[EXP] Ollama AI Infrastructure Exposure Memory Disclosure Risk in Self-Hosted Model Servers
Report Type:
EXP
Threat Category:
AI Infrastructure Exposure / Sensitive Runtime Context Disclosure
Assessment Date:
May 9, 2026
Primary Impact Domain:
Sensitive Data Exposure
Secondary Impact Domains:
Credential Exposure, Intellectual Property Exposure, Cloud and Repository Access Risk, Developer Workflow Disruption, AI Infrastructure Trust, Regulatory and Customer Assurance Risk
Affected Asset Class:
Self-Hosted AI Model Servers / Ollama Infrastructure
Threat Objective Classification:
Exposure Exploitation / Runtime Context Access / Downstream Credential Enablement
BLUF
[EXP] Ollama AI Infrastructure Exposure Memory Disclosure Risk in Self-Hosted Model Servers creates material enterprise risk by turning exposed AI model infrastructure into a potential path for sensitive runtime data exposure. The risk is driven by vulnerable or unpatched Ollama services that are reachable from the internet, untrusted internal networks, shared AI lab environments, developer systems, or broadly accessible model-serving paths. The threat posture is elevated because Ollama environments may process sensitive prompts, source code, credentials, API tokens, environment variables, tool outputs, customer data, internal documentation, and automation context. Executive action is required to validate exposure, confirm patch state, restrict unsafe access, preserve AI infrastructure telemetry, review suspicious model-ingestion activity, assess model artifact handling, investigate unusual outbound communication, and determine whether exposed runtime context created downstream credential, data, or operational risk.
Executive Risk Translation
This threat shifts business risk from isolated AI service exposure to loss of confidence in self-hosted model infrastructure that may process sensitive enterprise context. The primary concern is not only whether an Ollama server was vulnerable, but whether exposed model-serving infrastructure allowed untrusted interaction with model-ingestion, artifact-handling, or model-transfer functionality before remediation. If suspicious activity occurred, response may expand into service containment, model artifact review, prompt and data exposure assessment, credential and API-token rotation, repository and cloud access review, developer workflow validation, outbound communication analysis, legal review, business-unit assurance, and executive incident governance. This creates financial, operational, data-protection, intellectual-property, security-governance, and reputational exposure beyond the initially affected model server.
S3 — Why This Matters Now
· Ollama exposure should be treated as an AI infrastructure risk, not as a routine developer-tool issue.
· Self-hosted model servers may process prompts, source code, credentials, API tokens, tool outputs, customer information, and internal operational context.
· Exposed or broadly reachable Ollama services create risk when untrusted sources can interact with model-ingestion, model-import, artifact-handling, or model-push functionality.
· Memory disclosure risk is materially different from ordinary service exposure because sensitive runtime context may be exposed without clear evidence of traditional host compromise.
· Patch status alone does not prove that exposed or vulnerable Ollama infrastructure was not accessed or abused before remediation.
· Historical review is required for Ollama services that were internet-facing, reachable from untrusted internal networks, deployed in shared AI labs, or connected to sensitive workflows before patch validation.
· Detection must focus on behavior-led correlation across exposure, model-ingestion activity, artifact changes, runtime instability, outbound communication, and downstream credential or identity activity.
· Exposure-only telemetry should support prioritization and hunting, but it must not be treated as confirmed data exposure without suspicious interaction or follow-on evidence.
· Organizations without reliable asset inventory, route-level logs, endpoint telemetry, model artifact monitoring, container visibility, DNS logs, egress monitoring, and identity or credential-management telemetry face elevated risk of delayed detection and incomplete scoping.
S4 — Key Judgments
· Ollama AI infrastructure exposure creates a high-priority data-exposure and runtime-context risk when vulnerable or unpatched model servers are reachable from untrusted paths.
· The primary business risk is unauthorized exposure of sensitive prompts, credentials, source code, customer data, tool outputs, internal documentation, or environment context processed by self-hosted model infrastructure.
· The strongest enterprise risk signal is exposed Ollama infrastructure receiving suspicious model-ingestion activity followed by unusual model artifact creation, runtime instability, outbound communication, model-push behavior, or downstream credential activity.
· Exposed or vulnerable Ollama services should drive urgent remediation and retrospective review, but exposure alone should not be treated as confirmed compromise.
· Model artifact activity is a high-value detection anchor because suspicious model ingestion may create new model files, artifact changes, manifest updates, or abnormal writes to model storage paths.
· Outbound communication after suspicious model activity is a high-priority escalation signal because it may indicate artifact transfer, data movement, attacker-directed communication, or post-exposure activity.
· Identity, cloud, repository, and credential-management telemetry are important because the most damaging outcome may occur after exposed secrets or runtime context are used elsewhere.
· Detection must remain behavior-led because model names, artifact names, payload details, source infrastructure, destination infrastructure, and public proof-of-concept details can change quickly.
· Network-only visibility is insufficient because it may not confirm model artifact creation, memory-related instability, local file activity, or downstream credential use.
· Executive risk reduction depends on exposed asset identification, patch validation, access restriction, telemetry preservation, model artifact review, egress analysis, credential rotation where warranted, and validated detection coverage across AI infrastructure, endpoint, container, network, identity, cloud, and repository telemetry.
S5 — Executive Risk Summary
Business Risk
Ollama AI infrastructure exposure can create material data-protection, intellectual-property, operational, and security-governance risk when self-hosted model servers process sensitive prompts, source code, customer data, credentials, API tokens, environment variables, tool outputs, internal documentation, or automation context. Risk increases when affected systems support developer workflows, coding assistants, AI labs, shared model infrastructure, CI systems, cloud workloads, customer-support workflows, regulated data handling, or internal automation connected to privileged tools.
Technical Cause
The risk is driven by vulnerable or unpatched Ollama services that are reachable from internet-facing, untrusted internal, broadly accessible, or poorly segmented network paths. The enterprise detection model should focus on exposed service access, suspicious model-ingestion or model-transfer functionality, abnormal model artifact creation, runtime instability, process crashes, unusual outbound communication, model-push behavior, and downstream credential or identity activity.
Threat Posture
The threat posture is elevated because successful abuse may expose sensitive runtime context without requiring conventional malware deployment, persistent access, or obvious host compromise. The risk is amplified when Ollama environments are connected to repositories, development systems, cloud accounts, secrets, customer workflows, automation tools, or internal APIs. Affected organizations may need to determine not only whether the model server was exposed, but whether sensitive prompts, credentials, source code, model artifacts, or tool outputs were accessible during the exposure window.
Executive Decision Requirement
Executives must require immediate validation of Ollama asset inventory, exposure state, patch status, access restrictions, model-ingestion history, artifact changes, runtime instability, outbound communication, linked credentials, repository access, cloud activity, and telemetry coverage. Response leadership should also confirm that vulnerable or exposed systems receive retrospective review and downstream credential-risk assessment rather than being closed solely on patch completion.
S6 — Executive Cost Summary
[EXP] Ollama AI Infrastructure Exposure Memory Disclosure Risk in Self-Hosted Model Servers creates financial exposure based on exposed-server count, exposure duration, patch latency, sensitive prompt and data scope, credential and token footprint, developer workflow dependency, model artifact activity, outbound communication, telemetry completeness, downstream credential use, repository or cloud integration risk, containment burden, and the degree to which exposed model infrastructure may have processed proprietary code, customer data, secrets, tool outputs, or regulated information.
Low Impact Scenario
Rapid assessment confirms that affected Ollama services were patched or mitigated quickly, were not reachable from untrusted networks, access was limited to approved administrative paths, logs are preserved, no suspicious model-ingestion activity is observed, no unusual model artifacts were created, no runtime instability occurred near suspicious access, no abnormal outbound communication is linked to the exposure, and no downstream credential, repository, cloud, or identity activity indicates misuse. Response still requires emergency inventory validation, patch confirmation, access restriction review, limited model artifact review, targeted credential exposure assessment, endpoint and network hunting, and executive tracking because sensitive AI infrastructure exposure existed; estimated impact $250K to $2M.
Moderate Impact Scenario
One or more Ollama servers were vulnerable, unpatched, internet-facing, broadly reachable, or accessible through untrusted internal paths during the exposure window, and investigation identifies suspicious model-ingestion activity, unusual model artifact handling, runtime instability, rare outbound communication, model-push behavior, incomplete telemetry, or limited downstream credential concern without confirmed large-scale data exposure, sustained adversary control, or broad cloud, repository, or customer-data impact. Response requires incident-response mobilization, service containment, model artifact review, prompt and data exposure assessment, targeted credential and API-token rotation, developer workflow validation, egress analysis, endpoint and container review, cloud and repository access review, detection tuning, legal assessment, executive coordination, and business-unit or customer communications readiness; estimated impact $3M to $15M.
High Impact Scenario
Confirmed or strongly suspected exposure affects Ollama infrastructure connected to sensitive prompts, proprietary source code, customer data, credentials, API tokens, environment variables, cloud services, repositories, CI systems, internal APIs, or shared AI workflows, with evidence of suspicious model-ingestion activity, abnormal artifact creation, runtime instability, unusual outbound communication, model-push behavior, credential use, repository access, cloud activity, or incomplete historical telemetry. Response may require broad service containment, AI workflow suspension, model artifact quarantine, credential and token rotation at scale, repository and cloud access review, customer-data impact assessment, developer environment validation, automation review, infrastructure rebuild, legal and regulatory review, cyber insurance engagement, customer assurance where applicable, and board-level incident governance; estimated impact $20M to $100M or higher.
S6A — Key Cost Drivers
· Number of affected Ollama servers, self-hosted AI model servers, shared AI lab systems, developer workstations, container hosts, and cloud-hosted model-serving workloads.
· Whether affected Ollama services were internet-facing, externally reachable, broadly reachable internally, or accessible from untrusted network paths before remediation.
· Duration of exposure before patch validation, access restriction, service isolation, or compensating control deployment.
· Whether the affected environment processed proprietary source code, customer data, credentials, API tokens, secrets, tool outputs, regulated information, or sensitive internal prompts.
· Whether suspicious model-ingestion, model import, artifact handling, model-push, or model-transfer behavior occurred before remediation.
· Whether suspicious activity was followed by new model artifacts, model storage changes, unusually large model files, temporary model components, or writes outside approved model paths.
· Whether suspicious access was followed by Ollama crashes, process restarts, abnormal memory pressure, model-loading errors, service instability, container restarts, or runtime anomalies.
· Whether outbound communication occurred to newly observed, rare, unapproved, cloud-storage, file-sharing, anonymous-hosting, unknown model-registry, or low-prevalence destinations.
· Scope of credentials, API tokens, repository access tokens, cloud credentials, service-account keys, environment variables, secrets, or tool outputs potentially present in the Ollama runtime environment.
· Whether affected systems were connected to coding assistants, CI systems, cloud accounts, internal APIs, customer-support workflows, developer repositories, or automation tools.
· Availability and retention of reverse proxy logs, ingress logs, application logs, endpoint telemetry, file telemetry, container logs, DNS logs, firewall logs, NDR telemetry, egress records, cloud audit logs, identity logs, and credential-management activity.
· Ability to map Ollama hosts to owners, users, service accounts, repositories, cloud roles, deployment environments, approved model sources, and approved outbound destinations.
· Need for credential rotation, API-token replacement, cloud-key review, repository access review, secrets-management validation, model artifact review, prompt exposure assessment, or customer-data scoping.
· Degree to which incomplete telemetry forces broader containment, credential rotation, model artifact quarantine, developer workflow suspension, or executive incident governance.
· Need for legal review, regulatory assessment, customer assurance, contractual notification analysis, insurance reporting, workforce communications, or board-level oversight.
Most Likely Scenario Justification
Moderate scenario is most likely when exposed or vulnerable Ollama infrastructure requires historical compromise review and sensitive runtime context assessment, but available evidence does not confirm large-scale data exposure, sustained adversary control, broad credential misuse, repository compromise, cloud compromise, or customer-impacting disclosure. The estimate moves toward the lower end when telemetry confirms rapid remediation, short exposure duration, no suspicious model-ingestion activity, no unusual artifact creation, no runtime instability, no abnormal egress, no sensitive workflow connection, and no downstream credential activity. The estimate moves toward the upper end when affected systems are internet-facing, process sensitive prompts or source code, connect to cloud services or internal automation, have incomplete telemetry, show suspicious model activity, include unusual artifact handling, require credential rotation, or trigger repository, cloud, customer-data, or regulated-data review.
S6B — Compliance and Risk Context
Compliance Exposure Indicator
Moderate to High depending on whether sensitive prompts, customer data, regulated information, source code, credentials, API tokens, secrets, tool outputs, repository content, cloud access, downstream identity activity, customer-impact uncertainty, or incomplete forensic scoping affected systems subject to regulatory, contractual, privacy, customer, insurance, intellectual-property, or material business obligations.
Risk Register Entry
Risk Title
Ollama AI Infrastructure Exposure and Sensitive Runtime Context Disclosure Risk
Risk Description
Adversaries may access or abuse exposed, vulnerable, or unpatched Ollama model-serving infrastructure to interact with model-ingestion or model-transfer functionality, trigger abnormal model artifact handling, expose sensitive runtime context, communicate externally from AI infrastructure, or enable downstream use of credentials, API tokens, source code, prompts, customer data, environment variables, tool outputs, repositories, cloud services, or internal automation paths.
Likelihood
High.
Impact
Severe.
Risk Rating
Critical.
Annualized Risk Exposure
Estimated $5M to $35M or higher based on exposed Ollama server count, untrusted reachability, exposure duration, patch latency, sensitive prompt and data scope, credential and token footprint, developer workflow dependency, cloud or repository integration, model artifact activity, outbound communication, telemetry completeness, containment complexity, downstream credential risk, customer assurance requirements, and legal or regulatory obligations.
S7 — Risk Drivers
· Exposed or broadly reachable Ollama services create direct access paths to self-hosted AI model infrastructure.
· Vulnerable or unpatched model servers increase the likelihood that suspicious model-ingestion behavior can create sensitive runtime data exposure.
· Ollama environments may process prompts, source code, credentials, API tokens, environment variables, tool outputs, customer data, and internal operational context.
· AI lab systems and developer-hosted model servers may have weaker access controls, incomplete logging, temporary deployment patterns, or unclear ownership.
· Shared model infrastructure can expand blast-radius risk when multiple users, teams, workflows, or automation paths depend on the same model-serving environment.
· Model-ingestion, model import, artifact creation, and model-push behavior create durable detection anchors but may also overlap with legitimate AI experimentation.
· Runtime instability after suspicious model-ingestion activity may indicate abnormal model handling even when direct memory visibility is unavailable.
· Unusual outbound communication after model activity may indicate artifact transfer, data movement, attacker-directed communication, or follow-on activity.
· Credential or token exposure can force rotation across cloud accounts, repositories, CI systems, internal APIs, service accounts, developer tools, and secrets-management platforms.
· Patch validation does not prove exposed systems were uncompromised before remediation.
· Missing asset inventory, route-level logs, endpoint telemetry, file telemetry, container logs, DNS records, egress telemetry, identity logs, or credential-management records can materially weaken scoping.
· Legitimate model experimentation, model pulls, model imports, automation, patching, scanning, monitoring, and developer testing can resemble suspicious behavior without strong ownership and baseline context.
· Over-reliance on static exploit strings, public proof-of-concept artifacts, file names, model names, attacker infrastructure, or fixed payload indicators can miss evolved activity and post-exposure behavior.
S8 — Bottom Line for Executives
[EXP] Ollama AI Infrastructure Exposure Memory Disclosure Risk in Self-Hosted Model Servers should be treated as a high-priority AI infrastructure and sensitive runtime context risk because exposed model-serving environments may process prompts, source code, secrets, customer data, tool outputs, and credentials. The key executive concern is not only whether affected Ollama services were patched, but whether exposed systems received suspicious model-ingestion activity or generated follow-on evidence of abnormal artifact handling, outbound communication, runtime instability, or downstream credential use before remediation. Risk reduction depends on exposed asset scoping, patch validation, access restriction, log preservation, model artifact review, egress analysis, prompt and data exposure assessment, credential review, downstream cloud and repository hunting, and behavior-based detection coverage. Organizations should prioritize this report as an AI infrastructure trust issue because successful exposure can create data-protection uncertainty, intellectual-property risk, credential risk, developer workflow disruption, customer assurance pressure, regulatory uncertainty, and board-level incident governance requirements.
S9 — Board-Level Takeaway
Ollama exposure turns self-hosted AI model infrastructure into a potential sensitive-data and credential-risk surface. The board-level concern is that attackers may target the same systems used to process prompts, source code, credentials, tool outputs, customer data, and internal automation context. Leadership should require evidence that affected Ollama infrastructure has been identified, unsafe exposure has been removed or restricted, patch state has been validated, historical activity has been reviewed, model artifacts have been assessed, outbound communication has been analyzed, credentials and tokens have been evaluated, and downstream repository, cloud, identity, and secrets-management activity can be scoped with confidence. This report supports governance decisions around AI infrastructure security, sensitive data handling, exposure management, credential containment, telemetry readiness, incident-response escalation, regulatory posture, and executive oversight of self-hosted model-server risk
Figure 2
S10 — Threat Overview
Ollama AI Infrastructure Exposure Memory Disclosure Risk in Self-Hosted Model Servers concerns exposed or vulnerable self-hosted AI model infrastructure that may process sensitive enterprise runtime context. The core risk is that an Ollama service reachable from the internet, untrusted internal networks, shared AI labs, developer environments, or broadly accessible model-serving paths may receive suspicious model-ingestion or artifact-handling activity before remediation.
This exposure should be treated as an AI infrastructure risk rather than a standard web application issue. Ollama environments may process prompts, source code, credentials, API tokens, environment variables, tool outputs, internal documentation, customer data, and automation context. If vulnerable infrastructure is reachable from untrusted paths, the business concern is not limited to service exposure. The concern is whether sensitive runtime context, model artifacts, credentials, or downstream access paths were exposed, transferred, or later abused.
The highest-value threat model is behavior-led. Defenders should focus on exposed service reachability, suspicious model-ingestion activity, abnormal model artifact handling, runtime instability, unusual outbound communication, and downstream credential or identity activity. Exposure alone should not be treated as confirmed compromise. Suspicious model activity, artifact changes, egress, instability, or post-exposure credential use materially increases confidence and response priority.
S11 — Threat Classification and Type
Threat Type
AI infrastructure exposure and sensitive runtime context disclosure risk.
Threat Sub-Type
Self-hosted model server exposure with suspicious model-ingestion, artifact-handling, outbound communication, and downstream credential-risk potential.
Operational Classification
Exposed AI model-serving infrastructure with potential data-exposure, credential-exposure, developer-workflow, and downstream access implications.
Primary Function
The primary function of the threat is to create risk that sensitive runtime context processed by Ollama infrastructure may be exposed through vulnerable or untrusted interaction with the model-serving environment. The most material enterprise concern is unauthorized access to prompts, source code, credentials, tokens, model artifacts, tool outputs, customer data, or automation context associated with self-hosted AI workflows.
S12 — Campaign or Activity Overview
This report does not require a named adversary campaign to establish material risk. The relevant activity pattern is exposure of vulnerable or unpatched Ollama model-serving infrastructure to untrusted access paths, followed by suspicious interaction with model-ingestion, model-import, model artifact, or model-transfer functionality.
Observed or suspected activity should be evaluated through a sequence-based model. The most relevant sequence begins with exposed Ollama service reachability, progresses to suspicious model-ingestion or artifact-handling behavior, and becomes more serious when paired with new model artifacts, runtime instability, unusual outbound communication, model-push behavior, or downstream credential and identity anomalies.
The exposure is most concerning in environments where Ollama is connected to developer repositories, coding assistants, AI labs, CI systems, cloud services, internal APIs, secrets, customer workflows, or automation tools. In those environments, memory disclosure or sensitive runtime exposure can create downstream risk even when there is no evidence of traditional malware deployment, persistence, or confirmed host compromise.
This activity should be investigated as a potential data-exposure and credential-risk event when vulnerable Ollama infrastructure was reachable from untrusted networks or when suspicious model lifecycle behavior occurred during the exposure window.
S13 — Targets and Exposure Surface
Primary targets are self-hosted Ollama services and related AI model-serving environments that are vulnerable, unpatched, exposed, broadly reachable, or insufficiently segmented.
Relevant exposure surfaces include:
· Internet-facing Ollama services.
· Ollama services reachable from untrusted internal networks.
· Shared AI lab servers.
· Developer workstations running Ollama with broad network reach.
· Containerized Ollama deployments.
· Cloud-hosted model-serving workloads.
· Internal shared model infrastructure.
· CI or automation environments connected to Ollama.
· Model-serving systems connected to coding assistants, repositories, internal APIs, or cloud services.
· Ollama hosts that process prompts, source code, credentials, API tokens, tool outputs, customer data, or sensitive internal context.
The highest-risk exposure occurs when model-serving infrastructure is both reachable from untrusted paths and connected to sensitive workflows. Developer convenience deployments, AI labs, proof-of-concept servers, unmanaged containers, and temporary cloud instances may create elevated risk because they can combine sensitive context with weaker logging, weaker access control, unclear ownership, and incomplete monitoring.
S14 — Sectors / Countries Affected
Sectors Affected
· Technology, software development, AI engineering, and cloud-hosted enterprises.
· Financial services and banking.
· Healthcare and life sciences.
· Manufacturing and industrial operations.
· Energy, utilities, and critical infrastructure.
· Retail, ecommerce, and customer-support environments.
· Education, research institutions, and AI labs.
· Government and public-sector organizations.
· Telecommunications and managed service providers.
· Enterprise IT operations, security operations, and organizations running self-hosted AI infrastructure.
· Organizations using Ollama or comparable self-hosted model-serving environments to process source code, prompts, customer data, internal documentation, tool outputs, credentials, API tokens, cloud context, or automation workflows.
Countries Affected
· Global.
· Exposure is not limited to a single country or region because self-hosted Ollama deployments can exist anywhere organizations operate developer environments, AI labs, cloud workloads, research systems, shared model infrastructure, or internal automation.
· Countries with large technology sectors, cloud adoption, regulated industries, research institutions, software-development ecosystems, government AI adoption, or high-value enterprise data may face elevated operational exposure.
· Country-specific impact should be assessed by Ollama deployment presence, internet or untrusted-network reachability, patch state, sensitive workflow connection, telemetry quality, exposure duration, and incident-response readiness rather than geography alone.
S15 — Adversary Capability Profiling
Capability Level
Moderate to High.
Technical Sophistication
Technical sophistication is assessed as moderate to high because the most relevant activity requires identifying exposed AI model-serving infrastructure, interacting with model-ingestion or artifact-handling functionality, and potentially using exposed runtime context for downstream access. The activity does not require highly customized malware in every case, but it does require understanding AI infrastructure behavior, model lifecycle operations, exposed service paths, and the value of prompts, credentials, source code, and tool outputs.
Infrastructure Maturity
Infrastructure maturity may range from opportunistic scanning infrastructure to organized infrastructure used for staged access, model artifact transfer, outbound communication, or downstream credential use. Mature operators may rotate source infrastructure, vary model names, change artifact names, use cloud-hosted destinations, and avoid static indicators.
Operational Scale
Operational scale can range from opportunistic discovery of exposed Ollama services to targeted activity against organizations with valuable AI workflows, source code, customer data, cloud integrations, or developer automation. Scale increases when exposed services are discoverable, unpatched, unauthenticated, or deployed in shared lab and developer environments.
Escalation Likelihood
Escalation likelihood is moderate when exposed Ollama infrastructure is isolated, patched quickly, and not connected to sensitive workflows. Escalation likelihood becomes high when the service is internet-facing, unpatched, connected to repositories or cloud services, processing sensitive prompts or credentials, showing suspicious model-ingestion behavior, creating unusual artifacts, communicating with unfamiliar destinations, or followed by downstream credential activity.
S16 — Targeting Probability Assessment
Overall Targeting Probability
High for exposed, vulnerable, internet-facing, or broadly reachable Ollama infrastructure. Moderate for internal-only deployments with weak segmentation, shared access, sensitive workflow connections, or incomplete telemetry. Lower for patched, isolated, local-only deployments with strong access controls, no sensitive workflow connection, and reliable telemetry.
Targeting Drivers
· Internet-facing or broadly reachable Ollama services.
· Vulnerable or unpatched model-serving infrastructure.
· Weak authentication, access restriction, or segmentation around AI infrastructure.
· Developer, AI lab, or proof-of-concept deployments with unclear ownership.
· Ollama environments connected to source code, repositories, cloud services, internal APIs, CI systems, or automation tools.
· Runtime context that may include prompts, credentials, API tokens, secrets, tool outputs, or customer data.
· Incomplete logging, incomplete endpoint coverage, limited egress visibility, or weak model artifact monitoring.
· Public discoverability of exposed services and reusable model-serving access patterns.
Most Likely Targets
· Internet-facing Ollama services.
· Shared AI lab servers.
· Developer workstations or servers running Ollama with broad network reach.
· Cloud-hosted self-hosted model-serving workloads.
· Containerized Ollama deployments with exposed ports or weak ingress controls.
· Internal shared model infrastructure used by multiple teams.
· AI systems connected to coding assistants, repositories, CI systems, internal APIs, or cloud services.
· Organizations using self-hosted model infrastructure for sensitive prompts, proprietary code, customer data, or automation workflows.
S17 — MITRE ATT&CK Chain Flow Mapping
Stage 1 — Exposure Identification and Target Selection
Adversaries identify Ollama services reachable from the internet, untrusted internal networks, shared AI lab environments, cloud workloads, or broadly accessible model-serving paths. This stage may involve internet-scale discovery, targeted probing, or validation of access to exposed AI model infrastructure.
MITRE ATT&CK Mapping
T1595 — Active Scanning
Stage 2 — Initial Access Through Exposed Model Server
Adversaries interact with exposed Ollama service functionality and attempt to exploit or abuse vulnerable model-serving infrastructure. The core access path is exploitation or abuse of a public-facing or untrusted-reachable application service.
MITRE ATT&CK Mapping
T1190 — Exploit Public-Facing Application
Stage 3 — Suspicious Model Lifecycle Interaction
Adversaries may interact with model-ingestion, model-import, model artifact, blob, or model-push functionality. This stage is the key activity anchor for the report and should be assessed through route-level logs, proxy logs, endpoint file activity, model storage changes, and container telemetry where available.
MITRE ATT&CK Mapping
T1105 — Ingress Tool Transfer, conditional where model artifacts, files, or external content are transferred into the model-serving environment
Stage 4 — Conditional Sensitive Data or Credential Exposure
If vulnerable runtime context is exposed, adversaries may obtain sensitive prompts, credentials, API tokens, environment variables, source code, customer data, tool outputs, or other material processed by the Ollama environment. This stage should remain evidence-driven and should not be assumed without supporting telemetry, artifact review, credential activity, or incident-response findings.
MITRE ATT&CK Mapping
T1552 — Unsecured Credentials, conditional where exposed tokens, secrets, environment variables, or credentials are identified
Stage 5 — Conditional Outbound Transfer or External Communication
If suspicious model activity is followed by outbound communication, adversaries may transfer model artifacts, exposed runtime data, or related content through unfamiliar external infrastructure. This stage should require linkage to the Ollama host, container, model activity window, or related outbound destination. It should not be assumed from egress alone.
MITRE ATT&CK Mapping
T1567 — Exfiltration Over Web Service, conditional where outbound transfer uses cloud storage, file-sharing, web-service, or other externally hosted destinations.
T1041 — Exfiltration Over C2 Channel, conditional where outbound transfer is linked to suspected adversary-controlled communication rather than approved model registries, update services, telemetry, backups, monitoring, or container registry activity.
Stage 6 — Conditional Downstream Credential or Cloud Use
If credentials, API tokens, repository tokens, cloud keys, or service-account material were exposed, adversaries may attempt downstream access to cloud services, repositories, internal APIs, or automation platforms. This stage should require identity, repository, cloud, credential-management, or audit-log evidence.
MITRE ATT&CK Mapping
T1078 — Valid Accounts, conditional where exposed or stolen credentials are used for downstream access
S18 — Attack Path Narrative (Signal-Aligned Execution Flow)
Initial Exposure
The attack path begins when an Ollama model server is exposed to the internet, an untrusted internal network, a shared AI lab environment, a cloud workload, a container ingress path, or a developer environment with broad network reach. This exposure may occur through public IP association, permissive firewall rules, weak ingress controls, unmanaged lab infrastructure, temporary cloud deployment, or developer convenience configuration.
At this stage, the primary signal is exposure rather than confirmed compromise. The required defensive action is to validate whether the Ollama service is reachable from untrusted sources, whether the deployment is vulnerable or unpatched, and whether the service processes sensitive prompts, code, credentials, tool outputs, customer data, or automation context.
Model-Service Interaction
Adversaries interact with the exposed Ollama service from internet-originating, unfamiliar, untrusted, or otherwise unapproved infrastructure. This activity may appear as targeted probing, repeated access attempts, interaction with model-related API functionality, abnormal request timing, large request bodies, or access inconsistent with approved administrative or model-management workflows.
The primary signal is suspicious interaction with an exposed model-serving service. This should support investigation or exploit-attempt classification, but it should not be treated as confirmed data exposure without supporting artifact, runtime, egress, credential, or incident-response evidence.
Model Lifecycle Activity
If the exposed service is vulnerable or improperly controlled, attacker interaction may involve model ingestion, model import, artifact handling, blob activity, or model-push behavior. This is the key behavioral stage for the report because it connects untrusted access to model lifecycle functionality rather than ordinary service reachability.
The primary signals at this stage are suspicious model-ingestion activity, new or unusual model artifacts, model storage changes, manifest updates, temporary model components, unusual model file sizes, or writes outside approved model paths. These signals become more meaningful when they occur on internet-facing, unpatched, shared, or sensitive Ollama infrastructure.
Runtime and Artifact Anomalies
Suspicious model lifecycle activity may be followed by runtime instability or abnormal host, container, or storage behavior. Observable activity may include Ollama crashes, process restarts, container restarts, abnormal memory pressure, model-loading errors, service instability, or model artifact changes that do not align with approved model-management activity.
The primary signal is a time-linked relationship between suspicious model-service interaction and abnormal runtime or artifact behavior. Instability alone is not sufficient for confirmed compromise, but instability following untrusted model-ingestion activity should be treated as a high-priority investigation lead.
Outbound Communication
The attack path becomes more serious when suspicious model activity is followed by outbound communication from the Ollama host or container. Outbound behavior may include communication with newly observed, rare, unapproved, cloud-storage, file-sharing, anonymous-hosting, or unknown model-registry destinations.
The primary signal is a same-host or same-container relationship between suspicious model lifecycle activity and unusual outbound communication. This requires careful distinction between approved model pulls, approved model pushes, patching, telemetry, backups, monitoring, container registry activity, and unfamiliar destinations outside the approved model-source or egress baseline.
Conditional Downstream Credential or Data Use
If sensitive runtime context is exposed, downstream activity may appear in identity, cloud, repository, CI, internal API, secrets-management, or credential-management telemetry. Relevant activity may include unusual API-token use, service-account activity from unfamiliar sources, repository access anomalies, cloud API calls, secret reads, new access keys, or use of credentials associated with the Ollama environment.
This stage is conditional and should not be assumed without defensible linkage to the exposed model server, the exposure window, suspicious model lifecycle activity, or affected credentials and identities.
Compromise Classification
Exposure should be classified as exposed.
Suspicious access to an exposed Ollama service without meaningful model lifecycle activity should be classified as targeted or attempted interaction.
Suspicious access followed by model-ingestion activity, unusual model artifacts, runtime instability, abnormal storage behavior, or unfamiliar outbound communication should be classified as probable exploitation or probable suspicious use.
Confirmed compromise or confirmed data exposure should require supporting artifact review, endpoint evidence, application evidence, network evidence, credential-use evidence, cloud or repository evidence, or validated incident-response findings.
S19 — Attack Chain Risk Amplification Summary
AI Infrastructure Sensitivity
Risk is amplified because the exposed asset is an AI model-serving environment rather than a generic development service. Ollama infrastructure may process prompts, source code, credentials, API tokens, customer data, tool outputs, internal documentation, and automation context.
Runtime Context Exposure
Risk increases when defenders cannot determine what sensitive data, prompts, secrets, or workflow context existed in memory or runtime context during the exposure window. Even limited uncertainty can force credential review, prompt and data assessment, repository review, and downstream access validation.
Model Lifecycle Abuse
Risk increases when suspicious access is followed by model ingestion, artifact handling, model import, blob activity, model-push behavior, or abnormal model storage changes. These behaviors connect exposure to activity that is directly relevant to the Ollama risk scenario.
Artifact and Runtime Instability
Risk increases when suspicious model activity is followed by new model files, unusual artifacts, manifest changes, temporary components, Ollama crashes, process restarts, container restarts, memory pressure, or model-loading errors. These signals can indicate abnormal model handling even when direct memory visibility is unavailable.
Outbound Movement
Risk increases when the Ollama host or container communicates with newly observed, rare, unexplained, unapproved, cloud-storage, file-sharing, anonymous-hosting, or unknown model-registry destinations. This behavior may indicate artifact transfer, exposed data movement, or attacker-directed communication.
Downstream Credential Exposure
Risk increases when exposed runtime context may include API tokens, repository tokens, cloud keys, service-account material, environment variables, or automation secrets. Downstream credential use can convert an AI infrastructure exposure into a broader cloud, repository, identity, or internal API investigation.
Detection Confidence Dependency
Risk increases when asset inventory, route-level logs, endpoint telemetry, file telemetry, container logs, DNS records, egress telemetry, identity logs, repository logs, cloud audit logs, or credential-management records are missing or inconsistently retained.
Operational Ambiguity
Risk increases when legitimate model experimentation, model pulls, model imports, developer testing, AI platform automation, backups, patching, monitoring, or vulnerability scanning overlap with suspicious activity. Weak ownership records and incomplete baselines can make it difficult to separate approved model-management behavior from attacker-driven interaction.
Response Complexity
Risk increases when affected Ollama infrastructure supports developer workflows, coding assistants, AI labs, CI systems, customer-support workflows, cloud services, repositories, internal APIs, or shared model infrastructure. Containment may require service isolation, workflow suspension, credential rotation, model artifact review, repository review, and executive governance.
S20 — Tactics, Techniques, and Procedures
Figure 3
Exposure Targeting and Model-Service Discovery
· Attackers target internet-facing or untrusted-accessible Ollama services, shared AI lab servers, cloud-hosted model-serving workloads, containerized deployments, and developer environments with broad network reach.
· Attackers may use scanning, probing, low-volume validation, repeated service interaction, or access from unfamiliar infrastructure to identify exposed model-serving systems.
· Scan-only or exposure-only activity should remain classified as exposure or attempted interaction unless correlated with suspicious model lifecycle activity, artifact changes, runtime instability, outbound communication, or downstream credential use.
Interaction with Exposed Model-Serving Functionality
· Attackers interact with public-facing or untrusted-reachable Ollama functionality on vulnerable, unpatched, or weakly controlled deployments.
· Suspicious behavior may include interaction with model-related API functionality, abnormal request timing, repeated model-management attempts, large request bodies, or activity inconsistent with approved administrative sources.
· Interaction becomes higher confidence when it occurs against internet-facing, unpatched, shared, sensitive, or poorly segmented Ollama infrastructure.
Model Lifecycle Abuse
· Attackers may attempt to use or abuse model-ingestion, model-import, artifact-handling, blob, or model-push functionality.
· Observable procedures may include new model artifacts, abnormal model storage changes, manifest updates, temporary model components, unusual model file sizes, or writes outside approved model paths.
· Legitimate model operations can resemble suspicious activity, so validation must account for approved model pulls, imports, refreshes, backups, developer testing, AI platform automation, and documented maintenance activity.
Runtime and Artifact Anomalies
· Suspicious model activity may be followed by Ollama crashes, process restarts, container restarts, memory pressure, service instability, or model-loading errors.
· Runtime instability near suspicious model-ingestion activity should increase severity because it may indicate abnormal model handling or exploit-adjacent behavior.
· Instability should be evaluated against approved upgrades, service restarts, container redeployments, resource exhaustion, lab testing, and known unstable development workflows.
Outbound Communication and Artifact Transfer
· Attackers may cause or use outbound communication from the Ollama host or container after suspicious model activity.
· Observable procedures may include connections to newly observed, rare, unexplained, unapproved, cloud-storage, file-sharing, anonymous-hosting, or unknown model-registry destinations.
· Outbound communication should be evaluated against approved model registries, update services, cloud destinations, automation systems, backups, monitoring, telemetry, and container registry activity.
Conditional Downstream Credential Use
· If exposed runtime context includes credentials, API tokens, repository tokens, cloud keys, service-account material, or automation secrets, attackers may attempt downstream access outside the Ollama environment.
· Observable procedures may include unusual repository access, cloud API calls from unfamiliar infrastructure, rare service-account use, secret reads, new access keys, or API-token use after the exposure window.
· Downstream credential activity should be treated as conditional unless it is temporally and logically linked to exposed Ollama infrastructure, suspicious model activity, or affected credentials.
Evasion and Blending Behavior
· Attackers may blend with legitimate AI infrastructure activity by using low-volume access, delayed follow-on behavior, cloud-hosted infrastructure, ordinary-looking model operations, or artifact names that resemble normal model workflows.
· Attackers may vary source infrastructure, destination infrastructure, model names, artifact names, request timing, transfer size, and delivery patterns.
· Detection should remain behavior-led because exploit strings, public proof-of-concept artifacts, model names, file names, source IPs, and destination indicators can change quickly.
S20A — Adversary Tradecraft Summary
The adversary tradecraft in this report is best understood as exposure of self-hosted AI model infrastructure with potential sensitive runtime context consequences. The governing behavior is not phishing delivery, ransomware execution, destructive malware, or a guaranteed persistence playbook. The governing behavior is suspicious interaction with exposed Ollama model-serving functionality that may be followed by model lifecycle activity, artifact anomalies, runtime instability, outbound communication, or downstream credential use.
Attackers can vary source infrastructure, request timing, model names, artifact names, transfer size, destination infrastructure, and visible interaction patterns. The tradecraft should therefore be assessed through the relationship between exposed service access and subsequent model-serving behavior, including model ingestion, artifact changes, runtime anomalies, outbound communication, and credential or identity activity.
Operationally, exposed Ollama infrastructure requires urgent validation and hunting. Exposure indicates risk. Suspicious service interaction may indicate attempted exploitation or abuse. Suspicious model lifecycle activity followed by artifact changes, runtime instability, unusual outbound communication, or downstream credential use supports probable exploitation or probable suspicious use. Confirmed compromise requires stronger host, application, artifact, identity, cloud, repository, credential-management, or incident-response evidence.
The highest-confidence tradecraft signals are suspicious access to exposed Ollama infrastructure followed by one or more of the following: model-ingestion activity, abnormal model artifact creation, unexpected model storage changes, runtime instability, process or container restart behavior, unfamiliar outbound communication, model-push behavior, large egress, or downstream use of credentials, API tokens, repository tokens, cloud keys, or service accounts.
Tradecraft should be assessed conservatively. No actor identity, malware family, destructive objective, persistence mechanism, lateral-movement path, payload signature, or complete post-exploitation playbook should be asserted unless validated by vendor guidance, government reporting, forensic review, or incident-response evidence.
