CVE-2026-20079 and CVE-2026-20131 Cisco Secure Firewall Management Center Authentication Bypass and Remote Code Execution Vulnerabilities
BLUF
CVE-2026-20079 and CVE-2026-20131 introduce a critical enterprise infrastructure risk because an unauthenticated attacker can obtain root-level control of Cisco Secure Firewall Management Center, the centralized platform responsible for managing firewall policy across enterprise networks.
The vulnerabilities arise from an authentication bypass condition and an insecure deserialization flaw within the FMC web-based management interface that can be triggered through crafted HTTP requests or malicious serialized Java objects.
Both vulnerabilities are remotely exploitable without authentication and provide root-level control of firewall management infrastructure, creating a high-impact attack path capable of undermining enterprise network security controls and enabling manipulation of firewall policy across managed devices.
Organizations should immediately apply Cisco’s March 2026 security updates, restrict FMC management interface access to trusted internal networks, and review firewall configuration activity logs for anomalous administrative access or unauthorized policy changes.
S1A – Executive Risk Translation
For organizations operating Cisco firewall infrastructure, successful exploitation could allow attackers to gain control of centralized firewall management systems and manipulate network security policies governing enterprise traffic flows. Because FMC manages policy across multiple firewall appliances and network segments, compromise of the management platform could enable attackers to alter defensive controls affecting large portions of enterprise network infrastructure.
S2 – Key Judgments
· CVE-2026-20079 allows unauthenticated attackers to bypass authentication protections within the Cisco Secure Firewall Management Center web interface.
· CVE-2026-20131 allows unauthenticated remote code execution through insecure deserialization of a crafted Java object delivered to the FMC management interface.
· Successful exploitation provides root-level privileges on the underlying operating system of the FMC appliance.
· Cisco Secure Firewall Management Center functions as a centralized control plane responsible for firewall configuration, policy enforcement, monitoring, and analytics across enterprise environments.
· Compromise of the management platform could allow attackers to manipulate firewall rules, suppress monitoring visibility, or introduce unauthorized network access paths.
· Because FMC acts as a centralized security control platform, compromise could affect multiple managed firewall devices simultaneously.
· Restricting FMC management interface access to trusted internal networks significantly reduces the attack surface associated with these vulnerabilities.
· Immediate deployment of Cisco’s March 2026 security updates represents the most effective mitigation.
S3 – Risk Drivers
The operational risk associated with CVE-2026-20079 and CVE-2026-20131 is influenced primarily by the exposure and architectural role of Cisco Secure Firewall Management Center within enterprise network security infrastructure.
Key risk drivers include:
· Exposure of FMC web management interfaces to the public internet
· Centralized control of firewall policy across enterprise environments
· Delayed patch deployment across critical network security infrastructure
· Root-level privileges obtained through successful exploitation
· Large firewall fleets managed through a single FMC instance
· Trust relationships between FMC and managed firewall appliances
· Security monitoring and logging dependencies on FMC management systems
S4 – Executive Risk Summary
The vulnerabilities introduce a management-plane compromise risk affecting enterprise firewall infrastructure.
Threat Classification
· Internet-facing infrastructure management vulnerability
Primary Risk
· Unauthorized root-level control of firewall management infrastructure
Exploit Vector
· Crafted HTTP requests or malicious serialized Java objects delivered to the FMC web-based management interface
Operational Impact
· Unauthorized firewall rule modification
· Security monitoring evasion
· Network segmentation bypass
· Potential lateral movement across enterprise networks
Attack Surface
· Cisco Secure Firewall Management Center web-based management interface
S5 – Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
For organizations affected by CVE-2026-20079 and CVE-2026-20131, the primary financial exposure arises from investigation and remediation of compromised firewall management infrastructure and validation of enterprise network security policy integrity.
· Low-end total cost: $150,000 – $420,000
(limited exposure with management interface restricted and no confirmed attacker persistence)
· Typical expected range: $420,000 – $1.4M
(enterprise firewall fleet validation and extended incident investigation)
· Upper-bound realistic scenarios: $1.4M – $4.2M
(confirmed compromise requiring firewall infrastructure rebuild and enterprise policy validation)
S5A – Key Cost Drivers
· Number of firewall appliances managed by the affected FMC instance
· Scope of enterprise firewall policy validation required following potential compromise
· Incident response consulting and digital forensics engagement costs
· Operational disruption during firewall configuration validation
· Security monitoring expansion following suspected exploitation attempts
· Legal and compliance review if downstream network compromise is suspected
S6 – Bottom Line for Executives
For most organizations, CVE-2026-20079 and CVE-2026-20131 become operationally significant when firewall management systems are accessible from untrusted networks or when attackers obtain network access to the FMC management interface.
Financial and operational exposure typically arises from incident investigation, firewall policy validation, infrastructure patch deployment, and confirmation that attackers did not manipulate enterprise network security controls.
Management priorities should focus on:
· Applying Cisco’s March 2026 security updates across all FMC deployments
· Restricting management interface access to trusted internal networks
· Monitoring firewall configuration activity for unauthorized changes
· Reviewing administrative access logs associated with FMC management systems
S7 – Board-Level Takeaway
CVE-2026-20079 and CVE-2026-20131 represent governance risks affecting the centralized systems responsible for enforcing firewall policy across enterprise networks. Compromise of firewall management infrastructure could allow attackers to alter security controls that protect critical enterprise systems and network segmentation boundaries.
Board oversight should ensure that:
· Governance of patch management for critical security infrastructure
· Segmentation and protection of security management platforms
· Monitoring and auditing of firewall configuration activity
· Assurance that firewall management interfaces are not exposed to public networks
S7A – Executive Decision Trigger
Executive escalation should occur if investigation confirms:
· Unauthorized access to Cisco Secure Firewall Management Center
· Evidence of firewall policy manipulation or unauthorized configuration changes
· Active exploitation attempts targeting FMC management interfaces
· Exposure of the FMC management interface to the public internet
S8 – Priority Level and Response Window
CVE-2026-20079 and CVE-2026-20131 represent high-priority vulnerabilities affecting the centralized management platform used to control firewall policy across enterprise environments. Because successful exploitation provides root-level access to Cisco Secure Firewall Management Center, compromise could allow attackers to manipulate network security policy affecting multiple managed firewall devices.
The urgency of remediation depends primarily on whether the FMC management interface is accessible from untrusted networks and how many firewall appliances are managed by the platform. Organizations exposing management services to the internet or to poorly segmented internal networks face the highest operational risk.
Priority Level
· Critical security infrastructure vulnerability
Immediate Actions (0–24 hours)
· Determine whether FMC management interfaces are exposed to external or untrusted networks
· Review Cisco advisory guidance and confirm affected software versions
· Initiate emergency patch deployment planning
Short-Term Actions (24–72 hours)
· Deploy Cisco March 2026 security updates to affected systems
· Restrict FMC management interface access to trusted internal networks
· Review administrative access logs for anomalous activity
Follow-Up Actions (3–7 days)
· Validate firewall configuration integrity across managed devices
· Confirm that no unauthorized firewall policy modifications occurred
· Update monitoring rules for suspicious FMC management activity
S9 – Why This Matters Now
Cisco Secure Firewall Management Center serves as the centralized control plane for many enterprise firewall deployments. The platform distributes firewall policy, manages device configuration, and collects telemetry across multiple security zones.
