CVE-2026-20045 Cisco Unified Communications Unauthenticated Remote Code Execution
BLUF
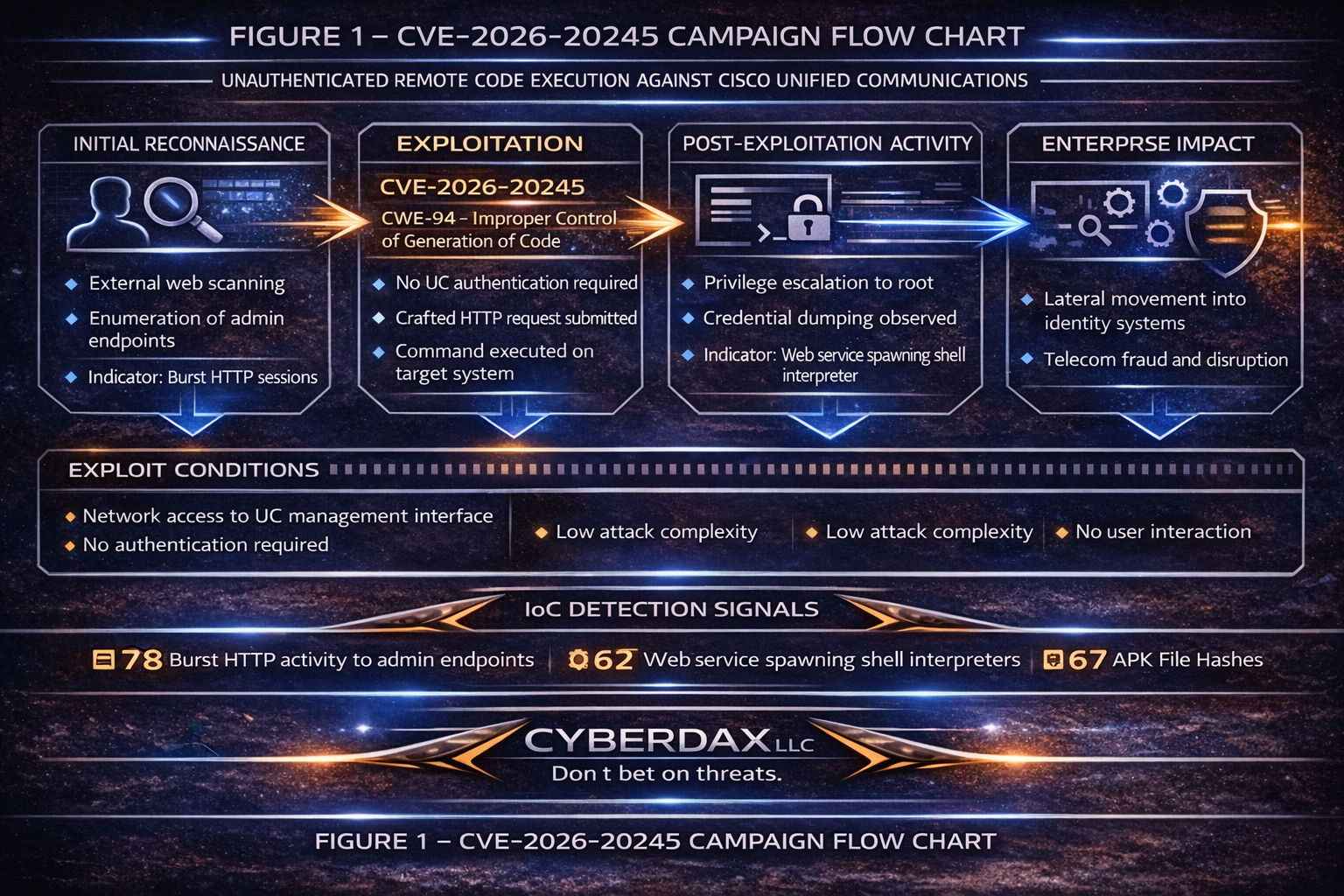
CVE-2026-20045 allows unauthenticated attackers to execute operating system commands via crafted HTTP requests targeting Cisco UC management interfaces.
Impact includes:
· Root-level system compromise
· Persistence establishment
· Credential harvesting
· Lateral movement into enterprise identity systems
· Telecom fraud
· Service disruption
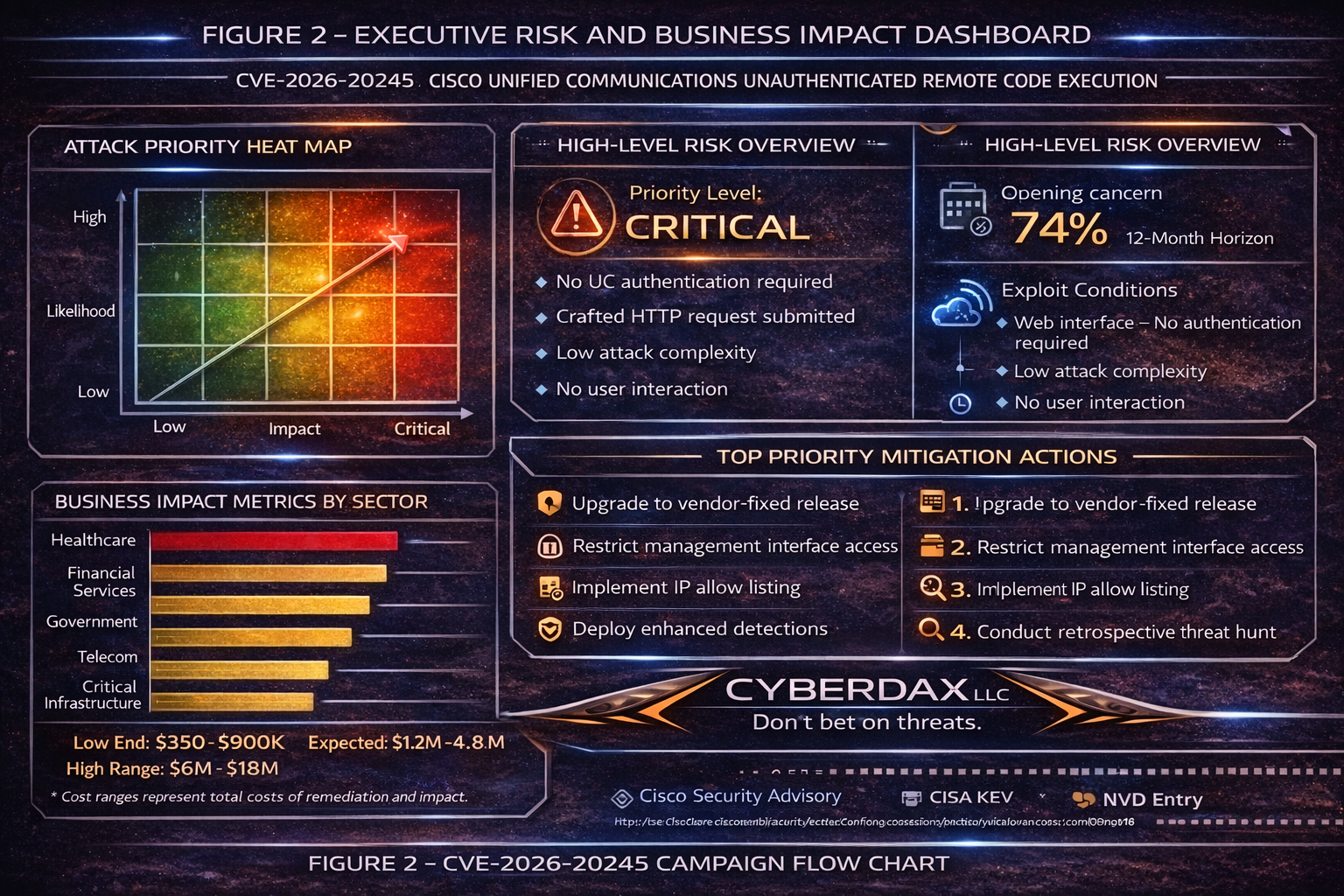
Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
“For organizations affected by exploitation of CVE-2026-20045 in Cisco Unified Communications environments, financial exposure will primarily depend on system criticality, duration of service disruption, and degree of lateral movement beyond voice infrastructure.”
· Low-end total cost: $350,000 – $900,000
o Isolated UC server compromise, rapid containment, no lateral spread
· Typical expected range: $1.2 million – $4.8 million
o Multi-system UC impact, limited credential exposure, short service disruption
· Upper-bound realistic scenarios: $6 million – $18 million
o Identity pivot, extended outage, regulatory review, fraud exposure
Key Cost Drivers
· Duration of voice and contact center downtime
· Extent of identity system integration with UC environment
· Need for enterprise-wide credential rotation
· Regulatory notification obligations triggered by data exposure
· Telecom fraud losses or call-routing manipulation
· Post-incident infrastructure hardening and segmentation upgrades
Bottom Line for Executives
For most mid-size to large organizations, exploitation of CVE-2026-20045 would likely result in $1 million to $5 million in total impact, primarily driven by business interruption rather than forensic costs.
Financial exposure increases if:
· Voice systems are tightly integrated with identity infrastructure
· Contact center operations are disrupted for multiple days
· Enterprise-wide credential rotation is required
This is fundamentally a resilience and continuity risk, not just a patching issue. Proactive remediation and access restriction are significantly less costly than recovery after compromise.
Priority Level
