[EXP] Cisco Catalyst SD-WAN Controller Authentication Bypass Enables Rogue Peering and Administrative Control
Report Type: EXP
Threat Category: Network Infrastructure Exploitation / SD-WAN Control-Plane Authentication Bypass
Assessment Date: May 14, 2026
Primary Impact Domain: Network Control-Plane Integrity
Secondary Impact Domains: Administrative Control; SD-WAN Fabric Trust; Routing and Traffic Steering; Branch and Site Connectivity; Cloud-Hosted Network Exposure; Internal Network Segmentation; Business Continuity
Affected Asset Class: Cisco Catalyst SD-WAN Controller, Manager, Validator, edge-device, NETCONF-exposed SD-WAN infrastructure, and cloud-hosted SD-WAN supporting assets
Threat Objective Classification: Rogue Peering, Unauthorized Administrative Access, SD-WAN Control-Plane Trust Abuse, Configuration Manipulation, and Post-Access Fabric Impact
BLUF
Cisco Catalyst SD-WAN Controller Authentication Bypass creates material enterprise risk by weakening confidence in SD-WAN control-plane trust, administrative access, routing behavior, policy enforcement, and branch-to-enterprise connectivity. The risk is driven by unauthorized peering, suspicious administrative authentication, NETCONF management activity, configuration manipulation, and potential SD-WAN fabric impact that may resemble legitimate provider administration, controller migration, emergency maintenance, disaster recovery, automation, or edge-device onboarding. Executive action is required to confirm controller exposure, approved peer inventory, administrative-source governance, NETCONF restrictions, configuration-audit visibility, change-management linkage, and readiness to investigate or reverse unauthorized SD-WAN fabric changes before routing, segmentation, branch connectivity, or data-center access risk expands.
Executive Risk Translation
Cisco Catalyst SD-WAN Controller Authentication Bypass shifts business risk from a narrow network-device vulnerability to an enterprise connectivity, segmentation, and administrative-control assurance issue. The primary concern is not only whether a vulnerable controller exists, but whether SD-WAN trust relationships, peer identity, administrative access, NETCONF workflows, configuration changes, and routing or policy updates can be trusted during suspicious activity. If exploitation or attempted exploitation occurred, response may expand into SD-WAN topology validation, controller and manager log review, administrative-access investigation, NETCONF source review, configuration-drift assessment, route and tunnel validation, branch and data-center connectivity assurance, service-provider coordination, privileged-access review, and executive reporting, creating financial, operational, resilience, compliance, security-governance, and business-continuity exposure beyond the affected SD-WAN controller.
S3 — Why This Matters Now
· Cisco SD-WAN Controllers and Managers sit in a high-trust position because they influence branch connectivity, routing, policy enforcement, device registration, control-plane relationships, and administrative workflows.
· Unauthorized SD-WAN control-plane trust activity can create business impact without resembling conventional malware execution or endpoint compromise.
· Rogue peering or unexpected peer-state changes may allow attacker-controlled infrastructure to appear operationally legitimate if topology baselines are weak.
· Successful administrative authentication or NETCONF access following suspicious control-plane activity creates a higher-risk path from network exposure to privileged SD-WAN management.
· Configuration changes affecting routes, tunnels, policies, certificates, device registration, peer state, or fabric trust can alter business connectivity and security boundaries.
· Service-provider access, managed-service workflows, emergency administration, disaster recovery, controller migration, automation, and edge onboarding can resemble suspicious activity without strong change context.
· Encrypted control-plane traffic and limited packet visibility make behavior-led correlation more important than payload inspection, scanner output, advisory references, or static exploit indicators.
· Organizations without centralized SD-WAN logs, topology inventory, approved peer lists, administrative-source baselines, NETCONF visibility, and configuration audit records face elevated risk of delayed detection and incomplete scoping.
S4 — Key Judgments
· Cisco Catalyst SD-WAN Controller Authentication Bypass creates a high-priority network-control-plane risk when unauthorized peering, administrative access, NETCONF activity, or configuration manipulation is possible.
· The primary business risk is loss of confidence that SD-WAN control-plane trust, administrative control, routing behavior, policy enforcement, and fabric relationships remain authorized and intact.
· The strongest enterprise risk signal is suspicious SD-WAN peering or peer-state activity followed by successful administrative authentication, NETCONF access, configuration change, or fabric-impact behavior.
· Control-plane traffic alone should not be treated as confirmed compromise, but it requires urgent review when the source, peer identity, timing, ASN, geography, access path, controller relationship, or topology context deviates from baseline.
· NETCONF access from unfamiliar or unauthorized sources is a high-value escalation signal when it follows suspicious peering, control-plane instability, administrative authentication, or peer identity mismatch.
· SD-WAN configuration changes are high-risk when they affect routes, tunnels, policies, certificates, device registration, peer state, controller relationships, or fabric trust without matching change authorization.
· Network-only visibility is insufficient because the highest-confidence evidence depends on correlation across controller logs, manager logs, authentication records, NETCONF records, configuration audits, topology inventory, and change-management data.
· Executive risk reduction depends on SD-WAN topology assurance, approved-peer validation, administrative-source governance, configuration-audit readiness, NETCONF control, change-management linkage, and response playbooks for suspected fabric manipulation.
S5 — Executive Risk Summary
Business Risk
Cisco Catalyst SD-WAN Controller Authentication Bypass can create material business risk by weakening confidence in the integrity of SD-WAN control-plane trust, administrative access, routing behavior, policy enforcement, and branch-to-enterprise connectivity. Risk increases when affected SD-WAN infrastructure supports critical branch operations, sensitive internal segmentation, data-center access, cloud connectivity, regulated business units, third-party administration, managed-service operations, or environments where routing and policy manipulation could expose sensitive systems.
Technical Cause
The risk is driven by unauthorized abuse of the SD-WAN control-plane authentication pathway, which may allow attacker activity to appear as trusted peering, administrative access, NETCONF management, or authorized infrastructure behavior. Suspicious activity may include rogue peer registration, unexpected peer identity fields, administrative authentication from unfamiliar sources, NETCONF access from unauthorized networks, configuration changes, route or tunnel manipulation, certificate or fabric-trust changes, device-registration changes, peer-state changes, and persistent access from unfamiliar infrastructure.
Threat Posture
The threat posture is elevated because SD-WAN control-plane compromise can blend into legitimate infrastructure behavior after trust is established. The risk is amplified when approved peer inventories are incomplete, administrative-source baselines are weak, NETCONF access is broadly permitted, configuration audit visibility is limited, change records lack object-level detail, or provider-managed workflows obscure source and actor context. Successful abuse may create routing disruption, segmentation erosion, unauthorized access paths, branch connectivity impact, cloud or data-center exposure, and executive-level operational uncertainty without a clear malware-based signal.
Executive Decision Requirement
Executives must require validation of Cisco SD-WAN Controller and Manager exposure, approved topology and peer inventory, administrative-source governance, NETCONF access controls, configuration-audit retention, change-management linkage, service-provider access boundaries, and SOC readiness for SD-WAN control-plane investigation. Response leadership should also confirm that suspicious peering, administrative authentication, NETCONF access, and configuration changes are reviewed historically rather than closed solely because the activity resembles normal SD-WAN operations.
S6 — Executive Cost Summary
Cisco Catalyst SD-WAN Controller Authentication Bypass creates financial exposure based on the number and criticality of affected SD-WAN controllers, managers, edge devices, branch sites, data-center links, cloud connections, administrative accounts, NETCONF-enabled systems, configuration changes, route and tunnel dependencies, managed-service paths, telemetry completeness, and the degree to which unauthorized control-plane activity may have altered SD-WAN fabric behavior.
Low Impact Scenario
Rapid assessment confirms that vulnerable or exposed Cisco SD-WAN infrastructure is limited, approved peer inventory is accurate, administrative sources are well governed, NETCONF access is restricted, no suspicious rogue peering is identified, no unauthorized administrative authentication is confirmed, no SD-WAN configuration drift is present, and change-management records align with observed controller and manager activity. Response remains limited to exposure validation, controller and manager log review, approved-peer verification, NETCONF source review, detection tuning, and executive tracking; estimated impact $200K to $1M.
Moderate Impact Scenario
One or more Cisco SD-WAN Controllers or Managers show suspicious control-plane access, unknown peer identity fields, peer-state anomalies, administrative authentication from unfamiliar sources, NETCONF access from unauthorized networks, incomplete change linkage, or limited configuration drift without confirmed broad routing manipulation, segmentation failure, data-center exposure, major branch outage, or sustained attacker control. Response requires SD-WAN topology validation, controller and manager log analysis, administrative-account review, NETCONF session investigation, configuration-drift assessment, route and tunnel review, service-provider coordination, change-record reconciliation, targeted containment, detection tuning, and executive incident coordination; estimated impact $1.2M to $8M.
High Impact Scenario
Confirmed or strongly suspected unauthorized SD-WAN control-plane trust activity results in rogue peering, privileged administrative access, NETCONF management activity, route or tunnel manipulation, policy modification, certificate or fabric-trust changes, device-registration abuse, persistent unfamiliar access, segmentation impact, branch disruption, or new connectivity into sensitive internal environments. Response may require emergency SD-WAN control-plane containment, controller and manager remediation, route and policy rollback, branch connectivity validation, segmentation review, privileged credential rotation, service-provider escalation, business-continuity coordination, forensic reconstruction, customer or business-unit assurance, legal review, regulatory assessment where applicable, cyber insurance coordination, and board-level incident governance; estimated impact $8M to $40M or higher.
S6A — Key Cost Drivers
· Number and criticality of affected Cisco SD-WAN Controllers, Managers, Validators, edge devices, branch sites, data-center connections, cloud connections, and managed-service paths.
· Whether suspicious activity involved rogue peering, unauthorized peer-state changes, unfamiliar System IPs, site IDs, domain IDs, peer types, public IPs, device identities, or controller relationships.
· Whether successful administrative authentication occurred from unfamiliar, external, unauthorized, cloud-hosted, VPN-associated, service-provider, or unmanaged source infrastructure.
· Whether NETCONF access occurred from unfamiliar or unauthorized sources, especially after suspicious peering, control-plane instability, or administrative authentication.
· Whether SD-WAN configuration changes affected routes, tunnels, policies, certificates, templates, device registration, peer state, controller relationships, or fabric trust.
· Whether unauthorized SD-WAN fabric changes created new access paths into sensitive internal segments, identity systems, management systems, backup systems, data-center environments, cloud networks, or regulated business environments.
· Completeness of Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, network-flow telemetry, firewall logs, topology inventory, and change-management records.
· Ability to distinguish legitimate controller migration, edge onboarding, disaster recovery, emergency access, automation, service-provider work, and managed-service administration from suspicious control-plane behavior.
· Scope of required route validation, tunnel validation, policy review, certificate review, peer inventory reconciliation, configuration rollback, branch connectivity testing, and segmentation assurance.
· Need for administrative-account review, privileged credential rotation, service-provider escalation, third-party assurance, legal review, regulatory assessment, cyber insurance coordination, business-unit communication, or board reporting.
Most Likely Scenario Justification
Moderate scenario is most likely when suspicious SD-WAN control-plane or administrative activity requires historical review, topology validation, NETCONF investigation, and configuration-drift assessment, but available evidence does not confirm broad fabric manipulation, sustained attacker control, regulated-data exposure, major branch outage, or enterprise-wide routing impact. The estimate moves toward the lower end when telemetry confirms narrow exposure, approved operational context, no unauthorized peer activity, no NETCONF misuse, no configuration drift, and no post-access traffic-flow change. The estimate moves toward the upper end when affected infrastructure supports critical branches, data-center access, cloud connectivity, regulated environments, service-provider administration, sensitive segmentation, incomplete logging, weak peer inventory, or configuration changes that cannot be confidently tied to approved activity.
S6B — Compliance and Risk Context
Compliance Exposure Indicator
Moderate to High depending on whether suspicious SD-WAN control-plane activity, unauthorized administrative access, NETCONF misuse, configuration manipulation, route or policy changes, segmentation impact, telemetry gaps, or incomplete forensic scoping affected regulated environments, customer-facing services, sensitive internal systems, contractual service obligations, third-party access paths, or evidence required for incident investigation.
Risk Register Entry
Risk Title
Cisco Catalyst SD-WAN Control-Plane Trust and Administrative-Control Exposure
Risk Description
Adversaries may abuse Cisco Catalyst SD-WAN Controller authentication weaknesses to establish unauthorized control-plane trust, create rogue peer relationships, gain administrative access, use NETCONF management paths, alter SD-WAN configuration, manipulate routes or policies, affect fabric trust, or create new access paths into sensitive enterprise environments. This can create operational, financial, compliance, resilience, third-party governance, and executive oversight exposure.
Likelihood
Medium to High.
Impact
Severe.
Risk Rating
Critical.
Annualized Risk Exposure
Estimated $2M to $18M or higher based on SD-WAN footprint, internet exposure, controller criticality, branch dependency, data-center and cloud connectivity, sensitive-segment reliance, approved-peer inventory quality, NETCONF access control, administrative-source governance, configuration-audit readiness, service-provider dependency, telemetry completeness, containment complexity, route and policy rollback burden, operational downtime, and legal or regulatory obligations.
S7 — Risk Drivers
· SD-WAN Controllers and Managers are high-trust infrastructure components that can influence routing, policy, branch connectivity, device registration, and fabric relationships.
· Unauthorized peering can create a trust problem that may not look like ordinary external intrusion once the activity appears as infrastructure behavior.
· Administrative authentication from unfamiliar sources creates elevated risk when it follows suspicious control-plane activity or peer-state change.
· NETCONF access can represent privileged SD-WAN management activity and should be treated as high value when source, timing, peer-state, or topology context is abnormal.
· Route, tunnel, policy, certificate, device-registration, peer-state, or fabric-trust changes can create business-impacting connectivity and segmentation consequences.
· Incomplete peer inventory makes it difficult to distinguish legitimate edge onboarding, controller relationships, provider activity, and rogue infrastructure.
· Weak administrative-source baselines can cause unauthorized access to blend with VPN, cloud, service-provider, managed-service, automation, or emergency-access workflows.
· Encrypted control-plane traffic reduces the value of payload inspection and increases dependence on topology-aware behavioral correlation.
· Configuration audit gaps can prevent responders from determining whether SD-WAN fabric state changed after suspicious access.
· Change-management gaps can create false confidence during controller migration, disaster recovery, edge onboarding, emergency maintenance, or service-provider support.
· Network-only visibility is insufficient because confirmation depends on controller-side logs, manager logs, authentication records, NETCONF evidence, configuration audit data, and approved topology context.
S8 — Bottom Line for Executives
Cisco Catalyst SD-WAN Controller Authentication Bypass should be treated as a high-priority network-control-plane and business-connectivity risk. The key executive concern is not only whether a vulnerable controller exists, but whether SD-WAN trust relationships, administrative access, NETCONF management, routing behavior, policy enforcement, and fabric changes remain authorized and explainable. Risk reduction depends on approved-peer validation, administrative-source governance, NETCONF restriction, configuration-audit readiness, topology inventory, service-provider access control, and SOC workflows that can correlate suspicious peering with administrative and configuration activity. Organizations should prioritize this report as an SD-WAN trust assurance issue because unauthorized control-plane activity can create routing disruption, segmentation exposure, branch impact, cloud and data-center access risk, compliance pressure, and board-level governance requirements.
S9 — Board-Level Takeaway
Cisco Catalyst SD-WAN Controller Authentication Bypass can turn trusted network-control-plane infrastructure into a business-risk amplifier. The board-level concern is that attackers may establish unauthorized trust, gain administrative control, manipulate SD-WAN configuration, or alter connectivity before the organization can confidently distinguish malicious activity from normal provider, migration, emergency, or branch operations. Leadership should require evidence that SD-WAN topology is known, peer relationships are approved, administrative access is governed, NETCONF sources are restricted, configuration changes are auditable, service-provider paths are controlled, and suspicious fabric activity can be investigated with sufficient evidence. This report supports governance decisions around SD-WAN resilience, segmentation assurance, privileged-access control, third-party administration, telemetry readiness, incident response maturity, and executive oversight of network-control-plane exposure.
Figure 2
S10 — Threat Overview
Cisco Catalyst SD-WAN Controller Authentication Bypass represents a high-impact network-control-plane exposure because successful abuse may allow unauthorized activity to move from external or unapproved access into trusted SD-WAN fabric behavior. The core risk is not limited to exploitation of a single controller. The broader concern is whether an attacker can establish or influence SD-WAN trust relationships, appear as a valid peer, access administrative functions, use NETCONF management paths, or manipulate configuration objects that affect routing, tunnels, policy, device registration, certificates, peer state, or fabric trust.
This activity is operationally significant because SD-WAN Controllers and Managers influence how distributed enterprise locations connect to internal systems, cloud environments, data centers, third-party networks, and sensitive business services. Unauthorized control-plane trust or administrative access can create downstream exposure across branch operations, segmentation boundaries, traffic routing, remote-site connectivity, and managed-service trust paths.
The threat model should be treated as behavior-led rather than indicator-led. The most important evidence is not a CVE string, scanner output, port observation, or advisory reference. The most important evidence is suspicious sequencing between control-plane activity, peer-state change, administrative authentication, NETCONF access, configuration modification, and SD-WAN fabric impact.
Detection and response should assume that successful activity may not look obviously malicious after trust is established. Once an attacker appears as a trusted peer or gains administrative access, activity may resemble controller migration, service-provider troubleshooting, emergency maintenance, automation, edge onboarding, or normal SD-WAN operations unless validated against approved topology, peer inventory, administrative-source baselines, and change-management records.
S11 — Threat Classification and Type
Threat Type
Network-control-plane exploitation and administrative-control abuse.
Threat Sub-Type
Cisco SD-WAN Controller authentication bypass enabling unauthorized peering, privileged management access, NETCONF activity, and configuration manipulation.
Operational Classification
High-impact infrastructure trust compromise affecting SD-WAN control-plane integrity, administrative assurance, routing confidence, segmentation reliability, and enterprise connectivity.
Primary Function
The primary function is to obtain unauthorized SD-WAN control-plane or management-plane positioning that may allow the attacker to appear trusted, access administrative workflows, interact with NETCONF-exposed infrastructure, alter SD-WAN configuration, or influence distributed enterprise connectivity.
S12 — Campaign or Activity Overview
This report does not require attribution to a specific threat actor or named campaign. The assessed activity model is based on the operational risk created by Cisco Catalyst SD-WAN Controller authentication bypass conditions and the post-access behaviors that matter most to enterprise defenders.
The most relevant activity pattern is a progression from unauthorized control-plane interaction toward trusted SD-WAN positioning or privileged management activity. This may include suspicious source access to Controller or Manager services, peer-state anomalies, unexpected peer identity fields, administrative authentication from unfamiliar infrastructure, NETCONF access, and configuration changes affecting SD-WAN fabric behavior.
A likely operational sequence may include:
· External or unauthorized access to Cisco SD-WAN Controller or Manager control-plane services.
· Attempted or successful interaction with SD-WAN peer-establishment or control-connection workflows.
· Appearance of unfamiliar source IPs, public IPs, System IPs, site IDs, domain IDs, peer types, device identities, or controller relationships.
· Successful administrative authentication from an unfamiliar, unauthorized, or poorly governed source path.
· NETCONF access to SD-WAN infrastructure from a source not aligned with approved administration, automation, emergency access, or service-provider workflows.
· Configuration changes affecting routes, tunnels, policies, certificates, templates, device registration, peer state, controller relationships, or fabric trust.
· New or unexpected traffic-flow behavior after suspicious control-plane, administrative, NETCONF, or configuration activity.
The activity should be assessed as an enterprise control-plane trust issue rather than a simple perimeter-access event. The operational concern is whether the attacker can use SD-WAN trust, management, or configuration pathways to affect connectivity, segmentation, data-center reachability, cloud access, branch operations, or sensitive internal environments.
S13 — Targets and Exposure Surface
The highest-risk targets are organizations where Cisco Catalyst SD-WAN infrastructure supports distributed connectivity, centralized routing and policy enforcement, managed-service administration, sensitive segmentation, or business-critical branch and data-center operations.
Primary exposure surfaces include:
· Cisco SD-WAN Controllers and Managers reachable from external, service-provider, managed-service, VPN, emergency-access, or administrative networks.
· Cisco SD-WAN control-plane services that support peering, control connections, peer-state changes, device registration, controller relationships, and fabric-trust workflows.
· SD-WAN administrative interfaces used for controller, manager, route, tunnel, policy, certificate, template, device-registration, peer-state, and fabric-trust administration.
· NETCONF-exposed SD-WAN infrastructure reachable from administrative, automation, provider, or insufficiently restricted source networks.
· Approved and expected peer relationships involving Controllers, Validators, Managers, edge devices, System IPs, site IDs, domain IDs, public IPs, device identities, and controller relationships.
· Administrative source networks, VPN paths, service-provider access paths, emergency-access paths, automation systems, and management networks.
· Configuration audit sources, topology inventories, change-management records, and maintenance-window records needed to validate whether observed SD-WAN changes were authorized.
· Branch, data-center, cloud, remote-site, and sensitive internal segments whose connectivity may be affected by route, tunnel, policy, certificate, or fabric-trust manipulation.
Exposure is highest where SD-WAN infrastructure is internet-reachable, externally administered, provider-managed, poorly baselined, weakly logged, or connected to sensitive internal routing and segmentation paths.
S14 — Sectors / Countries Affected
Sectors Affected
· Financial services, banking, insurance, payment-processing, and capital-markets organizations using SD-WAN for branch, data-center, cloud, or regulated network connectivity.
· Healthcare, life sciences, hospitals, clinics, medical research, and regulated care-delivery environments relying on SD-WAN for site connectivity and sensitive data access.
· Government, defense, public-sector, municipal, and critical public-service organizations using distributed network infrastructure and centralized policy enforcement.
· Telecommunications, managed service providers, network service providers, and enterprise IT service organizations administering or supporting SD-WAN infrastructure for customers.
· Energy, utilities, transportation, logistics, manufacturing, and industrial organizations relying on SD-WAN for operational sites, remote facilities, and business-continuity connectivity.
· Retail, ecommerce, hospitality, and distributed branch organizations using SD-WAN to connect stores, payment environments, warehouses, call centers, and corporate services.
· Technology, software development, cloud operations, SaaS, and engineering organizations with SD-WAN connectivity into development, production, management, or cloud environments.
· Education, research institutions, university systems, and shared campus environments with distributed sites and mixed administrative ownership.
· Legal, consulting, accounting, professional services, and business-services firms with distributed offices and sensitive client data access.
· Organizations with large branch networks, remote-site operations, third-party administered SD-WAN, provider-managed SD-WAN, centralized routing policy, sensitive segmentation requirements, or incomplete peer inventory.
· Organizations relying on Cisco Catalyst SD-WAN Controllers, Managers, Validators, NETCONF workflows, service-provider administration, automation, or centralized configuration management to operate enterprise connectivity.
Countries Affected
· Global.
· Exposure is not limited to a single country or region because Cisco SD-WAN infrastructure, distributed enterprise connectivity, service-provider administration, cloud connectivity, branch networking, and managed-service workflows are used globally.
· Countries with large financial, healthcare, government, telecommunications, energy, manufacturing, transportation, technology, retail, or managed-service sectors may face elevated operational exposure.
· Country-specific impact should be assessed by Cisco SD-WAN footprint, controller exposure, approved peer inventory, administrative-source governance, NETCONF restriction, topology quality, configuration-audit visibility, service-provider dependency, branch criticality, cloud and data-center connectivity, and incident-response readiness rather than geography alone.
S15 — Adversary Capability Profiling
Capability Level
Moderate to High.
Technical Sophistication
Moderate to High. Successful operational use requires understanding of Cisco SD-WAN control-plane behavior, peer relationships, administrative workflows, NETCONF access patterns, configuration objects, and post-access routing or policy impact. The initial vulnerability may reduce access complexity, but meaningful exploitation and persistence of impact require network-control-plane awareness.
Infrastructure Maturity
Moderate. The actor may need infrastructure capable of reaching exposed SD-WAN services, rotating through cloud, VPN, hosting, provider, or unmanaged networks, and sustaining access paths that can blend with administrative or service-provider activity. Higher maturity is required to maintain low-noise activity across peer establishment, administrative authentication, NETCONF access, and configuration manipulation.
Operational Scale
Moderate to High. Single-environment activity may be targeted and narrow, but the same operating model can scale across organizations with similar SD-WAN exposure, provider-managed access patterns, incomplete peer inventories, or weak configuration-audit practices. Broad scaling is most plausible where exposed controllers, common administrative patterns, or repeatable NETCONF and SD-WAN management workflows exist.
Escalation Likelihood
High when suspicious control-plane activity is followed by administrative authentication, NETCONF access, configuration changes, route or tunnel manipulation, policy changes, certificate changes, device-registration changes, peer-state changes, or new connectivity into sensitive internal environments. Lower confidence should be assigned when activity is limited to isolated access attempts without peer-state, authentication, NETCONF, configuration, or fabric-impact evidence.
S16 — Targeting Probability Assessment
Overall Targeting Probability
Medium to High.
Targeting Drivers
· Cisco SD-WAN Controllers and Managers occupy a high-trust position within enterprise network architecture.
· Successful abuse may provide access to routing, policy, device-registration, peer-state, NETCONF, certificate, and fabric-trust workflows.
· SD-WAN infrastructure often connects branch sites, data centers, cloud environments, remote sites, and sensitive internal systems.
· Externally reachable or provider-accessible SD-WAN services create attractive access paths for adversaries seeking infrastructure-level control.
· Managed-service, service-provider, VPN, automation, and emergency-access workflows may create ambiguity that attackers can exploit to blend with legitimate administration.
· Incomplete peer inventory, weak administrative-source governance, limited configuration-audit visibility, and poor change-management linkage increase attacker opportunity.
· Unauthorized SD-WAN configuration changes can affect segmentation, traffic routing, branch connectivity, cloud reachability, and access to sensitive internal environments.
· Encrypted control-plane traffic and limited payload visibility can delay detection if organizations depend on static indicators or port-only monitoring.
Most Likely Targets
· Organizations with internet-exposed or externally reachable Cisco SD-WAN Controllers or Managers.
· Large distributed enterprises with many branch, data-center, cloud, remote-site, or third-party connectivity dependencies.
· Financial services, healthcare, government, telecommunications, energy, transportation, retail, manufacturing, technology, and managed-service environments.
· Organizations with provider-managed, co-managed, or third-party administered SD-WAN infrastructure.
· Environments with incomplete peer inventory, weak administrative-source baselines, broad NETCONF access, or limited configuration audit retention.
· Organizations where SD-WAN routing, tunnel, policy, certificate, device-registration, or fabric-trust manipulation could affect sensitive internal network access.
· Environments with critical segmentation, regulated systems, cloud connectivity, high-value business services, or operational dependency on centralized SD-WAN policy enforcement.
S17 — MITRE ATT&CK Chain Flow Mapping
Stage 1 — Exposure and Remote Access Path
Cisco Catalyst SD-WAN Controller Authentication Bypass begins with a reachable SD-WAN control-plane or management-plane access path. This may include internet-facing controller exposure, provider-accessible infrastructure, VPN or managed-service paths, emergency-access workflows, or administrative networks with insufficient source restriction.
· ATT&CK mapping: External Remote Services T1133.
· Confidence: Conditional. Reachability is a relevant precondition, but exposure alone should not be treated as compromise.
Stage 2 — Unauthorized Control-Plane Interaction
The next stage is suspicious interaction with Cisco SD-WAN Controller or Manager control-plane services. This may include unknown source access, unexpected peer-state activity, control-connection anomalies, or unfamiliar peer identity fields. The operational concern is unauthorized interaction with SD-WAN trust-establishment behavior, not generic scanning.
· ATT&CK mapping: Exploit Public-Facing Application T1190.
· Confidence: Conditional to likely. Suspicious control-plane interaction is central to the report model, but it requires source, peer, timing, topology, and controller-side context.
Stage 3 — Administrative Authentication or NETCONF Management Access
If activity progresses, the actor may obtain or use administrative access, or interact with NETCONF-exposed SD-WAN infrastructure. This stage is higher priority when the source is unfamiliar, newly observed, external, unauthorized, or not aligned with approved administration, automation, service-provider, or emergency-access workflows.
· ATT&CK mapping: Valid Accounts T1078.
· ATT&CK mapping: Remote Services T1021.
· Confidence: Likely when successful administrative authentication or NETCONF access follows suspicious peering, peer-state activity, or control-plane anomalies.
Stage 4 — SD-WAN Topology or Configuration Review
After trusted or administrative positioning, the actor may review SD-WAN topology, peer relationships, route state, tunnel configuration, policy objects, controller relationships, device registration, certificate state, or fabric-trust context. This stage supports decision-making before configuration manipulation or fabric-impact activity.
· ATT&CK mapping: System Network Configuration Discovery T1016.
· Confidence: Conditional. Configuration or topology review should be assessed through SD-WAN Manager logs, Controller logs, NETCONF records, audit records, and administrative-session context.
Stage 5 — SD-WAN Configuration or Trust Manipulation
The actor may alter routes, tunnels, policies, certificates, templates, device-registration state, peer state, controller relationships, account or access artifacts, or fabric-trust objects. Configuration change becomes more concerning when the actor, source, object, timing, peer context, or approval record does not align with expected SD-WAN operations.
· ATT&CK mapping: Account Manipulation T1098.
· Confidence: Conditional. T1098 is applicable only where account, access, certificate, trust, or administrative-control artifacts are modified. Route, tunnel, policy, or peer-state manipulation should be described in SD-WAN operational terms and not forced into an ATT&CK mapping.
Stage 6 — Fabric Impact and Business Assurance Exposure
The final operational outcome is uncertainty over whether SD-WAN control-plane trust, administrative control, routing behavior, segmentation, branch connectivity, cloud access, and data-center reachability remained authorized and intact. This stage is most severe when affected infrastructure supports regulated environments, critical branches, sensitive segmentation, managed-service administration, or high-value internal systems.
· Confidence: High where suspicious peering, administrative authentication, NETCONF access, configuration change, topology mismatch, or traffic-flow change overlaps with critical SD-WAN infrastructure.
S18 — Attack Path Narrative (Signal-Aligned Execution Flow)
Cisco Catalyst SD-WAN Controller Authentication Bypass should be understood as a control-plane trust abuse path rather than a conventional malware execution chain. The attacker objective is to move from unauthorized reachability into trusted SD-WAN positioning, administrative access, NETCONF management activity, configuration manipulation, or fabric-impact behavior.
Stage 1 — SD-WAN Control-Plane Reachability
The attack path begins when Cisco SD-WAN Controller or Manager infrastructure is reachable from an external, provider, VPN, managed-service, emergency-access, automation, or otherwise unapproved source path. Reachability alone does not indicate compromise, but it creates the condition under which authentication bypass or unauthorized control-plane interaction may become operationally meaningful.
Relevant Signals
· External or unfamiliar source access to Cisco SD-WAN Controller or Manager infrastructure.
· Source IPs not present in approved SD-WAN peer, administrative-source, service-provider, automation, or emergency-access inventories.
· Repeated access attempts against SD-WAN control-plane or management-plane services.
· Newly observed source infrastructure interacting with SD-WAN assets.
Stage 2 — Unauthorized Peering or Control-Plane Interaction
The next stage involves suspicious interaction with SD-WAN peering, control-connection, peer-state, device-registration, or controller-relationship behavior. The attacker may attempt to appear as trusted SD-WAN infrastructure or trigger control-plane state changes that do not align with approved topology.
Relevant Signals
· Unknown or unexpected peer activity.
· Rogue peer registration or peer-state changes.
· Unfamiliar System IPs, site IDs, domain IDs, peer types, public IPs, device identities, or controller relationships.
· Control-connection anomalies or peer churn outside approved maintenance windows.
· Controller or Manager events that do not match approved peer inventory.
Stage 3 — Administrative Authentication or NETCONF Access
If control-plane trust abuse progresses, the attacker may attempt administrative authentication or NETCONF access against SD-WAN infrastructure. This stage is higher confidence when activity follows suspicious peering, peer-state change, or control-plane instability and originates from an unfamiliar or unauthorized source.
Relevant Signals
· Successful administrative authentication from unfamiliar, external, or unauthorized source networks.
· Administrative access inconsistent with approved VPN, service-provider, automation, or emergency-access paths.
· NETCONF access from unfamiliar, newly observed, or unauthorized sources.
· NETCONF activity following suspicious peering, control-plane instability, or administrative authentication.
· Failed-to-successful administrative authentication patterns involving SD-WAN management accounts.
Stage 4 — SD-WAN Configuration or Trust Manipulation
The attacker may attempt to change SD-WAN configuration, peer relationships, route behavior, tunnel state, policy enforcement, certificate posture, device registration, or fabric trust. This stage represents a major escalation because configuration manipulation can affect business connectivity and segmentation.
Relevant Signals
· SD-WAN configuration changes following suspicious control-plane or administrative activity.
· Route, tunnel, policy, certificate, template, device-registration, peer-state, or fabric-trust changes.
· Configuration changes without matching change ticket, maintenance record, service-provider record, automation record, or emergency-access record.
· Configuration export, import, rollback, synchronization, or policy deployment activity near suspicious access.
· Historical configuration drift after anomalous peering or NETCONF access.
Stage 5 — Fabric Impact and Continued Access
If configuration or trust manipulation succeeds, the attacker may create new access paths, alter routing, affect segmentation, disrupt branch connectivity, or preserve recurring access through unauthorized peer, account, certificate, or configuration artifacts. This stage should be treated as the highest operational concern because it may affect distributed enterprise connectivity.
Relevant Signals
· New or unexpected traffic-flow behavior after suspicious SD-WAN access.
· New communication paths involving branch, data-center, cloud, remote-site, or sensitive internal segments.
· Persistent or recurring access from unfamiliar sources after initial suspicious activity.
· Unauthorized key, account, certificate, peer, or configuration artifacts where telemetry supports review.
· Fabric-trust or configuration changes that survive restart, rollback, patching, or remediation.
S19 — Attack Chain Risk Amplification Summary
Cisco Catalyst SD-WAN Controller Authentication Bypass becomes materially more severe when activity progresses from exposure into trusted positioning, privileged management, configuration manipulation, or SD-WAN fabric impact. The risk is amplified because SD-WAN infrastructure controls routing, segmentation, branch connectivity, cloud reachability, and policy behavior across distributed enterprise environments.
Primary Amplification Factors
· Unauthorized peering can allow attacker-controlled infrastructure to appear operationally trusted.
· Administrative authentication or NETCONF access indicates movement from exposure into privileged SD-WAN management.
· Fabric-impacting changes can affect segmentation, traffic direction, branch reachability, data-center access, and cloud connectivity.
· Weak provider, VPN, automation, emergency-access, and managed-service governance can obscure attacker activity.
· Encrypted control-plane traffic and incomplete audit visibility can delay confirmation and increase scoping burden.
· Persistent unfamiliar access after remediation may indicate that trust, account, certificate, peer, or configuration artifacts remain active.
Highest-Risk Escalation Pattern
The highest-risk pattern is suspicious SD-WAN peering or control-plane activity followed by successful administrative authentication, NETCONF access, configuration modification, and new traffic-flow behavior affecting sensitive internal segments or critical connectivity paths.
Business Impact Path
The business impact path moves from infrastructure exposure to loss of confidence in SD-WAN trust, then to potential routing or policy manipulation, then to segmentation or connectivity impact. At that point, response may require emergency control-plane containment, route and policy validation, branch connectivity review, service-provider escalation, privileged-access review, and executive incident governance.
S20 — Tactics, Techniques, and Procedures
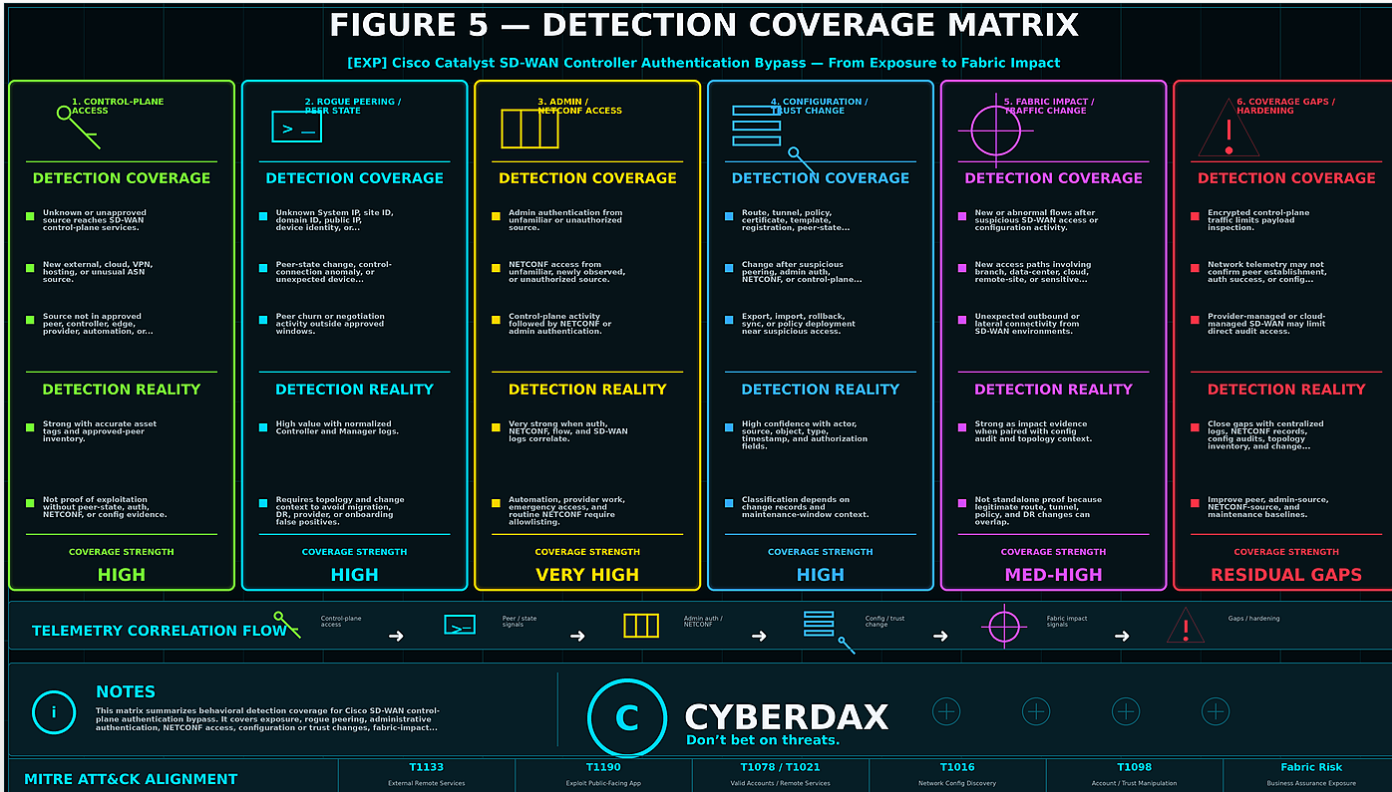
Figure 3
Access and Control-Plane Positioning
· Interact with externally reachable or provider-accessible Cisco SD-WAN control-plane services.
· Attempt to appear as approved SD-WAN infrastructure through unfamiliar peer identity, device-registration, or controller-relationship values.
· Use source infrastructure that blends with cloud, VPN, hosting, service-provider, managed-service, or emergency-access paths.
Administrative and NETCONF Activity
· Use administrative or NETCONF access paths from unfamiliar or unauthorized sources.
· Sequence management activity near peer-state anomalies, control-plane instability, or unexpected controller events.
· Blend activity into automation, service-provider support, emergency access, or normal management workflows where baselines are weak.
Configuration and Fabric Manipulation
· Review or alter routes, tunnels, policies, certificates, templates, device registration, peer state, controller relationships, or fabric-trust objects.
· Create configuration drift that lacks clear change-ticket, maintenance-window, service-provider, automation, or emergency-access justification.
· Preserve access through account, key, certificate, peer, trust, or configuration artifacts where access allows.
Impact and Persistence-Oriented Behavior
· Create or preserve new access paths between SD-WAN-managed environments and sensitive internal systems.
· Alter branch, data-center, cloud, or remote-site connectivity through SD-WAN fabric changes.
· Maintain recurring access from unfamiliar sources after initial suspicious activity.
Evasion and Blending Factors
· Operate during activity windows that resemble maintenance, migration, disaster recovery, edge onboarding, automation, or provider support.
· Benefit from encrypted control-plane traffic where packet-level visibility is limited.
· Exploit weak topology inventory, administrative-source baselines, NETCONF visibility, or configuration-audit retention.
S20A — Adversary Tradecraft Summary
Cisco Catalyst SD-WAN Controller Authentication Bypass tradecraft is best characterized as infrastructure-trust abuse. The attacker does not need to rely on noisy malware behavior if SD-WAN trust, administrative access, NETCONF workflows, or configuration pathways can be misused.
The most important tradecraft feature is the ability to make suspicious activity resemble legitimate SD-WAN operations. Rogue peer behavior may look like edge onboarding, provider troubleshooting, controller migration, or disaster recovery. Administrative and NETCONF access may look like automation, service-provider support, emergency access, or normal management activity. Configuration changes may appear routine unless actor, source, object, timing, peer-state context, and approval records are correlated.
The strongest defensive interpretation is behavior-led. Single signals should be handled carefully, but clustered activity involving peering, authentication, NETCONF access, configuration change, and traffic-flow impact should be treated as a high-priority escalation path.
The most consequential outcome is loss of assurance in SD-WAN fabric integrity. If unauthorized trust or configuration changes cannot be ruled out, organizations may need to validate route state, tunnel state, policy behavior, certificate posture, device registration, peer relationships, branch connectivity, segmentation boundaries, and access paths into sensitive internal environments before returning to normal operational confidence.
S21 — Detection Strategy Overview
Detection Philosophy
Behavioral detection for CVE-2026-20182 should focus on unauthorized SD-WAN control-plane trust establishment, rogue peering behavior, suspicious administrative authentication, NETCONF access, SD-WAN configuration manipulation, and post-access fabric impact.
The detection objective is not to identify the CVE name alone. The objective is to identify activity suggesting that an attacker has abused the Cisco SD-WAN control-plane authentication pathway to appear as a trusted peer, gain privileged access, or manipulate SD-WAN fabric behavior.
Detection content should be correlation-led, topology-aware, and resistant to minor implementation changes. Static advisory references, scanner findings, port activity, or CVE-string matches should not be treated as durable primary detection anchors.
Primary Detection Anchors
· Unauthorized SD-WAN Controller or Manager peering from unknown, unexpected, or unapproved source IP addresses.
· Rogue peer registration or peer-state changes inconsistent with approved SD-WAN topology.
· New or unexpected peer identity fields, including System IP, site ID, domain ID, peer type, public IP, device identity, or controller relationship.
· Successful administrative authentication from source networks not approved for SD-WAN administration.
· Successful SD-WAN administrative-account authentication from unknown, external, or unauthorized source IP addresses.
· NETCONF access to SD-WAN infrastructure from unfamiliar, newly observed, or unauthorized source networks.
· NETCONF access following suspicious peering, peer-state changes, administrative authentication, or control-plane instability.
· SD-WAN configuration changes following anomalous peering or administrative access.
· Route, tunnel, policy, device-registration, certificate, peer-state, or fabric-trust changes following suspicious control-plane activity.
· Persistent or recurring access from unfamiliar sources after initial peering or administrative-access anomalies.
· Administrative activity occurring outside approved maintenance windows, change windows, or emergency-access procedures.
Detection Prioritization Model
Detection priority should be based on the relationship between suspicious control-plane trust activity, administrative authentication, NETCONF access, SD-WAN configuration changes, and approved topology context.
Single-event alerts should be treated as lower confidence unless they directly confirm unauthorized successful administrative access or are correlated with supporting control-plane, authentication, NETCONF, or configuration-change signals.
· Highest priority should be assigned to suspicious SD-WAN peering followed by successful administrative authentication, NETCONF access, or SD-WAN configuration modification.
· Highest priority should be assigned to rogue peer activity followed by route, tunnel, policy, device-registration, certificate, peer-state, or fabric-trust changes.
· High priority should be assigned to unfamiliar peer identity fields that do not match approved SD-WAN inventory.
· High priority should be assigned to unfamiliar sources accessing NETCONF after control-plane anomalies.
· Medium priority should be assigned to repeated access attempts against SD-WAN control-plane services from unfamiliar sources without confirmed peering or authentication success.
· Medium priority should be assigned to peer churn, control-connection instability, or abnormal negotiation activity outside approved maintenance windows.
· Lower priority should be assigned to isolated failed access attempts that do not result in peering, authentication success, NETCONF access, configuration change, persistence activity, or repeated targeting.
Correlation Strategy
Strict correlation is required.
Cisco SD-WAN control-plane abuse can appear as trusted infrastructure behavior after successful exploitation. Detection logic should not rely on isolated port activity, vulnerability exposure, scanner output, or advisory references as compromise evidence.
Detection logic should prioritize combinations of the following:
· Suspicious SD-WAN peering followed by administrative authentication from the same source, related source, infrastructure cluster, ASN, VPN provider, cloud provider, or access path.
· Unknown peer identity fields followed by NETCONF access.
· Successful administrative authentication followed by SD-WAN configuration changes.
· UDP control-plane activity followed by TCP NETCONF access from the same or related source.
· New or unfamiliar System IP, site ID, domain ID, peer type, public IP, or device identity followed by route, tunnel, policy, certificate, registration, or fabric-trust changes.
· Control-plane instability followed by external access attempts and administrative activity.
· Unusual administrative access followed by device-registration, peer-state, configuration, or SD-WAN fabric changes.
· Authentication-log anomalies that align with SD-WAN Manager audit-log activity.
· Network-flow anomalies that align with controller-side logs, especially where encrypted control-plane traffic limits packet-level visibility.
· High-priority findings that do not align with approved topology, known peer inventory, administrative source networks, maintenance windows, or change-management records.
Telemetry Prioritization
Primary telemetry should come from SD-WAN Controller logs, SD-WAN Manager logs, authentication records, NETCONF records, configuration audit sources, topology inventory, and network-flow metadata.
Network telemetry should be used as high-value supporting context, but controller-side, authentication, and configuration-change records should drive final severity.
Highest-Value Telemetry
· SD-WAN Controller and Manager logs for peering, control-connection, peer-state, device-identity, and fabric-trust activity.
· Authentication logs for administrative-account access, source IP validation, authentication method, successful access, and failed-to-successful access patterns.
· NETCONF logs and network-flow telemetry for TCP port 830 access to SD-WAN management and control-plane infrastructure.
· SD-WAN configuration audit logs for policy, route, tunnel, device-registration, certificate, peer-state, and fabric-trust changes.
· Inventory and topology data for validation of approved System IPs, site IDs, domain IDs, peer types, public IPs, controller identities, device identities, and administrative source networks.
· Historical configuration snapshots for identifying unauthorized fabric drift after suspicious access.
Supporting Telemetry
· Network-flow telemetry for UDP control-plane activity to Cisco SD-WAN Controller and Manager systems.
· Firewall and NDR telemetry for external access paths, newly observed sources, abnormal timing, and repeated connection attempts.
· Change-management records for distinguishing authorized maintenance from suspicious control-plane behavior.
· File and persistence telemetry where supportable for unauthorized key, account, configuration, or persistence artifacts on SD-WAN infrastructure.
