Graphalgo Fake Recruiter Dev Tasks Seeding Malicious npm and PyPI Dependencies
BLUF
North Korea aligned operators publicly attributed to Lazarus are conducting fake recruiter outreach targeting Web3 and crypto developers. Victims are sent interview coding challenges that import malicious npm and PyPI dependencies such as graphalgo, graphnetworkx, and bigmathutils. These packages function as staged loaders that retrieve additional payloads from GitHub raw content infrastructure and deploy a remote access trojan workflow on developer systems.
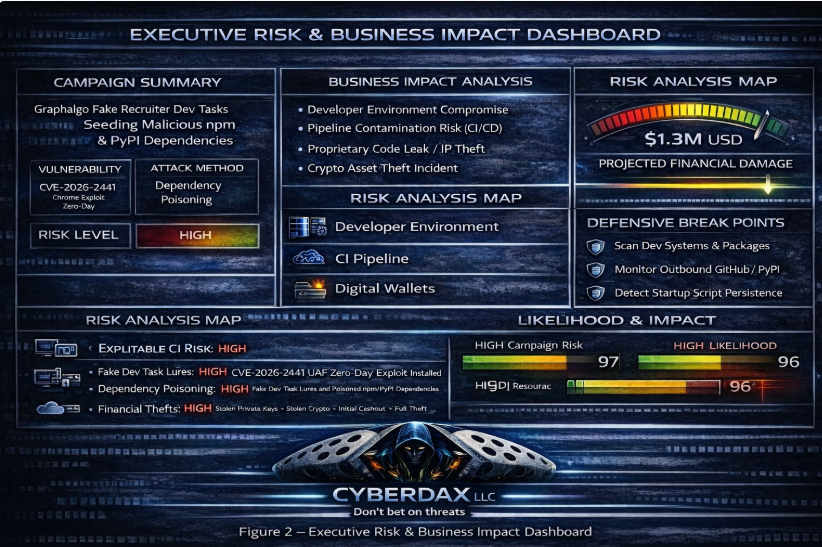
Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
“For organizations affected by malicious dependency seeding through fake developer recruitment tasks targeting npm and PyPI ecosystems, financial exposure extends beyond a single compromised endpoint into broader development and CI/CD environments.”
• Low-end total cost: $450,000 – $1.2 million
(Isolated developer workstation compromise with rapid containment and limited credential exposure)
• Typical expected range: $1.8 million – $4.5 million
(Multiple developer systems affected, CI/CD review required, credential rotation and external IR engagement)
• Upper-bound realistic scenarios: $6 million – $14 million
(Build pipeline contamination, intellectual property exposure, customer notification and regulatory review)
Key Cost Drivers
· Scope of developer endpoint and CI/CD environment contamination
· Volume of credentials, API keys, and tokens requiring rotation
· Potential intellectual property or proprietary code exposure
· Duration of undetected access within development environments
· Regulatory exposure if customer or financial data intersects compromised systems
Bottom Line for Executives
Compromise of developer environments and software supply chains presents a material operational and financial risk for mid-size to large organizations. Realistic cost exposure often falls in the $2 million to $5 million range, driven by incident response, credential rotation, dependency and code validation, and short-term disruption to release cycles. Costs can rise further when investigation extends into CI/CD systems or proprietary repositories, where remediation becomes more complex and business impact more sustained.
For executive leadership, the most effective approach is proactive: strengthening dependency governance, improving build pipeline integrity, and monitoring developer environments with production-level discipline. Treating software supply chain security as a core resilience and risk management priority helps reduce the likelihood of multi-million-dollar disruption while protecting long-term enterprise value.
Priority Level and Response Window
· High priority.
o Triage developer endpoints and CI systems within 24 hours.
Exploit Conditions Snapshot
· User execution required.
· Victim must clone or run the coding assignment or install and invoke the malicious dependency.
· Execution may trigger during normal library usage rather than during installation.
Today’s Hunt Focus
· Outbound connections to raw.githubusercontent.com with suspicious repository paths
· Node or Python processes writing unexpected files to user profile script paths
· Recently installed graph or big themed npm or PyPI packages on developer endpoints
Potential Exposure Scope
· Potential Affected Sectors
· Cryptocurrency firms
· Web3 platforms
· Blockchain engineering teams
· Software development and DevOps environments
Potential Impacted Countries
· Global
Date of First Reported Activity
· May 2025 for npm packages
· June 2025 for PyPI variants
Date of Last Reported Activity Update
· February 2026 reporting indicates continued activity cadence
Why This Matters to Defenders
· This campaign abuses trusted open source ecosystems and developer workflows. It bypasses perimeter controls and leverages legitimate platforms such as GitHub, npm, and PyPI. Compromise of developer workstations can lead to credential theft, source code access, CI pipeline compromise, and potential downstream supply chain impact.
