Phorpiex “Your Document” LNK Phishing leads to GLOBAL GROUP Ransomware
BLUF
Forcepoint X-Labs observed a high-volume phishing campaign using the subject “Your Document” with a double-extension attachment that is actually a Windows shortcut (.LNK). When executed, the LNK launches cmd.exe, which invokes PowerShell to download and execute a second-stage payload (e.g., spl.exe from 178.16.54.109) saved as windrv.exe. The delivered ransomware (GLOBAL GROUP) runs in “mute” mode: no C2, local key generation, and can execute offline/air-gapped, while also attempting artifact reduction (timer + self-delete) and anti-analysis behaviors.
Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
“For organizations affected by Phorpiex-delivered GLOBAL GROUP ransomware encrypting systems through LNK-based phishing…”
· Low-end total cost: $900,000 – $1.8 million
o Limited endpoint spread, rapid containment, strong tested backups
· Typical expected range: $2 million – $6 million
o Multi-department encryption, 3–7 days disruption, partial rebuild
· Upper-bound realistic scenarios: $8 million – $15 million
o Broad lateral movement, prolonged downtime, legal/insurance friction
Key Cost Drivers
Speed of isolation before domain-wide propagation
Backup immutability and restore readiness
Volume of endpoints encrypted before detection
Duration of operational downtime (per-day revenue impact)
Insurance deductible structure and post-claim premium increase
Bottom Line for Executives
While initial infection relies on a relatively simple phishing vector
Phorpiex “Your Document” LNK Ph…
, the financial exposure stems from encryption scale, recovery complexity, and operational disruption. For mid-size to large organizations, realistic total impact falls in the low single-digit millions under typical conditions, with materially higher exposure if lateral spread and downtime are not rapidly contained.
Potential affected sectors
· Broad / cross-sector
o Commodity/high-volume phishing distribution
o No single vertical specified in primary reporting
Potential impacted countries
· Potentially global
o This does not appear to be directly targeted at this time
Date of first reported activity
· February 9, 2026
· LNK sample first seen (MalwareBazaar): 2026-01-06 07:50:12 UTC.
· Payload sample first seen (MalwareBazaar): 2026-01-05 13:01:01 UTC.
Date of last reported activity update
· February 9, 2026
· Payload sample last seen (MalwareBazaar): 2026-01-06 17:08:28 UTC.
Why this matters to defenders
· Old technique, still high yield: weaponized LNK + double extension continues to drive clicks and execution.
· “Mute” ransomware reduces network signal: GLOBAL GROUP executes without C2, generates keys locally, and can operate offline, shifting detection priority to endpoint telemetry and behavioral controls.
· Impact-ready
o Encrypts broadly and drops ransom notes, uses robust ChaCha20-Poly1305 (Forcepoint notes decryption not possible without attacker key).
Associated APT groups
· None attributed
o At this time, no specific threat actor has been attributed. The activity appears consistent with a commodity botnet delivery method followed by a ransomware-as-a-service style deployment of GLOBAL GROUP ransomware, originating from the Phorpiex “Your Document” LNK phishing campaign.
Associated criminal organizations
· Phorpiex
o MaaS botnet active since 2010
§ Often distributes secondary payloads
· GLOBAL GROUP
o RaaS; described as successor to Mamona in this chain
Tools used in campaign
Delivery & execution
· Phishing email lure “Your Document” + weaponized .LNK with double extension.
· cmd.exe launching PowerShell for download-and-execute.
· PowerShell System.Net.WebClient download behavior (seen in LNK analysis telemetry and described in chain).
Ransomware capabilities (not exhaustive)
· Anti-analysis / anti-virtualization by enumerating processes
o Kills database-related processes to release locks.
· Persistence module
o Copies to %windir%\Temp\cleanup.exe, creates a Windows service, uses scheduled task “CoolTask” (run at startup as SYSTEM, triggers immediately, then deletes the task).
· Lateral movement
o LDAP/AD enumeration (ACTIVEDS.dll), remote service creation, worm-like propagation strings.
· Shadow copy deletion
· Event log manipulation/clearing.
