customer explicitly uses S3 buckets, object stores, lifecycle policies, or KMS keys as part of backup, recovery, vaulting, or disaster-recovery architecture.
· This rule is designed to detect destructive-impact amplification in AWS environments while preserving the report’s behavior-led detection model.
Required Telemetry
· AWS CloudTrail management events.
· AWS Backup events.
· Amazon EC2 EBS snapshot events.
· Amazon EC2 AMI events.
· Backup-vault policy events.
· IAM principal context.
· Source IP address.
· User agent.
· AWS account ID.
· AWS Region.
· Event name.
· Event source.
· Resource ARN or resource identifier.
· Error code and response status where available.
· Identity context for users, roles, federated sessions, and assumed roles.
Engineering Implementation Instructions
· Validate that CloudTrail management events are enabled for relevant AWS accounts and Regions.
· Validate ingestion into the customer’s detection platform, such as EventBridge, CloudWatch Logs, Security Lake, or SIEM.
· Scope monitoring to AWS Backup vaults, recovery points, EBS snapshots, AMIs, and accounts that support production workloads or critical recovery paths.
· Treat S3 and KMS monitoring as customer-specific extensions only where those services are part of the backup, archive, recovery, vaulting, or disaster-recovery architecture.
· Validate approved backup administrators, automation roles, break-glass roles, CI/CD roles, backup lifecycle jobs, AMI lifecycle workflows, snapshot lifecycle jobs, and disaster-recovery maintenance windows before enabling broad alerting.
· Prioritize events involving unusual principals, unusual source IPs, unusual Regions, new user agents, cross-account access, recent privilege changes, or actions outside approved maintenance windows.
· Correlate AWS recovery-path tampering with endpoint, workload, identity, backup, and SIEM telemetry where available.
· Do not use this rule as proof of local ransomware execution without workload telemetry.
Detection Quality
DRI
8.0
DRI Justification
The rule targets recovery-path, snapshot, AMI, and backup-vault policy tampering, which are durable destructive-ransomware impact behaviors and do not depend on VECT static artifacts.
Operational TCR
7.2
Operational TCR Justification
Operational confidence is moderate to strong where CloudTrail, AWS Backup, EC2 snapshot events, AMI activity, IAM context, account context, and Region context are available. Confidence degrades where CloudTrail coverage, multi-account aggregation, or recovery-asset tagging is incomplete.
Full-Telemetry TCR
8.5
Full-Telemetry TCR Justification
Full-telemetry confidence is high when CloudTrail management events, AWS Backup logs, EC2 snapshot activity, AMI activity, IAM identity context, asset criticality, and SIEM correlation are available across all relevant accounts and Regions.
Deployment Limitations
· This rule must not claim direct detection of local VECT encryption.
· This rule must not claim confirmed ransomware execution without endpoint or workload telemetry.
· This rule must not treat legitimate lifecycle expiration, backup automation, AMI lifecycle management, snapshot lifecycle management, or approved disaster-recovery maintenance as malicious without identity, timing, account, Region, or resource context.
· This rule requires customer validation of approved backup roles, automation roles, snapshot lifecycle policies, AMI lifecycle policies, vault policies, maintenance windows, and disaster-recovery workflows.
· S3 and KMS events should be added only when customer architecture confirms they are recovery-critical.
· This rule may miss destructive activity if CloudTrail is not enabled, logs are not centralized, or relevant AWS accounts and Regions are not monitored.
· This rule should be used as cloud recovery-path protection and destructive-impact amplification detection, not as VECT attribution.
Deployment Tier Guidance
Tier 1
Deploy against production AWS accounts, high-value workload accounts, and accounts containing EBS snapshots, AWS Backup vaults, AMIs, or recovery assets tied to critical systems.
Tier 2
Expand deployment across backup-management accounts, disaster-recovery accounts, security-tooling accounts, and accounts with privileged automation roles that can modify recovery resources.
Tier 3
Expand deployment across multi-account AWS Organizations environments where CloudTrail events are centrally aggregated and recovery assets can be enriched with account, Region, resource, and owner context.
Tier 4
Deploy broadly across all AWS accounts and Regions where centralized logging, identity enrichment, recovery-asset tagging, lifecycle-policy awareness, and SOC triage capacity support enterprise-scale monitoring.
Tier Usage Constraints
· Tiering changes account scope, Region scope, enrichment priority, and response routing; it must not weaken the requirement for suspicious recovery-path, snapshot, AMI, or backup-vault policy context.
· Smaller environments should prioritize production accounts and recovery assets supporting business-critical workloads.
· Larger environments should correlate AWS recovery-control events with IAM activity, endpoint telemetry, backup telemetry, asset criticality, and incident-response context where available.
· AWS tiering must account for lifecycle policies, approved automation, delegated administration, cross-account access, and disaster-recovery maintenance windows.
· S3 and KMS should be included as tier-specific extensions only where customer recovery architecture depends on S3 object storage, S3 lifecycle controls, or KMS key availability for backup and recovery.
Rule Code
{
"rule_name": "AWS Backup, Snapshot, AMI, and Backup-Vault Policy Tampering Associated with Destructive Ransomware Risk",
"rule_type": "CloudTrail EventBridge or SIEM detection logic",
"description": "Detects suspicious AWS Backup, EBS snapshot, AMI, backup-vault, or backup-vault policy tampering that may reduce recoverability during destructive ransomware events.",
"core_event_sources": [
"backup.amazonaws.com",
"ec2.amazonaws.com"
],
"core_event_names": [
"DeleteRecoveryPoint",
"DeleteBackupVault",
"DeleteBackupVaultAccessPolicy",
"PutBackupVaultAccessPolicy",
"DeleteBackupVaultLockConfiguration",
"UntagResource",
"DeleteSnapshot",
"ModifySnapshotAttribute",
"DeregisterImage"
],
"optional_customer_specific_recovery_extensions": {
"use_only_when_s3_or_kms_are_recovery_critical": true,
"event_sources": [
"s3.amazonaws.com",
"kms.amazonaws.com"
],
"event_names": [
"DeleteBucket",
"PutBucketLifecycleConfiguration",
"DeleteObject",
"DeleteObjects",
"ScheduleKeyDeletion",
"DisableKey"
],
"deployment_note": "Enable these extensions only when customer architecture confirms S3 buckets, S3 object lifecycle controls, or KMS keys are part of backup, recovery, vaulting, archive, or disaster-recovery workflows."
},
"selection_logic": {
"match": {
"detail.eventSource": [
"backup.amazonaws.com",
"ec2.amazonaws.com"
],
"detail.eventName": [
"DeleteRecoveryPoint",
"DeleteBackupVault",
"DeleteBackupVaultAccessPolicy",
"PutBackupVaultAccessPolicy",
"DeleteBackupVaultLockConfiguration",
"UntagResource",
"DeleteSnapshot",
"ModifySnapshotAttribute",
"DeregisterImage"
]
},
"context_required": [
"userIdentity.arn",
"userIdentity.type",
"sourceIPAddress",
"userAgent",
"recipientAccountId",
"awsRegion",
"eventTime",
"requestParameters",
"resources"
],
"raise_severity_when": [
"principal is not in customer_approved_backup_or_dr_roles",
"source IP is outside approved administrative ranges",
"action occurs outside approved maintenance window",
"event occurs in production or recovery account",
"event targets tagged critical recovery assets",
"same principal performs multiple recovery-impacting actions within customer_defined_time_window",
"activity follows recent privilege escalation or unusual role assumption",
"activity overlaps with endpoint-confirmed destructive file transformation"
],
"suppress_when": [
"principal is approved backup automation role",
"action matches documented snapshot lifecycle policy",
"action matches documented AMI lifecycle policy",
"action matches documented backup lifecycle policy",
"action occurs during approved disaster-recovery test",
"action occurs during approved maintenance window",
"resource is tagged non-production and not recovery-critical"
]
},
"severity": "high",
"deployment_notes": [
"Validate CloudTrail coverage across all relevant accounts and Regions.",
"Replace approved role, maintenance window, source network, asset tag, lifecycle policy, and recovery-asset placeholders with customer-validated values.",
"Enable S3 or KMS extension events only when those services are part of the customer's recovery architecture.",
"Do not treat this rule as direct local encryption detection without workload endpoint telemetry."
]
}
Azure
Azure Rule 1
Azure Recovery Services Vault, Backup Policy, and Recovery-Control Tampering Associated with Destructive Ransomware Risk
System-Native Format
Azure Activity Log and Log Analytics KQL detection logic.
Detection Objective
Detect suspicious Azure Recovery Services Vault, Backup vault, backup policy, protected item, snapshot, image, or recovery-control tampering that could reduce recoverability during a destructive ransomware event.
Detection Rationale
· VECT-aligned business impact increases when attackers impair recovery paths before or during destructive file transformation.
· Azure control-plane telemetry can identify backup, recovery, vault, protected-item, snapshot, and image tampering, but it does not directly prove local ransomware execution.
· Azure Backup and Recovery Services Vault telemetry can support detection of recovery-control activity where Activity Log, diagnostic settings, and Log Analytics ingestion are configured.
· Storage-account, Key Vault, and managed-disk events may be relevant only where the customer explicitly uses those services as part of backup, recovery, vaulting, encryption-key availability, archive, or disaster-recovery architecture.
· This rule is designed to detect destructive-impact amplification in Azure environments while preserving the report’s behavior-led detection model.
Required Telemetry
· Azure Activity Log.
· Azure Resource Manager administrative events.
· Azure Backup operation logs.
· Recovery Services Vault diagnostic logs where available.
· Backup vault diagnostic logs where available.
· Azure Monitor Log Analytics ingestion.
· Entra ID identity context.
· Subscription ID.
· Resource group.
· Resource ID.
· Operation name.
· Caller.
· Caller IP address.
· User agent where available.
· Result type and result status.
· Resource provider.
· Resource tags where available.
Engineering Implementation Instructions
· Validate Azure Activity Log ingestion for relevant subscriptions and management groups.
· Validate diagnostic settings for Recovery Services Vaults, Backup vaults, and backup-related resources.
· Validate Log Analytics ingestion for Azure Backup operation tables where used.
· Scope monitoring to Recovery Services Vaults, Backup vaults, backup policies, protected items, snapshots, images, and recovery assets that support production workloads or critical recovery paths.
· Treat storage-account, Key Vault, and managed-disk monitoring as customer-specific extensions only where those services are part of the backup, archive, recovery, vaulting, encryption-key, or disaster-recovery architecture.
· Validate approved backup administrators, automation identities, break-glass accounts, managed identities, CI/CD identities, backup lifecycle jobs, snapshot lifecycle jobs, image lifecycle workflows, and disaster-recovery maintenance windows before enabling broad alerting.
· Prioritize events involving unusual principals, unusual source IPs, unusual subscriptions, unexpected resource groups, new user agents, recent privilege changes, protected production assets, or actions outside approved maintenance windows.
· Correlate Azure recovery-path tampering with endpoint, workload, identity, backup, and SIEM telemetry where available.
· Do not use this rule as proof of local ransomware execution without workload endpoint telemetry.
Detection Quality
DRI
8.0
DRI Justification
The rule targets recovery-path, backup-policy, protected-item, snapshot, image, and vault-control tampering, which are durable destructive-ransomware impact behaviors and do not depend on VECT static artifacts.
Operational TCR
7.2
Operational TCR Justification
Operational confidence is moderate to strong where Azure Activity Log, Azure Backup operation logs, Recovery Services Vault diagnostics, Entra ID identity context, subscription context, and resource tagging are available. Confidence degrades where diagnostic settings, cross-subscription aggregation, or recovery-asset tagging are incomplete.
Full-Telemetry TCR
8.5
Full-Telemetry TCR Justification
Full-telemetry confidence is high when Activity Log, Azure Backup operation logs, vault diagnostics, identity context, subscription context, resource criticality, and SIEM correlation are available across all relevant Azure subscriptions.
Deployment Limitations
· This rule must not claim direct detection of local VECT encryption.
· This rule must not claim confirmed ransomware execution without endpoint or workload telemetry.
· This rule must not treat legitimate backup lifecycle expiration, vault administration, protected-item changes, snapshot lifecycle management, image lifecycle management, policy updates, or approved disaster-recovery maintenance as malicious without identity, timing, subscription, resource, or asset-context anomalies.
· This rule requires customer validation of approved backup roles, automation identities, managed identities, snapshot lifecycle policies, image lifecycle policies, backup policies, vault policies, maintenance windows, and disaster-recovery workflows.
· Storage-account, Key Vault, and managed-disk monitoring should be added only when customer architecture confirms those services are recovery-critical.
· This rule may miss destructive activity if Activity Log, diagnostic settings, Log Analytics ingestion, or relevant subscriptions are not monitored.
· This rule should be used as cloud recovery-path protection and destructive-impact amplification detection, not as VECT attribution.
Deployment Tier Guidance
Tier 1
Deploy against production Azure subscriptions, high-value workload subscriptions, and subscriptions containing Recovery Services Vaults, Backup vaults, protected items, snapshots, images, or recovery assets tied to critical systems.
Tier 2
Expand deployment across backup-management subscriptions, disaster-recovery subscriptions, security-tooling subscriptions, and subscriptions with privileged automation identities that can modify recovery resources.
Tier 3
Expand deployment across management groups and multi-subscription Azure environments where Activity Log, vault diagnostics, Azure Backup operation logs, and recovery assets can be enriched with subscription, resource group, Region, owner, and criticality context.
Tier 4
Deploy broadly across all relevant Azure subscriptions and Regions where centralized logging, identity enrichment, recovery-asset tagging, lifecycle-policy awareness, and SOC triage capacity support enterprise-scale monitoring.
Tier Usage Constraints
· Tiering changes subscription scope, Region scope, enrichment priority, and response routing; it must not weaken the requirement for suspicious recovery-path, backup-policy, protected-item, snapshot, image, or vault-control context.
· Smaller environments should prioritize production subscriptions and recovery assets supporting business-critical workloads.
· Larger environments should correlate Azure recovery-control events with Entra ID activity, endpoint telemetry, backup telemetry, asset criticality, and incident-response context where available.
· Azure tiering must account for lifecycle policies, approved automation, managed identities, delegated administration, cross-subscription access, and disaster-recovery maintenance windows.
· Storage-account, Key Vault, and managed-disk activity should be included as tier-specific extensions only where customer recovery architecture depends on those services for backup, recovery, vaulting, encryption-key availability, archive, or disaster-recovery workflows.
Rule Code
// Azure Activity Log and Log Analytics KQL detection logic
// Rule: Azure Recovery Services Vault, Backup Policy, and Recovery-Control Tampering Associated with Destructive Ransomware Risk
// Purpose: Detect suspicious Azure recovery-path, backup-policy, protected-item, snapshot, or vault-control tampering.
