Defense Industrial Base Supply-Chain Targeting via Hiring, Contractor Onboarding, and Direct-to-Individual Tradecraft
BLUF
Google Threat Intelligence Group (GTIG) reports increasing state-sponsored cyber-espionage pressure on the defense industrial base (DIB) where adversaries shift from classic perimeter intrusion toward compromising the supply chain through people and business processes—notably recruiting, job application workflows, contractor onboarding, and personal/unmanaged devices used by employees/candidates. This reduces defender visibility and increases risk of downstream compromise across the DIB ecosystem.
Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
For organizations affected by hiring, contractor onboarding, or personnel supply-chain targeting within the defense industrial base:
· Low-end total cost: $2.0M – $4.0M
o Limited credential exposure, rapid containment, minimal downstream partner impact
· Typical expected range: $4.5M – $9.5M
o HR/ATS compromise with contractor access review and moderate program disruption
· Upper-bound realistic scenarios: $10M – $18M
o Multi-partner trust-chain impact, extended investigation, strategic program delays
Key Cost Drivers
· Number of HR, ATS, and SSO identities requiring remediation
· Degree of contractor and partner access issued through affected workflows
· Duration of hiring or onboarding disruption for cleared roles
· Scope of regulatory notification and contractual disclosure obligations
· Extent of downstream program or bid schedule impact
Potential affected sectors
· Defense primes and subcontractors
· Aerospace and aviation suppliers
· Drone / advanced weapons supply chains
· Cleared engineering services and systems integrators
· Third-party HR/recruiting vendors supporting DIB hiring
Potential impacted countries
· United States and European Union defense industrial ecosystems (explicitly emphasized in reporting)
· Ukraine-linked defense support ecosystems noted in press summaries as frequent targeting context
Date of first reported activity
· Feb 10, 2026
Date of last reported activity update
· Feb 10, 2026
Why This Matters to Defenders
Visibility gap
· Attacks increasingly occur off-network (personal devices, personal email, candidate systems) where corporate SOC tooling may not collect telemetry.
Supply-chain blast radius
· One compromised individual or contractor pipeline can create trusted access into multiple partner networks.
Process compromise exploit compromise
· Adversaries “corrupt business processes” (recruiting/onboarding) to get legitimate credentials and footholds that bypass many controls.
Associated APT groups
· UNC3886
o China-nexus; examples include edge/appliance initial access trends impacting defense/aerospace risk
· UNC5221
o China-nexus; similarly cited in context of edge devices/appliances as initial access
Associated criminal organizations
· Not publicly specified as named criminal orgs in the GTIG post itself.
o Press summaries reference North Korea-linked infiltration of companies via remote IT worker schemes, which can involve financial theft objectives in other reporting contexts, but the GTIG post is framed around espionage pressure on DIB.
Tools used in campaign
· Not publicly enumerated as a tool list in the GTIG blog post/press summaries available.
· What defenders should assume (planning basis, not attribution):
· Web-based credential phishing kits / spoofed domains
· MFA fatigue or session theft where applicable
· Remote access tooling used after credential acquisition
Exposure Assessment Tool
(practical)
A lightweight “assessment tool” you can run with existing logs/controls:
Recruiting / HR workflow exposure
· List all recruiting platforms, contractor onboarding portals, ATS integrations, and SSO connections.
· Identify which are internet-facing, which allow external uploads, and which support password resets externally.
· Identity exposure
· Audit MFA enrollment and conditional access for HR/ATS apps.
· Detect logins to HR/ATS from new geos/new devices/new ASNs.
Personal device exposure
· Quantify roles that use personal devices for sensitive recruiting or engineering communications.
· Enforce “managed device required” for high-risk roles where feasible.
Supplier/partner exposure
· Verify contractor identity proofing requirements and access issuance steps for partner staff.
IOCs
Network / file / malware IOCs
· None publicly provided in the GTIG public blog post and major press summaries reviewed.
Confidence
· High (absence confirmed in sources)
Behavioral “IOCs”
Telemetry triggers
Confidence
· Medium (aligned to described tactics)
High-signal detections
· Lookalike recruiting domains targeting your brand or top suppliers (newly registered domains resembling {company}-careers, {company}-jobs, {company}-talent).
