Handala Wiper Attack Disrupts Stryker Global Medical Technology Infrastructure
BLUF
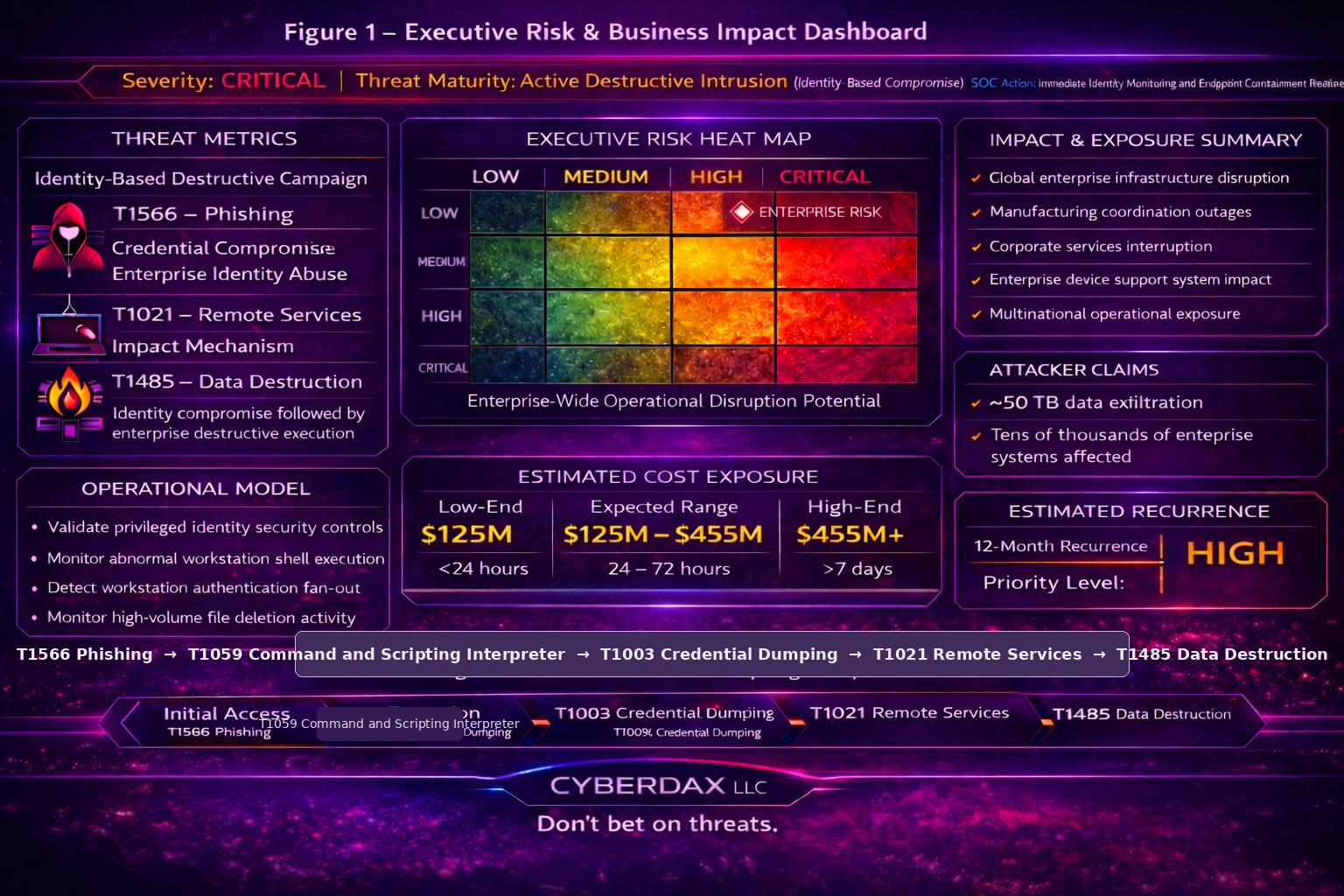
The incident highlights the growing vulnerability of globally integrated healthcare manufacturing supply chains to geopolitically motivated cyber disruption. A destructive cyberattack attributed to the Handala hacking group disrupted Stryker’s global enterprise infrastructure, impairing systems supporting manufacturing operations, corporate services, and internal technology platforms across multiple regions. The most likely intrusion model involved phishing-enabled credential compromise followed by enterprise lateral movement and staged destructive payload execution consistent with MITRE ATT&CK T1485 – Data Destruction. Current intelligence indicates an operationally capable destructive intrusion relying on identity compromise and administrative access rather than exploitation of a specific software vulnerability, enabling rapid propagation across enterprise endpoint environments once privileged access was achieved. Executive response should prioritize immediate validation of identity security controls, expansion of behavioral monitoring across email security gateway telemetry, endpoint process telemetry, and DNS or web proxy telemetry, and deployment of rapid endpoint containment capability capable of isolating destructive activity before enterprise-wide propagation occurs.
Executive Risk Translation
A destructive cyberattack affecting a multinational healthcare manufacturing enterprise can generate nine-figure operational disruption within days due to halted manufacturing operations, supply-chain interruption, and device support outages.
S2A. Why This Matters Now
· Destructive malware targeting healthcare manufacturing supply chains represents a shift from financially motivated cybercrime toward geopolitically driven disruption operations.
· Medical technology manufacturers operate highly interconnected global manufacturing, logistics, and service environments where enterprise IT outages can cascade into clinical supply disruption.
· The Handala campaign reflects a hybrid cyber operation combining data exfiltration, destructive malware execution, and influence messaging, amplifying operational and reputational damage.
· Early detection opportunities for destructive cyber events consistently appear across three telemetry domains:
· email security gateway telemetry detecting phishing-based initial access attempts
· endpoint process and EDR telemetry detecting malicious execution behavior
· DNS and web proxy telemetry detecting command-and-control activity or abnormal data transfer patterns
S3. Key Judgments
· The operation most likely represents geopolitically motivated disruptive cyber activity rather than financially motivated ransomware behavior.
· Initial access likely occurred through phishing-enabled credential compromise or identity infrastructure abuse consistent with previously observed Handala activity.
· Destructive impact likely resulted from enterprise-wide propagation of wiper malware capable of triggering large-scale endpoint data destruction events.
· The campaign demonstrates moderate to advanced operational maturity including coordinated messaging intended to amplify perceived operational damage.
· Healthcare manufacturing supply chains represent high-value geopolitical cyber targets due to their economic leverage and societal impact potential.
S4. Strategic Threat Context
Destructive cyber operations targeting industrial and healthcare manufacturing sectors have increased in frequency as geopolitical actors seek to generate economic pressure without kinetic escalation. Wiper malware campaigns are designed to destroy enterprise data and system functionality rather than extract financial ransom, producing immediate operational disruption and costly recovery requirements. Healthcare manufacturing environments are particularly vulnerable due to their dependence on globally distributed logistics networks, tightly integrated enterprise IT systems, and large endpoint fleets used for operational coordination. In this environment, identity compromise combined with destructive malware propagation can rapidly disable enterprise infrastructure supporting manufacturing scheduling, device servicing, and global supply chain management.
S5. Executive Risk Summary
CyberDax threat assessment:
· Threat Severity: Critical
· Operational Disruption Scope: Global enterprise infrastructure
· Attack Type: Destructive wiper malware mapped to MITRE ATT&CK T1485 – Data Destruction
· Adversary Type: Politically motivated cyber proxy actor
· Sector Risk Exposure: Healthcare manufacturing supply chain
Public reporting indicates attackers claimed:
· approximately 50 terabytes of data exfiltration
· destructive impact affecting tens of thousands of enterprise systems
· operational disruption spanning dozens of countries
While attacker claims require independent verification, confirmed enterprise outages indicate significant operational disruption consistent with destructive malware activity.
S5A. Estimated Probability of Recurrence (12-Month Horizon)
CyberDax recurrence modeling evaluates:
· attacker return on investment
· sector value to geopolitical actors
· exploit surface across healthcare manufacturing infrastructure
· historical targeting behavior of destructive cyber proxy groups
Modeled recurrence probabilities:
· Similar destructive operations targeting healthcare suppliers: 45–60 percent
· Expansion to additional healthcare manufacturing enterprises: 40–55 percent
· Escalation of geopolitical proxy cyber operations against Western supply chains: 35–50 percent
Primary recurrence drivers include:
· relatively low attacker infrastructure cost
· high psychological and economic disruption potential
· persistent geopolitical tensions
· limited destructive malware defensive maturity across industrial enterprises
S6. Executive Cost Summary
CyberDax financial exposure modeling evaluates operational drivers including manufacturing downtime, supply-chain disruption, recovery operations, and regulatory exposure.
Estimated organizational impact ranges:
· Manufacturing downtime and operational disruption
o $60M – $210M
· Supply chain and logistics interruption
o $25M – $90M
· Incident response, system restoration, and forensic investigation
o $20M – $70M
· Legal, regulatory, and compliance exposure
o $10M – $35M
· Brand damage and market perception impact
o $10M – $50M
· Estimated total enterprise financial exposure:
o $125M – $455M
S6A. Risk Drivers
Structural drivers increasing destructive cyber risk for healthcare manufacturing organizations include:
· geopolitical tensions encouraging state-aligned proxy cyber operations
· increasing digitization of medical manufacturing environments
· reliance on cloud identity infrastructure and remote administrative systems
· large enterprise endpoint fleets capable of rapid malware propagation
· limited segmentation across multinational corporate networks
· operational dependence on IT-enabled logistics systems, manufacturing scheduling platforms, and global device support infrastructure
These drivers collectively increase the probability of destructive cyber operations targeting healthcare manufacturing enterprises over the next 12–24 months.
S7. Bottom Line for Executives
Destructive cyber operations targeting healthcare manufacturing supply chains represent a growing threat capable of rapidly halting global production, logistics, and device support operations. Organizations must treat identity infrastructure, endpoint management systems, and enterprise telemetry visibility as critical defensive layers capable of preventing catastrophic destructive malware propagation.
S7A. Board-Level Takeaway
Boards should assume that future cyberattacks will increasingly prioritize operational disruption rather than financial ransom. Sustained investment in identity protection, behavioral detection across enterprise telemetry, automated containment capability, and resilient recovery architecture will be required to reduce enterprise exposure to destructive cyber events.
