CVE-2026-1603 Administrative Credential Exposure Risk in Enterprise Management Infrastructure
BLUF
CVE-2026-1603 introduces a significant enterprise security risk because the vulnerability allows unauthenticated attackers to bypass authentication protections protecting centralized management infrastructure that stores privileged administrative credentials.
The vulnerability results from flawed authentication logic that allows crafted network requests to reach credential management systems before authentication is completed.
Because the flaw is remotely exploitable without authentication and requires no user interaction, attackers could retrieve privileged administrative credentials or gain operational control over systems responsible for managing enterprise infrastructure.
Organizations should immediately deploy vendor security updates addressing CVE-2026-1603, restrict management interfaces to trusted internal networks, and review administrative access activity for abnormal credential access behavior.
S1A – Executive Risk Translation
For organizations operating centralized enterprise management platforms, exploitation of CVE-2026-1603 could expose privileged administrative credentials used to control enterprise systems.
Because these platforms govern configuration management, software deployment, and administrative control across large numbers of devices, compromise of the management service could allow attackers to expand access across enterprise infrastructure and maintain persistent administrative control.
S2 – Key Judgments
· CVE-2026-1603 allows attackers to bypass authentication protections protecting enterprise management services.
· The vulnerability allows unauthenticated network requests to reach credential management systems before identity validation occurs.
· Successful exploitation may expose privileged administrative credentials or allow attackers to perform administrative management actions.
· Enterprise management platforms commonly store credentials used for remote administration, infrastructure configuration, and automated software deployment.
· Exposure of privileged administrative credentials could allow attackers to pivot across enterprise infrastructure.
· Management platforms accessible from external networks or poorly segmented internal environments face the highest operational risk.
· Public disclosure of authentication bypass vulnerabilities affecting enterprise management infrastructure frequently leads to rapid proof-of-concept exploit development.
S3 – Risk Drivers
The operational risk associated with CVE-2026-1603 is driven primarily by the architectural role of centralized management platforms within enterprise environments.
Key risk drivers include:
· Exposure of enterprise management interfaces to external or untrusted networks
· Storage of privileged administrative credentials within centralized management infrastructure
· Centralized administrative control across large enterprise system fleets
· Delayed patch deployment affecting critical infrastructure services
· Broad network accessibility to administrative management interfaces
· Trust relationships between management platforms and managed enterprise systems
· Organizational dependence on centralized management services for operational control
S4 – Executive Risk Summary
The vulnerability introduces a management-plane compromise risk affecting enterprise administrative infrastructure.
Threat Classification
· Authentication bypass affecting enterprise management services
Primary Risk
· Unauthorized access to credential management systems and privileged administrative functionality
Exploit Vector
· Crafted network requests delivered to vulnerable administrative service endpoints
Operational Impact
· Exposure of privileged administrative credentials
· Unauthorized administrative system access
· Lateral movement across enterprise infrastructure
· Persistence within enterprise management platforms
Attack Surface
• Network-accessible administrative management interfaces
S5 – Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
For organizations affected by CVE-2026-1603, the primary financial exposure arises from investigation of potential privileged administrative credential exposure and validation of enterprise management infrastructure integrity.
· Low-end total cost: $150,000 – $450,000
(limited credential exposure investigation and validation of administrative infrastructure)
· Typical expected range: $450,000 – $1.6M
(enterprise credential rotation, infrastructure validation, and extended monitoring)
· Upper-bound realistic scenarios: $1.6M – $3.9M
(confirmed credential compromise requiring administrative infrastructure rebuild)
Key Cost Drivers
· Enterprise-wide rotation of privileged administrative credentials
· Scope of infrastructure validation following potential credential exposure
· Duration of incident response and forensic investigation
· Regulatory reporting and compliance review requirements
· Expansion of security monitoring following suspected credential compromise
S5A – Key Cost Drivers
· Enterprise-wide reset of privileged administrative accounts
· Validation of configuration integrity across managed enterprise systems
· Duration and scope of incident response investigation
· Regulatory review and compliance reporting requirements
· Expansion of monitoring and logging coverage following remediation
S6 – Bottom Line for Executives
For most organizations, CVE-2026-1603 becomes operationally significant when enterprise management platforms storing privileged administrative credentials are reachable from untrusted networks.
Financial and operational exposure typically arises from incident investigation, credential rotation, infrastructure remediation, and validation that attackers did not obtain privileged administrative access.
Management priorities should focus on:
· Applying vendor security updates addressing CVE-2026-1603
· Restricting management interface exposure to trusted internal networks
· Rotating privileged administrative credentials stored within management infrastructure
· Monitoring administrative service activity for anomalous access patterns
S7 – Board-Level Takeaway
CVE-2026-1603 represents a governance risk affecting enterprise management infrastructure responsible for storing privileged administrative credentials and coordinating system administration across enterprise environments.
Compromise of centralized management services could allow attackers to obtain privileged administrative credentials and expand access across enterprise systems.
Board oversight should ensure that organizations maintain:
· Accelerated patch management for critical infrastructure
· Strict segmentation protecting enterprise management services
· Continuous monitoring of administrative infrastructure
· Governance controls protecting privileged credential storage
S7A – Executive Decision Trigger
Executive escalation should occur if investigation confirms:
· Unauthorized access to enterprise management infrastructure
· Evidence that privileged administrative credentials were accessed or exfiltrated
· Administrative access originating from unfamiliar network locations
· Discovery that enterprise management interfaces are accessible from public or untrusted networks
S8 – Priority Level and Response Window
Priority Level
· High – Authentication bypass exposing enterprise administrative control infrastructure
Response Window
· Immediate remediation recommended
Operational Context
· CVE-2026-1603 affects enterprise management infrastructure responsible for storing privileged administrative credentials used to control enterprise systems.
· Centralized management platforms represent high-value targets because compromise may allow attackers to obtain credentials capable of administering large portions of enterprise infrastructure.
· Authentication bypass vulnerabilities affecting administrative control systems significantly increase enterprise risk because attackers may access credential management systems without prior authentication.
Exposure-Based Response Window
· Internet-accessible management infrastructure: remediate immediately within 24 hours
· Internally accessible enterprise management platforms: remediate within 48 hours
· Restricted administrative network deployments: remediate within 72 hours
Immediate Defensive Priorities
· Apply vendor security updates addressing CVE-2026-1603
· Restrict enterprise management interfaces to dedicated administrative network segments
· Validate integrity of privileged administrative credentials stored by management systems
· Review authentication and credential access activity for anomalous behavior
S9 – Why This Matters Now
Enterprise management infrastructure represents a high-value target because it stores privileged administrative credentials used to control large numbers of enterprise systems.