IOCs
Confidence rubric
· High: explicitly published by primary research (Forcepoint) or direct sample record (MalwareBazaar entry)
· Medium: derived from the described chain / observed behavior graph, but may vary per run
· Low: speculative (not used here)
Network
· hxxp://178[.]16[.]54[.]109/spl.exe (High)
· hxxp://178[.]16[.]54[.]109/lfuck.exe (High)
Host/IP
· 178.16.54.109 (High)
Host artifacts
Mutex
· Global\Fxo16jmdgujs437 (High)
Ransom note
· README.Reco.txt (High)
Encrypted extension
· .Reco (High)
Encrypted file marker
· xcrydtednotstill_amazingg_time!! (High)
Dropped file name/path examples
· %userprofile%\windrv.exe, C:\Windows\windrv.exe (Medium)
Persistence artifacts
· %windir%\Temp\cleanup.exe, task name CoolTask (Medium)
Figure 1 MITRE attack chain chart
Note: Some items (e.g., exact remote exec mechanism) are indicated by strings/telemetry and may vary by deployment; the underlying behaviors are described by Forcepoint and/or shown in behavior graphs.
Figure 2 TTP Flow chart
TTPs
Initial Access
· T1566.001 Spearphishing Attachment
o “Your Document” email carries a disguised LNK attachment.
Execution
· T1204.002 User Execution: Malicious File
o Victim clicks LNK (Document.doc.lnk).
· T1059.003 Windows Command Shell
o LNK launches cmd.exe with embedded arguments.
· T1059.001 PowerShell
o cmd invokes PowerShell download-and-execute sequence.
Persistence
· T1543.003 Windows Service
o “cleanup module” creates a service to persist.
· T1053.005 Scheduled Task
o Creates task “CoolTask” at startup (SYSTEM), triggers, deletes task.
Discovery / Collection of environment
· T1057 Process Discovery
o Enumerates processes to detect tools/VM and identify DB processes to kill.
· T1087.002 Domain Account Discovery / T1018 Remote System Discovery
o AD/LDAP enumeration described (domain objects/endpoints).
Lateral Movement
· T1021.002 SMB/Windows Admin Shares (likely)
o Behavior graph indicates SMB-related tagging; Forcepoint describes network propagation and remote service creation.
· T1543.003 Windows Service
o Remote service creation used to deploy across endpoints (as described).
Defense Evasion / Anti-Forensics
· T1036 Masquerading
o Uses system-like path/name windrv.exe.
· T1497 Virtualization/Sandbox Evasion
o Checks for sandbox/analysis processes.
· T1070.004 File Deletion
o Ping timer then deletes binary from disk.
· T1070.00 Clear Windows Event Logs
o Described ability to manipulate/clear logs.
Impact
· T1486 Data Encrypted for Impact
o Encrypts files, appends .Reco.
· T1490 Inhibit System Recovery
o Deletes shadow copies.
Figure 3 MITRE Att&ck chain
CVE
· There are no CVEs associated with this activity at this time.
What is the exploitability
· High
o User-assisted execution
o Common tooling
Observed exploitation
· Yes
Exposure risk
· High for orgs allowing LNK attachments / weak PowerShell controls; “mute” execution reduces network-only detection value.
Mitigation data
· Email / initial access
· Block/quarantine .lnk (including within archives), enforce file extension visibility, and add detections for double-extension patterns.
· Endpoint hardening
· Constrain PowerShell
o Enable script block logging, enforce Constrained Language Mode where possible, and alert on WebClient.DownloadFile + execution.
· Block/ Alert when a user opens a malicious shortcut file that causes Windows Explorer to launch Command Prompt, which then launches PowerShell to download and run a newly created file. This behavior is commonly used by attackers to deliver malware
Network
· Block 178.16.54.109 and related paths; retro-hunt for direct-IP EXE downloads.
Resilience
· Ensure offline backups and test restores; “mute” ransomware can still fully encrypt without C2.
Malware names / family
· Phorpiex (delivery/botnet MaaS)
· GLOBAL GROUP ransomware (payload; “mute/offline” mode)
· LNK sample is labeled Phorpiex.
· Payload sample is labeled GLOBAL (and tagged dropped-by-phorpiex).
sha256(s)
LNK (Document.zip.lnk) SHA256 70a4afab44d6a9ecd7f42ab77972be074dec8383a47a2011eb0133a230a4fae3 (High)
Payload (Spl.exe / lfuck.exe) SHA256 55f3a2d89485bb40ea45e5fa1f24828f71a81ef4ccc541b6657fc7a861ef3add (High)
Known decoding key
· None publicly available / not disclosed. Forcepoint states ChaCha20-Poly1305 is used and decryption is not possible without attacker private key.
