Mercenary Akula (UAC-0050) Judicial-Themed Spearphishing Deploying RMS Against a European Financial Institution
BLUF
UAC-0050, also known as Mercenary Akula, conducted a targeted spearphishing campaign against a European financial institution on February 9, 2026. The actor impersonated a Ukrainian judicial entity and delivered a legal-themed email linking to a staged archive hosted on a public file-sharing platform. The download ultimately executed a disguised file that installed Remote Manipulator System (RMS), providing the attacker remote access to the victim’s system. The activity aligns with intelligence gathering and potential financial theft objectives, particularly against procurement and finance-adjacent roles.Priority Level and Response Window
· Priority Level
o High
· Response Window
o 24 to 72 hours for finance, procurement, legal, treasury, and executive support roles
o 7 days for enterprise-wide hardening and detection expansion
Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
“For organizations affected by UAC-0050’s judicial-themed spearphishing campaign deploying Remote Manipulator System (RMS) against finance-adjacent roles…”
· Low-end total cost: $175,000 – $450,000
o Single-user compromise contained quickly, no confirmed financial transfer, limited forensic scope
· Typical expected range: $600,000 – $2.4 million
o Remote access established, expanded forensic review, temporary procurement control disruption
· Upper-bound realistic scenarios: $3 million – $8.5 million
o Multi-system access, attempted procurement fraud, regulatory review triggered
Key Cost Drivers
· Duration of undetected remote access before containment
· Exposure of procurement systems or payment authorization workflows
· Scope of forensic review across endpoints and executive mailboxes
· Regulatory notification obligations tied to financial or sensitive data
· Business interruption in treasury, legal, or procurement operations
· Cyber insurance deductible thresholds and renewal premium increases
Why This Matters Now
· This campaign demonstrates targeted access against finance-adjacent leadership roles, increasing exposure to procurement fraud and sensitive financial intelligence loss.
· Because the attack relies on user interaction rather than exploiting software flaws, it is inexpensive for the adversary to repeat and difficult to prevent through patching alone.
· The use of legitimate remote access software reduces detection friction and can extend attacker dwell time if governance controls are not tightly enforced.
Exploit Conditions Snapshot
· Exploit Preconditions
o User interaction required to click link, download archives, extract multiple layers, and execute payload
· Exploit Type
o Not applicable at this time
· Defensive Control Pressure Points
o Public file-sharing link delivery to bypass reputation controls
o Password-protected archive stage to reduce automated inspection and slow triage
o Legitimate remote access tool installation to blend into administrative activity
Today’s Hunt Focus
· Identify Pixeldrain downloads followed by first-seen execution from user-writable paths within 90 minutes on the same endpoint
· Identify execution of files ending in .pdf.exe from Downloads, Temp, or AppData followed by msiexec activity
· Identify RMS installation artifacts and remote session indicators on endpoints outside IT-managed device groups
Bottom Line for Executives
· The operation targets procurement-adjacent advisory roles with privileged operational and financial insight, increasing risk of vendor payment fraud, illicit transfers, and sensitive institutional data exposure.
· Because the chain does not rely on software exploitation, the probability of repetition remains elevated unless execution controls, email defenses, and remote tool governance are tightened.
