CVE-2026-21514 and CVE-2026-21513 Microsoft Office MSHTML Trust Boundary Bypass Enables Phishing-Based Initial Access Chain
BLUF
Enterprise organizations face an elevated phishing-driven intrusion risk because malicious Microsoft Office documents can bypass built-in trust protections and execute attacker-controlled web content through the MSHTML rendering engine. The issue results from a chained security bypass involving CVE-2026-21514 and CVE-2026-21513 that allows crafted documents to circumvent Mark-of-the-Web and Protected View safeguards designed to restrict active content in documents originating from untrusted sources. Exploit maturity should be considered elevated because document trust-boundary bypass vulnerabilities historically transition rapidly into large-scale phishing campaigns and require only limited user interaction to trigger execution. Executive leadership should prioritize accelerated Microsoft patch deployment, strengthen email attachment inspection and sandboxing controls, and direct security operations teams to monitor for abnormal Office processes initiating external web connections or spawning scripting activity.
S1A – Executive Risk Translation
For organizations relying on Microsoft Office workflows, these vulnerabilities convert a routine email attachment into a potential enterprise entry point capable of enabling credential theft, malware staging, or broader intrusion activity across enterprise environments.
S2 – Key Judgments
· CVE-2026-21514 enables a security bypass affecting Microsoft Office trust boundary enforcement associated with document origin protections.
· CVE-2026-21513 allows malicious HTML content rendered through the MSHTML engine to execute where security restrictions should limit active content.
· The vulnerabilities allow attackers to weaponize Office documents containing embedded HTML or web-rendered components.
· Phishing email delivery represents the most likely exploitation vector due to the document-based nature of the vulnerability chain.
· Organizations with heavy reliance on document exchange through email or collaboration platforms face elevated exposure risk.
· Detection opportunities exist through monitoring Office application network activity and abnormal document rendering behavior.
· Rapid weaponization is likely because document-based exploitation chains historically transition quickly into phishing campaigns after disclosure.
S3 – Risk Drivers
· Widespread enterprise reliance on Microsoft Office productivity software.
· Frequent document sharing through email attachments and collaboration platforms.
· User trust in documents received from partners, vendors, or internal sources.
· Embedded MSHTML rendering capabilities within Office document processing workflows.
· Security bypass mechanisms capable of circumventing Mark-of-the-Web trust boundaries.
· Phishing campaigns designed to exploit user interaction with attachments.
· Difficulty distinguishing malicious HTML rendering behavior from legitimate document content.
S4 – Executive Risk Summary
· The vulnerabilities introduce a phishing-based initial access risk affecting widely deployed enterprise productivity software.
Threat Classification
· Document-based exploitation
· Phishing-based initial access
Primary Risk
· Execution of attacker-controlled HTML or script content when malicious Office documents are opened or previewed.
Exploit Vector
· Phishing emails delivering crafted Office documents containing embedded HTML or web-rendered content.
Operational Impact
· Credential harvesting
· Malware delivery and staging
· Initial foothold for ransomware or intrusion campaigns
· Lateral movement following credential compromise
Attack Surface
· Microsoft Office document preview and editing workflows
· Email attachment handling systems
· Collaboration platforms used for document exchange
S5 – Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
For organizations affected by CVE-2026-21514 and CVE-2026-21513, the primary financial exposure arises from investigation of phishing-delivered malicious Office documents, validation of enterprise endpoint environment integrity, and remediation of potential credential compromise following document-based exploitation attempts.
· Low-end total cost: $180,000 – $520,000
(limited phishing campaign exposure requiring endpoint validation and targeted credential resets)
· Typical expected range: $520,000 – $1.8M
(enterprise phishing investigation, credential rotation, endpoint validation, and extended monitoring)
· Upper-bound realistic scenarios: $1.8M – $4.6M
(confirmed enterprise credential compromise requiring incident response engagement, endpoint rebuilds, and expanded security monitoring)
S5A – Key Cost Drivers
· Enterprise-wide credential reset across email, identity, and collaboration platforms
· Scope of endpoint investigation across employee workstations and document handling systems
· Duration and scale of incident response investigation and forensic analysis
· Operational disruption caused by credential resets and endpoint validation activities
· Expansion of email security monitoring and detection engineering following remediation
S6 – Bottom Line for Executives
For most organizations, CVE-2026-21514 and CVE-2026-21513 become operationally significant when phishing campaigns successfully deliver malicious Office documents to enterprise users and bypass document trust protections.
Financial and operational exposure typically arises from credential compromise investigation, endpoint validation, incident response engagement, and confirmation that attackers did not establish persistence within enterprise environments.
Management priorities should focus on the following actions.
· Deploy Microsoft security updates addressing CVE-2026-21514 and CVE-2026-21513
· Strengthen email attachment inspection and sandboxing controls
· Monitor Office application behavior for abnormal network connections or scripting activity
· Investigate credential access anomalies associated with phishing attempts
S7 – Board-Level Takeaway
CVE-2026-21514 and CVE-2026-21513 represent governance risks associated with enterprise productivity software widely used across corporate environments. Exploitation of document trust boundary bypass vulnerabilities can transform routine email attachments into entry points for broader intrusion activity.
Board oversight should ensure that organizations maintain the following governance controls.
· Accelerated patch management for enterprise productivity platforms
· Secure handling and inspection of externally received documents
· Continuous monitoring of credential access and endpoint behavior
· Governance controls addressing enterprise phishing resilience
S7A – Executive Decision Trigger
Executive escalation should occur if investigation confirms the following conditions.
· Evidence that malicious Office documents bypassed enterprise security controls
· Enterprise user credentials accessed or harvested through phishing infrastructure
· Office applications spawning abnormal scripting or external network activity
· Detection of malware staging or command-and-control activity linked to document execution
S8 – Priority Level and Response Window
Priority Level
· High – Security bypass enabling phishing-driven enterprise initial access
Response Window
· Immediate remediation recommended
Operational Context
· CVE-2026-21514 and CVE-2026-21513 affect Microsoft Office document handling mechanisms responsible for enforcing trust boundaries on externally sourced files
· Document trust boundary bypass vulnerabilities historically transition rapidly into active phishing exploitation campaigns following disclosure
· Enterprise environments relying heavily on Office document workflows face increased exposure when users frequently interact with externally sourced attachments
Exposure-Based Response Window
· Internet-facing email environments receiving external documents: remediate immediately within 24 hours
· Internal enterprise document workflows: remediate within 48 hours
· Restricted environments with attachment sandboxing and document isolation: remediate within 72 hours
Immediate Defensive Priorities
· Apply Microsoft security updates addressing CVE-2026-21514 and CVE-2026-21513
· Enable advanced email attachment sandboxing and detonation capabilities
· Monitor Office process network activity and script execution telemetry
· Investigate suspicious document behavior associated with recent phishing activity
S9 – Why This Matters Now
Enterprise reliance on Microsoft Office document workflows creates a significant operational attack surface when document trust boundary protections fail. CVE-2026-21514 and CVE-2026-21513 allow crafted Office documents to bypass Mark-of-the-Web and Protected View safeguards, enabling attacker-controlled HTML content to execute through the MSHTML rendering engine.
Document trust boundary bypass vulnerabilities historically transition quickly into phishing exploitation campaigns because attackers can weaponize common file types already trusted by enterprise users. Unlike macro-based attacks that often trigger visible security warnings, this vulnerability chain enables malicious content to execute in contexts where users may not immediately recognize suspicious behavior.
