CVE-2026-20127 Cisco Catalyst SD-WAN Manager and Controller Authentication Bypass Vulnerability Actively Exploited in the Wild
BLUF
CVE-2026-20127 is a critical authentication bypass vulnerability affecting Cisco Catalyst SD-WAN Manager and Controller platforms that enables unauthenticated administrative access to centralized SD-WAN control-plane infrastructure. Exploitation grants adversaries authoritative control over routing policy, peer relationships, and configuration state across connected enterprise sites.
Because this vulnerability targets orchestration infrastructure rather than isolated edge devices, a single compromise can propagate across the entire SD-WAN fabric. Impact includes enterprise-wide connectivity disruption, segmentation failure, traffic redirection risk, SLA breach exposure, regulatory reporting implications, and significant recovery cost driven by configuration trust re-establishment. Active exploitation has been confirmed. Immediate patching and strict management-plane isolation are required.
Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
For organizations affected by active exploitation of CVE-2026-20127 impacting Cisco SD-WAN control-plane infrastructure:
· Low-end total cost: $300,000 – $750,000
(rapid patching, no sustained outage, limited forensic scope)
· Typical expected range: $750,000 – $2.5 million
(multi-site validation, short-term instability, external IR engagement)
· Upper-bound realistic scenarios: $2.5 million – $6 million
(extended routing disruption, regulatory review, contractual penalties)
Key Cost Drivers
· Duration of control-plane instability or outage
· Scope of configuration integrity validation required
· Number of distributed sites dependent on SD-WAN
· Regulatory environment governing data flows
· Cyber insurance retention structure and renewal timing
Bottom Line for Executives
CVE-2026-20127 exposes centralized SD-WAN control infrastructure to unauthenticated administrative compromise. Because this vulnerability affects orchestration rather than individual devices, a single successful exploit can disrupt connectivity across the enterprise.
For mid-size to large organizations, realistic financial exposure typically ranges from $750,000 to $2.5 million, driven primarily by multi-site configuration validation, operational instability, and governance response. Extended disruption or regulatory escalation can materially increase that range.
Executive focus should be immediate remediation, strict management-plane isolation, and documented validation of configuration integrity across all sites. This is an enterprise resilience issue — not a routine patch cycle.
Priority Level and Response Window
Priority Level: Critical
Response Window:
· Internet-exposed SD-WAN control systems: Immediate same-day remediation
· Internally reachable management plane: Within 24 hours
· Segmented environments with enforced ACLs: Within 72 hours
Executive Escalation Criteria:
· Unauthorized peer relationship detected
· Privileged SSH key modification
· Firmware downgrade outside change window
· Log truncation on control-plane nodes
Why This Matters Now
· Control-plane compromise introduces systemic multi-site risk.
· Native administrative mechanisms reduce reliance on detectable malware.
· Recovery requires full routing policy and configuration validation across all sites.
· KEV inclusion elevates executive accountability and audit scrutiny.
· SD-WAN control infrastructure frequently underpins regulated, revenue-generating operations.
Financial Exposure Drivers:
· Multi-branch connectivity downtime
· SLA penalties and operational disruption
· Incident response and forensic validation cost
· Governance and compliance reporting burden
What we don’t yet know
· Confirmed malware families associated with exploitation
· Verified SHA256 payload artifacts
· Complete adversary infrastructure mapping
Exploit Conditions Snapshot
Attack Vector: Network
Authentication Required: None
User Interaction: None
Privileges Gained: Administrative non-root
Trust Boundary Impact:
· Compromise occurs at orchestration tier
· Enables systemic configuration manipulation
· Impacts all connected SD-WAN sites
Exposure Amplifiers:
· Internet-facing management interface
· Open TCP 830 NETCONF
· Weak management-plane segmentation
· Insufficient log retention
· Lack of firmware integrity monitoring
Exploit Complexity: Low
Workarounds: Not known at this time
Vendor Fix: Security update available
Today’s Hunt Focus (3 signals)
· Unauthorized SD-WAN peer insertion
· Firmware downgrade followed by revert sequence
· SSH authorized_keys modification correlated with log truncation
Sectors possibly impacted
· Telecommunications
· Financial Services
· Healthcare
· Government
· Energy
· Technology and Cloud Providers
· Manufacturing
· Retail
Known impacted sectors
· Not known at this time
Countries
· Global
First Activity
· Observed exploitation prior to public disclosure; earliest confirmed reporting: 2023.