· Service-provider, managed-service, VPN, and emergency-access records where those paths are approved for SD-WAN administration.
Detection Design Constraints
Detection content must remain behavior-led and should not overfit to CVE text, public advisory language, scanner output, port-only activity, or payload signatures.
Rules should avoid treating normal SD-WAN peering, NETCONF administration, controller migration, service-provider access, disaster-recovery activity, emergency maintenance, or planned topology changes as compromise by default.
Rules should require context from at least one of the following:
· Abnormal peer identity context.
· Abnormal administrative source context.
· Abnormal control-plane trust context.
· Abnormal NETCONF access context.
· Abnormal configuration-change context.
· Abnormal timing or maintenance-window context.
· Abnormal topology or inventory context.
· Abnormal controller relationship context.
· Abnormal route, tunnel, policy, certificate, or fabric-trust context.
· Abnormal persistence or recurring-access context.
Baseline and Deployment Requirements
Organizations should establish SD-WAN topology, administrative-access, NETCONF, and configuration-change baselines before promoting this detection model into high-severity production alerts.
Required baselines include:
· Approved Cisco Catalyst SD-WAN Controllers, Managers, Validators, edge devices, and control-plane components.
· Approved System IPs, site IDs, domain IDs, peer types, public IPs, device identities, controller relationships, and expected peer relationships.
· Approved administrative source networks, VPN paths, service-provider access paths, emergency-access paths, and automation sources.
· Approved NETCONF source networks and expected NETCONF administrative workflows.
· Normal SD-WAN peering, control-connection state changes, peer churn, controller-to-edge communication, administrative authentication, NETCONF access, and configuration-change patterns.
· Normal UDP control-plane and TCP NETCONF communication to SD-WAN infrastructure.
· Normal route, tunnel, policy, certificate, device-registration, peer-state, and fabric-trust change activity.
· Normal maintenance windows, emergency-change procedures, and change-management references for SD-WAN activity.
· Normal logging retention and field availability for delayed discovery, repeated access, persistence activity, configuration drift, and post-exploitation review.
Deployment should prioritize SD-WAN environments where control-plane compromise would create material business or operational impact.
· Internet-exposed SD-WAN Controller or Manager infrastructure.
· Large distributed branch environments.
· Critical network segmentation environments.
· Financial, healthcare, government, telecommunications, energy, transportation, and managed-service environments.
· Environments with high reliance on centralized SD-WAN policy enforcement.
· Environments with third-party or service-provider SD-WAN administration.
· Environments with incomplete peer inventory, weak change-management linkage, or limited configuration-audit visibility.
· Environments where SD-WAN routing, tunnel, or policy manipulation could affect sensitive internal network access.
Variant Resilience Requirements
Detection content must remain useful if the exploit implementation changes.
Variant-resilient detection should focus on:
· Unauthorized control-plane trust establishment.
· Rogue or unexpected SD-WAN peering.
· Unexpected peer identity fields.
· Administrative authentication from unfamiliar sources.
· NETCONF access after suspicious peering or authentication.
· SD-WAN configuration manipulation.
· Route, tunnel, policy, certificate, device-registration, peer-state, or fabric-trust changes.
· Persistent or recurring access from unfamiliar sources.
· Unauthorized key, account, peer, or configuration artifacts where telemetry allows.
· Post-access SD-WAN fabric drift or traffic-flow manipulation.
Detection content should not rely on:
· A specific CVE string as the primary detection condition.
· A specific scanner result.
· A specific advisory reference.
· A single port observation without surrounding context.
· Encrypted DTLS payload visibility.
· A single NETCONF session without source, identity, timing, peer-state, or configuration-change context.
· Assumptions that exploitation will always originate from the public internet.
· Assumptions that attacker activity will appear obviously malicious after trusted peer status is obtained.
Operational Detection Model
The operational model should use a staged approach.
Stage One - Exposure and Topology Identification
· Identify Cisco SD-WAN Controllers, Managers, Validators, edge devices, and control-plane components.
· Identify internet-exposed or externally reachable SD-WAN control-plane and management-plane services.
· Identify approved peers, System IPs, site IDs, domain IDs, peer types, public IPs, device identities, and controller relationships.
· Identify approved administrative source networks, NETCONF sources, service-provider paths, VPN paths, emergency-access paths, and automation sources.
· Identify environments where SD-WAN compromise would create high operational, segmentation, routing, or business-continuity impact.
Stage Two - Peering and Control-Plane Anomaly Detection
· Detect unauthorized SD-WAN peering from unknown, unexpected, or unapproved sources.
· Detect rogue peer registration or peer-state changes inconsistent with approved topology.
· Detect unfamiliar System IP, site ID, domain ID, peer type, public IP, device identity, or controller relationship values.
· Detect abnormal control-connection state changes, peer churn, or negotiation activity outside approved maintenance windows.
· Detect repeated control-plane access attempts from unfamiliar sources.
Stage Three - Administrative and NETCONF Access Detection
· Detect successful administrative authentication from unfamiliar or unauthorized source networks.
· Detect SD-WAN administrative-account authentication from unexpected sources.
· Detect NETCONF access from unfamiliar, newly observed, or unauthorized source networks.
· Detect NETCONF access following suspicious peering, control-plane instability, or administrative authentication.
· Detect authentication or NETCONF activity that does not align with approved maintenance, automation, service-provider, or emergency-access workflows.
Stage Four - Fabric Impact and Persistence Detection
· Detect SD-WAN configuration changes following suspicious peering or administrative access.
· Detect route, tunnel, policy, certificate, device-registration, peer-state, or fabric-trust changes after anomalous control-plane activity.
· Detect persistent or recurring access from unfamiliar sources after initial peering or authentication anomalies.
· Detect unauthorized key, account, peer, or configuration artifacts where telemetry allows.
· Detect SD-WAN fabric drift, unexpected traffic-flow changes, or new access paths created after suspicious control-plane activity.
Signal Usage Constraints
· Do not treat normal SD-WAN peering, NETCONF administration, control-plane communication, or configuration activity as suspicious by itself.
· Do not treat UDP control-plane traffic, NETCONF access, scanner output, advisory references, or vulnerability exposure as confirmed exploitation by itself.
· Do not rely on CVE text, port-only logic, or encrypted DTLS payload inspection as the primary detection method.
· Do not suppress unknown peer activity solely because the source belongs to a cloud, VPN, managed-service, or service-provider ASN.
· Do not ignore approved maintenance windows, disaster-recovery activity, emergency access, managed-service activity, or planned SD-WAN topology changes.
· Do not assign high-severity control-plane findings without baselines for approved peers, System IPs, site IDs, domain IDs, public IPs, device identities, controller relationships, NETCONF sources, and administrative source networks.
· Do not treat configuration changes as compromise indicators without correlating actor, source, time, object changed, change type, peer-state context, and change authorization.
· Do not assign compromise-level severity from a single weak signal unless the signal directly confirms unauthorized successful administrative access.
· Do not include actor-attribution language unless independent actor-specific intelligence supports attribution.
· Do not treat control-plane activity as malicious unless it can be distinguished from normal SD-WAN operations, approved peer behavior, and authorized fabric-impacting activity.
S22 — Primary Detection Signals
Primary Detection Signals
Primary detection signals for CVE-2026-20182 should focus on unauthorized SD-WAN control-plane trust establishment, rogue peering behavior, suspicious administrative authentication, NETCONF access, SD-WAN configuration manipulation, and fabric-impact activity.
The strongest signals are not advisory references, scanner findings, or CVE-string matches. The strongest signals are behavior patterns showing that an attacker may have gained trusted control-plane positioning or used that positioning to alter SD-WAN management, routing, policy, or fabric state.
· Unauthorized SD-WAN Controller or Manager peering from an unknown, unexpected, or unapproved source.
· Rogue peer registration or peer-state change inconsistent with approved SD-WAN topology.
· New or unfamiliar System IP, site ID, domain ID, peer type, public IP, device identity, or controller relationship.
· Successful SD-WAN administrative authentication from an unfamiliar, external, or unauthorized source network.
· Administrative authentication from a source not aligned with approved VPN, service-provider, automation, emergency-access, or management paths.
· NETCONF access to SD-WAN infrastructure from an unfamiliar, newly observed, or unauthorized source.
· NETCONF access following suspicious peering, control-plane instability, or administrative authentication.
· SD-WAN configuration changes following anomalous control-plane or administrative activity.
· Route, tunnel, policy, certificate, device-registration, peer-state, or fabric-trust changes following suspicious access.
· Persistent or recurring access from unfamiliar sources after initial peering or administrative-access anomalies.
Supporting Detection Signals
Supporting signals should provide context around source behavior, sequencing, operational timing, topology mismatch, and configuration drift. These signals should strengthen investigation confidence but should not be treated as standalone confirmation of exploitation.
· Repeated UDP control-plane access attempts against Cisco SD-WAN Controller or Manager infrastructure.
· Repeated TCP NETCONF access attempts against SD-WAN management or control-plane infrastructure.
· Newly observed source IPs communicating with SD-WAN control-plane or management-plane services.
· Control-plane communication from geographies, ASNs, VPN providers, cloud providers, or managed-service paths not normally associated with SD-WAN administration.
· Administrative access outside approved maintenance windows, change windows, emergency-access procedures, or service-provider support periods.
· Failed-to-successful administrative authentication patterns involving SD-WAN management accounts.
· Peer churn, control-connection instability, or abnormal negotiation activity near suspicious access attempts.
· Configuration changes without matching change ticket, maintenance record, emergency-access record, service-provider record, or expected automation event.
· SD-WAN inventory drift involving peer identity, controller relationships, registered devices, certificates, or fabric-trust state.
· Network-flow anomalies that align with SD-WAN Controller, Manager, authentication, or configuration-audit events.
Exploit Attempt and Instability Signals
Exploit-attempt and instability signals should be treated as early warning or triage context unless they are correlated with peer establishment, authentication success, NETCONF access, or configuration change.
· Repeated connection attempts to SD-WAN control-plane services from unfamiliar external sources.
· Abnormal control-connection negotiation attempts involving unknown or unexpected peer identity fields.
· Unexpected peer-state transitions near unusual external access activity.
· Sudden peer churn, controller instability, or control-plane state changes outside maintenance windows.
· Repeated failed authentication or negotiation activity followed by successful administrative access.
· Control-plane instability followed by NETCONF access or SD-WAN configuration activity.
· Access attempts from infrastructure that has not previously interacted with the SD-WAN control plane.
· Suspicious sequencing between external access, peer-state change, administrative authentication, and configuration modification.
· Unusual access patterns targeting SD-WAN control-plane and management-plane services within the same operational window.
Outbound Communication Signals
Outbound and post-access communication signals should be used to identify possible SD-WAN fabric manipulation, new access paths, traffic-flow changes, or infrastructure relationships created after suspicious control-plane activity.
· New or unexpected outbound connections from SD-WAN infrastructure after suspicious peering or administrative access.
· New traffic flows associated with unfamiliar peers, public IPs, controller relationships, or fabric-trust changes.
· Unexpected route, tunnel, or policy changes that redirect traffic toward unfamiliar destinations.
· New communication paths between SD-WAN-managed environments and sensitive internal network segments.
· Unexpected connectivity from SD-WAN infrastructure to cloud, VPN, hosting, or unmanaged external networks.
· New or abnormal management-plane communication following SD-WAN configuration changes.
· Changes in branch, data-center, cloud, or remote-site connectivity following suspicious control-plane activity.
· Unexpected traffic-flow changes after route, tunnel, certificate, policy, or fabric-trust modification.
· Outbound activity that aligns with persistent unfamiliar peer access or recurring administrative sessions.
Persistence and Post-Exploitation Signals (Conditional)
Persistence and post-exploitation signals should be evaluated when telemetry is available. These signals should be treated as high value when they follow suspicious peering, administrative authentication, NETCONF access, or configuration manipulation.
· Persistent rogue peer relationships or unauthorized device registrations.
· Repeated administrative access from unfamiliar sources after initial suspicious control-plane activity.
· Unauthorized key, account, certificate, peer, or configuration artifacts associated with SD-WAN infrastructure.
· Configuration changes that preserve access, weaken trust boundaries, or alter SD-WAN control-plane behavior.
· Recurring NETCONF access from sources not aligned with approved administrative workflows.
· Fabric-trust changes that survive maintenance, restart, policy refresh, or configuration review.
· Route, tunnel, or policy changes that create new access paths into sensitive internal environments.
· SD-WAN configuration drift that cannot be tied to approved maintenance, automation, service-provider activity, or emergency access.
· Continued administrative or peer activity after remediation actions, patching, or configuration rollback.
Lateral Movement and Expansion Signals (Conditional)
Lateral movement and expansion signals should focus on whether SD-WAN control-plane abuse enabled access to additional network segments, management systems, or sensitive environments.
· New SD-WAN routes or policies enabling access to internal segments not previously reachable from the observed source path.
· Traffic from suspicious or newly observed SD-WAN peer contexts toward identity, management, monitoring, backup, hypervisor, or network-administration systems.
· New connectivity between branch, data-center, cloud, or remote-site environments after suspicious control-plane activity.
· Access attempts to sensitive internal services following SD-WAN configuration manipulation.
· East-west traffic changes following route, tunnel, policy, certificate, or fabric-trust modification.
· Administrative access to additional network infrastructure after SD-WAN control-plane anomalies.
· New service reachability from locations, peers, or access paths not normally permitted by SD-WAN policy.
· Follow-on authentication, scanning, or management activity from paths enabled by suspicious SD-WAN configuration changes.
Signal Usage Constraints
· Do not treat control-plane exposure, scanner output, advisory references, or CVE-string matches as primary detection signals.
· Do not treat UDP control-plane traffic or NETCONF access as malicious without source, identity, timing, topology, and configuration-change context.
· Do not treat normal SD-WAN peering, control-plane communication, NETCONF administration, or configuration activity as suspicious by itself.
· Do not assign high confidence to instability signals unless they align with suspicious access, peer-state change, authentication, NETCONF, or configuration activity.
· Do not assume unfamiliar cloud, VPN, service-provider, or managed-service traffic is benign without validating approved administrative paths.
· Do not assume suspicious control-plane activity must originate from the public internet.
· Do not rely on encrypted payload visibility as the primary validation method.
· Do not treat configuration changes as compromise indicators without actor, source, object, timing, peer-state, and change-authorization context.
· Do not treat persistence or expansion signals as applicable unless the required telemetry exists.
· Do not use actor-attribution language unless independent actor-specific evidence supports attribution.
S23 — Telemetry Requirements
Endpoint and Process Execution Telemetry
Endpoint and process execution telemetry should be treated as supporting context for CVE-2026-20182. The highest-value evidence will usually come from SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, configuration audit sources, topology inventory, and network-flow metadata.
Where appliance, host, or managed-infrastructure telemetry is available, collection should prioritize activity that supports investigation of unauthorized administrative access, configuration manipulation, persistence, and post-access SD-WAN fabric impact.
· Administrative process execution associated with SD-WAN Controller or Manager systems.
· Command execution tied to SD-WAN administrative accounts or service accounts.
· Administrative shell activity on SD-WAN infrastructure where supported.
· Process activity related to configuration export, import, rollback, synchronization, or policy deployment.
· Process activity that aligns with suspicious authentication, NETCONF access, or configuration changes.
· Unusual use of native administrative utilities on SD-WAN infrastructure.
· Execution activity occurring outside approved maintenance, automation, service-provider, or emergency-access workflows.
· Process activity followed by SD-WAN configuration drift, peer-state changes, route changes, tunnel changes, or policy modification.
Memory and Execution Telemetry
Memory telemetry should not be required for production detection of this activity.
Detection should not depend on memory inspection, exploit payload recovery, or low-level runtime visibility. The durable detection surface is the operational behavior that follows control-plane trust abuse.
· Memory telemetry may provide supplemental investigative value if available.
· Memory telemetry should not be treated as a baseline requirement for detection viability.
· Execution telemetry should support administrative-access and configuration-change review where available.
· Detection logic should remain viable in environments where SD-WAN appliances do not provide memory-level visibility.
· Detection logic should prioritize peer-state, authentication, NETCONF, configuration, inventory, and network-flow evidence over memory artifacts.
· Absence of memory telemetry should not prevent investigation of suspicious SD-WAN peering, administrative access, or fabric modification.
Crash and Fault Telemetry
Crash and fault telemetry should be used to identify control-plane instability, abnormal negotiation behavior, service disruption, and timing relationships around suspicious access.
Crash or instability events should not be treated as exploitation evidence by themselves. They become more valuable when they align with unusual external access, rogue peering, administrative authentication, NETCONF activity, or configuration changes.
· SD-WAN control-plane service faults where available.
· SD-WAN Controller or Manager service restarts.
· Unexpected control-connection drops or resets.
· Sudden peer churn or repeated peer-state transitions.
· Abnormal control-plane negotiation failures.
· Controller instability outside approved maintenance windows.
· Device registration or peer-state errors near suspicious access attempts.
· Fault events followed by administrative authentication or NETCONF access.
· Fault events followed by route, tunnel, policy, certificate, peer-state, or fabric-trust changes.
· Monitoring gaps or telemetry interruptions that align with suspicious control-plane activity.
File and Persistence Telemetry
File and persistence telemetry should be collected where supportable, but it should not be assumed to be available in every SD-WAN deployment.
This telemetry is most valuable when it helps identify unauthorized administrative artifacts, persistent access, configuration drift, or changes that survive maintenance, restart, policy refresh, or configuration review.
· Authentication logs showing administrative-account access, source IP, authentication method, and outcome.
· Configuration files or configuration snapshots before and after suspicious access.
· Authorized-key, account, certificate, peer, or trust-artifact changes where visibility is available.
· SD-WAN policy, route, tunnel, device-registration, peer-state, and fabric-trust configuration changes.
· Configuration export, import, rollback, or synchronization activity.
· Unauthorized or unexpected administrative account changes.
· Persistent peer, device, certificate, or controller relationship artifacts.
· File or configuration changes that align with suspicious peering or NETCONF access.
· Configuration drift that cannot be tied to approved maintenance, automation, service-provider activity, or emergency access.
· Artifacts that remain active after patching, restart, rollback, or remediation activity.
Network and Outbound Communication Telemetry
Network telemetry is a high-value source for identifying suspicious control-plane access, NETCONF activity, source behavior, sequencing, and post-access fabric changes.
Network telemetry should be correlated with controller-side, authentication, inventory, and configuration-audit sources. Port activity alone should not be treated as confirmed exploitation.
· UDP control-plane traffic to Cisco SD-WAN Controller or Manager systems.
· TCP NETCONF traffic to SD-WAN management or control-plane infrastructure.
· Source IP, destination IP, port, protocol, timestamp, session duration, and connection volume.
· Newly observed sources communicating with SD-WAN control-plane or management-plane services.
· Traffic from geographies, ASNs, VPN providers, cloud providers, or managed-service paths not normally associated with SD-WAN administration.
· Control-plane access attempts outside approved administrative, service-provider, automation, or emergency-access paths.
· Network-flow sequences showing control-plane activity followed by NETCONF access.
· New or unexpected outbound connections from SD-WAN infrastructure after suspicious peering or administrative access.
· Traffic-flow changes following route, tunnel, policy, certificate, peer-state, or fabric-trust modification.
· New communication paths between SD-WAN-managed environments and sensitive internal segments.
· Repeated external access attempts that align with controller-side peer, authentication, or configuration events.
Web and Application Telemetry (Conditional Availability)
Web and application telemetry should be collected from SD-WAN Manager and related administrative interfaces when available.
This telemetry is most useful when it identifies administrative sessions, configuration changes, device-registration activity, policy changes, and user or automation context associated with suspicious control-plane behavior.
· SD-WAN Manager administrative session records.
· SD-WAN Manager audit logs.
· User, role, source IP, authentication method, and session outcome.
· API activity associated with SD-WAN administration or automation.
· Device registration, inventory, controller relationship, and peer-state changes.
· Policy, route, tunnel, certificate, peer-state, and fabric-trust changes.
· Configuration push, rollback, synchronization, or template activity.
· Failed-to-successful administrative access patterns.
· Administrative activity outside approved maintenance, automation, service-provider, or emergency-access workflows.
· Change activity that lacks corresponding approval, ticketing, or operational justification.
Telemetry Availability Requirements
Organizations should validate telemetry availability before promoting this detection model into high-severity alerting.
The required telemetry model should support correlation across SD-WAN control-plane activity, administrative authentication, NETCONF access, configuration changes, topology inventory, and network-flow evidence.
· SD-WAN Controller and Manager logs should be centrally collected or rapidly retrievable.
· Authentication logs should include username, source IP, timestamp, authentication method, and outcome.
· NETCONF telemetry should identify source, destination, timestamp, and session context where available.
· Network-flow telemetry should identify UDP control-plane and TCP NETCONF access to SD-WAN infrastructure.
· Configuration audit records should identify actor, source, object changed, change type, timestamp, and authorization context.
· Inventory data should identify approved Controllers, Managers, Validators, edge devices, System IPs, site IDs, domain IDs, peer types, public IPs, device identities, and controller relationships.
· Administrative-source baselines should identify approved VPN paths, service-provider paths, automation sources, emergency-access paths, and management networks.
· Change-management records should be available to validate planned maintenance, emergency activity, service-provider activity, and approved topology changes.
· Logging retention should support delayed discovery, repeated access review, configuration-drift investigation, and post-exploitation timeline reconstruction.
· SOC workflows should support correlation between network-flow, controller, authentication, NETCONF, configuration, and inventory sources.
Telemetry Limitations and Gaps
Telemetry limitations should be accounted for before assigning compromise-level severity.
Cisco SD-WAN control-plane abuse may appear as trusted peer or administrative behavior after successful exploitation. Detection therefore depends on strong baselines, controller-side visibility, authentication context, and configuration-change review.
· Encrypted control-plane traffic may limit packet-level inspection.
· SD-WAN appliance telemetry may vary by deployment model, version, hosting model, and management architecture.
· Some environments may not provide direct host-level, file-level, or memory-level visibility into SD-WAN infrastructure.
· Cloud-managed or provider-managed SD-WAN environments may require service-provider assistance for log access and investigation.
· NETCONF activity may be difficult to classify without source, identity, timing, peer-state, and configuration-change context.
· Network telemetry may identify suspicious access paths but may not confirm peer establishment or administrative success.
· Configuration audit visibility may be incomplete if logging is not centralized or retention is limited.
· Missing topology inventory can reduce confidence in identifying unauthorized peers or unexpected device identities.
· Legitimate maintenance, migration, disaster recovery, service-provider access, or emergency access may resemble suspicious control-plane behavior.
· Absence of a single telemetry source should not end investigation when other sources show suspicious peering, administrative authentication, NETCONF access, or SD-WAN fabric change.
S24 — Detection Opportunities and Gaps
Figure 4
Detection Opportunities
Detection opportunities for CVE-2026-20182 should focus on observable behavior created by unauthorized SD-WAN control-plane trust abuse rather than on CVE text, scanner output, or exploit-specific indicators.
The strongest opportunities come from correlating suspicious peering, administrative authentication, NETCONF access, configuration changes, topology mismatch, and post-access SD-WAN fabric impact.
· Unauthorized SD-WAN peering can be detected by comparing observed peer activity against approved topology, peer inventory, System IPs, site IDs, domain IDs, public IPs, device identities, and controller relationships.
· Rogue peer registration or peer-state changes can expose attempts to appear as trusted SD-WAN infrastructure.
· Administrative authentication from unfamiliar or unauthorized sources can identify activity that has moved beyond probing or exposure.
· NETCONF access following suspicious peering or administrative authentication can provide strong evidence of privileged SD-WAN management activity.
· SD-WAN configuration changes following anomalous control-plane activity can identify possible impact to routing, tunnels, policy, certificates, device registration, peer state, or fabric trust.
· Network-flow telemetry can identify suspicious sequencing between UDP control-plane activity, TCP NETCONF access, and post-access communication changes.
· Configuration audit logs can identify unauthorized or unexplained changes that affect SD-WAN fabric behavior.
· Historical configuration snapshots can expose fabric drift after suspicious access.
· Change-management, maintenance-window, emergency-access, and service-provider records can help separate authorized SD-WAN operations from suspicious activity.
· Inventory and topology baselines can increase confidence when unfamiliar peers, sources, or device identities appear in controller-side telemetry.
High-Value Detection Opportunities
· Suspicious peering followed by successful SD-WAN administrative authentication.
· Suspicious peering followed by NETCONF access.
· Suspicious peering followed by SD-WAN configuration changes.
· Unknown peer identity fields followed by route, tunnel, policy, certificate, device-registration, peer-state, or fabric-trust changes.
· Administrative authentication from unfamiliar sources followed by configuration export, import, rollback, synchronization, or policy deployment activity.
· Repeated control-plane access attempts followed by peer-state changes or authentication success.
· Control-plane instability followed by NETCONF access or configuration modification.
· Persistent or recurring access from unfamiliar sources after initial anomalous peering.
· SD-WAN configuration drift that does not align with approved maintenance, automation, service-provider activity, or emergency access.
· New traffic-flow patterns, access paths, or internal reachability changes following suspicious control-plane activity.
Detection Gaps
Detection gaps are most likely when organizations lack complete SD-WAN topology baselines, centralized controller logs, authentication records, NETCONF visibility, configuration audit history, or change-management context.
The largest detection risk is misclassifying attacker activity as normal SD-WAN control-plane behavior after an attacker obtains trusted peer positioning.
· Encrypted control-plane traffic may prevent payload-level inspection.
· Network telemetry may show access to SD-WAN services but may not confirm peer establishment, authentication success, or configuration impact.
· Some SD-WAN deployments may not provide direct host-level, file-level, memory-level, or appliance-level telemetry.
· Cloud-managed or provider-managed SD-WAN environments may limit direct access to controller, authentication, or configuration audit logs.
· Incomplete peer inventory may reduce confidence when identifying rogue peer activity.
· Incomplete administrative-source baselines may make it difficult to distinguish unauthorized access from service-provider, automation, VPN, or emergency-access activity.
· Limited NETCONF logging may reduce visibility into privileged management activity.
· Limited configuration audit retention may make it difficult to reconstruct fabric changes after suspicious access.
· Missing change-management linkage may create false positives during planned migrations, disaster recovery, emergency maintenance, or service-provider support.
· SD-WAN configuration changes may be difficult to classify without actor, source, object, timestamp, peer-state context, and authorization context.
· Post-access traffic changes may be difficult to attribute to malicious activity without configuration, routing, tunnel, or policy-change context.
· Absence of a single telemetry source may delay investigation if teams do not correlate across controller, authentication, configuration, inventory, and network-flow sources.
False Positive Considerations
Legitimate SD-WAN operations may resemble suspicious control-plane activity when viewed without topology, inventory, timing, or change-management context.
Common false-positive drivers include:
· Planned SD-WAN controller migration.
· Branch, data-center, cloud, or remote-site onboarding.
· Service-provider maintenance or troubleshooting.
· Managed-service administrative access.
· Disaster-recovery testing.
· Emergency access during outage response.
· Automation-driven configuration deployment.
· Certificate renewal or trust-store maintenance.
· Policy, route, tunnel, or template updates during approved change windows.
· Temporary peer churn during upgrades, patching, or network instability.
False Negative Considerations
False negatives are most likely when attacker activity blends into trusted SD-WAN control-plane behavior or when required telemetry is unavailable.
Common false-negative drivers include:
· Missing or incomplete SD-WAN Controller and Manager logs.
· Missing authentication source context.
· Missing NETCONF visibility.
· Missing configuration audit records.
· Incomplete topology or peer inventory.
· Incomplete administrative-source baselines.
· Insufficient logging retention.
· Lack of correlation between controller logs, network flows, authentication records, configuration changes, and change-management data.
· Overly broad suppression of cloud, VPN, managed-service, or service-provider traffic.
· Treating trusted peer behavior as benign without validating topology and authorization context.
· Assuming exploitation must originate from the public internet.
· Assuming encrypted control-plane traffic prevents meaningful detection.
Operational Gaps
Operational gaps can reduce detection effectiveness even when technical telemetry exists.
· SOC teams may not have direct access to SD-WAN topology inventory.
· SOC teams may not have rapid access to SD-WAN Manager audit logs or configuration history.
· Network, security, and service-provider teams may maintain separate records that are not easily correlated during investigation.
· Change-management records may not include enough detail to validate peer-state, routing, tunnel, certificate, or policy changes.
· Emergency-access procedures may not produce consistent approval or after-action records.
· Managed-service or provider-administered environments may require escalation outside normal SOC workflows.
· SD-WAN configuration backups may not be frequent enough to identify short-lived or rolled-back changes.
· Asset ownership may be unclear for externally reachable SD-WAN infrastructure.
· Teams may lack predefined investigation steps for suspicious SD-WAN peering, NETCONF access, or fabric-trust changes.
Detection Engineering Implications
Detection engineering should prioritize resilient behavioral correlation over isolated indicators.
Rules and analytic logic should identify suspicious control-plane trust activity and follow-on fabric-impact behavior while avoiding high-severity conclusions from weak single signals.
· Prioritize correlation between suspicious peering, administrative authentication, NETCONF access, and configuration changes.
· Use topology and inventory baselines to validate peer identity, source legitimacy, and controller relationships.
· Treat network-flow telemetry as supporting evidence unless paired with controller-side, authentication, or configuration-change records.
· Treat configuration changes as high value only when actor, source, object, timing, peer-state context, and authorization context can be assessed.
· Preserve investigation pathways when memory, file-level, or host-level telemetry is unavailable.
· Avoid overfitting to advisory text, scanner output, CVE strings, ports, or payload assumptions.
· Avoid suppressing unfamiliar peer or administrative activity solely because the source appears to be cloud, VPN, service-provider, or managed-service infrastructure.
· Maintain separate triage handling for exposure, suspicious control-plane behavior, and confirmed fabric-impact activity.
· Ensure detections can be tuned for legitimate maintenance, migration, disaster recovery, emergency access, automation, and provider-supported operations.
S25 Ultra-Tuned Detection Engineering Rules
NDR / Network Behavioral Analytics
Detection Viability Assessment
NDR / Network Behavioral Analytics has three rules for this EXP report.
· NDR / Network Behavioral Analytics is viable for detecting suspicious SD-WAN control-plane access, NETCONF access, newly observed source behavior, peer-adjacent traffic patterns, and post-access traffic-flow changes affecting Cisco SD-WAN infrastructure.
· NDR / Network Behavioral Analytics is strongest where network-flow metadata, firewall telemetry, asset inventory, approved-peer baselines, administrative-source baselines, and SD-WAN Controller or Manager context can be correlated.
· NDR / Network Behavioral Analytics can identify suspicious sequencing between UDP control-plane activity, TCP NETCONF access, new source infrastructure, and follow-on communication changes.
· NDR / Network Behavioral Analytics is not a standalone source for confirming successful CVE-2026-20182 exploitation because encrypted control-plane traffic, trusted peer behavior, and limited payload visibility may prevent direct exploitation confirmation.
· NDR / Network Behavioral Analytics rules should be correlated with Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, topology inventory, and change-management context before classifying activity as confirmed compromise.
· NDR / Network Behavioral Analytics detection content should be treated as high-value behavioral coverage for suspicious control-plane access and fabric-impact support, not direct exploit confirmation by itself.
Rule 1
Cisco SD-WAN Control-Plane Access From Unapproved or Newly Observed Source
Rule Format
NDR behavioral analytics rule suitable for network-flow, firewall, asset-inventory, topology, and approved-peer correlation after sensor coverage validation, SD-WAN asset tagging, control-plane service validation, source-baseline validation, and environment-specific tuning.
Detection Purpose
· Detect traffic to Cisco SD-WAN Controller or Manager control-plane services from sources that are unknown, newly observed, external, or not approved for SD-WAN peer communication.
· Identify possible precursor activity associated with unauthorized SD-WAN control-plane trust establishment.
· Prioritize activity involving unfamiliar source IPs, cloud infrastructure, VPN egress, hosting providers, unmanaged networks, unusual geographies, unusual ASNs, or sources not present in approved SD-WAN topology.
· Support investigation of exploited SD-WAN control-plane trust abuse without relying on CVE-string matches, scanner output, advisory references, payload visibility, or exploit-specific indicators.
· This rule does not prove successful rogue peering, administrative access, NETCONF use, or SD-WAN configuration manipulation without supporting controller-side, authentication, NETCONF, topology, or configuration-audit evidence.
Detection Logic
· Identify UDP control-plane traffic to Cisco SD-WAN Controller or Manager infrastructure from a source not present in approved SD-WAN peer inventories.
· Prioritize sources that are newly observed, external, associated with cloud or hosting infrastructure, associated with VPN egress, geographically unusual, ASN-unusual, or not linked to approved service-provider paths.
· Increase confidence when the source communicates with multiple SD-WAN Controller or Manager systems within the same operational window.
· Increase confidence when control-plane traffic is followed by TCP NETCONF access from the same source, related source, infrastructure cluster, ASN, cloud provider, VPN provider, or access path.
· Increase confidence when controller-side logs show unknown peer identity fields, peer-state changes, control-connection instability, or unexpected device-registration activity near the network event.
· Increase confidence when activity occurs outside approved maintenance, migration, disaster-recovery, service-provider, automation, or emergency-access windows.
· Reduce severity for approved peers, known controller relationships, expected edge-device communication, sanctioned service-provider access, planned topology changes, and documented maintenance activity.
· Do not classify UDP control-plane traffic as compromise without corroborating peer-state, authentication, NETCONF, configuration, topology, or change-management evidence.
Required Telemetry
· Network-flow telemetry.
· Firewall logs.
· NDR session metadata.
· Source IP.
· Destination IP.
· Destination port.
· Protocol.
· Timestamp.
· Session duration.
· Connection count.
· Directionality.
· Asset identity for Cisco SD-WAN Controller or Manager systems.
· Approved SD-WAN peer inventory.
· Approved System IP, site ID, domain ID, public IP, peer type, and device-identity context where available.
· Approved administrative and service-provider source networks.
· GeoIP, ASN, VPN, cloud-provider, and hosting-provider enrichment.
· Maintenance-window and change-management context.
· Cisco SD-WAN Controller or Manager log correlation where available.
· Authentication, NETCONF, and configuration-audit correlation where available.
Engineering Implementation Instructions
· Build an asset group for Cisco SD-WAN Controller and Manager infrastructure.
· Validate the control-plane service ports used by the organization’s Cisco SD-WAN deployment before production deployment.
· Build and maintain allowlists for approved SD-WAN peers, controller relationships, service-provider paths, automation sources, emergency-access paths, and management networks.
· Add enrichment for source geography, ASN, cloud provider, hosting provider, VPN provider, and first-seen timestamp.
· Tune the rule to distinguish approved edge-device and controller-to-controller traffic from unknown or newly observed external sources.
· Correlate suspicious source activity with controller-side peer-state, control-connection, device-registration, authentication, NETCONF, and configuration events.
· Use shorter correlation windows for rapid source-to-NETCONF sequencing and longer windows for slow control-plane probing or repeated access attempts.
· Avoid broad suppression for cloud, VPN, managed-service, or service-provider infrastructure because attacker and legitimate administrative paths may overlap.
· Treat this rule as higher priority when the source also performs NETCONF access, repeated control-plane access, or traffic toward multiple SD-WAN management assets.
· Use change-management and maintenance records as triage evidence before classifying the event as suspicious or confirmed control-plane abuse.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to unauthorized or newly observed access to SD-WAN control-plane services rather than static exploit indicators.
· The rule remains useful if exploit delivery changes but the attacker still needs to interact with SD-WAN control-plane infrastructure.
· The score is supported by the durability of source, destination, protocol, timing, asset, topology, and peer-inventory mismatch as observable network behaviors.
· The score is constrained by legitimate service-provider access, controller migration, disaster recovery, edge onboarding, cloud-hosted administration, and incomplete peer inventories.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on NDR sensor coverage, network-flow fidelity, accurate SD-WAN asset tagging, approved-peer inventory, administrative-source baselines, and maintenance-window context.
· Operational confidence is reduced where SD-WAN peer inventories are incomplete, service-provider access paths are poorly documented, or cloud and VPN egress overlap heavily with legitimate administration.
· Full-telemetry confidence improves when NDR events are enriched with Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, and change-management context.
· Even under full telemetry conditions, this rule should support escalation and investigation rather than standalone confirmation of successful exploitation.
Limitations
· This rule detects suspicious control-plane access, not successful exploitation.
· Encrypted control-plane traffic may limit payload visibility and prevent direct inspection of authentication behavior.
· Legitimate SD-WAN operations, edge onboarding, controller migration, managed-service activity, and disaster-recovery testing may overlap with the same network patterns.
· The rule requires accurate SD-WAN asset inventory, approved-peer baselines, and administrative-source baselines to remain reliable.
· Confirmation requires correlation with peer-state changes, administrative authentication, NETCONF access, SD-WAN configuration changes, topology mismatch, or unauthorized fabric-impact activity.
Detection Query Pattern
NDR behavioral query pattern requiring platform syntax validation, SD-WAN asset tagging, approved-peer validation, service-port validation, source-enrichment validation, timing-window tuning, and environment-specific allowlisting before production deployment.
NetworkEvent
WHERE DestinationAsset IN ASSET_GROUP(
"Cisco SD-WAN Controllers",
"Cisco SD-WAN Managers"
)
AND Protocol = "UDP"
AND DestinationPort IN ENV_CISCO_SDWAN_CONTROL_PLANE_PORTS
AND SourceIP NOT IN ASSET_GROUP(
"Approved SD-WAN Peers",
"Approved SD-WAN Controllers",
"Approved SD-WAN Edge Devices",
"Approved Service Provider SD-WAN Sources",
"Approved Automation Sources",
"Approved Emergency Access Sources"
)
AND (
SourceFirstSeen WITHIN ENV_NEW_SOURCE_WINDOW
OR SourceGeo NOT IN ENV_APPROVED_SDWAN_ADMIN_GEOS
OR SourceASN NOT IN ENV_APPROVED_SDWAN_ADMIN_ASNS
OR SourceProviderType IN ANY (
"cloud_hosting",
"vpn_provider",
"hosting_provider",
"unknown_external"
)
OR ConnectionCount >= ENV_SDWAN_CONTROL_PLANE_ATTEMPT_THRESHOLD
)
AND EVENT_NEAR WITHIN ENV_SDWAN_CORRELATION_WINDOW (
NetworkEvent.DestinationPort = 830
OR ControllerEvent.EventType IN ANY (
"Unknown Peer Observed",
"Peer State Changed",
"Control Connection Anomaly",
"Unexpected Device Registration",
"Unexpected Peer Identity"
)
OR AuthEvent.EventType IN ANY (
"Administrative Authentication Success",
"Failed To Successful Administrative Authentication"
)
)
AND NOT ChangeContext IN ANY (
"approved_sdwan_maintenance",
"approved_controller_migration",
"approved_edge_onboarding",
"approved_disaster_recovery",
"approved_service_provider_activity",
"approved_emergency_access"
)
Rule 2
Control-Plane Activity Followed by NETCONF Access to Cisco SD-WAN Infrastructure
Rule Format
NDR behavioral correlation rule suitable for network-flow and session-sequence detection after SD-WAN asset tagging, NETCONF service validation, source-relationship validation, baseline validation, and environment-specific tuning.
Detection Purpose
· Detect suspicious sequencing where control-plane access to Cisco SD-WAN infrastructure is followed by NETCONF access from the same or related source.
· Identify behavior consistent with progression from control-plane interaction to privileged SD-WAN management activity.
· Prioritize sources that are unfamiliar, newly observed, external, unauthorized, or not aligned with approved administrative and automation paths.
· Support investigation of possible SD-WAN control-plane trust abuse without requiring encrypted payload visibility.
· This rule does not prove successful exploitation or configuration manipulation without supporting SD-WAN Controller, Manager, authentication, NETCONF, or configuration-audit evidence.
Detection Logic
· Identify UDP control-plane traffic to Cisco SD-WAN Controller or Manager systems followed by TCP NETCONF access to SD-WAN management or control-plane infrastructure.
· Correlate events by source IP, related source IP, subnet, ASN, cloud provider, VPN provider, service-provider path, or infrastructure cluster.
· Prioritize activity where the source is not part of approved peer inventories, approved NETCONF source lists, administrative VPN paths, service-provider paths, automation sources, or emergency-access paths.
· Increase confidence when the source is newly observed or when the source accesses multiple SD-WAN Controller, Manager, or NETCONF destinations.
· Increase confidence when the sequence occurs near peer-state changes, control-connection instability, administrative authentication success, or configuration-audit activity.
· Increase confidence when activity occurs outside approved maintenance windows or lacks change-management justification.
· Reduce severity for approved automation, approved NETCONF management workflows, service-provider maintenance, planned migration, and documented emergency access.
· Do not classify NETCONF access as malicious without source, identity, timing, peer-state, topology, and configuration-change context.
Required Telemetry
· Network-flow telemetry.
· NDR session metadata.
· Firewall logs where available.
· Source IP.
· Destination IP.
· Destination port.
· Protocol.
· Timestamp.
· Session duration.
· Session count.
· Asset identity for Cisco SD-WAN Controller and Manager systems.
· Asset identity for NETCONF-exposed SD-WAN infrastructure.
· Approved NETCONF source lists.
· Approved SD-WAN administrative source networks.
· Approved peer and controller inventories.
· GeoIP, ASN, cloud-provider, VPN-provider, hosting-provider, and first-seen enrichment.
· Cisco SD-WAN Controller or Manager peer-state correlation where available.
· Authentication and configuration-audit correlation where available.
· Maintenance-window, automation, service-provider, and change-management context.
Engineering Implementation Instructions
· Build asset groups for Cisco SD-WAN Controller, Manager, and NETCONF-exposed SD-WAN infrastructure.
· Validate the organization’s NETCONF exposure and expected NETCONF source networks before enabling high-severity alerting.
· Correlate UDP control-plane activity and TCP NETCONF access by source, related source, source subnet, infrastructure cluster, ASN, VPN provider, cloud provider, or service-provider path.
· Tune correlation windows based on normal SD-WAN control-plane and NETCONF administrative workflows.
· Add allowlists for approved automation systems, administrative jump hosts, service-provider sources, emergency-access paths, and planned maintenance workflows.
· Avoid suppressing all NETCONF activity from broad infrastructure categories because both legitimate administrators and attackers may use cloud, VPN, or provider egress.
· Increase severity when NETCONF access follows unknown peer activity, peer-state changes, administrative authentication, or configuration modifications.
· Use Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, and configuration audit logs to determine whether the sequence indicates suspicious activity or authorized administration.
DRI Assessment
DRI
8.5 / 10
· The rule is behaviorally anchored to a durable sequence: control-plane access followed by NETCONF access.
· The rule remains useful if the exploit implementation changes but the attacker still proceeds from SD-WAN control-plane interaction to privileged management activity.
· The score is supported by the operational significance of NETCONF access following suspicious control-plane behavior.
· The score is constrained by legitimate automation, service-provider maintenance, emergency access, and environments where NETCONF is routinely used for authorized administration.
TCR Assessment
Operational TCR
7.5 / 10
Full-Telemetry TCR
9.0 / 10
· Operational confidence depends on network-flow fidelity, SD-WAN asset tagging, NETCONF source baselines, correlation timing, and approved administrative workflow documentation.
· Operational confidence is reduced where NETCONF source lists are incomplete, automation paths are poorly documented, or SD-WAN management traffic is not consistently visible to NDR sensors.
· Full-telemetry confidence improves when network sequencing is correlated with peer-state changes, authentication success, NETCONF records, configuration audit logs, and change-management context.
· Under full telemetry conditions, this rule can provide strong evidence of suspicious SD-WAN management activity, but confirmed exploitation still requires Cisco SD-WAN telemetry or configuration-impact evidence.
Limitations
· This rule detects suspicious control-plane-to-NETCONF sequencing, not successful exploitation by itself.
· NETCONF may be legitimate in environments with approved automation, service-provider management, or administrative workflows.
· Encrypted traffic and limited session metadata may restrict insight into command content or configuration intent.
· Related-source correlation may be imperfect when attackers rotate infrastructure or use shared cloud, VPN, or provider egress.
· Confirmation requires correlation with peer-state anomalies, administrative authentication, configuration changes, unauthorized source context, or topology mismatch.
Detection Query Pattern
NDR behavioral query pattern requiring platform syntax validation, SD-WAN asset tagging, NETCONF-source validation, related-source correlation validation, timing-window tuning, and environment-specific allowlisting before production deployment.
NetworkEvent AS ControlPlaneEvent
WHERE ControlPlaneEvent.DestinationAsset IN ASSET_GROUP(
"Cisco SD-WAN Controllers",
"Cisco SD-WAN Managers"
)
AND ControlPlaneEvent.Protocol = "UDP"
AND ControlPlaneEvent.DestinationPort IN ENV_CISCO_SDWAN_CONTROL_PLANE_PORTS
AND ControlPlaneEvent.SourceIP NOT IN ASSET_GROUP(
"Approved SD-WAN Peers",
"Approved SD-WAN Controllers",
"Approved SD-WAN Edge Devices",
"Approved Service Provider SD-WAN Sources"
)
AND EVENT_NEAR WITHIN ENV_SDWAN_NETCONF_SEQUENCE_WINDOW (
NetworkEvent AS NetconfEvent
WHERE NetconfEvent.Protocol = "TCP"
AND NetconfEvent.DestinationPort = 830
AND NetconfEvent.DestinationAsset IN ASSET_GROUP(
"Cisco SD-WAN Controllers",
"Cisco SD-WAN Managers",
"NETCONF Exposed SD-WAN Infrastructure"
)
AND RELATED_SOURCE(
ControlPlaneEvent.SourceIP,
NetconfEvent.SourceIP,
"same_ip",
"same_subnet",
"same_asn",
"same_cloud_provider",
"same_vpn_provider",
"same_infrastructure_cluster"
)
AND NetconfEvent.SourceIP NOT IN ASSET_GROUP(
"Approved NETCONF Sources",
"Approved SD-WAN Admin Sources",
"Approved Automation Sources",
"Approved Service Provider Sources",
"Approved Emergency Access Sources"
)
)
AND (
ControlPlaneEvent.SourceFirstSeen WITHIN ENV_NEW_SOURCE_WINDOW
OR ControlPlaneEvent.ConnectionCount >= ENV_SDWAN_CONTROL_PLANE_ATTEMPT_THRESHOLD
OR NetconfEvent.ConnectionCount >= ENV_NETCONF_ATTEMPT_THRESHOLD
OR SourceProviderType IN ANY (
"cloud_hosting",
"vpn_provider",
"hosting_provider",
"unknown_external"
)
)
AND NOT ChangeContext IN ANY (
"approved_sdwan_maintenance",
"approved_netconf_automation",
"approved_service_provider_activity",
"approved_emergency_access",
"approved_controller_migration"
)
Rule 3
Suspicious SD-WAN Traffic-Flow Change After Control-Plane or NETCONF Activity
Rule Format
NDR behavioral analytics and traffic-change correlation rule suitable for network-flow baselining, SD-WAN asset tagging, route or tunnel-impact inference, and post-access communication monitoring after baseline validation, topology validation, and environment-specific tuning.
Detection Purpose
· Detect new or unusual traffic-flow behavior after suspicious SD-WAN control-plane or NETCONF activity.
· Identify possible SD-WAN fabric-impact behavior, including new access paths, traffic redirection, unexpected internal reachability, or communication with unfamiliar external infrastructure.