· Critical
Response Window
· Immediate if internet exposed
· Maximum 72 hours if internally restricted
Why This Matters Now
CVE-2026-20045 is actively exploited and listed in the CISA Known Exploited Vulnerabilities catalog.
The vulnerability enables:
· Unauthenticated remote command execution
· Direct operating system access
· Potential root-level compromise
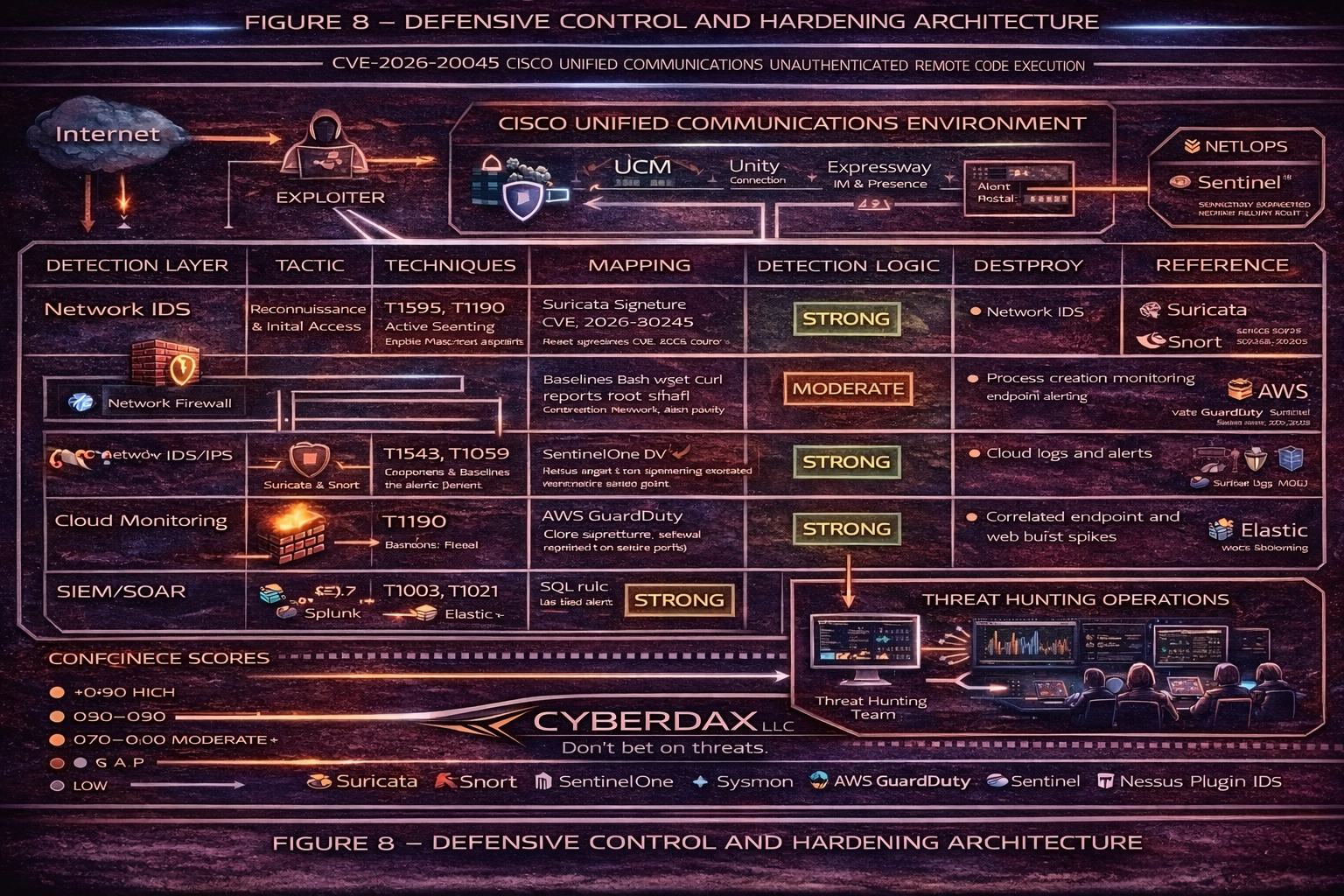
Unified Communications infrastructure commonly integrates with:
· Enterprise identity services
· Active Directory and LDAP
· Voicemail and contact center platforms
· Internal routing infrastructure
Compromise can therefore extend beyond service disruption into credential theft and enterprise pivoting.
Exploit Conditions Snapshot:
· Network access to web management interface
· No authentication required
· Low attack complexity
· No user interaction
Today’s Hunt Focus:
· Burst HTTP activity to administrative endpoints
· Web service spawning shell interpreters
· Unexpected privileged sessions
Sectors at Elevated Risk
· Healthcare
· Financial Services
· Government
· Telecommunications
· Critical Infrastructure
· Enterprise Contact Centers
Countries at Elevated Risk
· United States
· United Kingdom
· Germany
· France
· Canada
· Australia
First Activity
· January 21, 2026
Last Observed Activity
· Ongoing exploitation activity observed February 2026
Estimated Probability of Recurrence (12-Month Horizon)
Estimated Probability:
· 0.74
Confidence Level:
· High
Drivers:
· KEV inclusion
· Confirmed exploitation in the wild
· Broad enterprise deployment
· Low exploitation complexity
· Historical recurrence of UC remote code execution vulnerabilities
Vulnerability Overview
CVE:
· CVE-2026-20045
CWE:
· CWE-94 Improper Control of Generation of Code
Class:
· Unauthenticated Remote Code Execution
Description:
· Improper validation of HTTP parameters allows command injection
· Successful exploitation may allow privilege escalation to root
Workarounds:
· Not applicable at this time
CVSS Severity
CVSS:3.1
· (9.8) AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
Operational Severity Classification:
· Critical Infrastructure Service Compromise
Tenable ID
KEV Status
Is this listed in CISA Known Exploited Vulnerabilities