// Deployment note: Replace approved identity, subscription, resource tag, lifecycle policy, and threshold placeholders with customer-validated values.
let Lookback = 1h;
let RecoveryControlOperations = dynamic([
"Microsoft.RecoveryServices/vaults/delete",
"Microsoft.RecoveryServices/vaults/write",
"Microsoft.RecoveryServices/vaults/backupPolicies/delete",
"Microsoft.RecoveryServices/vaults/backupPolicies/write",
"Microsoft.RecoveryServices/vaults/backupFabrics/protectionContainers/protectedItems/delete",
"Microsoft.RecoveryServices/vaults/backupFabrics/protectionContainers/protectedItems/write",
"Microsoft.RecoveryServices/vaults/backupFabrics/protectionContainers/protectedItems/backup/action",
"Microsoft.RecoveryServices/vaults/backupFabrics/protectionContainers/protectedItems/recoveryPoints/delete",
"Microsoft.DataProtection/backupVaults/delete",
"Microsoft.DataProtection/backupVaults/write",
"Microsoft.DataProtection/backupVaults/backupPolicies/delete",
"Microsoft.DataProtection/backupVaults/backupPolicies/write",
"Microsoft.DataProtection/backupVaults/backupInstances/delete",
"Microsoft.DataProtection/backupVaults/backupInstances/write",
"Microsoft.Compute/snapshots/delete",
"Microsoft.Compute/snapshots/write",
"Microsoft.Compute/images/delete",
"Microsoft.Compute/galleries/images/versions/delete"
]);
let ApprovedBackupOrDRIdentities = dynamic([
"<customer_approved_backup_admin_or_automation_identity>"
]);
AzureActivity
| where TimeGenerated >= ago(Lookback)
| where OperationNameValue in~ (RecoveryControlOperations)
| extend CallerIdentity = tostring(Caller)
| extend CallerAddress = tostring(CallerIpAddress)
| extend AzureResourceId = tostring(_ResourceId)
| extend ResourceGroupName = tostring(ResourceGroup)
| extend Subscription = tostring(SubscriptionId)
| extend Operation = tostring(OperationNameValue)
| extend Status = tostring(ActivityStatusValue)
| extend ResourceProviderName = tostring(ResourceProviderValue)
| extend IsApprovedIdentity = CallerIdentity in~ (ApprovedBackupOrDRIdentities)
| extend IsRecoveryRelevant =
Operation has "RecoveryServices"
or Operation has "DataProtection"
or Operation has "snapshots"
or Operation has "images"
or Operation has "galleries/images/versions"
| where IsRecoveryRelevant == true
| where IsApprovedIdentity == false
| summarize
RecoveryControlEventCount = count(),
Operations = make_set(Operation, 20),
ResourceIds = make_set(AzureResourceId, 20),
ResourceGroups = make_set(ResourceGroupName, 20),
CallerIPs = make_set(CallerAddress, 20),
Statuses = make_set(Status, 10)
by bin(TimeGenerated, 15m), CallerIdentity, Subscription
| where RecoveryControlEventCount >= <customer_defined_recovery_control_event_threshold>
| extend Severity = "High"
| extend DetectionReason = "Azure recovery-path, backup-policy, protected-item, snapshot, or vault-control tampering observed outside approved administrative context"
| project TimeGenerated, CallerIdentity, Subscription, CallerIPs, Operations, ResourceIds, ResourceGroups, Statuses, RecoveryControlEventCount, Severity, DetectionReason
GCP
GCP Rule 1
GCP Backup, Snapshot, Image, and Recovery Asset Tampering Associated with Destructive Ransomware Risk
System-Native Format
Google Cloud Logging query logic for Cloud Audit Logs and SIEM ingestion.
Detection Objective
Detect suspicious GCP Backup and DR, Compute Engine snapshot, image, backup vault, or recovery-asset tampering that could reduce recoverability during a destructive ransomware event.
Detection Rationale
· VECT-aligned business impact increases when attackers impair recovery paths before or during destructive file transformation.
· GCP control-plane telemetry can identify backup, snapshot, image, and recovery-asset tampering, but it does not directly prove local ransomware execution.
· Compute Engine snapshots and images may be used as recovery assets, golden images, rollback points, or disaster-recovery resources; deletion or modification activity against these assets can weaken recovery readiness.
· Cloud Storage and Cloud KMS events may be relevant only where the customer explicitly uses buckets, object lifecycle controls, or KMS keys as part of backup, recovery, vaulting, archive, encryption-key availability, or disaster-recovery architecture.
· This rule is designed to detect destructive-impact amplification in GCP environments while preserving the report’s behavior-led detection model.
Required Telemetry
· Cloud Audit Logs.
· Google Cloud Backup and DR audit logs.
· Compute Engine audit logs.
· Snapshot and image administrative activity.
· IAM principal context.
· Source IP address where available.
· User agent where available.
· Project ID.
· Folder or organization context where available.
· Region or zone where available.
· Method name.
· Service name.
· Resource name.
· Resource type.
· Authentication info.
· Authorization info.
· Request metadata.
· Status and error context where available.
· Resource labels or tags where available.
Engineering Implementation Instructions
· Validate Cloud Audit Logs ingestion for relevant projects, folders, and organizations.
· Validate log routing into the customer’s detection platform, such as Cloud Logging, BigQuery, Chronicle, Security Command Center integrations, or SIEM.
· Scope monitoring to Backup and DR backup vaults, data sources, backups, Compute Engine snapshots, images, and projects that support production workloads or critical recovery paths.
· Treat Cloud Storage and Cloud KMS monitoring as customer-specific extensions only where those services are part of the backup, archive, recovery, vaulting, encryption-key, or disaster-recovery architecture.
· Validate approved backup administrators, automation service accounts, break-glass accounts, CI/CD service accounts, snapshot lifecycle jobs, image lifecycle workflows, delegated administration, and disaster-recovery maintenance windows before enabling broad alerting.
· Prioritize events involving unusual principals, unusual source IPs, unexpected projects, unexpected Regions or zones, new user agents, cross-project activity, recent privilege changes, protected production assets, or actions outside approved maintenance windows.
· Correlate GCP recovery-path tampering with workload endpoint, identity, backup, and SIEM telemetry where available.
· Do not use this rule as proof of local ransomware execution without workload endpoint telemetry.
Detection Quality
DRI
8.0
DRI Justification
The rule targets recovery-path, backup, snapshot, image, and backup-vault tampering, which are durable destructive-ransomware impact behaviors and do not depend on VECT static artifacts.
Operational TCR
7.1
Operational TCR Justification
Operational confidence is moderate to strong where Cloud Audit Logs, Backup and DR audit logs, Compute Engine audit logs, IAM principal context, project context, and recovery-asset labeling are available. Confidence degrades where log routing, multi-project aggregation, or recovery-asset tagging is incomplete.
Full-Telemetry TCR
8.5
Full-Telemetry TCR Justification
Full-telemetry confidence is high when Cloud Audit Logs, Backup and DR logs, Compute Engine snapshot and image activity, IAM identity context, project criticality, resource labels, and SIEM correlation are available across all relevant projects.
Deployment Limitations
· This rule must not claim direct detection of local VECT encryption.
· This rule must not claim confirmed ransomware execution without endpoint or workload telemetry.
· This rule must not treat legitimate backup lifecycle expiration, backup vault administration, snapshot cleanup, image cleanup, or approved disaster-recovery maintenance as malicious without identity, timing, project, zone, resource, or asset-context anomalies.
· This rule requires customer validation of approved backup roles, automation service accounts, snapshot lifecycle policies, image lifecycle policies, backup vault policies, maintenance windows, and disaster-recovery workflows.
· Cloud Storage and Cloud KMS monitoring should be added only when customer architecture confirms those services are recovery-critical.
· This rule may miss destructive activity if Cloud Audit Logs are not routed centrally, relevant projects are not monitored, or recovery assets are not labeled or inventoried.
· This rule should be used as cloud recovery-path protection and destructive-impact amplification detection, not as VECT attribution.
Deployment Tier Guidance
Tier 1
Deploy against production GCP projects, high-value workload projects, and projects containing Backup and DR backup vaults, backups, Compute Engine snapshots, images, or recovery assets tied to critical systems.
Tier 2
Expand deployment across backup-management projects, disaster-recovery projects, security-tooling projects, and projects with privileged automation service accounts that can modify recovery resources.
Tier 3
Expand deployment across folders and multi-project GCP environments where Cloud Audit Logs, Backup and DR audit logs, Compute Engine audit logs, and recovery assets can be enriched with project, folder, organization, location, owner, and criticality context.
Tier 4
Deploy broadly across all relevant GCP projects, folders, and organizations where centralized logging, identity enrichment, recovery-asset labeling, lifecycle-policy awareness, and SOC triage capacity support enterprise-scale monitoring.
Tier Usage Constraints
· Tiering changes project scope, folder scope, enrichment priority, and response routing; it must not weaken the requirement for suspicious recovery-path, backup, snapshot, image, or vault-control context.
· Smaller environments should prioritize production projects and recovery assets supporting business-critical workloads.
· Larger environments should correlate GCP recovery-control events with IAM activity, endpoint telemetry, backup telemetry, asset criticality, and incident-response context where available.
· GCP tiering must account for lifecycle policies, approved automation, service accounts, delegated administration, cross-project access, and disaster-recovery maintenance windows.
· Cloud Storage and Cloud KMS activity should be included as tier-specific extensions only where customer recovery architecture depends on those services for backup, recovery, vaulting, encryption-key availability, archive, or disaster-recovery workflows.
Rule Code
// Google Cloud Logging query logic for Cloud Audit Logs and SIEM ingestion
// Rule: GCP Backup, Snapshot, Image, and Recovery Asset Tampering Associated with Destructive Ransomware Risk
// Purpose: Detect suspicious GCP backup, snapshot, image, vault, or recovery-asset tampering.
// Deployment note: Replace approved principal, project, resource label, lifecycle policy, and threshold placeholders with customer-validated values.
logName:"cloudaudit.googleapis.com"
(
protoPayload.serviceName="backupdr.googleapis.com"
OR protoPayload.serviceName="compute.googleapis.com"
)
(
protoPayload.methodName=~".*(delete|remove).*"
OR protoPayload.methodName=~".*(backupVault|BackupVault|backup|Backup|snapshot|Snapshot|image|Image).*(patch|update|setIamPolicy).*"
)
(
protoPayload.methodName=~".*Backup.*"
OR protoPayload.methodName=~".*backup.*"
OR protoPayload.methodName=~".*BackupVault.*"
OR protoPayload.methodName=~".*backupVault.*"
OR protoPayload.methodName=~".*DataSource.*"
OR protoPayload.methodName=~".*dataSource.*"
OR protoPayload.methodName=~".*snapshots.*"
OR protoPayload.methodName=~".*images.*"
)
-protoPayload.authenticationInfo.principalEmail:("<customer_approved_backup_or_dr_principal>")
resource.labels.project_id:("<customer_monitored_project_or_project_pattern>")
S26 — Threat-to-Rule Traceability Matrix
Traceability Purpose
· This section maps the VECT ransomware-wiper threat behaviors identified in S21 through S24 to the finalized S25 detection rule set.
· The traceability model confirms that each deployed or conditional rule connects directly to observable telemetry, validated detection intent, and the VECT operational risk model.
· The S25 build remains behavior-led and does not depend on static VECT identity, ransom-note-only logic, extension-only logic, hash-only logic, network-only assumptions, or alert-chain dependencies.
· The final validated S25 distribution is 17 rules: SentinelOne 3, Splunk 3, Elastic 3, QRadar 2, SIGMA 2, YARA 1 conditional, AWS 1 conditional, Azure 1 conditional, GCP 1 conditional, and Suricata 0.
Traceability Summary
Destructive File Transformation
· SentinelOne Rule 1 maps to destructive file transformation from suspicious endpoint execution context.
· Splunk Rule 1 maps to high-volume file modification, rename, or creation activity correlated with ransom-note-like artifacts.
· Elastic Rule 1 maps to suspicious process execution followed by high-value file transformation.
· Elastic Rule 2 maps to file transformation followed by ransom-note staging.
· QRadar Rule 1 maps to correlated mass file transformation with ransomware-like context.
· SIGMA Rule 1 maps to ransomware-like file transformation across high-value paths.
· This behavior is the primary detection anchor because VECT’s business impact is driven by destructive file rewrite activity rather than reliably recoverable encryption.
Ransom-Note Staging with File-Impact Context
· SentinelOne Rule 2 maps to ransom-note staging correlated with ransomware-like file activity.
· Splunk Rule 1 maps to ransom-note-like artifact creation correlated with mass file transformation.
· Elastic Rule 2 maps to file transformation followed by ransom-note staging.
· This behavior is treated as supporting evidence only when paired with file transformation, suspicious execution, high-value paths, or affected asset context.
· Ransom-note-only logic remains insufficient for high-confidence detection.
Backup, Snapshot, and Recovery-Path Tampering
· SentinelOne Rule 3 maps to endpoint-visible recovery-path and virtualization-adjacent interference.
· Splunk Rule 2 maps to backup and recovery-control tampering near ransomware-like activity.
· Elastic Rule 3 maps to recovery-path and virtualization-adjacent interference activity.
· QRadar Rule 2 maps to recovery-path or virtualization-control tampering with suspicious administrative context.
· SIGMA Rule 2 maps to recovery suppression or virtualization-adjacent interference activity.
· AWS Rule 1 maps to AWS Backup, EBS snapshot, AMI, and backup-vault policy tampering.
· Azure Rule 1 maps to Azure Recovery Services Vault, Backup vault, backup-policy, protected-item, snapshot, image, and recovery-control tampering.
· GCP Rule 1 maps to GCP Backup and DR, backup vault, backup, snapshot, image, and recovery-asset tampering.
· This behavior is a high-priority detection path because recovery-path degradation materially increases destructive ransomware impact.
ESXi and Virtualization-Adjacent Impact
· SentinelOne Rule 3 maps to virtualization-adjacent endpoint activity where the monitored system has visibility into ESXi management, datastore interaction, or virtualization-adjacent file access.
· Splunk Rule 3 maps to ESXi, datastore, virtual disk, and virtualization-adjacent destructive activity correlation.
· Elastic Rule 3 maps to virtualization-adjacent command or process activity.
· QRadar Rule 2 maps to ESXi, datastore, or virtualization-control tampering where VMware or related administrative telemetry is normalized.
· SIGMA Rule 2 maps to virtualization-adjacent interference activity through portable command-line detection logic.
· This behavior remains critical because VECT is reported across Windows, Linux, and ESXi variants, and virtualization disruption can expand impact across multiple systems.