S21 — Detection Strategy Overview
Detection Philosophy
Detection for this exposure should treat Ollama as an AI infrastructure service, not as a standard web application or isolated developer utility. The primary detection objective is to identify when a self-hosted model server is reachable from an untrusted network path and receives behavior consistent with suspicious model-ingestion activity.
The highest-value detection approach is behavior-led correlation. Detection should not depend on a single static exploit string, model name, file name, or public proof-of-concept artifact. The defensive focus should be on the sequence of exposed service access, model-ingestion activity, abnormal model artifact handling, and possible outbound movement following model ingestion.
This issue should be handled as a potential data-exposure event when vulnerable Ollama infrastructure was reachable from the internet, exposed to untrusted internal networks, or connected to workflows that process secrets, prompts, source code, customer data, or tool outputs.
Primary Detection Anchors
Ollama service exposure on internet-facing, untrusted, or broadly reachable network interfaces.
Unexpected access to Ollama API functionality associated with model ingestion, model import, model artifact handling, or model push behavior.
Inbound requests from unfamiliar external infrastructure, scanning sources, anonymous hosting providers, or previously unseen internal systems.
Model-ingestion activity or model artifact modification outside approved administrative activity.
New or unusual GGUF or model-related artifacts written to disk by the Ollama process.
Ollama activity followed by unusual outbound traffic, model push behavior, large egress, or communication with unfamiliar destinations.
Process instability, crash behavior, abnormal memory pressure, or runtime anomalies occurring near suspicious model-ingestion activity.
Confirmed presence of unpatched Ollama infrastructure.
Detection Prioritization Model
Priority 1 detection should focus on vulnerable or potentially vulnerable Ollama services exposed to untrusted access and receiving requests associated with model ingestion.
Priority 2 detection should focus on model-ingestion activity followed by outbound communication, model push behavior, unexpected artifact transfer, or large data movement.
Priority 3 detection should focus on host-level and container-level evidence, including new model files, unexpected GGUF handling, abnormal writes to model storage paths, process crashes, or Ollama runtime instability.
Priority 4 detection should focus on compensating evidence where direct application telemetry is limited. This includes firewall logs, reverse proxy logs, endpoint telemetry, container runtime logs, DNS telemetry, ingress logs, and egress monitoring.
Single-source alerts should be treated as triage leads unless they contain strong evidence of exposed vulnerable service access and suspicious model lifecycle behavior. Confirmed escalation should require correlation across network, application, endpoint, container, or egress telemetry.
Correlation Strategy
Detection should require a sequence-based view of the activity rather than isolated event matching.
Minimum suspicious correlation should include an Ollama service reachable from an untrusted path, followed by access to model-ingestion functionality, followed by at least one supporting signal such as unusual model artifact creation, outbound transfer, unfamiliar destination communication, service instability, or suspicious post-event credential activity.
High-confidence escalation should require a stronger combination of signals. An unpatched Ollama service, untrusted access to model-ingestion functionality, new or abnormal model artifact creation, outbound communication to an unfamiliar destination, and downstream evidence of possible secret or token use should be treated as a severe incident.
Exposure alone should not be classified as confirmed exploitation. Exposure establishes risk. Suspicious model-ingestion activity establishes probable attack activity. Correlated outbound movement, artifact transfer, memory-related instability, or downstream credential use strengthens the case for confirmed or likely compromise.
Telemetry Prioritization
Network telemetry should be used to identify exposed Ollama services, inbound access sources, unusual request patterns, and outbound movement following model activity.
Reverse proxy, API gateway, ingress, and load balancer telemetry should be prioritized where Ollama is deployed behind infrastructure that can provide route-level visibility.
Endpoint telemetry should be used to confirm Ollama process behavior, model artifact creation, file-system writes, crash behavior, runtime anomalies, and unusual process or network activity.
Container telemetry should be used where Ollama runs in Docker, Kubernetes, developer labs, AI experimentation environments, CI systems, or ephemeral compute environments.
Identity, secrets, and cloud audit telemetry should be reviewed when suspicious exposure is confirmed, because the material risk may occur after memory disclosure through use of exposed credentials, tokens, prompts, or environment variables.
Detection Design Constraints
Detection logic should not assume that all Ollama usage is malicious. Local developer use, approved model experimentation, internal automation, and administrative model management may be legitimate.
Detection logic should not rely on static exploit names, public proof-of-concept strings, specific file names, or fixed model labels. Those indicators are fragile and likely to change.
Detection logic should not classify every exposed Ollama service as compromised. Public or broad exposure is a critical risk condition, but confirmed compromise requires suspicious interaction or follow-on evidence.
Detection logic should account for partial telemetry. Many self-hosted AI deployments may lack complete application logs, centralized endpoint telemetry, or consistent reverse proxy coverage.
Detection logic should distinguish between approved model pulls, approved model imports, normal local model management, and suspicious model-ingestion or push behavior involving unfamiliar sources, destinations, timing, or hosts.
Baseline and Deployment Requirements
Organizations should maintain an inventory of approved Ollama hosts, listening interfaces, exposed ports, owning teams, deployment environments, and expected access paths.
Baseline should include approved administrative sources, approved model registries, approved model storage paths, expected model artifact sizes, normal model-ingestion frequency, and expected outbound destinations.
High-priority monitoring should cover internet-facing deployments, lab environments, developer workstations, AI experimentation servers, internal shared model infrastructure, and systems connected to coding assistants or agentic workflows.
Where native application telemetry is incomplete, organizations should deploy compensating visibility through reverse proxies, endpoint telemetry, container logs, firewall logs, DNS monitoring, and egress controls.
Variant Resilience Requirements
Detections should remain effective when an attacker changes model names, artifact names, request timing, source infrastructure, destination infrastructure, payload size, or delivery pattern.
Detection should focus on the durable behavior pattern: exposed AI model service, untrusted interaction, model-ingestion activity, abnormal artifact handling, and suspicious outbound or post-exposure activity.
Detection should support both internet-exposed and internally exposed scenarios. Internal exposure remains material when untrusted users, compromised endpoints, contractor systems, lab networks, or lateral movement paths can reach the model server.
Detection should also generalize beyond this single issue. The broader defensive pattern is exposed AI model ingestion combined with sensitive process-memory risk.
Operational Detection Model
SOC triage should first determine whether the Ollama instance was unpatched, exposed to untrusted access, or reachable from a broad internal network segment.
The second triage step should determine whether model ingestion, model import, blob upload, model export, or model push behavior occurred during the exposure window.
The third triage step should review host, container, and storage telemetry for new model artifacts, abnormal file writes, runtime instability, or suspicious process behavior.
The fourth triage step should review outbound network traffic, DNS activity, cloud audit logs, identity logs, and secrets-management telemetry for signs that exposed memory contents may have enabled follow-on access.
Confirmed or strongly suspected exposure should trigger service containment, upgrade validation, exposure removal, secret rotation, prompt and data review, model artifact review, and downstream credential-abuse hunting.
S22 — Primary Detection Signals
Primary Detection Signals
Primary detection should focus on behavior indicating that an exposed Ollama service is receiving suspicious model-ingestion activity from an untrusted source.
The strongest primary signal is untrusted access to Ollama API functionality associated with model ingestion, model artifact handling, model import, or model push behavior. This signal becomes materially stronger when the source is external, newly observed, associated with scanning activity, or inconsistent with normal administrative access patterns.
Model-ingestion activity against an Ollama instance that is internet-facing, broadly reachable, or exposed to untrusted internal networks should be treated as a high-priority investigation. Exposure alone is a risk condition, but exposure combined with suspicious model-ingestion behavior creates a stronger detection signal.
New or unusual model artifacts written by the Ollama process are also primary signals. This includes model files, GGUF-related artifacts, temporary model components, or storage-path changes that occur outside normal administrative activity.
Ollama activity followed by outbound model push behavior, large egress, or communication with unfamiliar destinations should be treated as a primary escalation signal. This pattern is especially important when it follows model-ingestion activity from an untrusted source.
Supporting Detection Signals
Supporting signals should be used to increase confidence, establish timeline, and distinguish suspicious activity from legitimate model management.
Relevant supporting signals include newly observed source IP addresses, unfamiliar internal hosts reaching Ollama, unexpected user agents, unusual request timing, request patterns outside approved maintenance windows, or repeated interaction with model-related API functionality.
Additional supporting signals include changes to model storage directories, creation of unusually sized model artifacts, modification of model metadata, temporary file creation near model-ingestion events, or model lifecycle activity that does not match approved automation.
Environment context should also be used as supporting evidence. Suspicious activity is more severe when the Ollama instance is connected to coding assistants, agentic workflows, developer repositories, customer data, credentials, tool outputs, or other sensitive runtime context.
Patch state should be used as a confidence modifier. An unpatched Ollama instance exposed to suspicious model-ingestion activity should receive higher severity than a fully patched instance with the same network pattern.
Exploit Attempt and Instability Signals
Exploit-attempt detection should focus on observable behavior rather than payload construction details.
Suspicious instability signals include Ollama crashes, abnormal process restarts, memory pressure, unexpected service failures, model-loading errors, malformed model-handling events, or runtime anomalies occurring close to suspicious model-ingestion activity.
Repeated model-ingestion failures from the same source should be treated as suspicious when they occur against an exposed Ollama service. This may indicate probing, malformed model handling, or unsuccessful attempts to trigger abnormal model-loader behavior.
Service instability should not be treated as confirmed exploitation by itself. It becomes more meaningful when correlated with untrusted API access, new model artifacts, abnormal model handling, or outbound communication following model ingestion.
Outbound Communication Signals
Outbound communication after suspicious model-ingestion activity should receive high investigative priority.
Relevant outbound signals include connections from the Ollama host or container to unfamiliar external destinations, unexpected model registries, anonymous infrastructure, file-sharing services, newly observed domains, cloud object storage, or destinations not present in the approved baseline.
Large outbound transfers following model ingestion should be treated as a high-risk signal, especially when paired with new model artifacts or model push behavior.
DNS queries to unfamiliar domains after suspicious Ollama activity should be reviewed as supporting evidence. This is particularly important when direct application logs are incomplete or unavailable.
Outbound traffic should be evaluated against the approved model-source and model-registry baseline. Communication with approved internal registries or known update sources should be treated differently from unfamiliar external destinations.
Persistence and Post-Exploitation Signals (Conditional)
Persistence signals are conditional for this report. The primary risk is memory disclosure and data exposure, not guaranteed persistence.
Post-exploitation review should focus on downstream use of exposed information. Relevant signals include suspicious authentication attempts, unexpected API token use, cloud access from unfamiliar sources, newly created access keys, unusual repository access, abnormal credential-management activity, or unexpected use of credentials that may have existed in the Ollama runtime environment.
Persistence-related endpoint signals should be investigated when they occur after suspicious Ollama activity. These may include new services, scheduled tasks, unauthorized containers, unexpected startup entries, modified shell configuration, or new remote-access tooling on the Ollama host.
These signals should not be assumed to be part of every case. They should be treated as escalation indicators when they appear after confirmed or strongly suspected exposure.
Lateral Movement and Expansion Signals (Conditional)
Lateral movement signals are conditional and should be evaluated when the Ollama host has access to internal systems, repositories, credentials, model pipelines, cloud services, or agentic tooling.
Relevant signals include unusual internal connections from the Ollama host, access to systems outside its normal role, authentication attempts to developer platforms, movement toward credential-management systems, access to internal APIs, or interaction with shared model infrastructure.
Expansion risk is higher when Ollama runs on a developer workstation, shared AI lab server, CI host, cloud VM, or container platform with broad network reach.
Lateral movement should not be inferred from Ollama exposure alone. It should require follow-on evidence such as credential use, internal scanning, abnormal authentication, unexpected service access, or new connections from the Ollama environment to sensitive internal assets.
Signal Usage Constraints
Detection should not alert solely on the presence of Ollama.
Detection should not alert solely on local model usage.
Detection should not classify routine model pulls, approved model imports, or authorized model management as malicious without supporting context.
Detection should not rely on exploit-specific names, payload strings, artifact names, or public proof-of-concept indicators as the primary basis for detection.
Detection should not treat exposure alone as confirmed compromise. Exposure should trigger risk review and prioritization. Suspicious model-ingestion behavior should trigger investigation. Correlated artifact creation, outbound movement, instability, or downstream credential activity should trigger escalation.
Detection should not overstate persistence or lateral movement. Those behaviors are conditional and should only be included when supported by telemetry.
Signal confidence should be based on correlation across exposure, model-ingestion behavior, artifact activity, runtime instability, outbound movement, and downstream credential or identity activity.
S23 — Telemetry Requirements
Endpoint and Process Execution Telemetry
Endpoint telemetry should capture Ollama process execution, service start and stop events, process ownership, runtime path, command-line context, child-process activity, and host-level network activity.
Required endpoint visibility should include the Ollama binary path, service account or user context, execution environment, process start time, process restart frequency, and network connections initiated by the Ollama process.
Telemetry should also capture whether Ollama is running as a local user process, system service, containerized workload, developer workstation process, lab server process, or cloud-hosted service. This context is required to distinguish normal local experimentation from exposed infrastructure behavior.
Process execution telemetry should support correlation between Ollama runtime activity, model-ingestion events, file-system changes, service instability, and outbound communication.
Memory and Execution Telemetry
Memory and execution telemetry should be treated as supporting visibility, not as a requirement for direct memory inspection.
Useful signals include abnormal memory pressure, repeated process restarts, crash-adjacent runtime anomalies, unexpected service failures, and execution behavior inconsistent with normal model loading.
The practical detection requirement is not to inspect process memory directly. The practical requirement is to identify abnormal runtime behavior occurring near suspicious model-ingestion activity.
Organizations should avoid relying on memory-only indicators, because many environments will not have consistent memory telemetry across developer systems, containers, lab servers, and cloud-hosted workloads.
Crash and Fault Telemetry
Crash and fault telemetry should capture Ollama process crashes, abnormal exits, restart loops, segmentation fault indicators, service-manager restart events, container restarts, kernel-level fault messages, and application-level model-loading errors.
Crash events should be time-correlated with model-ingestion activity, newly written model artifacts, inbound access from untrusted sources, and outbound communication following the crash or restart window.
A crash or restart by itself should not be treated as confirmed exploitation. It becomes more significant when it occurs near suspicious model-handling activity or when followed by artifact transfer, unusual egress, or downstream credential activity.
Crash and fault telemetry is especially important in environments where application-layer logs are incomplete or where the Ollama service is not deployed behind a reverse proxy.
File and Persistence Telemetry
File telemetry should capture model artifact creation, modification, deletion, and movement within Ollama model storage paths and related temporary directories.
Required visibility should include new GGUF-related artifacts, model manifests, blob storage changes, unexpected model metadata changes, unusually sized model files, temporary files associated with model ingestion, and model artifacts created outside approved administrative windows.
File telemetry should also capture unexpected writes by the Ollama process to locations outside approved model storage paths.
Persistence telemetry should be collected as conditional evidence. New services, scheduled tasks, unauthorized containers, startup entries, modified shell configuration, or remote-access tooling should be investigated when they appear after suspicious Ollama activity.
Persistence should not be assumed as part of the primary exposure pattern. It should be treated as an escalation signal when supported by timeline and host evidence.
Network and Outbound Communication Telemetry
Network telemetry should identify exposed Ollama services, listening interfaces, inbound source addresses, destination ports, request timing, and traffic volume.
Required visibility should include inbound access from external sources, unfamiliar internal systems, scanning infrastructure, anonymous hosting providers, and systems outside approved administrative paths.
Outbound telemetry should capture connections from the Ollama host or container to unfamiliar destinations, unexpected model registries, cloud object storage, file-sharing services, newly observed domains, or infrastructure outside the approved model-source baseline.
Egress telemetry should support volume analysis, destination reputation review, timing correlation, and comparison against expected model-management behavior.
Network telemetry should also identify large outbound transfers, repeated outbound attempts, unusual DNS lookups, and new external destinations contacted after model-ingestion activity.
Web and Application Telemetry (Conditional Availability)
Web and application telemetry should be collected wherever Ollama is deployed behind a reverse proxy, ingress controller, API gateway, load balancer, service mesh, or other fronting infrastructure.
Useful application-layer visibility includes request path, request method, source address, forwarded headers, response status, request timing, response size, user agent, authentication context where present, and administrative source context.
Route-level visibility is especially valuable for identifying access to model-ingestion, model import, artifact handling, and model push functionality.
Where direct Ollama application logs are limited, reverse proxy and ingress telemetry should be treated as the preferred source for route-level detection.
Where authentication is present, access telemetry should identify the user, service account, automation identity, or administrative source associated with model-ingestion activity.
Telemetry Availability Requirements
Minimum viable telemetry should include network exposure data, inbound access logs, host or container process telemetry, file-system monitoring for model artifacts, and outbound network visibility.
Preferred telemetry should include route-level request logs, endpoint process telemetry, model storage monitoring, container runtime telemetry, DNS telemetry, egress volume monitoring, identity telemetry, and credential-management activity logs.
High-confidence detection requires the ability to correlate at least two telemetry classes. The most useful combinations are network plus file telemetry, application plus endpoint telemetry, endpoint plus egress telemetry, and exposure data plus identity or credential activity.
Organizations should maintain a current inventory of Ollama hosts, deployment locations, exposed interfaces, owning teams, approved administrative sources, approved model sources, and expected outbound destinations.
Telemetry should be retained long enough to support investigation across the exposure window, patch window, credential-rotation window, and downstream credential-abuse review period.
Telemetry Limitations and Gaps
Many self-hosted AI deployments may lack complete centralized logging. Developer workstations, lab servers, proof-of-concept systems, and temporary cloud instances may have limited visibility compared with production infrastructure.
Native application logs may not provide enough detail to identify every suspicious model-ingestion event. In those environments, reverse proxy logs, endpoint telemetry, container logs, firewall records, DNS logs, and egress monitoring become critical compensating sources.
Encrypted traffic, local-only deployments, container abstraction, short-lived workloads, and unmanaged developer systems may reduce detection fidelity.
Absence of observed outbound movement does not prove absence of exposure. Memory disclosure risk may involve sensitive prompts, credentials, or runtime context that require downstream review beyond network telemetry.
Telemetry gaps should be documented during triage. When direct evidence is incomplete, defenders should prioritize exposure validation, patch verification, model artifact review, credential rotation, and targeted hunting for downstream credential use.
S24 — Detection Opportunities and Gaps
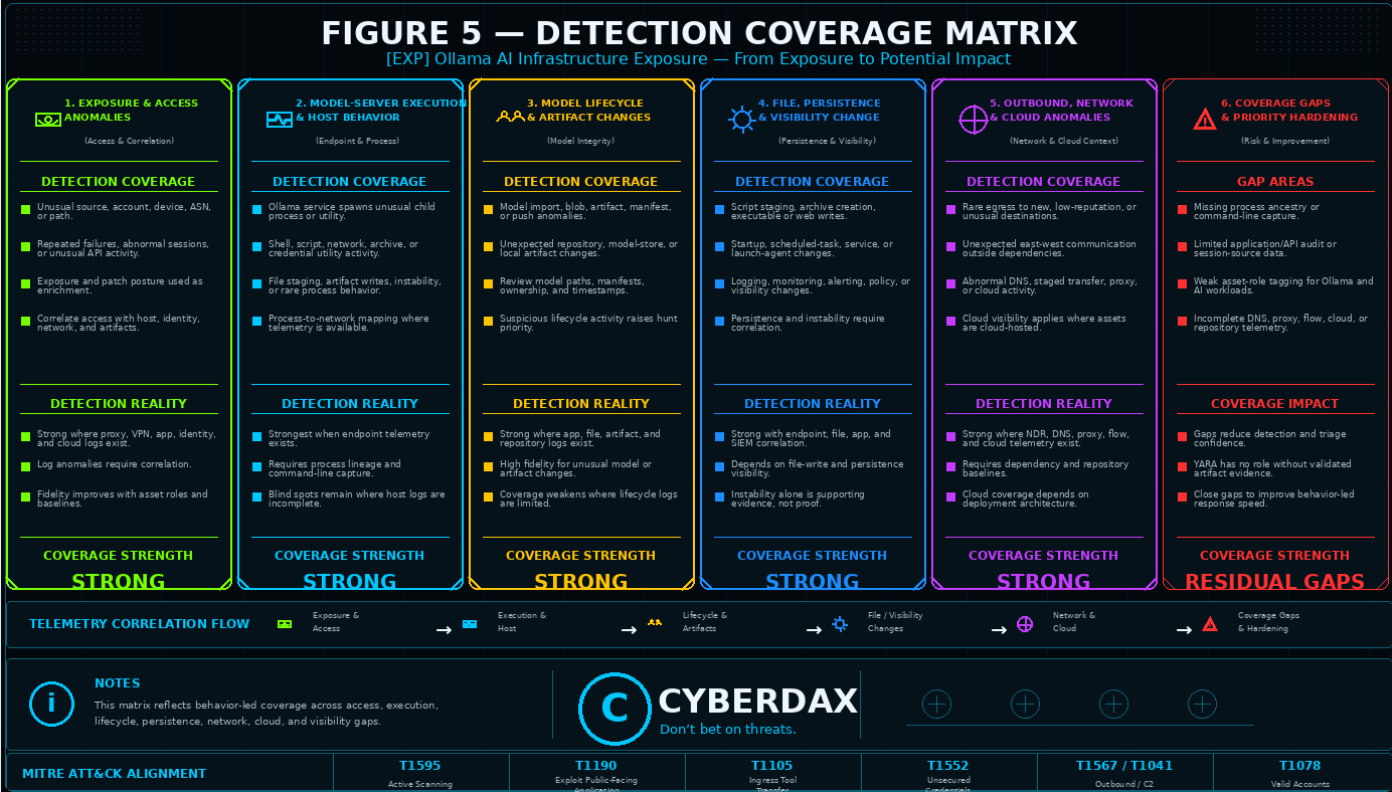
Figure 4
Detection Opportunities
The strongest detection opportunity is identifying exposed Ollama infrastructure that receives suspicious model-ingestion activity from an untrusted source. This provides a practical detection anchor because it combines exposure, service interaction, and behavior that is relevant to the risk scenario.
A second strong opportunity is correlation between model-ingestion activity and new or unusual model artifacts. Newly written GGUF-related files, model manifests, blob storage changes, temporary model components, or unexpected model storage activity can help distinguish routine service exposure from activity requiring investigation.
A third opportunity is identifying outbound movement after suspicious model-ingestion activity. Connections to unfamiliar destinations, unexpected model registries, cloud object storage, file-sharing services, newly observed domains, or large egress events can strengthen confidence that the activity may involve data exposure or artifact transfer.
Runtime instability creates another useful detection opportunity. Ollama process crashes, abnormal restarts, model-loading errors, service instability, or memory-pressure events occurring near suspicious model-ingestion activity should be treated as meaningful supporting evidence.
Credential and identity activity after suspicious exposure provides an important post-event hunting opportunity. Unusual API token use, abnormal cloud access, unfamiliar repository access, new access keys, or unexpected credential-management activity may indicate downstream use of exposed runtime context.
High-Value Correlation Opportunities
High-value detection should correlate untrusted access, model-ingestion activity, model artifact changes, and outbound communication.
A strong suspicious pattern is an exposed Ollama service receiving model-ingestion activity from a newly observed source, followed by creation of unusual model artifacts and outbound communication to an unfamiliar destination.
A strong escalation pattern is an unpatched Ollama service receiving suspicious model-ingestion activity, followed by runtime instability, artifact movement, and downstream credential or identity activity.
A strong internal-risk pattern is a broadly reachable Ollama service accessed by an unfamiliar internal host, followed by model artifact changes and connections from the Ollama environment to systems outside its normal role.
A strong compensating-control pattern is route-level proxy evidence of model-ingestion activity paired with endpoint evidence of model artifact creation, even when native application logs are incomplete.
Detection Gaps
The most significant detection gap is incomplete visibility into self-hosted AI infrastructure. Ollama may run on developer workstations, lab systems, temporary cloud instances, unmanaged servers, or containers that are not fully covered by centralized monitoring.
A second major gap is limited route-level application logging. Without reverse proxy, ingress, gateway, or application telemetry, defenders may only see network connections and host behavior, which can reduce confidence when assessing model-ingestion activity.
A third gap is lack of model artifact baselining. Without a known-good inventory of approved model storage paths, expected artifact sizes, approved model sources, and normal model-management frequency, defenders may struggle to distinguish legitimate experimentation from suspicious activity.
A fourth gap is incomplete egress visibility. If outbound traffic from AI infrastructure is not monitored, defenders may miss model push behavior, artifact transfer, communication with unfamiliar destinations, or large data movement after suspicious model ingestion.
A fifth gap is weak credential and identity correlation. The most damaging outcome may occur after exposed prompts, tokens, environment variables, or runtime context are used elsewhere. Without identity, cloud, repository, and credential-management telemetry, downstream impact may be difficult to confirm.
Environment-Specific Gaps
Developer workstation deployments may lack centralized logging, route-level visibility, consistent endpoint telemetry, or managed egress monitoring.
AI lab environments may have broad internal access, experimental model workflows, permissive network rules, and incomplete ownership records.
Containerized deployments may obscure host-level file paths, process lineage, storage mounts, and short-lived runtime activity unless container telemetry is retained.
Cloud-hosted deployments may expose services through misconfigured security groups, permissive firewall rules, temporary public IPs, or untracked test environments.
Internal shared model servers may be reachable by many users or systems, making it harder to separate approved use from suspicious access without source baselines and administrative ownership records.
False Positive Drivers
Legitimate model experimentation can resemble suspicious model-ingestion activity when developers create, import, modify, or test models outside standard maintenance windows.
Approved automation may create model artifacts, pull model data, or interact with model-management functionality in ways that appear unusual without ownership context.
Large model transfers may be expected during normal deployment, testing, model refresh, or migration activity.
Service crashes may occur during legitimate model loading, resource exhaustion, incompatible model handling, or unstable lab testing.
Internal access from unfamiliar hosts may be legitimate in environments where model servers are shared across teams, labs, or development workflows.
False Negative Drivers
Detection may miss activity when Ollama is directly exposed without a reverse proxy or route-level logging.
Detection may miss activity when model artifacts are written to locations not covered by file monitoring.
Detection may miss activity when outbound network activity is allowed broadly and not tied back to the Ollama host, process, or container.
Detection may miss activity when the service runs briefly in a temporary cloud instance, developer environment, or short-lived container.
Detection may miss downstream impact when exposed credentials are used from different infrastructure, at a later time, or through legitimate-looking access paths.
Detection may miss suspicious model-ingestion behavior when payload details are encrypted, application logs are unavailable, or endpoint telemetry is incomplete.
Compensating Detection Approaches
Where application logs are unavailable, defenders should prioritize reverse proxy logs, ingress logs, firewall records, endpoint process telemetry, container runtime telemetry, DNS activity, and egress monitoring.
Where endpoint telemetry is limited, defenders should prioritize network exposure validation, inbound source review, outbound destination review, and model storage monitoring.
Where file telemetry is limited, defenders should monitor model storage directories, container volumes, artifact repositories, and deployment automation records.
Where identity telemetry is limited, defenders should prioritize credential rotation, review of cloud audit logs, repository access logs, API token usage, and administrative account activity.
Where visibility is incomplete, defenders should treat confirmed unpatched exposure plus suspicious model-ingestion activity as sufficient to trigger containment, upgrade validation, artifact review, and downstream credential-abuse hunting.
Detection Improvement Priorities
Near-term improvement should focus on inventory, exposure validation, route-level logging, model artifact monitoring, and outbound destination baselining.
Security teams should establish approved administrative sources, approved model sources, expected model storage paths, and expected outbound destinations for Ollama deployments.
Shared or externally reachable Ollama services should have authenticated access controls, logging coverage, and monitored egress paths.
Detection improvement should prioritize telemetry that supports correlation across exposure, model ingestion, artifact activity, outbound movement, and downstream credential or identity activity.
Residual Detection Risk
Residual detection risk remains when Ollama runs in unmanaged, temporary, local, or experimental environments without reliable telemetry.
A clean detection outcome does not prove that no exposure occurred. It only means available telemetry did not identify suspicious activity.
Where telemetry is incomplete and exposure is confirmed, organizations should prioritize containment, patch validation, credential rotation, and downstream review.
S25 Ultra-Tuned Detection Engineering Rules
NDR / Network Behavioral Analytics
Detection Viability Assessment
NDR / Network Behavioral Analytics has three rules for this EXP report.
· NDR / Network Behavioral Analytics is viable for detecting exposed Ollama infrastructure, untrusted inbound access, source novelty, destination novelty, large outbound movement, unusual east-west access, and suspicious network sequencing around model-ingestion activity.
· NDR / Network Behavioral Analytics is strongest where service exposure, listening interfaces, inbound source identity, destination reputation, traffic timing, traffic volume, DNS activity, protocol metadata, and host or workload role context are available.
· NDR / Network Behavioral Analytics is not a standalone source for confirming memory disclosure, model artifact creation, process crashes, or local file activity. Those outcomes require endpoint, application, container, or SIEM correlation.
· NDR / Network Behavioral Analytics is most valuable for identifying suspicious access to exposed AI model infrastructure and prioritizing cases where model-ingestion activity is followed by unusual egress, unfamiliar destinations, or abnormal internal access patterns.
Rule 1
Suspicious Ollama Model-Ingestion Activity from Untrusted Source
Rule Format
NDR / Network Behavioral Analytics detection pattern suitable for behavioral alerting after asset tagging, service identification, exposure validation, approved-source baselining, destination baselining, and environment-specific tuning.
Detection Purpose
· Detect suspicious inbound access to Ollama model-ingestion functionality from external, untrusted, newly observed, or unapproved sources.
· Identify suspicious interaction with self-hosted AI model infrastructure without relying on exploit strings, public proof-of-concept artifacts, static payload names, or attacker-controlled infrastructure indicators.
· Prioritize exposed Ollama services that receive model-ingestion activity from sources outside approved administrative paths.
· This rule does not confirm memory disclosure or successful exploitation without supporting endpoint, application, artifact, instability, outbound, identity, or credential activity.
Detection Logic
· Identify network traffic to assets tagged or classified as Ollama servers, self-hosted AI model servers, AI lab servers, developer AI infrastructure, or shared model-serving infrastructure.
· Identify inbound sessions from external, untrusted, newly observed, rare, or unapproved sources.
· Prioritize sessions associated with Ollama API access, model-management behavior, model-ingestion routes where visible, large request bodies, repeated model-related requests, or abnormal interaction with the Ollama service port.
· Increase confidence when the destination is internet-facing, broadly reachable, unpatched, newly exposed, or inconsistent with the approved exposure baseline.
· Increase confidence when inbound access occurs outside approved administrative windows or from infrastructure associated with scanning, anonymous hosting, commodity cloud providers, or previously unseen internal hosts.
· Do not classify the activity as confirmed compromise without corroborating application, endpoint, file, outbound, identity, or credential evidence.
Required Telemetry
· Network flow telemetry.
· Service identification telemetry.
· Destination host identity.
· Destination host role or asset tag.
· Listening port and protocol metadata.
· Inbound source address.
· Source reputation or source classification where available.
· First-seen and last-seen source context.
· Traffic timing.
· Traffic volume.
· Request method and path metadata where available.
· DNS telemetry where available.
· Exposure context.
· Approved administrative source baseline.
· Patch or asset vulnerability context where available.
Engineering Implementation Instructions
· Validate that Ollama servers, AI lab servers, developer AI infrastructure, shared model-serving hosts, and containerized model-serving workloads are tagged in the NDR or asset inventory.
· Validate normal listening ports, approved access paths, administrative sources, and expected internal consumers for Ollama infrastructure.
· Tune the rule to prioritize untrusted, external, newly observed, rare, or unapproved sources rather than alerting on all Ollama access.
· Use route-level metadata only when the NDR, proxy, ingress, gateway, or decrypted inspection path provides it. Do not require route visibility in environments where only flow-level telemetry is available.
· Add suppressions for approved administrative systems, vulnerability scanners, model-management automation, internal testing networks, approved AI platform services, and known monitoring systems.
· Treat internet exposure, unpatched status, source novelty, request volume, and repeated interaction with model-management behavior as prioritization context.
· Use endpoint, application, file, container, SIEM, identity, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
8.5 / 10
· The rule is behaviorally anchored to untrusted access against exposed AI model infrastructure rather than brittle exploit artifacts.
· The rule remains useful if attacker infrastructure rotates, public proof-of-concept behavior changes, model names change, request paths are partially hidden, or request timing varies.
· The score is supported by the durability of exposed model-serving infrastructure receiving model-ingestion activity from untrusted sources.
· The score is constrained by environments where route-level visibility is unavailable or where approved experimentation creates frequent access from changing internal sources.
TCR Assessment
Operational TCR
7.5 / 10
Full-Telemetry TCR
9.0 / 10
· Operational confidence depends on service identification, host-role tagging, exposure context, source classification, approved-source baselining, and traffic metadata quality.
· Operational confidence is reduced where Ollama runs on unmanaged developer systems, temporary cloud hosts, short-lived containers, or networks without route-level visibility.
· Full-telemetry confidence improves when NDR data is enriched with proxy logs, endpoint telemetry, asset inventory, patch state, application logs, file telemetry, and identity activity.
· Even under full telemetry conditions, this rule requires correlation before confirmed compromise classification.
Limitations
· This rule detects suspicious access to exposed Ollama infrastructure, not memory disclosure itself.
· NDR may not see local model artifact creation, process crashes, model-loader errors, or credential use without enrichment.
· Legitimate model testing, approved automation, internal scanning, vulnerability management, and shared AI lab usage may overlap with this behavior.
· Route-level model-ingestion visibility depends on whether the environment provides HTTP metadata, proxy telemetry, ingress logs, gateway logs, or decrypted inspection.
· Confirmation requires correlation with suspicious model artifact activity, runtime instability, unusual outbound movement, credential activity, or other supporting evidence.
Detection Query Pattern
NDR / Network Behavioral Analytics query pattern requiring platform syntax, asset taxonomy, source-baseline, exposure-baseline, and field validation before production deployment.
DEST_ASSET_ROLE IN (
"Ollama Server",
"Self-Hosted AI Model Server",
"AI Lab Server",
"Developer AI Infrastructure",
"Shared Model Infrastructure"
)
AND DEST_SERVICE IN (
"ollama",
"ai-model-server",
"model-serving-api"
)
AND INBOUND_SOURCE_CLASS IN (
"external",
"untrusted",
"newly_observed",
"rare",
"unapproved_internal"
)
AND (
DEST_PORT IN (
11434,
APPROVED_OLLAMA_PORTS
)
OR SERVICE_FINGERPRINT = "ollama"
)
AND (
HTTP_PATH CONTAINS ANY (
"/api/create",
"/api/blobs",
"/api/push"
)
OR REQUEST_BODY_SIZE > ENV_BASELINE_MODEL_API_REQUEST_SIZE
OR SESSION_REQUEST_COUNT > ENV_BASELINE_MODEL_API_REQUEST_COUNT
OR SERVICE_INTERACTION_PATTERN = "model_management"
)
AND NOT SRC_IP IN APPROVED_OLLAMA_ADMIN_SOURCES
AND NOT SRC_ASSET_ROLE IN (
"Approved AI Platform Service",
"Approved Model Automation",
"Approved Vulnerability Scanner",
"Approved Monitoring System"
)
Rule 2
Rule
Ollama Model-Ingestion Activity Followed by Unusual Outbound Communication
Rule Format
NDR / Network Behavioral Analytics detection pattern suitable for sequence-based behavioral alerting after service tagging, egress baselining, approved-destination validation, timing-window validation, and environment-specific tuning.
Detection Purpose
· Detect suspicious outbound communication from an Ollama host or container after model-ingestion activity.
· Identify cases where exposed AI model infrastructure receives suspicious model-related interaction and then communicates with unfamiliar external destinations, unexpected model registries, cloud object storage, file-sharing services, or newly observed domains.
· Prioritize possible data exposure, model artifact transfer, or attacker-directed outbound movement without claiming direct memory-disclosure visibility from network telemetry alone.
· This rule does not confirm what data was transmitted without supporting packet, proxy, endpoint, application, artifact, or destination evidence.
Detection Logic
· Identify Ollama-associated hosts or containers that receive model-ingestion or model-management network activity.
· Within a defined investigation window, identify outbound connections from the same host, workload, or container to unfamiliar, rare, newly observed, unapproved, or high-risk destinations.
· Prioritize outbound communication involving unusual volume, uncommon ports, new domains, model registry-like destinations, cloud object storage, file-sharing services, or infrastructure outside the approved model-source baseline.
· Increase confidence when outbound communication follows access from an untrusted source, occurs near new model activity, or exceeds normal egress volume for the host.
· Increase confidence when the Ollama host is internet-facing, unpatched, broadly reachable, or outside approved deployment inventory.
· Do not classify the activity as confirmed data theft without corroborating endpoint, application, file, artifact, proxy, or identity evidence.
Required Telemetry
· Network flow telemetry.
· Inbound and outbound session telemetry.
· Host or workload identity.
· Container identity where available.
· Ollama service classification.
· Source and destination addresses.
· Destination reputation.
· Destination domain.
· DNS resolution telemetry.
· Traffic timing.
· Traffic volume.
· Egress baseline.
· Approved model registry baseline.
· Approved outbound destination baseline.
· Exposure context.
· Patch or vulnerability context where available.
Engineering Implementation Instructions
· Tag Ollama hosts, AI model servers, container workloads, and shared model infrastructure before deployment.
· Establish approved model registries, update sources, cloud destinations, automation services, and administrative egress paths.
· Tune the sequence window to the organization’s normal model-management behavior and investigation requirements.
· Prioritize outbound destinations that are newly observed, rare for the environment, rare for the host, external, anonymous, cloud-hosted, or outside the approved model-source baseline.
· Add suppressions for approved model pulls, approved model pushes, patching, telemetry agents, backups, monitoring systems, container registries, and authorized AI platform workflows.
· Use this rule as an escalation detector when paired with untrusted inbound access, unpatched status, runtime instability, unusual artifact creation, or credential activity.
· Do not infer memory disclosure from egress alone.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to suspicious sequencing between model-ingestion activity and unusual outbound communication.
· The rule remains useful if attacker infrastructure changes, model names vary, payload contents change, or the model-ingestion request is not visible in full detail.
· The score is supported by the durability of exposed AI model infrastructure communicating with unfamiliar destinations after suspicious model activity.
· The score is constrained by legitimate large model transfers, approved model registry communication, developer experimentation, and incomplete egress baselining.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on accurate host identity, service classification, egress baselining, destination reputation, DNS visibility, and timing correlation.
· Operational confidence is reduced where egress is broadly allowed, outbound destinations are poorly baselined, or model-transfer workflows are frequent and decentralized.
· Full-telemetry confidence improves when NDR telemetry is enriched with proxy logs, application logs, endpoint file activity, model artifact telemetry, container metadata, identity logs, and asset patch state.
· Even under full telemetry conditions, this rule supports escalation and investigation rather than standalone confirmation of data exposure.
Limitations
· This rule detects suspicious outbound behavior following model activity, not the contents of exposed memory.
· Legitimate model downloads, model pushes, development workflows, registry synchronization, cloud storage access, backups, and testing may overlap with this pattern.
