CVE-2026-20841 Windows Notepad App Remote Code Execution via Markdown Link Handling
Figure 1 campaign flow chart
BLUF
A high-severity Notepad RCE (CVSS 8.8) exists in Windows 11 Notepad (≤ 11.2510) where a user can be socially engineered into clicking a malicious Markdown link that triggers execution of local/remote content via non-HTTP(s) URI/protocol handlers. Microsoft has released a fix (Notepad update that adds warnings for non-http/hxxps links). There are no confirmed in-the-wild exploitation reports at this time.
Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
“For organizations affected by exploitation of the Windows 11 Notepad Markdown link remote code execution vulnerability (CVE-2026-20841), financial exposure varies significantly depending on containment speed and whether follow-on compromise occurs.”
· Low-end total cost: $250,000 – $500,000
o Single-user compromise, rapid containment, no lateral movement
· Typical expected range: $750,000 – $2.5 million
o Multi-endpoint exposure, enterprise-wide hunting, limited business disruption
· Upper-bound realistic scenarios: $3 million – $8 million
o Credential theft, lateral movement, data exposure requiring notification
Key Cost Drivers
· Speed of patch deployment across Windows 11 endpoints
· Presence (or absence) of EDR detection on Notepad child processes
· Privilege level of the initially compromised user
· Whether UNC/remote payload staging enabled lateral movement
· Data sensitivity within the compromised user’s access scope
Bottom Line for Leadership
This vulnerability is not inherently catastrophic. However, its low barrier to weaponization and broad deployment footprint Windows Notepad make it a cost-amplifier if patching and endpoint monitoring are delayed.
Proactive update enforcement and process-chain detection materially reduce financial exposure and keep potential impact in the lower cost band.
Potential affected sectors
· Government / Public Sector
· Finance
· Healthcare
· Education
· Technology / IT Services
· Critical Infrastructure orgs with Windows 11 admin/user workstations
(This is broad exposure rather than sector-targeted reporting.)
Potential impacted countries
· Potentially global
Date of first reported activity
· Feb 10, 2026
Date of last reported activity update
· Feb 11, 2026
Why This Matters to Defenders
· Very low attacker cost
o Weaponization can be as simple as a crafted .md file plus social engineering (phishing/IM lure).
· Execution happens in the user context
o Compromise impact scales with user privileges and can be chained into credential theft/lateral movement.
· Abusable protocol handlers
o File and URI link handling can allow a simple document open action to trigger code execution, often with little visible warning—especially if a user approves a prompt or is running an older, unpatched version.
Associated APT groups
· None known at this time
Associated Criminal Organizations
· None known at this time
Tools used in campaign
· No campaign tooling is confirmed.
o Public discussion indicates ease-of-exploit via crafted Markdown and links/URIs (PoC-style).
CVE-2026-20841
CVSS:3.1
· (8.8) AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H\
Nessus ID
· 298646
Is this on the CISA KEV list?
· Not at this time.
Patching / Mitigation Data
Patch release date
· Feb 2026 Patch Tuesday timeframe (Feb 10, 2026); public reporting ties the fix to February 2026 Patch Tuesday updates.
Mitigation notes
(practical)
· Ensure Store-delivered Notepad updates are not blocked.
· Consider enterprise controls:
o AppLocker/WDAC rules to restrict execution from user-writable locations.
o Reduce or restrict risky protocol handlers (where feasible) and monitor use.
What is the exploitability?
· Practical exploit path exists but requires User Interaction (UI:R) (user opens .md and clicks link / Ctrl+Click).
Has there been observed exploitation?
· No known exploitation in the wild per public reporting referencing Microsoft’s position.
What is the exposure risk?
· Moderate-to-High, driven by:
o Broad default deployment of Notepad
o Very simple lure delivery (email/IM/download)
o Endpoint-level execution in user context
…but reduced by required user click and availability of patch/auto-update via Microsoft Store.