S8. Targeted Organization
Stryker Corporation
Organizational profile:
· Global medical technology manufacturer headquartered in the United States
· Develops orthopedic implants, surgical robotics systems, hospital equipment, and medical technologies
· Serves hospitals, surgical centers, and healthcare providers across multiple continents
Operational characteristics relevant to cyber risk:
· globally distributed manufacturing infrastructure
· integrated enterprise logistics and supply-chain management platforms
· large enterprise endpoint fleet supporting engineering, operations, and corporate functions
· centralized identity infrastructure used to manage global workforce access
These characteristics increase exposure to destructive cyber activity because enterprise IT disruption can directly affect manufacturing scheduling, distribution coordination, and global device servicing operations.
S9. Sectors / Countries Affected
Primary Target Sector
· healthcare medical technology manufacturing
Secondary Exposure Sectors
· healthcare delivery infrastructure
· hospital equipment supply chains
· medical device servicing networks
· biomedical logistics and distribution providers
Countries Affected
· United States
· Ireland
· Australia
· Costa Rica
· Germany
· France
· additional European and Asia-Pacific operational locations
Due to the organization’s multinational operational footprint, enterprise cyber disruption can cascade across regional manufacturing plants, distribution hubs, and support infrastructure.
S10. Targeting Probability Assessment
CyberDax targeting probability modeling evaluates likelihood of similar organizations being targeted based on sector value, geopolitical incentives, operational disruption potential, and attacker return on investment.
High Probability Targets
· multinational healthcare manufacturing enterprises
· global medical device manufacturers
· healthcare equipment supply chain providers
Moderate Probability Targets
· pharmaceutical manufacturing companies
· healthcare technology vendors
· hospital technology infrastructure providers
Lower Probability Targets
· regional healthcare providers without large supply-chain dependencies
Primary targeting drivers include:
· high geopolitical visibility of healthcare supply chains
· economic pressure potential created through supply disruption
· large enterprise attack surfaces within multinational organizations
· operational dependence on centralized IT systems for manufacturing and logistics coordination
These characteristics increase the attractiveness of healthcare manufacturing organizations to geopolitically motivated cyber actors seeking disruptive impact rather than financial gain.
S11. Adversary Capability Profiling
Threat Actor
Handala
Actor overview:
· politically motivated hacktivist collective associated with the pro-Palestinian cyber ecosystem
· active since approximately 2023
· known for campaigns combining data exfiltration, destructive malware activity, and public messaging operations
CyberDax adversary capability assessment evaluates four operational dimensions.
Attacker Skill
· moderate malware development capability
· ability to conduct phishing and credential compromise campaigns
· capable of executing multi-stage intrusion operations
Infrastructure Maturity
· moderate infrastructure management capability
· reliance on publicly accessible communication platforms and cloud infrastructure
· limited evidence of hardened command-and-control infrastructure
Operational Scalability
· demonstrated ability to conduct campaigns affecting multinational organizations
· capable of coordinating disruptive activity across large enterprise environments
Escalation Likelihood
· moderate escalation probability driven by geopolitical motivations
· activity levels likely to increase during periods of regional political tension
Overall capability assessment:
Handala demonstrates mid-tier cyber operational capability with destructive intent, capable of generating significant enterprise disruption when targeting organizations with large digital attack surfaces.
S12. Exploit Status
Current intelligence assessment:
· no confirmed exploitation of a publicly disclosed software vulnerability
· no confirmed CVE associated with the destructive activity observed in this incident
Exploit Activity
Active exploitation not observed at this time.
Most likely intrusion pathways include:
· phishing-based credential compromise
· abuse of enterprise identity infrastructure
· lateral movement through administrative access channels
· propagation using enterprise management or administrative tools
The absence of a confirmed vulnerability suggests the operation relied primarily on identity compromise and operational access rather than software exploitation.
KEV Verification
· no associated CVE currently appears within the CISA Known Exploited Vulnerabilities catalog
Patch Status
· Not known at this time due to absence of a confirmed vulnerability associated with the incident
S13. Confidence & Assessment Statement
Assessment confidence level: Moderate
Confidence drivers include:
· credible reporting of enterprise operational disruption
· threat actor claims consistent with destructive cyber campaign behavior
· observed attack patterns consistent with previous wiper malware operations
Remaining intelligence gaps include:
· precise initial intrusion vector
· confirmed malware variant used during the destructive phase
· verified scope of endpoint destruction
· infrastructure used to coordinate the destructive execution stage
Despite these uncertainties, available evidence supports the assessment that the event represents a destructive cyber intrusion designed to disrupt enterprise operations rather than conduct financially motivated extortion.
S14. Campaign Timeline
Earliest Known Intrusion Window
Prior to March 5, 2026 — adversary intrusion activity likely began before destructive operations became visible inside Stryker’s internal network environment. The precise intrusion start date remains not known at this time.
Last Observed Activity
March 6, 2026 — destructive activity appears to have concluded shortly before containment procedures and recovery operations were initiated.
Public Reporting Date
March 5, 2026 — the incident became publicly known following reports of system outages affecting Stryker corporate operations.
Campaign Timeline Reconstruction
Initial intrusion window
· adversaries likely obtained access prior to March 5, 2026
· credential compromise or phishing represents the most plausible intrusion vector
Environment reconnaissance phase
· attackers likely enumerated internal infrastructure and system assets
· identification of operationally significant hosts and services
Privilege expansion phase
· privileged access likely obtained through compromised credentials
Destructive execution phase
· destructive payloads or automated scripts executed across compromised hosts
Operational disruption phase
· destructive activity triggered outages affecting internal services and operational systems
Containment and recovery phase
· affected systems isolated
· restoration procedures initiated
· forensic investigation of compromised hosts began
S15. Attack Overview
The campaign reflects a destructive cyber intrusion designed to disable systems and disrupt organizational operations.
Observed campaign characteristics include:
· identity-based intrusion rather than exploitation of a software vulnerability
· expansion of access through compromised credentials
· lateral movement across systems using remote administration mechanisms
· execution of destructive payloads targeting endpoint hosts
This operational model aligns with destructive cyber campaigns conducted by geopolitically motivated actors seeking rapid operational impact.
S16. MITRE ATT&CK Chain Flow Mapping
Observed campaign behavior aligns with several MITRE ATT&CK techniques commonly associated with destructive cyber operations.
Initial Access
T1566 — Phishing
Adversaries likely used phishing techniques to obtain credentials or establish initial access.
Execution
T1059 — Command and Scripting Interpreter
Command-line environments or scripting tools may have been used to execute malicious commands.
Persistence
T1547 — Boot or Logon Autostart Execution
Persistence mechanisms may have enabled attackers to maintain access within compromised systems.
Credential Access
T1003 — Credential Dumping
Credential harvesting techniques may have enabled expansion of privileged access.
Discovery
T1082 — System Information Discovery
Attackers likely enumerated internal systems to identify operational targets.
Lateral Movement
T1021 — Remote Services
Remote administration services may have enabled movement across compromised hosts.
Command and Control
T1102 — Web Service
Web-based communication channels may have supported attacker coordination.
Impact
T1485 — Data Destruction
Destructive activity likely deleted or corrupted system data to disable affected hosts.
S17. Attack Flow
The intrusion followed a structured destructive attack sequence.
Stage 1 — Initial Access
· phishing activity targeting organizational users
· compromise of user credentials
Stage 2 — Privileged Access
· escalation of privileges through compromised accounts
Stage 3 — Environment Discovery
· enumeration of internal systems and services
Stage 4 — Lateral Movement
· Adversaries moved between hosts using remote administration tools
Stage 5 — Destructive Payload Deployment
· destructive malware or scripts executed across compromised endpoints
Stage 6 — Operational Impact
· system outages and disruption of organizational operations
The sequence prioritizes rapid disruption once privileged access is achieved.
S18. Exploit Conditions Snapshot
Conditions likely required for the attack to succeed include:
· compromise of privileged credentials
· insufficient monitoring of privileged account activity
· ability to execute commands or scripts on endpoint systems
· access to management interfaces capable of distributing commands across multiple hosts
These conditions illustrate how identity compromise combined with privileged access can enable destructive cyber operations.
S19. Malware Analysis
Destructive malware associated with campaigns attributed to the Handala threat actor group focuses on operational disruption rather than financial extortion.
Typical destructive malware behavior includes:
· overwriting or deleting stored data
· corruption of file systems or operating system components
· disabling system functionality
· interference with system recovery mechanisms
The destructive payload likely targeted endpoint hosts within the corporate network.
Specific technical characteristics of the malware used in the Stryker incident remain not known at this time.
Analytical Note
The absence of artifact hashes does not reduce detection capability.
Behavioral detection across identity, endpoint, and network telemetry often provides earlier detection of destructive campaigns than signature-based malware detection.
S20. Malware Families
Public reporting linking specific malware families to the Stryker incident remains limited.
Threat actor activity attributed to Handala has previously involved:
· destructive wiper malware variants
· automated scripts used to initiate destructive actions
· loaders capable of distributing payloads across compromised hosts
The precise malware family used in this incident remains not known at this time.
Malware Artifacts and File Hash Intelligence
· No malware samples or SHA256 hashes associated with the Handala intrusion affecting Stryker were publicly available at the time of reporting.
Why no hashes exist yet
This situation is actually common for destructive attacks, especially early in an incident.
Reasons include:
· custom one-off malware builds
· fileless or script-based execution
· payload destruction after execution
· victim forensic containment before sample release
· no submission to public malware repositories
Handala has previously used custom destructive wipers targeting Windows and Linux systems, which often vary per campaign.
That makes hash reuse less likely.
S20A. Adversary Tradecraft Summary
The Handala intrusion affecting Stryker reflects a destructive intrusion model designed to maximize operational disruption rather than financial extortion.