Cloud Recovery-Control Tampering
· AWS Rule 1 maps to AWS recovery-path tampering through Backup, snapshot, AMI, and backup-vault policy activity.
· Azure Rule 1 maps to Azure recovery-control tampering through Recovery Services Vault, Backup vault, backup-policy, protected-item, snapshot, and image activity.
· GCP Rule 1 maps to GCP recovery-control tampering through Backup and DR, backup vault, backup, snapshot, image, and recovery-asset activity.
· Cloud rules are scoped to destructive-impact amplification and recovery-path protection.
· Cloud rules must not be represented as direct local VECT encryption detection unless workload endpoint telemetry is available.
Sample Classification and Malware Triage
· YARA Rule 1 maps to conditional VECT ransomware sample classification.
· The YARA rule supports malware triage, repository scanning, sandbox classification, endpoint file collection, and incident-response enrichment.
· The YARA rule does not prove active execution, file impact, backup tampering, ESXi impact, or enterprise scope by itself.
· YARA remains supplemental to endpoint, file, backup, virtualization, cloud-control, and SIEM-correlation coverage.
Network-Signature Coverage
· Suricata maps to no deployable S25 rule for this report.
· Suricata is excluded because current report evidence supports destructive file behavior, cross-platform execution, and recovery-path risk more strongly than stable network indicators, protocol traits, payload signatures, delivery infrastructure, or command-and-control patterns.
· Network telemetry may support investigation but does not provide primary VECT detection coverage unless validated network artifacts become available.
Rule-to-Threat Traceability
Suricata
Rule Count
0
Mapped Threat Behaviors
· No primary mapped S25 rule.
· Network telemetry remains supporting only.
Traceability Disposition
· Suricata is intentionally excluded from S25 because no validated VECT network signature or protocol behavior supports a low-noise deployable rule.
SentinelOne
SentinelOne Rule 1
Mapped Rule
Mass Destructive File Transformation from Suspicious Execution Context.
Mapped Threat Behaviors
· Destructive file transformation.
· Suspicious process execution.
· High-value path impact.
· Cross-platform ransomware-wiper behavior where endpoint visibility exists.
Telemetry Basis
· Process creation.
· File modification.
· File rename.
· Process lineage.
· Command line.
· User context.
· Host role.
· File path and file name.
Traceability Disposition
· Primary endpoint rule for active ransomware-wiper file impact.
SentinelOne Rule 2
Mapped Rule
Ransom-Note Staging Correlated with Ransomware-Like File Activity.
Mapped Threat Behaviors
· Ransom-note staging.
· Suspicious file modification.
· Ransomware-like execution context.
· High-value directory impact.
Telemetry Basis
· File creation.
· File modification.
· Process lineage.
· Command line.
· File path.
· User context.
· Host role.
Traceability Disposition
· Supporting endpoint rule that strengthens detection when ransom-note-like artifacts appear with ransomware-like file activity.
SentinelOne Rule 3
Mapped Rule
Recovery-Path and Virtualization-Adjacent Interference Before or During File Impact.
Mapped Threat Behaviors
· Backup suppression.
· Shadow copy interference.
· Recovery-control tampering.
· Event-log clearing.
· Virtualization-adjacent interference.
Telemetry Basis
· Process execution.
· Command line.
· File modification.
· File deletion where available.
· Process lineage.
· User context.
· Host role.
· Endpoint tamper events where available.
Traceability Disposition
· Primary endpoint rule for recovery-path and virtualization-adjacent destructive preparation.
Splunk
Splunk Rule 1
Mapped Rule
Mass File Transformation with Ransom-Note Correlation.
Mapped Threat Behaviors
· Mass file transformation.
· Ransom-note-like artifact creation.
· High-value repository impact.
· Ransomware-like file activity.
Telemetry Basis
· Endpoint file events.
· Process telemetry.
· User context.
· Host identity.
· Host role or asset criticality.
· File path and file name.
· File size where available.
Traceability Disposition
· Primary SIEM correlation rule for file-impact behavior with ransom-note support.
Splunk Rule 2
Mapped Rule
Backup and Recovery-Control Tampering Near Ransomware-Like Activity.
Mapped Threat Behaviors
· Backup tampering.
· Snapshot tampering.
· Recovery-control interference.
· Restore-control modification.
· Ransomware impact amplification.
Telemetry Basis
· Endpoint process execution.
· Command line.
· Backup-platform telemetry.
· Identity context.
· Administrative action logs.
· Backup, snapshot, vault, restore, or recovery-control events.
Traceability Disposition
· Primary SIEM correlation rule for recovery-path degradation.
Splunk Rule 3
Mapped Rule
ESXi or Virtualization-Adjacent Destructive Activity Correlation.
Mapped Threat Behaviors
· ESXi administrative abuse.
· Datastore activity.
· Virtual disk impact.
· Snapshot or VM manipulation.
· Virtualization-adjacent destructive activity.
Telemetry Basis
· VMware or ESXi logs.
· ESXi shell or command telemetry.
· Datastore access telemetry.
· Endpoint telemetry from management hosts.
· Identity telemetry.
· File telemetry for virtual disks or datastore paths where available.
Traceability Disposition
· Primary SIEM correlation rule for virtualization-impact detection.
Elastic
Elastic Rule 1
Mapped Rule
Suspicious Process Followed by High-Value File Transformation.
Mapped Threat Behaviors
· Suspicious process execution.
· High-value file transformation.
· User data, shared repository, archive, database, backup, or virtual disk impact.
Telemetry Basis
· Elastic Defend or equivalent process telemetry.
· File creation, modification, and rename telemetry.
· Process lineage.
· Command line.
· User context.
· Host identity.
· File path and file extension.
Traceability Disposition
· Primary Elastic endpoint sequence rule for process-to-file impact.
Elastic Rule 2
Mapped Rule
File Transformation Followed by Ransom-Note Staging.
Mapped Threat Behaviors
· File transformation.
· Ransom-note staging.
· High-value directory impact.
· Extortion-stage artifact creation.
Telemetry Basis
· File creation.
· File modification.
· File rename where available.
· Process context where available.
· User context.
· Host identity.
· File path.
Traceability Disposition
· Primary Elastic file-sequence rule for ransomware impact progression.
Elastic Rule 3
Mapped Rule
Recovery-Path and Virtualization-Adjacent Interference Activity.
Mapped Threat Behaviors
· Backup suppression.
· Recovery-control tampering.
· Event-log clearing.
· Virtualization-adjacent command activity.
Telemetry Basis
· Process execution.
· Command line.
· Process lineage.
· User context.
· Host identity.
· Host role.
· Endpoint tamper events where available.
Traceability Disposition
· Primary Elastic process activity rule for recovery-path and virtualization-adjacent interference.
QRadar
QRadar Rule 1
Mapped Rule
Correlated Mass File Transformation with Ransomware-Like Context.
Mapped Threat Behaviors
· High-volume file creation, modification, or rename activity.
· Distinct file or path spread.
· Ransomware-like file impact.
· High-value repository exposure.
Telemetry Basis
· Endpoint process telemetry.
· File creation telemetry.
· File modification telemetry.
· File rename telemetry where available.
· EDR or file-monitoring telemetry.
· User context.
· Host identity.
· File path and file name.
· Initiating process where available.
Traceability Disposition
· Moderate-confidence SIEM correlation rule dependent on upstream telemetry normalization.
QRadar Rule 2
Mapped Rule
Recovery-Path or Virtualization-Control Tampering with Suspicious Administrative Context.
Mapped Threat Behaviors
· Backup tampering.
· Recovery-control tampering.
· Snapshot or restore manipulation.
· ESXi, datastore, or virtualization-control activity.
· Suspicious administrative context.
Telemetry Basis
· Endpoint command-line telemetry.
· Backup-platform telemetry.
· VMware, ESXi, or vCenter telemetry where available.
· Identity telemetry.
· Administrative action logs.
· User and host context.
Traceability Disposition
· Moderate-confidence SIEM correlation rule for recovery and virtualization-control tampering.
Sigma
SIGMA Rule 1
Mapped Rule
Ransomware-Like File Transformation Across High-Value Paths.
Mapped Threat Behaviors
· File creation, modification, or rename across high-value paths.
· Archive, database, backup-adjacent, and virtualization-adjacent file impact.
· Portable ransomware-like file behavior.
Telemetry Basis
· File creation telemetry.
· File modification telemetry.
· File rename telemetry where available.
· File path.
· File name.
· File extension.
· Initiating image or process field where available.
· User and host context.
Traceability Disposition
· Portable detection rule dependent on backend translation and file-event telemetry quality.
SIGMA Rule 2
Mapped Rule
Recovery Suppression or Virtualization-Adjacent Interference Activity.
Mapped Threat Behaviors
· Backup suppression.
· Shadow copy deletion.
· Recovery-control tampering.
· Event-log clearing.
· Virtualization-adjacent operations.
Telemetry Basis
· Process creation telemetry.
· Command line.
· User context.
· Host identity.
· Parent process where available.
· Process image.
· Administrative tool execution telemetry where available.
Traceability Disposition
· Portable detection rule for recovery-path and virtualization-adjacent interference.
YARA
YARA Rule 1
Mapped Rule
Conditional VECT Ransomware Sample Classification.
Mapped Threat Behaviors
· VECT sample classification.
· Malware triage.
· Repository scanning.
· Sandbox classification.
· Incident-response enrichment.
Telemetry Basis
· Malware sample files.
· Endpoint file collection.
· Sandbox output.
· Malware repository scanning.
· File type identification.
· Extracted strings.
· Sample metadata.
Traceability Disposition
· Conditional classification rule only.
· Not primary enterprise detection.
AWS
AWS Rule 1
Mapped Rule
AWS Backup, Snapshot, AMI, and Backup-Vault Policy Tampering Associated with Destructive Ransomware Risk.
Mapped Threat Behaviors
· AWS Backup recovery-point tampering.
· Backup vault tampering.
· EBS snapshot modification or deletion.
· AMI deregistration.
· Backup-vault policy tampering.
· Recovery-path degradation.
Telemetry Basis
· AWS CloudTrail management events.
· AWS Backup events.
· EC2 snapshot and AMI events.
· IAM principal context.
· Source IP address.
· User agent.
· AWS account and Region context.
· Resource identifiers.
Traceability Disposition
· Conditional cloud-control rule for recovery-path protection and destructive-impact amplification.
Azure
Azure Rule 1
Mapped Rule
Azure Recovery Services Vault, Backup Policy, and Recovery-Control Tampering Associated with Destructive Ransomware Risk.
Mapped Threat Behaviors
· Recovery Services Vault tampering.
· Backup vault tampering.
· Backup-policy modification.
· Protected-item changes.
· Snapshot or image deletion.
· Recovery-control degradation.
Telemetry Basis
· Azure Activity Log.
· Azure Resource Manager administrative events.
· Azure Backup operation logs.
· Recovery Services Vault diagnostics where available.
· Log Analytics ingestion.
· Entra ID identity context.
· Subscription and resource context.
Traceability Disposition
· Conditional cloud-control rule for Azure recovery-path protection and destructive-impact amplification.
GCP
GCP Rule 1
Mapped Rule
GCP Backup, Snapshot, Image, and Recovery Asset Tampering Associated with Destructive Ransomware Risk.
Mapped Threat Behaviors
· GCP Backup and DR tampering.
· Backup vault activity.
· Snapshot modification or deletion.
· Image modification or deletion.
· Recovery-asset tampering.
· Cloud recovery-path degradation.
Telemetry Basis
· Cloud Audit Logs.
· Backup and DR audit logs.
· Compute Engine audit logs.
· IAM principal context.
· Project, folder, and organization context.
· Method name.
· Service name.
· Resource name.
· Request metadata.
Traceability Disposition
· Conditional cloud-control rule for GCP recovery-path protection and destructive-impact amplification.
Coverage Validation Summary
· Destructive file transformation is covered by SentinelOne, Splunk, Elastic, QRadar, and SIGMA.
· Ransom-note staging with file-impact context is covered by SentinelOne, Splunk, and Elastic.
· Backup and recovery-path tampering is covered by SentinelOne, Splunk, Elastic, QRadar, SIGMA, AWS, Azure, and GCP.
· ESXi and virtualization-adjacent impact is covered by SentinelOne, Splunk, Elastic, QRadar, and SIGMA where relevant telemetry exists.
· Sample classification is covered conditionally by YARA.
· Cloud recovery-control tampering is covered conditionally by AWS, Azure, and GCP.
· Network-signature detection is intentionally not covered by Suricata because validated VECT network artifacts are not currently sufficient for a deployable rule.
Traceability Gaps
· Suricata remains a deliberate gap because no validated VECT network artifact supports a deployable rule.
· YARA remains conditional because it depends on access to suspicious binaries or validated VECT sample artifacts.
· AWS, Azure, and GCP remain conditional because cloud-control logs detect recovery-path tampering, not local file encryption.
· QRadar and SIGMA remain telemetry-dependent because their effectiveness depends on upstream source quality, parser support, field normalization, and backend translation.
· ESXi coverage depends on VMware, ESXi, vCenter, datastore, administrative host, or virtualization-management telemetry being available.
· File-size-aware prioritization depends on whether file-size fields are captured and normalized.
· Detection confidence decreases where endpoint process lineage, command-line visibility, initiating-process attribution, host-role enrichment, backup-platform telemetry, or SIEM normalization is incomplete.
S27 — Behavior and Log Artifacts
Section Purpose
· This section identifies the observable behavior and log artifacts required to operationalize the VECT ransomware-wiper detection strategy.
· The artifact model is aligned to S21 through S26 and preserves the report’s behavior-led detection approach, with endpoint, file, backup, virtualization, SIEM, and conditional cloud-control telemetry prioritized over static indicators.
· Artifacts are grouped by observable behavior so detection engineers, SOC analysts, and incident responders can connect telemetry evidence to the finalized S25 rule set.
Primary Behavior Artifacts
Destructive File Transformation
· High-volume file creation, modification, rename, rewrite, overwrite, or deletion activity.
· Rapid directory traversal across local disks, mapped drives, file shares, NAS paths, user directories, operational repositories, database paths, archive locations, and backup-adjacent directories.
· File modification affecting high-value file types, including documents, archives, databases, virtual disks, backup files, and operational data stores.
· File transformation affecting operationally meaningful file sizes, especially where file-size telemetry can support prioritization around the reported VECT destructive threshold.
· Mass extension-change activity, including but not limited to VECT-associated extensions when correlated with process and file-impact context.
· File transformation activity initiated from suspicious execution paths, user-writable directories, temporary folders, staging locations, administrative shares, or recently created directories.
Relevant Log Artifacts
· File creation event.
· File modification event.
· File rename event.
· File deletion event.
· File path.
· File name.
· File extension.
· File size.
· File owner.
· Initiating process.