Authentication bypass vulnerabilities affecting these platforms introduce disproportionate operational risk because attackers may access credential management systems without prior authentication.
If attackers obtain privileged administrative credentials from centralized management infrastructure, they may perform administrative actions across enterprise environments and expand access rapidly.
Because management platforms maintain trusted relationships with many enterprise systems, compromise of these services can enable rapid privilege escalation and infrastructure-wide administrative control.
S10 – What We Don’t Yet Know
Several operational aspects of CVE-2026-1603 remain unclear at this time.
Key intelligence gaps include:
· Whether proof-of-concept exploit code has been publicly released
· Whether threat actors are actively scanning for exposed enterprise management interfaces
· Whether exploitation attempts have been observed targeting enterprise environments
· The full range of enterprise management deployments potentially affected by the vulnerability
· Whether attackers could combine this vulnerability with additional privilege escalation techniques
· These uncertainties reinforce the importance of rapid remediation and defensive monitoring.
S11 – Exploit Conditions Snapshot
Successful exploitation of CVE-2026-1603 requires several environmental conditions.
Required Conditions
· Vulnerable enterprise management platform deployed within the environment
· Administrative interface reachable from attacker-controlled network locations
· Vulnerable authentication logic present within the management service
Attack Vector
· Network
Exploit Complexity
· Low
Privileges Required
· None
User Interaction
· None
Authentication Requirement
· None
Exploit Maturity
· Public exploitation not confirmed at this time
Potential Outcomes
· Exposure of privileged administrative credentials
· Unauthorized administrative system access
· Lateral movement across enterprise infrastructure
· Persistent administrative access through centralized management platforms
S12 – Realistic Exploit Scenario
A realistic exploitation path may occur through the following sequence.
1. Discovery
An attacker identifies an enterprise management interface reachable from an external network or poorly segmented internal environment.
2. Exploit Attempt
The attacker sends crafted network requests targeting the authentication bypass vulnerability in the management service.
3. Authentication Bypass
The vulnerable authentication logic processes the request before authentication validation completes, allowing unauthorized access to credential management systems.
4. Credential Retrieval
The attacker retrieves privileged administrative credentials stored within the enterprise management platform.
5. Enterprise Access Expansion
Using these credentials, the attacker accesses managed enterprise systems and begins lateral movement across enterprise infrastructure.
S13 – Today’s Hunt Focus
Security teams should prioritize monitoring for reconnaissance or exploitation activity targeting enterprise management infrastructure.
Signal 1 – Authentication Bypass Probing
Signal
· Repeated malformed or anomalous authentication requests targeting enterprise management services
Telemetry
· Enterprise management platform authentication logs
· Management service API request logs
· Web application firewall telemetry associated with management portals
Why It Matters
· Attackers probing authentication mechanisms often generate repeated malformed or abnormal requests against administrative service endpoints.
Signal 2 – Privileged Credential Access Anomalies
Signal
· Unexpected retrieval or access of privileged administrative credentials
Telemetry
· Credential management system audit logs
· Identity provider authentication telemetry
· Privileged account monitoring systems
Why It Matters
· Abnormal credential access activity may indicate attempts to obtain privileged administrative credentials.
Signal 3 – Unauthorized Administrative Activity
Signal
· Administrative configuration changes outside approved operational workflows
Telemetry
· Enterprise management platform audit logs
· Configuration management change records
· Administrative command execution telemetry
Why It Matters
· Unexpected administrative activity may indicate attackers successfully obtained privileged administrative credentials.
S14 – Sectors / Countries Affected
Affected Environments
· Organizations operating Ivanti Endpoint Manager deployments
· Enterprise environments using centralized endpoint management infrastructure
Operational Exposure Factors
· Ivanti Endpoint Manager deployments prior to version 2024 SU5
· Network-accessible administrative management interfaces
· Credential storage within endpoint management infrastructure
Countries Affected
· Global exposure
Deployment Concentration
Enterprise adoption of Ivanti Endpoint Manager is most commonly observed in the following regions:
· North America
· Western Europe
· Asia-Pacific enterprise markets
Exposure risk is determined primarily by technology deployment rather than geographic location.
S15 – First Activity
First Public Activity
· 02/10/2026 – CVE-2026-1603 published in the National Vulnerability Database.
Disclosure Context
· The vulnerability was disclosed through Ivanti security advisory processes and incorporated into the CVE program and the National Vulnerability Database.
Operational Significance
· Vulnerabilities affecting enterprise endpoint management infrastructure receive elevated operational priority due to the administrative privileges associated with these systems.
S16 – Last Activity
Last Recorded Activity
· 03/09/2026 – NVD record metadata updated.
Current Status
· Vendor remediation guidance has been released.
Patch Status
· Ivanti Endpoint Manager version 2024 SU5 resolves the vulnerability.
Operational Monitoring
· Vulnerability intelligence platforms and security vendors continue monitoring exploit development and scanning activity targeting exposed endpoint management interfaces.
S17 – CVE Details
CVE-2026-1603
Vendor
· Ivanti
Affected Product
· Ivanti Endpoint Manager
Affected Versions
· Endpoint Manager versions prior to 2024 SU5
Vulnerability Type
· Authentication bypass allowing a remote unauthenticated attacker to leak specific stored credential data.
Root Cause
· Improper authentication validation allowing alternate access paths to bypass authentication checks.
Attack Characteristics
· Remote exploitation possible
· No authentication required
· No user interaction required
Primary Impact
· Leakage of specific stored credential data maintained by the endpoint management platform.