Because FMC governs security policy across multiple firewall appliances, compromise of the management platform could allow attackers to alter defensive controls protecting enterprise networks. Unlike vulnerabilities affecting individual devices, compromise of a centralized management system may enable policy manipulation across multiple network segments simultaneously.
The vulnerabilities affect both Cisco Secure FMC software deployments and Cisco Security Cloud Control firewall management environments, increasing the potential exposure surface across hybrid infrastructure architectures.
Although public exploitation has not been confirmed at this time, vulnerabilities that allow unauthenticated root-level access to network security management infrastructure historically attract rapid proof-of-concept development and opportunistic exploitation.
S10 – What We Don’t Yet Know
Several aspects of the threat landscape associated with CVE-2026-20079 and CVE-2026-20131 remain uncertain.
Key unknowns include:
· Whether threat actors are actively scanning for exposed FMC management interfaces
· Whether proof-of-concept exploit code targeting these vulnerabilities will become publicly available
· Whether automated exploitation tools will emerge targeting internet-accessible FMC deployments
· Whether opportunistic attackers will prioritize firewall management platforms due to their strategic operational impact
· Whether advanced threat actors may target centralized firewall control systems to weaken enterprise defensive controls
Continued monitoring of threat intelligence reporting and network telemetry will help determine whether exploitation activity increases following publication of Cisco’s advisory.
S11 – Exploit Conditions Snapshot
The vulnerabilities share similar exploitation conditions because both affect the Cisco Secure Firewall Management Center web-based management interface.
Exploit conditions include:
Attack Vector
· Network
Attack Surface
· Cisco Secure Firewall Management Center web-based management interface
Privileges Required
· None
User Interaction
· None
Exploit Method
· Crafted HTTP requests or malicious serialized Java objects delivered to the management interface
Resulting Privileges
· Root-level access to the underlying operating system
Exposure risk is significantly reduced when FMC management interfaces are restricted to trusted internal networks and not accessible from the public internet.
S12 – Realistic Exploit Scenario
A realistic exploitation scenario would begin with attackers identifying organizations that expose Cisco Secure Firewall Management Center management interfaces to the internet or to poorly segmented internal network environments.
Attackers could then send crafted HTTP requests or serialized Java payloads to the web-based management interface to exploit the authentication bypass or insecure deserialization vulnerabilities. Successful exploitation would allow the attacker to execute commands with root privileges on the FMC appliance.
Once control of the management platform is established, attackers could modify firewall rules, disable monitoring functions, or create unauthorized access paths across enterprise network boundaries. Because FMC distributes configuration changes to managed firewall devices, unauthorized policy updates could propagate simultaneously across multiple firewall appliances and network segments.
Attackers may also attempt to establish persistence within the FMC environment in order to maintain long-term influence over firewall policy and network traffic inspection controls.
S13 – Today’s Hunt Focus
SOC teams should prioritize monitoring for indicators associated with abnormal FMC management activity and unauthorized firewall configuration changes.
Signal
· Suspicious HTTP requests targeting FMC management endpoints
Telemetry
· FMC web server access logs
· Network traffic telemetry
· Firewall access logs
Why It Matters
· Repeated or abnormal requests may indicate attempts to exploit authentication bypass or insecure deserialization vulnerabilities
Signal
· Unexpected administrative logins or configuration changes within FMC
Telemetry
· FMC administrative audit logs
· Configuration change records
Why It Matters
· Unauthorized administrative activity may indicate compromise of the firewall management platform
Signal
· Firewall policy updates affecting multiple managed devices within a short time period
Telemetry
· Firewall configuration synchronization logs
· Policy deployment events
Why It Matters
· Unexpected policy changes may indicate manipulation of firewall rules following compromise of the management control plane
S14 – Sectors
Cisco Secure Firewall Management Center is widely deployed as the centralized policy and monitoring platform for enterprise firewall environments. Because the platform manages firewall configuration and policy distribution across multiple security zones, vulnerabilities affecting the management interface can impact organizations operating large or distributed network security architectures.
Primary sectors potentially affected include:
· Information Technology and Managed Service Providers
· Financial Services and Banking
· Healthcare and Medical Infrastructure
· Government and Public Sector Networks
· Telecommunications and Network Service Providers
· Energy and Critical Infrastructure Operators
Organizations operating large firewall fleets or multi-site network environments may experience greater operational exposure due to the centralized nature of firewall policy distribution.
S14A – Countries
Cisco firewall infrastructure and centralized firewall management platforms are deployed globally across enterprise and government environments. Exposure therefore depends primarily on the presence of vulnerable Cisco Secure Firewall Management Center deployments rather than geographic location.
Regions with significant enterprise Cisco infrastructure adoption include:
· United States
· Canada
· United Kingdom
· Germany
· France
· Australia
· Japan
· Singapore
S15 – Vulnerability Lifecycle Timeline
The lifecycle of CVE-2026-20079 and CVE-2026-20131 follows the standard discovery and disclosure process associated with enterprise network infrastructure vulnerabilities.
Key lifecycle milestones include:
· Discovery of authentication bypass and insecure deserialization vulnerabilities affecting Cisco Secure Firewall Management Center management services
· Vendor validation and internal investigation conducted by Cisco security teams
· Publication of Cisco security advisories describing the vulnerabilities
· Release of remediation updates through the Cisco March 2026 bundled security publication
· Public disclosure through vulnerability databases and security advisory distribution channels
· Following disclosure, continued security research may increase the likelihood of exploit development.
S16 – CVSS, CWE, KEV, Nessus and EPSS
Severity metrics and vulnerability classification frameworks provide context for remediation prioritization.
Key vulnerability classification elements include:
CVSS Severity
· Critical
Common Weakness Enumeration
· CWE-288 Authentication Bypass
· CWE-502 Deserialization of Untrusted Data
CISA Known Exploited Vulnerabilities Catalog
· Not known at this time
Nessus Detection Coverage
· Detection support expected through vendor and community plugin updates
Exploit Prediction Scoring System
· Not known at this time
· Severity scoring reflects the presence of unauthenticated remote exploitation paths combined with root-level operating system access.