· Initiating user.
· Host identity.
· Host role.
· Timestamp.
· Parent process where available.
· Asset criticality where available.
Detection Alignment
· SentinelOne Rule 1.
· Splunk Rule 1.
· Elastic Rule 1.
· Elastic Rule 2.
· QRadar Rule 1.
· SIGMA Rule 1.
Ransom-Note Staging
· Ransom-note-like files created across multiple directories.
· Ransom-note artifacts appearing during or after high-volume file rewrite activity.
· Ransom-note creation in user directories, shared repositories, operational repositories, file servers, backup-accessible systems, or virtualization-adjacent paths.
· Ransom-note-like content using recovery, restore, decrypt, or instruction-oriented naming patterns.
· Ransom-note creation initiated by a suspicious process, unknown binary, script interpreter, administrative tool, or newly staged executable.
Relevant Log Artifacts
· File creation event.
· File modification event.
· File name.
· File path.
· File extension.
· Initiating process.
· Process command line.
· Parent process.
· User context.
· Host identity.
· Affected directory count.
· Timestamp.
· File transformation activity within the same detection window.
Detection Alignment
· SentinelOne Rule 2.
· Splunk Rule 1.
· Elastic Rule 2.
Suspicious Execution Context
· Execution from temporary directories, user-writable paths, staging folders, public directories, downloads folders, administrative shares, removable media, or recently created directories.
· Execution by unknown, unsigned, low-prevalence, newly observed, or renamed binaries.
· Script interpreter, shell, remote administration, or command-line utility activity followed by file transformation.
· Cross-platform execution patterns across Windows, Linux, and ESXi-adjacent systems.
· Suspicious command-line activity involving file traversal, encryption-like behavior, backup interference, or virtualization-adjacent commands.
Relevant Log Artifacts
· Process creation event.
· Process termination event.
· Process name.
· Process path.
· Process hash.
· Process command line.
· Parent process.
· User context.
· Host identity.
· Host role.
· Process privilege level.
· First-seen timestamp.
· Signature or signer status where available.
· Endpoint prevalence where available.
Detection Alignment
· SentinelOne Rule 1.
· SentinelOne Rule 3.
· Splunk Rule 1.
· Splunk Rule 2.
· Elastic Rule 1.
· Elastic Rule 3.
· QRadar Rule 1.
· QRadar Rule 2.
· SIGMA Rule 2.
Backup, Snapshot, and Recovery-Path Tampering
· Backup job interruption, disablement, or deletion.
· Restore-point deletion.
· Snapshot deletion, modification, or removal.
· Retention-policy modification.
· Backup vault access policy modification.
· Backup vault deletion or control-plane tampering.
· Recovery configuration modification.
· Recovery-point deletion.
· Protected-item deletion or modification.
· Backup instance deletion or modification.
· Disaster-recovery or lifecycle policy activity outside approved context.
· Recovery-control activity performed by unusual users, hosts, service accounts, API callers, managed identities, automation roles, or source networks.
Relevant Log Artifacts
· Backup-platform event.
· Restore-point event.
· Snapshot event.
· Recovery-point event.
· Vault event.
· Policy change event.
· Protected-item event.
· Administrative action.
· API operation name.
· Caller identity.
· Source IP address.
· User agent.
· Host identity.
· Account, subscription, project, or Region context.
· Resource identifier.
· Result status.
· Maintenance-window context.
· Approved-role or approved-automation context.
Detection Alignment
· SentinelOne Rule 3.
· Splunk Rule 2.
· Elastic Rule 3.
· QRadar Rule 2.
· SIGMA Rule 2.
· AWS Rule 1.
· Azure Rule 1.
· GCP Rule 1.
ESXi and Virtualization-Adjacent Activity
· ESXi administrative command execution.
· Virtual machine disk modification.
· Datastore file modification.
· Snapshot removal or reconfiguration.
· Virtual machine removal or reconfiguration.
· Host service stoppage or suspicious host-management activity.
· Virtualization-management activity from unusual users, source hosts, jump hosts, or administrative sessions.
· Virtualization-adjacent file access involving .vmdk, datastore paths, VMFS paths, or management utilities.
· Virtual infrastructure activity outside approved maintenance windows.
Relevant Log Artifacts
· ESXi shell command.
· VMware or vCenter event.
· Datastore access event.
· Virtual disk file event.
· VM snapshot event.
· VM power or reconfiguration event.
· Administrative authentication event.
· Source host.
· Destination host.
· User identity.
· Command.
· Object name.
· Datastore path.
· Maintenance-window context.
· Host role.
· Asset criticality.
Detection Alignment
· SentinelOne Rule 3.
· Splunk Rule 3.
· Elastic Rule 3.
· QRadar Rule 2.
· SIGMA Rule 2.
Cloud Recovery-Control Tampering
· AWS Backup recovery-point, backup-vault, EBS snapshot, AMI, or backup-vault policy tampering.
· Azure Recovery Services Vault, Backup vault, backup-policy, protected-item, snapshot, image, or recovery-control tampering.
· GCP Backup and DR, backup vault, backup, snapshot, image, or recovery-asset tampering.
· Storage-account, object-storage, KMS, Key Vault, or managed-disk activity only where customer architecture confirms those services are recovery-critical.
· Cloud recovery-control actions from unusual identities, source IPs, Regions, projects, accounts, subscriptions, service accounts, managed identities, or automation roles.
Relevant Log Artifacts
· Cloud audit event.
· Service name.
· Method or operation name.
· Caller identity.
· Source IP address.
· User agent.
· Account, subscription, project, folder, organization, or Region context.
· Resource identifier.
· Resource tags or labels.
· Request parameters.
· Authorization context.
· Result status.
· Error code where available.
· Approved automation or maintenance context.
Detection Alignment
· AWS Rule 1.
· Azure Rule 1.
· GCP Rule 1.
Sample Classification Artifacts
· Suspicious PE or ELF sample.
· VECT-associated extension strings where validated.
· Ransom-note strings where validated.
· Cryptographic library strings where validated.
· Platform-specific strings related to Windows, Linux, or ESXi variants where validated.
· Sandbox classification.
· Malware repository match.
· Threat-intelligence enrichment.
· File hash and sample metadata.
Relevant Log Artifacts
· Malware sample file.
· File type.
· Extracted strings.
· Hash values.
· Sandbox output.
· Repository match.
· Sample metadata.
· Endpoint file collection source.
· Incident evidence package.
· Triage notes.
Detection Alignment
· YARA Rule 1.
Network and Outbound Communication Artifacts
· Outbound communication from a process also performing file transformation.
· Rare, newly observed, low-reputation, or unusual destination connections.
· DNS queries from suspicious processes or high-value systems during file activity.
· Direct IP connections from file servers, backup servers, administrative jump hosts, or ESXi-adjacent systems.
· Unusual encrypted outbound sessions during ransomware-like file activity.
· Potential staging or extortion-supporting network activity when supported by telemetry.
Relevant Log Artifacts
· DNS query.
· Destination IP address.
· Destination domain.
· Destination port.
· Protocol.
· TLS metadata.
· HTTP or HTTPS metadata.
· Proxy event.
· Firewall event.
· NetFlow event.
· Source process where available.
· Source host.
· User context.
· Byte count.
· Connection direction.
· First-seen status.
Detection Alignment
· Supporting telemetry only.
· No Suricata S25 rule is deployed.
· Network artifacts may enrich investigation but must not be promoted to primary detection without validated VECT network indicators.
Artifact Usage Constraints
· File extension artifacts must not be used alone.
· Ransom-note artifacts must not be used alone.
· YARA artifacts must remain sample-classification support unless tied to validated samples and incident context.
· Cloud-control artifacts must not be represented as direct evidence of local encryption unless workload telemetry is available.
· Network artifacts must remain supporting telemetry unless validated VECT network infrastructure, protocol traits, payload signatures, or delivery artifacts become available.
· File-volume artifacts must be interpreted against baseline, host role, user role, maintenance window, approved tools, and affected asset criticality.
· Backup and virtualization artifacts must include authorized-user validation, approved automation review, and maintenance-window context.
· Artifact interpretation must preserve direct telemetry-to-logic-to-output reasoning and must not depend on another CyberDax rule firing first.
S28 — Detection Strategy and SOC Implementation Guidance
Figure 5
Section Purpose
· This section translates the S21 through S27 detection model into SOC implementation guidance.
· The implementation model is designed to support the finalized 17-rule S25 build while preserving public-safe deployment guidance and avoiding proprietary internal tuning mechanics.
SOC Detection Objectives
· Identify active destructive file transformation before broad business-critical data impact occurs.
· Detect ransom-note staging only when correlated with file transformation, suspicious execution, affected path context, or host criticality.
· Detect recovery-path tampering before restore capability is degraded or destroyed.
· Detect ESXi and virtualization-adjacent activity where VMware or related administrative telemetry is available.
· Detect cloud recovery-control tampering in AWS, Azure, and GCP without claiming direct local encryption visibility.
· Use YARA only for sample classification, triage, repository scanning, sandbox enrichment, or incident-response support.
· Keep network telemetry as investigative enrichment unless validated VECT network artifacts become available.
SOC Intake Prioritization
Tier 1 Intake
· Prioritize alerts involving active mass file transformation.
· Prioritize alerts involving file transformation plus ransom-note staging.
· Prioritize alerts involving backup, snapshot, vault, restore-point, or recovery-control tampering.
· Prioritize alerts involving ESXi, datastore, virtual disk, or virtualization-management activity outside approved administrative context.
· Prioritize cloud recovery-control tampering involving production accounts, subscriptions, projects, recovery assets, or unusual identities.
· Prioritize YARA hits only when a suspicious sample is recovered from a system with related endpoint, file, backup, or virtualization evidence.
Tier 1 Triage Questions
· What host, user, process, or identity initiated the activity?
· Which files, paths, shares, repositories, databases, virtual disks, backups, or recovery assets were affected?
· Is the activity consistent with approved backup, maintenance, deployment, indexing, synchronization, compression, or encryption workflows?
· Is there evidence of ransom-note staging, extension changes, high-volume rewrites, backup tampering, or virtualization activity?
· Is the activity isolated to one endpoint, or does it involve shared storage, file servers, backup infrastructure, or virtualized infrastructure?
· Is workload endpoint telemetry available for cloud-hosted systems?
· Does the event indicate active destructive behavior, suspected pre-impact staging, recovery-path tampering, or post-impact artifact discovery?
Tier 2 Validation
· Validate process lineage, parent process, command line, executable path, user context, and host role.
· Validate file-event scope, distinct file count, distinct path count, affected extensions, affected directories, file sizes, and high-value repository exposure.
· Validate whether ransom-note-like artifacts appeared during or after file transformation.
· Validate backup, snapshot, vault, recovery-point, or retention-policy changes against approved maintenance and automation.
· Validate ESXi or virtualization-management activity against approved administrators, management hosts, maintenance windows, and change records.
· Validate cloud recovery-control activity against approved identities, automation roles, lifecycle policies, source IPs, Regions, projects, subscriptions, and accounts.
· Validate YARA matches against sample source, sandbox output, repository intelligence, and incident-specific telemetry.
Incident Response Escalation
· Escalate immediately when active mass file transformation affects file servers, shared repositories, database paths, backup-adjacent locations, virtual disks, or operational repositories.
· Escalate immediately when file transformation overlaps with backup deletion, snapshot removal, vault-policy change, recovery-point deletion, or protected-item modification.
· Escalate immediately when ESXi, vCenter, datastore, or virtual disk activity appears outside approved administrative context.
· Escalate immediately when cloud recovery-control tampering occurs in production or recovery-critical accounts, subscriptions, or projects.
· Escalate YARA matches when the matched sample is recovered from an affected host, staging path, administrative system, backup-accessible system, virtualization-management system, or incident evidence package.
· Do not delay containment waiting for lateral movement, persistence, exfiltration, or ransom-note confirmation if destructive file transformation is already visible.
Containment Guidance
· Isolate affected endpoints or servers when active destructive file transformation is observed.
· Suspend or contain compromised credentials, service accounts, privileged identities, cloud principals, managed identities, or automation accounts tied to recovery-control tampering.
· Preserve evidence before destructive activity expands, including process metadata, command lines, sample files, file-event records, backup-platform logs, virtualization logs, cloud audit logs, and identity events.
· Protect backup infrastructure, restore points, snapshots, vaults, and recovery assets from further modification.
· Review ESXi, vCenter, datastore, and virtualization-management sessions for active impact.
· Validate whether cloud recovery assets remain intact before initiating broad recovery.
· Coordinate containment with business continuity and backup teams to avoid destroying evidence or interrupting viable recovery paths.
Detection Tuning Guidance
· Establish baseline file-write, rename, delete, extension-change, and high-volume file activity by host role.
· Establish baseline backup administration, restore testing, retention-policy changes, vault access, snapshot activity, and recovery workflows.
· Establish baseline ESXi and virtualization-management commands, datastore interaction, VM power operations, snapshot activity, and maintenance windows.
· Establish baseline cloud recovery-control activity across AWS accounts, Azure subscriptions, and GCP projects.
· Scope allowlists narrowly to approved backup agents, deployment tools, indexing processes, synchronization clients, compression tools, encryption utilities, and maintenance automation.
· Review allowlists regularly and keep them role-specific, time-aware, and asset-specific.
· Avoid broad suppression of high-volume file activity because destructive ransomware can resemble legitimate enterprise file operations.
· Tune severity upward when destructive file transformation overlaps with backup tampering, ESXi activity, privileged execution, cloud recovery-control tampering, shared-storage access, or multi-host activity.
Correlation Guidance
· Correlate suspicious process execution with file modification, rename, extension change, or high-volume file activity.
· Correlate file transformation with ransom-note staging.
· Correlate backup, snapshot, vault, or recovery-control tampering with suspicious execution, privileged-user activity, or endpoint file impact.
· Correlate ESXi, vCenter, datastore, or virtual disk events with anomalous administrative sessions or endpoint activity on management hosts.
· Correlate cloud recovery-control events with identity activity, source IP address, user agent, account or subscription context, project context, and endpoint telemetry where available.
· Correlate YARA matches with endpoint execution, file transformation, backup activity, virtualization impact, and sample origin.
· Do not correlate by requiring another CyberDax rule to fire first.
· Use raw or normalized telemetry fields as the basis for correlation.
Platform Implementation Guidance
SentinelOne
· Deploy as primary endpoint coverage after tenant-specific field and event-label validation.
· Prioritize hosts with high-value file access, administrative access, backup access, or virtualization-adjacent access.
· Use SentinelOne detections to support immediate containment decisions when active file transformation or recovery-path interference is observed.
Splunk
· Deploy as primary SIEM correlation coverage where endpoint, file, backup, virtualization, identity, and cloud-control logs are normalized.