For organizations with high volumes of email attachments and external document collaboration, the combination of document rendering exploitation and phishing delivery increases the likelihood of credential harvesting, malware staging, or broader intrusion activity.
S10 – What We Don’t Yet Know
· Whether large-scale phishing campaigns exploiting CVE-2026-21514 and CVE-2026-21513 are already active in the wild
· Whether exploitation chains will incorporate credential harvesting infrastructure or malware delivery frameworks
· Whether threat actors will combine the vulnerability chain with additional browser or scripting exploitation techniques
· Whether targeted campaigns will focus on high-value sectors such as finance, government, or critical infrastructure
· Whether exploit kits or automated document weaponization tools will incorporate this vulnerability chain
S11 – Exploit Conditions Snapshot
Required Conditions
· Target users receive a malicious Microsoft Office document through email or collaboration platform delivery
· The document contains embedded HTML content rendered through the MSHTML engine
· Office document trust protections are bypassed through the chained exploitation of CVE-2026-21514 and CVE-2026-21513
User Interaction Requirement
· User opens or previews the malicious document
Execution Context
· HTML or script content executes through the MSHTML rendering engine embedded within Microsoft Office
Likely Initial Payload Objectives
· Credential harvesting through phishing infrastructure
· Malware download or staging through external URLs
· Establishment of attacker footholds for follow-on intrusion activity
S12 – Realistic Exploit Scenario
A threat actor distributes phishing emails containing weaponized Office documents disguised as invoices, procurement documents, or shared collaboration files. When a recipient opens or previews the document, embedded HTML content is rendered through the MSHTML engine, bypassing Mark-of-the-Web protections through the chained exploitation of CVE-2026-21514 and CVE-2026-21513.
The malicious content loads attacker-controlled infrastructure that may present credential harvesting forms or initiate malware download activity. If credentials are captured, the attacker may attempt authentication against enterprise identity services or cloud platforms. Alternatively, malware staged through the document may establish persistence within the endpoint environment, enabling reconnaissance, lateral movement, or ransomware preparation.
S13 – Today’s Hunt Focus
Signal 1 – Office Process Initiating External Network Connections
· Telemetry: Office application processes such as WINWORD.EXE, EXCEL.EXE, or POWERPNT.EXE initiating outbound HTTP or HTTPS connections
· Why It Matters: Office applications normally perform limited direct external web communication during document rendering
Signal 2 – Office Spawning Script or Browser Processes
· Telemetry: Office processes spawning scripting interpreters or browser-related processes such as powershell.exe, cmd.exe, or msedgewebview2.exe
· Why It Matters: Document rendering exploitation chains often trigger script execution during payload delivery
Signal 3 – Suspicious Document Rendering Activity
· Telemetry: Office documents triggering abnormal HTML rendering activity through the MSHTML engine
· Why It Matters: MSHTML-based document rendering activity may indicate exploitation attempts involving embedded web content
S14 – Sectors / Countries Affected
Confirmed sector-specific targeting associated with CVE-2026-21514 and CVE-2026-21513 has not been publicly attributed at this time. Vulnerabilities affecting Microsoft Office document security and the MSHTML rendering framework historically create elevated exposure across organizations that routinely process externally sourced documents.
Industries that rely heavily on document exchange through email, collaboration platforms, or shared file repositories represent the most exposed operational environments.
· Financial services organizations processing invoices, financial records, or procurement documentation
· Government and public-sector agencies exchanging administrative or policy documentation
· Legal and professional services firms distributing contracts and client documents
· Manufacturing and supply-chain organizations exchanging procurement documentation
· Technology and consulting firms collaborating through externally shared documents
Geographic targeting has not been confirmed. Because Microsoft Office deployments are globally distributed, potential exposure should be considered global in scope.
S15 – First Activity
Public disclosure associated with these vulnerabilities began in February 2026 following vendor advisory publication and vulnerability database indexing.
· CVE-2026-21514: February 2026
· CVE-2026-21513: February 2026
S16 – Last Activity
The most recent authoritative activity corresponds with the March 2026 Microsoft security update rollout, during which remediation updates and associated detection coverage were released.
· CVE-2026-21514: March 2026
· CVE-2026-21513: March 2026
S17 – CVE Details
CVE-2026-21514 and CVE-2026-21513 represent security feature bypass vulnerabilities affecting Microsoft Office document handling and the MSHTML rendering framework used by Windows and Office components.
CVE-2026-21514
· Vulnerability Type: Security feature bypass
· Component: Microsoft Office Word document security enforcement
· Weakness: CWE-807 – Reliance on Untrusted Inputs in a Security Decision
· Description: A crafted document may cause Microsoft Word to rely on untrusted input when making a security decision, allowing attackers to bypass built-in document security protections.
CVE-2026-21513
· Vulnerability Type: Security feature bypass
· Component: MSHTML framework used by Windows and Office components
· Weakness: CWE-693 – Protection Mechanism Failure
· Description: A protection mechanism failure in the Microsoft MSHTML framework allows an attacker to bypass a security feature over a network when a user interacts with specially crafted content.
Together these vulnerabilities create a document-based exploitation path capable of weakening built-in Office document protection mechanisms when malicious files are opened.
S18 – CVSS, CWE, KEV, Nessus, EPSS
CVSS
· CVSS v3.1 CVE-2026-21514: 7.8 (High)
· CVSS v3.1 CVE-2026-21513: 8.8 (High)
CWE
· CVE-2026-21514: CWE-807 – Reliance on Untrusted Inputs in a Security Decision
· CVE-2026-21513: CWE-693 – Protection Mechanism Failure
CISA Known Exploited Vulnerabilities Catalog
· CVE-2026-21514: Listed in KEV catalog
· CVE-2026-21513: Listed in KEV catalog
Nessus / Tenable Plugin Coverage
Tenable provides plugin identifiers associated with Microsoft security updates that address these vulnerabilities.
CVE-2026-21514
· 298975
CVE-2026-21513
· 298563
· 298562
· 298558
· 298556
· 298555
· 298554
· 298553
· 298552
· 298551
· 298549
· 298548
EPSS
· CVE-2026-21514: Not known at this time
· CVE-2026-21513: Not known at this time
S19 – Exploit Status
CVE-2026-21514 and CVE-2026-21513 are listed in the CISA Known Exploited Vulnerabilities catalog, confirming that exploitation of these vulnerabilities has been observed in the wild.
Successful exploitation requires user interaction with malicious content, typically through the opening of a crafted Office document or related document-delivery mechanism that triggers the underlying security bypass conditions.
· Exploitation has been observed in the wild and requires user interaction with a crafted Office document
· The vulnerabilities weaken document security protections designed to restrict unsafe content execution
· Attackers may chain the bypass conditions with additional payload delivery mechanisms
Because both vulnerabilities appear in the KEV catalog, unpatched environments remain exposed to document-based initial access attempts and should be prioritized for remediation.
