Apple dyld Memory Corruption Leading to Arbitrary Code Execution (Exploited in the Wild) CVE-2026-20700
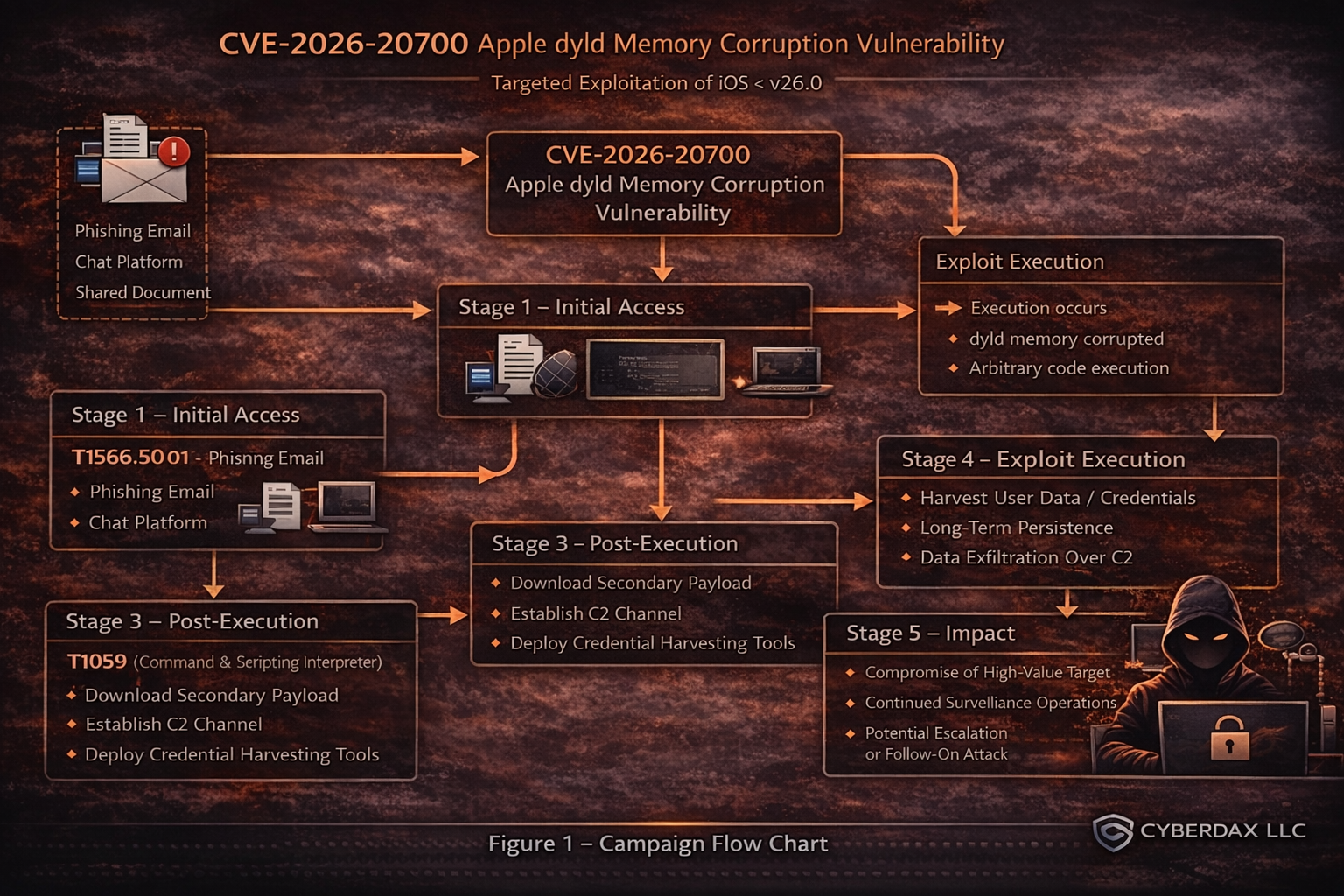
Figure 1 Cybersecurity attack flow chart CVE-2026-20700
BLUF
CVE-2026-20700 is an Apple dyld (Dynamic Link Editor) memory corruption vulnerability that can allow arbitrary code execution when an attacker already has memory write capability, and Apple states it may have been exploited in an extremely sophisticated attack against specific targeted individuals on iOS versions before iOS 26. CISA’s enrichment on the NVD record includes a direct reference to the CISA Known Exploited Vulnerabilities (KEV) catalog entry for this CVE, meaning defenders should treat this as an actively exploited, priority patch across iOS/iPadOS/macOS/watchOS/tvOS/visionOS and aggressively validate fleet compliance to the fixed releases (26.3).
Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
“For organizations affected by the in-the-wild exploitation of Apple dyld memory corruption (CVE-2026-20700) across iOS/macOS fleets, the primary financial exposure comes from rapid incident response, device remediation, and executive-targeted compromise containment.”
· Low-end total cost: $250K – $750K
o Limited device exposure, fast patching, no confirmed persistence
· Typical expected range: $1.5M – $5M
o Enterprise Apple footprint, targeted user investigations, partial operational disruption
· Upper-bound realistic scenarios: $6M – $15M
o Multi-device compromise, extended forensics, regulatory/legal escalation for executives
Key Cost Drivers
Scale of unpatched Apple endpoint population requiring urgent remediation
Depth of forensic review needed for high-risk executive and VIP devices
Business disruption from accelerated patch enforcement and device isolation
External IR and legal advisory hours ($400–$1,200/hr) during active response
Downstream credential/session resets and access revalidation across systems
Regulatory exposure if surveillance or sensitive data access is confirmed
Bottom Line for Leadership
CVE-2026-20700 represents a priority, in-the-wild exploited Apple endpoint vulnerability with financial exposure driven by rapid response, VIP-focused investigation, and compliance-driven escalation, not broad operational collapse.
For most mid-to-large enterprises, realistic total costs cluster in the $1.5M – $5M range, with upper-bound scenarios reaching $15M when compromise expands beyond a small targeted cohort.
Potential affected sectors
· Government / public sector (incl. high-value officials)
· Defense, aerospace
· Technology, telecom
· Media, NGOs / civil society
· Finance / legal (executive targets)
· Any enterprise with significant Apple endpoint footprint
Potential impacted countries
· Global
Date of first reported activity
· February 11, 2026
Date of last reported activity update
· Feb 12, 2026
Why This Matters to Defenders
· KEV-listed exploited vulnerability
o You should assume real-world weaponization and prioritize remediation accordingly.
· Mobile/endpoint intrusion risk
o Dyld sits at a critical boundary for loading code; successful exploitation can enable implant staging, credential access, or surveillance operations depending on the rest of the chain.
· Cross-platform exposure: Apple lists fixes across
o iOS/iPadOS/macOS/watchOS/tvOS/visionOS (broad estate).
Associated APT groups
· Not publicly attributed by Apple/NVD in currently available sources.
Associated criminal organizations
Not publicly identified in currently available sources.
Tools used in campaign
· Not publicly disclosed
o Reporting describes “extremely sophisticated” targeted exploitation but does not provide tool names, infrastructure, or exploit kit references.