· Prioritize activity where suspicious control-plane or NETCONF activity is followed by new flows involving sensitive internal segments, management systems, cloud networks, branch environments, data-center systems, or remote-site infrastructure.
· Support investigation of post-access impact without assuming that network telemetry alone can confirm configuration manipulation.
· This rule does not prove successful SD-WAN compromise without supporting configuration audit, controller-side, authentication, NETCONF, or change-management evidence.
Detection Logic
· Identify suspicious control-plane or NETCONF activity involving Cisco SD-WAN infrastructure.
· Detect new or unusual traffic flows after the suspicious access window.
· Prioritize flows involving sensitive internal segments, identity systems, management systems, monitoring systems, backup systems, hypervisor systems, network-administration systems, data-center systems, cloud networks, branch environments, or remote-site infrastructure.
· Increase confidence when traffic-flow changes involve unfamiliar peers, new public IPs, new controller relationships, newly reachable destinations, or previously unseen source-to-destination pairs.
· Increase confidence when flow changes occur after route, tunnel, policy, certificate, peer-state, or fabric-trust changes observed in SD-WAN Controller or Manager logs.
· Increase confidence when new access paths persist across multiple sessions or recur after remediation, rollback, patching, or maintenance.
· Reduce severity for approved routing changes, tunnel changes, policy deployments, migrations, disaster-recovery testing, service-provider maintenance, and documented network changes.
· Do not classify post-access traffic-flow change as compromise without correlating source, timing, topology, authorization context, and configuration-change evidence.
Required Telemetry
· Network-flow telemetry.
· NDR behavioral baselines.
· Firewall logs where available.
· Source IP.
· Destination IP.
· Destination port.
· Protocol.
· Timestamp.
· Session duration.
· Connection count.
· First-seen source-to-destination pair.
· Asset identity and asset criticality.
· Sensitive segment tags.
· SD-WAN Controller and Manager asset tags.
· Approved SD-WAN peer and controller relationship inventory.
· Approved route, tunnel, policy, and fabric-change context where available.
· Configuration audit correlation where available.
· Change-management and maintenance-window context.
· GeoIP, ASN, cloud-provider, VPN-provider, and hosting-provider enrichment.
· Post-remediation and rollback timing context where available.
Engineering Implementation Instructions
· Build asset groups for Cisco SD-WAN infrastructure, sensitive internal segments, identity systems, management systems, backup systems, hypervisor systems, network-administration systems, data-center environments, branch environments, cloud environments, and remote-site infrastructure.
· Establish baselines for normal SD-WAN-related traffic flows, expected branch-to-data-center communication, expected cloud connectivity, expected management access, and expected route or tunnel-driven traffic patterns.
· Correlate suspicious control-plane or NETCONF activity with subsequent first-seen or abnormal source-to-destination flows.
· Tune timing windows to account for immediate configuration impact and delayed traffic-flow changes after policy deployment or route propagation.
· Add allowlists for approved network changes, route deployments, tunnel deployments, policy pushes, migrations, disaster-recovery tests, service-provider maintenance, and emergency changes.
· Avoid broad suppression of new flows from SD-WAN environments because fabric compromise may create traffic that resembles legitimate route or policy changes.
· Increase severity when new traffic flows target sensitive internal services or create new reachability between previously unrelated environments.
· Use SD-WAN configuration audit logs and change-management records to determine whether the traffic change was authorized.
· Map abstract enrichment concepts such as peer context, site context, and fabric context to platform-specific fields before production use.
DRI Assessment
DRI
7.5 / 10
· The rule is behaviorally anchored to post-access traffic-flow changes that may follow SD-WAN control-plane trust abuse.
· The rule remains useful if the exploit implementation changes but the attacker uses SD-WAN fabric control to create new access paths or alter routing behavior.
· The score is supported by the durability of traffic-flow changes, new reachability, and sensitive-segment access as observable network outcomes.
· The score is constrained by legitimate network changes, route updates, tunnel adjustments, cloud connectivity changes, disaster-recovery testing, and incomplete flow baselines.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on flow coverage, sensitive-asset tagging, SD-WAN topology baselines, route and tunnel baselines, change-management linkage, and correlation with suspicious control-plane or NETCONF activity.
· Operational confidence is reduced where SD-WAN flow baselines are immature, sensitive-segment tagging is incomplete, or legitimate routing and policy changes are frequent.
· Full-telemetry confidence improves when traffic-flow changes are correlated with SD-WAN configuration audit logs, peer-state changes, authentication records, NETCONF activity, route changes, tunnel changes, policy changes, and change-management context.
· Even under full telemetry conditions, traffic-flow change should be treated as impact-supporting evidence rather than standalone proof of exploitation.
Limitations
· This rule detects suspicious post-access traffic-flow changes, not exploit execution.
· Legitimate route, tunnel, policy, migration, service-provider, disaster-recovery, and emergency network changes may overlap with the same behavior.
· NDR may not directly observe SD-WAN configuration intent or peer-state context.
· Incomplete sensitive-asset tagging or weak flow baselines may reduce confidence.
· Confirmation requires correlation with suspicious control-plane activity, NETCONF access, SD-WAN configuration changes, topology mismatch, or unauthorized change context.
Detection Query Pattern
NDR behavioral query pattern requiring platform syntax validation, SD-WAN asset tagging, sensitive-segment tagging, flow-baseline validation, change-context validation, timing-window tuning, and environment-specific allowlisting before production deployment.
NetworkEvent AS AccessEvent
WHERE AccessEvent.DestinationAsset IN ASSET_GROUP(
"Cisco SD-WAN Controllers",
"Cisco SD-WAN Managers",
"NETCONF Exposed SD-WAN Infrastructure"
)
AND (
(
AccessEvent.Protocol = "UDP"
AND AccessEvent.DestinationPort IN ENV_CISCO_SDWAN_CONTROL_PLANE_PORTS
)
OR (
AccessEvent.Protocol = "TCP"
AND AccessEvent.DestinationPort = 830
)
)
AND AccessEvent.SourceIP NOT IN ASSET_GROUP(
"Approved SD-WAN Peers",
"Approved SD-WAN Admin Sources",
"Approved NETCONF Sources",
"Approved Automation Sources",
"Approved Service Provider Sources",
"Approved Emergency Access Sources"
)
AND EVENT_AFTER WITHIN ENV_SDWAN_POST_ACCESS_WINDOW (
NetworkEvent AS PostAccessFlow
WHERE PostAccessFlow.IsFirstSeenFlow = true
OR PostAccessFlow.BaselineDeviation >= ENV_SDWAN_FLOW_DEVIATION_THRESHOLD
OR PostAccessFlow.DestinationAsset IN ASSET_GROUP(
"Identity Systems",
"Management Systems",
"Monitoring Systems",
"Backup Systems",
"Hypervisor Systems",
"Network Administration Systems",
"Sensitive Internal Segments",
"Critical Data Center Systems",
"Critical Cloud Systems"
)
OR PostAccessFlow.SourceToDestinationPair NOT IN BASELINE(
"Approved SD-WAN Traffic Flows"
)
)
AND (
RELATED_SOURCE(
AccessEvent.SourceIP,
PostAccessFlow.SourceIP,
"same_ip",
"same_subnet",
"same_sdwan_peer_context",
"same_site_context",
"same_fabric_context"
)
OR PostAccessFlow.SourceAsset IN ASSET_GROUP(
"Cisco SD-WAN Managed Branches",
"Cisco SD-WAN Managed Data Centers",
"Cisco SD-WAN Managed Cloud Segments",
"Cisco SD-WAN Managed Remote Sites"
)
)
AND NOT ChangeContext IN ANY (
"approved_route_change",
"approved_tunnel_change",
"approved_policy_deployment",
"approved_controller_migration",
"approved_disaster_recovery_test",
"approved_service_provider_activity",
"approved_emergency_change"
)
SentinelOne
Detection Viability Assessment
SentinelOne has three rules for this EXP report.
· SentinelOne is viable where Cisco SD-WAN Controller, Manager, or supporting infrastructure is deployed on monitored hosts, cloud workloads, virtual appliances, or adjacent management systems with endpoint or workload telemetry available.
· SentinelOne is strongest where process execution, command-line capture, process ancestry, file activity, account activity, network connection telemetry, endpoint identity, workload tags, and administrative-session context can be correlated.
· SentinelOne can support detection of suspicious administrative activity, unauthorized key or account artifacts, configuration export or manipulation behavior, and post-access persistence-adjacent activity on monitored SD-WAN infrastructure.
· SentinelOne is not a standalone source for confirming successful CVE-2026-20182 exploitation because the core behavior may occur through SD-WAN control-plane peering, NETCONF access, and controller-side configuration changes that may not always produce endpoint-level artifacts.
· SentinelOne rules should be correlated with Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, topology inventory, network-flow telemetry, and change-management context before classifying activity as confirmed compromise.
· SentinelOne detection content should be treated as high-value workload and endpoint behavioral coverage, not direct exploit confirmation by itself.
Rule 1
Suspicious Administrative Shell or Process Activity on Cisco SD-WAN Infrastructure
Rule Format
SentinelOne Deep Visibility query pattern suitable for STAR-style alerting after tenant syntax validation, field validation, SD-WAN workload tagging, administrative-tool baselining, approved-management-channel validation, and environment-specific tuning.
Detection Purpose
Detect suspicious administrative shell, process, or command activity on monitored Cisco SD-WAN Controller, Manager, or supporting infrastructure.
· Identify activity that may follow unauthorized SD-WAN control-plane trust establishment, suspicious administrative authentication, or NETCONF access.
· Prioritize activity involving unfamiliar users, unusual parent processes, interactive shells, remote sessions, temporary paths, user-writable paths, configuration directories, or unapproved administrative channels.
· Support investigation of post-access SD-WAN administrative behavior without relying on CVE-string matches, scanner output, advisory references, payload artifacts, or exploit branding.
· This rule does not prove successful SD-WAN exploitation, rogue peering, NETCONF misuse, or configuration manipulation without supporting controller-side, authentication, NETCONF, configuration-audit, topology, or network-flow evidence.
Detection Logic
Identify administrative shell or process execution on monitored Cisco SD-WAN Controller, Manager, or supporting infrastructure.
· Prioritize commands associated with configuration review, configuration export, configuration import, service manipulation, account review, authorized-key access, certificate handling, network inspection, or administrative file access.
· Increase confidence when execution occurs from unusual users, unusual parent processes, remote sessions, temporary paths, user-writable paths, or nonstandard administrative channels.
· Increase confidence when the same host or workload also shows suspicious network connections, NETCONF activity, controller-side peer anomalies, administrative authentication anomalies, or configuration audit events.
· Increase confidence when execution occurs outside approved maintenance, service-provider, automation, emergency-access, or change-management windows.
· Reduce severity for approved automation, documented service-provider activity, controller maintenance, planned migration, patching, backup operations, and authorized administrative runbooks.
· Do not classify administrative shell or process activity as compromise without corroborating SD-WAN control-plane, authentication, NETCONF, configuration, topology, or network-flow evidence.
Required Telemetry
SentinelOne process creation telemetry.
· Full command-line capture.
· Process ancestry.
· Source process name.
· Source process path.
· Parent process name.
· Parent process path.
· User and administrative context.
· Logon session context where available.
· Endpoint or workload identity.
· Endpoint or workload role tag.
· Operating system.
· File activity near the process event where available.
· Network connection telemetry where available.
· Endpoint agent status and heartbeat where available.
· SD-WAN Controller or Manager asset tagging.
· Approved administrative workflow context.
· Maintenance-window and change-management context.
· Timestamp.
Engineering Implementation Instructions
Validate SentinelOne tenant syntax and tenant field names for process event type, source process, target process, command line, user, parent process, endpoint identity, workload tag, network connection context, and timestamp before deployment.
· Scope the rule to monitored Cisco SD-WAN Controller, Manager, and supporting management infrastructure where SentinelOne telemetry is available.
· Tag SD-WAN workloads and supporting infrastructure separately from general servers to prevent broad alerting.
· Baseline approved administrative tools, service-provider access, automation tasks, backup workflows, patching activity, controller maintenance, and emergency-access procedures.
· Add allowlists for approved automation accounts, service-provider runbooks, maintenance scripts, backup utilities, monitoring tools, patching workflows, and sanctioned administrative paths.
· Avoid allowlisting broad shell, service, or account-management activity that could suppress suspicious use of the same utilities outside approved workflows.
· Treat activity as higher priority when paired with suspicious SD-WAN peering, administrative authentication, NETCONF access, configuration change, unauthorized key changes, or unusual outbound connections.
· Use Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, and NDR telemetry as triage evidence before classifying the case as confirmed SD-WAN compromise.
DRI Assessment
DRI
7.5 / 10
· The rule is behaviorally anchored to suspicious administrative activity on monitored SD-WAN infrastructure rather than static exploit indicators.
· The rule remains useful if the exploit implementation changes but attacker activity still produces administrative shell, process, service, account, or configuration-adjacent behavior on monitored infrastructure.
· The score is supported by the durability of process lineage, command-line, administrative context, and workload-role anomalies as observable endpoint behaviors.
· The score is constrained by legitimate maintenance, service-provider activity, automation, backup workflows, patching, controller migration, and inconsistent host-level telemetry on SD-WAN appliances.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
8.0 / 10
· Operational confidence depends on SentinelOne coverage for SD-WAN infrastructure, command-line capture, process lineage, workload tagging, approved administrative baselines, and maintenance-window context.
· Operational confidence is reduced where SD-WAN infrastructure is appliance-locked, provider-managed, cloud-managed, or not instrumented with SentinelOne.
· Full-telemetry confidence improves when SentinelOne events are enriched with Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, NDR telemetry, and change-management context.
· Even under full telemetry conditions, this rule should support escalation and investigation rather than standalone confirmation of successful exploitation.
Limitations
This rule detects suspicious administrative process behavior on monitored infrastructure, not successful exploitation.
· SentinelOne may not observe activity occurring entirely within SD-WAN control-plane logic, provider-managed infrastructure, encrypted peering flows, or systems where the agent is not deployed.
· Legitimate controller maintenance, service-provider support, automation, backup activity, patching, migration, and emergency administration may overlap with this behavior.
· The rule requires accurate SD-WAN asset tagging, process lineage, command-line capture, and administrative workflow baselines to remain reliable.
· Confirmation requires correlation with SD-WAN peer-state anomalies, administrative authentication, NETCONF access, configuration changes, topology mismatch, or network-flow evidence.
Detection Query Pattern
SentinelOne Deep Visibility query pattern requiring tenant syntax validation, SD-WAN workload tagging, administrative-tool validation, workflow allowlisting, timing-window validation, and environment-specific tuning before production deployment.
EndpointOS IN ANY (
"linux",
"windows"
)
AND EventType IN ANY (
"Process Creation",
"Process Execution"
)
AND AgentComputerName IN ASSET_GROUP (
"Cisco SD-WAN Controllers",
"Cisco SD-WAN Managers",
"Cisco SD-WAN Supporting Infrastructure",
"NETCONF Exposed SD-WAN Infrastructure"
)
AND (
SrcProcName IN ANY (
"bash",
"sh",
"zsh",
"dash",
"sudo",
"su",
"ssh",
"scp",
"sftp",
"python",
"python3",
"perl",
"curl",
"wget",
"openssl",
"systemctl",
"service",
"journalctl",
"netstat",
"ss",
"ip",
"ifconfig",
"tcpdump",
"vi",
"vim",
"nano",
"cat",
"cp",
"mv",
"chmod",
"chown",
"tar",
"gzip"
)
OR SrcProcCmdLine CONTAINS ANY (
"netconf",
"sdwan",
"vmanage",
"configuration",
"config",
"certificate",
"authorized_keys",
".ssh",
"systemctl",
"service",
"journalctl",
"tcpdump",
"route",
"policy",
"tunnel",
"peer",
"controller"
)
)
AND (
SrcProcParentName IN ANY (
"bash",
"sh",
"zsh",
"dash",
"sudo",
"su",
"ssh",
"python",
"python3",
"cron",
"systemd"
)
OR SrcProcCmdLine CONTAINS ANY (
"/tmp/",
"/var/tmp/",
"/dev/shm/",
"/home/",
"/root/",
"curl ",
"wget ",
"chmod +x",
"authorized_keys",
".ssh/"
)
OR UserName NOT IN ASSET_GROUP (
"Approved SD-WAN Administrators",
"Approved SD-WAN Automation Accounts",
"Approved Service Provider Accounts"
)
)
AND EVENT_NEAR WITHIN ENV_SDWAN_ENDPOINT_CORRELATION_WINDOW (
NetworkEvent.DstPort = 830
OR NetworkEvent.DstPort IN ENV_CISCO_SDWAN_CONTROL_PLANE_PORTS
OR FileEvent.TgtFilePath CONTAINS ANY (
".ssh",
"authorized_keys",
"certificate",
"config",
"backup",
"policy",
"template"
)
OR AuthEvent.EventType IN ANY (
"Administrative Authentication Success",
"Failed To Successful Administrative Authentication"
)
)
AND NOT ApprovedWorkflowContext IN ANY (
"approved_sdwan_maintenance",
"approved_backup_workflow",
"approved_patch_workflow",
"approved_controller_migration",
"approved_service_provider_activity",
"approved_automation_workflow",
"approved_emergency_access"
)
Rule 2
Unauthorized Key, Account, Certificate, or Configuration Artifact Activity on SD-WAN Infrastructure
Rule Format
SentinelOne Deep Visibility query pattern suitable for file, account, process, and configuration-adjacent activity correlation after tenant syntax validation, SD-WAN asset tagging, file-path validation, approved-workflow validation, and environment-specific tuning.
Detection Purpose
Detect unauthorized key, account, certificate, peer, or configuration artifact activity on monitored Cisco SD-WAN infrastructure.
· Identify persistence-adjacent or access-preservation behavior that may follow suspicious SD-WAN control-plane activity.
· Prioritize changes involving administrative keys, service accounts, certificates, configuration files, backup files, peer-related files, or controller relationship artifacts.
· Support investigation of post-access persistence and configuration drift without relying on exploit-specific files, payload hashes, public proof-of-concept artifacts, or CVE-string matches.
· This rule does not prove successful exploitation or persistent compromise without supporting authentication, controller-side, NETCONF, configuration-audit, topology, or network-flow evidence.
Detection Logic
Identify file creation, file modification, file rename, file deletion, account activity, or process activity affecting administrative key, account, certificate, or configuration-adjacent paths on monitored SD-WAN infrastructure.
· Prioritize activity involving .ssh, authorized_keys, certificate stores, configuration backups, policy files, template files, controller relationship artifacts, or service-account material.
· Increase confidence when activity is performed by unusual users, unusual parent processes, interactive shells, remote sessions, temporary paths, or nonstandard administrative channels.
· Increase confidence when artifact activity occurs near suspicious administrative authentication, NETCONF access, controller-side peer anomalies, or SD-WAN configuration changes.
· Increase confidence when changes persist after restart, policy refresh, rollback, patching, or remediation activity.
· Reduce severity for approved certificate renewal, backup workflows, configuration export, controller maintenance, service-provider activity, automation, and documented emergency access.
· Do not classify key, account, certificate, or configuration artifact activity as compromise without corroborating authentication, NETCONF, controller, configuration, topology, or network evidence.
Required Telemetry
SentinelOne file creation telemetry.
· SentinelOne file modification telemetry.
· File rename and file deletion telemetry where available.
· Process creation telemetry.
· Process ancestry.
· Source process name.
· Source process path.
· Source process command line.
· Parent process name.
· Parent process path.
· Target file path.
· Target file hash where available.
· User and administrative context.
· Account activity where available.
· Endpoint or workload identity.
· Endpoint or workload role tag.
· SD-WAN Controller or Manager asset tagging.
· Network connection telemetry where available.
· Agent heartbeat and endpoint availability telemetry where available.
· Maintenance-window and change-management context.
· Timestamp.
Engineering Implementation Instructions
Validate SentinelOne tenant syntax and tenant field names for file events, account events, source process, command line, target file path, user, endpoint identity, workload tag, network connection context, and timestamp before deployment.
· Validate how monitored SD-WAN infrastructure exposes administrative key paths, certificate paths, configuration paths, backup paths, and service-account activity.
· Scope the rule to Cisco SD-WAN Controller, Manager, and supporting management infrastructure where SentinelOne telemetry is available.
· Add allowlists for approved certificate renewal, backup workflows, configuration export, controller maintenance, patching, automation tasks, service-provider workflows, and emergency-access activity.
· Avoid suppressing broad key, certificate, or configuration paths because those same locations may be modified during suspicious post-access activity.
· Tune correlation windows around suspicious authentication, NETCONF access, peer-state change, configuration modification, restart, rollback, and remediation events.
· Treat activity as higher priority when paired with suspicious SD-WAN peering, unknown administrative source, NETCONF access, unauthorized configuration change, or recurring access from unfamiliar infrastructure.
· Use Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, topology inventory, and NDR telemetry as triage evidence before classifying the case as confirmed persistence or compromise.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to durable access-preservation and configuration-adjacent artifacts rather than exploit-specific payloads.
· The rule remains useful if attackers change the initial exploit path but still attempt to preserve access, alter trust, modify configuration, or maintain administrative reachability.
· The score is supported by the durability of administrative key, account, certificate, and configuration artifact changes as post-access behaviors.
· The score is constrained by legitimate certificate renewal, backup workflows, configuration export, service-provider maintenance, automation, patching, and inconsistent file visibility on SD-WAN infrastructure.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on file-event visibility, account-event visibility, process lineage, SD-WAN workload tagging, administrative workflow baselines, and path validation.
· Operational confidence is reduced where SD-WAN infrastructure is appliance-locked, provider-managed, cloud-managed, or does not expose file-level telemetry to SentinelOne.
· Full-telemetry confidence improves when file and account activity is correlated with controller logs, authentication records, NETCONF access, configuration audit logs, NDR telemetry, and change-management records.
· Even under full telemetry conditions, artifact changes should be treated as suspicious behavior requiring correlation rather than standalone confirmation of exploitation.
Limitations
This rule detects suspicious artifact activity, not successful exploitation by itself.
· Legitimate certificate renewal, backup activity, configuration export, controller maintenance, service-provider activity, and automation may overlap with this behavior.
· SentinelOne may not observe artifact activity on appliance-locked, provider-managed, or uninstrumented SD-WAN infrastructure.
· File path conventions may vary across versions, deployment models, and hosting architectures.
· Confirmation requires correlation with suspicious peering, administrative authentication, NETCONF access, configuration changes, topology mismatch, or unauthorized source context.
Detection Query Pattern
SentinelOne Deep Visibility query pattern requiring tenant syntax validation, SD-WAN asset tagging, file-path validation, account-event validation, approved workflow allowlisting, and timing-window tuning before production deployment.
EndpointOS IN ANY (
"linux",
"windows"
)
AND EventType IN ANY (
"File Creation",
"File Modification",
"File Rename",
"File Deletion",
"Process Creation",
"Account Modified",
"Account Created"
)
AND AgentComputerName IN ASSET_GROUP (
"Cisco SD-WAN Controllers",
"Cisco SD-WAN Managers",
"Cisco SD-WAN Supporting Infrastructure",
"NETCONF Exposed SD-WAN Infrastructure"
)
AND (
TgtFilePath CONTAINS ANY (
".ssh",
"authorized_keys",
"id_rsa",
"id_ed25519",
"certificate",
"cert",
"key",
"config",
"configuration",
"backup",
"template",
"policy",
"route",
"tunnel",
"peer",
"controller"
)
OR SrcProcCmdLine CONTAINS ANY (
"authorized_keys",
".ssh",
"certificate",
"cert",
"key",
"config",
"backup",
"template",
"policy",
"route",
"tunnel",
"peer",
"controller",
"useradd",
"usermod",
"passwd",
"chmod",
"chown"
)
)
AND (
SrcProcParentName IN ANY (
"bash",
"sh",
"zsh",
"dash",
"sudo",
"su",
"ssh",
"python",
"python3",
"cron",
"systemd"
)
OR SrcProcCmdLine CONTAINS ANY (
"/tmp/",
"/var/tmp/",
"/dev/shm/",
"/home/",
"/root/",
"chmod",
"chown",
"echo ",
"cat ",
"cp ",
"mv "
)
OR UserName NOT IN ASSET_GROUP (
"Approved SD-WAN Administrators",
"Approved SD-WAN Automation Accounts",
"Approved Service Provider Accounts"
)
)
AND EVENT_NEAR WITHIN ENV_SDWAN_PERSISTENCE_CORRELATION_WINDOW (
NetworkEvent.DstPort = 830
OR NetworkEvent.DstPort IN ENV_CISCO_SDWAN_CONTROL_PLANE_PORTS
OR AuthEvent.EventType IN ANY (
"Administrative Authentication Success",
"Failed To Successful Administrative Authentication"
)
OR ProcessEvent.SrcProcCmdLine CONTAINS ANY (
"config",
"backup",
"template",
"policy",
"route",
"tunnel",
"peer",
"controller"
)
)
AND NOT ApprovedWorkflowContext IN ANY (
"approved_certificate_renewal",
"approved_backup_workflow",
"approved_configuration_export",
"approved_controller_maintenance",
"approved_patch_workflow",
"approved_service_provider_activity",
"approved_automation_workflow",
"approved_emergency_access"
)
Rule 3
Suspicious Network Connection From SD-WAN Infrastructure After Administrative or Configuration Activity
Rule Format
SentinelOne Deep Visibility query pattern suitable for endpoint network-connection, process, file, and workload-context correlation after tenant syntax validation, network-event validation, SD-WAN asset tagging, approved-destination baselining, and environment-specific tuning.
Detection Purpose
Detect suspicious outbound or lateral network connections from monitored Cisco SD-WAN infrastructure after administrative, NETCONF, configuration, or artifact activity.
· Identify possible post-access behavior involving new destinations, sensitive internal segments, management systems, cloud infrastructure, or recurring external infrastructure.
· Prioritize connections from SD-WAN infrastructure to destinations not normally associated with approved management, monitoring, backup, service-provider, automation, or update workflows.
· Support investigation of possible SD-WAN fabric-impact or persistence behavior without assuming endpoint network telemetry alone confirms compromise.
· This rule does not prove successful exploitation or SD-WAN fabric manipulation without supporting controller-side, authentication, NETCONF, configuration-audit, topology, or NDR evidence.
Detection Logic
Identify outbound or lateral network connections from monitored Cisco SD-WAN Controller, Manager, or supporting infrastructure.
· Prioritize connections to newly observed destinations, unfamiliar cloud or hosting providers, unmanaged external networks, sensitive internal segments, identity systems, management systems, monitoring systems, backup systems, hypervisor systems, or network-administration systems.
· Increase confidence when the connection follows suspicious administrative shell activity, configuration file activity, account changes, certificate changes, NETCONF access, or controller-side configuration events.
· Increase confidence when the destination has not been historically contacted by the SD-WAN infrastructure or is not part of approved management, monitoring, update, automation, backup, or service-provider paths.
· Increase confidence when connections recur after remediation, rollback, patching, restart, or maintenance activity.
· Reduce severity for approved monitoring, backup, update, service-provider, automation, management, patching, and emergency-access workflows.
· Do not classify outbound or lateral connection activity as compromise without corroborating source, timing, administrative, configuration, topology, and authorization context.
Required Telemetry
SentinelOne network connection telemetry.
· Process creation telemetry.
· Process ancestry.
· Source process name.
· Source process path.
· Source process command line.
· User and administrative context.
· Endpoint or workload identity.
· Endpoint or workload role tag.
· Destination IP.
· Destination port.
· Protocol.
· Destination domain where available.
· Destination reputation where available.
· First-seen destination context.
· GeoIP, ASN, cloud-provider, VPN-provider, hosting-provider, and managed-service enrichment.
· File activity near the connection where available.
· Authentication and administrative context where available.
· Maintenance-window and change-management context.
· Timestamp.
Engineering Implementation Instructions
Validate SentinelOne tenant syntax and tenant field names for network connection events, process events, file events, source process, destination IP, destination port, destination domain, user, endpoint identity, workload tag, and timestamp before deployment.
· Scope the rule to monitored Cisco SD-WAN Controller, Manager, and supporting management infrastructure.
· Build approved destination baselines for monitoring, backup, update, logging, service-provider, automation, emergency-access, and management workflows.
· Add enrichment for destination reputation, first-seen destination, geography, ASN, cloud provider, hosting provider, VPN provider, and managed-service context.
· Tune the rule to distinguish approved platform communication from suspicious outbound or lateral behavior after administrative or configuration activity.
· Correlate suspicious connections with process execution, file activity, account activity, NETCONF access, configuration audit records, and NDR flow changes.
· Avoid broad suppression for cloud, VPN, hosting, or managed-service destinations because attacker infrastructure may use the same categories.
· Treat activity as higher priority when paired with suspicious SD-WAN peering, administrative authentication, NETCONF access, configuration changes, or persistence-adjacent artifact activity.
DRI Assessment
DRI
7.0 / 10
· The rule is behaviorally anchored to suspicious post-access network connections from monitored SD-WAN infrastructure.
· The rule remains useful if the exploit implementation changes but attacker activity creates new outbound, lateral, or recurring communication from SD-WAN infrastructure.
· The score is supported by the durability of first-seen destinations, unusual connection paths, and post-administrative network activity as observable endpoint behaviors.
· The score is constrained by legitimate monitoring, backup, update, service-provider, automation, management, and emergency-access communication that may overlap with the same patterns.
TCR Assessment
Operational TCR
6.0 / 10
Full-Telemetry TCR
8.0 / 10
· Operational confidence depends on SentinelOne network telemetry, destination baselines, SD-WAN workload tagging, process-to-connection linkage, destination enrichment, and maintenance-window context.
· Operational confidence is reduced where SD-WAN infrastructure has broad outbound communication, cloud-hosted workflows, service-provider access, or incomplete destination baselines.
· Full-telemetry confidence improves when SentinelOne network events are enriched with Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, NDR telemetry, and change-management context.
· Even under full telemetry conditions, this rule should be treated as post-access behavioral support rather than standalone proof of exploitation.
Limitations
This rule detects suspicious network connections from monitored SD-WAN infrastructure, not successful exploitation.
· Legitimate monitoring, backup, update, logging, service-provider, automation, management, patching, and emergency-access workflows may overlap with the same behavior.
· SentinelOne network telemetry may not show SD-WAN peer-state context, NETCONF command content, or configuration intent.
· Incomplete destination baselines may increase false positives.
· Confirmation requires correlation with suspicious peering, administrative authentication, NETCONF access, configuration changes, artifact activity, topology mismatch, or NDR flow evidence.
Detection Query Pattern
SentinelOne Deep Visibility query pattern requiring tenant syntax validation, SD-WAN asset tagging, network-event validation, destination-baseline validation, workflow allowlisting, and timing-window tuning before production deployment.
EndpointOS IN ANY (
"linux",
"windows"
)
AND EventType IN ANY (
"Network Connection",
"Process Creation",
"File Modification",
"File Creation"
)
AND AgentComputerName IN ASSET_GROUP (
"Cisco SD-WAN Controllers",
"Cisco SD-WAN Managers",
"Cisco SD-WAN Supporting Infrastructure",
"NETCONF Exposed SD-WAN Infrastructure"
)
AND (
DstIP NOT IN ASSET_GROUP (
"Approved SD-WAN Management Destinations",
"Approved Monitoring Destinations",
"Approved Backup Destinations",
"Approved Update Destinations",
"Approved Logging Destinations",
"Approved Automation Destinations",
"Approved Service Provider Destinations",
"Approved Emergency Access Destinations"
)
OR DstFirstSeen WITHIN ENV_NEW_DESTINATION_WINDOW
OR DstProviderType IN ANY (
"cloud_hosting",
"vpn_provider",
"hosting_provider",
"unknown_external"
)
OR DstAsset IN ASSET_GROUP (
"Identity Systems",
"Management Systems",
"Monitoring Systems",
"Backup Systems",
"Hypervisor Systems",
"Network Administration Systems",
"Sensitive Internal Segments"
)
)
AND EVENT_NEAR WITHIN ENV_SDWAN_POST_ADMIN_NETWORK_WINDOW (
ProcessEvent.SrcProcCmdLine CONTAINS ANY (
"netconf",
"config",
"configuration",
"backup",
"template",
"policy",
"route",
"tunnel",
"peer",
"controller",
"certificate",
"authorized_keys"
)
OR FileEvent.TgtFilePath CONTAINS ANY (
".ssh",
"authorized_keys",
"certificate",
"config",
"backup",
"template",
"policy"
)
OR AuthEvent.EventType IN ANY (
"Administrative Authentication Success",
"Failed To Successful Administrative Authentication"
)
)
AND NOT ApprovedWorkflowContext IN ANY (
"approved_monitoring_workflow",
"approved_backup_workflow",
"approved_update_workflow",
"approved_logging_workflow",
"approved_service_provider_activity",
"approved_automation_workflow",
"approved_emergency_access",
"approved_patch_workflow"
)
Splunk
Detection Viability Assessment
Splunk has three rules for this EXP report.
· Splunk is highly viable for detecting suspicious Cisco SD-WAN control-plane behavior because it can correlate SD-WAN Controller logs, Manager logs, authentication records, NETCONF telemetry, configuration audit records, network-flow data, firewall logs, topology inventory, and change-management context.
· Splunk is strongest where Cisco SD-WAN log sources are normalized, administrative source networks are baselined, SD-WAN assets are tagged, and peer identity fields can be enriched against approved topology.
· Splunk can identify high-confidence behavioral sequences involving suspicious peering, administrative authentication, NETCONF access, configuration modification, and post-access SD-WAN fabric impact.
· Splunk is not a standalone proof source unless the required Cisco SD-WAN telemetry and configuration context are available.
· Splunk rules should distinguish exposure, suspicious control-plane behavior, privileged management activity, and confirmed fabric-impact activity.
· Splunk detection content should be treated as high-value correlation coverage for exploited SD-WAN control-plane trust abuse.
Rule 1
Suspicious Cisco SD-WAN Peering or Control-Plane Activity From Unapproved Source
Rule Format
Splunk SPL correlation search suitable for Enterprise Security or scheduled alerting after index validation, source-type validation, SD-WAN field normalization, asset tagging, approved-peer baselining, and environment-specific tuning.
Detection Purpose
· Detect suspicious Cisco SD-WAN control-plane activity from sources that are unknown, newly observed, external, or not approved for SD-WAN peer communication.
· Identify possible unauthorized SD-WAN control-plane trust establishment.
· Prioritize events involving unfamiliar source IPs, unexpected peer identity fields, unusual geographies, unusual ASNs, cloud or VPN egress, or sources not present in approved SD-WAN topology.
· Support investigation of exploited SD-WAN control-plane trust abuse without relying on CVE-string matches, scanner output, advisory references, or exploit-specific indicators.
· This rule does not prove successful exploitation without supporting peer-state, authentication, NETCONF, configuration, topology, or change-management evidence.
Detection Logic
· Identify Cisco SD-WAN Controller or Manager control-plane events involving unknown, unexpected, or unapproved source IP addresses.
· Prioritize events where observed peer identity fields do not match approved SD-WAN inventory.
· Increase confidence when the source is newly observed or associated with cloud, VPN, hosting, unmanaged, unusual geography, or unusual ASN context.
· Increase confidence when the same source is associated with control-connection anomalies, peer-state changes, unexpected device registration, or unexpected peer identity fields.
· Increase confidence when activity is followed by administrative authentication, NETCONF access, or SD-WAN configuration changes.
· Increase confidence when activity occurs outside approved maintenance, migration, disaster-recovery, service-provider, automation, or emergency-access windows.
· Reduce severity for approved peers, known controller relationships, expected edge-device communication, sanctioned service-provider activity, planned topology changes, and documented maintenance activity.
· Do not classify control-plane activity as compromise without corroborating authentication, NETCONF, configuration, topology, or change-management evidence.
Required Telemetry
· Cisco SD-WAN Controller logs.
· Cisco SD-WAN Manager logs.
· Control-connection events.
· Peer-state events.
· Device-registration events.
· Source IP.
· Destination IP.
· Peer type.
· System IP.
· Site ID.
· Domain ID.
· Public IP.
· Device identity.
· Controller relationship.
· Event outcome.
· Timestamp.
· Network-flow telemetry where available.
· Firewall logs where available.
· GeoIP, ASN, VPN, cloud-provider, and hosting-provider enrichment.
· Approved SD-WAN peer inventory.
· Approved administrative and service-provider source networks.
· Maintenance-window and change-management context.
Engineering Implementation Instructions
· Validate Splunk indexes, source types, field names, and CIM alignment for Cisco SD-WAN Controller, Manager, network-flow, firewall, authentication, NETCONF, and configuration-audit sources.
· Normalize peer identity fields, including source IP, public IP, System IP, site ID, domain ID, peer type, device identity, controller relationship, and event outcome.
· Build lookup tables for approved SD-WAN peers, Controllers, Managers, edge devices, service-provider paths, automation sources, emergency-access paths, and administrative networks.
· Add enrichment for first-seen source, geography, ASN, cloud provider, VPN provider, and hosting provider.
· Correlate suspicious control-plane activity with authentication, NETCONF, configuration, and change-management records.
· Tune suppression logic for approved maintenance, migration, edge onboarding, disaster recovery, service-provider work, and emergency access.
· Avoid broad suppression for cloud, VPN, or service-provider sources because attacker and legitimate administrative paths may overlap.
· Use risk-based alerting where available to elevate events that combine peer anomalies, authentication success, NETCONF access, and configuration changes.
DRI Assessment
DRI
8.5 / 10
· The rule is behaviorally anchored to suspicious SD-WAN control-plane activity and peer identity mismatch rather than static exploit indicators.
· The rule remains useful if exploit delivery changes but the attacker still needs to interact with SD-WAN control-plane infrastructure.
· The score is supported by durable telemetry relationships across peer identity, source behavior, topology, and timing.
· The score is constrained by incomplete SD-WAN field normalization, incomplete peer inventories, service-provider activity, migrations, and legitimate edge onboarding.
TCR Assessment
Operational TCR
7.5 / 10
Full-Telemetry TCR
9.0 / 10
· Operational confidence depends on Cisco SD-WAN log ingestion, field normalization, approved-peer baselines, administrative-source baselines, and maintenance-window context.
· Operational confidence is reduced where Controller or Manager logs are incomplete, peer identity fields are not parsed, or service-provider paths are poorly documented.
· Full-telemetry confidence improves when Splunk correlates SD-WAN Controller logs, Manager logs, network-flow records, authentication logs, NETCONF telemetry, configuration audit logs, and change-management data.
· Even under full telemetry conditions, this rule should support investigation unless paired with authentication, NETCONF, or configuration-impact evidence.
Limitations
· This rule detects suspicious control-plane or peering behavior, not successful exploitation by itself.
· Legitimate SD-WAN operations, edge onboarding, controller migration, service-provider activity, and disaster-recovery testing may overlap with the same behavior.
· Incomplete topology inventory can reduce confidence in peer validation.
· Field normalization gaps may reduce detection accuracy.
· Confirmation requires correlation with administrative authentication, NETCONF access, configuration changes, topology mismatch, or unauthorized fabric-impact activity.
Detection Query Pattern
Splunk SPL pattern requiring index validation, source-type validation, Cisco SD-WAN field normalization, peer-inventory lookup validation, source-enrichment validation, and environment-specific tuning before production deployment.
index=sdwan sourcetype IN ("cisco:sdwan:controller","cisco:sdwan:manager")
(
event_type IN (
"peer_state_change",
"control_connection",
"device_registration",
"peer_identity",
"control_plane_event"
)
OR message IN (
"*peer*",
"*control connection*",
"*device registration*",
"*system-ip*",
"*site-id*",
"*domain-id*"
)
)
| eval src_ip=coalesce(src_ip, source_ip, public_ip, remote_ip)
| eval peer_type=coalesce(peer_type, remote_peer_type)
| eval system_ip=coalesce(system_ip, remote_system_ip)
| eval site_id=coalesce(site_id, remote_site_id)
| eval domain_id=coalesce(domain_id, remote_domain_id)
| lookup approved_sdwan_peers src_ip OUTPUT approved_peer, approved_peer_type, approved_site_id, approved_system_ip
| lookup approved_sdwan_admin_sources src_ip OUTPUT approved_admin_source
| lookup source_enrichment src_ip OUTPUT src_first_seen, src_geo, src_asn, src_provider_type
| where isnull(approved_peer)
OR approved_peer!="true"
OR peer_type!=approved_peer_type
OR site_id!=approved_site_id
OR system_ip!=approved_system_ip
OR src_first_seen>=relative_time(now(), "-7d")
OR src_provider_type IN ("cloud_hosting","vpn_provider","hosting_provider","unknown_external")
| lookup approved_sdwan_change_windows _time OUTPUT approved_change_context
| where isnull(approved_change_context)
| stats
min(_time) as first_seen
max(_time) as last_seen
values(event_type) as event_types
values(peer_type) as peer_types
values(system_ip) as system_ips
values(site_id) as site_ids
values(domain_id) as domain_ids
values(src_geo) as src_geos
values(src_asn) as src_asns
count as event_count
by src_ip dest host
| where event_count >= ENV_SDWAN_CONTROL_PLANE_EVENT_THRESHOLD
Rule 2
Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication
Rule Format
Splunk SPL correlation search suitable for Enterprise Security, risk-based alerting, or scheduled alerting after index validation, field normalization, authentication-source validation, NETCONF-source validation, timing-window validation, and environment-specific tuning.
Detection Purpose
· Detect suspicious sequencing where Cisco SD-WAN control-plane activity is followed by NETCONF access or administrative authentication.
· Identify behavior consistent with progression from control-plane interaction to privileged SD-WAN management activity.
· Prioritize sources that are unfamiliar, newly observed, external, unauthorized, or not aligned with approved administrative workflows.
· Support investigation of potential SD-WAN control-plane trust abuse without relying on encrypted payload inspection.
· This rule does not prove successful exploitation or configuration manipulation without supporting controller-side, authentication, NETCONF, configuration-audit, topology, or change-management evidence.
Detection Logic
· Identify suspicious SD-WAN control-plane or peer-state activity involving an unknown or unapproved source.
· Correlate the source or related source with successful administrative authentication or NETCONF access within the same operational window.
· Increase confidence when the source is newly observed, external, cloud-hosted, VPN-associated, hosting-provider-associated, or not part of approved administrative source lists.
· Increase confidence when the sequence occurs near peer-state changes, control-connection instability, device-registration activity, or unexpected peer identity fields.
· Increase confidence when NETCONF or authentication activity occurs outside approved maintenance, automation, service-provider, or emergency-access windows.
· Increase confidence when the sequence is followed by configuration audit activity.
· Reduce severity for approved automation, approved NETCONF management workflows, service-provider maintenance, planned migration, and documented emergency access.
· Do not classify NETCONF or administrative authentication as malicious without source, identity, timing, peer-state, topology, and configuration-change context.
Required Telemetry
· Cisco SD-WAN Controller logs.
· Cisco SD-WAN Manager logs.
· Authentication logs.
· NETCONF records or network-flow records for TCP port 830.
· Source IP.
· Destination IP.
· Username.
· Authentication method.
· Authentication outcome.
· NETCONF source.
· NETCONF destination.
· Peer-state context.
· Control-connection context.
· Device-registration context.
· Timestamp.
· Approved NETCONF source list.
· Approved SD-WAN administrative source networks.
· Approved peer and controller inventories.
· GeoIP, ASN, cloud-provider, VPN-provider, hosting-provider, and first-seen enrichment.
· Maintenance-window, automation, service-provider, and change-management context.
Engineering Implementation Instructions
· Validate Splunk indexes, source types, and field mappings for SD-WAN Controller, Manager, authentication, NETCONF, network-flow, and configuration-audit telemetry.
· Normalize source IP, destination IP, username, authentication outcome, NETCONF destination, peer identity fields, and timestamps.
· Build lookup tables for approved SD-WAN peers, approved administrative sources, approved NETCONF sources, automation sources, service-provider sources, and emergency-access paths.
· Correlate suspicious control-plane events with NETCONF and authentication events by source IP, related source IP, subnet, ASN, VPN provider, cloud provider, or infrastructure cluster.
· Tune correlation windows around normal SD-WAN administrative workflows and emergency-access procedures.
· Add suppression logic for approved maintenance, automation, service-provider operations, disaster recovery, controller migration, and emergency access.
· Avoid suppressing all NETCONF or administrative activity from broad infrastructure categories because attackers may use cloud, VPN, or provider egress.
· Use risk-based alerting to increase severity when the sequence is followed by configuration change or fabric-impact activity.
DRI Assessment
DRI
9.0 / 10
· The rule is behaviorally anchored to a durable progression from suspicious control-plane activity to privileged access.
· The rule remains useful if the exploit implementation changes but the attacker proceeds from control-plane interaction to administrative or NETCONF activity.
· The score is supported by the operational significance of NETCONF access or authentication following suspicious peering or peer-state activity.
· The score is constrained by legitimate automation, provider maintenance, emergency access, and incomplete NETCONF or authentication telemetry.
TCR Assessment
Operational TCR
8.0 / 10
Full-Telemetry TCR
9.5 / 10
· Operational confidence depends on reliable SD-WAN log ingestion, authentication visibility, NETCONF visibility, correlation timing, and approved administrative workflow documentation.
· Operational confidence is reduced where NETCONF records are unavailable, authentication logs lack source IP context, or approved source lists are incomplete.
· Full-telemetry confidence improves when the sequence is correlated with configuration audit records, peer-state changes, topology mismatch, and change-management context.
· Under full telemetry conditions, this rule provides strong suspicious-activity coverage, but confirmed exploitation still requires evidence of unauthorized peer status, configuration impact, or fabric change.
Limitations
· This rule detects suspicious control-plane-to-privileged-access sequencing, not successful exploitation by itself.
· NETCONF and administrative authentication may be legitimate in approved automation, service-provider, and emergency workflows.
· Related-source correlation may be imperfect when attackers rotate infrastructure or use shared cloud, VPN, or provider egress.
· Missing authentication or NETCONF fields can reduce confidence.
· Confirmation requires correlation with peer-state anomalies, unauthorized source context, configuration changes, topology mismatch, or fabric-impact evidence.
Detection Query Pattern
Splunk SPL pattern requiring index validation, source-type validation, authentication-field validation, NETCONF-field validation, lookup validation, related-source correlation validation, timing-window tuning, and environment-specific allowlisting before production deployment.