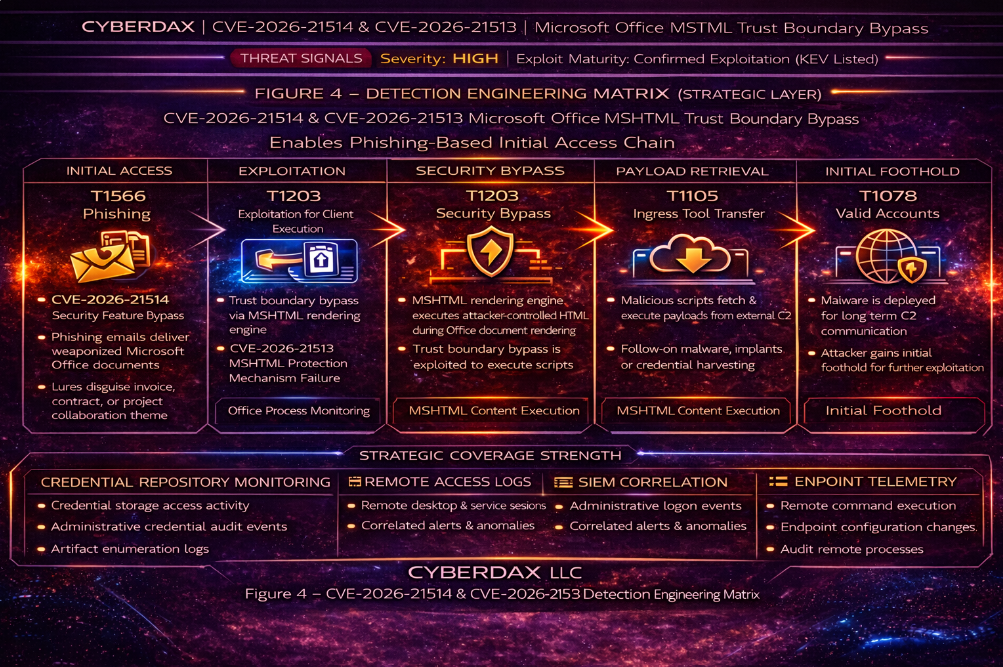
S20 – MITRE ATT&CK Chain Flow Mapping
The exploitation pathway associated with CVE-2026-21514 and CVE-2026-21513 maps to several MITRE ATT&CK techniques commonly observed in document-delivered intrusion campaigns. These vulnerabilities enable adversaries to distribute crafted Office documents that trigger a security feature bypass during document rendering, allowing malicious content execution following user interaction.
The observed attack pathway aligns with the following ATT&CK techniques:
· T1566 – Phishing
· T1204 – User Execution
· T1203 – Exploitation for Client Execution
· T1059 – Command and Scripting Interpreter
· T1105 – Ingress Tool Transfer
These techniques represent the common progression from document delivery through client-side exploitation and follow-on payload staging.
[Figure 3 Placeholder – MITRE ATT&CK Chain Flow Chart]
S21 – Stage-Based TTPs
Initial Access
T1566 – Phishing
Attackers distribute crafted Office documents through phishing emails or document-sharing platforms. The malicious attachment serves as the delivery mechanism for triggering the vulnerability chain.
Execution
T1204 – User Execution
Successful exploitation requires the victim to open or interact with the crafted Office document.
T1203 – Exploitation for Client Execution
The document triggers a security feature bypass within Microsoft Office or the MSHTML framework, enabling attacker-controlled content execution.
Post-Execution Activity
T1059 – Command and Scripting Interpreter
Following exploitation, malicious scripts or embedded content may execute to establish attacker control or initiate follow-on activity.
Payload Retrieval
T1105 – Ingress Tool Transfer
Attackers may retrieve secondary payloads or tooling from external infrastructure following successful document execution.
S22 – Malware and SHA256
No malware families have been publicly attributed to exploitation campaigns leveraging CVE-2026-21514 or CVE-2026-21513 at the time of reporting.
· Malware family attribution: Not known at this time
· Associated SHA256 indicators: Not known at this time
Document-based exploitation frequently acts as an initial access mechanism. Threat actors may embed scripts, credential harvesting infrastructure, or external payload retrieval mechanisms within crafted documents to deliver secondary tooling after exploitation.
S23 – Behavior and Log Artifacts
Successful exploitation may produce observable behaviors within endpoint telemetry and network logs associated with abnormal document execution activity.
Potential behavioral indicators include:
· Microsoft Office processes initiating unexpected outbound network connections
· Office applications spawning browser rendering or WebView components
· Execution of external content or script components during document rendering
· Office processes spawning unexpected child processes
· Outbound network traffic immediately following document opening
Common process lineage indicators may include:
· WINWORD.EXE spawning powershell.exe
· WINWORD.EXE spawning mshta.exe
· WINWORD.EXE spawning cmd.exe
· Office processes spawning command-line utilities or scripting interpreters
Security telemetry sources capable of capturing these artifacts include:
· Endpoint detection and response telemetry
· Windows event logs
· Proxy or network telemetry
· Email gateway security logs
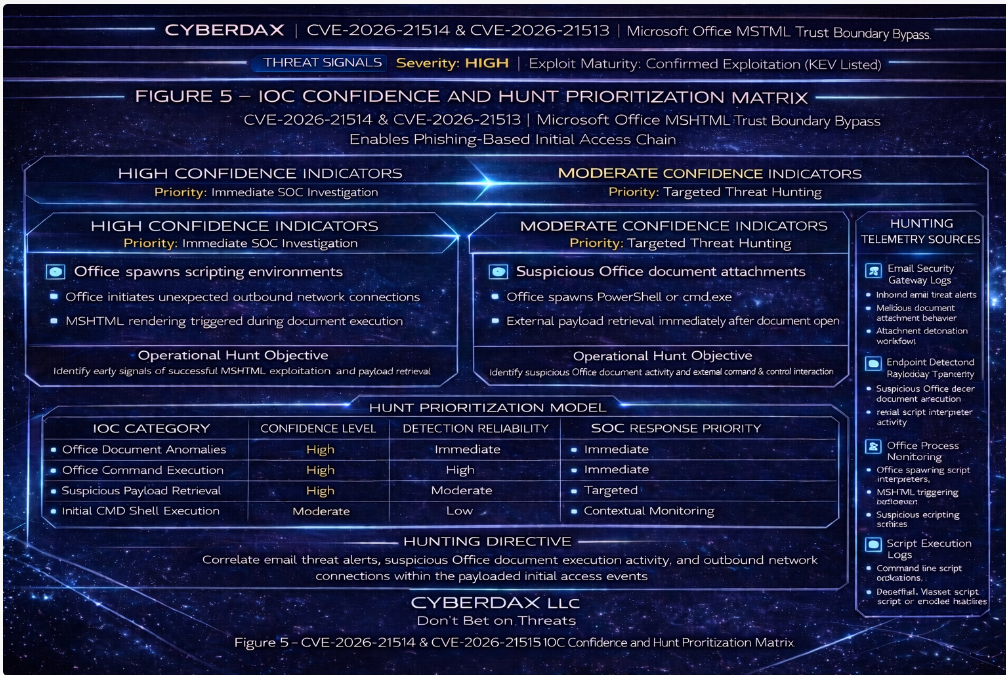
S24 – IOC Confidence and Hunt Prioritization
High Confidence Indicators
· Office processes spawning unexpected child processes following document execution
· Office applications spawning scripting interpreters such as powershell.exe or mshta.exe
· Outbound network connections immediately following document opening
Moderate Confidence Indicators
· Unexpected Office application network communications
· MSHTML-related execution activity triggered during document rendering
Low Confidence Indicators
· Standard Office process execution without additional suspicious behavior
· SOC teams should prioritize investigation of document-driven execution chains involving Microsoft Office processes when combined with suspicious child process creation or outbound network activity.