Observed and likely adversary tradecraft includes:
Initial Access
· phishing campaigns targeting enterprise users
· delivery of malicious documents or credential harvesting pages
Execution
· privileged shell execution on compromised workstation systems
· script-based loaders used to stage destructive payloads
Credential Access
· attempts to access LSASS memory
· use of administrative credentials obtained through phishing or credential reuse
Lateral Movement
· workstation authentication across multiple internal hosts
· use of remote administration protocols such as SMB, WinRM, or RDP
Impact
· high-volume deletion of user files and system data
· removal of recovery artifacts and backup resources
Operational Objective
· rapid disruption of enterprise operations rather than long-term persistence or financial extortion.
The tradecraft reflects a disruption-first operational model prioritizing speed of destructive impact over stealth.
S21. Indicators and Behavioral Artifacts
Indicators associated with destructive cyber intrusion campaigns provide detection opportunities across endpoint, identity, and network telemetry sources.
Because detailed forensic artifacts have not been publicly disclosed for the Stryker incident, several indicator categories remain limited. The following indicators and behavioral artifacts represent the most reliable detection signals currently associated with the campaign.
Network Indicators
Confidence: Not known at this time
· attacker command-and-control domains
· malicious IP infrastructure
· suspicious DNS resolution patterns
Specific network indicators associated with the intrusion remain not known at this time.
Host Indicators
Confidence: Not known at this time
· destructive executable hashes
· malware loader artifacts
· malicious scheduled task creation
Host-based forensic artifacts associated with the intrusion remain not known at this time.
Behavioral Indicators
Confidence: High
These behaviors represent the most reliable indicators currently associated with the campaign.
High Confidence Behavioral Indicators
· abnormal privileged account authentication activity
· administrative remote service connections between internal hosts
· command interpreter activity executed across multiple endpoints
· simultaneous system disruption affecting multiple hosts
Moderate Confidence Behavioral Indicators
Confidence: Moderate
· command interpreter activity initiated by privileged accounts outside normal administrative patterns
· rapid file deletion or modification activity across endpoint systems
· administrative utilities executed outside normal operational schedules
· abnormal remote management sessions between workstation systems
Low Confidence Behavioral Indicators
Confidence: Low
Indicators historically associated with campaigns attributed to the Handala actor group include:
· threat actor messaging claiming responsibility for disruptive cyber activity
· public disclosure of alleged data theft following operational disruption
Primary telemetry sources capable of capturing these artifacts include:
· endpoint detection and response telemetry
· authentication and identity logs
· DNS and network proxy telemetry
· Windows event logging
S22. Detection Coverage Matrix
Detection coverage varies depending on the telemetry visibility and monitoring maturity present within the security architecture.
Endpoint Telemetry
Strongest Coverage
· command interpreter execution monitoring
· destructive process behavior detection
· abnormal script execution detection
Primary Gaps
· administrative misuse of legitimate system utilities
· destructive activity executed through scheduled tasks
Residual Risk
· destructive commands executed through trusted administrative processes
Identity Telemetry
Strongest Coverage
· abnormal authentication activity detection
· privileged account monitoring
Primary Gaps
· credential misuse occurring during legitimate working hours
Residual Risk
· attackers operating with compromised credentials appearing as legitimate users
Network and DNS Telemetry
Strongest Coverage
· suspicious outbound network connections
· abnormal DNS resolution patterns
Primary Gaps
· lateral movement between trusted internal systems
Residual Risk
· administrative traffic appearing legitimate within internal networks
Email Security Telemetry
Strongest Coverage
· phishing detection and attachment analysis
Primary Gaps
· targeted spear-phishing campaigns
Residual Risk
· credential harvesting attacks bypassing email detection mechanisms
S23. Detection Engineering Matrix (Strategic Layer)
Strategic detection engineering focuses on identifying attacker behaviors across telemetry sources rather than relying solely on signatures.
Initial Access Detection
Relevant ATT&CK Technique
T1566 — Phishing
Strategic Detection Objective
· identify phishing interactions followed by abnormal authentication activity
Execution Detection
Relevant ATT&CK Technique
T1059 — Command and Scripting Interpreter
Strategic Detection Objective
· detect abnormal command interpreter activity initiated by privileged accounts
Credential Access Detection
Relevant ATT&CK Technique
T1003 — Credential Dumping
Strategic Detection Objective
· identify suspicious processes interacting with credential storage mechanisms
Discovery Detection
Relevant ATT&CK Technique
T1082 — System Information Discovery
Strategic Detection Objective
· detect abnormal enumeration of system configuration information
Lateral Movement Detection
Relevant ATT&CK Technique
T1021 — Remote Services
Strategic Detection Objective
· identify remote administrative activity between internal hosts
Impact Detection
Relevant ATT&CK Technique
T1485 — Data Destruction
Strategic Detection Objective
· detect rapid file deletion activity or destructive system behavior across endpoints
S24. Detection Engineering Matrix (Operational Layer)
Operational detection engineering converts strategic detection objectives into telemetry-based detection logic.
Initial Access Detection
ATT&CK Technique
T1566 — Phishing
Operational Detection Logic
· correlate email phishing alerts with authentication attempts within a defined time window
· identify authentication events following user interaction with malicious email content
Telemetry Dependency
· email security gateway telemetry
· authentication logs
Execution Detection
ATT&CK Technique
T1059 — Command and Scripting Interpreter
Operational Detection Logic
· detect command interpreter execution initiated by privileged accounts
· identify abnormal script execution across multiple endpoints
Telemetry Dependency
· endpoint process telemetry
· Windows Event ID 4688 process creation logs
Credential Access Detection
ATT&CK Technique
T1003 — Credential Dumping
Operational Detection Logic
· detect processes attempting to access credential storage mechanisms
· identify abnormal memory access associated with credential harvesting
Telemetry Dependency
· endpoint detection telemetry
· security event logs
Discovery Detection
ATT&CK Technique
T1082 — System Information Discovery
Operational Detection Logic
· detect execution of system information enumeration commands across multiple hosts
Telemetry Dependency
· endpoint process telemetry
· command-line auditing logs
Lateral Movement Detection
ATT&CK Technique
T1021 — Remote Services
Operational Detection Logic
· identify remote administrative connections between internal hosts
· detect abnormal authentication patterns across multiple systems
Telemetry Dependency
· authentication logs
· network telemetry
Impact Detection
ATT&CK Technique
T1485 — Data Destruction
Operational Detection Logic
· detect rapid file deletion events across endpoints
· identify destructive system activity affecting operating system integrity
Telemetry Dependency
· endpoint file monitoring telemetry
· EDR behavioral detection logs
S25. Ultra-Tuned Detection Engineering Rules
The following rules operationalize the behaviors identified in S21 through S24. Rules are grouped by system type, use the locked CyberDax field order, and are tuned to reduce avoidable alert noise through role scoping, parent-process suppression, bounded windows, aggregation thresholds, and approved-tool exclusions.
Suricata Detection Rules
Rule Name
Workstation Remote Administration Fan-Out
Purpose
Detect likely lateral movement from workstation-class systems to multiple internal destinations over administrative protocols.
ATT&CK Technique
T1021 — Remote Services
Telemetry Dependency
· Suricata network telemetry
· workstation subnet definitions
· approved jump host and management server allowlist
· internal server and domain controller asset inventory
Tuning Explanation
· restricted to workstation-origin traffic
· excludes approved management infrastructure through suppression and network-variable scoping
· tuned to repeated administrative protocol use rather than isolated support activity
· intended for promotion only when supported by destination-cardinality enrichment
Detection Logic
alert tcp $WORKSTATION_NET any -> $HOME_NET [135,139,445,3389,5985,5986] (
msg:"CYBERDAX workstation remote administration fan-out";
flow:established,to_server;
threshold:type both, track by_src, count 12, seconds 600;
classtype:attempted-admin;
sid:9302501;
rev:1;
)
Rule Name
Repeated External DNS Lookups to Non-Approved Domains
Purpose
Detect repeated workstation DNS lookups to external domains outside the approved enterprise set that may indicate staging or web-service coordination.
ATT&CK Technique
T1102 — Web Service
Telemetry Dependency
· Suricata DNS telemetry
· enterprise domain allowlist
· internal DNS resolver list
· workstation subnet definitions
Tuning Explanation
· scoped to workstation clients and excludes internal resolvers
· requires repeated lookups in a short interval
· designed to be paired with allowlist enrichment for common SaaS, identity, update, security, and CDN domains
· raises fidelity when the domain is newly observed in the environment
Detection Logic
alert dns $WORKSTATION_NET any -> !$DNS_RESOLVERS 53 (
msg:"CYBERDAX repeated endpoint DNS lookups to non-approved domain";
dns.query;
threshold:type both, track by_src, count 10, seconds 300;
classtype:trojan-activity;
sid:9302502;
rev:1;
)
SentinelOne Detection Rules
Rule Name
Privileged Shell Burst on Workstations
Purpose
Detect suspicious bursts of shell execution by privileged users on workstation systems.
ATT&CK Technique
T1059 — Command and Scripting Interpreter
Telemetry Dependency
· SentinelOne Deep Visibility process telemetry
· endpoint role tags
· privileged identity inventory
· approved management parent-process allowlist
Tuning Explanation
· limited to workstation endpoints
· excludes expected enterprise management tooling
· requires repeated shell execution inside a bounded window
· raises fidelity when parent lineage is Office, browser, script host, or unsigned launcher
Detection Logic
AgentOs = "windows"
AND EndpointType = "workstation"
AND ProcessName IN ("powershell.exe","pwsh.exe","cmd.exe","wscript.exe","cscript.exe")
AND UserName MATCHES "(?i).*(admin|adm|priv).*"
AND NOT ParentProcessName IN ("ccmexec.exe","intunemanagementextension.exe","pdqdeployrunner.exe","taniumclient.exe","kaceagent.exe","bomgar-scc.exe","teams.exe")
AND (
ParentProcessName IN ("winword.exe","excel.exe","outlook.exe","acrord32.exe","chrome.exe","msedge.exe","wscript.exe","cscript.exe")
OR SignedStatus != "signed_trusted"
)
GROUP BY AgentUuid, UserName, ParentProcessName
HAVING COUNT(ProcessName) >= 5 OVER 10m
Rule Name
Unauthorized LSASS Access or Dump Behavior
Purpose
Detect likely credential dumping behavior targeting LSASS.
