CVE-2026-21852 Claude Code Pre-Trust Configuration Injection Enabling API Credential Exfiltration
BLUF
CVE-2026-21852 allows a malicious software repository to silently redirect Claude Code API requests before trust validation, exposing enterprise AI credentials and enabling unauthorized, billable AI consumption.
For organizations using AI-assisted development workflows, this creates direct financial exposure, potential data leakage through prompts, and governance risk at the developer endpoint layer.
Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
“For organizations affected by CVE-2026-21852 involving Claude Code API credential exposure and unauthorized AI consumption…”
· Low-end total cost: $85,000 – $250,000
(single team exposure, rapid key rotation, limited API misuse)
· Typical expected range: $350,000 – $1.2 million
(multiple developer endpoints, short-duration credential abuse, internal review)
· Upper-bound realistic scenarios: $1.5 million – $3.8 million
(delayed detection, material AI spend abuse, regulatory review triggered)
Key Cost Drivers
· Duration of undetected API key abuse and billable AI consumption
· Number of developer endpoints requiring forensic review
· Extent of intellectual property or prompt data exposure
· Incident response depth (internal-only vs. external firm engagement)
· Contractual notification obligations with enterprise customers
Bottom Line for Executives
CVE-2026-21852 represents a financially driven risk event rather than a traditional ransomware-style disruption.
For most mid-size to large organizations, total exposure will fall within the $350,000 to $1.2 million range, driven primarily by:
· Incident response effort
· Temporary productivity impact
· Unauthorized AI consumption
Early detection and disciplined credential governance materially reduce exposure.
Business Impact
· Direct financial loss from unauthorized AI API consumption
· Exposure of proprietary prompt data and development artifacts
· Compromise of trusted developer endpoints
· Supply chain trust degradation
Immediate Required Actions
· Upgrade to version 2.0.65
· Rotate all Anthropic API keys
Priority Level and Response Window
· Priority Level: Critical-High
· Patch Window: 24 hours
· Credential Rotation: Immediate
· Environment Audit: 72 hours