Verdict
· Malicious (High confidence)
o Primary research reporting + corroborating sample telemetry
Primary Objective
The attacker’s main goal is to encrypt the victim’s files in order to extort payment.
This is indicated by:
· The creation of a ransom note
· Files being renamed with the .Reco extension
· Changes to the desktop wallpaper with a ransom message
· Behavior suggesting the use of Tor communications during the attack.
Threat actor context
· Phorpiex operators (or affiliates) appear to provide distribution scale, while GLOBAL GROUP operates as RaaS-style ransomware (Forcepoint calls it a successor to Mamona).
· No nation-state attribution is claimed.
Behavior analysis
Execution flow (high fidelity)
· User opens phishing email, sees attachment that looks like a document (double extension).
· LNK executes cmd.exe, which invokes PowerShell download+execute sequence.
· Payload downloaded from 178.16.54.109 (e.g., spl.exe) and written as %userprofile%\windrv.exe.
· Payload executes and proceeds into local/offline “mute” behavior; encrypts files and drops notes.
Encryption / impact
· Encrypts using ChaCha20-Poly1305, appends .Reco, drops README.Reco.txt, changes wallpaper.
· Anti-forensics and stealth
· Ping-based timer then self-delete (uses 127.0.0.7 with -n 3 for ~3 seconds).
· Enumerates processes for anti-VM/anti-analysis and kills DB processes to unlock files.
· Lateral movement and domain awareness
· AD/LDAP enumeration via ACTIVEDS.dll, remote service creation, worm-like strings/capability.
Expected User-Agent Patterns:
· User-Agent strings in this case are not a reliable indicator. The download is performed using PowerShell and .NET components (such as System.Net.WebClient), which typically generate generic or system-dependent web request headers. Because these headers can vary by environment and are not distinctive, they should not be relied upon alone for detection.
· Instead, focus on identifying the related process activity, command-line behavior, and the destination of the network connection, as these provide stronger and more consistent indicators of malicious activity.
Payload examples
As seen/derivable from telemetry
· LNK contains/initiates PowerShell download and execute, and MalwareBazaar highlights “payload URL: hxxp://178.16.54.109/spl.exe”.
· Behavior graph shows drop to C:\Users\user\windrv.exe and subsequent execution.
Log artifacts (what to pivot on)
Windows / Sysmon
Process creation
· Explorer.exe (user) spawning cmd.exe, which spawns powershell.exe with download-and-execute parameters.
File creation
· windrv.exe in user root or Windows directory; later deletion after ping delay.
Ransom note creation
· README.Reco.txt across locations; file renames adding .Reco.
· Shadow copy deletion indicators (e.g., vssadmin/similar behavior referenced).
Persistence
· service creation and transient scheduled task “CoolTask”; copies to %windir%\Temp\cleanup.exe.
Network
· Outbound HXXP to 178.16.54.109 retrieving /spl.exe or /lfuck.exe.
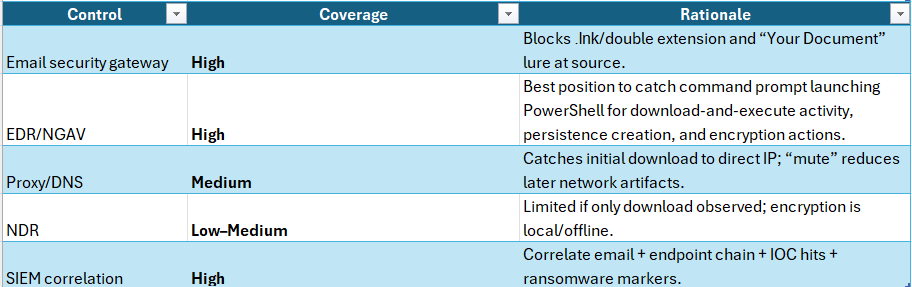
Figure 4 Detection Coverage Matrix
Detection Coverage by Control Type
Prevent
· Block LNK
· Restrict PowerShell
· Block known IP/URLs.