S18 – CVSS / CWE / KEV / Nessus / EPSS
Executive Risk Translation
· Confirmed exploitation combined with unauthenticated remote access places enterprise endpoint management infrastructure at elevated compromise risk until remediation is applied
CVSS 3.1 Score (NVD)
· 7.5 – High severity
CVSS Vector (NVD)
· AV:N / AC:L / PR:N / UI:N / S:U / C:H / I:N / A:N
CVSS 3.1 Score (CNA – Ivanti)
· 8.6 – High severity
CVSS Vector (CNA – Ivanti)
· AV:N / AC:L / PR:N / UI:N / S:C / C:H / I:N / A:N
CWE Classification
· CWE-288 – Authentication Bypass Using an Alternate Path or Channel
KEV Catalog Status
· Listed in the CISA Known Exploited Vulnerabilities catalog indicating confirmed exploitation in the wild
CISA Patch by date
· March 23, 2026
Tenable Nessus Plugin ID
· 298947
Plugin identifies vulnerable Ivanti Endpoint Manager deployments prior to version 2024 SU5
EPSS Probability
· 11.74% probability of exploitation within 30 days
EPSS Percentile
· 94th percentile relative exploitation likelihood
S19 – Exploit Status
Observed Exploitation
· Confirmed active exploitation
Evidence
· CVE-2026-1603 has been added to the CISA Known Exploited Vulnerabilities catalog indicating real-world exploitation activity
Exploit Availability
· Public exploit tooling has not been formally documented in open sources at this time
Exploit Feasibility
· The vulnerability is remotely exploitable without authentication and requires no user interaction
Threat Actor Interest
· Authentication bypass vulnerabilities affecting enterprise management infrastructure are high-value targets due to the potential exposure of administrative credentials
Operational Risk Assessment
· Organizations operating exposed or unpatched Ivanti Endpoint Manager deployments face elevated compromise risk until remediation is applied
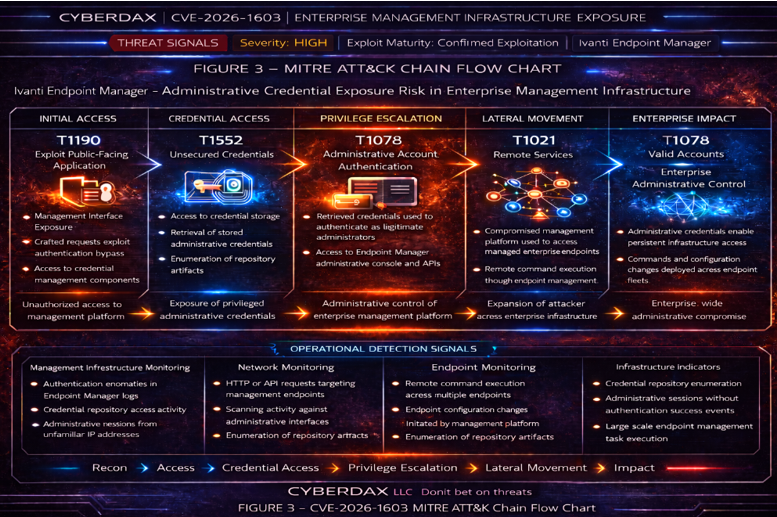
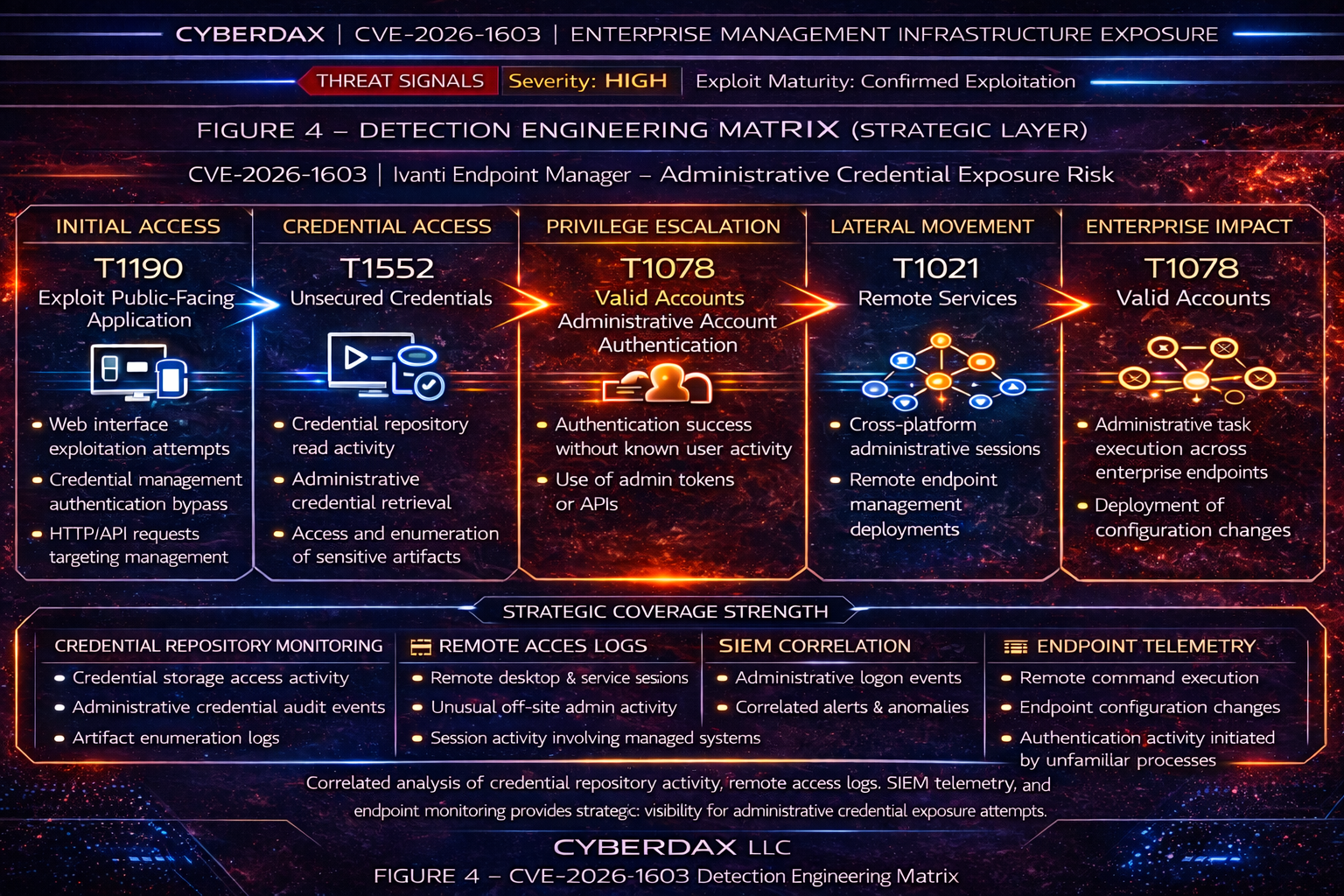
S20 – MITRE ATT&CK Chain Flow Mapping
Strategic Attack Chain
Initial Access
· T1190 – Exploit Public-Facing Application
Credential Access
· T1552 – Unsecured Credentials
Privilege Escalation
· T1078 – Valid Accounts
Lateral Movement
· T1021 – Remote Services
Persistence
· T1078 – Valid Accounts
S21 – Stage-Based TTPs
Reconnaissance
MITRE Technique
· T1595 – Active Scanning
How CVE Is Used
· Attackers identify internet-exposed Ivanti Endpoint Manager interfaces that may contain the authentication bypass vulnerability described in CVE-2026-1603.
