Grid Tide (GRIDTIDE) Global Espionage Campaign Leveraging Google Sheets API for Command and Control (UNC2814)
BLUF
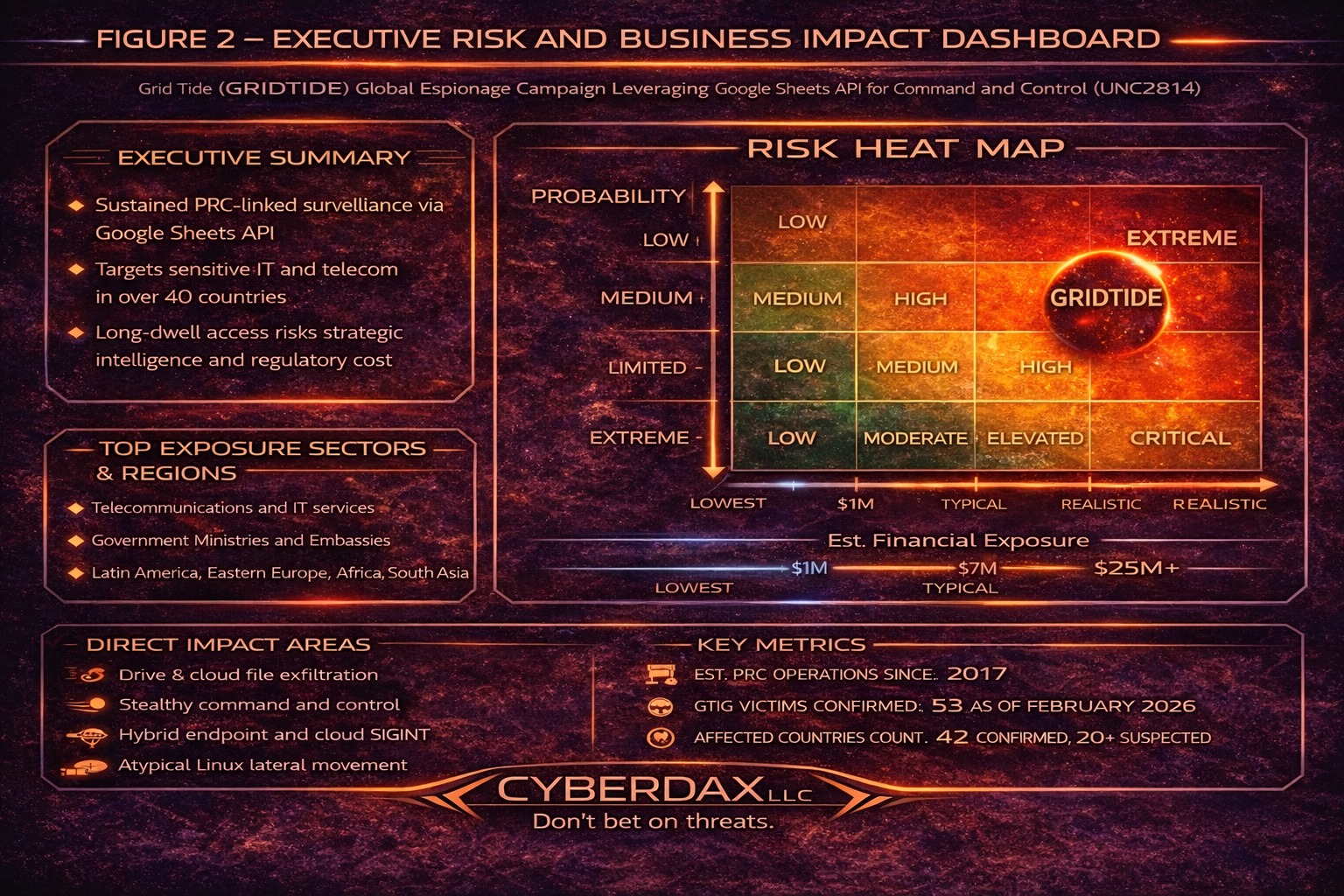
A PRC-nexus espionage actor tracked as UNC2814 conducted a global intrusion campaign using the GRIDTIDE backdoor, embedding command and control within legitimate Google Sheets API traffic to enable stealthy, long-dwell access inside victim environments. As of February 18, 2026, 53 confirmed victims across 42 countries have been identified, primarily in telecommunications and government sectors, with suspected activity in at least 20 additional countries. GRIDTIDE provides remote shell execution and file transfer capability and appears positioned for strategic surveillance objectives, including access to systems containing sensitive and personally identifiable information.
This campaign does not exploit a vulnerability in Google products. It represents deliberate abuse of trusted SaaS APIs, meaning defensive success depends on identity governance, endpoint telemetry, and API activity correlation rather than traditional exploit-centric controls alone.
This campaign demonstrates how trusted SaaS infrastructure can function as covert operational backbone for nation-state activity.
Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
For organizations affected by Grid Tide espionage activity using SaaS API command and control and long-dwell access on Linux servers, the estimated financial impact typically clusters as follows:
· Low-end total cost: $450,000 – $1,250,000
(single segment affected, rapid containment, limited identity compromise)
· Typical expected range: $1,500,000 – $6,500,000
(multiple servers impacted, broad hunting, moderate notification scope)
· Upper-bound realistic scenarios: $7,000,000 – $22,000,000
(extended dwell, regulated data exposure, multi-country legal response)
Key Cost Drivers
· Number of affected business units, regions, and regulated datasets
· Time-to-detection and dwell time driving scope of forensic review
· Identity and service account reset complexity and downstream outage risk
· External counsel and regulatory response breadth across jurisdictions
· Customer or partner notification volume and credit monitoring commitments
Executive Bottom Line for Executives
Grid Tide–style activity represents a strategic surveillance risk rather than a systems failure event. Financial impact is driven primarily by investigation scope, identity remediation, regulatory coordination, and executive oversight once long-dwell access is discovered.
For mid-size to large organizations, realistic exposure most commonly falls between $1.5 million and $6.5 million, with escalation into the low eight-figure range when regulated data, cross-border notification, or litigation becomes involved.
From a board and C-suite perspective:
· This is a governance and visibility stress test, not an infrastructure rebuild.
· Extended dwell time or insufficient logging materially increases financial exposure.
· Regulatory and legal response frequently exceed technical containment costs.
· Mature SaaS telemetry, service account discipline, and documented oversight significantly compress downstream financial impact.
Strategic takeaway
Organizations that elevate cloud API monitoring and identity governance to board-level risk controls reduce volatility, shorten response timelines, and contain total cost exposure.
Priority Level and Response Window
· Priority Level: Critical
· Response Window:
o First 4 hours: Hunt and contain active C2 and persistence
o First 24 hours: Eradicate implants and compromised identities, validate no residual access
o First 72 hours: Complete environment-wide sweep, implement durable detections and hardening
Why This Matters Now
· Adversaries are increasingly using trusted cloud services as covert command channels, which reduces defender advantage from perimeter controls and domain blocking because traffic appears as normal business HTTPS to reputable endpoints.
· Telecom and government environments carry outsized regulatory, geopolitical, and reputational exposure; long-dwell surveillance access can translate into strategic intelligence loss, customer harm, and downstream incident costs even without overt encryption or disruption.
· Google and partners disrupted known infrastructure, but GTIG explicitly expects UNC2814 to work to re-establish global footprint, so defenders should treat this as an active and adaptive threat.
What we don’t yet know
· Initial access vector for the campaign has not been determined.
· Extent of confirmed data exfiltration for specific victims is not directly observed by GTIG for this campaign, though the access pattern is consistent with espionage and historical telecom intrusions.
· Full scope of victim list, dwell time per victim, and whether all intrusions used GRIDTIDE versus adjacent tooling is not known.
Exploit Conditions Snapshot
· Preconditions:
o Attacker foothold on a Linux server, observed on CentOS
o Ability to execute binaries and establish persistence via systemd
o Outbound HTTPS connectivity to Google APIs
o Local presence of a 16-byte cryptographic key file used to decrypt Google Drive configuration for Sheets access
· Core enabling conditions:
o Abuse of Google Service Account credentials embedded in encrypted configuration, used to authenticate to Google Sheets API
o API call patterns consistent with batchClear and sheet cell polling for command retrieval
Today’s Hunt Focus (3 signals)
· Non-browser processes making outbound HTTPS requests to Sheets API endpoints, especially with URIs containing batchClear, batchUpdate, or valueRenderOption=FORMULA
· Creation or modification of suspicious configuration files in sensitive or atypical directories such as /usr/sbin, /sbin, or /var/tmp ending in .cfg
· systemd persistence artifacts referencing xapt.service and execution of /usr/sbin/xapt or /var/tmp/xapt, including nohup execution
Sectors / Countries Affected
Sectors affected:
· Telecommunications providers, primary focus
· Government organizations
Countries affected:
Confirmed:
· 42 countries across four continents, with 53 confirmed victims as of February 18, 2026
Suspected:
· At least 20 additional countries with suspected infections
· Regional concentration indicators reported in secondary coverage:
· Primary impact described as concentrated in Latin America, Eastern Europe, Africa, and parts of South Asia
First Activity
· Infrastructure and activity linked to UNC2814 is assessed as active since at least 2017, with IOCs related to infrastructure used since at least 2023.
· VPN configuration metadata suggests related infrastructure use since July 2018.
Last Activity
· Confirmed impacts as of February 18, 2026, with disruption actions disclosed February 25, 2026.
CVE Details
· This campaign is technique-driven rather than vulnerability-driven.
· Notes:
o This campaign is explicitly described as not being the result of a security vulnerability in Google products.
o Historical UNC2814 access patterns include exploiting and compromising web servers and edge systems, but no specific CVE is attributed in the disclosure.
