Microsoft Feb 2026 “ Six Actively Exploited Zero-Days” (Windows/Office)
BLUF
Six Microsoft vulnerabilities (Windows and Office) were added to CISA’s Known Exploited Vulnerabilities (KEV) catalog on Feb 10, 2026, indicating evidence of active exploitation in the wild.
Executive Cost Summary
This cost analysis was developed by the CyberDax team using expert judgment and assisted analytical tools to support clarity and consistency.
For organizations affected by actively exploited Microsoft Windows and Office zero-day vulnerabilities (KEV-listed, opportunistic exploitation in the wild), the realistic financial exposure is material even without a “catastrophic breach.”
· Low-end total cost: $250K – $900K
o Rapid patching, limited endpoint compromise, no lateral spread
· Typical expected range: $1.5M – $6M
o Multi-endpoint containment, Office phishing entry, moderate downtime
· Upper-bound realistic scenarios: $8M – $20M
o Privilege escalation on shared systems, broader operational disruption
Key Cost Drivers
· Speed and completeness of enterprise-wide patch deployment
· Number of endpoints/servers requiring forensic validation ($5K–$15K each)
· Business disruption from isolating RDS/VDI or critical Windows services
· Scope of credential resets and privileged access remediation
· Regulatory reporting obligations if sensitive data is accessed
· Post-incident hardening and monitoring expansion over 3–6 months
Potential affected sectors
· Government (incl. local/state/federal)
· Defense
· NGOs
· Critical infrastructure operators
o Energy
o Transport
· Healthcare
· Education
· Finance
· Manufacturing
Potential impacted countries
· Global
Date of first reported activity
· Feb 10, 2026
Date of last reported activity update
· Feb 10, 2026
Why this matters to defenders
· KEV inclusion means exploitation is not hypothetical—defenders should assume opportunistic scanning and rapid adoption by multiple actor types.
· The set spans Office security bypass and Windows components (Shell/RDS/RAS/IE), enabling multi-stage operations (initial access spawns execution spawns privilege escalation spawns persistence/lateral movement), depending on environment.
Associated APT groups
· These CVEs have not been associated with APT groups at this time
Associated criminal organizations
These CVEs have not been associated with any criminal organizations at this time.
Tools used in campaign
· Not publicly confirmed
o no authoritative reporting providing tooling/implant names tied to these six CVEs in sources reviewed
Exposure assessment tool
Use a layered approach:
· Vulnerability scanners
· Tenable Nessus / Tenable.io
· Qualys
· Rapid7.
Endpoint exposure
· Microsoft Defender Vulnerability Management / Intune update compliance.
Configuration exposure checks
· RDS exposure: external attack surface scanning and internal inventory of RDP listeners.
· IE/MSHTML usage: GPO/feature inventory and application compatibility lists.
· Office attack surface
o ASR rules posture
o Protected View/MOTW enforcement
o OLE/DDE hardening.
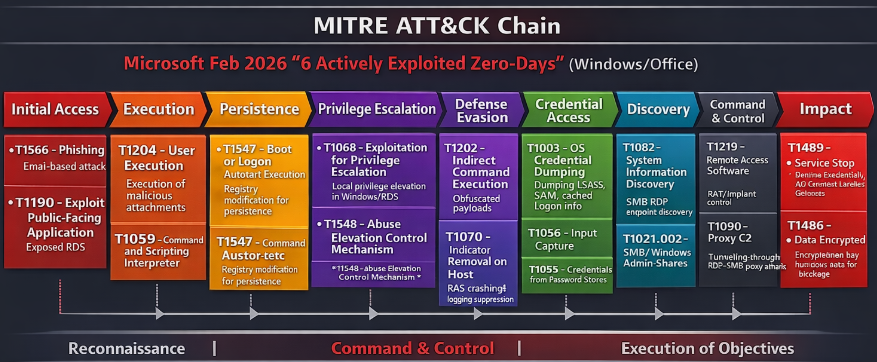
Figure 1 MITRE ATT&CK attack-chain chart
TTPs
Initial access & delivery
· T1566 Phishing
o Weaponized attachments/links to trigger Office/HTML rendering paths (relevant to Office/IE/MSHTML surfaces).
· T1204 User Execution
o Opening a document/previewing content that triggers vulnerable parsing or security decision bypass.
· T1133 External Remote Services
o Leveraging exposed RDP (relevant to RDS-related privilege escalation once access exists).
Execution & payload staging
· T1059 Command and Scripting Interpreter
o Post-exploitation payload execution via powershell.exe, cmd.exe, or script hosts.
· T1105 Ingress Tool Transfer
o Downloading second-stage payloads after initial code execution/bypass.