(
search index=sdwan sourcetype IN ("cisco:sdwan:controller","cisco:sdwan:manager")
(
event_type IN (
"peer_state_change",
"control_connection",
"device_registration",
"unexpected_peer_identity",
"control_plane_event"
)
OR message IN (
"*peer*",
"*control connection*",
"*device registration*",
"*unexpected peer*"
)
)
| eval src_ip=coalesce(src_ip, source_ip, public_ip, remote_ip)
| eval event_category="sdwan_control_plane"
| fields _time src_ip dest host event_category event_type message
)
| append [
search index=auth sourcetype IN ("linux_secure","cisco:sdwan:auth","auth_logs")
(
action="success"
OR outcome="success"
OR message="*authentication success*"
)
| eval src_ip=coalesce(src_ip, source_ip, remote_ip)
| eval user=coalesce(user, username, account)
| eval event_category="admin_authentication"
| fields _time src_ip dest host user event_category action outcome message
]
| append [
search index=netflow
(
dest_port=830
OR dport=830
)
| eval src_ip=coalesce(src_ip, source_ip)
| eval event_category="netconf_access"
| fields _time src_ip dest dest_port dport host event_category
]
| lookup approved_sdwan_peers src_ip OUTPUT approved_peer
| lookup approved_sdwan_admin_sources src_ip OUTPUT approved_admin_source
| lookup approved_netconf_sources src_ip OUTPUT approved_netconf_source
| lookup source_enrichment src_ip OUTPUT src_first_seen, src_geo, src_asn, src_provider_type
| bin _time span=ENV_SDWAN_SEQUENCE_BIN
| stats
values(event_category) as event_categories
values(user) as users
values(src_provider_type) as provider_types
values(src_geo) as geos
values(src_asn) as asns
count as event_count
by _time src_ip dest
| where mvfind(event_categories, "sdwan_control_plane") >= 0
AND (
mvfind(event_categories, "admin_authentication") >= 0
OR mvfind(event_categories, "netconf_access") >= 0
)
| where isnull(approved_peer)
OR approved_peer!="true"
OR isnull(approved_admin_source)
OR approved_admin_source!="true"
OR isnull(approved_netconf_source)
OR approved_netconf_source!="true"
OR src_first_seen>=relative_time(now(), "-7d")
OR provider_types IN ("cloud_hosting","vpn_provider","hosting_provider","unknown_external")
| lookup approved_sdwan_change_windows _time OUTPUT approved_change_context
| where isnull(approved_change_context)
Rule 3
Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity
Rule Format
Splunk SPL correlation search suitable for Enterprise Security, risk-based alerting, or scheduled alerting after configuration-audit source validation, SD-WAN field normalization, change-management lookup validation, asset tagging, and environment-specific tuning.
Detection Purpose
· Detect SD-WAN configuration changes that occur after suspicious control-plane activity, administrative authentication, or NETCONF access.
· Identify possible fabric-impact behavior involving routes, tunnels, policies, certificates, device registration, peer state, or fabric-trust relationships.
· Prioritize configuration changes involving unfamiliar sources, unauthorized users, unexpected peer identity fields, or changes lacking approval context.
· Support investigation of post-access SD-WAN fabric manipulation without treating configuration change alone as proof of compromise.
· This rule does not prove successful exploitation without supporting peering, authentication, NETCONF, topology, or authorization evidence.
Detection Logic
· Identify suspicious SD-WAN control-plane activity, administrative authentication, or NETCONF access.
· Correlate the activity with SD-WAN configuration changes within the same operational window.
· Prioritize changes affecting routes, tunnels, policies, certificates, templates, device registration, peer state, controller relationships, or fabric trust.
· Increase confidence when the actor, source, object changed, or change type does not align with approved administrative workflows.
· Increase confidence when the change lacks a matching change ticket, maintenance window, emergency-access record, automation record, or service-provider record.
· Increase confidence when the configuration change is followed by new traffic-flow patterns, newly reachable destinations, or persistent unfamiliar access.
· Reduce severity for approved maintenance, automation, service-provider activity, controller migration, disaster recovery, policy deployment, and emergency changes.
· Do not classify configuration changes as compromise without source, actor, timing, peer-state, topology, and change-authorization context.
Required Telemetry
· Cisco SD-WAN configuration audit logs.
· Cisco SD-WAN Manager audit logs.
· Cisco SD-WAN Controller logs.
· Authentication logs.
· NETCONF records or network-flow records for TCP port 830.
· Route change events.
· Tunnel change events.
· Policy change events.
· Certificate change events.
· Device-registration events.
· Peer-state events.
· Template or configuration push events.
· Actor.
· Source IP.
· Destination IP.
· Object changed.
· Change type.
· Change outcome.
· Timestamp.
· Approved change-management records.
· Approved automation records.
· Approved service-provider records.
· Approved emergency-access records.
· Topology and peer inventory.
Engineering Implementation Instructions
· Validate Splunk indexes, source types, and field mappings for SD-WAN configuration audit records, Manager audit records, Controller logs, authentication records, NETCONF records, and network-flow data.
· Normalize actor, source IP, object changed, change type, change outcome, peer identity, and timestamp fields.
· Build lookup tables for approved maintenance windows, change tickets, automation jobs, service-provider activity, emergency access, approved peers, and approved administrative sources.
· Correlate configuration changes with suspicious control-plane activity, authentication, and NETCONF access by source, actor, host, peer identity, and time window.
· Tag high-impact configuration objects such as routes, tunnels, policies, templates, certificates, device-registration objects, peer-state objects, and fabric-trust objects.
· Tune suppression logic for approved policy deployments, controller migrations, disaster recovery, provider maintenance, and emergency access.
· Avoid suppressing all configuration changes from automation accounts because automation credentials may be abused after control-plane compromise.
· Use risk-based alerting to elevate changes that follow suspicious peering or NETCONF access and affect fabric-impacting objects.
DRI Assessment
DRI
9.0 / 10
· The rule is behaviorally anchored to configuration change following suspicious control-plane or privileged access activity.
· The rule remains useful if exploit implementation changes but attacker objectives still include SD-WAN fabric manipulation.
· The score is supported by the durability of fabric-impacting configuration changes as observable post-access behavior.
· The score is constrained by legitimate automation, policy deployment, provider maintenance, migrations, and incomplete configuration audit visibility.
TCR Assessment
Operational TCR
8.0 / 10
Full-Telemetry TCR
9.5 / 10
· Operational confidence depends on configuration audit visibility, actor and source normalization, change-management linkage, SD-WAN topology inventory, and correlation with control-plane or privileged-access events.
· Operational confidence is reduced where configuration audit logs are incomplete, automation context is weak, or change-management records lack object-level detail.
· Full-telemetry confidence improves when configuration changes are correlated with suspicious peering, authentication, NETCONF access, network-flow changes, topology mismatch, and post-access fabric impact.
· Under full telemetry conditions, this rule can provide high-confidence evidence of suspicious SD-WAN fabric manipulation, but confirmed exploitation still requires unauthorized access or trust-establishment context.
Limitations
· This rule detects suspicious configuration change after suspicious access, not exploit execution.
· Legitimate policy deployment, route changes, tunnel changes, certificate renewal, service-provider activity, automation, disaster recovery, and emergency changes may overlap with the same behavior.
· Configuration audit records may vary by deployment model, logging configuration, and retention.
· Automation activity may obscure the original actor unless identity and source context are preserved.
· Confirmation requires correlation with suspicious peering, administrative authentication, NETCONF access, topology mismatch, unauthorized source context, or fabric-impact evidence.
Detection Query Pattern
Splunk SPL pattern requiring index validation, source-type validation, configuration-audit validation, actor-field validation, source-field validation, change-management lookup validation, and environment-specific tuning before production deployment.
(
search index=sdwan sourcetype IN ("cisco:sdwan:controller","cisco:sdwan:manager")
(
event_type IN (
"peer_state_change",
"control_connection",
"device_registration",
"unexpected_peer_identity",
"control_plane_event"
)
OR message IN (
"*peer*",
"*control connection*",
"*device registration*",
"*unexpected peer*"
)
)
| eval src_ip=coalesce(src_ip, source_ip, public_ip, remote_ip)
| eval actor=coalesce(user, username, account, actor)
| eval event_category="suspicious_access_context"
| fields _time src_ip actor dest host event_category event_type message
)
| append [
search index=auth sourcetype IN ("linux_secure","cisco:sdwan:auth","auth_logs")
(
action="success"
OR outcome="success"
OR message="*authentication success*"
)
| eval src_ip=coalesce(src_ip, source_ip, remote_ip)
| eval actor=coalesce(user, username, account)
| eval event_category="admin_authentication"
| fields _time src_ip actor dest host event_category action outcome message
]
| append [
search index=netflow
(
dest_port=830
OR dport=830
)
| eval src_ip=coalesce(src_ip, source_ip)
| eval event_category="netconf_access"
| fields _time src_ip dest host event_category dest_port dport
]
| append [
search index=sdwan sourcetype IN ("cisco:sdwan:audit","cisco:sdwan:manager")
(
event_type IN (
"configuration_change",
"policy_change",
"route_change",
"tunnel_change",
"certificate_change",
"template_push",
"device_registration_change",
"fabric_trust_change"
)
OR message IN (
"*configuration*",
"*policy*",
"*route*",
"*tunnel*",
"*certificate*",
"*template*",
"*fabric trust*"
)
)
| eval src_ip=coalesce(src_ip, source_ip, remote_ip)
| eval actor=coalesce(user, username, account, actor)
| eval object_changed=coalesce(object, object_name, target, config_object)
| eval change_type=coalesce(change_type, action, operation)
| eval event_category="sdwan_configuration_change"
| fields _time src_ip actor dest host object_changed change_type event_category event_type message
]
| lookup approved_sdwan_admin_sources src_ip OUTPUT approved_admin_source
| lookup approved_sdwan_change_windows _time OUTPUT approved_change_context
| lookup approved_sdwan_change_records actor object_changed change_type OUTPUT approved_change_record
| bin _time span=ENV_SDWAN_CONFIG_CORRELATION_BIN
| stats
values(event_category) as event_categories
values(actor) as actors
values(object_changed) as objects_changed
values(change_type) as change_types
values(approved_admin_source) as approved_admin_sources
values(approved_change_context) as approved_change_contexts
values(approved_change_record) as approved_change_records
count as event_count
by _time src_ip dest host
| where mvfind(event_categories, "sdwan_configuration_change") >= 0
AND (
mvfind(event_categories, "suspicious_access_context") >= 0
OR mvfind(event_categories, "admin_authentication") >= 0
OR mvfind(event_categories, "netconf_access") >= 0
)
| where mvfind(approved_admin_sources, "true") < 0
OR mvcount(approved_change_contexts)=0
OR mvcount(approved_change_records)=0
Elastic
Detection Viability Assessment
Elastic has three rules for this EXP report.
· Elastic is viable for detecting suspicious Cisco SD-WAN control-plane behavior when SD-WAN Controller logs, Manager logs, authentication records, NETCONF telemetry, configuration audit records, network-flow data, firewall logs, topology inventory, and asset context are ingested and normalized.
· Elastic is strongest where ECS-aligned fields, custom SD-WAN fields, host and network enrichment, approved-peer lookups, administrative-source baselines, and configuration-change context are available.
· Elastic can identify behavioral sequences involving suspicious peering, administrative authentication, NETCONF access, configuration modification, and post-access SD-WAN fabric impact.
· Elastic is not a standalone proof source unless the required Cisco SD-WAN telemetry and configuration context are available.
· Elastic rules should distinguish exposure, suspicious control-plane behavior, privileged management activity, and confirmed fabric-impact activity.
· Elastic detection content should be treated as high-value behavioral correlation coverage for exploited SD-WAN control-plane trust abuse.
Rule 1
Suspicious Cisco SD-WAN Control-Plane or Peer Activity From Unapproved Source
Rule Format
Elastic KQL / EQL-style detection rule suitable for Elastic Security after index validation, ECS field validation, Cisco SD-WAN field mapping, SD-WAN asset tagging, approved-peer enrichment, source-baseline validation, exception-list validation, and environment-specific tuning.
Detection Purpose
· Detect suspicious Cisco SD-WAN control-plane or peer activity from sources that are unknown, newly observed, external, or not approved for SD-WAN peer communication.
· Identify possible unauthorized SD-WAN control-plane trust establishment.
· Prioritize events involving unfamiliar source IPs, unexpected peer identity fields, unusual geographies, unusual ASNs, cloud or VPN egress, or sources not present in approved SD-WAN topology.
· Support investigation of exploited SD-WAN control-plane trust abuse without relying on CVE-string matches, scanner output, advisory references, payload visibility, or exploit-specific indicators.
· This rule does not prove successful exploitation without supporting peer-state, authentication, NETCONF, configuration, topology, or change-management evidence.
Detection Logic
· Identify Cisco SD-WAN Controller or Manager control-plane events involving unknown, unexpected, or unapproved source IP addresses.
· Prioritize events where observed peer identity fields do not match approved SD-WAN inventory.
· Increase confidence when the source is newly observed or associated with cloud, VPN, hosting, unmanaged, unusual geography, or unusual ASN context.
· Increase confidence when the same source is associated with control-connection anomalies, peer-state changes, unexpected device registration, or unexpected peer identity fields.
· Increase confidence when activity is followed by administrative authentication, NETCONF access, or SD-WAN configuration changes.
· Increase confidence when activity occurs outside approved maintenance, migration, disaster-recovery, service-provider, automation, or emergency-access windows.
· Reduce severity for approved peers, known controller relationships, expected edge-device communication, sanctioned service-provider activity, planned topology changes, and documented maintenance activity.
· Do not classify control-plane activity as compromise without corroborating authentication, NETCONF, configuration, topology, or change-management evidence.
Required Telemetry
· Cisco SD-WAN Controller logs.
· Cisco SD-WAN Manager logs.
· Control-connection events.
· Peer-state events.
· Device-registration events.
· Source IP.
· Destination IP.
· Peer type.
· System IP.
· Site ID.
· Domain ID.
· Public IP.
· Device identity.
· Controller relationship.
· Event outcome.
· Timestamp.
· Network-flow telemetry where available.
· Firewall logs where available.
· GeoIP, ASN, VPN, cloud-provider, and hosting-provider enrichment.
· Approved SD-WAN peer inventory.
· Approved administrative and service-provider source networks.
· Maintenance-window and change-management context.
Engineering Implementation Instructions
· Validate Elastic index patterns, data streams, ECS mappings, and custom Cisco SD-WAN fields for Controller, Manager, network-flow, firewall, authentication, NETCONF, and configuration-audit sources.
· Normalize peer identity fields, including source IP, public IP, System IP, site ID, domain ID, peer type, device identity, controller relationship, and event outcome.
· Build indicator match lists, enrich policies, value lists, or exception lists for approved SD-WAN peers, Controllers, Managers, edge devices, service-provider paths, automation sources, emergency-access paths, and administrative networks.
· Add enrichment for first-seen source, geography, ASN, cloud provider, VPN provider, and hosting provider.
· Correlate suspicious control-plane activity with authentication, NETCONF, configuration, and change-management records.
· Tune exceptions for approved maintenance, migration, edge onboarding, disaster recovery, service-provider work, and emergency access.
· Avoid broad exceptions for cloud, VPN, or service-provider sources because attacker and legitimate administrative paths may overlap.
· Use Elastic risk scoring, rule chaining, or event correlation where available to elevate events that combine peer anomalies, authentication success, NETCONF access, and configuration changes.
DRI Assessment
DRI
8.5 / 10
· The rule is behaviorally anchored to suspicious SD-WAN control-plane activity and peer identity mismatch rather than static exploit indicators.
· The rule remains useful if exploit delivery changes but the attacker still needs to interact with SD-WAN control-plane infrastructure.
· The score is supported by durable telemetry relationships across peer identity, source behavior, topology, and timing.
· The score is constrained by incomplete SD-WAN field normalization, incomplete peer inventories, service-provider activity, migrations, and legitimate edge onboarding.
TCR Assessment
Operational TCR
7.5 / 10
Full-Telemetry TCR
9.0 / 10
· Operational confidence depends on Cisco SD-WAN log ingestion, ECS or custom-field normalization, approved-peer baselines, administrative-source baselines, and maintenance-window context.
· Operational confidence is reduced where Controller or Manager logs are incomplete, peer identity fields are not mapped, or service-provider paths are poorly documented.
· Full-telemetry confidence improves when Elastic correlates SD-WAN Controller logs, Manager logs, network-flow records, authentication logs, NETCONF telemetry, configuration audit logs, and change-management data.
· Even under full telemetry conditions, this rule should support investigation unless paired with authentication, NETCONF, or configuration-impact evidence.
Limitations
· This rule detects suspicious control-plane or peering behavior, not successful exploitation by itself.
· Legitimate SD-WAN operations, edge onboarding, controller migration, service-provider activity, and disaster-recovery testing may overlap with the same behavior.
· Incomplete topology inventory can reduce confidence in peer validation.
· Field normalization gaps may reduce detection accuracy.
· Confirmation requires correlation with administrative authentication, NETCONF access, configuration changes, topology mismatch, or unauthorized fabric-impact activity.
Detection Query Pattern
Elastic KQL / EQL-style detection pattern requiring index validation, ECS field validation, Cisco SD-WAN field mapping, approved-peer enrichment validation, source-enrichment validation, exception-list validation, and environment-specific tuning before production deployment.
event.dataset in (
"cisco.sdwan.controller",
"cisco.sdwan.manager"
)
and event.action in (
"peer_state_change",
"control_connection",
"device_registration",
"peer_identity",
"control_plane_event"
)
and (
sdwan.enrichment.peer_approval_status : "unapproved"
or sdwan.enrichment.peer_approval_status : "unknown"
or sdwan.enrichment.admin_source_status : "unapproved"
or sdwan.enrichment.admin_source_status : "unknown"
or sdwan.enrichment.peer_identity_match : "false"
or sdwan.enrichment.topology_match : "false"
or sdwan.enrichment.source_first_seen_within : "ENV_NEW_SOURCE_WINDOW"
or source.as.organization.name in $ENV_UNUSUAL_OR_UNAPPROVED_ASNS
or source.geo.country_iso_code not in $ENV_APPROVED_SDWAN_ADMIN_GEOS
or source.provider_type in (
"cloud_hosting",
"vpn_provider",
"hosting_provider",
"unknown_external"
)
)
and not labels.change_context in (
"approved_sdwan_maintenance",
"approved_controller_migration",
"approved_edge_onboarding",
"approved_disaster_recovery",
"approved_service_provider_activity",
"approved_emergency_access"
)
Rule 2
Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication
Rule Format
Elastic EQL sequence rule suitable for Elastic Security after index validation, ECS field validation, SD-WAN field mapping, authentication-source validation, NETCONF-source validation, sequence-window tuning, exception-list validation, and environment-specific tuning.
Detection Purpose
· Detect suspicious sequencing where Cisco SD-WAN control-plane activity is followed by NETCONF access or administrative authentication.
· Identify behavior consistent with progression from control-plane interaction to privileged SD-WAN management activity.
· Prioritize sources that are unfamiliar, newly observed, external, unauthorized, or not aligned with approved administrative workflows.
· Support investigation of potential SD-WAN control-plane trust abuse without relying on encrypted payload inspection.
· This rule does not prove successful exploitation or configuration manipulation without supporting controller-side, authentication, NETCONF, configuration-audit, topology, or change-management evidence.
Detection Logic
· Identify suspicious SD-WAN control-plane or peer-state activity involving an unknown or unapproved source.
· Correlate the source or related source with successful administrative authentication or NETCONF access within the same operational window.
· Increase confidence when the source is newly observed, external, cloud-hosted, VPN-associated, hosting-provider-associated, or not part of approved administrative source lists.
· Increase confidence when the sequence occurs near peer-state changes, control-connection instability, device-registration activity, or unexpected peer identity fields.
· Increase confidence when NETCONF or authentication activity occurs outside approved maintenance, automation, service-provider, or emergency-access windows.
· Increase confidence when the sequence is followed by configuration audit activity.
· Reduce severity for approved automation, approved NETCONF management workflows, service-provider maintenance, planned migration, and documented emergency access.
· Do not classify NETCONF or administrative authentication as malicious without source, identity, timing, peer-state, topology, and configuration-change context.
Required Telemetry
· Cisco SD-WAN Controller logs.
· Cisco SD-WAN Manager logs.
· Authentication logs.
· NETCONF records or network-flow records for TCP port 830.
· Source IP.
· Destination IP.
· Username.
· Authentication method.
· Authentication outcome.
· NETCONF source.
· NETCONF destination.
· Peer-state context.
· Control-connection context.
· Device-registration context.
· Timestamp.
· Approved NETCONF source list.
· Approved SD-WAN administrative source networks.
· Approved peer and controller inventories.
· GeoIP, ASN, cloud-provider, VPN-provider, hosting-provider, and first-seen enrichment.
· Maintenance-window, automation, service-provider, and change-management context.
Engineering Implementation Instructions
· Validate Elastic index patterns, data streams, ECS fields, and custom mappings for SD-WAN Controller, Manager, authentication, NETCONF, network-flow, and configuration-audit telemetry.
· Normalize source IP, destination IP, username, authentication outcome, NETCONF destination, peer identity fields, and timestamps.
· Build indicator match lists, enrich policies, value lists, or exception lists for approved SD-WAN peers, approved administrative sources, approved NETCONF sources, automation sources, service-provider sources, and emergency-access paths.
· Correlate suspicious control-plane events with NETCONF and authentication events by source IP, related source IP, subnet, ASN, VPN provider, cloud provider, or infrastructure cluster.
· Tune sequence windows around normal SD-WAN administrative workflows and emergency-access procedures.
· Add exception logic for approved maintenance, automation, service-provider operations, disaster recovery, controller migration, and emergency access.
· Avoid suppressing all NETCONF or administrative activity from broad infrastructure categories because attackers may use cloud, VPN, or provider egress.
· Use Elastic risk score adjustment or chained detections to increase severity when the sequence is followed by configuration change or fabric-impact activity.
DRI Assessment
DRI
9.0 / 10
· The rule is behaviorally anchored to a durable progression from suspicious control-plane activity to privileged access.
· The rule remains useful if the exploit implementation changes but the attacker proceeds from control-plane interaction to administrative or NETCONF activity.
· The score is supported by the operational significance of NETCONF access or authentication following suspicious peering or peer-state activity.
· The score is constrained by legitimate automation, provider maintenance, emergency access, and incomplete NETCONF or authentication telemetry.
TCR Assessment
Operational TCR
8.0 / 10
Full-Telemetry TCR
9.5 / 10
· Operational confidence depends on reliable SD-WAN log ingestion, authentication visibility, NETCONF visibility, correlation timing, and approved administrative workflow documentation.
· Operational confidence is reduced where NETCONF records are unavailable, authentication logs lack source IP context, or approved source lists are incomplete.
· Full-telemetry confidence improves when the sequence is correlated with configuration audit records, peer-state changes, topology mismatch, and change-management context.
· Under full telemetry conditions, this rule provides strong suspicious-activity coverage, but confirmed exploitation still requires evidence of unauthorized peer status, configuration impact, or fabric change.
Limitations
· This rule detects suspicious control-plane-to-privileged-access sequencing, not successful exploitation by itself.
· NETCONF and administrative authentication may be legitimate in approved automation, service-provider, and emergency workflows.
· Related-source correlation may be imperfect when attackers rotate infrastructure or use shared cloud, VPN, or provider egress.
· Missing authentication or NETCONF fields can reduce confidence.
· Confirmation requires correlation with peer-state anomalies, unauthorized source context, configuration changes, topology mismatch, or fabric-impact evidence.
Detection Query Pattern
Elastic EQL-style sequence pattern requiring index validation, ECS field validation, Cisco SD-WAN field mapping, authentication-field validation, NETCONF-field validation, enrichment validation, sequence-window tuning, exception-list validation, and environment-specific allowlisting before production deployment.
sequence by source.ip with maxspan=ENV_SDWAN_SEQUENCE_WINDOW
[ any where
event.dataset in (
"cisco.sdwan.controller",
"cisco.sdwan.manager"
)
and event.action in (
"peer_state_change",
"control_connection",
"device_registration",
"unexpected_peer_identity",
"control_plane_event"
)
and (
sdwan.enrichment.peer_approval_status in (
"unapproved",
"unknown"
)
or sdwan.enrichment.peer_identity_match : "false"
or sdwan.enrichment.topology_match : "false"
or sdwan.enrichment.source_first_seen_within : "ENV_NEW_SOURCE_WINDOW"
or source.provider_type in (
"cloud_hosting",
"vpn_provider",
"hosting_provider",
"unknown_external"
)
or source.geo.country_iso_code not in $ENV_APPROVED_SDWAN_ADMIN_GEOS
)
]
[ any where
(
(
event.category : "authentication"
and event.outcome : "success"
and sdwan.enrichment.admin_source_status in (
"unapproved",
"unknown"
)
)
or
(
network.transport : "tcp"
and destination.port : 830
and sdwan.enrichment.netconf_source_status in (
"unapproved",
"unknown"
)
)
)
and not labels.change_context in (
"approved_sdwan_maintenance",
"approved_netconf_automation",
"approved_service_provider_activity",
"approved_emergency_access",
"approved_controller_migration"
)
]
Rule 3
Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity
Rule Format
Elastic EQL / KQL-style correlation rule suitable for Elastic Security after configuration-audit source validation, SD-WAN field normalization, change-management enrichment validation, asset tagging, sequence-window tuning, exception-list validation, and environment-specific tuning.
Detection Purpose
· Detect SD-WAN configuration changes that occur after suspicious control-plane activity, administrative authentication, or NETCONF access.
· Identify possible fabric-impact behavior involving routes, tunnels, policies, certificates, device registration, peer state, or fabric-trust relationships.
· Prioritize configuration changes involving unfamiliar sources, unauthorized users, unexpected peer identity fields, or changes lacking approval context.
· Support investigation of post-access SD-WAN fabric manipulation without treating configuration change alone as proof of compromise.
· This rule does not prove successful exploitation without supporting peering, authentication, NETCONF, topology, or authorization evidence.
Detection Logic
· Identify suspicious SD-WAN control-plane activity, administrative authentication, or NETCONF access.
· Correlate the activity with SD-WAN configuration changes within the same operational window.
· Prioritize changes affecting routes, tunnels, policies, certificates, templates, device registration, peer state, controller relationships, or fabric trust.
· Increase confidence when the actor, source, object changed, or change type does not align with approved administrative workflows.
· Increase confidence when the change lacks a matching change ticket, maintenance window, emergency-access record, automation record, or service-provider record.
· Increase confidence when the configuration change is followed by new traffic-flow patterns, newly reachable destinations, or persistent unfamiliar access.
· Reduce severity for approved maintenance, automation, service-provider activity, controller migration, disaster recovery, policy deployment, and emergency changes.
· Do not classify configuration changes as compromise without source, actor, timing, peer-state, topology, and change-authorization context.
Required Telemetry
· Cisco SD-WAN configuration audit logs.
· Cisco SD-WAN Manager audit logs.
· Cisco SD-WAN Controller logs.
· Authentication logs.
· NETCONF records or network-flow records for TCP port 830.
· Route change events.
· Tunnel change events.
· Policy change events.
· Certificate change events.
· Device-registration events.
· Peer-state events.
· Template or configuration push events.
· Actor.
· Source IP.
· Destination IP.
· Object changed.
· Change type.
· Change outcome.
· Timestamp.
· Approved change-management records.
· Approved automation records.
· Approved service-provider records.
· Approved emergency-access records.
· Topology and peer inventory.
Engineering Implementation Instructions
· Validate Elastic index patterns, data streams, ECS fields, and custom mappings for SD-WAN configuration audit records, Manager audit records, Controller logs, authentication records, NETCONF records, and network-flow data.
· Normalize actor, source IP, object changed, change type, change outcome, peer identity, and timestamp fields.
· Build enrich policies, indicator match lists, value lists, or exception lists for approved maintenance windows, change tickets, automation jobs, service-provider activity, emergency access, approved peers, and approved administrative sources.
· Correlate configuration changes with suspicious control-plane activity, authentication, and NETCONF access by source, actor, host, peer identity, and time window.
· Tag high-impact configuration objects such as routes, tunnels, policies, templates, certificates, device-registration objects, peer-state objects, and fabric-trust objects.
· Tune exception logic for approved policy deployments, controller migrations, disaster recovery, provider maintenance, and emergency access.
· Avoid suppressing all configuration changes from automation accounts because automation credentials may be abused after control-plane compromise.
· Use Elastic risk score adjustment or chained detections to elevate changes that follow suspicious peering or NETCONF access and affect fabric-impacting objects.
DRI Assessment
DRI
9.0 / 10
· The rule is behaviorally anchored to configuration change following suspicious control-plane or privileged access activity.
· The rule remains useful if exploit implementation changes but attacker objectives still include SD-WAN fabric manipulation.
· The score is supported by the durability of fabric-impacting configuration changes as observable post-access behavior.
· The score is constrained by legitimate automation, policy deployment, provider maintenance, migrations, and incomplete configuration audit visibility.
TCR Assessment
Operational TCR
8.0 / 10
Full-Telemetry TCR
9.5 / 10
· Operational confidence depends on configuration audit visibility, actor and source normalization, change-management linkage, SD-WAN topology inventory, and correlation with control-plane or privileged-access events.
· Operational confidence is reduced where configuration audit logs are incomplete, automation context is weak, or change-management records lack object-level detail.
· Full-telemetry confidence improves when configuration changes are correlated with suspicious peering, authentication, NETCONF access, network-flow changes, topology mismatch, and post-access fabric impact.
· Under full telemetry conditions, this rule can provide high-confidence evidence of suspicious SD-WAN fabric manipulation, but confirmed exploitation still requires unauthorized access or trust-establishment context.
Limitations
· This rule detects suspicious configuration change after suspicious access, not exploit execution.
· Legitimate policy deployment, route changes, tunnel changes, certificate renewal, service-provider activity, automation, disaster recovery, and emergency changes may overlap with the same behavior.
· Configuration audit records may vary by deployment model, logging configuration, and retention.
· Automation activity may obscure the original actor unless identity and source context are preserved.
· Confirmation requires correlation with suspicious peering, administrative authentication, NETCONF access, topology mismatch, unauthorized source context, or fabric-impact evidence.
Detection Query Pattern
Elastic EQL-style sequence pattern requiring index validation, ECS field validation, configuration-audit validation, actor-field validation, source-field validation, change-management enrichment validation, exception-list validation, and environment-specific tuning before production deployment.
sequence by source.ip with maxspan=ENV_SDWAN_CONFIG_CORRELATION_WINDOW
[ any where
(
(
event.dataset in (
"cisco.sdwan.controller",
"cisco.sdwan.manager"
)
and event.action in (
"peer_state_change",
"control_connection",
"device_registration",
"unexpected_peer_identity",
"control_plane_event"
)
and (
sdwan.enrichment.peer_approval_status in (
"unapproved",
"unknown"
)
or sdwan.enrichment.peer_identity_match : "false"
or sdwan.enrichment.topology_match : "false"
)
)
or
(
event.category : "authentication"
and event.outcome : "success"
and sdwan.enrichment.admin_source_status in (
"unapproved",
"unknown"
)
)
or
(
network.transport : "tcp"
and destination.port : 830
and sdwan.enrichment.netconf_source_status in (
"unapproved",
"unknown"
)
)
)
]
[ any where
event.dataset in (
"cisco.sdwan.audit",
"cisco.sdwan.manager"
)
and event.action in (
"configuration_change",
"policy_change",
"route_change",
"tunnel_change",
"certificate_change",
"template_push",
"device_registration_change",
"fabric_trust_change"
)
and cisco.sdwan.change.object.type in (
"route",
"tunnel",
"policy",
"certificate",
"template",
"device_registration",
"peer_state",
"fabric_trust"
)
and (
sdwan.enrichment.change_approval_status in (
"unapproved",
"unknown",
"missing"
)
or sdwan.enrichment.actor_approval_status in (
"unapproved",
"unknown"
)
or sdwan.enrichment.admin_source_status in (
"unapproved",
"unknown"
)
)
]
QRadar
Detection Viability Assessment
QRadar has three rules for this EXP report.
· QRadar is viable for detecting suspicious Cisco SD-WAN control-plane behavior when SD-WAN Controller logs, Manager logs, authentication records, NETCONF telemetry, configuration audit records, network-flow data, firewall logs, topology inventory, and change-management context are ingested and parsed.
· QRadar is strongest where DSM parsing, custom properties, reference sets, building blocks, asset profiles, flow telemetry, offense rules, and SD-WAN-specific enrichment are available.
· QRadar can identify behavioral sequences involving suspicious peering, administrative authentication, NETCONF access, configuration modification, and post-access SD-WAN fabric impact.
· QRadar is not a standalone proof source unless the required Cisco SD-WAN telemetry and configuration context are available.
· QRadar rules should distinguish exposure, suspicious control-plane behavior, privileged management activity, and confirmed fabric-impact activity.
· QRadar detection content should be treated as high-value correlation coverage for exploited SD-WAN control-plane trust abuse.
Rule 1
Suspicious Cisco SD-WAN Control-Plane or Peer Activity From Unapproved Source
Rule Format
QRadar correlation rule suitable for offense generation after DSM validation, custom property extraction, SD-WAN asset tagging, reference-set validation, flow-source validation, approved-peer baselining, and environment-specific tuning.
Detection Purpose
· Detect suspicious Cisco SD-WAN control-plane or peer activity from sources that are unknown, newly observed, external, or not approved for SD-WAN peer communication.
· Identify possible unauthorized SD-WAN control-plane trust establishment.
· Prioritize events involving unfamiliar source IPs, unexpected peer identity fields, unusual geographies, unusual ASNs, cloud or VPN egress, or sources not present in approved SD-WAN topology.
· Support investigation of exploited SD-WAN control-plane trust abuse without relying on CVE-string matches, scanner output, advisory references, payload visibility, or exploit-specific indicators.
· This rule does not prove successful exploitation without supporting peer-state, authentication, NETCONF, configuration, topology, or change-management evidence.
Detection Logic
· Identify Cisco SD-WAN Controller or Manager control-plane events involving unknown, unexpected, or unapproved source IP addresses.
· Prioritize events where observed peer identity fields do not match approved SD-WAN inventory.
· Increase confidence when the source is newly observed or associated with cloud, VPN, hosting, unmanaged, unusual geography, or unusual ASN context.
· Increase confidence when the same source is associated with control-connection anomalies, peer-state changes, unexpected device registration, or unexpected peer identity fields.
· Increase confidence when activity is followed by administrative authentication, NETCONF access, or SD-WAN configuration changes.
· Increase confidence when activity occurs outside approved maintenance, migration, disaster-recovery, service-provider, automation, or emergency-access windows.
· Reduce severity for approved peers, known controller relationships, expected edge-device communication, sanctioned service-provider activity, planned topology changes, and documented maintenance activity.
· Do not classify control-plane activity as compromise without corroborating authentication, NETCONF, configuration, topology, or change-management evidence.
Required Telemetry
· Cisco SD-WAN Controller logs.
· Cisco SD-WAN Manager logs.
· Control-connection events.
· Peer-state events.
· Device-registration events.
· Source IP.
· Destination IP.
· Peer type.
· System IP.
· Site ID.
· Domain ID.
· Public IP.
· Device identity.
· Controller relationship.
· Event outcome.
· Timestamp.
· QRadar flow telemetry where available.
· Firewall logs where available.
· GeoIP, ASN, VPN, cloud-provider, and hosting-provider enrichment.
· Approved SD-WAN peer reference sets.
· Approved administrative and service-provider source reference sets.
· Maintenance-window and change-management context.
Engineering Implementation Instructions
· Validate QRadar log sources, DSM parsing, event names, QIDs, custom properties, and flow sources for Cisco SD-WAN Controller, Manager, authentication, NETCONF, network-flow, firewall, and configuration-audit telemetry.
· Extract custom properties for source IP, public IP, System IP, site ID, domain ID, peer type, device identity, controller relationship, event outcome, object changed, change type, and username.
· Build reference sets for approved SD-WAN peers, Controllers, Managers, edge devices, NETCONF sources, service-provider paths, automation sources, emergency-access paths, and administrative networks.
· Add enrichment for first-seen source, geography, ASN, cloud provider, VPN provider, and hosting provider where available.
· Correlate suspicious control-plane activity with authentication, NETCONF, configuration, and change-management records.
· Tune rule response and offense creation for approved maintenance, migration, edge onboarding, disaster recovery, service-provider work, and emergency access.
· Avoid broad suppression for cloud, VPN, or service-provider sources because attacker and legitimate administrative paths may overlap.
· Use QRadar offense magnitude, building blocks, and rule chaining where available to elevate events that combine peer anomalies, authentication success, NETCONF access, and configuration changes.
DRI Assessment
DRI
8.5 / 10
· The rule is behaviorally anchored to suspicious SD-WAN control-plane activity and peer identity mismatch rather than static exploit indicators.
· The rule remains useful if exploit delivery changes but the attacker still needs to interact with SD-WAN control-plane infrastructure.
· The score is supported by durable telemetry relationships across peer identity, source behavior, topology, and timing.
· The score is constrained by incomplete DSM parsing, incomplete custom-property extraction, incomplete peer inventories, service-provider activity, migrations, and legitimate edge onboarding.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
9.0 / 10
· Operational confidence depends on Cisco SD-WAN log ingestion, DSM parsing quality, custom-property extraction, approved-peer reference sets, administrative-source baselines, and maintenance-window context.
· Operational confidence is reduced where Controller or Manager logs are incomplete, peer identity fields are not extracted, or service-provider paths are poorly documented.
· Full-telemetry confidence improves when QRadar correlates SD-WAN Controller logs, Manager logs, flow records, authentication logs, NETCONF telemetry, configuration audit logs, and change-management data.
· Even under full telemetry conditions, this rule should support investigation unless paired with authentication, NETCONF, or configuration-impact evidence.
Limitations
· This rule detects suspicious control-plane or peering behavior, not successful exploitation by itself.
· Legitimate SD-WAN operations, edge onboarding, controller migration, service-provider activity, and disaster-recovery testing may overlap with the same behavior.
· Incomplete topology inventory can reduce confidence in peer validation.
· DSM parsing or custom-property gaps may reduce detection accuracy.
· Confirmation requires correlation with administrative authentication, NETCONF access, configuration changes, topology mismatch, or unauthorized fabric-impact activity.
Detection Query Pattern
QRadar AQL-style detection pattern requiring DSM validation, custom-property validation, reference-set validation, flow-source validation, source-enrichment validation, and environment-specific tuning before production deployment.
SELECT
sourceip,
destinationip,
LOGSOURCENAME(logsourceid) AS log_source,
QIDNAME(qid) AS event_name,
"Peer Type" AS peer_type,
"System IP" AS system_ip,
"Site ID" AS site_id,
"Domain ID" AS domain_id,
"Device Identity" AS device_identity,
"Controller Relationship" AS controller_relationship,
COUNT(*) AS event_count,
MIN(starttime) AS first_seen,
MAX(starttime) AS last_seen
FROM events
WHERE LOGSOURCENAME(logsourceid) IN (
'Cisco SD-WAN Controller',
'Cisco SD-WAN Manager'
)
AND (
QIDNAME(qid) ILIKE '%peer%'
OR QIDNAME(qid) ILIKE '%control connection%'
OR QIDNAME(qid) ILIKE '%device registration%'
OR QIDNAME(qid) ILIKE '%control plane%'
OR "Event Type" IN (
'peer_state_change',
'control_connection',
'device_registration',
'peer_identity',
'control_plane_event'
)
)
AND (
"Peer Approval Status" IN (
'unapproved',
'unknown'
)
OR "Peer Identity Match" = 'false'
OR "Topology Match" = 'false'
OR "Source Approval Status" IN (
'unapproved',
'unknown'
)
OR "Source Provider Type" IN (
'cloud_hosting',
'vpn_provider',
'hosting_provider',
'unknown_external'
)
OR "Source Geo Approval Status" IN (
'unapproved',
'unknown'
)
)
AND NOT "Change Context" IN (
'approved_sdwan_maintenance',
'approved_controller_migration',
'approved_edge_onboarding',
'approved_disaster_recovery',
'approved_service_provider_activity',
'approved_emergency_access'
)
GROUP BY
sourceip,
destinationip,
logsourceid,
qid,
"Peer Type",
"System IP",
"Site ID",
"Domain ID",
"Device Identity",
"Controller Relationship"
HAVING event_count >= ENV_SDWAN_CONTROL_PLANE_EVENT_THRESHOLD
Rule 2
Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication
Rule Format
QRadar correlation rule suitable for offense generation after DSM validation, custom property extraction, flow-source validation, reference-set validation, sequence-window validation, building-block validation, and environment-specific tuning.
Detection Purpose
· Detect suspicious sequencing where Cisco SD-WAN control-plane activity is followed by NETCONF access or administrative authentication.
· Identify behavior consistent with progression from control-plane interaction to privileged SD-WAN management activity.
· Prioritize sources that are unfamiliar, newly observed, external, unauthorized, or not aligned with approved administrative workflows.
· Support investigation of potential SD-WAN control-plane trust abuse without relying on encrypted payload inspection.
· This rule does not prove successful exploitation or configuration manipulation without supporting controller-side, authentication, NETCONF, configuration-audit, topology, or change-management evidence.
Detection Logic
· Identify suspicious SD-WAN control-plane or peer-state activity involving an unknown or unapproved source.
· Correlate the source or related source with successful administrative authentication or NETCONF access within the same operational window.
· Increase confidence when the source is newly observed, external, cloud-hosted, VPN-associated, hosting-provider-associated, or not part of approved administrative source reference sets.
· Increase confidence when the sequence occurs near peer-state changes, control-connection instability, device-registration activity, or unexpected peer identity fields.
· Increase confidence when NETCONF or authentication activity occurs outside approved maintenance, automation, service-provider, or emergency-access windows.
· Increase confidence when the sequence is followed by configuration audit activity.
· Reduce severity for approved automation, approved NETCONF management workflows, service-provider maintenance, planned migration, and documented emergency access.
· Do not classify NETCONF or administrative authentication as malicious without source, identity, timing, peer-state, topology, and configuration-change context.
Required Telemetry
· Cisco SD-WAN Controller logs.
· Cisco SD-WAN Manager logs.
· Authentication logs.
· NETCONF records or QRadar flow records for TCP port 830.
· Source IP.
· Destination IP.
· Username.
· Authentication method.
· Authentication outcome.
· NETCONF source.
· NETCONF destination.
· Peer-state context.
· Control-connection context.
· Device-registration context.
· Timestamp.
· Approved NETCONF source reference set.
· Approved SD-WAN administrative source reference set.
· Approved peer and controller reference sets.
· GeoIP, ASN, cloud-provider, VPN-provider, hosting-provider, and first-seen enrichment.
· Maintenance-window, automation, service-provider, and change-management context.
Engineering Implementation Instructions
· Validate QRadar log sources, DSM parsing, event names, QIDs, custom properties, and flow sources for SD-WAN Controller, Manager, authentication, NETCONF, network-flow, and configuration-audit telemetry.
· Normalize source IP, destination IP, username, authentication outcome, NETCONF destination, peer identity fields, and timestamps into usable QRadar properties.
· Build reference sets for approved SD-WAN peers, approved administrative sources, approved NETCONF sources, automation sources, service-provider sources, and emergency-access paths.
· Correlate suspicious control-plane events with NETCONF and authentication events by source IP, related source IP, subnet, ASN, VPN provider, cloud provider, or infrastructure cluster.
· Tune sequence windows around normal SD-WAN administrative workflows and emergency-access procedures.
· Add rule tests or building blocks for approved maintenance, automation, service-provider operations, disaster recovery, controller migration, and emergency access.
· Avoid suppressing all NETCONF or administrative activity from broad infrastructure categories because attackers may use cloud, VPN, or provider egress.
· Use QRadar building blocks and offense magnitude to increase severity when the sequence is followed by configuration change or fabric-impact activity.
DRI Assessment
DRI
9.0 / 10
· The rule is behaviorally anchored to a durable progression from suspicious control-plane activity to privileged access.
· The rule remains useful if the exploit implementation changes but the attacker proceeds from control-plane interaction to administrative or NETCONF activity.
· The score is supported by the operational significance of NETCONF access or authentication following suspicious peering or peer-state activity.
· The score is constrained by legitimate automation, provider maintenance, emergency access, incomplete NETCONF visibility, and incomplete authentication telemetry.
TCR Assessment
Operational TCR
7.5 / 10
Full-Telemetry TCR
9.5 / 10
· Operational confidence depends on reliable SD-WAN log ingestion, authentication visibility, NETCONF visibility, QRadar flow visibility, sequence timing, and approved administrative workflow documentation.
· Operational confidence is reduced where NETCONF records are unavailable, authentication logs lack source IP context, or approved source reference sets are incomplete.
· Full-telemetry confidence improves when the sequence is correlated with configuration audit records, peer-state changes, topology mismatch, and change-management context.
· Under full telemetry conditions, this rule provides strong suspicious-activity coverage, but confirmed exploitation still requires evidence of unauthorized peer status, configuration impact, or fabric change.
Limitations
· This rule detects suspicious control-plane-to-privileged-access sequencing, not successful exploitation by itself.
· NETCONF and administrative authentication may be legitimate in approved automation, service-provider, and emergency workflows.
· Related-source correlation may be imperfect when attackers rotate infrastructure or use shared cloud, VPN, or provider egress.
· Missing authentication, NETCONF, or flow fields can reduce confidence.
· Confirmation requires correlation with peer-state anomalies, unauthorized source context, configuration changes, topology mismatch, or fabric-impact evidence.
Detection Query Pattern
QRadar AQL-style sequence pattern requiring DSM validation, custom-property validation, authentication-field validation, NETCONF-flow validation, reference-set validation, timing-window tuning, and environment-specific allowlisting before production deployment.
SELECT
sourceip,
destinationip,
username,
COUNT(*) AS event_count,
MIN(starttime) AS first_seen,
MAX(starttime) AS last_seen,
UNIQUECOUNT("Event Category") AS category_count
FROM events
WHERE (
(
LOGSOURCENAME(logsourceid) IN (
'Cisco SD-WAN Controller',
'Cisco SD-WAN Manager'
)
AND (
QIDNAME(qid) ILIKE '%peer%'
OR QIDNAME(qid) ILIKE '%control connection%'
OR QIDNAME(qid) ILIKE '%device registration%'
OR QIDNAME(qid) ILIKE '%unexpected peer%'
OR "Event Type" IN (
'peer_state_change',
'control_connection',
'device_registration',
'unexpected_peer_identity',
'control_plane_event'
)
)
AND (
"Peer Approval Status" IN (
'unapproved',
'unknown'
)
OR "Peer Identity Match" = 'false'
OR "Topology Match" = 'false'
)
)
OR (
"Event Category" = 'admin_authentication'
AND "Authentication Outcome" = 'success'
AND "Admin Source Approval Status" IN (
'unapproved',
'unknown'
)
)
OR (
"Event Category" = 'netconf_access'
AND destinationport = 830
AND "NETCONF Source Approval Status" IN (
'unapproved',
'unknown'
)
)
)
AND NOT "Change Context" IN (
'approved_sdwan_maintenance',
'approved_netconf_automation',
'approved_service_provider_activity',
'approved_emergency_access',
'approved_controller_migration'
)
GROUP BY
sourceip,
destinationip,
username
HAVING category_count >= 2
AND last_seen - first_seen <= ENV_SDWAN_SEQUENCE_WINDOW
Rule 3
Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity
Rule Format
QRadar correlation rule suitable for offense generation after configuration-audit source validation, DSM validation, custom property extraction, change-management reference-set validation, SD-WAN asset tagging, building-block validation, and environment-specific tuning.
Detection Purpose
· Detect SD-WAN configuration changes that occur after suspicious control-plane activity, administrative authentication, or NETCONF access.
· Identify possible fabric-impact behavior involving routes, tunnels, policies, certificates, device registration, peer state, or fabric-trust relationships.
· Prioritize configuration changes involving unfamiliar sources, unauthorized users, unexpected peer identity fields, or changes lacking approval context.
· Support investigation of post-access SD-WAN fabric manipulation without treating configuration change alone as proof of compromise.
· This rule does not prove successful exploitation without supporting peering, authentication, NETCONF, topology, or authorization evidence.
Detection Logic
· Identify suspicious SD-WAN control-plane activity, administrative authentication, or NETCONF access.
· Correlate the activity with SD-WAN configuration changes within the same operational window.