Initial Access
MITRE Technique
· T1190 – Exploit Public-Facing Application
How CVE Is Used
· CVE-2026-1603 allows attackers to bypass authentication controls and access the endpoint management service without valid credentials.
Credential Access
MITRE Technique
· T1552 – Unsecured Credentials
How CVE Is Used
· Successful exploitation allows attackers to retrieve specific stored credential data maintained within the endpoint management platform.
Privilege Escalation
MITRE Technique
· T1078 – Valid Accounts
How CVE Is Used
· Retrieved administrative credentials may be used to authenticate as legitimate administrators within the endpoint management infrastructure.
Lateral Movement
MITRE Technique
· T1021 – Remote Services
How CVE Is Used
· Compromised administrative credentials may enable attackers to access managed enterprise endpoints through remote management services.
S22 – Malware and SHA256
Associated Malware
· Not known at this time.
Observed Payloads
· No malware payloads have been publicly associated with exploitation of CVE-2026-1603.
Potential Post-Exploitation Activity
· If attackers obtain administrative credentials through exploitation of this vulnerability, they may use those credentials to access the endpoint management infrastructure and control managed enterprise endpoints.
· Post-exploitation activity may include unauthorized administrative actions, endpoint configuration changes, and execution of commands through the management platform.
Hash Indicators
· Not known at this time.
S23 – Behavior and Log Artifacts
Authentication Bypass Indicators
· HTTP requests to Endpoint Manager administrative API paths such as /api/, /admin/, or /core/ returning successful responses without corresponding authentication success events.
· HTTP response anomalies where requests to authenticated endpoints return 200 success responses instead of expected 401 or 403 authentication failures.
Management API Access Indicators
· Direct interaction with Endpoint Manager REST or management API endpoints from previously unseen external IP addresses.
· API requests interacting with administrative endpoints without valid session tokens or authentication artifacts.
Credential Exposure Indicators
· Access attempts against credential storage components or configuration repositories within the Endpoint Manager platform.
· Log entries indicating retrieval or enumeration of stored credential data associated with administrative accounts.
Administrative Session Indicators
· Creation of administrative sessions originating from source systems not previously associated with administrative activity.
· Administrative console actions executed without corresponding authentication success events in identity logs.
Endpoint Control Indicators
· Remote management commands executed across multiple managed endpoints from a single administrative session.
· Endpoint configuration changes initiated through the management server outside normal administrative maintenance windows.
Management Job Scheduling Indicators
· Creation of endpoint management deployment jobs or scheduled tasks originating from newly established administrative sessions.
· Rapid execution of endpoint management tasks across large numbers of endpoints shortly after administrative session creation.
Relevant Log Sources
· Endpoint Manager server application logs
· Management server host telemetry including Windows Event Logs, service logs, and scheduled task logs
· Web server and API access logs
· Identity and authentication logs
· Endpoint management command execution logs
· Endpoint telemetry from managed systems
S24 – IOC Confidence and Hunt Prioritization
High Confidence Indicators (85–95 confidence)
· Successful interaction with authenticated Endpoint Manager API endpoints without corresponding authentication events.
· Credential repository access activity within the Endpoint Manager server.
· Administrative sessions created from previously unseen external IP addresses interacting with the management interface.
Confidence Rationale
· These behaviors directly indicate authentication bypass exploitation or credential retrieval activity consistent with CVE-2026-1603.
Medium Confidence Indicators (65–80 confidence)
· Administrative command execution across multiple endpoints from newly established administrative sessions.
· Management API activity originating from systems not previously associated with administrative access.
Low Confidence Indicators (40–60 confidence)
· External scanning activity targeting Endpoint Manager web services or management API endpoints.
· Repeated connection attempts interacting with management interface resources.
Hunt Prioritization Guidance
· Prioritize investigation of credential repository access and unauthorized administrative session creation.
· Investigate endpoint management job scheduling activity initiated by new administrative sessions.
S25 – Detection Signals Layer
Signal 1
Signal
· Unauthenticated interaction with Endpoint Manager administrative web or API endpoints.
Telemetry
· Web server access logs
· Application authentication logs
Why It Matters
· CVE-2026-1603 enables attackers to bypass authentication controls and access management infrastructure services.
Signal 2
Signal
· Credential repository access within the Endpoint Manager server.
Telemetry
· Application audit logs
· Credential storage access logs
Why It Matters
· Successful exploitation may expose administrative credentials used to control enterprise endpoints.
Signal 3
Signal
· Administrative command execution across multiple managed endpoints from a newly created administrative session.
Telemetry
· Endpoint management command execution logs
· Endpoint telemetry from managed systems
Why It Matters
· Compromised administrative credentials may enable attackers to execute commands across enterprise endpoints.
Signal 4
Signal
· Creation or execution of endpoint management deployment jobs from newly established administrative sessions.
Telemetry
· Endpoint management task scheduling logs
· Management server job execution logs
Why It Matters
· Attackers frequently leverage the management platform itself to deploy commands or payloads across large numbers of endpoints.
