UAT-10027 Dohdoor Backdoor – Cloudflare DNS over HTTPS Command and Control Campaign
BLUF
Dohdoor is an actively deployed stealth backdoor used by threat cluster UAT-10027 targeting United States education and healthcare organizations since at least December 2025. The malware uses DNS over HTTPS routed through Cloudflare infrastructure to conceal command and control traffic within legitimate encrypted HTTPS sessions.
The campaign stages an in-memory secondary payload assessed to be Cobalt Strike Beacon, materially increasing the probability of credential theft, lateral movement, and ransomware-scale operational disruption. Encrypted DNS-based command and control reduces traditional network detection visibility, increasing dwell time and financial exposure.
Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
“For organizations affected by the Dohdoor DNS-over-HTTPS backdoor campaign leveraging Cloudflare infrastructure for covert command and control…”
· Low-end total cost: $275,000 – $650,000
(single endpoint cluster contained early; no lateral spread or data loss)
· Typical expected range: $850,000 – $2.4 million
(multi-system investigation; credential reset; limited operational disruption)
· Upper-bound realistic scenarios: $3.5 million – $8.5 million
(Beacon deployment, lateral movement, regulatory reporting, prolonged downtime)
Key Cost Drivers
Length of attacker dwell time before detection
· Whether secondary payload (e.g., Cobalt Strike) achieved domain-level access
· Number of systems requiring forensic triage and rebuild
· Operational downtime in education or healthcare environments
· Regulatory notification thresholds triggered
· Cyber insurance deductible levels and premium recalibration
Bottom Line for Executives
Dohdoor represents a covert access risk, not an immediate disruptive event. Its financial impact is driven by detection speed and scope of secondary activity — not the initial infection itself.
This campaign is best understood as a visibility stress test for encrypted DNS governance and endpoint telemetry maturity.
Executive Risk Framing
For leadership, three variables determine financial exposure:
· Duration of unauthorized access before detection
· Privileged credential exposure
· Confirmation of lateral movement or secondary tooling deployment
If contained before privilege escalation, this remains a contained incident response event.
If domain-level access or secondary tooling is confirmed, exposure expands materially due to forensic scope, credential resets, regulatory review, and operational disruption.
Financial Impact Snapshot
· Contained early, no lateral movement: $300,000 – $900,000
· Credential exposure or limited lateral movement: $1.5 million – $3 million
· Operational disruption and regulatory implications: $4 million – $8 million
o The dominant cost multiplier in this campaign is dwell time.
Strategic Implication
Encrypted DNS traffic is increasingly standard within enterprise environments. Dohdoor exploits this normalization.
The executive issue is not whether Cloudflare should be blocked.
The issue is whether encrypted outbound DNS-over-HTTPS activity is:
· Governed
· Logged
· Monitored
· Correlated to endpoint behavior
If encrypted command channels can operate without detection for extended periods, the organization carries a silent persistence risk that will only surface during escalation.
Priority Level and Response Window
· Priority Level: High
· Response Window: 72 hours for confirm-or-clear validation
· Executive Escalation Threshold: Beacon confirmation, credential harvesting, or lateral movement
Why This Matters Now
Encrypted DNS adoption continues to expand across enterprise environments. Dohdoor leverages DNS over HTTPS communications through Cloudflare infrastructure, blending malicious activity with trusted traffic flows. Organizations without DNS entropy analytics, TLS inspection, or behavioral endpoint correlation face material blind spots. Delayed detection increases regulatory, operational, and governance risk.