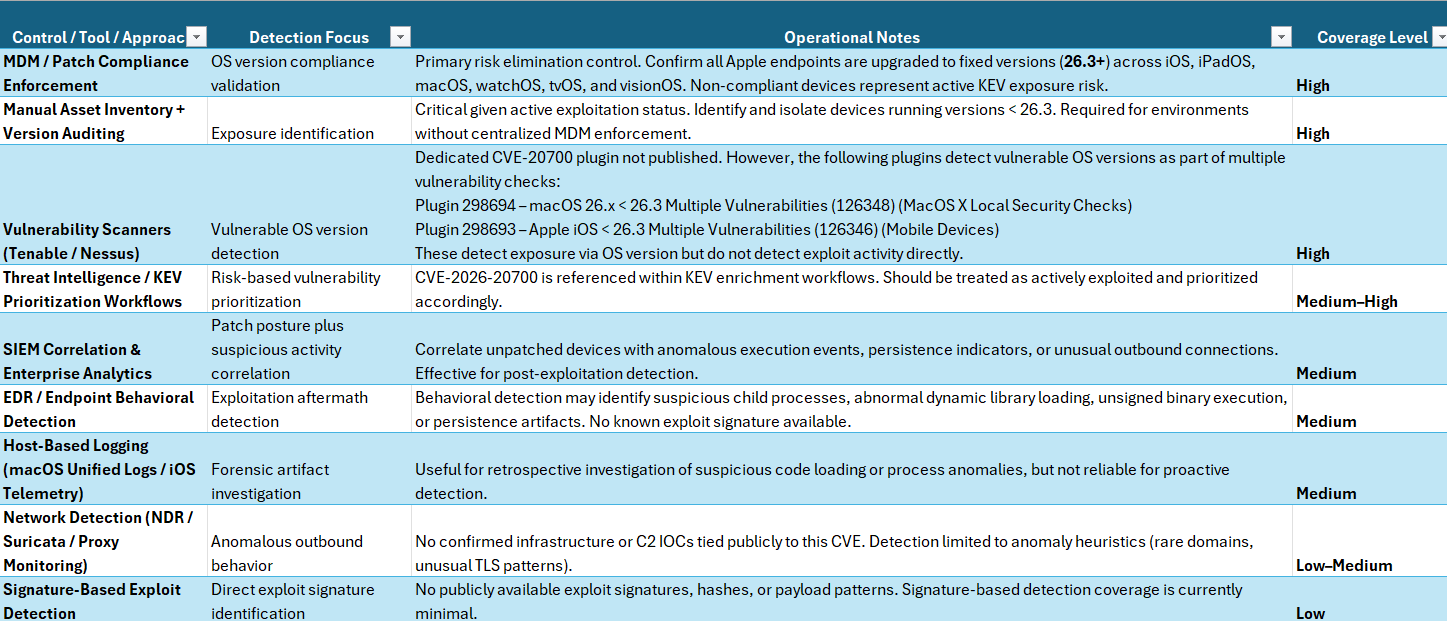
Exposure Assessment Tool
Goal: determine (1) vulnerable versions present, (2) patch status, (3) any high-risk-device anomalies.
· Version compliance (primary control)
o Identify endpoints running < 26.3 (iOS/iPadOS/macOS Tahoe/watchOS/tvOS/visionOS).
· MDM compliance query
o Pull device inventory from MDM; flag any device below fixed versions for immediate action.
· High-risk user validation
o Confirm patch status first for executives, journalists, security staff, and travel/high-risk profiles.
· Scanner reality check
o Tenable currently Nessus plugins for CVE-2026-20700.
IOCs
There are currently no publicly attributed domains, IPs, file hashes, or exploit binaries tied to CVE-2026-20700.
HIGH Confidence Indicators (80–100)
Unpatched devices running versions earlier than the security updates that address CVE-2026-20700 (iOS/iPadOS 26.3, macOS 26.3, watchOS 26.3, tvOS 26.3, visionOS 26.3).
· This is the strongest exposure signal.
· While not proof of compromise, devices not updated should be considered high-risk and prioritized for review.
· Confidence: HIGH 95
Evidence that the user/device fits Apple’s described threat model (targeted attack against specific individuals) combined with device instability.
· Example: suspicious activity reported by high-value individuals, journalists, executives, government staff.
· Correlation between suspicious browsing/messaging activity and system instability increases likelihood.