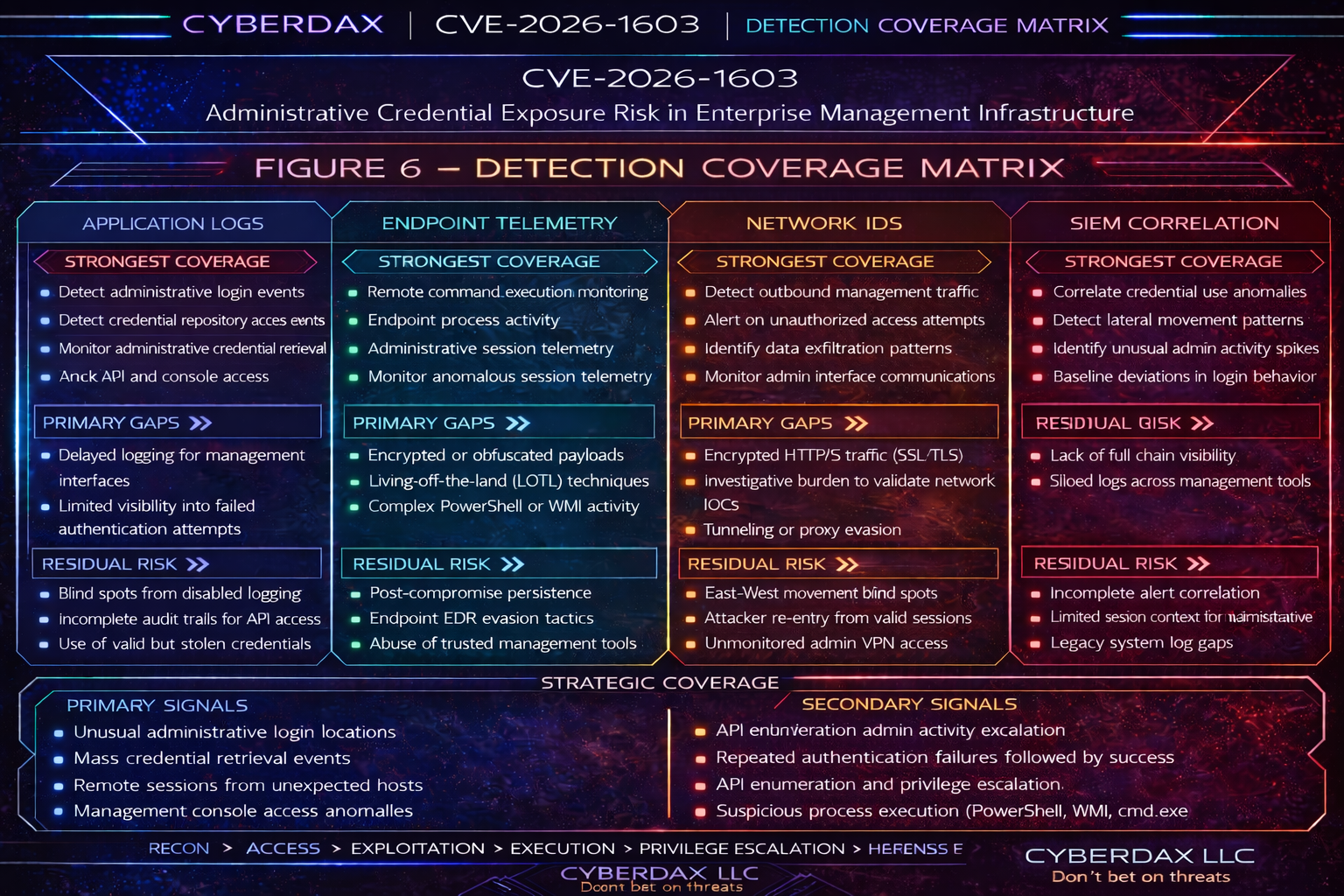
S26 – Detection Coverage Matrix
Network Monitoring Layer
· Detect inbound HTTP or API traffic interacting with Endpoint Manager administrative interfaces.
· Identify scanning activity targeting management server web services or API endpoints.
Identity Monitoring Layer
· Detect administrative sessions created without corresponding authentication success events.
· Identify administrative access originating from previously unseen IP addresses interacting with the management server.
Application Monitoring Layer
· Monitor credential repository access activity within Endpoint Manager server application logs.
· Detect management API access executed immediately after credential repository access events.
Management Server Monitoring Layer
· Monitor Endpoint Manager server host telemetry for administrative session creation and management job scheduling activity.
· Detect abnormal job deployment or endpoint management task creation outside approved maintenance windows.
Endpoint Monitoring Layer
· Identify remote command execution across multiple managed endpoints initiated by the management server.
· Detect endpoint configuration changes executed through the management platform outside normal administrative workflows.
S27 – Detection Engineering Matrix (Operational Rule Layer)
Network Detection Opportunities
· Generate alerts for repeated HTTP or API requests interacting with Endpoint Manager administrative endpoints from external sources.
· Detect scanning activity targeting management service ports associated with the Endpoint Manager server.
Identity Detection Opportunities
· Alert when administrative sessions appear without corresponding authentication success events.
· Detect administrative logins from previously unseen IP addresses interacting with the management infrastructure.
Application Detection Opportunities
· Alert on credential repository access events within Endpoint Manager server application logs.
· Correlate credential repository access followed by administrative session creation within a short time interval.
Management Server Detection Opportunities
· Alert when new endpoint management deployment jobs are created from newly established administrative sessions.
· Detect abnormal job scheduling or endpoint management tasks executed across large numbers of endpoints.
Endpoint Detection Opportunities
· Detect large-scale remote command execution across multiple managed endpoints originating from a single management server session.
· Correlate administrative session creation followed by endpoint command execution across the enterprise environment.
S28 – SOC Investigation Pivot Fields
Primary Pivot Fields
· Source IP address interacting with Endpoint Manager administrative interface
· Destination management server hostname or IP address
· Endpoint Manager API request paths (/api/, /admin/, /core/)
· Administrative account identifiers associated with management server sessions
Authentication Pivot Fields
· Administrative session creation timestamps
· Failed or missing authentication events associated with API requests
· Identity provider authentication logs associated with management server access
Credential Access Pivot Fields
· Credential repository file paths
· Credential access events within Endpoint Manager application logs
· Privileged account usage associated with management server activity
Endpoint Activity Pivot Fields
· Managed endpoint hostname receiving commands from management server
· Endpoint command execution process names
· Endpoint configuration changes initiated through management platform
Operational Pivot Strategy
· Begin investigation from management server logs
· Pivot into identity logs for administrative session creation
· Pivot into endpoint telemetry for command execution activity
S29 – Ultra-Tuned Detection Engineering Rules
Suricata
Rule Title
· Endpoint Manager Administrative API Path Access From External Network
Detection Intent
· Detect suspicious external access to sensitive Endpoint Manager administrative interface paths associated with authentication bypass activity.
Purpose
· Identify inbound requests from untrusted networks targeting management interface paths that should not be directly reachable from the internet or non-administrative segments.