Privilege escalation & persistence
· T1068 Exploitation for Privilege Escalation
o Using local elevation bugs (e.g., RDS EoP) after establishing a foothold.
· T1547 Boot or Logon Autostart Execution
o Establish persistence once elevated.
Lateral movement & impact
· T1021 Remote Services
o Lateral movement via RDP/WMI/SMB once credentials or elevated context is obtained.
· T1489 Service Stop / T1490 Inhibit System Recovery
o Common in disruptive/ransomware-adjacent playbooks (no public confirmation these CVEs were used this way; listed for hunt scoping).
Figure 2 MITRE Att&ck chain
CVE sections (details per CVE)
CVE-2026-21510
Windows Shell Security Feature Bypass Vulnerability
Summary
Protection mechanism failure in Windows Shell that can allow bypass of a security feature over a network.
Nessus ID
· Not at this time
Exploitability
CVSS:3.1
· (8.8) /AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H (Base 8.8 High).
Practical take
· network reachable and user interaction required
o Likely some form of user click/open/preview
Has there been reported exploitation?
· Yes (KEV listed). Date added Feb 10, 2026.
CISA patch by Date
· March 03, 2026
Exposure risk
· High where:
o User endpoints process untrusted content regularly
o Windows Shell features interact with remote content (shares/web/archives)
o Mark of the web (MOTW)/Protected View controls are weak.
Recommended actions
Patch via Microsoft security updates for affected Windows versions (see MSRC link below).
Increase hardening:
Enforce MOTW,
Disable/limit automatic file preview behaviors in risky zones,
Tighten SMB/NTLM exposure.
Verdict
· Patch immediately; treat as active exploitation with unknown tradecraft.
CVE-2026-21513
Microsoft Internet Explorer Protection Mechanism Failure Vulnerability
Summary
· Protection mechanism failure in Microsoft Internet Explorer that can allow security feature bypass over a network.
Exploitability
CVSS:3.1
· (8.8) /AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H (Base 8.8 High)
Nessus ID
· Not applicable at this time
Is this in the KEV catalog?
· Yes
What is the CISA patch by date?
· March 03, 2026
Practical take
· Requires network and user interaction
o Likely web content / embedded rendering
Has there been reported exploitation?
· Yes
Exposure risk
Highest where:
· IE remains installed/used (legacy apps),
· MSHTML is used by other components,
· users browse untrusted content or receive HTML-lures.
Recommended actions
· Apply Microsoft patches.
· Reduce attack surface:
o Retire IE usage where feasible,
o Restrict legacy browser components,
o Strengthen URL filtering and attachment sandboxing.
Verdict
· High priority for environments with any residual IE/MSHTML dependency.
CVE-2026-21514
Microsoft Office Word Security Feature Bypass (Reliance on untrusted inputs)
Summary
· Reliance on untrusted inputs in a security decision in Microsoft Office Word allows bypass of a security feature locally.
Exploitability
CVSS:3.1
· (7.8) AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H
Nessus ID
· Not applicable at this time
Is this in the KEV catalog?
· Yes
What is the CISA patch by date?
· March 03, 2026
Practical take
· Likely triggered when Word processes crafted content and makes a trust decision incorrectly.
Has there been reported exploitation?
· Yes
Exposure risk
High for users receiving:
· External documents,
· Spearphishing attachments,
· Files transferred from collaboration platforms.
Recommended actions
· Patch Office/Word immediately.
· Tighten Office attack surface:
· Enforce Protected View for Internet-zone files,
· Enforce ASR rules for Office child-process creation,
· Block macros from the Internet (where applicable).
Verdict
· Treat as phishing-adjacent high risk; patch and enforce Office hardening immediately.
CVE-2026-21519
A privilege-escalation vulnerability in Microsoft Desktop Window Manager (DWM),
Summary
CVE-2026-21519 is a security flaw that can allow an attacker to trigger unintended behavior (typically privilege escalation, memory corruption, or remote code execution) in a specific affected component.
CVSS:3.1
· (7.8) AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H
Nessus ID
· Not applicable at this time
Is this in the KEV catalog?
· Yes
What is the CISA patch by date?
· March 03, 2026
Practical take
· Requires local access a successful use of this CVE would allow users to elevate privileges and likely lead to system takeover
Recommended actions
· Patch per MSRC; validate coverage using:
· Windows Update compliance,
· Vulnerability scanning,
· Endpoint posture reporting.
Verdict
· Patch and verify (treat as exploited pending confirmation from MSRC/KEV details in your environment).
CVE-2026-21525
Windows Remote Access Connection Manager (RAS) Denial of Service
Summary
· NULL pointer dereference in Windows Remote Access Connection Manager allowing local DoS.
