CVE-2026-21385 Qualcomm Display Driver Memory Corruption Zero-Day in Active Targeted Exploitation
BLUF
CVE-2026-21385 is a high-severity memory corruption vulnerability in Qualcomm display drivers impacting Android devices and confirmed under limited targeted exploitation. The flaw enables local privilege escalation and potential arbitrary code execution in a privileged or kernel context. Enterprise exposure includes executive mobile compromise, credential theft, surveillance enablement, and regulated data leakage through trusted mobile access channels. Immediate patch validation, accelerated remediation for high-risk users, and mobile telemetry-driven hunting are required to reduce operational and regulatory impact within a seven-day containment window.
Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
“For organizations affected by CVE-2026-21385 involving targeted Android device privilege escalation, financial exposure is primarily driven by executive device compromise and whether regulated data access occurred.”
· Low-end total cost: $350,000 – $900,000
(isolated executive remediation, no data loss confirmed)
· Typical expected range: $900,000 – $3.5 million
(multiple high-risk devices, enterprise credential resets and legal review)
· Upper-bound realistic scenarios: $3.5 million – $7.5 million
(confirmed sensitive data exposure requiring regulatory notification)
Key Cost Drivers
· Patch velocity across executive and privileged mobile devices
· Extent of credential and token invalidation
· Confirmation of regulated or contractual data exposure
· Number of leadership-tier devices requiring forensic review
· Insurance retention thresholds and renewal timing
Bottom Line for Executives (Public Company Context)
CVE-2026-21385 presents a targeted mobile privilege escalation risk that becomes financially significant only if executive or regulated data access is confirmed. For most organizations, exposure is likely to remain below traditional materiality thresholds if rapid patching and containment are executed and no sensitive data loss is identified. The primary financial drivers are legal review, identity trust restoration, and potential notification obligations—not infrastructure rebuild.
Management’s focus should be on:
· Confirming scope of device impact
· Determining whether regulated or investor-relevant data was accessed
· Documenting remediation speed and control effectiveness
Speed and documentation directly influence both cost containment and disclosure posture.
Board-Level Takeaway (Materiality & Disclosure Framing)
At present, CVE-2026-21385 represents a contingent risk rather than an automatic material event. The issue approaches disclosure sensitivity only if exploitation results in confirmed access to regulated data, executive communications, financial reporting systems, or material nonpublic information.
Under realistic scenarios
· Limited executive device impact with no data exfiltration is unlikely to trigger Form 8-K materiality thresholds.
· Confirmed sensitive data access, regulatory engagement, or prolonged operational disruption could elevate the event into disclosure territory depending on scale and timing.
Board oversight should concentrate on:
· Whether the incident alters financial condition or operational continuity
· Whether investor-relevant systems or communications were affected
· Whether remediation actions demonstrate reasonable control effectiveness
In short, the technical vulnerability alone is not material. Materiality hinges on demonstrable business impact and data exposure.
Priority Level and Response Window
· Priority Level: Critical – Active Exploitation Confirmed
· Executive Risk Category: Mobile Privilege Escalation and Data Exposure
· SOC Action Level: Immediate
Response Window:
· Exposure assessment within 24 hours
· Executive device patch validation within 48 hours
· Fleet-wide remediation within 7 days
· Hunt cycle completion within 72 hours
Why This Matters Now
· Exploitation confirmed in the wild
· Mobile endpoints often lack deep kernel-level telemetry
· Executive Android devices provide direct access to corporate identity systems
· Privileged mobile compromise can bypass traditional endpoint monitoring
· Regulatory risk increases if protected communications or MFA tokens are accessed
What we don’t yet know
· Full exploit chain composition used in observed attacks
· Initial access vector (malicious app, exploit chain, or chained vulnerability)
· Attribution to specific threat actors
· Geographic distribution of victims
· Whether exploit tooling has proliferated beyond limited operators
Exploit Conditions Snapshot
Component
· Qualcomm Display Driver Subsystem
Vulnerability Class
· Memory Corruption
CWE
· CWE-787 – Out-of-bounds Write
Attack Vector
· Local
Privileges Required
· Low or none depending on exploit chain
User Interaction
· Not known at this time
Security Boundary Impact
· Kernel or privileged process context
Primary Risk Outcomes
· Privilege escalation
· Arbitrary code execution
· Security control bypass
Today’s Hunt Focus (3 Signals)