S16A – CVE-2026-20079 and CVE-2026-20131
CVE-2026-20079
Vendor
· Cisco
Affected Platform
· Cisco Secure Firewall Management Center Software
· Cisco Security Cloud Control Firewall Management
Vulnerability Type
· Authentication bypass
Impact Scope
· Unauthenticated remote access to the FMC web interface followed by execution of scripts and commands with root privileges on the underlying operating system
CVSS v3.1
· Severity: 10.0 (Critical)
· Vector: AV:N / AC:L / PR:N / UI:N / S:C / C:H / I:H / A:H
CWE
· CWE-288 – Authentication Bypass Using an Alternate Path or Channel
CISA KEV
· Not listed at this time
Nessus Plugin Coverage
· Plugin-specific coverage not published at this time
· Tenable classifies the CVE as Vulnerability Being Monitored
· Tenable plugin page status: Coming Soon
EPSS
· 0.00185
Exploit Path Summary
· Crafted HTTP requests delivered to the FMC management interface may bypass authentication and allow execution of scripts and commands as root
CVE-2026-20131
Vendor
· Cisco
Affected Platform
· Cisco Secure Firewall Management Center Software
· Cisco Security Cloud Control Firewall Management
Vulnerability Type
· Remote code execution
Impact Scope
· Unauthenticated remote delivery of crafted serialized Java objects to the FMC web management interface may result in arbitrary Java code execution as root
CVSS v3.1
· Severity: 10.0 (Critical)
· Vector: AV:N / AC:L / PR:N / UI:N / S:C / C:H / I:H / A:H
CWE
· CWE-502 – Deserialization of Untrusted Data
CISA KEV
· Not listed at this time
Nessus Plugin Coverage
· Plugin-specific coverage not published at this time
· Tenable classifies the CVE as Vulnerability Being Monitored
· Tenable plugin page status: Coming Soon
EPSS
· 0.00437
Exploit Path Summary
· Crafted serialized Java payloads delivered to the FMC web-based management interface may enable arbitrary code execution and root-level control of the appliance
Analyst Validation Notes
· Cisco assigns both vulnerabilities a CVSS v3.1 base score of 10.0 and identifies no workarounds in the published advisories.
· NVD currently shows both records as awaiting analysis, but displays Cisco CNA scoring and the associated CWE mappings for CVE-2026-20079.
· CISA’s KEV catalog is the authoritative source for known exploited vulnerability status; these CVEs are not listed there at this time.
· Tenable has pages for both CVEs and marks them as Vulnerability Being Monitored; the associated plugin pages currently show Coming Soon rather than published plugin IDs.
· Both vulnerabilities affect the Cisco Secure Firewall Management Center web management interface and enable attackers to obtain full administrative control of the underlying appliance.
S17 – Exploit Status
Current publicly available information indicates limited confirmed exploitation activity associated with these vulnerabilities.
Exploit status indicators include:
· Public proof-of-concept exploit code
· Not known at this time
· Confirmed exploitation in the wild
· Not known at this time
· Active threat actor campaigns targeting these vulnerabilities
· Not known at this time
Although confirmed exploitation has not been reported, vulnerabilities that enable unauthenticated remote access to network security infrastructure frequently attract rapid research and exploit development following disclosure.
S18 – Confidence & Assessment Statement
The analysis presented in this report is based on vendor advisories, vulnerability database records, and publicly available technical documentation describing the exploit conditions.
Confidence levels associated with this assessment include:
· Vulnerability existence and technical characteristics
· High confidence
· Exploit feasibility under documented conditions
· High confidence
· Current threat actor activity targeting these vulnerabilities
· Not known at this time
· Likelihood of exploit development following disclosure
· Moderate confidence
· This assessment reflects analysis of Cisco security advisories, NVD vulnerability records, and publicly available technical documentation describing exploit conditions.
· No confirmed exploitation campaigns were identified in open-source reporting at the time of publication.
· Analytic judgments regarding potential attacker behavior are based on historical patterns observed following disclosure of vulnerabilities affecting enterprise security infrastructure.
S19 – Threat Actor Opportunity
Threat actors may view vulnerabilities affecting centralized firewall management platforms as high-value targets because these systems influence enterprise network security controls.