Campaign Summary
· Threat Actor
o UAC-0050
· Alternate Naming in Reporting
o Mercenary Akula
o DaVinci Group
· Primary Objectives
o Intelligence gathering
o Financial theft
· Observed Target Profile
o Senior legal and policy advisor involved in procurement at a European financial institution
· Primary Tooling Observed
o Remote Manipulator System (RMS) delivered via MSI
Sectors and Countries
· Sectors
o Financial services and financial institutions
· Countries and Regions
o Western Europe (targeted financial institution)
o Ukraine (impersonated judicial domain theme)
First Activity and Last Activity
· First Activity
o Not applicable at this time (public sources cited for this report do not provide a reliable first-seen date)
· Last Activity
o February 9, 2026 observed attack activity described in reporting dated February 24, 2026
Estimated Probability of Recurrence (12-month horizon)
· Estimate
o 0.65
· Rationale
o User-execution chain is low-cost and repeatable (phishing link, archive staging, masquerade)
o RMS and similar remote access tool tradecraft supports repeated access attempts without exploit development
o Targeting expansion signal increases addressable victim surface
Malware and Tooling
· Remote Manipulator System (RMS)
o Role
§ Remote control, desktop sharing, file transfer
· LiteManager
o Role
§ Legitimate remote access software previously associated with the actor in reporting context
· Remcos
o Role
§ Not applicable at this time (referenced as prior associated tooling in reporting context, not confirmed in the February 2026 event chain)
Malware and SHA256
SHA256
o Not applicable at this time (public sources cited do not provide file hashes for the described samples)
Infrastructure and Hosting
· Hosting and staging
o pixeldrain[.]com
· Impersonation theme
o Spoofed Ukrainian judicial domain described in reporting
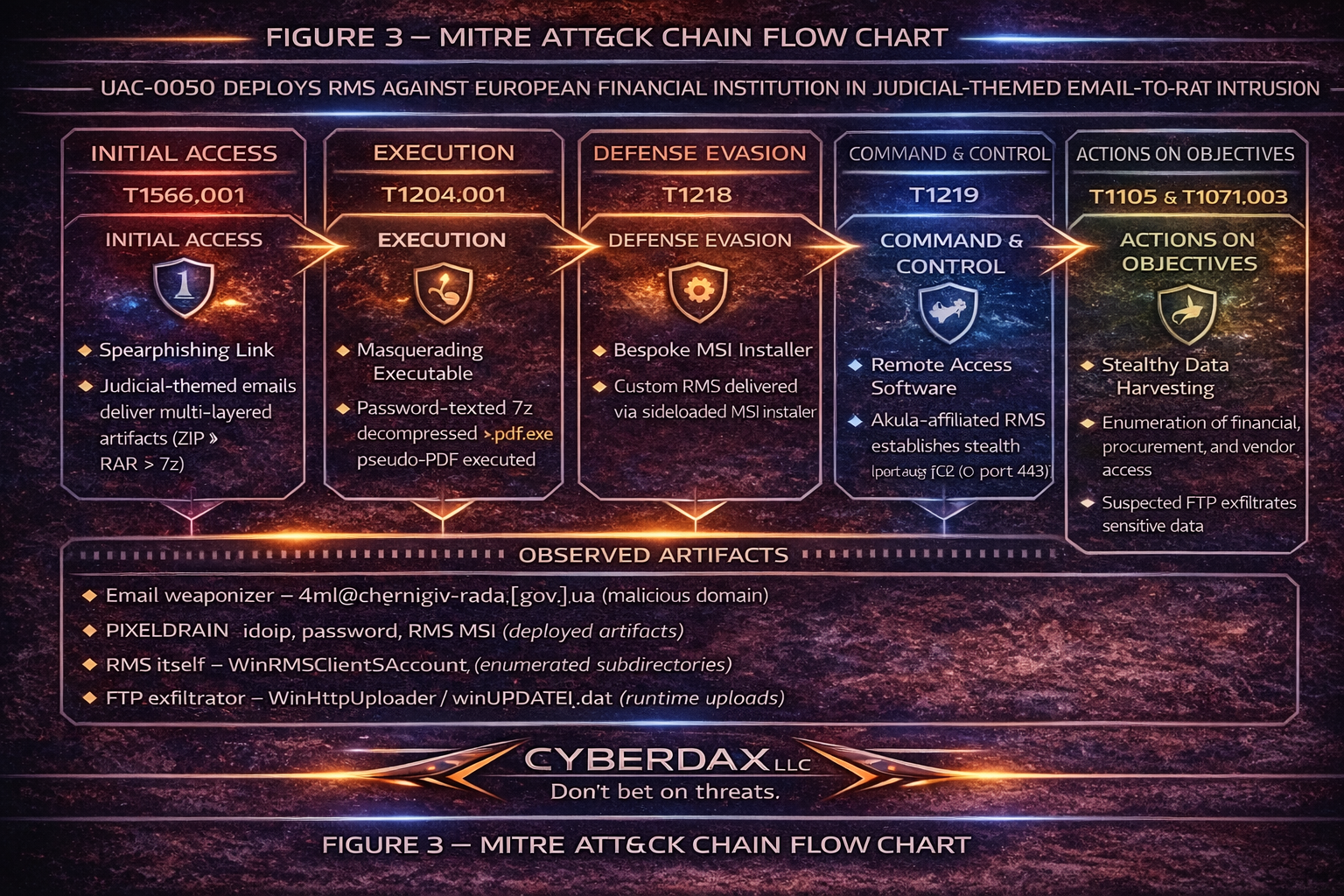
MITRE ATT&CK Mapping
· T1583.001 – Acquire Infrastructure: Domains
o Tactic: Resource Development
o Actor leveraged domain infrastructure to spoof a Ukrainian judicial identity and increase legitimacy of legal-themed lures.