· Validate indexes, sourcetypes, CIM mapping, field names, lookups, and baselines before production use.
· Use Splunk to connect behaviors across telemetry sources that individual tools cannot fully contextualize.
Elastic
· Deploy as endpoint and EQL sequence coverage where Elastic Defend or equivalent endpoint telemetry is available.
· Validate ECS mappings, event categories, event actions, and index patterns before production use.
· Use Elastic for ordered behavior such as process-to-file transformation and file transformation followed by ransom-note staging.
QRadar
· Deploy where upstream file, EDR, backup, VMware, and identity telemetry is available and normalized.
· Validate custom properties, reference sets, log sources, event mappings, and performance impact before production use.
· Treat QRadar coverage as moderate and dependent on upstream telemetry quality.
SIGMA
· Deploy after backend translation validation.
· Use SIGMA as portable detection guidance, not as proof that all target SIEMs will produce identical behavior.
· Validate backend field mappings, file-event support, command-line preservation, parser behavior, and false-positive behavior before production use.
YARA
· Deploy conditionally for malware triage, sandbox classification, repository scanning, endpoint file collection, and incident-response enrichment.
· Treat YARA hits as classification evidence, not proof of active execution or enterprise impact.
· Correlate YARA output with endpoint and operational telemetry before assigning incident severity.
AWS
· Deploy conditionally for Backup, snapshot, AMI, and backup-vault policy tampering.
· Keep S3 and KMS as optional recovery-architecture extensions only where customer architecture confirms those services are recovery-critical.
· Do not claim direct local encryption detection without workload endpoint telemetry.
Azure
· Deploy conditionally for Recovery Services Vault, Backup vault, backup-policy, protected-item, snapshot, image, and recovery-control tampering.
· Keep storage-account, Key Vault, and managed-disk monitoring as optional recovery-architecture extensions only where recovery-critical.
· Do not claim direct local encryption detection without workload endpoint telemetry.
GCP
· Deploy conditionally for Backup and DR, backup vault, backup, snapshot, image, and recovery-asset tampering.
· Keep Cloud Storage and Cloud KMS as optional recovery-architecture extensions only where recovery-critical.
· Do not claim direct local encryption detection without workload endpoint telemetry.
Suricata
· Do not deploy a Suricata rule for VECT at this stage.
· Use network telemetry only as supporting context when endpoint-confirmed file transformation, staging, recovery-path tampering, or extortion-supporting activity is already under investigation.
· Reassess only if validated VECT network artifacts become available.
SOC Output Requirements
· Alerts must identify whether the activity represents active destructive behavior, suspected pre-impact staging, recovery-path tampering, virtualization-adjacent impact, cloud recovery-control tampering, sample classification, or supporting network activity.
· Alerts must include host, user, process, file, path, asset role, timestamp, and telemetry source where available.
· Backup and cloud-control alerts must include resource, identity, source, action, account or subscription or project context, and result status where available.
· ESXi and virtualization alerts must include user, source host, management target, datastore or VM object, command or action, and maintenance-window context where available.
· YARA outputs must include sample source, match metadata, hash, file type, and investigation context.
S29 — Detection Coverage Summary
Section Purpose
· This section summarizes the validated detection coverage produced by the S25 rule set.
· Coverage is assessed by observable behavior, system role, telemetry dependency, and conditionality.
· The final S25 build evaluates 10 systems and contains 17 rules across 9 rule-bearing systems, with Suricata intentionally excluded due to lack of validated VECT network artifacts.
Final Rule Distribution
Suricata
0 rules.
SentinelOne
3 rules.
Splunk
3 rules.
Elastic
3 rules.
QRadar
2 rules.
SIGMA
2 rules.
YARA
1 conditional rule.
AWS
1 conditional rule.
Azure
1 conditional rule.
GCP
1 conditional rule.
Total S25 Rule Count
17 rules.
Primary Coverage Areas
Destructive File Transformation
· Covered by SentinelOne, Splunk, Elastic, QRadar, and SIGMA.
· Coverage is strongest where endpoint process telemetry, file telemetry, user context, host role, and affected-path information are available.
· Coverage weakens where file telemetry, file-size visibility, initiating-process attribution, command-line visibility, or host-role enrichment is incomplete.
· This is the strongest detection coverage area because VECT’s operational impact centers on destructive file modification.
Ransom-Note Staging with File-Impact Context
· Covered by SentinelOne, Splunk, and Elastic.
· Coverage is strongest when ransom-note-like artifacts appear during or after high-volume file transformation.
· Coverage is intentionally not built around ransom-note-only logic.
· Ransom-note artifacts remain supporting evidence unless paired with file, process, user, or asset-context evidence.
Recovery-Path Tampering
· Covered by SentinelOne, Splunk, Elastic, QRadar, SIGMA, AWS, Azure, and GCP.
· Coverage includes backup suppression, shadow copy interference, restore-point deletion, snapshot removal, vault policy changes, protected-item changes, AMI or image activity, and cloud recovery-control tampering.
· Coverage is strongest where backup-platform telemetry, cloud audit logs, identity context, maintenance-window awareness, and asset criticality are available.
· This is a high-value coverage area because recovery-path degradation materially increases destructive ransomware impact.
ESXi and Virtualization-Adjacent Impact
· Covered by SentinelOne, Splunk, Elastic, QRadar, and SIGMA where relevant telemetry exists.
· Coverage includes datastore activity, virtual disk activity, ESXi management commands, vCenter or VMware administrative activity, and virtualization-adjacent recovery interference.
· Coverage is strongest where ESXi, vCenter, VMware, datastore, management-host, identity, and endpoint telemetry are available.
· Coverage weakens significantly in environments without VMware or hypervisor-adjacent telemetry.
Cloud Recovery-Control Tampering
· Covered conditionally by AWS, Azure, and GCP.
· Coverage is limited to destructive-impact amplification through recovery-path, snapshot, backup, image, vault, and recovery-asset tampering.
· Cloud rules do not detect local VECT encryption unless workload endpoint telemetry is available.
· Coverage is strongest where logs are centralized, identity context is preserved, recovery assets are tagged, lifecycle policies are understood, and production recovery assets are scoped.
Sample Classification
· Covered conditionally by YARA.
· Coverage supports malware triage, repository scanning, sandbox classification, endpoint file collection, and incident-response enrichment.
· Coverage does not prove active execution, file impact, backup tampering, ESXi impact, or enterprise scope.
· Coverage depends on access to suspicious binaries or validated sample artifacts.
Network-Signature Detection
· Not covered by Suricata in S25.
· Network telemetry remains supporting investigation context.
· This is an intentional quality decision because current evidence does not support stable VECT network signatures, protocol traits, payload signatures, delivery infrastructure, or command-and-control patterns.
· Suricata should be reassessed only if validated network artifacts become available.
Coverage Strength Assessment
Strong Coverage
· Endpoint process-to-file transformation.
· File transformation with ransom-note staging.
· Backup and recovery-path tampering.
· SIEM correlation where endpoint, file, backup, virtualization, identity, and cloud-control fields are normalized.
· Elastic and SentinelOne endpoint coverage where telemetry is complete.
· Splunk correlation coverage where data sources are mature and mapped.
Moderate Coverage
· QRadar correlation coverage where custom properties and upstream telemetry are reliable.
· SIGMA portable detection where backend translation and file-event support are validated.
· ESXi and virtualization-adjacent coverage where VMware telemetry exists but is not uniformly complete.
· File-size-aware prioritization where file-size fields are available.
Conditional Coverage
· YARA sample classification.
· AWS recovery-control tampering.
· Azure recovery-control tampering.
· GCP recovery-control tampering.
· Network enrichment tied to suspicious endpoint or file activity.
· Crash, fault, instability, persistence, and lateral movement enrichment where supporting telemetry exists.
Not Covered as Primary Detection
· Suricata network signature detection.
· Network-only VECT detection.
· Extension-only VECT detection.
· Ransom-note-only detection.
· Hash-only detection.
· YARA-only enterprise detection.
· Cloud-control-only local encryption detection.
· Crash-only detection.
· Ransom-payment or decryptor-failure detection logic.
Coverage Dependencies
Endpoint Dependencies
· Process creation.
· Parent-child process lineage.
· Command line.
· Executable path.
· User context.
· Host identity.
· Host role.
· File creation, modification, rename, and deletion.
· File path, extension, and size.
· Endpoint tamper events where available.
SIEM Dependencies
· Normalized process fields.
· Normalized file fields.
· User and host context.
· Asset criticality.
· Backup-platform events.
· Virtualization events.
· Cloud-control events.
· Lookup or enrichment support for approved administrators, maintenance windows, and asset roles.
· Cross-source correlation windows based on ransomware execution tempo.
Backup and Recovery Dependencies
· Backup job events.
· Restore-point events.
· Snapshot events.
· Vault events.
· Retention-policy events.
· Protected-item events.
· Recovery-control events.
· Approved administrator and automation context.
Virtualization Dependencies
· ESXi logs.
· vCenter or VMware events.
· Datastore activity.
· Virtual disk activity.
· Snapshot activity.
· VM reconfiguration activity.
· Administrative authentication.
· Management-host telemetry.
Cloud Dependencies
· AWS CloudTrail, AWS Backup, EC2 snapshot and AMI activity.
· Azure Activity Log, Recovery Services Vault diagnostics, Azure Backup operation logs, Log Analytics ingestion.
· GCP Cloud Audit Logs, Backup and DR audit logs, Compute Engine snapshot and image activity.
· Identity context, resource context, lifecycle policy context, asset tags or labels, and recovery-asset scoping.
Coverage Gap Summary
· Suricata coverage remains unavailable because validated VECT network artifacts are not available.
· YARA remains conditional because sample artifacts can change and sample access is not guaranteed.
· Cloud detection remains conditional because control-plane logs do not directly observe local file encryption.
· ESXi coverage depends on VMware and virtualization-management telemetry that may not exist in all environments.
· QRadar and SIGMA effectiveness depends on parser quality, field normalization, backend translation, and upstream telemetry.
· File-size-aware detection depends on file-size fields that may not be available across all endpoint or SIEM sources.
· Recovery-path visibility depends on backup-platform and cloud-control telemetry being ingested and normalized.
Coverage Conclusion
· The S25 rule set provides strong behavioral coverage for VECT-aligned destructive ransomware activity across endpoint, SIEM, file, backup, recovery, and virtualization surfaces.
· The rule set appropriately avoids forcing weak network coverage and avoids overclaiming YARA or cloud-control visibility.
· The strongest operational coverage exists where endpoint process telemetry, file telemetry, backup telemetry, virtualization telemetry, identity context, cloud-control telemetry, and SIEM normalization are available.
· The final coverage model is appropriate for a ransomware-wiper report because it prioritizes destructive behavior, recovery-path risk, and virtualization impact over fragile static indicators.
S30 — Intelligence Maturity Assessment
Section Purpose
· This section assesses the maturity of the detection intelligence developed for the VECT ransomware-wiper report.
· The maturity assessment evaluates how well the report converts threat behavior, telemetry requirements, detection opportunities, and validated rules into deployable defensive guidance.
· The assessment is public-safe and does not disclose proprietary CyberDax scoring mechanics, internal calibration logic, rule-selection methodology, or implementation architecture.
Overall Intelligence Maturity
Maturity Rating
High for behavior-led detection strategy.
Maturity Qualification
Moderate to High for deployable detection engineering because several systems require customer telemetry validation, backend field validation, or conditional deployment scope.
Assessment Summary
· The report demonstrates strong intelligence maturity because detection is anchored to destructive operational behavior rather than static VECT identity.
· The report correctly prioritizes endpoint, file, backup, virtualization, and SIEM-correlation telemetry as the primary operational detection surfaces.
· The report appropriately treats YARA as conditional sample classification and cloud-control telemetry as recovery-path tampering detection.
· The report correctly excludes Suricata until validated network artifacts become available.
· The report maintains alignment from S21 strategy through S26 traceability and into the S27 through S30 operational model.
Behavioral Intelligence Maturity
Rating
High.
Rationale
· The report identifies destructive file transformation as the central detection behavior.
· The report treats ransom-note staging as meaningful only when correlated with file impact or suspicious execution.
· The report prioritizes backup, snapshot, vault, recovery-control, and virtualization-adjacent tampering because those behaviors directly increase destructive ransomware impact.
· The report remains resilient to VECT version changes, extension changes, ransom-note changes, binary renaming, packing changes, and possible correction of the current encryption flaw.
· The behavioral model supports Windows, Linux, and ESXi-aware detection rather than Windows-only assumptions.
Telemetry Maturity
Rating
Moderate to High.
Rationale
· The report clearly defines minimum viable telemetry and strong telemetry requirements across endpoint, file, backup, virtualization, identity, SIEM, network, web, application, and cloud-control sources.
· Endpoint and file telemetry are well defined as primary requirements.
· Backup and virtualization telemetry are properly prioritized as required for recovery-path and ESXi-impact visibility.
· Cloud-control telemetry is correctly scoped to recovery-path tampering and not direct local encryption visibility.
· Maturity remains partly conditional because real-world environments may lack file-size fields, initiating-process attribution, command-line visibility, ESXi telemetry, backup-platform logs, or normalized SIEM fields.
Detection Engineering Maturity
Rating
High.
Rationale
· The finalized S25 rule set contains 17 rules with system-specific detection roles and deployment constraints.
· Rule coverage aligns directly to S21 through S24 and is traceable in S26.
· Endpoint and SIEM platforms carry the primary detection burden, while YARA and cloud platforms remain conditional where appropriate.
· Rules avoid static IOC dependence, extension-only logic, ransom-note-only logic, hash-only logic, network-only assumptions, and alert-chain dependencies.
· Deployment guidance includes telemetry validation, field validation, baselining, allowlist governance, and customer-environment scoping.
· Maturity remains bounded by the need for customer-specific field validation, baseline definition, and platform-specific deployment testing.
Operational SOC Maturity
Rating
Moderate to High.
Rationale
· The report gives SOC workflows clear prioritization around active file transformation, backup tampering, ESXi activity, ransom-note staging, and cloud recovery-control tampering.
· The detection model distinguishes active destructive behavior, suspected pre-impact staging, recovery-path tampering, sample classification, and supporting network activity.
· The report supports Tier 1 triage, Tier 2 validation, incident-response escalation, containment prioritization, and threat hunting.
· Operational maturity depends on whether the customer can enrich alerts with host role, asset criticality, user context, maintenance windows, approved automation, and recovery-asset ownership.
· Environments without mature SIEM normalization or response playbooks may require additional operational preparation before high-confidence detection can be fully realized.
Threat Intelligence Maturity
Rating
Moderate to High.
Rationale
· The report incorporates public VECT behavioral traits without overfitting to fragile static artifacts.