What We Don’t Yet Know
· Confirmed initial access vector
· Complete command and control infrastructure inventory
· Full SHA256 hashes of active payload variants
· Confirmed data exfiltration scope
· Attribution beyond UAT-10027 tracking designation
· Confirmed ransomware affiliate linkage
Exploit Conditions Snapshot
· Outbound HTTPS allowed without TLS inspection
· Public DNS over HTTPS resolvers permitted
· Incomplete PowerShell script block logging
· Weak DLL sideload monitoring
· Limited ntdll memory tampering detection
· No DNS entropy monitoring
Today’s Hunt Focus (3 signals)
· Non-browser process initiating HTTPS to Cloudflare DNS endpoints
· propsys.dll or batmeter.dll executed through legitimate Windows binaries
· PowerShell spawning batch script followed by DLL sideload execution
Sectors Affected
· Education
· Healthcare
· Managed Service Providers
Countries Affected
· United States
First Activity
· At least December 2025 for the currently documented campaign
Last Activity
· Public reporting published February 26, 2026
CVE Details
· Not applicable at this time
CVSS and CWE and KEV and Nessus and EPSS
· CVSS: Not applicable at this time
· CWE: Not applicable at this time
· CISA KEV Catalog: Not applicable at this time
· Nessus Plugin: Not applicable at this time
· EPSS Probability: Not applicable at this time
Exploit Status
· Active in the wild
· Targeted campaign
· Staged script-based loader chain
· Not automated mass exploitation
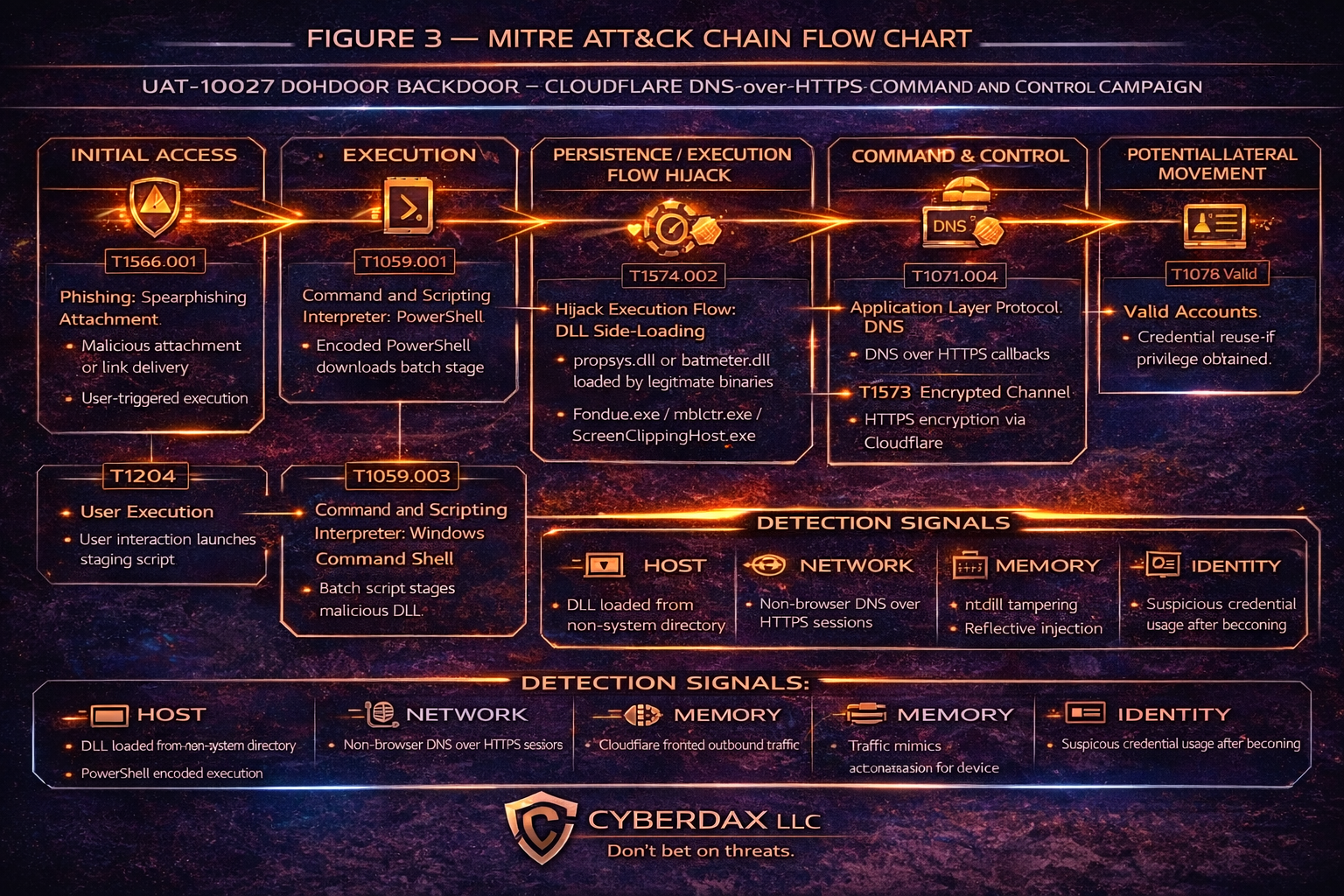
MITRE ATT&CK Chain Flow Mapping
· Initial Access
· Execution
· Persistence
· Defense Evasion
· Command and Control
· Exfiltration
o This structure forms the basis for Figure 3.