· Yes
Date Added
· January 21, 2026
What as the CISA Patch by Date
· February 11, 2026
Exploit Status
· Confirmed in the wild
Affected Products
· Cisco Unified Communications Manager
· Cisco Unified Communications Manager SME
· Cisco Unified Communications Manager IM and Presence
· Cisco Unity Connection
· Cisco Webex Calling Dedicated Instance
Patch and Remediation
· Upgrade to vendor-fixed releases
· Restrict management interface exposure
· Implement IP allow listing
· Rotate credentials if compromise suspected
· Conduct retrospective log review
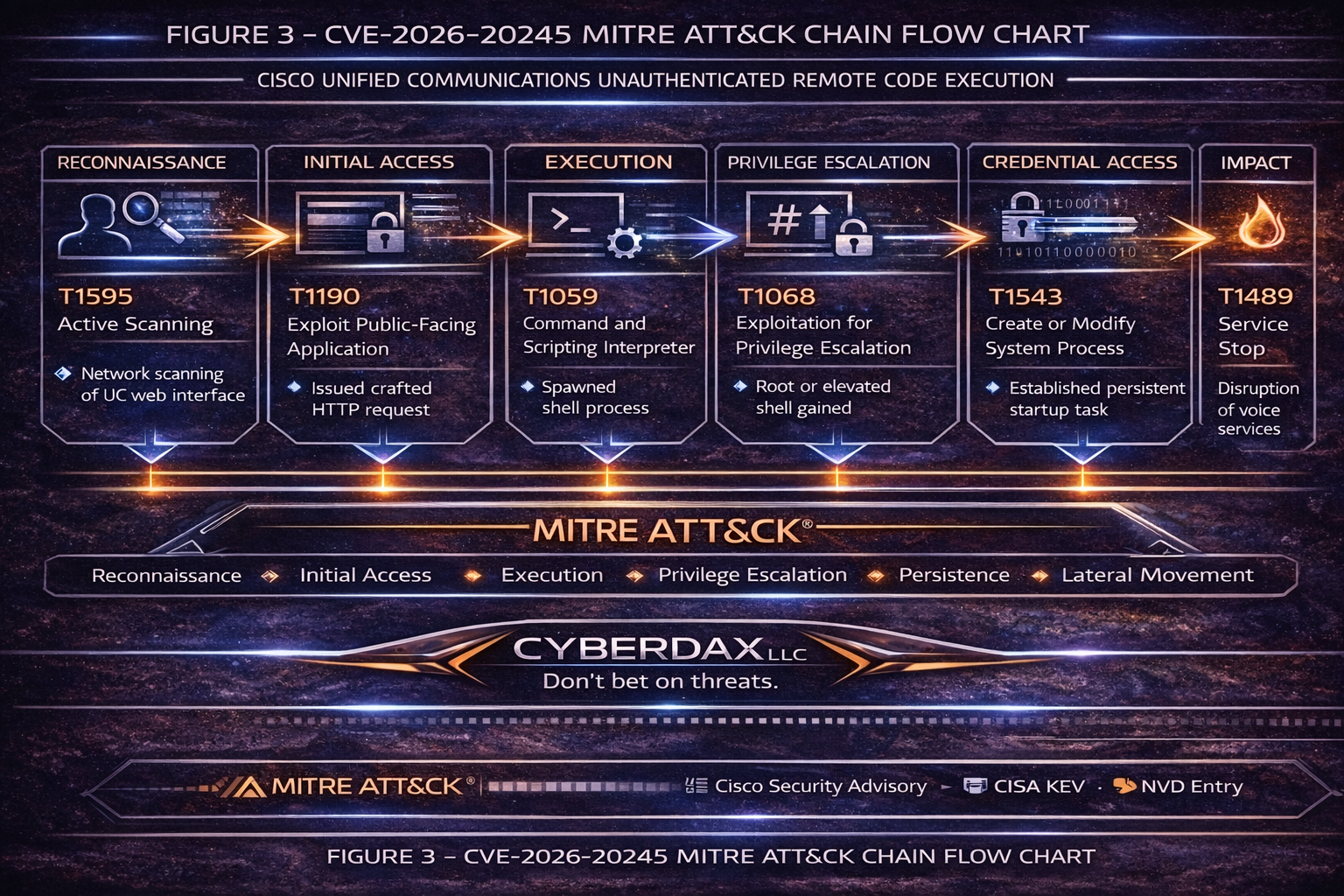
MITRE ATT&CK Mapping
Reconnaissance
· T1595 – Active Scanning
Initial Access
· T1190 – Exploit Public-Facing Application
Execution
· T1059 – Command and Scripting Interpreter
Privilege Escalation
· T1068 – Exploitation for Privilege Escalation
Persistence
· T1543 – Create or Modify System Process
Credential Access
· T1003 – OS Credential Dumping
Discovery
· T1082 – System Information Discovery
Lateral Movement
· T1021 – Remote Services
Impact
· T1489 – Service Stop
What We Don’t Yet Know
· Confirmed threat actor attribution
· Whether exploitation is opportunistic mass scanning or targeted campaigns
· Availability of stable exploit automation tooling
· Most common persistence mechanisms observed in real incidents
· Verified telecom fraud monetization tied directly to this CVE
· Confirmed lateral movement patterns into identity infrastructure
· Presence of repeatable secondary payload families
Analytical Confidence:
· Moderate
Reason:
· Exploitation confirmed
· Post-compromise tradecraft reporting remains limited
Stage-Based TTPs
Stage 1 – Reconnaissance
· Technique ID: T1595
· Observed Behavior: External scanning of UC administrative endpoints
Stage 2 – Initial Access
· Technique ID: T1190
· Observed Behavior: Crafted HTTP request triggering command injection
Stage 3 – Execution
· Technique ID: T1059
· Observed Behavior: Shell or interpreter spawned from web service process
Stage 4 – Privilege Escalation
· Technique ID: T1068
· Observed Behavior: Escalation to root or elevated system context
Stage 5 – Persistence
· Technique ID: T1543
· Observed Behavior: Service modification or startup task creation
