Hackers Actively Scanning for BeyondTrust RCE Exploit CVE-2026-1731
BLUF
A critical pre-auth OS command injection → RCE flaw in BeyondTrust RS/PRA (CVE-2026-1731) has broad internet exposure (reporting cites large exposed population), making it highly likely to attract rapid opportunistic scanning and exploit attempts even if confirmed exploitation is not publicly documented yet.
Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
“For organizations affected by opportunistic scanning and potential exploitation of the BeyondTrust RS/PRA pre-authentication RCE vulnerability (CVE-2026-1731), costs will primarily stem from urgent containment, accelerated patching, and downstream risk mitigation for privileged access systems.”
· Low-end total cost: $150K – $400K
o Rapid patching before compromise, minimal forensic scope required
· Typical expected range: $600K – $2.5M
o Short-term exposure window, investigation plus privileged credential resets
· Upper-bound realistic scenarios: $3M – $8M
o Confirmed intrusion, broader environment hardening, potential ransomware staging
Key Cost Drivers
· Scope of exposed RS/PRA infrastructure and privileged connectivity
· Duration between vulnerability disclosure and patch containment
· Need for enterprise-wide credential rotation and access review
· Extent of forensic investigation across privileged systems
· Business disruption from emergency downtime or remote access restrictions
· Regulatory exposure if privileged access paths lead to sensitive data
Overall Executive Takeaway
Even in a pre-exploitation phase, a critical pre-auth RCE in a privileged access gateway can realistically drive six- to seven-figure response costs for most mid-to-large enterprises, with upper-bound scenarios reaching $8M if intrusion or ransomware staging occurs.
Potential affected sectors
· BeyondTrust Remote Support / Privileged Remote Access users, particularly self-hosted.
Potential impacted countries
· Global
Date of first reported activity
Feb 6, 2026
Date of last reported activity update (last 24h)
· Feb 11, 2026
Why this matters to defenders
· RS/PRA are “gateway” tools into privileged environments; pre-auth RCE can be a straight-to-admin path and is a known ransomware precursor class of vulnerability.
Associated APT groups
· There have been no publicly available ties to an APT group at this time.
Associated criminal organizations
· There have been no publicly available ties to an criminal organizations at this time.
o Treat as high-likelihood opportunistic targeting due to exposure and severity.
Tools used in campaign
· No specific post-exploitation toolset is publicly confirmed in the sources reviewed (yet).
Exposure Assessment Tool
· Nessus: Plugin 298510 (BeyondTrust Remote Support < 25.3.2 pre-auth RCE)
· Tenable pipeline references plugin IDs 298510 / 298511 for the issue.
· Rapid7: authenticated checks availability noted for Feb 9 content release (InsightVM/Nexpose)
IOCs
· No reliable public IOCs (IPs/domains/hashes) were provided in the sources reviewed because BeyondTrust has not publicly confirmed active exploitation.
Confidence
· N/A
CVE-2026-1731
CWE-78 OS command injection leading to RCE
Exploitability
· Very high
o Network reachable
o No authentication
o No user interaction
· Public PoC exists
o Do not treat this as proof of exploitation, but it increases risk
Has there been observed exploitation?
· Vendor and major reporting reviewed state no known active exploitation at this time.
Exposure risk
· High where RS/PRA is internet-facing, especially self-hosted instances not auto-updated.
Exposure estimates referenced publicly
· 11,000 exposed, with approximately 8,500 on-prem potentially vulnerable if unpatched (as cited in reporting/ETR).
Recommended action
Apply BeyondTrust patches immediately (or upgrade track as required).
If you cannot patch within hours
· Temporarily restrict exposure (VPN/IP allowlist)
· Monitor WAF/reverse proxy logs for abnormal request patterns
· Audit privileged access logs and session telemetry from the vulnerable window.
CVSS vectors (3.1 and 4.0)
CVSS 4.0 (CNA: BeyondTrust): CVSS:4.0/AV:N/AC:L/AT:N/PR:N/UI:N/VC:H/VI:H/VA:H/SC:L/SI:H/SA:L
CVSS 3.1: NVD base score not provided yet.
Nessus ID
· 298510
· 298511
Is CVE-2026-1731 on the KEV list
· No
Patching / mitigation data
· BeyondTrust advisory BT26-02 indicates SaaS patched as of Feb 2, 2026, and provides patch packages/upgrade guidance for self-hosted.