Potential attacker objectives include:
· Manipulating firewall rules to create unauthorized network access paths
· Disabling traffic inspection or monitoring functions
· Establishing persistence within network security infrastructure
· Facilitating lateral movement across enterprise network segments
· Because Cisco Secure Firewall Management Center distributes configuration updates to multiple firewall devices, compromise of the platform could allow attackers to influence defensive controls across a broad portion of enterprise infrastructure.
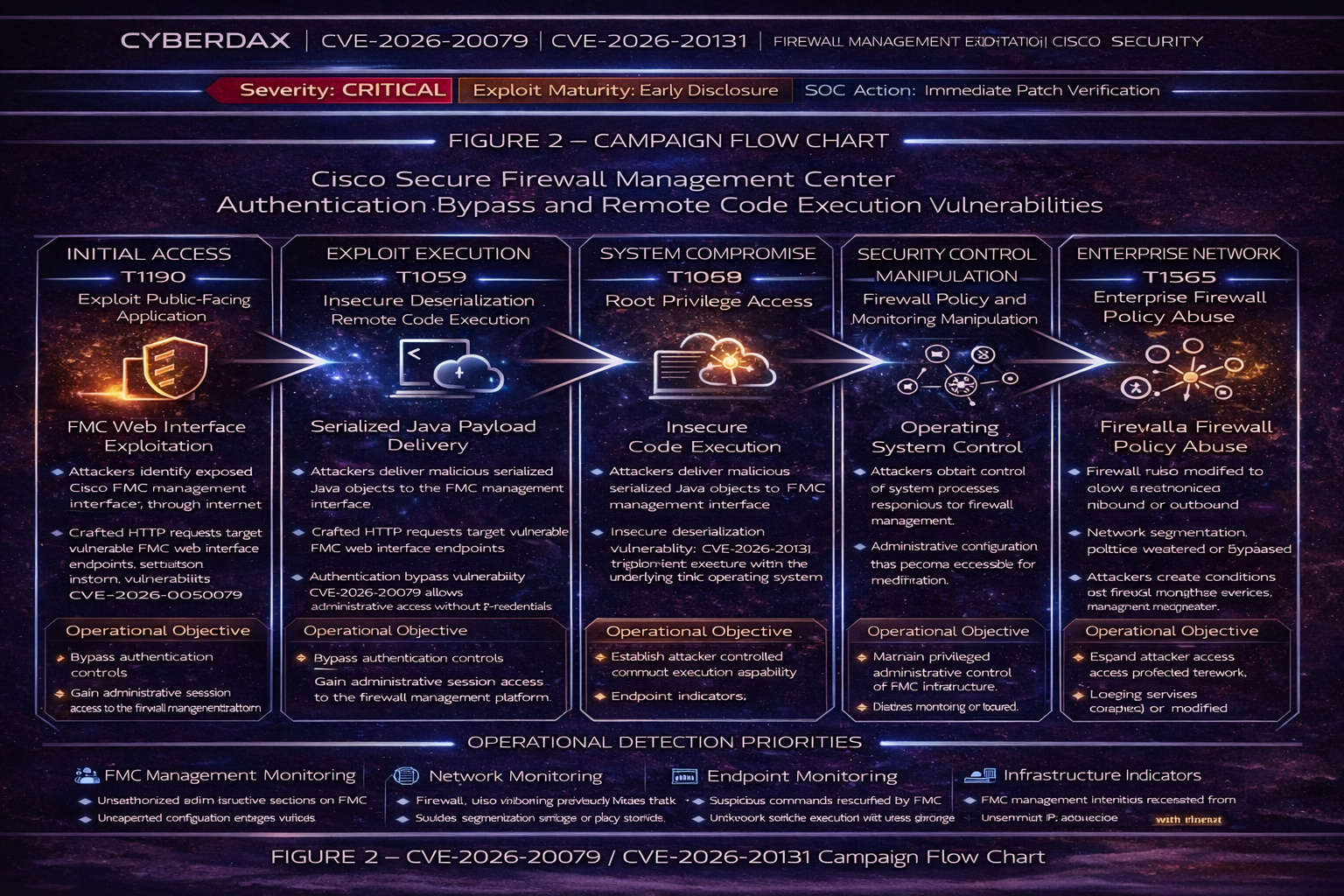
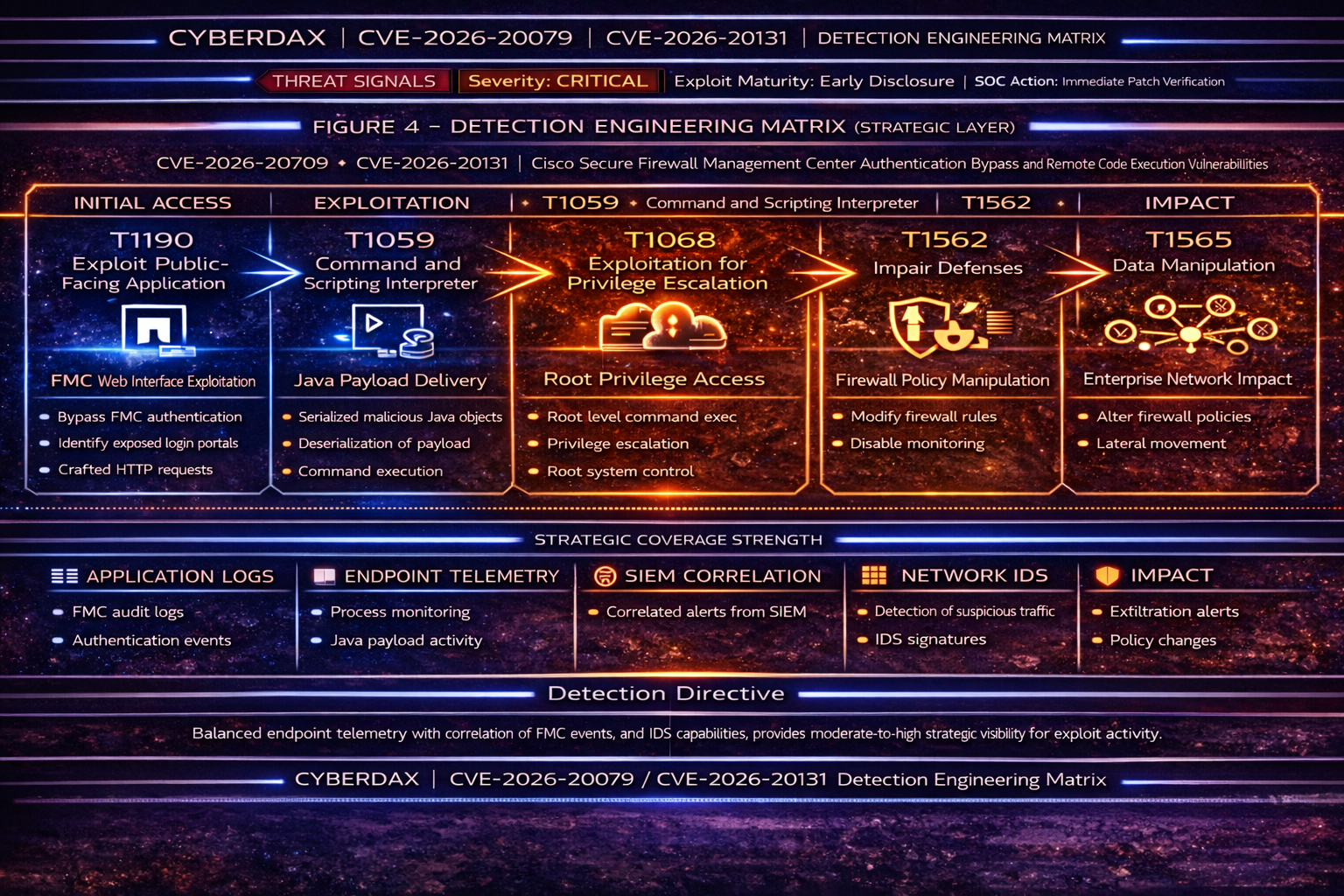
S20 – MITRE ATT&CK Chain Flow Mapping
The vulnerabilities align with MITRE ATT&CK techniques associated with exploitation of internet-accessible management systems.
Initial Access
· T1190 – Exploit Public-Facing Application
· Crafted HTTP requests or serialized payloads delivered to the FMC management interface
Execution
· T1059 – Command and Scripting Interpreter
· Successful exploitation enables command execution on the FMC appliance
Persistence
· T1505 – Server Software Component
· Attackers may deploy scripts or modify system components to maintain access
Privilege Escalation
· T1068 – Exploitation for Privilege Escalation
· Vulnerabilities provide root-level operating system access
Defense Evasion
· T1562 – Impair Defenses
· Attackers may modify firewall logging or monitoring configurations
Impact
· T1565 – Data Manipulation
· Firewall policy changes may alter network security enforcement
S21 – Stage-Based TTPs
T1190 – Exploit Public-Facing Application
· Attackers may deliver crafted HTTP requests or serialized Java payloads to the Cisco Secure Firewall Management Center web-based management interface to trigger authentication bypass or insecure deserialization conditions.
Operational Objective
· Gain unauthenticated access to the FMC management plane
Artifacts
· Crafted HTTP requests targeting administrative web endpoints
· Serialized Java payload structures delivered through HTTP POST requests
· External connections to exposed FMC management services
Detection Relevance
· Monitor inbound management interface traffic for abnormal request structures or serialized payload delivery patterns
T1059 – Command and Scripting Interpreter
· Successful exploitation allows attackers to execute operating system commands or scripts with root privileges on the FMC appliance.
Operational Objective
· Execute attacker-controlled commands within the management appliance
Artifacts
· Unexpected shell or command execution under root privileges
· System commands originating from the web management process
· Administrative command activity outside normal maintenance operations
Detection Relevance
· Monitor appliance process logs for root-level command execution events associated with the management service
T1505 – Server Software Component
· Attackers may modify service components or scripts within the FMC environment to maintain persistent administrative access.
Operational Objective
· Establish persistence within the firewall management system
Artifacts
· Modified service configuration files
· Unauthorized changes to application scripts or startup components
· Persistent administrative access mechanisms
Detection Relevance
· Monitor system directories and service configurations for unexpected modification events
T1068 – Exploitation for Privilege Escalation
· The documented vulnerabilities allow attackers to gain root-level operating system access following successful exploitation.
Operational Objective
· Obtain full administrative control of the FMC appliance
Artifacts
· Root-level command execution
· Elevated process activity originating from the web management component
· Administrative privilege escalation events
Detection Relevance
· Investigate root-level activity associated with web management service operations
T1562 – Impair Defenses
· Attackers controlling the FMC platform may alter monitoring or logging functions to reduce detection visibility.
Operational Objective
· Reduce defensive monitoring capability
Artifacts
· Disabled or modified logging settings
· Changes to audit configuration
· Suppression of monitoring or alert generation
Detection Relevance
· Monitor configuration changes affecting logging, monitoring, or audit controls
T1565 – Data Manipulation
· Attackers may alter firewall rules or policy objects to change enterprise network traffic enforcement.