Associated APT Groups
· Lazarus Group
Associated Criminal Organizations
· Not applicable at this time
Threat Actor Context
· Uses fake recruiter personas, staged companies, and GitHub organizations to deliver malicious coding tasks consistent with previous DPRK operations.
Primary Objectives
· Developer environment compromise
· Credential harvesting
· Access to crypto wallets or exchange infrastructure
Tools Used in Campaign
· GitHub repositories
· npm registry
· PyPI registry
· Social engineering via recruiter messaging
Exposure Assessment Tool
· OpenSSF OSV malicious package database
· ReversingLabs Spectra Assure
IOCs with Confidence Level Scoring
High Confidence Indicators (0.90 – 0.95)
Artifact Hashes (SHA256)
· 50c06ef08dc76e72bdc78082ce89a830f60bfcf42fd9217d17b5622d732a3acd
o Confidence Level: High (0.95)
o Explanation: OSV-confirmed malicious artifact tied directly to graphnetworkx.
· 12b124e4a03debd491edf59b6c4f40ae3a41fac5ef33689178ce4f80d55399ff
o Confidence Level: High (0.95)
o Explanation: Second OSV-confirmed malicious artifact from the same dependency poisoning cluster.
Staged Retrieval Infrastructure
· raw.githubusercontent.com/johns92/blog_app/refs/heads/main/server/.env.example
o Confidence Level: High (0.93)
o Explanation: Explicit GitHub raw path documented as staged payload retrieval infrastructure.
Malicious Packages
· Graphnetworkx
o Confidence Level: High (0.92)
o Explanation: Confirmed malicious PyPI dependency with tracked artifacts and staged loader behavior.
· Graphalgo
o Confidence Level: High (0.90)
o Explanation: Vendor-identified malicious dependency delivered through recruiter-based coding tasks.
High Confidence Indicators (0.85 – 0.89)
· Malicious Packages
o bigmathutils
o Confidence Level: High (0.88)
o Explanation: Documented malicious package within the same Graphalgo dependency seeding campaign cluster.
· Recruiter-themed coding assignment repository delivery artifact
o Confidence Level: High (0.88)
o Explanation: Social engineering delivery mechanism confirmed as primary campaign vector.
· bignumx
o Confidence Level: High (0.85)
o Explanation: Package naming and behavioral traits consistent with confirmed malicious dependency set.
· Node or Python process invoking malicious dependency import
o Confidence Level: High (0.85)
o Explanation: Required execution trigger for staged loader activation on developer endpoints.
Behavioral Indicators
o File creation under user profile script or Chrome-related directories
Confidence Level: Medium (0.70)
· Explanation: Reported persistence-related artifact, but environment-specific and not uniquely attributable.
Medium Confidence Indicators (0.60 – 0.69)
· Malware Classification
· Multi-stage loader and remote access trojan behavior observed
· Confidence Level: Medium (0.60)
· Explanation: Staged RAT deployment confirmed, but no consistent vendor family name assigned publicly.
CyberDax IOC Handling Guidance
· High-confidence indicators above should be prioritized for:
· Dependency blocklisting across npm and PyPI
· CI/CD dependency allowlisting enforcement
· Proxy monitoring for GitHub raw stage retrieval
· Endpoint hunting for node and python execution tied to suspicious imports
Malware Names
High-confidence indicators above should be prioritized for:
· Multi stage loader and remote access trojan
Malware Family
· Not identified at this time
sha256
50c06ef08dc76e72bdc78082ce89a830f60bfcf42fd9217d17b5622d732a3acd
12b124e4a03debd491edf59b6c4f40ae3a41fac5ef33689178ce4f80d55399ff
Known Decoding Key
· Argument driven execution gating. Not applicable at this time for static reusable key.
Verdict
· Malicious supply chain dependency. Immediate removal required.