S25 – Detection Signals Layer
The following detection signals represent telemetry patterns commonly associated with document-based exploitation involving Microsoft Office applications and the MSHTML framework. These signals should be prioritized for monitoring across endpoint detection platforms, email security gateways, and network inspection systems.
Primary detection signals
· Office applications initiating outbound network connections immediately following document execution
· Office processes spawning scripting interpreters such as powershell.exe, mshta.exe, or wscript.exe
· Office processes spawning unexpected child processes including cmd.exe or rundll32.exe
· Office processes triggering execution of embedded or external content during document rendering
Secondary detection signals
· Suspicious document attachments originating from external senders
· Office document execution followed by immediate DNS or HTTP requests to external infrastructure
· Unusual MSHTML-related execution activity triggered during document rendering
These signals represent early-stage indicators of document-delivered intrusion activity and should be incorporated into proactive monitoring and threat hunting workflows.
S26 – Detection Coverage Matrix
The following coverage mapping aligns telemetry sources with the attack stages identified in the MITRE ATT&CK chain described earlier in the report.
Initial access – phishing delivery
· Email security gateways
· Attachment sandboxing systems
· Secure email filtering platforms
User execution – document interaction
· Endpoint detection and response telemetry
· Windows process creation logging
· Application behavior monitoring
Client-side exploitation – Office and MSHTML execution
· Endpoint telemetry capturing Office process lineage
· Application behavior monitoring systems
· Windows event logging for abnormal application activity
Command and script execution
· PowerShell logging and script block logging
· Endpoint telemetry monitoring abnormal child processes
· SIEM correlation of suspicious process relationships
Payload retrieval
· Network proxy logs
· DNS telemetry monitoring
· Firewall and network traffic inspection systems
These telemetry sources provide layered visibility across the attack lifecycle and enable defenders to identify exploitation attempts as they progress through the intrusion chain.
S27 – Detection Engineering Matrix (Operational Rule Layer)
This section defines operational detection opportunities derived from the MITRE ATT&CK techniques identified earlier in the report. These detection points represent the behavioral patterns that detection engineering rules will monitor across security platforms.
Initial access detection opportunities
· Identification of suspicious Office document attachments originating from external senders
· Attachment sandbox analysis detecting abnormal Office document behavior
Execution detection opportunities
· Monitoring Office applications spawning scripting interpreters or command-line utilities
· Detection of abnormal process lineage relationships involving Office applications
Client exploitation detection opportunities
· Monitoring abnormal execution behavior triggered during Office document rendering
· Detection of unexpected MSHTML-related execution activity
Command and script execution detection opportunities
· Monitoring PowerShell execution initiated by Office processes
· Detection of script interpreter execution immediately following document interaction
Payload retrieval detection opportunities
· Detection of outbound HTTP or DNS traffic triggered immediately after document execution
· Monitoring suspicious external network connections originating from Office processes
These detection engineering opportunities form the foundation for the system-specific detection rules defined in the subsequent sections of this report.
S28 – SOC Investigation Pivot Fields
Security operations teams investigating potential exploitation attempts associated with CVE-2026-21514 and CVE-2026-21513 should prioritize telemetry fields that enable rapid correlation of document execution activity, suspicious process lineage, and potential follow-on payload retrieval.
These pivot fields provide analysts with structured investigation entry points across endpoint, network, email, and file telemetry sources. Effective use of these fields enables analysts to reconstruct the full execution chain from document delivery through potential attacker command execution or payload staging.
Endpoint process investigation pivots
· process.parent.name – Identify Office parent processes such as WINWORD.EXE, EXCEL.EXE, POWERPNT.EXE, or OUTLOOK.EXE
· process.name – Detect suspicious child processes including powershell.exe, cmd.exe, mshta.exe, wscript.exe, cscript.exe, rundll32.exe, and regsvr32.exe
· process.command_line – Identify encoded commands, external download references, or suspicious script execution parameters
· process.executable.path – Confirm execution paths for suspicious interpreters or system utilities
· process.hash.sha256 – Correlate suspicious binaries or scripts with threat intelligence repositories and sandbox results
Host and user context investigation pivots
· host.name – Identify affected endpoints executing suspicious document activity
· host.ip – Correlate network activity with the originating host system
· user.name – Determine which user account initiated document execution
· user.domain – Identify potential compromised or targeted domain accounts
· logon.session.id – Correlate process execution with specific user sessions
Network telemetry investigation pivots
· network.destination.ip – Identify outbound connections triggered immediately after document execution
· network.destination.domain – Detect connections to suspicious or newly observed external infrastructure
· network.protocol – Identify HTTP, HTTPS, or DNS traffic associated with payload retrieval activity
· network.http.uri – Detect retrieval of suspicious script or executable content
· dns.query.name – Identify suspicious domain resolution activity initiated by endpoint processes
Email telemetry investigation pivots
· email.sender.address – Identify suspicious external senders distributing malicious documents
· email.sender.domain – Detect spoofed or newly registered domains used in phishing campaigns
· email.attachment.name – Identify Office document attachments associated with exploitation attempts
· email.attachment.hash.sha256 – Correlate attachment hashes with threat intelligence sources
· email.message.subject – Identify phishing campaigns using recurring lure themes
File and document artifact pivots
· file.name – Identify suspicious document filenames associated with phishing activity
· file.path – Confirm document execution locations within user directories or temporary paths
· file.hash.sha256 – Correlate suspicious documents with threat intelligence feeds or sandbox outputs
· file.extension – Identify potentially weaponized Office document formats or script-enabled files
SOC analysts should correlate these pivot fields across multiple telemetry sources to reconstruct attacker behavior and identify related activity across affected systems.
Using structured investigation pivots enables security teams to rapidly expand investigations, identify additional affected hosts, and determine whether document-based exploitation attempts have progressed into follow-on attacker activity.
S29 – Ultra-Tuned Detection Engineering Rules
Suricata
Rule Title
Suspicious External Script Retrieval With Office Exploitation Follow-On Potential
Detection Intent
Detect outbound retrieval of script or payload content from external infrastructure that may represent second-stage activity following malicious document execution.
Purpose
This rule is intended to surface suspicious network retrieval behavior commonly seen after document-based exploitation, including script and LOLBin-driven fetch activity.
Tuning Explanation
Suricata cannot observe Office parent-child process lineage, so this rule is intentionally positioned as a supporting network detection rather than a primary exploit detector. Tuning should exclude trusted enterprise update services, approved cloud storage platforms, sanctioned collaboration domains, and known software distribution infrastructure. Analysts should correlate hits with endpoint telemetry showing Office execution, suspicious child processes, or immediate post-document network activity.
System Ready Rule Code
alert http $HOME_NET any -> $EXTERNAL_NET any (
msg:"Possible post-document exploit external script retrieval";
flow:to_server,established;
http.method; content:"GET";
http.uri; pcre:"/\.(ps1|vbs|js|jse|hta|sct|wsf)(\?|$)/Ui";
http.host; content:!"microsoft.com"; nocase;
http.host; content:!"office.com"; nocase;
http.host; content:!"office.net"; nocase;
http.host; content:!"sharepoint.com"; nocase;
http.host; content:!"onedrive.com"; nocase;
classtype:trojan-activity;
sid:420001;
rev:4;
)
SentinelOne
Rule Title
Office Process Spawning Suspicious Interpreter or LOLBin
Detection Intent
Detect Microsoft Office processes spawning scripting engines or living-off-the-land binaries associated with document exploitation chains.