· The report acknowledges VECT’s destructive implementation flaw while avoiding detection logic that depends on the flaw remaining unchanged.
· The report supports sample classification through YARA only where validated sample artifacts or malware repository context are available.
· The report avoids elevating unsupported network indicators to primary detection.
· Intelligence maturity remains conditional where future VECT variants change artifacts, fix implementation defects, alter ransomware workflow, or introduce new delivery and infrastructure patterns.
Cloud Detection Maturity
Rating
Moderate.
Rationale
· AWS, Azure, and GCP coverage is appropriately scoped to recovery-path, backup, snapshot, image, vault, and recovery-control tampering.
· The cloud rules are useful for detecting destructive-impact amplification in cloud-hosted or hybrid environments.
· The report does not overclaim cloud-control telemetry as direct local encryption visibility.
· Maturity remains moderate because cloud detection depends on audit-log enablement, log centralization, identity context, recovery-asset tagging, lifecycle-policy awareness, and workload endpoint telemetry for local execution confirmation.
Virtualization Detection Maturity
Rating
Moderate to High.
Rationale
· The report correctly prioritizes ESXi, datastore, virtual disk, and virtualization-management activity because VECT includes ESXi targeting.
· Splunk, SentinelOne, Elastic, QRadar, and SIGMA all contribute virtualization-adjacent coverage where telemetry exists.
· Maturity is high where ESXi, vCenter, VMware, datastore, administrative host, identity, and endpoint telemetry are available.
· Maturity is moderate where virtualization telemetry is incomplete or where virtualization activity is only visible through downstream symptoms.
Sample Classification Maturity
Rating
Moderate.
Rationale
· YARA is appropriately scoped to conditional malware sample classification and enrichment.
· The YARA rule uses a compound artifact model and avoids hash-only, extension-only, ransom-note-only, and generic crypto-only matching.
· Sample classification maturity remains moderate because YARA depends on access to suspicious binaries, sample artifacts, sandbox output, malware repository matches, and validation against benign software.
· YARA does not detect active enterprise execution or operational impact by itself.
Network Detection Maturity
Rating
Low for primary detection.
Rationale
· Network telemetry can support investigation but does not currently support a deployable Suricata rule for VECT.
· The report correctly avoids forcing a Suricata rule without validated network artifacts.
· Network maturity may improve if future VECT reporting provides validated C2 infrastructure, protocol markers, payload signatures, delivery patterns, TLS traits, HTTP structures, or other network artifacts.
· Until then, network telemetry remains supporting context only.
Maturity Improvement Priorities
Priority 1
Strengthen endpoint and file telemetry coverage.
· Ensure process lineage, command line, file action, file path, file size, initiating process, user context, and host role are available.
· Prioritize systems with access to high-value repositories, shared storage, backups, databases, and virtualization assets.
Priority 2
Improve recovery-path telemetry.
· Ensure backup-platform logs, snapshot activity, vault events, restore-point changes, retention-policy changes, and protected-item events are collected.
· Validate approved administrators, automation accounts, maintenance windows, and lifecycle policies.
Priority 3
Improve virtualization telemetry.
· Collect ESXi, vCenter, datastore, VM snapshot, VM reconfiguration, administrative session, and management-host telemetry.
· Enrich virtualization events with user, source host, object, datastore, maintenance-window, and asset-criticality context.
Priority 4
Improve SIEM normalization.
· Normalize process, file, user, host, backup, virtualization, identity, and cloud-control fields.
· Preserve fields needed for cross-source correlation and response context.
· Validate lookups or enrichment sources for host role, asset criticality, maintenance windows, approved administrators, and approved tools.
Priority 5
Improve cloud recovery-control monitoring.
· Validate AWS, Azure, and GCP audit-log coverage.
· Centralize logs across accounts, subscriptions, projects, Regions, folders, and organizations.
· Tag or label recovery-critical assets.
· Document lifecycle policies and approved automation.
· Correlate cloud recovery-control events with workload endpoint telemetry where available.
Priority 6
Maintain sample-classification readiness.
· Use YARA for malware triage, sandbox analysis, repository scanning, and incident evidence enrichment.
· Validate sample-derived artifacts before operational use.
· Keep YARA secondary to behavioral detection.
Final Intelligence Maturity Assessment
· The VECT Block 4 detection model is mature enough to support operational deployment planning after environment-specific telemetry validation.
· The detection strategy is strongest in environments with endpoint process telemetry, file telemetry, backup telemetry, virtualization telemetry, identity context, SIEM normalization, and cloud audit-log coverage.
· The report is appropriately conservative where evidence is conditional, including Suricata, YARA, and cloud-control detection.
· The final maturity posture is strong because the detection model prioritizes durable ransomware-wiper behavior, recovery impact, and virtualization risk while avoiding unsupported static or speculative detection claims.
S31 — Telemetry Dependencies
VECT defensive readiness depends on telemetry that can confirm destructive file transformation, identify the initiating process, determine affected file scope, validate recovery-path integrity, and expose virtualization-adjacent activity. The highest-value telemetry sources are endpoint process telemetry, file telemetry, backup-platform telemetry, virtualization telemetry, identity context, cloud-control telemetry, and SIEM correlation.
Endpoint and Process Dependencies
· Endpoint telemetry must capture process creation, process termination, parent-child process lineage, executable path, command line, process hash, user context, host identity, host role, timestamp, and privilege context where available.
· Endpoint telemetry must identify execution from user-writable paths, temporary directories, staging folders, administrative shares, recently created directories, removable media, and remote management contexts.
· Endpoint telemetry must preserve process relationships for binaries that initiate file enumeration, high-volume file writes, rename activity, extension changes, ransom-note placement, backup interference, or virtualization-adjacent access.
· Endpoint telemetry must support Windows, Linux, and ESXi-adjacent visibility where deployed because VECT’s risk model is cross-platform and cannot rely on Windows-only assumptions.
· Endpoint telemetry must support host-role enrichment so activity on file servers, backup servers, administrative jump hosts, database servers, virtualization management hosts, and privileged workstations can be prioritized.
File and Repository Dependencies
· File telemetry must capture creation, modification, rename, deletion, extension change, file path, file name, file size, file type, initiating process, initiating user, host identity, timestamp, and affected directory where available.
· File telemetry must cover local disks, mapped drives, network shares, file servers, NAS paths, database storage, backup staging areas, and virtualization datastore paths where available.
· File-size visibility is a high-value dependency because current VECT reporting identifies the destructive threshold at files larger than 131,072 bytes.
· File telemetry must support detection of high-volume file rewrite activity, rapid directory traversal, mass extension changes, ransom-note staging, and abnormal access to high-value repositories.
· File telemetry must be baseline-aware because backup jobs, indexing, data migration, software deployment, compression, encryption tools, antivirus scanning, and synchronization clients can generate high file volume.
Backup and Recovery Dependencies
· Backup-platform telemetry must capture backup job status, restore-point changes, snapshot creation and deletion, vault access, retention-policy modification, protected workload removal, backup job disablement, and unusual restore configuration changes.
· Recovery-control telemetry must preserve initiating identity, source host, administrative action, affected object, timestamp, maintenance-window context, and automation context.
· Backup-dependent environments require recovery telemetry because destructive ransomware risk cannot be accurately prioritized without visibility into whether recovery paths were impaired before, during, or after file transformation.
· Immutable, offline, or logically isolated backup validation remains required because detection alone does not restore data after destructive file transformation.
· Backup telemetry must be correlated with endpoint and file activity to distinguish ordinary backup administration from ransomware-aligned recovery-path interference.
Virtualization Dependencies
· VMware and ESXi environments require telemetry from ESXi hosts, vCenter, datastore activity, virtual disk interaction, VM snapshot activity, VM reconfiguration events, administrative authentication, and management-host activity.
· Virtualization telemetry must capture user context, source host, destination host, object name, datastore name, VM name, command activity, timestamp, and maintenance-window context where available.
· Virtualization visibility is required because damage to virtual disks, datastores, or snapshots can rapidly escalate from host-level compromise to multi-system operational disruption.
· Virtualization events must be correlated with endpoint, identity, file, backup, and SIEM telemetry where available.
· Environments without ESXi or virtualization-management telemetry may not detect hypervisor-adjacent impact until downstream service disruption or file damage becomes visible.
Cloud-Control Dependencies
· Cloud-hosted environments require workload endpoint telemetry for direct ransomware execution detection and cloud-control telemetry for backup, snapshot, image, storage, vault, recovery, and administrative tampering.
· AWS telemetry should include CloudTrail, AWS Backup events, EC2 snapshot activity, AMI activity, IAM identity context, account context, Region context, resource identifiers, and recovery-asset tags where available.
· Azure telemetry should include Activity Log, Recovery Services Vault diagnostics, Backup vault diagnostics, Azure Backup operation logs, Log Analytics ingestion, Entra ID context, subscription context, resource group, resource ID, and operation name.
· GCP telemetry should include Cloud Audit Logs, Backup and DR audit events, Compute Engine snapshot and image activity, storage-control events, project context, organization or folder context, identity context, and resource labels.
· Cloud-control telemetry must not be treated as direct local encryption visibility unless paired with workload endpoint, file, or EDR telemetry from the affected system.
SIEM and Correlation Dependencies
· SIEM normalization must preserve source, host, user, process, command line, file, action, timestamp, platform, identity, asset role, and control-plane fields needed for cross-source correlation.
· SIEM correlation must support time-window analysis between suspicious execution, file transformation, ransom-note staging, backup tampering, ESXi impact, outbound communication, and privileged activity.
· Cross-source correlation must use raw or normalized telemetry inputs and must not depend on another CyberDax rule firing first.
· Enrichment sources should include host role, asset criticality, approved administrators, maintenance windows, approved automation, backup ownership, recovery-asset tags, and virtualization ownership.
· Correlation quality depends on consistent field mapping, timestamp integrity, event retention, parser reliability, and operational context.
S32 — Detection Limitations
VECT detection is constrained by telemetry availability, field completeness, normalization quality, and the ability to distinguish destructive file transformation from legitimate high-volume enterprise activity. The strongest detection model is behavior-led, but even strong behavioral logic can degrade when endpoint, file, backup, virtualization, identity, or SIEM telemetry is incomplete.
Endpoint and File Visibility Limitations
· Environments without endpoint process telemetry cannot reliably identify the initiating process behind file transformation, ransom-note staging, or backup interference.
· Environments without file telemetry cannot reliably detect the mass rewrite, rename, extension-change, or size-aware file activity that defines the highest-confidence VECT detection surface.
· Environments without file-size visibility cannot directly evaluate the reported 131,072-byte destructive threshold and must rely on broader file-type, repository, and asset-criticality context.
· Environments without command-line visibility may miss staging behavior, administrative-tool abuse, backup suppression commands, virtualization-management activity, and suspicious shell execution.
· Environments without host-role or asset-criticality enrichment may generate excessive noise because high-volume file activity has different meaning on endpoints, file servers, backup servers, administrative jump hosts, database servers, and virtualization hosts.
Backup and Recovery Limitations
· Environments without backup-platform telemetry cannot reliably detect recovery-path interference before restore attempts fail.
· Backup job failures, restore-point gaps, snapshot removal, vault changes, and retention-policy changes may be missed if backup logs are not centralized and normalized.
· Legitimate backup administration can resemble recovery-path tampering unless user, host, timing, process, object, automation, and maintenance-window context are available.
· Recovery confidence cannot be inferred from backup product presence alone.
· Immutable or offline backup validation remains necessary because detection cannot reverse destructive file loss.
Virtualization Limitations
· Environments without ESXi, vCenter, datastore, or virtualization-management telemetry cannot reliably detect hypervisor-adjacent impact until symptoms appear in downstream systems.
· Datastore and virtual disk activity may be difficult to distinguish from approved maintenance unless administrative identity, source host, object scope, maintenance window, and asset role are available.
· Endpoint-only telemetry may not show direct ESXi or datastore impact unless management-host activity or virtualization-adjacent file access is visible.
· Virtualization-impact detection is strongest only where VMware, ESXi, identity, endpoint, backup, and SIEM telemetry can be correlated.
· ESXi impact can create multi-system business disruption faster than endpoint-only triage workflows may expect.
Cloud-Control Limitations
· Cloud-control-only environments cannot directly detect local VECT encryption or destructive file transformation unless endpoint or workload telemetry is available.
· AWS, Azure, and GCP audit logs can identify recovery-path tampering, snapshot deletion, backup modification, vault changes, image changes, storage-control changes, and unusual administrative activity, but they do not prove local ransomware execution by themselves.
· Cloud detection depends on audit-log enablement, log centralization, identity context, account or subscription or project coverage, recovery-asset tagging, lifecycle-policy awareness, and retention.
· Cloud recovery-control detections must be scoped as destructive-impact amplification unless workload endpoint telemetry confirms local execution.
· Multi-cloud and hybrid environments may fragment visibility across separate logging pipelines unless SIEM normalization is mature.
Network and Sample Classification Limitations
· Network-only environments cannot provide adequate VECT ransomware-wiper detection because the most reliable observable behavior is local destructive file transformation rather than stable network communication.
· Suricata deployment remains unsupported without validated VECT network indicators, protocol traits, payload signatures, delivery infrastructure, or command-and-control patterns.
· YARA-only coverage is insufficient for enterprise detection because sample classification does not prove active execution, file impact, backup tampering, ESXi impact, or operational scope.
· YARA should support malware triage, sandbox classification, repository scanning, and incident-response enrichment, not primary enterprise detection.
· Static indicators, file extensions, ransom-note names, hashes, and sample strings may change across variants, affiliates, or copycat tooling.
Operational Limitations
· Detection must not trigger on file volume alone.
· Detection must not rely on ransom-note artifacts alone.
· Detection must not rely on extension-only logic.
· Detection must not depend on another CyberDax rule firing first.
· Detection must not treat legitimate backup, virtualization, cloud, or administrative maintenance as malicious without context.
· Detection must not overfit to the current VECT encryption flaw because future variants may correct the defect while retaining destructive ransomware behavior.
· Detection must not treat ransom payment, decryptor failure, or post-incident recovery outcome as detection inputs.
S33 — Defensive Control & Hardening Improvements
Defensive hardening for VECT must prioritize containment of destructive file transformation, protection of recovery paths, restriction of privileged write access, validation of virtualization controls, and telemetry coverage for behavior-led detection. The most important improvements are those that reduce blast radius and preserve recoverability even when endpoint execution occurs.
Endpoint and Execution Hardening
· Enforce application control or execution control on servers, administrative workstations, backup-accessible hosts, and systems with access to high-value repositories.
· Restrict execution from user-writable directories, temporary folders, staging paths, administrative shares, recently created directories, and removable media where business operations allow.