Recommended action
· Update Notepad to a fixed version (ensure > 11.2510; confirm via installed app version inventory).
· Temporarily disable/limit Markdown rendering in Notepad (where manageable) and/or restrict untrusted .md handling.
· Add detections for Notepad spawning interpreters/installers and for Notepad-driven access to remote shares/URIs (details below).
· Security awareness: treat .md attachments/links as active content.
Malware associated with CVE-2026-20841
· There is no malware associated with CVE-2026-20841 at this time
Exposure Assessment Tool
Practical checks
1) Endpoint version inventory
· Identify hosts with Notepad ≤ 11.2510 (at-risk per Tenable plugin title).
2) Local validation (Windows)
· Confirm whether Notepad displays warnings for non-http/hxxps URIs when clicking links (expected post-fix behavior).
3) Hunt for suspicious behavior (high-signal)
· notepad.exe spawning:
o cmd.exe, powershell.exe, wscript.exe, cscript.exe, mshta.exe, rundll32.exe, regsvr32.exe
· Notepad accessing remote UNC paths shortly after .md open (SMB share execution chain).
IOCs
Because no confirmed exploitation campaign is reported, below are behavioral / analytic IOCs (not hard attribution indicators):
High Confidence IOCs
Markdown Files Containing Non-HTTP URI Schemes
Indicator: Unsafe URI schemes embedded in Markdown links
Examples:
· file://
· ms-appinstaller://
· ms-settings:
Why it matters:
· This is the core exploit trigger mechanism in CVE-2026-20841.
Notepad Launching External Protocol Handlers or Child Processes
Indicator: notepad.exe spawning suspicious executables
Examples:
· notepad.exe → cmd.exe
· notepad.exe → powershell.exe
· notepad.exe → mshta.exe
· notepad.exe → rundll32.exe
Why it matters
· Exploitation requires Notepad to invoke an external handler leading to execution.
Medium Confidence IOCs
UNC Path Execution Embedded in Markdown Links
Indicator: Remote share execution references in .md files
Example:
\\attacker\share\payload.exe
Why it matters
· UNC execution is a plausible payload delivery path through Markdown link abuse.
Markdown Lure Files Opened from Common Delivery Locations
Indicator: .md file opened from user-controlled directories
Example Paths:
· C:\Users\<user>\Downloads\*.md
· C:\Users\<user>\Desktop\*.md
Why it matters
· These are typical phishing attachment drop locations.
Low Confidence IOCs
Immediate Network Connections After Markdown Link Interaction
Indicator: Outbound traffic shortly after Notepad link click
Examples:
· SMB connections to remote hosts
· HTTP/S downloads of secondary payloads
Why it matters
· Follow-on tooling may require remote payload retrieval, but this is not unique to this CVE.
Suspicious Protocol Handler Invocation Events
Indicator: Execution of unusual registered URI handlers
Examples:
· shell: URIs
· Custom protocol handlers
· Non-standard Windows URI execution events
Why it matters
· Attackers may abuse protocol handlers, but legitimate applications also use them.
Confidence Summary
High
· Non-HTTP URI schemes in Markdown
· Notepad spawning execution processes
Medium
· UNC share execution links
· .md lure files in Downloads/Desktop
Low
· Post-click network activity
· Protocol handler invocation telemetry
Figure 2 MITRE attack chain chart
TTPs
Stage: Initial Access
· T1566.001 Phishing Spearphishing Attachment
o Deliver a crafted .md file to a user; lure them to open in Notepad and click the embedded link. (Plausible/likely delivery pattern for document-style lures.)
· T1204.002 User Execution Malicious File
o User opens the Markdown file and performs the required click/Ctrl+click action.
Stage: Execution
· T1059 – Command and Scripting Interpreter
o If the link triggers execution of cmd.exe/PowerShell or launches a scriptable payload after initial execution. (Not inherent, but a common post-compromise step.)
· T1106 – Native API
o Payloads executed may use native Windows APIs once launched.