· The rule requires egress baselining and destination classification to reduce false positives.
· NDR may not determine whether outbound traffic contains model artifacts, prompts, credentials, or other sensitive content without additional telemetry.
· Confirmation requires correlation with application logs, endpoint file activity, model artifact review, proxy records, identity activity, or credential-management evidence.
Detection Query Pattern
NDR / Network Behavioral Analytics sequence pattern requiring platform syntax, service identity, timing-window, destination-baseline, and egress-field validation before production deployment.
SEQUENCE WITHIN ENV_MODEL_ACTIVITY_WINDOW
STEP 1:
DEST_ASSET_ROLE IN (
"Ollama Server",
"Self-Hosted AI Model Server",
"AI Lab Server",
"Developer AI Infrastructure",
"Shared Model Infrastructure"
)
AND DEST_SERVICE IN (
"ollama",
"ai-model-server",
"model-serving-api"
)
AND (
HTTP_PATH CONTAINS ANY (
"/api/create",
"/api/blobs",
"/api/push"
)
OR REQUEST_BODY_SIZE > ENV_BASELINE_MODEL_API_REQUEST_SIZE
OR SERVICE_INTERACTION_PATTERN = "model_management"
)
FOLLOWED BY STEP 2:
SRC_HOST = STEP_1.DEST_HOST
AND OUTBOUND_DEST_CLASS IN (
"newly_observed",
"rare",
"unapproved",
"external",
"anonymous_hosting",
"cloud_storage",
"file_sharing",
"unknown_model_registry"
)
AND (
OUTBOUND_BYTES > ENV_BASELINE_OLLAMA_EGRESS_BYTES
OR DEST_DOMAIN NOT IN APPROVED_MODEL_REGISTRIES
OR DEST_IP NOT IN APPROVED_OLLAMA_EGRESS_DESTINATIONS
OR DEST_REPUTATION IN (
"unknown",
"suspicious",
"low_prevalence"
)
)
AND NOT DEST_DOMAIN IN APPROVED_MODEL_REGISTRIES
AND NOT DEST_IP IN APPROVED_OLLAMA_EGRESS_DESTINATIONS
Rule 3
Rule
Unfamiliar Internal Host Accessing Shared Ollama Infrastructure Followed by Abnormal Network Behavior
Rule Format
NDR / Network Behavioral Analytics detection pattern suitable for internal exposure and east-west behavioral alerting after internal-source baselining, asset-role tagging, network-zone mapping, and shared-service tuning.
Detection Purpose
· Detect suspicious internal access to shared or broadly reachable Ollama infrastructure from unfamiliar internal hosts.
· Identify cases where an internal host accesses model-serving infrastructure outside normal administrative or consumer patterns and is followed by abnormal outbound or east-west network behavior.
· Prioritize internal exposure scenarios where compromised endpoints, unmanaged lab systems, contractor hosts, or lateral movement paths may reach self-hosted AI infrastructure.
· This rule does not infer lateral movement or compromise from internal access alone. It requires follow-on abnormal network behavior for escalation.
Detection Logic
· Identify internal access to Ollama infrastructure from hosts that are newly observed, rare, unmanaged, outside approved network zones, or not part of the approved administrative or AI platform source baseline.
· Prioritize access to shared Ollama infrastructure, lab model servers, developer AI infrastructure, or broadly reachable internal model-serving systems.
· Within a defined investigation window, identify abnormal network behavior involving either the source host or Ollama host.
· Relevant follow-on behavior includes unusual outbound communication, connections to sensitive internal services outside normal role, repeated access attempts, unusual DNS activity, large data transfer, or communication with destinations not observed in the normal baseline.
· Increase confidence when the Ollama service is unpatched, broadly reachable, connected to sensitive workflows, or located in an environment with weak access segmentation.
· Do not classify internal access as malicious without follow-on abnormal network behavior or supporting endpoint, identity, application, or file evidence.
Required Telemetry
· Internal network flow telemetry.
· East-west traffic visibility.
· Host identity.
· Source asset role.
· Destination asset role.
· Network zone mapping.
· Ollama service classification.
· First-seen source context.
· Approved internal consumer baseline.
· Approved administrative source baseline.
· Traffic timing.
· Traffic volume.
· DNS telemetry where available.
· Outbound destination telemetry.
· Sensitive service access context where available.
· Patch or exposure context where available.
Engineering Implementation Instructions
· Tag internal Ollama systems, AI lab servers, developer model infrastructure, shared model-serving hosts, and approved AI platform consumers.
· Define approved internal source zones, approved administrative hosts, approved automation services, and expected consumer systems.
· Tune the rule to focus on unfamiliar internal hosts, rare source-to-service relationships, unmanaged systems, contractor networks, lab networks, and broad internal access paths.
· Require follow-on abnormal network behavior before escalating the alert beyond investigation priority.
· Add suppressions for approved developer systems, AI platform services, model automation, monitoring, scanning, patching, and known lab workflows.
· Use identity, endpoint, application, model artifact, and credential-management telemetry to confirm whether the internal source or Ollama environment shows evidence of compromise.
· Avoid treating internal access alone as malicious.
DRI Assessment
DRI
7.5 / 10
· The rule is behaviorally anchored to internal exposure and abnormal access sequencing rather than static exploit indicators.
· The rule remains useful if the activity originates from compromised internal systems, unmanaged developer devices, lab networks, or lateral movement paths.
· The score is supported by the durability of unfamiliar internal hosts accessing shared AI infrastructure followed by abnormal network behavior.
· The score is constrained by noisy internal AI experimentation, shared lab environments, weak ownership records, and incomplete internal source baselining.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
8.0 / 10
· Operational confidence depends on east-west visibility, source baselining, network-zone mapping, host-role tagging, service identification, and internal consumer inventory quality.
· Operational confidence is reduced where internal model servers are broadly shared, developer hosts are unmanaged, and lab networks lack stable baselines.
· Full-telemetry confidence improves when NDR data is enriched with endpoint telemetry, identity logs, application logs, container metadata, asset inventory, patch state, and credential-management activity.
· Even under full telemetry conditions, this rule should be treated as an internal-risk escalation signal requiring correlation.
Limitations
· This rule detects suspicious internal access and abnormal network behavior, not exploitation by itself.
· Legitimate developer activity, lab testing, model experimentation, automation, monitoring, vulnerability scanning, and shared-service access may overlap with this pattern.
· The rule requires internal source baselining, east-west visibility, network-zone mapping, and asset ownership data to remain reliable.
· NDR may not identify model artifact creation, runtime instability, local process behavior, or credential use without enrichment.
· Confirmation requires correlation with endpoint, application, file, identity, credential-management, or SIEM evidence.
Detection Query Pattern
NDR / Network Behavioral Analytics sequence pattern requiring platform syntax, internal baseline, network-zone mapping, host-role tagging, and timing-window validation before production deployment.
SEQUENCE WITHIN ENV_INTERNAL_RISK_WINDOW
STEP 1:
DEST_ASSET_ROLE IN (
"Ollama Server",
"Self-Hosted AI Model Server",
"AI Lab Server",
"Developer AI Infrastructure",
"Shared Model Infrastructure"
)
AND DEST_SERVICE IN (
"ollama",
"ai-model-server",
"model-serving-api"
)
AND SRC_NETWORK_SCOPE = "internal"
AND SRC_ASSET_CLASS IN (
"newly_observed",
"rare_for_service",
"unmanaged",
"unapproved_zone",
"contractor_network",
"lab_network",
"unknown_role"
)
AND SRC_HOST NOT IN APPROVED_OLLAMA_ADMIN_SOURCES
AND SRC_HOST NOT IN APPROVED_OLLAMA_CONSUMERS
FOLLOWED BY STEP 2:
(
SRC_HOST = STEP_1.SRC_HOST
OR SRC_HOST = STEP_1.DEST_HOST
)
AND (
OUTBOUND_DEST_CLASS IN (
"newly_observed",
"rare",
"unapproved",
"external",
"unknown"
)
OR EAST_WEST_DEST_ROLE IN (
"Credential Management System",
"Source Code Repository",
"Cloud Control Plane",
"Internal API",
"Shared Model Infrastructure",
"Administrative Service"
)
OR OUTBOUND_BYTES > ENV_BASELINE_INTERNAL_OLLAMA_RELATED_EGRESS
OR DNS_DOMAIN_PREVALENCE = "low"
OR CONNECTION_COUNT > ENV_BASELINE_INTERNAL_OLLAMA_RELATED_CONNECTIONS
)
AND NOT SRC_HOST IN APPROVED_AI_PLATFORM_SERVICES
AND NOT SRC_HOST IN APPROVED_MONITORING_OR_SCANNING_SYSTEMS
SentinelOne
Detection Viability Assessment
SentinelOne has three rules for this EXP report.
· SentinelOne is viable for detecting endpoint-level behavior on Ollama servers, developer AI systems, AI lab hosts, shared model-serving infrastructure, and container hosts where endpoint telemetry is available.
· SentinelOne is strongest where process ancestry, command-line capture, file activity, process-to-network mapping, user context, service-account context, host-role tagging, and runtime stability events are available.
· SentinelOne is not a standalone source for confirming the original network request, route-level API access, memory disclosure, or outbound data content without application, proxy, network, or SIEM correlation.
· SentinelOne is most valuable for identifying suspicious Ollama process behavior, unusual model artifact writes, runtime instability, abnormal process-to-network activity, and host-level activity that may follow suspicious model-ingestion events.
Rule 1
Ollama Process Writes Unusual Model Artifacts or GGUF-Related Files
Rule Format
SentinelOne Deep Visibility query pattern suitable for STAR-style alerting after tenant syntax validation, field validation, host-role tagging, Ollama path validation, model storage baselining, and environment-specific path tuning.
Detection Purpose
· Detect unusual model artifact creation, modification, or staging activity initiated by the Ollama process or an Ollama-associated service context.
· Identify suspicious model artifact handling without relying on exploit strings, public proof-of-concept artifacts, static payload names, attacker infrastructure, or one implementation-specific file name.
· Prioritize model artifact activity on exposed, shared, unpatched, or sensitive Ollama infrastructure where model-ingestion activity may create data-exposure risk.
· This rule does not prove memory disclosure or malicious model content without supporting network, application, runtime, outbound, identity, or credential evidence.
Detection Logic
· Identify file creation, file modification, file rename, or file attribute changes on hosts tagged as Ollama servers, self-hosted AI model servers, AI lab servers, developer AI infrastructure, shared model infrastructure, or container hosts running Ollama.
· Prioritize activity initiated by the Ollama process, Ollama service account, container runtime tied to Ollama, shell or interpreter process launched near Ollama activity, or model-management automation context.
· Prioritize file activity affecting model storage directories, blob storage paths, manifest locations, temporary model-ingestion directories, container-mounted model volumes, or unusual locations outside approved model storage paths.
· Increase confidence when file activity involves GGUF-related artifacts, unusually sized model files, model manifests, blob changes, temporary staging files, or artifact changes outside approved administrative windows.
· Increase confidence when file activity follows suspicious inbound access, untrusted model-ingestion activity, service instability, unusual outbound communication, or unpatched exposure.
· Do not classify the file activity as confirmed compromise without corroborating network, application, artifact review, runtime, outbound, identity, or credential evidence.
Required Telemetry
· SentinelOne file creation telemetry.
· SentinelOne file modification telemetry.
· File rename or file attribute telemetry where available.
· Process ancestry.
· Source process name.
· Source process path.
· Source process command line where available.
· Target file path.
· Target file extension where available.
· File hash where available.
· File size where available.
· User and service-account context where available.
· Host identity.
· Host role or asset tag.
· Endpoint operating system.
· Container context where available.
· Timestamp.
· Network connection mapping where available.
Engineering Implementation Instructions
· Validate SentinelOne tenant syntax and tenant field names for file event type, source process, target file path, command line, user, host identity, container context, and timestamp before deployment.
· Scope the rule to hosts tagged as Ollama servers, self-hosted AI model servers, AI lab systems, developer AI infrastructure, shared model infrastructure, or container hosts running Ollama.
· Validate the organization’s Ollama model storage paths, blob paths, manifest paths, container-mounted model volumes, temporary directories, and approved model-management directories.
· Tune source process names and paths to the organization’s Ollama deployment pattern, including local binary execution, service execution, containerized workloads, and automation workflows.
· Add allowlists for approved model pulls, model imports, model refreshes, patching, backups, migration workflows, AI platform automation, and authorized developer testing.
· Treat unusual artifact writes as higher priority when paired with untrusted inbound access, unpatched exposure, service instability, rare egress, or credential activity.
· Use network, application, proxy, container, SIEM, identity, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to suspicious model artifact handling rather than static artifact names or exploit-specific payloads.
· The rule remains useful if attackers rename artifacts, change model names, vary file sizes, alter delivery timing, or avoid public proof-of-concept naming conventions.
· The score is supported by the durability of model artifact creation and modification as an observable host-level behavior around model-ingestion activity.
· The score is constrained by legitimate model experimentation, model refresh workflows, approved imports, developer testing, and incomplete model storage baselining.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on file telemetry fidelity, process ancestry, command-line capture, host-role tagging, model storage path awareness, and maintenance baseline quality.
· Operational confidence is reduced where Ollama runs on unmanaged developer systems, ephemeral containers, temporary lab hosts, or poorly documented model storage paths.
· Full-telemetry confidence improves when SentinelOne telemetry is enriched with proxy logs, NDR data, application activity, container telemetry, model-ingestion context, egress behavior, and identity activity.
· Even under full telemetry conditions, unusual model artifact activity requires correlation before confirmed compromise classification.
Limitations
· This rule detects suspicious model artifact activity, not memory disclosure itself.
· Legitimate model pulls, model imports, model refreshes, backups, migrations, testing, and approved automation may overlap with this behavior.
· This rule requires file telemetry, process lineage, path awareness, endpoint coverage, and host-role scoping to remain reliable.
· SentinelOne may not identify route-level model-ingestion activity unless enriched by proxy, application, or network telemetry.
· Confirmation requires correlation with suspicious inbound access, runtime instability, unusual outbound communication, identity activity, credential-management activity, or artifact review.
Detection Query Pattern
SentinelOne Deep Visibility query pattern requiring tenant syntax, field validation, path validation, host-role tagging, and environment-specific tuning before production deployment.
EndpointOS IN ("windows", "linux", "macos")
AND EventType IN ANY (
"File Creation",
"File Modification",
"File Rename",
"File Attribute Change"
)
AND AgentComputerName IN ASSET_GROUP (
"Ollama Servers",
"Self-Hosted AI Model Servers",
"AI Lab Servers",
"Developer AI Infrastructure",
"Shared Model Infrastructure",
"Container Hosts Running Ollama"
)
AND SrcProcName IN ANY (
"ollama",
"ollama.exe",
"ollama app.exe",
"docker",
"containerd",
"containerd-shim",
"runc",
"podman"
)
AND (
TgtFilePath CONTAINS ANY (
"/.ollama/models/",
"/usr/share/ollama/",
"/var/lib/ollama/",
"/opt/ollama/",
"/models/",
"/model-cache/",
"\\.ollama\\models\\",
"\\ProgramData\\Ollama\\"
)
OR TgtFilePath ENDSWITH ANY (
".gguf",
".manifest"
)
)
AND (
TgtFilePath CONTAINS ANY (
"gguf",
"blob",
"manifest",
"models",
"modelfile"
)
OR TgtFileSize > ENV_BASELINE_OLLAMA_ARTIFACT_SIZE
OR FileOperationContext = "model_artifact_change"
)
AND NOT SrcProcCmdLine CONTAINS ANY (
"approved_model_pull",
"approved_model_import",
"approved_model_refresh",
"approved_backup_workflow",
"approved_migration_workflow",
"approved_ai_platform_automation",
"approved_developer_test"
)
Rule 2
Ollama Runtime Instability Near Suspicious Model-Ingestion Activity
Rule Format
SentinelOne Deep Visibility query pattern suitable for runtime and fault-adjacent alerting after tenant syntax validation, process-event validation, service-restart validation, host-role tagging, and environment-specific tuning.
Detection Purpose
· Detect Ollama process crashes, abnormal exits, repeated restarts, service instability, or runtime anomalies that occur near suspicious model-ingestion activity or model artifact handling.
· Identify host-level instability that may support investigation of abnormal model-loader behavior without publishing exploit-construction detail.
· Prioritize instability events on exposed, unpatched, shared, or sensitive Ollama infrastructure.
· This rule does not confirm exploitation or memory disclosure without supporting network, application, artifact, outbound, identity, or credential evidence.
Detection Logic
· Identify Ollama process termination, abnormal exit, crash-related events, restart loops, service-manager restarts, or container restart behavior on tagged Ollama infrastructure.
· Identify crash-adjacent execution events involving Ollama, container runtime processes, service supervisors, or model-management automation.
· Prioritize runtime instability occurring near model artifact creation, model artifact modification, large model-related file writes, suspicious inbound access, or unusual outbound communication.
· Increase confidence when instability occurs on an unpatched, internet-facing, broadly reachable, or shared Ollama deployment.
· Increase confidence when the same host shows repeated instability during a short investigation window.
· Do not classify instability as confirmed compromise without corroborating model-ingestion, artifact, network, outbound, identity, or credential evidence.
Required Telemetry
· SentinelOne process lifecycle telemetry.
· Process termination or abnormal exit telemetry where available.
· Process restart telemetry where available.
· Service-manager activity where available.
· Container runtime telemetry where available.
· Process ancestry.
· Command-line capture where available.
· Source process and target process names.
· Source process and target process paths.
· Host identity.
· Host role or asset tag.
· Endpoint operating system.
· User and service-account context where available.
· Timestamp.
· File activity near the runtime event.
· Network connection mapping where available.
Engineering Implementation Instructions
· Validate SentinelOne tenant syntax and tenant field names for process lifecycle, crash-related, service activity, source process, target process, command line, host identity, container context, and timestamp before deployment.
· Scope the rule to hosts tagged as Ollama servers, self-hosted AI model servers, AI lab systems, developer AI infrastructure, shared model infrastructure, or container hosts running Ollama.
· Validate how the environment records Ollama crashes, abnormal exits, service restarts, container restarts, and service-supervisor behavior.
· Tune correlation windows around model artifact writes, suspicious inbound access, model-ingestion events, and outbound communication.
· Add allowlists for approved service restarts, patching, upgrades, resource maintenance, container redeployments, lab testing, and known unstable development workflows.
· Treat runtime instability as higher priority when paired with untrusted inbound access, unpatched exposure, unusual model artifact activity, rare egress, or credential activity.
· Use application, network, proxy, container, SIEM, identity, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
7.5 / 10
· The rule is behaviorally anchored to suspicious runtime instability around model-ingestion activity rather than exploit-specific payload matching.
· The rule remains useful if request contents, model names, attacker infrastructure, or artifact names change.
· The score is supported by the durability of crash-adjacent runtime anomalies as a useful supporting signal for abnormal model-handling behavior.
· The score is constrained by legitimate crashes, resource exhaustion, incompatible model handling, lab testing, container redeployments, and incomplete crash telemetry.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
8.0 / 10
· Operational confidence depends on process lifecycle fidelity, crash-event visibility, service-restart visibility, host-role tagging, model artifact context, and timing correlation.
· Operational confidence is reduced where SentinelOne does not capture detailed crash context, container restart behavior, or service-manager activity.
· Full-telemetry confidence improves when SentinelOne telemetry is enriched with application logs, NDR telemetry, proxy records, container logs, file activity, asset patch state, and egress activity.
· Even under full telemetry conditions, instability should be treated as supporting evidence rather than standalone confirmation of exploitation.
Limitations
· This rule detects runtime instability near suspicious model activity, not the original request or memory disclosure.
· Legitimate model loading, resource exhaustion, incompatible model testing, upgrades, restarts, container redeployments, and lab workflows may overlap with this behavior.
· The rule requires reliable process lifecycle, host-role, timing, and model artifact context to remain useful.
· SentinelOne may not confirm whether instability was caused by malicious input without application, proxy, or model artifact evidence.
· Confirmation requires correlation with suspicious model-ingestion activity, artifact changes, outbound movement, identity activity, credential-management activity, or other supporting evidence.
Detection Query Pattern
SentinelOne Deep Visibility query pattern requiring tenant syntax, field validation, crash-event validation, timing-window validation, host-role tagging, and environment-specific tuning before production deployment.
EndpointOS IN ("windows", "linux", "macos")
AND AgentComputerName IN ASSET_GROUP (
"Ollama Servers",
"Self-Hosted AI Model Servers",
"AI Lab Servers",
"Developer AI Infrastructure",
"Shared Model Infrastructure",
"Container Hosts Running Ollama"
)
AND (
(
EventType IN ANY (
"Process Termination",
"Process Exit",
"Process Crash",
"Service Restart",
"Container Restart"
)
AND TgtProcName IN ANY (
"ollama",
"ollama.exe",
"ollama app.exe",
"docker",
"containerd",
"containerd-shim",
"runc",
"podman"
)
)
OR (
EventType = "Process Creation"
AND SrcProcName IN ANY (
"systemd",
"systemctl",
"launchd",
"services.exe",
"svchost.exe",
"docker",
"containerd",
"podman"
)
AND TgtProcName IN ANY (
"ollama",
"ollama.exe",
"ollama app.exe"
)
)
)
AND EVENT_NEAR WITHIN ENV_MODEL_ACTIVITY_WINDOW (
FileEvent.TgtFilePath CONTAINS ANY (
"/.ollama/models/",
"/usr/share/ollama/",
"/var/lib/ollama/",
"/models/",
"\\.ollama\\models\\",
"\\ProgramData\\Ollama\\"
)
OR NetworkEvent.RemoteSourceClass IN (
"external",
"untrusted",
"newly_observed",
"rare"
)
OR NetworkEvent.RemoteDestClass IN (
"newly_observed",
"rare",
"unapproved",
"external"
)
)
AND NOT SrcProcCmdLine CONTAINS ANY (
"approved_patch_workflow",
"approved_upgrade_workflow",
"approved_restart_workflow",
"approved_container_redeploy",
"approved_lab_test",
"approved_resource_maintenance"
)
Rule 3
Ollama Process Followed by Unusual Network or Runtime Behavior
Rule Format
SentinelOne Deep Visibility query pattern suitable for process-to-network and runtime-behavior alerting after tenant syntax validation, process-network mapping validation, destination baselining, host-role tagging, and environment-specific tuning.
Detection Purpose
· Detect Ollama process activity followed by unusual outbound network communication, unfamiliar destination access, suspicious process-to-network behavior, or abnormal runtime context.
· Identify host-level behavior that may support investigation of possible data exposure, artifact movement, or attacker-directed outbound activity.
· Prioritize Ollama hosts or containers that communicate with destinations outside approved model-source, update, registry, automation, or administrative baselines.
· This rule does not determine transmitted content or confirm memory disclosure without supporting network, proxy, application, file, identity, or credential evidence.
Detection Logic
· Identify Ollama process execution or Ollama-associated service activity on tagged AI model-serving hosts.
· Identify outbound network connections initiated by the Ollama process, an Ollama-associated container, or a model-management automation process.
· Prioritize destination classes that are newly observed, rare, external, unapproved, anonymous hosting, cloud storage, file sharing, unknown model registry, or low-prevalence domains.
· Increase confidence when outbound activity follows suspicious model artifact creation, runtime instability, untrusted inbound access, or unpatched exposure.
· Increase confidence when the destination is outside the approved model registry, update, monitoring, and automation baseline.
· Do not classify outbound activity as confirmed data theft without corroborating proxy, NDR, file, artifact, identity, or credential evidence.
Required Telemetry
· SentinelOne process creation telemetry.
· Process-to-network connection telemetry.
· Process ancestry.
· Command-line capture where available.
· Source process name.
· Source process path.
· Destination IP address.
· Destination domain where available.
· Destination port.
· Destination reputation where available.
· User and service-account context where available.
· Host identity.
· Host role or asset tag.
· Container context where available.
· Timestamp.
· File activity near the outbound event where available.
· Exposure or patch context where available.
Engineering Implementation Instructions
· Validate SentinelOne tenant syntax and tenant field names for process events, network events, destination fields, source process, command line, host identity, user, container context, and timestamp before deployment.
· Scope the rule to hosts tagged as Ollama servers, self-hosted AI model servers, AI lab systems, developer AI infrastructure, shared model infrastructure, or container hosts running Ollama.
· Establish approved model registries, update services, cloud destinations, automation systems, container registries, telemetry systems, and administrative destinations.
· Tune the rule to prioritize rare, newly observed, unapproved, low-prevalence, and external destinations rather than alerting on all Ollama network activity.
· Add allowlists for approved model pulls, approved model pushes, patching, backups, monitoring, container registry access, AI platform automation, and authorized developer workflows.
· Treat unusual outbound activity as higher priority when paired with model artifact writes, runtime instability, untrusted inbound access, unpatched status, or credential activity.
· Use NDR, proxy, application, file, SIEM, identity, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to unusual process-to-network activity from Ollama infrastructure rather than static payload indicators.
· The rule remains useful if attacker infrastructure rotates, model names change, artifact names vary, or outbound timing changes.
· The score is supported by the durability of model-serving infrastructure communicating with unfamiliar destinations after suspicious host activity.
· The score is constrained by legitimate model downloads, model pushes, developer experimentation, registry synchronization, cloud storage access, and incomplete destination baselining.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on process-to-network mapping, destination visibility, destination baselining, command-line capture, host-role tagging, and container context.
· Operational confidence is reduced where endpoint telemetry lacks reliable destination domains, container process mapping, or approved outbound baselines.
· Full-telemetry confidence improves when SentinelOne telemetry is enriched with NDR data, proxy logs, DNS telemetry, application logs, model artifact activity, asset patch state, and identity activity.
· Even under full telemetry conditions, this rule should support escalation and investigation rather than standalone confirmation of data exposure.
Limitations
· This rule detects unusual outbound behavior from Ollama infrastructure, not the content of transmitted data.
· Legitimate model management, update workflows, telemetry agents, backups, testing, registry access, and cloud storage workflows may overlap with this behavior.
· The rule requires process-to-network mapping, destination baselining, endpoint coverage, and host-role scoping to remain reliable.
· SentinelOne may not determine whether outbound communication contains prompts, credentials, model artifacts, or other sensitive runtime content.
· Confirmation requires correlation with NDR telemetry, proxy records, application logs, file activity, model artifact review, identity activity, or credential-management evidence.
Detection Query Pattern
SentinelOne Deep Visibility query pattern requiring tenant syntax, field validation, process-to-network validation, destination-baseline validation, host-role tagging, and environment-specific tuning before production deployment.
EndpointOS IN ("windows", "linux", "macos")
AND EventType IN ANY (
"Network Connection",
"Process Creation"
)
AND AgentComputerName IN ASSET_GROUP (
"Ollama Servers",
"Self-Hosted AI Model Servers",
"AI Lab Servers",
"Developer AI Infrastructure",
"Shared Model Infrastructure",
"Container Hosts Running Ollama"
)
AND SrcProcName IN ANY (
"ollama",
"ollama.exe",
"ollama app.exe",
"docker",
"containerd",
"containerd-shim",
"runc",
"podman"
)
AND (
RemoteDestClass IN (
"newly_observed",
"rare",
"unapproved",
"external",
"anonymous_hosting",
"cloud_storage",
"file_sharing",
"unknown_model_registry"
)
OR RemoteDomain NOT IN APPROVED_OLLAMA_DESTINATIONS
OR RemoteIP NOT IN APPROVED_OLLAMA_EGRESS_DESTINATIONS
OR RemoteReputation IN (
"unknown",
"suspicious",
"low_prevalence"
)
)
AND EVENT_NEAR WITHIN ENV_MODEL_ACTIVITY_WINDOW (
FileEvent.TgtFilePath CONTAINS ANY (
"/.ollama/models/",
"/usr/share/ollama/",
"/var/lib/ollama/",
"/models/",
"\\.ollama\\models\\",
"\\ProgramData\\Ollama\\"
)
OR ProcessEvent.TgtProcName IN ANY (
"ollama",
"ollama.exe",
"ollama app.exe"
)
OR NetworkEvent.RemoteSourceClass IN (
"external",
"untrusted",
"newly_observed",
"rare"
)
)
AND NOT SrcProcCmdLine CONTAINS ANY (
"approved_model_pull",
"approved_model_push",
"approved_patch_workflow",
"approved_backup_workflow",
"approved_monitoring_workflow",
"approved_container_registry",
"approved_ai_platform_automation",
"approved_developer_workflow"
)
Splunk
Detection Viability Assessment
Splunk has three rules for this EXP report.
· Splunk is viable for correlating exposed Ollama infrastructure, model-ingestion activity, model artifact changes, outbound communication, identity activity, credential-management activity, and asset or patch context.
· Splunk is strongest where proxy logs, ingress logs, endpoint telemetry, container telemetry, DNS logs, firewall logs, cloud logs, asset inventory, vulnerability data, and identity telemetry are normalized or consistently searchable.
· Splunk should not be treated as a standalone source for confirming memory disclosure unless the underlying telemetry provides strong supporting evidence of suspicious model-ingestion activity, artifact movement, outbound transfer, or downstream credential use.
· Splunk is most valuable for multi-source correlation because this exposure requires sequence-based detection rather than single-event matching.
Rule 1
Untrusted Source Access to Ollama Model-Ingestion Functionality
Rule Format
Splunk SPL correlation search pattern suitable for scheduled detection after index validation, sourcetype validation, field normalization, asset tagging, approved-source baselining, and environment-specific tuning.
Detection Purpose
· Detect access to Ollama model-ingestion or model-transfer functionality from external, untrusted, newly observed, rare, or unapproved sources.
· Identify suspicious interaction with self-hosted AI model infrastructure without relying on exploit strings, public proof-of-concept artifacts, static payload names, or attacker infrastructure.
· Prioritize Ollama services that are internet-facing, broadly reachable, unpatched, or outside approved administrative access patterns.
· This rule does not confirm memory disclosure or successful exploitation without supporting endpoint, artifact, runtime, outbound, identity, or credential-management evidence.
Detection Logic
· Identify HTTP, reverse proxy, ingress, load balancer, API gateway, or application logs associated with Ollama infrastructure.
· Identify requests to Ollama model-ingestion, blob, or model-transfer functionality where route-level telemetry is available.
· Identify source addresses, users, service accounts, or source systems that are external, untrusted, newly observed, rare for the service, or outside approved administrative baselines.
· Increase confidence when the destination is tagged as an Ollama server, self-hosted AI model server, AI lab host, developer AI infrastructure, or shared model infrastructure.
· Increase confidence when the destination is internet-facing, unpatched, newly exposed, broadly reachable, or associated with sensitive AI workflows.
· Do not classify the activity as confirmed compromise without corroborating endpoint, file, container, outbound, identity, or credential-management evidence.
Required Telemetry
· Reverse proxy logs.
· Ingress logs.
· API gateway logs.
· Load balancer logs.
· Application access logs where available.
· Source IP address.
· Destination host.
· Request path.
· Request method.
· Response status.
· User agent where available.
· Authentication context where available.
· Asset role or host tag.
· Exposure context.
· Approved administrative source baseline.
· Patch or vulnerability context where available.
· Timestamp.
Engineering Implementation Instructions
· Validate Splunk indexes, sourcetypes, field names, and field extractions for proxy, ingress, gateway, load balancer, and application logs before deployment.
· Scope the rule to assets tagged as Ollama servers, self-hosted AI model servers, AI lab servers, developer AI infrastructure, shared model infrastructure, or containerized model-serving workloads.
· Validate approved administrative sources, approved automation sources, internal AI platform services, vulnerability scanners, monitoring systems, and known testing networks.
· Use route-level request paths only where the telemetry source provides reliable path visibility.
· Avoid alerting on all Ollama access. Require untrusted, newly observed, rare, external, or unapproved source context.
· Treat internet exposure, unpatched status, source novelty, repeated route access, large request size, or abnormal timing as prioritization context.
· Use endpoint, NDR, container, file, DNS, egress, identity, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
8.5 / 10
· The rule is behaviorally anchored to untrusted access against exposed AI model infrastructure rather than brittle exploit artifacts.
· The rule remains useful if attacker infrastructure rotates, model names change, request timing varies, or public proof-of-concept details change.
· The score is supported by the durability of untrusted access to model-ingestion functionality as an observable control-plane signal.
· The score is constrained by environments without route-level logs, weak asset tagging, incomplete approved-source baselines, or decentralized developer deployments.
TCR Assessment
Operational TCR
7.5 / 10
Full-Telemetry TCR
9.0 / 10
· Operational confidence depends on route-level logging, source normalization, host-role tagging, exposure context, patch context, and approved-source baselining.
· Operational confidence is reduced when Ollama is directly exposed without proxy logs, when developer systems are unmanaged, or when application logs are incomplete.
· Full-telemetry confidence improves when Splunk correlates proxy logs with endpoint telemetry, NDR activity, DNS telemetry, egress logs, vulnerability data, and identity events.
· Even under full telemetry conditions, this rule requires supporting evidence before confirmed compromise classification.
Limitations
· This rule detects suspicious access to Ollama model-ingestion functionality, not memory disclosure itself.
· Route-level visibility may be unavailable when Ollama is directly exposed or when logs are not collected from the fronting infrastructure.
· Legitimate model management, developer testing, approved automation, vulnerability scanning, and monitoring activity may overlap with this behavior.
· Confirmation requires correlation with model artifact activity, runtime instability, outbound communication, identity activity, credential-management activity, or other supporting evidence.
Detection Query Pattern
Splunk SPL correlation search pattern requiring index, sourcetype, field, asset, and lookup validation before production deployment.
index IN (
proxy,
ingress,
api_gateway,
load_balancer,
application
)
sourcetype IN (
nginx:access,
apache:access,
envoy:access,
alb:access,
cloudflare:logs,
api_gateway:access,
app:ollama
)
(
dest_asset_role IN (
"Ollama Server",
"Self-Hosted AI Model Server",
"AI Lab Server",
"Developer AI Infrastructure",
"Shared Model Infrastructure"
)
OR dest_service IN (
"ollama",
"ai-model-server",
"model-serving-api"
)
OR dest_port=11434
)
uri_path IN (
"/api/create",
"/api/blobs",
"/api/push"
)
| lookup approved_ollama_admin_sources.csv src_ip OUTPUT src_ip AS approved_src
| lookup ollama_asset_inventory.csv dest OUTPUT dest_asset_role exposure_status patch_status owner
| eval untrusted_source=if(
isnull(approved_src)
AND (
src_category IN ("external","untrusted","newly_observed","rare","unapproved_internal")
OR isnull(src_category)
),
1,
0
)
| where untrusted_source=1
| eval risk_context=mvappend(src_category, exposure_status, patch_status)
| stats
count AS request_count
values(uri_path) AS uri_paths
values(http_method) AS methods
values(status) AS statuses
values(user_agent) AS user_agents
values(risk_context) AS risk_context
min(_time) AS first_seen
max(_time) AS last_seen
BY src_ip dest dest_asset_role owner
| where request_count >= ENV_BASELINE_OLLAMA_MODEL_INGESTION_REQUEST_COUNT
Rule 2
Rule
Ollama Model-Ingestion Activity Followed by Artifact Creation and Outbound Communication
Rule Format
Splunk SPL sequence-based correlation search pattern suitable for scheduled detection after data-model validation, index validation, sourcetype validation, asset tagging, timing-window validation, and environment-specific tuning.
Detection Purpose
· Detect model-ingestion activity followed by new or unusual model artifact creation and outbound communication from the same Ollama host or workload.
· Identify a stronger behavioral sequence that may indicate suspicious model handling, artifact transfer, or data-exposure risk.
· Prioritize cases where multiple telemetry sources align across application, endpoint, file, network, DNS, or egress data.
· This rule does not determine the content of outbound communication without supporting packet, proxy, endpoint, artifact, or destination evidence.
Detection Logic
· Identify Ollama model-ingestion or model-transfer activity from application, proxy, ingress, API gateway, or load balancer logs.
· Correlate the destination host with endpoint or file telemetry showing new model artifacts, GGUF-related files, blob changes, manifest updates, temporary model components, or unusual model storage activity.
· Correlate the same host or workload with outbound connections to unfamiliar, rare, unapproved, newly observed, cloud storage, file-sharing, anonymous hosting, or unknown model-registry destinations.
· Increase confidence when the Ollama host is unpatched, internet-facing, broadly reachable, or outside approved deployment inventory.
· Increase confidence when the sequence occurs outside approved administrative windows or involves source systems outside approved administrative baselines.
· Do not classify the sequence as confirmed data theft without corroborating outbound content, artifact review, identity activity, or credential-management evidence.
Required Telemetry
· Proxy, ingress, gateway, load balancer, or application logs.
· Endpoint process telemetry.
· Endpoint file telemetry.
· Container telemetry where available.
· Firewall or network flow logs.
· DNS logs.
· Egress telemetry.
· Source and destination IP addresses.
· Host identity.
· Asset role or host tag.
· Model storage path telemetry.
· Destination reputation where available.
· Approved destination baseline.
· Patch or vulnerability context where available.
· Timestamp.
Engineering Implementation Instructions
· Validate Splunk indexes, sourcetypes, and normalized fields for application, proxy, endpoint, file, container, DNS, firewall, and egress data sources.
· Validate host identity joins across proxy, endpoint, container, DNS, firewall, and asset inventory data.
· Scope the rule to tagged Ollama infrastructure and approved model-serving environments.
· Establish approved model storage paths, approved model registries, approved outbound destinations, approved administrative sources, and approved model-management windows.
· Tune the correlation window to reflect normal model-ingestion and model-management workflows.
· Add suppressions for approved model pulls, approved model pushes, patching, backups, migration workflows, container registry access, monitoring, AI platform automation, and authorized developer testing.
· Treat this rule as high priority when untrusted inbound access, unpatched exposure, unusual artifact creation, and unfamiliar outbound communication occur in the same sequence.
DRI Assessment
DRI
8.5 / 10
· The rule is behaviorally anchored to a multi-stage sequence rather than a single fragile indicator.
· The rule remains useful if model names, artifact names, source infrastructure, request timing, or outbound destinations change.
· The score is supported by the durability of model-ingestion activity followed by artifact changes and unusual outbound communication as a high-value detection pattern.
· The score is constrained by environments where host identity joins are unreliable, endpoint telemetry is incomplete, or model transfer workflows are frequent and decentralized.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
9.0 / 10
· Operational confidence depends on route-level visibility, endpoint file telemetry, egress telemetry, host identity correlation, asset tagging, and destination baselining.
· Operational confidence is reduced where model storage paths are poorly documented, outbound destinations are not baselined, or container telemetry is incomplete.
· Full-telemetry confidence improves when Splunk correlates proxy logs, endpoint telemetry, file telemetry, container telemetry, DNS logs, firewall logs, NDR data, asset inventory, and patch context.
· Even under full telemetry conditions, this rule requires artifact review and supporting evidence before confirmed data-exposure classification.
Limitations
· This rule detects a suspicious behavioral sequence, not memory disclosure itself.
· Legitimate model imports, model refreshes, model pushes, backups, migrations, registry synchronization, developer testing, and approved automation may overlap with this pattern.
· The rule requires reliable host identity correlation across multiple data sources.
· Splunk can only correlate the data that is ingested and normalized. Missing endpoint, file, proxy, DNS, or egress telemetry reduces confidence.