· Repeated display or surfaceflinger fatal crash logs
· Unexpected UID transition from untrusted_app to root or system
· SELinux denial events immediately followed by privileged process creation
Sectors
· Government
· Telecommunications
· Defense and aerospace
· Financial services
· Executive leadership populations
Countries
· Global targeted
o Exploitation suggests selective targeting
First Activity
· Observed prior to coordinated disclosure – exact date Not known at this time
Last Activity
· Active at time of reporting
CVE Details
CVE
· CVE-2026-21385
Vendor
· Qualcomm
Affected Platform
· Android devices utilizing impacted Qualcomm display components
Vulnerability Type
· Memory corruption in display driver
Impact Scope
· Local privilege escalation and potential arbitrary code execution
CVSS v3.1
· (7.8) AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H
CWE
· CWE-787 – Out-of-bounds Write
CISA KEV Status:
· Yes, this is in the KEV catalog
Due Date
· March 24, 2026
Nessus Plugin Coverage
· This does not have a plugin at this time
EPSS Score
· Not known at this time
Exploit Status
· Confirmed under limited targeted exploitation
Public exploit code
· Not known at this time
Weaponization Maturity
· Operational use confirmed
Exploit chaining
· Not known at this time
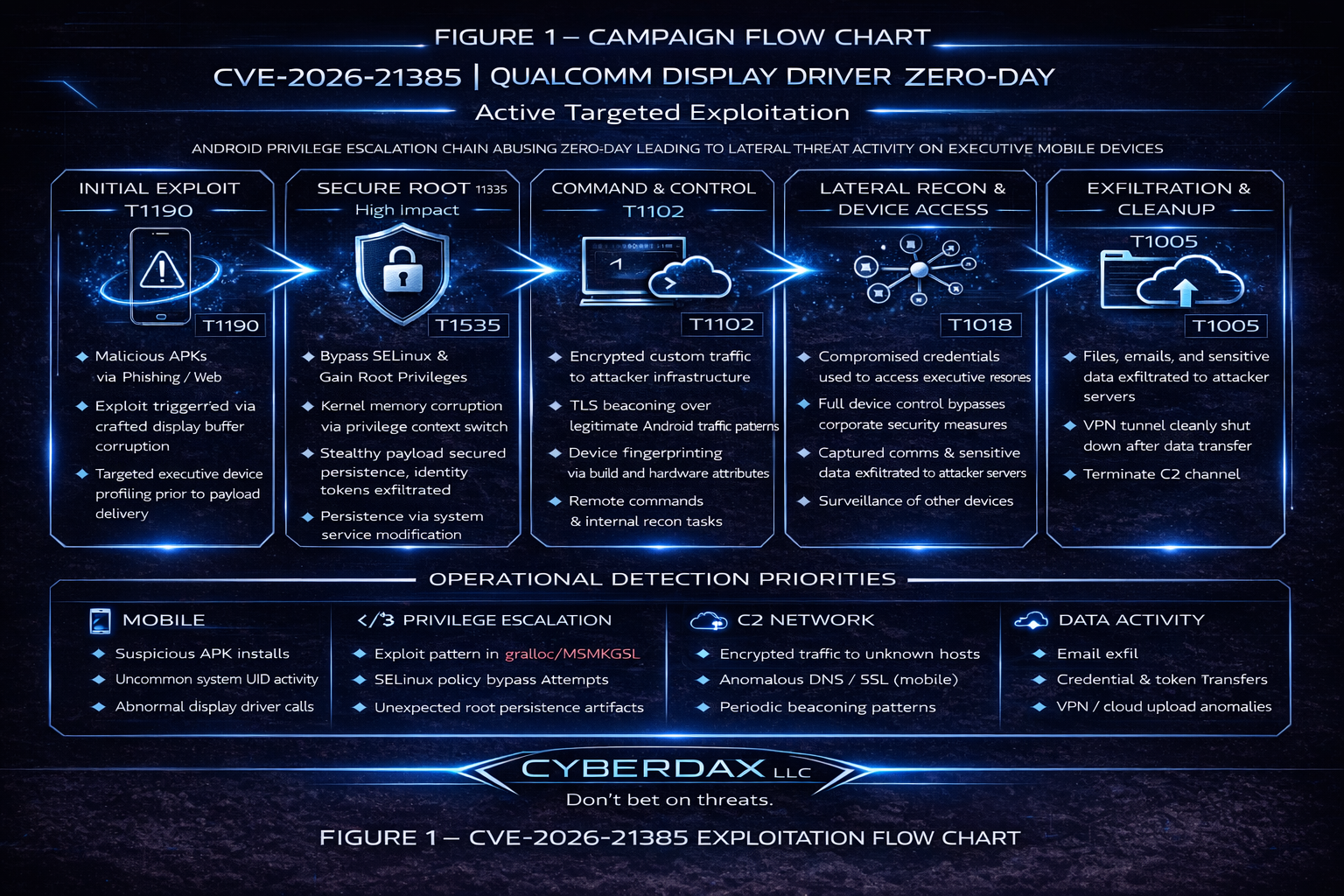
MITRE ATT&CK Chain Flow Mapping
· CVE-2026-21385 – Qualcomm Display Driver Memory Corruption Zero-Day
Active Targeted Exploitation (Android Context)
· This section maps the end-to-end attack progression from entry to impact.
Initial Access
· T1475 Deliver Malicious App
o Malicious or trojanized Android application used to deliver exploit trigger payload.
· T1190 Exploit Public-Facing Application (Conditional)
o Exploit may be chained with exposed Android services or remote interfaces.
Execution
· T1203 Exploitation for Client Execution
o Crafted display buffer triggers memory corruption inside Qualcomm display driver.
Privilege Escalation
· T1068 Exploitation for Privilege Escalation
o Kernel memory corruption enables privilege context switch to elevated/root execution.
Persistence
· T1547 Boot or Logon Autostart Execution
o System service or initialization component modified for reboot persistence.
· T1620 Reflective Code Loading
o Payload loaded directly into memory to reduce filesystem artifacts.
Defense Evasion
· T1622 Debugger Evasion
o Exploit checks for sandbox or emulation environments.
· T1070 Indicator Removal on Host
o Removal of logs and exploit artifacts post-deployment.
Credential Access
· T1555 Credentials from Password Stores
o Extraction of enterprise authentication tokens and stored credentials.
· T1414 Access Sensitive Data in Device
o Access to enterprise email, collaboration apps, and session artifacts.
Discovery
· T1082 System Information Discovery
o Collection of device build, hardware identifiers, installed apps.
· T1518 Software Discovery
o Enumeration of enterprise and security applications.
Lateral Movement
· T1021 Remote Services
o Use of harvested credentials to access enterprise services.
· T1550 Use of Stolen Authentication Tokens
o Reuse of captured OAuth or session tokens for cloud access.
Command and Control
· T1102 Web Service
o Encrypted HTTPS communications to attacker-controlled infrastructure.
· T1071.001 Application Layer Protocol: Web Protocols
o Beaconing embedded within legitimate Android HTTPS traffic.
Collection
· T1114 Email Collection
o Executive mailbox access and staging.
· T1513 Screen Capture
o Capture of sensitive device session content.
Exfiltration
· T1041 Exfiltration Over C2 Channel
o Sensitive data transmitted over encrypted outbound channels.
· T1567 Exfiltration to Cloud Storage
o Staged uploads to attacker-controlled cloud infrastructure.
Stage-Based TTPs
This section provides mechanics-level detail for the most critical techniques used in the exploitation chain.
Only high-impact techniques are expanded.
· T1203 Exploitation for Client Execution
o The exploit delivers crafted display buffer input to the Qualcomm display driver, causing memory corruption that enables arbitrary code execution within device context.
· T1068 Exploitation for Privilege Escalation
o Memory corruption allows escalation from application UID context to elevated or root privileges by triggering kernel-level context manipulation.
This is the pivotal trust-breaking event in the chain.
· T1547 Boot or Logon Autostart Execution
o Persistence achieved through modification of Android service initialization components, ensuring privileged execution survives reboot cycles.
· T1555 Credentials from Password Stores
o Post-escalation access to stored enterprise credentials, authentication tokens, and mobile device management profiles.
· T1102 Web Service
o Command-and-control traffic embedded within encrypted HTTPS sessions, blending into normal Android network activity patterns.
· T1041 Exfiltration Over C2 Channel
o Sensitive executive communications, credentials, and device artifacts transmitted over encrypted outbound channels to attacker infrastructure.