Stage 6 – Credential Access
· Technique ID: T1003
· Observed Behavior: Attempted credential extraction
Stage 7 – Lateral Movement
· Technique ID: T1021
· Observed Behavior: Pivot via remote services
Stage 8 – Impact
· Technique ID: T1489
· Observed Behavior: Service disruption or call processing degradation
Delivery Method
Primary:
· Crafted HTTP request exploitation of the web-based management interface
Secondary:
· Not applicable at this time
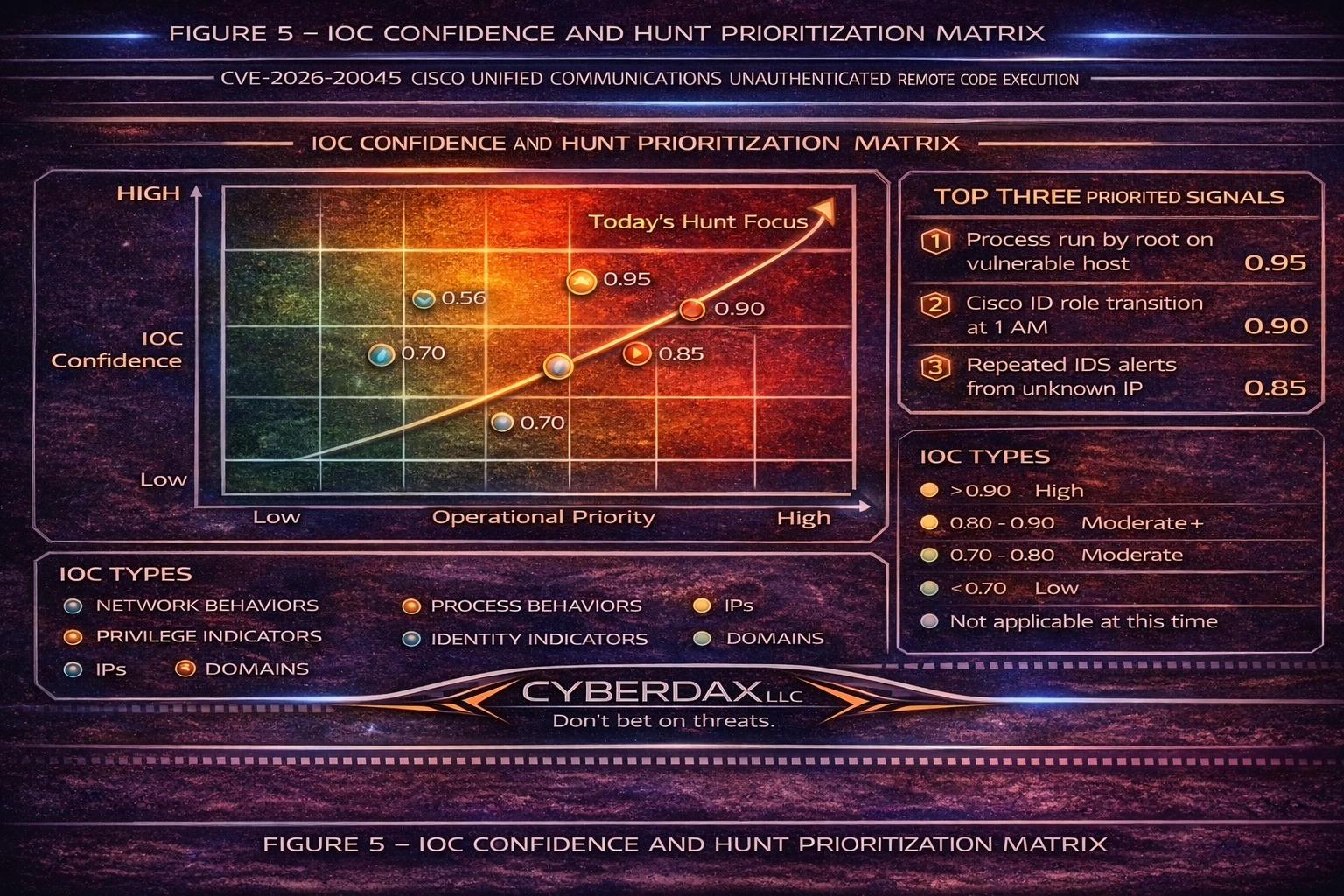
Composite IOC Reliability Score
IOC Confidence Blocks
Network Behavioral Indicators:
· Administrative endpoint request bursts
· Confidence Score: 0.70
Process Behavioral Indicators:
· Web service spawning shell binaries
· Confidence Score: 0.85
Privilege Escalation Indicators:
· Unexpected root sessions
· Confidence Score: 0.80
Static IP Indicators:
· Not applicable at this time
· Confidence Score: 0.20
Malware Hash Indicators:
· Not applicable at this time
· Confidence Score: 0.10
Malware and SHA256
· Not applicable at this time
Behavior and Log Artifacts
· Repeated HTTP POST requests to administrative paths
· Elevated error responses during burst activity
· Apache, nginx, tomcat, or httpd spawning shell interpreters
· Unexpected privileged sessions
· Service restarts outside approved maintenance windows
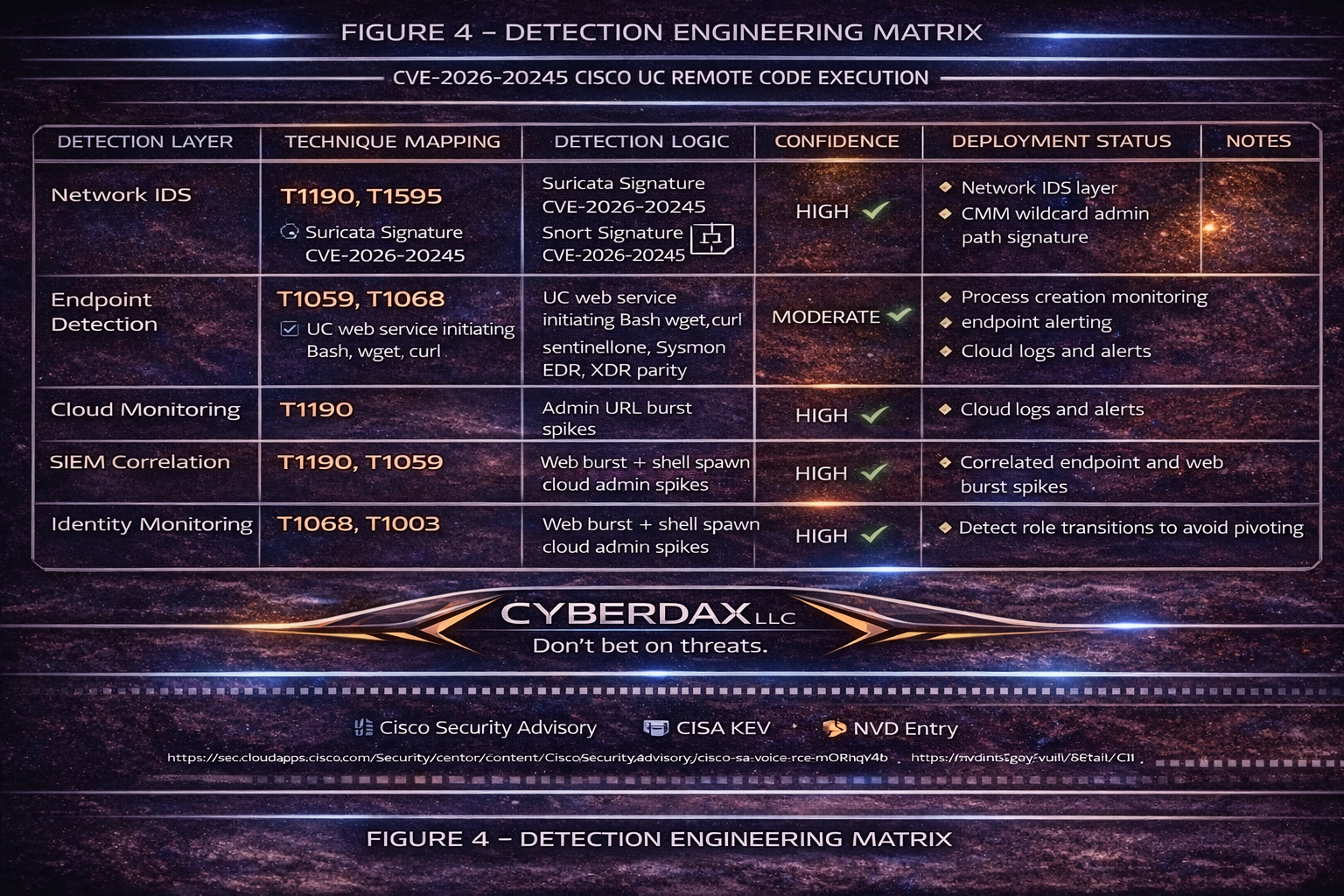
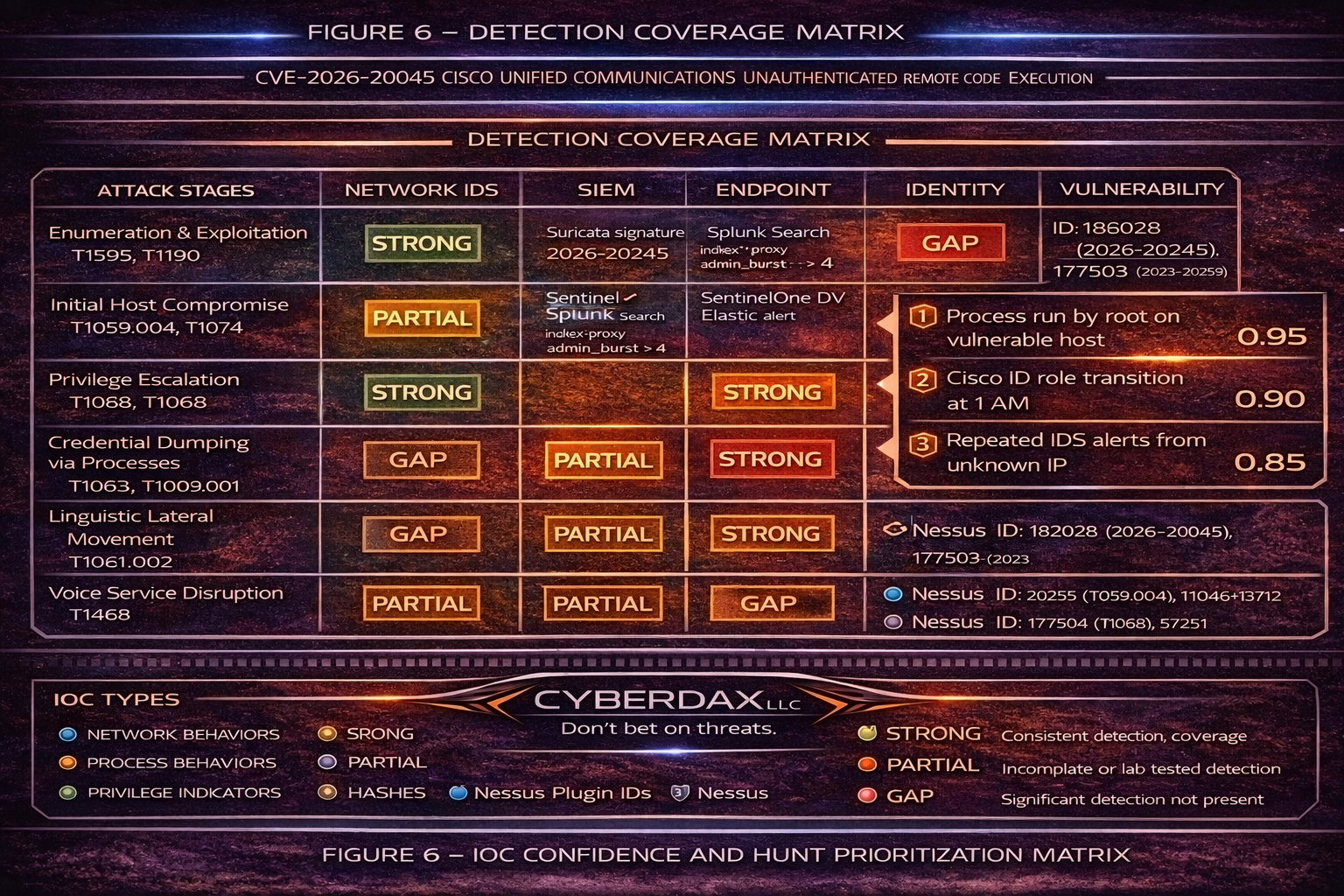
Detection Coverage Matrix
Network IDS Layer:
· Suricata signature coverage
· Snort signature coverage
· Coverage Confidence: High
Endpoint Layer:
· Process creation monitoring
· Privilege transition detection
· Coverage Confidence: Moderate
SIEM Correlation:
· HTTP burst correlated with shell execution
· Coverage Confidence: High
Identity Monitoring:
· Administrative role change detection
· Coverage Confidence: Moderate
Vulnerability Management:
· Version validation
· KEV-based prioritization
· Coverage Confidence: High
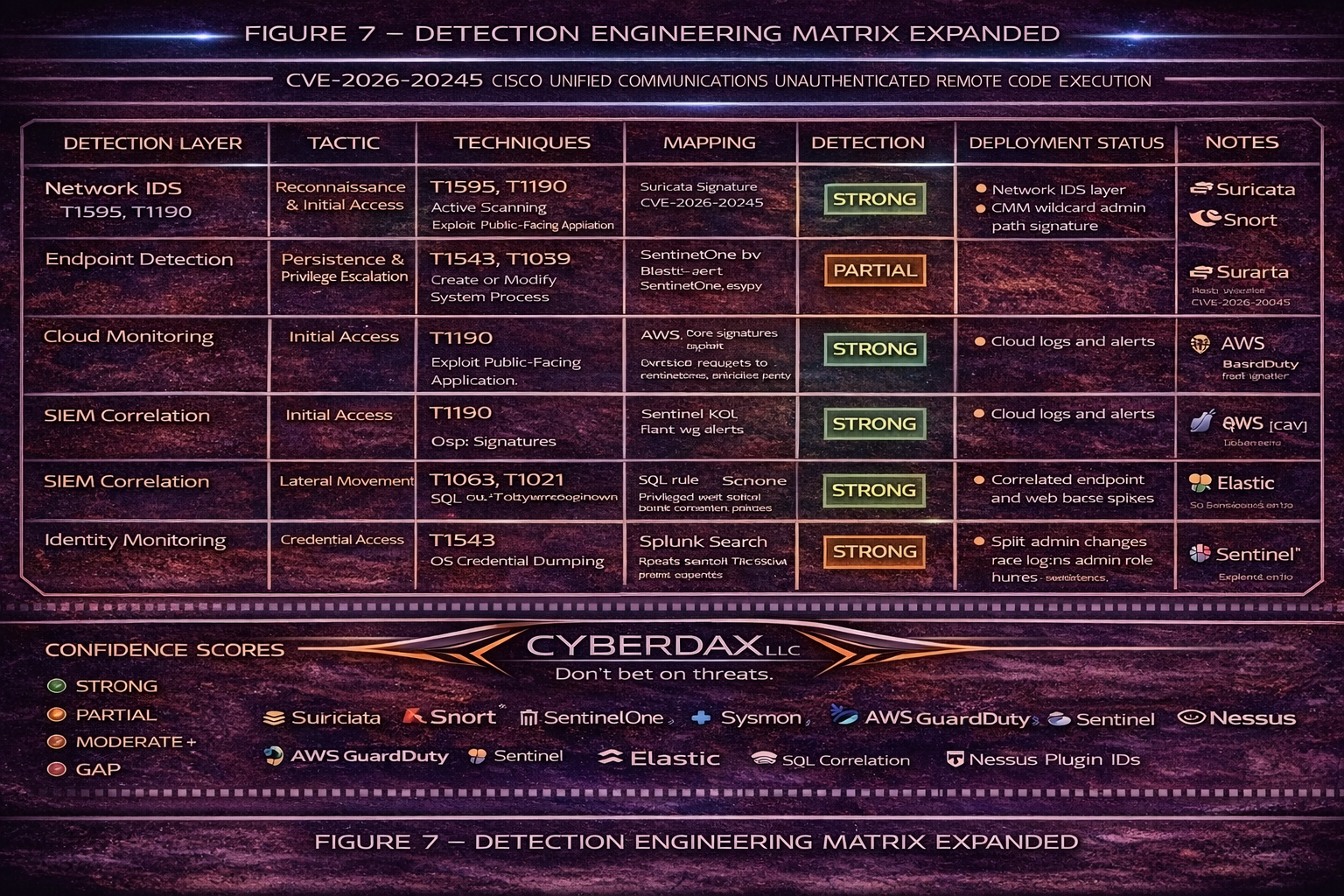
Detection Engineering Matrix
Network IDS and IPS Layer
· Coverage Objective
o Detect exploit scanning and exploitation attempts against UC administrative endpoints
· Primary MITRE ATT&CK Techniques
o T1595 – Active Scanning