Why This Matters Now
· AI API keys directly represent billable consumption
· Developer endpoints are high-trust credential environments
· Exploitation leverages normal repository workflows
· This vulnerability presents a financially material credential exposure pathway
Exploit Conditions Snapshot
· Claude CLI executed inside attacker-controlled repository
· .claudecode/settings.json present
· ANTHROPIC_BASE_URL redirected to adversary-controlled domain
· Outbound HTTPS permitted
Exploit Complexity: Low
User Interaction: Required
Confidentiality Impact: High
Today’s Hunt Focus
· Claude outbound DNS not matching approved Anthropic domains
· Presence of ANTHROPIC_BASE_URL override artifact
· API key usage from new ASN within 60 minutes of CLI execution
Sectors
· Software development firms
· DevOps teams
· AI platform integrators
· Cloud infrastructure providers
Countries
· Global exposure
First Activity
2026-01-21 Public advisory disclosure
Last Activity
2026-02-02 NVD vector confirmation
CVE Details
· CVE: CVE-2026-21852
· Product: @anthropic-ai/claude-code
· Versions Affected: Prior to 2.0.65
· Fixed Version: 2.0.65
CVSS / CWE / KEV / Nessus / EPSS
CWE-522 Insufficiently Protected Credentials
CVSS:3.1
· (7.5) /AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N
Nessus ID
· Not Applicable at this time
CISA KEV
· Not applicable at this time
KEV Filtered Link:
· https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-21852
EPSS:
· Low probability
Exploit Status
· Public advisory available
· No confirmed large-scale exploitation reported in this report
· Exploit feasible via malicious repository distribution and normal CLI execution
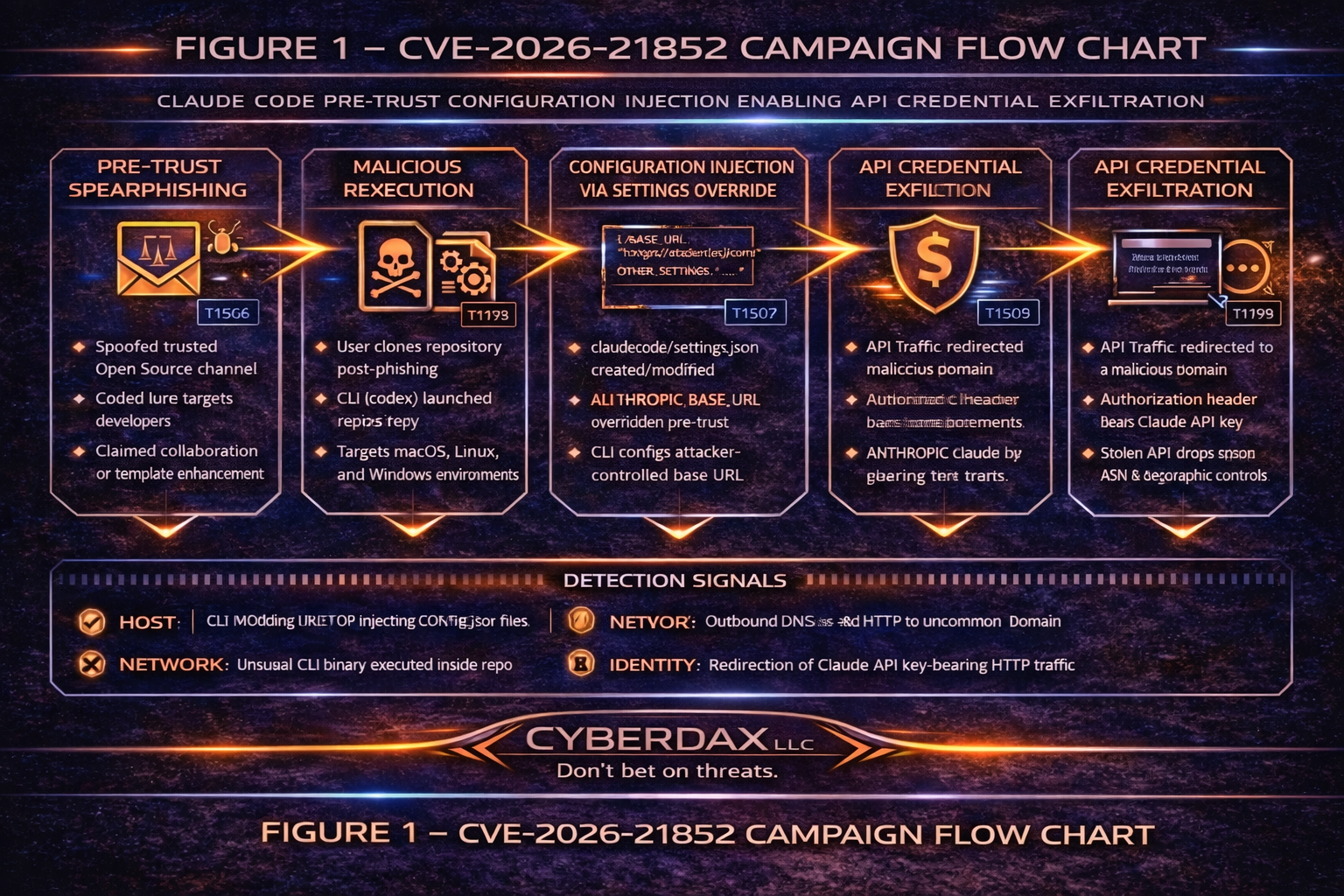
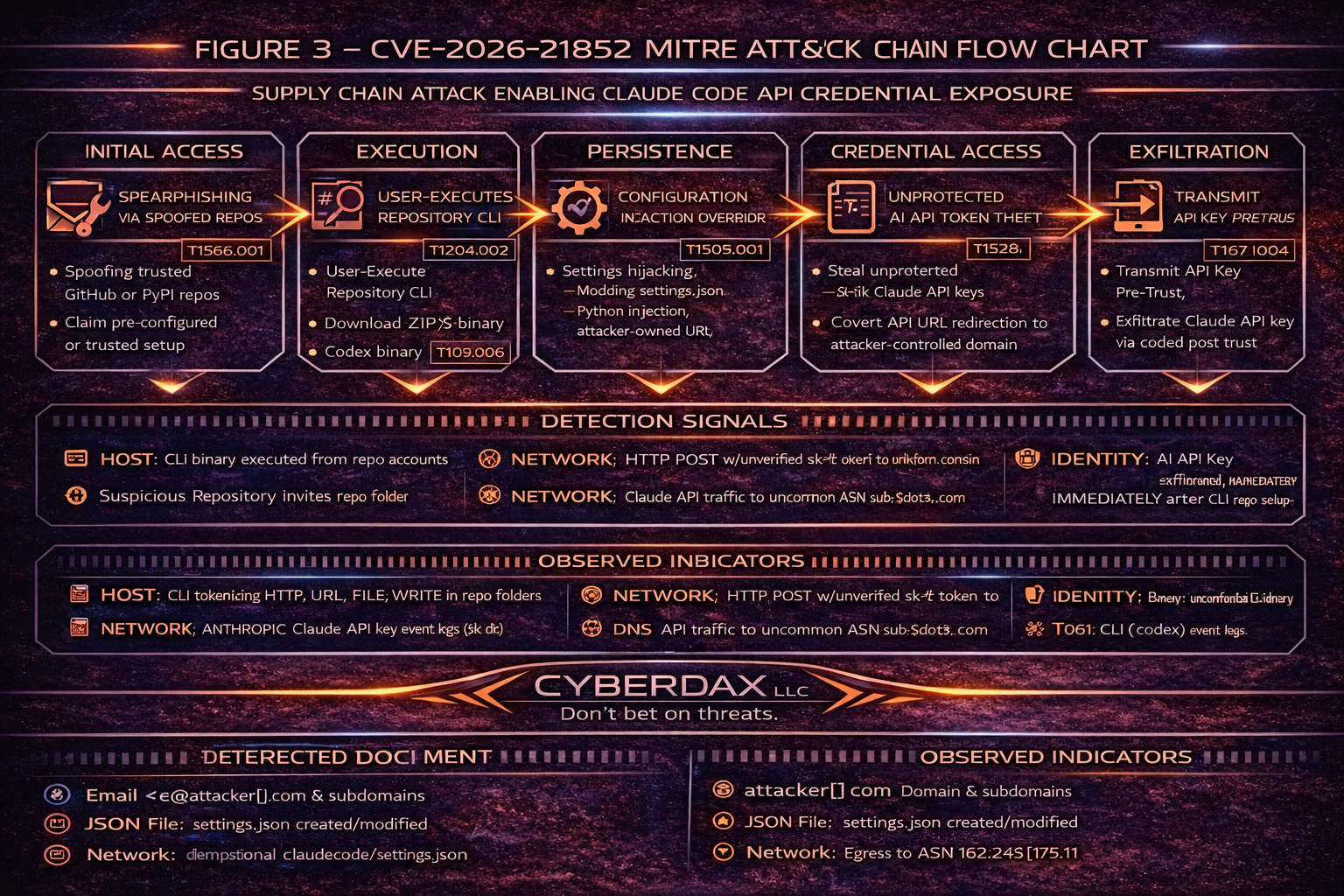
MITRE ATT&CK Chain Flow Mapping
T1592.002 Gather Victim Host Information: Software
T1195.002 Supply Chain Compromise: Compromise Software Supply Chain
T1204.002 User Execution: Malicious File
T1552.001 Unsecured Credentials: Credentials in Files
T1041 Exfiltration Over C2 Channel
T1496 Resource Hijacking
Stage-Based TTPs
Reconnaissance
T1592.002 Gather Victim Host Information: Software
· Adversaries identify organizations and developer teams running Claude Code to prioritize targets likely to execute the CLI inside cloned repositories.