· Confidence: HIGH 90
Crash reports referencing dyld, dyld4, ImageLoader, Loader, or memory corruption errors such as EXC_BAD_ACCESS occurring near the suspected compromise window.
· Especially relevant if clustered in time.
· Failed exploit attempts often produce crashes before successful exploitation.
· Confidence 85
MEDIUM Confidence Indicators (50–79)
Repeated Safari or WebKit process crashes (Safari, WebContent, com.apple.WebKit.*) with dyld referenced in the backtrace.
· Exploit chains often involve browser or content rendering components.
· Not unique to this CVE, but meaningful when correlated.
· Confidence: Medium 75
macOS unified logs showing abnormal dynamic loader behavior during the suspected timeframe.
· Repeated loader failures
· Abnormal library load errors
· Unexpected abort signals tied to dyld
· Confidence: Medium 70
Process execution anomalies immediately following a dyld-related crash.
· Example: browser crash followed by rapid spawning of an unfamiliar binary.
· Particularly suspicious if the child process is unsigned or runs from user-writable directories.
· Confidence: Medium 65
Endpoint telemetry indicating memory manipulation behaviors shortly before anomalous execution.
· task_for_pid usage
· Debug attach attempts
· Unusual memory-write behaviors
· EDR alerts for runtime manipulation
· Confidence: Medium 60
Since the vulnerability describes memory corruption leading to arbitrary code execution, memory tampering telemetry adds contextual weight.
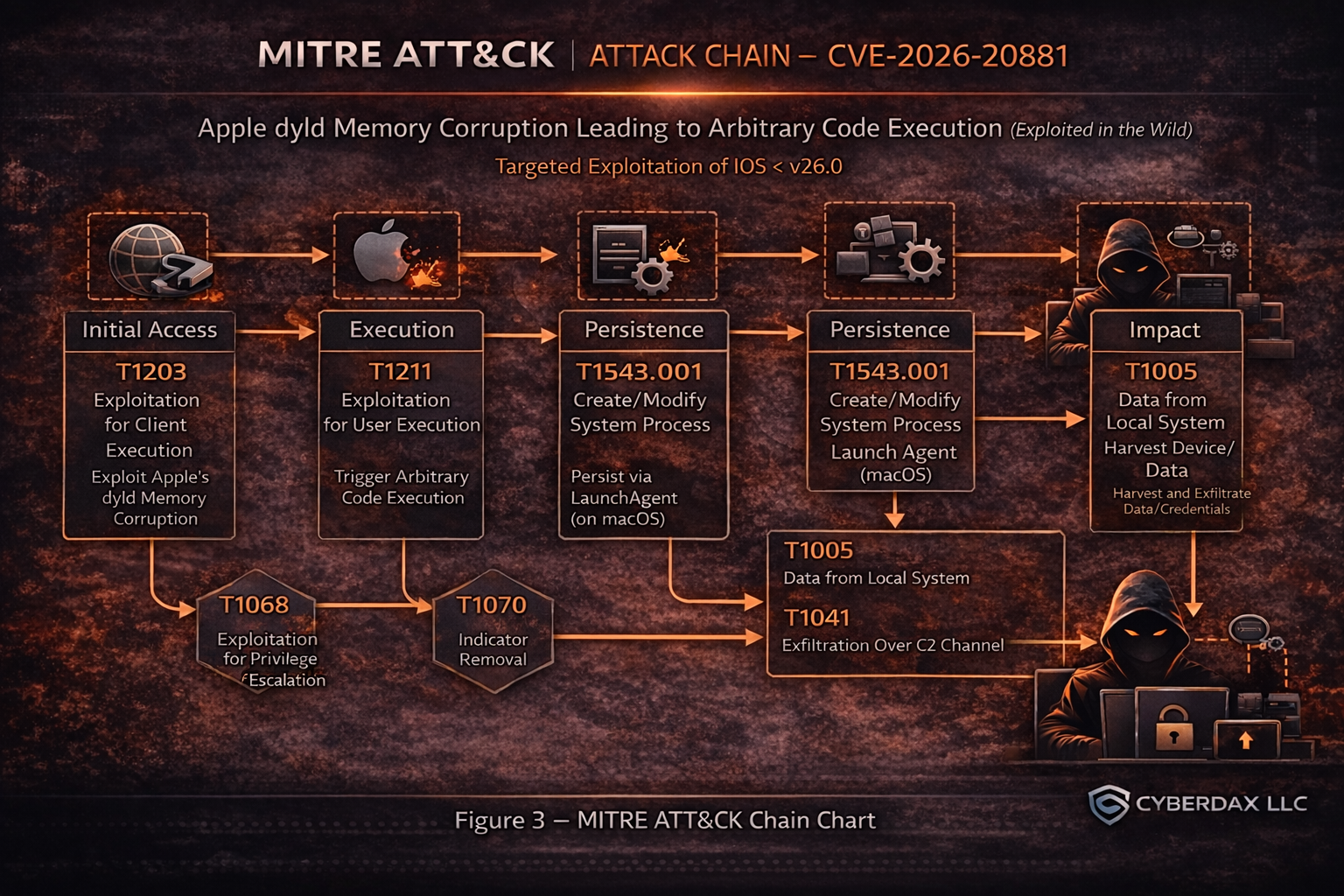
MITRE ATT&CK attack chain chart
(applicable high-confidence mapping)
Figure 2 MITRE ATT&CK attack
Because this is a memory corruption RCE in a core loader component, the most defensible ATT&CK alignment is “exploit to execute → establish foothold → collect → exfiltrate,” even though the exact chain details are not public.
TTPs
Stage: Initial Access / Execution
· T1203 Exploitation for Client Execution
o Use dyld memory corruption to execute code in user/system context (exact delivery vector not published).
Stage: Persistence