Last Activity
· Ongoing exploitation reporting through 2026
o Exact last observed timestamp: Not known at this time
CVE Details
CVE ID: CVE-2026-20127
Weakness: Improper Authentication
CVSS 3.1
o (10.0) AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H
· CWE: CWE-287 Improper Authentication
· Is this in the KEV catalog
o Yes
· KEV remediation due date:
o February 27, 2026
· Nessus Plugin ID: 299998
Affected Systems:
· Cisco Catalyst SD-WAN Manager
· Cisco Catalyst SD-WAN Controller
Impact: Unauthenticated administrative session establishment allowing routing policy and peer manipulation.
Exploit Status
Exploited in the wild: Yes
Public exploit code: Not known at this time
Exploit maturity: Operational
Observed chaining behavior:
· Firmware downgrade enabling escalation
· SSH key persistence
· Log artifact manipulation
MITRE ATT&CK Chain Flow Mapping
· T1595 – Active Scanning
· T1190 – Exploit Public-Facing Application
· T1601.002 – Modify System Image: Downgrade
· T1068 – Exploitation for Privilege Escalation
· T1098.004 – Account Manipulation: SSH Authorized Keys
· T1136.001 – Create Account: Local Account
· T1037 – Boot or Logon Initialization Scripts
· T1070 – Indicator Removal on Host
· T1021.004 – Remote Services: SSH
· T1565 – Data Manipulation
Stage-Based TTPs (MITRE ID, Title, how used)
· T1190 – Exploit Public-Facing Application
o Bypasses authentication via crafted management-plane requests.
· T1601.002 – Modify System Image: Downgrade
o Reverts firmware to vulnerable version to enable escalation.
· T1068 – Exploitation for Privilege Escalation
o Escalates from non-root administrative context.
· T1098.004 – Account Manipulation: SSH Authorized Keys
o Establishes persistent privileged access.
· T1070 – Indicator Removal on Host
o Truncates log artifacts to reduce visibility.
· T1565 – Data Manipulation
o Modifies routing and peer configuration via NETCONF.
Malware and SHA256