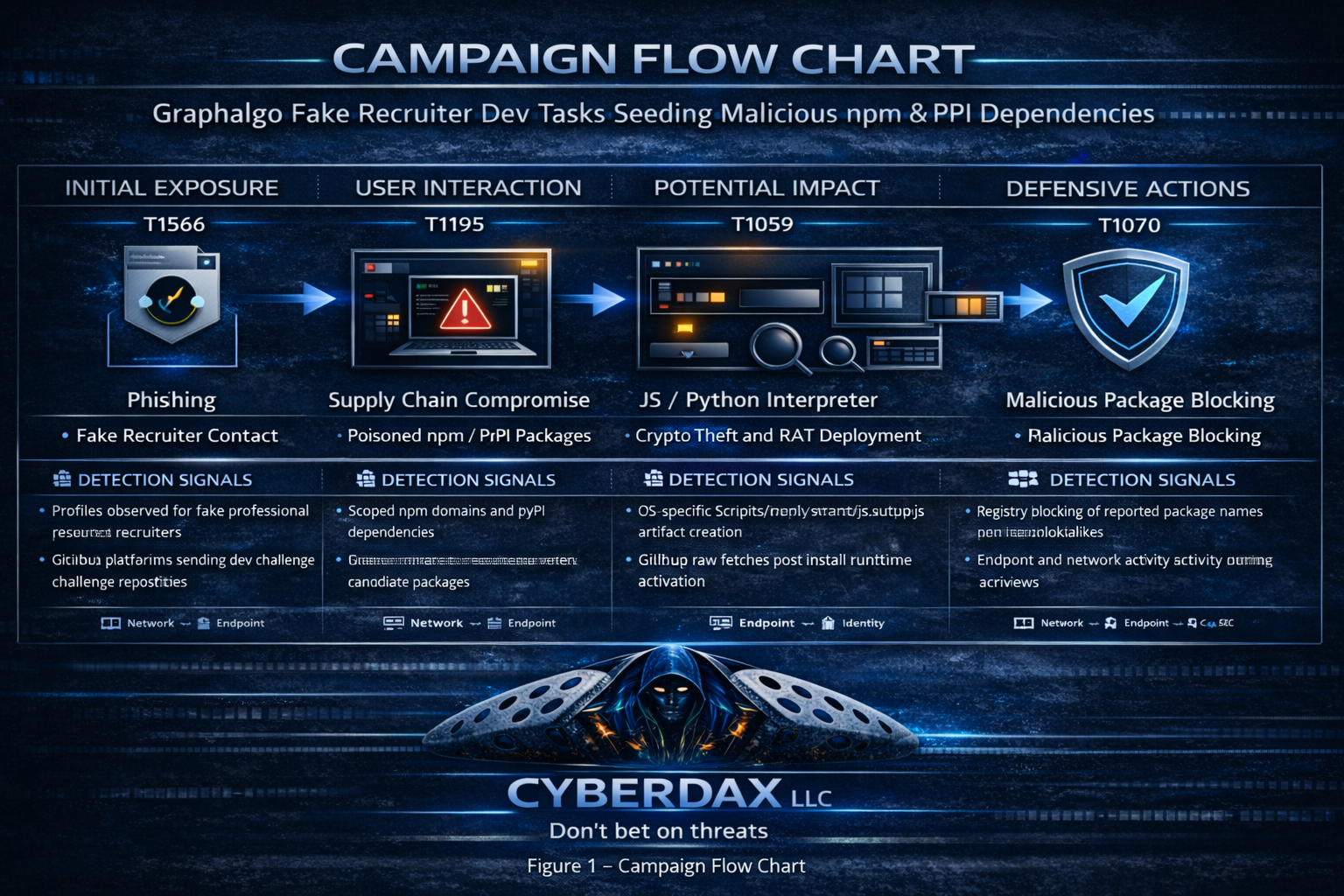
MITRE ATT&CK Campaign Flow
Stage 1 Resource Development
· T1583 Acquire Infrastructure
· T1587 Develop Capabilities
Stage 2 Initial Access
· T1566 Phishing
· T1204 User Execution
Stage 3 Execution
· T1059 Command and Scripting Interpreter
· T1105 Ingress Tool Transfer
Stage 4 Persistence and Defense Evasion
· T1547 Boot or Logon Autostart Execution
· T1070 Indicator Removal on Host
Stage 5 Command and Control
· T1071 Application Layer Protocol
TTPs
· T1587 Develop Capabilities
o Malicious npm and PyPI packages act as staged loaders.
· T1566 Phishing
o Fake recruiter outreach delivers coding task repositories.
· T1204 User Execution
o Victim executes project code invoking malicious dependency.
· T1105 Ingress Tool Transfer
o Payload retrieved from GitHub raw content infrastructure.
· T1547 Boot or Logon Autostart Execution
o Scripts written to user profile paths for persistence.