Purpose
Malicious Office documents commonly launch scripting interpreters or LOLBins to download payloads, execute commands, or stage additional attacker tooling.
Tuning Explanation
The rule focuses on suspicious Office parent-child relationships combined with command-line indicators suggesting script execution or payload retrieval. Analysts should prioritize alerts where the child process establishes network connections, writes a new script or executable, or launches additional processes.
System Ready Rule Logic
EventType = "Process Creation"
AND ParentProcessName IN ("WINWORD.EXE","EXCEL.EXE","POWERPNT.EXE","OUTLOOK.EXE")
AND ProcessName IN ("powershell.exe","pwsh.exe","cmd.exe","mshta.exe","wscript.exe","cscript.exe","rundll32.exe","regsvr32.exe")
AND CommandLine CONTAINS ("http","https","download","invoke","iex","FromBase64String","-enc","-encodedcommand")
Elastic
Rule Title
Office Parent Launching Suspicious Interpreter With Network Indicators
Detection Intent
Detect suspicious Office process lineage where interpreters or command shells are launched with command-line indicators consistent with payload retrieval or script execution.
Purpose
Office applications rarely spawn interpreters under normal operation. When combined with network-related command-line indicators, this behavior may signal document exploitation activity.
Tuning Explanation
Detection correlates Office parent-child process relationships with suspicious command-line arguments. Exclusions should be implemented for legitimate document automation tools.
System Ready Rule Code
process.parent.name: ("WINWORD.EXE","EXCEL.EXE","POWERPNT.EXE","OUTLOOK.EXE")
AND process.name: ("powershell.exe","cmd.exe","mshta.exe","wscript.exe","cscript.exe","rundll32.exe","regsvr32.exe")
AND process.command_line: ("http" OR "https" OR "download" OR "invoke" OR "iex")
Sigma
Rule Title
Office Application Launching Suspicious Interpreter With Network Indicators
Detection Intent
Detect Office applications spawning interpreters or system utilities with command-line patterns associated with script execution or payload retrieval.
Purpose
Malicious documents frequently trigger Office applications to launch scripting engines or command interpreters used to retrieve attacker tooling.
Tuning Explanation
Detection logic focuses on suspicious process lineage combined with network-related command-line indicators. Environment-specific automation processes should be allow-listed.
Sigma Rule
title: Office Application Launching Suspicious Interpreter With Network Indicators
logsource:
category: process_creation
product: windows
detection:
parent:
ParentImage:
- '*\WINWORD.EXE'
- '*\EXCEL.EXE'
- '*\POWERPNT.EXE'
- '*\OUTLOOK.EXE'
child:
Image:
- '*\powershell.exe'
- '*\cmd.exe'
- '*\mshta.exe'
- '*\wscript.exe'
- '*\cscript.exe'
- '*\rundll32.exe'
- '*\regsvr32.exe'
cli:
CommandLine:
- '*http*'
- '*download*'
- '*invoke*'
- '*iex*'
condition: parent and child and cli
level: high
YARA
Rule Title
Supplemental Office Document Script Reference Triage Rule
Detection Intent
Support retrospective scanning and sandbox triage for documents containing suspicious references to interpreters or script execution utilities.
Purpose
This rule is not intended to serve as a primary detector for exploitation. It is designed to help analysts quickly flag suspicious documents for deeper behavioral review.
Tuning Explanation
Because this attack chain is behavior-driven and document content may be obfuscated, YARA should be treated as a low-confidence enrichment control. Hits should be correlated with endpoint telemetry, sandbox detonation results, attachment provenance, and process lineage before escalation.
YARA Rule
rule Supplemental_Office_Document_Script_Reference_Triage
{
meta:
description = "Supplemental triage rule for Office documents referencing scripting interpreters"
author = "CyberDax"
confidence = "low"
use_case = "retrospective triage and sandbox enrichment"
strings:
$ps = "powershell" ascii wide
$hta = "mshta" ascii wide
$cmd = "cmd.exe" ascii wide
$wscript = "wscript" ascii wide
$cscript = "cscript" ascii wide
$enc = "FromBase64String" ascii wide
condition:
2 of ($*)
}
S30 – SIEM Correlation Logic
Security information and event management platforms should correlate endpoint telemetry, Office application behavior, and network activity to identify document-driven exploitation attempts associated with CVE-2026-21514 and CVE-2026-21513. Document-based exploitation typically produces a short sequence of related behaviors rather than a single definitive indicator. Effective detection therefore relies on correlating multiple events occurring within a limited time window following document execution.
Correlation models should combine signals from endpoint telemetry, network monitoring systems, and email security platforms to reconstruct the execution chain beginning with document delivery and extending through potential payload retrieval or script execution.
Correlation Pattern 1
Document Execution Followed by Suspicious Child Process
· Microsoft Office process execution (WINWORD.EXE, EXCEL.EXE, POWERPNT.EXE, or OUTLOOK.EXE)
· Followed within five minutes by creation of a scripting interpreter or command shell such as powershell.exe, cmd.exe, mshta.exe, wscript.exe, or cscript.exe
· Followed by outbound network activity originating from the spawned process
Operational Interpretation
This sequence strongly indicates document-triggered execution consistent with exploitation chains that launch interpreters to retrieve attacker-controlled payloads.
Correlation Pattern 2
Office Execution Followed by External Content Retrieval
· Microsoft Office document execution event
· Followed within two minutes by outbound HTTP or HTTPS connections from the same endpoint
· Followed by DNS resolution for previously unseen external domains
Operational Interpretation
Document exploitation chains frequently retrieve external content or secondary payloads shortly after document interaction. This sequence helps identify early-stage payload retrieval activity.
Correlation Pattern 3
Suspicious Email Attachment Followed by Endpoint Activity
· Email security logs showing delivery of an Office document attachment from an external sender
· Followed within thirty minutes by execution of the same document on an endpoint system
· Followed by suspicious process creation or abnormal outbound network activity
Operational Interpretation
This sequence links phishing delivery telemetry with endpoint behavior to identify successful execution of malicious document attachments.
Correlation Pattern 4
Office Execution Followed by Encoded Script Activity
· Microsoft Office process execution event
· Followed by command-line activity containing encoded or obfuscated script parameters
· Followed by interpreter execution spawning additional processes or initiating outbound network communication
Operational Interpretation
Encoded script execution initiated by Office applications frequently indicates post-exploitation activity associated with document-based attack chains.
Correlation Outcome Guidance
Security operations teams should treat correlation sequences combining Office execution, interpreter launch activity, and outbound network communication as high-confidence exploitation indicators requiring immediate investigation.
Medium-confidence correlations include Office process execution followed by abnormal network connections or suspicious command-line parameters. These events may indicate early-stage exploitation attempts.
Low-confidence correlations include isolated Office network activity without interpreter execution. These events should be monitored for escalation but do not independently confirm exploitation.
S31 – Delivery Methods
Threat actors leveraging CVE-2026-21514 and CVE-2026-21513 typically rely on document-based delivery mechanisms that require user interaction to initiate the exploitation chain. These vulnerabilities enable attackers to bypass certain document security protections and execute follow-on actions when a crafted Microsoft Office document is opened.
The most common delivery vector involves phishing campaigns distributing weaponized Office documents designed to exploit weaknesses in document security enforcement or MSHTML rendering behavior.