· Prioritize changes affecting routes, tunnels, policies, certificates, templates, device registration, peer state, controller relationships, or fabric trust.
· Increase confidence when the actor, source, object changed, or change type does not align with approved administrative workflows.
· Increase confidence when the change lacks a matching change ticket, maintenance window, emergency-access record, automation record, or service-provider record.
· Increase confidence when the configuration change is followed by new traffic-flow patterns, newly reachable destinations, or persistent unfamiliar access.
· Reduce severity for approved maintenance, automation, service-provider activity, controller migration, disaster recovery, policy deployment, and emergency changes.
· Do not classify configuration changes as compromise without source, actor, timing, peer-state, topology, and change-authorization context.
Required Telemetry
· Cisco SD-WAN configuration audit logs.
· Cisco SD-WAN Manager audit logs.
· Cisco SD-WAN Controller logs.
· Authentication logs.
· NETCONF records or QRadar flow records for TCP port 830.
· Route change events.
· Tunnel change events.
· Policy change events.
· Certificate change events.
· Device-registration events.
· Peer-state events.
· Template or configuration push events.
· Actor.
· Source IP.
· Destination IP.
· Object changed.
· Change type.
· Change outcome.
· Timestamp.
· Approved change-management records.
· Approved automation records.
· Approved service-provider records.
· Approved emergency-access records.
· Topology and peer inventory.
Engineering Implementation Instructions
· Validate QRadar log sources, DSM parsing, event names, QIDs, custom properties, and flow sources for SD-WAN configuration audit records, Manager audit records, Controller logs, authentication records, NETCONF records, and network-flow data.
· Normalize actor, source IP, object changed, change type, change outcome, peer identity, and timestamp fields into QRadar custom properties.
· Build reference sets or building blocks for approved maintenance windows, change tickets, automation jobs, service-provider activity, emergency access, approved peers, and approved administrative sources.
· Correlate configuration changes with suspicious control-plane activity, authentication, and NETCONF access by source, actor, host, peer identity, and time window.
· Tag high-impact configuration objects such as routes, tunnels, policies, templates, certificates, device-registration objects, peer-state objects, and fabric-trust objects.
· Tune rule tests for approved policy deployments, controller migrations, disaster recovery, provider maintenance, and emergency access.
· Avoid suppressing all configuration changes from automation accounts because automation credentials may be abused after control-plane compromise.
· Use QRadar offense magnitude, building blocks, and follow-on flow evidence to elevate changes that follow suspicious peering or NETCONF access and affect fabric-impacting objects.
DRI Assessment
DRI
9.0 / 10
· The rule is behaviorally anchored to configuration change following suspicious control-plane or privileged access activity.
· The rule remains useful if exploit implementation changes but attacker objectives still include SD-WAN fabric manipulation.
· The score is supported by the durability of fabric-impacting configuration changes as observable post-access behavior.
· The score is constrained by legitimate automation, policy deployment, provider maintenance, migrations, and incomplete configuration audit visibility.
TCR Assessment
Operational TCR
7.5 / 10
Full-Telemetry TCR
9.5 / 10
· Operational confidence depends on configuration audit visibility, actor and source normalization, change-management linkage, SD-WAN topology inventory, and correlation with control-plane or privileged-access events.
· Operational confidence is reduced where configuration audit logs are incomplete, automation context is weak, or change-management records lack object-level detail.
· Full-telemetry confidence improves when configuration changes are correlated with suspicious peering, authentication, NETCONF access, network-flow changes, topology mismatch, and post-access fabric impact.
· Under full telemetry conditions, this rule can provide high-confidence evidence of suspicious SD-WAN fabric manipulation, but confirmed exploitation still requires unauthorized access or trust-establishment context.
Limitations
· This rule detects suspicious configuration change after suspicious access, not exploit execution.
· Legitimate policy deployment, route changes, tunnel changes, certificate renewal, service-provider activity, automation, disaster recovery, and emergency changes may overlap with the same behavior.
· Configuration audit records may vary by deployment model, logging configuration, and retention.
· Automation activity may obscure the original actor unless identity and source context are preserved.
· Confirmation requires correlation with suspicious peering, administrative authentication, NETCONF access, topology mismatch, unauthorized source context, or fabric-impact evidence.
Detection Query Pattern
QRadar AQL-style correlation pattern requiring configuration-audit validation, DSM validation, custom-property validation, change-management reference-set validation, source-field validation, timing-window tuning, and environment-specific allowlisting before production deployment.
SELECT
sourceip,
destinationip,
username,
"Object Changed" AS object_changed,
"Change Type" AS change_type,
COUNT(*) AS event_count,
MIN(starttime) AS first_seen,
MAX(starttime) AS last_seen,
UNIQUECOUNT("Event Category") AS category_count
FROM events
WHERE (
(
LOGSOURCENAME(logsourceid) IN (
'Cisco SD-WAN Controller',
'Cisco SD-WAN Manager'
)
AND (
QIDNAME(qid) ILIKE '%peer%'
OR QIDNAME(qid) ILIKE '%control connection%'
OR QIDNAME(qid) ILIKE '%device registration%'
OR "Event Type" IN (
'peer_state_change',
'control_connection',
'device_registration',
'unexpected_peer_identity',
'control_plane_event'
)
)
AND (
"Peer Approval Status" IN (
'unapproved',
'unknown'
)
OR "Peer Identity Match" = 'false'
OR "Topology Match" = 'false'
)
)
OR (
"Event Category" = 'admin_authentication'
AND "Authentication Outcome" = 'success'
AND "Admin Source Approval Status" IN (
'unapproved',
'unknown'
)
)
OR (
"Event Category" = 'netconf_access'
AND destinationport = 830
AND "NETCONF Source Approval Status" IN (
'unapproved',
'unknown'
)
)
OR (
LOGSOURCENAME(logsourceid) IN (
'Cisco SD-WAN Audit',
'Cisco SD-WAN Manager'
)
AND (
"Event Type" IN (
'configuration_change',
'policy_change',
'route_change',
'tunnel_change',
'certificate_change',
'template_push',
'device_registration_change',
'fabric_trust_change'
)
OR QIDNAME(qid) ILIKE '%configuration%'
OR QIDNAME(qid) ILIKE '%policy%'
OR QIDNAME(qid) ILIKE '%route%'
OR QIDNAME(qid) ILIKE '%tunnel%'
OR QIDNAME(qid) ILIKE '%certificate%'
OR QIDNAME(qid) ILIKE '%template%'
OR QIDNAME(qid) ILIKE '%fabric trust%'
)
AND "Object Type" IN (
'route',
'tunnel',
'policy',
'certificate',
'template',
'device_registration',
'peer_state',
'fabric_trust'
)
AND (
"Change Approval Status" IN (
'unapproved',
'unknown',
'missing'
)
OR "Actor Approval Status" IN (
'unapproved',
'unknown'
)
OR "Admin Source Approval Status" IN (
'unapproved',
'unknown'
)
)
)
)
GROUP BY
sourceip,
destinationip,
username,
"Object Changed",
"Change Type"
HAVING category_count >= 2
AND last_seen - first_seen <= ENV_SDWAN_CONFIG_CORRELATION_WINDOW
SIGMA
Detection Viability Assessment
SIGMA has three rules for this EXP report.
· SIGMA is viable as a portable behavioral rule format for expressing suspicious Cisco SD-WAN control-plane, authentication, NETCONF, and configuration-change patterns across SIEM platforms.
· SIGMA is strongest where Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF telemetry, configuration audit records, network-flow data, topology inventory, and enrichment fields are normalized before translation into a target SIEM.
· SIGMA can provide reusable detection logic for suspicious peering, administrative authentication, NETCONF access, and SD-WAN configuration modification.
· SIGMA is not a standalone proof source because final detection fidelity depends on the target SIEM, field mappings, log-source availability, enrichment quality, and correlation support.
· SIGMA rules should remain abstract enough to support different Cisco SD-WAN log schemas, SIEM backends, and enrichment models.
· SIGMA detection content should be treated as portable behavioral coverage for exploited SD-WAN control-plane trust abuse, not direct exploit confirmation by itself.
Rule 1
Suspicious Cisco SD-WAN Control-Plane or Peer Activity From Unapproved Source
Rule Format
SIGMA rule pattern suitable for translation into SIEM-specific logic after log-source validation, field mapping, Cisco SD-WAN event normalization, approved-peer enrichment, source-baseline validation, and environment-specific tuning.
Detection Purpose
Detect suspicious Cisco SD-WAN control-plane or peer activity from sources that are unknown, newly observed, external, or not approved for SD-WAN peer communication.
· Identify possible unauthorized SD-WAN control-plane trust establishment.
· Prioritize events involving unfamiliar source IPs, unexpected peer identity fields, unusual geographies, unusual ASNs, cloud or VPN egress, or sources not present in approved SD-WAN topology.
· Support investigation of exploited SD-WAN control-plane trust abuse without relying on CVE-string matches, scanner output, advisory references, payload visibility, or exploit-specific indicators.
· This rule does not prove successful exploitation without supporting peer-state, authentication, NETCONF, configuration, topology, or change-management evidence.
Detection Logic
Identify Cisco SD-WAN Controller or Manager events involving peer-state changes, control connections, device registration, peer identity activity, or control-plane events.
· Prioritize events where source approval status, peer approval status, topology match, or peer identity match indicates unknown, unapproved, or mismatched context.
· Increase confidence when the source is newly observed or associated with cloud, VPN, hosting, unmanaged, unusual geography, or unusual ASN context.
· Increase confidence when the same source is associated with control-connection anomalies, unexpected peer identity fields, or device-registration activity.
· Increase confidence when activity is followed by administrative authentication, NETCONF access, or SD-WAN configuration changes.
· Reduce severity for approved peers, known controller relationships, expected edge-device communication, sanctioned service-provider activity, planned topology changes, and documented maintenance activity.
· Do not classify control-plane activity as compromise without corroborating authentication, NETCONF, configuration, topology, or change-management evidence.
Required Telemetry
Cisco SD-WAN Controller logs.
· Cisco SD-WAN Manager logs.
· Control-connection events.
· Peer-state events.
· Device-registration events.
· Source IP.
· Destination IP.
· Peer type.
· System IP.
· Site ID.
· Domain ID.
· Public IP.
· Device identity.
· Controller relationship.
· Event outcome.
· Timestamp.
· Source approval status.
· Peer approval status.
· Peer identity match status.
· Topology match status.
· GeoIP, ASN, VPN, cloud-provider, and hosting-provider enrichment.
· Approved SD-WAN peer inventory.
· Maintenance-window and change-management context.
Engineering Implementation Instructions
Validate the target SIEM log source, source category, index, sourcetype, parser, or data stream before translating this SIGMA pattern.
· Normalize Cisco SD-WAN Controller and Manager events into consistent event names for peer-state, control-connection, device-registration, peer-identity, and control-plane activity.
· Map source IP, destination IP, System IP, site ID, domain ID, peer type, public IP, device identity, controller relationship, and event outcome into target SIEM fields.
· Enrich events with approved peer status, source approval status, peer identity match, topology match, source first-seen status, source geography, ASN, cloud-provider, VPN-provider, and hosting-provider context.
· Add environment-specific exceptions for approved maintenance, controller migration, edge onboarding, disaster recovery, service-provider activity, automation, and emergency access.
· Avoid broad exceptions for cloud, VPN, managed-service, or service-provider sources because attacker and legitimate administrative paths may overlap.
· Treat this rule as higher priority when paired with administrative authentication, NETCONF access, configuration changes, or post-access SD-WAN fabric impact.
· Translate and validate the SIGMA rule in the target SIEM before production use.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to suspicious SD-WAN control-plane activity and peer identity mismatch rather than static exploit indicators.
· The rule remains useful if exploit delivery changes but the attacker still needs to interact with SD-WAN control-plane infrastructure.
· The score is supported by durable telemetry relationships across peer identity, source behavior, topology, and timing.
· The score is constrained by target-SIEM field mapping, enrichment availability, incomplete peer inventories, service-provider activity, migrations, and legitimate edge onboarding.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on Cisco SD-WAN log ingestion, parser quality, normalized field mapping, approved-peer enrichment, administrative-source baselines, and maintenance-window context.
· Operational confidence is reduced where the target SIEM lacks consistent Cisco SD-WAN parsing or approved topology enrichment.
· Full-telemetry confidence improves when the translated SIGMA logic is enriched with Controller logs, Manager logs, network-flow records, authentication logs, NETCONF telemetry, configuration audit logs, and change-management data.
· Even under full telemetry conditions, this rule should support investigation unless paired with authentication, NETCONF, or configuration-impact evidence.
Limitations
This rule detects suspicious control-plane or peering behavior, not successful exploitation by itself.
· SIGMA portability depends on accurate translation into the target SIEM.
· Legitimate SD-WAN operations, edge onboarding, controller migration, service-provider activity, and disaster-recovery testing may overlap with the same behavior.
· Incomplete topology inventory or enrichment gaps can reduce confidence.
· Confirmation requires correlation with administrative authentication, NETCONF access, configuration changes, topology mismatch, or unauthorized fabric-impact activity.
Detection Query Pattern
SIGMA-style detection pattern requiring target-SIEM translation, Cisco SD-WAN field mapping, approved-peer enrichment validation, source-enrichment validation, and environment-specific tuning before production deployment.
title: Suspicious Cisco SD-WAN Control-Plane or Peer Activity From Unapproved Source
id: ENV_GENERATED_SIGMA_RULE_ID_1
status: test
description: Detects Cisco SD-WAN control-plane or peer activity from unknown, unapproved, or topology-mismatched sources.
logsource:
product: cisco
service: sdwan
category: network
detection:
selection_sdwan_control_plane:
event.action:
- peer_state_change
- control_connection
- device_registration
- peer_identity
- control_plane_event
selection_peer_approval_anomaly:
sdwan.enrichment.peer_approval_status:
- unapproved
- unknown
selection_source_approval_anomaly:
sdwan.enrichment.source_approval_status:
- unapproved
- unknown
selection_identity_anomaly:
sdwan.enrichment.peer_identity_match:
- false
selection_topology_anomaly:
sdwan.enrichment.topology_match:
- false
selection_new_source:
sdwan.enrichment.source_first_seen_within:
- ENV_NEW_SOURCE_WINDOW
selection_unusual_source_provider:
source.provider_type:
- cloud_hosting
- vpn_provider
- hosting_provider
- unknown_external
filter_approved_change_context:
labels.change_context:
- approved_sdwan_maintenance
- approved_controller_migration
- approved_edge_onboarding
- approved_disaster_recovery
- approved_service_provider_activity
- approved_emergency_access
condition: selection_sdwan_control_plane and (1 of selection_*_anomaly or selection_new_source or selection_unusual_source_provider) and not filter_approved_change_context
fields:
- source.ip
- destination.ip
- event.action
- sdwan.peer.type
- sdwan.system.ip
- sdwan.site.id
- sdwan.domain.id
- sdwan.device.identity
- sdwan.controller.relationship
- sdwan.enrichment.peer_approval_status
- sdwan.enrichment.source_approval_status
- sdwan.enrichment.topology_match
falsepositives:
- Approved SD-WAN edge onboarding
- Controller migration
- Service-provider maintenance
- Disaster-recovery testing
- Emergency access
level: medium
Rule 2
Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication
Rule Format
SIGMA correlation-style rule pattern suitable for translation into SIEM-specific sequence logic after log-source validation, authentication-field mapping, NETCONF-field mapping, sequence-window validation, enrichment validation, and environment-specific tuning.
Detection Purpose
Detect suspicious sequencing where Cisco SD-WAN control-plane activity is followed by NETCONF access or administrative authentication.
· Identify behavior consistent with progression from control-plane interaction to privileged SD-WAN management activity.
· Prioritize sources that are unfamiliar, newly observed, external, unauthorized, or not aligned with approved administrative workflows.
· Support investigation of potential SD-WAN control-plane trust abuse without relying on encrypted payload inspection.
· This rule does not prove successful exploitation or configuration manipulation without supporting controller-side, authentication, NETCONF, configuration-audit, topology, or change-management evidence.
Detection Logic
Identify suspicious SD-WAN control-plane or peer-state activity involving an unknown or unapproved source.
· Correlate the source or related source with successful administrative authentication or NETCONF access within the same operational window.
· Increase confidence when the source is newly observed, external, cloud-hosted, VPN-associated, hosting-provider-associated, or not part of approved administrative source lists.
· Increase confidence when the sequence occurs near peer-state changes, control-connection instability, device-registration activity, or unexpected peer identity fields.
· Increase confidence when NETCONF or authentication activity occurs outside approved maintenance, automation, service-provider, or emergency-access windows.
· Increase confidence when the sequence is followed by configuration audit activity.
· Reduce severity for approved automation, approved NETCONF management workflows, service-provider maintenance, planned migration, and documented emergency access.
· Do not classify NETCONF or administrative authentication as malicious without source, identity, timing, peer-state, topology, and configuration-change context.
Required Telemetry
Cisco SD-WAN Controller logs.
· Cisco SD-WAN Manager logs.
· Authentication logs.
· NETCONF records or network-flow records for TCP port 830.
· Source IP.
· Destination IP.
· Username.
· Authentication method.
· Authentication outcome.
· NETCONF source.
· NETCONF destination.
· Peer-state context.
· Control-connection context.
· Device-registration context.
· Timestamp.
· Source approval status.
· NETCONF source approval status.
· Administrative source approval status.
· Approved peer and controller inventories.
· GeoIP, ASN, cloud-provider, VPN-provider, hosting-provider, and first-seen enrichment.
· Maintenance-window, automation, service-provider, and change-management context.
Engineering Implementation Instructions
Validate whether the target SIEM supports SIGMA correlation, rule chaining, or sequence logic before translating this rule.
· Normalize Cisco SD-WAN control-plane events, authentication events, and NETCONF events into consistent event categories.
· Map source IP, destination IP, username, authentication outcome, NETCONF destination, peer identity fields, and timestamps into target SIEM fields.
· Enrich events with approved SD-WAN peer status, administrative source approval status, NETCONF source approval status, source first-seen status, and provider context.
· Tune sequence windows around normal SD-WAN administrative workflows, automation jobs, emergency access, and service-provider maintenance.
· Add exceptions for approved maintenance, approved NETCONF automation, service-provider activity, emergency access, and controller migration.
· Avoid suppressing all NETCONF or administrative activity from broad infrastructure categories because attackers may use cloud, VPN, or provider egress.
· Use target-SIEM risk scoring, chained alerts, or correlation rules to increase severity when this sequence is followed by configuration change or fabric-impact activity.
DRI Assessment
DRI
8.5 / 10
· The rule is behaviorally anchored to a durable progression from suspicious control-plane activity to privileged access.
· The rule remains useful if the exploit implementation changes but the attacker proceeds from control-plane interaction to administrative or NETCONF activity.
· The score is supported by the operational significance of NETCONF access or authentication following suspicious peering or peer-state activity.
· The score is constrained by target-SIEM correlation support, legitimate automation, provider maintenance, emergency access, incomplete NETCONF visibility, and incomplete authentication telemetry.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
9.0 / 10
· Operational confidence depends on reliable SD-WAN log ingestion, authentication visibility, NETCONF visibility, correlation timing, normalized fields, and approved administrative workflow documentation.
· Operational confidence is reduced where the target SIEM does not support sequence logic or where SIGMA translation cannot preserve the intended correlation window.
· Full-telemetry confidence improves when the translated rule is correlated with configuration audit records, peer-state changes, topology mismatch, and change-management context.
· Under full telemetry conditions, this rule provides strong suspicious-activity coverage, but confirmed exploitation still requires evidence of unauthorized peer status, configuration impact, or fabric change.
Limitations
This rule detects suspicious control-plane-to-privileged-access sequencing, not successful exploitation by itself.
· Some target SIEMs may require this SIGMA pattern to be implemented as multiple linked rules rather than a single correlation rule.
· NETCONF and administrative authentication may be legitimate in approved automation, service-provider, and emergency workflows.
· Related-source correlation may be imperfect when attackers rotate infrastructure or use shared cloud, VPN, or provider egress.
· Confirmation requires correlation with peer-state anomalies, unauthorized source context, configuration changes, topology mismatch, or fabric-impact evidence.
Detection Query Pattern
SIGMA correlation-style pattern requiring target-SIEM translation, sequence-rule support, field validation, enrichment validation, and environment-specific allowlisting before production deployment.
title: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication
id: ENV_GENERATED_SIGMA_RULE_ID_2
status: test
description: Detects suspicious Cisco SD-WAN control-plane activity followed by NETCONF access or successful administrative authentication.
logsource:
product: cisco
service: sdwan
category: network
correlation:
type: temporal
rules:
- sdwan_control_plane_anomaly
- sdwan_privileged_access
group-by:
- source.ip
timespan: ENV_SDWAN_SEQUENCE_WINDOW
detection:
selection_sdwan_control_plane_anomaly:
event.action:
- peer_state_change
- control_connection
- device_registration
- unexpected_peer_identity
- control_plane_event
sdwan.enrichment.peer_approval_status:
- unapproved
- unknown
selection_admin_auth_success:
event.category:
- authentication
event.outcome:
- success
sdwan.enrichment.admin_source_status:
- unapproved
- unknown
selection_netconf_access:
event.category:
- network
destination.port:
- 830
sdwan.enrichment.netconf_source_status:
- unapproved
- unknown
filter_approved_change_context:
labels.change_context:
- approved_sdwan_maintenance
- approved_netconf_automation
- approved_service_provider_activity
- approved_emergency_access
- approved_controller_migration
condition: selection_sdwan_control_plane_anomaly and (selection_admin_auth_success or selection_netconf_access) and not filter_approved_change_context
fields:
- source.ip
- destination.ip
- user.name
- event.category
- event.action
- event.outcome
- destination.port
- sdwan.enrichment.peer_approval_status
- sdwan.enrichment.admin_source_status
- sdwan.enrichment.netconf_source_status
falsepositives:
- Approved NETCONF automation
- Service-provider administration
- Emergency access
- Controller migration
- Approved maintenance
level: high
Rule 3
Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity
Rule Format
SIGMA correlation-style rule pattern suitable for translation into SIEM-specific correlation logic after configuration-audit source validation, SD-WAN field normalization, actor-field validation, change-management enrichment validation, and environment-specific tuning.
Detection Purpose
Detect SD-WAN configuration changes that occur after suspicious control-plane activity, administrative authentication, or NETCONF access.
· Identify possible fabric-impact behavior involving routes, tunnels, policies, certificates, device registration, peer state, or fabric-trust relationships.
· Prioritize configuration changes involving unfamiliar sources, unauthorized users, unexpected peer identity fields, or changes lacking approval context.
· Support investigation of post-access SD-WAN fabric manipulation without treating configuration change alone as proof of compromise.
· This rule does not prove successful exploitation without supporting peering, authentication, NETCONF, topology, or authorization evidence.
Detection Logic
Identify suspicious SD-WAN control-plane activity, administrative authentication, or NETCONF access.
· Correlate the activity with SD-WAN configuration changes within the same operational window.
· Prioritize changes affecting routes, tunnels, policies, certificates, templates, device registration, peer state, controller relationships, or fabric trust.
· Increase confidence when the actor, source, object changed, or change type does not align with approved administrative workflows.
· Increase confidence when the change lacks a matching change ticket, maintenance window, emergency-access record, automation record, or service-provider record.
· Increase confidence when the configuration change is followed by new traffic-flow patterns, newly reachable destinations, or persistent unfamiliar access.
· Reduce severity for approved maintenance, automation, service-provider activity, controller migration, disaster recovery, policy deployment, and emergency changes.
· Do not classify configuration changes as compromise without source, actor, timing, peer-state, topology, and change-authorization context.
Required Telemetry
Cisco SD-WAN configuration audit logs.
· Cisco SD-WAN Manager audit logs.
· Cisco SD-WAN Controller logs.
· Authentication logs.
· NETCONF records or network-flow records for TCP port 830.
· Route change events.
· Tunnel change events.
· Policy change events.
· Certificate change events.
· Device-registration events.
· Peer-state events.
· Template or configuration push events.
· Actor.
· Source IP.
· Destination IP.
· Object changed.
· Change type.
· Change outcome.
· Timestamp.
· Change approval status.
· Actor approval status.
· Administrative source approval status.
· Approved change-management records.
· Approved automation records.
· Approved service-provider records.
· Approved emergency-access records.
· Topology and peer inventory.
Engineering Implementation Instructions
Validate whether the target SIEM supports SIGMA correlation, temporal grouping, or rule chaining before translation.
· Normalize Cisco SD-WAN control-plane events, authentication events, NETCONF events, and configuration audit events into consistent categories.
· Map actor, source IP, destination IP, object changed, change type, change outcome, peer identity, and timestamp fields into target SIEM fields.
· Enrich events with change approval status, actor approval status, administrative source approval status, peer approval status, and topology match context.
· Tag high-impact configuration objects such as routes, tunnels, policies, templates, certificates, device-registration objects, peer-state objects, and fabric-trust objects.
· Add exceptions for approved policy deployments, controller migrations, disaster recovery, provider maintenance, emergency access, and approved automation.
· Avoid suppressing all configuration changes from automation accounts because automation credentials may be abused after control-plane compromise.
· Use target-SIEM risk scoring, chained alerts, or correlation rules to elevate high-impact configuration changes that follow suspicious peering, authentication, or NETCONF activity.
DRI Assessment
DRI
8.5 / 10
· The rule is behaviorally anchored to configuration change following suspicious control-plane or privileged access activity.
· The rule remains useful if exploit implementation changes but attacker objectives still include SD-WAN fabric manipulation.
· The score is supported by the durability of fabric-impacting configuration changes as observable post-access behavior.
· The score is constrained by target-SIEM correlation support, legitimate automation, policy deployment, provider maintenance, migrations, and incomplete configuration audit visibility.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
9.0 / 10
· Operational confidence depends on configuration audit visibility, actor and source normalization, change-management enrichment, SD-WAN topology inventory, and correlation with control-plane or privileged-access events.
· Operational confidence is reduced where SIGMA translation cannot preserve the intended sequence logic or where configuration audit logs lack actor, source, or object context.
· Full-telemetry confidence improves when configuration changes are correlated with suspicious peering, authentication, NETCONF access, network-flow changes, topology mismatch, and post-access fabric impact.
· Under full telemetry conditions, this rule can provide high-confidence evidence of suspicious SD-WAN fabric manipulation, but confirmed exploitation still requires unauthorized access or trust-establishment context.
Limitations
This rule detects suspicious configuration change after suspicious access, not exploit execution.
· Some target SIEMs may require this SIGMA pattern to be implemented as multiple linked rules rather than a single correlation rule.
· Legitimate policy deployment, route changes, tunnel changes, certificate renewal, service-provider activity, automation, disaster recovery, and emergency changes may overlap with the same behavior.
· Automation activity may obscure the original actor unless identity and source context are preserved.
· Confirmation requires correlation with suspicious peering, administrative authentication, NETCONF access, topology mismatch, unauthorized source context, or fabric-impact evidence.
Detection Query Pattern
SIGMA correlation-style pattern requiring target-SIEM translation, configuration-audit validation, actor-field validation, change-management enrichment validation, sequence-window tuning, and environment-specific allowlisting before production deployment.
title: Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity
id: ENV_GENERATED_SIGMA_RULE_ID_3
status: test
description: Detects high-impact Cisco SD-WAN configuration changes following suspicious control-plane, authentication, or NETCONF activity.
logsource:
product: cisco
service: sdwan
category: configuration
correlation:
type: temporal
rules:
- sdwan_suspicious_access_context
- sdwan_configuration_change
group-by:
- source.ip
timespan: ENV_SDWAN_CONFIG_CORRELATION_WINDOW
detection:
selection_suspicious_peer_context:
event.action:
- peer_state_change
- control_connection
- device_registration
- unexpected_peer_identity
- control_plane_event
sdwan.enrichment.peer_approval_status:
- unapproved
- unknown
selection_suspicious_admin_auth:
event.category:
- authentication
event.outcome:
- success
sdwan.enrichment.admin_source_status:
- unapproved
- unknown
selection_suspicious_netconf_access:
event.category:
- network
destination.port:
- 830
sdwan.enrichment.netconf_source_status:
- unapproved
- unknown
selection_configuration_change:
event.action:
- configuration_change
- policy_change
- route_change
- tunnel_change
- certificate_change
- template_push
- device_registration_change
- fabric_trust_change
sdwan.change.object.type:
- route
- tunnel
- policy
- certificate
- template
- device_registration
- peer_state
- fabric_trust
selection_unapproved_change_status:
sdwan.enrichment.change_approval_status:
- unapproved
- unknown
- missing
selection_unapproved_actor_status:
sdwan.enrichment.actor_approval_status:
- unapproved
- unknown
selection_unapproved_admin_source_status:
sdwan.enrichment.admin_source_status:
- unapproved
- unknown
filter_approved_change_context:
labels.change_context:
- approved_sdwan_maintenance
- approved_policy_deployment
- approved_controller_migration
- approved_disaster_recovery
- approved_service_provider_activity
- approved_emergency_access
condition: (selection_suspicious_peer_context or selection_suspicious_admin_auth or selection_suspicious_netconf_access) and selection_configuration_change and (selection_unapproved_change_status or selection_unapproved_actor_status or selection_unapproved_admin_source_status) and not filter_approved_change_context
fields:
- source.ip
- destination.ip
- user.name
- event.action
- sdwan.change.object.type
- sdwan.change.object.name
- sdwan.enrichment.change_approval_status
- sdwan.enrichment.actor_approval_status
- sdwan.enrichment.admin_source_status
falsepositives:
- Approved policy deployment
- Controller migration
- Disaster-recovery testing
- Service-provider maintenance
- Emergency change
level: high
YARA
Detection Viability Assessment
YARA has zero rules for this EXP report.
· YARA is not viable as a primary detection-rule system for this report because the core detection problem is behavioral, control-plane, topology, authentication, NETCONF, configuration-change, and network-flow based rather than static-file or malware-signature based.
· The strongest detection logic depends on unauthorized SD-WAN control-plane trust establishment, rogue peering, unexpected peer identity fields, suspicious administrative authentication, NETCONF access, route changes, tunnel changes, policy changes, certificate changes, device-registration changes, peer-state changes, and fabric-trust modification.
· YARA is not suitable for confirming Cisco SD-WAN peer establishment, control-plane trust abuse, administrative authentication, NETCONF activity, SD-WAN configuration manipulation, topology mismatch, routing impact, tunnel modification, policy deployment, or SD-WAN fabric impact.
· YARA rules against generic Cisco SD-WAN files, configuration exports, certificate files, backup artifacts, logs, templates, administrative scripts, or appliance artifacts would create high false-positive risk because legitimate maintenance, backup, migration, service-provider support, certificate renewal, troubleshooting, and policy-deployment workflows may share similar file characteristics.
· YARA rules based on public proof-of-concept artifacts, static strings, file names, repository content, exploit branding, advisory text, or CVE references would be brittle and easy to evade through minor artifact changes.
· YARA would not provide reliable visibility into the activity sequence that matters most for this report, including suspicious peering, administrative authentication, NETCONF access, configuration changes, topology mismatch, and post-access fabric impact.
· YARA should not be used to claim detection of CVE-2026-20182 exploitation, rogue SD-WAN peering, unauthorized control-plane trust establishment, NETCONF misuse, configuration manipulation, persistence, or SD-WAN fabric compromise.
Limited Operational Use
· YARA may be useful for controlled internal research if an incident produces a confirmed malicious file, tool, payload, or reusable artifact associated with post-access SD-WAN compromise.
· YARA may support retrospective lab analysis of a specific artifact after SD-WAN Controller, Manager, authentication, NETCONF, configuration-audit, topology, and network-flow evidence has already validated the artifact as suspicious.
· YARA may assist malware or tool-family classification if a stable malicious file family emerges around SD-WAN control-plane abuse.
· YARA may support targeted incident scoping across collected forensic images, quarantined files, or confirmed suspicious artifacts when the rule is built from validated incident evidence rather than public proof-of-concept content.
· YARA should not be used for broad production detection against generic Cisco SD-WAN configuration files, logs, certificates, backups, templates, administrative scripts, appliance files, or deployment artifacts.
· YARA should not be used as the primary S25 detection method for this report.
Final Outcome
No YARA rules survive.
AWS
Detection Viability Assessment
AWS has three rules for this EXP report.
· AWS is viable when Cisco SD-WAN Controller, Manager, or supporting infrastructure is hosted in AWS or when AWS network telemetry observes access paths to SD-WAN infrastructure.
· AWS is strongest where VPC Flow Logs, CloudTrail records, security group change events, network ACL change events, load balancer logs, AWS Network Firewall logs, Security Lake records, asset tags, approved administrative-source baselines, and change-management context are available.
· AWS can support detection of cloud-hosted SD-WAN exposure, suspicious inbound access, NETCONF access, cloud-network policy changes, and post-access traffic-flow changes affecting SD-WAN infrastructure.
· AWS should not be treated as a standalone source for confirming successful CVE-2026-20182 exploitation because AWS telemetry generally observes cloud-network access, exposure, and infrastructure-change behavior rather than Cisco SD-WAN peer-state or configuration intent.
· AWS rules should be correlated with Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, topology inventory, NDR telemetry, and change-management context before classifying activity as confirmed compromise.
· AWS detection content should be treated as cloud-hosted exposure and access-path coverage for SD-WAN infrastructure, not direct exploit confirmation by itself.
Rule 1
Cloud-Hosted Cisco SD-WAN Control-Plane or NETCONF Access From Unapproved Source
Rule Format
AWS detection rule suitable for CloudWatch Logs Insights, Security Lake, Athena, SIEM-forwarded AWS telemetry, or CSPM/SIEM correlation after VPC Flow Log validation, SD-WAN asset tagging, security group validation, NETCONF exposure validation, approved-source baselining, and environment-specific tuning.
Detection Purpose
Detect access to AWS-hosted Cisco SD-WAN Controller, Manager, or NETCONF-exposed infrastructure from unknown, newly observed, external, or unapproved sources.
· Identify suspicious inbound paths to SD-WAN control-plane or management-plane services.
· Prioritize traffic involving unfamiliar source IPs, unusual geographies, unusual ASNs, cloud or VPN egress, hosting providers, unmanaged networks, or sources not aligned with approved SD-WAN administration.
· Support investigation of exploited SD-WAN control-plane trust abuse without relying on CVE-string matches, scanner output, advisory references, payload visibility, or exploit-specific indicators.
· This rule does not prove successful exploitation, rogue peering, NETCONF misuse, or configuration manipulation without supporting Cisco SD-WAN Controller, Manager, authentication, NETCONF, configuration-audit, topology, or network-flow evidence.
Detection Logic
Identify inbound traffic to AWS-hosted Cisco SD-WAN Controller, Manager, or NETCONF-exposed infrastructure.
· Prioritize accepted traffic to validated SD-WAN control-plane ports or TCP port 830 from sources not present in approved peer, administrative, service-provider, automation, or emergency-access baselines.
· Increase confidence when the source is newly observed, geographically unusual, ASN-unusual, VPN-associated, cloud-hosted, hosting-provider-associated, unmanaged, or associated with a provider type not normally used for SD-WAN administration.
· Increase confidence when the source communicates with multiple SD-WAN instances, load balancers, elastic network interfaces, public IPs, or subnets within the same operational window.
· Increase confidence when inbound access is followed by SD-WAN authentication, NETCONF activity, configuration change, or post-access traffic-flow change.
· Increase confidence when activity occurs outside approved maintenance, migration, disaster-recovery, service-provider, automation, or emergency-access windows.
· Reduce severity for approved administrative paths, approved service-provider sources, expected controller relationships, planned migrations, approved edge onboarding, and documented emergency access.
· Do not classify inbound control-plane or NETCONF traffic as compromise without corroborating peer-state, authentication, NETCONF, configuration, topology, or change-management evidence.
Required Telemetry
VPC Flow Logs.
AWS Security Lake network telemetry where available.
· CloudWatch Logs where VPC Flow Logs are delivered.
· Elastic Load Balancing logs where applicable.
· AWS Network Firewall logs where applicable.
· Security group metadata.
· Network ACL metadata.
· EC2 instance tags.
· Elastic network interface tags.
· Public IP and private IP mappings.
· Source IP.
· Destination IP.
· Destination port.
· Protocol.
· Action.
· Timestamp.
· Packet count and byte count where available.
· Approved SD-WAN asset inventory.
· Approved administrative source baselines.
· Approved service-provider source baselines.
· Approved NETCONF source baselines.
· GeoIP, ASN, VPN, cloud-provider, and hosting-provider enrichment.
· Maintenance-window and change-management context.
· Cisco SD-WAN Controller, Manager, authentication, NETCONF, and configuration-audit correlation where available.
Engineering Implementation Instructions
Tag AWS-hosted Cisco SD-WAN Controller, Manager, and NETCONF-exposed infrastructure using consistent asset tags.
· Validate the AWS accounts, VPCs, subnets, elastic network interfaces, public IPs, private IPs, and load balancers that host or front SD-WAN infrastructure.
· Validate the SD-WAN control-plane ports used by the organization before enabling high-severity alerting.
· Validate whether NETCONF is exposed and which administrative sources are approved.
· Build approved source lists for SD-WAN peers, administrative VPN paths, service-provider paths, automation sources, emergency-access paths, and management networks.
· Add enrichment for source first-seen status, geography, ASN, cloud provider, VPN provider, hosting provider, and managed-service context.
· Correlate suspicious AWS network telemetry with Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, and NDR telemetry.
· Avoid broad suppression for cloud, VPN, hosting, managed-service, or service-provider infrastructure because attacker and legitimate administrative paths may overlap.
· Treat this rule as higher priority when access is followed by authentication, NETCONF activity, SD-WAN configuration changes, or new traffic-flow behavior.
· Use change-management and maintenance records to distinguish approved AWS-hosted SD-WAN operations from suspicious access.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to suspicious access toward cloud-hosted SD-WAN control-plane or NETCONF services rather than static exploit indicators.
· The rule remains useful if exploit delivery changes but the attacker still needs to access AWS-hosted SD-WAN infrastructure.
· The score is supported by durable source, destination, port, protocol, timing, asset, and approval-context relationships.
· The score is constrained by legitimate service-provider access, cloud-hosted administration, emergency access, controller migration, incomplete asset tagging, and incomplete approved-source baselines.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on VPC Flow Log coverage, SD-WAN asset tagging, public IP mapping, approved-source baselines, flow-log delivery quality, and maintenance-window context.
· Operational confidence is reduced where SD-WAN infrastructure is not consistently tagged, where public IP ownership is unclear, or where approved administrative paths are poorly documented.
· Full-telemetry confidence improves when AWS network telemetry is correlated with Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, NDR telemetry, and change-management context.
· Even under full telemetry conditions, this rule should support escalation and investigation rather than standalone confirmation of successful exploitation.
Limitations
This rule detects suspicious AWS network access to SD-WAN infrastructure, not successful exploitation.
· VPC Flow Logs generally do not provide payload visibility or SD-WAN peer-state context.
· Legitimate administration, service-provider support, automation, maintenance, controller migration, and emergency access may overlap with the same network patterns.
· The rule requires accurate SD-WAN asset tagging, approved-source baselines, and control-plane service validation.
· Confirmation requires correlation with Cisco SD-WAN peer-state anomalies, administrative authentication, NETCONF access, configuration changes, topology mismatch, or post-access fabric-impact evidence.
Detection Query Pattern
AWS CloudWatch Logs Insights / Security Lake / Athena-style detection pattern requiring telemetry-source validation, SD-WAN asset tagging, approved-source validation, port validation, source-enrichment validation, and environment-specific tuning before production deployment.
SELECT
account_id,
region,
vpc_id,
interface_id,
srcaddr,
dstaddr,
dstport,
protocol,
action,
COUNT(*) AS connection_count,
MIN(start_time) AS first_seen,
MAX(end_time) AS last_seen
FROM aws_network_telemetry
WHERE dstaddr IN ASSET_GROUP(
'AWS Hosted Cisco SD-WAN Controllers',
'AWS Hosted Cisco SD-WAN Managers',
'AWS Hosted NETCONF Exposed SD-WAN Infrastructure'
)
AND action = 'ACCEPT'
AND (
dstport IN ENV_CISCO_SDWAN_CONTROL_PLANE_PORTS
OR dstport = 830
)
AND (
source_approval_status IN (
'unapproved',
'unknown'
)
OR source_first_seen_within = 'ENV_NEW_SOURCE_WINDOW'
OR source_provider_type IN (
'cloud_hosting',
'vpn_provider',
'hosting_provider',
'unknown_external'
)
OR source_geo_approval_status IN (
'unapproved',
'unknown'
)
OR source_asn_approval_status IN (
'unapproved',
'unknown'
)
)
AND change_context NOT IN (
'approved_sdwan_maintenance',
'approved_controller_migration',
'approved_edge_onboarding',
'approved_disaster_recovery',
'approved_service_provider_activity',
'approved_emergency_access'
)
GROUP BY
account_id,
region,
vpc_id,
interface_id,
srcaddr,
dstaddr,
dstport,
protocol,
action
HAVING connection_count >= ENV_AWS_SDWAN_ACCESS_THRESHOLD
Rule 2
AWS Security Group or Network ACL Change Exposing Cisco SD-WAN Infrastructure
Rule Format
AWS CloudTrail / Security Hub / SIEM correlation rule suitable for detecting cloud-network exposure changes after CloudTrail validation, security group and network ACL parsing validation, SD-WAN asset tagging, change-approval validation, and environment-specific tuning.
Detection Purpose
Detect AWS security group, network ACL, route, load balancer, or network firewall exposure changes that permit new inbound access to Cisco SD-WAN Controller, Manager, or NETCONF-exposed infrastructure.
· Identify cloud-network changes that may increase SD-WAN control-plane or management-plane exposure.
· Prioritize changes involving public ingress, broad CIDR ranges, unfamiliar source ranges, SD-WAN control-plane ports, NETCONF, administrative access paths, or unapproved change actors.
· Support investigation of exposure changes that could enable or support SD-WAN control-plane abuse.
· This rule does not prove successful exploitation without supporting access, authentication, NETCONF, configuration, topology, or SD-WAN Controller evidence.
Detection Logic
Identify CloudTrail events that modify security groups, network ACLs, routes, load balancer listeners, target groups, or network firewall policies affecting AWS-hosted Cisco SD-WAN infrastructure.
· Prioritize changes that permit inbound access to SD-WAN control-plane ports or TCP port 830 from public, broad, unknown, or unapproved source ranges.
· Increase confidence when the changed resource is attached to a tagged SD-WAN Controller, Manager, load balancer, elastic network interface, subnet, route table, or security boundary.
· Increase confidence when the actor, role, source IP, assumed role session, automation context, or change approval context is unknown, unapproved, newly observed, or outside normal change workflows.
· Increase confidence when exposure change is followed by inbound access to SD-WAN infrastructure, administrative authentication, NETCONF activity, or SD-WAN configuration changes.
· Reduce severity for approved maintenance, approved migration, approved disaster recovery, service-provider activity, emergency access, and documented security group or firewall policy changes.
· Do not classify an exposure change as compromise without corroborating suspicious access, authentication, NETCONF, configuration change, or SD-WAN fabric-impact evidence.
Required Telemetry
CloudTrail management events.
· EC2 security group change events.
· Network ACL change events.
· Route table change events where applicable.
· Elastic Load Balancing listener and target group change events where applicable.
· AWS Network Firewall policy change events where applicable.
· IAM principal.
· Assumed role session context.
· Source IP.
· AWS account ID.
· Region.
· Resource ID.
· Security group ID.
· Network ACL ID.
· Route table ID.
· Load balancer ID where applicable.
· Target group ID where applicable.
· Changed port.
· Changed protocol.
· Changed source CIDR.
· Changed action.
· SD-WAN asset tags.
· Approved change-management records.
· Approved automation records.
· Approved service-provider records.
· Approved emergency-access records.
· Maintenance-window context.
Engineering Implementation Instructions
Identify all AWS resources that expose or protect Cisco SD-WAN Controller, Manager, and NETCONF-exposed infrastructure.
· Tag security groups, network ACLs, load balancers, target groups, route tables, subnets, and network firewall policies associated with SD-WAN infrastructure.
· Validate CloudTrail coverage for EC2, Elastic Load Balancing, Network Firewall, IAM, and related control-plane events.
· Build approved change-context enrichment for security group changes, network ACL changes, route changes, firewall policy changes, load balancer listener changes, and emergency access.
· Build approved actor lists for SD-WAN administrators, cloud network administrators, automation roles, service-provider roles, and emergency-access roles.
· Tune logic for approved maintenance, controller migration, edge onboarding, policy deployment, provider work, and disaster recovery.
· Avoid suppressing all automation-role activity because automation credentials may be abused or used outside approved workflows.
· Correlate exposure changes with VPC Flow Logs, load balancer logs, Cisco SD-WAN logs, authentication records, NETCONF records, configuration audit logs, and NDR telemetry.
· Elevate severity when exposure change is followed by accepted inbound access from unfamiliar or unapproved sources.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to cloud-network exposure changes affecting SD-WAN infrastructure.
· The rule remains useful if exploit delivery changes but attackers or misused credentials create or benefit from exposed SD-WAN control-plane or management paths.
· The score is supported by the durability of security group, network ACL, firewall, route, and load balancer changes as observable AWS control-plane events.
· The score is constrained by legitimate maintenance, migration, automation, provider work, emergency access, and incomplete tagging of SD-WAN-related AWS resources.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on CloudTrail coverage, asset tagging, resource relationship mapping, approved change context, IAM principal context, and maintenance-window data.
· Operational confidence is reduced where SD-WAN resource tagging is incomplete, where cloud-network ownership is unclear, or where approved automation records are weak.
· Full-telemetry confidence improves when exposure changes are correlated with VPC Flow Logs, load balancer logs, Cisco SD-WAN logs, authentication records, NETCONF records, configuration audit logs, and change-management records.
· Even under full telemetry conditions, this rule detects exposure and access-path risk rather than confirmed exploitation by itself.
Limitations
This rule detects exposure changes affecting AWS-hosted SD-WAN infrastructure, not successful exploitation.
· Legitimate cloud-network maintenance, service-provider work, disaster recovery, migrations, and emergency changes may overlap with this behavior.
· CloudTrail events may show that access was permitted but not whether SD-WAN trust was established.
· Missing asset tags or incomplete resource relationship mapping can reduce detection reliability.
· Confirmation requires correlation with accepted traffic, SD-WAN peer-state anomalies, administrative authentication, NETCONF access, configuration changes, or fabric-impact evidence.
Detection Query Pattern
AWS CloudTrail / SIEM-style detection pattern requiring CloudTrail validation, SD-WAN resource tagging, security group and network ACL parsing validation, approval-context enrichment, and environment-specific tuning before production deployment.