CVSS and CWE and KEV and Nessus and EPSS
· CVSS: Not known at this time
· CWE: Not known at this time
· CISA KEV: Not known at this time
· Nessus: Not known at this time
· EPSS: Not known at this time
Exploit Status
· Confirmed:
o Active exploitation of victim environments by UNC2814 with deployment of GRIDTIDE in real intrusions
· Not confirmed:
o Specific exploit chain or vulnerability identifiers used for initial foothold
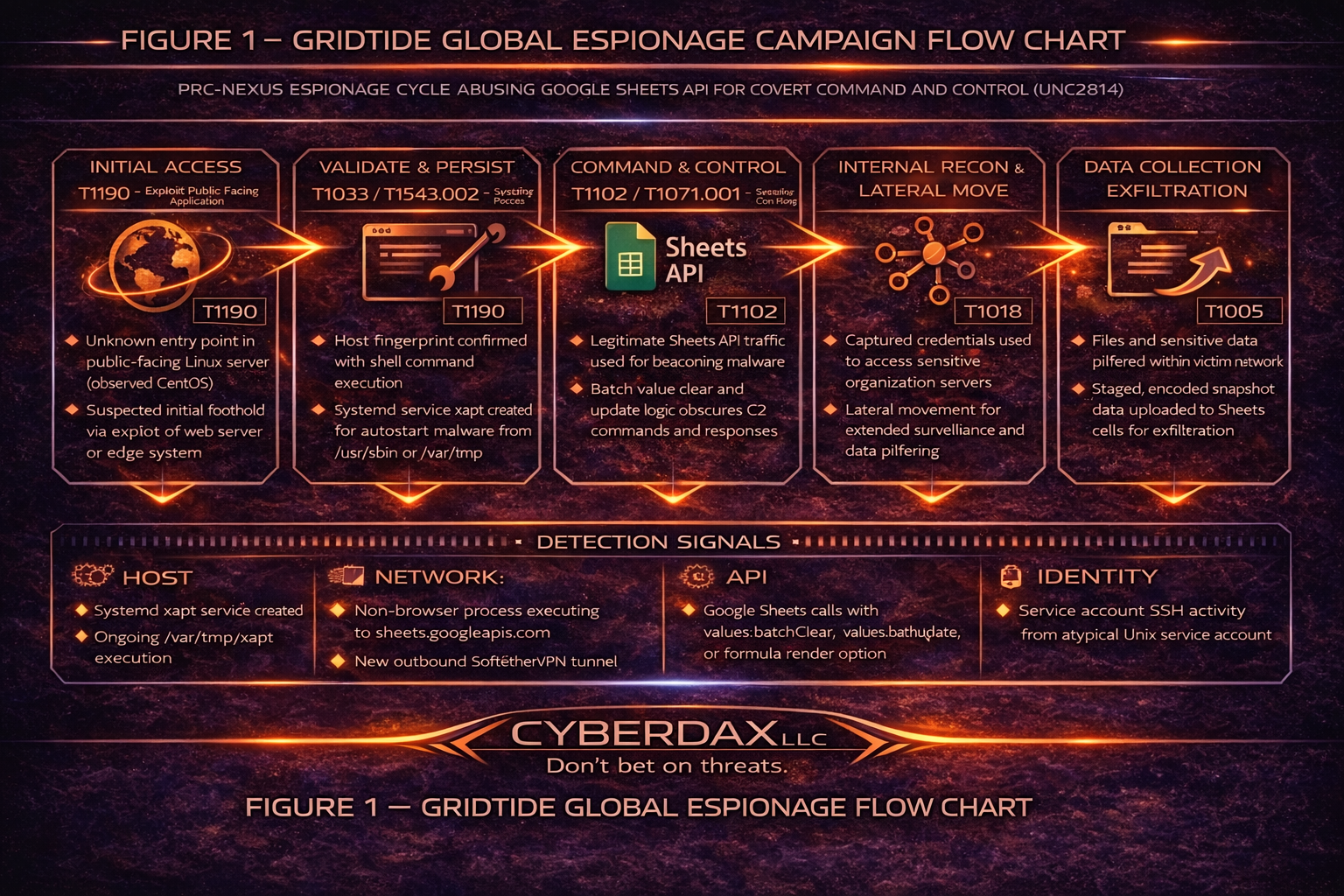
MITRE ATT&CK Chain Flow Mapping
· Reconnaissance and resource development:
o T1583.001 – Acquire Infrastructure: Domains
o T1583.002 – Acquire Infrastructure: DNS Server
o T1587.001 – Develop Capabilities: Malware
· Initial access:
o T1190 – Exploit Public-Facing Application (historical pattern noted, not confirmed for this campaign)
· Execution:
o T1059.004 – Command and Scripting Interpreter: Unix Shell
· Privilege escalation and validation:
o T1069.001 – Permission Groups Discovery: Local Groups (supporting discovery)
o T1033 – System Owner or User Discovery
o T1082 – System Information Discovery
· Persistence:
o T1543.002 – Create or Modify System Process: Systemd Service
· Defense evasion:
o T1036 – Masquerading (xapt naming to resemble legitimate tooling)
o T1027 – Obfuscated Files or Information (URL-safe Base64)
· Credential access:
o Not known at this time
· Discovery:
o T1016 – System Network Configuration Discovery
o T1049 – System Network Connections Discovery
· Lateral movement:
o T1021.004 – Remote Services: SSH
· Command and control:
o T1102 – Web Service (SaaS API based command channel)
o T1071.001 – Application Layer Protocol: Web Protocols
· Exfiltration:
o T1567.002 – Exfiltration to Cloud Storage (via spreadsheet as exchange channel)
Stage-Based TTPs (MITRE ID, Title, how used)
· Stage 1: Initial foothold
o T1190 – Exploit Public-Facing Application
§ How used: UNC2814 is described as historically gaining entry by exploiting web servers and edge systems; specific method for this campaign is not determined
· Stage 2: Privilege escalation confirmation
o T1059.004 – Unix Shell
§ How used: /var/tmp/xapt spawning shell and running sh -c id to validate root privileges
· Stage 3: Internal movement
o T1021.004 – SSH
§ How used: Threat actor used a service account to move laterally via SSH
· Stage 4: Persistence establishment
o T1543.002 – Systemd Service
§ How used: /etc/systemd/system/xapt.service created; service spawns malware instance from /usr/sbin/xapt
· Stage 5: Command and control setup
o T1102 – Web Service
§ How used: Google Sheets API used as high-availability C2, treating the sheet as a communications channel
o T1071.001 – Web Protocols
§ How used: HTTPS API calls to sheets.googleapis.com including batchClear and batchUpdate patterns
· Stage 6: Data staging and potential exfiltration
o T1567.002 – Exfiltration to Cloud Storage
§ How used: Data and command outputs staged in spreadsheet cell ranges A2 through An and host fingerprint stored in V1
· Stage 7: Alternate encrypted tunnel
o T1090 – Proxy (supporting concept)
§ How used: SoftEther VPN Bridge deployed to establish outbound encrypted connection to external infrastructure
Malware and SHA256
· GRIDTIDE and related host-based artifacts:
o xapt (GRIDTIDE): ce36a5fc44cbd7de947130b67be9e732a7b4086fb1df98a5afd724087c973b47
o xapt.cfg (key file): 01fc3bd5a78cd59255a867ffb3dfdd6e0b7713ee90098ea96cc01c640c6495eb
o xapt.service (systemd persistence): eb08c840f4c95e2fa5eff05e5f922f86c766f5368a63476f046b2b9dbffc2033
o hamcore.se2 (SoftEtherVPN component): 4eb994b816a1a24cf97bfd7551d00fe14b810859170dbf15180d39e05cd7c0f9
o fire (SoftEtherVPN component, renamed from vmlog): 4eb994b816a1a24cf97bfd7551d00fe14b810859170dbf15180d39e05cd7c0f9
o vpn_bridge.config (SoftEther configuration): 669917bad46a57e5f2de037f8ec200a44fb579d723af3e2f1be1e8479a267966
Behavior and Log Artifacts
· Endpoint process artifacts:
o /var/tmp/xapt spawning /bin/sh and executing sh -c id 2>&1
o nohup execution pattern for persistence of xapt
· Filesystem artifacts:
o /etc/systemd/system/xapt.service creation and enablement