Operational Objective
· Modify firewall policy to influence network access controls
Artifacts
· Unauthorized firewall rule modifications
· Policy deployment activity outside scheduled change windows
· Configuration updates affecting multiple managed firewall devices
Detection Relevance
· Monitor firewall configuration deployment logs and rule modification events
S22 – Malware and SHA256
Associated malware family
· Not known at this time
Exploit payload SHA256
· Not known at this time
S23 – Behavior and Log Artifacts
Network Artifacts
· Repeated HTTP requests targeting Cisco Secure Firewall Management Center administrative endpoints
· Serialized Java payload delivery attempts through the web management interface
· Abnormally structured HTTP POST requests directed at management services
Host Artifacts
· Root-level command execution on the FMC appliance
· Creation or modification of system scripts within administrative directories
· Unexpected process activity associated with the web management service
Log Artifacts
· Administrative sessions originating from unfamiliar network addresses
· Firewall configuration deployment events outside scheduled maintenance windows
· Authentication events associated with unknown administrative source systems
· Changes to logging or monitoring settings within the management platform
S24 – IOC Confidence and Hunt Prioritization (Numeric Scores)
Scoring Model
· Signal Fidelity (0–40)
· Exploit Correlation (0–40)
· Operational Impact (0–20)
Maximum Score: 100
Immediate Priority
· Unauthorized firewall configuration deployment affecting multiple managed devices — 95
· Root-level command execution associated with FMC management interface activity — 93
· Administrative access from unfamiliar external network locations followed by configuration changes — 91
High Priority
· Serialized Java payload delivery attempts detected in inbound HTTP traffic — 87
· Repeated HTTP requests targeting FMC management endpoints from a single external host — 84
· Administrative login attempts occurring outside normal operational time windows — 80
Moderate Priority
· Generic network scanning targeting FMC administrative web interfaces — 60
· Isolated anomalous HTTP request patterns without additional suspicious behavior — 55
S25 – Detection Signals Layer
Primary Signals
· Repeated HTTP POST requests targeting Cisco Secure Firewall Management Center management interface endpoints
· Serialized Java object delivery patterns associated with insecure deserialization attempts
· Root-level command execution spawned from Java or web service contexts within the FMC appliance
Secondary Signals
· Administrative session establishment originating from unfamiliar network locations
· Firewall policy deployment activity occurring outside scheduled maintenance windows
· Changes to logging, monitoring, or audit configuration within the FMC platform
Detection Interpretation
· Exploitation attempts typically produce both network-layer and appliance-level signals
· Detection confidence increases when suspicious inbound management traffic precedes privileged command execution or configuration modification
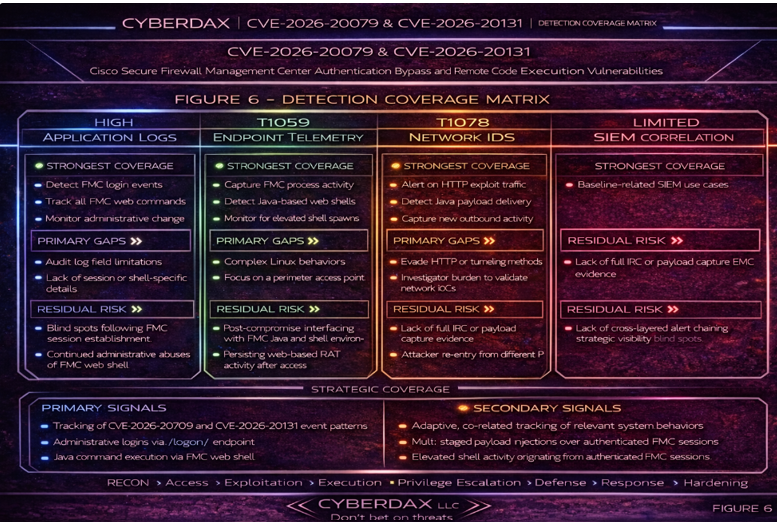
S26 – Detection Coverage Matrix (Strategic Detection Layer)
Network Telemetry
· Detect repeated HTTP POST requests targeting FMC management interface paths
· Identify serialized Java payload indicators within inbound HTTP traffic
Appliance Telemetry
· Detect root-level command execution associated with web or Java service processes
· Monitor authentication and administrative session creation events
Configuration Monitoring
· Detect firewall policy deployment events affecting managed devices
· Detect rule modification or configuration changes within the FMC platform
SIEM Correlation
· Correlate suspicious inbound management interface access with appliance command execution or configuration deployment activity
Coverage Interpretation
· The strongest detection occurs when network exploit delivery signals are correlated with appliance-level command execution or configuration changes
Residual Detection Risk
· Exploit payloads that mimic legitimate administrative request structure may appear syntactically normal at the network layer
SOC Priority
· Prioritize investigation when suspicious inbound management traffic precedes root-level execution or firewall policy modification
S27 – Detection Engineering Matrix (Operational Rule Layer)
Detection Goal
Detect exploitation of Cisco Secure Firewall Management Center vulnerabilities by correlating suspicious inbound management interface activity with privileged execution and configuration manipulation events.
Detection Strategy
Network Layer
· Detect repeated POST requests targeting FMC administrative web endpoints
· Detect serialized Java payload indicators consistent with insecure deserialization exploitation attempts
Appliance Layer
· Detect root-level shell or script execution originating from Java or web service processes
· Detect administrative sessions established from unfamiliar external source addresses
Configuration Layer
· Detect firewall rule modification or policy deployment events affecting managed firewall devices
· Detect configuration changes impacting logging, monitoring, or audit visibility
Correlation Layer
· Correlate suspicious inbound HTTP activity with root-level command execution or configuration changes occurring within a short time window
High Confidence Exploit Pattern
1. External host initiates POST requests to FMC management interface
2. Serialized Java payload indicator or abnormal request pattern is observed
3. Root-level command execution occurs within the appliance
4. Firewall configuration modification or policy deployment activity follows
This sequence should be treated as probable exploitation of the FMC management platform.
S28 – SOC Investigation Pivot Fields
Primary Pivot Fields
· host – FMC appliance hostname or system identifier
· source_ip – remote host initiating connection
· username – administrative account associated with the session
· http_uri – management endpoint accessed
· http_method – HTTP request method used
· process_name – process associated with command execution
· command_line – executed command context
Secondary Pivot Fields
· parent_process
· session_id
· firewall_policy_id
· configuration_change_id
· device_group
· user_agent
· destination_port
Operational Investigation Guidance
1. Confirm whether the FMC management interface is exposed to external networks
2. Identify the source IP associated with suspicious HTTP POST activity
3. Review administrative session establishment or authentication events
4. Investigate root-level command execution originating from web service processes
5. Pivot across configuration deployment logs for unauthorized firewall policy changes
6. Validate FMC patch status and management interface exposure
S29 – Ultra-Tuned Detection Engineering Rules
Suricata
Rule Name
CyberDax FMC Serialized Java Deserialization Attempt
Purpose
· Detect serialized Java payload delivery attempts targeting FMC management endpoints.