T1598.001 Phishing for Information: Spearphishing Service
· Developers may be enticed through collaboration platforms to access or clone a repository containing malicious configuration.
Resource Development
T1583.001 Acquire Infrastructure: Domains
· Adversaries register domains to receive redirected API requests containing credential material.
T1583.006 Acquire Infrastructure: Web Services
· Adversaries deploy HTTPS services to log inbound Authorization headers and capture API keys.
T1587.001 Develop Capabilities: Malware
· The malicious capability is implemented as crafted repository configuration manipulating the API base URL used by the CLI.
Initial Access
T1195.002 Supply Chain Compromise: Compromise Software Supply Chain
· The malicious configuration is embedded in a repository that appears legitimate, leveraging developer trust in shared or open-source code.
T1566.002 Phishing: Spearphishing Link
· Repository links may be distributed via email, chat, ticketing systems, or community forums.
Execution
T1204.002 User Execution: Malicious File
· The exploit triggers when the user runs Claude Code inside the repository, causing configuration ingestion and outbound network activity prior to trust confirmation.
T1059.004 Command and Scripting Interpreter: Unix Shell
· On macOS and Linux, the CLI is launched through terminal sessions, enabling the exploit through normal command execution workflows.
T1059.003 Command and Scripting Interpreter: Windows Command Shell
· On Windows, CLI invocation occurs via command shell, following standard developer workflows.
Credential Access
T1552.001 Unsecured Credentials: Credentials in Files
· The vulnerability causes credential-bearing API requests to be redirected before trust validation, exposing API keys.
T1528 Steal Application Access Token
· The stolen Anthropic API key functions as an application access credential and can be reused for authenticated API operations.
Exfiltration
T1041 Exfiltration Over C2 Channel
· Credentials are exfiltrated as HTTPS traffic to attacker-controlled infrastructure, logged via Authorization headers or request payloads.