· ATS/HR account takeover signals: impossible travel, new device + password reset, OAuth consent anomalies.
· Candidate-file weaponization signals: unusual macro-enabled docs or archive formats submitted through application portals.
· Remote IT worker indicators: repeated identity inconsistencies during onboarding; device fingerprint mismatch; shared infrastructure across “different” hires.
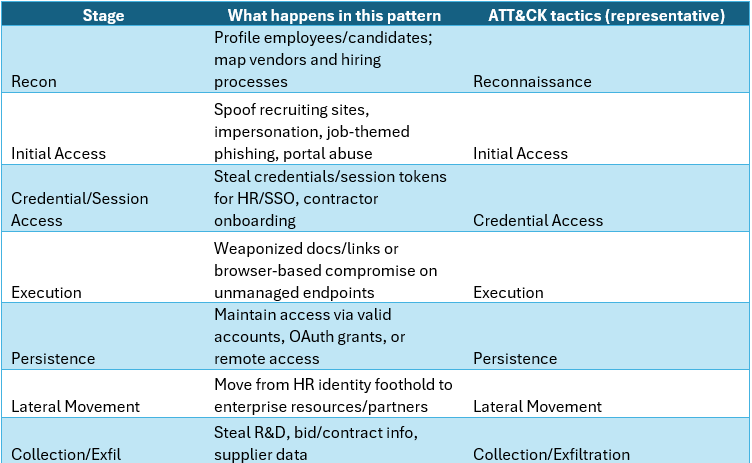
Figure 1 MITRE ATT&CK attack chain chart
ATT&CK tactics (representative)
Recon
Profile employees/candidates; map vendors and hiring processes
Reconnaissance
Initial Access
Spoof recruiting sites, impersonation, job-themed phishing, portal abuse
Initial Access
Credential/Session Access
Steal credentials/session tokens for HR/SSO, contractor onboarding
Credential Access
Execution
Weaponized docs/links or browser-based compromise on unmanaged endpoints
Execution
Persistence
Maintain access via valid accounts, OAuth grants, or remote access
Persistence
Lateral Movement
Move from HR identity foothold to enterprise resources/partners
Lateral Movement
Collection/Exfil
Steal R&D, bid/contract info, supplier data
Collection/Exfiltration
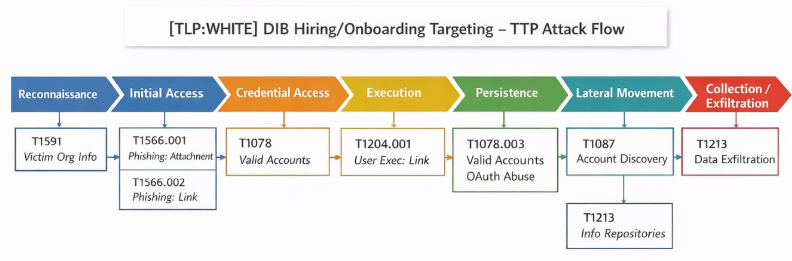
Figure 2 Supply chain life cycle
TTPs
Stage 1 Recon / Targeting
· T1591 – Gather Victim Org Information → map DIB org charts, suppliers, recruiting contacts.
· T1598 – Phishing for Information → elicit onboarding/recruiting details pre-attack.
Stage 2 Initial Access (Hiring/Personnel vector)
· T1566.002 Phishing: Link
o Fake job portals, spoofed contractor sites.
· T1566.001 Phishing: Attachment
o “offer letter”, “benefits”, “clearance forms” themes (common in hiring abuse; consistent with “job application channels” targeting).
· T1583.001 Acquire Infrastructure Domains
o Register lookalike recruiting domains.
· T1583.006 Acquire Infrastructure Web Services
o Host spoof portals quickly and cheaply.
Stage 3 Credential/Identity Access
· T1078 Valid Accounts
o Compromise HR/ATS/SSO accounts and operate as legitimate users.
· T1110 Brute Force / T1556 Modify Authentication Process
o Not confirmed; include only if your telemetry shows it.