· T1070 Indicator Removal on Host
o Payload deletes itself and patches invoking file to reduce detection.
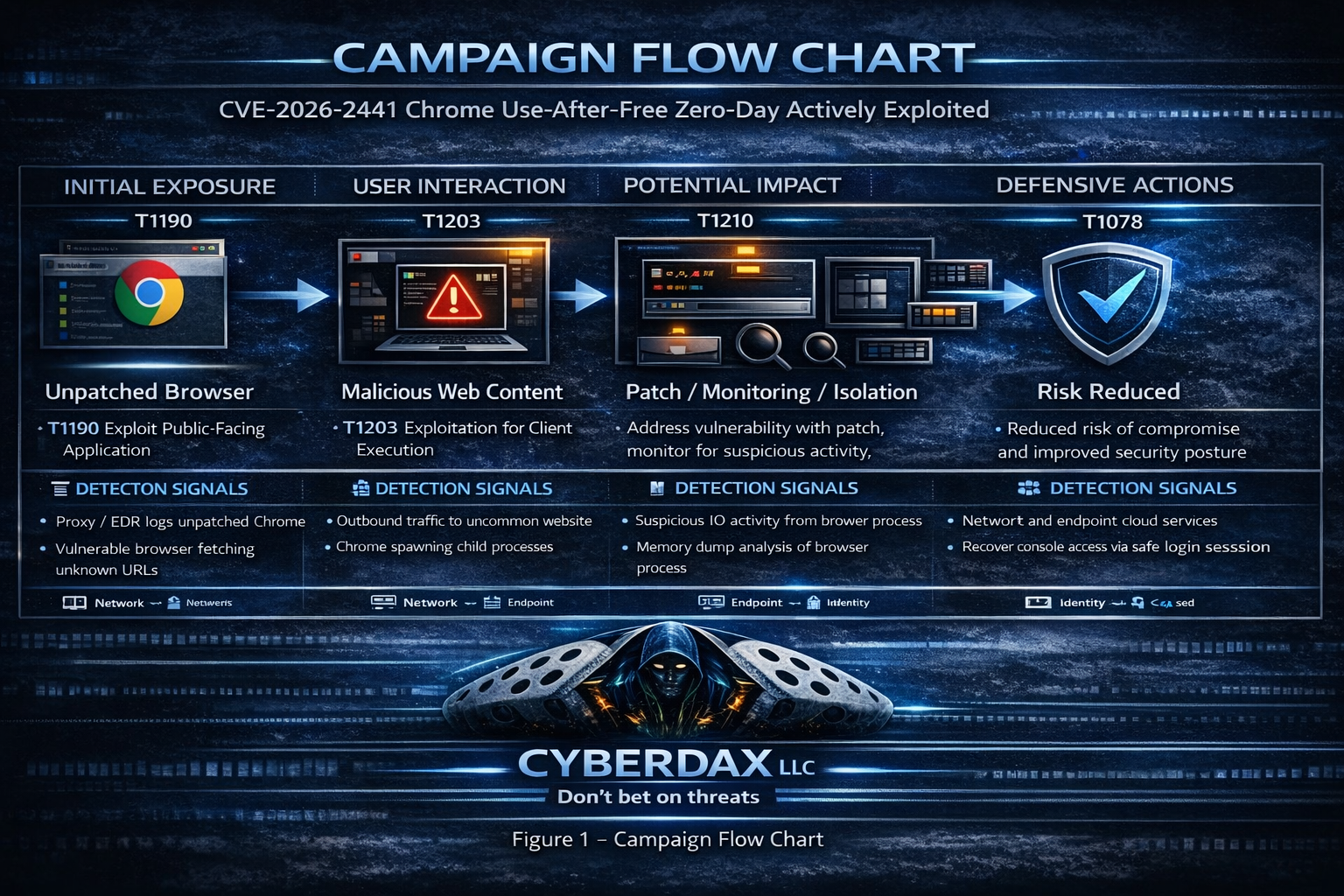
Vulnerability and Exploitation Details
CVE
· There have not been any CVEs associated with this activity at this time.