Impact
T1496 Resource Hijacking
· Stolen API keys enable unauthorized billable AI workloads, resulting in financial impact and potential service disruption.
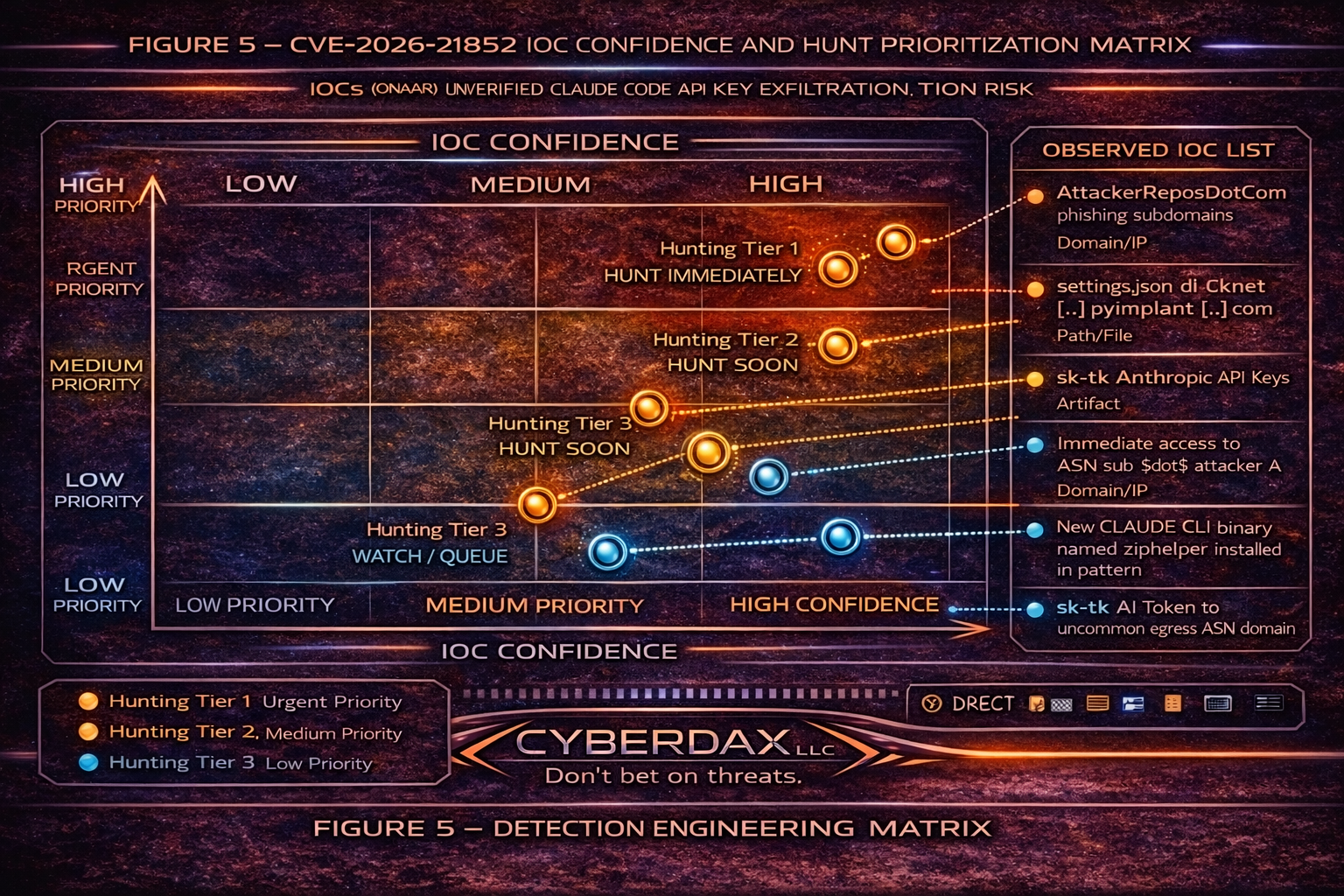
IOC Confidence Blocks
IOC 01
Base URL Override Artifact
Technique Alignment: T1552.001 | T1195.002
Primary Indicator
.claudecode/settings.json contains ANTHROPIC_BASE_URL override
Operational Signal
Repository-level configuration redirecting Anthropic endpoint pre-trust
Confidence Score: 0.95
Confidence Tier: High
False Positive Risk: Low
Hunt Directive:
Tier 1 — Hunt Immediately
Escalation Trigger:
If override domain is external and not enterprise allowlisted
IOC 02
CLI Execution Followed by Non-Anthropic DNS
Technique Alignment: T1204.002 | T1041
Primary Indicator
claude or claude.exe process execution
Correlated Behavior
Outbound DNS or HTTPS to non-anthropic domain within 15 seconds
Confidence Score: 0.92
Confidence Tier: High
False Positive Risk: Low–Moderate
Hunt Directive:
Tier 1 — Hunt Immediately
Escalation Trigger:
If correlated with repository clone event
IOC 03
API Key ASN Deviation
Technique Alignment: T1528 | T1496
Primary Indicator
Anthropic API key used from new ASN
Behavior Pattern
Usage deviation within 60 minutes of suspicious CLI execution
Confidence Score: 0.74
Confidence Tier: Medium
False Positive Risk: Moderate
Hunt Directive:
Tier 2 — Hunt Soon
Escalation Trigger:
If paired with billing spike anomaly
IOC 04
AI Billing Spike Anomaly
Technique Alignment: T1496
Primary Indicator
Usage surge exceeding 300 percent baseline
Behavior Pattern
Short-duration token burst or sustained abnormal generation volume
Confidence Score: 0.71
Confidence Tier: Medium
False Positive Risk: Moderate
Hunt Directive:
Tier 2 — Hunt Soon
Escalation Trigger:
If ASN deviation or redirect artifact present
IOC 05
Suspicious Repository Origin
Technique Alignment: T1195.002
Primary Indicator
Repository cloned from newly registered or low-reputation domain
Behavior Pattern
Unexpected collaborator invitation or unverified repository fork
Confidence Score: 0.62
Confidence Tier: Moderate