· T1566.002 – Phishing: Spearphishing Link
o Tactic: Initial Access
o Email delivered a link directing the target to download staged payload archives hosted on a public file-sharing platform.
· T1204.002 – User Execution: Malicious File
o Tactic: Execution
o Victim manually extracted multi-layer compressed archives and executed the final payload.
· T1036.007 – Masquerading: Double File Extension
o Tactic: Defense Evasion
o Final executable used .pdf.exe naming convention to appear as a document while remaining executable.
· T1027 – Obfuscated or Encrypted Files or Information
o Tactic: Defense Evasion
o Password-protected archive stage and layered compression reduced automated inspection and delayed analysis.
· T1219 – Remote Access Software
o Tactic: Command and Control
o Remote Manipulator System (RMS) installed via MSI to establish persistent remote desktop and file transfer capability.
· T1657 – Financial Theft
o Tactic: Impact
o Campaign objectives aligned to financial data access, procurement manipulation, and potential payment fraud.
Stage-Based TTPs
· Stage 1: Targeting and Pretext Construction
o T1583.001 – Acquire Infrastructure: Domains
§ Use of spoofed domain theming to increase legitimacy of legal communications and induce trust
· Stage 2: Initial Access Delivery
o T1566.002 – Phishing: Spearphishing Link
§ Legal-themed spearphishing email includes a link that drives download of staged archives from Pixeldrain
· Stage 3: User-Driven Execution Enablement
o T1204.002 – User Execution: Malicious File
§ Victim extracts multi-layer archives and executes masqueraded payload
· Stage 4: Defense Evasion and Scanning Resistance
o T1027 – Obfuscated Files or Information
§ Password-protected archive stage and layered compression inhibit automated inspection and delay triage
o T1036.007 – Masquerading: Double File Extension
§ Payload uses .pdf.exe naming to appear document-like while remaining executable
· Stage 5: Remote Access Establishment
o T1219 – Remote Access Software
§ MSI installs RMS to establish interactive remote access and file transfer capabilities
· Stage 6: Monetization and Objective Actions
o T1657 – Financial Theft
§ Objective alignment includes financial theft and intelligence gathering targeting financially sensitive roles
IOC Confidence Blocks
· High Confidence
o Indicator
§ pixeldrain[.]com
o Confidence Score
§ 0.80
o Rationale
§ Explicitly cited as payload staging service in the described chain
o Indicator
§ Layered archive chain with password-protected 7z and separate password text file
o Confidence Score
§ 0.80
o Rationale
§ Explicitly described infection chain behavior
o Indicator
§ Double-extension executable masquerade (.pdf.exe)
o Confidence Score
§ 0.80
o Rationale
§ Explicitly described technique used to masquerade payload
· Medium Confidence
o Indicator
§ RMS installation via MSI
o Confidence Score
§ 0.70
o Rationale
§ Explicitly described in reporting as deployed payload
· Low Confidence
o Not applicable at this time
CVE, CVSS 3.1 and CVSS 4.0
· Not applicable at this time
KEV and Nessus
· KEV
o Not applicable at this time
· Nessus
o Not applicable at this time
Patch Data
· Not applicable at this time
Behavior and Log Artifacts
· Email telemetry
o Legal and court-themed messaging intended to drive link click behavior
o Link to Pixeldrain included in message body
· Host telemetry
o Archive extraction sequence consistent with multi-layer compressed content and password-protected stage
o Process execution of a file ending in .pdf.exe from user-writable paths
o msiexec execution installing RMS MSI package
· Network telemetry
o HTTP or HTTPS access to pixeldrain.com preceding first-seen execution activity
Detection Coverage Matrix
· Email Security
o Coverage strengths
§ URL filtering and impersonation protections can surface link-based lures
o Coverage gaps
§ Public file-sharing links may bypass reputation controls
§ Password-protected archives reduce content inspection
· Endpoint Security
o Coverage strengths
§ Process creation telemetry can detect .pdf.exe execution and msiexec follow-on