Stage: Defense Evasion / Persistence / Lateral Movement
· T1036 Masquerading
· T1112 Modify Registry
· T1021.002 SMB/Windows Admin Shares
Figure 3 MITRE ATT&CK Chain
Behavior Analysis (what it looks like)
· User opens .md in Notepad (Markdown mode enabled).
· User clicks a malicious link that uses a non-http(s) URI/protocol.
· On vulnerable versions, the click can result in launching “unverified protocols” and executing remote/local content; newer versions show warnings for non-http(s) schemes.
Expected User-Agent patterns
· None reliable
o This is primarily local protocol-handling/OS behavior. If the chain triggers web fetches, UA depends on the handler/application (not stable enough to key on confidently).
Payload examples
(conceptual)
· Markdown with clickable link referencing:
o file://C:/Users/.../payload.exe
o \\attacker\share\payload.exe
o ms-appinstaller://?...
(Examples are derived from publicly described mechanisms; not provided as weaponized code.)
Log Artifacts
(high-value)
Windows (recommended telemetry)
· Security 4688 (Process Creation): child process launched by notepad.exe
· Sysmon 1 (Process Create): same, but richer
· Sysmon 3 (Network Connect): Notepad/protocol handler → remote host
· SMB logs (e.g., 5145 where enabled): access to remote executables shortly after .md open
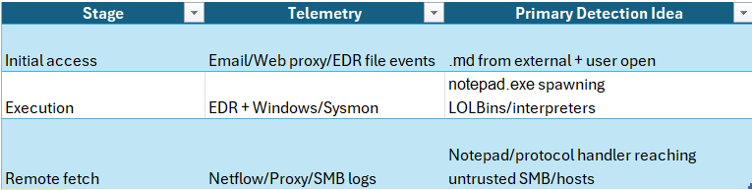
Figure 4 Table Detection Coverage Matrix
Detection coverage by control type
EDR (high value)
· Parent/child chains from Notepad; app protocol launches
Network (medium)
· SMB remote binary pulls; unusual outbound after .md open
SIEM (high)
· Correlation rules: Notepad open → process spawn → network
Suggested rules / potential hunts
Suricata
CVE-2026-20841 HUNT – Markdown lure retrieved (sets xbit)
o Uses a tight .md filename pattern (reduces .md5, weird suffixes).
o Biases toward Windows UA (optional but reduces noise).
o Requires a response-side hint (Content-Type or Content-Disposition suggests an actual file download)
alert http $HOME_NET any -> $EXTERNAL_NET $HTTP_PORTS (
msg:"CVE-2026-20841 HUNT Markdown (.md) retrieved - set xbit for follow-on SMB execution chain";
flow:established,to_server;
http.method; content:"GET"; nocase;
/* Stronger URI match (avoid common false positives like .md5, .md~ etc.) */
http.uri; pcre:"/\/[^?\s]{1,260}\.md(?:\?|$)/Ui";
/* Optional: bias toward typical lure delivery (tune/remove if too strict) */
http.request_headers; pcre:"/User-Agent\x3a[^\r\n]*(Windows|Win64|WOW64)/i";
/* Increase confidence: server responds with markdown-ish types (best effort) */
flow:to_client;
http.response_headers; pcre:"/(Content-Type\x3a[^\r\n]*(text\/markdown|text\/plain|application\/octet-stream)|Content-Disposition\x3a[^\r\n]*filename=\"?[^\r\n\"]+\.md\"?)/i";
/* Set a host-scoped bit for the SRC (client) for 10 minutes */
xbits:set,cve_2026_20841_md_lure,track ip_src,expire 600;
classtype:trojan-activity;
sid:99028410; rev:3;
metadata:service http, cve CVE-2026-20841, confidence high, deployment perimeter;
)
CVE-2026-20841 HUNT – SMB fetch of EXE/DLL/PS1 after Markdown lure
o It only fires when the same host recently pulled a .md (via xbits).
o It narrows SMB to 445 and focuses on high-risk extensions (exe|dll|ps1).