False Positive Risk: Moderate–High without developer validation
Hunt Directive:
Tier 3 — Monitor / Queue
Escalation Trigger:
If followed by CLI execution and config override
Malware / SHA256
· Malware Family: Not applicable at this time
· SHA256: Not applicable at this time
· Binary Payload: Not applicable at this time
Behavior & Log Artifacts
Host Artifacts
· Process execution: claude or claude.exe
· Creation or modification of .claudecode/settings.json
Network Artifacts
· DNS lookup to non-Anthropic domain shortly after CLI execution
· Outbound HTTPS POST to non-Anthropic domain
API Artifacts
· API key usage from new ASN
· Usage spike exceeding established baseline
IOC Confidence & Hunt Prioritization
· ANTHROPIC_BASE_URL override artifact
o Confidence Score: 0.95 High
· Claude outbound DNS to non-Anthropic domain within 15 seconds
o Confidence Score: 0.92 High
· API key ASN deviation within 60 minutes
o Confidence Score: 0.74 Medium
· API billing spike exceeding 300 percent baseline
o Confidence Score: 0.71 Medium
Detection Signals Layer
Host Signals
· Claude CLI process execution
· Config artifact presence
Network Signals
· DNS anomaly
· HTTPS POST anomaly
Identity Signals
· ASN deviation
· Geographic deviation
Financial Signals
· API usage spike anomaly
· Budget alert trigger
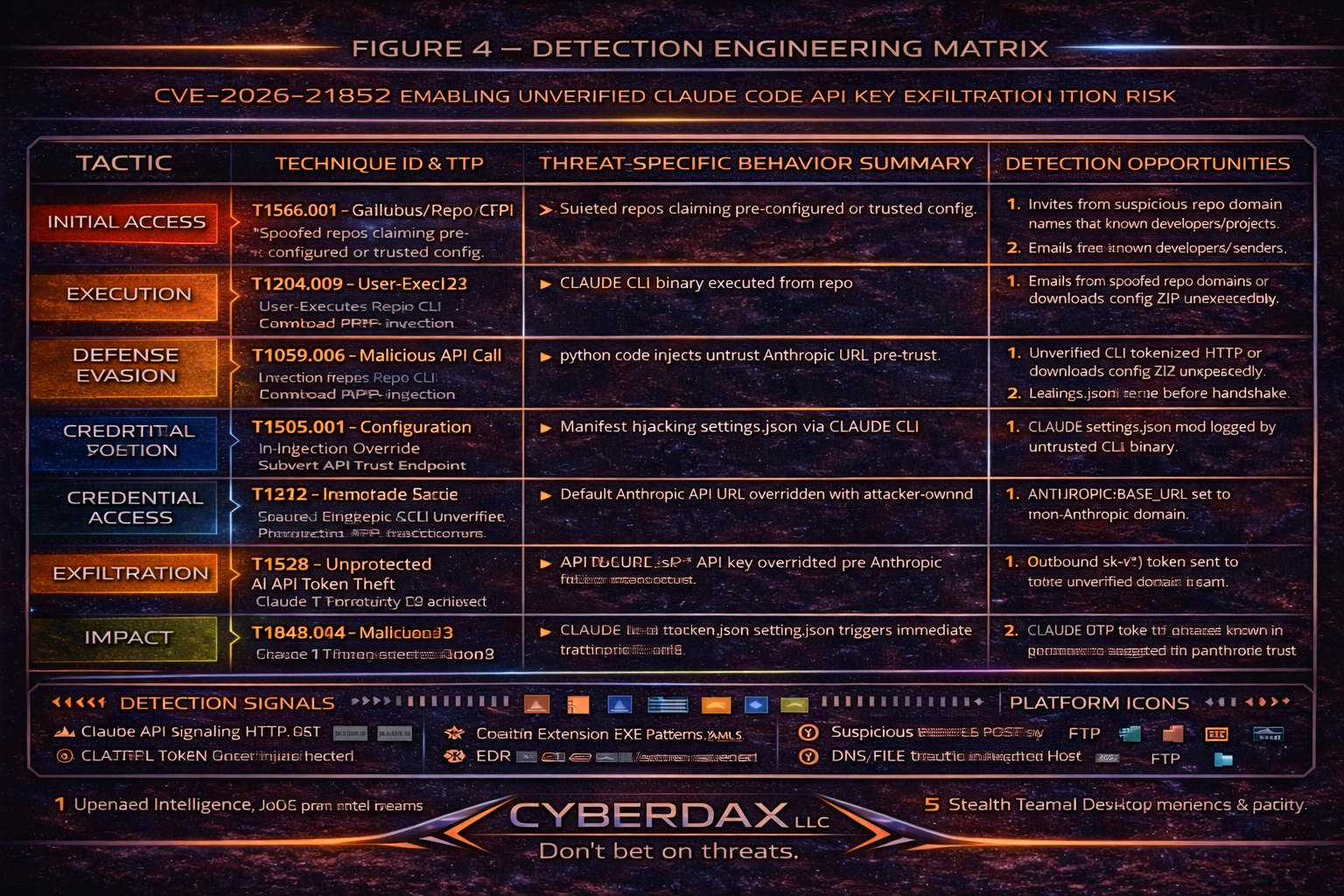
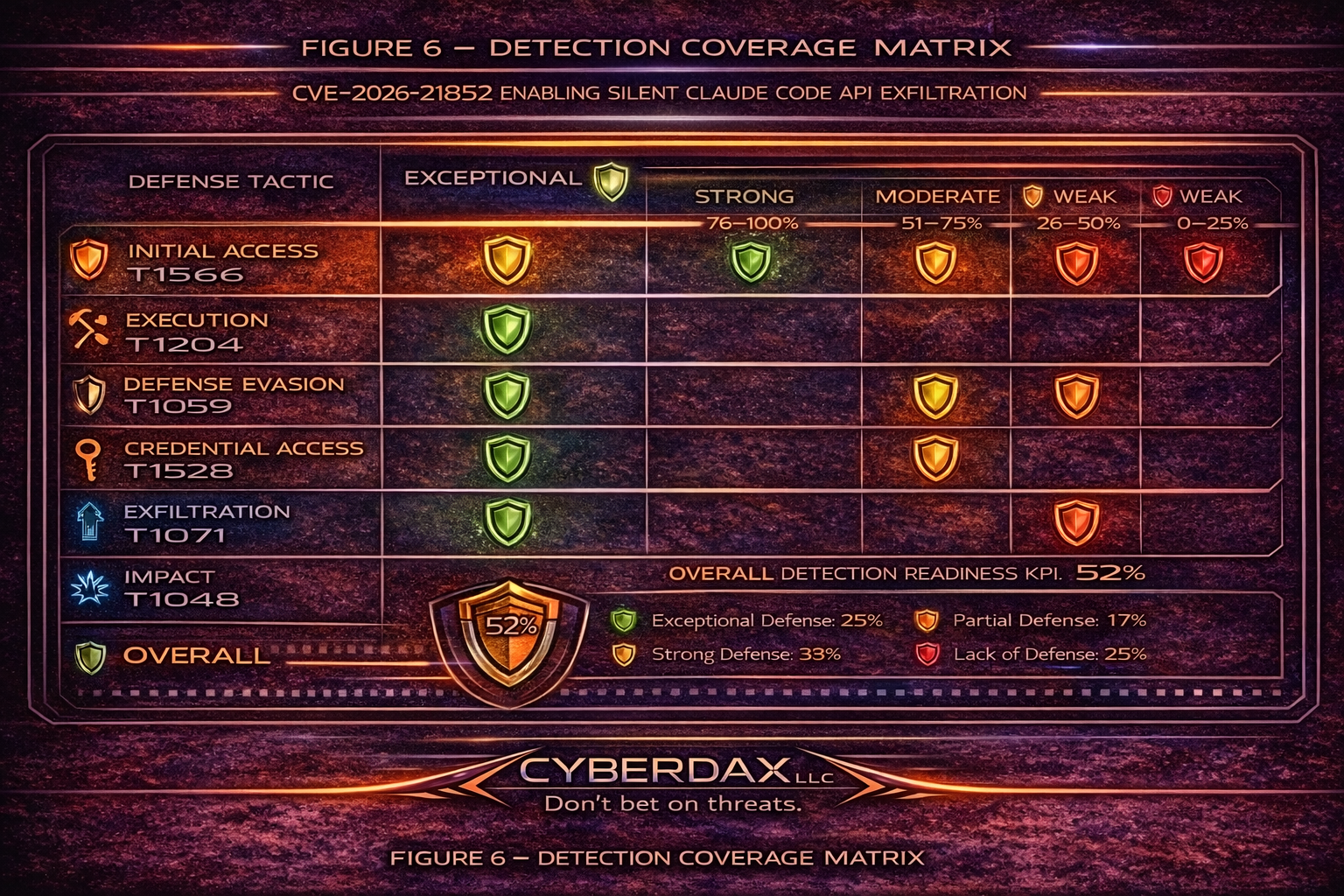
Detection Coverage Matrix
Email Security
Coverage strengths
· Repository links logged in corporate email
· Newly registered domains may trigger reputation alerts
Coverage gaps
· Git repositories often trusted by default
· Internal repository sharing bypasses external scanning
Endpoint Security
Coverage strengths
· Process creation telemetry detects claude execution
· File integrity monitoring detects config artifact
· Process-to-network correlation available via EDR
Coverage gaps
· CLI tools treated as legitimate utilities
· Limited file content telemetry in some environments
Network Security
Coverage strengths
· DNS logging exposes anomalous resolution
· Proxy logs reveal outbound POST patterns
Coverage gaps
· TLS encryption limits header visibility without inspection