· Malware: Not known at this time
· SHA256: Not known at this time
· Exploitation primarily leverages legitimate administrative interfaces.
Behavior and Log Artifacts
· control-connection-state-change anomalies
· Unexpected peer-type mismatches
· NETCONF session spikes
· SSH configuration modifications
· PermitRootLogin enabled
· authorized_keys additions for privileged accounts
· Firmware downgrade and revert logs
· syslog, wtmp, lastlog truncation
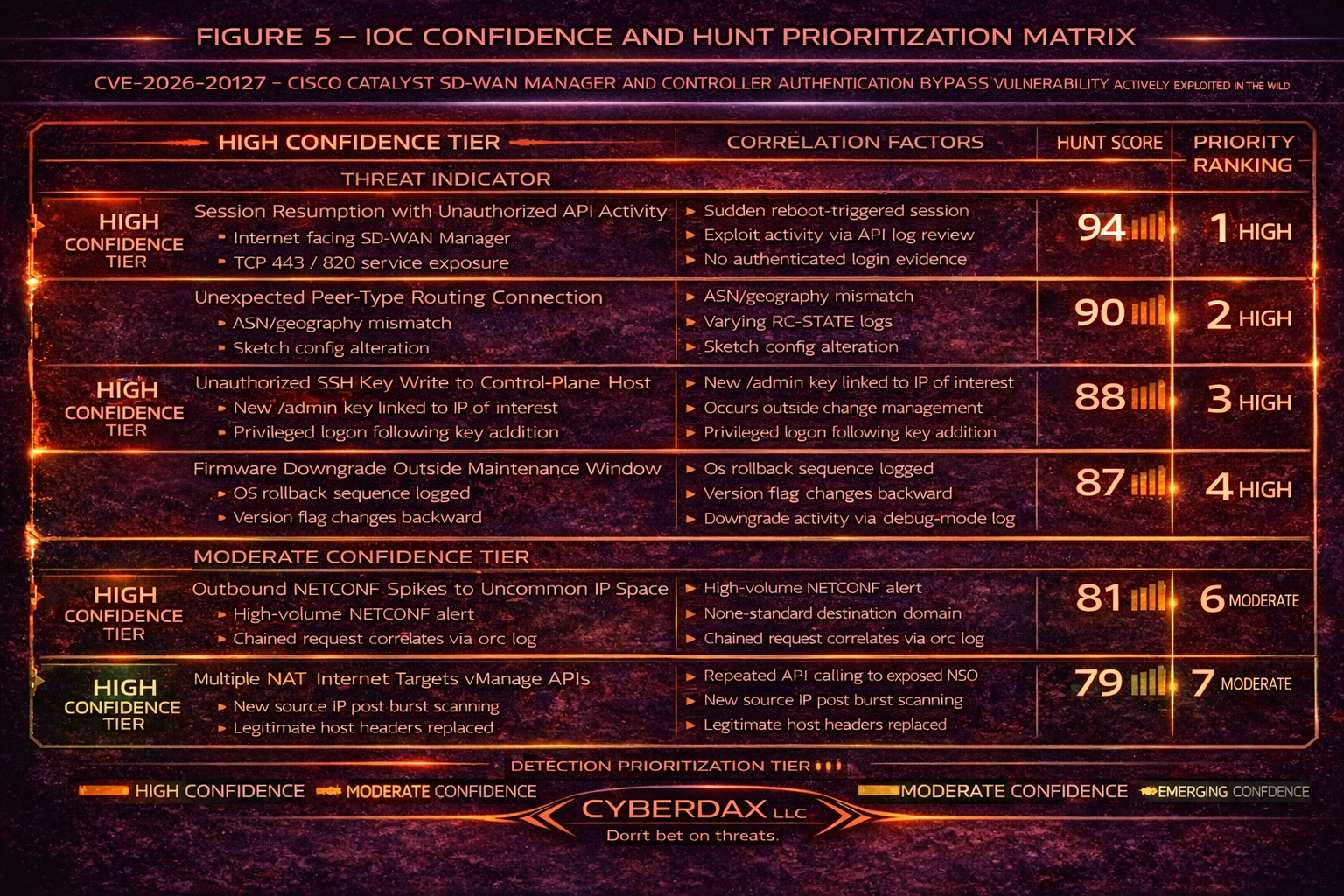
IOC Confidence and Hunt Prioritization
Static IOCs
· IP addresses: Not known at this time
· Domains: Not known at this time
· Hashes: Not known at this time
Behavioral IOCs
· Indicator: Root authorized_keys modification
o Detection Surface: Host
o MITRE Mapping: T1098.004
o Confidence: 95
o Hunt Priority: Immediate
· Indicator: Firmware downgrade-revert sequence
o Detection Surface: Host / Control Plane
o MITRE Mapping: T1601.002
o Confidence: 92
o Hunt Priority: High
· Indicator: Unauthorized peer injection
o Detection Surface: Control Plane
o MITRE Mapping: T1565
o Confidence: 90
o Hunt Priority: High
· Indicator: NETCONF spike from unbaselined IP
o Detection Surface: Network
o MITRE Mapping: T1190
o Confidence: 75
o Hunt Priority: Moderate
Confidence Tier Roll-Up
High Confidence Indicators:
· Root authorized_keys modification
· Firmware downgrade-revert sequence
· Unauthorized peer injection
Moderate Confidence Indicators:
· NETCONF spike from unbaselined IP
Contextual Indicators:
· Single anomalous peer event without supporting artifacts
Detection Signals Layer
· Network: NETCONF concentration deviation
· Identity: Privileged SSH key modification
· Host: Log truncation artifacts
· Control Plane: Peer relationship deviation
· Integrity: Firmware downgrade outside change window
Detection Coverage Matrix
· Initial Access (T1190): Moderate visibility; encrypted management traffic limits inspection.