ATT&CK Technique
T1003 — Credential Dumping
Telemetry Dependency
· SentinelOne memory access telemetry
· process telemetry
· approved security-tool allowlist
Tuning Explanation
· excludes expected EDR, AV, IR, and Microsoft security tooling
· requires direct LSASS access or recognized dump behavior
· suppresses common legitimate Windows parentage
· tuned to reduce noise from ordinary system inspection activity
Detection Logic
AgentOs = "windows"
AND (
(TgtProcName = "lsass.exe" AND EventType = "Process Accessed")
OR ProcessName IN ("procdump.exe","mimikatz.exe","rundll32.exe")
OR SrcProcCmdLine CONTAINS_ANY ("MiniDump","sekurlsa::logonpasswords","comsvcs.dll")
)
AND NOT ProcessName IN ("MsMpEng.exe","SentinelAgent.exe","csfalconservice.exe","xagt.exe","taskmgr.exe","procexp.exe")
AND NOT ParentProcessName IN ("services.exe","wininit.exe","lsass.exe")
Rule Name
Rapid User-Directory Deletion Spike
Purpose
Detect destructive deletion behavior on workstation endpoints consistent with wipe activity.
ATT&CK Technique
T1485 — Data Destruction
Telemetry Dependency
· SentinelOne file telemetry
· endpoint role tags
· approved sync, backup, migration, and installer process allowlist
Tuning Explanation
· restricted to user-facing directories on workstation endpoints
· excludes approved sync, backup, migration, and installer tooling
· requires high deletion volume in a short interval
· increases fidelity when parent process is a shell, script host, or unsigned binary
Detection Logic
AgentOs = "windows"
AND EndpointType = "workstation"
AND EventType = "File Deleted"
AND FileFullName MATCHES "(?i)C:\\Users\\[^\\]+\\(Desktop|Documents|Downloads|Pictures)\\.*"
AND NOT ProcessName IN ("onedrive.exe","teams.exe","robocopy.exe","veeamagent.exe","usmtutils.exe","trustedinstaller.exe","msiexec.exe","explorer.exe")
GROUP BY AgentUuid, ProcessName, ParentProcessName
HAVING COUNT(FileFullName) >= 500 OVER 5m
Splunk Detection Rules
Rule Name
Malicious Email Followed by Suspicious Interactive Authentication
Purpose
Detect likely phishing-driven credential misuse shortly after malicious email delivery or click activity.
ATT&CK Technique
T1566 — Phishing
Telemetry Dependency
· email security gateway logs
· identity provider authentication logs
· MFA result logs
· user-to-IP baseline lookup
· phishing simulation allowlist
Tuning Explanation
· excludes internal training and simulation campaigns
· restricted to successful interactive authentication
· suppresses service accounts, token refreshes, and background application sessions
· raises fidelity when login originates from a new IP, MFA is bypassed, or geography is unusual
Detection Logic
index=email_security (verdict="malicious" OR threat_category="phish" OR click_action="clicked")
NOT sender_domain IN ("phishsim.company.com","training.company.com")
| eval phish_time=_time
| rename recipient as user
| fields user phish_time message_id sender_domain url_domain
| join type=inner user max=0 [
search index=idp_auth action="success" auth_type="interactive" earliest=-30m latest=+30m
NOT user IN ("svc_backup","svc_sync","svc_siem","svc_adfs")
NOT app IN ("Background Token Refresh","Service Authentication","Daemon")
| eval auth_time=_time
| fields user auth_time src_ip country mfa_result app
]
| where auth_time>=phish_time AND auth_time<=phish_time+1800
| lookup user_ip_baseline user src_ip OUTPUT is_known_ip
| eval suspicious=if(isnull(is_known_ip) OR mfa_result IN ("bypass","fatigue_accepted","not_enforced"),1,0)
| where suspicious=1
| stats earliest(phish_time) as first_phish earliest(auth_time) as first_auth values(src_ip) as src_ip values(country) as country values(mfa_result) as mfa_result values(app) as app by user
Rule Name
Workstation Authentication Fan-Out to Multiple Internal Hosts
Purpose
Detect likely lateral movement through successful workstation-origin authentication to multiple internal hosts.
ATT&CK Technique
T1021 — Remote Services
Telemetry Dependency
· Windows authentication logs
· asset inventory lookup
· approved management infrastructure allowlist
Tuning Explanation
· restricted to workstation-origin traffic
· excludes domain controllers, jump hosts, SCCM, patch servers, and approved management infrastructure
· requires multiple distinct destinations within a bounded window
· tuned to successful network logons only
Detection Logic
index=wineventlog sourcetype=WinEventLog:Security EventCode=4624 Logon_Type=3
| lookup asset_inventory ip as Source_Network_Address OUTPUTNEW src_asset_role src_host
| lookup asset_inventory host as ComputerName OUTPUT dest_asset_role
| where src_asset_role="workstation"
| search NOT ComputerName IN ("jump01","jump02","sccm01","patch01","dc01","dc02")
| bin _time span=10m
| stats dc(ComputerName) as distinct_targets values(ComputerName) as targets count by _time, user, Source_Network_Address
| where distinct_targets >= 5 AND count >= 8
Rule Name
Mass Deletion Correlation on Workstations
Purpose
Detect destructive deletion spikes from EDR-ingested file telemetry on workstation endpoints.
ATT&CK Technique
T1485 — Data Destruction
Telemetry Dependency
· EDR file telemetry ingested into Splunk
· asset role inventory
· approved process allowlist
Tuning Explanation
· limited to workstation assets
· scoped to user-facing paths
· excludes approved sync, backup, migration, and installer tooling
· requires substantial deletion volume in a short window
Detection Logic
index=edr_files event_action="delete"
| lookup asset_inventory host OUTPUT asset_role
| where asset_role="workstation"
| regex file_path="(?i)^C:\\\\Users\\\\[^\\\\]+\\\\(Desktop|Documents|Downloads|Pictures)\\\\"
| search NOT process_name IN ("onedrive.exe","robocopy.exe","veeamagent.exe","usmtutils.exe","trustedinstaller.exe","msiexec.exe","explorer.exe")
| bin _time span=5m
| stats count values(process_name) as process_name by _time, host, user
| where count >= 500
Elastic Detection Rules
Rule Name
Multi-Host Discovery Command Burst
Purpose
Detect repeated system enumeration behavior across multiple endpoints.
ATT&CK Technique
T1082 — System Information Discovery
Telemetry Dependency
· Elastic Defend process events
· endpoint role inventory
· approved management-tool allowlist
Tuning Explanation
· excludes approved inventory and management tooling
· tuned to reduce noise from isolated diagnostics
· requires repeated discovery behavior within a bounded window
· implemented as a self-contained threshold-style ES|QL detection
Detection Logic
FROM logs-endpoint.events.process-*
| WHERE host.os.type == "windows"
AND process.name IN ("cmd.exe","powershell.exe","pwsh.exe","wmic.exe")
AND (
process.command_line LIKE "*systeminfo*" OR
process.command_line LIKE "*hostname*" OR
process.command_line LIKE "*ipconfig*" OR
process.command_line LIKE "*whoami*" OR
process.command_line LIKE "*Get-ComputerInfo*" OR
process.command_line LIKE "*wmic computersystem*"
)
AND process.parent.name NOT IN ("ccmexec.exe","IntuneManagementExtension.exe","TaniumClient.exe","PDQDeployRunner.exe")
| EVAL time_bucket = DATE_TRUNC(10 minutes, @timestamp)
| STATS execution_count = COUNT(*), distinct_hosts = COUNT_DISTINCT(host.name)
BY user.name, process.parent.name, time_bucket
| WHERE execution_count >= 5 AND distinct_hosts >= 3
Rule Name
Internal Remote Service Lateral Movement on Workstations
Purpose
Detect suspicious internal remote administration from workstation sources.
ATT&CK Technique
T1021 — Remote Services
Telemetry Dependency
· Elastic authentication telemetry
· network telemetry
· workstation and server asset inventory
Tuning Explanation
· restricted to workstation-origin activity
· excludes approved management servers and jump hosts
· uses self-contained fan-out logic with distinct destination thresholds
· tuned to reduce noise from isolated support activity
Detection Logic
FROM logs-windows.security-*, logs-system.security-*
| WHERE host.os.type == "windows"
AND winlog.event_id == 4624
AND winlog.event_data.LogonType == "3"
AND source.ip IS NOT NULL
AND destination.ip IS NOT NULL
AND source.ip != destination.ip
AND destination.hostname NOT IN ("jump01","jump02","sccm01","patch01","dc01","dc02")
| EVAL time_bucket = DATE_TRUNC(10 minutes, @timestamp)
| STATS distinct_targets = COUNT_DISTINCT(destination.hostname), total_events = COUNT(*)
BY source.ip, user.name, time_bucket
| WHERE distinct_targets >= 5 AND total_events >= 8
Rule Name
Endpoint Mass File Deletion Detection
Purpose
Detect destructive deletion behavior on workstation endpoints.
ATT&CK Technique
T1485 — Data Destruction
Telemetry Dependency
· Elastic Defend file events
· process lineage telemetry
· asset role inventory
Tuning Explanation
· scoped to workstation endpoints and user-facing directories
· excludes approved sync, backup, migration, and installer tooling
· uses self-contained thresholding
· raises severity when linked process is a shell, script host, or unsigned binary
Detection Logic
FROM logs-endpoint.events.file-*
| WHERE host.os.type == "windows"
AND event.action == "deletion"
AND (
file.path LIKE "C:\\Users\\%\\Documents\\%" OR
file.path LIKE "C:\\Users\\%\\Desktop\\%" OR
file.path LIKE "C:\\Users\\%\\Downloads\\%" OR
file.path LIKE "C:\\Users\\%\\Pictures\\%"
)
AND process.name NOT IN ("onedrive.exe","robocopy.exe","veeamagent.exe","usmtutils.exe","trustedinstaller.exe","msiexec.exe","explorer.exe")
| EVAL time_bucket = DATE_TRUNC(5 minutes, @timestamp)
| STATS deletion_count = COUNT(*)
BY host.name, process.name, process.parent.name, time_bucket
| WHERE deletion_count >= 500
QRadar Detection Rules
Rule Name
Malicious Email Followed by Suspicious Successful Login
Purpose
Detect likely phishing-driven credential abuse using QRadar correlation logic.