· T1543.001 Create/Modify System Process
o Launch Agent: persist via LaunchAgents on macOS endpoints if the campaign includes macOS. (Not confirmed—hunt hypothesis.)
Stage: Collection / Exfiltration (conditional)
· T1005 Data from Local System
o Gather local device data once code execution is obtained.
· T1041 Exfiltration Over C2 Channel
o Move collected data out over HXXPS.
(These are common follow-ons; not confirmed for this specific exploitation.)
Figure 3 Figure 3 MITRE ATT&CK attack chain CVE-2026-20700
CVSS 3.1
· (7.8) AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H
Nessus ID
· 298694
· 298693
Is this on the KEV list?
· Yes
Patch release date
· Feb 11, 2026
URL link to patch information
· hxxps://support.apple.com/en-us/126353
Malware names / malware family / hashes / decoding key
· There has not been malware associated with CVE-2026-20700 at this time.
What is the exploitability?
· Apple/NVD describe a memory corruption fixed via improved state management; exploitation requires an attacker with memory write capability, and can result in arbitrary code execution.
Has there been observed exploitation?
· Apple states it is aware of a report that it may have been exploited in an “extremely sophisticated attack” against targeted individuals (pre–iOS 26).
What is the exposure risk?
· High for unpatched Apple endpoints, especially high-risk users and organizations; KEV inclusion elevates remediation priority.
Recommended action
· Patch immediately to 26.3 (or platform equivalent) across iOS/iPadOS/macOS Tahoe/watchOS/tvOS/visionOS; enforce via MDM and validate completion.
· For high-risk populations: shorten update grace periods, validate device integrity (jailbreak/root indicators), and review unusual profiles/config changes.
Verdict
· Priority patch now. This is a KEV-referenced, in-the-wild exploited Apple dyld memory corruption that can enable arbitrary code execution, and it affects multiple Apple platforms—making it a high-consequence risk for any organization with Apple endpoints, especially those with high-risk users.