o /usr/sbin/xapt presence and execution
o .cfg file used as key material for AES decryption of Google Drive configuration
· Network artifacts:
o Outbound HTTPS to sheets.googleapis.com with batchClear and batchUpdate usage
o SoftEther VPN Bridge outbound encrypted connection patterns
· Cloud API artifacts:
o Google Sheets API batchClear used to clear first 1000 rows across columns A to Z
o Spreadsheet cell roles:
§ A1 for command polling and status responses
§ A2 through An for file and output transfer
§ V1 for victim fingerprint metadata
IOC Confidence and Hunt Prioritization (numeric scores)
Scoring scale:
o 90 to 100: High-confidence, campaign-specific indicators
o 70 to 89: Strong indicators with some reuse risk
o 40 to 69: Contextual indicators requiring correlation
High-confidence host-based IOCs (95):
o ce36a5fc44cbd7de947130b67be9e732a7b4086fb1df98a5afd724087c973b47 (xapt)
o 01fc3bd5a78cd59255a867ffb3dfdd6e0b7713ee90098ea96cc01c640c6495eb (xapt.cfg)
o eb08c840f4c95e2fa5eff05e5f922f86c766f5368a63476f046b2b9dbffc2033 (xapt.service)
High-confidence network IOCs (90):
o 130.94.6.228 (C2 server hosting apt.tar.gz and related archives)
o 38.60.194.21 (SoftEtherVPN server)
o 38.180.205.14 (target of curl -ik test)
Strong domain IOCs (85):
o mms.bumbleshrimp.com
o modgood.gleeze.com
o mysql.casacam.net
o transport.dynuddns.net
Contextual behavior indicators (60):
o Non-browser process to sheets.googleapis.com with batchClear patterns
o systemd service creation in /etc/systemd/system combined with xapt naming and nohup execution
Detection Signals Layer
· Identity and access signals:
o Service account usage for lateral movement via SSH where service account context is atypical for the host role
· Endpoint signals:
o Executable launched from /var/tmp with short alphanumeric filename spawning a shell
o Creation of systemd unit file xapt.service and subsequent execution from /usr/sbin/xapt
· Network and proxy signals:
o Outbound HTTPS connections to sheets.googleapis.com from non-browser processes targeting batchClear, batchUpdate, or formula rendering endpoints
o SoftEther VPN Bridge traffic to known IPs and new outbound tunnels following systemd persistence events
· Data movement signals:
o Repeated small and regular API polling patterns consistent with A1 polling and periodic backoff behavior
o URL-safe Base64 payload patterns in HTTP bodies or logs where available
Detection Coverage Matrix
· Endpoint detection and response:
o Covers:
§ /var/tmp execution and shell spawning
§ systemd unit creation and suspicious service enablement
§ nohup persistence behavior
o Gaps:
§ Pure API abuse without malware on endpoints
· Network detection and response:
o Covers:
§ Known malicious IPs, SoftEther tunnel endpoints
§ Unusual process-based egress classification
o Gaps:
§ Legitimate Google endpoints require behavioral detections, not blocking
· Cloud and SaaS logs:
o Covers:
§ API call volume anomalies to Sheets endpoints, especially batchClear
§ OAuth and service account usage anomalies if your environment has visibility
o Gaps:
§ If API visibility is limited to perimeter logs only, fine-grained request path inspection may be missing
· Security analytics and SIEM:
o Covers:
§ Correlation rules tying endpoint process lineage to specific API destinations
§ Multi-signal detections aligning host events with network egress
o Gaps:
§ Requires normalized process to network telemetry mapping
Detection Engineering Matrix
Initial Access – T1190 (Exploit Public-Facing Application)
Threat Behavior Summary
· Initial foothold obtained on internet-facing Linux server
· Exploitation of exposed application or weak service configuration
· Dropper or shell execution from atypical directories
· Immediate outbound HTTPS to Google Sheets API endpoints
Engineering Focus
· Detect shell execution from /tmp or /var/tmp
· Identify process spawning from web service parent (nginx, apache, gunicorn)
· Correlate new outbound HTTPS session immediately following exploitation
· Alert on non-browser HTTPS traffic to sheets.googleapis.com
Detection Control Points