ATT&CK Technique
T1566 — Phishing
Telemetry Dependency
· email security events
· authentication success events
· MFA events
· user baseline reference sets
Tuning Explanation
· excludes internal phishing simulation traffic and service identities
· requires suspicious email plus successful interactive authentication
· offense logic requires new source IP, unusual geography, or MFA bypass to reduce noise
· implemented as a completed CRE offense design rather than a standalone AQL search
Detection Logic
SELECT username, sourceip, destinationip, QIDNAME(qid) AS event_name, devicetime
FROM events
WHERE
(
LOGSOURCETYPENAME(devicetype) ILIKE '%email%'
AND (UTF8(payload) ILIKE '%phish%' OR UTF8(payload) ILIKE '%malicious%' OR UTF8(payload) ILIKE '%credential%')
)
OR
(
LOGSOURCETYPENAME(devicetype) ILIKE '%authentication%'
AND QIDNAME(qid) ILIKE '%login success%'
AND UTF8(payload) NOT ILIKE '%svc_%'
)
LAST 30 MINUTES
QRadar CRE Rule Logic
Rule Test 1
- Event matches suspicious email delivery or phishing interaction
- Username is not in Service_Accounts
- Sender or campaign is not in Approved_Phishing_Simulations
Rule Test 2
- Successful interactive authentication occurs for the same username within 30 minutes
Rule Test 3
- At least one of the following is true:
- source IP not in User_Baseline_IPs reference set
- source country in High_Risk_Geographies reference set
- MFA result indicates bypass, fatigue acceptance, or not enforced
Offense Action
- Create offense: CYBERDAX phishing followed by suspicious login
- Magnitude: High
- Source equals username
Rule Name
Workstation Internal Authentication Fan-Out
Purpose
Detect likely lateral movement using successful workstation-origin authentication to multiple internal systems.
ATT&CK Technique
T1021 — Remote Services
Telemetry Dependency
· Windows authentication events
· asset role reference sets
· network flow enrichment
Tuning Explanation
· excludes domain controllers, jump hosts, and approved admin subnets
· threshold is encoded directly in the AQL
· offense generation is limited to workstation-class sources
Detection Logic
SELECT sourceip, username, COUNT(DISTINCT destinationip) AS distinct_targets, COUNT(*) AS total_events
FROM events
WHERE LOGSOURCETYPENAME(devicetype) ILIKE '%windows%'
AND QIDNAME(qid) ILIKE '%login success%'
AND sourceip <> destinationip
LAST 10 MINUTES
GROUP BY sourceip, username
HAVING COUNT(DISTINCT destinationip) >= 5 AND COUNT(*) >= 8
QRadar CRE Rule Logic
Rule Test 1
- Event matches Workstation Internal Authentication Fan-Out AQL result
Rule Test 2
- Source asset belongs to Asset_Role_Workstations reference set
Rule Test 3
- Source asset is not in Approved_Management_Assets or Helpdesk_Assets reference sets
Offense Action
- Create offense: CYBERDAX workstation authentication fan-out
- Magnitude: High
- Source equals source IP and username
Sigma Detection Rules
Rule Name
Privileged Shell Execution on Workstations
Purpose
Detect suspicious shell execution from privileged users or suspicious parent lineage on workstation systems.
ATT&CK Technique
T1059 — Command and Scripting Interpreter
Telemetry Dependency
· Windows process creation logs
· workstation tagging
· approved management-tool allowlist
Tuning Explanation
· excludes known enterprise management tooling
· raises fidelity when parent process is Office, browser, or script engine
· suitable for SIEM-side thresholding rather than alerting on every event
Detection Logic
title: CyberDax Privileged Shell Execution on Workstations
id: cdx-1059-priv-shell-01
status: experimental
logsource:
product: windows
category: process_creation
detection:
shell:
Image|endswith:
- '\cmd.exe'
- '\powershell.exe'
- '\pwsh.exe'
- '\wscript.exe'
- '\cscript.exe'
suspicious_parent:
ParentImage|endswith:
- '\winword.exe'
- '\excel.exe'
- '\outlook.exe'
- '\acrord32.exe'
- '\chrome.exe'
- '\msedge.exe'
- '\wscript.exe'
- '\cscript.exe'
suspicious_user:
User|contains:
- 'admin'
- 'adm'
- 'priv'
filter_legit:
ParentImage|endswith:
- '\ccmexec.exe'
- '\IntuneManagementExtension.exe'
- '\PDQDeployRunner.exe'
- '\TaniumClient.exe'
condition: shell and (suspicious_parent or suspicious_user) and not filter_legit
level: high
Rule Name
System Discovery Command Burst
Purpose
Detect suspicious system-information enumeration activity.
ATT&CK Technique
T1082 — System Information Discovery
Telemetry Dependency
· Windows process creation logs
· command-line auditing
· approved inventory-tool allowlist
Tuning Explanation
· excludes approved inventory and management tooling
· intended for aggregation across hosts or repeated executions by the same user
· tuned to reduce false positives from isolated support actions
Detection Logic
title: CyberDax System Discovery Command Burst
id: cdx-1082-discovery-01
status: experimental
logsource:
product: windows
category: process_creation
detection:
image:
Image|endswith:
- '\cmd.exe'
- '\powershell.exe'
- '\pwsh.exe'
- '\wmic.exe'
cli:
CommandLine|contains:
- 'systeminfo'
- 'hostname'
- 'ipconfig'
- 'whoami'
- 'Get-ComputerInfo'
- 'wmic computersystem'
filter_legit:
ParentImage|endswith:
- '\ccmexec.exe'
- '\IntuneManagementExtension.exe'
- '\TaniumClient.exe'
- '\PDQDeployRunner.exe'
condition: image and cli and not filter_legit
level: medium
YARA Detection Rules
Rule Name
Destructive Script and Wiper Artifact Detection
Purpose
Identify scripts or dropped artifacts containing multiple destructive patterns associated with wipe or mass-deletion activity.
ATT&CK Technique
T1485 — Data Destruction
Telemetry Dependency
· malware repository ingestion
· EDR quarantine export feed
· sandbox file triage
Tuning Explanation
· requires multiple destructive indicators rather than a single generic string
· intended for triage and quarantine pipelines rather than blanket scanning of all repositories
· suppress known internal admin-cleanup repositories where applicable
Detection Logic
rule CYBERDAX_Destructive_Wiper_Artifacts
{
meta:
description = "Detects destructive script or wiper artifact patterns"
author = "CyberDax"
date = "2026-03-11"
confidence = "high"
strings:
$s1 = "vssadmin delete shadows" nocase ascii wide
$s2 = "wbadmin delete catalog" nocase ascii wide
$s3 = "wevtutil cl" nocase ascii wide
$s4 = "cipher /w:" nocase ascii wide
$s5 = "del /f /q /s" nocase ascii wide
$s6 = "bcdedit /set {default} recoveryenabled no" nocase ascii wide
condition:
3 of ($s*)
}
Rule Name
Credential Dumping Tooling Artifact Detection
Purpose
Identify artifacts containing strings associated with credential dumping.
ATT&CK Technique
T1003 — Credential Dumping
Telemetry Dependency
· malware triage scanning
· EDR quarantine exports
· sandbox artifact ingestion
Tuning Explanation
· requires multiple credential-dumping related strings to reduce false positives
· intended for malware triage rather than unrestricted scanning of development repositories or sanctioned test libraries
Detection Logic
rule CYBERDAX_Credential_Dumping_Artifacts
{
meta:
description = "Detects credential dumping artifact strings"
author = "CyberDax"
date = "2026-03-11"
confidence = "medium"
strings:
$a1 = "sekurlsa::logonpasswords" nocase ascii wide
$a2 = "MiniDumpWriteDump" ascii wide
$a3 = "lsass" nocase ascii wide
$a4 = "wdigest" nocase ascii wide
$a5 = "mimikatz" nocase ascii wide
condition:
2 of ($a*)
}
AWS Detection Rules
Rule Name
Suspicious IAM Privilege Escalation by Human Principal
Purpose
Detect high-risk AWS IAM policy or credential changes by non-approved, non-automation identities.
ATT&CK Technique
T1078 — Valid Accounts
Telemetry Dependency
· AWS CloudTrail
· approved automation-role allowlist
· approved change window calendar
· identity baseline by source IP and region
Tuning Explanation
· excludes Terraform, CloudFormation, CI/CD, and approved break-glass automation roles
· prioritizes human principals, after-hours changes, new source IPs, or unusual regions
· repeated high-risk IAM actions are required for alert promotion
Detection Logic
SELECT userIdentity.arn,
userIdentity.type,
sourceIPAddress,
awsRegion,
COUNT(*) AS action_count,
MIN(eventTime) AS first_seen,
MAX(eventTime) AS last_seen
FROM aws_cloudtrail
WHERE eventSource = 'iam.amazonaws.com'
AND eventName IN ('AttachUserPolicy','AttachRolePolicy','PutUserPolicy','PutRolePolicy','CreateAccessKey','UpdateAssumeRolePolicy')
AND userIdentity.type = 'IAMUser'
AND userIdentity.arn NOT LIKE '%role/Terraform%'
AND userIdentity.arn NOT LIKE '%role/CloudFormation%'
AND userIdentity.arn NOT LIKE '%role/ci-cd%'
AND userIdentity.arn NOT LIKE '%role/breakglass-automation%'
GROUP BY userIdentity.arn, userIdentity.type, sourceIPAddress, awsRegion, DATE_BIN(INTERVAL '10' MINUTE, eventTime)
HAVING COUNT(*) >= 2
Rule Name
Destructive AWS Snapshot or Backup Deletion by Non-Approved Principal
Purpose
Detect suspicious deletion of AWS recovery artifacts outside approved maintenance paths.