Fixed versions / patch paths
· Remote Support (RS): Affected 25.3.1 and prior; fixed in 25.3.2+ or via Patch BT26-02-RS (v21.3–25.3.1)
· Privileged Remote Access (PRA): Affected 24.3.4 and prior; fixed in 25.1.1+ or via Patch BT26-02-PRA (v22.1–24.x)
· Versions older than RS 21.3 or PRA 22.1 require upgrade to reach patchable releases.
Patch release date
· Advisory context Feb 6, 2026.
Malware names / family / hashes / decoding key
There have no confirmed in-the-wild payload set published yet).
Verdict
· URGENT PATCH / PRE-EXPLOIT “HIGH LIKELIHOOD” due to exposure and pre-auth RCE characteristics.
· Even absent confirmed exploitation, the combination of pre-auth RCE plus broad exposure plus an available proof of concept makes this a high-likelihood targeting vulnerability.
Primary Objectives
Expected if exploited
· Initial foothold on RS/PRA server
· Privileged access expansion (credential access, lateral movement)
· Data access/exfiltration and/or ransomware staging (scenario-based for this class of asset)
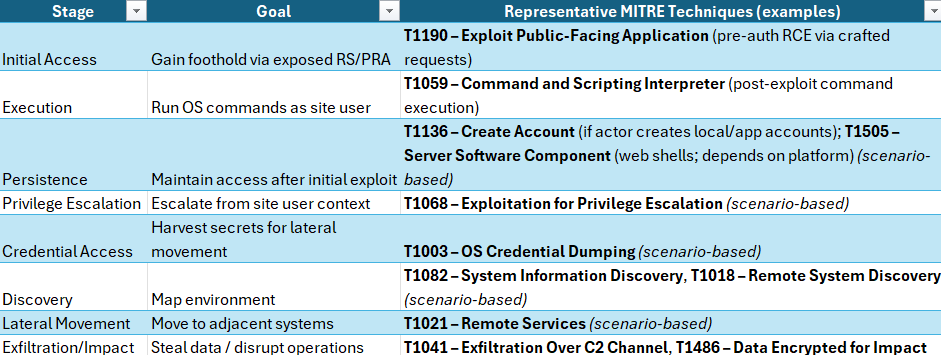
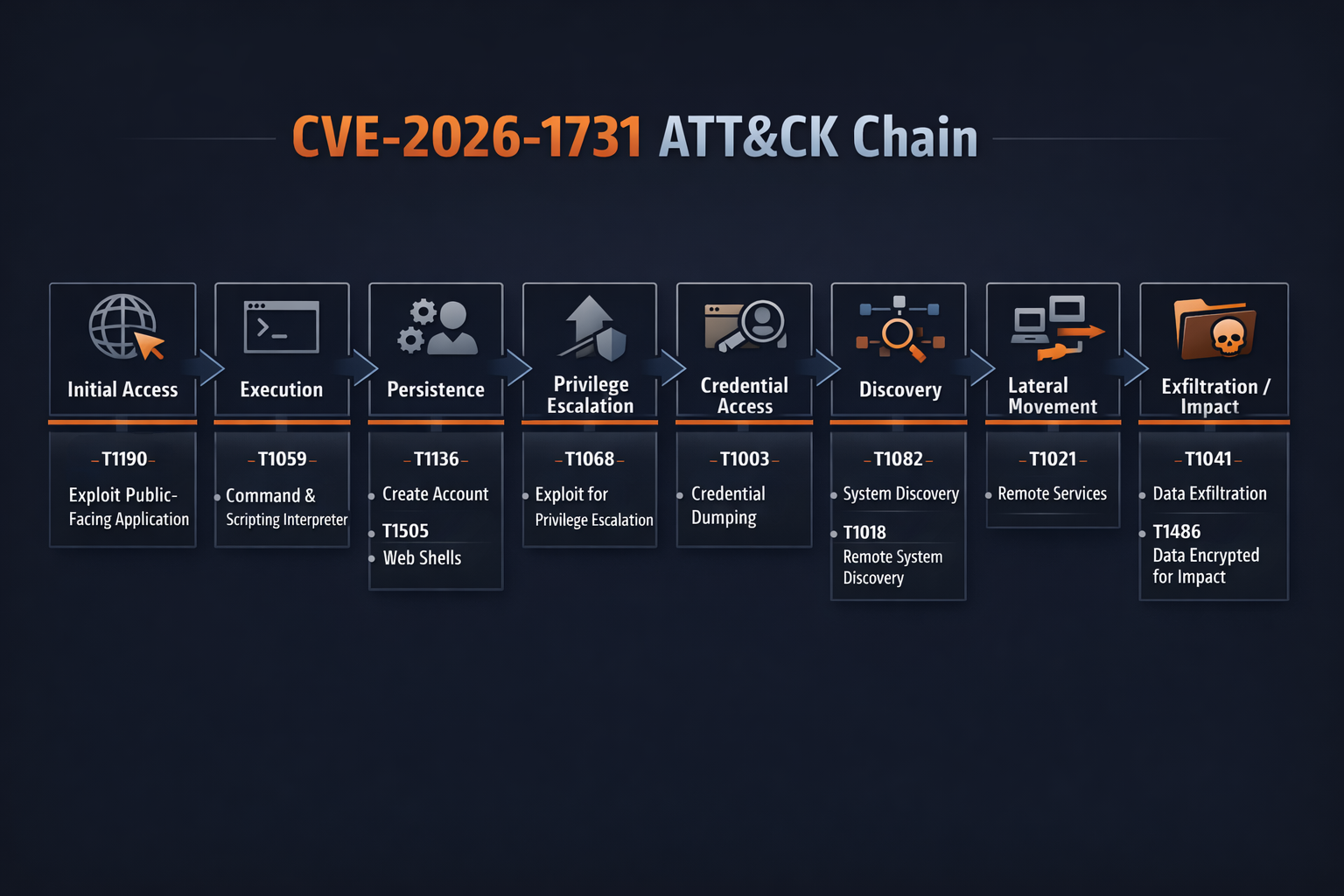
Figure 2 MITRE Att&ck Chain Chart
TTPs
Initial Access
· T1190 Exploit Public-Facing Application
o Crafted requests trigger pre-auth command execution on RS/PRA.
Execution
· T1059 Command and Scripting Interpreter
o Attacker executes OS commands in the site-user context post-trigger.
Post-Exploitation
Likely, not publicly confirmed for this CVE
· T1105 Ingress Tool Transfer
o Fetch additional tooling once code execution is obtained.
· T1021 Remote Services
o Leverage harvested creds/privilege to pivot.
· T1486 Data Encrypted for Impact
o Ransomware outcomes if access is maintained.
Figure 3 TTP MITRE Att&ck Chain flow
Threat Actor Context