Common delivery methods include:
· Phishing emails containing malicious Office document attachments designed to appear as legitimate business communications
· Spear-phishing campaigns targeting specific individuals or departments such as finance, procurement, or human resources
· Cloud file-sharing invitations distributing weaponized documents through platforms such as OneDrive or SharePoint
· Malicious document links embedded within email messages that redirect users to externally hosted weaponized files
· Compromised collaboration platforms or shared workspaces distributing malicious documents through trusted communication channels
· Social engineering campaigns encouraging victims to download or open externally hosted Office documents
In many campaigns the malicious document is disguised as routine business content such as invoices, financial reports, purchase orders, or project documentation. The document may contain embedded content or external references that trigger the security bypass conditions required for exploitation.
Attackers frequently combine these delivery techniques with social engineering tactics intended to increase the likelihood that recipients will interact with the document. Once opened, the malicious document may initiate execution activity that leads to script execution, payload retrieval, or additional attacker-controlled actions on the endpoint.
Organizations should treat document-based phishing campaigns as a primary initial access vector for vulnerabilities affecting Office document processing components.
S32 – Exposure Conditions
Successful exploitation of CVE-2026-21514 and CVE-2026-21513 requires specific environmental conditions within enterprise environments. The vulnerabilities enable a document trust-boundary bypass affecting Microsoft Office document handling and the MSHTML rendering framework. Exploitation typically occurs when malicious Office documents containing attacker-controlled HTML content are delivered to users and executed during normal document interaction.
Network Exposure Factors
· Enterprise email systems receiving externally sourced Microsoft Office document attachments
· Collaboration platforms or shared file repositories allowing document exchange with external organizations
· Cloud storage platforms distributing Office documents through shared links
· Endpoint systems capable of retrieving external web content referenced within Office documents during rendering
Infrastructure Exposure Factors
· Microsoft Office deployments using MSHTML-based document rendering components
· Endpoint systems where externally sourced documents can execute embedded HTML or web content
· Environments where Office applications are permitted to initiate outbound network connections during document rendering
Credential Exposure Factors
· Enterprise environments where phishing campaigns may target user credentials through document-delivered content
· Office documents capable of loading attacker-controlled web infrastructure designed to harvest authentication information
· User sessions authenticated to enterprise identity services during document interaction
Monitoring Gaps
· Limited endpoint telemetry capturing Office process execution and child process creation
· Lack of monitoring for outbound network connections initiated by Office applications
· Insufficient correlation between email attachment delivery and endpoint document execution activity
Enterprise Risk Amplifiers
· Large enterprise environments processing high volumes of externally sourced documents
· Business operations relying heavily on document exchange through email or collaboration platforms
· Departments frequently interacting with externally provided documents such as finance, procurement, legal, or administration
These exposure conditions increase the likelihood that malicious Office documents can successfully trigger the vulnerability chain and initiate follow-on attacker activity within enterprise environments. Organizations that combine high volumes of external document exchange with limited monitoring of Office execution behavior face the greatest operational risk.
S33 – Exploit Preconditions
Successful exploitation of CVE-2026-21514 and CVE-2026-21513 requires several technical and operational conditions to exist within the target environment. These vulnerabilities enable a chained security feature bypass affecting Microsoft Office document security enforcement and the MSHTML rendering framework. Exploitation occurs when a crafted Office document triggers a trust-boundary bypass that allows attacker-controlled content to execute during document rendering.
Unlike remote service exploitation, this attack chain depends on user interaction with a malicious document and the ability of the document to load external or embedded content through the MSHTML engine.
Document Preconditions
· A malicious Microsoft Office document containing attacker-controlled HTML or embedded web content
· Document structure capable of triggering the security feature bypass conditions associated with CVE-2026-21514 and CVE-2026-21513
· Document delivery through email attachments, shared collaboration platforms, or externally hosted files
User Interaction Preconditions
· A user opens or previews the malicious Office document
· The document is processed by Microsoft Office applications such as Word, Excel, or PowerPoint
· Document rendering occurs within the MSHTML engine or related document processing components
Endpoint Execution Preconditions
· Microsoft Office installed on the endpoint system
· The endpoint system capable of rendering embedded HTML or web-based content within Office documents
· Local security controls do not prevent execution of document-initiated content or associated scripting activity
Network Preconditions
· The endpoint system can establish outbound network connections to external infrastructure
· External domains or URLs referenced within the malicious document are reachable during document rendering
· Network security controls do not block retrieval of externally hosted web content or payloads
Operational Preconditions
· Security monitoring systems do not immediately detect or block the document execution chain
· Email security controls or attachment sandboxing systems do not intercept the malicious document prior to delivery
· Endpoint protection controls allow Office applications to initiate follow-on processes or network activity
When these preconditions are satisfied, attackers can trigger the document trust-boundary bypass and execute follow-on actions such as loading attacker-controlled web content, retrieving secondary payloads, or initiating credential harvesting activity. The presence of these conditions increases the likelihood that malicious document delivery campaigns can successfully establish an initial foothold within enterprise environments.
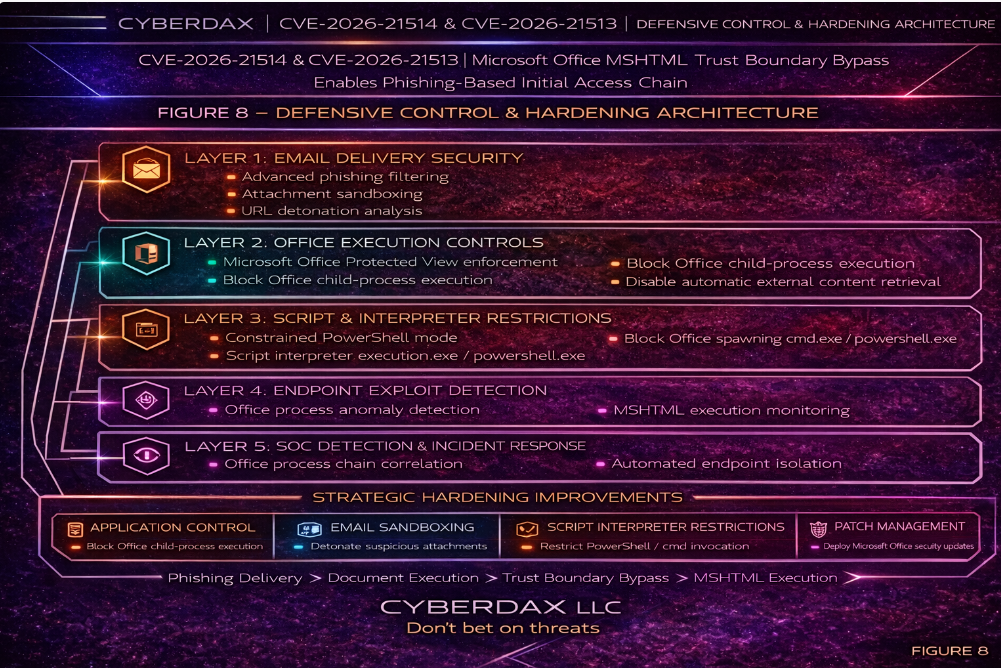
S34 – Defensive Controls and Hardening Recommendations
Exploitation chains involving CVE-2026-21514 and CVE-2026-21513 rely on malicious Microsoft Office documents that bypass document trust protections and execute attacker-controlled content through the MSHTML rendering engine. Defensive controls should focus on preventing malicious document delivery, detecting abnormal Office application behavior, and restricting attacker-controlled payload retrieval following document interaction.
Recommended defensive controls include the following.