o Coverage gaps
§ Remote access tools may be treated as legitimate without governance policy enforcement
· Network Security
o Coverage strengths
§ Proxy logging can expose pixeldrain access and download patterns
o Coverage gaps
§ Legitimate business use of file-sharing requires scoped allowlisting to maintain signal quality
Detection Engineering Matrix
· Collection prerequisites
o Email gateway logs including URLs and sender authentication outcomes
o Endpoint process creation with full command line
o MSI installation telemetry and Windows service creation telemetry
o Web proxy logs with URL, host, user, device mapping
· High-fidelity correlations
o Pixeldrain download followed by first-seen executable launch from user-writable locations within 90 minutes
o .pdf.exe execution followed by msiexec MSI installation activity within 30 minutes
o RMS presence on endpoints outside IT-managed device groups
· Suppression guidance
o Allowlist approved remote access tooling and deployment methods
o Allowlist known sanctioned Pixeldrain usage by defined teams if applicable
IOC Confidence and Hunt Prioritization Matrix
· Priority Tier 1
o pixeldrain[.]com access followed by .pdf.exe execution and msiexec activity on the same endpoint
· Priority Tier 2
o .pdf.exe execution from Downloads, Temp, or AppData paths without known business justification
o MSI installs initiated from user-writable paths on non-IT endpoints
· Priority Tier 3
o RMS installation artifacts detected on finance-adjacent endpoints outside approved remote tool allowlists
Ultra-Tuned Detection Content
Splunk SPL
Judicial-themed spearphishing with Pixeldrain link targeting finance-adjacent roles
· Purpose
o Identify legal or court-themed spearphishing messages that contain Pixeldrain links delivered to finance-adjacent roles described as targeted in reporting
· Tuning Explanation
o Tune subject and keyword list to local language equivalents and organizational lures
o Suppress known legitimate court and regulatory correspondents
o Scope by recipient role or org unit to reduce noise
· Syntax
index=email
( subject="*court*" OR subject="*judicial*" OR subject="*administrative*" OR subject="*case*" OR subject="*procurement*" )
( body="*pixeldrain*" OR urls="*pixeldrain*" )
| eval recipient_role=coalesce(recipient_role,"UNKNOWN")
| where recipient_role IN ("FINANCE","PROCUREMENT","LEGAL","TREASURY","EXECUTIVE_SUPPORT")
| stats earliest(_time) as first_seen latest(_time) as last_seen values(sender) as senders values(recipient) as recipients values(subject) as subjects values(urls) as urls count by message_id
· SQL Syntax
SELECT
received_time,
message_id,
sender,
recipient,
subject,
body_urls
FROM email_events
WHERE
(
LOWER(subject) LIKE '%court%'
OR LOWER(subject) LIKE '%judicial%'
OR LOWER(subject) LIKE '%administrative%'
OR LOWER(subject) LIKE '%case%'
OR LOWER(subject) LIKE '%procurement%'
)
AND LOWER(body_urls) LIKE '%pixeldrain%'
AND recipient_role IN ('FINANCE','PROCUREMENT','LEGAL','TREASURY','EXECUTIVE_SUPPORT');
· MSIEXEC MSI installation initiated from user-writable paths
· Purpose
o Detect RMS-style delivery patterns where MSI installation occurs from user-writable paths consistent with staged delivery and remote tool installation
· Tuning Explanation
o Suppress trusted software distribution tooling and known managed installer paths
o Elevate severity when installer is first-seen or when host is not IT-managed
· Syntax
index=endpoint (EventCode=4688 OR sourcetype="XmlWinEventLog:Microsoft-Windows-Sysmon/Operational" OR sourcetype="WinEventLog:Security")
(Image="*\\msiexec.exe" OR NewProcessName="*\\msiexec.exe")
(CommandLine="* /i *" OR CommandLine="* /package *")
( CommandLine="*\\Users\\*" OR CommandLine="*\\Downloads\\*" OR CommandLine="*\\AppData\\*" OR CommandLine="*\\Temp\\*" )
| stats earliest(_time) as first_seen latest(_time) as last_seen values(ParentImage) as parent values(CommandLine) as cmd count by host user Image
· SQL Syntax
SELECT
event_time,
host,
user_name,
process_name,