Malware and SHA256
Associated malware family: Not known at this time
Exploit payload SHA256: Not known at this time
Surveillance toolkit linkage: Not confirmed
Behavior and Log Artifacts
· Logcat entries referencing display driver faults or SIGSEGV
· Surfaceflinger fatal crash events
· Kernel panic or abnormal reboot patterns
· SELinux audit logs indicating denied then successful privileged access
· Root-level process creation following application context execution
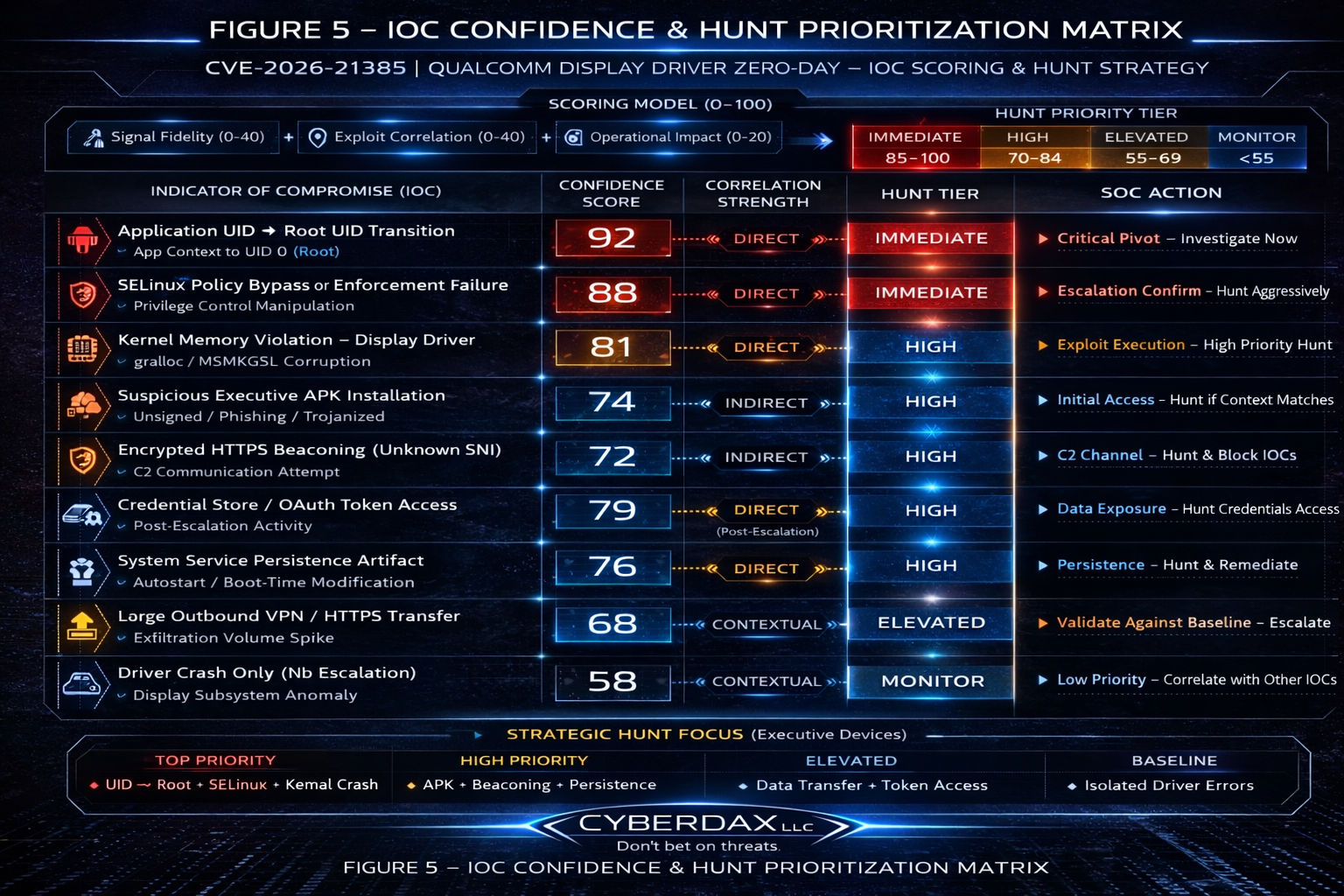
IOC Confidence and Hunt Prioritization
Scoring Model Overview
Each indicator is evaluated using three weighted dimensions:
Signal Fidelity (0–40 points) – Reliability and false-positive likelihood
· Exploit Correlation Strength (0–40 points) – Directness of linkage to CVE-2026-21385 chain
· Operational Impact Potential (0–20 points) – Risk if confirmed on executive device
Maximum Possible Score: 100
Hunt Priority Tiers:
· Immediate (85–100) – Direct exploit pivot indicators
· High (70–84) – Strong exploit correlation or high-risk behavior
· Elevated Monitoring (55–69) – Contextual but requires correlation
· Baseline Monitoring (<55) – Low-confidence contextual noise
Application UID to Root UID Transition
· Confidence Score: 92 / 100
· Signal Fidelity: High
· Exploit Correlation: Direct
· Operational Impact: Critical
· Hunt Priority: Immediate
Rationale:
· Privilege escalation is the pivotal trust-breaking event in this exploit chain. Transition from application context to UID 0 on Android executive devices is highly anomalous and strongly correlated with T1068 exploitation.
SELinux Enforcement State Change or Policy Bypass
· Confidence Score: 88 / 100
· Signal Fidelity: High
· Exploit Correlation: Direct
· Operational Impact: High
· Hunt Priority: Immediate
Rationale:
· Successful exploitation requires bypass or manipulation of privilege enforcement controls. SELinux anomalies on executive devices are rare and strongly tied to escalation attempts.
Kernel Memory Violation Associated with Display Driver (gralloc / MSMKGSL)
· Confidence Score: 81 / 100
· Signal Fidelity: Medium-High
· Exploit Correlation: Direct
· Operational Impact: High
· Hunt Priority: High
Rationale:
· Memory corruption within Qualcomm display components is core to CVE-2026-21385. Kernel anomaly logs tied to these subsystems significantly increase exploitation likelihood.
Suspicious APK Installation Targeting Executive Devices
· Confidence Score: 74 / 100
· Signal Fidelity: Medium
· Exploit Correlation: Indirect
· Operational Impact: High
· Hunt Priority: High
Rationale:
· Initial delivery vector likely involves malicious or trojanized application. While not inherently malicious alone, correlation with escalation artifacts raises priority.
Encrypted Outbound HTTPS Beaconing to Unknown Hosts
· Confidence Score: 72 / 100
· Signal Fidelity: Medium
· Exploit Correlation: Indirect
· Operational Impact: High
· Hunt Priority: High
Rationale:
· C2 traffic blends into legitimate Android HTTPS patterns. Unknown SNI combined with device-level anomalies materially increases exploitation probability.
Credential Store or OAuth Token Access Anomalies
· Confidence Score: 79 / 100
· Signal Fidelity: Medium-High
· Exploit Correlation: Direct (Post-Escalation Phase)
· Operational Impact: Critical
· Hunt Priority: High
Rationale:
· Post-root access to stored enterprise tokens indicates expansion from device compromise to enterprise access risk.
System Service Modification or Unauthorized Autostart Entry
· Confidence Score: 76 / 100
· Signal Fidelity: Medium-High
· Exploit Correlation: Direct (Persistence Phase)
· Operational Impact: High
· Hunt Priority: High
Rationale:
· Persistence artifacts on Android executive devices are uncommon and strongly associated with deliberate compromise.
Large Outbound HTTPS or VPN Upload Deviation from Baseline
· Confidence Score: 68 / 100
· Signal Fidelity: Medium
· Exploit Correlation: Contextual
· Operational Impact: High
· Hunt Priority: Elevated Monitoring
Rationale:
· Exfiltration behavior alone is not unique to this exploit but materially increases confidence when paired with escalation signals.
Abnormal Display Driver Crash Without Escalation Indicators
· Confidence Score: 58 / 100
· Signal Fidelity: Medium-Low
· Exploit Correlation: Contextual
· Operational Impact: Moderate
· Hunt Priority: Elevated Monitoring
Rationale:
· Driver crashes are noisy but relevant when correlated with UID transitions or SELinux anomalies.
Executive Interpretation of Prioritization Model
The highest-confidence indicators are
· UID transition to root
· SELinux enforcement bypass
· Kernel memory violation within display driver
These represent the exploit pivot zone and should trigger immediate investigation on executive devices.