· Privilege Escalation (T1068): Moderate visibility; firmware telemetry required.
· Persistence (T1098.004): High visibility if file integrity monitoring enabled.
· Defense Evasion (T1070): Moderate visibility; dependent on adequate retention.
Residual Detection Risk: Medium without cross-domain telemetry correlation and behavioral baselining.
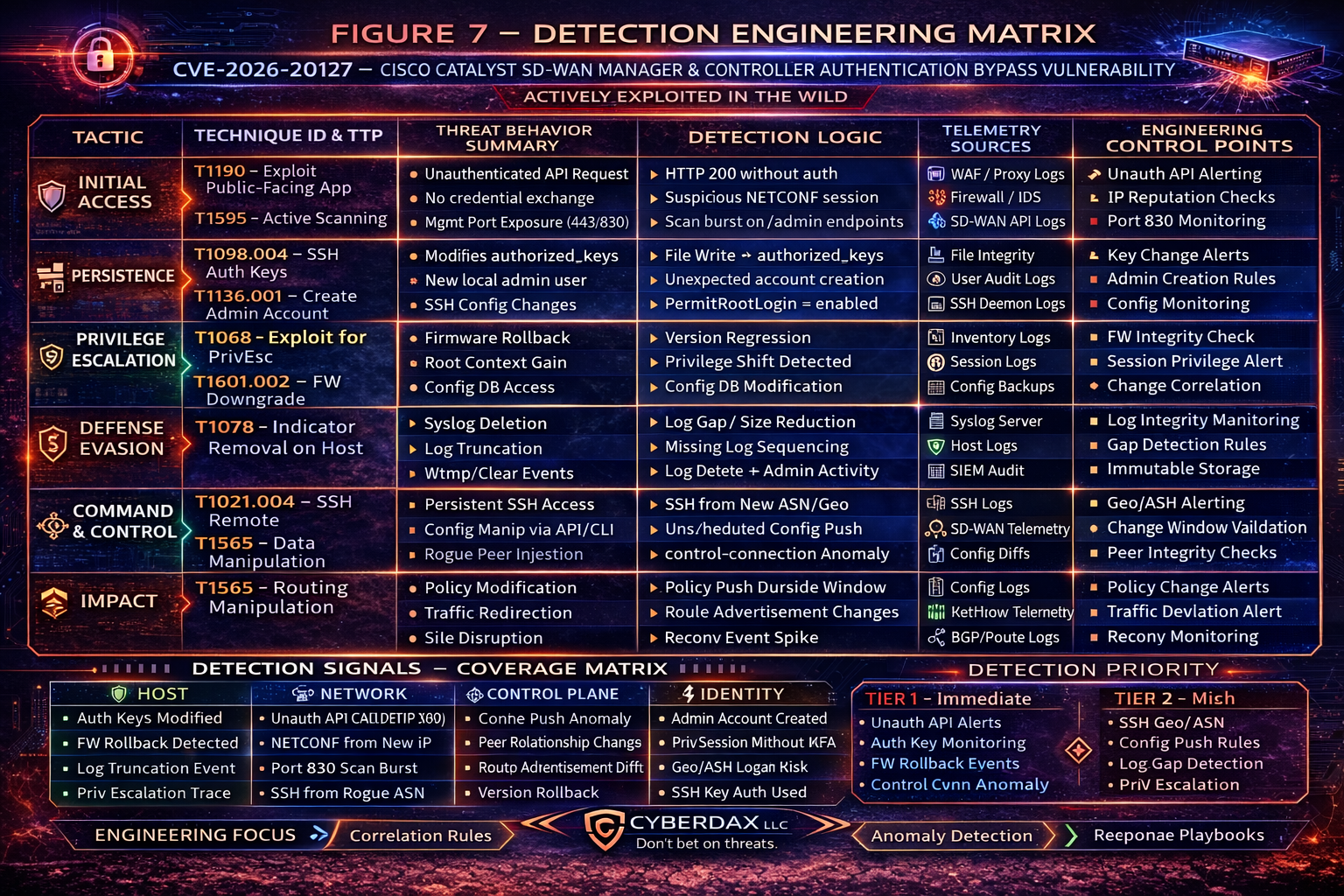
Detection Engineering Matrix
Initial Access – T1190 / T1595 Threat Behavior Summary
· Internet-facing SD-WAN Manager or Controller exposed over HTTPS or NETCONF
· Crafted unauthenticated management-plane API request
· Administrative session established without valid credential exchange
· External scanning activity targeting TCP 443 / 830
Engineering Focus
· Detect unauthenticated API calls returning HTTP 200 responses
· Baseline NETCONF session origination IP space
· Identify burst scanning against management endpoints
· Correlate session establishment without login audit event
Detection Control Points
· WAF / reverse proxy logs
· SD-WAN API audit logs
· Firewall telemetry
· IDS monitoring TCP 830
Persistence – T1098.004 / T1136.001 Threat Behavior Summary
· Authorized_keys file modified on SD-WAN control node
· Creation of new local administrative account
· SSH configuration altered to enable persistent privileged access
· Access survives reboot
Engineering Focus
· Alert on writes to /.ssh/authorized_keys
· Detect local account creation outside maintenance window
· Identify PermitRootLogin configuration change
· Correlate privileged login following key insertion
Detection Control Points
· File integrity monitoring
· SD-WAN local user audit logs
· SSH configuration monitoring
· SIEM correlation rules
Privilege Escalation – T1068 / T1601.002 Threat Behavior Summary
· Firmware downgrade to vulnerable version
· Version rollback outside scheduled change window
· Escalation from limited admin to root context
· Access to configuration database backend
Engineering Focus
· Detect firmware version regression events
· Alert on system image checksum mismatch
· Identify privilege context shift within active session
· Correlate downgrade followed by config change
Detection Control Points
· Device inventory telemetry
· Firmware version logging
· Session privilege metadata
· Configuration diff monitoring
Defense Evasion – T1070 Threat Behavior Summary
· syslog truncation or deletion
· wtmp / lastlog cleared
· Log continuity break preceding configuration changes
· Activity masked as maintenance
Engineering Focus