Detect
· Process-chain analytics
· Suspicious PowerShell commandline
· Ransomware markers and shadow copy deletion.
Respond
· Isolate host at download/exec stage; rapid containment (lateral movement capability is described).
Suggested rules / potential hunts
Suricata
· TLP_WHITE Phorpiex LNK → GLOBAL GROUP download from 178.16.54.109
alert hxxp $HOME_NET any -> $EXTERNAL_NET any (
msg:"TLP_WHITE Phorpiex->GLOBAL GROUP payload download (178.16.54.109 spl.exe/lfuck.exe)";
flow:established,to_server;
hxxp.host; content:"178.16.54.109";
hxxp.uri; pcre:"/\/(spl|lfuck)\.exe$/Ui";
classtype:trojan-activity;
sid:9902602; rev:1;
)
SentinelOne
· Phorpiex LNK Execution Chain (Explorer to CMD to PowerShell)
Purpose
Detects the initial execution chain used by Phorpiex “Your Document” LNK phishing, where a user launches a malicious shortcut that spawns the command prompt and subsequently executes PowerShell.
Severity: High
MITRE: T1204 (User Execution), T1059 (Command and Scripting Interpreter)
Deep Visibility Query
ProcessName = "cmd.exe"
AND ParentProcessName = "explorer.exe"
AND ChildProcessName = "powershell.exe"
· PowerShell WebClient Download and Execute
Purpose
Detects malicious PowerShell activity using the .NET WebClient class to download and execute remote payloads, consistent with Phorpiex loader behavior.
Severity: High
MITRE: T1059.001, T1105
Deep Visibility Query
ProcessName = "powershell.exe"
AND CommandLine contains "System.Net.WebClient"
AND CommandLine contains "DownloadFile"
· Phorpiex Payload or Network Indicator Detection
Purpose
Detects known indicators associated with Phorpiex and GLOBAL GROUP ransomware, including a known payload name and hard-coded IP address.
Severity: Critical
MITRE: T1105 (Ingress Tool Transfer)
Deep Visibility Query
ProcessName = "powershell.exe"
AND CommandLine contains_any ("windrv.exe", "178.16.54.109")
· GLOBAL GROUP Ransom Note Creation
Purpose
Detects the creation of the GLOBAL GROUP ransomware ransom note, indicating encryption activity has begun or completed.
Severity: Critical
MITRE: T1486 (Data Encrypted for Impact)
Deep Visibility Query
EventType = "FileCreate"
AND FileName = "README.Reco.txt"
· Mass File Rename with .Reco Extension
Purpose
Detects ransomware encryption behavior by identifying mass file rename activity appending the .Reco extension.
Severity: Critical
MITRE: T1486
Recommended Alert Setting:
Enable frequency thresholding (multiple events within a short time window on the same endpoint).
Deep Visibility Query
EventType = "FileRename"
AND TargetFileExtension = ".Reco"
· Shadow Copy Deletion and Recovery Inhibition
· Purpose
o Detects ransomware attempts to prevent system recovery by deleting shadow copies or disabling recovery options.
o Severity: Critical
o MITRE: T1490 (Inhibit System Recovery)
Deep Visibility Query
ProcessName contains_any ("cmd.exe", "powershell.exe")
AND CommandLine contains_any (
"vssadmin delete shadows",
"wmic shadowcopy delete",
"bcdedit /set {default} recoveryenabled no"
)
Splunk
· GGROUP download+execute via PowerShell
(index=wineventlog EventCode=4688) OR (index=sysmon EventCode=1)
(Image="*\\powershell.exe" AND CommandLine="*System.Net.WebClient*" AND CommandLine="*DownloadFile*")
| eval has_ip=if(like(CommandLine,"%178.16.54.109%"),1,0)
| stats earliest(_time) as firstSeen latest(_time) as lastSeen values(ParentImage) values(Image) values(CommandLine) values(has_ip) count by host user
| convert ctime(firstSeen) ctime(lastSeen)
Fast triage checklist (email → endpoint → network)
Email gateway: quarantine/block .lnk (and .lnk inside archives) + match subject "Your Document".
Endpoint process chain: hunt explorer.exe → cmd.exe → powershell.exe with WebClient/DownloadFile plus execution (Start-Process).
File system: hunt for dropped windrv.exe (e.g., %userprofile%\windrv.exe or C:\Windows\windrv.exe) and note README.Reco.txt / .Reco extensions.