Exploitability
CVSS:3.1
· (6.2) AV:L/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H (Base 6.2 Medium)
Nessus ID
· Not applicable at this time
Is this in the KEV catalog?
· Yes
What is the CISA patch by date?
· March 03, 2026
Practical take
· Requires local access; primarily availability impact.
Has there been reported exploitation?
· Yes
Exposure risk
· Higher where attackers already have footholds (post-compromise), or where shared/terminal environments allow untrusted local execution.
Recommended actions
· Patch Windows systems per MSRC.
· Add resilience measures:
o Monitor for repeated RAS-related crashes,
o Correlate with suspicious user/process activity.
Verdict
· Patch, but prioritize first where you have signs of compromise or high local attacker exposure.
CVE-2026-21533
Windows Remote Desktop Services Elevation of Privilege
Summary
· Improper privilege management in Windows Remote Desktop allows an authorized attacker to elevate privileges locally.
Exploitability
CVSS:3.1
· (7.8) AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H.
Nessus ID
· Not applicable at this time
Is this in the KEV catalog?
· Yes
What is the CISA patch by date?
· March 03, 2026
Practical take
· Needs local authenticated context (PR:L), but yields full CIA impact.
Has there been reported exploitation?
· Yes
Exposure risk
High where:
· RDS is widely enabled (servers, VDI, shared systems),
· privileged users RDP frequently,
· credential hygiene is weak (increases chance of PR:L foothold).
Recommended actions
· Patch affected Windows systems immediately (especially RDS/terminal servers).
· Additional hardening:
o Restrict RDP exposure
§ VPN
§ Allowlists
o enable MFA for remote access,
· tighten local privilege boundaries; monitor token/privilege changes.
Verdict
· High urgency for RDS-heavy estates; patch and reduce RDP/RDS attack surface.
IOCs (with confidence scoring)
IOCs
· No authoritative IOC sets (domains, IPs, file hashes) were found publicly tied to these six CVEs in the sources reviewed.
Behavioral IOCs / detection pivots”
Behavioral IOC pivots
Useful across this campaign set
· Office - child process spawn
o WINWORD.EXE spawns cmd.exe/powershell.exe/rundll32.exe)
Confidence
· High usefulness
· Common post-exploitation pattern
o Not unique to these CVEs
RDS privilege escalation signs
· Sudden token privilege changes
· Unusual service installs
· Unexpected SeDebugPrivilege use
Confidence
· Medium usefulness
Repeated RAS/RACM crashes (possible CVE-2026-21525 DoS activity)
Confidence
· Medium usefulness
Expected User-Agent patterns
For IE-related surfaces (CVE-2026-21513):
· Expect legacy UA strings (IE11/Trident) where applicable
o However no public exploitation telemetry was found tying UA strings to this CVE.
For Office/Word surfaces
· UA is generally not applicable (document-based).
Payload examples / log artifacts
(generic pivots; not exploit code)
Likely log artifacts to pivot on
Windows Security logs:
· 4688 (process creation): Office spawning interpreters
· 4624/4625 (auth): unusual RDP logons patterns around privilege changes
Sysmon (if deployed):
· Event 1 (Process Create)
· Event 3 (Network connect)
· Event 7 (Image loaded)
Application logs
· Office crash telemetry (Word/Office) near suspicious document opens
· RAS/RACM service faults near interactive user sessions
Figure 3 Detection Coverage Matrix (high-level)
Detection coverage by control type
Prevent
· Patching
o IE retirement
o Office Protected View/ASR
o RDP exposure reduction
Detect
· EDR behavior rules
· Windows logging (4688/4624)
· IDS on RDP exposure
· Proxy logs for suspicious HTML delivery
Respond
· Isolate endpoint
· Collect crash dumps if needed
· Rotate creds where PR:L foothold suspected.\
Suggested rules / Potential hunts
Suricata
· These are hunt-oriented (high FP potential) without specific IOC intel.