· Confirmation requires review of application activity, endpoint artifacts, outbound destinations, identity activity, credential-management activity, and incident timeline.
Detection Query Pattern
Splunk SPL sequence-based correlation search pattern requiring index, sourcetype, field, lookup, timing-window, and host-identity validation before production deployment.
(
search index IN (
proxy,
ingress,
api_gateway,
load_balancer,
application
)
(
dest_asset_role IN (
"Ollama Server",
"Self-Hosted AI Model Server",
"AI Lab Server",
"Developer AI Infrastructure",
"Shared Model Infrastructure"
)
OR dest_service IN (
"ollama",
"ai-model-server",
"model-serving-api"
)
OR dest_port=11434
)
uri_path IN (
"/api/create",
"/api/blobs",
"/api/push"
)
| eval event_stage="model_ingestion"
| eval correlation_host=coalesce(dest_host,dest)
| fields _time correlation_host src_ip dest uri_path http_method event_stage
)
| append [
search index IN (
endpoint,
edr,
file_integrity,
container
)
EventType IN (
"File Creation",
"File Modification",
"File Rename",
"File Attribute Change"
)
(
process_name IN (
"ollama",
"ollama.exe",
"docker",
"containerd",
"containerd-shim",
"runc",
"podman"
)
OR file_path IN (
"*/.ollama/models/*",
"*/usr/share/ollama/*",
"*/var/lib/ollama/*",
"*\\.ollama\\models\\*",
"*\\ProgramData\\Ollama\\*"
)
)
(
file_path="*.gguf"
OR file_path="*.manifest"
OR file_path="*blob*"
OR file_path="*modelfile*"
OR file_size > ENV_BASELINE_OLLAMA_ARTIFACT_SIZE
)
| eval event_stage="artifact_activity"
| eval correlation_host=coalesce(host,dest_host,container_host)
| fields _time correlation_host process_name file_path file_size event_stage
]
| append [
search index IN (
firewall,
network,
dns,
proxy,
ndr
)
| lookup approved_ollama_destinations.csv dest_domain OUTPUT dest_domain AS approved_domain
| eval unusual_dest=if(
dest_category IN (
"newly_observed",
"rare",
"unapproved",
"external",
"anonymous_hosting",
"cloud_storage",
"file_sharing",
"unknown_model_registry"
)
OR isnull(approved_domain),
1,
0
)
| where unusual_dest=1
| eval event_stage="unusual_egress"
| eval correlation_host=coalesce(src_host,host)
| fields _time correlation_host dest_ip dest_domain bytes_out dest_category event_stage
]
| stats
earliest(_time) AS first_seen
latest(_time) AS last_seen
values(event_stage) AS stages
values(src_ip) AS src_ips
values(uri_path) AS uri_paths
values(file_path) AS file_paths
values(dest_domain) AS dest_domains
values(dest_ip) AS dest_ips
sum(bytes_out) AS total_bytes_out
BY correlation_host
| where mvfind(stages,"model_ingestion") >= 0
AND mvfind(stages,"artifact_activity") >= 0
AND mvfind(stages,"unusual_egress") >= 0
AND last_seen-first_seen <= ENV_MODEL_ACTIVITY_WINDOW_SECONDS
Rule 3
Unpatched Ollama Exposure with Suspicious Model Lifecycle and Credential Activity
Rule Format
Splunk SPL risk-based correlation search pattern suitable for scheduled detection after asset inventory validation, vulnerability-data validation, identity-source validation, credential-management telemetry validation, and environment-specific tuning.
Detection Purpose
· Detect unpatched or exposed Ollama infrastructure with suspicious model lifecycle activity and downstream identity or credential-management anomalies.
· Identify cases where exposed AI infrastructure may have created downstream credential or access risk after suspicious model-ingestion activity.
· Prioritize response when technical exposure, suspicious service behavior, and post-event identity activity align.
· This rule does not prove credential theft or memory disclosure without supporting identity, credential, endpoint, application, or network evidence.
Detection Logic
· Identify Ollama infrastructure that is unpatched, internet-facing, broadly reachable, or located outside approved deployment inventory.
· Identify suspicious model lifecycle activity involving model ingestion, model import, model artifact changes, model push behavior, unusual outbound communication, or runtime instability.
· Identify downstream identity or credential-management activity after the exposure window, including unusual API token use, new access keys, abnormal cloud access, unfamiliar repository access, unusual service-account activity, or credential-management anomalies.
· Increase confidence when identity activity involves accounts, service accounts, tokens, hosts, or repositories associated with the Ollama environment.
· Increase confidence when identity or credential activity originates from unfamiliar infrastructure, unfamiliar geography, unfamiliar ASN, rare user-agent context, or unexpected automation context.
· Do not classify this activity as confirmed credential compromise without identity investigation and supporting evidence.
Required Telemetry
· Asset inventory.
· Exposure management data.
· Vulnerability or patch-state data.
· Proxy, ingress, gateway, or application logs.
· Endpoint telemetry.
· File telemetry.
· Container telemetry where available.
· Firewall or network flow logs.
· DNS logs.
· Identity provider logs.
· Cloud audit logs where applicable.
· Repository access logs where applicable.
· Credential-management activity logs where available.
· User, service-account, token, or key identifiers where available.
· Host identity.
· Timestamp.
Engineering Implementation Instructions
· Validate Splunk lookups or indexes for Ollama asset inventory, exposure context, patch state, approved deployments, and approved administrative sources.
· Validate identity, cloud, repository, and credential-management telemetry sources before deployment.
· Scope the rule to identity or credential activity occurring after suspicious Ollama exposure or model lifecycle activity.
· Establish approved administrative identities, service accounts, automation accounts, repository access patterns, cloud access patterns, and credential-management workflows.
· Tune the post-exposure investigation window to organizational incident-response and credential-rotation requirements.
· Add suppressions for approved maintenance, approved key rotation, scheduled automation, known CI/CD workflows, approved repository automation, and approved cloud administration.
· Treat the rule as a high-priority correlation alert, not as standalone proof of credential theft.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to exposure, model lifecycle activity, and downstream credential or identity anomalies.
· The rule remains useful if attacker infrastructure changes, model artifact names vary, or model-ingestion details are only partially visible.
· The score is supported by the durability of downstream credential and identity review after suspected runtime exposure.
· The score is constrained by identity noise, normal key rotation, automation-heavy environments, incomplete credential-management logs, and weak asset-to-identity mapping.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on asset inventory quality, patch-state accuracy, identity telemetry, credential-management logs, cloud audit logs, repository logs, and host-to-identity mapping.
· Operational confidence is reduced when exposed Ollama hosts are not mapped to users, service accounts, repositories, cloud roles, or credential stores.
· Full-telemetry confidence improves when Splunk correlates exposure data, model lifecycle activity, endpoint telemetry, egress telemetry, identity provider logs, cloud audit logs, repository logs, and credential-management activity.
· Even under full telemetry conditions, this rule requires analyst review before confirmed credential compromise classification.
Limitations
· This rule detects suspicious downstream identity or credential activity after Ollama exposure, not memory disclosure itself.
· Legitimate key rotation, CI/CD automation, cloud administration, repository automation, and incident-response activity may overlap with this pattern.
· The rule requires reliable asset-to-identity mapping and credential-management telemetry to remain useful.
· Missing identity, cloud, repository, or credential-management logs can significantly reduce confidence.
· Confirmation requires credential review, identity investigation, artifact review, and incident timeline validation.
Detection Query Pattern
Splunk SPL risk-based correlation search pattern requiring asset, vulnerability, identity, cloud, repository, and credential-management field validation before production deployment.
(
search index IN (
asset_inventory,
vulnerability,
exposure_management
)
(
asset_role IN (
"Ollama Server",
"Self-Hosted AI Model Server",
"AI Lab Server",
"Developer AI Infrastructure",
"Shared Model Infrastructure"
)
OR service="ollama"
OR port=11434
)
(
patch_status="unpatched"
OR exposure_status IN (
"internet_facing",
"broad_internal_access",
"unapproved_exposure"
)
)
| eval event_stage="exposed_unpatched_ollama"
| eval correlation_host=coalesce(host,dest,asset_id)
| fields _time correlation_host asset_role patch_status exposure_status owner linked_identity linked_service_account
)
| append [
search index IN (
proxy,
ingress,
api_gateway,
application,
endpoint,
edr,
file_integrity,
container,
firewall,
dns,
ndr
)
(
uri_path IN (
"/api/create",
"/api/blobs",
"/api/push"
)
OR file_path IN (
"*/.ollama/models/*",
"*/var/lib/ollama/*",
"*\\.ollama\\models\\*",
"*\\ProgramData\\Ollama\\*"
)
OR process_name IN (
"ollama",
"ollama.exe"
)
OR dest_category IN (
"newly_observed",
"rare",
"unapproved",
"external"
)
)
| eval event_stage="suspicious_model_lifecycle"
| eval correlation_host=coalesce(dest_host,host,src_host,container_host)
| fields _time correlation_host src_ip uri_path file_path process_name dest_domain dest_category event_stage
]
| append [
search index IN (
identity,
cloud_audit,
repository,
credential_management
)
(
action IN (
"api_token_used",
"access_key_created",
"access_key_used",
"service_account_used",
"credential_accessed",
"secret_read",
"repository_access",
"cloud_api_call"
)
OR risk_event IN (
"rare_source",
"new_country",
"new_asn",
"new_user_agent",
"unusual_service_account_use",
"unusual_token_use",
"credential_management_anomaly"
)
)
| eval event_stage="credential_or_identity_anomaly"
| eval linked_identity=coalesce(user,service_account,token_subject,access_key_owner)
| fields _time linked_identity src_ip src_country src_asn user_agent action risk_event repository cloud_account event_stage
]
| eventstats
values(linked_identity) AS linked_identities
values(linked_service_account) AS linked_service_accounts
BY correlation_host
| where isnotnull(correlation_host)
| stats
earliest(_time) AS first_seen
latest(_time) AS last_seen
values(event_stage) AS stages
values(patch_status) AS patch_status
values(exposure_status) AS exposure_status
values(src_ip) AS src_ips
values(action) AS actions
values(risk_event) AS risk_events
values(repository) AS repositories
values(cloud_account) AS cloud_accounts
BY correlation_host linked_identity
| where mvfind(stages,"exposed_unpatched_ollama") >= 0
AND mvfind(stages,"suspicious_model_lifecycle") >= 0
AND mvfind(stages,"credential_or_identity_anomaly") >= 0
AND last_seen-first_seen <= ENV_POST_EXPOSURE_IDENTITY_REVIEW_WINDOW_SECONDS
Elastic
Detection Viability Assessment
Elastic has three rules for this EXP report.
· Elastic is viable for detecting and correlating Ollama exposure, model-ingestion activity, endpoint artifact changes, container activity, DNS activity, outbound communication, and identity or cloud telemetry where Elastic integrations are deployed.
· Elastic is strongest where Elastic Agent, endpoint events, web or proxy logs, firewall logs, DNS logs, cloud logs, container telemetry, asset metadata, and vulnerability context are consistently ingested.
· Elastic should not be treated as a standalone source for confirming memory disclosure unless the underlying telemetry supports suspicious model-ingestion activity, artifact movement, unusual outbound communication, runtime instability, or downstream credential activity.
· Elastic is most valuable where the deployment can correlate endpoint, network, web, container, and cloud data around an exposed Ollama host or workload.
Rule 1
Untrusted Access to Ollama Model-Ingestion Functionality
Rule Format
Elastic KQL detection pattern suitable for rule deployment after index validation, data-stream validation, ECS field normalization, asset tagging, source-baseline validation, and environment-specific tuning.
Detection Purpose
· Detect access to Ollama model-ingestion or model-transfer functionality from external, untrusted, newly observed, rare, or unapproved sources.
· Identify suspicious access to self-hosted AI model infrastructure without relying on exploit strings, public proof-of-concept artifacts, static payload names, or attacker infrastructure.
· Prioritize exposed Ollama services that receive model-ingestion activity from sources outside approved administrative paths.
· This rule does not confirm memory disclosure or successful exploitation without supporting endpoint, artifact, runtime, outbound, identity, or credential-management evidence.
Detection Logic
· Identify HTTP, reverse proxy, ingress, load balancer, API gateway, or application events associated with Ollama infrastructure.
· Identify access to Ollama model-ingestion, blob, or model-transfer routes where route-level telemetry is available.
· Identify source addresses, users, service accounts, or systems that are external, untrusted, newly observed, rare for the service, or outside approved administrative baselines.
· Increase confidence when the destination is tagged as an Ollama server, self-hosted AI model server, AI lab host, developer AI infrastructure, shared model infrastructure, or containerized model-serving workload.
· Increase confidence when the destination is internet-facing, unpatched, newly exposed, broadly reachable, or associated with sensitive AI workflows.
· Do not classify the activity as confirmed compromise without corroborating endpoint, file, container, outbound, identity, or credential-management evidence.
Required Telemetry
· Elastic web or proxy logs.
· Ingress, API gateway, or load balancer logs.
· Application access logs where available.
· Source IP address.
· Destination host.
· Request path.
· Request method.
· Response status.
· User agent where available.
· Authentication context where available.
· Asset role or host tag.
· Exposure context.
· Approved administrative source baseline.
· Patch or vulnerability context where available.
· Timestamp.
Engineering Implementation Instructions
· Validate Elastic index patterns, data streams, event categories, and ECS field mappings for web, proxy, ingress, gateway, load balancer, and application logs before deployment.
· Scope the rule to assets tagged as Ollama servers, self-hosted AI model servers, AI lab systems, developer AI infrastructure, shared model infrastructure, or containerized model-serving workloads.
· Validate approved administrative sources, approved automation sources, internal AI platform services, vulnerability scanners, monitoring systems, and known testing networks.
· Use route-level request paths only where the telemetry source provides reliable path visibility.
· Avoid alerting on all Ollama access. Require untrusted, newly observed, rare, external, or unapproved source context.
· Treat internet exposure, unpatched status, source novelty, repeated route access, large request size, or abnormal timing as prioritization context.
· Use endpoint, NDR, container, file, DNS, egress, identity, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to untrusted access against exposed AI model infrastructure rather than brittle exploit artifacts.
· The rule remains useful if attacker infrastructure rotates, request timing varies, model names change, or public proof-of-concept details change.
· The score is supported by the durability of untrusted access to model-ingestion functionality as an observable control-plane signal.
· The score is constrained by environments without route-level logs, weak asset tagging, incomplete source baselines, or decentralized developer deployments.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on route-level logging, ECS field normalization, source classification, host-role tagging, exposure context, patch context, and approved-source baselining.
· Operational confidence is reduced when Ollama is directly exposed without proxy logs, when developer systems are unmanaged, or when application logs are incomplete.
· Full-telemetry confidence improves when Elastic correlates web logs with endpoint telemetry, NDR activity, DNS telemetry, egress logs, vulnerability context, and identity events.
· Even under full telemetry conditions, this rule requires supporting evidence before confirmed compromise classification.
Limitations
· This rule detects suspicious access to Ollama model-ingestion functionality, not memory disclosure itself.
· Route-level visibility may be unavailable when Ollama is directly exposed or when logs are not collected from fronting infrastructure.
· Legitimate model management, developer testing, approved automation, vulnerability scanning, and monitoring activity may overlap with this behavior.
· Elastic field availability and ECS mapping quality vary by deployment and integration.
· Confirmation requires correlation with model artifact activity, runtime instability, outbound communication, identity activity, credential-management activity, or other supporting evidence.
Detection Query Pattern
Elastic KQL detection pattern requiring index, ECS field, asset, source-baseline, and exception-list validation before production deployment.
event.dataset : (
"nginx.access" or
"apache.access" or
"envoyproxy.access" or
"aws.elb" or
"cloudflare.logpush" or
"httpjson" or
"application"
)
and (
host.asset.role : (
"Ollama Server" or
"Self-Hosted AI Model Server" or
"AI Lab Server" or
"Developer AI Infrastructure" or
"Shared Model Infrastructure"
)
or service.name : (
"ollama" or
"ai-model-server" or
"model-serving-api"
)
or destination.port : 11434
)
and url.path : (
"/api/create" or
"/api/blobs" or
"/api/push"
)
and (
source.category : (
"external" or
"untrusted" or
"newly_observed" or
"rare" or
"unapproved_internal"
)
or not source.ip : $APPROVED_OLLAMA_ADMIN_SOURCES
)
and not source.ip : $APPROVED_OLLAMA_ADMIN_SOURCES
and not source.asset.role : (
"Approved AI Platform Service" or
"Approved Model Automation" or
"Approved Vulnerability Scanner" or
"Approved Monitoring System"
)
Rule 2
Ollama Model-Ingestion Activity Followed by Model Artifact Creation
Rule Format
Elastic EQL sequence detection pattern suitable for rule deployment after data-stream validation, ECS field validation, host identity validation, timing-window validation, model-path validation, and environment-specific tuning.
Detection Purpose
· Detect model-ingestion or model-transfer activity followed by model artifact creation or modification on the same Ollama host or workload.
· Identify a higher-confidence host sequence that may indicate suspicious model handling, unexpected artifact creation, or model storage manipulation.
· Prioritize cases where web or proxy telemetry aligns with endpoint file telemetry.
· This rule does not prove malicious model content or memory disclosure without supporting runtime, outbound, artifact-review, identity, or credential-management evidence.
Detection Logic
· Identify model-ingestion or model-transfer activity involving an Ollama server, AI model server, or model-serving API.
· Correlate the destination host with endpoint file telemetry showing new model artifacts, GGUF-related files, blob changes, manifest updates, temporary model components, or unusual model storage activity.
· Increase confidence when artifact activity occurs outside approved administrative windows, outside approved model storage paths, or on unpatched, internet-facing, broadly reachable, or shared Ollama infrastructure.
· Increase confidence when the sequence follows untrusted source access or occurs near unusual outbound communication.
· Do not classify the sequence as confirmed compromise without corroborating outbound, runtime, application, identity, or credential-management evidence.
Required Telemetry
· Elastic web or proxy logs.
· Ingress, gateway, load balancer, or application logs where available.
· Elastic endpoint file telemetry.
· Endpoint process telemetry.
· Container telemetry where available.
· Host identity.
· Asset role or host tag.
· Request path.
· Source IP address.
· File path.
· File extension.
· File size where available.
· Process name.
· Process ancestry where available.
· Model storage path baseline.
· Timestamp.
Engineering Implementation Instructions
· Validate Elastic index patterns and ECS mappings for web, endpoint, file, process, and container telemetry before deployment.
· Validate host identity joins between web or proxy data and endpoint or container data.
· Scope the rule to tagged Ollama infrastructure and approved model-serving environments.
· Establish approved model storage paths, approved model-ingestion windows, approved model-management processes, and approved automation workflows.
· Tune the sequence window to the organization’s normal model-ingestion and model-management behavior.
· Add exceptions for approved model pulls, model imports, model refreshes, backups, migrations, AI platform automation, container redeployments, and authorized developer testing.
· Treat the rule as higher priority when paired with untrusted inbound access, unpatched exposure, runtime instability, unusual outbound communication, or credential activity.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to a host-level sequence rather than a single static file name or exploit artifact.
· The rule remains useful if model names, artifact names, source infrastructure, request timing, or file sizes change.
· The score is supported by the durability of model-ingestion activity followed by model artifact changes as a meaningful detection pattern.
· The score is constrained by legitimate model experimentation, model refresh workflows, approved imports, developer testing, incomplete path baselining, and host identity join quality.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on route-level visibility, endpoint file telemetry, host identity correlation, ECS field quality, asset tagging, and model storage path baselining.
· Operational confidence is reduced where model storage paths are poorly documented, endpoint file telemetry is incomplete, or container metadata is unavailable.
· Full-telemetry confidence improves when Elastic correlates web logs, endpoint file telemetry, process telemetry, container telemetry, NDR data, DNS logs, egress telemetry, asset inventory, and patch context.
· Even under full telemetry conditions, this rule requires artifact review and supporting evidence before confirmed data-exposure classification.
Limitations
· This rule detects a suspicious model-ingestion and artifact sequence, not memory disclosure itself.
· Legitimate model imports, model refreshes, model pulls, backups, migrations, container workflows, developer testing, and approved automation may overlap with this pattern.
· The rule requires reliable host identity correlation between web and endpoint telemetry.
· Elastic can only correlate data that is ingested, normalized, and retained.
· Confirmation requires application activity review, endpoint artifact review, runtime context, outbound communication review, identity activity, and credential-management evidence.
Detection Query Pattern
Elastic EQL sequence pattern requiring ECS field, index, timing-window, asset, and file-path validation before production deployment.
sequence by host.id with maxspan=$ENV_MODEL_ACTIVITY_WINDOW
[network where
event.dataset in (
"nginx.access",
"apache.access",
"envoyproxy.access",
"aws.elb",
"cloudflare.logpush",
"httpjson",
"application"
)
and (
host.asset.role in (
"Ollama Server",
"Self-Hosted AI Model Server",
"AI Lab Server",
"Developer AI Infrastructure",
"Shared Model Infrastructure"
)
or service.name in (
"ollama",
"ai-model-server",
"model-serving-api"
)
or destination.port == 11434
)
and url.path in (
"/api/create",
"/api/blobs",
"/api/push"
)
]
[file where
event.action in (
"creation",
"modification",
"rename",
"attribute_change"
)
and (
process.name in (
"ollama",
"ollama.exe",
"docker",
"containerd",
"containerd-shim",
"runc",
"podman"
)
or file.path like "*/.ollama/models/*"
or file.path like "*/usr/share/ollama/*"
or file.path like "*/var/lib/ollama/*"
or file.path like "*\\.ollama\\models\\*"
or file.path like "*\\ProgramData\\Ollama\\*"
)
and (
file.extension in (
"gguf",
"manifest"
)
or file.path like "*blob*"
or file.path like "*modelfile*"
or file.size > $ENV_BASELINE_OLLAMA_ARTIFACT_SIZE
)
and not process.command_line in $APPROVED_OLLAMA_MODEL_WORKFLOWS
]
Rule 3
Ollama Host with Unusual Outbound Communication After Model Activity
Rule Format
Elastic EQL sequence detection pattern suitable for rule deployment after endpoint-network mapping validation, destination-baseline validation, DNS field validation, asset tagging, and environment-specific tuning.
Detection Purpose
· Detect unusual outbound communication from an Ollama host or workload after model-ingestion activity, model artifact changes, or Ollama process activity.
· Identify possible artifact transfer, attacker-directed outbound communication, or post-event data-exposure risk without claiming direct visibility into transmitted content.
· Prioritize destinations outside approved model-source, update, registry, automation, cloud storage, or administrative baselines.
· This rule does not determine transmitted content or confirm memory disclosure without supporting proxy, NDR, file, application, identity, or credential-management evidence.
Detection Logic
· Identify Ollama process activity, model artifact changes, or model-ingestion activity on a tagged Ollama host or workload.
· Identify outbound network connections from the same host, workload, or container to unfamiliar, rare, newly observed, unapproved, external, anonymous hosting, cloud storage, file-sharing, or unknown model-registry destinations.
· Increase confidence when outbound activity follows suspicious model artifact creation, runtime instability, untrusted inbound access, or unpatched exposure.
· Increase confidence when destination reputation is unknown, low-prevalence, suspicious, or outside approved egress baselines.
· Do not classify outbound activity as confirmed data theft without corroborating proxy, NDR, endpoint file, artifact, identity, or credential-management evidence.
Required Telemetry
· Elastic endpoint process telemetry.
· Endpoint network telemetry.
· DNS logs.
· Firewall or network flow logs where available.
· Proxy logs where available.
· Endpoint file telemetry.
· Container telemetry where available.
· Host identity.
· Container identity where available.
· Source process name.
· Destination IP address.
· Destination domain where available.
· Destination port.
· Destination reputation where available.
· Approved destination baseline.
· Asset role or host tag.
· Timestamp.
Engineering Implementation Instructions
· Validate Elastic index patterns and ECS mappings for endpoint process, endpoint network, DNS, firewall, proxy, file, and container telemetry.
· Scope the rule to assets tagged as Ollama servers, self-hosted AI model servers, AI lab systems, developer AI infrastructure, shared model infrastructure, or container hosts running Ollama.
· Establish approved model registries, update services, cloud destinations, automation systems, container registries, telemetry systems, and administrative destinations.
· Tune the rule to prioritize rare, newly observed, unapproved, low-prevalence, and external destinations rather than alerting on all Ollama network activity.
· Add exceptions for approved model pulls, approved model pushes, patching, backups, monitoring, container registry access, AI platform automation, and authorized developer workflows.
· Treat unusual outbound activity as higher priority when paired with model artifact writes, runtime instability, untrusted inbound access, unpatched status, or credential activity.
· Use NDR, proxy, application, file, SIEM, identity, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to unusual outbound communication from Ollama infrastructure after model-related activity.
· The rule remains useful if attacker infrastructure rotates, model names change, artifact names vary, or outbound timing changes.
· The score is supported by the durability of model-serving infrastructure communicating with unfamiliar destinations after suspicious host activity.
· The score is constrained by legitimate model downloads, model pushes, developer experimentation, registry synchronization, cloud storage access, and incomplete destination baselining.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on endpoint-network mapping, destination visibility, DNS telemetry, destination baselining, ECS mapping quality, host-role tagging, and container context.
· Operational confidence is reduced where endpoint telemetry lacks reliable destination domains, container process mapping, or approved outbound baselines.
· Full-telemetry confidence improves when Elastic telemetry is enriched with NDR data, proxy logs, DNS telemetry, application logs, model artifact activity, asset patch state, and identity activity.
· Even under full telemetry conditions, this rule should support escalation and investigation rather than standalone confirmation of data exposure.
Limitations
· This rule detects unusual outbound behavior from Ollama infrastructure, not the content of transmitted data.
· Legitimate model management, update workflows, telemetry agents, backups, testing, registry access, and cloud storage workflows may overlap with this behavior.
· The rule requires endpoint-network mapping, destination baselining, ECS field quality, endpoint coverage, and host-role scoping to remain reliable.
· Elastic may not determine whether outbound communication contains prompts, credentials, model artifacts, or other sensitive runtime content.
· Confirmation requires correlation with NDR telemetry, proxy records, application logs, file activity, model artifact review, identity activity, or credential-management evidence.
Detection Query Pattern
Elastic EQL sequence pattern requiring ECS field validation, destination-baseline validation, host-role tagging, process-to-network validation, and environment-specific tuning before production deployment.
sequence by host.id with maxspan=$ENV_MODEL_ACTIVITY_WINDOW
[any where
(
process.name in (
"ollama",
"ollama.exe",
"docker",
"containerd",
"containerd-shim",
"runc",
"podman"
)
or file.path like "*/.ollama/models/*"
or file.path like "*/usr/share/ollama/*"
or file.path like "*/var/lib/ollama/*"
or file.path like "*\\.ollama\\models\\*"
or file.path like "*\\ProgramData\\Ollama\\*"
or url.path in (
"/api/create",
"/api/blobs",
"/api/push"
)
)
and (
host.asset.role in (
"Ollama Server",
"Self-Hosted AI Model Server",
"AI Lab Server",
"Developer AI Infrastructure",
"Shared Model Infrastructure"
)
or service.name in (
"ollama",
"ai-model-server",
"model-serving-api"
)
)
]
[network where
event.action in (
"connection_attempted",
"connection_established",
"network_connection"
)
and (
destination.category in (
"newly_observed",
"rare",
"unapproved",
"external",
"anonymous_hosting",
"cloud_storage",
"file_sharing",
"unknown_model_registry"
)
or destination.domain not in $APPROVED_OLLAMA_DESTINATIONS
or destination.ip not in $APPROVED_OLLAMA_EGRESS_DESTINATIONS
or destination.reputation in (
"unknown",
"suspicious",
"low_prevalence"
)
)
and not destination.domain in $APPROVED_OLLAMA_DESTINATIONS
and not destination.ip in $APPROVED_OLLAMA_EGRESS_DESTINATIONS
]
QRadar
Detection Viability Assessment
QRadar has three rules for this EXP report.
· QRadar is viable for correlating suspicious Ollama access, exposed service context, model-ingestion activity, network flow behavior, endpoint or file telemetry, DNS activity, cloud activity, and identity or credential-management events where those sources are ingested.
· QRadar is strongest where offense rules can use normalized events, network flows, asset roles, vulnerability context, log source types, reference sets, building blocks, and custom properties for Ollama service identification.
· QRadar should not be treated as a standalone source for confirming memory disclosure unless the underlying log and flow sources support suspicious model-ingestion activity, artifact movement, unusual outbound communication, or downstream credential activity.
· QRadar is most valuable for offense-driven correlation across application logs, proxy logs, firewall logs, DNS logs, endpoint telemetry, asset inventory, vulnerability data, and identity sources.
Rule 1
Untrusted Source Access to Ollama Model-Ingestion Functionality
Rule Format
QRadar offense rule pattern suitable for custom rule deployment after log source validation, custom property extraction, reference set validation, asset tagging, vulnerability context validation, and approved-source tuning.
Detection Purpose
· Detect access to Ollama model-ingestion or model-transfer functionality from external, untrusted, newly observed, rare, or unapproved sources.
· Identify suspicious access to self-hosted AI model infrastructure without relying on exploit strings, public proof-of-concept artifacts, static payload names, or attacker infrastructure.
· Prioritize exposed Ollama services that receive model-ingestion activity from sources outside approved administrative paths.
· This rule does not confirm memory disclosure or successful exploitation without supporting endpoint, artifact, runtime, outbound, identity, or credential-management evidence.
Detection Logic
· Identify events from proxy, ingress, API gateway, load balancer, or application logs associated with Ollama infrastructure.
· Identify request paths associated with model-ingestion, blob, or model-transfer functionality where route-level telemetry is available.
· Identify source addresses, users, service accounts, or systems that are external, untrusted, newly observed, rare for the service, or outside approved administrative reference sets.
· Increase confidence when the destination asset is tagged as an Ollama server, self-hosted AI model server, AI lab host, developer AI infrastructure, shared model infrastructure, or containerized model-serving workload.
· Increase confidence when the destination asset is internet-facing, unpatched, newly exposed, broadly reachable, or associated with sensitive AI workflows.
· Do not classify the activity as confirmed compromise without corroborating endpoint, file, container, outbound flow, identity, or credential-management evidence.
Required Telemetry
· Proxy logs.
· Ingress logs.
· API gateway logs.
· Load balancer logs.
· Application access logs where available.
· QRadar network flow records.
· Source IP address.
· Destination IP address.
· Destination host.
· Request path custom property.
· Request method custom property where available.
· Response status where available.
· User agent where available.
· Authentication context where available.
· Asset role or host tag.
· Reference set for approved Ollama administrative sources.
· Reference set for approved AI platform services.
· Vulnerability or patch-state context where available.
· Timestamp.
Engineering Implementation Instructions
· Validate QRadar log source types, custom properties, event categories, and normalized fields for proxy, ingress, gateway, load balancer, and application logs before deployment.
· Create or validate reference sets for approved Ollama administrative sources, approved AI platform services, approved model automation, vulnerability scanners, and monitoring systems.
· Scope the rule to destination assets tagged as Ollama servers, self-hosted AI model servers, AI lab systems, developer AI infrastructure, shared model infrastructure, or containerized model-serving workloads.
· Use request-path custom properties only where the telemetry source provides reliable path visibility.
· Avoid alerting on all Ollama access. Require external, untrusted, newly observed, rare, or unapproved source context.
· Treat internet exposure, unpatched status, source novelty, repeated route access, large request size, or abnormal timing as prioritization context.
· Use endpoint, NDR, container, file, DNS, egress, identity, and credential-management telemetry as evidence before classifying the offense as confirmed compromise.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to untrusted access against exposed AI model infrastructure rather than brittle exploit artifacts.
· The rule remains useful if attacker infrastructure rotates, request timing varies, model names change, or public proof-of-concept details change.
· The score is supported by the durability of untrusted access to model-ingestion functionality as an observable control-plane signal.
· The score is constrained by environments without route-level logs, weak asset tagging, incomplete reference sets, or decentralized developer deployments.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on route-level logging, custom property quality, source classification, asset tagging, exposure context, vulnerability context, and approved-source reference sets.
· Operational confidence is reduced when Ollama is directly exposed without proxy logs, when developer systems are unmanaged, or when request-path fields are not extracted.
· Full-telemetry confidence improves when QRadar correlates application logs with network flows, endpoint telemetry, DNS activity, egress logs, vulnerability data, and identity events.
· Even under full telemetry conditions, this rule requires supporting evidence before confirmed compromise classification.
Limitations
· This rule detects suspicious access to Ollama model-ingestion functionality, not memory disclosure itself.
· Route-level visibility may be unavailable when Ollama is directly exposed or when request-path custom properties are not extracted.
· Legitimate model management, developer testing, approved automation, vulnerability scanning, and monitoring activity may overlap with this behavior.
· QRadar confidence depends heavily on custom property extraction, reference set quality, and asset-role accuracy.
· Confirmation requires correlation with model artifact activity, runtime instability, outbound communication, identity activity, credential-management activity, or other supporting evidence.
Detection Query Pattern
QRadar offense rule pattern requiring log source, custom property, asset, reference set, and vulnerability-context validation before production deployment.
WHEN events are detected by one or more of:
Proxy Logs
Ingress Logs
API Gateway Logs
Load Balancer Logs
Application Access Logs
AND when the destination asset role is one of:
Ollama Server
Self-Hosted AI Model Server
AI Lab Server
Developer AI Infrastructure
Shared Model Infrastructure
AND when any of the following are true:
destination port is 11434
destination service is ollama
service fingerprint is ollama
AND when request_path is one of:
/api/create
/api/blobs
/api/push
AND when any of the following are true:
source network is external
source classification is untrusted
source is newly observed for this service
source is rare for this destination
source is not in reference set Approved_Ollama_Admin_Sources
AND when source is not in reference set Approved_AI_Platform_Services
AND when source is not in reference set Approved_Model_Automation
AND when source is not in reference set Approved_Vulnerability_Scanners
AND when source is not in reference set Approved_Monitoring_Systems
THEN create an offense with the destination asset, source IP, request path, exposure context, patch context, and owner context.
Rule 2
Ollama Model-Ingestion Activity Followed by Unusual Outbound Flow
Rule Format
QRadar sequence-style offense rule pattern suitable for correlation after log source validation, network flow validation, custom property extraction, reference set validation, timing-window validation, and environment-specific tuning.
Detection Purpose
· Detect model-ingestion or model-transfer activity followed by unusual outbound network flow behavior from the same Ollama host or workload.
· Identify possible artifact transfer, attacker-directed outbound communication, or post-event data-exposure risk without claiming direct visibility into transmitted content.
· Prioritize destinations outside approved model-source, update, registry, automation, cloud storage, or administrative baselines.
· This rule does not determine transmitted content or confirm memory disclosure without supporting proxy, NDR, endpoint, file, application, identity, or credential-management evidence.
Detection Logic
· Identify Ollama model-ingestion or model-transfer events from application, proxy, ingress, gateway, or load balancer logs.
· Within a defined investigation window, identify outbound flows from the same destination asset, host, workload, or container host.
· Prioritize outbound flows to destinations classified as newly observed, rare, unapproved, external, anonymous hosting, cloud storage, file sharing, unknown model registry, low prevalence, or suspicious.
· Increase confidence when outbound bytes exceed the normal baseline for the Ollama host or when the destination is outside approved egress reference sets.
· Increase confidence when the sequence involves an untrusted inbound source, unpatched exposure, broadly reachable service, or sensitive AI workflow.
· Do not classify outbound activity as confirmed data theft without corroborating proxy, NDR, endpoint file, artifact, identity, or credential-management evidence.
Required Telemetry
· Proxy, ingress, gateway, load balancer, or application logs.
· QRadar network flow telemetry.
· DNS logs where available.
· Source IP address.
· Destination IP address.
· Destination host.
· Destination port.
· Request path custom property.
· Destination domain where available.
· Flow bytes.
· Flow direction.
· Destination classification or reputation where available.
· Asset role or host tag.
· Reference set for approved Ollama egress destinations.
· Reference set for approved model registries.
· Exposure context.
· Vulnerability or patch-state context where available.
· Timestamp.
Engineering Implementation Instructions
· Validate QRadar log sources, flow sources, normalized fields, custom properties, and timing behavior before deployment.
· Validate host identity correlation between application events and outbound network flows.
· Create or validate reference sets for approved model registries, approved Ollama egress destinations, approved cloud destinations, approved automation destinations, and known update paths.
· Tune the sequence window to the organization’s model-ingestion and model-management workflows.
· Add suppressions for approved model pulls, approved model pushes, patching, backups, monitoring, container registry access, AI platform automation, and authorized developer workflows.
· Treat unusual outbound flow as higher priority when paired with untrusted inbound access, unpatched exposure, model artifact activity, runtime instability, or credential activity.
· Use endpoint, application, NDR, proxy, file, SIEM, identity, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to suspicious sequencing between model-ingestion activity and unusual outbound flow behavior.
· The rule remains useful if attacker infrastructure rotates, request timing varies, model names change, or outbound destinations change.
· The score is supported by the durability of exposed model-serving infrastructure communicating with unfamiliar destinations after suspicious model activity.
· The score is constrained by legitimate model downloads, approved model pushes, registry synchronization, developer testing, and incomplete destination baselining.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on application event visibility, flow telemetry, host identity correlation, destination classification, egress baselining, asset tagging, and reference set quality.
· Operational confidence is reduced where flow telemetry lacks domain context, egress baselines are incomplete, or host identity joins are unreliable.
· Full-telemetry confidence improves when QRadar correlates application logs, network flows, DNS logs, endpoint telemetry, vulnerability context, asset inventory, and identity events.
· Even under full telemetry conditions, this rule supports escalation and investigation rather than standalone confirmation of data exposure.
Limitations
· This rule detects unusual outbound flow behavior following model activity, not the content of transmitted data.
· Legitimate model downloads, model pushes, development workflows, registry synchronization, cloud storage access, backups, and testing may overlap with this pattern.
· QRadar may not determine whether outbound traffic contains model artifacts, prompts, credentials, or other sensitive runtime content.
· The rule requires reliable flow data, custom properties, destination reference sets, and host identity correlation.
· Confirmation requires correlation with application logs, endpoint file activity, model artifact review, proxy records, identity activity, or credential-management evidence.
Detection Query Pattern
QRadar sequence-style offense rule pattern requiring log source, flow source, reference set, timing-window, and asset-correlation validation before production deployment.
WHEN an event is detected by one or more of:
Proxy Logs
Ingress Logs
API Gateway Logs
Load Balancer Logs
Application Access Logs
AND when the destination asset role is one of:
Ollama Server
Self-Hosted AI Model Server
AI Lab Server
Developer AI Infrastructure
Shared Model Infrastructure
AND when request_path is one of:
/api/create
/api/blobs
/api/push
FOLLOWED WITHIN ENV_MODEL_ACTIVITY_WINDOW BY
WHEN a network flow is observed where:
flow source asset equals the prior destination asset
AND when any of the following are true:
destination classification is newly observed
destination classification is rare
destination classification is unapproved
destination network is external
destination category is anonymous hosting
destination category is cloud storage
destination category is file sharing
destination category is unknown model registry
destination reputation is unknown
destination reputation is suspicious
destination reputation is low prevalence
outbound bytes exceed ENV_BASELINE_OLLAMA_EGRESS_BYTES
AND when destination is not in reference set Approved_Ollama_Egress_Destinations
AND when destination is not in reference set Approved_Model_Registries
THEN create an offense with the source asset, prior inbound source, outbound destination, request path, bytes transferred, exposure context, patch context, and owner context.