· No specific actor attribution for CVE-2026-1731.
Behavior Analysis
High-signal behaviors on RS/PRA hosts:
· External requests immediately followed by creation of suspicious child processes (shells, scripting engines)
· Unusual modifications to RS/PRA configuration, users, or auth integrations
· Outbound connections newly initiated by RS/PRA host (downloaders, tunnels, C2-like patterns)
These are detection pivots; they are not “confirmed” for this specific CVE.
Expected User-Agent Patterns
· Not publicly available for this CVE.
· If opportunistic scanning begins, typical scanner UAs (low-confidence) may include:
o curl/*, python-requests/*, Go-http-client/*
o Confidence: Low (heuristic; not sourced)
Payload Examples
· There are no publicly available exploit payload strings or step-by-step exploitation details.
Defensive “payload indicators” you can hunt for in logs instead:
· Requests containing command-injection metacharacters (;, |, `, $() in unexpected parameters/JSON fields
· Abnormal WebSocket/HTTP request spikes to RS/PRA endpoints followed by immediate server-side process creation
Log Artifacts (high-value)
Reverse proxy/WAF logs
· Unusual inbound bursts to RS/PRA, large or malformed requests, suspicious metacharacters
OS audit logs (Windows Security / Sysmon, Linux auditd)
· New process creation where parent is RS/PRA service
BeyondTrust appliance/application logs
· Unexpected admin actions, config changes, session creation anomalies
Detection Coverage by Control Type
(practical)
· Preven
o Patch/upgrade; remove internet exposure; allowlist admin access.
· Detect
o Process creation anomalies; new persistence; suspicious outbound.
· Respond
o Isolate RS/PRA host; rotate privileged creds; review privileged access sessions.