Tuning Explanation
· This rule uses URI path matching with OR logic across known administrative paths and does not restrict to a single HTTP method. This improves coverage for exploitation and follow-on probing while keeping focus on sensitive management routes. Tune by limiting destination hosts to known Endpoint Manager servers where possible.
System Ready Code
alert http $EXTERNAL_NET any -> $HOME_NET any (
msg:"CyberDax Endpoint Manager suspicious administrative API path access";
flow:to_server,established;
http.uri; pcre:"/\/(api|admin|core)(\/|$)/Ui";
classtype:web-application-attack;
sid:20601603;
rev:6;
)
SentinelOne
Rule Title
· Endpoint Manager Administrative Access And Follow-On Execution From Untrusted Source
Detection Intent
· Detect suspicious management-driven execution or task creation on the Endpoint Manager server after access from an untrusted source.
Purpose
· Identify likely post-exploitation use of administrative access to create jobs, tasks, or deployment activity through the management platform.
Tuning Explanation
· This logic focuses on successful administrator logon or session creation on management infrastructure and correlates it with process execution or tasking artifacts shortly afterward. Tune by maintaining an allowlist of approved management jump hosts and administrative subnets. Final field normalization should be validated against tenant-specific Deep Visibility schema.
System Ready Code
(
ProcessName ContainsCIS "EndpointManager"
OR ProcessCmd ContainsCIS "EndpointManager"
OR ProcessCmd ContainsCIS "deploy"
OR ProcessCmd ContainsCIS "job"
OR ProcessCmd ContainsCIS "task"
OR TaskName ContainsCIS "EndpointManager"
OR TaskPath ContainsCIS "EndpointManager"
)
AND AgentName ContainsCIS "EndpointManager"
AND SrcIP Is Not Empty
AND SrcIP Not In "Trusted_Admin_Networks"
Splunk
Rule Title
· Endpoint Manager Credential Repository Access On Management Server
Detection Intent
· Detect repeated access to Endpoint Manager credential storage or configuration artifacts on designated management servers.
Purpose
· Identify likely credential retrieval or enumeration activity consistent with successful authentication bypass exploitation.
Tuning Explanation
· This search is tightly scoped to management server hosts and Endpoint Manager-specific credential or configuration paths. Thresholding reduces noise from legitimate single-touch access during routine operations. Tune host and sourcetype constraints to your environment.
SIEM / System Ready Code
index=endpoint_manager_logs host_role="endpoint_manager_server"
(
file_path="*\\EndpointManager\\credentials\\*" OR
file_path="*\\EndpointManager\\config\\*" OR
file_path="*/EndpointManager/credentials/*" OR
file_path="*/EndpointManager/config/*" OR
file_path="*authstore*" OR
file_path="*credential*repository*"
)
| stats count earliest(_time) as firstSeen latest(_time) as lastSeen by user host file_path process_name
| where count >= 3
Elastic
Rule Title
· Endpoint Manager Administrative Access Followed By Deployment Activity
Detection Intent
· Detect suspicious deployment or command activity on the Endpoint Manager server shortly after administrative access.
Purpose
· Identify likely exploitation chains where exposed credentials or bypassed access are immediately used to push jobs, tasks, or commands through the management server.
Tuning Explanation
· This rule uses an EQL sequence with a bounded time window and a shared host key. It requires a suspicious access event and a follow-on deployment or execution event on the same management host. Tune the login event source and process names to your local logging schema.
System Ready Code
sequence by host.name with maxspan=5m
[ authentication where
host.role == "endpoint_manager_server" and
event.outcome == "success" and
source.ip != null and
cidrMatch(source.ip, "10.0.0.0/8", "172.16.0.0/12", "192.168.0.0/16") == false
]
[ process where
host.role == "endpoint_manager_server" and
process.parent.name like~ ("EndpointManager*", "Ivanti*", "LANDesk*") and
process.command_line like~ ("*deploy*", "*job*", "*task*")
]
Sigma
Rule Title
· Endpoint Manager Administrative Access And Deployment Correlation
Detection Intent
· Detect suspicious deployment activity shortly after administrative access to Endpoint Manager infrastructure.
Purpose
· Provide a backend-portable Sigma implementation that separates base detections from correlation, which is the recommended way to express this logic at production quality.
Tuning Explanation
· This implementation uses two base detections and one temporal correlation rule. Tune the administrative account patterns, service names, and management-server host selectors to your environment.
System Ready Code
title: Endpoint Manager Administrative Login
id: 7e4b8c51-1b4e-4d3d-a7f7-em-admin-login
status: experimental
logsource:
product: windows
service: security
detection:
selection:
EventID: 4624
admin_user:
TargetUserName|contains:
- admin
- administrator
mgmt_host:
ComputerName|contains:
- EndpointManager
- Ivanti
- LANDesk
condition: selection and admin_user and mgmt_host
level: medium
---
title: Endpoint Manager Deployment Activity
id: 0ce0b4f9-9a27-4f4d-a22d-em-deploy-activity
status: experimental
logsource:
product: windows
detection:
proc_create:
EventID: 4688
CommandLine|contains:
- endpointmanager
- deploy
- job
- task
mgmt_host:
ComputerName|contains:
- EndpointManager
- Ivanti
- LANDesk
condition: proc_create and mgmt_host
level: high
---
title: Endpoint Manager Administrative Access Followed By Deployment Activity
id: 2f8d76a0-2f17-4a8d-b0f5-em-correlation
status: experimental
correlation:
type: temporal
rules:
- 7e4b8c51-1b4e-4d3d-a7f7-em-admin-login
- 0ce0b4f9-9a27-4f4d-a22d-em-deploy-activity
group-by:
- ComputerName
- TargetUserName
timespan: 5m
level: high
YARA
Rule Title
Endpoint Manager Credential Repository Artifact Pattern Detection
Detection Intent
· Detect credential repository artifacts associated with Endpoint Manager installations on suspected compromised systems.
Purpose
· Identify local artifacts indicating exposed or harvested management credential storage.
Tuning Explanation
· This rule requires multiple credential-related indicators and at least one Endpoint Manager directory reference to reduce false positives. It is intended for triage and forensic scanning on suspected management servers.