o Optional extra constraints push it toward higher-suspicion paths/shares.
alert smb $HOME_NET any -> $EXTERNAL_NET 445 (
msg:"CVE-2026-20841 HUNT SMB access to executable/script shortly after .md lure (possible Notepad Markdown->SMB execution chain)";
flow:established,to_server;
/* Only alert if the client recently downloaded a .md lure */
xbits:isset,cve_2026_20841_md_lure,track ip_src;
/* Best-effort file extension match for Windows payload types */
pcre:"/\\\S{1,260}\.(exe|dll|ps1)(\x00)?$/i";
/* Reduce noise: many benign SMB accesses occur; focus on suspicious patterns */
/* Common attacker-ish shares/paths (optional; remove if too strict) */
pcre:"/(\\\S{1,80}\\(users|programdata|windows|temp|appdata)\\|\\\S{1,80}\\(public|admin\$|c\$)\\)/i";
classtype:trojan-activity;
sid:99028411; rev:3;
metadata:service smb, cve CVE-2026-20841, confidence medium, deployment internal;
)
SentinelOne
CVE-2026-20841 — Notepad spawning suspicious child processes with UNC/URL/user-writable indicators
What this does (why it’s tuned)
· Requires Notepad as the parent (high signal for this CVE chain).
· Requires a known LOLBin / interpreter as the child.
· Requires one of the key execution pivots: UNC path, URL, or user-writable path.
· Adds an optional “abuse pattern” gate (encoded PowerShell, IEX, certutil, etc.) to reduce noise.
· If that last block is too restrictive for your environment, remove the final AND (...)
section.event_type = "Process Creation"
AND parent_process_name ~= "notepad.exe"
AND (
process_name ~= "cmd.exe" OR
process_name ~= "powershell.exe" OR
process_name ~= "wscript.exe" OR
process_name ~= "cscript.exe" OR
process_name ~= "mshta.exe" OR
process_name ~= "rundll32.exe" OR
process_name ~= "regsvr32.exe"
)
AND (
process_cmdline contains "\\\\" OR
process_cmdline matches "(?i)https?://" OR
process_cmdline matches "(?i)\\\(users|programdata)\\.*\\\(downloads|desktop|appdata|temp|tmp)\\"
)
AND (
/* Optional tuning: reduce benign noise by focusing on script/LOLBin abuse patterns */
process_cmdline matches "(?i)(-enc|encodedcommand|frombase64string|iex|downloadstring|invoke-webrequest|bitsadmin|certutil|msiexec|rundll32\\s+javascript:|scrobj\\.dll)"
OR process_name ~= "mshta.exe"
OR process_name ~= "regsvr32.exe"
)
Alternate version (path-based, catches renamed binaries)
Use this if your tenant records full paths more reliably than names:
event_type = "Process Creation"
AND parent_process_path endswith "\\notepad.exe"
AND (
process_path endswith "\\cmd.exe" OR
process_path endswith "\\powershell.exe" OR
process_path endswith "\\wscript.exe" OR
process_path endswith "\\cscript.exe" OR
process_path endswith "\\mshta.exe" OR
process_path endswith "\\rundll32.exe" OR
process_path endswith "\\regsvr32.exe"
)
AND (
process_cmdline contains "\\\\" OR
process_cmdline matches "(?i)https?://" OR
process_cmdline matches "(?i)\\users\\[^\\]+\\(downloads|desktop|appdata|temp)\\"
)
Splunk
· CVE-2026-20841 suspicious Notepad child process
index=win* (EventCode=4688 OR source="XmlWinEventLog:Microsoft-Windows-Sysmon/Operational" EventCode=1)
(ParentImage="*\\notepad.exe" OR ParentProcessName="notepad.exe")
(Image="*\\cmd.exe" OR Image="*\\powershell.exe" OR Image="*\\wscript.exe" OR Image="*\\cscript.exe" OR Image="*\\mshta.exe" OR Image="*\\rundll32.exe" OR Image="*\\regsvr32.exe")
| stats count min(_time) as firstSeen max(_time) as lastSeen values(CommandLine) as cmd values(ParentImage) as parent by host user Image