Stage-Based TTPs
Initial Access
· T1566.001 – Phishing: Spearphishing Attachment
o Suspected delivery vector initiating PowerShell execution.
· T1204 – User Execution
o User interaction required to activate malicious content.
Execution
· T1059.001 – Command and Scripting Interpreter: PowerShell
o Executes staging script and downloads batch component.
· T1059.003 – Command and Scripting Interpreter: Windows Command Shell
o Batch script stages malicious DLL.
· T1574.002 – Hijack Execution Flow: DLL Side-Loading
o propsys.dll or batmeter.dll loaded by Fondue.exe, mblctr.exe, or ScreenClippingHost.exe.
Persistence
· Not known at this time
Defense Evasion
· T1562.001 – Impair Defenses: Disable or Modify Tools
o Syscall unhooking within ntdll.dll to bypass user-mode EDR hooks.
· T1027 – Obfuscated/Compressed Files and Information
o Encrypted configuration and payload routines.
· T1055 – Process Injection
o Reflective in-memory execution of secondary payload.
Command and Control
· T1071.004 – Application Layer Protocol: DNS
o DNS over HTTPS used for C2 communications.
· T1573 – Encrypted Channel
o HTTPS encryption masks DNS query traffic.
· T1001.003 – Data Obfuscation: Protocol Impersonation
o Traffic disguised as legitimate DNS update checks.
Exfiltration
· Not known at this time
Malware and SHA256
• Dohdoor DLL (propsys.dll) – SHA256: Not applicable at this time
• Dohdoor DLL (batmeter.dll) – SHA256: Not applicable at this time
• Secondary payload assessed as Cobalt Strike Beacon – SHA256: Not applicable at this time
Behavior and Log Artifacts
Endpoint
• PowerShell encoded command execution
• Batch script staging under ProgramData or Public directories
• DLL loaded by legitimate Windows binary
• ntdll memory modification behavior
• In-memory payload retrieval
Network
• HTTPS traffic to Cloudflare infrastructure
• DNS over HTTPS request patterns
• Non-browser outbound TCP 443 sessions
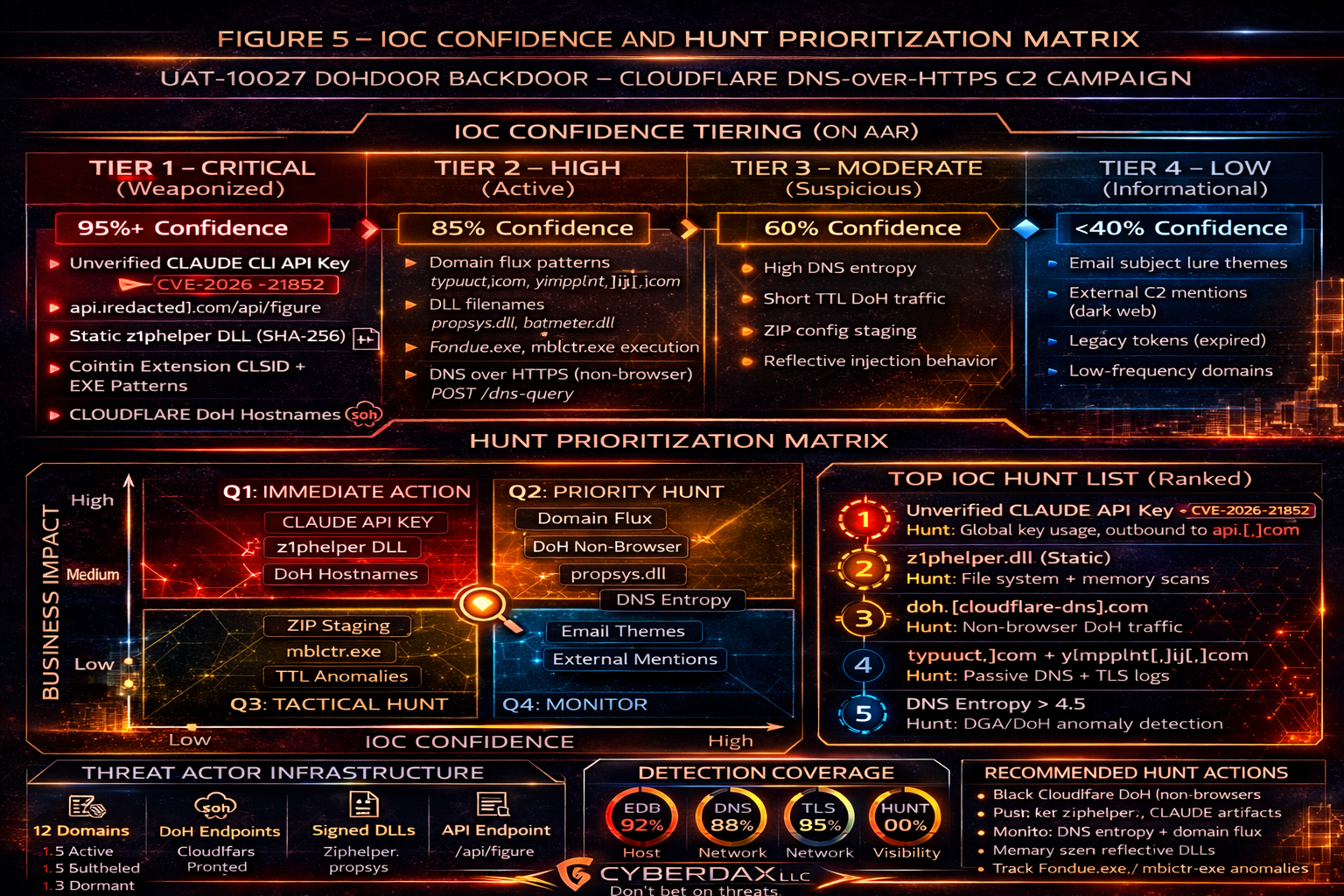
IOC Confidence and Hunt Prioritization
(numeric scores)
Network Indicators
• DNS over HTTPS C2 behavior – 90
• Cloudflare-fronted outbound HTTPS anomaly – 85
Host Indicators
• propsys.dll staged and executed – 95
• batmeter.dll staged and executed – 95
Execution Chain Indicators
• Legitimate binary DLL sideload chain – 92
• PowerShell to batch to DLL sequence – 88
Evasion Indicators
• ntdll unhooking behavior – 80
Hunt Priority Ranking
• Critical: DLL sideload detection
• High: Non-browser DoH detection