Network-only anomalies without device context should not drive panic but should elevate when correlated.
Strategic Hunt Guidance
Immediate Hunt Focus:
· Any executive Android device exhibiting UID transition
· SELinux enforcement state modification
· Kernel crash tied to display subsystem
Correlation-Based Hunt:
· Unknown HTTPS SNI + token access
· APK install + privilege anomaly
· Persistence artifact + outbound beacon
Detection Signals Layer
· Kernel crash telemetry spikes
· Abnormal binder IPC behavior
· Root-level process spawn anomalies
· MDM integrity drift signals
· Policy tampering attempts
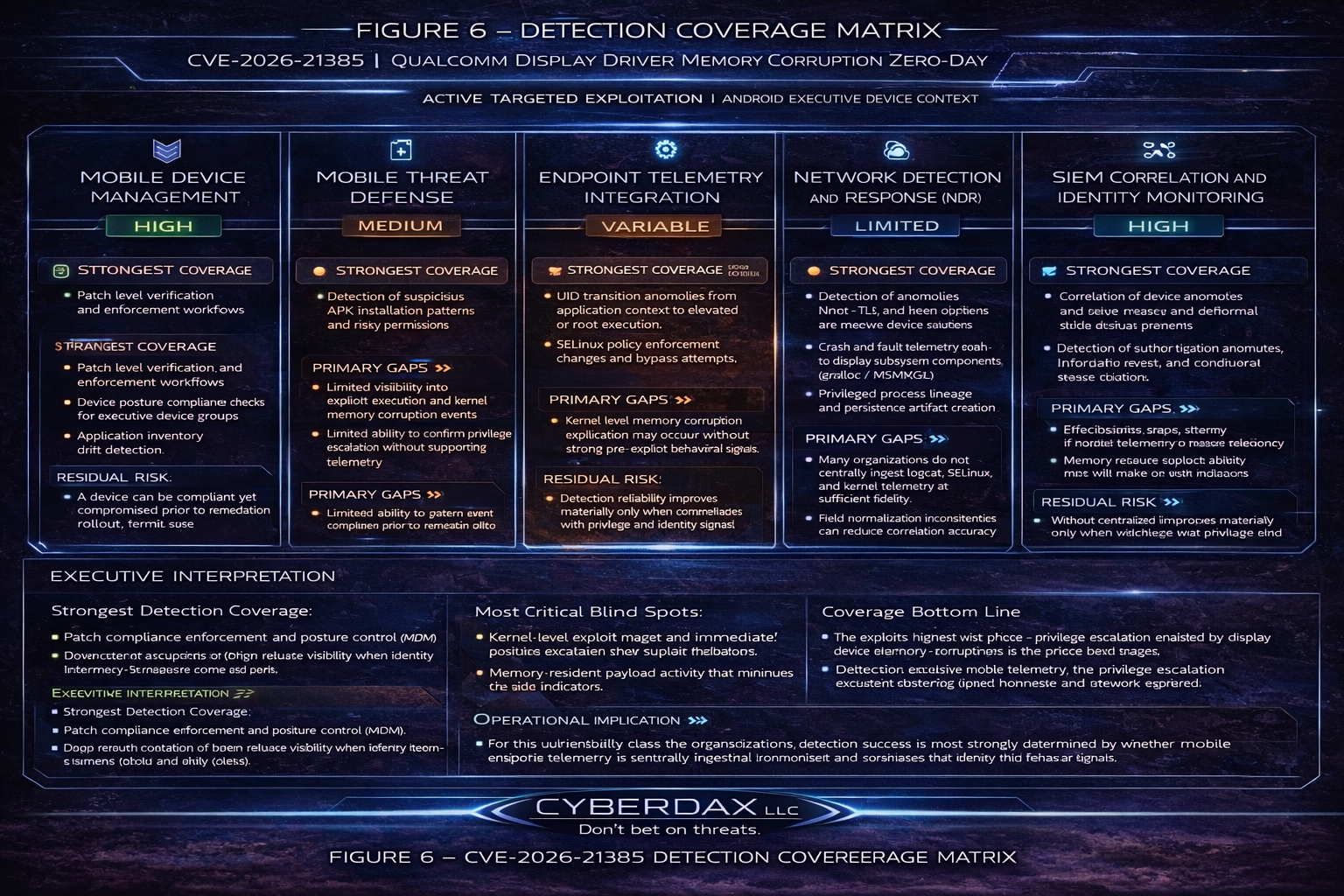
Detection Coverage Matrix
CVE-2026-21385 – Qualcomm Display Driver Memory Corruption Zero-Day
Active Targeted Exploitation (Android Executive Device Context)
Mobile Device Management (MDM)
· Coverage Level: High for compliance and patch enforcement
Strongest Coverage:
· Patch level verification and enforcement workflows
· Device posture compliance checks for executive device groups
· Application inventory drift detection
Primary Gaps:
· Limited visibility into exploit execution and kernel memory corruption events
· Limited ability to confirm privilege escalation without supporting telemetry
Residual Risk:
· A device can be compliant yet compromised prior to remediation rollout
Mobile Threat Defense (MTD)
Coverage Level: Medium for behavioral detection and post-exploitation artifacts
· Strongest Coverage:
o Detection of suspicious APK installation patterns and risky permissions
o Root detection heuristics and device integrity degradation indicators
o Anomalous process and behavior alerts on high-risk devices
Primary Gaps:
· Kernel-level memory corruption exploitation may occur without strong pre-exploit behavioral signals
o Memory-resident payloads can reduce artifact-based detection
Residual Risk:
· Detection reliability improves materially only when correlated with privilege and identity signals
Endpoint Telemetry Integration (Mobile EDR, Logcat, Kernel, SELinux)
Coverage Level: Variable – environment dependent and often the decisive control plane
Strongest Coverage (when integrated into SIEM):
· UID transition anomalies from application context to elevated or root execution
· SELinux policy enforcement changes and bypass attempts
· Crash and fault telemetry tied to display subsystem components (gralloc / MSMKGSL)
· Privileged process lineage and persistence artifact creation
Primary Gaps:
· Many organizations do not centrally ingest logcat, SELinux, and kernel telemetry at sufficient fidelity
· Field normalization inconsistencies can reduce correlation accuracy
Residual Risk:
· Without centralized mobile telemetry, the privilege escalation pivot may be effectively invisible
Network Detection and Response (NDR)
Coverage Level: Limited for the local exploit phase; Moderate once C2 is established
Strongest Coverage:
· Detection of anomalous DNS, TLS, and beaconing patterns from executive device subnets
· Identification of unknown SNI, certificate anomalies, or rare destination infrastructure
· Detection of unusual outbound volume spikes consistent with staged exfiltration
Primary Gaps:
· Local privilege escalation and kernel memory corruption have minimal network observables
· Encrypted mobile traffic reduces inspection depth in many enterprises
Residual Risk:
· Network-only programs may detect compromise late, after persistence or data staging has begun
SIEM Correlation and Identity Monitoring
Coverage Level: High when cross-domain telemetry is available and tuned
Strongest Coverage:
· Correlation of device anomalies with token misuse and abnormal cloud access patterns
· Detection of authentication anomalies, impossible travel, and conditional access failures
· High-confidence alerts when credential store access aligns with outbound beaconing
Primary Gaps:
· Effectiveness drops sharply if mobile telemetry and identity telemetry remain siloed
· Alert fatigue risk if correlation rules are not scoped to executive and high-risk device groups
Residual Risk:
· Identity-focused detection often identifies downstream abuse rather than the initial exploit pivot
Executive Interpretation
Strongest Detection Coverage:
· Patch compliance enforcement and posture control (MDM)
· Downstream credential or token misuse visibility when identity telemetry is mature (SIEM and IAM)
Most Critical Blind Spots:
· Kernel-level exploit trigger and immediate privilege escalation pivot without integrated mobile telemetry
· Memory-resident payload activity that minimizes on-disk indicators
Operational Implication:
· For this vulnerability class, the organization’s detection success is most strongly determined by whether mobile endpoint telemetry is centrally ingested, normalized, and correlated with identity and network signals
Coverage Bottom Line
· The exploit’s highest-risk phase privilege escalation enabled by display driver memory corruption is the phase least visible to network-only detection and only reliably detectable when mobile endpoint telemetry and identity correlation are implemented at scale.