| convert ctime(firstSeen) ctime(lastSeen)
YARA
file-content heuristic for malicious Markdown lures
· Title: Potential Notepad Markdown RCE Lure (URI Schemes)
· Rule Notepad_Markdown_URI_Lure_CVE_2026_20841
{
meta:
description = "Heuristic: Markdown containing risky URI schemes discussed in CVE-2026-20841 writeups"
reference = "CVE-2026-20841"
confidence = "medium"
strings:
$md_link = /\[[^\]]{1,80}\]\([^)]+\)/ nocase
$s1 = "ms-appinstaller://" nocase
$s2 = "ms-settings:" nocase
$s3 = "file://" nocase
$s4 = "\\\\" // UNC path indicator
condition:
$md_link and 1 of ($s1,$s2,$s3,$s4)
}
Sigma
process chain
· Notepad Spawning Suspicious Child Process (Possible CVE-2026-20841 Chain)
id: 5c7caa8e-6e76-4ac0-9f6f-3d2c6b2f8a41
status: experimental
Description
· Detects notepad.exe spawning common LOLBins/interpreters; investigate for malicious Markdown link execution chain.
references:
- CVE-2026-20841
logsource:
product: windows
category: process_creation
detection:
selection_parent:
ParentImage|endswith: '\notepad.exe'
selection_child:
Image|endswith:
- '\cmd.exe'
- '\powershell.exe'
- '\wscript.exe'
- '\cscript.exe'
- '\mshta.exe'
- '\rundll32.exe'
- '\regsvr32.exe'
condition: selection_parent and selection_child
falsepositives:
- Rare legitimate workflows; validate with command line and parent chain
level: high
Delivery Methods
(likely)
· Phishing email or chat message with .md attachment or link to download .md (“documentation”, “release notes”, “incident report”, “runbook”, “invoice”, “PO details”).
o Dev/IT themed lures are especially plausible given .md normality in engineering contexts.
Verdict
· High-severity, easily lured user-interaction RCE on Windows 11 Notepad (≤ 11.2510). Patch immediately and add process-chain detections. No confirmed in-the-wild exploitation reported yet, but the exploit pattern is low-friction and likely to be adopted rapidly.
Primary Objectives
(Expected if exploited)
· Initial foothold on endpoint
· Execute payload in user context
· Stage follow-on tooling for credential theft / persistence (depends on attacker)
What we don’t know
(as of now)
· Any confirmed threat actor adoption (APT/criminal) using this CVE.
· Any reliable IOCs (domains, hashes, infrastructure) tied to real intrusions.
· Definitive KEV status from authoritative CISA feeds in this environment (feeds are access-restricted here).
Steps to consider over the next 7 days
· Inventory Notepad versions; prioritize updating anything ≤ 11.2510.
· Deploy detections for notepad.exe spawning interpreters/LOLBins (EDR + SIEM).
· Hunt retrospectively (30–90 days): .md opens followed by process spawn/network access.
· Restrict execution from user-writable paths (WDAC/AppLocker) where feasible.
· Review protocol handler exposure and monitor non-http(s) handler invocations.
· Awareness push: treat .md as active content; warn against clicking embedded links in untrusted markdown.
· Add Nessus coverage using plugin 298646 and validate scan results.
References
NVD
· hxxps://nvd.nist.gov/vuln/detail/CVE-2026-20841
Tenable
· hxxps://www.tenable.com/cve/CVE-2026-20841/plugins
Bleeping Computer
· hxxps://www.bleepingcomputer.com/news/microsoft/windows-11-notepad-flaw-let-files-execute-silently-via-markdown-links/
The Register
· hxxps://www.theregister.com/2026/02/11/notepad_rce_flaw/
MSRC Microsoft
· hxxps://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841