CVSS Vectors 3.1
· Not applicable at this time
Nessus ID
· Not applicable at this time
KEV List Status
· Not applicable at this time
CISA patch by date
· Not applicable at this time
Mitigation Guidance
· Remove malicious packages and validate dependency trees
Patch Release Date
· Not applicable at this time
URL Link to Patch Information
· Not applicable at this time
Exploitability
· Social engineering based execution
Observed Exploitation Status
· Active campaign with multiple malicious packages confirmed
Exposure Risk
· High for developer endpoints and CI pipelines
Recommended Action
· Remove packages
· Rotate secrets
· Implement dependency allowlisting
· Audit build runners
Vendor Advisory URL
· hxxps://www.reversinglabs.com/blog/inside-graphalgo
Behavior Analysis
· Stage gated execution logic
· GitHub raw content retrieval
· Script file drops under user profile
· Self modification of invoking files
Expected User-Agent Patterns
· Not known at this time
Payload Examples
· GitHub raw .env example path retrieval
Log Artifacts
· Outbound HTTPS to raw.githubusercontent.com
· File creation under user script directories
Detection Coverage Matrix
· Network Controls
o Detect GitHub raw content retrieval to suspicious paths
· Endpoint Controls
o Detect node or python creating unexpected script files
· Identity Controls
o Monitor anomalous GitHub or package registry authentication
· Email Security Controls
o Recruiter themed lure detection
· Cloud Security Controls
o Monitor CI pulling new public dependencies
· Detection Coverage by Control Type
o Explicit mapping above enforced per CyberDax standard
Threat Hunting and Detection Rules
Suricata
Rule
· Graphalgo GitHub Raw Stage Retrieval
Purpose
· Detect high confidence stage two payload retrieval from GitHub raw content path.
Tuning Explanation
· Scoped to known malicious path to reduce GitHub baseline noise.
alert http $HOME_NET any -> $EXTERNAL_NET any (
msg:"Graphalgo suspicious GitHub raw stage retrieval";
flow:established,to_server;
http.host; content:"raw.githubusercontent.com"; nocase;
http.uri; content:"/johns92/blog_app/refs/heads/main/server/.env.example"; nocase;
classtype:trojan-activity;
sid:9902601; rev:2;
)
SentinelOne
Rule
· Graphalgo Suspicious Dependency Execution
Purpose
· Identify node or python processes referencing known malicious dependency names.
Tuning Explanation
· Package names limited to confirmed malicious variants.
EventType = "Process Creation"
AND (
ImagePath ENDSWITH "\\node.exe"
OR ImagePath ENDSWITH "\\python.exe"
)
AND (
CommandLine CONTAINS "graphalgo"
OR CommandLine CONTAINS "graphnetworkx"
OR CommandLine CONTAINS "bigmathutils"
)
Splunk
Rule
· Graphalgo GitHub Raw Retrieval in Proxy Logs
Purpose
· Surface outbound traffic to known malicious GitHub raw path.
Tuning Explanation
· Exact URI matching prevents excessive GitHub noise.
index=proxy
| search http_host="raw.githubusercontent.com"
| search uri_path="/johns92/blog_app/refs/heads/main/server/.env.example"
| stats count by src_ip user
YARA
Rule
· Graphalgo Embedded Raw GitHub Path Indicator
Purpose
· Detect artifact containing hard coded malicious GitHub raw URL.
Tuning Explanation
· High precision string match. Expand only if actor rotates repo path.
rule Graphalgo_Raw_GitHub_Path
{
strings:
$u1 = "raw.githubusercontent.com/johns92/blog_app/refs/heads/main/server/.env.example" ascii nocase
condition:
$u1
}
Sigma
Rule
· Graphalgo GitHub Raw Stage Retrieval
Purpose
· Portable SIEM detection of outbound malicious GitHub path access.
Tuning Explanation
· URI specific matching to reduce false positives.
title: Graphalgo Suspicious GitHub Raw Stage Retrieval
logsource:
category: proxy
detection:
selection:
cs-host|contains: raw.githubusercontent.com
cs-uri-stem|contains: /johns92/blog_app/refs/heads/main/server/.env.example
condition: selection
level: high
Delivery Methods
· Fake recruiter outreach delivering coding challenge repositories that reference malicious dependencies.
Defender Action Plan
· Day 1 Identify installed malicious packages across endpoints and CI
· Day 2 Block known indicators at proxy and DNS
· Day 3 Rotate developer secrets
· Day 4 Audit package lockfiles
· Day 5 Deploy detection rules
· Day 6 Conduct scoped threat hunt
· Day 7 Update hiring and dependency review process
References
ReversingLabs
· hxxps://www.reversinglabs.com/blog/inside-graphalgo
MITRE ATT&CK T1105
· hxxps://attack.mitre.org/techniques/T1105/
OpenSSF OSV
· hxxps://osv.dev/vulnerability/MAL-2025-21882