Tuning Explanation
· Restricted to known FMC hosts to prevent triggering on unrelated web traffic
· Requires POST request, management endpoint path, and Java serialization header
· Designed to detect insecure deserialization exploit delivery rather than normal administrator browsing
System-Ready Rule
alert http $EXTERNAL_NET any -> $FMC_SERVERS 443 (
msg:"CYBERDAX FMC Serialized Java Deserialization Attempt";
flow:to_server,established;
http.method; content:"POST";
http.uri; pcre:"/\/(api|fmc|admin|j_security_check)\b/i";
content:"|AC ED 00 05|"; fast_pattern;
classtype:web-application-attack;
sid:2026200793;
rev:2;
)
Operational Guidance
· Escalate when repeated POST requests originate from a single external host
· Promote to high severity when correlated with root-level execution events
SentinelOne (Deep Visibility)
Rule Name
CyberDax FMC Web Process Shell Execution
Purpose
· Detect root-level shell or script execution originating from Java or web service processes within the FMC appliance.
Tuning Explanation
· Requires web-service parent process context
· Limits detection to common attacker utilities
· Prevents alerts on standard FMC service activity
System-Ready Query
EventType = "Process Creation"
AND User = "root"
AND (
ProcessName IN ("bash","sh","python","perl","curl","wget","nc","socat")
)
AND (
ParentProcessName IN ("java","tomcat","httpd","apache2","nginx")
)
AND HostRole = "FMC"
Operational Guidance
· Treat as high-confidence post-exploitation behavior
· Escalate to critical when preceded by suspicious inbound management interface access
Splunk
Rule Name
CyberDax FMC Exploit Delivery Followed by Root Execution
Purpose
· Correlate suspicious HTTP POST activity to FMC management endpoints with root-level command execution.
Tuning Explanation
· Requires both network exploit delivery signal and process execution signal
· Restricts detection to FMC hosts to reduce noise
· Uses short correlation window to eliminate unrelated activity
System-Ready Rule
(
search index=web_logs dest_port=443 method=POST uri_path IN ("/api/*","/fmc/*","/admin/*")
| eval event_type="exploit_delivery"
| table _time src_ip host uri_path
)
OR
(
search index=endpoint_logs host_category="FMC"
user=root process_name IN ("bash","sh","python","perl","curl","wget")
| eval event_type="root_exec"
| table _time host process_name
)
| sort 0 _time
| transaction host maxspan=3m
| search event_type="exploit_delivery" event_type="root_exec"
| stats values(src_ip) as src_ip values(uri_path) as uri_path values(process_name) as process_name by host
| eval severity="critical"
Operational Guidance
· Treat as probable exploitation when both signals occur on the same FMC host
Elastic (EQL)
Rule Name
CyberDax FMC External Access Leading to Root Execution
Purpose
· Detect exploitation attempts by correlating inbound management interface traffic with root shell execution.
System-Ready Rule
sequence by host.name with maxspan=5m
[network where destination.port == 443
and host.role == "fmc"]
[process where user.name == "root"
and process.name in ("bash","sh","python","perl","curl","wget")
and process.parent.name in ("java","httpd","apache2","nginx","tomcat")]
Operational Guidance
· Treat as high confidence on FMC hosts
· Investigate request paths, source IP reputation, and process lineage
Sigma
Rule Name
FMC Web Context Root Shell Execution
Purpose
· Detect root-level shell execution originating from web service processes within FMC.
System-Ready Rule
title: FMC Web Context Root Shell Execution
id: 92d0d0c2-cve-2026-20079-fmc-shell
status: experimental
logsource:
category: process_creation
product: linux
detection:
parent_selection:
ParentImage|endswith:
- '/java'
- '/tomcat'
- '/httpd'
- '/apache2'
- '/nginx'
child_selection:
Image|endswith:
- '/bash'
- '/sh'
- '/python'
- '/perl'
- '/curl'
- '/wget'
User: root
condition: parent_selection and child_selection
level: high
tags:
- attack.t1190
- attack.t1059
Operational Guidance
· Tune using FMC host allowlists and maintenance windows
YARA
Rule Name
CyberDax Java Deserialization Payload Hunt
Purpose
· Assist retrospective hunting for serialized Java exploit payload artifacts associated with insecure deserialization exploitation.
System-Ready Rule
rule CYBERDAX_FMC_Java_Deserialization_Hunt
{
meta:
description = "Serialized Java exploit payload artifact"
author = "CyberDax"
version = "2"
strings:
$magic = { AC ED 00 05 }
$ysoserial = "ysoserial"
$objectstream = "java.io.ObjectInputStream"
$readobject = "readObject"
condition:
$magic and 1 of ($ysoserial,$objectstream,$readobject)
}
Operational Guidance
· Intended for exploit sample hunting and forensic review rather than direct SOC alerting
S29A – Confidence Tiers for Analysts
Supportive / Low-Confidence Telemetry
· Isolated suspicious POST requests targeting FMC management paths
· Single external access attempt to the management interface
High-Confidence Exploit Correlation
· Suspicious inbound management traffic followed by root shell execution
· External management access followed by firewall policy deployment or configuration modification
Post-Compromise Indicators
· Root-level command execution spawned by Java or web service processes
· Unauthorized firewall policy deployment
· Changes to logging or monitoring configuration within FMC
S29B – SOC Investigation Playbook
Phase 1 – Alert Validation
Determine whether the alert represents legitimate administrative activity or potential exploitation.
· Confirm host identity as FMC appliance
· Validate source IP reputation and network location
· Review request path and HTTP method
Phase 2 – Management Access Analysis
· Identify repeated POST requests targeting management endpoints
· Determine whether the interface should be externally accessible
Phase 3 – Command Execution Investigation
· Review root-level process execution
· Inspect parent-child process relationships
Phase 4 – Configuration Impact Assessment
· Investigate firewall rule modifications and policy deployment events
· Identify unauthorized configuration changes
Phase 5 – Containment and Remediation
· Restrict management interface exposure
· Patch FMC appliances
· Reset administrative credentials and validate firewall policy integrity
S29C – SOC Hunt Pivot and Analyst Quick Reference
Primary Investigation Pivot Fields
· source_ip
· host
· username
· http_uri
· process_name
· command_line
Secondary Investigation Pivot Fields
· parent_process
· firewall_policy_id
· configuration_change_id
· session_id
· device_group
Enterprise Hunting Queries
· Repeated POST requests targeting FMC management endpoints
· Root shell execution spawned by Java or web service processes
· Firewall policy deployment events occurring outside scheduled maintenance windows
Rapid Triage Workflow
1. Confirm FMC patch status
2. Identify external source IP
3. Review administrative activity
4. Investigate root command execution
5. Validate firewall configuration integrity
Indicators of Exploit Campaign Activity
· Repeated serialized payload delivery attempts
· Similar management interface access patterns across multiple FMC environments
· Root execution followed by firewall policy modification
S30 – SIEM Correlation Logic (High Confidence Detection)
Rule Name
FMC Management Exploitation Activity Correlation
Detection Intent
· Detect probable exploitation of Cisco Secure Firewall Management Center by correlating suspicious management interface traffic with privileged execution and configuration manipulation.