Email security controls
· Implement attachment sandboxing capable of detonating Microsoft Office documents in isolated analysis environments prior to user delivery
· Enforce phishing detection policies designed to identify malicious Office document attachments and externally hosted document links
· Monitor newly registered or suspicious domains associated with phishing campaigns distributing weaponized documents
· Enable email gateway inspection of embedded links or externally referenced content contained within Office documents
Endpoint security controls
· Deploy endpoint detection and response platforms capable of monitoring Microsoft Office process lineage and abnormal child process creation
· Monitor Office applications spawning scripting interpreters such as powershell.exe, cmd.exe, mshta.exe, wscript.exe, cscript.exe, rundll32.exe, or regsvr32.exe
· Enable PowerShell logging, command-line telemetry collection, and interpreter execution monitoring across enterprise endpoints
· Monitor for abnormal outbound network connections initiated by Office processes immediately following document execution
Network security controls
· Monitor DNS telemetry for suspicious domain resolution activity triggered shortly after document interaction
· Inspect outbound network traffic originating from internal endpoints for script retrieval or payload staging behavior
· Implement proxy monitoring capable of identifying suspicious HTTP or HTTPS requests initiated by Office applications
· Correlate outbound network connections with document execution events observed on endpoint systems
Document security controls
· Disable automatic retrieval of external content within Microsoft Office documents where operationally feasible
· Enforce Protected View and Mark-of-the-Web policies for externally sourced documents
· Restrict automatic execution of embedded scripts or macros within Office documents
· Apply document isolation or application control policies for high-risk document environments
User awareness and operational controls
· Train employees to recognize suspicious document attachments and phishing messages
· Encourage reporting of suspicious documents to security teams for rapid analysis and containment
· Reinforce secure document-handling procedures across departments frequently targeted by phishing campaigns
· Conduct periodic phishing simulation exercises to improve organizational resilience against document-based attacks
Organizations implementing these defensive controls significantly reduce the likelihood that malicious Office documents will successfully trigger exploitation activity associated with CVE-2026-21514 and CVE-2026-21513 while improving visibility into document-driven intrusion attempts.
S35 – Strategic Defensive Improvements
Organizations defending against exploitation chains involving CVE-2026-21514 and CVE-2026-21513 should implement strategic defensive improvements focused on reducing the effectiveness of document-delivered phishing campaigns and limiting the ability of malicious Office documents to trigger follow-on execution activity. These vulnerabilities exploit weaknesses in document trust enforcement and MSHTML rendering behavior, making layered controls across email security, endpoint monitoring, and document execution environments essential.
Strategic improvements should prioritize the prevention of malicious document delivery, rapid detection of abnormal Office application behavior, and containment of post-execution activity initiated by attacker-controlled content.
Recommended strategic defensive improvements include the following.
· Expand enterprise attachment sandboxing capabilities capable of detonating Microsoft Office documents in isolated analysis environments prior to user delivery
· Deploy advanced email security gateways capable of detecting phishing campaigns distributing weaponized Office attachments or externally hosted documents
· Implement dynamic attachment detonation and behavioral analysis systems capable of observing Office document execution behavior and embedded web content retrieval
· Implement endpoint telemetry collection capable of monitoring Microsoft Office process lineage relationships and abnormal child process execution
· Enforce PowerShell script block logging and command-line telemetry collection across enterprise endpoints
· Expand DNS and proxy monitoring capabilities to identify suspicious outbound connections initiated by Office applications
· Integrate threat intelligence feeds capable of identifying attacker infrastructure associated with phishing campaigns and malicious document distribution
· Monitor MSHTML rendering activity triggered during Microsoft Office document execution where telemetry visibility is available
· Implement detection engineering rules specifically monitoring Office applications spawning scripting interpreters or command-line utilities
Organizations should also strengthen document execution controls to reduce the likelihood that externally sourced documents can trigger malicious content execution.
Recommended document security improvements include the following.
· Disable automatic retrieval of external content within Microsoft Office documents where operationally feasible
· Enforce enterprise macro security policies restricting automatic execution of embedded scripts or macros
· Implement application control policies capable of restricting unauthorized interpreter execution on endpoint systems
· Restrict Office application execution in high-risk environments using application allow-listing or virtualization controls
· Configure Protected View and Mark-of-the-Web enforcement policies to ensure externally sourced documents open within restricted execution environments
Strategic improvements should also include continued investment in detection engineering capabilities capable of identifying document-driven intrusion activity across enterprise environments. Security operations teams should maintain detection rules capable of identifying abnormal Office application behavior, suspicious interpreter execution, MSHTML rendering activity, and outbound network connections initiated shortly after document interaction.
Organizations that combine improved email security controls, enhanced endpoint telemetry visibility, stronger document security policies, and proactive detection engineering significantly reduce the likelihood that malicious Office documents will successfully trigger exploitation activity within enterprise environments.
S36 – Defensive Control and Hardening Architecture
Defending against document-based exploitation campaigns involving CVE-2026-21514 and CVE-2026-21513 requires a layered defensive architecture capable of preventing malicious document delivery, detecting abnormal Office application behavior, and restricting attacker-controlled payload retrieval. These vulnerabilities weaken document trust enforcement and enable MSHTML-rendered content to execute during Office document processing, increasing risk in enterprise environments that routinely exchange external documents.
Effective defensive architecture should combine controls across email security infrastructure, endpoint detection platforms, network monitoring systems, and document execution safeguards. A defense-in-depth model ensures that malicious documents can be blocked, detected, or contained across multiple stages of the attack lifecycle.
Recommended defensive controls include the following.
Email security controls
· Attachment sandboxing and detonation environments for Microsoft Office documents prior to user delivery
· Advanced phishing detection and filtering policies capable of identifying malicious document attachments or externally hosted files
· Domain reputation analysis and monitoring for newly registered domains associated with phishing infrastructure
· Email gateway inspection of embedded links or externally referenced document resources
Endpoint security controls
· Endpoint detection and response platforms capable of monitoring Microsoft Office process lineage and abnormal child process creation
· Application behavior monitoring focused on Office applications interacting with embedded or externally retrieved web content
· Script execution monitoring including PowerShell logging, interpreter activity tracking, and command-line telemetry collection
· Monitoring MSHTML rendering activity triggered during document execution where telemetry visibility is available
Network security controls
· DNS monitoring and anomaly detection capable of identifying suspicious domain resolution activity following document execution
· Proxy inspection of outbound network traffic originating from internal systems
· Firewall monitoring for abnormal outbound connections initiated by Office applications
· Network telemetry correlation identifying payload retrieval activity shortly after document interaction
Document security controls
· Disable automatic retrieval of external content within Office documents where operationally feasible
· Enforce macro security policies and document trust settings across enterprise environments
· Configure Protected View and Mark-of-the-Web enforcement policies for externally sourced documents
· Restrict Office application execution in high-risk environments using application control or virtualization policies
User awareness and operational controls
· Train employees to recognize suspicious document attachments and phishing attempts
· Reinforce secure document-handling practices across departments frequently targeted by phishing campaigns
· Encourage reporting of suspicious documents to security teams for rapid analysis and containment
A layered defensive architecture significantly reduces the likelihood that malicious Office documents will successfully trigger exploitation activity while improving enterprise visibility into document-driven intrusion attempts and phishing-based initial access campaigns.
S37 – Seven-Day Response Plan
Vulnerabilities listed in the Known Exploited Vulnerabilities catalog should be treated as high-priority remediation items due to confirmed exploitation activity in the wild. The following response plan outlines recommended defensive actions during the first seven days following identification of exposure within the enterprise environment.