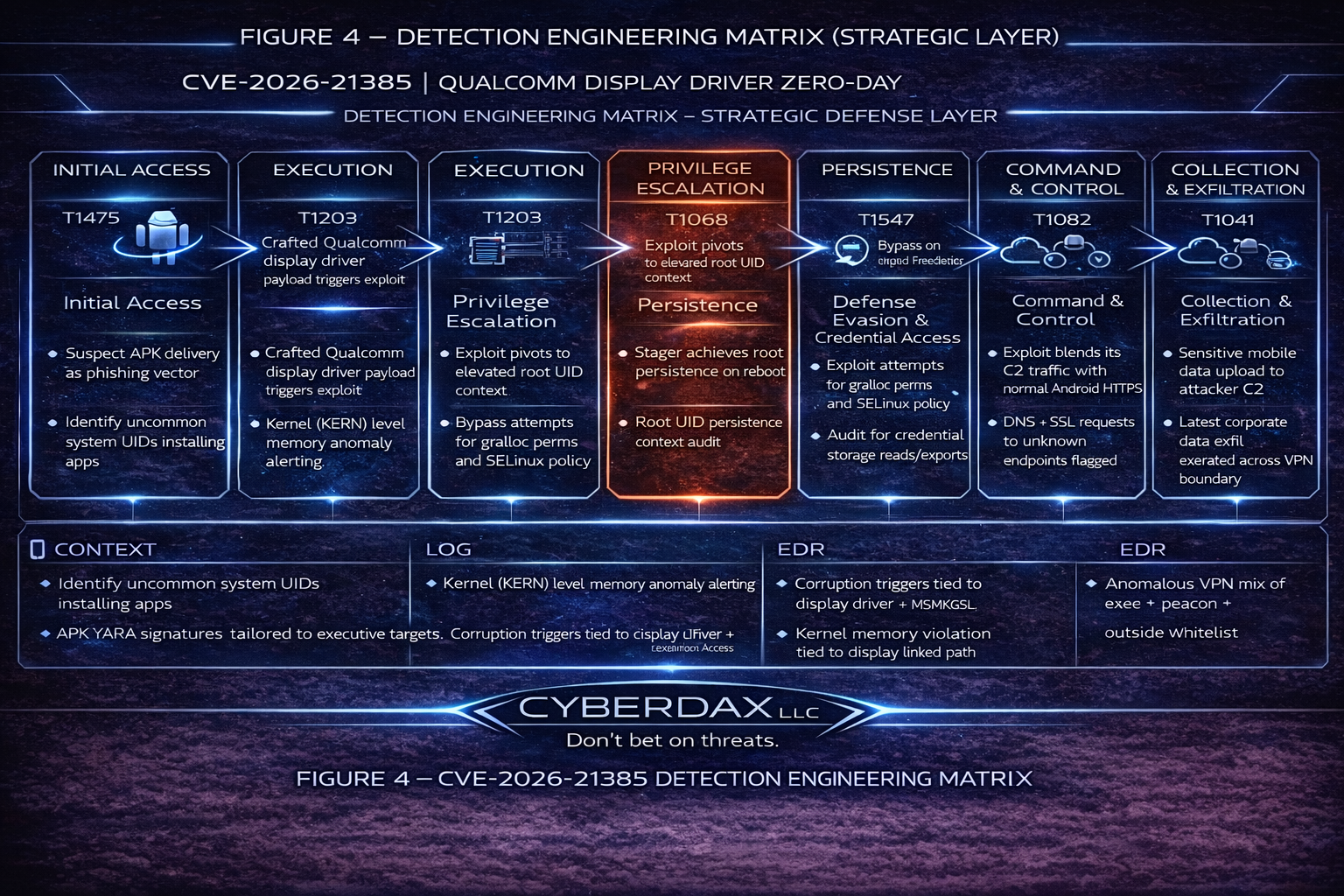
Detection Engineering Matrix (Operational Rule Layer)
Privilege Escalation Pivot Detection
MITRE: T1068 – Exploitation for Privilege Escalation
Detection Intent
Identify transition from application UID to elevated or root execution on managed Android devices.
Operational Signals
· UID change to 0 (root) initiated by non-system application
· Unexpected spawning of privileged shell processes
· SELinux enforcement mode change events
Log Sources
· logcat (security events)
· SELinux audit logs
· Kernel process telemetry
· Mobile EDR process lineage
Correlation Logic
Trigger High-Severity alert when:
· UID transition + SELinux policy change
OR
· UID transition + suspicious APK installation within 24h
False Positive Risk
Low in executive device groups with restricted administrative tooling.
Display Driver Exploit Trigger Monitoring
MITRE: T1203 – Exploitation for Client Execution
Detection Intent
Identify anomalous crash or memory fault events within Qualcomm display subsystem.
Operational Signals
· Kernel crash referencing gralloc / MSMKGSL
· Repeated segmentation fault in display driver context
· Unusual GPU memory access errors
Log Sources
· Android kernel crash logs
· Logcat crash dumps
· Mobile EDR kernel anomaly telemetry
Correlation Logic
Elevate to High only if:
• Display driver crash + UID anomaly
OR
• Crash event + persistence artifact within 48h
False Positive Risk
· Moderate (isolated driver crashes occur in production).
Persistence Artifact Detection
MITRE: T1547 – Boot or Logon Autostart Execution
Detection Intent
Identify unauthorized modification of system service or boot-time execution components.
Operational Signals
· New or modified system service entries
· Unexpected autostart registration
· Privileged process executed during boot sequence
Log Sources
· Service configuration logs
· Boot sequence telemetry
· File integrity monitoring (system paths)
Correlation Logic
High-Severity alert when:
· Persistence artifact + privilege escalation
OR
· Persistence artifact + outbound C2 beacon
False Positive Risk
Low for hardened executive device profiles.