ATT&CK Technique
T1485 — Data Destruction
Telemetry Dependency
· AWS CloudTrail
· AWS Backup logs
· approved backup and maintenance role allowlist
· maintenance window calendar
Tuning Explanation
· excludes backup service roles, lifecycle jobs, and approved automation
· tuned to recovery-impairing actions rather than generic object cleanup
· repeated destructive actions are required for alert promotion
Detection Logic
SELECT userIdentity.arn,
userIdentity.type,
sourceIPAddress,
COUNT(*) AS action_count,
MIN(eventTime) AS first_seen,
MAX(eventTime) AS last_seen
FROM aws_cloudtrail
WHERE eventName IN ('DeleteSnapshot','DeleteDBSnapshot','DeleteRecoveryPoint','DeleteBackupVault')
AND userIdentity.arn NOT LIKE '%role/aws-backup%'
AND userIdentity.arn NOT LIKE '%role/Terraform%'
AND userIdentity.arn NOT LIKE '%role/CloudFormation%'
AND userIdentity.arn NOT LIKE '%role/approved-maintenance%'
GROUP BY userIdentity.arn, userIdentity.type, sourceIPAddress, DATE_BIN(INTERVAL '10' MINUTE, eventTime)
HAVING COUNT(*) >= 3
Azure Detection Rules
Rule Name
Suspicious Azure Role Assignment or Privileged Identity Change
Purpose
Detect unauthorized RBAC or privileged identity changes by non-approved Azure or Entra principals.
ATT&CK Technique
T1078 — Valid Accounts
Telemetry Dependency
· Azure Activity Logs
· Entra ID AuditLogs
· approved service principal allowlist
· PIM workflow context
· change window calendar
Tuning Explanation
· excludes approved automation service principals and expected PIM activation workflows
· focuses on role assignment, credential addition, and privileged application changes
· repeated privileged actions are required for alert promotion
Detection Logic
union AzureActivity, AuditLogs
| where OperationNameValue in (
"Microsoft.Authorization/roleAssignments/write",
"Add member to role",
"Add service principal credentials",
"Update application"
)
| where Caller !in~ ("terraform-spn","azure-devops-spn","approved-automation-spn","pim-service-principal")
| summarize action_count=count(), first_seen=min(TimeGenerated), last_seen=max(TimeGenerated) by Caller, bin(TimeGenerated, 10m)
| where action_count >= 2
Rule Name
Suspicious Azure Backup, Snapshot, or Storage Destructive Change
Purpose
Detect destructive actions against Azure recovery and storage resources by non-approved principals.
ATT&CK Technique
T1485 — Data Destruction
Telemetry Dependency
· Azure Activity Logs
· storage diagnostics
· approved maintenance principal allowlist
· maintenance window calendar
Tuning Explanation
· suppresses approved backup retention workflows and infrastructure automation
· tuned to destructive actions affecting snapshots, disks, recovery items, and blob deletions
· repeated destructive actions are required for alert promotion
Detection Logic
AzureActivity
| where OperationNameValue in (
"Microsoft.Compute/snapshots/delete",
"Microsoft.Compute/disks/delete",
"Microsoft.RecoveryServices/vaults/backupFabrics/protectionContainers/protectedItems/delete",
"Microsoft.Storage/storageAccounts/blobServices/containers/blobs/delete"
)
| where Caller !in~ ("approved-backup-spn","terraform-spn","approved-automation-spn","approved-maintenance-spn")
| summarize action_count=count(), first_seen=min(TimeGenerated), last_seen=max(TimeGenerated) by Caller, bin(TimeGenerated, 10m)
| where action_count >= 3
GCP Detection Rules
Rule Name
Suspicious GCP IAM Policy or Service Account Key Change
Purpose
Detect privilege escalation or persistence-oriented IAM changes by non-approved identities.
ATT&CK Technique
T1078 — Valid Accounts
Telemetry Dependency
· GCP Audit Logs
· approved automation principal allowlist
· principal baseline by source IP or device context
· approved maintenance window calendar
Tuning Explanation
· excludes approved Terraform, deployment, and automation principals
· focuses on SetIamPolicy and service account key creation
· embeds repeated IAM-change thresholding into the detection logic
· raises fidelity for human identities and unfamiliar source context
Detection Logic
resource.type="audited_resource"
(protoPayload.methodName="SetIamPolicy" OR protoPayload.methodName="google.iam.admin.v1.CreateServiceAccountKey")
NOT protoPayload.authenticationInfo.principalEmail=("terraform@" OR "deployment@" OR "approved-automation@" OR "approved-maintenance@")
| stats count by protoPayload.authenticationInfo.principalEmail, sourceLocation.ip, resource.labels.project_id, window(10m)
| where count >= 2
Rule Name
Suspicious GCP Snapshot or Object Destruction by Non-Approved Principal
Purpose
Detect destructive actions affecting GCP snapshots, backups, or storage objects by non-approved identities.
ATT&CK Technique
T1485 — Data Destruction
Telemetry Dependency
· GCP Audit Logs
· storage audit logs
· approved maintenance principal allowlist
· approved maintenance window calendar
Tuning Explanation
· suppresses lifecycle policies and approved automation accounts
· tuned to snapshot deletion, backup deletion, and storage-object destruction
· embeds repeated destructive-action thresholding into the detection logic
· raises fidelity outside approved maintenance windows
Detection Logic
(protoPayload.methodName="v1.compute.snapshots.delete" OR protoPayload.methodName="storage.objects.delete" OR protoPayload.methodName="backupdr.backupPlanAssociations.delete")
NOT protoPayload.authenticationInfo.principalEmail=("approved-backup@" OR "terraform@" OR "approved-automation@" OR "approved-maintenance@")
| stats count by protoPayload.authenticationInfo.principalEmail, sourceLocation.ip, resource.labels.project_id, window(10m)
| where count >= 3
S26. Threat-to-Rule Traceability Matrix
ATT&CK Technique
T1566 — Phishing
Threat Behavior
· phishing-driven credential compromise
· malicious email followed by suspicious successful authentication
Detection Rule
· Malicious Email Followed by Suspicious Interactive Authentication
· Malicious Email Followed by Suspicious Successful Login
Telemetry Source
· email security gateway telemetry
· IdP authentication logs
· MFA logs
Coverage Disposition
· Detected
ATT&CK Technique
T1059 — Command and Scripting Interpreter
Threat Behavior
· suspicious shell execution on workstation endpoints
· script-driven execution by privileged accounts
Detection Rule
· Privileged Shell Burst on Workstations
· Privileged Shell Execution on Workstations
Telemetry Source
· SentinelOne endpoint process telemetry
· Windows process creation logs
Coverage Disposition
· Detected
ATT&CK Technique
T1003 — Credential Dumping
Threat Behavior
· LSASS access
· dump utility execution
· credential dumping artifact presence
Detection Rule
· Unauthorized LSASS Access or Dump Behavior
· Credential Dumping Tooling Artifact Detection
Telemetry Source
· SentinelOne memory and process telemetry
· YARA malware triage feeds
Coverage Disposition
· Detected
ATT&CK Technique
T1082 — System Information Discovery
Threat Behavior
· system reconnaissance and enumeration across internal hosts
Detection Rule
· Multi-Host Discovery Command Burst
· System Discovery Command Burst
Telemetry Source
· Elastic Defend process telemetry
· Windows command-line logging
Coverage Disposition
· Detected
ATT&CK Technique
T1021 — Remote Services
Threat Behavior
· workstation-to-workstation lateral movement
· remote administration fan-out across internal hosts
Detection Rule
· Workstation Remote Administration Fan-Out
· Workstation Authentication Fan-Out to Multiple Internal Hosts
· Internal Remote Service Lateral Movement on Workstations
· Workstation Internal Authentication Fan-Out
Telemetry Source
· Suricata internal network telemetry
· Splunk Windows logon telemetry
· Elastic authentication and network telemetry
· QRadar authentication events
Coverage Disposition
· Detected
ATT&CK Technique
T1485 — Data Destruction
Threat Behavior
· mass endpoint file deletion
· destructive script activity
· cloud recovery artifact deletion
Detection Rule
· Rapid User-Directory Deletion Spike
· Mass Deletion Correlation on Workstations
· Endpoint Mass File Deletion Detection
· Destructive Script and Wiper Artifact Detection
· Destructive AWS Snapshot or Backup Deletion by Non-Approved Principal
· Suspicious Azure Backup, Snapshot, or Storage Destructive Change
· Suspicious GCP Snapshot or Object Destruction by Non-Approved Principal
Telemetry Source
· SentinelOne file telemetry
· Splunk EDR file telemetry
· Elastic file telemetry
· YARA artifact scanning
· AWS CloudTrail and backup logs
· Azure Activity Logs
· GCP Audit Logs
Coverage Disposition
· Detected
ATT&CK Technique
T1078 — Valid Accounts
Threat Behavior
· valid-account abuse for cloud privilege escalation
· unauthorized policy, role, or IAM changes using compromised credentials
Detection Rule
· Suspicious IAM Privilege Escalation by Human Principal
· Suspicious Azure Role Assignment or Privileged Identity Change
· Suspicious GCP IAM Policy or Service Account Key Change
Telemetry Source
· AWS CloudTrail
· Azure Activity Logs and Entra ID AuditLogs
· GCP Audit Logs
Coverage Disposition
· Detected
Coverage Disposition Definitions
Detected
· telemetry and detection logic provide direct alerting capability
Partially Detected
· behavior is observable but depends on enrichment, baseline data, or multi-source correlation
Hunt Only
· activity is visible but requires analyst-driven hunting rather than automated alerting
Not Covered
· no current telemetry or detection logic provides reliable coverage
S27. Defensive Control and Hardening Architecture
Effective defense against destructive cyber campaigns requires layered controls aligned to the intrusion lifecycle.