Rule 3
Unpatched Ollama Exposure with Suspicious Model Lifecycle and Identity Activity
Rule Format
QRadar offense correlation pattern suitable for rule deployment after asset inventory validation, vulnerability-data validation, identity-source validation, credential-management telemetry validation, reference set validation, and environment-specific tuning.
Detection Purpose
· Detect unpatched or exposed Ollama infrastructure with suspicious model lifecycle activity and downstream identity or credential-management anomalies.
· Identify cases where exposed AI infrastructure may have created downstream credential or access risk after suspicious model-ingestion activity.
· Prioritize response when technical exposure, suspicious service behavior, and post-event identity activity align.
· This rule does not prove credential theft or memory disclosure without supporting identity, credential, endpoint, application, or network evidence.
Detection Logic
· Identify Ollama infrastructure that is unpatched, internet-facing, broadly reachable, or located outside approved deployment inventory.
· Identify suspicious model lifecycle activity involving model ingestion, model import, model artifact changes, model push behavior, unusual outbound communication, or runtime instability.
· Identify downstream identity or credential-management activity after the exposure window, including unusual API token use, new access keys, abnormal cloud access, unfamiliar repository access, unusual service-account activity, or credential-management anomalies.
· Increase confidence when identity activity involves accounts, service accounts, tokens, hosts, or repositories associated with the Ollama environment.
· Increase confidence when identity or credential activity originates from unfamiliar infrastructure, unfamiliar geography, unfamiliar ASN, rare user-agent context, or unexpected automation context.
· Do not classify this activity as confirmed credential compromise without identity investigation and supporting evidence.
Required Telemetry
· QRadar asset inventory.
· Vulnerability or patch-state data.
· Exposure management data where available.
· Proxy, ingress, gateway, or application logs.
· Endpoint telemetry.
· File telemetry where available.
· Network flow logs.
· DNS logs.
· Identity provider logs.
· Cloud audit logs where applicable.
· Repository access logs where applicable.
· Credential-management activity logs where available.
· User, service-account, token, or key identifiers where available.
· Host identity.
· Reference sets for approved identities, service accounts, automation accounts, and administrative sources.
· Timestamp.
Engineering Implementation Instructions
· Validate QRadar asset inventory, vulnerability context, exposure context, identity sources, cloud audit logs, repository logs, and credential-management log sources before deployment.
· Create or validate reference sets for approved administrative identities, service accounts, automation accounts, CI/CD workflows, cloud administration sources, and repository automation.
· Scope identity or credential activity to events occurring after suspicious Ollama exposure or model lifecycle activity.
· Establish mappings between Ollama assets, owners, service accounts, repositories, cloud roles, and credential stores where available.
· Tune the post-exposure investigation window to organizational incident-response and credential-rotation requirements.
· Add suppressions for approved maintenance, approved key rotation, scheduled automation, known CI/CD workflows, approved repository automation, and approved cloud administration.
· Treat the rule as a high-priority offense, not as standalone proof of credential theft.
DRI Assessment
DRI
7.5 / 10
· The rule is behaviorally anchored to exposure, model lifecycle activity, and downstream credential or identity anomalies.
· The rule remains useful if attacker infrastructure changes, model artifact names vary, or model-ingestion details are only partially visible.
· The score is supported by the durability of downstream credential and identity review after suspected runtime exposure.
· The score is constrained by identity noise, normal key rotation, automation-heavy environments, incomplete credential-management logs, and weak asset-to-identity mapping.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
8.0 / 10
· Operational confidence depends on asset inventory quality, patch-state accuracy, identity telemetry, credential-management logs, cloud audit logs, repository logs, and host-to-identity mapping.
· Operational confidence is reduced when exposed Ollama hosts are not mapped to users, service accounts, repositories, cloud roles, or credential stores.
· Full-telemetry confidence improves when QRadar correlates exposure data, model lifecycle activity, endpoint telemetry, egress telemetry, identity provider logs, cloud audit logs, repository logs, and credential-management activity.
· Even under full telemetry conditions, this rule requires analyst review before confirmed credential compromise classification.
Limitations
· This rule detects suspicious downstream identity or credential activity after Ollama exposure, not memory disclosure itself.
· Legitimate key rotation, CI/CD automation, cloud administration, repository automation, and incident-response activity may overlap with this pattern.
· The rule requires reliable asset-to-identity mapping and credential-management telemetry to remain useful.
· Missing identity, cloud, repository, or credential-management logs can significantly reduce confidence.
· Confirmation requires credential review, identity investigation, artifact review, and incident timeline validation.
Detection Query Pattern
QRadar offense correlation pattern requiring asset, vulnerability, exposure, identity, cloud, repository, and credential-management validation before production deployment.
WHEN an asset is identified where:
asset role is one of:
Ollama Server
Self-Hosted AI Model Server
AI Lab Server
Developer AI Infrastructure
Shared Model Infrastructure
AND when any of the following are true:
patch status is unpatched
exposure status is internet facing
exposure status is broad internal access
exposure status is unapproved exposure
AND when an event or flow is observed involving the same asset where any of the following are true:
request_path is /api/create
request_path is /api/blobs
request_path is /api/push
file path contains /.ollama/models/
file path contains /var/lib/ollama/
process name is ollama
outbound destination is newly observed
outbound destination is rare
outbound destination is unapproved
outbound destination is external
FOLLOWED WITHIN ENV_POST_EXPOSURE_IDENTITY_REVIEW_WINDOW BY
WHEN identity, cloud, repository, or credential-management activity is observed where any of the following are true:
API token is used from rare source
access key is created
access key is used from unfamiliar source
service account is used from unusual context
credential is accessed
repository is accessed from unusual source
cloud API call is made from rare infrastructure
credential-management anomaly is generated
AND when the identity, service account, repository, token owner, or cloud account is associated with the exposed Ollama asset where mapping is available
THEN create an offense with the Ollama asset, identity, service account, exposure context, model lifecycle context, credential activity, and owner context.
SIGMA
Detection Viability Assessment
SIGMA has three rules for this EXP report.
· SIGMA is viable for expressing portable detection logic for Ollama-related web, endpoint file, process, and network events where the target SIEM can translate fields reliably.
· SIGMA is strongest where logs are normalized into consistent fields for HTTP request paths, source IPs, destination hosts, process names, file paths, network destinations, host roles, and approved-source exceptions.
· SIGMA should not be treated as a complete correlation layer by itself. Multi-stage correlation, host identity joins, baselining, and risk scoring should be implemented in the target SIEM after SIGMA translation.
· SIGMA is most valuable for portable rule logic that can be adapted into Splunk, Elastic, QRadar, or another SIEM without relying on exploit strings, static payload names, or public proof-of-concept artifacts.
Rule 1
Ollama Model-Ingestion Route Access from Untrusted Source
Rule Format
SIGMA rule pattern suitable for translation into SIEM-native logic after log-source validation, field mapping, approved-source baselining, asset tagging, and environment-specific tuning.
Detection Purpose
· Detect access to Ollama model-ingestion or model-transfer routes from external, untrusted, newly observed, rare, or unapproved sources.
· Provide portable detection logic for suspicious access to self-hosted AI model infrastructure.
· Prioritize Ollama services that receive model-ingestion activity from sources outside approved administrative paths.
· This rule does not confirm memory disclosure or successful exploitation without supporting endpoint, artifact, runtime, outbound, identity, or credential-management evidence.
Detection Logic
· Identify HTTP, reverse proxy, ingress, gateway, load balancer, or application events associated with Ollama infrastructure.
· Identify requests to model-ingestion, blob, or model-transfer routes where route-level telemetry is available.
· Identify source addresses or systems outside approved administrative baselines.
· Increase confidence when the destination host is tagged as an Ollama server, self-hosted AI model server, AI lab host, developer AI infrastructure, or shared model infrastructure.
· Increase confidence when the destination is internet-facing, unpatched, newly exposed, or broadly reachable.
· Do not classify the activity as confirmed compromise without corroborating endpoint, file, network, container, identity, or credential-management evidence.
Required Telemetry
· HTTP access logs.
· Reverse proxy logs.
· Ingress logs.
· API gateway logs.
· Load balancer logs.
· Application access logs where available.
· Source IP address.
· Destination host.
· Destination port.
· Request path.
· Request method.
· Response status where available.
· User agent where available.
· Asset role or host tag.
· Approved administrative source baseline.
· Timestamp.
Engineering Implementation Instructions
· Validate log source names, field names, and SIGMA-to-SIEM field mappings before deployment.
· Scope the translated rule to assets tagged as Ollama servers, self-hosted AI model servers, AI lab systems, developer AI infrastructure, or shared model infrastructure.
· Use request-path fields only where the telemetry source provides reliable route-level visibility.
· Add exceptions for approved administrative sources, approved AI platform services, approved model automation, vulnerability scanners, monitoring systems, and known testing networks.
· Avoid alerting on all Ollama access. Require untrusted, rare, external, newly observed, or unapproved source context.
· Use endpoint, file, egress, DNS, identity, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
7.5 / 10
· The rule is behaviorally anchored to suspicious access to model-ingestion routes rather than exploit-specific payloads.
· The rule remains useful if attacker infrastructure changes, model names vary, request timing shifts, or public proof-of-concept details change.
· The score is supported by the durability of untrusted access to model-ingestion functionality as a portable detection pattern.
· The score is constrained by field-mapping differences, missing route-level logs, incomplete source baselines, and variation across target SIEM backends.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
8.0 / 10
· Operational confidence depends on HTTP route visibility, field normalization, asset tagging, source classification, and approved-source exception quality.
· Operational confidence is reduced where SIGMA translation loses key fields or the SIEM lacks asset and source context.
· Full-telemetry confidence improves when the translated rule is enriched with endpoint telemetry, NDR data, DNS logs, egress telemetry, vulnerability context, and identity events.
· Even under full telemetry conditions, this rule requires supporting evidence before confirmed compromise classification.
Limitations
· This rule detects suspicious route access, not memory disclosure itself.
· SIGMA portability does not guarantee exact field availability in every SIEM.
· Route-level visibility may be unavailable when Ollama is directly exposed or logs are incomplete.
· Legitimate model management, developer testing, approved automation, scanning, and monitoring may overlap with this pattern.
· Confirmation requires correlation with model artifact activity, runtime instability, outbound communication, identity activity, or credential-management evidence.
Detection Query Pattern
SIGMA rule pattern requiring field mapping, log-source validation, asset-tag enrichment, and exception-list tuning before production deployment.
title: Ollama Model-Ingestion Route Access from Untrusted Source
id: 00000000-0000-4000-8000-ollama-sigma-001
status: experimental
description: Detects access to Ollama model-ingestion or model-transfer routes from untrusted or unapproved sources.
logsource:
category: webserver
detection:
selection_route:
url.path:
- '/api/create'
- '/api/blobs'
- '/api/push'
selection_service_port:
destination.port: 11434
selection_service_name:
service.name:
- 'ollama'
- 'ai-model-server'
- 'model-serving-api'
filter_approved_sources:
source.ip:
- '%APPROVED_OLLAMA_ADMIN_SOURCES%'
filter_approved_roles:
source.asset.role:
- 'Approved AI Platform Service'
- 'Approved Model Automation'
- 'Approved Vulnerability Scanner'
- 'Approved Monitoring System'
condition: selection_route and (selection_service_port or selection_service_name) and not 1 of filter_approved_*
fields:
- source.ip
- destination.ip
- destination.host
- destination.port
- url.path
- http.request.method
- http.response.status_code
- user_agent.original
falsepositives:
- Approved model-management automation.
- Approved administrative access.
- Vulnerability scanning.
- Monitoring workflows.
level: medium
Rule 2
Ollama Process Creates or Modifies Unusual Model Artifacts
Rule Format
SIGMA rule pattern suitable for translation into endpoint or SIEM detection logic after endpoint telemetry validation, file-path mapping, process-field validation, asset tagging, and model-storage tuning.
Detection Purpose
· Detect unusual model artifact creation, modification, rename, or attribute changes associated with Ollama or Ollama-hosted model infrastructure.
· Provide portable endpoint detection logic for suspicious model artifact handling.
· Prioritize file activity involving model storage paths, GGUF-related artifacts, manifests, blobs, temporary model components, or unusually large model files.
· This rule does not prove malicious model content or memory disclosure without supporting network, application, runtime, outbound, identity, or credential-management evidence.
Detection Logic
· Identify file creation, modification, rename, or attribute changes on hosts tagged as Ollama infrastructure.
· Prioritize file activity initiated by Ollama, container runtime processes associated with Ollama, or approved model-management service context.
· Identify model storage paths, blob paths, manifest files, GGUF-related files, or unusually large model artifacts.
· Increase confidence when file activity occurs outside approved administrative windows or after suspicious model-ingestion activity.
· Increase confidence when the Ollama host is exposed, unpatched, shared, or connected to sensitive AI workflows.
· Do not classify file activity as confirmed compromise without supporting network, application, outbound, identity, or artifact-review evidence.
Required Telemetry
· Endpoint file telemetry.
· Endpoint process telemetry.
· File creation events.
· File modification events.
· File rename events where available.
· Source process name.
· Source process path.
· Source process command line where available.
· Target file path.
· File extension.
· File size where available.
· Host identity.
· Host role or asset tag.
· Container context where available.
· Timestamp.
Engineering Implementation Instructions
· Validate SIGMA field mapping to endpoint telemetry in the target SIEM.
· Scope the translated rule to tagged Ollama servers, AI lab systems, developer AI infrastructure, shared model infrastructure, and container hosts running Ollama.
· Validate approved Ollama model storage paths, blob paths, manifest paths, container-mounted model volumes, and temporary directories.
· Tune file path and process filters to the organization’s Ollama deployment model.
· Add exceptions for approved model pulls, imports, refreshes, backups, migrations, AI platform automation, and authorized developer testing.
· Use application, network, proxy, container, SIEM, identity, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
7.5 / 10
· The rule is behaviorally anchored to model artifact activity rather than static exploit artifacts.
· The rule remains useful if attackers rename artifacts, vary file sizes, alter model names, or avoid public proof-of-concept naming conventions.
· The score is supported by the durability of model artifact creation and modification as observable host-level behavior.
· The score is constrained by legitimate model experimentation, approved imports, developer testing, incomplete file telemetry, and variation in endpoint field mapping.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
8.0 / 10
· Operational confidence depends on endpoint file telemetry, process lineage, file path normalization, asset tagging, model storage awareness, and exception quality.
· Operational confidence is reduced where endpoint telemetry does not map cleanly into SIGMA-compatible fields or where model storage paths are poorly documented.
· Full-telemetry confidence improves when the translated rule is enriched with model-ingestion context, proxy logs, NDR telemetry, egress behavior, runtime instability, and identity activity.
· Even under full telemetry conditions, unusual model artifact activity requires correlation before confirmed compromise classification.
Limitations
· This rule detects unusual model artifact activity, not memory disclosure itself.
· Legitimate model pulls, imports, refreshes, backups, migrations, testing, and approved automation may overlap with this behavior.
· SIGMA translation quality varies by backend and endpoint telemetry source.
· The rule requires file telemetry, process lineage, path awareness, endpoint coverage, and host-role scoping.
· Confirmation requires correlation with suspicious inbound access, runtime instability, unusual outbound communication, identity activity, credential-management activity, or artifact review.
Detection Query Pattern
SIGMA rule pattern requiring backend translation, endpoint-field validation, path tuning, and exception-list validation before production deployment.
title: Ollama Process Creates or Modifies Unusual Model Artifacts
id: 00000000-0000-4000-8000-ollama-sigma-002
status: experimental
description: Detects unusual model artifact creation or modification associated with Ollama infrastructure.
logsource:
category: file_event
detection:
selection_process:
process.name:
- 'ollama'
- 'ollama.exe'
- 'docker'
- 'containerd'
- 'containerd-shim'
- 'runc'
- 'podman'
selection_paths:
file.path|contains:
- '/.ollama/models/'
- '/usr/share/ollama/'
- '/var/lib/ollama/'
- '/opt/ollama/'
- '/models/'
- '/model-cache/'
- '\.ollama\models\'
- '\ProgramData\Ollama\'
selection_extensions:
file.extension:
- 'gguf'
- 'manifest'
selection_keywords:
file.path|contains:
- 'blob'
- 'manifest'
- 'models'
- 'modelfile'
filter_approved_workflows:
process.command_line|contains:
- 'approved_model_pull'
- 'approved_model_import'
- 'approved_model_refresh'
- 'approved_backup_workflow'
- 'approved_migration_workflow'
- 'approved_ai_platform_automation'
- 'approved_developer_test'
condition: selection_process and (selection_paths or selection_extensions or selection_keywords) and not filter_approved_workflows
fields:
- host.name
- process.name
- process.command_line
- file.path
- file.extension
- file.size
falsepositives:
- Approved model pulls.
- Approved model imports.
- Approved model refreshes.
- Backup or migration workflows.
- Authorized developer testing.
level: medium
Rule 3
Ollama Host Communicates with Unfamiliar External Destination After Model Activity
Rule Format
SIGMA rule pattern suitable for translation into SIEM or endpoint-network detection logic after network telemetry validation, destination-baseline mapping, asset tagging, and environment-specific tuning.
Detection Purpose
· Detect unusual outbound communication from an Ollama host or workload after model-related activity.
· Provide portable detection logic for possible artifact transfer, attacker-directed outbound communication, or post-event data-exposure risk.
· Prioritize outbound destinations outside approved model-source, registry, update, automation, cloud storage, or administrative baselines.
· This rule does not determine transmitted content or confirm memory disclosure without supporting proxy, NDR, endpoint file, application, identity, or credential-management evidence.
Detection Logic
· Identify outbound network connections from hosts tagged as Ollama infrastructure or from processes associated with Ollama.
· Identify destinations that are external, newly observed, rare, unapproved, low-prevalence, anonymous hosting, cloud storage, file-sharing, or unknown model-registry destinations.
· Increase confidence when outbound behavior occurs near model artifact creation, model-ingestion activity, runtime instability, or unpatched exposure.
· Increase confidence when the destination is outside approved egress or model-registry baselines.
· Do not classify outbound activity as confirmed data theft without corroborating proxy, NDR, file, application, identity, or credential-management evidence.
Required Telemetry
· Endpoint network telemetry.
· Firewall logs.
· Proxy logs where available.
· DNS logs where available.
· Source host.
· Source process name where available.
· Destination IP address.
· Destination domain where available.
· Destination port.
· Destination reputation where available.
· Destination category where available.
· Host role or asset tag.
· Approved destination baseline.
· Timestamp.
Engineering Implementation Instructions
· Validate SIGMA field mapping for network, proxy, DNS, and endpoint-network telemetry in the target backend.
· Scope translated detections to tagged Ollama servers, AI lab hosts, developer AI infrastructure, shared model infrastructure, and container hosts running Ollama.
· Establish approved model registries, update services, cloud destinations, automation services, container registries, monitoring destinations, and administrative destinations.
· Tune destination classification and exception logic for the target SIEM.
· Add exceptions for approved model pulls, approved model pushes, patching, backups, monitoring, container registry access, AI platform automation, and authorized developer workflows.
· Treat unusual outbound activity as higher priority when paired with model artifact activity, runtime instability, untrusted inbound access, unpatched status, or credential activity.
· Use NDR, proxy, application, file, identity, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
7.5 / 10
· The rule is behaviorally anchored to unusual outbound communication from Ollama infrastructure rather than static payload indicators.
· The rule remains useful if attacker infrastructure changes, model names vary, artifact names change, or outbound timing shifts.
· The score is supported by the durability of model-serving infrastructure communicating with unfamiliar destinations after suspicious host activity.
· The score is constrained by legitimate model downloads, model pushes, developer experimentation, registry synchronization, cloud storage access, and backend-specific correlation limits.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
8.0 / 10
· Operational confidence depends on network telemetry, destination classification, destination baselining, host-role tagging, process-to-network mapping, and exception quality.
· Operational confidence is reduced where destination classification is not available or SIGMA translation cannot preserve process-to-network context.
· Full-telemetry confidence improves when the translated rule is enriched with endpoint file activity, proxy logs, DNS logs, NDR telemetry, model-ingestion context, asset inventory, and identity activity.
· Even under full telemetry conditions, this rule should support escalation and investigation rather than standalone confirmation of data exposure.
Limitations
· This rule detects unusual outbound behavior, not transmitted content.
· Legitimate model management, update workflows, backups, testing, registry access, telemetry agents, and cloud storage workflows may overlap with this behavior.
· SIGMA translation quality varies by backend and available field mappings.
· This rule may require backend-specific correlation to enforce “after model activity” sequencing.
· Confirmation requires correlation with NDR telemetry, proxy records, application logs, file activity, model artifact review, identity activity, or credential-management evidence.
Detection Query Pattern
SIGMA rule pattern requiring backend translation, destination-baseline validation, process-to-network validation, and correlation tuning before production deployment.
title: Ollama Host Communicates with Unfamiliar External Destination After Model Activity
id: 00000000-0000-4000-8000-ollama-sigma-003
status: experimental
description: Detects unusual outbound communication from Ollama infrastructure or Ollama-associated processes. Backend-specific correlation should be used to tie this behavior to recent model activity.
logsource:
category: network_connection
detection:
selection_process:
process.name:
- 'ollama'
- 'ollama.exe'
- 'docker'
- 'containerd'
- 'containerd-shim'
- 'runc'
- 'podman'
selection_destination:
destination.category:
- 'newly_observed'
- 'rare'
- 'unapproved'
- 'external'
- 'anonymous_hosting'
- 'cloud_storage'
- 'file_sharing'
- 'unknown_model_registry'
selection_reputation:
destination.reputation:
- 'unknown'
- 'suspicious'
- 'low_prevalence'
filter_approved_destinations:
destination.domain:
- '%APPROVED_OLLAMA_DESTINATIONS%'
filter_approved_ips:
destination.ip:
- '%APPROVED_OLLAMA_EGRESS_DESTINATIONS%'
condition: selection_process and (selection_destination or selection_reputation) and not 1 of filter_approved_*
fields:
- host.name
- process.name
- process.command_line
- destination.ip
- destination.domain
- destination.port
- destination.category
- destination.reputation
falsepositives:
- Approved model pulls.
- Approved model pushes.
- Container registry access.
- Approved update workflows.
- Approved monitoring or telemetry agents.
- Authorized developer workflows.
level: medium
YARA
Detection Viability Assessment
YARA has zero rules for this EXP report.
· YARA is not viable as a primary detection-rule system for this report because the core detection problem is behavioral, not static-file or malware-signature based.
· The strongest detection logic depends on exposed service access, model-ingestion activity, model artifact handling, runtime instability, outbound communication, and downstream identity or credential activity.
· YARA is not suitable for confirming memory disclosure, exposed service access, route-level API activity, outbound communication, process instability, or downstream credential use.
· YARA rules against generic model files, GGUF-related content, or model artifact structure would create high false-positive risk because legitimate AI model artifacts may share similar file characteristics.
· YARA would also risk overfitting to public proof-of-concept artifacts, static strings, file names, or artifact structures that are not durable enough for reliable production detection.
Limited Operational Use
· YARA may be useful for controlled internal research against a known malicious artifact after an incident has produced a confirmed sample.
· YARA may support retrospective lab analysis of a specific artifact when the artifact has been validated as suspicious by endpoint, network, application, or forensic evidence.
· YARA should not be used as the primary S25 detection method for this report.
Final Outcome
No YARA rules survive.
AWS
Detection Viability Assessment
AWS has three rules for this EXP report.
· AWS is viable for detecting exposed Ollama infrastructure, permissive network paths, unusual workload egress, load balancer access patterns, cloud audit activity, IAM anomalies, and downstream credential or service-account activity where Ollama infrastructure runs in AWS.
· AWS is strongest where VPC Flow Logs, Elastic Load Balancing access logs, CloudTrail, GuardDuty, Security Hub, Route 53 Resolver query logs, AWS Config, Systems Manager inventory, ECR or container telemetry, and IAM activity are available.
· AWS should not be treated as a standalone source for confirming memory disclosure, model artifact content, or endpoint-level model-loader behavior unless the relevant workload, application, endpoint, or container telemetry is also collected.
· AWS is most valuable for identifying exposed cloud-hosted Ollama workloads, suspicious inbound access, unusual outbound destinations, and post-exposure IAM or credential activity.
Rule 1
AWS-Hosted Ollama Exposure to Untrusted Networks
Rule Format
AWS-native detection pattern suitable for Security Hub, CloudWatch, EventBridge, GuardDuty, AWS Config, or SIEM-forwarded detection after asset tagging, network exposure validation, log-source validation, and environment-specific tuning.
Detection Purpose
· Detect AWS-hosted Ollama infrastructure that is reachable from untrusted networks or the public internet.
· Identify cloud exposure conditions that increase the likelihood of suspicious model-ingestion activity against self-hosted AI model infrastructure.
· Prioritize EC2 instances, ECS tasks, EKS workloads, load balancers, or containerized model-serving workloads associated with Ollama service exposure.
· This rule does not confirm exploitation or memory disclosure without supporting access logs, endpoint telemetry, model artifact activity, outbound movement, identity activity, or credential-management evidence.
Detection Logic
· Identify AWS compute, container, or load-balanced workloads tagged as Ollama servers, self-hosted AI model servers, AI lab systems, developer AI infrastructure, or shared model infrastructure.
· Identify security groups, network ACLs, load balancers, public IP assignments, ingress rules, or exposed listeners that allow access to Ollama service ports or model-serving API paths from untrusted or public networks.
· Prioritize exposure where the workload is unpatched, unapproved, outside expected inventory, internet-facing, or associated with sensitive AI workflows.
· Increase confidence when exposed services receive inbound traffic from unfamiliar, external, newly observed, rare, or unapproved sources.
· Increase confidence when exposure is paired with route-level access to model-ingestion or model-transfer functionality through load balancer, proxy, or application logs.
· Do not classify exposure alone as compromise without suspicious access, model lifecycle activity, unusual egress, runtime instability, or downstream identity activity.
Required Telemetry
· AWS Config.
· Security group configuration.
· Network ACL configuration.
· Elastic Load Balancing access logs where available.
· VPC Flow Logs.
· CloudTrail.
· EC2, ECS, EKS, or container inventory.
· Public IP or internet-facing load balancer context.
· Asset tags.
· Workload owner context.
· Patch or vulnerability context where available.
· Approved administrative source baseline.
· Approved deployment inventory.
· Timestamp.
Engineering Implementation Instructions
· Validate asset tagging for EC2 instances, ECS services, EKS workloads, load balancers, and container hosts associated with Ollama infrastructure.
· Validate which ports, listeners, paths, and services are approved for Ollama or model-serving access.
· Use AWS Config, Security Hub, CloudTrail, VPC Flow Logs, and load balancer logs to identify exposure and inbound access context.
· Scope the rule to workloads tagged as Ollama servers, self-hosted AI model servers, AI lab systems, developer AI infrastructure, or shared model infrastructure.
· Add exceptions for approved private subnets, approved internal load balancers, approved administrative sources, approved AI platform services, vulnerability scanners, and monitoring systems.
· Treat exposure as higher priority when paired with unpatched status, unfamiliar inbound sources, unusual request timing, model-ingestion activity, or abnormal egress.
· Use endpoint, container, application, NDR, SIEM, identity, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to cloud exposure and suspicious access conditions rather than exploit-specific payloads.
· The rule remains useful if attacker infrastructure changes, model names vary, request timing shifts, or public proof-of-concept details change.
· The score is supported by the durability of identifying exposed AWS-hosted AI model infrastructure as a high-value risk condition.
· The score is constrained by incomplete asset tagging, unmanaged cloud deployments, missing load balancer logs, incomplete patch context, and legitimate development exposure patterns.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on AWS Config coverage, VPC Flow Log availability, load balancer logging, asset tagging, security group visibility, patch context, and approved-source baselining.
· Operational confidence is reduced where Ollama workloads are temporary, untagged, deployed outside approved accounts, or directly exposed without consistent application logging.
· Full-telemetry confidence improves when AWS telemetry is enriched with endpoint telemetry, container logs, proxy logs, NDR data, application logs, vulnerability data, and identity activity.
· Even under full telemetry conditions, exposure should be treated as a high-priority risk condition, not confirmed compromise by itself.
Limitations
· This rule detects exposed AWS-hosted Ollama infrastructure, not memory disclosure itself.
· Public exposure, security group misconfiguration, or unapproved listeners do not prove exploitation.
· Legitimate lab testing, developer access, vulnerability scanning, approved temporary exposure, and internal AI workflows may overlap with this behavior.
· AWS telemetry may not provide route-level model-ingestion visibility unless load balancer, proxy, or application logs are enabled.
· Confirmation requires correlation with suspicious inbound access, model lifecycle activity, endpoint artifact changes, unusual outbound communication, identity activity, or credential-management evidence.
Detection Query Pattern
AWS-native detection pattern requiring account, region, tag, Config, flow, and load balancer log validation before production deployment.
AWS_CONFIG_RESOURCE_TYPE IN (
"AWS::EC2::Instance",
"AWS::ECS::Service",
"AWS::EKS::Cluster",
"AWS::ElasticLoadBalancingV2::LoadBalancer",
"AWS::EC2::SecurityGroup"
)
AND RESOURCE_TAGS CONTAINS ANY (
"Ollama Server",
"Self-Hosted AI Model Server",
"AI Lab Server",
"Developer AI Infrastructure",
"Shared Model Infrastructure"
)
AND (
SECURITY_GROUP_INGRESS_CIDR IN (
"0.0.0.0/0",
"::/0"
)
OR LOAD_BALANCER_SCHEME = "internet-facing"
OR PUBLIC_IP_ASSIGNED = true
)
AND (
EXPOSED_PORT IN (
11434,
APPROVED_OLLAMA_PORTS
)
OR SERVICE_NAME IN (
"ollama",
"ai-model-server",
"model-serving-api"
)
)
AND NOT SOURCE_CIDR IN APPROVED_OLLAMA_ADMIN_SOURCES
AND NOT RESOURCE_ID IN APPROVED_PUBLIC_OLLAMA_DEPLOYMENTS
Rule 2
AWS Ollama Workload with Unusual Egress After Model Activity
Rule Format
AWS-native sequence detection pattern suitable for CloudWatch, EventBridge, GuardDuty enrichment, Security Lake, or SIEM-forwarded detection after VPC Flow Log validation, DNS visibility validation, workload identity mapping, destination baselining, and timing-window tuning.
Detection Purpose
· Detect unusual outbound communication from an AWS-hosted Ollama workload after model-ingestion activity, model artifact activity, or suspicious inbound access.
· Identify possible artifact transfer, attacker-directed outbound communication, or post-event data-exposure risk without claiming direct visibility into transmitted content.
· Prioritize destinations outside approved model-source, update, registry, automation, cloud storage, or administrative baselines.
· This rule does not determine transmitted content or confirm memory disclosure without supporting proxy, endpoint, container, application, artifact, identity, or credential-management evidence.
Detection Logic
· Identify AWS-hosted Ollama workloads using EC2, ECS, EKS, load balancer, container, or asset tags.
· Identify model-ingestion activity, model-transfer activity, suspicious inbound access, or model-related application behavior where route-level logs are available.
· Within a defined investigation window, identify outbound traffic from the same workload, instance, task, pod, or container host to unfamiliar, rare, newly observed, unapproved, external, anonymous hosting, cloud storage, file-sharing, or unknown model-registry destinations.
· Increase confidence when outbound bytes exceed the normal baseline for the workload or when DNS activity resolves unfamiliar destinations after model activity.
· Increase confidence when the workload is unpatched, internet-facing, broadly reachable, or outside approved deployment inventory.
· Do not classify outbound activity as confirmed data theft without corroborating application, endpoint, container, artifact, proxy, identity, or credential-management evidence.
Required Telemetry
· VPC Flow Logs.
· Route 53 Resolver query logs where available.
· Elastic Load Balancing access logs where available.
· CloudTrail.
· EC2, ECS, EKS, or container workload inventory.
· Host, instance, task, pod, or container identity.
· Source and destination IP addresses.
· Destination domain where available.
· Destination port.
· Flow bytes.
· Flow direction.
· Destination classification or reputation where available.
· Approved egress destination baseline.
· Approved model registry baseline.
· Asset tags.
· Exposure context.
· Patch or vulnerability context where available.
· Timestamp.
Engineering Implementation Instructions
· Validate VPC Flow Logs, Route 53 Resolver query logs, load balancer logs, CloudTrail, and workload inventory coverage before deployment.
· Map Ollama workloads across EC2 instances, ECS tasks, EKS workloads, load balancers, and container hosts.
· Establish approved model registries, approved update destinations, approved cloud destinations, approved AI platform automation, approved container registries, and known monitoring destinations.
· Tune the sequence window to the organization’s model-ingestion, model-management, and cloud egress patterns.
· Add exceptions for approved model pulls, approved model pushes, patching, backups, monitoring, container registry access, telemetry agents, AI platform automation, and authorized developer workflows.
· Treat unusual egress as higher priority when paired with untrusted inbound access, unpatched exposure, model artifact activity, runtime instability, or identity activity.
· Use endpoint, application, proxy, NDR, container, SIEM, identity, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to unusual AWS workload egress after model-related activity.
· The rule remains useful if attacker infrastructure changes, model names vary, artifact names change, or outbound timing shifts.
· The score is supported by the durability of exposed model-serving workloads communicating with unfamiliar destinations after suspicious activity.
· The score is constrained by legitimate model downloads, model pushes, registry synchronization, cloud storage access, backups, and incomplete egress baselining.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on VPC Flow Logs, DNS visibility, workload identity mapping, egress baselining, destination classification, asset tagging, and load balancer or application context.
· Operational confidence is reduced where flow logs are incomplete, DNS visibility is missing, egress destinations are not baselined, or workload identity mapping is unreliable.
· Full-telemetry confidence improves when AWS telemetry is enriched with endpoint telemetry, application logs, container logs, proxy logs, NDR telemetry, file activity, vulnerability data, and identity activity.
· Even under full telemetry conditions, this rule supports escalation and investigation rather than standalone confirmation of data exposure.
Limitations
· This rule detects unusual outbound behavior from AWS-hosted Ollama infrastructure, not transmitted content.
· Legitimate model management, update workflows, telemetry agents, backups, testing, registry access, and cloud storage workflows may overlap with this behavior.
· AWS network telemetry may not identify model artifacts, prompts, credentials, or other sensitive runtime content.
· Route-level model-ingestion visibility requires load balancer, proxy, application, or container logs.
· Confirmation requires correlation with application logs, endpoint file activity, container telemetry, model artifact review, identity activity, or credential-management evidence.
Detection Query Pattern
AWS-native sequence pattern requiring VPC Flow Log, DNS, workload mapping, destination-baseline, and timing-window validation before production deployment.
SEQUENCE WITHIN ENV_MODEL_ACTIVITY_WINDOW
STEP 1:
AWS_WORKLOAD_TAGS CONTAINS ANY (
"Ollama Server",
"Self-Hosted AI Model Server",
"AI Lab Server",
"Developer AI Infrastructure",
"Shared Model Infrastructure"
)
AND (
ELB_REQUEST_PATH IN (
"/api/create",
"/api/blobs",
"/api/push"
)
OR APPLICATION_ROUTE IN (
"/api/create",
"/api/blobs",
"/api/push"
)
OR INBOUND_SOURCE_CLASS IN (
"external",
"untrusted",
"newly_observed",
"rare",
"unapproved_internal"
)
OR MODEL_ACTIVITY_CONTEXT = "model_ingestion"
)
FOLLOWED BY STEP 2:
AWS_WORKLOAD_ID = STEP_1.AWS_WORKLOAD_ID
AND FLOW_DIRECTION = "egress"
AND (
DESTINATION_CLASS IN (
"newly_observed",
"rare",
"unapproved",
"external",
"anonymous_hosting",
"cloud_storage",
"file_sharing",
"unknown_model_registry"
)
OR DESTINATION_DOMAIN NOT IN APPROVED_OLLAMA_DESTINATIONS
OR DESTINATION_IP NOT IN APPROVED_OLLAMA_EGRESS_DESTINATIONS
OR BYTES_OUT > ENV_BASELINE_OLLAMA_EGRESS_BYTES
)
AND NOT DESTINATION_DOMAIN IN APPROVED_OLLAMA_DESTINATIONS
AND NOT DESTINATION_IP IN APPROVED_OLLAMA_EGRESS_DESTINATIONS
Rule 3
AWS Identity or Credential Activity Following Suspicious Ollama Exposure Window
Rule Format
AWS-native identity and audit correlation pattern suitable for CloudTrail, IAM Access Analyzer, GuardDuty, Security Hub, EventBridge, or SIEM-forwarded detection after identity-source validation, asset-to-identity mapping, credential-baseline validation, and environment-specific tuning.
Detection Purpose
· Detect suspicious IAM, access key, role, service-account, repository, or cloud API activity after suspicious AWS-hosted Ollama exposure or model lifecycle activity.
· Identify downstream credential or access risk when exposed AI infrastructure may have processed sensitive runtime context.
· Prioritize cases where suspicious Ollama exposure aligns with unusual identity activity from unfamiliar sources, roles, accounts, regions, user agents, or automation contexts.
· This rule does not prove credential theft or memory disclosure without supporting identity investigation, endpoint evidence, application evidence, or credential-management evidence.
Detection Logic
· Identify AWS-hosted Ollama infrastructure that is unpatched, exposed, broadly reachable, or associated with suspicious model-ingestion or model lifecycle activity.
· Identify IAM, CloudTrail, access key, role assumption, service account, or cloud API activity occurring after the suspicious exposure window.
· Prioritize events involving new access keys, unusual access key use, rare role assumption, service-account activity from unusual infrastructure, cloud API calls from unfamiliar locations, unusual user agents, or access to resources associated with the Ollama workload.
· Increase confidence when the identity, role, access key, repository, secret, or cloud account is mapped to the Ollama workload or its owner.
· Increase confidence when activity originates from unfamiliar geography, unfamiliar ASN, rare user-agent context, unexpected automation, or newly observed source infrastructure.
· Do not classify this activity as confirmed credential compromise without analyst review and supporting evidence.
Required Telemetry
· CloudTrail.
· IAM activity logs.
· GuardDuty findings where available.
· Security Hub findings where available.
· IAM Access Analyzer where available.
· AWS Config.
· Access key creation and use events.
· Role assumption events.
· Service account or workload identity context.
· Source IP address.
· User agent.
· AWS region.
· Account ID.
· Resource identity.
· Ollama workload owner mapping.
· Asset-to-identity mapping.
· Credential-management activity logs where available.
· Timestamp.
Engineering Implementation Instructions
· Validate CloudTrail coverage across relevant accounts and regions.
· Validate GuardDuty, Security Hub, IAM Access Analyzer, AWS Config, and credential-management telemetry sources before deployment.
· Establish mappings between Ollama workloads, owners, IAM roles, service accounts, repositories, secrets, and cloud accounts where available.