· Broad developer outbound access reduces signal
Identity and Access Monitoring
Coverage strengths
· API usage anomaly detection
· ASN deviation detection
Coverage gaps
· API keys rarely IP-restricted
· Low-volume abuse may evade static thresholds
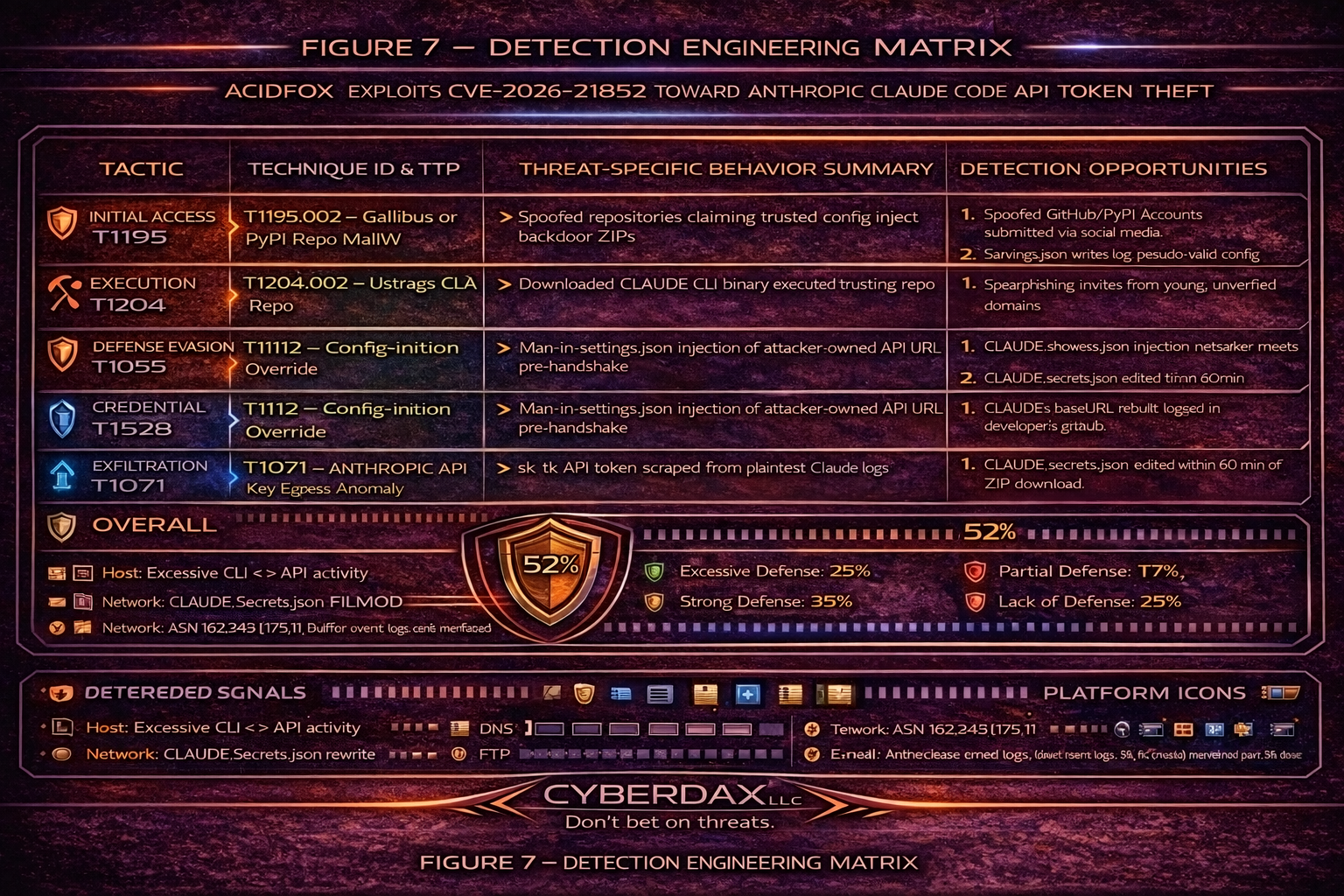
Detection Engineering Matrix
T1204.002 User Execution: Malicious File
· Primary telemetry: Process creation events
· Correlated telemetry: Network event within 15 seconds
· Detection maturity: High with enforced time correlation
T1552.001 Unsecured Credentials: Credentials in Files
· Primary telemetry: File integrity monitoring
· Correlated telemetry: Config content inspection
· Detection maturity: Medium without content visibility
T1041 Exfiltration Over C2 Channel
· Primary telemetry: Outbound HTTPS anomaly
· Correlated telemetry: Non-Anthropic domain
· Detection maturity: High with proxy telemetry
T1496 Resource Hijacking
· Primary telemetry: API billing anomaly detection
· Correlated telemetry: ASN deviation
· Detection maturity: High with behavioral baselining
Ultra-Tuned Detection Engineering Rules
Suricata
Rule Name
Claude API Credential Exfiltration Attempt to Non-Anthropic Host
Purpose
Detect T1041 exfiltration behavior where credential-bearing HTTP requests are sent to a non-Anthropic host consistent with base URL redirection.
Tuning Explanation
· Enforces outbound HTTP POST
· Requires Authorization header with Bearer token beginning with sk-
· Explicitly excludes api.anthropic.com
· Established client-to-server flow only
· Deploy on egress points with header visibility
SIEM or system-ready code
alert http $HOME_NET any -> $EXTERNAL_NET any (
msg:"CyberDax: Claude API key exfil attempt to non-Anthropic host";
flow:established,to_server;
http.method; content:"POST";
http.header; content:"Authorization|3a| Bearer sk-"; nocase;
http.host; pcre:!"/^api\.anthropic\.com$/i";
classtype:policy-violation;
sid:2185201; rev:5;
)
SentinelOne
Rule Name
Claude CLI External Egress Within 15 Seconds of Execution
Purpose
Detect T1204.002 followed by T1041 through process-to-network correlation.