Credential and Token Access Monitoring
MITRE: T1555 – Credentials from Password Stores
Detection Intent
Detect abnormal access to stored enterprise authentication tokens.
Operational Signals
· Secure storage read operations from non-standard process
· OAuth token extraction behavior
· Unusual access to enterprise MDM profiles
Log Sources
· Mobile application logs
· Identity provider logs
Secure enclave access telemetry
Correlation Logic
Elevate to Critical when:
· Credential access plus UID transition
OR
· Credential access plus abnormal cloud login within 1h
False Positive Risk
· Medium (legitimate token refresh events must be baseline-modeled).
Command and Control Beaconing Detection
MITRE: T1102 – Web Service
MITRE: T1071.001 – Application Layer Protocol (Web Protocols)
Detection Intent
Identify encrypted outbound communications indicative of C2 activity.
Operational Signals
· Periodic outbound HTTPS connections with consistent interval
· Unknown SNI or newly registered domain
· TLS fingerprint deviation from baseline
Log Sources
· DNS logs
· Firewall logs
Proxy logs
· Mobile network telemetry
Correlation Logic
Escalate to High when:
· Beaconing pattern + persistence artifact
OR
· Beaconing + credential access event
False Positive Risk
· Moderate (requires baseline tuning for executive travel patterns).
Data Exfiltration Monitoring
MITRE: T1041 – Exfiltration Over C2 Channel
Detection Intent
Identify abnormal outbound data volume or sensitive data transfer from executive devices.
Operational Signals
· Unusual VPN or HTTPS upload spike
· Large outbound transfer outside baseline hours
· Email synchronization anomalies
Log Sources
· VPN logs
· Proxy and firewall telemetry
· Email platform audit logs
· Cloud access logs
Correlation Logic
Critical alert when:
· Data transfer spike + credential store access
OR
· Data transfer spike + beaconing infrastructure
False Positive Risk
· Medium; requires behavioral baseline modeling.
Cross-Domain Correlation Rules (High-Confidence Fusion Logic)
To reduce noise and increase detection precision:
Trigger Immediate Incident Response when any of the following combinations occur:
· UID Transition + SELinux Bypass
· UID Transition + Display Driver Crash
· Credential Access + Abnormal Cloud Login
· Persistence Artifact + Beaconing Pattern
· Token Access + Large Outbound Transfer
These represent exploit-chain alignment.
SOC Operational Priority Mapping
Immediate Escalation:
· Privilege escalation confirmed
· SELinux enforcement manipulation
· Credential store access after UID transition
High Priority Hunt:
· Driver crash anomalies
· Persistence artifacts
· Beaconing patterns
Elevated Monitoring:
· Isolated HTTPS anomaly
· Isolated driver crash
Operational Engineering Notes
· Executive device groups should use stricter threshold tuning
· Correlation window: 24–48 hours recommended
· Telemetry normalization across Android OEM variants required
· Memory-resident exploit detection dependent on kernel log ingestion
Suggested Rules
Suricata
Rule Name
· Android Suspicious TLS Exfiltration Post Privilege Escalation
Detection Intent
· Identify suspicious outbound TLS traffic patterns from mobile segments during exploitation window
Purpose
· Highlight potential command and control or exfiltration following device compromise
Tuning Explanation
· Deploy on mobile VLAN or Android egress segment
· Focus on rare top-level domains
· Adjust threshold to match baseline
alert tls $HOME_NET any -> $EXTERNAL_NET 443 (
msg:"CYBERDAX Android suspicious TLS SNI possible C2";
flow:established,to_server;
tls.sni;
pcre:"/(\.top|\.xyz|\.click|\.cam|\.site|\.online|\.icu)$/i";
threshold:type both, track by_src, count 5, seconds 300;
classtype:trojan-activity;
sid:226213851;
rev:1;
)
Sentinel One
Rule Name
· Android Suspicious Root Execution from Application Context
Detection Intent
· Detect root-level process execution spawned from a non-system Android application context, consistent with local privilege escalation behavior.
Purpose
· Identify post-exploitation privilege escalation outcomes potentially linked to CVE-2026-21385.
Tuning Explanation
· Restricts to Android platform
· Excludes legitimate system_server lineage
· Looks for common privilege escalation utilities
· Designed for Deep Visibility or STAR rule conversion
· Intended for executive or high-risk device scope first
EndpointOS = "android"
AND (
ProcessUser = "root"
OR ProcessUserId = "0"
)
AND (
ProcessName IN ("su","sh","toybox","busybox")
OR ProcessCmd RegExp "su\\s|setenforce\\s+0|chmod\\s+4[0-9]{3}"
)
AND ParentProcessName NOT IN ("system_server","init","zygote")
AND ParentProcessPath RegExp "/data/app/|/data/local/tmp/"
Elastic
Rule Name
Display Crash Followed by Privileged Execution Sequence
Detection Intent
Correlate display fault events with privileged process spawn
Purpose
Increase confidence detection through event sequencing
Tuning Explanation
· Requires Android log ingestion
· Adjust field mappings to ECS equivalent
sequence by host.id with maxspan=10m
[any where event.dataset == "android.logcat" and
(message like "*display*" or message like "*surfaceflinger*") and
(message like "*Fatal*" or message like "*SIGSEGV*")]
[process where user.name in ("root","system")]
Rule Name
Android Privilege Escalation Root Spawn – Auto Mitigate
Detection Intent
Detect and automatically mitigate unauthorized root-context process execution originating from non-system Android application paths.
Purpose
Contain exploitation behavior consistent with CVE-2026-21385 post-exploitation privilege escalation.
Tuning Explanation
· Restricted to Android endpoints
· Requires root user or UID 0
· Excludes legitimate system parents
· Focuses on common privilege-escalation utilities
· Designed for STAR Custom Rule with Kill + Quarantine action
STAR Detection Logic (Deep Visibility Compatible)
EndpointOS = "android"
AND (
ProcessUser = "root"
OR ProcessUserId = "0"
)
AND (
ProcessName IN ("su","sh","toybox","busybox")
OR ProcessCmd RegExp "su\\s|setenforce\\s+0|chmod\\s+4[0-9]{3}"
)
AND ParentProcessName NOT IN ("system_server","init","zygote")
AND ParentProcessPath RegExp "/data/app/|/data/local/tmp/"
STAR Response Actions
· Kill Process
· Quarantine File (if applicable)
· Mark as Threat
· Trigger Network Containment (optional for executive devices)
Deployment Guidance
· Roll out initially in Detect mode for 24 hours
· Promote to Protect mode once false positive baseline confirmed
· Scope to high-risk device groups first
Rule Name
Android Privilege Escalation – Executive Device Protection
Detection Intent
Aggressively detect root-context execution on executive-assigned Android devices.
Purpose
Provide heightened protection for C-Suite, legal, board, and travel-exposed personnel.