o T1190 – Exploit Public-Facing Application
· Primary Signals
o HTTP request bursts to UC admin paths
o Anomalous URI patterns and parameter anomalies
o External source IPs targeting management endpoints
· Primary Detection Logic
o Suricata signature on UC admin paths with source-based thresholding
o Snort parity signature with equivalent thresholding
· Confidence Rating
o Strong
· Tuning Controls
o Restrict scope to known UC servers only
o Allow-list approved admin jump hosts and enterprise scanners
o Baseline request volumes by business hours and maintenance windows
· Output Destination
o SIEM alert stream and incident queue for correlation with host signals
SIEM Correlation Layer
· Coverage Objective
o Raise fidelity by correlating web-layer exploitation indicators with host process execution
· Primary MITRE ATT&CK Techniques
o T1190 – Exploit Public-Facing Application
o T1059 – Command and Scripting Interpreter
· Primary Signals
o Web endpoint burst followed by shell interpreter or retrieval tool execution on same host
o Timing correlation within a five-minute window
· Primary Detection Logic
o Correlation search joining web logs and process logs by host and time window
o Burst threshold tuned to environment baseline
· Confidence Rating
o Strong
· Tuning Controls
o Enforce host allow-list for UC systems
o Exclude planned maintenance and approved admin automation
o Escalate severity when process is root or when command line shows download and execute patterns
· Output Destination
o High-priority incident with enriched context and linked raw events
Endpoint and Process Telemetry Layer
· Coverage Objective
o Detect post-exploitation execution and privilege transitions
· Primary MITRE ATT&CK Techniques
o T1059 – Command and Scripting Interpreter
o T1068 – Exploitation for Privilege Escalation
o T1543 – Create or Modify System Process
· Primary Signals
o Web service parent process spawning shell interpreters
o Execution of curl, wget, python, perl from web parent lineage
o Unexpected privileged sessions outside change windows
· Primary Detection Logic
o SentinelOne Deep Visibility query for process lineage and tool execution
o Linux process creation monitoring where available