• High: ntdll tamper correlation
• Medium: Suspicious PowerShell staging without DLL
Detection Signals Layer
• Process ancestry anomaly
• DLL load from non-system directory
• Memory protection change followed by outbound 443
• Non-browser DoH session
• In-memory payload execution
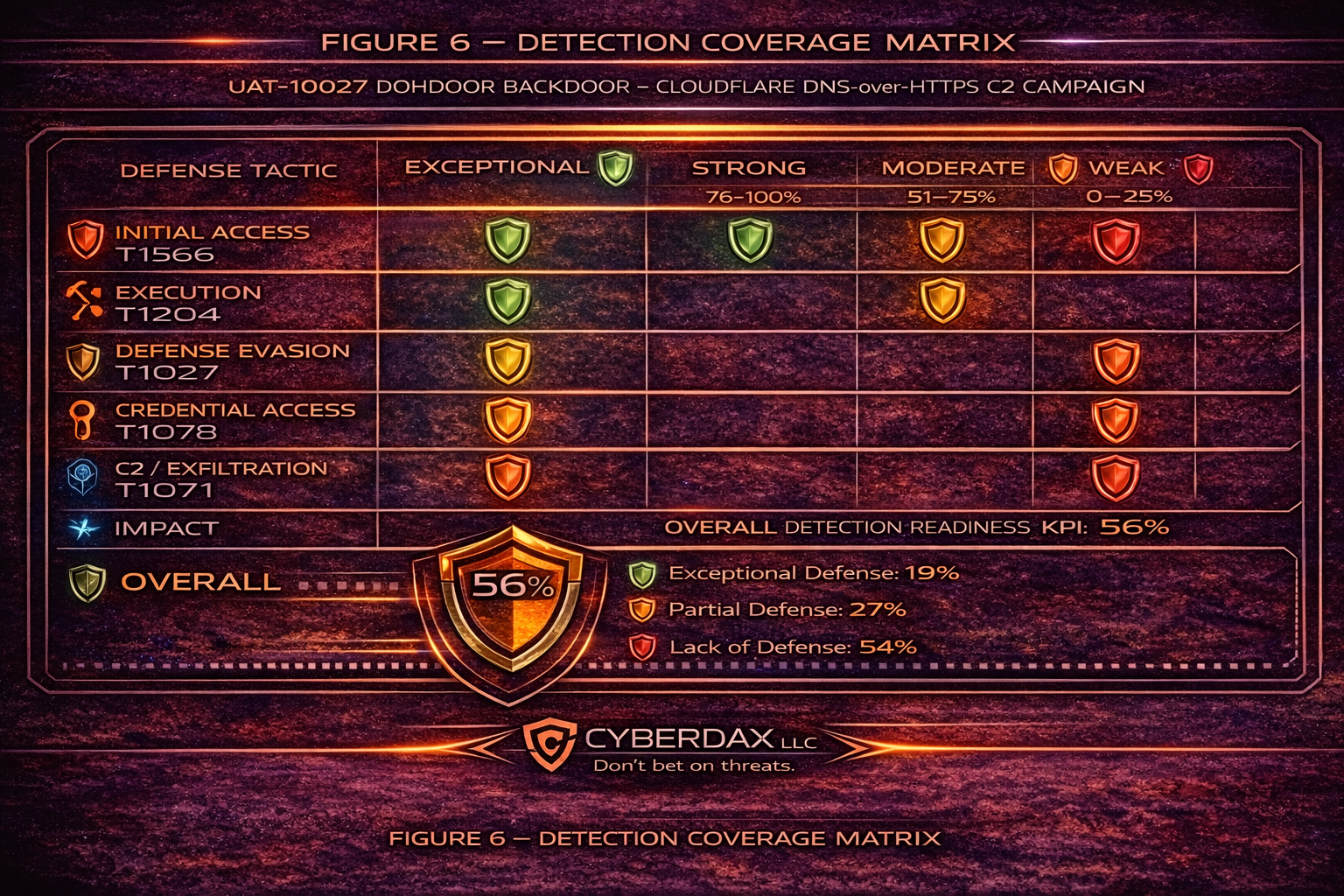
Detection Coverage Matrix
· Firewall – Limited visibility due to HTTPS encryption
· IDS – Low visibility without TLS decryption
· EDR – Moderate with user-mode bypass risk
· DNS Monitoring – Low coverage for DoH
· TLS Inspection – Often disabled
· Memory Integrity Monitoring – Rare
Detection Engineering Matrix
UAT-10027 Dohdoor Backdoor – Cloudflare DNS-over-HTTPS C2 Campaign
This section aligns directly with Figure 4 and enumerates detection logic, telemetry expectations, and engineering focus areas per MITRE ATT&CK tactic.
Initial Access – T1566.001 / T1204
Threat Behavior Summary
· Spearphishing attachment or malicious link delivery
· User-triggered execution of encoded PowerShell
Engineering Focus
· Correlate email client process → PowerShell spawn
· Alert on base64-encoded PowerShell arguments
· Detect attachment-origin execution chains
Detection Control Points
· EDR process ancestry monitoring
· PowerShell Script Block Logging
· Email gateway attachment sandboxing
Execution – T1059.001 / T1059.003
Threat Behavior Summary
· Encoded PowerShell downloads batch stage
· Batch script writes malicious DLL to non-system directory
Engineering Focus
· Identify PowerShell writing DLL files
· Detect cmd.exe execution immediately after PowerShell
· Flag file writes to ProgramData / Public paths
Detection Control Points
· EDR file creation telemetry
· Command-line logging
· Parent-child execution correlation
Persistence / Execution Flow Hijack – T1574.002
Threat Behavior Summary
· propsys.dll or batmeter.dll side-loaded
· Execution via legitimate Windows binaries (Fondue.exe, mblctr.exe, ScreenClippingHost.exe)
Engineering Focus
· Detect DLL loads from non-standard directories
· Alert on legitimate binaries executed outside default path
· Validate module hash mismatches
Detection Control Points
· EDR module load monitoring
· Windows Sysmon Event ID 7
· File integrity monitoring
Defense Evasion – T1562.001 / T1027 / T1055
Threat Behavior Summary
· ntdll syscall unhooking
· Encrypted configuration
· Reflective in-memory injection
Engineering Focus
· Detect memory protection changes to ntdll