Suggested Rules / Potential Hunts
Suricata
· Suspicious metacharacters in HTTP request to RS/PRA hosts
o Tune
§ Apply only to RS/PRA destination IPs/ports to reduce noise.
alert http $EXTERNAL_NET any -> $HOME_NET any (
msg:"POSSIBLE Command Injection Attempt (metacharacters) targeting RS/PRA";
flow:established,to_server;
http.method; content:"POST"; nocase;
pcre:"/(\%3b|;|\%7c|\||\%60|`|\%24\(|\$\()/Ui";
classtype:web-application-attack;
sid:9902001; rev:1;
)
SentinelOne
· RS/PRA service spawning shells/scripting
EventType = Process Creation
AND (ProcessName In ("cmd.exe","powershell.exe","bash","sh","python","perl","nc","curl","wget"))
AND (ParentProcessName ContainsCIS ("beyondtrust")
OR ParentProcessPath ContainsCIS ("beyondtrust")
OR ParentProcessCommandLine ContainsCIS ("beyondtrust"))
Splunk
· Inbound spike to RS/PRA + rapid process execution (requires proxy + endpoint logs)
(
index=proxy (dest_host IN ("<RS_PRA_HOST1>","<RS_PRA_HOST2>")) earliest=-15m
| stats count as req_count, values(src_ip) as src by dest_host span=1m _time
)
| join dest_host _time
[ search index=endpoint host IN ("<RS_PRA_HOST1>","<RS_PRA_HOST2>") earliest=-15m
(process_name IN ("cmd.exe","powershell.exe","bash","sh","python","perl","curl","wget"))
| stats values(process_name) as procs values(parent_process_name) as parents by host span=1m _time ]
| where req_count > 50
| sort - req_count
· Detect suspicious characters in URI/query (proxy/WAF)
index=proxy (dest_host IN ("<RS_PRA_HOST1>","<RS_PRA_HOST2>"))
| where match(uri_query, "(%3b|;|%7c|\\||%60|`|%24\\(|\\$\\()")
| stats count values(src_ip) values(useragent) by dest_host uri_path
Sigma
(process creation) – RS/PRA spawning command interpreters
title: BeyondTrust RS/PRA Suspicious Child Process Execution
id: 6c5dcb2e-7b12-4b9a-a0d5-79d26b0b7f9d
status: experimental
logsource:
product: windows
category: process_creation
detection:
selection:
ParentImage|contains:
- "BeyondTrust"
- "beyondtrust"
Image|endswith:
- '\cmd.exe'
- '\powershell.exe'
- '\wscript.exe'
- '\cscript.exe'
condition: selection
falsepositives:
- Administrative scripts launched legitimately from the RS/PRA host
level: high
YARA
· Suspicious command-injection metachar presence in captured request bodies/files
o Rule Possible_Command_Injection_Metachars_Generic
{
meta:
description = "Detects common command-injection metacharacter patterns in logs/request captures"
author = "Defender"
strings:
$m1 = ";"
$m2 = "|"
$m3 = "`"
$m4 = "$("
condition:
2 of ($m*)
}
Delivery Methods
· Exploitation of internet-exposed RS/PRA via crafted requests (pre-auth RCE).
Steps to Consider Over the Next 7 Days
· Day 0–1
o Inventory and identify internet-exposed RS/PRA; run vuln scans (Nessus 298510) and authenticated checks.
· Day 0–1
o Patch/upgrade per BT26-02; confirm RS ≥ 25.3.2 and PRA ≥ 25.1.1 (or apply vendor patch in supported ranges).
· Day 1–2
o Implement temporary compensating controls: VPN/IP allowlists, WAF rules for metachar patterns, rate limiting.
· Day 2–4
o Hunt for suspicious child processes and new persistence on RS/PRA hosts; review admin actions and sessions.
· Day 4–7
o Rotate credentials used by RS/PRA service accounts; review privileged access integrations; harden egress from RS/PRA host.
References
https://www.beyondtrust.com/trust-center/security-advisories/bt26-02
https://nvd.nist.gov/vuln/detail/CVE-2026-1731
https://www.rapid7.com/blog/post/etr-cve-2026-1731-critical-unauthenticated-remote-code-execution-rce-beyondtrust-remote-support-rs-privileged-remote-access-pra/
https://www.tenable.com/plugins/nessus/298510
https://www.techradar.com/pro/security/beyondtrust-rce-flaw-lets-hackers-run-code-without-logging-in
https://github.com/win3zz/CVE-2026-1731