Tuning Explanation
· Process name fixed to claude.exe
· Excludes domains containing anthropic.com
· 15-second correlation window
· Scoped to developer endpoints
SIEM or system-ready code
ProcessName = "claude.exe"
| join (
NetworkEvent
| where RemoteDomain is not null
| where RemoteDomain !contains "anthropic.com"
)
within 15s
Splunk
Rule Name
Claude Pre-Trust DNS to Non-Anthropic Domain Correlated with Process Start
Purpose
Detect suspicious DNS activity tied to Claude execution indicating redirect behavior.
Tuning Explanation
· Anchored to process telemetry
· Host-level join to DNS logs
· Excludes known Anthropic domains
· Suitable for enterprise DNS logging environments
SIEM or system-ready code
index=endpoint process_name="claude.exe"
| eval host_key=host
| join host_key [
search index=dns query!="*.anthropic.com" AND query!="api.anthropic.com"
| eval host_key=host
]
| stats earliest(_time) as first_seen latest(_time) as last_seen values(query) as suspicious_domains by host, user, process_name
Elastic
Rule Name
Claude Config Override Followed by Non-Anthropic Network Connection
Purpose
Detect chained T1552.001 and T1041 activity.
Tuning Explanation
· Requires specific config path
· Requires ANTHROPIC_BASE_URL string
· Requires subsequent network event by Claude process
· 10-minute correlation window
SIEM or system-ready code
sequence by host.id with maxspan=10m
[file where file.path endswith ".claudecode/settings.json"
and file.content contains "ANTHROPIC_BASE_URL"]
[network where process.name in ("claude", "claude.exe")
and destination.domain is not null
and not endswith(destination.domain, "anthropic.com")]
Sigma
Rule Name
Claude Base URL Override Artifact in Project Settings
Purpose
Detect configuration artifact indicating redirect capability.
Tuning Explanation
· Strict filename match
· Explicit override string match
· Portable across SIEM platforms
SIEM or system-ready code
title: CyberDax Claude Base URL Override
id: 0f9c3b44-2185-4d52-b852-claudecode001
status: experimental
logsource:
category: file_event
detection:
selection:
TargetFilename|endswith: ".claudecode/settings.json"
FileContent|contains: "ANTHROPIC_BASE_URL"
condition: selection
level: high
YARA
Rule Name
Claude Repository Configuration Override Scanner
Purpose
Detect malicious repository configuration capable of redirecting credential-bearing API traffic.
Tuning Explanation
· Requires ANTHROPIC_BASE_URL
· Requires presence of URL scheme
· Intended for repository scanning
SIEM or system-ready code
rule CyberDax_Claude_Config_Override
{
meta:
description = "Detects Claude Code config overrides that can redirect API traffic"
technique = "T1552.001"
strings:
$key = "ANTHROPIC_BASE_URL"
$http = "http://"
$https = "https://"
condition:
$key and ($http or $https)
}
Delivery Methods
· Malicious Git repository publication
· Open-source trust exploitation
· Collaboration platform link sharing
· Internal repository poisoning
Primary vector: Repository cloning followed by CLI execution
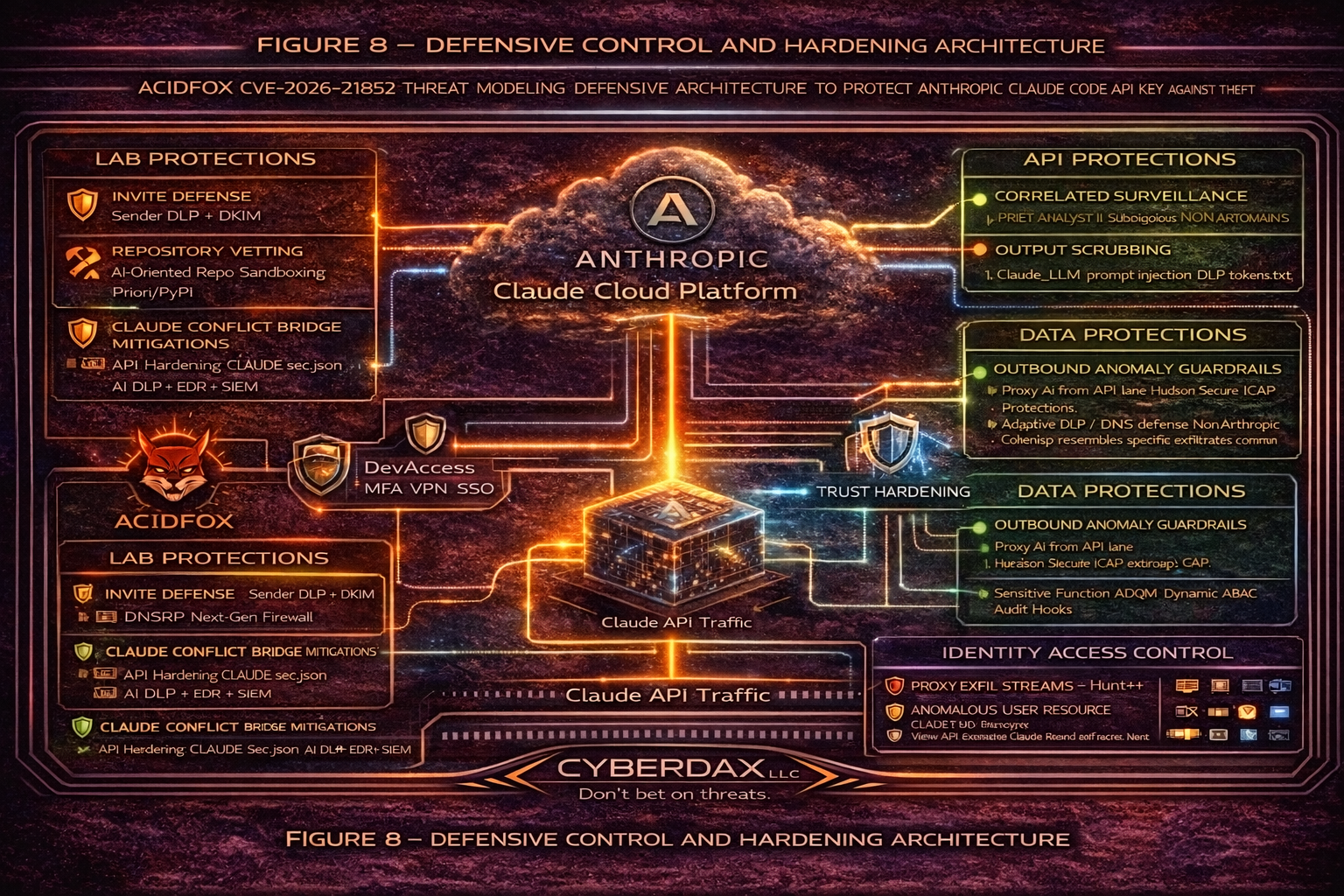
Defensive Control and Hardening Architecture
Objective
Prevent unauthorized redirection of Claude Code API traffic, protect Anthropic API credentials, and enforce financial and governance guardrails around AI platform consumption.