· EDR process lineage telemetry
· Web server logs
· Proxy and firewall egress logs
· IDS HTTPS inspection metadata
Execution & Persistence – T1059.004 (Unix Shell) / T1543.002 (Create or Modify System Process: Systemd Service)
Threat Behavior Summary
· nohup or background shell execution
· Creation of systemd service (xapt.service or variant)
· Binary staged in /var/tmp or disguised system path
· Persistence survives reboot
Engineering Focus
· Alert on new systemd unit file creation
· Detect execution from /var/tmp with executable permission change
· Identify abnormal service names not matching baseline
· Correlate persistence creation with outbound Sheets API traffic
Detection Control Points
· File integrity monitoring
· systemd service creation logs
· EDR command-line telemetry
· SIEM correlation rules
Credential Access & Lateral Movement – T1552.001 (Unsecured Credentials) / T1021.004 (SSH)
Threat Behavior Summary
· SSH key harvesting from typical directories
· Service account SSH pivoting
· Lateral movement between Linux hosts
· Distinct host-to-host pivot chain
Engineering Focus
· Detect SSH from non-interactive service accounts
· Identify new SSH key reads across multiple hosts
· Alert on SSH sessions from atypical ASN or geography
· Correlate lateral movement after persistence establishment
Detection Control Points
· SSH authentication logs
· Identity audit logs
· EDR network telemetry
· SIEM geo/ASN enrichment
Command and Control – T1071.001 (Application Layer Protocol: Web Protocols) / T1102 (Web Service)
Threat Behavior Summary
· Persistent HTTPS beaconing to sheets.googleapis.com
· API calls to values:batchUpdate or values:batchClear
· Use of valueRenderOption=FORMULA parameter
· A1 cell polling and A2–An data upload pattern
Engineering Focus
· Detect non-browser Sheets API usage
· Identify OAuth tokens used by server-side processes
· Alert on regular polling interval beacon pattern
· Correlate Sheets API activity with systemd persistence
Detection Control Points
· Proxy logs
· CASB telemetry
· API gateway logs
· OAuth token monitoring
Defense Evasion – T1036 (Masquerading) / T1070 (Indicator Removal)
Threat Behavior Summary
· Binary named to resemble system process
· Execution from trusted directory
· Log manipulation or minimal artifact footprint
· Blended normal HTTPS traffic
Engineering Focus
· Detect process masquerading via name mismatch vs. binary path
· Identify unusual parent-child process relationships
· Alert on sudden reduction in log verbosity
Monitor HTTPS user-agent anomalies
Detection Control Points
· EDR behavioral analytics
· Log integrity validation
· Network user-agent inspection
· SIEM anomaly detection logic
Impact / Data Exfiltration – T1041 (Exfiltration Over C2 Channel)
Threat Behavior Summary
· Data staged locally before upload
· Encoded content transmitted to Google Sheets cells
· Gradual exfiltration to avoid volume-based detection
· Long-dwell espionage objective
Engineering Focus
· Detect encoded outbound payload patterns
· Identify unusual POST payload structure to Sheets endpoints
· Correlate file read activity preceding API calls
· Alert on prolonged Sheets API session persistence
Detection Control Points
· DLP inspection
· Proxy content logging
· EDR file access telemetry
· CASB data transfer monitoring
Detection Engineering Prioritization Summary (GRIDTIDE)
Priority Tier 1 – Immediate Validation
· Non-browser Sheets API beacon detection
· systemd persistence creation alerts
· OAuth token abuse from server process
· Correlated persistence + API activity
Priority Tier 2 – High
· SSH service account lateral movement
· Suspicious execution from /var/tmp
· Abnormal Sheets API volume spikes
Priority Tier 3 – Tactical Enhancement
· User-agent anomaly detection
· OAuth token lifecycle baselining
· Encoded payload inspection tuning
Suggested Rules
Suricata
Detection Intent: Detects potential GRIDTIDE command-and-control traffic by identifying non-standard Google Sheets API usage patterns associated with batchClear, batchUpdate, and formula-rendering parameters.