SELECT
eventTime,
recipientAccountId,
awsRegion,
eventSource,
eventName,
userIdentity.arn AS actor_arn,
sourceIPAddress,
requestParameters.groupId AS security_group_id,
requestParameters.networkAclId AS network_acl_id,
requestParameters.routeTableId AS route_table_id,
requestParameters.loadBalancerArn AS load_balancer_arn,
requestParameters.ipPermissions AS ip_permissions,
requestParameters.cidrBlock AS cidr_block
FROM cloudtrail_management_events
WHERE eventName IN (
'AuthorizeSecurityGroupIngress',
'ModifySecurityGroupRules',
'CreateSecurityGroup',
'ReplaceNetworkAclEntry',
'CreateNetworkAclEntry',
'CreateRoute',
'ReplaceRoute',
'CreateListener',
'ModifyListener',
'ModifyRule',
'UpdateFirewallPolicy'
)
AND affected_resource IN ASSET_GROUP(
'AWS Hosted Cisco SD-WAN Controllers',
'AWS Hosted Cisco SD-WAN Managers',
'AWS Hosted NETCONF Exposed SD-WAN Infrastructure',
'AWS SD-WAN Security Groups',
'AWS SD-WAN Network ACLs',
'AWS SD-WAN Load Balancers',
'AWS SD-WAN Route Tables',
'AWS SD-WAN Network Firewall Policies'
)
AND (
changed_port IN ENV_CISCO_SDWAN_CONTROL_PLANE_PORTS
OR changed_port = 830
OR changed_port IN ENV_SDWAN_ADMIN_PORTS
)
AND (
changed_source_cidr IN (
'0.0.0.0/0',
'::/0'
)
OR changed_source_approval_status IN (
'unapproved',
'unknown'
)
OR actor_approval_status IN (
'unapproved',
'unknown'
)
OR change_approval_status IN (
'unapproved',
'unknown',
'missing'
)
)
AND change_context NOT IN (
'approved_sdwan_maintenance',
'approved_controller_migration',
'approved_edge_onboarding',
'approved_disaster_recovery',
'approved_service_provider_activity',
'approved_emergency_access',
'approved_cloud_network_change'
)
Rule 3
Post-Access AWS Traffic Change From Cisco SD-WAN Infrastructure
Rule Format
AWS network-behavior correlation rule suitable for VPC Flow Logs, Security Lake, Athena, CloudWatch Logs Insights, or SIEM-forwarded telemetry after SD-WAN asset tagging, destination-baseline validation, sensitive-segment tagging, timing-window validation, and environment-specific tuning.
Detection Purpose
Detect new or unusual AWS network traffic from Cisco SD-WAN infrastructure after suspicious control-plane, NETCONF, administrative, or exposure-change activity.
· Identify possible post-access behavior involving new destinations, sensitive internal segments, management systems, cloud workloads, or recurring external infrastructure.
· Prioritize traffic from SD-WAN infrastructure to destinations not normally associated with approved management, monitoring, backup, service-provider, update, or automation workflows.
· Support investigation of possible SD-WAN fabric-impact or persistence behavior without assuming AWS network telemetry alone confirms compromise.
· This rule does not prove successful exploitation or SD-WAN fabric manipulation without supporting Cisco SD-WAN Controller, Manager, authentication, NETCONF, configuration-audit, topology, or NDR evidence.
Detection Logic
Identify suspicious access, NETCONF activity, or exposure-change context involving AWS-hosted Cisco SD-WAN infrastructure.
· Detect new, unusual, or baseline-deviating traffic from SD-WAN infrastructure after the suspicious access or exposure-change window.
· Prioritize flows to sensitive AWS workloads, identity systems, management systems, monitoring systems, backup systems, network-administration systems, peered VPCs, transit gateways, VPN paths, or unfamiliar external destinations.
· Increase confidence when the destination is first-seen, not approved, associated with cloud or hosting infrastructure, or not part of expected SD-WAN management, logging, monitoring, backup, update, automation, or service-provider workflows.
· Increase confidence when traffic-flow changes align with Cisco SD-WAN route, tunnel, policy, certificate, peer-state, or fabric-trust changes.
· Increase confidence when new traffic persists across multiple sessions or recurs after rollback, restart, patching, or remediation.
· Reduce severity for approved routing changes, tunnel changes, VPC connectivity changes, transit gateway changes, monitoring, backup, update, service-provider maintenance, automation, and emergency workflows.
· Do not classify post-access AWS traffic-flow change as compromise without corroborating source, timing, topology, authorization, and SD-WAN configuration-change evidence.
Required Telemetry
VPC Flow Logs.
AWS Security Lake network telemetry where available.
· Transit Gateway Flow Logs where available.
· Elastic Load Balancing logs where applicable.
· AWS Network Firewall logs where applicable.
· Route 53 Resolver logs where applicable.
· EC2 instance tags.
· Elastic network interface tags.
· VPC and subnet metadata.
· Transit Gateway and VPC peering metadata where applicable.
· Source IP.
· Destination IP.
· Destination port.
· Protocol.
· Action.
· Timestamp.
· Packet count and byte count where available.
· First-seen destination context.
· Destination approval status.
· Sensitive asset tags.
· Approved SD-WAN traffic baselines.
· Approved destination baselines.
· Change-management context.
· Cisco SD-WAN configuration audit correlation where available.
· NDR correlation where available.
Engineering Implementation Instructions
Build asset groups for AWS-hosted Cisco SD-WAN infrastructure, sensitive AWS workloads, management systems, identity systems, monitoring systems, backup systems, network-administration systems, peered VPCs, transit gateways, and external destination categories.
· Establish baselines for normal SD-WAN-related traffic flows, expected AWS management traffic, expected monitoring and logging traffic, expected backup traffic, expected update traffic, service-provider traffic, and expected VPC or transit-gateway paths.
· Correlate suspicious SD-WAN access, NETCONF activity, or exposure changes with subsequent first-seen or abnormal source-to-destination traffic.
· Tune timing windows to account for immediate configuration impact and delayed traffic-flow changes after policy deployment, route propagation, or cloud-network change propagation.
· Add allowlists for approved route changes, tunnel changes, policy changes, monitoring, backup, update, service-provider maintenance, automation, disaster recovery, and emergency access.
· Avoid broad suppression of new flows from SD-WAN environments because SD-WAN fabric compromise may create traffic that resembles legitimate route or policy changes.
· Increase severity when new traffic targets sensitive AWS workloads or creates new reachability between previously unrelated environments.
· Use Cisco SD-WAN configuration audit logs, NDR telemetry, CloudTrail, and change-management records to determine whether the traffic change was authorized.
DRI Assessment
DRI
7.5 / 10
· The rule is behaviorally anchored to post-access traffic-flow changes from AWS-hosted SD-WAN infrastructure.
· The rule remains useful if exploit implementation changes but attacker activity creates new outbound, lateral, or recurring communication paths from SD-WAN infrastructure.
· The score is supported by durable first-seen destination, unusual traffic path, sensitive-destination, and post-access timing relationships.
· The score is constrained by legitimate routing, tunnel, transit gateway, VPC, monitoring, backup, update, provider, automation, and emergency-access changes.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on VPC Flow Log coverage, SD-WAN asset tagging, destination baselines, sensitive-asset tagging, VPC relationship mapping, and change-management linkage.
· Operational confidence is reduced where AWS traffic baselines are immature, where sensitive-asset tagging is incomplete, or where SD-WAN-related traffic paths frequently change.
· Full-telemetry confidence improves when AWS traffic changes are correlated with Cisco SD-WAN configuration audit logs, peer-state changes, authentication records, NETCONF activity, NDR telemetry, CloudTrail records, and change-management context.
· Even under full telemetry conditions, traffic-flow change should be treated as impact-supporting evidence rather than standalone proof of exploitation.
Limitations
This rule detects suspicious AWS traffic-flow change after suspicious access or exposure context, not exploit execution.
· Legitimate route, tunnel, policy, VPC, transit gateway, service-provider, disaster-recovery, automation, and emergency changes may overlap with the same behavior.
· AWS network telemetry may not show SD-WAN peer-state context, NETCONF command content, or configuration intent.
· Incomplete destination baselines or sensitive-asset tagging may increase false positives.
· Confirmation requires correlation with suspicious control-plane activity, NETCONF access, SD-WAN configuration changes, topology mismatch, unauthorized change context, or fabric-impact evidence.
Detection Query Pattern
AWS network-behavior query pattern requiring VPC Flow Log validation, SD-WAN asset tagging, sensitive-asset tagging, flow-baseline validation, change-context validation, timing-window tuning, SIEM correlation fields, and environment-specific allowlisting before production deployment.
SELECT
account_id,
region,
vpc_id,
interface_id,
srcaddr,
dstaddr,
dstport,
protocol,
action,
COUNT(*) AS connection_count,
MIN(start_time) AS first_seen,
MAX(end_time) AS last_seen
FROM aws_network_telemetry
WHERE srcaddr IN ASSET_GROUP(
'AWS Hosted Cisco SD-WAN Controllers',
'AWS Hosted Cisco SD-WAN Managers',
'AWS Hosted NETCONF Exposed SD-WAN Infrastructure'
)
AND action = 'ACCEPT'
AND correlation_context IN (
'suspicious_sdwan_control_plane_access',
'suspicious_netconf_access',
'sdwan_exposure_change',
'suspicious_sdwan_admin_authentication',
'sdwan_configuration_change'
)
AND (
destination_first_seen_within = 'ENV_NEW_DESTINATION_WINDOW'
OR destination_approval_status IN (
'unapproved',
'unknown'
)
OR destination_asset IN ASSET_GROUP(
'AWS Identity Systems',
'AWS Management Systems',
'AWS Monitoring Systems',
'AWS Backup Systems',
'AWS Network Administration Systems',
'Sensitive AWS Workloads',
'Critical AWS Data Systems',
'Peered VPC Sensitive Segments',
'Transit Gateway Sensitive Routes'
)
OR source_to_destination_pair_status IN (
'new',
'rare',
'baseline_deviation'
)
)
AND change_context NOT IN (
'approved_route_change',
'approved_tunnel_change',
'approved_policy_deployment',
'approved_vpc_change',
'approved_transit_gateway_change',
'approved_monitoring_workflow',
'approved_backup_workflow',
'approved_update_workflow',
'approved_service_provider_activity',
'approved_emergency_change'
)
GROUP BY
account_id,
region,
vpc_id,
interface_id,
srcaddr,
dstaddr,
dstport,
protocol,
action
HAVING connection_count >= ENV_AWS_POST_ACCESS_FLOW_THRESHOLD
Azure
Detection Viability Assessment
Azure has three rules for this EXP report.
· Azure is viable when Cisco SD-WAN Controller, Manager, or supporting infrastructure is hosted in Azure or when Azure network telemetry observes access paths to SD-WAN infrastructure.
· Azure is strongest where NSG Flow Logs, Azure Firewall logs, Application Gateway logs, Azure Load Balancer context, Azure Activity Logs, Microsoft Defender for Cloud alerts, asset tags, approved administrative-source baselines, and change-management context are available.
· Azure can support detection of cloud-hosted SD-WAN exposure, suspicious inbound access, NETCONF access, cloud-network policy changes, and post-access traffic-flow changes affecting SD-WAN infrastructure.
· Azure should not be treated as a standalone source for confirming successful CVE-2026-20182 exploitation because Azure telemetry generally observes cloud-network access, exposure, and infrastructure-change behavior rather than Cisco SD-WAN peer-state or configuration intent.
· Azure rules should be correlated with Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, topology inventory, NDR telemetry, and change-management context before classifying activity as confirmed compromise.
· Azure detection content should be treated as cloud-hosted exposure and access-path coverage for SD-WAN infrastructure, not direct exploit confirmation by itself.
Rule 1
Cloud-Hosted Cisco SD-WAN Control-Plane or NETCONF Access From Unapproved Source
Rule Format
Azure detection rule suitable for Microsoft Sentinel, Log Analytics, Azure Monitor, SIEM-forwarded Azure telemetry, or CSPM/SIEM correlation after NSG Flow Log validation, Azure Firewall validation, SD-WAN asset tagging, NETCONF exposure validation, approved-source baselining, and environment-specific tuning.
Detection Purpose
· Detect access to Azure-hosted Cisco SD-WAN Controller, Manager, or NETCONF-exposed infrastructure from unknown, newly observed, external, or unapproved sources.
· Identify suspicious inbound paths to SD-WAN control-plane or management-plane services.
· Prioritize traffic involving unfamiliar source IPs, unusual geographies, unusual ASNs, cloud or VPN egress, hosting providers, unmanaged networks, or sources not aligned with approved SD-WAN administration.
· Support investigation of exploited SD-WAN control-plane trust abuse without relying on CVE-string matches, scanner output, advisory references, payload visibility, or exploit-specific indicators.
· This rule does not prove successful exploitation, rogue peering, NETCONF misuse, or configuration manipulation without supporting Cisco SD-WAN Controller, Manager, authentication, NETCONF, configuration-audit, topology, or network-flow evidence.
Detection Logic
· Identify inbound traffic to Azure-hosted Cisco SD-WAN Controller, Manager, or NETCONF-exposed infrastructure.
· Prioritize accepted traffic to validated SD-WAN control-plane ports or TCP port 830 from sources not present in approved peer, administrative, service-provider, automation, or emergency-access baselines.
· Increase confidence when the source is newly observed, geographically unusual, ASN-unusual, VPN-associated, cloud-hosted, hosting-provider-associated, unmanaged, or associated with a provider type not normally used for SD-WAN administration.
· Increase confidence when the source communicates with multiple SD-WAN virtual machines, network interfaces, public IPs, load balancers, application gateways, or subnets within the same operational window.
· Increase confidence when inbound access is followed by SD-WAN authentication, NETCONF activity, configuration change, or post-access traffic-flow change.
· Increase confidence when activity occurs outside approved maintenance, migration, disaster-recovery, service-provider, automation, or emergency-access windows.
· Reduce severity for approved administrative paths, approved service-provider sources, expected controller relationships, planned migrations, approved edge onboarding, and documented emergency access.
· Do not classify inbound control-plane or NETCONF traffic as compromise without corroborating peer-state, authentication, NETCONF, configuration, topology, or change-management evidence.
Required Telemetry
· NSG Flow Logs.
· Azure Firewall logs where applicable.
· Application Gateway logs where applicable.
· Load balancer and public IP mapping context where available.
· Azure Monitor logs.
· Log Analytics workspace data.
· Microsoft Sentinel data tables where available.
· Network security group metadata.
· Route table metadata.
· Virtual network and subnet metadata.
· Virtual machine tags.
· Network interface tags.
· Public IP and private IP mappings.
· Source IP.
· Destination IP.
· Destination port.
· Protocol.
· Flow action.
· Timestamp.
· Packet count and byte count where available.
· Approved SD-WAN asset inventory.
· Approved administrative source baselines.
· Approved service-provider source baselines.
· Approved NETCONF source baselines.
· GeoIP, ASN, VPN, cloud-provider, and hosting-provider enrichment.
· Maintenance-window and change-management context.
· Cisco SD-WAN Controller, Manager, authentication, NETCONF, and configuration-audit correlation where available.
Engineering Implementation Instructions
· Tag Azure-hosted Cisco SD-WAN Controller, Manager, and NETCONF-exposed infrastructure using consistent asset tags.
· Validate the Azure subscriptions, resource groups, virtual networks, subnets, network interfaces, public IPs, private IPs, load balancers, and application gateways that host or front SD-WAN infrastructure.
· Validate the SD-WAN control-plane ports used by the organization before enabling high-severity alerting.
· Validate whether NETCONF is exposed and which administrative sources are approved.
· Build approved source lists for SD-WAN peers, administrative VPN paths, service-provider paths, automation sources, emergency-access paths, and management networks.
· Add enrichment for source first-seen status, geography, ASN, cloud provider, VPN provider, hosting provider, and managed-service context.
· Correlate suspicious Azure network telemetry with Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, and NDR telemetry.
· Avoid broad suppression for cloud, VPN, hosting, managed-service, or service-provider infrastructure because attacker and legitimate administrative paths may overlap.
· Treat this rule as higher priority when access is followed by authentication, NETCONF activity, SD-WAN configuration changes, or new traffic-flow behavior.
· Use change-management and maintenance records to distinguish approved Azure-hosted SD-WAN operations from suspicious access.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to suspicious access toward cloud-hosted SD-WAN control-plane or NETCONF services rather than static exploit indicators.
· The rule remains useful if exploit delivery changes but the attacker still needs to access Azure-hosted SD-WAN infrastructure.
· The score is supported by durable source, destination, port, protocol, timing, asset, and approval-context relationships.
· The score is constrained by legitimate service-provider access, cloud-hosted administration, emergency access, controller migration, incomplete asset tagging, and incomplete approved-source baselines.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on NSG Flow Log coverage, Azure Firewall coverage, SD-WAN asset tagging, public IP mapping, approved-source baselines, log delivery quality, and maintenance-window context.
· Operational confidence is reduced where SD-WAN infrastructure is not consistently tagged, where public IP ownership is unclear, or where approved administrative paths are poorly documented.
· Full-telemetry confidence improves when Azure network telemetry is correlated with Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, NDR telemetry, and change-management context.
· Even under full telemetry conditions, this rule should support escalation and investigation rather than standalone confirmation of successful exploitation.
Limitations
· This rule detects suspicious Azure network access to SD-WAN infrastructure, not successful exploitation.
· NSG Flow Logs and Azure Firewall logs generally do not provide SD-WAN peer-state context or configuration intent.
· Legitimate administration, service-provider support, automation, maintenance, controller migration, and emergency access may overlap with the same network patterns.
· The rule requires accurate SD-WAN asset tagging, approved-source baselines, and control-plane service validation.
· Confirmation requires correlation with Cisco SD-WAN peer-state anomalies, administrative authentication, NETCONF access, configuration changes, topology mismatch, or post-access fabric-impact evidence.
Detection Query Pattern
Azure KQL-style detection pattern requiring NSG Flow Log validation, Azure Firewall validation, SD-WAN asset tagging, approved-source validation, port validation, source-enrichment validation, and environment-specific tuning before production deployment.
AzureNetworkTelemetry
| where DestinationIp in (
ASSET_GROUP_AZURE_HOSTED_CISCO_SDWAN_CONTROLLERS,
ASSET_GROUP_AZURE_HOSTED_CISCO_SDWAN_MANAGERS,
ASSET_GROUP_AZURE_HOSTED_NETCONF_EXPOSED_SDWAN_INFRASTRUCTURE
)
| where FlowAction == "Allow"
| where DestinationPort in (ENV_CISCO_SDWAN_CONTROL_PLANE_PORTS)
or DestinationPort == 830
| where SourceApprovalStatus in (
"unapproved",
"unknown"
)
or SourceFirstSeenWithin == "ENV_NEW_SOURCE_WINDOW"
or SourceProviderType in (
"cloud_hosting",
"vpn_provider",
"hosting_provider",
"unknown_external"
)
or SourceGeoApprovalStatus in (
"unapproved",
"unknown"
)
or SourceAsnApprovalStatus in (
"unapproved",
"unknown"
)
| where ChangeContext !in (
"approved_sdwan_maintenance",
"approved_controller_migration",
"approved_edge_onboarding",
"approved_disaster_recovery",
"approved_service_provider_activity",
"approved_emergency_access"
)
| summarize
ConnectionCount = count(),
FirstSeen = min(TimeGenerated),
LastSeen = max(TimeGenerated)
by
SubscriptionId,
ResourceGroup,
VNetId,
SubnetId,
NetworkInterfaceId,
SourceIp,
DestinationIp,
DestinationPort,
Protocol,
FlowAction
| where ConnectionCount >= ENV_AZURE_SDWAN_ACCESS_THRESHOLD
Rule 2
Azure Network Security or Routing Change Exposing Cisco SD-WAN Infrastructure
Rule Format
Azure Activity Log / Microsoft Sentinel / SIEM correlation rule suitable for detecting cloud-network exposure changes after Activity Log validation, NSG and route-table parsing validation, SD-WAN asset tagging, change-approval validation, and environment-specific tuning.
Detection Purpose
· Detect Azure network security group, route table, firewall policy, load balancer, application gateway, or public IP exposure changes that permit new inbound access to Cisco SD-WAN Controller, Manager, or NETCONF-exposed infrastructure.
· Identify cloud-network changes that may increase SD-WAN control-plane or management-plane exposure.
· Prioritize changes involving public ingress, broad CIDR ranges, unfamiliar source ranges, SD-WAN control-plane ports, NETCONF, administrative access paths, or unapproved change actors.
· Support investigation of exposure changes that could enable or support SD-WAN control-plane abuse.
· This rule does not prove successful exploitation without supporting access, authentication, NETCONF, configuration, topology, or SD-WAN Controller evidence.
Detection Logic
· Identify Azure Activity Log events that modify network security groups, security rules, route tables, firewall policies, load balancers, application gateways, public IP associations, or network interfaces affecting Azure-hosted Cisco SD-WAN infrastructure.
· Prioritize changes that permit inbound access to SD-WAN control-plane ports or TCP port 830 from public, broad, unknown, or unapproved source ranges.
· Increase confidence when the changed resource is attached to a tagged SD-WAN Controller, Manager, load balancer, application gateway, network interface, subnet, route table, firewall policy, or security boundary.
· Increase confidence when the actor, role, source IP, service principal, managed identity, automation context, or change approval context is unknown, unapproved, newly observed, or outside normal change workflows.
· Increase confidence when exposure change is followed by inbound access to SD-WAN infrastructure, administrative authentication, NETCONF activity, or SD-WAN configuration changes.
· Reduce severity for approved maintenance, approved migration, approved disaster recovery, service-provider activity, emergency access, and documented network security or firewall policy changes.
· Do not classify an exposure change as compromise without corroborating suspicious access, authentication, NETCONF, configuration change, or SD-WAN fabric-impact evidence.
Required Telemetry
· Azure Activity Logs.
· Azure Resource Manager operation logs.
· Network security group rule change events.
· Route table change events where applicable.
· Azure Firewall policy change events where applicable.
· Load balancer rule change events where applicable.
· Application Gateway listener and routing rule change events where applicable.
· Public IP association events where applicable.
· Actor identity.
· Service principal or managed identity context.
· Source IP.
· Subscription ID.
· Resource group.
· Resource ID.
· Network security group ID.
· Security rule name.
· Route table ID.
· Firewall policy ID.
· Load balancer ID where applicable.
· Application Gateway ID where applicable.
· Changed port.
· Changed protocol.
· Changed source CIDR.
· Changed action.
· SD-WAN asset tags.
· Approved change-management records.
· Approved automation records.
· Approved service-provider records.
· Approved emergency-access records.
· Maintenance-window context.
Engineering Implementation Instructions
· Identify all Azure resources that expose or protect Cisco SD-WAN Controller, Manager, and NETCONF-exposed infrastructure.
· Tag network security groups, security rules, route tables, load balancers, application gateways, public IPs, network interfaces, subnets, and firewall policies associated with SD-WAN infrastructure.
· Validate Azure Activity Log and Azure Resource Manager operation coverage for Microsoft.Network, Microsoft.Compute, Microsoft.Authorization, and related control-plane events.
· Build approved change-context enrichment for network security group changes, route changes, firewall policy changes, load balancer rule changes, application gateway listener changes, public IP changes, and emergency access.
· Build approved actor lists for SD-WAN administrators, cloud network administrators, automation identities, service-provider identities, and emergency-access identities.
· Tune logic for approved maintenance, controller migration, edge onboarding, policy deployment, provider work, and disaster recovery.
· Avoid suppressing all automation-identity activity because automation credentials may be abused or used outside approved workflows.
· Correlate exposure changes with NSG Flow Logs, Azure Firewall logs, Cisco SD-WAN logs, authentication records, NETCONF records, configuration audit logs, and NDR telemetry.
· Elevate severity when exposure change is followed by accepted inbound access from unfamiliar or unapproved sources.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to cloud-network exposure changes affecting SD-WAN infrastructure.
· The rule remains useful if exploit delivery changes but attackers or misused credentials create or benefit from exposed SD-WAN control-plane or management paths.
· The score is supported by the durability of network security group, route table, firewall policy, load balancer, application gateway, and public IP changes as observable Azure control-plane events.
· The score is constrained by legitimate maintenance, migration, automation, provider work, emergency access, and incomplete tagging of SD-WAN-related Azure resources.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on Activity Log coverage, asset tagging, resource relationship mapping, approved change context, actor identity context, and maintenance-window data.
· Operational confidence is reduced where SD-WAN resource tagging is incomplete, where cloud-network ownership is unclear, or where approved automation records are weak.
· Full-telemetry confidence improves when exposure changes are correlated with NSG Flow Logs, Azure Firewall logs, Cisco SD-WAN logs, authentication records, NETCONF records, configuration audit logs, and change-management records.
· Even under full telemetry conditions, this rule detects exposure and access-path risk rather than confirmed exploitation by itself.
Limitations
· This rule detects exposure changes affecting Azure-hosted SD-WAN infrastructure, not successful exploitation.
· Legitimate cloud-network maintenance, service-provider work, disaster recovery, migrations, and emergency changes may overlap with this behavior.
· Azure Activity Logs may show that access was permitted but not whether SD-WAN trust was established.
· Missing asset tags or incomplete resource relationship mapping can reduce detection reliability.
· Confirmation requires correlation with accepted traffic, SD-WAN peer-state anomalies, administrative authentication, NETCONF access, configuration changes, or fabric-impact evidence.
Detection Query Pattern
Azure Activity Log / Sentinel KQL-style detection pattern requiring Activity Log validation, SD-WAN resource tagging, network security group and route-table parsing validation, approval-context enrichment, and environment-specific tuning before production deployment.
AzureActivity
| where OperationNameValue in (
"Microsoft.Network/networkSecurityGroups/securityRules/write",
"Microsoft.Network/networkSecurityGroups/write",
"Microsoft.Network/routeTables/routes/write",
"Microsoft.Network/routeTables/write",
"Microsoft.Network/azureFirewalls/write",
"Microsoft.Network/firewallPolicies/write",
"Microsoft.Network/loadBalancers/write",
"Microsoft.Network/applicationGateways/write",
"Microsoft.Network/publicIPAddresses/write",
"Microsoft.Network/networkInterfaces/write"
)
| where AffectedResource in (
ASSET_GROUP_AZURE_HOSTED_CISCO_SDWAN_CONTROLLERS,
ASSET_GROUP_AZURE_HOSTED_CISCO_SDWAN_MANAGERS,
ASSET_GROUP_AZURE_HOSTED_NETCONF_EXPOSED_SDWAN_INFRASTRUCTURE,
ASSET_GROUP_AZURE_SDWAN_NETWORK_SECURITY_GROUPS,
ASSET_GROUP_AZURE_SDWAN_ROUTE_TABLES,
ASSET_GROUP_AZURE_SDWAN_LOAD_BALANCERS,
ASSET_GROUP_AZURE_SDWAN_APPLICATION_GATEWAYS,
ASSET_GROUP_AZURE_SDWAN_FIREWALL_POLICIES
)
| where ChangedPort in (ENV_CISCO_SDWAN_CONTROL_PLANE_PORTS)
or ChangedPort == 830
or ChangedPort in (ENV_SDWAN_ADMIN_PORTS)
| where ChangedSourceCidr in (
"0.0.0.0/0",
"::/0"
)
or ChangedSourceApprovalStatus in (
"unapproved",
"unknown"
)
or ActorApprovalStatus in (
"unapproved",
"unknown"
)
or ChangeApprovalStatus in (
"unapproved",
"unknown",
"missing"
)
| where ChangeContext !in (
"approved_sdwan_maintenance",
"approved_controller_migration",
"approved_edge_onboarding",
"approved_disaster_recovery",
"approved_service_provider_activity",
"approved_emergency_access",
"approved_cloud_network_change"
)
| project
TimeGenerated,
SubscriptionId,
ResourceGroup,
OperationNameValue,
Caller,
CallerIpAddress,
AffectedResource,
ChangedPort,
ChangedProtocol,
ChangedSourceCidr,
ChangedAction,
ChangeApprovalStatus,
ActorApprovalStatus,
ChangeContext
Rule 3
Post-Access Azure Traffic Change From Cisco SD-WAN Infrastructure
Rule Format
Azure network-behavior correlation rule suitable for NSG Flow Logs, Azure Firewall logs, Microsoft Sentinel, Log Analytics, Azure Monitor, or SIEM-forwarded telemetry after SD-WAN asset tagging, destination-baseline validation, sensitive-segment tagging, timing-window validation, and environment-specific tuning.
Detection Purpose
· Detect new or unusual Azure network traffic from Cisco SD-WAN infrastructure after suspicious control-plane, NETCONF, administrative, or exposure-change activity.
· Identify possible post-access behavior involving new destinations, sensitive internal segments, management systems, cloud workloads, peered virtual networks, or recurring external infrastructure.
· Prioritize traffic from SD-WAN infrastructure to destinations not normally associated with approved management, monitoring, backup, service-provider, update, or automation workflows.
· Support investigation of possible SD-WAN fabric-impact or persistence behavior without assuming Azure network telemetry alone confirms compromise.
· This rule does not prove successful exploitation or SD-WAN fabric manipulation without supporting Cisco SD-WAN Controller, Manager, authentication, NETCONF, configuration-audit, topology, or NDR evidence.
Detection Logic
· Identify suspicious access, NETCONF activity, or exposure-change context involving Azure-hosted Cisco SD-WAN infrastructure.
· Detect new, unusual, or baseline-deviating traffic from SD-WAN infrastructure after the suspicious access or exposure-change window.
· Prioritize flows to sensitive Azure workloads, identity systems, management systems, monitoring systems, backup systems, network-administration systems, peered virtual networks, VPN paths, ExpressRoute paths, or unfamiliar external destinations.
· Increase confidence when the destination is first-seen, not approved, associated with cloud or hosting infrastructure, or not part of expected SD-WAN management, logging, monitoring, backup, update, automation, or service-provider workflows.
· Increase confidence when traffic-flow changes align with Cisco SD-WAN route, tunnel, policy, certificate, peer-state, or fabric-trust changes.
· Increase confidence when new traffic persists across multiple sessions or recurs after rollback, restart, patching, or remediation.
· Reduce severity for approved routing changes, tunnel changes, virtual network connectivity changes, peering changes, monitoring, backup, update, service-provider maintenance, automation, and emergency workflows.
· Do not classify post-access Azure traffic-flow change as compromise without corroborating source, timing, topology, authorization, and SD-WAN configuration-change evidence.
Required Telemetry
· NSG Flow Logs.
· Azure Firewall logs where applicable.
· Application Gateway logs where applicable.
· Load balancer and public IP mapping context where available.
· Azure Monitor logs.
· Log Analytics workspace data.
· Microsoft Sentinel data tables where available.
· Route table metadata.
· Virtual network and subnet metadata.
· Virtual network peering metadata where applicable.
· VPN Gateway and ExpressRoute metadata where applicable.
· Virtual machine tags.
· Network interface tags.
· Source IP.
· Destination IP.
· Destination port.
· Protocol.
· Flow action.
· Timestamp.
· Packet count and byte count where available.
· First-seen destination context.
· Destination approval status.
· Sensitive asset tags.
· Approved SD-WAN traffic baselines.
· Approved destination baselines.
· Change-management context.
· Cisco SD-WAN configuration audit correlation where available.
· NDR correlation where available.
Engineering Implementation Instructions
· Build asset groups for Azure-hosted Cisco SD-WAN infrastructure, sensitive Azure workloads, management systems, identity systems, monitoring systems, backup systems, network-administration systems, peered virtual networks, VPN gateways, ExpressRoute paths, and external destination categories.
· Establish baselines for normal SD-WAN-related traffic flows, expected Azure management traffic, expected monitoring and logging traffic, expected backup traffic, expected update traffic, service-provider traffic, and expected virtual network or ExpressRoute paths.
· Correlate suspicious SD-WAN access, NETCONF activity, or exposure changes with subsequent first-seen or abnormal source-to-destination traffic.
· Tune timing windows to account for immediate configuration impact and delayed traffic-flow changes after policy deployment, route propagation, or cloud-network change propagation.
· Add allowlists for approved route changes, tunnel changes, policy changes, monitoring, backup, update, service-provider maintenance, automation, disaster recovery, and emergency access.
· Avoid broad suppression of new flows from SD-WAN environments because SD-WAN fabric compromise may create traffic that resembles legitimate route or policy changes.
· Increase severity when new traffic targets sensitive Azure workloads or creates new reachability between previously unrelated environments.
· Use Cisco SD-WAN configuration audit logs, NDR telemetry, Azure Activity Logs, and change-management records to determine whether the traffic change was authorized.
DRI Assessment
DRI
7.5 / 10
· The rule is behaviorally anchored to post-access traffic-flow changes from Azure-hosted SD-WAN infrastructure.
· The rule remains useful if exploit implementation changes but attacker activity creates new outbound, lateral, or recurring communication paths from SD-WAN infrastructure.
· The score is supported by durable first-seen destination, unusual traffic path, sensitive-destination, and post-access timing relationships.
· The score is constrained by legitimate routing, tunnel, virtual network, peering, VPN, ExpressRoute, monitoring, backup, update, provider, automation, and emergency-access changes.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on NSG Flow Log coverage, Azure Firewall coverage, SD-WAN asset tagging, destination baselines, sensitive-asset tagging, virtual network relationship mapping, and change-management linkage.
· Operational confidence is reduced where Azure traffic baselines are immature, where sensitive-asset tagging is incomplete, or where SD-WAN-related traffic paths frequently change.
· Full-telemetry confidence improves when Azure traffic changes are correlated with Cisco SD-WAN configuration audit logs, peer-state changes, authentication records, NETCONF activity, NDR telemetry, Azure Activity Logs, and change-management context.
· Even under full telemetry conditions, traffic-flow change should be treated as impact-supporting evidence rather than standalone proof of exploitation.
Limitations
· This rule detects suspicious Azure traffic-flow change after suspicious access or exposure context, not exploit execution.
· Legitimate route, tunnel, policy, virtual network, peering, VPN, ExpressRoute, service-provider, disaster-recovery, automation, and emergency changes may overlap with the same behavior.
· Azure network telemetry may not show SD-WAN peer-state context, NETCONF command content, or configuration intent.
· Incomplete destination baselines or sensitive-asset tagging may increase false positives.
· Confirmation requires correlation with suspicious control-plane activity, NETCONF access, SD-WAN configuration changes, topology mismatch, unauthorized change context, or fabric-impact evidence.
Detection Query Pattern
Azure network-behavior KQL-style query pattern requiring NSG Flow Log validation, Azure Firewall validation, SD-WAN asset tagging, sensitive-asset tagging, flow-baseline validation, change-context validation, timing-window tuning, SIEM correlation fields, and environment-specific allowlisting before production deployment.
AzureNetworkTelemetry
| where SourceIp in (
ASSET_GROUP_AZURE_HOSTED_CISCO_SDWAN_CONTROLLERS,
ASSET_GROUP_AZURE_HOSTED_CISCO_SDWAN_MANAGERS,
ASSET_GROUP_AZURE_HOSTED_NETCONF_EXPOSED_SDWAN_INFRASTRUCTURE
)
| where FlowAction == "Allow"
| where CorrelationContext in (
"suspicious_sdwan_control_plane_access",
"suspicious_netconf_access",
"sdwan_exposure_change",
"suspicious_sdwan_admin_authentication",
"sdwan_configuration_change"
)
| where DestinationFirstSeenWithin == "ENV_NEW_DESTINATION_WINDOW"
or DestinationApprovalStatus in (
"unapproved",
"unknown"
)
or DestinationAsset in (
ASSET_GROUP_AZURE_IDENTITY_SYSTEMS,
ASSET_GROUP_AZURE_MANAGEMENT_SYSTEMS,
ASSET_GROUP_AZURE_MONITORING_SYSTEMS,
ASSET_GROUP_AZURE_BACKUP_SYSTEMS,
ASSET_GROUP_AZURE_NETWORK_ADMINISTRATION_SYSTEMS,
ASSET_GROUP_SENSITIVE_AZURE_WORKLOADS,
ASSET_GROUP_CRITICAL_AZURE_DATA_SYSTEMS,
ASSET_GROUP_PEERED_VNET_SENSITIVE_SEGMENTS,
ASSET_GROUP_EXPRESSROUTE_SENSITIVE_ROUTES
)
or SourceToDestinationPairStatus in (
"new",
"rare",
"baseline_deviation"
)
| where ChangeContext !in (
"approved_route_change",
"approved_tunnel_change",
"approved_policy_deployment",
"approved_vnet_change",
"approved_vnet_peering_change",
"approved_expressroute_change",
"approved_monitoring_workflow",
"approved_backup_workflow",
"approved_update_workflow",
"approved_service_provider_activity",
"approved_emergency_change"
)
| summarize
ConnectionCount = count(),
FirstSeen = min(TimeGenerated),
LastSeen = max(TimeGenerated)
by
SubscriptionId,
ResourceGroup,
VNetId,
SubnetId,
NetworkInterfaceId,
SourceIp,
DestinationIp,
DestinationPort,
Protocol,
FlowAction
| where ConnectionCount >= ENV_AZURE_POST_ACCESS_FLOW_THRESHOLD
GCP
Detection Viability Assessment
GCP has three rules for this EXP report.
· GCP is viable when Cisco SD-WAN Controller, Manager, or supporting infrastructure is hosted in Google Cloud or when GCP network telemetry observes access paths to SD-WAN infrastructure.
· GCP is strongest where VPC Flow Logs, Cloud Audit Logs, firewall rule changes, route changes, forwarding-rule changes, load balancer logs, Cloud NAT logs, Security Command Center findings, asset tags, approved administrative-source baselines, and change-management context are available.
· GCP can support detection of cloud-hosted SD-WAN exposure, suspicious inbound access, NETCONF access, cloud-network policy changes, and post-access traffic-flow changes affecting SD-WAN infrastructure.
· GCP should not be treated as a standalone source for confirming successful CVE-2026-20182 exploitation because GCP telemetry generally observes cloud-network access, exposure, and infrastructure-change behavior rather than Cisco SD-WAN peer-state or configuration intent.
· GCP rules should be correlated with Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, topology inventory, NDR telemetry, and change-management context before classifying activity as confirmed compromise.
· GCP detection content should be treated as cloud-hosted exposure and access-path coverage for SD-WAN infrastructure, not direct exploit confirmation by itself.
Rule 1
Cloud-Hosted Cisco SD-WAN Control-Plane or NETCONF Access From Unapproved Source
Rule Format
GCP detection rule suitable for Cloud Logging, BigQuery-exported VPC Flow Logs, Chronicle, Security Command Center, or SIEM-forwarded GCP telemetry after VPC Flow Log validation, firewall rule validation, SD-WAN asset tagging, NETCONF exposure validation, approved-source baselining, and environment-specific tuning.
Detection Purpose
· Detect access to GCP-hosted Cisco SD-WAN Controller, Manager, or NETCONF-exposed infrastructure from unknown, newly observed, external, or unapproved sources.
· Identify suspicious inbound paths to SD-WAN control-plane or management-plane services.
· Prioritize traffic involving unfamiliar source IPs, unusual geographies, unusual ASNs, cloud or VPN egress, hosting providers, unmanaged networks, or sources not aligned with approved SD-WAN administration.
· Support investigation of exploited SD-WAN control-plane trust abuse without relying on CVE-string matches, scanner output, advisory references, payload visibility, or exploit-specific indicators.
· This rule does not prove successful exploitation, rogue peering, NETCONF misuse, or configuration manipulation without supporting Cisco SD-WAN Controller, Manager, authentication, NETCONF, configuration-audit, topology, or network-flow evidence.
Detection Logic
· Identify inbound traffic to GCP-hosted Cisco SD-WAN Controller, Manager, or NETCONF-exposed infrastructure.
· Prioritize accepted traffic to validated SD-WAN control-plane ports or TCP port 830 from sources not present in approved peer, administrative, service-provider, automation, or emergency-access baselines.
· Increase confidence when the source is newly observed, geographically unusual, ASN-unusual, VPN-associated, cloud-hosted, hosting-provider-associated, unmanaged, or associated with a provider type not normally used for SD-WAN administration.
· Increase confidence when the source communicates with multiple SD-WAN virtual machines, network interfaces, forwarding rules, public IPs, load balancers, or subnets within the same operational window.
· Increase confidence when inbound access is followed by SD-WAN authentication, NETCONF activity, configuration change, or post-access traffic-flow change.
· Increase confidence when activity occurs outside approved maintenance, migration, disaster-recovery, service-provider, automation, or emergency-access windows.
· Reduce severity for approved administrative paths, approved service-provider sources, expected controller relationships, planned migrations, approved edge onboarding, and documented emergency access.
· Do not classify inbound control-plane or NETCONF traffic as compromise without corroborating peer-state, authentication, NETCONF, configuration, topology, or change-management evidence.
Required Telemetry
· VPC Flow Logs.
· Cloud Logging records.
· BigQuery-exported network telemetry where available.
· Cloud Firewall logging where applicable.
· Cloud Load Balancing logs where applicable.
· Cloud NAT logs where applicable.
· Cloud Armor logs where applicable.
· VPC firewall rule metadata.
· Route table metadata.
· VPC and subnet metadata.
· Compute Engine instance tags.
· Network interface tags.
· Public IP and private IP mappings.
· Source IP.
· Destination IP.
· Destination port.
· Protocol.
· Flow disposition or action.
· Timestamp.
· Packet count and byte count where available.
· Approved SD-WAN asset inventory.
· Approved administrative source baselines.
· Approved service-provider source baselines.
· Approved NETCONF source baselines.
· GeoIP, ASN, VPN, cloud-provider, and hosting-provider enrichment.
· Maintenance-window and change-management context.
· Cisco SD-WAN Controller, Manager, authentication, NETCONF, and configuration-audit correlation where available.
Engineering Implementation Instructions
· Tag GCP-hosted Cisco SD-WAN Controller, Manager, and NETCONF-exposed infrastructure using consistent asset tags.
· Validate the GCP projects, folders, VPC networks, subnets, network interfaces, public IPs, private IPs, forwarding rules, and load balancers that host or front SD-WAN infrastructure.
· Validate the SD-WAN control-plane ports used by the organization before enabling high-severity alerting.
· Validate whether NETCONF is exposed and which administrative sources are approved.
· Build approved source lists for SD-WAN peers, administrative VPN paths, service-provider paths, automation sources, emergency-access paths, and management networks.
· Add enrichment for source first-seen status, geography, ASN, cloud provider, VPN provider, hosting provider, and managed-service context.
· Correlate suspicious GCP network telemetry with Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, and NDR telemetry.
· Avoid broad suppression for cloud, VPN, hosting, managed-service, or service-provider infrastructure because attacker and legitimate administrative paths may overlap.
· Treat this rule as higher priority when access is followed by authentication, NETCONF activity, SD-WAN configuration changes, or new traffic-flow behavior.
· Use change-management and maintenance records to distinguish approved GCP-hosted SD-WAN operations from suspicious access.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to suspicious access toward cloud-hosted SD-WAN control-plane or NETCONF services rather than static exploit indicators.
· The rule remains useful if exploit delivery changes but the attacker still needs to access GCP-hosted SD-WAN infrastructure.
· The score is supported by durable source, destination, port, protocol, timing, asset, and approval-context relationships.
· The score is constrained by legitimate service-provider access, cloud-hosted administration, emergency access, controller migration, incomplete asset tagging, and incomplete approved-source baselines.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on VPC Flow Log coverage, firewall logging coverage, SD-WAN asset tagging, public IP mapping, approved-source baselines, log delivery quality, and maintenance-window context.
· Operational confidence is reduced where SD-WAN infrastructure is not consistently tagged, where public IP ownership is unclear, or where approved administrative paths are poorly documented.
· Full-telemetry confidence improves when GCP network telemetry is correlated with Cisco SD-WAN Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, NDR telemetry, and change-management context.
· Even under full telemetry conditions, this rule should support escalation and investigation rather than standalone confirmation of successful exploitation.
Limitations
· This rule detects suspicious GCP network access to SD-WAN infrastructure, not successful exploitation.
· VPC Flow Logs and firewall logs generally do not provide SD-WAN peer-state context or configuration intent.
· Legitimate administration, service-provider support, automation, maintenance, controller migration, and emergency access may overlap with the same network patterns.
· The rule requires accurate SD-WAN asset tagging, approved-source baselines, and control-plane service validation.
· Confirmation requires correlation with Cisco SD-WAN peer-state anomalies, administrative authentication, NETCONF access, configuration changes, topology mismatch, or post-access fabric-impact evidence.
Detection Query Pattern
GCP BigQuery / Cloud Logging / SIEM-style detection pattern requiring VPC Flow Log validation, firewall logging validation, SD-WAN asset tagging, approved-source validation, port validation, source-enrichment validation, and environment-specific tuning before production deployment.
SELECT
project_id,
region,
vpc_name,
subnet_name,
instance_id,
src_ip,
dest_ip,
dest_port,
protocol,
disposition,
COUNT(*) AS connection_count,
MIN(timestamp) AS first_seen,
MAX(timestamp) AS last_seen
FROM gcp_network_telemetry
WHERE dest_ip IN ASSET_GROUP(
'GCP Hosted Cisco SD-WAN Controllers',
'GCP Hosted Cisco SD-WAN Managers',
'GCP Hosted NETCONF Exposed SD-WAN Infrastructure'
)
AND disposition IN (
'ALLOWED',
'ACCEPT'
)
AND (
dest_port IN ENV_CISCO_SDWAN_CONTROL_PLANE_PORTS
OR dest_port = 830
)
AND (
source_approval_status IN (
'unapproved',
'unknown'
)
OR source_first_seen_within = 'ENV_NEW_SOURCE_WINDOW'
OR source_provider_type IN (
'cloud_hosting',
'vpn_provider',
'hosting_provider',
'unknown_external'
)
OR source_geo_approval_status IN (
'unapproved',
'unknown'
)
OR source_asn_approval_status IN (
'unapproved',
'unknown'
)
)
AND change_context NOT IN (
'approved_sdwan_maintenance',
'approved_controller_migration',
'approved_edge_onboarding',
'approved_disaster_recovery',
'approved_service_provider_activity',
'approved_emergency_access'
)
GROUP BY
project_id,
region,
vpc_name,
subnet_name,
instance_id,
src_ip,
dest_ip,
dest_port,
protocol,
disposition
HAVING connection_count >= ENV_GCP_SDWAN_ACCESS_THRESHOLD
Rule 2
GCP Firewall, Route, or Load Balancer Change Exposing Cisco SD-WAN Infrastructure
Rule Format
GCP Cloud Audit Logs / Security Command Center / SIEM correlation rule suitable for detecting cloud-network exposure changes after audit-log validation, firewall-rule parsing validation, route-change validation, SD-WAN asset tagging, change-approval validation, and environment-specific tuning.
Detection Purpose
· Detect GCP firewall rule, route, forwarding rule, load balancer, target proxy, backend service, public IP, or network interface changes that permit new inbound access to Cisco SD-WAN Controller, Manager, or NETCONF-exposed infrastructure.
· Identify cloud-network changes that may increase SD-WAN control-plane or management-plane exposure.
· Prioritize changes involving public ingress, broad CIDR ranges, unfamiliar source ranges, SD-WAN control-plane ports, NETCONF, administrative access paths, or unapproved change actors.
· Support investigation of exposure changes that could enable or support SD-WAN control-plane abuse.
· This rule does not prove successful exploitation without supporting access, authentication, NETCONF, configuration, topology, or SD-WAN Controller evidence.
Detection Logic
· Identify Cloud Audit Logs that modify firewall rules, routes, forwarding rules, load balancers, target proxies, backend services, public IP associations, or network interfaces affecting GCP-hosted Cisco SD-WAN infrastructure.
· Prioritize changes that permit inbound access to SD-WAN control-plane ports or TCP port 830 from public, broad, unknown, or unapproved source ranges.
· Increase confidence when the changed resource is attached to a tagged SD-WAN Controller, Manager, load balancer, network interface, subnet, route, forwarding rule, firewall rule, or security boundary.
· Increase confidence when the actor, role, source IP, service account, automation context, or change approval context is unknown, unapproved, newly observed, or outside normal change workflows.