· Detect sudden reduction in log file size
· Identify missing log sequence continuity
· Alert on log deletion followed by admin activity
· Baseline expected log rotation timing
Detection Control Points
· Log integrity monitoring
· Syslog forwarding validation
· SIEM gap detection logic
· Immutable log repository validation
Command and Control / Remote Management Abuse – T1021.004 / T1565 Threat Behavior Summary
· Persistent SSH session to controller
· Configuration manipulation via CLI or API
· Rogue peer relationship injection
· Multi-site policy push executed
Engineering Focus
· Detect SSH session from new ASN or geography
· Identify rapid configuration propagation across sites
· Monitor control-connection-state-change anomalies
· Flag peer-type mismatches
Detection Control Points
· SD-WAN telemetry logs
· SSH connection logs
· Control-plane state-change events
· Routing table diff monitoring
Impact – T1565 Threat Behavior Summary
· Routing policy modification
· Traffic redirection
· Segmentation degradation
· Enterprise-wide connectivity disruption potential
Engineering Focus
· Alert on policy push outside maintenance window
· Detect abnormal site reconvergence frequency
· Monitor route advertisement anomalies
· Correlate config changes with traffic path deviation
Detection Control Points
· Configuration diff engine
· Network flow telemetry
· SD-WAN site health monitoring
· Routing anomaly monitoring
Detection Engineering Prioritization Summary
Priority Tier 1 – Immediate Engineering Validation
· Unauthenticated API success response detection
· Authorized_keys modification telemetry validation
· Firmware downgrade / rollback alerts
· Control-connection-state-change anomaly correlation
Priority Tier 2 – High
· SSH geo/ASN deviation detection
· Configuration push outside change window alerting
· Log truncation anomaly detection
· Privilege escalation tracking
Priority Tier 3 – Tactical Enhancement
· Routing behavior anomaly baselining
· Peer relationship integrity monitoring
· Firmware integrity validation automation
· Configuration drift detection
Ultra-Tuned Detection Engineering Rules
Suricata
Title: SD-WAN NETCONF Concentration Deviation
Purpose: Detect abnormal NETCONF spikes
Tuning Explanation: Scope to controller IP range; exclude maintenance IPs; baseline admin windows
Telemetry Requirement: IDS visibility on TCP 830
False Positive Risk: Moderate during patch cycles
alert tcp $EXTERNAL_NET any -> $SDWAN_CTRL 830 (
msg:"CyberDax CVE-2026-20127 NETCONF deviation";
flow:to_server,established;