Primary objectives
(likely, based on “targeted individuals” framing)
· Covert access / surveillance enablement
· Credential/session/access harvesting post-compromise
· Long-term persistence on select devices (not confirmed; plausible objective for “sophisticated targeted attacks”)
Threat actor context
· No attribution in Apple advisory beyond acknowledging reporting sources/research context; Apple credits Google Threat Analysis Group on the iOS 26.3 security page.
Behavior analysis
Expected User-Agent patterns
· Not reliably known from public reporting. If the exploit chain involved web delivery, Safari/WebKit iOS user agents from iOS < 26 would be expected, but the delivery vector is not published.
Payload examples
· Not publicly disclosed.
Log artifacts
(what to hunt)
· MDM / device management logs: devices remaining on < 26.3, repeated failed update attempts, unusual profile installs.
· macOS endpoint telemetry (if applicable): unusual creation/modification of LaunchAgents/LaunchDaemons, unexpected dylib loads, abnormal child process spawning from normally quiet apps (hypothesis-based)
Figure 4 Detection Coverage Matrix CVE-2026-20700
Detection coverage by control type
Prevent
· Forced updates, device compliance gating (Conditional Access)
Detect
· Behavior analytics (persistence, suspicious executions), anomaly detection for rare destinations
Respond
· Isolate noncompliant devices; investigate high-risk users with suspicious signals
Suggested rules / potential hunts
Suricata
· Rare destination exfil burst” hunt
alert http $HOME_NET any -> $EXTERNAL_NET any (
msg:"HUNT Possible Apple endpoint exfiltration burst (rare dest heuristic)";
flow:established,to_server;
http.method; content:"POST"; nocase;
detection_filter:track by_src, count 20, seconds 300;
classtype:policy-violation;
sid:99020700; rev:2;
)
SentinelOne
Title
· CVE-2026-20700 macOS — Unsigned Launchd Persistence Execution (High Confidence)
Confidence Level
· Very High
Why this is top-tier
· Unsigned binaries launched by launchd from writable directories are rarely legitimate.
OsType = "macOS"
AND EventType = "Process Creation"
AND (
ParentProcessName IN ("launchd","launchctl")
OR ProcessAncestorName CONTAINS "launchd"
)
AND (
ProcessPath CONTAINS "/Users/"
OR ProcessPath CONTAINS "/Library/"
OR ProcessPath CONTAINS "/private/var/"
OR ProcessPath CONTAINS "/tmp/"
)
AND (
ProcessSignatureStatus IN ("Unsigned","Untrusted","Invalid","Unknown")
OR ProcessSigner = ""
)
AND ProcessPath NOT STARTSWITH "/System/"
AND ProcessPath NOT STARTSWITH "/usr/"
Title
· CVE-2026-20700 macOS — LaunchAgent Persistence Followed by Untrusted Execution
Confidence Level
· Very High
Why this is extremely strong
· Combines persistence and execution, which is the classic malware chain.
OsType = "macOS"
AND (
(
EventType IN ("File Creation","File Modification")
AND (
TargetFilePath CONTAINS "/Library/LaunchAgents/"
OR TargetFilePath CONTAINS "/Library/LaunchDaemons/"
)
AND TargetFilePath ENDSWITH ".plist"
AND InitiatingProcessName NOT IN (
"softwareupdated","installer","InstallAssistant",
"mdmclient","jamf","IntuneMdmAgent"
)
)
OR
(
EventType = "Process Creation"
AND ParentProcessName IN ("launchd","launchctl")
AND (
ProcessSignatureStatus IN ("Unsigned","Untrusted","Invalid","Unknown")
OR ProcessSigner = ""
)
)
)
Title
· CVE-2026-20700 macOS — Untrusted Launchd Binary Outbound Egress (High Confidence)
Confidence Level
· High
Why high confidence
· Persistence malware calling out over non-standard ports is a strong escalation signal.