Purpose:
Identify outbound HTTPS sessions to Sheets API paths linked to known campaign behaviors.
Tuning Guidance:
Require URI constraints and pair with endpoint telemetry to reduce false positives from legitimate Google API usage. Treat as Stage 1 signal requiring correlation.
alert tls $HOME_NET any -> $EXTERNAL_NET 443 (
msg:"GRIDTIDE stage1: TLS SNI sheets.googleapis.com";
flow:established,to_server;
tls.sni; content:"sheets.googleapis.com"; nocase;
classtype:trojan-activity;
sid:4202814001; rev:2;
)
alert http $HOME_NET any -> $EXTERNAL_NET 443 (
msg:"GRIDTIDE stage1: Sheets API values endpoints of interest";
flow:established,to_server;
http.host; content:"sheets.googleapis.com"; nocase;
http.uri; pcre:"/\/v4\/spreadsheets\/[^\\s]+\/values(:batchUpdate|:batchClear)|valueRenderOption=FORMULA/i";
classtype:trojan-activity;
sid:4202814002; rev:2;
)
alert ip $HOME_NET any -> $EXTERNAL_NET any (
msg:"GRIDTIDE stage1: Known GTIG IOC IP contact";
flow:established,to_server;
dst_ip:130.94.6.228;
classtype:trojan-activity;
sid:4202814003; rev:2;
)
Splunk (Correlation Rule)
Detection Intent: Raises high-severity alert when Linux persistence artifacts correlate with non-browser Sheets API traffic on the same host within a defined time window.
Purpose:
Elevate severity only when endpoint execution behavior aligns with suspicious Sheets API access.
Tuning Guidance:
Exclude approved automation hosts and require persistence artifacts within ±15 minutes of API activity.
| multisearch
[ search index=suricata (alert.signature_id=4202814002 OR alert.signature_id=4202814001)
| eval host=coalesce(src_host, host, dest_host)
| eval s_time=_time
| table host s_time alert.signature_id alert.signature ]
[ search index=proxy (dest_host="sheets.googleapis.com" OR url_domain="sheets.googleapis.com")
(uri_path="*/v4/spreadsheets/*/values:batchUpdate*" OR uri_path="*/v4/spreadsheets/*/values:batchClear*" OR uri_query="*valueRenderOption=FORMULA*")
| eval host=coalesce(src_host, host)
| eval p_time=_time
| table host p_time uri_path uri_query user user_agent ]
[ tstats summariesonly=false count min(_time) as e_first max(_time) as e_last
from datamodel=Endpoint.Processes
where (Processes.process_path="/var/tmp/xapt" OR Processes.process_path="/usr/sbin/xapt"
OR like(Processes.process,"%nohup%") OR like(Processes.process,"%sh -c id%"))
by Processes.dest Processes.user Processes.process_path Processes.process_name
| eval host=Processes.dest
| eval e_time=e_last
| table host e_time Processes.user Processes.process_path Processes.process_name count ]
| stats
min(s_time) as suricata_time
min(p_time) as proxy_time
min(e_time) as edr_time
by host
| eval window_ok = if(
abs(suricata_time - proxy_time) <= 900 AND abs(proxy_time - edr_time) <= 900,
"true","false"
)
| where window_ok="true"
SentinelOne
Detection Intent: Identifies GRIDTIDE-style Linux persistence and execution behavior combined with suspicious Google Sheets API egress.
Purpose:
Detect systemd service creation, execution from atypical directories, and Sheets API communication from non-browser processes.
Tuning Guidance:
Scope to Linux servers and require multi-signal correlation for high-confidence alerting.
EventType = Process Creation
AND (ProcessPath CONTAINS "/var/tmp/xapt" OR ProcessPath CONTAINS "/usr/sbin/xapt")
AND (CommandLine CONTAINS "nohup" OR CommandLine CONTAINS "sh -c id")
EventType = File Creation
AND TargetFilePath = "/etc/systemd/system/xapt.service"
EventType = Network Connection
AND DestinationDomain CONTAINS "sheets.googleapis.com"
AND InitiatingProcessPath NOT CONTAINS "/chrome"
AND InitiatingProcessPath NOT CONTAINS "/firefox"
AND InitiatingProcessPath NOT CONTAINS "/safari"
AND InitiatingProcessPath NOT CONTAINS "/msedge"
Elastic
Detection Intent: Detects Linux persistence artifacts and correlates them with Google Sheets API usage consistent with GRIDTIDE command-and-control behavior.
Purpose:
Identify suspicious systemd service creation, execution from non-standard paths, and outbound Sheets API calls.
Tuning Guidance:
Filter for Linux systems and require either persistence artifacts or anomalous API path usage for alerting.
(
event.category:process and host.os.type:linux and
(
process.executable:"/var/tmp/xapt" or
process.executable:"/usr/sbin/xapt" or
process.command_line:*"nohup"*
)
)
or
(
event.category:file and host.os.type:linux and
file.path:"/etc/systemd/system/xapt.service"
)
or
(
event.category:network and
destination.domain:"sheets.googleapis.com" and
url.path:(*batchClear* or *batchUpdate* or *valueRenderOption=FORMULA*)
)
Sigma
Detection Intent: Detects creation and execution of GRIDTIDE-related persistence artifacts on Linux systems.