detection_filter:track by_src,count 25,seconds 300;
sid:2026201271; rev:8;
)
SentinelOne
Title: Privileged SSH Key Modification
Purpose: Detect persistence
Tuning Explanation: Alert only for root and vmanage-admin
Telemetry Requirement: File integrity monitoring enabled
False Positive Risk: Low
EventType=FileModification AND
(TargetFilePath ENDSWITH "/.ssh/authorized_keys") AND
(User IN ("root","vmanage-admin"))
Splunk
Title: Rogue Peer Injection Correlation
Purpose: Detect repeated peer insertion
Tuning Explanation: Correlate with change window logs
Telemetry Requirement: control-connection-state-change ingestion
False Positive Risk: Moderate without maintenance calendar integration
index=sdwan_logs "control-connection-state-change"
| stats count by peer_system_ip host
| where count > 5
Elastic
Title: Log Truncation Detection
Purpose: Detect abnormal log size reduction indicating potential defense evasion
Tuning Explanation: Alert only when log size drops below defined baseline threshold outside scheduled rotation window
Telemetry Requirement: File metadata monitoring enabled for /var/log directory
False Positive Risk: Moderate if log rotation schedule not integrated
file.path : "/var/log/*" and file.size < 5120
Sigma
title: SD-WAN SSH Authorized Keys Modification
logsource:
product: linux
category: file_event
detection:
selection:
TargetFilename|endswith: "/.ssh/authorized_keys"
condition: selection
level: high
YARA
rule CyberDax_SDWAN_Firmware_Downgrade
{
strings:
$s1="Software upgrade not confirmed"
$s2="control-connection-state-change"
condition:
2 of ($s*)
}
Delivery Methods
· Crafted management-plane network requests
· Rogue peer injection
· NETCONF configuration manipulation
· SSH key persistence placement
7-Day Response Plan
· Day 1: Patch and isolate management plane
· Day 2: Validate firmware versions
· Day 3: Baseline peer relationships
· Day 4: Rotate privileged credentials
· Day 5: Validate logging integrity
· Day 6: Deploy tuned detection controls
· Day 7: Conduct configuration integrity validation
Defensive Control and Hardening Architecture
Objective
· Prevent unauthenticated control-plane administrative access
· Detect firmware downgrade and configuration manipulation attempts
· Block persistent SSH-based administrative footholds
· Reduce blast radius of orchestration-layer compromise
· Strengthen governance visibility over SD-WAN control infrastructure
Layer 1
Management-Plane Exposure Elimination
Control Focus: Remove external attack surface for SD-WAN orchestration components.