alert http $HOME_NET any -> $EXTERNAL_NET any (
msg:"HUNT Possible IE/MSHTML exploit delivery (legacy Trident UA)";
flow:to_server,established;
http.user_agent; content:"Trident/"; nocase;
classtype:trojan-activity;
sid:226021513; rev:1;
)
alert tcp $EXTERNAL_NET any -> $HOME_NET 3389 (
msg:"HUNT RDP exposed inbound connection attempt";
flow:to_server,established;
classtype:attempted-admin;
sid:226021533; rev:1;
)
SentinelOne
Office Child Process Burst (Potential exploitation / post-exploitation)
SQL
EventType = "Process Creation"
AND ParentImageName IN ("WINWORD.EXE","EXCEL.EXE","POWERPNT.EXE","OUTLOOK.EXE")
AND ImageName IN ("cmd.exe","powershell.exe","rundll32.exe","regsvr32.exe","mshta.exe","wscript.exe")
AND (
CommandLine CONTAINS "-enc"
OR CommandLine CONTAINS "IEX"
OR CommandLine CONTAINS "FromBase64String"
OR CommandLine CONTAINS "bitsadmin"
OR CommandLine CONTAINS "certutil -urlcache"
)
Splunk
· Office spawning suspicious child processes
index=windows EventCode=4688
(ParentImage="*\\WINWORD.EXE" OR ParentImage="*\\EXCEL.EXE" OR ParentImage="*\\POWERPNT.EXE" OR ParentImage="*\\OUTLOOK.EXE")
(Image="*\\cmd.exe" OR Image="*\\powershell.exe" OR Image="*\\rundll32.exe" OR Image="*\\regsvr32.exe" OR Image="*\\mshta.exe" OR Image="*\\wscript.exe")
| stats count values(CommandLine) as cmdlines by Computer, ParentImage, Image, User
| where count > 2
· RDP logon spikes to servers (possible staging for CVE-2026-21533 follow-on)
index=wineventlog (EventCode=4624 LogonType=10)
| timechart span=15m count by Computer
Sigma rules
Sigma (Windows process creation — Office child process)
Title
· Office Spawns Suspicious Child Process (Hunt)
id: 9d8b1c4a-2260-4c86-9f0d-21514hunt
status: experimental
logsource:
product: windows
category: process_creation
detection:
selection_parent:
ParentImage|endswith:
- '\WINWORD.EXE'
- '\EXCEL.EXE'
- '\POWERPNT.EXE'
- '\OUTLOOK.EXE'
selection_child:
Image|endswith:
- '\cmd.exe'
- '\powershell.exe'
- '\rundll32.exe'
- '\regsvr32.exe'
- '\mshta.exe'
- '\wscript.exe'
condition: selection_parent and selection_child
falsepositives:
- Legitimate add-ins, automation, enterprise macros
level: high
YARA
rule Suspicious_PowerShell_Stager_Keywords_Hunt
{
meta:
description = "Hunt rule: common PowerShell stager keywords"
author = "SOC"
date = "2026-02-10"
strings:
$a = "FromBase64String" nocase
$b = "IEX" nocase
$c = "Invoke-Expression" nocase
$d = "-enc" nocase
$e = "DownloadString" nocase
condition:
2 of ($a,$b,$c,$d,$e)
}
Delivery methods
· Phishing using Microsoft Word documents
o Themes
§ Invoice/payment
§ HR/policy updates
§ Secure document
§ Shared via SharePoint/OneDrive
§ Meeting minutes
IE/ Microsoft HTML engine themes
· Account verification
· Web portal update
· Shared report link
· Security notice
What we don’t know
as of Feb 10, 2026, from sources reviewed
· Confirmed actor attribution (APT or criminal) for each CVE.
· Campaign-specific IOCs
o IPs/domains/hashes
o Exploit builders
o Payload families tied to these six CVEs.
· Reliable “first seen” exploitation timestamps prior to KEV inclusion.
Steps to consider over the next 7 days
Day 0–1
· Patch validation sprint (Windows and Office) for all impacted SKUs; confirm via build numbers and compliance reports.
Day 0–2: Reduce attack surface
· Restrict RDP exposure (VPN/allowlist),
· Disable/limit IE/legacy MSHTML where possible,
· Enforce Office Protected View and ASR rules.
Day 1–3: Hunt
· Office child-process and suspicious command lines,
· RDP logon anomalies and privilege elevation events,
· service crashes consistent with DoS attempts (RAS/RACM).
Day 2–5: Tighten detections:
· Deploy Sigma/Splunk hunts, tune thresholds,
· Add Suricata hunt rules at egress/proxy points,
· Ensure EDR prevention policies are on for Office abuse behaviors.
Day 5–7: Lessons learned and coverage review:
· Confirm telemetry retention,
· Validate incident response playbooks,
· Update user awareness messaging for document/web lures.
References
CISA KEV catalog
KEV List
· hxxps://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-21510
· hxxps://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-21513
· hxxps://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-21514
· hxxps://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-21519
· hxxps://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-21525
· hxxps://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-21533
NVD
· hxxps://nvd.nist.gov/vuln/detail/ CVE-2026-21510
· hxxps://nvd.nist.gov/vuln/detail/ CVE-2026-21513
· hxxps://nvd.nist.gov/vuln/detail/ CVE-2026-21514
· hxxps://nvd.nist.gov/vuln/detail/ CVE-2026-21519
· hxxps://nvd.nist.gov/vuln/detail/CVE-2026-21533
· hxxps://nvd.nist.gov/vuln/detail/CVE-2026-21514