· Confidence Rating
o Partial to Strong depending on telemetry availability on UC platforms
· Tuning Controls
o Restrict to UC host group
o Exclude vendor update processes and approved scripts
o Tag root context execution as high severity
· Output Destination
o Endpoint alerting and SIEM correlation layer
Identity Monitoring Layer
· Coverage Objective
o Detect privilege abuse and identity pivoting following UC compromise
· Primary MITRE ATT&CK Techniques
o T1078 – Valid Accounts
o T1098 – Account Manipulation
· Primary Signals
o Unexpected privileged group changes
o New administrative sessions or role assignments following UC exploitation window
o Anomalous authentication from UC segments
· Primary Detection Logic
o Identity provider alerts for privileged group changes and admin sign-ins
o Correlate identity anomalies to UC host exploitation alerts
· Confidence Rating
o Moderate
· Tuning Controls
o Focus on privileged roles and tier-zero groups
o Apply short correlation windows after UC exploitation signals
o Require change-ticket validation for privileged modifications
· Output Destination
o Identity risk queue and SIEM for cross-domain correlation
Vulnerability Management Layer
· Coverage Objective
o Validate exposure and confirm remediation completion at scale
· Primary Reference Signals
o Nessus plugin detections mapped to affected UC products
o Patch status verification following remediation windows
· Primary Detection Logic
o Scheduled scans with plugin-based identification
o Exceptions only for approved compensating controls
· Confidence Rating
o Strong for exposure validation, Moderate for exploitation detection
· Required Nessus Plugin IDs
o 296364 – Cisco Unified Communications Manager remote code execution
o 296365 – Cisco Unified Communications Manager IM and Presence remote code execution
o 295030 – Cisco Unity Connection remote code execution
· Tuning Controls
o Separate internet-exposed scope from internal-only scope
o Require proof of management interface restriction if patch delay exists
o Re-scan within 24 to 72 hours post-change
· Output Destination
o Executive remediation dashboard and patch compliance reporting
Confidence and Operational Use
· Highest-fidelity detections