· Remove public internet exposure of SD-WAN Manager and Controller interfaces
· Restrict TCP 443 and TCP 830 to approved IP allowlists only
· Enforce VPN or bastion-host-only administrative access
· Disable unused management services and APIs
· Implement rate limiting on management endpoints
Risk Mitigated
· T1190 – Exploit Public-Facing Application
· T1595 – Active Scanning
Layer 2
Authentication & Privilege Hardening
Control Focus: Prevent unauthorized administrative persistence.
· Disable password-based SSH authentication
· Enforce key-based SSH with strict key lifecycle management
· Disable PermitRootLogin
· Require MFA for all administrative access paths
· Enforce role-based access control with least privilege
Risk Mitigated
· T1098.004 – Account Manipulation: SSH Authorized Keys
· T1136.001 – Create Account: Local Account
· T1078 – Valid Accounts
Layer 3
Firmware Integrity & Downgrade Protection
Control Focus: Prevent version rollback exploitation and privilege escalation.
· Enforce signed firmware validation at boot
· Disable downgrade capability where supported
· Alert on firmware version regression events
· Validate image checksums against trusted repository
· Require documented change approval for firmware modification
Risk Mitigated
· T1601.002 – Modify System Image: Downgrade
· T1068 – Exploitation for Privilege Escalation
Layer 4
Configuration Integrity & Drift Monitoring
Control Focus: Detect unauthorized control-plane manipulation.
· Enable automated configuration diff monitoring
· Alert on policy push outside maintenance window
· Monitor peer-type mismatches and unexpected peer injection
· Validate routing table changes against approved change requests
· Maintain immutable configuration backups
Risk Mitigated
· T1565 – Data Manipulation
· T1021.004 – Remote Services: SSH
Layer 5
Control-Plane Behavioral Monitoring
Control Focus: Detect anomalous orchestration activity.
· Baseline control-connection-state-change events
· Alert on rapid multi-site configuration propagation
· Detect SSH sessions from new ASN or geography
· Monitor NETCONF spikes from non-baselined IPs
· Correlate admin session to configuration change event
Risk Mitigated
· T1021.004 – Remote Services: SSH
· T1565 – Data Manipulation
Layer 6
Logging Integrity & Anti-Tamper Controls
Control Focus: Prevent log deletion and defense evasion.
· Forward logs to centralized immutable storage
· Alert on syslog truncation or file size reduction
· Detect missing log sequence continuity
· Enforce write-once storage for critical telemetry
· Validate log retention minimum of 180 days
Risk Mitigated
· T1070 – Indicator Removal on Host
· Prolonged undetected persistence
Layer 7
Egress Filtering & Network Segmentation
Control Focus: Reduce survivability of unauthorized remote management.
· Restrict outbound SSH from control-plane hosts
· Enforce deny-by-default east-west segmentation
· Monitor route advertisement anomalies
· Baseline site reconvergence frequency
· Restrict controller communication to approved peers
Risk Mitigated
· T1021.004 – Remote Services
· Lateral movement across SD-WAN fabric
Layer 8
Governance & Executive Oversight Controls
Control Focus: Align orchestration-layer risk with enterprise governance.
· Classify SD-WAN control plane as Tier Zero infrastructure
· Establish executive reporting on management-plane exposure
· Conduct quarterly red-team simulation of control-plane compromise
· Track detection coverage against MITRE ATT&CK mapping
· Require documented approval for management-plane exposure changes
Risk Mitigated
· Governance visibility gaps
· Unmonitored orchestration-layer compromise
Architectural Outcome
When fully implemented, this layered defensive model:
· Eliminates internet-exposed control-plane attack surface
· Detects firmware downgrade attempts early
· Prevents unauthorized SSH persistence
· Detects rogue peer and routing manipulation
· Reduces probability of enterprise-wide SD-WAN disruption
· Shortens attacker dwell time within orchestration layer
· Aligns control-plane protection with executive risk posture
Estimated Probability of Recurrence (12-month horizon)
High
Drivers:
· Low exploitation complexity
· Broad SD-WAN enterprise deployment footprint
· Continued targeting of centralized orchestration infrastructure
Post-incident insights and recommendations
Key Post-Incident Insights
· Authentication bypass occurred at the management-plane boundary, exposing centralized orchestration authority rather than a single edge device.