Tuning Explanation
· Scoped to specific SentinelOne Policy Group (e.g., “Executive-Mobile”)
· Removes some parent exclusions to increase sensitivity
· Includes detection of abnormal shell invocation even without su
· Designed for Protect Mode
Deep Visibility / STAR Logic
EndpointOS = "android"
AND PolicyName = "Executive-Mobile"
AND (
ProcessUser = "root"
OR ProcessUserId = "0"
)
AND (
ProcessName IN ("su","sh","toybox","busybox")
OR ProcessCmd RegExp "setenforce\\s+0|mount\\s+-o\\s+remount|chmod\\s+4[0-9]{3}"
)
AND ParentProcessPath RegExp "/data/app/|/data/local/tmp/"
Recommended Response
· Kill Process
· Immediate Network Containment
SOC High Priority Alert
· Automated ticket creation
Rationale
Executive devices carry:
· MFA tokens
· Board communications
· Sensitive legal data
· Travel-based exposure risk
False positive tolerance should be near zero for this group.
Rule Name
Android Repeated Root Utility Execution Anomaly
Detection Intent
Detect repeated suspicious root utility usage outside baseline system activity.
Purpose
Provide sustainable long-term monitoring with minimal false positives.
Tuning Explanation
Requires repeated execution within time window
· Maintains system parent exclusions
· Suitable for always-on monitoring
· No auto-kill recommended
Deep Visibility Query
EndpointOS = "android"
AND (
ProcessUser = "root"
OR ProcessUserId = "0"
)
AND ProcessName IN ("su","toybox","busybox")
AND ParentProcessName NOT IN ("system_server","init","zygote")
| group by EndpointName, ProcessName
| filter count() >= 3
Recommended Response
• Alert Only
• SOC Review
• Trigger secondary log review (logcat + SELinux events)
Noise Reduction Controls
• Exclude known developer device group
• Exclude managed test devices
• Exclude sanctioned root-enabled devices
Deployment Strategy Recommendation
· Phase 1 (Immediate)
o Deploy Executive Policy Rule in Protect Mode
· Phase 2 (48 Hours)
o Deploy STAR Auto-Mitigation in Detect Mode enterprise-wide
· Phase 3 (After Baseline)
o Promote STAR rule to Protect Mode
o Enable Low-Noise Rule for continuous monitoring
Sigma
Rule Name
· Android Root Process from Untrusted App Context
Detection Intent
· Detect root-level execution originating from application UID range
Purpose
· Privilege escalation outcome detection
Tuning Explanation
· Map UID or app lineage fields appropriately
Title: Android Root Process from App Context
logsource:
product: android
category: process_creation
detection:
selection_root:
user|contains: "root"
selection_parent:
parent_image|contains:
- "com."
- "/data/app/"
condition: selection_root and selection_parent
level: high
tags:
- attack.t1068
Yara
Rule Name
Android Post Exploit Privilege Escalation Heuristic
Detection Intent
Detect post-exploit artifacts staged to disk
Purpose
Support forensic artifact scanning
Tuning Explanation
· Heuristic only
· Tune with environment-specific strings
rule CYBERDAX_Android_PostExploit_Heuristic
{
meta:
description = "Android post privilege escalation heuristic"
author = "CyberDax LLC"
version = "1"
strings:
$s1 = "setenforce 0" ascii nocase
$s2 = "chmod 4755" ascii nocase
$s3 = "/data/local/tmp" ascii
$s4 = "su -c" ascii nocase
condition:
2 of ($s*)
}
Delivery Methods
· Malicious sideloaded application
· Trojanized legitimate application
· Targeted surveillance toolkit deployment
· Exploit chaining with other local vulnerabilities
7-Day Response Plan
Day 1
· Identify Qualcomm chipset exposure
· Initiate hunt queries
Day 2–3
· Validate Android patch level
· Prioritize executive and high-risk devices
Day 4–5
· Enforce security updates
· Disable sideloading if permitted
Day 6
· Conduct targeted mobile forensic review
Day 7
· Executive risk validation and remediation confirmation
Defensive Control and Hardening Architecture
Objective
· Prevent zero-day exploitation of Qualcomm display driver memory corruption
· Detect and contain privilege escalation to root context
· Prevent persistence on executive Android devices
· Disrupt credential harvesting and token abuse
· Reduce enterprise blast radius from mobile compromise
· Elevate executive device risk to Tier-Zero governance visibility
Layer 1
Exploit Surface Reduction & Device Hygiene
Control Focus: Reduce likelihood of exploit trigger during zero-day window.
· Enforce rapid patch deployment prioritizing Qualcomm chipset devices
· Disable sideloading and unknown APK installation enterprise-wide
· Implement executive device application allow-listing
· Disable developer mode and USB debugging
· Restrict WebView and browser exposure to approved configurations
· Block installation from third-party app stores
Risk Mitigated
· T1475 – Deliver Malicious App
· T1203 – Exploitation for Client Execution
Layer 2
Kernel & Privilege Escalation Containment
Control Focus: Detect and suppress UID-to-root transition.
· Centralize logcat, SELinux, and kernel telemetry ingestion
· Alert on UID transition from application context to UID 0
· Alert on SELinux enforcement state modification
· Automatically quarantine device upon confirmed root detection
· Require re-attestation before restoring enterprise access
Risk Mitigated
· T1068 Exploitation for Privilege Escalation
· T1548 Abuse Elevation Control Mechanism
Layer 3
Persistence & System Integrity Enforcement
Control Focus: Prevent durable foothold post-escalation.
· Monitor system service and autostart modifications
· Enforce verified boot and integrity validation
· Implement file integrity monitoring on system partitions
· Block execution from world-writable directories
· Validate system service registry against baseline on reboot
Risk Mitigated
· T1547 Boot or Logon Autostart Execution
· Long-dwell privileged persistence
Layer 4
Identity & Token Containment Architecture
Control Focus: Prevent enterprise expansion after mobile compromise.
· Enforce conditional access re-authentication upon device risk elevation
· Shorten OAuth token lifetimes for executive roles
· Enable continuous access evaluation
· Require step-up MFA for high-sensitivity cloud access
· Revoke tokens automatically upon device compromise signal
Risk Mitigated
· T1555 Credentials from Password Stores
· T1550 Use of Stolen Authentication Tokens
· T1021 Remote Services
Layer 5
Command and Control Suppression
Control Focus: Reduce survivability of encrypted outbound C2.
· Implement DNS anomaly detection for executive device groups
· Baseline TLS fingerprints for managed mobile fleet
· Alert on rare SNI or newly registered domains
· Enforce secure DNS with logging enabled
· Weight anomaly scoring higher for executive device traffic
Risk Mitigated
· T1102 Web Service
· T1071.001 Web Protocols
Layer 6
Data Exfiltration & Cloud Abuse Monitoring
Control Focus: Detect staged data removal from compromised device.
· Monitor large outbound HTTPS and VPN transfer deviations
· Alert on abnormal email synchronization spikes
· Detect token reuse across new geolocations
· Enable mobile DLP for executive mailboxes
· Monitor cloud upload anomalies originating from mobile sessions
Risk Mitigated
· T1041 Exfiltration Over C2 Channel
· T1567 Exfiltration to Cloud Storage
Layer 7
Telemetry Integrity & Anti-Tamper Controls
Control Focus: Prevent stealth and logging suppression.