o SIEM correlation of admin endpoint bursts with host shell execution
o Web-layer threshold alerts scoped to UC servers and non-trusted sources
· Most common gaps
o Limited endpoint telemetry on UC appliances
o Incomplete process visibility for child process lineage
o Reduced identity correlation when UC is not well-segmented
· Priority operational action
o Treat correlated signals as incident-grade, not informational alerts
Suggested Rules
Suricata Rule
Title:
· Cisco UC Administrative Endpoint Exploitation Attempt
Purpose:
· Detect burst access to UC administrative endpoints consistent with exploitation
Tuning Explanation:
· Scope to UC hosts
· Whitelist approved admin IP ranges
· Adjust threshold after baseline analysis
Technique Mapping:
· T1190 – Exploit Public-Facing Application
· T1595 – Active Scanning
Detection Logic:
alert http $EXTERNAL_NET any -> $HOME_NET any (
msg:"CVE-2026-20045 Cisco UC exploitation attempt";
flow:to_server,established;
content:"/ccmadmin"; nocase;
threshold:type both, track by_src, count 5, seconds 60;
sid:202620045;
rev:13;
)
Snort Rule
Title:
· Cisco UC Administrative Endpoint Exploitation Attempt
Purpose:
· Provide signature parity in Snort deployments
Tuning Explanation:
· Align thresholds with Suricata baseline
· Exclude authorized scanning sources
Technique Mapping:
· T1190 – Exploit Public-Facing Application
· T1595 – Active Scanning
Detection Logic:
alert tcp $EXTERNAL_NET any -> $HOME_NET $HTTP_PORTS (
msg:"CVE-2026-20045 Cisco UC exploitation attempt";
flow:to_server,established;
content:"/ccmadmin"; http_uri; nocase;
detection_filter:track by_src, count 5, seconds 60;
sid:202620046;
rev:4;
)
SentinelOne Deep Visibility Rule
Title:
· UC Web Parent Shell Execution
Purpose:
· Detect post-exploitation shell execution
Tuning Explanation:
· Restrict to UC hosts
· Exclude maintenance windows
Technique Mapping:
· T1059 – Command and Scripting Interpreter
· T1068 – Exploitation for Privilege Escalation
Detection Logic:
ProcessName IN ("bash","sh","dash","curl","wget","python","perl")
AND ParentProcessName CONTAINS ("apache","nginx","tomcat","httpd")
Splunk Rule
Title:
· UC Administrative Burst Detection
Purpose:
· Identify abnormal request volume