· Administrative sessions were established without corresponding credential validation or MFA challenge events.
· Configuration changes propagated across multiple sites without approved change-ticket correlation.
· Firmware downgrade activity preceded configuration manipulation in observed exploitation patterns.
· SSH persistence via authorized_keys insertion enabled continued privileged access beyond the initial exploit window.
· Log continuity gaps reduced forensic reconstruction fidelity.
· Peer relationship anomalies and route advertisement deviations were secondary indicators rather than primary detection triggers.
· Governance controls focused on data-plane monitoring failed to prioritize orchestration-layer telemetry.
Key Recommendations – Immediate Controls
· Remove public exposure of all SD-WAN Manager and Controller interfaces.
· Validate firmware version integrity across all nodes and disable downgrade capability where supported.
· Rotate all administrative credentials and re-issue SSH keys.
· Enable immutable centralized logging for control-plane telemetry.
· Baseline control-connection-state-change events and peer relationships.
· Correlate configuration pushes with authenticated administrative session events.
· Alert on administrative activity outside defined maintenance windows.
Key Recommendations – Detection Enhancements
· Detect HTTP 200 responses to management endpoints without corresponding authentication log events.
· Alert on firmware regression or unexpected image checksum deviations.
· Identify SSH sessions from new ASN, geography, or non-baseline IP ranges.
· Monitor NETCONF spikes and abnormal API invocation volume.
· Detect rapid multi-site configuration propagation within compressed time windows.
· Implement automated log gap detection logic for control-plane systems.
Strategic Defensive Improvements & Hardening Initiatives
Segmentation
· Isolate SD-WAN control-plane systems from corporate and production subnets.
· Enforce jump-host mediated administrative access.
· Implement deny-by-default east-west segmentation between orchestration components.
Configuration Integrity
· Automate configuration drift detection with real-time differential alerts.
· Require formal change-ticket validation for all policy pushes.
· Maintain immutable configuration snapshots for rollback and forensic assurance.
Firmware Governance
· Maintain a trusted firmware repository with checksum validation.
· Alert on version rollback or downgrade attempts.
· Enforce signed image validation wherever supported.
Identity & Access Governance
· Enforce MFA across all privileged access paths.
· Monitor abnormal administrative login timing patterns.
· Implement privileged access management with session recording.
· Disable dormant or orphaned accounts immediately.
Logging & Telemetry Resilience
· Forward logs to WORM or immutable storage.
· Monitor log size reductions or sequence discontinuity.
· Retain control-plane logs for a minimum of 180 days.
· Correlate SSH, API, firmware, and configuration logs within SIEM.
Architectural Lesson Learned
The SD-WAN control plane must be treated as Tier Zero infrastructure. Compromise at the orchestration layer amplifies risk beyond a single device and enables enterprise-wide routing manipulation within minutes. Detection strategy must prioritize management-plane exposure, administrative session integrity, firmware integrity, configuration propagation anomalies, and log tamper detection.
Executive Takeaway
Control-plane compromise is a resilience and governance issue, not merely a patch management event. Organizations that apply identity-tier rigor to orchestration infrastructure materially reduce the probability of multi-site disruption, unauthorized routing manipulation, and extended attacker dwell time.
References
Cisco Security Advisory
· hxxps://sec[.]cloudapps[.]cisco[.]com/security/center/content/CiscoSecurityAdvisory/cisco-sa-sdwan-rpa-EHchtZk
NIST NVD
· hxxps://nvd[.]nist[.]gov/vuln/detail/CVE-2026-20127
CISA KEV
· hxxps://www[.]cisa[.]gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-20127
Tenable Nessus Plugin
· hxxps://www[.]tenable[.]com/plugins/nessus/299998