Network: block & retro-hunt 178.16.54.109 and paths /spl.exe, /lfuck.exe.
Impact markers: wallpaper change message, mutex, encrypted file marker string.
Suggested “EAT” SPL queries (drop-in)
A. PowerShell download/execute from cmd
(index=wineventlog EventCode=4688) OR (index=sysmon EventCode=1)
(CommandLine="*System.Net.WebClient*" AND CommandLine="*DownloadFile*" AND CommandLine="*Start-Process*")
| stats earliest(_time) as firstSeen latest(_time) as lastSeen values(ParentImage) values(Image) values(CommandLine) count by host user
| convert ctime(firstSeen) ctime(lastSeen)
B. Ransomware markers
index=edr OR index=sysmon OR index=wineventlog
("README.Reco.txt" OR ".Reco" OR "Global\\Fxo16jmdgujs437" OR "xcrydtednotstill_amazingg_time!!")
| stats earliest(_time) as firstSeen latest(_time) as lastSeen values(file_name) values(process_name) count by host
| convert ctime(firstSeen) ctime(lastSeen)
YARA
· Ransomware_GLOBAL_GROUP_Markers_TLP_WHITE
{
meta:
tlp = "WHITE"
description = "Detect GLOBAL GROUP ransomware markers from Forcepoint report"
reference = "Forcepoint X-Labs Feb 9 2026"
strings:
$mutex = "Global\\Fxo16jmdgujs437" ascii wide
$marker = "xcrydtednotstill_amazingg_time!!" ascii wide
$note = "README.Reco.txt" ascii wide
$ext = ".Reco" ascii wide
condition:
2 of ($mutex,$marker,$note,$ext)
}
Sigma
· TLP_WHITE Phorpiex LNK PowerShell DownloadFile + Start-Process
o TLP_WHITE Phorpiex LNK -> PowerShell WebClient DownloadFile -> Execute
id: 8ab0f6e8-0d54-4c5f-9c52-20260210-phorpiex-ggroup
status: experimental
logsource:
product: windows
category: process_creation
detection:
selection_ps:
Image|endswith: '\powershell.exe'
CommandLine|contains|all:
- 'System.Net.WebClient'
- 'DownloadFile'
selection_exec:
CommandLine|contains:
- 'Start-Process'
- '\windrv.exe'
- '178.16.54.109'
condition: selection_ps and selection_exec
level: high
tags:
- attack.t1566.001
- attack.t1204.002
- attack.t1059.003
- attack.t1059.001
Delivery methods
· specific themes
· Email subject: “Your Document”
· Attachment: LNK disguised as document via double extension (e.g., Document.doc.lnk)
Steps to consider over the next 7 days
· Block .lnk (and .lnk in archives) at the email boundary; add “Your Document” lure detections.
· Retro-hunt proxy/DNS for 178.16.54.109 and /spl.exe /lfuck.exe; block immediately.
· EDR hunt for explorer→cmd→powershell download+execute patterns and windrv.exe creation/execution.
· Deploy marker detections: mutex, .Reco, README.Reco.txt, and encrypted file marker string.
· Validate ransomware controls: shadow copy protection, backup immutability, restore testing.
· Watch for persistence: %windir%\Temp\cleanup.exe, service creation, and evidence of task “CoolTask” creation/deletion.
· Contain quickly on any host with early-stage indicators due to described lateral movement capability.
References
Force Point
· hxxps://www.forcepoint.com/blog/x-labs/phorpiex-global-group-ransomware-lnk-phishing
MalwareBazaar Abuse
· hxxps://bazaar.abuse.ch/sample/70a4afab44d6a9ecd7f42ab77972be074dec8383a47a2011eb0133a230a4fae3/
· hxxps://bazaar.abuse.ch/sample/55f3a2d89485bb40ea45e5fa1f24828f71a81ef4ccc541b6657fc7a861ef3add/
VirusTotal
· hxxps://www.virustotal.com/gui/file/70a4afab44d6a9ecd7f42ab77972be074dec8383a47a2011eb0133a230a4fae3
· hxxps://www.virustotal.com/gui/file/55f3a2d89485bb40ea45e5fa1f24828f71a81ef4ccc541b6657fc7a861ef3add