· Require command-line logging, process lineage capture, parent-child process visibility, and endpoint tamper protection across high-value systems.
· Prioritize EDR coverage on file servers, database servers, backup servers, administrative jump hosts, virtualization management systems, privileged workstations, and cloud workloads.
· Harden endpoint protection policies to prevent unauthorized disabling, policy weakening, exclusion creation, telemetry suppression, and remediation bypass.
· Monitor abnormal CPU, disk I/O, file-handle activity, and process restarts when paired with high-volume file activity.
File, Storage, and Repository Hardening
· Limit write access to shared drives, file servers, NAS paths, database storage, and operational repositories using least privilege.
· Reduce persistent mapped-drive exposure for users and service accounts that do not require broad write access.
· Segment high-value repositories so a single compromised endpoint cannot modify broad enterprise data.
· Implement file-integrity monitoring or file-activity monitoring for critical repositories, databases, virtual disks, backup staging paths, and operational storage.
· Establish baselines for normal file write, rename, delete, extension-change, and directory traversal behavior by host role and repository type.
· Alert when high-volume file transformation affects business-critical paths or operationally meaningful file sizes.
Backup and Recovery Hardening
· Maintain immutable, offline, or logically isolated backups for systems supporting critical business services.
· Restrict backup administration to dedicated privileged roles, approved administrative hosts, and monitored workflows.
· Require MFA and privileged access governance for backup consoles, recovery vaults, snapshot systems, restore-management platforms, and backup automation.
· Monitor restore-point deletion, snapshot removal, retention-policy modification, vault access changes, protected workload removal, backup job disablement, and unusual restore configuration changes.
· Test restoration regularly for critical repositories, databases, virtual machines, backup artifacts, and business-service dependencies.
· Preserve snapshot and backup logs in a location not easily modified by the same identities that administer recovery systems.
Virtualization Hardening
· Restrict ESXi, vCenter, datastore, VM snapshot, and virtual disk administration to approved administrators, approved management hosts, and monitored maintenance windows.
· Enforce MFA and privileged access controls for virtualization management platforms.
· Monitor VM power operations, VM reconfiguration, snapshot removal, datastore file modification, virtual disk access, host service changes, and ESXi shell activity.
· Segment virtualization management networks from standard endpoint and user networks.
· Harden administrative jump hosts used for virtualization and backup management.
· Validate that virtual machine restoration, datastore recovery, and snapshot recovery can be performed from trusted sources after destructive activity.
Cloud Recovery-Control Hardening
· Enable and centralize AWS, Azure, and GCP audit logs for accounts, subscriptions, projects, Regions, folders, and organizations that support critical workloads or recovery assets.
· Restrict snapshot, image, vault, backup-policy, storage, KMS, and recovery-control modification to approved roles and automation.
· Tag or label recovery-critical assets so destructive-impact events can be prioritized.
· Monitor unusual identity, source IP, user agent, Region, project, subscription, account, or maintenance-window deviations.
· Document lifecycle policies so approved retention and snapshot actions can be distinguished from destructive tampering.
· Correlate cloud recovery-control events with workload endpoint telemetry where available.
SOC and Response Hardening
· Prioritize alerts involving active mass file transformation, recovery-path tampering, ESXi impact, ransom-note staging, shared-storage impact, or cloud recovery-control tampering.
· Ensure Tier 1 workflows escalate active file transformation and backup tampering immediately.
· Ensure Tier 2 workflows validate initiating process, user legitimacy, host role, affected-file scope, backup status, and virtualization exposure.
· Ensure incident response workflows prioritize host isolation, credential containment, backup protection, ESXi administrative review, snapshot preservation, and evidence capture.
· Maintain playbooks for destructive ransomware, backup-protection actions, virtualization containment, cloud recovery-control review, and affected-file scoping.
· Preserve telemetry before restoration activity overwrites evidence needed to reconstruct the destructive window.
S34 — Defensive Control & Hardening Architecture
Figure 6
The defensive architecture for VECT should be built around layered containment, behavior-led detection, recovery-path protection, and virtualization resilience. The architecture must assume that a single compromised host with broad write access can cause enterprise-scale damage if it can reach shared storage, backups, databases, or virtual disks.
Architecture Layer 1 — Execution Control and Endpoint Visibility
· Endpoint protection, EDR, process telemetry, command-line visibility, process lineage, file telemetry, and tamper protection form the first defensive layer.
· Application control should restrict unapproved binaries, scripts, and administrative tools on high-value systems.
· Execution from user-writable, temporary, staging, and administrative-share paths should be restricted or heavily monitored.
· Endpoint telemetry must provide enough context to determine initiating process, parent process, command line, user, host role, and affected file scope.
· Endpoint controls should be hardened so attackers cannot easily disable protection, suppress telemetry, add broad exclusions, or weaken remediation.
Architecture Layer 2 — File Repository and Storage Segmentation
· File servers, NAS paths, shared drives, operational repositories, database storage, and backup staging paths should be segmented by business criticality and access need.
· Privileged write access should be minimized, reviewed, and monitored.
· High-value repositories should have file-activity monitoring, file-integrity monitoring, and anomaly detection for mass modification, rename bursts, extension changes, and delete activity.
· Repository access should be enriched with user role, host role, service-account purpose, and approved workflow context.
· Broad write access from endpoints, jump hosts, and service accounts should be treated as a material ransomware blast-radius risk.
Architecture Layer 3 — Backup and Recovery Protection
· Backup systems, recovery vaults, restore-point repositories, snapshot systems, and retention-policy controls should be isolated from standard endpoint access.
· Backup administration should require dedicated privileged access, MFA, approved administrative hosts, monitored change windows, and strong logging.
· Immutable or offline backup copies should be maintained for critical systems and tested regularly.
· Recovery logs should be protected against modification by the same accounts that administer production backups.
· Restore validation must include databases, file shares, virtual machines, operational repositories, and business-service dependencies.
Architecture Layer 4 — Virtualization and ESXi Protection
· ESXi hosts, vCenter, datastores, virtual disks, VM snapshots, and virtualization-management interfaces should be treated as high-risk ransomware impact surfaces.
· Virtualization management networks should be segmented and restricted to approved administrative paths.
· Administrative access should be logged, MFA-protected, and correlated with endpoint activity on management hosts.
· Datastore file modification, VM reconfiguration, snapshot removal, host service changes, and ESXi shell activity should be monitored.
· Virtualization recovery plans should account for datastore integrity, virtual disk recovery, backup dependencies, and management-plane compromise.
Architecture Layer 5 — Cloud Recovery-Control Protection
· Cloud recovery controls should be monitored across AWS, Azure, and GCP where cloud-hosted workloads or hybrid recovery models are used.
· Cloud audit logs should be centralized and correlated with identity, workload, endpoint, backup, and SIEM telemetry.
· Snapshot deletion, image deregistration, vault-policy modification, backup deletion, protected-resource removal, storage-control changes, and key-disabling activity should be treated as recovery-impact events.
· Cloud detection must remain scoped to recovery-path tampering unless endpoint or workload telemetry confirms local ransomware execution.
· Cloud recovery assets should be tagged or labeled so SOC teams can prioritize activity affecting critical systems.
Architecture Layer 6 — SIEM Correlation and SOC Operations
· SIEM architecture should normalize endpoint, file, backup, virtualization, identity, cloud-control, and network telemetry into fields that support cross-source correlation.
· Correlation should join suspicious execution, file transformation, ransom-note staging, recovery-path tampering, ESXi activity, privileged identity activity, and cloud recovery-control changes.
· Detection outputs should distinguish active destructive behavior, suspected pre-impact staging, recovery-path tampering, sample classification, cloud recovery-control tampering, and supporting network activity.
· SOC routing should prioritize alerts involving high-value repositories, backup systems, ESXi infrastructure, privileged users, shared storage, or multi-host file activity.
· Response architecture should support rapid isolation, credential containment, backup protection, snapshot preservation, ESXi review, and evidence capture.
S35 — Defensive Control Mapping Matrix
Endpoint Detection and Response
· Maps to destructive file transformation, suspicious execution, process lineage, command-line activity, endpoint tampering, ransom-note staging, and local recovery interference.
· Supports early containment when suspicious execution is paired with high-volume file modification or recovery-path activity.
· Requires process telemetry, file telemetry, user context, host identity, host role, and command-line visibility.
· Control maturity is strongest where EDR can capture initiating process, affected file scope, and endpoint tamper events.
File Integrity and File Activity Monitoring
· Maps to mass file modification, rename bursts, extension changes, delete activity, ransom-note placement, and abnormal file-access concentration.
· Supports detection of ransomware-wiper behavior across endpoints, file servers, NAS paths, shared repositories, databases, archives, virtual disks, and backup staging paths.
· Requires file path, file name, file action, file size, initiating process, user, host, timestamp, and repository context.
· Control maturity is strongest where file telemetry includes file-size fields and initiating-process attribution.
Backup and Recovery Controls
· Maps to restore-point deletion, snapshot removal, vault-policy changes, retention-policy modification, protected workload removal, backup job disablement, and recovery-control tampering.
· Supports recoverability assurance and detection of destructive-impact amplification.
· Requires backup-platform logs, administrative identity, source host, affected object, maintenance-window context, and approved automation context.
· Control maturity is strongest where backup telemetry is centralized, immutable backup validation exists, and recovery changes are correlated with endpoint file activity.
Virtualization and ESXi Controls
· Maps to datastore modification, virtual disk access, VM snapshot removal, VM reconfiguration, ESXi shell activity, vCenter activity, and virtualization-management access.
· Supports detection of multi-system disruption risk through virtual infrastructure.
· Requires ESXi logs, vCenter events, datastore telemetry, virtual disk activity, administrative authentication, management-host telemetry, and SIEM correlation.
· Control maturity is strongest where virtualization events are enriched with user, source host, object, datastore, maintenance-window, and asset-criticality context.
Identity and Privileged Access Management
· Maps to privileged execution, administrative context, backup-console access, virtualization management access, cloud recovery-control changes, and shared-storage reach.
· Supports blast-radius reduction by limiting which users, service accounts, and hosts can modify critical data or recovery assets.
· Requires identity logs, MFA status, privileged access workflow records, service-account ownership, session context, and administrative role mapping.
· Control maturity is strongest where privileged actions are time-bound, role-specific, monitored, and tied to approved administrative hosts.
Cloud Security and Recovery-Control Monitoring
· Maps to AWS Backup, EBS snapshot, AMI, backup-vault policy, Azure Recovery Services Vault, backup policy, protected item, snapshot, image, GCP snapshot, image, backup, storage, and recovery-control tampering.
· Supports detection of cloud recovery-path degradation and destructive-impact amplification.
· Requires audit-log coverage, identity context, account or subscription or project context, resource identifiers, tags or labels, lifecycle-policy context, and centralized logging.
· Control maturity is strongest where cloud recovery-control events are correlated with workload endpoint telemetry and recovery-asset criticality.
SIEM and Correlation Engineering
· Maps to cross-source detection of suspicious execution, file transformation, ransom-note staging, backup tampering, ESXi impact, cloud recovery-control tampering, identity activity, and supporting network signals.
· Supports enterprise detection where individual signals are weak but combined behavior is high confidence.
· Requires normalized process, file, user, host, backup, virtualization, identity, cloud-control, timestamp, and asset fields.
· Control maturity is strongest where correlation windows, field mappings, lookups, baselines, and response routing are validated.
Network, DNS, and Web Telemetry
· Maps to supporting evidence for suspicious outbound communication, possible staging, potential exfiltration, rare destinations, direct IP connections, unusual DNS, and web download activity.
· Supports investigation and enrichment when paired with endpoint-confirmed destructive file activity.
· Requires source host, source process where available, user, destination, port, protocol, timestamp, byte count, direction, reputation, and first-seen status.
· Control maturity remains supporting because current VECT detection is not network-signature-led.
Malware Analysis and YARA Classification
· Maps to sample triage, sandbox classification, repository scanning, endpoint file collection, malware-lab analysis, and incident-response enrichment.
· Supports VECT sample identification where validated artifacts are available.
· Requires suspicious binaries, extracted strings, file type, PE or ELF handling, sandbox output, malware repository context, and false-positive validation.
· Control maturity remains conditional because YARA classification does not prove active execution or operational impact.
S36 — CyberDax Intelligence Maturity Assessment
Overall Intelligence Maturity
High for behavior-led defensive strategy.
Moderate to High for deployable defensive maturity because several controls require customer telemetry validation, field normalization, environment-specific baselines, recovery-asset mapping, and operational testing.
Behavioral Intelligence Maturity
High.
The defensive model is mature because it prioritizes destructive file transformation, recovery-path interference, ESXi and virtualization impact, and cross-source telemetry correlation over fragile static indicators. The model remains resilient if VECT changes file extension, ransom-note name, binary filename, packing, infrastructure, delivery path, or corrects the current encryption flaw.
Telemetry Maturity
Moderate to High.
The telemetry model clearly identifies minimum viable coverage and strong coverage requirements across endpoint, file, backup, virtualization, identity, SIEM, cloud-control, network, web, application, and malware-analysis sources. Maturity remains conditional because real-world environments may lack file-size fields, initiating-process attribution, command-line visibility, ESXi logs, backup-platform logs, cloud asset tags, or normalized SIEM fields.
Defensive Control Maturity
Moderate to High.
The control model appropriately prioritizes endpoint visibility, file repository protection, backup isolation, virtualization hardening, cloud recovery-control monitoring, privileged access governance, and SOC correlation. Maturity remains conditional because control effectiveness depends on whether the organization can enforce least privilege, validate recovery, monitor privileged actions, and distinguish approved administrative workflows from ransomware-aligned behavior.
Recovery Resilience Maturity
Moderate.
The report strongly identifies backup and recovery controls as critical to VECT resilience. Maturity remains moderate because recoverability depends on immutable or offline backups, restore testing, backup-log integrity, snapshot protection, vault governance, and the ability to restore virtualized and database-backed services after destructive file transformation.
Virtualization Maturity
Moderate to High.
The report correctly prioritizes ESXi, vCenter, datastore, virtual disk, VM snapshot, and management-host telemetry because VECT includes ESXi targeting. Maturity is high where virtualization telemetry is complete and correlated with identity, endpoint, backup, and SIEM data. Maturity is moderate where virtualization visibility is incomplete or downstream disruption is the first observable sign of impact.
Cloud Recovery-Control Maturity
Moderate.
AWS, Azure, and GCP coverage is appropriately scoped to recovery-path, snapshot, image, vault, backup-policy, storage, and administrative tampering. Maturity remains moderate because cloud telemetry does not directly detect local ransomware execution without workload endpoint visibility, and because effective cloud recovery monitoring depends on centralized audit logs, resource tagging, lifecycle-policy awareness, identity context, and cross-account or cross-project coverage.