Purpose:
Alert on systemd service creation and execution of binaries from atypical directories associated with GRIDTIDE.
Tuning Guidance:
Pair with a separate rule monitoring Sheets API egress to elevate severity.
title: GRIDTIDE Linux xapt Systemd Persistence
id: 2b0f2a5e-2814-4f5a-9b3b-000000000001
status: stable
logsource:
product: linux
category: file_event
detection:
selection:
TargetFilename: "/etc/systemd/system/xapt.service"
condition: selection
level: high
---
title: GRIDTIDE Linux xapt Execution From Var Tmp Or Usr Sbin
id: 2b0f2a5e-2814-4f5a-9b3b-000000000002
status: stable
logsource:
product: linux
category: process_creation
detection:
selection:
Image|contains:
- "/var/tmp/xapt"
- "/usr/sbin/xapt"
selection_cmd:
CommandLine|contains:
- "nohup"
- "sh -c id"
condition: selection or (selection and selection_cmd)
level: high
YARA
Detection Intent: Identifies potential GRIDTIDE binaries by matching distinctive strings tied to Google Sheets API interaction and cell-based command channel logic.
Purpose:
Support malware hunting and triage validation of suspected binaries.
Tuning Guidance:
Use as hunting rule; confirm via hash comparison against known campaign samples.
rule GRIDTIDE_Sheets_API_C2_Hunt
{
meta:
description = "Hunt for potential GRIDTIDE samples leveraging Google Sheets API cell-based C2"
author = "CyberDax LLC"
reference = "GTIG GridTide campaign writeup"
strings:
$s1 = "sheets.googleapis.com" ascii nocase
$s2 = "batchClear" ascii nocase
$s3 = "batchUpdate" ascii nocase
$s4 = "valueRenderOption=FORMULA" ascii nocase
$s5 = "A1" ascii
$s6 = "V1" ascii
$s7 = "AES-128" ascii nocase
$s8 = "CBC" ascii nocase
condition:
3 of ($s*)
}
Delivery Methods
· Likely entry and staging:
o Not known at this time for initial access vector
o Historical pattern includes exploitation of web servers and edge systems
· Observed delivery and installation behaviors:
o Download of archives including apt.tar.gz from 130.94.6.228, containing GRIDTIDE
o Additional archives update.tar.gz and amp.tar.gz associated with SoftEtherVPN Bridge components
o Execution of xapt from /var/tmp followed by persistence as systemd service
7-Day Response Plan
· Day 1
o Block and alert on known malicious IPs and domains where safe to do so
o Sweep for xapt, xapt.cfg, xapt.service, pmp variants, and listed SHA256 values
o Identify any hosts with non-browser Sheets API activity patterns described by GTIG
· Day 2
o For confirmed hosts:
§ Isolate, memory capture if required, remove persistence, rotate credentials
§ Hunt laterally for SSH movements from service accounts
· Day 3
o Enforce egress policy:
§ Require proxy inspection logging for API request paths to sheets.googleapis.com
§ Add correlation rules in SIEM tying process lineage to API egress
· Day 4
o Validate no residual access:
§ Check for SoftEther artifacts and outbound tunnels
§ Review systemd services for anomalies across fleet
· Day 5
o Hardening:
§ Reduce internet exposure of edge systems
§ Apply least privilege for service accounts and SSH
§ Implement command allowlists and privileged access monitoring
· Day 6
o Tabletop and detection validation:
§ Simulate API misuse patterns to ensure detections fire
§ Validate alert routing to SOC playbooks and on-call
· Day 7
o Executive and regulator-ready summary:
§ Confirm scope, dwell, and remediation completion
§ Document control improvements and monitoring commitments
Defensive Control and Hardening Architecture
Objective
· Prevent covert SaaS-based command and control over Google Sheets API
· Detect Linux persistence mechanisms leveraging systemd services
· Disrupt OAuth token abuse and unauthorized API usage
· Reduce lateral movement via SSH service account compromise
· Strengthen governance visibility over SaaS API telemetry and identity controls
Layer 1
External Exposure & Attack Surface Reduction
Control Focus: Minimize initial foothold opportunity on internet-facing Linux systems.
· Eliminate unnecessary public-facing services and management ports
· Enforce reverse proxy or WAF protection for exposed applications
· Disable unused web modules and APIs
· Restrict administrative interfaces to VPN or bastion-only access
· Apply virtual patching for internet-exposed services
Risk Mitigated
· T1190 – Exploit Public-Facing Application
· T1595 – Active Scanning
Layer 2
Linux Persistence & System Integrity Hardening
Control Focus: Prevent unauthorized system-level persistence.
· Restrict systemd service creation to privileged change windows
· Enforce file integrity monitoring on /etc/systemd and /var/tmp
· Alert on execution from world-writable directories
· Disable execution permissions in /tmp and /var/tmp where feasible
· Harden service account permissions to least privilege
Risk Mitigated
· T1543.002 – Create or Modify System Process: Systemd Service
· T1059.004 – Unix Shell
· Long-dwell persistent foothold
Layer 3
Identity & SSH Access Governance
Control Focus: Prevent credential harvesting and SSH-based lateral movement.