· Increase confidence when exposure change is followed by inbound access to SD-WAN infrastructure, administrative authentication, NETCONF activity, or SD-WAN configuration changes.
· Reduce severity for approved maintenance, approved migration, approved disaster recovery, service-provider activity, emergency access, and documented network security or firewall policy changes.
· Do not classify an exposure change as compromise without corroborating suspicious access, authentication, NETCONF, configuration change, or SD-WAN fabric-impact evidence.
Required Telemetry
· Cloud Audit Logs.
· Admin Activity audit logs.
· Data Access audit logs where applicable.
· VPC firewall rule change events.
· Route change events where applicable.
· Forwarding rule change events where applicable.
· Cloud Load Balancing change events where applicable.
· Cloud NAT change events where applicable.
· Cloud Armor policy change events where applicable.
· Public IP or address association events where applicable.
· Actor identity.
· Service account context.
· Source IP.
· Project ID.
· Folder or organization context where available.
· Region.
· Resource ID.
· Firewall rule ID.
· Route ID.
· Forwarding rule ID.
· Load balancer ID where applicable.
· Backend service ID where applicable.
· Changed port.
· Changed protocol.
· Changed source CIDR.
· Changed action.
· SD-WAN asset tags.
· Approved change-management records.
· Approved automation records.
· Approved service-provider records.
· Approved emergency-access records.
· Maintenance-window context.
Engineering Implementation Instructions
· Identify all GCP resources that expose or protect Cisco SD-WAN Controller, Manager, and NETCONF-exposed infrastructure.
· Tag firewall rules, routes, forwarding rules, load balancers, backend services, public IPs, network interfaces, subnets, and security policies associated with SD-WAN infrastructure.
· Validate Cloud Audit Log coverage for Compute Engine, VPC firewall rules, routes, forwarding rules, Cloud Load Balancing, Cloud NAT, Cloud Armor, IAM, and related control-plane events.
· Build approved change-context enrichment for firewall rule changes, route changes, forwarding rule changes, load balancer changes, public IP changes, security policy changes, and emergency access.
· Build approved actor lists for SD-WAN administrators, cloud network administrators, automation service accounts, service-provider identities, and emergency-access identities.
· Tune logic for approved maintenance, controller migration, edge onboarding, policy deployment, provider work, and disaster recovery.
· Avoid suppressing all automation or service-account activity because automation credentials may be abused or used outside approved workflows.
· Correlate exposure changes with VPC Flow Logs, firewall logs, Cisco SD-WAN logs, authentication records, NETCONF records, configuration audit logs, and NDR telemetry.
· Elevate severity when exposure change is followed by accepted inbound access from unfamiliar or unapproved sources.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to cloud-network exposure changes affecting SD-WAN infrastructure.
· The rule remains useful if exploit delivery changes but attackers or misused credentials create or benefit from exposed SD-WAN control-plane or management paths.
· The score is supported by the durability of firewall rule, route, forwarding rule, load balancer, backend service, public IP, and security policy changes as observable GCP control-plane events.
· The score is constrained by legitimate maintenance, migration, automation, provider work, emergency access, and incomplete tagging of SD-WAN-related GCP resources.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on Cloud Audit Log coverage, asset tagging, resource relationship mapping, approved change context, actor identity context, service-account context, and maintenance-window data.
· Operational confidence is reduced where SD-WAN resource tagging is incomplete, where cloud-network ownership is unclear, or where approved automation records are weak.
· Full-telemetry confidence improves when exposure changes are correlated with VPC Flow Logs, firewall logs, Cisco SD-WAN logs, authentication records, NETCONF records, configuration audit logs, and change-management records.
· Even under full telemetry conditions, this rule detects exposure and access-path risk rather than confirmed exploitation by itself.
Limitations
· This rule detects exposure changes affecting GCP-hosted SD-WAN infrastructure, not successful exploitation.
· Legitimate cloud-network maintenance, service-provider work, disaster recovery, migrations, and emergency changes may overlap with this behavior.
· Cloud Audit Logs may show that access was permitted but not whether SD-WAN trust was established.
· Missing asset tags or incomplete resource relationship mapping can reduce detection reliability.
· Confirmation requires correlation with accepted traffic, SD-WAN peer-state anomalies, administrative authentication, NETCONF access, configuration changes, or fabric-impact evidence.
Detection Query Pattern
GCP Cloud Audit Logs / SIEM-style detection pattern requiring audit-log validation, SD-WAN resource tagging, firewall-rule and route-change parsing validation, approval-context enrichment, and environment-specific tuning before production deployment.
SELECT
timestamp,
project_id,
region,
protoPayload.serviceName AS service_name,
protoPayload.methodName AS method_name,
protoPayload.authenticationInfo.principalEmail AS actor,
protoPayload.requestMetadata.callerIp AS caller_ip,
resource_name,
changed_port,
changed_protocol,
changed_source_cidr,
changed_action,
change_approval_status,
actor_approval_status,
change_context
FROM gcp_audit_logs
WHERE protoPayload.methodName IN (
'v1.compute.firewalls.insert',
'v1.compute.firewalls.update',
'v1.compute.firewalls.patch',
'v1.compute.routes.insert',
'v1.compute.routes.patch',
'v1.compute.forwardingRules.insert',
'v1.compute.forwardingRules.patch',
'v1.compute.targetProxies.insert',
'v1.compute.targetProxies.patch',
'v1.compute.backendServices.insert',
'v1.compute.backendServices.patch',
'v1.compute.addresses.insert',
'v1.compute.instances.updateNetworkInterface',
'v1.compute.securityPolicies.patch'
)
AND affected_resource IN ASSET_GROUP(
'GCP Hosted Cisco SD-WAN Controllers',
'GCP Hosted Cisco SD-WAN Managers',
'GCP Hosted NETCONF Exposed SD-WAN Infrastructure',
'GCP SD-WAN Firewall Rules',
'GCP SD-WAN Routes',
'GCP SD-WAN Forwarding Rules',
'GCP SD-WAN Load Balancers',
'GCP SD-WAN Network Interfaces',
'GCP SD-WAN Security Policies'
)
AND (
changed_port IN ENV_CISCO_SDWAN_CONTROL_PLANE_PORTS
OR changed_port = 830
OR changed_port IN ENV_SDWAN_ADMIN_PORTS
)
AND (
changed_source_cidr IN (
'0.0.0.0/0',
'::/0'
)
OR changed_source_approval_status IN (
'unapproved',
'unknown'
)
OR actor_approval_status IN (
'unapproved',
'unknown'
)
OR change_approval_status IN (
'unapproved',
'unknown',
'missing'
)
)
AND change_context NOT IN (
'approved_sdwan_maintenance',
'approved_controller_migration',
'approved_edge_onboarding',
'approved_disaster_recovery',
'approved_service_provider_activity',
'approved_emergency_access',
'approved_cloud_network_change'
)
Rule 3
Post-Access GCP Traffic Change From Cisco SD-WAN Infrastructure
Rule Format
GCP network-behavior correlation rule suitable for VPC Flow Logs, Cloud Logging, BigQuery, Chronicle, Security Command Center, or SIEM-forwarded telemetry after SD-WAN asset tagging, destination-baseline validation, sensitive-segment tagging, timing-window validation, and environment-specific tuning.
Detection Purpose
· Detect new or unusual GCP network traffic from Cisco SD-WAN infrastructure after suspicious control-plane, NETCONF, administrative, or exposure-change activity.
· Identify possible post-access behavior involving new destinations, sensitive internal segments, management systems, cloud workloads, peered VPCs, VPN paths, interconnect paths, or recurring external infrastructure.
· Prioritize traffic from SD-WAN infrastructure to destinations not normally associated with approved management, monitoring, backup, service-provider, update, or automation workflows.
· Support investigation of possible SD-WAN fabric-impact or persistence behavior without assuming GCP network telemetry alone confirms compromise.
· This rule does not prove successful exploitation or SD-WAN fabric manipulation without supporting Cisco SD-WAN Controller, Manager, authentication, NETCONF, configuration-audit, topology, or NDR evidence.
Detection Logic
· Identify suspicious access, NETCONF activity, or exposure-change context involving GCP-hosted Cisco SD-WAN infrastructure.
· Detect new, unusual, or baseline-deviating traffic from SD-WAN infrastructure after the suspicious access or exposure-change window.
· Prioritize flows to sensitive GCP workloads, identity systems, management systems, monitoring systems, backup systems, network-administration systems, peered VPCs, Cloud VPN paths, Cloud Interconnect paths, or unfamiliar external destinations.
· Increase confidence when the destination is first-seen, not approved, associated with cloud or hosting infrastructure, or not part of expected SD-WAN management, logging, monitoring, backup, update, automation, or service-provider workflows.
· Increase confidence when traffic-flow changes align with Cisco SD-WAN route, tunnel, policy, certificate, peer-state, or fabric-trust changes.
· Increase confidence when new traffic persists across multiple sessions or recurs after rollback, restart, patching, or remediation.
· Reduce severity for approved routing changes, tunnel changes, VPC connectivity changes, peering changes, Cloud VPN changes, Cloud Interconnect changes, monitoring, backup, update, service-provider maintenance, automation, and emergency workflows.
· Do not classify post-access GCP traffic-flow change as compromise without corroborating source, timing, topology, authorization, and SD-WAN configuration-change evidence.
Required Telemetry
· VPC Flow Logs.
· Cloud Logging records.
· BigQuery-exported network telemetry where available.
· Cloud Firewall logs where applicable.
· Cloud NAT logs where applicable.
· Cloud Load Balancing logs where applicable.
· Cloud DNS logs where applicable.
· VPC and subnet metadata.
· VPC peering metadata where applicable.
· Cloud VPN metadata where applicable.
· Cloud Interconnect metadata where applicable.
· Compute Engine instance tags.
· Network interface tags.
· Source IP.
· Destination IP.
· Destination port.
· Protocol.
· Flow disposition or action.
· Timestamp.
· Packet count and byte count where available.
· First-seen destination context.
· Destination approval status.
· Sensitive asset tags.
· Approved SD-WAN traffic baselines.
· Approved destination baselines.
· Change-management context.
· Cisco SD-WAN configuration audit correlation where available.
· NDR correlation where available.
Engineering Implementation Instructions
· Build asset groups for GCP-hosted Cisco SD-WAN infrastructure, sensitive GCP workloads, management systems, identity systems, monitoring systems, backup systems, network-administration systems, peered VPCs, Cloud VPN paths, Cloud Interconnect paths, and external destination categories.
· Establish baselines for normal SD-WAN-related traffic flows, expected GCP management traffic, expected monitoring and logging traffic, expected backup traffic, expected update traffic, service-provider traffic, and expected VPC, Cloud VPN, or Cloud Interconnect paths.
· Correlate suspicious SD-WAN access, NETCONF activity, or exposure changes with subsequent first-seen or abnormal source-to-destination traffic.
· Tune timing windows to account for immediate configuration impact and delayed traffic-flow changes after policy deployment, route propagation, or cloud-network change propagation.
· Add allowlists for approved route changes, tunnel changes, policy changes, monitoring, backup, update, service-provider maintenance, automation, disaster recovery, and emergency access.
· Avoid broad suppression of new flows from SD-WAN environments because SD-WAN fabric compromise may create traffic that resembles legitimate route or policy changes.
· Increase severity when new traffic targets sensitive GCP workloads or creates new reachability between previously unrelated environments.
· Use Cisco SD-WAN configuration audit logs, NDR telemetry, Cloud Audit Logs, and change-management records to determine whether the traffic change was authorized.
DRI Assessment
DRI
7.5 / 10
· The rule is behaviorally anchored to post-access traffic-flow changes from GCP-hosted SD-WAN infrastructure.
· The rule remains useful if exploit implementation changes but attacker activity creates new outbound, lateral, or recurring communication paths from SD-WAN infrastructure.
· The score is supported by durable first-seen destination, unusual traffic path, sensitive-destination, and post-access timing relationships.
· The score is constrained by legitimate routing, tunnel, VPC, peering, Cloud VPN, Cloud Interconnect, monitoring, backup, update, provider, automation, and emergency-access changes.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on VPC Flow Log coverage, firewall logging coverage, SD-WAN asset tagging, destination baselines, sensitive-asset tagging, VPC relationship mapping, and change-management linkage.
· Operational confidence is reduced where GCP traffic baselines are immature, where sensitive-asset tagging is incomplete, or where SD-WAN-related traffic paths frequently change.
· Full-telemetry confidence improves when GCP traffic changes are correlated with Cisco SD-WAN configuration audit logs, peer-state changes, authentication records, NETCONF activity, NDR telemetry, Cloud Audit Logs, and change-management context.
· Even under full telemetry conditions, traffic-flow change should be treated as impact-supporting evidence rather than standalone proof of exploitation.
Limitations
· This rule detects suspicious GCP traffic-flow change after suspicious access or exposure context, not exploit execution.
· Legitimate route, tunnel, policy, VPC, peering, Cloud VPN, Cloud Interconnect, service-provider, disaster-recovery, automation, and emergency changes may overlap with the same behavior.
· GCP network telemetry may not show SD-WAN peer-state context, NETCONF command content, or configuration intent.
· Incomplete destination baselines or sensitive-asset tagging may increase false positives.
· Confirmation requires correlation with suspicious control-plane activity, NETCONF access, SD-WAN configuration changes, topology mismatch, unauthorized change context, or fabric-impact evidence.
Detection Query Pattern
GCP network-behavior query pattern requiring VPC Flow Log validation, firewall logging validation, SD-WAN asset tagging, sensitive-asset tagging, flow-baseline validation, change-context validation, timing-window tuning, SIEM correlation fields, and environment-specific allowlisting before production deployment.
SELECT
project_id,
region,
vpc_name,
subnet_name,
instance_id,
src_ip,
dest_ip,
dest_port,
protocol,
disposition,
COUNT(*) AS connection_count,
MIN(timestamp) AS first_seen,
MAX(timestamp) AS last_seen
FROM gcp_network_telemetry
WHERE src_ip IN ASSET_GROUP(
'GCP Hosted Cisco SD-WAN Controllers',
'GCP Hosted Cisco SD-WAN Managers',
'GCP Hosted NETCONF Exposed SD-WAN Infrastructure'
)
AND disposition IN (
'ALLOWED',
'ACCEPT'
)
AND correlation_context IN (
'suspicious_sdwan_control_plane_access',
'suspicious_netconf_access',
'sdwan_exposure_change',
'suspicious_sdwan_admin_authentication',
'sdwan_configuration_change'
)
AND (
destination_first_seen_within = 'ENV_NEW_DESTINATION_WINDOW'
OR destination_approval_status IN (
'unapproved',
'unknown'
)
OR destination_asset IN ASSET_GROUP(
'GCP Identity Systems',
'GCP Management Systems',
'GCP Monitoring Systems',
'GCP Backup Systems',
'GCP Network Administration Systems',
'Sensitive GCP Workloads',
'Critical GCP Data Systems',
'Peered VPC Sensitive Segments',
'Cloud VPN Sensitive Routes',
'Cloud Interconnect Sensitive Routes'
)
OR source_to_destination_pair_status IN (
'new',
'rare',
'baseline_deviation'
)
)
AND change_context NOT IN (
'approved_route_change',
'approved_tunnel_change',
'approved_policy_deployment',
'approved_vpc_change',
'approved_vpc_peering_change',
'approved_cloud_vpn_change',
'approved_cloud_interconnect_change',
'approved_monitoring_workflow',
'approved_backup_workflow',
'approved_update_workflow',
'approved_service_provider_activity',
'approved_emergency_change'
)
GROUP BY
project_id,
region,
vpc_name,
subnet_name,
instance_id,
src_ip,
dest_ip,
dest_port,
protocol,
disposition
HAVING connection_count >= ENV_GCP_POST_ACCESS_FLOW_THRESHOLD
S26 Threat-to-Rule Traceability Matrix
Traceability Purpose
This section maps the report’s behavior-led threat model to the S25 detection-rule set. The purpose is to show how suspicious SD-WAN control-plane behavior, privileged management activity, configuration change, cloud exposure, and post-access impact signals are covered across the selected detection systems.
Traceability Standard
· Direct coverage means the rule detects a primary behavior in the suspected exploitation, access, or post-access chain.
· Supporting coverage means the rule provides access-path visibility, enrichment, correlation context, or impact evidence but does not independently confirm exploitation.
· Non-primary coverage means the system may support investigation but should not be used as a production detection claim for this behavior.
· No single rule or system should be treated as standalone confirmation of CVE-2026-20182 exploitation.
· Confirmation requires correlation across SD-WAN control-plane activity, authentication activity, NETCONF access, configuration changes, topology context, network behavior, and change-management evidence.
Threat Behavior
Suspicious Cisco SD-WAN control-plane or peer activity from an unapproved source.
Direct Rule Coverage
· NDR / Network Behavioral Analytics: Suspicious Cisco SD-WAN Control-Plane or Peering Activity From Unapproved Source.
· Splunk: Suspicious Cisco SD-WAN Peering or Control-Plane Activity From Unapproved Source.
· Elastic: Suspicious Cisco SD-WAN Control-Plane or Peer Activity From Unapproved Source.
· QRadar: Suspicious Cisco SD-WAN Control-Plane or Peer Activity From Unapproved Source.
· SIGMA: Suspicious Cisco SD-WAN Control-Plane or Peer Activity From Unapproved Source.
Supporting Rule Coverage
· AWS: Cloud-Hosted Cisco SD-WAN Control-Plane or NETCONF Access From Unapproved Source.
· Azure: Cloud-Hosted Cisco SD-WAN Control-Plane or NETCONF Access From Unapproved Source.
· GCP: Cloud-Hosted Cisco SD-WAN Control-Plane or NETCONF Access From Unapproved Source.
Traceability Assessment
This behavior is strongly covered across the network, SIEM, and portable detection layers. Cloud rules provide supporting visibility when SD-WAN infrastructure is hosted in or exposed through AWS, Azure, or GCP. This behavior should be treated as suspicious control-plane activity, not confirmed exploitation, unless it is paired with peer-state anomaly, administrative authentication, NETCONF access, configuration change, topology mismatch, or fabric-impact evidence.
Threat Behavior
Unexpected or unauthorized SD-WAN peer identity, topology relationship, or control-plane trust relationship.
Direct Rule Coverage
· NDR / Network Behavioral Analytics: Suspicious Cisco SD-WAN Control-Plane or Peering Activity From Unapproved Source.
· Splunk: Suspicious Cisco SD-WAN Peering or Control-Plane Activity From Unapproved Source.
· Elastic: Suspicious Cisco SD-WAN Control-Plane or Peer Activity From Unapproved Source.
· QRadar: Suspicious Cisco SD-WAN Control-Plane or Peer Activity From Unapproved Source.
· SIGMA: Suspicious Cisco SD-WAN Control-Plane or Peer Activity From Unapproved Source.
Supporting Rule Coverage
· AWS: Cloud-Hosted Cisco SD-WAN Control-Plane or NETCONF Access From Unapproved Source.
· Azure: Cloud-Hosted Cisco SD-WAN Control-Plane or NETCONF Access From Unapproved Source.
· GCP: Cloud-Hosted Cisco SD-WAN Control-Plane or NETCONF Access From Unapproved Source.
Traceability Assessment
Peer-identity and topology mismatch are high-value detection anchors because they are closer to SD-WAN trust abuse than generic network access. The strongest coverage depends on comparing observed peer behavior against approved topology, System IP, site ID, domain ID, controller relationship, and approved peer inventory. Cloud telemetry supports this behavior when it shows suspicious access paths into hosted SD-WAN infrastructure, but it does not replace appliance or controller-side peer-state evidence.
Threat Behavior
Cisco SD-WAN control-plane activity followed by NETCONF access or administrative authentication.
Direct Rule Coverage
· NDR / Network Behavioral Analytics: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
· Splunk: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
· Elastic: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
· QRadar: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
· SIGMA: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
Supporting Rule Coverage
· AWS: Cloud-Hosted Cisco SD-WAN Control-Plane or NETCONF Access From Unapproved Source.
· Azure: Cloud-Hosted Cisco SD-WAN Control-Plane or NETCONF Access From Unapproved Source.
· GCP: Cloud-Hosted Cisco SD-WAN Control-Plane or NETCONF Access From Unapproved Source.
Traceability Assessment
This is one of the strongest behavioral sequences in the report because it links suspicious control-plane interaction to privileged management-plane activity. The rule family provides direct coverage when authentication or NETCONF telemetry is available and source identity can be correlated. Cloud rules provide supporting evidence when NETCONF or administrative access occurs through cloud-hosted network paths.
Threat Behavior
Suspicious administrative authentication associated with SD-WAN control-plane activity.
Direct Rule Coverage
· NDR / Network Behavioral Analytics: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
· Splunk: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
· Elastic: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
· QRadar: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
· SIGMA: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
Supporting Rule Coverage
· SentinelOne: Suspicious Administrative Shell or Process Activity on SD-WAN-Adjacent Host.
· AWS: Cloud-Hosted Cisco SD-WAN Control-Plane or NETCONF Access From Unapproved Source.
· Azure: Cloud-Hosted Cisco SD-WAN Control-Plane or NETCONF Access From Unapproved Source.
· GCP: Cloud-Hosted Cisco SD-WAN Control-Plane or NETCONF Access From Unapproved Source.
Traceability Assessment
Administrative authentication becomes high-value when it follows suspicious peer or control-plane behavior, originates from an unapproved source, occurs outside approved maintenance context, or is followed by NETCONF access or configuration change. SentinelOne provides supporting host-level visibility where SD-WAN-related management hosts, workloads, jump systems, or adjacent administrative systems are instrumented.
Threat Behavior
NETCONF access associated with suspicious SD-WAN control-plane activity.
Direct Rule Coverage
· NDR / Network Behavioral Analytics: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
· Splunk: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
· Elastic: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
· QRadar: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
· SIGMA: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
Supporting Rule Coverage
· AWS: Cloud-Hosted Cisco SD-WAN Control-Plane or NETCONF Access From Unapproved Source.
· Azure: Cloud-Hosted Cisco SD-WAN Control-Plane or NETCONF Access From Unapproved Source.
· GCP: Cloud-Hosted Cisco SD-WAN Control-Plane or NETCONF Access From Unapproved Source.
Traceability Assessment
NETCONF access is a strong management-plane signal when it is tied to suspicious control-plane behavior, unapproved sources, unfamiliar infrastructure, or abnormal timing. The detection model does not require encrypted payload visibility. It depends on source, destination, destination port, timing, approval context, and follow-on SD-WAN configuration or topology evidence.
Threat Behavior
Cisco SD-WAN configuration change following suspicious control-plane, NETCONF, or administrative activity.
Direct Rule Coverage
· NDR / Network Behavioral Analytics: Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity.
· Splunk: Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity.
· Elastic: Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity.
· QRadar: Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity.
· SIGMA: Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity.
Supporting Rule Coverage
· SentinelOne: Suspicious SD-WAN Key, Certificate, Account, or Configuration Artifact Activity.
· AWS: AWS Security Group or Network ACL Change Exposing Cisco SD-WAN Infrastructure.
· Azure: Azure Network Security or Routing Change Exposing Cisco SD-WAN Infrastructure.
· GCP: GCP Firewall, Route, or Load Balancer Change Exposing Cisco SD-WAN Infrastructure.
Traceability Assessment
Configuration change following suspicious access is one of the highest-confidence post-access behaviors in the report. Direct coverage depends on audit visibility into route, tunnel, policy, certificate, template, device-registration, peer-state, or fabric-trust changes. Cloud exposure-change rules provide supporting context when infrastructure-level changes expand access to SD-WAN assets or precede suspicious access.
Threat Behavior
Route, tunnel, policy, certificate, template, device-registration, peer-state, or fabric-trust modification.
Direct Rule Coverage
· NDR / Network Behavioral Analytics: Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity.
· Splunk: Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity.
· Elastic: Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity.
· QRadar: Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity.
· SIGMA: Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity.
Supporting Rule Coverage
· SentinelOne: Suspicious SD-WAN Key, Certificate, Account, or Configuration Artifact Activity.
· AWS: Post-Access AWS Traffic Change From Cisco SD-WAN Infrastructure.
· Azure: Post-Access Azure Traffic Change From Cisco SD-WAN Infrastructure.
· GCP: Post-Access GCP Traffic Change From Cisco SD-WAN Infrastructure.
Traceability Assessment
This behavior maps directly to SD-WAN fabric-impact potential. The strongest detections require SD-WAN configuration audit telemetry and object-level context. Endpoint and cloud detections are supporting sources because they may show artifact access, credential or certificate handling, or downstream traffic effects, but they do not replace SD-WAN configuration evidence.
Threat Behavior
Cloud-hosted exposure or access-path change affecting Cisco SD-WAN infrastructure.
Direct Rule Coverage
· AWS: AWS Security Group or Network ACL Change Exposing Cisco SD-WAN Infrastructure.
· Azure: Azure Network Security or Routing Change Exposing Cisco SD-WAN Infrastructure.
· GCP: GCP Firewall, Route, or Load Balancer Change Exposing Cisco SD-WAN Infrastructure.
Supporting Rule Coverage
· NDR / Network Behavioral Analytics: Suspicious Cisco SD-WAN Control-Plane or Peering Activity From Unapproved Source.
· Splunk: Suspicious Cisco SD-WAN Peering or Control-Plane Activity From Unapproved Source.
· Elastic: Suspicious Cisco SD-WAN Control-Plane or Peer Activity From Unapproved Source.
· QRadar: Suspicious Cisco SD-WAN Control-Plane or Peer Activity From Unapproved Source.
· SIGMA: Suspicious Cisco SD-WAN Control-Plane or Peer Activity From Unapproved Source.
Traceability Assessment
Cloud exposure changes provide direct coverage for infrastructure-level access-path risk when SD-WAN assets are hosted in cloud environments. These rules do not confirm SD-WAN exploitation. They identify conditions that may enable or support exploitation, including exposed management services, NETCONF access paths, permissive firewall rules, public ingress, and unapproved cloud-network changes.
Threat Behavior
Post-access traffic-flow change from Cisco SD-WAN infrastructure.
Direct Rule Coverage
· NDR / Network Behavioral Analytics: Post-Access SD-WAN Traffic-Flow or Fabric-Impact Change.
· AWS: Post-Access AWS Traffic Change From Cisco SD-WAN Infrastructure.
· Azure: Post-Access Azure Traffic Change From Cisco SD-WAN Infrastructure.
· GCP: Post-Access GCP Traffic Change From Cisco SD-WAN Infrastructure.
Supporting Rule Coverage
· Splunk: Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity.
· Elastic: Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity.
· QRadar: Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity.
· SIGMA: Cisco SD-WAN Configuration Change Following Suspicious Control-Plane or Administrative Activity.
Traceability Assessment
Post-access traffic-flow changes provide impact-supporting evidence when they follow suspicious control-plane activity, NETCONF access, administrative authentication, or SD-WAN configuration changes. These detections are strongest when paired with approved-baseline deviation, sensitive-destination tagging, new path creation, topology mismatch, and SD-WAN configuration audit records.
Threat Behavior
Suspicious host-level activity on SD-WAN-adjacent systems, workloads, or management hosts.
Direct Rule Coverage
· SentinelOne: Suspicious Administrative Shell or Process Activity on SD-WAN-Adjacent Host.
· SentinelOne: Suspicious SD-WAN Key, Certificate, Account, or Configuration Artifact Activity.
· SentinelOne: Suspicious Network Connection After SD-WAN Administrative or Configuration Activity.
Supporting Rule Coverage
· Splunk: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
· Elastic: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
· QRadar: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
· SIGMA: Cisco SD-WAN Control-Plane Activity Followed by NETCONF or Administrative Authentication.
Traceability Assessment
SentinelOne provides direct endpoint or workload coverage only where the relevant systems are instrumented. It should not be treated as appliance-native SD-WAN visibility. Its strongest use is detecting suspicious administrative process activity, credential or certificate artifact access, and network connections from adjacent management systems after suspicious SD-WAN activity.
Threat Behavior
Static malicious file, exploit string, public proof-of-concept artifact, or file-signature-based detection opportunity.
Direct Rule Coverage
None.
Supporting Rule Coverage
· YARA: Limited operational use only after a confirmed malicious artifact is recovered.
Traceability Assessment
YARA has no production rules for this report. The threat model is behavioral, control-plane, authentication, NETCONF, configuration-change, topology, and network-flow based. YARA may support controlled research or retrospective analysis of a validated malicious artifact, but it should not be used to claim detection of CVE-2026-20182 exploitation, rogue peering, NETCONF misuse, SD-WAN configuration manipulation, or fabric compromise.
Coverage Summary
Directly Covered Behaviors
· Suspicious SD-WAN control-plane or peer activity from unapproved sources.
· Unexpected peer identity, topology, or control-plane trust relationship.
· Control-plane activity followed by NETCONF access.
· Control-plane activity followed by administrative authentication.
· Configuration change following suspicious control-plane or privileged activity.
· High-impact SD-WAN route, tunnel, policy, certificate, template, device-registration, peer-state, or fabric-trust modification.
· Cloud-hosted exposure changes affecting SD-WAN infrastructure.
· Post-access cloud traffic-flow changes from SD-WAN infrastructure where cloud telemetry is available.
· Suspicious host-level behavior on monitored SD-WAN-adjacent systems.
Supporting Coverage Only
· Cloud telemetry that observes access paths but not SD-WAN peer-state or configuration intent.
· Endpoint telemetry from adjacent systems that does not provide appliance-native SD-WAN visibility.
· Network-flow telemetry that shows communication patterns but not command content or configuration intent.
· YARA-based artifact analysis after a validated suspicious file is recovered.
Non-Covered or Non-Primary Detection Areas
· Static file matching as a primary detection strategy.
· CVE-string or advisory-text matching as a primary detection strategy.
· Scanner-output-only detection.
· Port-only detection without source, asset, timing, approval, topology, or follow-on behavior context.
· Standalone cloud telemetry confirmation of successful SD-WAN exploitation.
· Standalone endpoint telemetry confirmation of SD-WAN fabric compromise.
· YARA production detection for generic Cisco SD-WAN files, configuration exports, logs, certificates, backups, templates, scripts, or public proof-of-concept artifacts.
Traceability Conclusion
S25 provides strong behavioral traceability for CVE-2026-20182 exploitation risk when SD-WAN control-plane, authentication, NETCONF, configuration-audit, network-flow, cloud, and endpoint-adjacent telemetry are correlated. The strongest direct coverage comes from NDR / Network Behavioral Analytics, Splunk, Elastic, QRadar, and SIGMA rule families that detect suspicious peer activity, privileged management sequencing, and configuration change. Cloud rules provide environment-specific access-path and post-access impact coverage. SentinelOne provides adjacent-host and workload visibility where deployed. YARA does not provide viable production detection for this report.
S27 Behavior & Log Artifacts
Behavioral Artifact Summary
CVE-2026-20182 detection is driven by suspicious SD-WAN control-plane behavior, peer identity anomalies, privileged management sequencing, configuration-change activity, cloud access-path exposure, and post-access traffic-flow changes. The highest-value artifacts are correlated operational events that show an unapproved or unusual source interacting with SD-WAN control-plane or management-plane services, followed by authentication, NETCONF access, configuration change, topology mismatch, or fabric-impact behavior.
Control-Plane Artifacts
· Control-plane activity from an unknown, newly observed, external, or unapproved source.
· Peer-state changes involving unfamiliar source IPs, unexpected peer identity fields, or mismatched topology context.
· Control-connection events involving unfamiliar System IP, site ID, domain ID, controller relationship, or device identity values.
· Device-registration activity from sources that do not align with approved SD-WAN inventory.
· Repeated or clustered control-plane events from cloud, VPN, hosting, unmanaged, unusual geography, or unusual ASN sources.
· Control-plane activity occurring outside approved maintenance, migration, disaster-recovery, service-provider, automation, or emergency-access windows.
Detection Value
Control-plane artifacts provide the strongest early signal when they show peer identity mismatch, topology mismatch, unapproved source context, or unusual timing. These artifacts should not be treated as standalone proof of compromise unless they are followed by administrative authentication, NETCONF access, configuration change, or fabric-impact evidence.
Authentication Artifacts
· Successful administrative authentication after suspicious SD-WAN control-plane activity.
· Authentication from unfamiliar source IPs, geographies, ASNs, VPN providers, hosting providers, or unmanaged networks.
· Authentication by users, roles, service accounts, or automation identities that do not align with approved SD-WAN administration workflows.
· Authentication outside expected maintenance, migration, emergency-access, service-provider, or automation windows.
· Administrative session creation near suspicious peer-state, control-connection, or device-registration activity.
· Authentication followed by NETCONF access, configuration change, route change, tunnel change, policy change, or certificate activity.
Detection Value
Authentication artifacts become high-value when tied to suspicious control-plane activity or followed by management-plane actions. Authentication alone should not be treated as compromise evidence without source, timing, identity, peer-state, NETCONF, configuration, or change-management context.
NETCONF Artifacts
· NETCONF access to SD-WAN infrastructure from unapproved or unfamiliar sources.
· TCP port 830 activity involving SD-WAN Controller, Manager, or NETCONF-exposed infrastructure.
· NETCONF access following suspicious control-plane or peer-state activity.
· NETCONF access from cloud, VPN, hosting, unmanaged, unusual geography, or unusual ASN sources.
· NETCONF access outside approved automation, maintenance, service-provider, migration, or emergency-access windows.
· NETCONF access followed by SD-WAN configuration changes or post-access traffic-flow changes.
Detection Value
NETCONF artifacts are strong management-plane signals when correlated with suspicious control-plane activity or unapproved source context. NETCONF detection does not require payload visibility. The detection value comes from source, destination, timing, approval status, and follow-on configuration or traffic-impact evidence.
Configuration and Fabric Artifacts
· Route changes following suspicious control-plane, authentication, or NETCONF activity.
· Tunnel changes following suspicious control-plane, authentication, or NETCONF activity.
· Policy changes affecting SD-WAN traffic steering, segmentation, access, routing, or reachability.
· Certificate changes involving SD-WAN trust, peer relationships, authentication, or management-plane access.
· Template pushes, device-registration changes, peer-state changes, or fabric-trust modifications.
· Configuration changes performed by unfamiliar actors, unapproved sources, unexpected automation accounts, or identities lacking approved change context.
· Configuration changes without matching maintenance windows, change tickets, service-provider records, automation records, or emergency-access records.
Detection Value
Configuration and fabric artifacts provide high-value post-access evidence. They are strongest when the changed object affects route, tunnel, policy, certificate, template, device-registration, peer-state, or fabric-trust behavior and when the change follows suspicious control-plane, authentication, or NETCONF activity.
Network and Traffic-Flow Artifacts
· New or unusual traffic from SD-WAN infrastructure after suspicious control-plane, NETCONF, administrative, or configuration activity.
· Traffic to first-seen destinations, sensitive systems, management systems, identity systems, backup systems, monitoring systems, or cloud workloads.
· New source-to-destination pairs from SD-WAN infrastructure.
· Persistent or recurring outbound traffic after rollback, restart, patching, or remediation.
· Unusual flows across peered cloud networks, VPN paths, transit gateways, ExpressRoute, Cloud Interconnect, or sensitive internal segments.
· Traffic-flow changes aligned with route, tunnel, policy, certificate, peer-state, or fabric-trust modifications.
Detection Value
Traffic-flow artifacts provide impact-supporting evidence. They should be correlated with SD-WAN control-plane, authentication, NETCONF, configuration-audit, topology, and change-management evidence before they are treated as compromise-supporting activity.
Cloud Access-Path Artifacts
· Public or broad inbound access to SD-WAN Controller, Manager, or NETCONF-exposed infrastructure.
· Security group, network security group, firewall rule, route, network ACL, forwarding rule, load balancer, application gateway, or public IP changes affecting SD-WAN infrastructure.
· Cloud-network changes that expose SD-WAN control-plane, management-plane, or NETCONF services.
· Cloud access from unapproved sources, unusual geographies, unusual ASNs, cloud providers, VPN providers, hosting providers, or unmanaged networks.
· Cloud exposure changes without matching change-management or maintenance context.
· Cloud exposure changes followed by accepted inbound traffic, authentication, NETCONF access, or SD-WAN configuration activity.
Detection Value
Cloud artifacts provide access-path and exposure evidence. They do not confirm SD-WAN exploitation by themselves. Their value increases when cloud exposure changes are followed by suspicious SD-WAN control-plane activity, administrative authentication, NETCONF access, configuration changes, or post-access traffic-flow changes.
Endpoint and Adjacent-Host Artifacts
· Suspicious administrative shell or process activity on SD-WAN-adjacent management hosts.
· Access to SD-WAN keys, certificates, configuration exports, administrative scripts, backup files, or management artifacts from unusual users or processes.
· Network connections from SD-WAN-adjacent hosts after suspicious administrative or configuration activity.
· Tool execution, scripting activity, credential access behavior, or unusual file access on hosts used to administer SD-WAN infrastructure.
· Activity from jump hosts, management systems, automation systems, or workloads that does not align with approved SD-WAN administration.
Detection Value
Endpoint artifacts provide adjacent-host visibility only where relevant systems are instrumented. They should not be treated as appliance-native SD-WAN evidence. Their strongest role is supporting investigation when endpoint activity aligns with suspicious SD-WAN control-plane, authentication, NETCONF, or configuration behavior.
Low-Value or Non-Primary Artifacts
· CVE-string matches.
· Advisory-text matches.
· Scanner-output-only findings.
· Port-only observations without source, timing, asset, approval, topology, or follow-on behavior context.
· Public proof-of-concept file names, repository strings, exploit branding, or static artifact names.
· Generic Cisco SD-WAN configuration files, logs, certificates, templates, backups, or scripts without suspicious context.
· YARA matches not based on validated incident artifacts.
Detection Value
These artifacts should not drive production detection by themselves. They may support triage, enrichment, or retrospective research, but they do not provide durable behavioral confirmation of exploitation or SD-WAN fabric compromise.
S28 Detection Strategy and SOC Implementation Guidance
Figure 5
Implementation Objective
The SOC should implement this detection model as a behavior-led correlation strategy. The objective is to detect suspicious SD-WAN control-plane interaction, privileged management sequencing, configuration modification, cloud access-path exposure, and post-access traffic-flow change without relying on CVE strings, exploit branding, scanner output, public proof-of-concept artifacts, or static file signatures.
Primary SOC Detection Approach
· Prioritize SD-WAN control-plane and peer-state anomalies from unapproved or unfamiliar sources.
· Correlate suspicious control-plane behavior with administrative authentication and NETCONF access.
· Correlate suspicious access with route, tunnel, policy, certificate, template, device-registration, peer-state, or fabric-trust changes.
· Correlate SD-WAN configuration changes with post-access traffic-flow changes.
· Correlate cloud exposure changes with accepted inbound access and SD-WAN management activity.
· Correlate endpoint or adjacent-host activity only where it supports SD-WAN control-plane, authentication, NETCONF, or configuration evidence.
SOC Triage Priority
High-priority triage should focus on behavior sequences that combine multiple detection anchors.
· Suspicious peer or control-plane activity from an unapproved source followed by administrative authentication.
· Suspicious peer or control-plane activity from an unapproved source followed by NETCONF access.
· Suspicious peer or control-plane activity followed by route, tunnel, policy, certificate, template, device-registration, peer-state, or fabric-trust change.
· Cloud exposure change affecting SD-WAN infrastructure followed by accepted inbound access.
· Accepted inbound access followed by SD-WAN authentication, NETCONF access, or configuration change.
· SD-WAN configuration change followed by new traffic-flow behavior, sensitive-destination access, or baseline deviation.
Initial SOC Validation Steps
· Confirm whether the affected asset is a Cisco SD-WAN Controller, Manager, NETCONF-exposed system, SD-WAN-adjacent management host, or cloud-hosted SD-WAN supporting asset.
· Validate whether the source IP, ASN, geography, provider type, VPN path, hosting provider, or administrative network is approved.
· Compare observed peer identity, System IP, site ID, domain ID, controller relationship, and device identity against approved topology.
· Confirm whether the activity occurred during an approved maintenance, migration, disaster-recovery, service-provider, automation, or emergency-access window.
· Determine whether authentication, NETCONF, configuration, or traffic-flow activity occurred after the suspicious control-plane event.
· Identify whether the same source, actor, service account, automation identity, or infrastructure cluster appears across multiple detection systems.
Correlation Requirements
· SD-WAN control-plane logs should be correlated with authentication logs.
· Authentication logs should be correlated with NETCONF access records.
· NETCONF access should be correlated with configuration audit records.
· Configuration audit records should be correlated with route, tunnel, policy, certificate, template, device-registration, peer-state, and fabric-trust changes.
· Network-flow records should be correlated with pre-change and post-change traffic baselines.
· Cloud logs should be correlated with asset tags, public IP mappings, firewall rules, security group rules, load balancer context, route changes, and accepted inbound access.
· Endpoint telemetry should be correlated with SD-WAN administration workflows, credential or certificate access, and management-host network behavior.
Escalation Criteria
Escalate to incident response when one or more of the following are present.
· Suspicious SD-WAN control-plane activity from an unapproved source followed by successful administrative authentication.
· Suspicious SD-WAN control-plane activity followed by NETCONF access.
· Unexpected peer identity or topology mismatch followed by configuration change.
· Unauthorized or unexplained route, tunnel, policy, certificate, template, device-registration, peer-state, or fabric-trust modification.
· Cloud exposure change affecting SD-WAN infrastructure followed by accepted inbound access.
· SD-WAN configuration change followed by new or unusual traffic-flow behavior.
· Activity that persists after patching, rollback, service restart, credential rotation, or configuration correction.
· Multiple systems independently show aligned control-plane, authentication, NETCONF, configuration, or traffic-flow evidence.
False Positive Reduction
· Suppress only documented maintenance windows, migrations, service-provider work, automation activity, disaster-recovery testing, approved edge onboarding, and emergency-access workflows.
· Avoid broad suppression for cloud providers, VPN providers, hosting providers, managed-service providers, automation accounts, or service-provider ranges.
· Require source, destination, asset, timing, approval, topology, or follow-on behavior context before raising severity.
· Validate whether route, tunnel, policy, certificate, template, or peer-state changes were authorized and expected.
· Validate whether cloud-network changes were tied to approved change records.
· Treat scanner traffic, port-only activity, or advisory-string matches as low-confidence unless paired with behavior-based evidence.
Telemetry Readiness Requirements
· Cisco SD-WAN Controller logs must be ingested and normalized.
· Cisco SD-WAN Manager logs must be ingested and normalized.
· Authentication records must include source, actor, outcome, and timestamp context.
· NETCONF access visibility must identify source, destination, destination port, and timing.
· Configuration audit logs must identify actor, source, object changed, change type, change outcome, and timestamp.
· Network-flow telemetry must support source, destination, destination port, protocol, action, timestamp, and baseline comparison.
· Cloud telemetry must include network access logs, control-plane changes, asset tags, public IP mappings, firewall or security-rule context, and change-management enrichment.
· Endpoint telemetry must be available for SD-WAN-adjacent management systems where SentinelOne coverage is expected.
SOC Investigation Workflow
· Start with the highest-confidence behavior sequence, not the loudest individual alert.
· Confirm the SD-WAN asset role and exposure path.
· Validate the source, actor, and peer identity against approved inventories.
· Review authentication and NETCONF activity within the same operational window.
· Review configuration audit records for route, tunnel, policy, certificate, template, device-registration, peer-state, or fabric-trust changes.
· Review network-flow changes after the suspicious event.
· Review cloud exposure changes if SD-WAN infrastructure is hosted in AWS, Azure, or GCP.
· Review endpoint activity on SD-WAN-adjacent management hosts if host telemetry is available.
· Escalate when multiple evidence types align across control-plane, authentication, NETCONF, configuration, cloud, endpoint, or network-flow telemetry.
Containment Guidance
· Validate and preserve SD-WAN Controller, Manager, authentication, NETCONF, configuration-audit, network-flow, and cloud logs before making broad changes.
· Review and revert unauthorized route, tunnel, policy, certificate, template, device-registration, peer-state, or fabric-trust changes.
· Restrict unapproved control-plane, management-plane, and NETCONF access paths.
· Review cloud security groups, network security groups, firewall rules, route tables, forwarding rules, public IP mappings, and load balancer exposure.
· Rotate or revoke credentials, certificates, tokens, service accounts, or automation identities only after preserving relevant forensic context.
· Increase monitoring for post-remediation persistence, recurring traffic-flow changes, repeated authentication attempts, and reappearing exposure paths.
Operational Constraints
· Do not treat a single port 830 observation as confirmed NETCONF misuse.
· Do not treat a CVE string, exploit label, public proof-of-concept name, or scanner finding as confirmed exploitation.
· Do not treat cloud exposure as confirmed SD-WAN compromise without SD-WAN-side evidence.
· Do not treat endpoint activity on adjacent systems as appliance-native SD-WAN evidence.
· Do not suppress broad cloud, VPN, hosting, service-provider, or automation activity without approved workflow context.
· Do not use YARA as a production detection method for this report unless a validated malicious artifact is recovered and scoped separately.
S29 Detection Coverage Summary
Coverage Summary
The S25 detection model provides strong behavioral coverage for suspicious SD-WAN control-plane activity, peer identity mismatch, privileged management sequencing, configuration change, cloud-hosted exposure, and post-access traffic-flow impact. Coverage is strongest when Cisco SD-WAN telemetry is correlated with authentication, NETCONF, configuration-audit, network-flow, cloud, and adjacent-host telemetry.
High-Confidence Coverage Areas
· Suspicious Cisco SD-WAN control-plane or peer activity from unapproved sources.
· Unexpected peer identity, topology relationship, System IP, site ID, domain ID, controller relationship, or device identity.
· Control-plane activity followed by administrative authentication.
· Control-plane activity followed by NETCONF access.
· NETCONF access from unfamiliar or unapproved sources.
· SD-WAN configuration change following suspicious control-plane, authentication, or NETCONF activity.
· Route, tunnel, policy, certificate, template, device-registration, peer-state, or fabric-trust modification.
· Cloud access-path exposure affecting SD-WAN infrastructure.
· Post-access traffic-flow changes from SD-WAN infrastructure.
· Suspicious activity on SD-WAN-adjacent management hosts where endpoint telemetry is deployed.
Moderate-Confidence Coverage Areas
· Cloud-hosted access attempts where SD-WAN-side peer-state or configuration telemetry is unavailable.
· Network-flow anomalies without SD-WAN configuration-audit evidence.
· Administrative authentication from unusual sources without follow-on NETCONF or configuration activity.
· Endpoint activity on adjacent management hosts without SD-WAN-side confirmation.
· Cloud security-rule or firewall exposure changes without accepted inbound traffic or SD-WAN management activity.
· First-seen or unusual destinations from SD-WAN infrastructure without confirmed configuration change.
Low-Confidence Coverage Areas
· Port-only detection.
· Scanner-output-only detection.
· CVE-string or advisory-text matching.
· Public proof-of-concept artifact matching.
· Static file names, repository strings, exploit labels, or branding.
· Generic Cisco SD-WAN file, log, backup, certificate, template, or script matching.
· YARA matching not based on a validated incident artifact.
System Coverage Summary
NDR / Network Behavioral Analytics
NDR provides high-value behavioral coverage for suspicious SD-WAN control-plane activity, peer anomalies, management-plane sequencing, and post-access traffic-flow changes. It is strongest when network telemetry can be enriched with SD-WAN asset inventory, approved peer context, source baselines, and topology expectations.