· Forward mobile logs to centralized immutable storage
Alert on log truncation or logging silence
· Enforce write-once retention for security telemetry
· Monitor for debugger or sandbox evasion artifacts
· Maintain minimum 180-day searchable retention
Risk Mitigated
· T1070 Indicator Removal on Host
· Long-dwell stealth persistence
Layer 8
Executive Device Segmentation & Governance
Control Focus: Treat executive Android devices as Tier-Zero digital assets.
· Place executive devices in dedicated policy group
· Apply stricter anomaly thresholds and lower detection tolerance
· Implement dedicated SOC hunt queries for executive fleet
· Require board-level reporting on executive device risk posture
· Conduct annual red-team simulation of mobile privilege escalation
Risk Mitigated
· High-value targeting risk
· Extended espionage dwell time
· Governance visibility gaps
Architectural Outcome
When fully implemented, this layered architecture:
· Reduces zero-day exploit window impact
· Contains privilege escalation before enterprise pivot
· Prevents durable root persistence
· Disrupts token theft and cloud lateral movement
· Detects encrypted command channels
· Limits blast radius of executive mobile compromise
· Aligns Android zero-day defense with enterprise identity governance
Estimated Probability of Recurrence (12-Month Horizon)
· 70 percent
Justification:
· Memory corruption vulnerabilities remain prevalent
· Qualcomm components widely deployed
· Active exploitation increases replication likelihood
Post-Incident Insights and Recommendations
Structural Lessons
Mobile Endpoints Are Identity Infrastructure, Not Peripheral Devices
Enterprise security models continue to treat mobile devices as user productivity tools rather than identity-bearing control planes. Executive Android devices often hold persistent authentication tokens, MFA approvals, encrypted communications, and cloud session artifacts. A kernel-level compromise on mobile is functionally equivalent to compromising a privileged workstation. Control architecture must reflect that reality.
Compliance Does Not Equal Detection
Patch dashboards and MDM compliance metrics provide hygiene visibility, not exploit visibility. During active zero-day windows, organizations relying solely on compliance status lack the telemetry required to detect privilege escalation events. Kernel-level exploitation can occur while a device remains “compliant.”
Privilege Escalation Is the True Risk Pivot
The memory corruption flaw itself is not the enterprise risk event. The risk materializes at the moment of UID-to-root transition. Organizations without centralized logcat, SELinux, and kernel telemetry ingestion are structurally blind at the most critical trust-breaking stage of the attack chain.
Identity Containment Speed Determines Financial Impact
In mobile exploit scenarios, financial exposure is driven less by initial compromise and more by the speed of token invalidation, conditional access enforcement, and executive device containment. Delays in identity containment expand blast radius across SaaS, email, and cloud systems.
Executive Device Segmentation Is Often Insufficient
High-risk users frequently operate under the same mobile policy baselines as general workforce populations. This creates disproportionate exposure. Executive device groups require stricter anomaly thresholds, faster patch cadence, and dedicated SOC monitoring.
Network-Only Detection Strategies Are Structurally Inadequate
Local privilege escalation and kernel exploitation produce minimal network indicators in early stages. Enterprises relying primarily on network telemetry will detect compromise only after persistence or data staging begins. Detection strategy must extend into endpoint kernel-level visibility.
Zero-Day Windows Expose Architectural Maturity Gaps
Active exploitation events test whether organizations have layered defensive controls or rely on single-point compliance. Mature environments demonstrate:
· Mobile telemetry parity with desktop EDR
· Cross-domain correlation between device and identity signals
· Executive rapid-patch pathways
· Automated token containment triggers
Less mature environments rely on reactive patch cycles and ad hoc hunting.
Governance Visibility for Mobile Risk Is Often Underdeveloped
Board and executive reporting frequently emphasizes server and cloud threats while underrepresenting mobile risk exposure. As mobile devices increasingly serve as identity hubs, governance frameworks must elevate mobile compromise scenarios to Tier-Zero reporting categories.
Structural Conclusion
CVE-2026-21385 does not merely expose a chipset vulnerability.
It exposes architectural assumptions about mobile risk, identity trust, and detection maturity.
As executive devices increasingly function as identity control planes, kernel-level mobile compromise must be treated as a Tier-Zero enterprise event.
Organizations that recalibrate mobile security as identity infrastructure — not endpoint hygiene — will materially reduce financial, regulatory, and disclosure exposure in future zero-day cycles.
Enterprise Risk Implications
· Mobile devices represent Tier-Zero identity endpoints and must be monitored with parity to desktop EDR coverage.
· Kernel-level zero-day exploitation can occur without traditional network indicators, reducing reliance on perimeter detection.
· Privilege escalation on executive mobile devices presents disproportionate enterprise risk due to token reuse and SaaS access.
· Compliance-driven security programs create a false sense of control when kernel-level telemetry is absent.
· Identity containment speed is as critical as exploit detection speed.
Architectural Recommendations
Elevate Mobile Telemetry to First-Class Security Signal
· Ingest logcat, SELinux, and kernel telemetry into central SIEM.
· Apply privilege-escalation correlation rules equivalent to Windows/Linux EDR standards.
· Treat mobile privilege escalation alerts as high-severity identity events.
Establish Executive Rapid-Patch Pathway
· Create a controlled but accelerated patch deployment exception process for executive device groups.
· Allow emergency vendor firmware updates to bypass standard rollout delays.
· Implement executive device compliance validation within 24–48 hours of vendor advisory.
3. Formalize Continuous Android Exploit Hunting Cadence
· Implement quarterly mobile exploit simulation exercises.
· Establish recurring hunt queries for UID transition, SELinux manipulation, and kernel crash anomalies.
· Maintain exploit telemetry baselines per chipset family (e.g., Qualcomm variants).
Harden Application Control Policies
· Enforce strict application allow-listing for executive devices.
· Disable sideloading and unknown APK installation enterprise-wide.
· Restrict developer mode and debugging capabilities.
Strengthen Mobile Conditional Access Enforcement
· Require step-up MFA when device risk score changes.
· Shorten OAuth token lifetimes for executive roles.
· Enforce continuous access evaluation for mobile sessions.
· Automatically revoke tokens upon confirmed device compromise.
Treat Executive Mobile Devices as Tier-Zero Assets
· Apply stricter anomaly thresholds.
· Segregate executive devices into dedicated monitoring policies.
· Provide quarterly board-level reporting on executive mobile risk posture.
Executive Closing Insight
Mobile zero-day exploitation has become a primary identity compromise vector with disproportionate financial impact when executive devices are involved.
Organizations that do not:
· Centralize mobile telemetry
· Enforce rapid executive patch cycles
· Contain token blast radius
will experience disproportionate impact from targeted mobile exploitation campaigns.
References
Qualcomm Security Bulletin
· hxxps://www[.]qualcomm[.]com/company/product-security/bulletins
National Vulnerability Database
· hxxps://nvd.nist[.]gov/vuln/detail/CVE-2026-21385
CISA Known Exploited Vulnerabilities Catalog
· hxxps://www[.]cisa[.]gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-21385