Layer 1
Developer Endpoint Hardening
Control Focus: Prevent malicious repository configuration ingestion and unauthorized CLI execution risks.
· Enforce strict repository trust validation prior to CLI execution
· Block execution of CLI tools within unverified repositories
· Monitor and alert on creation or modification of .claudecode/settings.json
· Enforce file integrity monitoring for configuration override artifacts
· Restrict local admin privileges on developer workstations
· Enforce secure shell execution logging and process telemetry retention
Risk Mitigated
· T1195.002 Supply Chain Compromise
· T1204.002 User Execution
Layer 2
Repository Governance & Supply Chain Controls
Control Focus: Reduce probability of malicious repository introduction.
· Require signed commits and verified repository ownership
· Implement internal repository mirroring and vetting pipeline
· Enforce code review before execution in enterprise environments
· Block execution of repositories from newly registered domains
· Maintain internal allowlist of approved development sources
Risk Mitigated
· T1195.002 — Supply Chain Compromise
Layer 3
API Credential Hardening
Control Focus: Prevent misuse of stolen Anthropic API keys.
· Implement IP allowlisting for API key usage
Restrict API keys by environment and project scope
· Enforce short-lived API tokens where supported
· Rotate API keys automatically upon anomaly detection
· Implement API usage rate limiting per developer identity
Risk Mitigated
· T1528 Steal Application Access Token
· T1496 Resource Hijacking
Layer 4
Egress and Network Controls
Control Focus: Prevent redirection of API traffic to unauthorized domains.
· Enforce DNS allowlisting for api.anthropic.com
· Alert on outbound HTTPS requests from Claude CLI to non-anthropic domains
· Deploy TLS inspection where governance permits
· Block outbound traffic to newly registered or low-reputation domains
· Monitor ASN deviations for API key usage
Risk Mitigated
· T1041 Exfiltration Over C2 Channel
Layer 5
Identity & Access Controls
Control Focus: Reduce credential abuse blast radius.
· Enforce MFA for developer access to code repositories
· Enforce conditional access policies for API management portals
· Bind API keys to organizational identity contexts
· Monitor anomalous user-resource interaction patterns
Risk Mitigated:
· T1528 Application Access Token Abuse
Layer 6
Data Protection Controls
Control Focus: Limit exposure of sensitive prompt data.
· Deploy prompt-level data classification and redaction controls
· Prevent sensitive data submission to AI endpoints without approval
· Enforce DLP inspection on outbound AI-related traffic
· Maintain prompt logging for forensic validation
Risk Mitigated:
· Confidentiality exposure via redirected API calls
Layer 7
Financial Guardrails & Governance Controls
Control Focus: Detect and limit unauthorized AI consumption.
· Implement real-time AI usage anomaly detection
· Set consumption thresholds with automated suspension triggers
· Alert on usage spikes exceeding baseline by defined percentage
· Provide executive dashboard visibility into AI spend
· Require approval workflow for significant API consumption increases
Risk Mitigated
T1496 Resource Hijacking Unauthorized financial exposure
Layer 8
Trust Validation Hardening
Control Focus: Ensure trust confirmation occurs before external communication.
· Enforce pre-execution configuration validation
· Block external API communication until repository trust confirmed
· Monitor configuration injection attempts in CLI context
· Maintain secure defaults preventing base URL override without explicit approval
Risk Mitigated
· Root vulnerability condition in CVE-2026-21852
Architectural Outcome
When fully implemented, this layered model:
· Reduces likelihood of malicious repository execution
· Prevents credential redirection
· Limits API key blast radius
· Detects anomalous usage rapidly
· Protects financial and intellectual property assets
· Aligns AI governance to enterprise risk tolerance
7-Day Response Plan
Day 1
· Patch to 2.0.65
· Rotate API keys
Day 2
· Audit outbound DNS and proxy logs
Day 3
· Identify suspicious repositories
Day 4
· Implement egress allowlisting
Day 5
· Deploy API anomaly detection
Day 6
· Harden developer workstation governance
Day 7
· Executive validation
Estimated Probability of Recurrence (12-Month Horizon)
· 38 percent
References
Reporting Group: GitHub Security Advisory
· hxxps://github[.]com/advisories/GHSA-jh7p-qr78-84p7
Reporting Group: National Vulnerability Database
· hxxps://nvd.nist[.]gov/vuln/detail/CVE-2026-21852
Reporting Group: MITRE
· hxxps://cve.mitre[.]org/cgi-bin/cvename.cgi?name=CVE-2026-21852