SentinelOne
SentinelOne provides coverage for SD-WAN-adjacent management hosts, workloads, jump systems, and administrative endpoints where the agent is deployed. It supports detection of suspicious process activity, credential or certificate artifact access, configuration artifact handling, and post-administration network connections. It should not be treated as appliance-native SD-WAN visibility.
Splunk
Splunk provides strong correlation coverage when SD-WAN Controller logs, Manager logs, authentication records, NETCONF telemetry, configuration audit logs, network-flow data, cloud logs, and change-management context are normalized and enriched. Splunk is one of the strongest systems for multi-source behavioral correlation.
Elastic
Elastic provides strong detection coverage when SD-WAN telemetry is mapped into ECS-aligned or custom fields and enriched with approved-source, peer, topology, cloud, and change-management context. It is strong for sequence-based control-plane, authentication, NETCONF, and configuration-change detections.
QRadar
QRadar provides strong correlation coverage when DSM parsing, custom properties, reference sets, building blocks, asset profiles, and offense rules are configured for SD-WAN telemetry. It is effective for detecting suspicious source context, peer anomalies, privileged activity, and configuration changes when parsing quality is mature.
SIGMA
SIGMA provides portable behavioral detection patterns for SIEM translation. Its coverage depends on target-platform field mapping, correlation support, enrichment quality, and log-source availability. SIGMA should be treated as a rule-portability layer rather than a standalone detection engine.
YARA
YARA provides no production detection coverage for this report. The detection problem is behavioral and control-plane driven rather than static-file driven. YARA may support retrospective research only if a confirmed malicious artifact is recovered.
AWS
AWS provides supporting and direct cloud-environment coverage when SD-WAN infrastructure is hosted in AWS or exposed through AWS network paths. It detects suspicious access, cloud-network exposure changes, and post-access traffic-flow changes, but it does not confirm SD-WAN exploitation without Cisco SD-WAN telemetry.
Azure
Azure provides supporting and direct cloud-environment coverage when SD-WAN infrastructure is hosted in Azure or exposed through Azure network paths. It detects suspicious access, Azure network-security or routing exposure changes, and post-access traffic-flow changes, but it does not confirm SD-WAN exploitation without Cisco SD-WAN telemetry.
GCP
GCP provides supporting and direct cloud-environment coverage when SD-WAN infrastructure is hosted in Google Cloud or exposed through GCP network paths. It detects suspicious access, GCP firewall or routing exposure changes, and post-access traffic-flow changes, but it does not confirm SD-WAN exploitation without Cisco SD-WAN telemetry.
Coverage Dependencies
· Approved SD-WAN peer inventory.
· Approved controller, Manager, edge-device, and administrative-source baselines.
· SD-WAN topology context.
· Authentication logs with source and actor fields.
· NETCONF visibility.
· Configuration audit logs with object-level change detail.
· Network-flow telemetry.
· Cloud asset tags and public IP mappings.
· Cloud control-plane change logs.
· Endpoint telemetry on adjacent management systems.
· Change-management, maintenance-window, automation, service-provider, and emergency-access context.
Coverage Limitations
· No single rule confirms exploitation independently.
· Cloud telemetry does not provide SD-WAN peer-state or configuration intent by itself.
· Endpoint telemetry does not provide appliance-native SD-WAN visibility by itself.
· Network telemetry may not show encrypted command content.
· NETCONF visibility may be limited to metadata and flow context.
· Configuration audit quality may vary by deployment and logging configuration.
· Approved-source and topology baselines must be maintained to reduce false positives.
· Static artifact detection is not a viable primary detection strategy for this report.
Coverage Conclusion
The overall coverage model is strong when telemetry is correlated across SD-WAN control-plane, authentication, NETCONF, configuration-audit, network-flow, cloud, and endpoint-adjacent sources. The highest-confidence detections come from behavior sequences that connect suspicious control-plane activity to privileged access, configuration change, and traffic-flow impact. The weakest coverage areas are static file detection, scanner-only findings, advisory-string matching, and isolated cloud or endpoint observations without SD-WAN-side confirmation.
S30 Intelligence Maturity Assessment
Intelligence Maturity Summary
The intelligence maturity level for this report is moderate-to-high when SD-WAN telemetry, authentication records, NETCONF visibility, configuration audit logs, network-flow telemetry, cloud logs, endpoint-adjacent telemetry, and change-management context are available. The detection model is behavior-led and resilient to minor exploit implementation changes because it focuses on control-plane trust behavior, privileged management sequencing, configuration modification, and post-access impact patterns.
Maturity Level
Moderate-to-High
Maturity Rationale
· The report uses behavioral detection anchors rather than brittle static indicators.
· The strongest rules focus on suspicious control-plane activity, peer identity mismatch, authentication sequencing, NETCONF access, configuration change, and traffic-flow impact.
· The detection model remains useful if exploit delivery details change but attacker behavior still affects SD-WAN control-plane, management-plane, configuration, or fabric behavior.
· Maturity depends heavily on SD-WAN log quality, configuration-audit visibility, topology baselines, approved-source inventories, and cloud asset tagging.
· Maturity decreases when telemetry is limited to port observations, scanner output, advisory references, or isolated cloud exposure findings.
High-Maturity Indicators
· SD-WAN Controller logs are ingested, normalized, and retained.
· SD-WAN Manager logs are ingested, normalized, and retained.
· Peer-state, control-connection, device-registration, System IP, site ID, domain ID, controller relationship, and peer identity fields are available.
· Authentication records include actor, source, outcome, method, and timestamp context.
· NETCONF access can be identified through management logs, flow telemetry, or both.
· Configuration audit records identify actor, source, object changed, change type, outcome, and timestamp.
· Network-flow telemetry supports baseline comparison and post-access traffic analysis.
· Cloud telemetry includes access-path exposure, firewall or security-rule changes, public IP mappings, and asset tags.
· Endpoint telemetry covers SD-WAN-adjacent management hosts and administrative systems.
· Change-management records can distinguish approved maintenance from suspicious activity.
Moderate-Maturity Indicators
· SD-WAN telemetry is partially available but not fully normalized.
· Authentication and NETCONF records exist but require manual correlation.
· Configuration audit logs exist but object-level detail is inconsistent.
· Network-flow telemetry is available but baselines are incomplete.
· Cloud asset tagging exists but does not fully map SD-WAN infrastructure relationships.
· Endpoint telemetry covers some adjacent management systems but not all relevant hosts.
· Approved peer, source, topology, and maintenance-window baselines require manual validation.
Low-Maturity Indicators
· SD-WAN Controller or Manager logs are unavailable or inconsistently retained.
· Peer identity, topology, System IP, site ID, domain ID, or controller relationship fields are missing.
· Authentication logs lack source or actor context.
· NETCONF visibility is unavailable.
· Configuration audit logs are missing or lack object-level detail.
· Network-flow telemetry is unavailable or not tied to SD-WAN assets.
· Cloud exposure logs are available but assets are not tagged.
· Change-management records cannot be correlated with telemetry.
· Detection relies primarily on scanner findings, advisory text, CVE strings, or static artifact matching.
Operational Intelligence Strengths
· The behavior model is durable across exploit variations.
· The rule set supports multiple detection layers, including NDR, endpoint, SIEM, portable SIGMA logic, and cloud telemetry.
· The model distinguishes direct SD-WAN evidence from supporting cloud and endpoint context.
· The model avoids over-reliance on static artifacts, public proof-of-concept details, or exploit branding.
· The model supports escalation based on correlated evidence rather than single-alert conclusions.
Operational Intelligence Gaps
· The model requires accurate SD-WAN topology and peer inventory.
· Detection quality depends on parsing and normalization of SD-WAN-specific fields.
· Cloud rules require accurate asset tagging and public IP mapping.
· Endpoint rules require coverage of adjacent management systems.
· NETCONF visibility may be limited to metadata and flow-level context.
· Configuration audit visibility may vary across deployment models.
· Traffic-flow impact may be difficult to interpret without mature baselines.
· False positives may occur during maintenance, migration, emergency access, service-provider activity, edge onboarding, or disaster-recovery testing.
Maturity Improvement Priorities
· Normalize SD-WAN Controller and Manager logs.
· Maintain approved SD-WAN peer, topology, and administrative-source inventories.
· Validate authentication and NETCONF telemetry coverage.
· Improve configuration audit logging for route, tunnel, policy, certificate, template, device-registration, peer-state, and fabric-trust changes.
· Tag SD-WAN infrastructure consistently across AWS, Azure, and GCP.
· Build cloud access-path baselines for SD-WAN-hosted environments.
· Establish network-flow baselines for normal SD-WAN traffic behavior.
· Expand endpoint telemetry coverage across SD-WAN-adjacent management systems.
· Improve change-management correlation with maintenance, automation, service-provider, disaster-recovery, and emergency-access workflows.
Analytical Confidence
Moderate-to-High
Confidence Rationale
· Confidence is high when suspicious control-plane behavior is followed by administrative authentication, NETCONF access, configuration change, or post-access traffic-flow change.
· Confidence is moderate when only cloud exposure, network access, or endpoint-adjacent activity is available.
· Confidence is low when evidence is limited to scanner output, CVE strings, public proof-of-concept references, port-only observations, or static artifact matches.
· Confidence increases when multiple independent telemetry sources align around the same source, actor, asset, timing window, and change sequence.
Final Intelligence Assessment
The report’s intelligence maturity is strong enough to support operational detection engineering when SD-WAN, SIEM, cloud, endpoint, and network-flow telemetry are available and correlated. The model is behavior-led, public-facing, and resilient against minor exploit variation. The primary maturity constraint is not detection concept quality; it is telemetry completeness, field normalization, topology accuracy, and change-management correlation.
S31 — Telemetry Dependencies
Cisco Catalyst SD-WAN Controller Authentication Bypass detection depends on telemetry that can validate whether observed control-plane, administrative, NETCONF, configuration, and fabric behavior aligns with approved SD-WAN topology and change context. No single telemetry source should be treated as sufficient by itself. The strongest visibility comes from correlated Controller logs, Manager audit records, authentication records, NETCONF evidence, configuration-change history, network-flow metadata, topology inventory, and change-management records.
Primary Telemetry Dependencies
· Cisco SD-WAN Controller logs for peering, control-connection, peer-state, device-registration, controller relationship, and fabric-trust activity.
· Cisco SD-WAN Manager logs for administrative sessions, audit activity, configuration changes, policy changes, device registration, peer-state changes, and template activity.
· Authentication records for administrative-account access, source IP, username, authentication method, timestamp, outcome, and failed-to-successful patterns.
· NETCONF records or network-flow telemetry identifying TCP port 830 access to SD-WAN management or control-plane infrastructure.
· SD-WAN configuration audit logs identifying actor, source, object changed, change type, change outcome, timestamp, and authorization context.
· Network-flow and firewall telemetry showing source IP, destination IP, destination port, protocol, session timing, connection volume, and newly observed source behavior.
· Approved peer inventory identifying Controllers, Managers, Validators, edge devices, System IPs, site IDs, domain IDs, peer types, public IPs, device identities, and controller relationships.
· Approved administrative-source inventory identifying management networks, VPN paths, automation systems, service-provider paths, managed-service paths, emergency-access paths, and jump hosts.
· Approved NETCONF source lists identifying expected systems, automation sources, administrative workflows, and service-provider access paths.
· Change-management records identifying maintenance windows, controller migrations, disaster-recovery events, edge onboarding, service-provider work, emergency access, automation jobs, and approved SD-WAN configuration changes.
Supporting Telemetry Dependencies
· GeoIP, ASN, VPN-provider, cloud-provider, hosting-provider, and managed-service enrichment for source and destination context.
· Asset inventory and criticality tagging for Cisco SD-WAN Controllers, Managers, Validators, edge devices, NETCONF-exposed infrastructure, branch environments, data-center assets, cloud segments, and sensitive internal systems.
· Configuration snapshots or historical state records for identifying route, tunnel, policy, certificate, device-registration, peer-state, and fabric-trust drift.
· NDR and firewall telemetry for newly observed source behavior, unusual communication paths, post-access traffic-flow changes, and sensitive-segment reachability.
· Endpoint or workload telemetry where SD-WAN infrastructure, management hosts, jump systems, or supporting infrastructure are instrumented.
· Service-provider and managed-service records for validating approved administrative access, support actions, escalation activity, and emergency change activity.
· SOC case-management and ticketing records for linking suspicious activity to investigation, triage, approval, and response actions.
Minimum Viable Telemetry
· Cisco SD-WAN Controller and Manager logs.
· Administrative authentication records with source IP and outcome.
· Network-flow or firewall visibility for SD-WAN control-plane and NETCONF access.
· Approved peer inventory.
· Approved administrative-source inventory.
· Approved NETCONF source list.
· Configuration audit records.
· Change-management context.
Telemetry Quality Requirements
· Logs should be centrally collected or rapidly retrievable during investigation.
· SD-WAN peer and administrative-source baselines should be current and maintained as authoritative reference data.
· NETCONF visibility should identify source, destination, timing, and expected workflow context.
· Configuration audit records should preserve actor, source, object, action, outcome, and timestamp.
· Change-management data should include object-level detail sufficient to validate route, tunnel, policy, certificate, peer-state, and fabric-trust changes.
· Retention should support delayed discovery, recurring access review, configuration-drift investigation, and post-remediation validation.
S32 — Detection Limitations
Cisco Catalyst SD-WAN Controller Authentication Bypass detection has meaningful limitations because successful activity may resemble legitimate SD-WAN infrastructure behavior after trust or administrative access is obtained. Detection confidence depends on topology baselines, source governance, controller-side telemetry, configuration audit quality, and change-management linkage.
Primary Detection Limitations
· Encrypted SD-WAN control-plane traffic may limit packet-level inspection and reduce payload-based validation.
· Network-flow telemetry may show access to SD-WAN services but may not confirm successful peering, administrative authentication, NETCONF command intent, or configuration impact.
· Cisco SD-WAN Controller and Manager logs may vary by deployment model, version, logging configuration, hosting model, and provider-management arrangement.
· Provider-managed or co-managed SD-WAN environments may limit direct visibility into administrative actions, source paths, and configuration history.
· Incomplete peer inventory can make rogue peering, unexpected device identity, or unauthorized controller relationship activity difficult to classify.
· Weak administrative-source baselines can cause unauthorized activity to blend with VPN, service-provider, automation, emergency-access, or managed-service workflows.
· NETCONF access may be difficult to interpret without source, identity, timing, peer-state, and configuration-change context.
· Configuration changes may be difficult to classify without actor, source, object changed, change type, peer-state context, approval record, and change window.
· Legitimate controller migration, disaster recovery, edge onboarding, provider support, automation, emergency access, and maintenance activity may resemble suspicious control-plane behavior.
· Post-access traffic-flow changes may be difficult to attribute without route, tunnel, policy, topology, configuration, and change-management evidence.
False Positive Drivers
· Planned SD-WAN controller migration.
· Edge-device onboarding or branch expansion.
· Service-provider maintenance or troubleshooting.
· Managed-service administrative access.
· Emergency access during outage response.
· Disaster-recovery testing.
· Automation-driven configuration deployment.
· Certificate renewal or trust-store maintenance.
· Route, tunnel, policy, or template updates during approved change windows.
· Temporary peer churn during upgrades, patching, failover, or network instability.
False Negative Drivers
· Missing Cisco SD-WAN Controller or Manager logs.
· Missing authentication source context.
· Missing NETCONF visibility.
· Missing or incomplete configuration audit records.
· Incomplete topology and peer inventory.
· Incomplete administrative-source baselines.
· Overly broad suppression of cloud, VPN, hosting, provider, or managed-service traffic.
· Failure to correlate Controller, Manager, authentication, NETCONF, configuration, topology, network-flow, and change-management records.
· Treating trusted peer behavior as benign without validating topology and authorization.
· Assuming exploitation must originate from the public internet.
· Assuming encrypted control-plane traffic prevents meaningful behavior-led detection.
Operational Limitations
· SOC teams may not have direct access to SD-WAN topology inventory or configuration history.
· Network, security, service-provider, and infrastructure teams may maintain separate records that are difficult to correlate during investigation.
· Change records may not include enough detail to validate peer-state, route, tunnel, certificate, policy, or fabric-trust changes.
· Provider-managed environments may require escalation outside normal SOC workflows.
· SD-WAN configuration snapshots may not be frequent enough to detect short-lived or rolled-back changes.
· Asset ownership may be unclear for externally reachable or provider-managed SD-WAN infrastructure.
S33 — Defensive Control & Hardening Improvements
Defensive improvement should focus on preserving SD-WAN control-plane trust, restricting administrative and NETCONF access, validating approved topology, improving configuration-change assurance, and ensuring the SOC can distinguish legitimate operations from suspicious infrastructure-trust abuse.
Control-Plane Exposure Reduction
· Restrict Cisco SD-WAN Controller and Manager access to approved management networks, service-provider paths, VPN paths, emergency-access paths, and automation sources.
· Remove unnecessary internet exposure for SD-WAN control-plane and management-plane services.
· Enforce network-layer access controls for Controller, Manager, Validator, edge-device, and NETCONF-exposed infrastructure.
· Validate that control-plane service exposure matches approved architecture, provider agreements, and emergency-access procedures.
· Monitor for newly exposed SD-WAN services after migration, disaster recovery, edge onboarding, or provider support activity.
Peer and Topology Governance
· Maintain an authoritative inventory of approved Controllers, Managers, Validators, edge devices, System IPs, site IDs, domain IDs, peer types, public IPs, device identities, and controller relationships.
· Reconcile observed peer-state activity against approved topology on a recurring schedule.
· Require approval and documentation for new peer relationships, device registration, controller relationship changes, and fabric-trust modifications.
· Investigate unknown peer identity fields, unexpected peer-state transitions, or control-connection anomalies outside approved maintenance windows.
· Preserve historical topology snapshots to support drift analysis during investigation.
Administrative and NETCONF Hardening
· Restrict SD-WAN administrative and NETCONF access to approved source networks, managed jump hosts, automation systems, service-provider paths, and emergency-access workflows.
· Enforce strong authentication and least privilege for SD-WAN administrative accounts, provider accounts, automation accounts, and emergency-access accounts.
· Require ticket, change, automation, provider, or emergency-access linkage for privileged SD-WAN activity.
· Monitor administrative authentication and TCP port 830 access from unfamiliar, external, newly observed, or unauthorized sources.
· Review automation credentials and source paths used for NETCONF workflows.
Configuration and Fabric Integrity
· Enable and retain SD-WAN configuration audit logs for routes, tunnels, policies, certificates, templates, device registration, peer state, controller relationships, and fabric-trust changes.
· Require object-level change records for SD-WAN configuration changes.
· Compare current configuration state against approved baseline and recent snapshots.
· Investigate configuration changes that lack maintenance-window, automation, service-provider, emergency-access, or change-ticket alignment.
· Validate route, tunnel, policy, certificate, and fabric-trust state after suspicious control-plane or administrative activity.
Monitoring and Response Readiness
· Build SOC playbooks for suspicious SD-WAN peering, administrative authentication, NETCONF access, configuration drift, and fabric-impact review.
· Ensure SOC teams can access Controller logs, Manager logs, authentication records, NETCONF records, topology inventory, configuration audits, and change-management context.
· Establish escalation paths with network engineering, service providers, managed-service teams, cloud operations, and incident response.
· Preserve logs and configuration snapshots during suspected SD-WAN control-plane abuse.
· Conduct tabletop exercises for rogue peering, unauthorized NETCONF access, route manipulation, and branch connectivity impact.
S34 — Defensive Control & Hardening Architecture
Figure 6
The defensive architecture should treat Cisco SD-WAN infrastructure as a high-trust control-plane environment with layered protections. Each layer should answer a different assurance question: who can reach the control plane, who can administer it, which peers are trusted, which automated workflows are allowed, what changed, and how the organization will respond if trust cannot be confirmed.
Control-Plane Access Layer
· Defines which networks, providers, VPN paths, automation sources, emergency-access paths, and managed jump hosts may reach SD-WAN control-plane or management-plane services.
· Blocks unnecessary internet or unmanaged-source exposure.
· Produces source-context evidence for suspicious access from new, external, cloud, VPN, hosting, provider, or unmanaged infrastructure.
Identity and Administrative Governance Layer
· Validates that administrative users, provider accounts, automation accounts, and emergency-access accounts are authorized for the observed action.
· Connects privileged sessions to approved tickets, change records, provider records, automation records, or emergency-access records.
· Supports rapid review of successful access from unfamiliar or unauthorized sources.
Peer and Fabric Trust Layer
· Validates that observed System IPs, site IDs, domain IDs, peer types, public IPs, device identities, and controller relationships match approved topology.
· Flags rogue peer registration, unexpected device registration, unexpected peer-state changes, and control-connection anomalies.
· Preserves baseline and historical topology state for drift and rollback review.
NETCONF and Automation Layer
· Defines which systems may perform NETCONF or automated SD-WAN management activity.
· Separates machine-driven administration from human administrative access.
· Links automation-driven changes to approved workflows and expected source paths.
Configuration Assurance Layer
· Captures actor, source, object changed, change type, outcome, timestamp, peer context, and approval context for SD-WAN configuration changes.
· Preserves route, tunnel, policy, certificate, template, device-registration, peer-state, controller-relationship, and fabric-trust history.
· Supports validation of unauthorized or unexplained configuration drift.
Detection and Response Layer
· Correlates Controller logs, Manager logs, authentication records, NETCONF evidence, network-flow telemetry, configuration audits, topology inventory, and change-management records.
· Prioritizes sequences involving suspicious peering followed by administrative authentication, NETCONF access, configuration change, or traffic-flow impact.
· Drives containment, route validation, policy rollback, credential review, peer inventory reconciliation, service-provider escalation, and executive incident reporting.
S35 — Defensive Control Mapping Matrix
Control Area
SD-WAN control-plane exposure management.
Primary Defensive Purpose
Reduce unauthorized reachability to Cisco SD-WAN Controller, Manager, Validator, and NETCONF-exposed infrastructure.
Relevant Improvements
· Restrict control-plane and management-plane access to approved sources.
· Remove unnecessary internet exposure.
· Monitor newly observed sources reaching SD-WAN infrastructure.
Detection and Response Value
Exposure reduction lowers opportunity for unauthorized control-plane interaction and improves confidence when unfamiliar sources appear in logs or network telemetry.
Control Area
Approved peer and topology governance.
Primary Defensive Purpose
Ensure observed SD-WAN peer activity matches known, approved infrastructure relationships.
Relevant Improvements
· Maintain approved peer inventory.
· Validate System IPs, site IDs, domain IDs, peer types, public IPs, device identities, and controller relationships.
· Alert on rogue peer registration and unexpected peer-state changes.
Detection and Response Value
Peer governance allows defenders to distinguish legitimate edge onboarding, controller migration, and provider activity from suspicious trusted-positioning behavior.
Control Area
Administrative-source governance.
Primary Defensive Purpose
Restrict and validate privileged SD-WAN administration.
Relevant Improvements
· Enforce approved source networks for administrative access.
· Require strong authentication and least privilege.
· Monitor successful administrative authentication from unfamiliar sources.
Detection and Response Value
Administrative-source governance raises confidence when suspicious authentication follows control-plane anomalies or peer-state changes.
Control Area
NETCONF restriction and monitoring.
Primary Defensive Purpose
Limit privileged SD-WAN management access and detect unauthorized management activity.
Relevant Improvements
· Restrict NETCONF to approved administrative, automation, and provider sources.
· Monitor TCP port 830 access to SD-WAN infrastructure.
· Correlate NETCONF access with suspicious peering, authentication, configuration changes, and change records.
Detection and Response Value
NETCONF monitoring helps identify movement from control-plane interaction into privileged SD-WAN management activity.
Control Area
Configuration audit and drift management.
Primary Defensive Purpose
Detect unauthorized or unexplained route, tunnel, policy, certificate, template, device-registration, peer-state, controller relationship, and fabric-trust changes.
Relevant Improvements
· Centralize configuration audit logs.
· Preserve actor, source, object, change type, outcome, timestamp, and approval context.
· Compare current state to approved baseline and historical snapshots.
Detection and Response Value
Configuration audit visibility supports confirmation of fabric-impact behavior and reduces uncertainty after suspicious access.
Control Area
Change-management integration.
Primary Defensive Purpose
Separate approved SD-WAN operations from suspicious infrastructure-trust abuse.
Relevant Improvements
· Require object-level change detail for SD-WAN modifications.
· Link migration, onboarding, provider support, automation, emergency access, and disaster recovery to observable records.
· Review changes that lack approval, ticket, or maintenance-window alignment.
Detection and Response Value
Change linkage reduces false positives and prevents suspicious fabric changes from being dismissed as routine operations.
Control Area
Network-flow and NDR correlation.
Primary Defensive Purpose
Identify suspicious source behavior, NETCONF sequencing, and post-access traffic-flow changes.
Relevant Improvements
· Monitor SD-WAN control-plane and NETCONF traffic.
· Enrich sources with first-seen, ASN, geography, VPN, cloud, hosting, and provider context.
· Detect new source-to-destination flows after suspicious access.
Detection and Response Value
Network-flow correlation provides supporting evidence for suspicious access paths and possible fabric-impact outcomes.
Control Area
Service-provider and managed-service governance.
Primary Defensive Purpose
Prevent provider access ambiguity from obscuring unauthorized SD-WAN control-plane activity.
Relevant Improvements
· Document approved provider source networks, accounts, support windows, escalation paths, and emergency procedures.
· Require provider activity records for administrative access and configuration changes.
· Include providers in incident response escalation workflows.
Detection and Response Value
Provider governance reduces ambiguity where attacker infrastructure overlaps with legitimate service-provider or managed-service patterns.
Control Area
Incident response readiness.
Primary Defensive Purpose
Ensure suspicious SD-WAN control-plane activity can be investigated and contained quickly.
Relevant Improvements
· Build playbooks for rogue peering, unauthorized administrative authentication, NETCONF access, configuration drift, and fabric-impact review.
· Define containment, rollback, credential-review, route-validation, and service-provider escalation steps.
· Preserve logs and configuration snapshots during investigation.
Detection and Response Value
Prepared response workflows reduce dwell time, scoping uncertainty, and business disruption after suspected SD-WAN compromise.
S36 — CyberDax Intelligence Maturity Assessment
Cisco Catalyst SD-WAN Controller Authentication Bypass requires intelligence maturity beyond vulnerability identification. Mature programs should be able to understand SD-WAN topology, identify unauthorized trust activity, correlate administrative and NETCONF access, validate configuration changes, and assess business impact across branch, data-center, cloud, provider, and sensitive internal environments.
Current Maturity Requirement
Advanced. The report requires mature correlation across SD-WAN control-plane telemetry, administrative authentication, NETCONF access, configuration audit records, topology inventory, network-flow metadata, provider records, and change-management context.
Foundational Maturity Indicators
· Cisco SD-WAN Controller and Manager logs are collected or rapidly retrievable.
· Approved peer inventory exists and is actively maintained.
· Administrative-source baselines are documented.
· NETCONF source lists are defined.
· Configuration audit records are available for SD-WAN changes.
· Change-management records identify approved maintenance, provider work, emergency access, automation, and migration activity.
· SOC teams know how to escalate suspicious SD-WAN control-plane activity to network engineering and service-provider teams.
Intermediate Maturity Indicators
· SD-WAN telemetry is normalized into SIEM or detection platforms.
· Peer identity fields are enriched against approved topology.
· Administrative authentication is correlated with source network, user, role, and change context.
· NETCONF access is monitored and correlated with administrative and configuration activity.
· Configuration changes are evaluated against object-level approval records.
· NDR or firewall telemetry identifies newly observed sources and post-access traffic-flow changes.
· Incident response workflows include SD-WAN-specific containment, route validation, policy review, and provider escalation.
Advanced Maturity Indicators
· Risk-based correlation combines suspicious peering, administrative authentication, NETCONF access, configuration changes, and traffic-flow impact.
· Approved topology, administrative-source, NETCONF-source, and change-management datasets are continuously maintained.
· Historical configuration snapshots support drift analysis and rollback validation.
· Service-provider and managed-service activity is integrated into monitoring and investigation workflows.
· High-value branch, data-center, cloud, and sensitive-segment dependencies are mapped to SD-WAN fabric state.
· SOC and network teams can rapidly determine whether suspicious activity affected routing, segmentation, policy behavior, or branch connectivity.
· Post-remediation monitoring detects recurring unfamiliar access, persistent rogue peers, unauthorized certificates, trust artifacts, or configuration drift.
Maturity Gaps That Increase Risk
· SD-WAN logs are available only through manual provider request.
· Peer inventory is incomplete or outdated.
· Administrative-source baselines are informal or undocumented.
· NETCONF access is not restricted or monitored.
· Configuration audit retention is short or incomplete.
· Change records lack object-level detail.
· Provider support activity is not integrated into security monitoring.
· SOC teams lack playbooks for SD-WAN control-plane abuse.
· Branch, cloud, data-center, and sensitive-segment dependencies are not mapped to SD-WAN routes, tunnels, or policy state.
CyberDax Maturity Judgment
Organizations with centralized SD-WAN logs, maintained topology inventory, administrative-source governance, NETCONF restriction, configuration-audit visibility, and integrated change records can achieve high-confidence detection and response. Organizations lacking those controls should treat this exposure as a higher-risk assurance gap because attacker activity may appear as legitimate SD-WAN operations and remain difficult to classify.
S37 — Strategic Defensive Improvements
Strategic defensive improvement should turn SD-WAN from a high-trust but difficult-to-validate control plane into a governed, observable, and auditable infrastructure domain. The objective is to preserve confidence that SD-WAN trust relationships, administrative access, NETCONF workflows, configuration changes, and fabric behavior remain authorized.
Priority 1 — Establish SD-WAN Control-Plane Assurance
· Build authoritative inventories for Controllers, Managers, Validators, edge devices, peer relationships, System IPs, site IDs, domain IDs, public IPs, device identities, and controller relationships.
· Restrict SD-WAN control-plane and management-plane exposure to approved sources.
· Treat unknown peer identity fields and unexpected peer-state changes as high-priority investigation triggers.
· Preserve historical topology states to support drift analysis.
Priority 2 — Strengthen Administrative and NETCONF Governance
· Restrict administrative and NETCONF access to approved networks, roles, jump hosts, service-provider paths, automation systems, and emergency-access workflows.
· Enforce strong authentication and least privilege for SD-WAN administrative users, provider accounts, automation accounts, and emergency-access accounts.
· Review NETCONF exposure, automation credentials, and source paths on a recurring basis.
· Alert on administrative authentication or NETCONF access from unfamiliar, external, newly observed, or unauthorized sources.
Priority 3 — Improve Configuration Integrity and Change Assurance
· Centralize SD-WAN configuration audit logs.
· Require object-level approval records for route, tunnel, policy, certificate, template, device-registration, peer-state, controller relationship, and fabric-trust changes.
· Maintain configuration snapshots and compare current state to approved baseline.
· Validate route, tunnel, policy, and segmentation state after suspicious access.
Priority 4 — Integrate Provider and Managed-Service Oversight
· Document approved provider source networks, accounts, access windows, escalation procedures, and emergency workflows.
· Require provider activity records for administrative sessions and configuration changes.
· Ensure incident response plans include provider escalation and evidence-preservation requirements.
· Avoid broad suppression of provider, VPN, cloud, hosting, or managed-service infrastructure.
Priority 5 — Build SD-WAN Incident Response Readiness
· Create playbooks for suspicious peering, unauthorized administrative authentication, NETCONF access, configuration drift, route manipulation, and fabric-impact review.
· Pre-stage procedures for route validation, tunnel validation, policy rollback, credential review, and service-provider coordination.
· Trigger executive incident governance when SD-WAN fabric integrity, segmentation, branch connectivity, cloud access, or data-center reachability cannot be confirmed.
· Conduct tabletop exercises for rogue peering, unauthorized NETCONF activity, and SD-WAN configuration manipulation.
Priority 6 — Mature Behavior-Led Detection
· Correlate suspicious peering with administrative authentication, NETCONF access, configuration changes, and traffic-flow impact.
· Enrich source activity with first-seen, ASN, geography, cloud-provider, VPN-provider, hosting-provider, and service-provider context.
· Use topology-aware and change-aware alerting rather than port-only or CVE-string logic.
· Review recurring unfamiliar access after remediation, rollback, patching, or configuration correction.
S38 — Attack Economics & Organizational Impact Model
Figure 7
Adversary Cost Advantage
Cisco Catalyst SD-WAN Controller Authentication Bypass can provide favorable attacker economics because successful control-plane abuse may convert limited network reachability into high-leverage SD-WAN trust or management positioning. The attacker does not need to compromise every branch, data-center connection, cloud path, or internal segment individually if control-plane trust, peer behavior, administrative access, NETCONF workflows, or configuration pathways can be abused through a smaller number of exposed systems.
The economic advantage increases where SD-WAN Controllers or Managers are externally reachable, provider-accessible, weakly source-restricted, poorly baselined, or connected to sensitive routing and segmentation paths. In those conditions, attacker effort can remain concentrated on the control plane while organizational impact may expand across branch connectivity, cloud reachability, data-center access, service-provider trust paths, and security-boundary assurance.
Defender Cost Disadvantage
Defenders face elevated response cost because suspected SD-WAN control-plane compromise cannot be resolved by confirming whether a single appliance was patched. Response may require historical validation of peering, administrative authentication, NETCONF access, configuration changes, route state, tunnel state, policy behavior, certificate posture, peer inventory, provider activity, and post-access traffic-flow changes.
The defender burden increases when topology inventory is incomplete, configuration audit visibility is limited, NETCONF records are unavailable, provider-managed access is difficult to validate, or change records do not provide object-level detail. In those environments, review may expand across network engineering, SOC operations, service providers, cloud teams, legal stakeholders, executive leadership, and business units dependent on SD-WAN connectivity.
Operational Leverage for Attackers
Successful exploitation or credible suspected compromise can create outsized organizational impact because SD-WAN infrastructure occupies a privileged role in enterprise connectivity. It influences routing, policy enforcement, branch reachability, cloud access, data-center communication, service-provider paths, and segmentation boundaries.
The highest leverage occurs when unauthorized peering, administrative authentication, NETCONF access, or configuration manipulation creates uncertainty over whether SD-WAN fabric behavior remains authorized. Even without confirmed broad disruption, the organization may need to validate whether routes, tunnels, policies, certificates, device registration, peer state, and fabric trust were altered before returning to normal operational confidence.
Organizational Impact Model
Low Impact Scenario
Estimated impact $200K to $1M.
Low impact occurs when assessment confirms limited vulnerable or exposed Cisco SD-WAN infrastructure, accurate approved peer inventory, well-governed administrative sources, restricted NETCONF access, no suspicious rogue peering, no unauthorized administrative authentication, no SD-WAN configuration drift, and change-management records that align with observed Controller and Manager activity.
Moderate Impact Scenario
Estimated impact $1.2M to $8M.
Moderate impact occurs when one or more Cisco SD-WAN Controllers or Managers show suspicious control-plane access, unknown peer identity fields, peer-state anomalies, administrative authentication from unfamiliar sources, NETCONF access from unauthorized networks, incomplete change linkage, or limited configuration drift without confirmed broad routing manipulation, segmentation failure, data-center exposure, major branch outage, or sustained attacker control.
High Impact Scenario
Estimated impact $8M to $40M or higher.
High impact occurs when confirmed or strongly suspected unauthorized SD-WAN control-plane trust activity results in rogue peering, privileged administrative access, NETCONF management activity, route or tunnel manipulation, policy modification, certificate or fabric-trust changes, device-registration abuse, persistent unfamiliar access, segmentation impact, branch disruption, or new connectivity into sensitive internal environments.
Economic Pressure Points
· Criticality of affected Cisco SD-WAN Controllers, Managers, Validators, edge devices, branch sites, data-center connections, cloud connections, and managed-service paths.
· Presence of rogue peering, unauthorized peer-state changes, unfamiliar System IPs, site IDs, domain IDs, peer types, public IPs, device identities, or controller relationships.
· Successful administrative authentication from unfamiliar, external, unauthorized, cloud-hosted, VPN-associated, service-provider, or unmanaged source infrastructure.
· NETCONF access from unfamiliar or unauthorized sources after suspicious peering, control-plane instability, or administrative authentication.
· SD-WAN configuration changes affecting routes, tunnels, policies, certificates, templates, device registration, peer state, controller relationships, or fabric trust.
· New access paths into sensitive internal segments, identity systems, management systems, backup systems, data-center environments, cloud networks, or regulated business environments.
· Completeness of Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, network-flow telemetry, topology inventory, and change-management records.
· Need for route validation, tunnel validation, policy review, certificate review, peer inventory reconciliation, configuration rollback, branch connectivity testing, segmentation assurance, service-provider escalation, credential review, legal review, or board reporting.
S39 — Economic Impact & Organizational Exposure
Estimated Economic Exposure
Estimated economic exposure should be modeled through three scenario bands.
Low Impact Scenario
Estimated impact $200K to $1M.
Rapid assessment confirms that vulnerable or exposed Cisco SD-WAN infrastructure is limited, approved peer inventory is accurate, administrative sources are well governed, NETCONF access is restricted, no suspicious rogue peering is identified, no unauthorized administrative authentication is confirmed, no SD-WAN configuration drift is present, and change-management records align with observed Controller and Manager activity. Response remains limited to exposure validation, Controller and Manager log review, approved-peer verification, NETCONF source review, detection tuning, and executive tracking.
Moderate Impact Scenario
Estimated impact $1.2M to $8M.
One or more Cisco SD-WAN Controllers or Managers show suspicious control-plane access, unknown peer identity fields, peer-state anomalies, administrative authentication from unfamiliar sources, NETCONF access from unauthorized networks, incomplete change linkage, or limited configuration drift without confirmed broad routing manipulation, segmentation failure, data-center exposure, major branch outage, or sustained attacker control. Response requires SD-WAN topology validation, Controller and Manager log analysis, administrative-account review, NETCONF session investigation, configuration-drift assessment, route and tunnel review, service-provider coordination, change-record reconciliation, targeted containment, detection tuning, and executive incident coordination.
High Impact Scenario
Estimated impact $8M to $40M or higher.
Confirmed or strongly suspected unauthorized SD-WAN control-plane trust activity results in rogue peering, privileged administrative access, NETCONF management activity, route or tunnel manipulation, policy modification, certificate or fabric-trust changes, device-registration abuse, persistent unfamiliar access, segmentation impact, branch disruption, or new connectivity into sensitive internal environments. Response may require emergency SD-WAN control-plane containment, Controller and Manager remediation, route and policy rollback, branch connectivity validation, segmentation review, privileged credential rotation, service-provider escalation, business-continuity coordination, forensic reconstruction, customer or business-unit assurance, legal review, regulatory assessment where applicable, cyber insurance coordination, and board-level incident governance.
Annualized Risk Exposure
Estimated annualized risk exposure is $2M to $18M or higher.
Annualized risk exposure is based on SD-WAN footprint, internet exposure, controller criticality, branch dependency, data-center and cloud connectivity, sensitive-segment reliance, approved-peer inventory quality, NETCONF access control, administrative-source governance, configuration-audit readiness, service-provider dependency, telemetry completeness, containment complexity, route and policy rollback burden, operational downtime, and legal or regulatory obligations.
Operational Dependency
Organizations with high dependency on SD-WAN for branch operations, data-center access, cloud connectivity, remote-site communication, service-provider administration, or centralized routing policy face elevated economic exposure because control-plane uncertainty can create broad business assurance requirements.
Control Trust
Economic impact increases when the organization cannot quickly confirm that SD-WAN peer relationships, administrative access, NETCONF workflows, configuration changes, route state, tunnel behavior, policy enforcement, certificate posture, and fabric-trust relationships remain authorized.
Visibility Confidence
Exposure increases when Controller logs, Manager logs, authentication records, NETCONF records, configuration audit logs, network-flow telemetry, peer inventory, topology records, provider records, or change-management data are missing, delayed, incomplete, or difficult to correlate.
Change-Control Confidence
Cost increases when SD-WAN route, tunnel, policy, certificate, template, device-registration, peer-state, controller-relationship, or fabric-trust changes cannot be tied to approved maintenance, automation, service-provider activity, emergency access, disaster recovery, or documented change records.
Downstream Dependency
Organizational exposure expands when suspicious SD-WAN activity could affect sensitive internal segments, identity systems, management systems, backup systems, data-center environments, cloud networks, regulated systems, customer-facing services, or business-critical branch operations.
Customer and Regulatory Exposure
Customer and regulatory exposure depends on whether unauthorized SD-WAN trust activity, administrative access, NETCONF use, configuration manipulation, segmentation impact, or connectivity disruption affected regulated environments, contractual service obligations, customer-facing services, sensitive systems, or evidence required for incident investigation.
Residual Economic Risk
Patching, mitigation, exposure removal, or vendor remediation reduces future risk, but it does not prove that pre-remediation exploitation did not occur. Systems exposed before mitigation still require historical review of peering activity, administrative authentication, NETCONF access, configuration changes, topology drift, route and tunnel behavior, policy changes, traffic-flow impact, and recurring unfamiliar access.
Proof-of-Concept Behavioral Coverage Assessment
This report’s behavioral detection model is designed to evaluate Cisco SD-WAN control-plane abuse patterns that align with unauthorized peering, suspicious administrative authentication, NETCONF access, configuration manipulation, peer-state anomalies, route or tunnel changes, policy modification, certificate or fabric-trust changes, and post-access traffic-flow impact. The report remains behavior-led and should not be interpreted as limited to a single CVE, exploit script, or proof-of-concept implementation.
CVE-2026-20127 is the primary vulnerability record used to anchor this report’s Cisco Catalyst SD-WAN Controller authentication-bypass model. Related Cisco SD-WAN exploitation reports, proof-of-concept behavior, or newly disclosed vulnerabilities should be evaluated against whether the observed activity follows the same SD-WAN trust-establishment, administrative-control, NETCONF, or configuration-impact sequence.
Detection Engineering Coverage Interpretation
The S25 detection content would provide coverage for CVE-2026-20127-style activity where observable behavior includes suspicious SD-WAN control-plane interaction, rogue peering, unexpected peer-state changes, unfamiliar peer identity fields, successful administrative authentication from unfamiliar sources, NETCONF access from unauthorized networks, configuration changes, or traffic-flow impact following suspicious SD-WAN access.
Coverage is strongest where related activity produces observable artifacts already aligned to S25 logic, including unauthorized peering, suspicious administrative authentication, NETCONF access, configuration manipulation, peer-state anomalies, topology mismatch, route or tunnel changes, policy modification, certificate or fabric-trust changes, and new communication paths involving branch, data-center, cloud, remote-site, or sensitive internal segments.
Direct Coverage
Direct behavioral coverage applies where CVE-2026-20127-style activity produces telemetry matching existing S25 rule logic without material changes. This includes SD-WAN control-plane, administrative, NETCONF, configuration, topology, peer-state, and traffic-flow behavior already represented in the report’s S25 detection model.
Relevant S25 coverage areas include:
· Suspicious SD-WAN peering or control-plane interaction.
· Rogue peer registration or unexpected peer-state changes.
· Unfamiliar System IPs, site IDs, domain IDs, peer types, public IPs, device identities, or controller relationships.
· Successful administrative authentication from unfamiliar, external, unauthorized, cloud-hosted, VPN-associated, service-provider, or unmanaged source infrastructure.
· NETCONF access from unfamiliar or unauthorized sources.
· SD-WAN configuration changes affecting routes, tunnels, policies, certificates, templates, device registration, peer state, controller relationships, or fabric trust.
· New or unexpected traffic-flow behavior after suspicious control-plane, administrative, NETCONF, or configuration activity.
· Persistent or recurring access from unfamiliar sources after remediation, rollback, patching, or configuration correction.
Coverage With Adaptation
Coverage with adaptation applies where related Cisco SD-WAN activity is aligned with the S25 model but requires local tuning for affected component scope, deployment model, provider-management arrangement, administrative-source baselines, NETCONF exposure, topology inventory, configuration-object types, or platform-specific logging.
Adaptation should focus on:
· Scoping detections to affected Cisco SD-WAN Controllers, Managers, Validators, edge devices, NETCONF-exposed infrastructure, and provider-managed access paths.
· Mapping local telemetry for control-plane activity, peer-state changes, administrative authentication, NETCONF access, configuration audit logs, network-flow metadata, and topology inventory.
· Updating approved peer inventories for System IPs, site IDs, domain IDs, peer types, public IPs, device identities, and controller relationships.
· Integrating administrative-source baselines, provider records, automation records, emergency-access records, and change-management context into the correlation model.
· Tuning approved controller migration, disaster recovery, edge onboarding, service-provider support, automation, maintenance-window, and emergency-access workflows.
Non-Coverage Conditions
Non-coverage applies where related activity does not produce observable SD-WAN control-plane, administrative, NETCONF, configuration, topology, peer-state, or traffic-flow artifacts. Activity limited to unrelated software flaws, endpoint-only compromise, non-SD-WAN infrastructure, non-management-plane exploitation, or activity that cannot be observed through available SD-WAN telemetry should not be represented as covered by this report.
Where activity occurs against Cisco SD-WAN infrastructure but lacks sufficient telemetry to validate peering, authentication, NETCONF access, configuration change, topology drift, or traffic-flow impact, the correct report output is an exposure or assurance finding rather than a confirmed detection claim.
Current Coverage Count
Directly covered CVEs / proof-of-concept behavior patterns: 1 — CVE-2026-20127-style Cisco Catalyst SD-WAN Controller authentication-bypass activity involving unauthorized control-plane trust, rogue peering, administrative access, NETCONF management, configuration manipulation, or SD-WAN fabric-impact behavior.
Covered with adaptation: 0.
Not currently counted as separately covered: 0.
Total CVE / proof-of-concept behavior patterns directly or largely covered by this report’s behavioral detection model: 1.
Coverage Qualification
This count should be treated as a living analytical note, not a universal-coverage claim. A related Cisco SD-WAN CVE, exploitation report, or proof-of-concept should only be added when it shares enough observable behavior with the report’s detection model to support credible detection or detection-readiness coverage. A related CVE or proof-of-concept should not be counted when it depends on an unrelated exploitation mechanism, lacks sufficient technical detail, produces no aligned telemetry, or requires a separate detection model.
S40 — References
Vendor / Platform Documentation
Cisco Catalyst SD-WAN Controller Authentication Bypass Vulnerability
hxxps://sec[.]cloudapps[.]cisco[.]com/security/center/content/CiscoSecurityAdvisory/cisco-sa-sdwan-rpa-EHchtZk
Cisco Catalyst SD-WAN Hardening Guide
hxxps://sec[.]cloudapps[.]cisco[.]com/security/center/resources/Cisco-Catalyst-SD-WAN-HardeningGuide
Vulnerability Records
CVE Record — CVE-2026-20127 vulnerability details
hxxps://www[.]cve[.]org/CVERecord?id=CVE-2026-20127
NVD Record — CVE-2026-20127 vulnerability details
hxxps://nvd[.]nist[.]gov/vuln/detail/CVE-2026-20127
Known Exploited Vulnerabilities
CISA and Partners Release Guidance for Ongoing Global Exploitation of Cisco SD-WAN Systems
hxxps://www[.]cisa[.]gov/news-events/alerts/2026/02/25/cisa-and-partners-release-guidance-ongoing-global-exploitation-cisco-sd-wan-systems
Threat Tradecraft and Intrusion Patterns
MITRE ATT&CK Framework — Enterprise Matrix
hxxps://attack[.]mitre[.]org