Sample Classification Maturity
Moderate.
YARA and malware-analysis support are useful for sample classification, sandbox triage, repository scanning, endpoint file collection, and incident-response enrichment. Maturity remains moderate because sample classification depends on access to suspicious binaries, validated artifacts, sandbox output, malware repository context, and false-positive review. YARA does not detect active destructive enterprise behavior by itself.
SOC Operational Maturity
Moderate to High.
The SOC model is mature where Tier 1 can rapidly escalate active file transformation, backup tampering, ESXi impact, ransom-note staging, and cloud recovery-control tampering; Tier 2 can validate execution context, affected asset role, user legitimacy, file scope, host criticality, backup status, and virtualization exposure; and incident response can isolate hosts, protect backups, preserve snapshots, review ESXi activity, contain credentials, and capture evidence. Maturity remains conditional where playbooks, enrichment, retention, or response authority are incomplete.
Final Intelligence Maturity Assessment
The VECT defensive model is mature enough to support operational hardening and deployment planning after environment-specific telemetry validation. The strongest maturity exists where endpoint process telemetry, file telemetry, backup telemetry, virtualization telemetry, identity context, cloud-control telemetry, and SIEM normalization are available. The model is appropriately conservative where evidence is conditional, including network detection, YARA classification, and cloud-control visibility. Final maturity is strong because the report prioritizes durable ransomware-wiper behavior, recovery impact, and virtualization risk while avoiding unsupported static or speculative detection claims.
S37 — Strategic Defensive Improvements
Priority 1 — Strengthen Endpoint and File Telemetry
· Ensure endpoint telemetry captures process lineage, command line, user context, host identity, host role, executable path, parent process, and timestamp.
· Ensure file telemetry captures file creation, modification, rename, deletion, extension change, file path, file name, file size, initiating process, initiating user, and affected directory.
· Prioritize telemetry on file servers, database servers, backup-accessible systems, administrative workstations, virtualization management hosts, privileged-user systems, and cloud workloads.
· Validate that endpoint and file telemetry can support rapid affected-file scoping during destructive ransomware activity.
Priority 2 — Reduce Shared-Storage Blast Radius
· Limit broad write access to shared drives, file servers, NAS paths, operational repositories, database storage, and backup staging paths.
· Remove unnecessary persistent mapped drives and excessive service-account permissions.
· Segment high-value repositories by business criticality and access need.
· Monitor abnormal file activity by user, process, source host, repository, and time window.
· Treat broad repository write access as a ransomware-wiper risk condition.
Priority 3 — Harden Backup and Recovery Controls
· Maintain immutable, offline, or logically isolated backups for critical business systems.
· Monitor backup deletion, restore-point changes, snapshot removal, vault access, retention-policy changes, protected workload removal, and backup job disablement.
· Restrict backup administration to approved privileged roles, approved administrative hosts, and monitored workflows.
· Test restoration for critical file repositories, databases, virtual machines, backup artifacts, and business-service dependencies.
· Protect backup logs from modification by the same identities that administer recovery platforms.
Priority 4 — Improve ESXi and Virtualization Resilience
· Centralize ESXi, vCenter, datastore, VM snapshot, virtual disk, VM reconfiguration, administrative session, and management-host telemetry.
· Restrict virtualization management access to approved administrators, approved hosts, and approved maintenance windows.
· Segment virtualization management networks from standard endpoint and user networks.
· Monitor datastore modification, virtual disk access, VM removal, snapshot removal, host service changes, and ESXi shell activity.
· Validate recovery procedures for virtual disks, datastores, VM snapshots, and virtualization management-plane compromise.
Priority 5 — Strengthen Cloud Recovery-Control Monitoring
· Validate AWS, Azure, and GCP audit-log coverage for all accounts, subscriptions, projects, Regions, folders, and organizations that support critical workloads.
· Monitor backup, snapshot, image, vault, storage, KMS, recovery-policy, protected-resource, and administrative tampering.
· Tag or label recovery-critical cloud assets.
· Document lifecycle policies and approved automation to reduce false positives.
· Correlate cloud recovery-control events with workload endpoint telemetry where available.
Priority 6 — Improve SIEM Normalization and Correlation
· Normalize process, command line, file, user, host, backup, virtualization, identity, cloud-control, timestamp, asset-role, and action fields.
· Preserve fields needed to correlate suspicious execution, file transformation, ransom-note staging, backup tampering, ESXi activity, cloud recovery-control changes, and privileged activity.
· Validate lookups for approved administrators, maintenance windows, approved automation, host roles, asset criticality, backup ownership, and recovery-asset tags.
· Ensure correlation logic uses raw or normalized telemetry inputs and does not depend on alert-to-alert chaining.
· Route high-severity alerts based on destructive file activity, recovery-path interference, ESXi impact, and high-value asset exposure.
Priority 7 — Maintain Behavior-Led Detection and Response Readiness
· Keep detection focused on destructive file transformation, suspicious execution context, recovery-path interference, virtualization-adjacent activity, and affected-file scope.
· Treat ransom-note artifacts, extensions, hashes, YARA matches, and network indicators as supporting evidence unless validated and correlated.
· Maintain playbooks for destructive ransomware, backup protection, ESXi review, cloud recovery-control review, credential containment, and affected-file scoping.
· Run exercises that test host isolation, backup protection, snapshot preservation, virtualization recovery, and restoration assurance.
· Review detection logic when future VECT variants change artifacts, correct encryption defects, alter delivery paths, or introduce validated network indicators.
S38 — Attack Economics & Organizational Impact Model
Figure 7
VECT changes the economic model of ransomware response because payment, negotiation, or attacker-provided decryption may not restore affected files. The current VECT 2.0 implementation creates a destructive file-loss condition for files larger than the reported 131,072-byte threshold, which means the attacker’s extortion model may still generate pressure even when the malware cannot support reliable recovery.
The primary organizational impact is not limited to ransom demand exposure. The larger business risk is recovery uncertainty across file repositories, databases, archives, backup artifacts, virtual disks, shared storage, and virtualized infrastructure. Once destructive file transformation reaches those assets, the organization must determine which files were modified, which files are recoverable, whether backup copies remain trustworthy, whether virtual infrastructure was affected, and whether business services can be restored without reintroducing corrupted data.
VECT increases attacker leverage by compressing the response timeline. A single system with broad write access to shared repositories, backup-accessible paths, or virtualization infrastructure can create enterprise-scale disruption before the organization has full incident scope. This creates immediate pressure on executive leadership, legal teams, incident response, infrastructure teams, backup administrators, business continuity leaders, and customer-facing stakeholders.
The economic model is most severe when destructive file transformation overlaps with recovery-path interference. Backup deletion, snapshot removal, vault-policy modification, restore-point tampering, retention-policy changes, event-log clearing, or endpoint-control degradation can shift the event from contained ransomware response to broad operational restoration. Recovery cost increases further when the organization lacks endpoint process telemetry, file-size visibility, initiating-process attribution, ESXi telemetry, backup-platform logs, or normalized SIEM correlation.
Virtualization impact materially expands economic exposure. If VECT-like activity affects ESXi hosts, vCenter-managed environments, datastores, virtual disks, VM snapshots, or virtualization management systems, the business impact can extend across many dependent systems. Affected organizations may need to validate datastore integrity, restore virtual machines, rebuild management-plane trust, confirm backup consistency, and sequence recovery around business-service dependencies.
Cloud-hosted environments create a separate but related economic exposure. Cloud-control logs may show backup, snapshot, image, storage, vault, or recovery-policy tampering, but they do not prove local ransomware execution without workload endpoint telemetry. Where cloud recovery assets are affected, recovery cost can include account-level investigation, identity review, snapshot validation, image assurance, recovery-policy restoration, and workload-level forensic scoping.
The most likely economic outcome is a moderate to high response-cost event even when the attack is contained before full enterprise disruption. Destructive ransomware-wiper activity requires more assurance work than ordinary commodity malware because responders must validate file integrity, backup integrity, recovery viability, virtualization exposure, and telemetry completeness before leadership can declare operational confidence.
S39 — Economic Impact & Organizational Exposure
VECT creates economic exposure through destructive data loss, recovery uncertainty, operational downtime, infrastructure restoration, legal and regulatory review, customer assurance, and executive governance. The financial impact is driven by how far file transformation spreads, whether recovery controls remain intact, and whether virtualization or shared-storage infrastructure is affected.
Low Impact Exposure
Low impact exposure occurs when VECT-like activity is detected rapidly on a small number of endpoints or non-critical systems, with no confirmed impact to file servers, databases, backup repositories, virtual disks, ESXi infrastructure, regulated data stores, production systems, or customer-facing services.
· Expected response includes endpoint isolation, forensic validation, telemetry review, limited recovery testing, detection tuning, and executive incident tracking.
· Business interruption remains limited because critical repositories and recovery systems are not affected.
· Recovery confidence is restored quickly because endpoint and file telemetry confirm limited scope.
· Estimated economic impact remains aligned to the Block 1 low scenario of $1M to $4M.
Moderate Impact Exposure
Moderate impact exposure occurs when destructive file transformation affects a meaningful but contained set of endpoints, servers, shared repositories, backup-accessible systems, or virtualization-adjacent assets. Recovery remains achievable, but assurance requires deeper validation across files, backups, systems, and infrastructure dependencies.
· Expected response includes endpoint isolation, affected-file scoping, backup validation, selective restoration, credential containment, SOC surge activity, forensic review, legal coordination, detection tuning, and business-unit recovery planning.
· Recovery confidence depends on validating that backups, snapshots, databases, virtual disks, and shared repositories were not broadly impaired.
· Operational disruption may affect business units, internal service availability, recovery timelines, and customer assurance workflows.
· Estimated economic impact remains aligned to the Block 1 moderate scenario of $6M to $25M.
High Impact Exposure
High impact exposure occurs when destructive file transformation affects business-critical repositories, databases, virtual disks, VMware ESXi datastores, backup systems, recovery controls, production workloads, regulated data stores, or customer-facing services. This scenario can produce prolonged operational interruption and broad recovery uncertainty.
· Expected response includes enterprise containment, broad restoration activity, backup rehydration, database recovery, virtual machine recovery, data-integrity validation, virtualization review, legal and regulatory analysis, customer assurance, insurance reporting, and board-level incident governance.
· Recovery may be delayed by incomplete telemetry, damaged files, impaired backups, unavailable snapshots, corrupted virtual disks, or uncertainty around whether restored data is trustworthy.
· Business impact may include service downtime, revenue disruption, contractual exposure, customer confidence loss, regulatory scrutiny, and increased cyber insurance complexity.
· Estimated economic impact remains aligned to the Block 1 high scenario of $30M to $150M or higher.
Organizational Exposure Drivers
· Scope of affected endpoints, servers, file shares, databases, virtual disks, backup artifacts, cloud workloads, and ESXi infrastructure.
· Whether files larger than the reported 131,072-byte threshold were modified, corrupted, or rendered unrecoverable.
· Degree of shared-storage, mapped-drive, NAS, database, and repository exposure from the compromised context.
· Availability and integrity of immutable, offline, or logically isolated backups.
· Evidence of backup deletion, snapshot removal, vault-policy modification, restore-point tampering, or retention-policy changes.
· Availability of endpoint process telemetry, file telemetry, file-size fields, command-line visibility, initiating-process attribution, and host-role enrichment.
· Availability of ESXi, vCenter, datastore, VM snapshot, virtual disk, and virtualization-management telemetry.
· Availability of cloud audit logs and workload endpoint telemetry for cloud-hosted systems.
· Ability to distinguish malicious file transformation from backup jobs, indexing, data migration, synchronization, compression, encryption tools, and approved administrative workflows.
· Need for legal review, regulatory notification analysis, customer assurance, cyber insurance reporting, executive incident governance, and board-level reporting.
Organizational Impact Assessment
The organizational impact of VECT should be assessed as high because the event can undermine confidence in data integrity and recovery viability. Even when compromise is contained, the organization may need to validate whether affected files were recoverable, whether backup copies are trustworthy, whether virtual infrastructure remains intact, and whether business services can resume without hidden data corruption.
The highest exposure condition occurs when destructive file transformation, recovery-path interference, and virtualization impact converge. In that condition, the incident may no longer be a standard ransomware response; it becomes an enterprise resilience event requiring coordinated recovery, legal oversight, customer communication, infrastructure validation, and executive decision-making.
S40 — References
Vendor / Platform Documentation
VMware Documentation — vSphere documentation library
· hxxps://docs[.]vmware[.]com/en/VMware-vSphere/index.html
Amazon Web Services Documentation — AWS Backup developer guide
· hxxps://docs[.]aws.amazon[.]com/aws-backup/latest/devguide/whatisbackup.html
Amazon Web Services Documentation — AWS CloudTrail user guide
· hxxps://docs[.]aws.amazon[.]com/awscloudtrail/latest/userguide/cloudtrail-user-guide.html
Microsoft Learn — Azure Backup monitoring and reporting
· hxxps://learn[.]microsoft[.]com/en-us/azure/backup/monitor-azure-backup
Microsoft Learn — Azure Activity Log overview
· hxxps://learn[.]microsoft[.]com/en-us/azure/azure-monitor/platform/activity-log
Google Cloud Documentation — Cloud Audit Logs overview
· hxxps://cloud[.]google[.]com/logging/docs/audit
Google Cloud Documentation — Backup and DR Service overview
· hxxps://cloud[.]google[.]com/backup-disaster-recovery/docs/concepts/backup-dr
Threat Technique Framework
MITRE ATT&CK Framework — Enterprise Matrix / Techniques Catalog
· hxxps://attack[.]mitre[.]org/
Security Vendor Analysis
Check Point Research — VECT: Ransomware by design, Wiper by accident
· hxxps://research[.]checkpoint[.]com/2026/vect-ransomware-by-design-wiper-by-accident/
Check Point Blog — VECT ransomware: why paying will not get your files back
· hxxps://blog[.]checkpoint[.]com/security/vect-ransomware-why-paying-wont-get-your-files-back/
The Hacker News — VECT 2.0 ransomware irreversibly destroys files over 131KB on Windows, Linux, and ESXi
· hxxps://thehackernews[.]com/2026/04/vect-20-ransomware-irreversibly.html
BleepingComputer — Broken VECT 2.0 ransomware acts as a data wiper for large files
· hxxps://www[.]bleepingcomputer[.]com/news/security/broken-vect-20-ransomware-acts-as-a-data-wiper-for-large-files/
Threat Tradecraft and Intrusion Patterns
CISA — StopRansomware guidance
· hxxps://www[.]cisa[.]gov/stopransomware
CISA — Ransomware guide
· hxxps://www[.]cisa[.]gov/resources-tools/resources/ransomware-guide