· Alert on WriteProcessMemory followed by outbound connection
· Flag RWX memory allocation patterns
Detection Control Points
· EDR memory telemetry
· Kernel callback monitoring
· Behavioral injection heuristics
Command and Control – T1071.004 / T1573 / T1001.003
Threat Behavior Summary
· DNS over HTTPS callbacks via Cloudflare
· HTTPS encrypted tunnel masking DNS queries
· Traffic mimics legitimate DNS update behavior
Engineering Focus
· Identify non-browser DoH traffic
· Monitor DNS entropy anomalies
· Correlate Cloudflare egress with endpoint anomalies
Detection Control Points
· DNS logging
· TLS inspection (if enabled)
· Proxy logs
· JA3 / JA3S fingerprinting
Secondary Tooling – T1105 / T1055
Threat Behavior Summary
· Modular payload retrieval
· In-memory Cobalt Strike Beacon
Engineering Focus
· Detect Beacon-like network jitter patterns
· Identify sleep-beacon communication intervals
· Hunt for reflective injection artifacts
Detection Control Points
· EDR behavioral analytics
· Network anomaly detection
· Memory artifact scanning
Potential Lateral Movement – T1078
Threat Behavior Summary
· Credential reuse after C2 establishment
Engineering Focus
· Identify abnormal privileged login activity
· Correlate login anomalies after DoH C2
· Detect new service creation or SMB/RDP pivoting
Detection Control Points
· Identity provider logs
· Windows Event ID 4624 anomaly detection
· Lateral movement correlation engine
Detection Engineering Prioritization Summary
Priority Tier 1 – Immediate Engineering Validation
· Non-browser DNS over HTTPS detection
· DLL side-loading telemetry validation
· ntdll memory tampering alerts
Priority Tier 2 – High
· Beacon jitter pattern detection
· DNS entropy monitoring
· Process injection correlation
Priority Tier 3 – Tactical Enhancement
· Credential anomaly baselining
· File system artifact hunting
Suggested Rules
Suricata
Title: CYBERDAX_DOHDOOR_DoH_Pattern
Purpose: Detect suspicious DNS over HTTPS traffic
Tuning Explanation: Matches DoH URI patterns; allow-list sanctioned resolvers
alert http any any -> any any (
msg:"CYBERDAX DOHDOOR suspected DoH C2";
flow:established,to_server;
http.uri; content:"dns-query"; nocase;
sid:9909001; rev:1;
)
SentinelOne
Title: CYBERDAX_DOHDOOR_NTDLL_Unhook_Then_HTTPS
Purpose: Detect syscall tampering followed by outbound HTTPS
Tuning Explanation: Correlates memory modification and network connection within 5 minutes
EventType = "Process Modification"