Correlation Logic
1. External host accesses FMC management interface
2. Suspicious POST activity or serialized payload indicator is detected
3. Root-level command execution occurs within five minutes
4. Optional severity escalation if:
· Firewall policy deployment occurs
· Logging or monitoring settings are modified
· Repeated access attempts originate from the same external host
This sequence should be treated as probable exploitation of FMC management infrastructure.
S31 – Delivery Methods
Exploit Delivery Context
· Attackers must reach the Cisco Secure Firewall Management Center web-based management interface
· Exploitation occurs through crafted HTTP requests or serialized Java payloads delivered to the management service
Primary Delivery Methods
External Management Interface Exposure
· Direct HTTPS access to FMC management interface from the public internet
· Automated scanning infrastructure identifying exposed administrative services
Serialized Java Payload Delivery
· Crafted serialized Java objects delivered through HTTP POST requests
· Payloads designed to trigger insecure deserialization behavior within the Java application runtime
Authentication Bypass Exploitation
· Crafted HTTP requests exploiting improper process initialization conditions
· Requests bypass authentication checks and reach privileged application components
Targeted Exploitation Activity
· Reconnaissance identifying exposed firewall management infrastructure
· Exploit attempts targeting high-value enterprise firewall management systems
Operational Implication
· Organizations exposing the FMC management interface to external networks face significantly higher exploitation risk
S32 – Exposure Conditions
Conditions Increasing Exposure Risk
Management Interface Exposure
· FMC web management interface accessible from external or untrusted networks
· Firewall management services reachable through internet-facing infrastructure
Network Segmentation Weakness
· Management networks not isolated from enterprise user networks
· Insufficient segmentation between administrative infrastructure and production environments
Administrative Access Practices
· Management interface accessible from broad internal network ranges
· Administrative access not restricted to dedicated management hosts
Infrastructure Deployment Factors
· Large distributed firewall environments with centralized policy management
· Remote administrative access requiring broad management interface reachability
Risk Reduction Practices
· Restrict FMC administrative access to dedicated management networks
· Require VPN-based administrative access for remote operators
· Implement strict network segmentation protecting firewall management infrastructure
S33 – Exploit Preconditions
Successful exploitation requires the following technical conditions.
Network Reachability
· Attacker must establish network connectivity to the FMC management interface
Interface Accessibility
· Web-based administrative interface must accept inbound HTTP or HTTPS requests
Exploit Payload Delivery
· Crafted HTTP requests or serialized Java payloads must reach vulnerable application components
Vulnerable Software Version
· FMC appliance must run a software version affected by CVE-2026-20079 or CVE-2026-20131
Privilege Escalation Outcome
· Successful exploitation allows execution of scripts or commands with root privileges on the appliance
Operational Impact Conditions
· Administrative control of FMC may allow modification of firewall rules and policy deployment across managed devices
S34 – Defensive Controls and Hardening Recommendations
Immediate Defensive Controls
Network Segmentation
· Restrict FMC management interface access to dedicated administrative networks
· Prevent direct exposure of the management interface to the public internet
Access Control
· Limit administrative access to authorized management hosts
· Enforce strong authentication controls for administrative accounts
Patch Management
· Apply Cisco remediation updates addressing CVE-2026-20079 and CVE-2026-20131
· Validate FMC version compliance with the Cisco March 2026 bundled security publication
Monitoring and Logging
· Enable detailed administrative audit logging within FMC
· Monitor appliance process execution and system activity
Configuration Integrity Monitoring
· Track firewall rule changes and configuration deployment activity
· Alert on configuration modifications outside approved change windows
Detection Integration
· Integrate FMC telemetry with SIEM detection rules defined in S30
· Monitor management interface activity against detection signals defined in S25
Incident Preparedness
· Maintain incident response procedures for firewall management platform compromise
· Validate firewall policy integrity following suspected administrative compromise
S35 – Strategic Defensive Improvements
Management Plane Isolation
· Separate firewall management infrastructure from general enterprise network segments
· Restrict access to dedicated management networks and administrative hosts
Privileged Access Governance
· Enforce identity-based authentication and role-based administrative access
· Limit privileges for firewall management systems to required operational roles
Privileged Activity Monitoring
· Monitor administrative session establishment and privileged command execution
· Correlate privileged activity with network telemetry and configuration change events
Centralized Security Telemetry
· Integrate FMC logs with enterprise SIEM platforms
· Correlate firewall management telemetry with network and endpoint monitoring systems
Security Architecture Improvements
· Deploy management network segmentation protecting critical infrastructure
· Implement continuous monitoring of administrative configuration activity
Operational Security Review
· Conduct periodic review of firewall management system exposure
· Validate that management interfaces remain isolated from untrusted network segments
Long-Term Security Outcome
· Reduced attack surface for centralized firewall management systems
· Improved detection capability for exploitation attempts targeting administrative infrastructure
S36 – Defensive Control and Hardening Architecture
Security Architecture Layers
Management Plane Isolation
· Deploy Cisco Secure Firewall Management Center within dedicated management network segments
· Prevent direct exposure of the FMC administrative interface to public networks
· Restrict administrative access to trusted management workstations
Identity and Administrative Access Controls
· Enforce strong authentication for FMC administrative accounts
· Limit access privileges to authorized operational roles
· Require secure remote access channels for administrators operating outside trusted networks
Network Security Monitoring Layer
· Monitor inbound connections targeting FMC management interfaces
· Detect abnormal HTTP POST activity and serialized payload indicators defined in detection signals in S25
· Correlate management access activity with SIEM correlation logic defined in S30
Configuration Integrity Monitoring Layer
· Monitor firewall rule changes and policy deployment events
· Alert on configuration changes occurring outside approved change windows
· Validate integrity of firewall policy following administrative actions
Security Outcome
· Layered monitoring of management access, privileged execution, and configuration modification improves detection of exploitation attempts targeting firewall management infrastructure
S37 – Seven-Day Response Plan
Immediate operational response following vulnerability disclosure should prioritize exposure reduction, monitoring activation, and remediation validation.
Day 1 – Exposure Assessment
· Identify all Cisco Secure Firewall Management Center systems deployed within the organization
· Determine whether management interfaces are accessible from external or untrusted networks
· Confirm current software version for each FMC appliance
Day 2 – Risk Containment
· Restrict management interface access to trusted administrative networks
· Remove unnecessary external connectivity to firewall management infrastructure
· Validate administrative access control policies
Day 3 – Patch Deployment Planning
· Review Cisco remediation guidance within the March 2026 bundled security publication
· Identify upgrade paths for vulnerable FMC versions
· Schedule remediation within maintenance windows
Day 4 – Detection Monitoring Activation
· Deploy SIEM correlation logic defined in S30
· Monitor exploit signals defined in S25
· Investigate abnormal HTTP POST requests targeting management endpoints
Day 5 – Patch Implementation
· Apply Cisco software updates addressing CVE-2026-20079 and CVE-2026-20131
· Validate successful upgrade of FMC appliances
Day 6 – Configuration Validation
· Review firewall policy deployment history
· Confirm configuration integrity across managed firewall devices
· Investigate unauthorized rule modification events
Day 7 – Security Posture Review
· Review firewall management network architecture
· Confirm continued isolation of management interfaces
· Update operational security procedures and incident response documentation
S38 – Post-Incident Insights and Recommendations
BLUF – Bottom Line Up Front
· The vulnerabilities CVE-2026-20079 and CVE-2026-20131 expose a control-plane risk affecting Cisco Secure Firewall Management Center (FMC).