Stage 4 Execution / Persistence on endpoints (often unmanaged)
· T1204.001 User Execution Malicious Link
o Drive-by to spoof portal on personal device.
· T1059 Command and Scripting Interpreter
o Typical follow-on once execution achieved
Stage 5 Lateral Movement / Collection
· T1087 Account Discovery
o Find reachable internal resources after HR foothold (not confirmed by GTIG in public post).
· T1213 Data from Information Repositories
o Pull bid, contract, engineering docs.
Figure 3 TTP attack cycle
CVE
· Not publicly specified.
What is the exploitability?
· This activity is not associated with a CVE at this time.
Has there been observed exploitation?
· Yes
o Observed activity pattern (hiring/personnel targeting)
What is the exposure risk?
High for organizations with:
· External-facing recruiting/onboarding portals
· Weak identity proofing for contractors
· HR/ATS apps without conditional access
· High use of unmanaged/personal devices for sensitive comms
Recommended action
· Require MFA + conditional access for HR/ATS/SSO
· “Managed device required” for sensitive recruiting / engineering comms
· Domain monitoring for recruiting lookalikes
· Tighten contractor onboarding identity proofing & device attestation
· Security review of HR/ATS integrations (OAuth, SCIM, API tokens)
CVSS vectors 3.1
· This activity is not associated with a CVE at this time.
Nessus ID
· This activity is not associated with a CVE at this time.
KEV list
· This activity is not associated with a CVE at this time.
Malware names
· There has not been malware identified in public reporting
Verdict
· High strategic risk
o This is a defense supply-chain compromise pattern that bypasses traditional perimeter controls by targeting the hiring and contractor trust chain.
Primary objectives
· Espionage: R&D theft
· Preparatory access
· Supplier intelligence
· Defense capability insights
Threat actor context
China-nexus activity volume against DIB, and describes broader state-sponsored activity
· Russia
· Iran
· North Korea
· China
Behavior analysis
· Spoofed recruiting sites for primes/suppliers; impersonation of recruiters
· Targeting of employees/candidates on personal devices outside corp monitoring
· Abuse of business workflows to obtain legitimate credentials and access
Expected User-Agent patterns
Because activity often uses web portals:
· Common browser UAs (Chrome/Edge/Safari) to blend into normal candidate traffic
· Potential automation UAs during credential stuffing or portal enumeration (not confirmed; watch for unusual headless/browser-automation fingerprints)
· ATS API clients (if integrations are abused) — monitor atypical API tokens / clients
Payload examples
(representative)
· “Offer letter / benefits / clearance onboarding” themed lure pages or docs
· Lookalike careers portals capturing credentials
· Contractor onboarding invitations directing to spoof SSO flows
Log artifacts
What to hunt
SSO logs
· new device + new geo + HR/ATS app logins; suspicious OAuth consents
DNS/Proxy
· Newly registered domains resembling your recruiting branding
Email security
· Inbound recruiter impersonations; vendor invoice/onboarding spoofing
HR/ATS audit logs
· Mass downloads/exports; role changes; API token creation
EDR (managed endpoints)
· HR staff clicking job-themed links; browser credential store access anomalies
Figure 4 Detection Coverage Matrix
Detection coverage by control type
Prevent
· Conditional access
· Device compliance
· Phishing-resistant MFA
· Domain takedown/monitoring
Detect
· IdP anomaly detection
· HR/ATS audit correlation
· Brand spoof monitoring
Respond
· Rapid account disable
· Session revocation
· OAuth token purge
· Supplier notification workflow
Suggested rules / potential hunts
Suricata
Network-Based Rules
· Recruitment-Themed Phishing Documents
o Look for HTTP/TLS traffic containing keywords like "Salary," "Contract," or "Job_Description" combined with suspicious file extensions (.zip, .iso, .lnk).
alert http $EXTERNAL_NET any -> $HOME_NET any (msg:"DIB Recruitment Phish - Possible Malicious Job Desc"; file_data; content:".zip"; content:"Job_Description"; nocase; sid:1000001; rev:1;)
· Direct-to-Individual Communication (D2I)
o Detect traffic to unofficial messaging platforms (e.g., Telegram, WhatsApp Desktop) from sensitive subnets.
alert dns $HOME_NET any -> any any (msg:"Suspicious D2I App DNS Query - Potential Out-of-Band Recruitment"; dns_query; content:"telegram.org"; sid:1000002; rev:1;)
SentinelOne
· Suspicious Document-to-Shell Execution
o Identify "onboarding" documents (Word/PDF) that spawn PowerShell or CMD to download secondary payloads.