command_line,
parent_process_name
FROM edr_process_events
WHERE
LOWER(process_name) = 'msiexec.exe'
AND (LOWER(command_line) LIKE '% /i %' OR LOWER(command_line) LIKE '% /package %')
AND (
LOWER(command_line) LIKE '%\\users\\%'
OR LOWER(command_line) LIKE '%\\downloads\\%'
OR LOWER(command_line) LIKE '%\\appdata\\%'
OR LOWER(command_line) LIKE '%\\temp\\%'
);
SentinelOne
Rule 1 Double-extension execution ending in .pdf.exe from user-writable paths
· Purpose
o Detect execution of masqueraded payloads using double-extension filenames consistent with the described .pdf.exe method
· Tuning Explanation
o Suppress known benign internal installers that legitimately contain multiple extensions
o Elevate when initiating process is an archiver, email client, or when file is unsigned or first-seen
· Syntax
DeviceProcessEvents
| where FileName endswith ".pdf.exe"
| where FolderPath has @"\Users\" or FolderPath has @"\Downloads\" or FolderPath has @"\AppData\" or FolderPath has @"\Temp\"
| project Timestamp, DeviceName, AccountName, FileName, FolderPath, ProcessCommandLine, InitiatingProcessFileName, InitiatingProcessFolderPath
· SQL Syntax
SELECT
event_time,
host,
user_name,
process_name,
process_path,
command_line,
parent_process_name
FROM edr_process_events
WHERE
LOWER(process_name) LIKE '%.pdf.exe'
AND (
LOWER(process_path) LIKE '%\\users\\%'
OR LOWER(process_path) LIKE '%\\downloads\\%'
OR LOWER(process_path) LIKE '%\\appdata\\%'
OR LOWER(process_path) LIKE '%\\temp\\%'
);
Rule 2 RMS installation or remote access tooling signals from user-writable origin
· Purpose
o Identify suspicious remote access tooling installation patterns and RMS-related indicators consistent with the observed chain
· Tuning Explanation
o Allowlist approved remote tools and approved IT device groups
o Elevate when observed on finance, procurement, treasury, or executive support endpoints
· Syntax
EventType = "Process Creation"
AND (ProcessName contains "msiexec" OR ProcessCommandLine contains "Remote Manipulator" OR ProcessCommandLine contains "RMS")
AND (ProcessPath contains "\Users\" OR ProcessPath contains "\Downloads\" OR ProcessPath contains "\AppData\" OR ProcessPath contains "\Temp\")
· SQL Syntax
SELECT
event_time,
host,
user_name,
process_name,
process_path,
command_line
FROM edr_process_events
WHERE
(
LOWER(process_name) = 'msiexec.exe'
OR LOWER(command_line) LIKE '%remote manipulator%'
OR LOWER(command_line) LIKE '%rms%'
)
AND (
LOWER(process_path) LIKE '%\\users\\%'
OR LOWER(process_path) LIKE '%\\downloads\\%'
OR LOWER(process_path) LIKE '%\\appdata\\%'
OR LOWER(process_path) LIKE '%\\temp\\%'
);
Suricata
· Possible staging via Pixeldrain download
· Purpose
o Flag HTTP traffic to pixeldrain.com consistent with payload retrieval staging described in reporting
· Tuning Explanation
o If Pixeldrain is used legitimately, scope by egress segment, user group, or destination categories
o Elevate when correlated with endpoint execution events soon after download
· Syntax
alert http any any -> any any (
msg:"CYBERDAX UAC-0050 possible staging via pixeldrain download";
flow:established,to_server;
http.host; content:"pixeldrain.com"; nocase;
classtype:trojan-activity;
sid:4200501;
rev:3;
)
· SQL Syntax
SELECT
event_time,
src_ip,
dst_ip,
http_host,
uri,
user_agent,
user_name,
host
FROM http_events
WHERE
LOWER(http_host) = 'pixeldrain.com';
Sigma
· Execution of double-extension executable masquerading as document
· Purpose
o Detect process creation where the true extension is executable but presented as document-like double-extension, aligned to T1036.007 usage
· Tuning Explanation
o Suppress known internal packaging workflows
o Elevate when parent process is an archive utility or email client, or when executed from Downloads or Temp
· Syntax
title: Execution of Double Extension Document-Like Executable from User-Writable Paths
id: 9b6c2d2b-3d7b-4e1c-9a3d-7f1b8d8a4b21
status: experimental
description: Detects execution of files ending with document-like double extensions such as .pdf.exe from user-writable paths.