· Successful exploitation could allow attackers to bypass authentication, execute privileged commands, and manipulate firewall policies across multiple managed devices.
· Because FMC governs enterprise network security enforcement, compromise represents a Tier-0 infrastructure event requiring accelerated patching, restricted administrative access, continuous monitoring, and immediate SOC escalation for suspicious administrative activity.
Strategic Insight
The vulnerabilities CVE-2026-20079 and CVE-2026-20131 highlight the systemic risk associated with compromise of centralized security management infrastructure. Cisco Secure Firewall Management Center (FMC) functions as the control plane responsible for firewall policy deployment and monitoring across enterprise environments.
Successful exploitation could allow attackers to bypass authentication controls, execute privileged commands, and manipulate firewall policies across multiple managed devices.
Because FMC governs network security enforcement, compromise represents a control-plane security event capable of weakening enterprise defenses and enabling adversaries to conceal malicious activity within enterprise network segments.
Attack Path Summary
The exploitation pathway aligns with the attack chain illustrated in Figure 3 – MITRE ATT&CK Chain Flow Chart.
· T1190 – Exploit Public-Facing Application
Attackers target exposed FMC administrative interfaces.
· T1059 – Command and Scripting Interpreter
Exploitation enables execution of attacker-controlled commands within FMC service processes.
· T1068 – Exploitation for Privilege Escalation
Attackers escalate privileges and obtain administrative control of the system.
· T1565 – Data Manipulation
Compromise allows modification of firewall policies and monitoring rules protecting enterprise network segments.
This sequence allows adversaries to manipulate defensive controls while reducing visibility into malicious activity.
Detection and Monitoring Lessons
Analysis of the Detection Coverage Matrix (Figure 6) and Operational Detection Rules (Figure 7) shows that reliable detection depends on correlating telemetry across application, host, and network monitoring systems.
Security teams should prioritize monitoring for:
Administrative Authentication Anomalies
· Repeated authentication attempts targeting FMC administrative endpoints
· Administrative logins from unfamiliar IP addresses or geographic locations
· Authentication activity occurring outside normal operational windows
Privileged Command Execution
· Shell commands executed by FMC application or web service processes
· New privileged processes spawned by FMC service accounts
· Command execution immediately following authentication events
Configuration Manipulation
· Firewall policy deployments occurring outside approved change windows
· Administrative configuration changes affecting multiple managed firewall devices
· Unauthorized modification of logging or monitoring configurations
Suspicious Network Activity
· Outbound communications originating from FMC infrastructure to unknown hosts
· DNS requests generated by firewall management systems
· Network connections consistent with command-and-control activity
SOC teams should treat anomalous administrative activity involving firewall management systems as critical-severity alerts requiring immediate investigation and escalation.
Recommended Defensive Actions
Organizations should implement the controls outlined in Figure 8 – Defensive Control and Hardening Architecture.
Priority defensive actions include:
· Apply Cisco security updates addressing CVE-2026-20079 and CVE-2026-20131
· Restrict FMC administrative access to dedicated internal management networks
· Enforce multi-factor authentication for administrative accounts
· Monitor firewall policy deployments and configuration changes for unauthorized activity
· Review FMC logs for suspicious administrative sessions or command execution
· Validate firewall rule integrity across managed devices after any suspected compromise
If unauthorized access is detected, affected FMC systems should be immediately isolated, investigated, and rebuilt to ensure the integrity of firewall policies and monitoring configurations.
Operational Priority Actions
Security teams should implement the following immediate operational actions:
1. Apply security patches for CVE-2026-20079 and CVE-2026-20131 across all FMC deployments.
2. Restrict administrative access to firewall management systems to internal management networks only.
3. Enable multi-factor authentication for all firewall administration accounts.
4. Establish alerting for authentication anomalies and command execution events involving FMC systems.
5. Conduct retrospective log analysis to identify potential historical exploitation attempts.
6. Validate firewall rule integrity and policy deployment history across managed devices.
These actions should be treated as priority remediation steps for organizations operating Cisco Secure Firewall Management Center infrastructure.
Governance and Security Architecture Considerations
Security management platforms such as Cisco Secure Firewall Management Center should be treated as Tier-0 infrastructure assets because they control enterprise network defenses.
Organizations should enforce strict administrative access controls, continuous monitoring, and accelerated patch management for these systems.
Security governance programs should ensure that vulnerabilities affecting security control-plane systems receive priority remediation and executive visibility within enterprise risk management processes.
Board-Level Takeaway
The vulnerabilities CVE-2026-20079 and CVE-2026-20131 demonstrate the enterprise risk associated with compromise of centralized firewall management infrastructure. Because Cisco Secure Firewall Management Center controls network policy enforcement across the organization, successful exploitation could allow attackers to manipulate defensive controls and weaken security across the environment. Executive leadership should ensure these systems are treated as Tier-0 assets, with accelerated patching, restricted administrative access, and continuous monitoring to protect the enterprise network control plane.
S39 – Attack Economics & Organizational Impact Model
Vulnerabilities affecting centralized security management platforms create a highly favorable economic model for attackers because a single successful exploitation pathway can provide privileged access to infrastructure responsible for enforcing enterprise network security policy. When vulnerabilities such as CVE-2026-20079 and CVE-2026-20131 affect platforms like Cisco Secure Firewall Management Center, attackers may gain the ability to manipulate firewall rules, alter monitoring configurations, or obscure malicious traffic across multiple network segments.
In contrast, organizations incur substantially greater operational costs when responding to even suspected compromise of firewall management infrastructure. Defensive investigations often require forensic review of administrative activity, validation of firewall policy integrity across managed devices, credential rotation for privileged accounts, and enterprise-wide log analysis to determine whether security controls were modified or bypassed.
This imbalance illustrates a common pattern in cyber operations: relatively modest attacker investment can trigger significant defensive expenditure when vulnerabilities affect security control-plane systems responsible for enterprise network policy enforcement.
Figure 10
Figure 10 illustrates the economic lifecycle of a firewall management exploitation scenario, highlighting the relationship between attacker discovery and exploitation effort, the operational advantages gained through control of security infrastructure, and the investigative and remediation costs incurred by organizations.
Organizations that minimize patch latency, restrict administrative access to firewall management interfaces, and maintain continuous monitoring of security infrastructure significantly reduce the economic return on investment for attackers targeting control-plane systems.
S40 – References
Primary Vendor Advisory
· hxxps://sec[.]cloudapps[.]cisco[.]com/security/center/content/CiscoSecurityAdvisory/cisco-sa-onprem-fmc-authbypass-5JPp45V2
· hxxps://sec[.]cloudapps[.]cisco[.]com/security/center/content/CiscoSecurityAdvisory/cisco-sa-fmc-rce-NKhnULJh
National Vulnerability Database
· hxxps://nvd[.]nist[.]gov/vuln/detail/CVE-2026-20079
· hxxps://nvd[.]nist[.]gov/vuln/detail/CVE-2026-20131
MITRE ATT&CK Catalog
· hxxps://attack[.]mitre[.]org/