AND TargetModule = "ntdll.dll"
AND EventSubType IN ("Memory Protection Change","Write Process Memory")
FOLLOWED BY
EventType = "Network Connect"
AND DestinationPort = 443
AND ProcessName NOT IN ("chrome.exe","msedge.exe","firefox.exe")
WITHIN 5m
Splunk
Title: CYBERDAX_DOHDOOR_Sideload_Chain
Purpose: Detect PowerShell to DLL sideload chain
Tuning Explanation: Correlates staged process chain within 10 minutes
index=endpoint
(process_name="powershell.exe" OR process_name="cmd.exe" OR process_name IN ("Fondue.exe","mblctr.exe","ScreenClippingHost.exe"))
| transaction host maxspan=10m
| search process_name="powershell.exe" AND process_name="cmd.exe"
Elastic
Title: CYBERDAX_DOHDOOR_NonBrowser_443
Purpose: Detect non-browser outbound HTTPS sessions
Tuning Explanation: Filters common browsers
network.transport:tcp and destination.port:443 and
not process.name:(chrome.exe or msedge.exe or firefox.exe)
Sigma
Title: CYBERDAX_DOHDOOR_DLL_Sideload
Purpose: Detect execution of noted legitimate binaries outside system paths
Tuning Explanation: Flags suspicious execution context
title: CYBERDAX DOHDOOR DLL Sideload
logsource:
category: process_creation
detection:
selection:
Image|endswith:
- '\Fondue.exe'
- '\mblctr.exe'
- '\ScreenClippingHost.exe'
condition: selection
level: high
YARA
Title: CYBERDAX_DOHDOOR_DoH_Config
Purpose: Identify DoH-related configuration strings
Tuning Explanation: Baseline triage string rule
rule CYBERDAX_DOHDOOR_DoH_Config
{
strings:
$a = "dns-query"
$b = "dns-message"
condition:
2 of them
}
Delivery Methods
· Suspected spearphishing attachment
· PowerShell staged loader
· Batch script download and DLL sideload execution
7-Day Response Plan
· Day 1
o Identify endpoints executing DLL sideload chain
· Day 2
o Inventory DNS over HTTPS usage
· Day 3
o Deploy detection rules enterprise-wide
· Day 4
o Validate EDR telemetry coverage
· Day 5
o Conduct memory triage
· Day 6
o Review segmentation and privileged access
· Day 7
o Executive containment briefing
Defensive Control and Hardening Architecture
Objective
• Prevent establishment of covert DNS-over-HTTPS command and control channels
• Detect and block DLL side-loading execution chains
• Reduce dwell time through memory tamper detection
• Limit credential abuse and lateral movement risk
• Strengthen governance visibility over encrypted outbound traffic
Layer 1
Endpoint Execution Hardening
Control Focus: Prevent malicious DLL staging and unauthorized execution chains.