· Tune the post-exposure review window to the organization’s incident-response and credential-rotation requirements.
· Add exceptions for approved key rotation, scheduled automation, approved CI/CD workflows, approved administrative activity, approved repository automation, and approved cloud operations.
· Treat the rule as high priority when identity activity follows untrusted inbound access, model-ingestion activity, unusual egress, runtime instability, or unpatched exposure.
· Use endpoint, application, proxy, container, NDR, SIEM, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
7.5 / 10
· The rule is behaviorally anchored to downstream IAM and credential activity after suspicious Ollama exposure.
· The rule remains useful if model artifact names change, attacker infrastructure rotates, or model-ingestion details are only partially visible.
· The score is supported by the durability of reviewing cloud identity activity after suspected runtime exposure.
· The score is constrained by identity noise, normal key rotation, automation-heavy environments, incomplete asset-to-identity mapping, and missing credential-management telemetry.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on CloudTrail coverage, IAM event fidelity, GuardDuty or Security Hub context, asset-to-identity mapping, owner mapping, credential-management telemetry, and post-exposure timing.
· Operational confidence is reduced where AWS accounts are fragmented, CloudTrail is incomplete, workload identities are not mapped, or automation creates frequent identity changes.
· Full-telemetry confidence improves when AWS identity telemetry is enriched with application logs, endpoint telemetry, egress telemetry, asset inventory, repository logs, credential-management activity, and incident timeline context.
· Even under full telemetry conditions, this rule requires analyst review before confirmed credential compromise classification.
Limitations
· This rule detects suspicious downstream AWS identity or credential activity after Ollama exposure, not memory disclosure itself.
· Legitimate key rotation, CI/CD automation, cloud administration, incident-response actions, and repository automation may overlap with this pattern.
· The rule requires reliable mapping between Ollama workloads, owners, IAM roles, service accounts, and credentials.
· Missing CloudTrail, GuardDuty, Security Hub, repository, or credential-management telemetry can reduce confidence.
· Confirmation requires credential review, identity investigation, artifact review, application context, and incident timeline validation.
Detection Query Pattern
AWS-native identity correlation pattern requiring CloudTrail, IAM, account, region, asset-to-identity, and timing-window validation before production deployment.
SEQUENCE WITHIN ENV_POST_EXPOSURE_IDENTITY_REVIEW_WINDOW
STEP 1:
AWS_WORKLOAD_TAGS CONTAINS ANY (
"Ollama Server",
"Self-Hosted AI Model Server",
"AI Lab Server",
"Developer AI Infrastructure",
"Shared Model Infrastructure"
)
AND (
EXPOSURE_STATUS IN (
"internet_facing",
"broad_internal_access",
"unapproved_exposure"
)
OR PATCH_STATUS = "unpatched"
OR MODEL_ACTIVITY_CONTEXT IN (
"model_ingestion",
"model_artifact_activity",
"unusual_egress",
"runtime_instability"
)
)
FOLLOWED BY STEP 2:
AWS_IDENTITY_EVENT IN (
"CreateAccessKey",
"UpdateAccessKey",
"AssumeRole",
"GetSecretValue",
"GetParameter",
"Decrypt",
"ConsoleLogin",
"CreateLoginProfile",
"AttachUserPolicy",
"PutUserPolicy",
"CreateServiceSpecificCredential"
)
AND (
IDENTITY_SOURCE_CLASS IN (
"newly_observed",
"rare",
"unapproved",
"external",
"unfamiliar_geo",
"unfamiliar_asn",
"unusual_user_agent"
)
OR ROLE_OR_KEY_OWNER IN STEP_1.RELATED_IDENTITIES
OR RESOURCE_ACCOUNT IN STEP_1.RELATED_AWS_ACCOUNTS
)
AND NOT IDENTITY IN APPROVED_CLOUD_ADMIN_IDENTITIES
AND NOT EVENT_CONTEXT IN APPROVED_KEY_ROTATION_OR_AUTOMATION
Azure
Detection Viability Assessment
AZURE has three rules for this EXP report.
· Azure is viable for detecting exposed Ollama infrastructure, permissive network paths, suspicious inbound access, unusual outbound communication, workload identity activity, cloud audit activity, and downstream credential or service-principal anomalies where Ollama infrastructure runs in Azure.
· Azure is strongest where Azure Activity Logs, Microsoft Entra ID logs, NSG Flow Logs, Azure Firewall logs, Application Gateway or Front Door logs, Defender for Cloud, Azure Resource Graph, VM inventory, container telemetry, and Key Vault or credential-management telemetry are available.
· Azure should not be treated as a standalone source for confirming memory disclosure, model artifact content, or endpoint-level model-loader behavior unless the relevant workload, endpoint, application, or container telemetry is also collected.
· Azure is most valuable for identifying exposed Azure-hosted Ollama workloads, suspicious inbound access, unusual outbound destinations, and post-exposure identity or credential activity.
Rule 1
Azure-Hosted Ollama Exposure to Untrusted Networks
Rule Format
Azure-native detection pattern suitable for Microsoft Sentinel, Defender for Cloud, Azure Monitor, Azure Resource Graph, or SIEM-forwarded detection after subscription validation, resource tagging, network exposure validation, log-source validation, and environment-specific tuning.
Detection Purpose
· Detect Azure-hosted Ollama infrastructure that is reachable from untrusted networks or the public internet.
· Identify cloud exposure conditions that increase the likelihood of suspicious model-ingestion activity against self-hosted AI model infrastructure.
· Prioritize Azure VMs, VM scale sets, AKS workloads, container workloads, Application Gateway deployments, public load balancers, or model-serving infrastructure associated with Ollama service exposure.
· This rule does not confirm exploitation or memory disclosure without supporting access logs, endpoint telemetry, model artifact activity, outbound movement, identity activity, or credential-management evidence.
Detection Logic
· Identify Azure compute, container, AKS, or load-balanced workloads tagged as Ollama servers, self-hosted AI model servers, AI lab systems, developer AI infrastructure, or shared model infrastructure.
· Identify network security groups, Azure Firewall rules, public IP assignments, public load balancers, Application Gateway listeners, Front Door routes, or exposed service paths that allow access to Ollama service ports or model-serving API paths from untrusted or public networks.
· Prioritize exposure where the workload is unpatched, unapproved, outside expected inventory, internet-facing, or associated with sensitive AI workflows.
· Increase confidence when exposed services receive inbound traffic from unfamiliar, external, newly observed, rare, or unapproved sources.
· Increase confidence when exposure is paired with route-level access to model-ingestion or model-transfer functionality through Application Gateway, Front Door, proxy, ingress, or application logs.
· Do not classify exposure alone as compromise without suspicious access, model lifecycle activity, unusual egress, runtime instability, or downstream identity activity.
Required Telemetry
· Azure Activity Logs.
· Azure Resource Graph.
· Network Security Group configuration.
· Azure Firewall configuration where available.
· Public IP assignment data.
· Application Gateway logs where available.
· Azure Front Door logs where available.
· Load balancer or ingress logs where available.
· NSG Flow Logs.
· Defender for Cloud findings where available.
· VM, AKS, container, or workload inventory.
· Asset tags.
· Workload owner context.
· Patch or vulnerability context where available.
· Approved administrative source baseline.
· Approved deployment inventory.
· Timestamp.
Engineering Implementation Instructions
· Validate resource tagging for Azure VMs, VM scale sets, AKS clusters, container workloads, load balancers, Application Gateways, Front Door profiles, and container hosts associated with Ollama infrastructure.
· Validate which ports, listeners, paths, and services are approved for Ollama or model-serving access.
· Use Azure Resource Graph, Azure Activity Logs, Defender for Cloud, NSG Flow Logs, Azure Firewall logs, and Application Gateway or Front Door logs to identify exposure and inbound access context.
· Scope the rule to workloads tagged as Ollama servers, self-hosted AI model servers, AI lab systems, developer AI infrastructure, or shared model infrastructure.
· Add exceptions for approved private subnets, approved internal load balancers, approved administrative sources, approved AI platform services, vulnerability scanners, and monitoring systems.
· Treat exposure as higher priority when paired with unpatched status, unfamiliar inbound sources, unusual request timing, model-ingestion activity, or abnormal egress.
· Use endpoint, container, application, NDR, SIEM, identity, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to Azure cloud exposure and suspicious access conditions rather than exploit-specific payloads.
· The rule remains useful if attacker infrastructure changes, model names vary, request timing shifts, or public proof-of-concept details change.
· The score is supported by the durability of identifying exposed Azure-hosted AI model infrastructure as a high-value risk condition.
· The score is constrained by incomplete asset tagging, unmanaged cloud deployments, missing Application Gateway or Front Door logs, incomplete patch context, and legitimate development exposure patterns.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on Azure Resource Graph coverage, NSG Flow Log availability, Application Gateway or Front Door logging, asset tagging, network security group visibility, patch context, and approved-source baselining.
· Operational confidence is reduced where Ollama workloads are temporary, untagged, deployed outside approved subscriptions, or directly exposed without consistent application logging.
· Full-telemetry confidence improves when Azure telemetry is enriched with endpoint telemetry, container logs, proxy logs, NDR data, application logs, vulnerability data, and identity activity.
· Even under full telemetry conditions, exposure should be treated as a high-priority risk condition, not confirmed compromise by itself.
Limitations
· This rule detects exposed Azure-hosted Ollama infrastructure, not memory disclosure itself.
· Public exposure, permissive network security rules, or unapproved listeners do not prove exploitation.
· Legitimate lab testing, developer access, vulnerability scanning, approved temporary exposure, and internal AI workflows may overlap with this behavior.
· Azure telemetry may not provide route-level model-ingestion visibility unless Application Gateway, Front Door, proxy, ingress, or application logs are enabled.
· Confirmation requires correlation with suspicious inbound access, model lifecycle activity, endpoint artifact changes, unusual outbound communication, identity activity, or credential-management evidence.
Detection Query Pattern
Azure-native detection pattern requiring subscription, resource group, tag, network security, flow, and Application Gateway or Front Door log validation before production deployment.
AZURE_RESOURCE_TYPE IN (
"Microsoft.Compute/virtualMachines",
"Microsoft.Compute/virtualMachineScaleSets",
"Microsoft.ContainerService/managedClusters",
"Microsoft.ContainerInstance/containerGroups",
"Microsoft.Network/loadBalancers",
"Microsoft.Network/applicationGateways",
"Microsoft.Cdn/profiles",
"Microsoft.Network/networkSecurityGroups",
"Microsoft.Network/publicIPAddresses"
)
AND RESOURCE_TAGS CONTAINS ANY (
"Ollama Server",
"Self-Hosted AI Model Server",
"AI Lab Server",
"Developer AI Infrastructure",
"Shared Model Infrastructure"
)
AND (
NSG_INBOUND_SOURCE IN (
"0.0.0.0/0",
"::/0",
"Internet"
)
OR PUBLIC_IP_ASSIGNED = true
OR LOAD_BALANCER_SCHEME = "public"
OR APPLICATION_GATEWAY_PUBLIC_LISTENER = true
OR FRONT_DOOR_PUBLIC_ROUTE = true
)
AND (
EXPOSED_PORT IN (
11434,
APPROVED_OLLAMA_PORTS
)
OR SERVICE_NAME IN (
"ollama",
"ai-model-server",
"model-serving-api"
)
)
AND NOT SOURCE_CIDR IN APPROVED_OLLAMA_ADMIN_SOURCES
AND NOT RESOURCE_ID IN APPROVED_PUBLIC_OLLAMA_DEPLOYMENTS
Rule 2
Azure Ollama Workload with Unusual Outbound Communication After Model Activity
Rule Format
Azure-native sequence detection pattern suitable for Microsoft Sentinel, Azure Monitor, Defender for Cloud enrichment, or SIEM-forwarded detection after NSG Flow Log validation, DNS visibility validation, workload identity mapping, destination baselining, and timing-window tuning.
Detection Purpose
· Detect unusual outbound communication from an Azure-hosted Ollama workload after model-ingestion activity, model artifact activity, or suspicious inbound access.
· Identify possible artifact transfer, attacker-directed outbound communication, or post-event data-exposure risk without claiming direct visibility into transmitted content.
· Prioritize destinations outside approved model-source, update, registry, automation, cloud storage, or administrative baselines.
· This rule does not determine transmitted content or confirm memory disclosure without supporting proxy, endpoint, container, application, artifact, identity, or credential-management evidence.
Detection Logic
· Identify Azure-hosted Ollama workloads using VM, VM scale set, AKS, container, load balancer, Application Gateway, Front Door, or asset tags.
· Identify model-ingestion activity, model-transfer activity, suspicious inbound access, or model-related application behavior where route-level logs are available.
· Within a defined investigation window, identify outbound traffic from the same workload, VM, pod, container, or container host to unfamiliar, rare, newly observed, unapproved, external, anonymous hosting, cloud storage, file-sharing, or unknown model-registry destinations.
· Increase confidence when outbound bytes exceed the normal baseline for the workload or when DNS activity resolves unfamiliar destinations after model activity.
· Increase confidence when the workload is unpatched, internet-facing, broadly reachable, or outside approved deployment inventory.
· Do not classify outbound activity as confirmed data theft without corroborating application, endpoint, container, artifact, proxy, identity, or credential-management evidence.
Required Telemetry
· NSG Flow Logs.
· Azure Firewall logs where available.
· Azure DNS or DNS proxy logs where available.
· Application Gateway logs where available.
· Azure Front Door logs where available.
· Azure Activity Logs.
· VM, AKS, container, or workload inventory.
· Host, VM, pod, workload, or container identity.
· Source and destination IP addresses.
· Destination domain where available.
· Destination port.
· Flow bytes.
· Flow direction.
· Destination classification or reputation where available.
· Approved egress destination baseline.
· Approved model registry baseline.
· Asset tags.
· Exposure context.
· Patch or vulnerability context where available.
· Timestamp.
Engineering Implementation Instructions
· Validate NSG Flow Logs, Azure Firewall logs, DNS telemetry, Application Gateway logs, Front Door logs, Azure Activity Logs, and workload inventory coverage before deployment.
· Map Ollama workloads across Azure VMs, VM scale sets, AKS workloads, container workloads, load balancers, Application Gateways, Front Door routes, and container hosts.
· Establish approved model registries, approved update destinations, approved cloud destinations, approved AI platform automation, approved container registries, and known monitoring destinations.
· Tune the sequence window to the organization’s model-ingestion, model-management, and cloud egress patterns.
· Add exceptions for approved model pulls, approved model pushes, patching, backups, monitoring, container registry access, telemetry agents, AI platform automation, and authorized developer workflows.
· Treat unusual egress as higher priority when paired with untrusted inbound access, unpatched exposure, model artifact activity, runtime instability, or identity activity.
· Use endpoint, application, proxy, NDR, container, SIEM, identity, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to unusual Azure workload egress after model-related activity.
· The rule remains useful if attacker infrastructure changes, model names vary, artifact names change, or outbound timing shifts.
· The score is supported by the durability of exposed model-serving workloads communicating with unfamiliar destinations after suspicious activity.
· The score is constrained by legitimate model downloads, model pushes, registry synchronization, cloud storage access, backups, and incomplete egress baselining.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on NSG Flow Logs, DNS visibility, workload identity mapping, egress baselining, destination classification, asset tagging, and Application Gateway, Front Door, or application context.
· Operational confidence is reduced where flow logs are incomplete, DNS visibility is missing, egress destinations are not baselined, or workload identity mapping is unreliable.
· Full-telemetry confidence improves when Azure telemetry is enriched with endpoint telemetry, application logs, container logs, proxy logs, NDR telemetry, file activity, vulnerability data, and identity activity.
· Even under full telemetry conditions, this rule supports escalation and investigation rather than standalone confirmation of data exposure.
Limitations
· This rule detects unusual outbound behavior from Azure-hosted Ollama infrastructure, not transmitted content.
· Legitimate model management, update workflows, telemetry agents, backups, testing, registry access, and cloud storage workflows may overlap with this behavior.
· Azure network telemetry may not identify model artifacts, prompts, credentials, or other sensitive runtime content.
· Route-level model-ingestion visibility requires Application Gateway, Front Door, proxy, ingress, application, or container logs.
· Confirmation requires correlation with application logs, endpoint file activity, container telemetry, model artifact review, identity activity, or credential-management evidence.
Detection Query Pattern
Azure-native sequence pattern requiring NSG Flow Log, DNS, workload mapping, destination-baseline, and timing-window validation before production deployment.
SEQUENCE WITHIN ENV_MODEL_ACTIVITY_WINDOW
STEP 1:
AZURE_WORKLOAD_TAGS CONTAINS ANY (
"Ollama Server",
"Self-Hosted AI Model Server",
"AI Lab Server",
"Developer AI Infrastructure",
"Shared Model Infrastructure"
)
AND (
APPLICATION_GATEWAY_REQUEST_PATH IN (
"/api/create",
"/api/blobs",
"/api/push"
)
OR FRONT_DOOR_REQUEST_PATH IN (
"/api/create",
"/api/blobs",
"/api/push"
)
OR APPLICATION_ROUTE IN (
"/api/create",
"/api/blobs",
"/api/push"
)
OR INBOUND_SOURCE_CLASS IN (
"external",
"untrusted",
"newly_observed",
"rare",
"unapproved_internal"
)
OR MODEL_ACTIVITY_CONTEXT = "model_ingestion"
)
FOLLOWED BY STEP 2:
AZURE_WORKLOAD_ID = STEP_1.AZURE_WORKLOAD_ID
AND FLOW_DIRECTION = "egress"
AND (
DESTINATION_CLASS IN (
"newly_observed",
"rare",
"unapproved",
"external",
"anonymous_hosting",
"cloud_storage",
"file_sharing",
"unknown_model_registry"
)
OR DESTINATION_DOMAIN NOT IN APPROVED_OLLAMA_DESTINATIONS
OR DESTINATION_IP NOT IN APPROVED_OLLAMA_EGRESS_DESTINATIONS
OR BYTES_OUT > ENV_BASELINE_OLLAMA_EGRESS_BYTES
)
AND NOT DESTINATION_DOMAIN IN APPROVED_OLLAMA_DESTINATIONS
AND NOT DESTINATION_IP IN APPROVED_OLLAMA_EGRESS_DESTINATIONS
Rule 3
Azure Identity or Credential Activity Following Suspicious Ollama Exposure Window
Rule Format
Azure-native identity and audit correlation pattern suitable for Microsoft Sentinel, Microsoft Entra ID logs, Defender for Cloud, Azure Monitor, Event Grid, or SIEM-forwarded detection after identity-source validation, asset-to-identity mapping, credential-baseline validation, and environment-specific tuning.
Detection Purpose
· Detect suspicious Microsoft Entra ID, service principal, managed identity, application credential, role assignment, Key Vault, or cloud API activity after suspicious Azure-hosted Ollama exposure or model lifecycle activity.
· Identify downstream credential or access risk when exposed AI infrastructure may have processed sensitive runtime context.
· Prioritize cases where suspicious Ollama exposure aligns with unusual identity activity from unfamiliar sources, tenants, subscriptions, locations, user agents, or automation contexts.
· This rule does not prove credential theft or memory disclosure without supporting identity investigation, endpoint evidence, application evidence, or credential-management evidence.
Detection Logic
· Identify Azure-hosted Ollama infrastructure that is unpatched, exposed, broadly reachable, or associated with suspicious model-ingestion or model lifecycle activity.
· Identify Microsoft Entra ID, Azure Activity, service principal, managed identity, Key Vault, role assignment, application credential, or cloud API activity occurring after the suspicious exposure window.
· Prioritize events involving new credentials, unusual service principal activity, rare managed identity use, role assignment changes, Key Vault access, secret reads, cloud API calls from unfamiliar locations, unusual user agents, or access to resources associated with the Ollama workload.
· Increase confidence when the identity, service principal, managed identity, application, Key Vault, subscription, repository, or resource group is mapped to the Ollama workload or its owner.
· Increase confidence when activity originates from unfamiliar geography, unfamiliar ASN, rare user-agent context, unexpected automation, or newly observed source infrastructure.
· Do not classify this activity as confirmed credential compromise without analyst review and supporting evidence.
Required Telemetry
· Microsoft Entra ID sign-in logs.
· Microsoft Entra ID audit logs.
· Azure Activity Logs.
· Defender for Cloud findings where available.
· Azure Monitor logs.
· Key Vault access logs where available.
· Managed identity activity where available.
· Service principal activity.
· Application credential creation or update events.
· Role assignment events.
· Source IP address.
· User agent.
· Azure region.
· Tenant ID.
· Subscription ID.
· Resource identity.
· Ollama workload owner mapping.
· Asset-to-identity mapping.
· Credential-management activity logs where available.
· Timestamp.
Engineering Implementation Instructions
· Validate Microsoft Entra ID logging, Azure Activity coverage, Defender for Cloud, Azure Monitor, Key Vault logging, and credential-management telemetry before deployment.
· Establish mappings between Ollama workloads, owners, managed identities, service principals, application registrations, repositories, Key Vaults, resource groups, and subscriptions where available.
· Tune the post-exposure review window to the organization’s incident-response and credential-rotation requirements.
· Add exceptions for approved key rotation, scheduled automation, approved CI/CD workflows, approved administrative activity, approved repository automation, approved service principal changes, and approved cloud operations.
· Treat the rule as high priority when identity activity follows untrusted inbound access, model-ingestion activity, unusual egress, runtime instability, or unpatched exposure.
· Use endpoint, application, proxy, container, NDR, SIEM, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
7.5 / 10
· The rule is behaviorally anchored to downstream identity and credential activity after suspicious Azure-hosted Ollama exposure.
· The rule remains useful if model artifact names change, attacker infrastructure rotates, or model-ingestion details are only partially visible.
· The score is supported by the durability of reviewing cloud identity activity after suspected runtime exposure.
· The score is constrained by identity noise, normal key rotation, automation-heavy environments, incomplete asset-to-identity mapping, and missing credential-management telemetry.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on Microsoft Entra ID coverage, Azure Activity fidelity, Defender for Cloud context, asset-to-identity mapping, owner mapping, Key Vault telemetry, credential-management telemetry, and post-exposure timing.
· Operational confidence is reduced where subscriptions are fragmented, Entra ID logs are incomplete, workload identities are not mapped, or automation creates frequent identity changes.
· Full-telemetry confidence improves when Azure identity telemetry is enriched with application logs, endpoint telemetry, egress telemetry, asset inventory, repository logs, credential-management activity, and incident timeline context.
· Even under full telemetry conditions, this rule requires analyst review before confirmed credential compromise classification.
Limitations
· This rule detects suspicious downstream Azure identity or credential activity after Ollama exposure, not memory disclosure itself.
· Legitimate key rotation, CI/CD automation, cloud administration, incident-response actions, service principal maintenance, and repository automation may overlap with this pattern.
· The rule requires reliable mapping between Ollama workloads, owners, managed identities, service principals, application credentials, and Key Vault resources.
· Missing Entra ID logs, Azure Activity Logs, Defender for Cloud, Key Vault logs, repository logs, or credential-management telemetry can reduce confidence.
· Confirmation requires credential review, identity investigation, artifact review, application context, and incident timeline validation.
Detection Query Pattern
Azure-native identity correlation pattern requiring Microsoft Entra ID, Azure Activity, subscription, tenant, asset-to-identity, and timing-window validation before production deployment.
SEQUENCE WITHIN ENV_POST_EXPOSURE_IDENTITY_REVIEW_WINDOW
STEP 1:
AZURE_WORKLOAD_TAGS CONTAINS ANY (
"Ollama Server",
"Self-Hosted AI Model Server",
"AI Lab Server",
"Developer AI Infrastructure",
"Shared Model Infrastructure"
)
AND (
EXPOSURE_STATUS IN (
"internet_facing",
"broad_internal_access",
"unapproved_exposure"
)
OR PATCH_STATUS = "unpatched"
OR MODEL_ACTIVITY_CONTEXT IN (
"model_ingestion",
"model_artifact_activity",
"unusual_egress",
"runtime_instability"
)
)
FOLLOWED BY STEP 2:
AZURE_IDENTITY_EVENT IN (
"Add service principal credentials",
"Update application credentials",
"Add app role assignment",
"Add member to role",
"Add eligible member to role",
"ServicePrincipalSignIn",
"ManagedIdentitySignIn",
"SecretGet",
"SecretList",
"KeyGet",
"RoleAssignmentCreate",
"Microsoft.Authorization/roleAssignments/write",
"Microsoft.KeyVault/vaults/secrets/read"
)
AND (
IDENTITY_SOURCE_CLASS IN (
"newly_observed",
"rare",
"unapproved",
"external",
"unfamiliar_geo",
"unfamiliar_asn",
"unusual_user_agent"
)
OR IDENTITY_OR_APP_OWNER IN STEP_1.RELATED_IDENTITIES
OR SUBSCRIPTION_ID IN STEP_1.RELATED_SUBSCRIPTIONS
OR RESOURCE_GROUP IN STEP_1.RELATED_RESOURCE_GROUPS
)
AND NOT IDENTITY IN APPROVED_CLOUD_ADMIN_IDENTITIES
AND NOT EVENT_CONTEXT IN APPROVED_KEY_ROTATION_OR_AUTOMATION
GCP
Detection Viability Assessment
GCP has three rules for this EXP report.
· GCP is viable for detecting exposed Ollama infrastructure, permissive firewall exposure, suspicious inbound access, unusual outbound communication, workload identity activity, cloud audit activity, and downstream service-account or credential anomalies where Ollama infrastructure runs in Google Cloud.
· GCP is strongest where Cloud Audit Logs, VPC Flow Logs, Cloud Load Balancing logs, Cloud DNS logs, Security Command Center findings, Cloud Asset Inventory, Compute Engine inventory, GKE telemetry, Cloud Run logs, Artifact Registry activity, Secret Manager logs, and IAM activity are available.
· GCP should not be treated as a standalone source for confirming memory disclosure, model artifact content, or endpoint-level model-loader behavior unless the relevant workload, endpoint, application, or container telemetry is also collected.
· GCP is most valuable for identifying exposed Google Cloud-hosted Ollama workloads, suspicious inbound access, unusual outbound destinations, and post-exposure IAM, service-account, or credential activity.
Rule 1
GCP-Hosted Ollama Exposure to Untrusted Networks
Rule Format
GCP-native detection pattern suitable for Security Command Center, Cloud Logging, Eventarc, Cloud Monitoring, or SIEM-forwarded detection after project validation, resource labeling, firewall exposure validation, log-source validation, and environment-specific tuning.
Detection Purpose
· Detect GCP-hosted Ollama infrastructure that is reachable from untrusted networks or the public internet.
· Identify cloud exposure conditions that increase the likelihood of suspicious model-ingestion activity against self-hosted AI model infrastructure.
· Prioritize Compute Engine instances, GKE workloads, Cloud Run services, containerized workloads, load balancers, or model-serving infrastructure associated with Ollama service exposure.
· This rule does not confirm exploitation or memory disclosure without supporting access logs, endpoint telemetry, model artifact activity, outbound movement, identity activity, or credential-management evidence.
Detection Logic
· Identify GCP compute, container, GKE, Cloud Run, or load-balanced workloads tagged or labeled as Ollama servers, self-hosted AI model servers, AI lab systems, developer AI infrastructure, or shared model infrastructure.
· Identify VPC firewall rules, public IP assignments, external load balancers, forwarding rules, ingress paths, or exposed service routes that allow access to Ollama service ports or model-serving API paths from untrusted or public networks.
· Prioritize exposure where the workload is unpatched, unapproved, outside expected inventory, internet-facing, or associated with sensitive AI workflows.
· Increase confidence when exposed services receive inbound traffic from unfamiliar, external, newly observed, rare, or unapproved sources.
· Increase confidence when exposure is paired with route-level access to model-ingestion or model-transfer functionality through load balancer, proxy, ingress, or application logs.
· Do not classify exposure alone as compromise without suspicious access, model lifecycle activity, unusual egress, runtime instability, or downstream identity activity.
Required Telemetry
· Cloud Audit Logs.
· Cloud Asset Inventory.
· VPC firewall rule configuration.
· Public IP assignment data.
· Cloud Load Balancing logs where available.
· VPC Flow Logs.
· Cloud DNS logs where available.
· Security Command Center findings where available.
· Compute Engine, GKE, Cloud Run, or container workload inventory.
· Asset labels or tags.
· Workload owner context.
· Patch or vulnerability context where available.
· Approved administrative source baseline.
· Approved deployment inventory.
· Timestamp.
Engineering Implementation Instructions
· Validate resource labeling for Compute Engine instances, GKE workloads, Cloud Run services, container workloads, load balancers, forwarding rules, and container hosts associated with Ollama infrastructure.
· Validate which ports, listeners, paths, and services are approved for Ollama or model-serving access.
· Use Cloud Asset Inventory, Cloud Audit Logs, Security Command Center, VPC Flow Logs, firewall rules, and Cloud Load Balancing logs to identify exposure and inbound access context.
· Scope the rule to workloads tagged or labeled as Ollama servers, self-hosted AI model servers, AI lab systems, developer AI infrastructure, or shared model infrastructure.
· Add exceptions for approved private subnets, approved internal load balancers, approved administrative sources, approved AI platform services, vulnerability scanners, and monitoring systems.
· Treat exposure as higher priority when paired with unpatched status, unfamiliar inbound sources, unusual request timing, model-ingestion activity, or abnormal egress.
· Use endpoint, container, application, NDR, SIEM, identity, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to GCP cloud exposure and suspicious access conditions rather than exploit-specific payloads.
· The rule remains useful if attacker infrastructure changes, model names vary, request timing shifts, or public proof-of-concept details change.
· The score is supported by the durability of identifying exposed Google Cloud-hosted AI model infrastructure as a high-value risk condition.
· The score is constrained by incomplete asset labeling, unmanaged cloud deployments, missing load balancer logs, incomplete patch context, and legitimate development exposure patterns.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on Cloud Asset Inventory coverage, VPC Flow Log availability, Cloud Load Balancing logging, asset labeling, firewall visibility, patch context, and approved-source baselining.
· Operational confidence is reduced where Ollama workloads are temporary, unlabeled, deployed outside approved projects, or directly exposed without consistent application logging.
· Full-telemetry confidence improves when GCP telemetry is enriched with endpoint telemetry, container logs, proxy logs, NDR data, application logs, vulnerability data, and identity activity.
· Even under full telemetry conditions, exposure should be treated as a high-priority risk condition, not confirmed compromise by itself.
Limitations
· This rule detects exposed GCP-hosted Ollama infrastructure, not memory disclosure itself.
· Public exposure, permissive firewall rules, public IP assignment, or unapproved listeners do not prove exploitation.
· Legitimate lab testing, developer access, vulnerability scanning, approved temporary exposure, and internal AI workflows may overlap with this behavior.
· GCP telemetry may not provide route-level model-ingestion visibility unless Cloud Load Balancing, proxy, ingress, or application logs are enabled.
· Confirmation requires correlation with suspicious inbound access, model lifecycle activity, endpoint artifact changes, unusual outbound communication, identity activity, or credential-management evidence.
Detection Query Pattern
GCP-native detection pattern requiring project, folder, organization, label, firewall, flow, and load balancer log validation before production deployment.
GCP_RESOURCE_TYPE IN (
"compute.googleapis.com/Instance",
"container.googleapis.com/Cluster",
"run.googleapis.com/Service",
"compute.googleapis.com/ForwardingRule",
"compute.googleapis.com/BackendService",
"compute.googleapis.com/Firewall",
"compute.googleapis.com/Address"
)
AND RESOURCE_LABELS CONTAINS ANY (
"Ollama Server",
"Self-Hosted AI Model Server",
"AI Lab Server",
"Developer AI Infrastructure",
"Shared Model Infrastructure"
)
AND (
FIREWALL_ALLOWED_SOURCE IN (
"0.0.0.0/0",
"::/0"
)
OR EXTERNAL_IP_ASSIGNED = true
OR LOAD_BALANCER_SCHEME = "external"
OR PUBLIC_FORWARDING_RULE = true
)
AND (
EXPOSED_PORT IN (
11434,
APPROVED_OLLAMA_PORTS
)
OR SERVICE_NAME IN (
"ollama",
"ai-model-server",
"model-serving-api"
)
)
AND NOT SOURCE_CIDR IN APPROVED_OLLAMA_ADMIN_SOURCES
AND NOT RESOURCE_ID IN APPROVED_PUBLIC_OLLAMA_DEPLOYMENTS
Rule 2
GCP Ollama Workload with Unusual Outbound Communication After Model Activity
Rule Format
GCP-native sequence detection pattern suitable for Cloud Logging, Security Command Center enrichment, Cloud Monitoring, Eventarc, or SIEM-forwarded detection after VPC Flow Log validation, DNS visibility validation, workload identity mapping, destination baselining, and timing-window tuning.
Detection Purpose
· Detect unusual outbound communication from a GCP-hosted Ollama workload after model-ingestion activity, model artifact activity, or suspicious inbound access.
· Identify possible artifact transfer, attacker-directed outbound communication, or post-event data-exposure risk without claiming direct visibility into transmitted content.
· Prioritize destinations outside approved model-source, update, registry, automation, cloud storage, or administrative baselines.
· This rule does not determine transmitted content or confirm memory disclosure without supporting proxy, endpoint, container, application, artifact, identity, or credential-management evidence.
Detection Logic
· Identify GCP-hosted Ollama workloads using Compute Engine, GKE, Cloud Run, load balancer, container, or asset labels.
· Identify model-ingestion activity, model-transfer activity, suspicious inbound access, or model-related application behavior where route-level logs are available.
· Within a defined investigation window, identify outbound traffic from the same workload, instance, pod, container, or container host to unfamiliar, rare, newly observed, unapproved, external, anonymous hosting, cloud storage, file-sharing, or unknown model-registry destinations.
· Increase confidence when outbound bytes exceed the normal baseline for the workload or when DNS activity resolves unfamiliar destinations after model activity.
· Increase confidence when the workload is unpatched, internet-facing, broadly reachable, or outside approved deployment inventory.
· Do not classify outbound activity as confirmed data theft without corroborating application, endpoint, container, artifact, proxy, identity, or credential-management evidence.
Required Telemetry
· VPC Flow Logs.
· Cloud DNS logs where available.
· Cloud Load Balancing logs where available.
· Cloud Audit Logs.
· Compute Engine, GKE, Cloud Run, or container workload inventory.
· Host, instance, pod, workload, or container identity.
· Source and destination IP addresses.
· Destination domain where available.
· Destination port.
· Flow bytes.
· Flow direction.
· Destination classification or reputation where available.
· Approved egress destination baseline.
· Approved model registry baseline.
· Asset labels or tags.
· Exposure context.
· Patch or vulnerability context where available.
· Timestamp.
Engineering Implementation Instructions
· Validate VPC Flow Logs, Cloud DNS logs, Cloud Load Balancing logs, Cloud Audit Logs, and workload inventory coverage before deployment.
· Map Ollama workloads across Compute Engine instances, GKE workloads, Cloud Run services, load balancers, forwarding rules, and container hosts.
· Establish approved model registries, approved update destinations, approved cloud destinations, approved AI platform automation, approved container registries, and known monitoring destinations.
· Tune the sequence window to the organization’s model-ingestion, model-management, and cloud egress patterns.
· Add exceptions for approved model pulls, approved model pushes, patching, backups, monitoring, container registry access, telemetry agents, AI platform automation, and authorized developer workflows.
· Treat unusual egress as higher priority when paired with untrusted inbound access, unpatched exposure, model artifact activity, runtime instability, or identity activity.
· Use endpoint, application, proxy, NDR, container, SIEM, identity, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
8.0 / 10
· The rule is behaviorally anchored to unusual GCP workload egress after model-related activity.
· The rule remains useful if attacker infrastructure changes, model names vary, artifact names change, or outbound timing shifts.
· The score is supported by the durability of exposed model-serving workloads communicating with unfamiliar destinations after suspicious activity.
· The score is constrained by legitimate model downloads, model pushes, registry synchronization, cloud storage access, backups, and incomplete egress baselining.
TCR Assessment
Operational TCR
7.0 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on VPC Flow Logs, DNS visibility, workload identity mapping, egress baselining, destination classification, asset labeling, and load balancer or application context.
· Operational confidence is reduced where flow logs are incomplete, DNS visibility is missing, egress destinations are not baselined, or workload identity mapping is unreliable.
· Full-telemetry confidence improves when GCP telemetry is enriched with endpoint telemetry, application logs, container logs, proxy logs, NDR telemetry, file activity, vulnerability data, and identity activity.
· Even under full telemetry conditions, this rule supports escalation and investigation rather than standalone confirmation of data exposure.
Limitations
· This rule detects unusual outbound behavior from GCP-hosted Ollama infrastructure, not transmitted content.
· Legitimate model management, update workflows, telemetry agents, backups, testing, registry access, and cloud storage workflows may overlap with this behavior.
· GCP network telemetry may not identify model artifacts, prompts, credentials, or other sensitive runtime content.
· Route-level model-ingestion visibility requires Cloud Load Balancing, proxy, ingress, application, or container logs.
· Confirmation requires correlation with application logs, endpoint file activity, container telemetry, model artifact review, identity activity, or credential-management evidence.
Detection Query Pattern
GCP-native sequence pattern requiring VPC Flow Log, DNS, workload mapping, destination-baseline, and timing-window validation before production deployment.
SEQUENCE WITHIN ENV_MODEL_ACTIVITY_WINDOW
STEP 1:
GCP_WORKLOAD_LABELS CONTAINS ANY (
"Ollama Server",
"Self-Hosted AI Model Server",
"AI Lab Server",
"Developer AI Infrastructure",
"Shared Model Infrastructure"
)
AND (
LOAD_BALANCER_REQUEST_PATH IN (
"/api/create",
"/api/blobs",
"/api/push"
)
OR APPLICATION_ROUTE IN (
"/api/create",
"/api/blobs",
"/api/push"
)
OR INBOUND_SOURCE_CLASS IN (
"external",
"untrusted",
"newly_observed",
"rare",
"unapproved_internal"
)
OR MODEL_ACTIVITY_CONTEXT = "model_ingestion"
)
FOLLOWED BY STEP 2:
GCP_WORKLOAD_ID = STEP_1.GCP_WORKLOAD_ID
AND FLOW_DIRECTION = "egress"
AND (
DESTINATION_CLASS IN (
"newly_observed",
"rare",
"unapproved",
"external",
"anonymous_hosting",
"cloud_storage",
"file_sharing",
"unknown_model_registry"
)
OR DESTINATION_DOMAIN NOT IN APPROVED_OLLAMA_DESTINATIONS
OR DESTINATION_IP NOT IN APPROVED_OLLAMA_EGRESS_DESTINATIONS
OR BYTES_OUT > ENV_BASELINE_OLLAMA_EGRESS_BYTES
)
AND NOT DESTINATION_DOMAIN IN APPROVED_OLLAMA_DESTINATIONS
AND NOT DESTINATION_IP IN APPROVED_OLLAMA_EGRESS_DESTINATIONS
Rule 3
GCP Identity or Credential Activity Following Suspicious Ollama Exposure Window
Rule Format
GCP-native identity and audit correlation pattern suitable for Cloud Audit Logs, IAM Recommender context, Security Command Center, Cloud Logging, Eventarc, or SIEM-forwarded detection after identity-source validation, asset-to-identity mapping, credential-baseline validation, and environment-specific tuning.