· Disable password-based SSH authentication
· Enforce key-based SSH with lifecycle governance
· Rotate service account keys regularly
· Restrict service account SSH to explicit host allowlists
· Enforce MFA for all interactive administrative access
Risk Mitigated
· T1552.001 – Unsecured Credentials
· T1021.004 – Remote Services: SSH
· T1078 – Valid Accounts
Layer 4
SaaS API Abuse Prevention & OAuth Governance
Control Focus: Prevent covert command and control through Google Sheets API.
· Enforce OAuth token issuance monitoring and approval workflows
· Alert on server-side processes invoking Sheets API endpoints
· Restrict API token scope to least privilege
· Implement CASB monitoring for Google Workspace APIs
· Block non-approved service accounts from Sheets API usage
Risk Mitigated
· T1071.001 – Application Layer Protocol: Web Protocols
· T1102 – Web Service
· Covert SaaS-based C2
Layer 5
Network-Level Containment
Control Focus: Reduce survivability of covert outbound C2.
· Implement deny-by-default outbound filtering
· Require proxy inspection for all HTTPS egress
· Alert on non-browser traffic to sheets.googleapis.com
· Baseline normal Sheets API volume and polling intervals
· Detect ASN or geography anomalies for outbound sessions
Risk Mitigated
· T1071.001 – Web Protocols
· T1041 – Exfiltration Over C2 Channel
Layer 6
Content-Level Detection
Control Focus: Detect structured data staging and slow exfiltration.
· Enable DLP inspection for outbound HTTPS
· Monitor encoded payload structures in API POST requests
· Detect repeated A1 polling and A2–An upload patterns
· Alert on large or anomalous Sheets API write operations
· Enforce API rate limits and anomaly thresholds
Risk Mitigated
· T1041 – Exfiltration Over C2 Channel
· Long-duration stealth exfiltration
Layer 7
Log Integrity & Anti-Tamper Controls
Control Focus: Prevent defense evasion and prolonged dwell time.
· Forward host logs to centralized immutable storage
· Enforce write-once retention for critical telemetry
· Alert on log truncation or abrupt logging silence
· Validate systemd and auth logs for continuity
· Maintain minimum 180-day searchable log retention
Risk Mitigated
· T1070 – Indicator Removal on Host
· Prolonged undetected persistence
Layer 8
Governance & Executive Oversight Controls
Control Focus: Elevate SaaS API and identity abuse risk to enterprise governance level.
· Classify SaaS API abuse as Tier Zero identity risk
· Establish executive reporting on OAuth and API telemetry
· Conduct quarterly red-team simulation of SaaS-based C2
· Map detection coverage to MITRE ATT&CK techniques
· Require formal approval for high-scope service account privileges
Risk Mitigated
· Governance visibility gaps
· Long-dwell espionage risk
· Undetected SaaS-based command infrastructure
Architectural Outcome
When fully implemented, this layered defensive model:
· Eliminates unmanaged Linux persistence vectors
· Disrupts covert Google Sheets API command channels
· Prevents unauthorized OAuth token misuse
· Reduces SSH-based lateral movement risk
· Detects slow, structured exfiltration patterns
· Shortens attacker dwell time in Linux environments
· Aligns SaaS API abuse protection with executive-level risk governance
Estimated Probability of Recurrence (12-month horizon)
· Estimated Probability of Recurrence:
o 55 percent for telecom and government entities with internet-exposed edge systems and limited SaaS API telemetry
§ Technique reuse risk remains elevated due to SaaS abuse model.
o 25 percent for organizations with strong egress controls, endpoint enforcement, and API-aware detections
· Rationale:
o GTIG expects UNC2814 will work to re-establish footprint after disruption and the technique leverages legitimate cloud functionality rather than exploit-specific infrastructure.
Post-incident insights and recommendations
· Make SaaS API abuse detectable:
o Capture and retain proxy logs with URL paths for Google APIs
o Alert on batchClear and batchUpdate sequences to Sheets from non-browser user agents or non-interactive hosts
· Treat service accounts as privileged identities:
o Monitor SSH usage from service accounts, enforce key rotation, require just-in-time elevation
· Reduce Linux persistence surface:
o File integrity monitoring on /etc/systemd/system
o Alert on creation of new unit files and service enablement
· Apply staged containment:
o Do not indiscriminately block Google endpoints; isolate by host, process, and identity context
· Institutionalize correlation:
o Any combination of systemd service creation, var tmp execution, and Sheets API calls should be high-severity by default
References (Reporting Group, URL)
• Google Threat Intelligence Group and Mandiant
hxxps://cloud[.]google[.]com/blog/topics/threat-intelligence/disrupting-gridtide-global-espionage-campaign
• The Register
hxxps://www[.]theregister[.]com/2026/02/25/google_and_friends_disrupt_unc2814/
• The Hacker News
hxxps://thehackernews[.]com/2026/02/google-disrupts-unc2814-gridtide[.]html
• SecurityWeek
hxxps://www[.]securityweek[.]com/google-disrupts-chinese-cyberespionage-campaign-targeting-telecoms-governments/