· Block DLL execution from user-writable directories (ProgramData, Public, Temp)
· Enforce application control policies for Fondue.exe, mblctr.exe, ScreenClippingHost.exe
· Enable PowerShell constrained language mode where feasible
· Alert on encoded PowerShell execution
· Monitor cmd.exe spawned by PowerShell within short time window
· Restrict local administrative privileges
Risk Mitigated
· T1059.001 – Command and Scripting Interpreter: PowerShell
· T1059.003 – Windows Command Shell
· T1574.002 – DLL Side-Loading
Layer 2
DLL Integrity & Module Load Monitoring
Control Focus: Detect execution flow hijacking.
· Enable Sysmon Event ID 7 (Image Loaded) enterprise-wide
· Alert on DLL loads from non-system directories
· Validate digital signatures for loaded modules
· Monitor unexpected module load paths for legitimate Windows binaries
· Enforce file integrity monitoring on high-risk directories
Risk Mitigated
· T1574.002 – Hijack Execution Flow: DLL Side-Loading
Layer 3
Memory Protection & EDR Hardening
Control Focus: Detect defense evasion via syscall unhooking and injection.
· Alert on memory protection changes to ntdll.dll
· Monitor WriteProcessMemory followed by outbound network activity
· Detect reflective injection and RWX memory allocations
· Enable kernel-level telemetry to reduce user-mode bypass risk
· Validate EDR tamper protection policies
Risk Mitigated
· T1562.001 – Impair Defenses
· T1055 – Process Injection
· T1027 – Obfuscated/Compressed Files
Layer 4
DNS-over-HTTPS Governance Controls
Control Focus: Prevent covert command channel establishment.
· Restrict DNS-over-HTTPS usage to approved resolvers
· Alert on non-browser processes initiating DoH traffic
· Monitor outbound HTTPS traffic to Cloudflare IP ranges by non-browser processes
· Implement DNS entropy anomaly detection
· Correlate endpoint anomalies with DoH sessions
Risk Mitigated
· T1071.004 – Application Layer Protocol: DNS
· T1573 – Encrypted Channel
· T1001.003 – Protocol Impersonation
Layer 5
Egress Filtering & Network Hardening
Control Focus: Reduce C2 survivability.
· Block outbound HTTPS from non-approved system binaries
· Restrict newly registered or low-reputation domains
· Monitor ASN deviations for outbound traffic
· Enable TLS inspection where governance permits
· Baseline normal DNS query frequency per host
Risk Mitigated
· T1041 – Exfiltration Over C2 Channel
· T1105 – Ingress Tool Transfer
Layer 6
Credential & Identity Controls
Control Focus: Reduce blast radius if secondary tooling deployed.
· Enforce multi-factor authentication across privileged accounts
· Monitor abnormal logon patterns following DoH establishment
· Detect credential reuse from unusual source systems
· Restrict lateral movement via SMB and RDP segmentation
· Implement privileged access management controls
Risk Mitigated
· T1078 – Valid Accounts
Layer 7
Logging & Telemetry Retention
Control Focus: Reduce dwell time through improved visibility.
· Enable full PowerShell Script Block Logging
· Retain DNS logs with query entropy metadata
· Centralize endpoint, memory, and network telemetry in SIEM
· Implement cross-domain correlation rules (Process → Memory → Network)
· Retain logs for minimum 180 days for retrospective hunting
Risk Mitigated
· Prolonged undetected persistence
· Delayed forensic reconstruction
Layer 8
Governance & Executive Oversight Controls
Control Focus: Align detection maturity with enterprise risk tolerance.