Detection Purpose
· Detect suspicious IAM, service account, key, token, Secret Manager, repository, or cloud API activity after suspicious GCP-hosted Ollama exposure or model lifecycle activity.
· Identify downstream credential or access risk when exposed AI infrastructure may have processed sensitive runtime context.
· Prioritize cases where suspicious Ollama exposure aligns with unusual identity activity from unfamiliar sources, projects, service accounts, locations, user agents, or automation contexts.
· This rule does not prove credential theft or memory disclosure without supporting identity investigation, endpoint evidence, application evidence, or credential-management evidence.
Detection Logic
· Identify GCP-hosted Ollama infrastructure that is unpatched, exposed, broadly reachable, or associated with suspicious model-ingestion or model lifecycle activity.
· Identify Cloud Audit Logs, IAM, service account, service account key, Secret Manager, Artifact Registry, repository, or cloud API activity occurring after the suspicious exposure window.
· Prioritize events involving service account key creation, unusual service account use, rare token use, IAM policy changes, Secret Manager access, repository access, cloud API calls from unfamiliar locations, unusual user agents, or access to resources associated with the Ollama workload.
· Increase confidence when the identity, service account, key, repository, secret, project, or resource is mapped to the Ollama workload or its owner.
· Increase confidence when activity originates from unfamiliar geography, unfamiliar ASN, rare user-agent context, unexpected automation, or newly observed source infrastructure.
· Do not classify this activity as confirmed credential compromise without analyst review and supporting evidence.
Required Telemetry
· Cloud Audit Logs.
· IAM activity logs.
· Security Command Center findings where available.
· Service account activity.
· Service account key creation and use events.
· Secret Manager access logs where available.
· Artifact Registry activity where available.
· Repository access logs where applicable.
· Source IP address.
· User agent.
· GCP region.
· Project ID.
· Folder or organization context.
· Resource identity.
· Ollama workload owner mapping.
· Asset-to-identity mapping.
· Credential-management activity logs where available.
· Timestamp.
Engineering Implementation Instructions
· Validate Cloud Audit Logs coverage across relevant organizations, folders, projects, and regions.
· Validate Security Command Center, IAM activity, Secret Manager logs, Artifact Registry logs, repository logs, and credential-management telemetry before deployment.
· Establish mappings between Ollama workloads, owners, service accounts, repositories, secrets, projects, folders, and organizations where available.
· Tune the post-exposure review window to the organization’s incident-response and credential-rotation requirements.
· Add exceptions for approved key rotation, scheduled automation, approved CI/CD workflows, approved administrative activity, approved repository automation, approved service account changes, and approved cloud operations.
· Treat the rule as high priority when identity activity follows untrusted inbound access, model-ingestion activity, unusual egress, runtime instability, or unpatched exposure.
· Use endpoint, application, proxy, container, NDR, SIEM, and credential-management telemetry as triage evidence before classifying the case as confirmed compromise.
DRI Assessment
DRI
7.5 / 10
· The rule is behaviorally anchored to downstream IAM and credential activity after suspicious GCP-hosted Ollama exposure.
· The rule remains useful if model artifact names change, attacker infrastructure rotates, or model-ingestion details are only partially visible.
· The score is supported by the durability of reviewing cloud identity activity after suspected runtime exposure.
· The score is constrained by identity noise, normal key rotation, automation-heavy environments, incomplete asset-to-identity mapping, and missing credential-management telemetry.
TCR Assessment
Operational TCR
6.5 / 10
Full-Telemetry TCR
8.5 / 10
· Operational confidence depends on Cloud Audit Logs coverage, IAM event fidelity, Security Command Center context, asset-to-identity mapping, owner mapping, Secret Manager telemetry, credential-management telemetry, and post-exposure timing.
· Operational confidence is reduced where projects are fragmented, audit logs are incomplete, workload identities are not mapped, or automation creates frequent identity changes.
· Full-telemetry confidence improves when GCP identity telemetry is enriched with application logs, endpoint telemetry, egress telemetry, asset inventory, repository logs, credential-management activity, and incident timeline context.
· Even under full telemetry conditions, this rule requires analyst review before confirmed credential compromise classification.
Limitations
· This rule detects suspicious downstream GCP identity or credential activity after Ollama exposure, not memory disclosure itself.
· Legitimate key rotation, CI/CD automation, cloud administration, incident-response actions, service account maintenance, and repository automation may overlap with this pattern.
· The rule requires reliable mapping between Ollama workloads, owners, service accounts, keys, Secret Manager resources, repositories, and projects.
· Missing Cloud Audit Logs, Security Command Center, Secret Manager logs, repository logs, or credential-management telemetry can reduce confidence.
· Confirmation requires credential review, identity investigation, artifact review, application context, and incident timeline validation.
Detection Query Pattern
GCP-native identity correlation pattern requiring Cloud Audit Logs, IAM, project, folder, organization, asset-to-identity, and timing-window validation before production deployment.
SEQUENCE WITHIN ENV_POST_EXPOSURE_IDENTITY_REVIEW_WINDOW
STEP 1:
GCP_WORKLOAD_LABELS CONTAINS ANY (
"Ollama Server",
"Self-Hosted AI Model Server",
"AI Lab Server",
"Developer AI Infrastructure",
"Shared Model Infrastructure"
)
AND (
EXPOSURE_STATUS IN (
"internet_facing",
"broad_internal_access",
"unapproved_exposure"
)
OR PATCH_STATUS = "unpatched"
OR MODEL_ACTIVITY_CONTEXT IN (
"model_ingestion",
"model_artifact_activity",
"unusual_egress",
"runtime_instability"
)
)
FOLLOWED BY STEP 2:
GCP_IDENTITY_EVENT IN (
"google.iam.admin.v1.CreateServiceAccountKey",
"google.iam.admin.v1.SetIamPolicy",
"google.iam.admin.v1.CreateServiceAccount",
"google.iam.credentials.v1.GenerateAccessToken",
"google.cloud.secretmanager.v1.AccessSecretVersion",
"google.devtools.artifactregistry.v1.UploadArtifact",
"google.cloud.audit.ServiceAccountKeyCreated",
"google.cloud.audit.ServiceAccountUsed",
"storage.objects.get",
"storage.objects.create"
)
AND (
IDENTITY_SOURCE_CLASS IN (
"newly_observed",
"rare",
"unapproved",
"external",
"unfamiliar_geo",
"unfamiliar_asn",
"unusual_user_agent"
)
OR IDENTITY_OR_SERVICE_ACCOUNT IN STEP_1.RELATED_IDENTITIES
OR PROJECT_ID IN STEP_1.RELATED_PROJECTS
OR RESOURCE_NAME IN STEP_1.RELATED_RESOURCES
)
AND NOT IDENTITY IN APPROVED_CLOUD_ADMIN_IDENTITIES
AND NOT EVENT_CONTEXT IN APPROVED_KEY_ROTATION_OR_AUTOMATION
S26 Threat-to-Rule Traceability Matrix
Traceability Purpose
S26 maps the S25 rule set to the threat behaviors defined across the detection strategy.
· This section validates that the surviving rules align to the report’s behavioral risk model.
· This section does not introduce new detection logic.
· This section does not replace S25 engineering detail.
· This section does not claim direct memory-disclosure detection.
· This section uses plain-text traceability mapping instead of tables for cleaner publishing and copy-paste handling.
Primary Threat Behavior
Exposed Ollama infrastructure reachable from public or untrusted networks.
Mapped Detection Rules
· NDR / Network Behavioral Analytics: Suspicious Ollama Model-Ingestion Activity from Untrusted Source.
· Splunk: Untrusted Source Access to Ollama Model-Ingestion Functionality.
· Elastic: Untrusted Access to Ollama Model-Ingestion Functionality.
· QRadar: Untrusted Source Access to Ollama Model-Ingestion Functionality.
· SIGMA: Ollama Model-Ingestion Route Access from Untrusted Source.
· AWS: AWS-Hosted Ollama Exposure to Untrusted Networks.
· AZURE: Azure-Hosted Ollama Exposure to Untrusted Networks.
· GCP: GCP-Hosted Ollama Exposure to Untrusted Networks.
Traceability Assessment
· Coverage is strong across network analytics, SIEM correlation, portable detection logic, and cloud-native telemetry.
· Exposure is treated as a high-priority risk condition, not confirmed compromise.
· Confidence increases when exposure is paired with suspicious access, model lifecycle behavior, outbound movement, endpoint evidence, identity activity, or credential-management evidence.
· Cloud-native exposure detection depends on accurate asset tagging, labeling, inventory, and network configuration visibility.
Coverage Status
Strong.
Primary Threat Behavior
Untrusted access to model-ingestion or model-transfer functionality.
Mapped Detection Rules
· NDR / Network Behavioral Analytics: Suspicious Ollama Model-Ingestion Activity from Untrusted Source.
· Splunk: Untrusted Source Access to Ollama Model-Ingestion Functionality.
· Elastic: Untrusted Access to Ollama Model-Ingestion Functionality.
· QRadar: Untrusted Source Access to Ollama Model-Ingestion Functionality.
· SIGMA: Ollama Model-Ingestion Route Access from Untrusted Source.
· AWS: AWS Ollama Workload with Unusual Egress After Model Activity.
· AZURE: Azure Ollama Workload with Unusual Outbound Communication After Model Activity.
· GCP: GCP Ollama Workload with Unusual Outbound Communication After Model Activity.
Traceability Assessment
· Coverage is strong where route-level proxy, ingress, application, gateway, or load balancer logs are available.
· NDR, SIEM, and SIGMA coverage depend on service identification and route visibility.
· Cloud-native coverage is strongest when load balancer, application, proxy, container, or SIEM-forwarded logs are available.
· Endpoint-only telemetry should not be used to claim route-level model-ingestion visibility unless enriched by another source.
Coverage Status
Strong with route-level telemetry. Moderate where only flow-level telemetry is available.
Primary Threat Behavior
Model artifact creation, modification, staging, or unusual model storage activity.
Mapped Detection Rules
· SentinelOne: Ollama Process Writes Unusual Model Artifacts or GGUF-Related Files.
· Splunk: Ollama Model-Ingestion Activity Followed by Artifact Creation and Outbound Communication.
· Elastic: Ollama Model-Ingestion Activity Followed by Model Artifact Creation.
· SIGMA: Ollama Process Creates or Modifies Unusual Model Artifacts.
· QRadar: Unpatched Ollama Exposure with Suspicious Model Lifecycle and Identity Activity.
· AWS: AWS Ollama Workload with Unusual Egress After Model Activity.
· AZURE: Azure Ollama Workload with Unusual Outbound Communication After Model Activity.
· GCP: GCP Ollama Workload with Unusual Outbound Communication After Model Activity.
Traceability Assessment
· Coverage is strongest in SentinelOne, Splunk, Elastic, and SIGMA where endpoint or file telemetry is available.
· QRadar can support artifact traceability when endpoint, file, application, or SIEM-enriched telemetry is ingested.
· Cloud-native systems provide supporting context when model activity is visible through application, container, endpoint, or SIEM-enriched telemetry.
· NDR alone should not be used to claim model artifact creation because network telemetry does not directly observe local file activity.
· YARA does not provide primary coverage because the detection problem is behavioral rather than static-artifact based.
Coverage Status
Strong with endpoint or file telemetry. Limited with network-only telemetry.
Primary Threat Behavior
Runtime instability, process crashes, abnormal restarts, or fault-adjacent behavior near model activity.
Mapped Detection Rules
· SentinelOne: Ollama Runtime Instability Near Suspicious Model-Ingestion Activity.
· Splunk: Ollama Model-Ingestion Activity Followed by Artifact Creation and Outbound Communication.
· Elastic: Ollama Model-Ingestion Activity Followed by Model Artifact Creation.
· QRadar: Unpatched Ollama Exposure with Suspicious Model Lifecycle and Identity Activity.
· AWS: AWS Identity or Credential Activity Following Suspicious Ollama Exposure Window.
· AZURE: Azure Identity or Credential Activity Following Suspicious Ollama Exposure Window.
· GCP: GCP Identity or Credential Activity Following Suspicious Ollama Exposure Window.
Traceability Assessment
· Direct runtime instability coverage is strongest in SentinelOne.
· Splunk, Elastic, and QRadar can correlate runtime instability when endpoint, service, container, or application telemetry is ingested.
· Cloud-native systems provide supporting context only when runtime signals are forwarded through workload, container, endpoint, or application telemetry.
· Runtime instability should be treated as supporting evidence, not standalone proof of exploitation.
Coverage Status
Moderate to strong depending on endpoint, service, and container telemetry availability.
Primary Threat Behavior
Unusual outbound communication after model-ingestion activity or model artifact activity.
Mapped Detection Rules
· NDR / Network Behavioral Analytics: Ollama Model-Ingestion Activity Followed by Unusual Outbound Communication.
· SentinelOne: Ollama Process Followed by Unusual Network or Runtime Behavior.
· Splunk: Ollama Model-Ingestion Activity Followed by Artifact Creation and Outbound Communication.
· Elastic: Ollama Host with Unusual Outbound Communication After Model Activity.
· QRadar: Ollama Model-Ingestion Activity Followed by Unusual Outbound Flow.
· SIGMA: Ollama Host Communicates with Unfamiliar External Destination After Model Activity.
· AWS: AWS Ollama Workload with Unusual Egress After Model Activity.
· AZURE: Azure Ollama Workload with Unusual Outbound Communication After Model Activity.
· GCP: GCP Ollama Workload with Unusual Outbound Communication After Model Activity.
Traceability Assessment
· Coverage is strong across NDR, endpoint, SIEM, portable detection logic, and cloud-native telemetry.
· This is one of the strongest cross-platform detection anchors because outbound communication can be observed from multiple telemetry layers.
· Rules should not infer transmitted content unless packet, proxy, application, endpoint, or artifact evidence supports that conclusion.
· Egress baselining and approved-destination management are required to reduce false positives.
Coverage Status
Strong.
Primary Threat Behavior
Large egress, unfamiliar external destination access, unknown model registry communication, or file-sharing destination communication.
Mapped Detection Rules
· NDR / Network Behavioral Analytics: Ollama Model-Ingestion Activity Followed by Unusual Outbound Communication.
· NDR / Network Behavioral Analytics: Unfamiliar Internal Host Accessing Shared Ollama Infrastructure Followed by Abnormal Network Behavior.
· SentinelOne: Ollama Process Followed by Unusual Network or Runtime Behavior.
· Splunk: Ollama Model-Ingestion Activity Followed by Artifact Creation and Outbound Communication.
· Elastic: Ollama Host with Unusual Outbound Communication After Model Activity.
· QRadar: Ollama Model-Ingestion Activity Followed by Unusual Outbound Flow.
· SIGMA: Ollama Host Communicates with Unfamiliar External Destination After Model Activity.
· AWS: AWS Ollama Workload with Unusual Egress After Model Activity.
· AZURE: Azure Ollama Workload with Unusual Outbound Communication After Model Activity.
· GCP: GCP Ollama Workload with Unusual Outbound Communication After Model Activity.
Traceability Assessment
· Coverage is strong when destination classification, DNS visibility, egress flow records, proxy logs, or endpoint-network mapping are available.
· NDR and cloud-native telemetry provide strong volume and destination visibility.
· Endpoint and SIEM coverage improves attribution by tying egress back to process, host, container, user, or workload identity.
· Detection quality depends heavily on approved-destination baselines.
Coverage Status
Strong with egress and DNS telemetry. Moderate without destination baselining.
Primary Threat Behavior
Suspicious internal access to shared or broadly reachable Ollama infrastructure.
Mapped Detection Rules
· NDR / Network Behavioral Analytics: Unfamiliar Internal Host Accessing Shared Ollama Infrastructure Followed by Abnormal Network Behavior.
· Splunk: Unpatched Ollama Exposure with Suspicious Model Lifecycle and Credential Activity.
· Elastic: Ollama Host with Unusual Outbound Communication After Model Activity.
· QRadar: Unpatched Ollama Exposure with Suspicious Model Lifecycle and Identity Activity.
Traceability Assessment
· Coverage is strongest in NDR where east-west traffic, internal source baselining, and network-zone context are available.
· Splunk and QRadar can provide stronger correlation when internal access is enriched with asset, identity, file, and credential-management data.
· Elastic can support this pattern when endpoint-network and host identity data are available.
· Internal access should not be treated as malicious without follow-on abnormal behavior or supporting evidence.
Coverage Status
Moderate to strong depending on east-west visibility and internal source baselining.
Primary Threat Behavior
Downstream credential, identity, service-account, token, or cloud-control activity after suspicious exposure.
Mapped Detection Rules
· Splunk: Unpatched Ollama Exposure with Suspicious Model Lifecycle and Credential Activity.
· QRadar: Unpatched Ollama Exposure with Suspicious Model Lifecycle and Identity Activity.
· AWS: AWS Identity or Credential Activity Following Suspicious Ollama Exposure Window.
· AZURE: Azure Identity or Credential Activity Following Suspicious Ollama Exposure Window.
· GCP: GCP Identity or Credential Activity Following Suspicious Ollama Exposure Window.
Traceability Assessment
· Coverage is strong across SIEM and cloud-native systems when identity, credential-management, cloud audit, repository, and service-account logs are available.
· This behavior is downstream correlation, not proof that credentials were exposed through Ollama.
· High-confidence assessment requires asset-to-identity mapping, workload ownership, credential activity logs, cloud audit logs, and timeline validation.
· Analyst review remains required before confirmed credential-compromise classification.
Coverage Status
Strong with identity and credential-management telemetry. Moderate where asset-to-identity mapping is incomplete.
Primary Threat Behavior
Cloud-hosted Ollama exposure in AWS, Azure, or GCP.
Mapped Detection Rules
· AWS: AWS-Hosted Ollama Exposure to Untrusted Networks.
· AZURE: Azure-Hosted Ollama Exposure to Untrusted Networks.
· GCP: GCP-Hosted Ollama Exposure to Untrusted Networks.
· Splunk: Unpatched Ollama Exposure with Suspicious Model Lifecycle and Credential Activity.
· QRadar: Unpatched Ollama Exposure with Suspicious Model Lifecycle and Identity Activity.
Traceability Assessment
· Coverage is strong for cloud-native exposure validation when asset tags, labels, cloud inventory, security rules, public IP assignment, load balancer context, and flow logs are available.
· SIEM correlation adds value when cloud exposure is combined with model lifecycle activity and identity anomalies.
· Exposure should trigger risk prioritization, validation, containment review, and downstream hunting.
· Exposure alone should not be represented as confirmed compromise.
Coverage Status
Strong.
Primary Threat Behavior
Static malicious artifact, known malicious file, or durable model-file signature.
Mapped Detection Rules
· YARA: No surviving rules.
Traceability Assessment
· Static artifact detection is not a strong fit for this report.
· The report’s primary detection model is behavior-led and telemetry-correlated.
· Generic YARA rules against model artifacts, GGUF files, or model-file structures would create high false-positive risk.
· YARA may be used only for controlled internal research after a specific suspicious artifact is confirmed.
Coverage Status
Not applicable for primary detection.
Rule Coverage Summary
Group 1
NDR / Network Behavioral Analytics
· Surviving rules: 3.
· Primary coverage: exposed service access, untrusted source behavior, unusual outbound communication, large egress, internal access anomalies, east-west network behavior.
· Coverage strength: Strong.
SentinelOne
· Surviving rules: 3.
· Primary coverage: model artifact writes, runtime instability, process-to-network behavior, host-level correlation.
· Coverage strength: Strong with endpoint coverage.
Splunk
· Surviving rules: 3.
· Primary coverage: route-level access, multi-source correlation, artifact activity, egress, identity, credential-management activity, asset and patch context.
· Coverage strength: Strong.
Group 2
Elastic
· Surviving rules: 3.
· Primary coverage: route-level access, endpoint artifact activity, endpoint-network behavior, sequence detection, cloud or identity enrichment where ingested.
· Coverage strength: Strong with normalized telemetry.
QRadar
· Surviving rules: 3.
· Primary coverage: offense correlation, route-level access, outbound flow behavior, identity activity, asset and vulnerability context.
· Coverage strength: Strong with custom properties and reference sets.
SIGMA
· Surviving rules: 3.
· Primary coverage: portable web, endpoint file, and network detection logic.
· Coverage strength: Moderate to strong after backend-specific translation and tuning.
YARA
· Surviving rules: 0.
· Primary coverage: no primary coverage.
· Coverage strength: Not applicable.
Group 3
AWS
· Surviving rules: 3.
· Primary coverage: AWS-hosted exposure, unusual egress, IAM and credential activity after exposure.
· Coverage strength: Strong with AWS logging and workload mapping.
AZURE
· Surviving rules: 3.
· Primary coverage: Azure-hosted exposure, unusual egress, Microsoft Entra ID, managed identity, service principal, and Key Vault activity after exposure.
· Coverage strength: Strong with Azure logging and workload mapping.
GCP
· Surviving rules: 3.
· Primary coverage: GCP-hosted exposure, unusual egress, IAM, service account, Secret Manager, and cloud audit activity after exposure.
· Coverage strength: Strong with GCP logging and workload mapping.
Overall Traceability Assessment
The S25 rule set provides broad behavioral coverage across network analytics, endpoint telemetry, SIEM correlation, portable detection logic, and cloud-native telemetry.
· Exposure is covered by NDR, SIEM, SIGMA, AWS, AZURE, and GCP.
· Model-ingestion activity is covered by NDR, Splunk, Elastic, QRadar, SIGMA, and cloud-native rules where route-level telemetry exists.
· Model artifact activity is covered most directly by SentinelOne, Splunk, Elastic, and SIGMA.
· Runtime instability is covered most directly by SentinelOne and indirectly by SIEM or cloud systems when runtime telemetry is ingested.
· Unusual outbound communication is covered strongly across NDR, SentinelOne, Splunk, Elastic, QRadar, SIGMA, AWS, AZURE, and GCP.
· Downstream identity and credential activity is covered by Splunk, QRadar, AWS, AZURE, and GCP.
· Static artifact detection is intentionally not covered by YARA because it is not durable for this report’s threat model.
Residual Traceability Gaps
· Direct memory disclosure is not directly detected by any rule system.
· Endpoint artifact visibility depends on endpoint, file, or container telemetry.
· Route-level model-ingestion visibility depends on proxy, ingress, load balancer, gateway, application, or enriched telemetry.
· Cloud-native exposure detection depends on accurate tagging, labeling, inventory, and network configuration visibility.
· Credential or identity follow-on detection depends on asset-to-identity mapping and credential-management telemetry.
· SIGMA coverage depends on backend-specific translation, field mapping, and tuning.
· YARA is intentionally excluded from primary coverage because the report’s detection model is behavioral.
Traceability Conclusion
The rule set provides strong coverage for the durable behavioral pattern associated with this report:
· Exposed AI model-serving infrastructure.
· Suspicious model-ingestion activity.
· Model artifact activity.
· Runtime instability where available.
· Unusual outbound communication.
· Downstream credential or identity activity.
The rule set does not claim direct memory-disclosure detection. It prioritizes realistic, telemetry-supported correlation across exposure, model lifecycle behavior, endpoint activity, egress, identity, and cloud control-plane activity.
S27 Behavior & Log Artifacts
Behavioral Artifact Summary
Behavior and log artifacts should be interpreted as correlated evidence, not standalone proof of memory disclosure. The strongest artifacts are those that show exposed Ollama infrastructure receiving suspicious model-ingestion activity, followed by model artifact changes, runtime instability, unusual outbound communication, or downstream identity and credential activity.
· Exposed Ollama service activity from untrusted, external, newly observed, rare, or unapproved sources.
· Requests associated with model-ingestion, model import, blob handling, model artifact transfer, or model push behavior.
· New or unusual model artifacts written near suspicious model-ingestion activity.
· Runtime instability, abnormal restarts, model-loading errors, or crash-adjacent behavior near suspicious model activity.
· Outbound communication from the Ollama host, workload, or container to unfamiliar destinations after model-ingestion activity.
· Downstream identity, cloud, repository, token, service-account, or credential-management activity after a suspicious exposure window.
Network Artifacts
Network artifacts provide the earliest and most durable evidence of exposure and suspicious interaction.
· Inbound traffic to Ollama service ports or model-serving API endpoints from external, rare, newly observed, or unapproved sources.
· Access to model-ingestion, blob, model import, model artifact handling, or model push routes where route-level telemetry is available.
· Repeated interaction with model-management functionality from sources outside approved administrative paths.
· Inbound activity from scanning infrastructure, anonymous hosting providers, commodity cloud sources, unfamiliar internal hosts, contractor networks, or unmanaged systems.
· Public exposure through internet-facing interfaces, permissive firewall rules, public load balancers, exposed listeners, broad internal access, or unapproved service publication.
· Unusual traffic timing, request volume, large request bodies, repeated model-related requests, or access outside approved administrative windows.
Proxy, Gateway, and Application Artifacts
Proxy, gateway, ingress, and application artifacts are high-value when route-level visibility is available.
· Request paths associated with model-ingestion, model import, blob handling, or model transfer.
· Source IP address, forwarded source context, request method, response status, request timing, response size, and user-agent values.
· Requests from sources that are not part of approved administrative, automation, monitoring, or AI platform workflows.
· Route-level access to model-management functionality on internet-facing, broadly reachable, or unpatched Ollama infrastructure.
· Abnormal request frequency or repeated failed model-management activity from the same source.
· Application-layer evidence that helps distinguish approved model administration from suspicious model-ingestion behavior.
Endpoint and Process Artifacts
Endpoint artifacts help validate whether suspicious network activity produced meaningful host-level effects.
· Ollama process execution on servers, developer systems, AI lab hosts, shared model infrastructure, or container hosts.
· Ollama service starts, stops, crashes, abnormal exits, restart loops, or service-manager restarts near suspicious model activity.
· Process-to-network activity from Ollama, an Ollama-associated container, or model-management automation to unfamiliar destinations.
· Ollama process activity outside expected runtime paths, service contexts, or administrative windows.
· Unexpected command-line context associated with model-management activity.
· Runtime behavior inconsistent with normal model loading, model refresh, model import, or approved experimentation.
File and Model Artifacts
File artifacts are important because suspicious model-ingestion activity may produce observable model storage changes.
· Creation, modification, movement, or deletion of files in Ollama model storage paths.
· New GGUF-related files, model manifests, blob storage changes, model metadata changes, or temporary model components.
· Model artifacts created outside approved administrative windows.
· Model-related files written to unusual locations outside approved model storage paths.
· Unusually large model artifacts or artifact changes that do not match approved model-management workflows.
· Container-mounted model volume changes associated with Ollama activity.
Runtime Instability Artifacts
Runtime instability should be treated as supporting evidence, not standalone proof of exploitation.
· Ollama process crashes near suspicious model-ingestion activity.
· Abnormal process restarts, service failures, model-loading errors, or crash-adjacent runtime anomalies.
· Memory pressure, resource exhaustion, or repeated failure patterns occurring near suspicious model-handling activity.
· Container restarts, service-supervisor restarts, or host-level fault messages near model artifact changes.
· Repeated model-ingestion failures from the same source against exposed infrastructure.
· Instability followed by outbound communication, artifact movement, or downstream credential activity.
Outbound Communication Artifacts
Outbound artifacts are high-value escalation evidence when they follow suspicious model-ingestion or artifact activity.
· Connections from the Ollama host, workload, or container to newly observed, rare, external, unapproved, anonymous hosting, file-sharing, cloud storage, or unknown model-registry destinations.
· Large outbound transfers after model-ingestion activity.
· DNS queries to unfamiliar domains after suspicious Ollama activity.
· Outbound activity outside approved model registry, update, telemetry, backup, or automation baselines.
· Repeated outbound connection attempts after model artifact creation or service instability.
· Egress behavior that differs from the host’s normal model-management pattern.
Identity and Credential Artifacts
Identity and credential artifacts are downstream indicators and require timeline validation.
· Unusual API token use after suspicious Ollama exposure.
· New access keys, service-account activity, role assumptions, application credential changes, or managed identity activity after the exposure window.
· Cloud API calls from unfamiliar infrastructure, geographies, ASNs, user agents, or automation contexts.
· Secret access, Key Vault activity, Secret Manager activity, credential-management anomalies, or repository access tied to the Ollama environment.
· Identity activity involving accounts, service accounts, tokens, repositories, secrets, or cloud resources associated with the exposed workload.
· Credential activity that occurs after suspicious model-ingestion, unusual egress, runtime instability, or confirmed unpatched exposure.
Artifact Usage Constraints
Artifacts should be used to build confidence through correlation.
· Do not treat the presence of Ollama as suspicious by itself.
· Do not treat public or broad exposure as confirmed compromise by itself.
· Do not treat runtime instability as exploitation by itself.
· Do not infer transmitted content from egress metadata alone.
· Do not infer credential theft from suspicious identity activity without investigation.
· Do not rely on static exploit strings, public proof-of-concept indicators, fixed model names, or specific file names as primary detection evidence.
· Escalation should require correlation across exposure, model-ingestion activity, artifact activity, instability, outbound movement, or downstream identity and credential activity.
S28 Detection Strategy and SOC Implementation Guidance
Figure 5
SOC Implementation Objective
SOC implementation should convert the detection strategy into a repeatable triage workflow that prioritizes exposed Ollama infrastructure, suspicious model-ingestion activity, model artifact changes, unusual outbound communication, and downstream credential or identity risk.
· Identify whether Ollama infrastructure was exposed to untrusted access.
· Determine whether model-ingestion or model-transfer activity occurred during the exposure window.
· Correlate host, container, file, runtime, network, identity, and credential-management evidence.
· Determine whether containment, upgrade validation, artifact review, credential rotation, or downstream hunting is required.
· Avoid treating any single event as confirmed compromise unless the evidence supports that conclusion.
Initial Triage Workflow
Triage should begin with exposure validation and service identification.
· Identify all Ollama servers, developer AI systems, AI lab hosts, shared model infrastructure, container hosts, and cloud-hosted model-serving workloads.
· Determine whether the Ollama service was internet-facing, broadly reachable, internally exposed, or reachable from untrusted network paths.
· Confirm whether the exposed service was patched, unpatched, unknown-state, or outside approved deployment inventory.
· Identify the owning team, deployment environment, access path, listening interface, public IP status, load balancer path, and expected administrative sources.
· Review inbound access from unfamiliar sources, external infrastructure, rare internal hosts, contractor networks, lab systems, or systems outside approved administrative paths.
Model-Ingestion Review Workflow
The SOC should next determine whether suspicious model lifecycle behavior occurred.
· Review route-level logs for model-ingestion, model import, blob handling, model artifact transfer, or model push activity.
· Review application, proxy, ingress, gateway, and load balancer logs where route-level visibility exists.
· Identify repeated model-management requests, large request bodies, abnormal timing, unusual user agents, or access from unapproved sources.
· Compare activity against approved model pulls, model imports, model refreshes, automation, testing, and maintenance windows.
· Treat untrusted model-ingestion activity against exposed or unpatched infrastructure as a high-priority investigation.
Host and Artifact Review Workflow
Host and artifact review should validate whether suspicious access produced observable local effects.
· Review endpoint telemetry for Ollama process activity, service restarts, process crashes, child-process behavior, and process-to-network activity.
· Review file telemetry for new or unusual model artifacts, GGUF-related files, manifest changes, blob storage changes, temporary model components, and writes outside approved model storage paths.
· Review container telemetry for container restarts, mounted volume changes, short-lived workload behavior, and container-to-host storage activity.
· Compare model artifact changes against approved model-management activity and expected model storage baselines.
· Escalate when model artifact changes occur near untrusted model-ingestion activity, runtime instability, unusual outbound communication, or suspicious identity activity.
Outbound Communication Review Workflow
Outbound communication should be reviewed after suspicious model-ingestion or model artifact activity.
· Review egress from the Ollama host, container, workload, or cloud resource during and after the suspicious activity window.
· Identify connections to unfamiliar destinations, unknown model registries, anonymous hosting, cloud storage, file-sharing services, newly observed domains, or destinations outside approved egress baselines.
· Review DNS queries, destination reputation, destination category, outbound byte volume, repeated connection attempts, and timing correlation.
· Compare outbound destinations against approved model registries, update sources, telemetry services, backup systems, and automation workflows.
· Do not infer data theft from egress metadata alone. Use outbound communication as escalation evidence requiring additional review.
Identity and Credential Review Workflow
Identity and credential review should be triggered when suspicious exposure, model-ingestion activity, artifact changes, unusual egress, or runtime instability is present.
· Review identity provider logs, cloud audit logs, repository access logs, credential-management logs, and service-account activity.
· Identify unusual API token use, new access keys, suspicious role assumptions, new service principal credentials, managed identity anomalies, Key Vault or Secret Manager access, repository access, and unusual cloud API calls.
· Correlate identity activity to Ollama workload owners, service accounts, repositories, secrets, cloud projects, subscriptions, accounts, and resource groups.
· Review activity from unfamiliar geographies, ASNs, user agents, source infrastructure, or automation contexts.
· Treat suspicious identity activity as downstream correlation evidence requiring analyst review, not standalone proof of credential theft.
Severity and Escalation Guidance
Escalation should be based on correlation strength and operational impact.
· Low severity should apply to isolated Ollama presence, local-only usage, or exposure without suspicious interaction.
· Medium severity should apply to exposed or broadly reachable Ollama infrastructure with untrusted access but limited supporting evidence.
· High severity should apply to untrusted model-ingestion activity against exposed or unpatched infrastructure with supporting artifact, instability, or outbound evidence.
· Critical severity should apply when suspicious exposure, model-ingestion activity, artifact changes, unusual egress, and downstream credential or identity activity align.
· Confirmed compromise should require evidence beyond exposure, such as validated unauthorized access, artifact transfer, credential misuse, or confirmed data exposure.
Containment and Response Guidance
Containment should be proportional to the evidence and exposure scope.
· Remove unapproved public or broad internal access to Ollama infrastructure.
· Restrict access to approved administrative sources, private networks, authenticated paths, or approved AI platform services.
· Validate upgrade status and confirm remediation across all exposed Ollama deployments.
· Preserve relevant logs before restarting, rebuilding, or deleting workloads.
· Review model artifacts created during the exposure window.
· Review outbound destinations and block confirmed unauthorized destinations where appropriate.
· Rotate credentials, tokens, service-account keys, API keys, repository tokens, and cloud secrets associated with the exposed environment when exposure and suspicious activity are confirmed.
· Hunt for downstream use of credentials, prompts, tool outputs, source code, or runtime context that may have been accessible to the exposed service.
Tuning and False Positive Reduction
Tuning should focus on baselines and approved workflows.
· Maintain an approved inventory of Ollama hosts, deployment environments, owners, listening interfaces, access paths, and expected users.
· Maintain approved administrative source lists and approved AI platform service lists.
· Maintain approved model registries, model storage paths, expected artifact sizes, model-management windows, and approved outbound destinations.
· Suppress approved model pulls, approved model imports, model refresh workflows, backups, migrations, monitoring, vulnerability scanning, container registry access, and authorized developer testing.
· Revisit tuning after new AI lab deployments, cloud migrations, developer platform changes, or model-management workflow changes.
SOC Handoff Requirements
Escalated cases should include enough context for incident response to validate exposure and downstream risk.
· Affected Ollama host, container, workload, account, subscription, project, or resource group.
· Exposure path, public IP status, firewall or security rule context, and approved-source comparison.
· Inbound source details, request timing, model-ingestion evidence, and route-level evidence where available.
· File and model artifact changes during the investigation window.
· Runtime instability, crashes, restarts, or abnormal service behavior.
· Outbound destination details, DNS activity, egress volume, and approved-destination comparison.
· Identity, credential, repository, cloud audit, or secret-management activity after the exposure window.
· Patch status, owner, containment status, and recommended next response action.
S29 Detection Coverage Summary
Coverage Summary
Detection coverage is strongest when the organization can correlate exposure, model-ingestion activity, endpoint or file activity, outbound communication, and downstream identity or credential activity.
· The rule set provides strong coverage for exposed Ollama infrastructure.
· The rule set provides strong coverage for suspicious model-ingestion activity where route-level logs are available.
· The rule set provides strong coverage for unusual outbound communication after model activity.
· The rule set provides strong endpoint coverage where SentinelOne, Elastic endpoint telemetry, or equivalent file and process visibility exists.
· The rule set provides strong cloud-native exposure coverage across AWS, AZURE, and GCP where inventory, tagging, flow logs, and identity telemetry are available.
· The rule set intentionally does not claim direct memory-disclosure detection.
Strong Coverage Areas
The strongest detection areas are durable behaviors that can be observed across multiple telemetry layers.
· Exposed Ollama infrastructure reachable from public, untrusted, or broad internal network paths.
· Untrusted access to model-ingestion or model-transfer functionality.
· Suspicious model lifecycle behavior from unfamiliar sources or outside approved administrative workflows.
· Model artifact creation or modification near suspicious model-ingestion activity.
· Unusual outbound communication to unfamiliar, rare, unapproved, anonymous, cloud storage, file-sharing, or unknown model-registry destinations.
· Downstream credential, identity, service-account, cloud-control, repository, or secret-management activity after suspicious exposure.
· Cloud-hosted exposure in AWS, AZURE, and GCP environments.
Moderate Coverage Areas
Moderate coverage areas depend heavily on telemetry quality and environment maturity.
· Runtime instability near suspicious model activity.
· Internal access to shared Ollama infrastructure by unfamiliar internal hosts.
· Containerized Ollama workload behavior in short-lived or ephemeral environments.
· Model artifact changes where file telemetry is incomplete.
· Route-level activity where Ollama is directly exposed without reverse proxy, gateway, ingress, load balancer, or application logs.
· Downstream identity activity where asset-to-identity mapping is incomplete.
Limited Coverage Areas
Limited coverage areas should be clearly understood during triage.
· Direct memory disclosure is not directly detected by the rule set.
· Transmitted content cannot be determined from flow metadata alone.
· Model artifact intent cannot be determined from file creation alone.
· Runtime instability cannot be treated as exploitation without supporting evidence.
· Credential theft cannot be confirmed from downstream identity anomalies without analyst review.
· YARA does not provide primary detection coverage because the detection problem is behavioral rather than static-file based.
Coverage by Telemetry Layer
Network analytics provides strong exposure, inbound source, destination novelty, egress, and east-west visibility.
· Best coverage: exposure, untrusted inbound access, unusual egress, internal access anomalies, destination novelty, large outbound movement.
· Key dependency: service identification, asset tagging, DNS visibility, destination classification, and egress baselining.
· Main limitation: network telemetry does not directly observe local model artifact creation, runtime memory state, or credential use.
Endpoint telemetry provides strong host-level validation.
· Best coverage: Ollama process behavior, model artifact writes, runtime instability, process-to-network mapping, file activity, container-adjacent host behavior.
· Key dependency: endpoint coverage, process lineage, file telemetry, host-role tagging, and model storage path baselining.
· Main limitation: endpoint telemetry does not reliably provide route-level model-ingestion context without proxy or application enrichment.
SIEM correlation provides the broadest cross-source detection coverage.
· Best coverage: multi-stage correlation across exposure, route access, artifact activity, outbound communication, identity activity, credential-management activity, and asset context.
· Key dependency: normalized data, reliable host identity joins, lookup quality, source baselines, destination baselines, and retained telemetry.