OsType = "macOS"
AND EventType IN ("Network Connect","Network Connection")
AND Direction = "Outbound"
AND RemoteIpType = "Public"
AND (
InitiatingProcessSignatureStatus IN ("Unsigned","Untrusted","Invalid","Unknown")
OR InitiatingProcessSigner = ""
)
AND (
InitiatingProcessParentName IN ("launchd","launchctl")
OR InitiatingProcessAncestorName CONTAINS "launchd"
)
AND RemotePort NOT IN (80,443,53)
Best Practice Deployment
· Alert immediately on Rule 1
· Escalate to incident if Rule 2 occurs
· Treat Rule 3 as confirmation of active compromise
Splunk
· Title
o Apple Fleet Devices Below Fixed Version (26.3)
index=mdm sourcetype=mdm:inventory (os_family IN ("iOS","iPadOS","macOS","watchOS","tvOS","visionOS"))
| eval noncompliant=if(version_compare(os_version,"26.3")<0,1,0)
| where noncompliant=1
| stats latest(os_version) as os_version latest(last_checkin) as last_checkin by device_id user os_family
| sort - last_checkin
· Title
o macOS LaunchAgent Creation (Persistence Hunt)
index=endpoint sourcetype IN ("osquery:results","edr:telemetry","sysmon:macos")
(path="*/Library/LaunchAgents/*" OR path="*/Library/LaunchDaemons/*")
| stats count earliest(_time) as first latest(_time) as last values(process_name) as proc by host user path
| sort -count
Sigma
(baseline persistence telemetry — macOS)
Title
· HUNT macOS LaunchAgent or LaunchDaemon Creation
id: 0b6f0b1a-2070-4c2b-a4b5-207000000002
status: experimental
logsource:
product: macos
category: file_event
detection:
selection:
TargetFilename|contains:
- "/Library/LaunchAgents/"
- "/Library/LaunchDaemons/"
condition: selection
falsepositives:
- Legitimate software installs and updates
level: medium
YARA
Template use once you have a sample
· Rule TEMPLATE_Apple_Targeted_Implant_Generic
{
meta:
description = "Template: replace strings/hashes once a validated sample exists"
confidence = "LOW"
strings:
$a1 = "/Library/LaunchAgents/" nocase
$a2 = "/Library/LaunchDaemons/" nocase
$a3 = "com.apple." nocase
condition:
2 of ($a*)
}
Delivery methods
· Not publicly disclosed for this CVE; treat delivery vector as unknown and focus on patch posture + behavior-based hunting.
What we don’t know
· Initial access vector (web, app, physical, supply chain) and full exploit chain composition
· Actor attribution and infrastructure
· Malware family, hashes, and decrypt/decoding keys
· Any robust IOC set that defenders can use for block/detect
Steps to consider over the next seven days
1. Enforce 26.3+ upgrades across all Apple platforms via MDM; quarantine or restrict access for noncompliant devices.
2. Validate patch status for high-risk users first; document exceptions and compensating controls.
3. Run macOS persistence hunts (LaunchAgents/Daemons creation) and unusual execution analytics (if macOS is in scope).
4. Stand up network anomaly hunts (rare destinations, burst exfil patterns) for high-risk device cohorts.
5. Re-check NVD for updated CVSS scoring and any added references/analysis.
6. Track Tenable plugin availability changes (currently none).
7. Prepare an IR playbook for targeted Apple endpoint compromise (rapid isolation, credential/session resets for impacted users, device forensic workflow).
References
Support Apple
· hxxps://support.apple.com/en-us/126346
NVD
· hxxps://nvd.nist.gov/vuln/detail/CVE-2026-20700
CISA KEV Catalog
· hxxps://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-20700
Tenable
· hxxps://www.tenable.com/cve/CVE-2026-20700/plugins
Security Week
· hxxps://www.securityweek.com/apple-patches-ios-zero-day-exploited-in-extremely-sophisticated-attack