· Establish encrypted traffic governance policy
· Implement executive reporting for detection readiness gaps
· Conduct quarterly adversary simulation targeting DoH channels
· Track detection coverage KPI against MITRE ATT&CK mapping
· Require documented approval for DNS-over-HTTPS enablement
Risk Mitigated
· Visibility maturity gaps
· Unmonitored encrypted command channels
Architectural Outcome
When fully implemented, this layered defensive model:
· Reduces probability of DLL side-loading success
· Detects syscall tampering earlier
· Prevents unauthorized DNS-over-HTTPS command channels
· Limits credential-based lateral movement
· Shortens attacker dwell time
· Improves enterprise encrypted traffic governance
· Aligns technical controls to executive risk posture
Estimated Probability of Recurrence (12-month horizon)
High
Drivers
Encrypted DNS growth
Active campaign
Cloudflare fronting reduces detection
Flexible secondary payload staging
Post-Incident Insights and Recommendations
CyberDax Strategic Defensive Improvements Framework
This heading will be used in all future CyberDax LLC reports following Figure 8.
Post-Incident Insights
Encrypted DNS as a Covert Channel
• DNS-over-HTTPS traffic blended with legitimate encrypted outbound activity
• Browser impersonation techniques reduced signature-based detection reliability
• Lack of non-browser DoH visibility extended dwell time
Operational Insight:
Encrypted DNS must be governed as a privileged protocol, not treated as default benign traffic.
DLL Side-Loading Remains Highly Effective
• Legitimate Windows binaries executed attacker-controlled DLLs
• Application allowlisting alone did not prevent execution flow hijacking
• Module load visibility gaps enabled stealth persistence
Operational Insight:
Execution context validation is more important than binary reputation alone.
Syscall Unhooking and Memory Tampering Reduce EDR Visibility
• ntdll memory modification bypassed user-mode hooks
• Reflective injection avoided traditional file-based artifacts
• Delayed detection increased response cost and forensic complexity
Operational Insight:
Kernel-level telemetry and memory anomaly monitoring are essential for modern endpoint defense.
4. Secondary Tooling Drives Financial Escalation
• Once C2 established, follow-on tooling increases breach scope
• Credential reuse enables pivot risk across trust boundaries
• Financial exposure correlates directly to dwell time duration
Operational Insight:
Initial access containment window is the primary cost control lever.
Strategic Recommendations
Immediate (0–30 Days)
• Enable detection for non-browser DNS-over-HTTPS traffic
• Alert on DLL loads from non-system directories
• Monitor memory protection changes to ntdll
• Hunt for PowerShell encoded command execution artifacts
• Validate EDR tamper protection policies
Near-Term (30–90 Days)
• Implement DNS entropy anomaly monitoring
• Correlate endpoint process telemetry with encrypted egress
• Restrict execution of legitimate binaries from non-default paths
• Harden privileged account monitoring baselines
Long-Term (Strategic Maturity)
• Establish encrypted traffic governance policy
• Integrate process → memory → network behavioral correlation models
• Conduct adversary simulation exercises targeting DoH channels
• Implement enterprise dwell-time KPI tracking
•[ ]Align detection readiness metrics to board-level reporting
Architectural Improvement Outcome
When implemented, these improvements:
• Reduce probability of covert DNS-over-HTTPS command channels
• Shorten attacker dwell time
• Increase DLL side-loading detection accuracy
• Limit credential pivot potential
• Improve executive visibility into encrypted traffic risk
• Strengthen alignment between technical controls and financial exposure tolerance
References (Reporting Group, URL)
Cisco Talos Intelligence Group
· hxxps[:]//thehackernews[.]com/2026/02/uat-10027-targets-us-education-and.html
MITRE Corporation – ATT&CK Enterprise Matrix
· hxxps[:]//attack[.]mitre[.]org/matrices/enterprise/
Cloudflare – DNS over HTTPS Documentation
· hxxps[:]//developers[.]cloudflare[.]com/1.1.1.1/encryption/dns-over-https/
Microsoft – Dynamic-Link Library Search Order Documentation
· hxxps[:]//learn[.]microsoft[.]com/windows/win32/dlls/dynamic-link-library-search-order
Microsoft – Windows Memory Protection and Process Injection APIs
· hxxps[:]//learn[.]microsoft[.]com/windows/win32/api/memoryapi/