author: CyberDax LLC
date: 2026-02-24
logsource:
product: windows
category: process_creation
detection:
selection_ext:
Image|endswith: ".pdf.exe"
selection_path:
Image|contains:
- "\Users\"
- "\Downloads\"
- "\AppData\Local\Temp\"
- "\AppData\Roaming\"
condition: selection_ext and selection_path
fields:
- Image
- CommandLine
- ParentImage
- User
falsepositives:
- Rare legitimate tools using misleading naming conventions
level: high
· SQL Syntax
SELECT
event_time,
host,
user_name,
process_name,
process_path,
command_line,
parent_process_name
FROM edr_process_events
WHERE
LOWER(process_name) LIKE '%.pdf.exe'
AND (
LOWER(process_path) LIKE '%\\users\\%'
OR LOWER(process_path) LIKE '%\\downloads\\%'
OR LOWER(process_path) LIKE '%\\appdata\\%'
OR LOWER(process_path) LIKE '%\\temp\\%'
);
YARA
· Heuristic identification of PE files with .pdf.exe naming
· Purpose
o Provide a triage heuristic to flag PE files masquerading as PDFs through double extension
· Tuning Explanation
o Use in combination with signer checks, file origin, and first-seen logic
o Elevate when written to Downloads, Temp, or AppData prior to execution
· Syntax
rule CYBERDAX_Masqueraded_Document_DoubleExtension_PDF_EXE
{
meta:
author = "CyberDax LLC"
date = "2026-02-24"
description = "Heuristic rule for PE files masquerading as PDF via .pdf.exe naming."
strings:
$mz = { 4D 5A }
$ext = ".pdf.exe" ascii nocase
condition:
$mz at 0 and $ext
}
· SQL Syntax
SELECT
event_time,
host,
user_name,
file_name,
file_path,
file_hash_sha256
FROM file_create_events
WHERE
LOWER(file_name) LIKE '%.pdf%.exe'
AND (
LOWER(file_path) LIKE '%\\downloads\\%'
OR LOWER(file_path) LIKE '%\\temp\\%'
OR LOWER(file_path) LIKE '%\\appdata\\%'
);
Delivery Methods
· Spearphishing email using legal and court-themed lure content
· Link-based download staging via Pixeldrain
· Layered archive chain: ZIP containing RAR containing password-protected 7z with separate password text file
· Double-extension executable masquerading as a PDF (.pdf.exe)
· MSI installation of RMS via msiexec
Defensive Control and Hardening Architecture
· Email and identity controls
o Enforce DMARC, SPF, and DKIM alignment with quarantine or reject actions for failing alignment on high-risk mailboxes
o Increase impersonation detections for government and judicial-themed lures consistent with this campaign
· Endpoint execution controls
o Block execution from Downloads and Temp for non-developer endpoints where feasible
o Restrict MSI installation from user-writable paths and require elevated approval for non-IT endpoints
o Enforce policies to reveal file extensions and reduce double-extension deception effectiveness
· Remote tool governance
o Maintain explicit allowlists for remote access tooling, approved signers, approved deployment methods, and IT-managed device groups
o Alert on RMS installation or service creation outside approved groups
· Network controls
o Monitor and optionally restrict public file-sharing services for high-risk groups, with documented exceptions
o Correlate proxy downloads with endpoint execution to increase detection fidelity
7-Day Steps
· Day 1
o Run email hunts for legal-themed lures with Pixeldrain links against high-risk role mailboxes
o Run endpoint hunts for .pdf.exe execution from user-writable paths
· Day 2
o Hunt for msiexec MSI installation from Downloads, Temp, or AppData paths
o Identify endpoints with RMS artifacts outside IT-managed device groups
· Day 3
o Implement correlation detection: Pixeldrain download then first-seen execution within 90 minutes
o Validate telemetry completeness for process creation and MSI installation events
· Day 4
o Tighten MSI install control policy for user-writable origins
o Validate remote tool allowlists and establish approval workflow for exceptions
· Day 5
o Implement out-of-band verification for vendor and payment change requests in procurement workflows
· Day 6
o Deliver targeted awareness for finance-adjacent roles on layered archives, password text files, and double-extension payloads
· Day 7
o Conduct tabletop exercise for remote tool abuse and payment fraud scenarios aligned to this chain
References
BlueVoyant
· hxxps://www.bluevoyant[.]com/blog/mercenary-akula-hits-financial-institution
The Hacker News
· hxxps://thehackernews[.]com/2026/02/uac-0050-targets-european-financial[.]html
MITRE ATT&CK
· hxxps://attack[.]mitre[.]org