SIEM / System Ready Code
rule EndpointManager_Credential_Artifacts
{
meta:
description = "Detect Endpoint Manager credential repository artifacts"
author = "CyberDax"
reference = "CVE-2026-1603"
strings:
$cred1 = "EndpointManagerCredentialStore" ascii wide
$cred2 = "AdminCredentialRepository" ascii wide
$cred3 = "EndpointManagerAuthToken" ascii wide
$path1 = "EndpointManager\\config" ascii wide
$path2 = "EndpointManager\\credentials" ascii wide
$path3 = "/EndpointManager/config" ascii wide
$path4 = "/EndpointManager/credentials" ascii wide
condition:
2 of ($cred*) and 1 of ($path*)
}
S29A – Confidence Tiers for Analysts
High Confidence Indicators
· Credential repository access followed by administrative authentication and management job deployment on the same management server
· Administrative session creation followed by command execution across multiple managed endpoints
Medium Confidence Indicators
· Administrative API access anomalies followed by successful administrative login activity
· Endpoint Manager command execution originating from newly created administrative sessions
Low Confidence Indicators
· External scanning activity targeting administrative API paths
· Repeated probing of management interface endpoints without authentication success
Analyst Guidance
· High confidence detections should trigger immediate containment and credential rotation procedures
· Medium confidence events should be correlated with endpoint management job activity and endpoint command execution
· Low confidence events should be monitored for escalation into higher-confidence activity chains
S29B – SOC Investigation Playbook
Step 1 – Identify Administrative API Interaction
· Review management server web and API logs for external access to administrative paths such as /api/, /admin/, or /core/.
Step 2 – Validate Authentication Activity
· Examine authentication logs for successful administrative logins associated with the same source IP address or session identifier.
Step 3 – Investigate Credential Repository Access
· Review management server file, application, and audit logs for access to credential storage artifacts or configuration repositories.
Step 4 – Review Management Job Deployment
· Identify management job creation, deployment task execution, or scheduled activity associated with the identified administrative account.
Step 5 – Inspect Managed Endpoint Activity
· Review endpoint telemetry for command execution, service creation, or configuration changes initiated by the management server.
Step 6 – Determine Scope Of Impact
· Identify additional endpoints, accounts, sessions, or job executions linked to the same activity chain and determine whether credential rotation and containment are required immediately.
S29C – SOC Hunt Pivot And Analyst Quick Reference
Network Pivot Fields
· Source IP interacting with management server
· Request URI targeting /api/, /admin/, or /core/ paths
· HTTP response status codes associated with administrative requests
Identity Pivot Fields
· Administrative account username
· Authentication timestamp
· Session identifiers linked to management access
Application Pivot Fields
· Credential repository file paths
· Management job identifiers
· Deployment task identifiers
· Endpoint Manager service log entries tied to the same account or session
Endpoint Pivot Fields
· Managed endpoint hostname
· Command execution process name
· Endpoint group or deployment target
Operational Hunt Strategy
· Begin with management server API logs
· Pivot to authentication logs
· Investigate credential repository access
· Review management job execution
· Validate endpoint command execution across managed systems
S30 – SIEM Correlation Logic
Correlation Pattern 1
· Administrative API access anomaly
· Followed by successful administrative authentication on the same management server within 5 minutes
· Followed by credential repository access or management job creation within 5 minutes
Correlation Pattern 2
· Credential repository access on an Endpoint Manager server
· Followed by administrative session creation for the same account within 5 minutes
· Followed by deployment or task execution activity within 10 minutes
Correlation Pattern 3
· New administrative session on management infrastructure
· Followed by fan-out command execution or configuration changes across multiple managed endpoints within 10 minutes
Correlation Outcome Guidance
· Any sequence containing credential repository access plus administrative authentication plus management job activity should be treated as high-confidence exploitation activity
· Any sequence containing new administrative access plus rapid endpoint fan-out should be escalated for immediate containment
S31 – Delivery Methods
Primary Exploitation Channel
· Direct interaction with the Endpoint Manager administrative interface through HTTP or API requests targeting management services.
Initial Access Techniques
· Network discovery activity identifying exposed administrative web consoles or management APIs.
· HTTP requests targeting administrative paths including /api/, /admin/, and /core.
· Retrieval or misuse of administrative credentials stored within the management platform.
Command Deployment Method
· Creation of administrative jobs or deployment tasks within the Endpoint Manager platform.
· Execution of commands across managed endpoints using legitimate management orchestration services.
Operational Characteristics
· Exploitation leverages native platform functionality rather than introducing external malware payloads.
· Activity may resemble legitimate administrative operations because commands originate from trusted management infrastructure.
Operational Impact
· The management server becomes an attacker-controlled orchestration platform capable of distributing commands across the enterprise endpoint environment.
S32 – Exposure Conditions
Network Exposure Factors
· Administrative management interfaces accessible from internal enterprise networks without segmentation controls.
· Administrative web consoles reachable from untrusted internal network segments.
Infrastructure Exposure Factors
· Management servers deployed within general enterprise network zones rather than isolated administrative segments.
Administrative access permitted from broad address ranges rather than dedicated management networks.
Credential Exposure Factors
· Administrative credentials stored within management platform configuration repositories.
· Lack of monitoring or auditing of credential retrieval activity.
Monitoring Gaps
· Limited telemetry collection from management infrastructure.
· Lack of correlation between authentication activity and management job execution events.
Enterprise Risk Amplifiers
· Large endpoint populations managed through centralized management platforms.
· Operational dependence on a single infrastructure component for endpoint orchestration.
S33 – Exploit Preconditions
System Preconditions
· Deployment of Endpoint Manager infrastructure with administrative services enabled.
Network Preconditions
· Network connectivity to the management server administrative interface.
Authentication Preconditions
· Access to valid administrative credentials or ability to retrieve stored credentials.
Operational Preconditions
· Management server configured to execute jobs or configuration changes across managed endpoints.
Security Preconditions
· Lack of segmentation protecting management infrastructure from enterprise network segments.
Monitoring Preconditions
· Limited monitoring of administrative authentication and management activity.
S34 – Defensive Controls and Hardening Recommendations
Network Security Controls
· Restrict management server administrative interfaces to dedicated management networks.
· Eliminate direct internet exposure of administrative management services.
Identity and Authentication Controls
· Enforce strong authentication for administrative management accounts.
· Implement role-based access controls limiting platform administrative privileges.
Credential Protection Controls
· Remove administrative credential storage from platform configuration files where possible.
· Implement credential vaulting and privileged access management solutions.
Monitoring Controls
· Monitor administrative API access anomalies.
· Correlate administrative authentication with job deployment telemetry.