Identity Security Layer
· enforce phishing-resistant multi-factor authentication for privileged users
· eliminate standing administrative privilege where operationally feasible
· separate administrative identities from user productivity identities
· monitor impossible travel, new IP use, MFA bypass, and MFA fatigue acceptance
Endpoint Security Layer
· deploy EDR with process, memory, and file telemetry enabled on all workstations and servers
· enable command-line, script-block, and process lineage auditing
· block unsigned or unapproved administrative tooling where feasible
· pre-authorize automatic host isolation for high-confidence destructive activity
Network Security Layer
· inspect DNS and east-west administrative traffic
· restrict workstation-to-workstation administrative protocols by policy
· route privileged administration through approved jump hosts only
· baseline remote administration behavior and suppress approved management infrastructure
Email Security Layer
· sandbox attachments and links
· aggressively score credential harvesting lures
· suppress phishing simulation traffic from production detections
· correlate phish delivery with downstream identity activity
Cloud Security Layer
· monitor IAM, role, policy, key, and service principal changes across AWS, Azure, and GCP
· protect backups, snapshots, vaults, and storage deletion actions with approval controls
· suppress approved infrastructure-as-code and change-window activity
· alert on destructive cloud actions by human identities or new execution contexts
Security Operations Layer
· correlate email, identity, endpoint, network, and cloud telemetry
· maintain high-fidelity behavioral analytics for phishing, privilege abuse, reconnaissance, lateral movement, and destruction
· pre-stage containment playbooks for endpoint isolation, identity disablement, token revocation, and cloud principal suspension
· continuously validate that every ATT&CK-mapped behavior has at least one rule or an explicit documented gap
S28. Today’s Hunt Focus
Signal 1
· Privileged shell execution bursts on workstation systems
Telemetry
· SentinelOne Deep Visibility process telemetry
· Windows process creation logs
· Splunk endpoint telemetry
· Elastic Defend process events
Why It Matters
· The most reliable early behavioral signal in this incident model is abnormal shell execution activity on workstation systems shortly after user interaction with malicious content.
· This aligns with T1059 – Command and Scripting Interpreter and commonly precedes credential harvesting, lateral movement, or destructive payload staging.
Hunt Directive
· Identify workstation systems where privileged or administrator-associated users executed:
o powershell.exe
o pwsh.exe
o cmd.exe
o wscript.exe
o cscript.exe
· Prioritize events where the parent process lineage includes:
o winword.exe
o excel.exe
o outlook.exe
o acrord32.exe
o chrome.exe
o msedge.exe
· Escalate immediately when the same host also generates:
o LSASS access attempts
o workstation authentication fan-out
o rapid file deletion activity
Signal 2
· Workstation authentication fan-out to multiple internal systems
Telemetry
· Windows Security Event ID 4624
· Splunk authentication telemetry
· Elastic authentication logs
· QRadar authentication events
· Suricata east-west traffic telemetry
Why It Matters
· Lateral movement is required before destructive execution can impact large numbers of systems.
· Workstation-origin authentication across multiple internal hosts aligns with T1021 – Remote Services and strongly indicates credential misuse or privileged expansion.
Hunt Directive
· Identify workstation systems authenticating successfully to five or more distinct internal hosts within ten minutes.
· Exclude expected infrastructure systems:
o domain controllers
o jump hosts
o SCCM infrastructure
o patch management systems
o approved helpdesk assets
· Prioritize events where the same host previously triggered shell-execution alerts or phishing-linked authentication activity.
Signal 3
· High-volume deletion activity on workstation endpoints
Telemetry
· SentinelOne file telemetry
· Elastic endpoint file events
· Splunk EDR-ingested file activity
Why It Matters
· Rapid deletion behavior in user-facing directories is one of the strongest behavioral indicators of T1485 – Data Destruction.
· This signal frequently appears shortly before or during the final operational impact phase of destructive campaigns.
Hunt Directive
· Identify endpoints generating 500 or more file deletions within five minutes inside:
o Desktop
o Documents
o Downloads
o Pictures
· Exclude approved tooling:
o OneDrive
o backup agents
o migration utilities
o enterprise installers
· Escalate immediately when deletion spikes are associated with:
o shell processes
o script engines
o unsigned binaries
o recently escalated user accounts
S29. Detection Gaps and Residual Risk
Primary Detection Gaps
· limited public disclosure of malware artifacts reduces the availability of reliable IOC-based detection
· environments without workstation versus server asset-role classification experience reduced lateral movement detection accuracy
· DNS anomaly detection becomes less reliable where enterprise allowlists and baseline models are incomplete.
· cloud privilege-change detections depend heavily on identity baselines and maintenance-window governance
· environments lacking endpoint file telemetry retention may fail to detect deletion thresholds associated with destructive activity
Residual Risk Areas
· credential misuse performed during normal working hours may resemble legitimate administrative activity
· attackers using approved enterprise management tools may partially blend with routine operations
· destructive execution may occur rapidly after privilege escalation, reducing available response time
· identity misuse in cloud environments may resemble legitimate change activity where governance controls are immature
· limited malware disclosure means artifact detection remains weaker than behavioral detection
Coverage Disposition
Detected
· phishing-linked credential misuse
· privileged shell execution bursts
· workstation authentication fan-out
· high-volume destructive deletion activity
· cloud privilege escalation attempts
· cloud recovery-asset destruction attempts
Partially Detected
· DNS-based staging or web service coordination
· credential dumping behaviors where memory telemetry is limited
· discovery commands executed through legitimate administration tooling
Hunt Only
· early reconnaissance activity with low execution volume
· attacker testing activity before lateral movement begins
· low-volume command execution that falls below alert thresholds
Residual Risk Statement
· Behavioral detection across email telemetry, endpoint telemetry, and network telemetry remains the strongest defensive approach for this campaign due to the limited availability of reliable malware artifacts.
S30. Intelligence Maturity Assessment
CyberDax Intelligence Maturity Domains
· threat detection capability
· telemetry coverage
· detection engineering maturity
· response readiness
· defensive hardening maturity
Threat Detection Maturity
· Moderate
Assessment
· Behavioral detection coverage exists for the key phases of this campaign including phishing access, privileged shell execution, lateral movement, and destructive deletion activity.
· Maturity remains limited by the absence of detailed malware indicators from public sources.
Telemetry Coverage Maturity
· Moderate
Assessment
· Endpoint and authentication telemetry provide the strongest visibility into this threat model.
· Maturity improves significantly when organizations maintain:
o workstation versus server asset classification
o user-to-IP baseline models
o approved management infrastructure inventories
o cloud identity baseline telemetry
Detection Engineering Maturity
· Moderate to High
Assessment
· Detection rules developed in this report provide cross-platform behavioral coverage across endpoint, network, identity, and cloud environments.
· Maturity decreases when environments lack enrichment data required for rule suppression and context-aware filtering.
Response Readiness Maturity
· Moderate
Assessment
· Organizations with pre-approved host isolation capabilities and privileged identity containment procedures are better positioned to contain destructive campaigns quickly.
· Environments lacking destructive-incident playbooks face longer containment timelines.
Security Hardening Maturity
· Moderate
Assessment
· Organizations that enforce strict privileged identity segmentation and restrict east-west administrative access significantly reduce the potential spread of destructive attacks.
Overall Intelligence Maturity Rating
· Moderate
Key Maturity Improvement Priorities
· strengthen asset-role classification across endpoint populations
· improve privileged identity monitoring and baseline analytics
· expand DNS anomaly baselines and allowlist governance
· implement rapid containment workflows for destructive behaviors
· protect backup and recovery infrastructure from unauthorized deletion
S31. Organizational Security Posture Impact
Operational Security Impact
· The attack model demonstrated in this incident highlights that many organizations remain more prepared to detect ransomware extortion activity than fast-moving destructive operations.
· Destructive attacks require less infrastructure than extortion campaigns and may execute with minimal warning once access is established.
Key Posture Exposures
· privileged user activity occurring on workstation endpoints
· insufficient controls restricting workstation-origin administrative access
· limited monitoring of rapid file deletion behavior
· inadequate protection of recovery and backup infrastructure
· incomplete identity baselines for cloud environments
Operational Detection Weaknesses Observed Across Enterprises
· identity monitoring without endpoint behavioral analytics
· endpoint monitoring without east-west authentication visibility
· reliance on signature-based malware detection rather than behavior detection
· lack of correlation across email, endpoint, and network telemetry domains
Posture Improvement Outcomes if Controls Are Implemented
· earlier detection of phishing-driven credential misuse
· faster identification of abnormal privileged shell activity
· improved visibility into lateral movement across workstation systems
· earlier detection of destructive execution before enterprise-wide impact
· stronger protection of recovery infrastructure and backup systems
CyberDax Posture Assessment Conclusion
· Organizations combining phishing-resistant identity protection, workstation behavioral detection, east-west authentication monitoring, and protected recovery infrastructure are substantially more resilient against destructive campaigns similar to the Handala intrusion model.
S32. Defensive Architecture Implementation
This section defines the defensive architecture required to reduce both the probability of compromise and the operational impact of destructive cyber campaigns similar to the Handala intrusion affecting Stryker.
The architecture emphasizes layered detection and containment across the three primary CyberDax telemetry pillars:
· email security gateway telemetry
· endpoint process and file telemetry
· DNS and internal network telemetry
These controls directly address the behaviors observed in this campaign, including phishing access, privileged shell execution, lateral movement, and destructive deletion activity.
Defensive Layer 1
Email and Initial Access Protection
Primary Objective
· reduce the probability of phishing-driven credential compromise.
Core Controls
· phishing-resistant multi-factor authentication for privileged identities
· attachment detonation and sandboxing within the email security gateway
· URL rewriting and real-time link detonation
· detection of credential harvesting domains
· blocking of executable and macro-enabled attachments where operationally feasible
Operational Benefit
· reduces the likelihood that malicious documents or credential harvesting campaigns successfully establish initial footholds.
Defensive Layer 2
Endpoint Behavioral Detection
Primary Objective
· detect abnormal command execution and credential harvesting behavior on workstation systems.
Core Controls
· endpoint detection and response telemetry coverage across workstation populations
· monitoring for abnormal command execution bursts
· detection of LSASS memory access attempts
· monitoring of suspicious parent-child process relationships
· detection of unsigned or rare executable activity
Operational Benefit
· enables detection of attacker activity shortly after execution rather than relying on signature-based malware identification.
Defensive Layer 3
Lateral Movement Containment
Primary Objective
· limit attacker movement across internal systems following credential compromise.
Core Controls
· restriction of workstation-origin administrative access to servers
· segmentation of administrative management networks
· enforcement of administrative access through hardened jump hosts
· monitoring for workstation authentication fan-out activity
· alerting on abnormal remote service usage
Operational Benefit
· limits the scale of destructive impact by preventing attackers from spreading administrative access across large numbers of systems.
Defensive Layer 4
Destructive Behavior Detection
Primary Objective
· detect destructive activity before enterprise-wide disruption occurs.