Tuning Explanation:
· Baseline normal activity
· Exclude automation tools
Technique Mapping:
· T1190 – Exploit Public-Facing Application
Detection Logic:
index=web (uri_path="*admin*" OR uri_path="*ccmadmin*")
| stats count by src_ip
| where count > 20
Microsoft Sentinel KQL Rule
Title:
· Cisco UC Admin Endpoint Burst
Purpose:
· Detect high-rate administrative path access
Tuning Explanation:
· Filter to UC resources
· Adjust threshold per baseline
Technique Mapping:
· T1190 – Exploit Public-Facing Application
Detection Logic:
AzureDiagnostics
| where tostring(requestUri_s) has "admin"
| summarize count() by CallerIPAddress
| where count_ > 20
Elastic Rule
Title:
· UC Web Parent Spawning Shell
Purpose:
· Detect suspicious process lineage
Tuning Explanation:
· Apply only to UC hosts
Technique Mapping:
· T1059 – Command and Scripting Interpreter
Detection Logic:
process.parent.name : ("apache","nginx","tomcat","httpd") and
process.name : ("bash","sh","dash","curl","wget","python","perl")
SQL Correlation Rule
Title:
· Administrative Burst and Shell Correlation
Purpose:
· Correlate HTTP bursts with shell execution
Tuning Explanation:
· Five-minute correlation window
Technique Mapping:
· T1190 – Exploit Public-Facing Application
· T1059 – Command and Scripting Interpreter
Detection Logic:
SELECT *
FROM web_logs w
JOIN process_logs p
ON w.host = p.host
WHERE w.uri LIKE '%admin%'
AND p.process_name IN ('bash','sh','dash','curl','wget','python','perl')
AND w.event_time BETWEEN p.event_time - INTERVAL '5 minutes'
AND p.event_time;
Seven-Day Response Plan
Day 1:
· Inventory exposure
Day 2:
· Restrict access
Day 3:
· Patch systems
Day 4:
· Deploy detections
Day 5:
· Conduct retrospective hunt
Day 6:
· Rotate credentials
Day 7:
· Implement continuous KEV prioritization
References
Cisco Security Advisory
· hxxps://sec[.]cloudapps[.]cisco[.]com/security/center/content/CiscoSecurityAdvisory/cisco-sa-voice-rce-mORhqY4b
NVD Entry
· hxxps://nvd[.]nist[.]gov/vuln/detail/CVE-2026-20045
CISA KEV
· hxxps://www[.]cisa[.]gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-20045
MITRE ATT&CK
· hxxps://attack[.]mitre[.]org
Tenable
· hxxps://www[.]tenable[.]com/cve/CVE-2026-20045/plugins