ObjectType = "Process" AND ParentProcessName IN ("winword.exe", "excel.exe", "powerpnt.exe", "acrord32.exe") AND (ProcessName = "powershell.exe" OR ProcessName = "cmd.exe")
· Persistence via New Contractor Profile
o Look for unusual registry modifications or scheduled tasks created shortly after a new local user account is added (common in "contractor" onboarding scenarios).
ObjectType = "Registry" AND RegistryKey PATH "HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows\\CurrentVersion\\Run" AND User NOT IN ("Trusted_Admin_List")
Splunk
· Anomalous Onboarding Access
o Search for new user accounts created outside of standard HR windows or by non-HR administrators.
index=wineventlog EventCode=4720 | stats count by user, src_user | lookup hr_staff_list.csv user AS src_user OUTPUT is_hr | where is_hr!="true"
· LNK File Execution from Downloads
Detect recruitment-themed .lnk files (common in "Job Offer" scams) executing from the Downloads folder.
index=windows_logs process_name="cmd.exe" OR process_name="powershell.exe" | search "Downloads" AND "*.lnk" | eval recruitment_keywords=if(match(_raw, "(?i)(Job|Offer|Salary|Contract)"), "Yes", "No") | where recruitment_keywords="Yes"
Splunk
· IdP anomalies for HR/ATS apps
index=idp (app="ATS" OR app="HRIS" OR app="Recruiting")
| stats earliest(_time) as firstSeen latest(_time) as lastSeen values(src_ip) as src_ip values(user_agent) as ua values(device_id) as device by user
| where mvcount(device)>1 OR mvcount(src_ip)>2
· HR/ATS bulk export / mass download
index=hr_audit action IN ("export","bulk_download","report_download","api_token_created","role_changed")
| stats count earliest(_time) as firstSeen latest(_time) as lastSeen values(action) as actions by user
| where count > 10 OR mvfind(actions,"api_token_created")>=0 OR mvfind(actions,"role_changed")>=0
YARA
· Not applicable as a standalone deliverable without a disclosed malware sample/hash family from GTIG. (If you have a sample from your environment, I can write YARA against it.)
Sigma
Deployable concept
Rule concept: “HR/ATS IdP Anomalous Login + OAuth Consent”
Condition: HR/ATS app login from new geo/new device AND OAuth consent/token grant within short window.
Map to your IdP log schema (Okta/Azure AD/Google Workspace, etc.).
Delivery methods
· Recruiting impersonation (spoof recruiter identities)
· Fake job portals / careers sites
· Job application channel abuse (links/docs)
· Contractor onboarding infiltration / remote worker schemes (as cited in press summaries)
Steps to consider over the next seven days
· Turn on or tighten phishing-resistant MFA for HR/ATS/SSO admin roles.
· Enforce conditional access (managed device required) for HR/ATS and recruiting mailboxes.
· Implement brand/domain monitoring for lookalike recruiting domains; auto-ticket take-downs.
· Add HR/ATS audit log forwarding to SIEM; create bulk export/token creation detections.
· Review contractor onboarding: identity proofing, device compliance, least privilege, time-bound access.
· Run a tabletop: “candidate portal spoof → HR credential theft → supplier pivot.”
· Communicate to HR/recruiting: known lures, verification steps, and escalation workflow.
References
Cloud Google
· hxxps://cloud.google.com/blog/topics/threat-intelligence/threats-to-defense-industrial-base/
The Guardian
· hxxps://www.theguardian.com/world/2026/feb/10/state-sponsored-hackers-targeting-defence-sector-employees-google-says
Tech HQ
· hxxps://techhq.com/news/google-hiring-devices-and-supply-chains-are-under-attack/
Cyber News
hxxps://cybernews.com/security/cyberattacks-defense-industrial-base-contractors-google/