Endpoint Monitoring Controls
· Alert on abnormal command execution originating from management infrastructure.
S35 – Strategic Defensive Improvements
Governance Strategy
· Classify enterprise management platforms as critical operational control systems within cybersecurity governance frameworks.
Control-Plane Security Strategy
· Treat centralized management infrastructure as enterprise control-plane assets requiring dedicated protection and monitoring.
Access Governance Strategy
· Require administrative access through controlled jump-host environments and dedicated management networks.
Credential Governance Strategy
· Implement enterprise privileged access management controlling all administrative authentication to management platforms.
Detection Strategy
· Develop detection engineering programs focused specifically on enterprise control-plane infrastructure.
Enterprise Risk Strategy
· Incorporate management infrastructure compromise scenarios into enterprise cyber risk modeling and board-level security discussions.
S36 – Defensive Control and Hardening Architecture
Management Infrastructure Network Architecture
· Deploy management servers within isolated administrative network zones separated from enterprise user networks.
Administrative Access Architecture
· Require administrative access through hardened jump hosts or dedicated management workstations.
Identity Security Architecture
· Separate infrastructure administration identities from standard enterprise user identities.
Credential Protection Architecture
· Implement centralized credential vaulting systems protecting management infrastructure authentication secrets.
Telemetry Architecture
· Aggregate management platform application logs, authentication logs, and API telemetry into centralized SIEM platforms.
Detection Architecture
· Correlate authentication events, API access activity, and management job deployment telemetry.
Endpoint Security Architecture
· Monitor endpoint command execution initiated through management infrastructure.
Operational Security Architecture
· Deploy layered monitoring across network telemetry, identity systems, management servers, and endpoint sensors.
S37 – Seven-Day Response Plan
Day 0 – Immediate Containment
· Restrict administrative interface access to management infrastructure.
· Rotate administrative credentials associated with the management platform.
Day 1 – Authentication Investigation
· Review administrative authentication events originating from unusual network locations.
Day 2 – Credential Repository Analysis
· Investigate access to credential storage artifacts within management infrastructure.
Day 3 – Management Job Investigation
· Identify job creation or deployment events associated with administrative sessions.
Day 4 – Endpoint Impact Assessment
· Investigate managed endpoints for command execution initiated by management infrastructure.
Day 5 – Infrastructure Hardening
· Implement segmentation protecting management infrastructure.
Day 6 – Detection Deployment
· Deploy detection rules defined in S29 across SIEM and endpoint monitoring platforms.
Day 7 – Monitoring Validation
· Confirm no additional unauthorized job deployment or endpoint command execution.
S38 – Post-Incident Insights and Recommendations
Operational Insight
· Enterprise management infrastructure functions as a centralized command platform capable of controlling large endpoint populations.
Detection Engineering Insight
· Management platform telemetry must be treated as high-risk operational activity rather than routine administrative traffic.
Architectural Insight
· Systems capable of orchestrating enterprise-wide configuration changes represent high-value targets for attackers.
Programmatic Recommendation
· Deploy dedicated monitoring for enterprise control-plane infrastructure including endpoint management platforms.
Executive Recommendation
· Incorporate management infrastructure compromise scenarios into executive cyber risk governance and security planning.
S39 – Attack Economics and Organizational Impact Model
Enterprise management platforms represent high-value control-plane infrastructure within modern enterprise environments. When vulnerabilities affect these systems, the economic balance between attacker effort and organizational defensive cost often becomes highly asymmetric.
Vulnerabilities affecting centralized enterprise management platforms create a favorable operational and economic model for attackers because successful exploitation of a single management system can provide privileged access to infrastructure responsible for administering large portions of enterprise environments.
In the case of CVE-2026-1603, the authentication bypass vulnerability affecting Ivanti Endpoint Manager may allow unauthenticated attackers to reach credential management components responsible for storing privileged administrative credentials used to control enterprise systems.
Because endpoint management platforms orchestrate software deployment, configuration management, and remote administrative operations across large endpoint populations, compromise of the management service can allow attackers to rapidly expand access across enterprise infrastructure.
From an attacker perspective, this architecture provides substantial operational leverage. Rather than compromising individual endpoints through multiple intrusion attempts, attackers may retrieve privileged administrative credentials from the management platform and use the trusted management infrastructure itself to execute commands across enterprise environments.
A single compromised management server may therefore provide operational access equivalent to compromising hundreds or thousands of endpoints individually.
Management platforms also provide legitimate administrative mechanisms for executing commands and deploying configuration changes. As a result, malicious activity originating from the management infrastructure may resemble routine administrative operations, potentially delaying detection and enabling attackers to maintain persistence within enterprise environments.
In contrast, organizations incur significantly higher operational costs when responding to even suspected compromise of centralized management infrastructure.
Defensive response typically requires forensic review of administrative activity, validation of management platform integrity, enterprise-wide rotation of privileged administrative credentials, and analysis of endpoint activity initiated through the management server.
Organizations must also confirm that attackers did not use the management platform to deploy unauthorized commands, configuration changes, or credential harvesting activity across managed endpoints. In large enterprise environments, this verification process may require extensive endpoint telemetry review and coordination between incident response, infrastructure operations, and security engineering teams.
This imbalance reflects a common pattern in cyber operations: relatively modest attacker effort can trigger substantial defensive expenditure when vulnerabilities affect enterprise control-plane systems responsible for coordinating administrative activity across large infrastructure environments.
Figure 10 illustrates the economic lifecycle of a centralized management infrastructure exploitation scenario, highlighting the relationship between attacker discovery and exploitation effort, the operational advantages gained through control of endpoint management infrastructure, and the investigative and remediation costs incurred by organizations responding to potential administrative credential exposure.
Organizations that minimize patch latency, restrict administrative access to management interfaces, and maintain continuous monitoring of enterprise management infrastructure significantly reduce the operational return on investment for attackers targeting centralized control-plane systems.
S40 – References
National Institute of Standards and Technology (NVD)
CVE Record – CVE-2026-1603
· hxxps://nvd[.]nist[.]gov/vuln/detail/CVE-2026-1603
Cybersecurity and Infrastructure Security Agency (CISA)
Known Exploited Vulnerabilities Catalog – CVE-2026-1603
· hxxps://www[.]cisa[.]gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-1603
Tenable Security Research
Vulnerability Intelligence – CVE-2026-1603
· hxxps://www[.]tenable[.]com/cve/CVE-2026-1603