Immediate actions (Day 0–1)
· Identify vulnerable Microsoft Office and Windows systems across the enterprise environment
· Validate Microsoft Office version inventory across managed endpoints
· Notify security operations teams of the exploitation risk associated with malicious document attachments
· Prioritize patch deployment for systems exposed to external email, document collaboration platforms, or shared file workflows
· Initiate monitoring for suspicious Office process activity involving interpreters or unexpected child processes
Short-term response (Day 2–3)
· Deploy vendor security updates addressing CVE-2026-21514 and CVE-2026-21513 across affected endpoints
· Review email gateway policies to strengthen attachment inspection and sandbox detonation of Office documents
· Initiate threat hunting focused on Office parent-child process relationships and abnormal outbound network connections following document execution
· Review endpoint telemetry for evidence of script interpreter execution initiated by Office applications
Operational monitoring (Day 4–5)
· Monitor endpoint detection platforms for suspicious Office execution chains
· Investigate outbound network activity initiated shortly after document interaction
· Review email telemetry to identify potential phishing campaigns distributing malicious documents
· Validate that suspicious document artifacts are submitted to sandbox or malware analysis systems
Validation and hardening (Day 6–7)
· Confirm patch deployment coverage across all vulnerable endpoints
· Validate remediation timelines meet CISA KEV remediation expectations
· Review and tune endpoint detection rules monitoring Office application behavior and interpreter execution
· Document lessons learned and update internal detection playbooks for document-based exploitation activity
This response timeline enables organizations to rapidly mitigate exploitation risk while maintaining visibility into potential intrusion activity associated with malicious document campaigns.
S38 – Post-Incident Insights and Recommendations
Analysis of CVE-2026-21514 and CVE-2026-21513 highlights several operational and strategic lessons for organizations defending document-driven enterprise environments. Vulnerabilities affecting widely deployed productivity platforms frequently become high-value targets for phishing campaigns because they can be combined with social engineering to initiate reliable initial access attempts.
Several lessons emerge from this analysis.
· Vulnerabilities affecting commonly used enterprise productivity platforms can quickly become operationalized within phishing infrastructure following disclosure
· Threat actors often incorporate newly disclosed vulnerabilities into existing phishing toolkits and campaign templates, allowing rapid scaling of exploitation attempts
· Inclusion of these vulnerabilities in the Known Exploited Vulnerabilities catalog confirms active exploitation and increases the likelihood of continued targeting by opportunistic threat actors
· Document-based attacks that require user interaction remain highly effective because enterprise workflows frequently involve opening externally received documents
· Malicious documents distributed through legitimate communication channels such as corporate email and collaboration platforms can bypass traditional perimeter security controls
These insights reinforce the importance of treating document-driven exploitation as a persistent operational risk rather than a single vulnerability remediation task.
Organizations should implement defensive practices that reduce the likelihood of successful document-based intrusion attempts.
Recommended security actions include the following.
· Prioritize rapid patch deployment for vulnerabilities affecting widely deployed productivity software platforms
· Strengthen email security controls capable of identifying and sandboxing suspicious document attachments and externally hosted document links
· Expand endpoint monitoring focused on abnormal Microsoft Office process behavior and interpreter execution initiated by document activity
· Implement user awareness programs that improve phishing recognition and reinforce safe handling of externally received documents
· Maintain proactive threat hunting focused on document execution chains, script interpreter activity, and outbound network connections following document interaction
Organizations that combine rapid vulnerability remediation with layered detection capabilities and strong user awareness programs significantly reduce the effectiveness of phishing campaigns attempting to exploit document-based vulnerabilities.
S39 – Attack Economics and Organizational Impact Model
Document-processing vulnerabilities affecting widely deployed enterprise productivity platforms create a highly asymmetric economic model between attackers and defenders. When exploitation can be triggered through routine business workflows such as opening an email attachment, the cost of attack preparation remains relatively low while the potential operational impact for organizations can become significant.
CVE-2026-21514 and CVE-2026-21513 enable attackers to bypass Microsoft Office document trust protections and execute attacker-controlled content through the MSHTML rendering framework. Because Microsoft Office remains one of the most widely deployed enterprise productivity platforms globally, this vulnerability chain provides attackers with a scalable entry point capable of targeting large numbers of organizations through phishing campaigns.
From an attacker perspective, document-based exploitation offers several economic advantages. Malicious documents can be distributed through inexpensive phishing infrastructure and require minimal technical complexity compared to exploitation of hardened network services. Once weaponized, a single document template can be reused across large campaigns targeting thousands of potential victims.
The operational return on investment for attackers increases when document exploitation chains enable follow-on activity such as credential harvesting, malware staging, or command execution within enterprise environments. Even if only a small percentage of targeted users interact with malicious documents, attackers may still achieve successful initial access into enterprise networks.
For organizations, the defensive cost profile is significantly different. Investigation of suspected document-based exploitation typically requires analysis across multiple security layers including email systems, endpoint telemetry, and network monitoring infrastructure. Security teams must determine whether malicious documents were delivered, whether endpoints executed embedded content, and whether follow-on attacker activity occurred after document interaction.
If credential harvesting or payload delivery occurs, organizations may also incur additional operational costs associated with credential rotation, endpoint investigation, and incident response engagement. Large enterprise environments processing high volumes of documents must often perform extensive telemetry review to confirm that malicious document execution did not lead to broader compromise.
This economic imbalance reflects a recurring pattern in modern cyber operations: relatively low-cost phishing campaigns can generate disproportionate defensive cost and operational disruption when vulnerabilities affect widely deployed productivity platforms used in daily business workflows.
Organizations that reduce patch latency, implement attachment sandboxing, monitor Microsoft Office process behavior, and restrict abnormal script execution significantly decrease the operational return on investment for attackers attempting to exploit document-based vulnerabilities.
Figure 10 illustrates the economic lifecycle of document-driven exploitation campaigns, highlighting the relationship between low-cost phishing delivery infrastructure, scalable document weaponization techniques, and the investigative and remediation costs organizations incur when responding to potential document-based intrusion attempts.
S40 – References
Microsoft Security Response Center
CVE Record – CVE-2026-21514
· hxxps://msrc[.]microsoft[.]com/update-guide/vulnerability/CVE-2026-21514
CVE Record – CVE-2026-21513
· hxxps://msrc[.]microsoft[.]com/update-guide/vulnerability/CVE-2026-21513
National Institute of Standards and Technology (NVD)
CVE Record – CVE-2026-21514
· hxxps://nvd[.]nist[.]gov/vuln/detail/CVE-2026-21514
CVE Record – CVE-2026-21513
· hxxps://nvd[.]nist[.]gov/vuln/detail/CVE-2026-21513
Cybersecurity and Infrastructure Security Agency (CISA)
Known Exploited Vulnerabilities Catalog – CVE-2026-21514
· hxxps://www[.]cisa[.]gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-21514
Known Exploited Vulnerabilities Catalog – CVE-2026-21513
· hxxps://www[.]cisa[.]gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-21513
Tenable Security Research
Vulnerability Intelligence – CVE-2026-21514
· hxxps://www[.]tenable[.]com/cve/CVE-2026-21514/plugins
Vulnerability Intelligence – CVE-2026-21513
· hxxps://www[.]tenable[.]com/cve/CVE-2026-21513/plugins