Core Controls
· monitoring for high-volume deletion activity in user directories
· detection of shadow copy deletion commands
· monitoring for system recovery configuration modification
· detection of large file deletion spikes on workstation systems
Operational Benefit
· enables security teams to identify destructive execution activity early enough to isolate compromised hosts.
Defensive Layer 5
Recovery Infrastructure Protection
Primary Objective
· protect backup and recovery infrastructure from attacker manipulation.
Core Controls
· identity separation for backup administration
· immutable backup storage policies
· monitoring for snapshot deletion or recovery-point removal
· monitoring for unauthorized backup configuration changes
Operational Benefit
· ensures recovery capability remains available even if destructive activity affects production infrastructure.
Defensive Layer 6
Cloud Identity Governance
Primary Objective
· prevent attackers from escalating privileges or impairing recovery systems within cloud environments.
Core Controls
· monitoring for IAM privilege escalation events
· monitoring for service account key creation
· monitoring for role assignment changes
· enforcement of maintenance-window governance for privileged operations
Operational Benefit
· reduces the ability of attackers to establish persistent administrative access or disable cloud recovery infrastructure.
S33. Strategic Defensive Improvements
The following improvements represent the most impactful defensive investments for reducing exposure to destructive cyber campaigns similar to the Handala incident.
Identity Security Improvements
· enforce phishing-resistant multi-factor authentication for privileged identities
· separate administrative identities from user productivity identities
· establish baseline models for user login locations and devices
· monitor for authentication activity from previously unseen IP addresses
Endpoint Security Improvements
· ensure full endpoint telemetry coverage across workstation systems
· monitor for abnormal command execution patterns
· restrict execution of unsigned binaries where operationally feasible
· maintain rapid host isolation capability for compromised systems
Network Security Improvements
· restrict workstation-origin administrative access to servers
· enforce administrative access through hardened jump hosts
· monitor east-west authentication activity across internal systems
· deploy internal network telemetry where feasible
Cloud Security Improvements
· monitor for IAM role assignment changes
· detect privilege escalation activity
· alert on backup or storage deletion events
· enforce identity separation for infrastructure automation roles
Recovery Security Improvements
· enforce immutable backup storage policies
· monitor backup infrastructure access logs
· restrict identity access to recovery systems
· regularly test recovery procedures for destructive attack scenarios
Operational Security Improvements
· develop containment playbooks for destructive malware incidents
· establish rapid endpoint isolation procedures
· implement escalation workflows for deletion-spike alerts
· train SOC analysts on destructive campaign indicators
S34. Estimated Probability of Recurrence
Assessment Horizon
· twelve months
Recurrence Probability
· Moderate to High
Assessment Rationale
Destructive cyber campaigns have increased in frequency over the past several years and are often associated with geopolitical tensions or ideological motivations.
The operational intrusion pattern observed in this campaign relies primarily on widely available techniques rather than rare exploit chains.
Key behaviors supporting recurrence likelihood include:
· phishing-based credential compromise
· privileged shell execution on workstation systems
· lateral movement through remote services
· destructive deletion activity affecting enterprise systems
These techniques are widely used across destructive malware operations and do not require specialized infrastructure.
Risk-Increasing Factors
· continued geopolitical cyber activity
· large enterprise attack surfaces
· widespread use of workstation administrative privileges
· incomplete monitoring of internal authentication activity
Risk-Reducing Factors
· improved adoption of endpoint detection platforms
· increased use of phishing-resistant authentication methods
· stronger monitoring of privileged account activity
· growing awareness of destructive cyber campaigns
CyberDax Recurrence Assessment
· while the specific malware or attacker infrastructure may change, the operational intrusion model remains common and likely to appear again in future campaigns.
S35. Estimated Financial Risk Reduction from Defensive Controls
Financial Risk Model
· risk modeling evaluates operational disruption, recovery costs, and productivity loss associated with destructive cyber incidents.
Primary Cost Drivers
· operational downtime affecting enterprise systems
· incident response and forensic investigation costs
· system rebuild and infrastructure restoration costs
· productivity loss during recovery operations
Potential Operational Impact
· destructive campaigns can disrupt enterprise operations for multiple days depending on the scale of system compromise.
· recovery operations frequently require extensive rebuilding of workstation and server infrastructure.
Estimated Financial Impact Range
· moderate destructive incidents may generate recovery costs in the millions of dollars
· enterprise-wide disruption can produce substantially larger financial impact depending on operational dependencies
Estimated Risk Reduction From Defensive Controls
Organizations implementing the defensive architecture described in this report can reduce destructive campaign impact through:
· earlier detection of attacker activity before destructive execution
· reduced lateral movement across internal systems
· faster containment through endpoint isolation
· protection of backup and recovery infrastructure
Estimated Financial Risk Reduction
· organizations implementing these controls may reduce destructive incident impact by approximately 40 to 60 percent, depending on detection maturity and response readiness.
CyberDax Financial Risk Assessment
· the greatest financial benefit comes from earlier behavioral detection and rapid containment, which significantly reduces the number of systems affected by destructive execution.
S36. Strategic Implications
The Handala intrusion affecting Stryker illustrates the growing use of destructive cyber operations as instruments of geopolitical pressure rather than financially motivated cybercrime. Unlike ransomware campaigns that delay disruption to maximize payment leverage, destructive operations often prioritize immediate operational impact once privileged access has been achieved.
This operational model significantly compresses defender response timelines. Once adversaries obtain administrative credentials or privileged execution capability, destructive payload deployment can occur rapidly across enterprise endpoint populations, leaving limited opportunity for containment before operational disruption occurs.
The campaign also reinforces the strategic importance of identity security within modern enterprise environments. In this intrusion model, operational impact does not depend on exploitation of software vulnerabilities but instead relies on credential compromise, administrative access misuse, and rapid propagation through trusted management channels. Organizations maintaining weak identity monitoring or excessive standing administrative privilege face significantly elevated exposure to destructive campaigns.
Another implication is the increasing targeting of operational infrastructure supporting critical economic sectors. Healthcare manufacturing supply chains represent particularly attractive disruption targets because enterprise IT outages can cascade into device production delays, logistics failures, and service interruptions affecting healthcare delivery environments.
Finally, the campaign demonstrates the declining effectiveness of purely signature-based security models. Destructive operations frequently rely on custom malware, script-based payloads, or one-time builds that produce limited reusable indicators. Behavioral detection across email telemetry, endpoint process telemetry, and internal network telemetry therefore remains the most reliable method for identifying destructive campaigns before enterprise-wide impact occurs.
Organizations that integrate identity protection, behavioral detection, lateral movement monitoring, and protected recovery infrastructure significantly reduce the probability that destructive cyber operations result in large-scale operational disruption.
S37. Board-Level Takeaway
Destructive cyber campaigns present a fundamentally different risk profile than ransomware or financially motivated cybercrime.
In ransomware scenarios, attackers typically delay operational disruption in order to maximize financial leverage.
In destructive campaigns, system disruption may occur immediately once attackers achieve privileged access.
For organizations operating large enterprise environments similar to Stryker, this creates several board-level risk considerations:
· operational disruption may occur with minimal warning
· recovery infrastructure may be intentionally targeted
· enterprise systems may require extensive rebuilding following destructive execution
· incident recovery timelines may extend beyond traditional ransomware recovery expectations
Board-level oversight should prioritize investment in the following defensive capabilities:
· phishing-resistant identity protection
· behavioral detection across endpoint systems
· internal authentication monitoring
· protection of backup and recovery infrastructure
Organizations implementing these controls materially reduce the probability that destructive campaigns result in prolonged operational disruption.
S38. References
All references below are provided as deduplicated primary-source URLs in accordance with the CyberDax reporting standard. URLs are intentionally defanged.
Incident Reporting Sources
· hxxps://www[.]securityweek[.]com/medtech-giant-stryker-crippled-by-iran-linked-hacker-attack/
· hxxps://www[.]newsweek[.]com/stryker-cyber-attack-iran-handala-outage-11660284
These sources document the operational disruption affecting Stryker and attribution claims involving the Handala threat actor.
Threat Actor Intelligence
· hxxps://malpedia[.]caad[.]fkie[.]fraunhofer[.]de/actor/handala
· hxxps://falconfeeds[.]io/blogs/unmasking-handala-iran-cyber-threat-psyops
· hxxps://cyberint[.]com/blog/threat-intelligence/handala-hack-what-we-know-about-the-rising-threat-actor/
· hxxps://industrialcyber[.]co/ransomware/symantec-reports-iranian-seedworm-hackers-infiltrate-us-infrastructure-and-defense-supply-chain-networks/
These sources describe Handala threat actor operations, ideological motivations, and historical cyber activity.
Destructive Malware and Wiper Research
· hxxps://www[.]splunk[.]com/en_us/blog/security/handalas-wiper-threat-analysis-and-detections[.]html
This research analyzes destructive malware patterns associated with Handala activity.
Geopolitical Cyber Activity Context
· hxxps://unit42[.]paloaltonetworks[.]com/iranian-cyberattacks-2026/
· hxxps://www[.]sophos[.]com/en-us/blog/cyber-advisory-increased-cyber-risk-amid-u-s-israel-iran-escalation
These sources describe broader cyber operations conducted by Iran-aligned groups and proxy actors.
Government and Security Authority Sources
· hxxps://www[.]cisa[.]gov/known-exploited-vulnerabilities-catalog
· hxxps://www[.]cisa[.]gov/news-events/cybersecurity-advisories
These sources provide authoritative vulnerability and threat advisory information.
MITRE ATT&CK Technique References
· hxxps://attack[.]mitre[.]org/techniques/T1059
· hxxps://attack[.]mitre[.]org/techniques/T1021
· hxxps://attack[.]mitre[.]org/techniques/T1485
· hxxps://attack[.]mitre[.]org/techniques/T1003
· hxxps://attack[.]mitre[.]org/techniques/T1566
These technique pages support ATT&CK mapping used throughout the report.
Malware Intelligence Repositories
· hxxps://bazaar[.]abuse[.]ch
· hxxps://www[.]virustotal[.]com
These repositories are used for malware artifact verification and hash intelligence correlation when samples become publicly available.