· Main limitation: correlation is only as strong as the ingested sources and field normalization.
Portable SIGMA logic provides reusable detection patterns.
· Best coverage: route-access logic, model artifact file activity, and unusual outbound destination logic.
· Key dependency: backend translation, field mapping, exception handling, and SIEM-specific correlation.
· Main limitation: SIGMA is not a complete correlation engine by itself.
Cloud-native telemetry provides strong exposure and identity coverage.
· Best coverage: public exposure, permissive network paths, cloud workload egress, IAM or identity anomalies, credential activity, service-account activity, and cloud audit trails.
· Key dependency: asset tagging or labeling, workload mapping, flow logging, cloud audit logging, identity logging, and credential-management telemetry.
· Main limitation: cloud-native telemetry does not directly observe endpoint model-loader behavior unless workload, endpoint, container, or application telemetry is collected.
Coverage by System Group
Group 1
NDR / Network Behavioral Analytics
· Coverage strength: Strong.
· Best coverage: exposed service access, untrusted source behavior, unusual outbound communication, large egress, internal access anomalies, east-west behavior.
· Primary limitation: cannot confirm local model artifact creation, process crashes, memory disclosure, or credential use without enrichment.
SentinelOne
· Coverage strength: Strong with endpoint coverage.
· Best coverage: model artifact writes, runtime instability, process-to-network behavior, host-level correlation.
· Primary limitation: cannot confirm route-level model-ingestion activity or transmitted content without proxy, application, or network telemetry.
Splunk
· Coverage strength: Strong.
· Best coverage: multi-source correlation, route-level access, artifact activity, egress, identity activity, credential-management activity, asset and patch context.
· Primary limitation: depends on normalized data, reliable host identity joins, and complete source ingestion.
Group 2
Elastic
· Coverage strength: Strong with normalized telemetry.
· Best coverage: route-level access, endpoint artifact activity, endpoint-network behavior, sequence detection, and cloud or identity enrichment where ingested.
· Primary limitation: depends on ECS mapping quality, retained telemetry, and host identity correlation.
QRadar
· Coverage strength: Strong with custom properties and reference sets.
· Best coverage: offense correlation, route-level access, outbound flow behavior, identity activity, asset context, and vulnerability context.
· Primary limitation: depends on custom property extraction, reference set quality, and asset-role accuracy.
SIGMA
· Coverage strength: Moderate to strong after backend translation and tuning.
· Best coverage: portable web, endpoint file, and network detection logic.
· Primary limitation: backend-specific field mapping and correlation are required.
YARA
· Coverage strength: Not applicable for primary detection.
· Best coverage: controlled internal research after a confirmed suspicious artifact is available.
· Primary limitation: static model-file matching is not durable for this report’s behavioral detection model.
Group 3
AWS
· Coverage strength: Strong with AWS logging and workload mapping.
· Best coverage: AWS-hosted exposure, unusual egress, IAM activity, access key activity, role activity, and credential activity after exposure.
· Primary limitation: does not provide endpoint-level model-loader visibility without endpoint, workload, container, or application telemetry.
AZURE
· Coverage strength: Strong with Azure logging and workload mapping.
· Best coverage: Azure-hosted exposure, unusual egress, Microsoft Entra ID activity, managed identity activity, service principal activity, and Key Vault activity after exposure.
· Primary limitation: does not provide endpoint-level model-loader visibility without endpoint, workload, container, or application telemetry.
GCP
· Coverage strength: Strong with GCP logging and workload mapping.
· Best coverage: GCP-hosted exposure, unusual egress, IAM activity, service-account activity, Secret Manager activity, and cloud audit activity after exposure.
· Primary limitation: does not provide endpoint-level model-loader visibility without endpoint, workload, container, or application telemetry.
Coverage Conclusion
The detection coverage is strong for the durable behaviors that matter most: exposure, suspicious model-ingestion activity, artifact activity, unusual outbound communication, and downstream identity or credential activity.
The remaining detection gaps are expected and should be managed through telemetry improvement, exposure reduction, access control, egress baselining, credential review, and incident-response playbooks.
S30 Intelligence Maturity Assessment
Maturity Assessment Summary
The intelligence maturity for this report is moderate to high for behavioral detection and moderate for direct technical confirmation. The report benefits from a durable behavioral model, but confidence depends on telemetry quality, deployment visibility, and the organization’s ability to correlate across network, endpoint, application, cloud, and identity data.
· The issue is suitable for behavior-led detection.
· The strongest intelligence value comes from exposure validation, model-ingestion context, artifact activity, egress behavior, and downstream identity review.
· Direct confirmation of memory disclosure remains difficult without strong supporting evidence.
· Intelligence maturity improves significantly when telemetry is centralized, normalized, retained, and mapped to asset ownership.
Analytic Confidence
Analytic confidence is moderate to high for identifying exposed and suspiciously accessed Ollama infrastructure.
· Confidence is high when exposed Ollama infrastructure is confirmed and route-level model-ingestion activity is visible.
· Confidence is high when suspicious model-ingestion activity is followed by model artifact changes and unusual outbound communication.
· Confidence is moderate when only flow-level network telemetry is available.
· Confidence is moderate when runtime instability is present without endpoint, application, or artifact context.
· Confidence is lower when Ollama runs on unmanaged developer systems, temporary cloud instances, lab hosts, or short-lived containers without centralized logging.
Detection Intelligence Maturity
Detection intelligence maturity is strong when defenders use a correlation-led approach.
· Mature detection focuses on exposed AI model-serving infrastructure, not generic web exploitation.
· Mature detection avoids static exploit strings, public proof-of-concept artifacts, fixed file names, or one-off indicators.
· Mature detection correlates exposure, model-ingestion activity, artifact activity, runtime instability, outbound communication, and downstream identity activity.
· Mature detection distinguishes approved model management from suspicious model-ingestion behavior.
· Mature detection accounts for partial telemetry and uses compensating sources where direct application logs are unavailable.
Telemetry Maturity
Telemetry maturity determines whether the organization can move from exposure identification to credible incident assessment.
· Low telemetry maturity means the organization can identify exposure but may not confirm suspicious model-ingestion activity.
· Moderate telemetry maturity means the organization can correlate network access with endpoint, file, or egress telemetry.
· High telemetry maturity means the organization can correlate route-level access, endpoint artifacts, runtime behavior, egress, identity, cloud audit, and credential-management activity.
· Very high telemetry maturity includes reliable asset-to-identity mapping, approved source baselines, approved destination baselines, model storage baselines, and retained investigation windows.
Operational Maturity
Operational maturity depends on whether teams can identify, contain, and review self-hosted AI infrastructure quickly.
· Mature organizations maintain an inventory of Ollama hosts, owners, environments, access paths, exposed ports, and expected users.
· Mature organizations restrict model-serving infrastructure to approved access paths and authenticated administrative workflows.
· Mature organizations monitor model artifact storage, outbound destinations, and model-management workflows.
· Mature organizations retain logs long enough to support exposure review, patch validation, credential rotation, and downstream identity investigation.
· Mature organizations can coordinate SOC, infrastructure, cloud, endpoint, identity, and AI platform teams during triage.
Threat Intelligence Maturity
Threat intelligence maturity is strongest when the report is treated as an AI infrastructure exposure issue rather than only a software vulnerability issue.
· Intelligence should track exposed AI model infrastructure patterns.
· Intelligence should track suspicious model-ingestion behavior.
· Intelligence should track attacker interest in self-hosted model servers, developer AI tooling, AI labs, and cloud-hosted model-serving infrastructure.
· Intelligence should track downstream risk to prompts, tokens, environment variables, source code, tool outputs, repository access, and cloud credentials.
· Intelligence should avoid overfitting to public proof-of-concept artifacts or static vulnerability references.
Control Maturity
Control maturity is strongest when exposure reduction and telemetry hardening are implemented together.
· Access controls should limit Ollama access to approved administrative sources, internal AI platform services, and authenticated workflows.
· Network controls should restrict public access, broad internal access, and unmanaged lab exposure.
· Egress controls should limit outbound communication to approved model registries, update sources, telemetry services, backup paths, and automation destinations.
· Endpoint and container controls should monitor model artifact paths, runtime instability, and process-to-network behavior.
· Identity controls should support rapid credential review, token rotation, service-account validation, and cloud audit investigation.
Maturity Gaps
The main maturity gaps are visibility, ownership, and correlation.
· Self-hosted AI systems may exist outside formal asset inventory.
· Developer and lab deployments may not have centralized logging.
· Route-level visibility may be missing when Ollama is directly exposed.
· Endpoint or container telemetry may not cover all AI infrastructure.
· Approved model sources, model storage paths, and outbound destinations may not be baselined.
· Asset-to-identity mapping may be incomplete.
· Credential-management and repository telemetry may not be integrated into SOC workflows.
Maturity Improvement Priorities
Near-term maturity improvements should focus on practical visibility and containment.
· Inventory all Ollama deployments and identify owners.
· Remove unapproved public exposure and broad internal reachability.
· Enforce authenticated and approved access paths.
· Enable route-level logging through reverse proxy, ingress, gateway, load balancer, or application telemetry.
· Enable endpoint, container, file, DNS, egress, and identity telemetry for AI model-serving infrastructure.
· Baseline approved model registries, model storage paths, model-management workflows, and outbound destinations.
· Create incident-response guidance for exposed AI model infrastructure, including patch validation, artifact review, credential rotation, and downstream hunting.
Maturity Rating
Overall intelligence maturity is moderate to high.
· Behavioral detection maturity: High.
· Direct memory-disclosure confirmation maturity: Moderate to low.
· Network and cloud exposure maturity: High where logging and inventory are available.
· Endpoint and model artifact maturity: Moderate to high where endpoint or container telemetry is available.
· Identity and credential follow-on maturity: Moderate to high where asset-to-identity mapping and credential-management logs are available.
· Static artifact detection maturity: Low and not recommended as the primary detection model.
Maturity Conclusion
This report has a mature behavioral detection model and a realistic intelligence posture. The strongest value comes from identifying exposed self-hosted AI model infrastructure, detecting suspicious model-ingestion activity, correlating model artifact and outbound behavior, and reviewing downstream identity or credential activity.
The primary maturity limitation is not analytic quality. The primary limitation is telemetry completeness across self-hosted AI infrastructure, especially developer systems, lab environments, temporary cloud workloads, and containerized deployments.
S31 — Telemetry Dependencies
Primary Telemetry Dependencies
Ollama exposure detection depends on the ability to correlate service reachability, model lifecycle activity, artifact behavior, runtime instability, outbound communication, and downstream credential or identity activity. No single telemetry source should be treated as sufficient for confirmed compromise.
Required telemetry dependencies include:
· Asset inventory identifying Ollama servers, self-hosted AI model servers, AI lab systems, developer AI infrastructure, shared model infrastructure, container hosts, and cloud-hosted model-serving workloads.
· Exposure management data showing whether Ollama services are internet-facing, broadly reachable internally, reachable from untrusted paths, or outside approved deployment inventory.
· Patch and vulnerability context for Ollama infrastructure.
· Reverse proxy, ingress, API gateway, load balancer, or application logs where available.
· Endpoint process telemetry showing Ollama process execution, service activity, runtime behavior, process restarts, crashes, and host-level network activity.
· File telemetry covering model storage paths, model manifests, blob storage, temporary model components, model artifacts, and writes outside approved model paths.
· Container telemetry for Docker, Kubernetes, container runtime, container restart, mounted volume, and short-lived workload activity.
· Network telemetry showing inbound access, source novelty, destination identity, traffic timing, session volume, internal access, and outbound communication.
· DNS, proxy, firewall, NDR, and egress telemetry showing unfamiliar destinations, newly observed domains, unusual egress, model-registry-like destinations, cloud-storage services, file-sharing services, and anonymous-hosting infrastructure.
· Identity, cloud, repository, CI, internal API, secrets-management, and credential-management telemetry to evaluate downstream credential or token use.
Minimum Viable Telemetry
· Ollama asset inventory.
· Exposure state.
· Patch state.
· Inbound access records.
· Host or container process telemetry.
· Model artifact or file-system telemetry.
· Outbound network visibility.
· Identity or credential-management telemetry for systems connected to sensitive workflows.
Preferred Telemetry
· Route-level request visibility for model-ingestion, model-import, blob, artifact-handling, and model-push functionality.
· Endpoint and container telemetry tied to the Ollama process or workload.
· Model storage baselines, approved model sources, approved administrative sources, and expected outbound destinations.
· DNS and egress telemetry correlated to host, process, container, or workload identity.
· Repository, cloud, CI, service-account, API-token, and secrets-management logs mapped to affected Ollama hosts and users.
· Retention sufficient to cover the exposure window, remediation window, credential-rotation window, and downstream credential-review window.
Telemetry Dependency Risk
Detection confidence decreases when Ollama runs outside managed production environments, when services are directly exposed without fronting infrastructure, when model storage paths are not monitored, when egress is broadly allowed, or when exposed hosts are not mapped to owners, service accounts, cloud roles, repositories, or automation workflows.
S32 — Detection Limitations
Exposure Does Not Equal Compromise
Exposure of an Ollama service should trigger urgent review, but it should not be classified as confirmed compromise without suspicious service interaction or follow-on evidence. Public or broad reachability establishes risk. Suspicious model lifecycle activity, artifact changes, runtime instability, outbound communication, or downstream credential use increases confidence.
Memory Disclosure May Not Be Directly Observable
The central risk involves sensitive runtime context, but most environments will not have direct memory visibility. Detection must rely on practical supporting evidence such as suspicious model-ingestion activity, artifact behavior, crashes, process restarts, outbound communication, and downstream credential activity.
Application Visibility May Be Incomplete
Native Ollama logs may not provide complete route-level visibility. When Ollama is directly exposed or deployed in developer environments, defenders may lack request path, request body size, authentication context, source enrichment, or response metadata.
Developer and AI Lab Activity Can Resemble Suspicious Behavior
Approved model experimentation, model pulls, model imports, model pushes, automation, testing, patching, backups, monitoring, and vulnerability scanning may overlap with suspicious activity. Strong ownership, approved-source baselines, approved model registries, and maintenance-window context are required to reduce false positives.
Container and Cloud Deployments May Obscure Evidence
Containerized or cloud-hosted deployments may obscure host paths, process lineage, mounted volumes, short-lived runtime activity, source identity, egress identity, and artifact persistence unless container and cloud telemetry are retained.
Network Telemetry Alone Is Insufficient
Network telemetry can identify exposure, inbound access, outbound communication, and destination novelty, but it cannot confirm model artifact creation, memory disclosure, local file activity, process instability, credential exposure, or data content without enrichment.
Endpoint Telemetry Alone Is Insufficient
Endpoint telemetry can identify file activity, process behavior, runtime instability, and process-to-network activity, but it may not confirm the original model-serving request, source access path, route-level behavior, or external destination context without proxy, network, or application telemetry.
Downstream Credential Use May Be Delayed
If runtime context included credentials, API tokens, repository tokens, cloud keys, or service-account material, follow-on use may occur later, from different infrastructure, or through legitimate-looking access paths. Detection requires identity, cloud, repository, and credential-management review beyond the Ollama host itself.
S33 — Defensive Control & Hardening Improvements
Exposure Reduction
· Remove internet-facing or broadly reachable Ollama services unless explicitly approved.
· Restrict Ollama access to trusted administrative sources, approved AI platform services, and defined internal consumers.
· Place shared Ollama infrastructure behind authenticated reverse proxies, ingress controls, VPN, service mesh, or controlled internal gateways.
· Block direct untrusted access to Ollama ports and model-serving APIs.
· Enforce segmentation around AI lab systems, developer model servers, shared model infrastructure, and cloud-hosted model workloads.
Patch and Version Control
· Validate Ollama version state across servers, developer systems, containers, cloud workloads, and lab environments.
· Prioritize patching or mitigation for internet-facing, shared, sensitive, or untrusted-reachable deployments.
· Track patch completion with asset inventory, exposure state, and owner accountability.
· Retire or isolate unowned, temporary, unmanaged, or proof-of-concept Ollama deployments.
Authentication and Access Control
· Require authentication for shared or remotely reachable Ollama deployments.
· Restrict administrative model-management actions to approved users, service accounts, automation identities, and source networks.
· Enforce least privilege for systems connected to repositories, cloud services, CI pipelines, internal APIs, secrets stores, or customer workflows.
· Disable unnecessary model-push, model-import, or remote model-management paths where not required.
Model Lifecycle Controls
· Maintain approved model sources, approved model registries, approved model storage paths, and expected model artifact baselines.
· Monitor model-ingestion, model-import, artifact-handling, blob, and model-push activity.
· Alert on model lifecycle activity from untrusted sources, unfamiliar internal hosts, unusual timing, or unapproved destinations.
· Review new or unusual model files, manifest changes, temporary model components, and writes outside approved model paths.
Egress and Destination Controls
· Establish approved outbound destinations for model registries, updates, telemetry, backups, monitoring, and container registries.
· Restrict outbound communication from Ollama hosts and containers to approved destinations where feasible.
· Alert on large egress, newly observed destinations, low-prevalence domains, cloud-storage services, file-sharing services, anonymous-hosting infrastructure, and unknown model-registry destinations.
· Tie egress telemetry back to host, process, container, and workload identity.
Credential and Secret Protection
· Remove credentials, API tokens, repository tokens, cloud keys, and sensitive environment variables from Ollama runtime environments wherever possible.
· Use secrets-management systems rather than local environment variables, shell history, local configuration files, or developer-managed secrets.
· Rotate credentials associated with exposed or suspicious Ollama infrastructure when sensitive runtime context may have been present.
· Review downstream use of credentials, service accounts, cloud keys, repository tokens, and automation secrets after suspicious exposure.
Telemetry and Monitoring Improvements
· Deploy route-level visibility through reverse proxies, ingress controllers, API gateways, or load balancers where possible.
· Enable endpoint telemetry on Ollama servers, developer AI systems, lab systems, shared infrastructure, and container hosts.
· Monitor model storage paths, temporary directories, container-mounted volumes, and artifact repositories.
· Retain DNS, proxy, firewall, NDR, cloud, identity, repository, CI, and credential-management logs long enough to support downstream review.
· Maintain baselines for approved administrative sources, approved model sources, approved model paths, expected model artifact sizes, and expected outbound destinations.
S34 — Defensive Control & Hardening Architecture
Figure 6
Recommended Architecture
Ollama infrastructure should be treated as a managed AI service layer rather than an unmanaged developer utility. The target defensive architecture should reduce exposure, control model lifecycle actions, isolate sensitive workflows, preserve telemetry, and support downstream credential review.
Access Layer
Ollama services should not be directly reachable from the internet or broad internal networks. Access should pass through controlled ingress paths such as reverse proxies, API gateways, service mesh controls, VPN, or internal access brokers. These controls should enforce authentication, source restrictions, request logging, rate limiting, and route-level visibility where feasible.
Segmentation Layer
Ollama hosts, AI lab servers, shared model infrastructure, developer AI systems, and cloud-hosted model workloads should be segmented based on sensitivity. Systems connected to repositories, CI pipelines, cloud services, customer workflows, internal APIs, or secrets should receive stricter isolation than local-only experimentation environments.
Model Lifecycle Control Layer
Model ingestion, model import, artifact handling, blob activity, and model-push behavior should be governed by approved sources, approved users, approved automation, approved storage paths, and approved outbound destinations. Model artifact creation and modification should be monitored and baselined.
Runtime and Host Monitoring Layer
Endpoint and container telemetry should monitor Ollama process behavior, service starts and stops, process restarts, crash behavior, abnormal memory pressure, model-loading errors, file writes, mounted volumes, and process-to-network activity. Runtime instability should be correlated with suspicious model lifecycle activity rather than treated as standalone compromise evidence.
Egress Control Layer
Outbound communication from Ollama hosts and containers should be restricted and monitored. Approved destinations should include only necessary model registries, update services, monitoring systems, backup systems, container registries, and enterprise automation. Newly observed, rare, unapproved, cloud-storage, file-sharing, anonymous-hosting, or unknown model-registry destinations should trigger investigation when linked to suspicious model activity.
Credential Protection Layer
Ollama runtime environments should be kept free of unnecessary credentials, API tokens, repository tokens, cloud keys, service-account material, and sensitive environment variables. Where secrets are required, they should be managed through controlled secret stores with audit logging, least privilege, rotation capability, and downstream usage monitoring.
Correlation and Response Layer
SIEM and SOC workflows should correlate exposure state, patch state, inbound service interaction, model lifecycle activity, artifact behavior, runtime instability, outbound communication, and downstream credential or identity activity. Confirmed or strongly suspected cases should trigger containment, patch validation, artifact review, credential review, prompt and data exposure assessment, and downstream hunting.
S35 — Defensive Control Mapping Matrix
Exposure Management
Control Objective
Identify and reduce unsafe Ollama reachability.
Mapped Controls
· Maintain an inventory of Ollama hosts, cloud workloads, containers, lab systems, shared model servers, and developer deployments.
· Identify internet-facing, untrusted-reachable, broadly reachable, or unapproved Ollama services.
· Remove unnecessary exposure and restrict access to approved sources.
Detection / Validation Focus
· Asset inventory.
· Exposure management.
· Listening ports.
· Network reachability.
· Source access baselines.
· Patch state.
Access Control
Control Objective
Prevent untrusted users or systems from interacting with model-serving functionality.
Mapped Controls
· Require authentication for shared or remote Ollama access.
· Restrict administrative and model-management functionality.
· Enforce source restrictions and approved administrative paths.
· Separate local experimentation from shared or production AI infrastructure.
Detection / Validation Focus
· Reverse proxy logs.
· Ingress logs.
· Authentication records.
· Administrative source baselines.
· Model-management activity.
Model Lifecycle Governance
Control Objective
Control and monitor model ingestion, artifact handling, model import, blob activity, and model-push behavior.
Mapped Controls
· Define approved model sources and approved model registries.
· Baseline expected model artifact sizes, paths, and update frequency.
· Monitor model storage paths and temporary model-ingestion directories.
· Review suspicious model artifacts and abnormal writes.
Detection / Validation Focus
· File telemetry.
· Model storage monitoring.
· Endpoint telemetry.
· Container-mounted volume telemetry.
· Artifact review.
Runtime Protection
Control Objective
Detect abnormal Ollama process, service, and container behavior.
Mapped Controls
· Monitor Ollama crashes, process restarts, service instability, memory pressure, model-loading errors, and container restarts.
· Correlate runtime anomalies with suspicious model-service interaction.
· Suppress known approved maintenance, upgrades, redeployments, and lab testing.
Detection / Validation Focus
· Endpoint telemetry.
· Process lifecycle events.
· Crash and fault logs.
· Container runtime logs.
· Service-manager activity.
Egress Control
Control Objective
Detect and restrict suspicious outbound communication from Ollama infrastructure.
Mapped Controls
· Establish approved outbound destinations.
· Monitor large egress, rare destinations, cloud-storage destinations, file-sharing services, unknown model registries, and anonymous-hosting infrastructure.
· Correlate outbound communication with model lifecycle activity.
Detection / Validation Focus
· DNS logs.
· Proxy logs.
· Firewall logs.
· NDR telemetry.
· Egress volume monitoring.
· Destination reputation.
Credential and Secret Protection
Control Objective
Reduce downstream impact if runtime context is exposed.
Mapped Controls
· Remove unnecessary secrets from Ollama runtime environments.
· Use managed secret stores.
· Restrict service-account and cloud-role permissions.
· Rotate credentials associated with suspicious exposure.
· Monitor downstream use of tokens, keys, and service accounts.
Detection / Validation Focus
· Secrets-management logs.
· Identity logs.
· Cloud audit logs.
· Repository access logs.
· CI/CD logs.
· API-token usage.
Incident Response Readiness
Control Objective
Support rapid scoping, containment, and downstream review.
Mapped Controls
· Define playbooks for exposed Ollama infrastructure.
· Preserve logs across exposure, patch, credential-rotation, and downstream-review windows.
· Contain affected hosts or containers when suspicious model activity is confirmed.
· Review prompt, data, artifact, credential, repository, cloud, and identity exposure.
Detection / Validation Focus
· SIEM correlation.
· Timeline reconstruction.
· Artifact review.
· Credential review.
· Cloud and repository review.
· Executive incident governance.
S36 — CyberDax Intelligence Maturity Assessment
CyberDax Intelligence Maturity Rating
Moderate.
Assessment Summary
CyberDax intelligence maturity for this threat is assessed as moderate because the exposure pathway is clear, but confirmation depends heavily on telemetry quality, ownership mapping, and downstream credential review. The technical risk is understandable: exposed Ollama infrastructure may receive suspicious model lifecycle activity that creates sensitive runtime context, artifact, outbound communication, or credential-use risk. The operational challenge is determining whether the organization can validate exposure, reconstruct activity, assess sensitive runtime context, and confirm or rule out downstream use of exposed credentials or tokens.
A mature posture requires more than identifying Ollama exposure. It requires linking asset inventory, exposure state, patch status, model lifecycle activity, artifact behavior, runtime instability, outbound communication, identity activity, cloud logs, repository logs, and credential-management telemetry into a defensible investigation timeline.
Maturity by Intelligence Function
Exposure Intelligence
High when asset inventory and exposure-management coverage are reliable.
Organizations can identify exposed Ollama services, listening ports, internet-facing deployments, broadly reachable internal systems, and unapproved model-serving infrastructure when inventory and scanning programs are mature.
Behavioral Detection Intelligence
Moderate to High when telemetry correlation is available.
The core behavioral pattern is durable: exposed service access, model lifecycle activity, artifact anomalies, runtime instability, outbound communication, and downstream credential use. Detection maturity depends on whether these signals can be correlated across host, network, application, container, file, identity, cloud, repository, and credential-management telemetry.
Runtime Exposure Intelligence
Moderate to Low in most environments.
Direct proof of memory disclosure may be difficult. Maturity depends on supporting evidence, including model activity timelines, artifact review, runtime instability, credential presence, prompt and data exposure assessment, and downstream usage review.
Model Lifecycle Intelligence
Moderate.
Maturity depends on whether the organization has approved model sources, approved model registries, expected model storage paths, expected model artifact sizes, model-management baselines, and visibility into model-ingestion or model-push behavior.
Downstream Credential Intelligence
Moderate.
Downstream intelligence is strongest when Ollama hosts are mapped to users, repositories, service accounts, cloud roles, CI systems, secrets, automation workflows, and credential stores. It is weaker when developer deployments are unmanaged or credential-management logs are incomplete.
Operational Response Intelligence
Moderate.
Response maturity improves when teams can identify affected hosts, owners, exposure windows, model activity, artifact changes, outbound destinations, linked credentials, and connected workflows. Response maturity decreases when telemetry retention, ownership mapping, and downstream identity correlation are incomplete.
CyberDax Maturity Constraints
· Direct memory-disclosure evidence may be unavailable.
· Ollama deployments may exist on developer workstations, AI lab servers, temporary cloud workloads, unmanaged hosts, or containers with inconsistent telemetry.
· Legitimate model experimentation can resemble suspicious model lifecycle activity.
· Downstream impact may occur outside the Ollama host if exposed credentials, API tokens, cloud keys, repository tokens, or automation secrets are later used elsewhere.
· A clean telemetry review does not prove absence of exposure when route-level logging, endpoint telemetry, egress monitoring, identity records, or credential-management logs are incomplete.
CyberDax Maturity Improvement Priorities
· Improve Ollama asset inventory and ownership mapping.
· Establish approved access paths and approved administrative sources.
· Baseline model lifecycle behavior, model sources, model storage paths, and outbound destinations.
· Improve route-level request visibility for exposed or shared Ollama infrastructure.
· Correlate model activity with endpoint, container, file, DNS, egress, identity, cloud, repository, and credential-management telemetry.
· Map Ollama infrastructure to repositories, cloud roles, service accounts, CI systems, secrets, and automation workflows.
· Define incident response playbooks for exposed AI infrastructure and sensitive runtime context exposure.
· Retain telemetry long enough to support downstream credential-use review after exposure.
S37 — Strategic Defensive Improvements
Strategic Priority 1 — Govern Self-Hosted AI as Enterprise Infrastructure
Ollama and comparable self-hosted model-serving systems should be governed as enterprise infrastructure when they process prompts, source code, credentials, customer data, tool outputs, or automation context. Strategic ownership should include inventory, business owner assignment, exposure approval, access control, telemetry requirements, secrets handling, and incident-response accountability.
Strategic Priority 2 — Establish an AI Infrastructure Exposure Standard
Organizations should create a standard that defines where self-hosted AI services may run, who may administer them, which networks may reach them, what authentication is required, which telemetry must be collected, and when exposure must be removed or escalated.
Strategic Priority 3 — Centralize Model Lifecycle Governance
Security and platform teams should define approved model sources, model registries, model storage locations, model-management workflows, and artifact baselines. This reduces ambiguity between legitimate experimentation and suspicious model lifecycle behavior.
Strategic Priority 4 — Build Egress Governance for AI Workloads
Self-hosted AI infrastructure should not have unrestricted outbound access by default. Strategic controls should define approved model registries, update services, cloud destinations, telemetry paths, container registries, and automation endpoints. Egress outside approved baselines should be investigated when linked to suspicious model activity.
Strategic Priority 5 — Reduce Runtime Secret Exposure
Organizations should reduce the presence of credentials, API tokens, repository tokens, cloud keys, service-account material, and sensitive environment variables in AI runtime environments. Long-term improvement should prioritize managed secret stores, least privilege, audit logging, rotation readiness, and clear ownership of service accounts connected to AI workflows.
Strategic Priority 6 — Improve AI-to-Enterprise Dependency Mapping
Security teams should map Ollama infrastructure to repositories, CI systems, cloud roles, internal APIs, customer workflows, service accounts, secrets, and automation platforms. This allows faster scoping when runtime context exposure is suspected.
Strategic Priority 7 — Standardize AI Exposure Response
Organizations should maintain a response playbook for exposed AI infrastructure. The playbook should define how to validate exposure, preserve logs, remove unsafe access, confirm patch state, review model artifacts, assess prompt and data exposure, rotate credentials, contain affected hosts or containers, and hunt for downstream credential use.
Strategic Priority 8 — Keep Detection Behavior-Led
Strategic detection should remain anchored to durable behavior rather than static indicators. The most resilient model is the sequence of exposed AI model infrastructure, untrusted service interaction, suspicious model lifecycle activity, artifact anomalies, runtime instability, outbound communication, and downstream credential or identity activity.
S38 — Attack Economics & Organizational Impact Model
Figure 7
Adversary Cost Advantage
Ollama AI Infrastructure Exposure Memory Disclosure Risk in Self-Hosted Model Servers creates favorable attacker economics because the exposed asset may be a self-hosted AI model service reachable from the internet, untrusted internal networks, shared AI lab environments, developer systems, or cloud-hosted workloads. Attackers do not need to begin with broad enterprise intrusion if exposed model-serving functionality is reachable and vulnerable.
The attacker advantage comes from the combination of exposed service reachability, model lifecycle functionality, sensitive runtime context, and potential downstream credential value. A single exposed model-serving system may process prompts, source code, API tokens, environment variables, tool outputs, customer data, repository context, cloud context, or automation outputs. This can create high leverage from limited initial interaction.
Defender Cost Disadvantage
Defenders face elevated cost because remediation is not limited to patching or removing exposure. Affected organizations must validate exposure history, confirm patch state, preserve logs, review model lifecycle activity, inspect model artifacts, analyze outbound communication, assess prompt and data exposure, evaluate credential risk, and hunt for downstream use of exposed tokens or secrets.
The defender burden increases when Ollama deployments are informal, unmanaged, temporary, containerized, cloud-hosted, or developer-owned. These environments may lack complete ownership records, route-level logs, endpoint telemetry, model artifact baselines, egress controls, or credential-management visibility.
Operational Leverage for Attackers
Successful exploitation or strongly suspected abuse can create outsized organizational impact because the affected system may sit at the intersection of AI workflows, developer activity, sensitive prompts, source code, cloud services, repositories, CI systems, internal APIs, customer workflows, and automation tools.
The highest leverage does not come from the model server alone. It comes from what the model server processed, what credentials or secrets were present in runtime context, what repositories or cloud services were connected, and whether outbound communication or downstream credential activity occurred during or after the exposure window.
Organizational Impact Model
Low impact occurs when affected Ollama services were patched or mitigated quickly, were not reachable from untrusted networks, showed no suspicious model-ingestion activity, produced no unusual artifacts, showed no runtime instability, had no abnormal outbound communication, and had no downstream credential, repository, cloud, or identity activity indicating misuse.
Moderate impact occurs when one or more Ollama servers were vulnerable, unpatched, internet-facing, broadly reachable, or accessible through untrusted internal paths, and investigation identifies suspicious model-ingestion activity, unusual model artifact handling, runtime instability, rare outbound communication, model-push behavior, incomplete telemetry, or limited downstream credential concern without confirmed large-scale data exposure, sustained adversary control, or broad cloud, repository, or customer-data impact.
High impact occurs when confirmed or strongly suspected exposure affects Ollama infrastructure connected to sensitive prompts, proprietary source code, customer data, credentials, API tokens, environment variables, cloud services, repositories, CI systems, internal APIs, or shared AI workflows, with evidence of suspicious model-ingestion activity, abnormal artifact creation, runtime instability, unusual outbound communication, model-push behavior, credential use, repository access, cloud activity, or incomplete historical telemetry.
Economic Pressure Points
· Number of affected Ollama servers, self-hosted AI model servers, shared AI lab systems, developer workstations, container hosts, and cloud-hosted model-serving workloads.
· Exposure duration before patch validation, access restriction, service isolation, or compensating control deployment.
· Whether affected environments processed proprietary source code, customer data, credentials, API tokens, secrets, tool outputs, regulated information, or sensitive internal prompts.
· Whether suspicious model-ingestion, model import, artifact handling, model-push, or model-transfer behavior occurred before remediation.
· Whether suspicious activity was followed by new model artifacts, model storage changes, runtime instability, or outbound communication.
· Scope of credentials, API tokens, repository access tokens, cloud credentials, service-account keys, environment variables, secrets, or tool outputs potentially present in the Ollama runtime environment.
· Whether affected systems were connected to coding assistants, CI systems, cloud accounts, internal APIs, customer-support workflows, developer repositories, or automation tools.
· Availability and retention of reverse proxy logs, ingress logs, application logs, endpoint telemetry, file telemetry, container logs, DNS logs, firewall logs, NDR telemetry, egress records, cloud audit logs, identity logs, and credential-management activity.
· Need for credential rotation, API-token replacement, cloud-key review, repository access review, secrets-management validation, model artifact review, prompt exposure assessment, or customer-data scoping.
· Degree to which incomplete telemetry forces broader containment, credential rotation, model artifact quarantine, developer workflow suspension, or executive incident governance.
· Need for legal review, regulatory assessment, customer assurance, contractual notification analysis, insurance reporting, workforce communications, or board-level oversight.
S39 — Economic Impact & Organizational Exposure
Estimated Economic Exposure
Estimated economic exposure should be modeled through three scenario bands.
Low Impact Scenario
Estimated impact $250K to $2M.
Low impact applies when exposure was limited, remediation was rapid, logs were preserved, and review finds no suspicious model-ingestion activity, artifact anomalies, runtime instability, abnormal outbound communication, or downstream credential, repository, cloud, or identity misuse.
Moderate Impact Scenario
Estimated impact $3M to $15M.
Moderate impact applies when exposed or unpatched Ollama infrastructure shows suspicious model lifecycle activity, unusual artifact handling, runtime instability, rare outbound communication, model-push behavior, incomplete telemetry, or limited downstream credential concern without confirmed large-scale data exposure, sustained adversary control, or broad cloud, repository, or customer-data impact.
High Impact Scenario
Estimated impact $20M to $100M or higher.
High impact applies when confirmed or strongly suspected exposure involves sensitive prompts, proprietary source code, customer data, credentials, API tokens, cloud services, repositories, CI systems, internal APIs, or shared AI workflows, especially where evidence indicates abnormal artifact creation, outbound communication, credential use, repository access, cloud activity, or incomplete historical telemetry.
Annualized Risk Exposure
Estimated annualized risk exposure is $5M to $35M or higher.
Annualized risk exposure is driven by exposed Ollama server count, untrusted reachability, exposure duration, patch latency, sensitive prompt and data scope, credential and token footprint, developer workflow dependency, cloud or repository integration, model artifact activity, outbound communication, telemetry completeness, containment complexity, downstream credential risk, customer assurance requirements, and legal or regulatory obligations.
Operational Dependency
Economic exposure increases when Ollama infrastructure supports developer workflows, coding assistants, AI labs, shared model infrastructure, CI systems, cloud workloads, customer-support workflows, regulated data handling, or internal automation connected to privileged tools.
Control Trust
Control trust is reduced when self-hosted AI infrastructure is internet-facing, broadly reachable, unpatched, weakly authenticated, poorly segmented, or connected to sensitive workflows without strong access controls and monitoring.
Visibility Confidence
Visibility confidence depends on asset inventory, exposure management, route-level logs, endpoint telemetry, model artifact monitoring, container telemetry, DNS logs, egress visibility, cloud audit logs, identity logs, repository logs, and credential-management records.
Change-Control Confidence
Change-control confidence decreases when Ollama deployments are developer-owned, lab-based, temporary, unmanaged, containerized, or cloud-hosted without clear ownership, approved model-source baselines, approved egress baselines, or documented administrative workflows.
Downstream Dependency
Downstream exposure increases when the affected Ollama environment is connected to repositories, cloud services, CI systems, internal APIs, service accounts, secrets stores, automation tools, customer workflows, or developer platforms.
Customer and Regulatory Exposure
Customer and regulatory exposure increases when sensitive prompts, customer data, regulated information, source code, credentials, API tokens, secrets, tool outputs, repository content, cloud access, downstream identity activity, customer-impact uncertainty, or incomplete forensic scoping affect systems subject to regulatory, contractual, privacy, customer, insurance, intellectual-property, or material business obligations.
Residual Economic Risk
Patching, mitigation, exposure removal, or vendor remediation reduces future risk but does not prove that pre-remediation exploitation did not occur. Historical review remains required for systems that were exposed before mitigation, especially when affected environments processed sensitive prompts, source code, credentials, customer data, cloud context, repository access, tool outputs, or automation workflows.
S40 — References
Vendor / Platform Documentation
Release v0.17.1 · ollama/ollama · GitHub
hxxps://github[.]com/ollama/ollama/releases/tag/v0.17.1
ggml: ensure tensor size is valid · ollama/ollama@88d57d0 · GitHub
hxxps://github[.]com/ollama/ollama/commit/88d57d0483cca907e0b23a968c83627a20b21047
Vulnerability Records
CVE Record — CVE-2026-7482 vulnerability details
hxxps://www.cve[.]org/CVERecord?id=CVE-2026-7482
Security Vendor Analysis
Bleeding Llama: Critical Unauthenticated Memory Leak in Ollama
hxxps://www.cyera[.]com/research/bleeding-llama-critical-unauthenticated-memory-leak-in-ollama
Ollama vulnerability CVE-2026-7482: Find impacted assets
hxxps://www.runzero[.]com/blog/ollama/
Threat Tradecraft and Intrusion Patterns
MITRE ATT&CK Framework — Enterprise Matrix
hxxps://attack.mitre[.]org/matrices/enterprise